Table of Contents
- USG/ZyWALL Series
- User’s Guide
- Introduction
- Initial Setup Wizard
- 2.1 Initial Setup Wizard Screens
- 2.1.1 Internet Access Setup - WAN Interface
- 2.1.2 Internet Access: Ethernet
- 2.1.3 Internet Access: PPPoE
- 2.1.4 Internet Access: PPTP
- 2.1.5 Internet Access: L2TP
- 2.1.6 Internet Access Setup - Second WAN Interface
- 2.1.7 Internet Access: Finish
- 2.1.8 Date and Time Settings
- 2.1.9 Register Device
- 2.1.10 Activate Service
- 2.1.11 Wireless Settings: AP Controller
- 2.1.12 Wireless Settings: SSID & Security
- 2.1 Initial Setup Wizard Screens
- Hardware, Interfaces and Zones
- Easy Mode
- 4.1 Overview
- 4.2 Initial Setup Wizard - Language and Overview
- 4.3 Initial Setup Wizard - Security Service
- 4.4 Initial Setup Wizard - Port Forwarding
- 4.5 Initial Setup Wizard - Guest LAN
- 4.6 Initial Setup Wizard - VPN
- 4.6.1 VPN Setup Wizard: Wizard Type
- 4.6.2 VPN Express Wizard - Scenario
- 4.6.3 VPN Express Wizard - Configuration
- 4.6.4 VPN Express Wizard - Summary
- 4.6.5 VPN Express Wizard - Finish
- 4.6.6 VPN Advanced Wizard - Scenario
- 4.6.7 VPN Advanced Wizard - Phase 1 Settings
- 4.6.8 VPN Advanced Wizard - Phase 2
- 4.6.9 VPN Advanced Wizard - Summary
- 4.6.10 VPN Advanced Wizard - Finish
- 4.7 VPN Settings for Configuration Provisioning Wizard: Wizard Type
- 4.7.1 Configuration Provisioning Express Wizard - VPN Settings
- 4.7.2 Configuration Provisioning VPN Express Wizard - Configuration
- 4.7.3 VPN Settings for Configuration Provisioning Express Wizard - Summary
- 4.7.4 VPN Settings for Configuration Provisioning Express Wizard - Finish
- 4.7.5 VPN Settings for Configuration Provisioning Advanced Wizard - Scenario
- 4.7.6 VPN Settings for Configuration Provisioning Advanced Wizard - Phase 1 Settings
- 4.7.7 VPN Settings for Configuration Provisioning Advanced Wizard - Phase 2
- 4.7.8 VPN Settings for Configuration Provisioning Advanced Wizard - Summary
- 4.7.9 VPN Settings for Configuration Provisioning Advanced Wizard- Finish
- 4.8 VPN Settings for L2TP VPN Settings Wizard
- 4.9 Port Forwarding
- 4.10 Wi-Fi and Guest Network Wizard
- 4.11 Security Service Wizard
- 4.12 MyZyxel Portal
- 4.13 One Security Portal
- Quick Setup Wizards
- 5.1 Quick Setup Overview
- 5.2 WAN Interface Quick Setup
- 5.3 VPN Setup Wizard
- 5.3.1 Welcome
- 5.3.2 VPN Setup Wizard: Wizard Type
- 5.3.3 VPN Express Wizard - Scenario
- 5.3.4 VPN Express Wizard - Configuration
- 5.3.5 VPN Express Wizard - Summary
- 5.3.6 VPN Express Wizard - Finish
- 5.3.7 VPN Advanced Wizard - Scenario
- 5.3.8 VPN Advanced Wizard - Phase 1 Settings
- 5.3.9 VPN Advanced Wizard - Phase 2
- 5.3.10 VPN Advanced Wizard - Summary
- 5.3.11 VPN Advanced Wizard - Finish
- 5.4 VPN Settings for Configuration Provisioning Wizard: Wizard Type
- 5.4.1 Configuration Provisioning Express Wizard - VPN Settings
- 5.4.2 Configuration Provisioning VPN Express Wizard - Configuration
- 5.4.3 VPN Settings for Configuration Provisioning Express Wizard - Summary
- 5.4.4 VPN Settings for Configuration Provisioning Express Wizard - Finish
- 5.4.5 VPN Settings for Configuration Provisioning Advanced Wizard - Scenario
- 5.4.6 VPN Settings for Configuration Provisioning Advanced Wizard - Phase 1 Settings
- 5.4.7 VPN Settings for Configuration Provisioning Advanced Wizard - Phase 2
- 5.4.8 VPN Settings for Configuration Provisioning Advanced Wizard - Summary
- 5.4.9 VPN Settings for Configuration Provisioning Advanced Wizard- Finish
- 5.5 VPN Settings for L2TP VPN Settings Wizard
- Dashboard
- 6.1 Overview
- 6.2 Main Dashboard Screen
- 6.2.1 Device Information Screen
- 6.2.2 System Status Screen
- 6.2.3 VPN Status Screen
- 6.2.4 DHCP Table Screen
- 6.2.5 Number of Login Users Screen
- 6.2.6 System Resources Screen
- 6.2.7 CPU Usage Screen
- 6.2.8 Memory Usage Screen
- 6.2.9 Active Sessions Screen
- 6.2.10 Extension Slot Screen
- 6.2.11 Interface Status Summary Screen
- 6.2.12 Secured Service Status Screen
- 6.2.13 Content Filter Statistics Screen
- 6.2.14 Top 5 Viruses Screen
- 6.2.15 Top 5 Intrusions Screen
- 6.2.16 Top 5 IPv4/IPv6 Security Policy Rules that Blocked Traffic Screen
- 6.2.17 The Latest Alert Logs Screen
- Technical Reference
- Monitor
- 7.1 Overview
- 7.2 The Port Statistics Screen
- 7.3 Interface Status Screen
- 7.4 The Traffic Statistics Screen
- 7.5 The Session Monitor Screen
- 7.6 IGMP Statistics
- 7.7 The DDNS Status Screen
- 7.8 IP/MAC Binding
- 7.9 The Login Users Screen
- 7.10 The Dynamic Guest Screen
- 7.11 Cellular Status Screen
- 7.12 The UPnP Port Status Screen
- 7.13 USB Storage Screen
- 7.14 Ethernet Neighbor Screen
- 7.15 Wireless
- 7.16 The Printer Status Screen
- 7.17 The IPSec Monitor Screen
- 7.18 The SSL Screen
- 7.19 The L2TP over IPSec Session Monitor Screen
- 7.20 The App Patrol Screen
- 7.21 The Content Filter Screen
- 7.22 The IDP Screen
- 7.23 The Anti-Virus Screen
- 7.24 The Anti-Spam Screens
- 7.25 The SSL Inspection Screens
- 7.26 Log Screens
- Licensing
- Wireless
- Interfaces
- 10.1 Interface Overview
- 10.2 Port Role
- 10.3 Port Group
- 10.4 Ethernet Summary Screen
- 10.5 PPP Interfaces
- 10.6 Cellular Configuration Screen
- 10.7 Tunnel Interfaces
- 10.8 VLAN Interfaces
- 10.9 Bridge Interfaces
- 10.10 LAG
- 10.11 VTI
- 10.12 Trunk Overview
- 10.13 The Trunk Summary Screen
- 10.14 Interface Technical Reference
- Routing
- DDNS
- NAT
- Redirect Service
- ALG
- UPnP
- IP/MAC Binding
- Layer 2 Isolation
- DNS Inbound LB
- Web Authentication
- Hotspot
- Printer Manager
- Free Time
- SMS
- IPnP
- Walled Garden
- Advertisement Screen
- Security Policy
- Cloud CNM
- IPSec VPN
- SSL VPN
- SSL User Screens
- Zyxel Device SecuExtender (Windows)
- L2TP VPN
- BWM (Bandwidth Management)
- Application Patrol
- Content Filtering
- IDP
- Anti-Virus
- Anti-Spam
- SSL Inspection
- Device HA
- Object
- 43.1 Zones Overview
- 43.2 User/Group Overview
- 43.3 AP Profile Overview
- 43.4 MON Profile
- 43.5 Application
- 43.6 Address/Geo IP Overview
- 43.7 Service Overview
- 43.8 Schedule Overview
- 43.9 AAA Server Overview
- 43.10 Auth. Method Overview
- 43.11 Certificate Overview
- 43.12 ISP Account Overview
- 43.13 SSL Application Overview
- 43.14 DHCPv6 Overview
- System
- 44.1 Overview
- 44.2 Host Name
- 44.3 USB Storage
- 44.4 Date and Time
- 44.5 Console Port Speed
- 44.6 DNS Overview
- 44.6.1 DNS Server Address Assignment
- 44.6.2 Configuring the DNS Screen
- 44.6.3 (IPv6) Address Record
- 44.6.4 PTR Record
- 44.6.5 Adding an (IPv6) Address/PTR Record
- 44.6.6 CNAME Record
- 44.6.7 Adding a CNAME Record
- 44.6.8 Domain Zone Forwarder
- 44.6.9 Adding a Domain Zone Forwarder
- 44.6.10 MX Record
- 44.6.11 Adding a MX Record
- 44.6.12 Security Option Control
- 44.6.13 Editing a Security Option Control
- 44.6.14 Adding a DNS Service Control Rule
- 44.7 WWW Overview
- 44.8 SSH
- 44.9 Telnet
- 44.10 FTP
- 44.11 SNMP
- 44.12 Authentication Server
- 44.13 Language Screen
- 44.14 IPv6 Screen
- 44.15 Zyxel One Network (ZON) Utility
- Log and Report
- File Manager
- Diagnostics
- Packet Flow Explore
- Shutdown
- Troubleshooting
- Customer Support
- Legal Information
- Product Features
- Index
- Monitor
Zyxel ZyWALL 1100 User Manual
Displayed below is the user manual for ZyWALL 1100 by Zyxel which is a product in the Hardware Firewalls category. This manual has pages.
Related Manuals

Default Login Details
User’s Guide
USG/ZyWALL Series
Copyright © 2017 Zyxel Communications Corporation
LAN Port IP Address https://192.168.1.1
User Name admin
Password 1234
Version 4.25 Edition 1, 3/2017
IMPORTANT!
READ CAREFULLY BEFORE USE.
KEEP THIS GUIDE FOR FUTURE REFERENCE.
This is a User’s Guide for a series of products. Not all products support all firmware features.
Screenshots and graphics in this book may differ slightly from your product due to differences in
your product firmware or your computer operating system. Every effort has been made to ensure
that the information in this manual is accurate.
Related Documentation
•Quick Start Guide
The Quick Start Guide shows how to connect the Zyxel Device and access the Web Configurator
wizards. (See the wizard real time help for information on configuring each screen.) It also contains a
connection diagram and package contents list.
•CLI Reference Guide
The CLI Reference Guide explains how to use the Command-Line Interface (CLI) to configure the
Zyxel Device.
Note: It is recommended you use the Web Configurator to configure the Zyxel Device.
• Web Configurator Online Help
Click the help icon in any screen for help in configuring that screen and supplementary information.
•More Information
Go to support.zyxel.com to find other information on Zyxel Device.

USG/ZyWALL User’s Guide
3
Part I: User’s Guide..........................................................................................23
Chapter 1
Introduction ........................................................................................................................................24
1.1 Overview ......................................................................................................................................... 24
1.2 Registration at myZyxel.com ......................................................................................................... 25
1.2.1 Grace Period ......................................................................................................................... 26
1.2.2 Applications ........................................................................................................................... 26
1.3 Management Overview ................................................................................................................ 29
1.4 Web Configurator ........................................................................................................................... 30
1.4.1 Web Configurator Access .................................................................................................... 31
1.4.2 Web Configurator Screens Overview ................................................................................. 33
1.4.3 Navigation Panel .................................................................................................................. 37
1.4.4 Tables and Lists ...................................................................................................................... 44
Chapter 2
Initial Setup Wizard.............................................................................................................................47
2.1 Initial Setup Wizard Screens .......................................................................................................... 47
2.1.1 Internet Access Setup - WAN Interface ............................................................................. 48
2.1.2 Internet Access: Ethernet .................................................................................................... 49
2.1.3 Internet Access: PPPoE ......................................................................................................... 50
2.1.4 Internet Access: PPTP ........................................................................................................... 52
2.1.5 Internet Access: L2TP ............................................................................................................ 53
2.1.6 Internet Access Setup - Second WAN Interface ............................................................... 54
2.1.7 Internet Access: Finish .......................................................................................................... 55
2.1.8 Date and Time Settings ........................................................................................................ 55
2.1.9 Register Device ..................................................................................................................... 56
2.1.10 Activate Service .................................................................................................................. 57
2.1.11 Wireless Settings: AP Controller ......................................................................................... 59
2.1.12 Wireless Settings: SSID & Security ...................................................................................... 59
Chapter 3
Hardware, Interfaces and Zones......................................................................................................61
3.1 Hardware Overview ....................................................................................................................... 61
3.1.1 Front Panels ............................................................................................................................ 61
3.1.2 Rear Panels ............................................................................................................................ 65
3.2 Mounting ......................................................................................................................................... 67
3.2.1 Rack-mounting ...................................................................................................................... 67
3.2.2 USG2200-VPN Rack Mounting ............................................................................................. 68
3.2.3 Wall-mounting ....................................................................................................................... 71
3.3 Default Zones, Interfaces, and Ports ............................................................................................ 72
3.4 Stopping the Zyxel Device ............................................................................................................ 74

USG/ZyWALL User’s Guide
4
Chapter 4
Easy Mode..........................................................................................................................................75
4.1 Overview ........................................................................................................................................ 75
4.1.1 Wizards and Links .................................................................................................................. 75
4.1.2 Easy Mode Settings ............................................................................................................... 76
4.1.3 Easy Mode Dashboard ......................................................................................................... 77
4.2 Initial Setup Wizard - Language and Overview ........................................................................ 80
4.2.1 Initial Setup Wizard - Internet ........................................................................................... 81
4.2.2 Initial Setup Wizard - Internet Access Errors ..................................................................... 82
4.2.3 Initial Setup Wizard - Date and Time ................................................................................ 83
4.2.4 Initial Setup Wizard - Register Device .............................................................................. 84
4.2.5 Initial Setup Wizard - Activate Services ............................................................................ 85
4.2.6 Initial Setup Wizard - Wi-Fi .................................................................................................. 87
4.2.7 Initial Setup Wizard - Congratulations .............................................................................. 88
4.3 Initial Setup Wizard - Security Service ....................................................................................... 89
4.4 Initial Setup Wizard - Port Forwarding ......................................................................................... 91
4.5 Initial Setup Wizard - Guest LAN ................................................................................................. 92
4.5.1 Connecting AP Scenarios .................................................................................................... 94
4.6 Initial Setup Wizard - VPN ............................................................................................................. 96
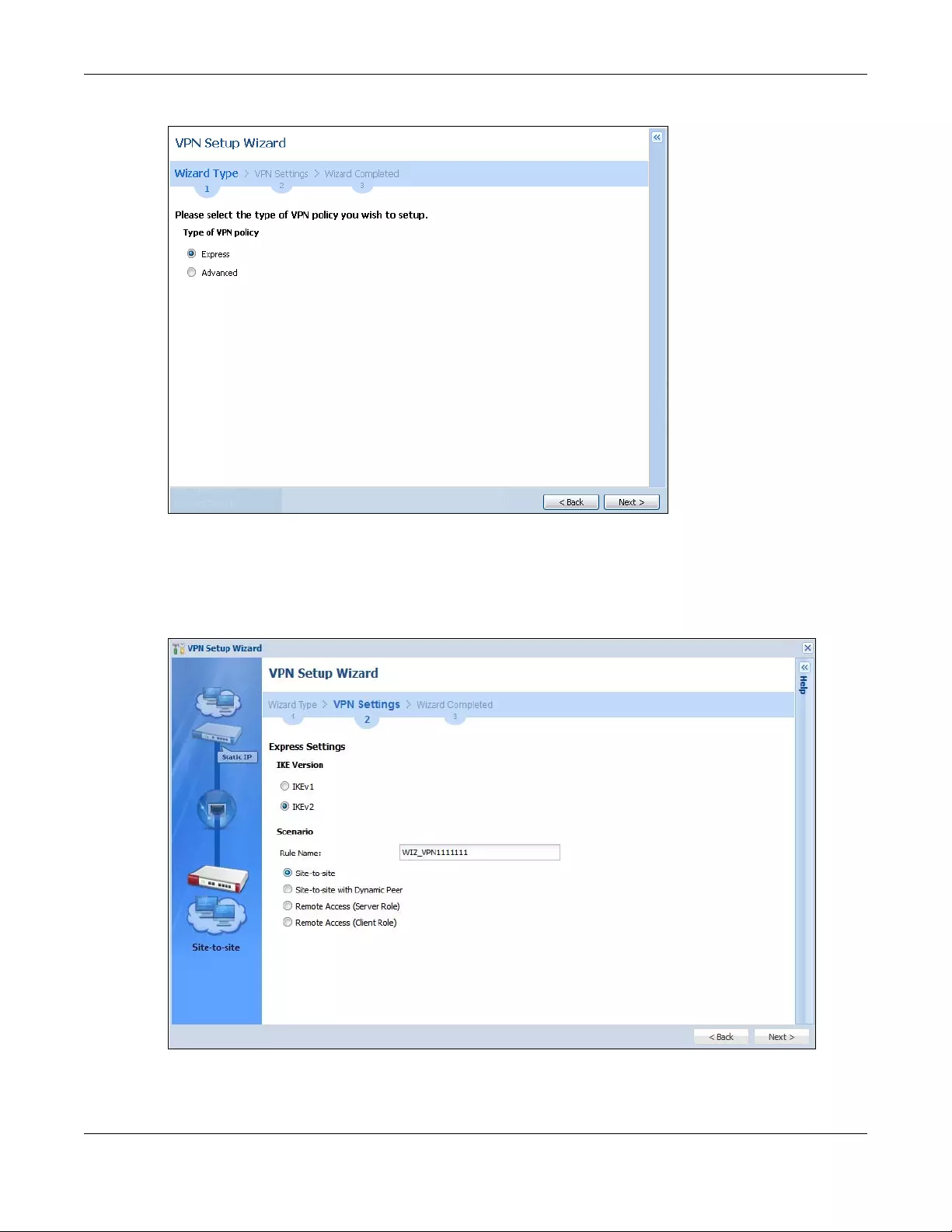
4.6.1 VPN Setup Wizard: Wizard Type ........................................................................................ 97
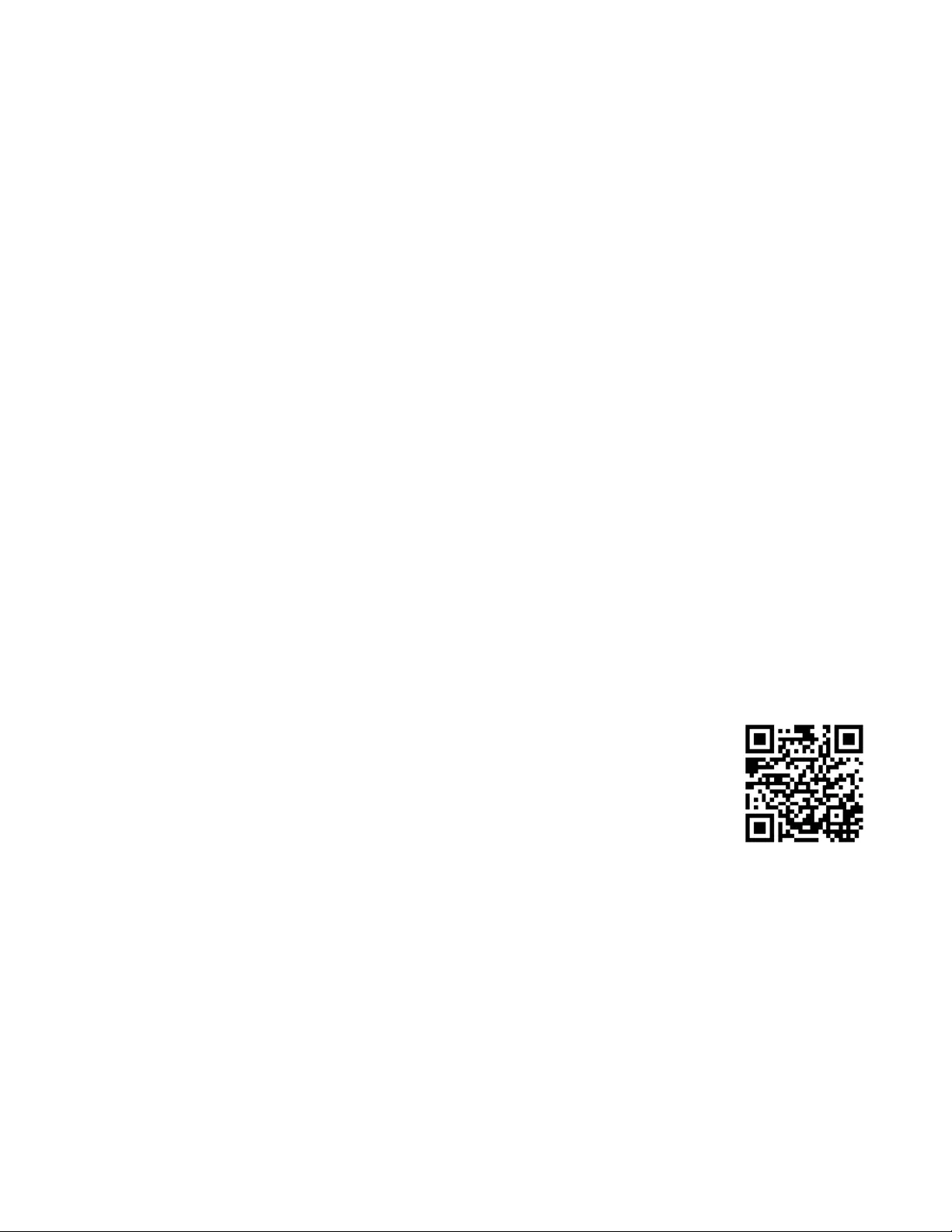
4.6.2 VPN Express Wizard - Scenario ........................................................................................... 97
4.6.3 VPN Express Wizard - Configuration .................................................................................. 99
4.6.4 VPN Express Wizard - Summary .......................................................................................... 99
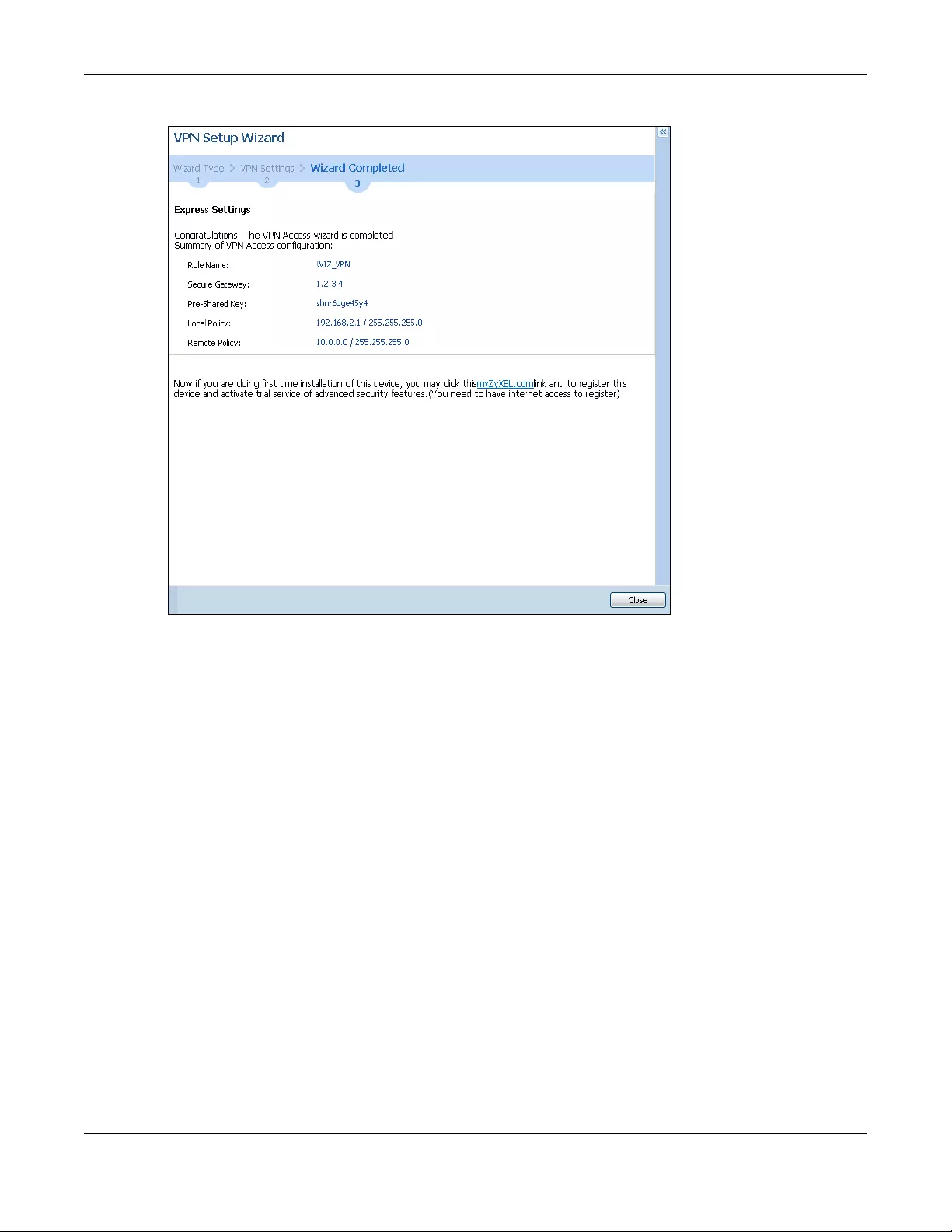
4.6.5 VPN Express Wizard - Finish ............................................................................................... 100
4.6.6 VPN Advanced Wizard - Scenario .................................................................................. 101
4.6.7 VPN Advanced Wizard - Phase 1 Settings ..................................................................... 102
4.6.8 VPN Advanced Wizard - Phase 2 .................................................................................... 104
4.6.9 VPN Advanced Wizard - Summary ................................................................................. 105
4.6.10 VPN Advanced Wizard - Finish ...................................................................................... 106
4.7 VPN Settings for Configuration Provisioning Wizard: Wizard Type ......................................... 106
4.7.1 Configuration Provisioning Express Wizard - VPN Settings ............................................ 107
4.7.2 Configuration Provisioning VPN Express Wizard - Configuration ................................. 108
4.7.3 VPN Settings for Configuration Provisioning Express Wizard - Summary ..................... 109
4.7.4 VPN Settings for Configuration Provisioning Express Wizard - Finish .............................. 110
4.7.5 VPN Settings for Configuration Provisioning Advanced Wizard - Scenario ................ 111
4.7.6 VPN Settings for Configuration Provisioning Advanced Wizard - Phase 1 Settings .... 112
4.7.7 VPN Settings for Configuration Provisioning Advanced Wizard - Phase 2 ................. 113
4.7.8 VPN Settings for Configuration Provisioning Advanced Wizard - Summary ............... 114
4.7.9 VPN Settings for Configuration Provisioning Advanced Wizard- Finish ....................... 116
4.8 VPN Settings for L2TP VPN Settings Wizard ............................................................................... 117
4.8.1 L2TP VPN Settings 1 ............................................................................................................. 118
4.8.2 L2TP VPN Settings 2 ............................................................................................................ 119
4.8.3 VPN Settings for L2TP VPN Setting Wizard - Summary ................................................... 120

USG/ZyWALL User’s Guide
5
4.8.4 VPN Settings for L2TP VPN Setting Wizard Completed .................................................. 121
4.9 Port Forwarding ........................................................................................................................... 122
4.9.1 Port Forwarding > Add Client .......................................................................................... 123
4.9.2 Port Forwarding > Add Service ........................................................................................ 123
4.9.3 Port Forwarding > UPnP .................................................................................................... 123
4.10 Wi-Fi and Guest Network Wizard ........................................................................................... 125
4.10.1 Guest LAN (Wired Network) ........................................................................................... 126
4.10.2 Connecting AP Scenarios ................................................................................................ 127
4.11 Security Service Wizard .......................................................................................................... 128
4.11.1 Security Service Wizard 2 - Content Filter Categories ............................................... 130
4.11.2 Security Service Wizard 3 - Websites ........................................................................... 132
4.11.3 Security Service Wizard 4 - Exemptions ...................................................................... 133
4.11.4 Security Service Wizard 5 - IDP/AV .............................................................................. 134
4.12 MyZyxel Portal ......................................................................................................................... 135
4.13 One Security Portal ................................................................................................................. 136
Chapter 5
Quick Setup Wizards........................................................................................................................138
5.1 Quick Setup Overview ................................................................................................................. 138
5.2 WAN Interface Quick Setup ........................................................................................................ 139
5.2.1 Choose an Ethernet Interface ........................................................................................... 139
5.2.2 Select WAN Type ................................................................................................................. 140
5.2.3 Configure WAN IP Settings ................................................................................................. 140
5.2.4 ISP and WAN and ISP Connection Settings ...................................................................... 141
5.2.5 Quick Setup Interface Wizard: Summary ......................................................................... 144
5.3 VPN Setup Wizard ......................................................................................................................... 145
5.3.1 Welcome .............................................................................................................................. 145
5.3.2 VPN Setup Wizard: Wizard Type ........................................................................................ 146
5.3.3 VPN Express Wizard - Scenario .......................................................................................... 147
5.3.4 VPN Express Wizard - Configuration ................................................................................. 148
5.3.5 VPN Express Wizard - Summary ......................................................................................... 149
5.3.6 VPN Express Wizard - Finish ................................................................................................ 150
5.3.7 VPN Advanced Wizard - Scenario ................................................................................... 150
5.3.8 VPN Advanced Wizard - Phase 1 Settings ...................................................................... 152
5.3.9 VPN Advanced Wizard - Phase 2 ..................................................................................... 153
5.3.10 VPN Advanced Wizard - Summary ................................................................................ 154
5.3.11 VPN Advanced Wizard - Finish ....................................................................................... 154
5.4 VPN Settings for Configuration Provisioning Wizard: Wizard Type ........................................... 155
5.4.1 Configuration Provisioning Express Wizard - VPN Settings ............................................. 156
5.4.2 Configuration Provisioning VPN Express Wizard - Configuration .................................. 157
5.4.3 VPN Settings for Configuration Provisioning Express Wizard - Summary ...................... 158
5.4.4 VPN Settings for Configuration Provisioning Express Wizard - Finish .............................. 159
5.4.5 VPN Settings for Configuration Provisioning Advanced Wizard - Scenario ................. 160

USG/ZyWALL User’s Guide
6
5.4.6 VPN Settings for Configuration Provisioning Advanced Wizard - Phase 1 Settings .... 161
5.4.7 VPN Settings for Configuration Provisioning Advanced Wizard - Phase 2 .................. 162
5.4.8 VPN Settings for Configuration Provisioning Advanced Wizard - Summary ................ 163
5.4.9 VPN Settings for Configuration Provisioning Advanced Wizard- Finish ........................ 165
5.5 VPN Settings for L2TP VPN Settings Wizard ................................................................................. 166
5.5.1 L2TP VPN Settings ................................................................................................................ 167
5.5.2 L2TP VPN Settings ................................................................................................................ 168
5.5.3 VPN Settings for L2TP VPN Setting Wizard - Summary .................................................... 169
5.5.4 VPN Settings for L2TP VPN Setting Wizard Completed ................................................... 170
Chapter 6
Dashboard........................................................................................................................................171
6.1 Overview ....................................................................................................................................... 171
6.1.1 What You Can Do in this Chapter ..................................................................................... 171
6.2 Main Dashboard Screen .............................................................................................................. 171
6.2.1 Device Information Screen ................................................................................................173
6.2.2 System Status Screen .......................................................................................................... 174
6.2.3 VPN Status Screen ............................................................................................................... 175
6.2.4 DHCP Table Screen ............................................................................................................. 177
6.2.5 Number of Login Users Screen ........................................................................................... 178
6.2.6 System Resources Screen ................................................................................................... 178
6.2.7 CPU Usage Screen .............................................................................................................. 179
6.2.8 Memory Usage Screen ....................................................................................................... 180
6.2.9 Active Sessions Screen ....................................................................................................... 181
6.2.10 Extension Slot Screen ........................................................................................................ 182
6.2.11 Interface Status Summary Screen ................................................................................... 182
6.2.12 Secured Service Status Screen ........................................................................................ 184
6.2.13 Content Filter Statistics Screen ......................................................................................... 184
6.2.14 Top 5 Viruses Screen ......................................................................................................... 185
6.2.15 Top 5 Intrusions Screen ..................................................................................................... 186
6.2.16 Top 5 IPv4/IPv6 Security Policy Rules that Blocked Traffic Screen ............................... 186
6.2.17 The Latest Alert Logs Screen ............................................................................................187
Part II: Technical Reference.........................................................................188
Chapter 7
Monitor..............................................................................................................................................189
7.1 Overview ....................................................................................................................................... 189
7.1.1 What You Can Do in this Chapter ..................................................................................... 189
7.2 The Port Statistics Screen ............................................................................................................ 190
7.2.1 The Port Statistics Graph Screen ....................................................................................... 191

USG/ZyWALL User’s Guide
7
7.3 Interface Status Screen ................................................................................................................ 192
7.4 The Traffic Statistics Screen .......................................................................................................... 195
7.5 The Session Monitor Screen ........................................................................................................ 198
7.6 IGMP Statistics ............................................................................................................................... 199
7.7 The DDNS Status Screen ............................................................................................................... 200
7.8 IP/MAC Binding ............................................................................................................................. 201
7.9 The Login Users Screen ................................................................................................................ 201
7.10 The Dynamic Guest Screen ...................................................................................................... 202
7.11 Cellular Status Screen ................................................................................................................ 204
7.11.1 More Information .............................................................................................................. 206
7.12 The UPnP Port Status Screen ..................................................................................................... 207
7.13 USB Storage Screen .................................................................................................................... 208
7.14 Ethernet Neighbor Screen ........................................................................................................ 209
7.15 Wireless ........................................................................................................................................ 210
7.15.1 Wireless AP Information: AP List ....................................................................................... 210
7.15.2 AP List More Information ................................................................................................. 212
7.15.3 Config AP .......................................................................................................................... 214
7.15.4 Wireless AP Information: Radio List .................................................................................. 215
7.15.5 Radio List More Information .............................................................................................217
7.15.6 Wireless Station Info .......................................................................................................... 218
7.15.7 Detected Device ............................................................................................................. 219
7.16 The Printer Status Screen ........................................................................................................... 220
7.17 The IPSec Monitor Screen .......................................................................................................... 221
7.17.1 Regular Expressions in Searching IPSec SAs ................................................................... 222
7.18 The SSL Screen ............................................................................................................................. 222
7.19 The L2TP over IPSec Session Monitor Screen ............................................................................ 223
7.20 The App Patrol Screen ............................................................................................................... 223
7.21 The Content Filter Screen .......................................................................................................... 225
7.22 The IDP Screen ............................................................................................................................ 226
7.23 The Anti-Virus Screen .................................................................................................................. 228
7.24 The Anti-Spam Screens .............................................................................................................. 230
7.24.1 Anti-Spam Report .............................................................................................................. 230
7.24.2 The Anti-Spam Status Screen ........................................................................................... 232
7.25 The SSL Inspection Screens ........................................................................................................ 234
7.25.1 Certificate Cache List ....................................................................................................... 235
7.26 Log Screens ................................................................................................................................. 236
7.26.1 View Log ............................................................................................................................ 236
7.26.2 View AP Log ....................................................................................................................... 238
7.26.3 Dynamic Users Log ............................................................................................................ 240
Chapter 8
Licensing...........................................................................................................................................242
8.1 Registration Overview .................................................................................................................. 242

USG/ZyWALL User’s Guide
8
8.1.1 What you Need to Know ....................................................................................................242
8.1.2 Registration Screen ............................................................................................................. 242
8.1.3 Service Screen ..................................................................................................................... 243
8.2 Signature Update ......................................................................................................................... 245
8.2.1 What you Need to Know ....................................................................................................245
8.2.2 The Anti-Virus Update Screen ............................................................................................ 245
8.2.3 The IDP/AppPatrol Update Screen ................................................................................... 246
Chapter 9
Wireless .............................................................................................................................................249
9.1 Overview ....................................................................................................................................... 249
9.1.1 What You Can Do in this Chapter ..................................................................................... 249
9.2 Controller Screen ......................................................................................................................... 249
9.3 AP Management Screens ........................................................................................................... 250
9.3.1 Mgnt. AP List ....................................................................................................................... 250
9.3.2 AP Policy .............................................................................................................................. 254
9.3.3 AP Group ............................................................................................................................. 255
9.3.4 Firmware ............................................................................................................................... 259
9.4 MON Mode ................................................................................................................................... 261
9.4.1 Add/Edit Rogue/Friendly List .............................................................................................. 262
9.5 Auto Healing ................................................................................................................................. 263
9.6 RTLS Overview ............................................................................................................................... 264
9.6.1 What You Can Do in this Chapter ..................................................................................... 265
9.6.2 Before You Begin ................................................................................................................. 265
9.6.3 Configuring RTLS .................................................................................................................. 265
9.7 Technical Reference .................................................................................................................... 266
9.7.1 Dynamic Channel Selection .............................................................................................. 266
9.7.2 Load Balancing ................................................................................................................... 267
Chapter 10
Interfaces..........................................................................................................................................269
10.1 Interface Overview .................................................................................................................... 269
10.1.1 What You Can Do in this Chapter ................................................................................... 269
10.1.2 What You Need to Know ................................................................................................. 270
10.1.3 What You Need to Do First ...............................................................................................274
10.2 Port Role ....................................................................................................................................... 274
10.3 Port Group ................................................................................................................................... 275
10.4 Ethernet Summary Screen ......................................................................................................... 276
10.4.1 Ethernet Edit ...................................................................................................................... 278
10.4.2 Virtual Interfaces .............................................................................................................. 293
10.4.3 Virtual Interfaces Add/Edit ............................................................................................... 293
10.4.4 Object References ............................................................................................................ 294
10.4.5 Add/Edit DHCPv6 Request/Release Options ................................................................. 295

USG/ZyWALL User’s Guide
9
10.4.6 Add/Edit DHCP Extended Options ................................................................................. 295
10.5 PPP Interfaces ............................................................................................................................. 297
10.5.1 PPP Interface Summary .................................................................................................... 298
10.5.2 PPP Interface Add or Edit ................................................................................................ 299
10.6 Cellular Configuration Screen ................................................................................................... 304
10.6.1 Cellular Choose Slot ......................................................................................................... 307
10.6.2 Add / Edit Cellular Configuration .................................................................................... 307
10.7 Tunnel Interfaces ........................................................................................................................ 313
10.7.1 Configuring a Tunnel ........................................................................................................ 315
10.7.2 Tunnel Add or Edit Screen ................................................................................................ 316
10.8 VLAN Interfaces ......................................................................................................................... 319
10.8.1 VLAN Summary Screen .....................................................................................................321
10.8.2 VLAN Add/Edit ................................................................................................................. 322
10.9 Bridge Interfaces ........................................................................................................................ 333
10.9.1 Bridge Summary ................................................................................................................ 334
10.9.2 Bridge Add/Edit ................................................................................................................ 336
10.10 LAG ............................................................................................................................................ 344
10.10.1 LAG Summary Screen .....................................................................................................345
10.10.2 LAG Add/Edit ................................................................................................................. 346
10.11 VTI ............................................................................................................................................... 352
10.11.1 Restrictions for IPSec Virtual Tunnel Interface .............................................................. 352
10.11.2 VTI Screen ........................................................................................................................ 352
10.11.3 VTI Add/Edit ..................................................................................................................... 353
10.12 Trunk Overview ......................................................................................................................... 355
10.12.1 What You Need to Know ............................................................................................... 356
10.13 The Trunk Summary Screen ...................................................................................................... 358
10.13.1 Configuring a User-Defined Trunk ................................................................................. 360
10.13.2 Configuring the System Default Trunk .......................................................................... 362
10.14 Interface Technical Reference ............................................................................................... 363
Chapter 11
Routing..............................................................................................................................................367
11.1 Policy and Static Routes Overview ........................................................................................... 367
11.1.1 What You Can Do in this Chapter ................................................................................... 367
11.1.2 What You Need to Know ................................................................................................ 368
11.2 Policy Route Screen ................................................................................................................... 369
11.2.1 Policy Route Edit Screen .................................................................................................. 371
11.3 IP Static Route Screen ................................................................................................................ 376
11.3.1 Static Route Add/Edit Screen .......................................................................................... 376
11.4 Policy Routing Technical Reference ........................................................................................378
11.5 Routing Protocols Overview ..................................................................................................... 378
11.5.1 What You Need to Know ................................................................................................. 379
11.6 The RIP Screen ............................................................................................................................. 379

USG/ZyWALL User’s Guide
10
11.7 The OSPF Screen ......................................................................................................................... 381
11.7.1 Configuring the OSPF Screen .......................................................................................... 384
11.7.2 OSPF Area Add/Edit Screen ........................................................................................... 385
11.7.3 Virtual Link Add/Edit Screen ...........................................................................................387
11.8 Routing Protocol Technical Reference .................................................................................... 388
Chapter 12
DDNS ...............................................................................................................................................389
12.1 DDNS Overview ........................................................................................................................... 389
12.1.1 What You Can Do in this Chapter ................................................................................... 389
12.1.2 What You Need to Know ................................................................................................. 389
12.2 The DDNS Screen ........................................................................................................................ 390
12.2.1 The Dynamic DNS Add/Edit Screen ................................................................................ 391
Chapter 13
NAT ....................................................................................................................................................395
13.1 NAT Overview ............................................................................................................................. 395
13.1.1 What You Can Do in this Chapter ................................................................................... 395
13.1.2 What You Need to Know ................................................................................................. 395
13.2 The NAT Screen ........................................................................................................................... 395
13.2.1 The NAT Add/Edit Screen .................................................................................................397
13.3 NAT Technical Reference .......................................................................................................... 400
Chapter 14
Redirect Service...............................................................................................................................402
14.1 Overview ..................................................................................................................................... 402
14.1.1 HTTP Redirect ..................................................................................................................... 402
14.1.2 SMTP Redirect .................................................................................................................... 402
14.1.3 What You Can Do in this Chapter ................................................................................... 403
14.1.4 What You Need to Know ................................................................................................. 403
14.2 The Redirect Service Screen ..................................................................................................... 405
14.2.1 The Redirect Service Edit Screen ..................................................................................... 406
Chapter 15
ALG....................................................................................................................................................408
15.1 ALG Overview ............................................................................................................................. 408
15.1.1 What You Need to Know ................................................................................................. 408
15.1.2 Before You Begin ............................................................................................................... 411
15.2 The ALG Screen .......................................................................................................................... 411
15.3 ALG Technical Reference ......................................................................................................... 414
Chapter 16
UPnP...................................................................................................................................................416

USG/ZyWALL User’s Guide
11
16.1 UPnP and NAT-PMP Overview ................................................................................................... 416
16.2 What You Need to Know ........................................................................................................... 416
16.2.1 NAT Traversal ..................................................................................................................... 416
16.2.2 Cautions with UPnP and NAT-PMP .................................................................................. 417
16.3 UPnP Screen ................................................................................................................................ 417
16.4 Technical Reference .................................................................................................................. 418
16.4.1 Turning on UPnP in Windows 7 Example ......................................................................... 418
16.4.2 Using UPnP in Windows XP Example ................................................................................ 420
16.4.3 Web Configurator Easy Access ....................................................................................... 422
Chapter 17
IP/MAC Binding................................................................................................................................425
17.1 IP/MAC Binding Overview ......................................................................................................... 425
17.1.1 What You Can Do in this Chapter ................................................................................... 425
17.1.2 What You Need to Know ................................................................................................. 425
17.2 IP/MAC Binding Summary ......................................................................................................... 426
17.2.1 IP/MAC Binding Edit .......................................................................................................... 426
17.2.2 Static DHCP Edit ................................................................................................................ 427
17.3 IP/MAC Binding Exempt List ....................................................................................................... 428
Chapter 18
Layer 2 Isolation...............................................................................................................................430
18.1 Overview ..................................................................................................................................... 430
18.1.1 What You Can Do in this Chapter ................................................................................... 430
18.2 Layer-2 Isolation General Screen ............................................................................................. 430
18.3 White List Screen ......................................................................................................................... 431
18.3.1 Add/Edit White List Rule ................................................................................................... 432
Chapter 19
DNS Inbound LB................................................................................................................................434
19.1 DNS Inbound Load Balancing Overview ................................................................................. 434
19.1.1 What You Can Do in this Chapter ................................................................................... 434
19.2 The DNS Inbound LB Screen ...................................................................................................... 435
19.2.1 The DNS Inbound LB Add/Edit Screen ............................................................................ 436
19.2.2 The DNS Inbound LB Add/Edit Member Screen ............................................................ 438
Chapter 20
Web Authentication ........................................................................................................................440
20.1 Web Auth Overview ................................................................................................................... 440
20.1.1 What You Can Do in this Chapter ................................................................................... 440
20.1.2 What You Need to Know ................................................................................................. 441
20.2 Web Authentication General Screen ...................................................................................... 441
20.2.1 User-aware Access Control Example ............................................................................. 446

USG/ZyWALL User’s Guide
12
20.2.2 Authentication Type Screen ............................................................................................ 451
20.2.3 Custom Web Portal / User Agreement File Screen ....................................................... 455
20.3 SSO Overview .............................................................................................................................. 457
20.4 SSO - Zyxel Device Configuration ............................................................................................. 458
20.4.1 Configuration Overview ................................................................................................... 458
20.4.2 Configure the Zyxel Device to Communicate with SSO .............................................. 459
20.4.3 Enable Web Authentication ............................................................................................ 460
20.4.4 Create a Security Policy ................................................................................................... 461
20.4.5 Configure User Information ..............................................................................................461
20.4.6 Configure an Authentication Method ........................................................................... 462
20.4.7 Configure Active Directory ..............................................................................................463
20.5 SSO Agent Configuration .......................................................................................................... 464
Chapter 21
Hotspot..............................................................................................................................................468
21.1 Overview ..................................................................................................................................... 468
21.2 Billing Overview ........................................................................................................................... 468
21.2.1 What You Need to Know ................................................................................................. 468
21.3 The General Screen ................................................................................................................... 469
21.4 The Billing Profile Screen ............................................................................................................. 471
21.4.1 The Account Generator Screen ...................................................................................... 472
21.4.2 The Account Redeem Screen ......................................................................................... 475
21.4.3 The Billing Profile Add/Edit Screen ................................................................................... 477
21.5 The Discount Screen ................................................................................................................... 478
21.5.1 The Discount Add/Edit Screen ......................................................................................... 480
21.6 The Payment Service General Screen ..................................................................................... 480
21.6.1 The Payment Service Desktop View / Mobile View Screen ......................................... 482
Chapter 22
Printer Manager ...............................................................................................................................486
22.1 Printer Manager Overview ........................................................................................................ 486
22.1.1 What You Can Do in this Chapter ................................................................................... 486
22.2 The General Setting Screen ....................................................................................................... 486
22.2.1 Add Printer Rule ................................................................................................................. 489
22.2.2 Edit Printer Rule .................................................................................................................. 489
22.2.3 Discover Printer ................................................................................................................. 490
22.2.4 Edit Printer Manager (Discover Printer) .......................................................................... 491
22.3 The Printout Configuration Screen ............................................................................................ 492
22.4 Printer Reports Overview ........................................................................................................... 493
22.4.1 Key Combinations ............................................................................................................. 493
22.4.2 Daily Account Summary .................................................................................................. 494
22.4.3 Monthly Account Summary ............................................................................................. 494
22.4.4 Account Report Notes ..................................................................................................... 495

USG/ZyWALL User’s Guide
13
22.4.5 System Status ..................................................................................................................... 495
Chapter 23
Free Time...........................................................................................................................................497
23.1 Free Time Overview .................................................................................................................... 497
23.1.1 What You Can Do in this Chapter ................................................................................... 497
23.2 The Free Time Screen ................................................................................................................. 497
Chapter 24
SMS....................................................................................................................................................501
24.1 SMS Overview ........................................................................................................................... 501
24.1.1 What You Can Do in this Chapter ................................................................................... 501
24.2 The SMS Screen ........................................................................................................................... 501
Chapter 25
IPnP....................................................................................................................................................503
25.1 IPnP Overview ............................................................................................................................. 503
25.1.1 What You Can Do in this Chapter ................................................................................... 503
25.2 IPnP Screen .................................................................................................................................. 504
Chapter 26
Walled Garden... .... ................... .................. .... .................. .................. .... ................... ......................505
26.1 Walled Garden Overview ......................................................................................................... 505
26.2 General Screen ........................................................................................................................... 505
26.3 URL Base Screen ......................................................................................................................... 506
26.3.1 Adding/Editing a Walled Garden URL ........................................................................... 507
26.4 Domain/IP Base Screen ............................................................................................................. 508
26.4.1 Adding/Editing a Walled Garden Domain or IP ........................................................... 508
26.4.2 Walled Garden Login Example ....................................................................................... 509
Chapter 27
Advertisement Screen................. .... .................. .... .... .................. .... .................. .... .... ......................511
27.1 Advertisement Overview ........................................................................................................... 511
27.1.1 Adding/Editing an Advertisement URL .......................................................................... 512
Chapter 28
Security Policy..................................................................................................................................513
28.1 Overview ..................................................................................................................................... 513
28.2 One Security ................................................................................................................................ 514
28.3 What You Can Do in this Chapter ............................................................................................ 517
28.3.1 What You Need to Know ................................................................................................. 518
28.4 The Security Policy Screen ......................................................................................................... 519
28.4.1 Configuring the Security Policy Control Screen ............................................................ 520

USG/ZyWALL User’s Guide
14
28.4.2 The Security Policy Control Add/Edit Screen ................................................................. 523
28.5 Anomaly Detection and Prevention Overview ...................................................................... 525
28.5.1 The Anomaly Detection and Prevention General Screen ........................................... 526
28.5.2 Creating New ADP Profiles ..............................................................................................527
28.5.3 Traffic Anomaly Profiles ................................................................................................... 528
28.5.4 Protocol Anomaly Profiles ................................................................................................ 531
28.6 The Session Control Screen ........................................................................................................ 534
28.6.1 The Session Control Add/Edit Screen .............................................................................. 535
28.7 Security Policy Example Applications ......................................................................................536
Chapter 29
Cloud CNM.....................................................................................................................................539
29.1 Cloud CNM Overview ................................................................................................................ 539
29.1.1 What You Can Do in this Chapter ................................................................................... 539
29.2 Cloud CNM SecuManager ........................................................................................................ 539
29.3 Cloud CNM SecuReporter ......................................................................................................... 542
Chapter 30
IPSec VPN .........................................................................................................................................545
30.1 Virtual Private Networks (VPN) Overview ................................................................................. 545
30.1.1 What You Can Do in this Chapter ................................................................................... 547
30.1.2 What You Need to Know ................................................................................................. 547
30.1.3 Before You Begin ............................................................................................................... 550
30.2 The VPN Connection Screen ..................................................................................................... 550
30.2.1 The VPN Connection Add/Edit Screen .......................................................................... 552
30.3 The VPN Gateway Screen ......................................................................................................... 559
30.3.1 The VPN Gateway Add/Edit Screen ............................................................................... 560
30.4 VPN Concentrator ..................................................................................................................... 567
30.4.1 VPN Concentrator Requirements and Suggestions ...................................................... 567
30.4.2 VPN Concentrator Screen ............................................................................................... 568
30.4.3 The VPN Concentrator Add/Edit Screen ........................................................................ 568
30.5 Zyxel Device IPSec VPN Client Configuration Provisioning .................................................... 569
30.6 IPSec VPN Background Information ......................................................................................... 571
Chapter 31
SSL VPN..............................................................................................................................................581
31.1 Overview ..................................................................................................................................... 581
31.1.1 What You Can Do in this Chapter ................................................................................... 581
31.1.2 What You Need to Know ................................................................................................. 581
31.2 The SSL Access Privilege Screen ................................................................................................ 582
31.2.1 The SSL Access Privilege Policy Add/Edit Screen ......................................................... 583
31.3 The SSL Global Setting Screen ................................................................................................... 586
31.3.1 How to Upload a Custom Logo ...................................................................................... 587

USG/ZyWALL User’s Guide
15
31.4 Zyxel Device SecuExtender ....................................................................................................... 588
31.4.1 Example: Configure Zyxel Device for SecuExtender ..................................................... 589
Chapter 32
SSL User Screens............................................................................................................... ................592
32.1 Overview ..................................................................................................................................... 592
32.1.1 What You Need to Know ................................................................................................. 592
32.2 Remote SSL User Login ............................................................................................................... 593
32.3 The SSL VPN User Screens ........................................................................................................... 596
32.4 Bookmarking the Zyxel Device .................................................................................................. 597
32.5 Logging Out of the SSL VPN User Screens ................................................................................ 598
32.6 SSL User Application Screen ...................................................................................................... 598
32.7 SSL User File Sharing .................................................................................................................... 599
32.7.1 The Main File Sharing Screen ........................................................................................... 599
32.7.2 Opening a File or Folder ................................................................................................... 600
32.7.3 Downloading a File ........................................................................................................... 601
32.7.4 Saving a File ....................................................................................................................... 601
32.7.5 Creating a New Folder ..................................................................................................... 602
32.7.6 Renaming a File or Folder ................................................................................................ 602
32.7.7 Deleting a File or Folder .................................................................................................... 603
32.7.8 Uploading a File ................................................................................................................ 603
Chapter 33
Zyxel Device SecuExtender (Windows).........................................................................................605
33.1 The Zyxel Device SecuExtender Icon ....................................................................................... 605
33.2 Status ............................................................................................................................................ 605
33.3 View Log ...................................................................................................................................... 606
33.4 Suspend and Resume the Connection ................................................................................... 607
33.5 Stop the Connection ................................................................................................................. 607
33.6 Uninstalling the Zyxel Device SecuExtender ............................................................................ 607
Chapter 34
L2TP VPN...................... .................. .... .................. ................... ... ................... .....................................609
34.1 Overview ..................................................................................................................................... 609
34.1.1 What You Can Do in this Chapter ................................................................................... 609
34.1.2 What You Need to Know ................................................................................................. 609
34.2 L2TP VPN Screen ......................................................................................................................... 610
34.2.1 Example: L2TP and Zyxel Device Behind a NAT Router ................................................ 612
Chapter 35
BWM (Bandwidth Management) .................................................................................................614
35.1 Overview ..................................................................................................................................... 614
35.1.1 What You Can Do in this Chapter ................................................................................... 614

USG/ZyWALL User’s Guide
16
35.1.2 What You Need to Know ................................................................................................ 614
35.2 The Bandwidth Management Screen ...................................................................................... 618
35.2.1 The Bandwidth Management Add/Edit Screen ............................................................ 621
Chapter 36
Application Patrol ............................................................................................................................629
36.1 Overview ..................................................................................................................................... 629
36.1.1 What You Can Do in this Chapter ................................................................................... 629
36.1.2 What You Need to Know ................................................................................................ 629
36.2 Application Patrol Profile ........................................................................................................... 630
36.2.1 The Application Patrol Profile Add/Edit Screen ............................................................. 632
36.2.2 The Application Patrol Profile Rule Add Application Screen ....................................... 633
Chapter 37
Content Filtering...............................................................................................................................635
37.1 Overview ..................................................................................................................................... 635
37.1.1 What You Can Do in this Chapter ................................................................................... 635
37.1.2 What You Need to Know ................................................................................................. 635
37.1.3 Before You Begin ............................................................................................................... 637
37.2 Content Filter Profile Screen ...................................................................................................... 637
37.3 Content Filter Profile Add or Edit Screen .................................................................................. 639
37.3.1 Content Filter Add Profile Category Service .................................................................. 639
37.3.2 Content Filter Add Filter Profile Custom Service ........................................................... 647
37.4 Content Filter Trusted Web Sites Screen ................................................................................. 650
37.5 Content Filter Forbidden Web Sites Screen ............................................................................ 651
37.6 Content Filter Technical Reference ......................................................................................... 652
Chapter 38
IDP .....................................................................................................................................................654
38.1 Overview ..................................................................................................................................... 654
38.1.1 What You Can Do in this Chapter ................................................................................... 654
38.1.2 What You Need To Know ................................................................................................. 654
38.1.3 Before You Begin ............................................................................................................... 654
38.2 The IDP Profile Screen ................................................................................................................. 655
38.2.1 Base Profiles ....................................................................................................................... 656
38.2.2 Adding / Editing Profiles .................................................................................................. 657
38.2.3 Profile > Group View Screen ............................................................................................ 658
38.2.4 Add Profile > Query View ................................................................................................ 661
38.2.5 Query Example .................................................................................................................. 665
38.3 IDP Custom Signatures .............................................................................................................. 666
38.3.1 Add / Edit Custom Signatures ......................................................................................... 669
38.3.2 Custom Signature Example ............................................................................................. 673
38.3.3 Applying Custom Signatures ............................................................................................ 675

USG/ZyWALL User’s Guide
17
38.3.4 Verifying Custom Signatures ............................................................................................ 675
38.4 IDP Technical Reference ........................................................................................................... 676
Chapter 39
Anti-Virus...........................................................................................................................................679
39.1 Overview ..................................................................................................................................... 679
39.1.1 What You Can Do in this Chapter ................................................................................... 679
39.1.2 What You Need to Know ................................................................................................. 680
39.2 Anti-Virus Profile Screen ............................................................................................................. 681
39.2.1 Anti-Virus Profile Add or Edit ............................................................................................. 683
39.3 Anti-Virus Black List ...................................................................................................................... 685
39.3.1 Anti-Virus Black List or White List Add/Edit ...................................................................... 685
39.3.2 Anti-Virus White List ............................................................................................................ 686
39.4 AV Signature Searching ............................................................................................................. 687
39.5 Anti-Virus Technical Reference ................................................................................................. 688
Chapter 40
Anti-Spam.........................................................................................................................................690
40.1 Overview ..................................................................................................................................... 690
40.1.1 What You Can Do in this Chapter ................................................................................... 690
40.1.2 What You Need to Know ................................................................................................. 690
40.2 Before You Begin ........................................................................................................................ 691
40.3 The Anti-Spam Profile Screen .................................................................................................... 692
40.3.1 The Anti-Spam Profile Add or Edit Screen ...................................................................... 693
40.4 The Mail Scan Screen ................................................................................................................. 695
40.5 The Anti-Spam Black List Screen ............................................................................................... 697
40.5.1 The Anti-Spam Black or White List Add/Edit Screen ...................................................... 699
40.5.2 Regular Expressions in Black or White List Entries ........................................................... 700
40.6 The Anti-Spam White List Screen ............................................................................................... 700
40.7 The DNSBL Screen ....................................................................................................................... 702
40.8 Anti-Spam Technical Reference ............................................................................................... 704
Chapter 41
SSL Inspection...................................................................................................................................708
41.1 SSL Inspection Overview ............................................................................................................ 708
41.1.1 What You Can Do in this Chapter ................................................................................... 708
41.1.2 What You Need To Know ................................................................................................. 709
41.1.3 Before You Begin ............................................................................................................... 709
41.2 The SSL Inspection Profile Screen .............................................................................................. 709
41.2.1 Add / Edit SSL Inspection Profiles .................................................................................... 710
41.3 Exclude List Screen .................................................................................................................... 713
41.4 Certificate Update Screen ....................................................................................................... 714
41.5 Install a CA Certificate in a Browser ......................................................................................... 715

USG/ZyWALL User’s Guide
18
Chapter 42
Device HA.........................................................................................................................................718
42.1 Overview ..................................................................................................................................... 718
42.1.1 What You Can Do in These Screens ................................................................................ 718
42.2 Device HA General .................................................................................................................... 719
42.2.1 Before You Begin ............................................................................................................... 719
42.3 Device HA Pro ............................................................................................................................. 721
42.3.1 Deploying Device HA Pro ................................................................................................ 721
42.3.2 Configuring Device HA Pro .............................................................................................. 722
42.4 The Active-Passive Mode Screen ............................................................................................. 724
42.4.1 Configuring Active-Passive Mode Device HA ............................................................... 725
42.5 Active-Passive Mode Edit Monitored Interface ...................................................................... 728
42.6 Device HA Technical Reference .............................................................................................. 730
Chapter 43
Object...............................................................................................................................................733
43.1 Zones Overview .......................................................................................................................... 733
43.1.1 What You Need to Know ................................................................................................. 733
43.1.2 The Zone Screen ................................................................................................................ 734
43.2 User/Group Overview ................................................................................................................ 736
43.2.1 What You Need To Know ................................................................................................. 736
43.2.2 User/Group User Summary Screen .................................................................................. 738
43.2.3 User/Group Group Summary Screen .............................................................................. 741
43.2.4 User/Group Setting Screen ............................................................................................. 743
43.2.5 User/Group MAC Address Summary Screen ................................................................ 747
43.2.6 User /Group Technical Reference .................................................................................. 748
43.3 AP Profile Overview .................................................................................................................... 749
43.3.1 Radio Screen ..................................................................................................................... 750
43.3.2 SSID Screen ....................................................................................................................... 756
43.4 MON Profile ................................................................................................................................ 764
43.4.1 Overview ............................................................................................................................ 764
43.4.2 MON Profile ........................................................................................................................ 764
43.4.3 Technical Reference ........................................................................................................ 767
43.5 Application .................................................................................................................................. 768
43.5.1 Add Application Rule ....................................................................................................... 770
43.5.2 Application Group Screen .............................................................................................. 773
43.6 Address/Geo IP Overview ......................................................................................................... 775
43.6.1 What You Need To Know ................................................................................................. 775
43.6.2 Address Summary Screen ................................................................................................ 775
43.6.3 Address Group Summary Screen .................................................................................... 779
43.6.4 Geo IP Summary Screen .................................................................................................. 781
43.7 Service Overview ........................................................................................................................ 783
43.7.1 What You Need to Know ................................................................................................. 783

USG/ZyWALL User’s Guide
19
43.7.2 The Service Summary Screen .......................................................................................... 784
43.7.3 The Service Group Summary Screen ............................................................................. 786
43.8 Schedule Overview ................................................................................................................... 787
43.8.1 What You Need to Know ................................................................................................. 788
43.8.2 The Schedule Screen ........................................................................................................ 788
43.8.3 The Schedule Group Screen ............................................................................................ 791
43.9 AAA Server Overview ............................................................................................................... 793
43.9.1 Directory Service (AD/LDAP) ........................................................................................... 793
43.9.2 RADIUS Server .................................................................................................................... 794
43.9.3 ASAS .................................................................................................................................... 794
43.9.4 What You Need To Know ................................................................................................. 794
43.9.5 Active Directory or LDAP Server Summary ..................................................................... 796
43.9.6 RADIUS Server Summary ...................................................................................................799
43.10 Auth. Method Overview ........................................................................................................ 801
43.10.1 Before You Begin ............................................................................................................. 801
43.10.2 Example: Selecting a VPN Authentication Method ................................................... 801
43.10.3 Authentication Method Objects ................................................................................... 802
43.11 Certificate Overview ............................................................................................................... 804
43.11.1 What You Need to Know ............................................................................................... 804
43.11.2 Verifying a Certificate .................................................................................................... 806
43.11.3 The My Certificates Screen ............................................................................................ 807
43.11.4 The Trusted Certificates Screen .................................................................................... 814
43.11.5 Certificates Technical Reference ................................................................................. 819
43.12 ISP Account Overview ............................................................................................................ 819
43.12.1 ISP Account Summary ....................................................................................................819
43.13 SSL Application Overview ....................................................................................................... 822
43.13.1 What You Need to Know ............................................................................................... 822
43.13.2 The SSL Application Screen ............................................................................................ 824
43.14 DHCPv6 Overview .................................................................................................................... 827
43.14.1 The DHCPv6 Request Screen ......................................................................................... 827
43.14.2 The DHCPv6 Lease Screen ............................................................................................. 829
Chapter 44
System...............................................................................................................................................831
44.1 Overview ..................................................................................................................................... 831
44.1.1 What You Can Do in this Chapter ................................................................................... 831
44.2 Host Name ................................................................................................................................... 832
44.3 USB Storage ................................................................................................................................. 832
44.4 Date and Time ............................................................................................................................ 833
44.4.1 Pre-defined NTP Time Servers List ..................................................................................... 836
44.4.2 Time Server Synchronization ............................................................................................ 836
44.5 Console Port Speed ................................................................................................................... 837
44.6 DNS Overview ............................................................................................................................. 838
USG/ZyWALL User’s Guide
20
44.6.1 DNS Server Address Assignment ...................................................................................... 838
44.6.2 Configuring the DNS Screen ............................................................................................ 838
44.6.3 (IPv6) Address Record ...................................................................................................... 841
44.6.4 PTR Record ......................................................................................................................... 842
44.6.5 Adding an (IPv6) Address/PTR Record .......................................................................... 842
44.6.6 CNAME Record ................................................................................................................. 842
44.6.7 Adding a CNAME Record ................................................................................................ 843
44.6.8 Domain Zone Forwarder ................................................................................................. 843
44.6.9 Adding a Domain Zone Forwarder ................................................................................. 844
44.6.10 MX Record ...................................................................................................................... 844
44.6.11 Adding a MX Record ...................................................................................................... 845
44.6.12 Security Option Control .................................................................................................. 845
44.6.13 Editing a Security Option Control .................................................................................. 845
44.6.14 Adding a DNS Service Control Rule .............................................................................. 846
44.7 WWW Overview .......................................................................................................................... 847
44.7.1 Service Access Limitations ............................................................................................... 847
44.7.2 System Timeout .................................................................................................................. 848
44.7.3 HTTPS ................................................................................................................................... 848
44.7.4 Configuring WWW Service Control ................................................................................. 849
44.7.5 Service Control Rules ........................................................................................................ 852
44.7.6 Customizing the WWW Login Page ................................................................................ 853
44.7.7 HTTPS Example ................................................................................................................... 858
44.8 SSH ............................................................................................................................................. 865
44.8.1 How SSH Works .................................................................................................................. 866
44.8.2 SSH Implementation on the Zyxel Device ...................................................................... 867
44.8.3 Requirements for Using SSH ..............................................................................................867
44.8.4 Configuring SSH ................................................................................................................. 867
44.8.5 Secure Telnet Using SSH Examples .................................................................................. 868
44.9 Telnet ........................................................................................................................................... 870
44.9.1 Configuring Telnet ............................................................................................................. 870
44.10 FTP .............................................................................................................................................. 871
44.10.1 Configuring FTP ................................................................................................................ 871
44.11 SNMP ......................................................................................................................................... 872
44.11.1 SNMPv3 and Security ...................................................................................................... 873
44.11.2 Supported MIBs ............................................................................................................... 874
44.11.3 SNMP Traps ....................................................................................................................... 874
44.11.4 Configuring SNMP ........................................................................................................... 874
44.11.5 Add SNMPv3 User ............................................................................................................ 876
44.12 Authentication Server .............................................................................................................. 877
44.12.1 Add/Edit Trusted RADIUS Client .................................................................................... 879
44.13 Language Screen ..................................................................................................................... 879
44.14 IPv6 Screen ................................................................................................................................ 880
44.15 Zyxel One Network (ZON) Utility ............................................................................................. 880

USG/ZyWALL User’s Guide
21
44.15.1 Zyxel One Network (ZON) System Screen .................................................................... 882
Chapter 45
Log and Report.................. .... .................. ................... ... ................... .................. .... ..........................883
45.1 Overview ..................................................................................................................................... 883
45.1.1 What You Can Do In this Chapter .................................................................................. 883
45.2 Email Daily Report ....................................................................................................................... 883
45.3 Log Setting Screens ................................................................................................................... 885
45.3.1 Log Setting Summary ........................................................................................................ 886
45.3.2 Edit System Log Settings .................................................................................................. 887
45.3.3 Edit Log on USB Storage Setting ..................................................................................... 892
45.3.4 Edit Remote Server Log Settings ..................................................................................... 894
45.3.5 Log Category Settings Screen ......................................................................................... 897
Chapter 46
File Manager ....................................................................................................................................902
46.1 Overview ..................................................................................................................................... 902
46.1.1 What You Can Do in this Chapter ................................................................................... 902
46.1.2 What you Need to Know .................................................................................................. 902
46.2 The Configuration File Screen ................................................................................................... 904
46.3 Firmware Management .......................................................................................................... 908
46.3.1 Cloud Helper ..................................................................................................................... 908
46.3.2 The Firmware Management Screen ............................................................................... 910
46.3.3 Firmware Upgrade via USB Stick ...................................................................................... 912
46.4 The Shell Script Screen .............................................................................................................. 913
Chapter 47
Diagnostics ......................................................................................................................................915
47.1 Overview ..................................................................................................................................... 915
47.1.1 What You Can Do in this Chapter ................................................................................... 915
47.2 The Diagnostic Screen ............................................................................................................... 915
47.2.1 The Diagnostics Files Screen ............................................................................................916
47.3 The Packet Capture Screen ...................................................................................................... 917
47.3.1 The Packet Capture Files Screen .................................................................................... 919
47.4 The System Log Screen .............................................................................................................. 920
47.5 The Network Tool Screen ........................................................................................................... 921
47.6 The Wireless Frame Capture Screen ........................................................................................922
47.6.1 The Wireless Frame Capture Files Screen ...................................................................... 924
Chapter 48
Packet Flow Explore .......................................................................................................................925
48.1 Overview ..................................................................................................................................... 925
48.1.1 What You Can Do in this Chapter ................................................................................... 925

USG/ZyWALL User’s Guide
22
48.2 The Routing Status Screen ......................................................................................................... 925
48.3 The SNAT Status Screen .............................................................................................................. 930
Chapter 49
Shutdown..........................................................................................................................................933
49.1 Overview ..................................................................................................................................... 933
49.1.1 What You Need To Know ................................................................................................. 933
49.2 The Shutdown Screen ................................................................................................................ 933
Chapter 50
Troubleshooting................................................................................................................................934
50.1 Resetting the Zyxel Device ........................................................................................................ 946
50.2 Getting More Troubleshooting Help .........................................................................................946
Appendix A Customer Support ..................................................................................................... 947
Appendix B Legal Information....................................................................................................... 953
Appendix C Product Features ....................................................................................................... 969
Index .................................................................................................................................................980
23
PART I
User’s Guide
USG/ZyWALL User’s Guide
24
CHAPTER 1
Introduction
1.1 Overview
Zyxel Device refers to all USG, VPN and ZyWALL models in this series as outlined below.
Besides performance variance, the following are the key feature differences between the models:
• UTM (Unified Threat Management) features include the following:
• ZyWALL models need a license for UTM functionality.
• USG models need a UTM license after one year
• The following UTM features work without a UTM license:
• Configuration > Content Filter > Trusted Web Sites
• Configuration > IDP > Custom Signatures
• Configuration > Anti-Virus > Black/White List
• Configuration > Anti-Spam > Black/White List
• ZyWALL models do not support SSL Inspection
• USG40 / USG40W / USG60 / USG60W support UTM but not SSL Inspection
• USG20-VPN and USG20W-VPN support UTM consisting of Content Filter and Anti-Spam
• USG2200-VPN supports UTM consisting of Content Filter, Anti-Spam and SSL Inspection
Table 1 Zyxel Device Models
USG MODELS VPN MODELS ZYWALL MODELS
USG40 USG20-VPN ZyWALL 110
USG40W USG20W-VPN ZyWALL 310
USG60 USG2200-VPN ZyWALL 1100
USG60W
USG110
USG210
USG310
USG1100
USG1900
• Application Patrol (AP) • Intrusion Detection & Prevention (IDP)
• Anomaly Detection & Prevention (ADP) • Content Filtering (CF)
• Anti-Virus (AV) • Anti-Spam (AS)
• Secure Socket Layer (SSL) encrypted traffic
Inspection
•

Chapter 1 Introduction
USG/ZyWALL User’s Guide
25
• The following models support Hotspot Management:
Note: At the time of writing, if the Zyxel Device is registered and with firmware version 4.25, the Zyxel
Device will get a free 30-day Hotspot Management trial license.
• USG20W-VPN / USG40W / USG60W have built-in Wi-Fi functionality
• The following models support Device HA (High Availability):
• The following models support Link Aggregation Group (LAG):
• USG20-VPN and USG20W-VPN do not support the AP controller function.
• The following models have Easy Mode wizards. Initial setup wizards for these models have a different
style to the other models.
• Some interface names vary by model - see Table 17 on page 72 for default port / interface name
mapping. See Table 18 on page 73 and Table 19 on page 74 for default interface / zone mapping.
See the product’s datasheet for detailed information on a specific model.
1.2 Registration at myZyxel.com
myZyxelZyxel.com is Zyxel’s online services center where you can register your Zyxel Device and
manage subscription services available for your Zyxel Device (see Configuration > Licensing >
Registration > Service for services available for your Zyxel Device).
• For Zyxel Devices that already have firmware version 4.25 or later, you have to register your Zyxel
Device and activate the corresponding service at myZyxel.com (through your Zyxel Device).
• For Zyxel Devices upgrading to firmware version 4.25, you may skip registering your Zyxel Device and
activating the corresponding service at myZyxel.com (through your Zyxel Device). However, it is highly
recommended to at least register your Zyxel Device. At the time of writing, the Firmware Upgrade
license providing Cloud Helper new firmware notifications, is free when you register your Zyxel Device.
• ZyWALL 110 • ZyWALL 310 • ZyWALL 1100
• USG110 • USG210 • USG310
• USG1100 • USG1900 • USG2200-VPN
• ZyWALL 110 • ZyWALL 310 • ZyWALL 1100
• USG110 • USG210 • USG310
• USG1100 • USG1900 • USG2200-VPN
• ZyWALL 310 • USG310 • ZyWALL 1100
• USG1100 • USG1900 • USG2200-VPN
• USG20-VPN • USG20W-VPN
• USG40 • USG40W
• USG60 • USG60W
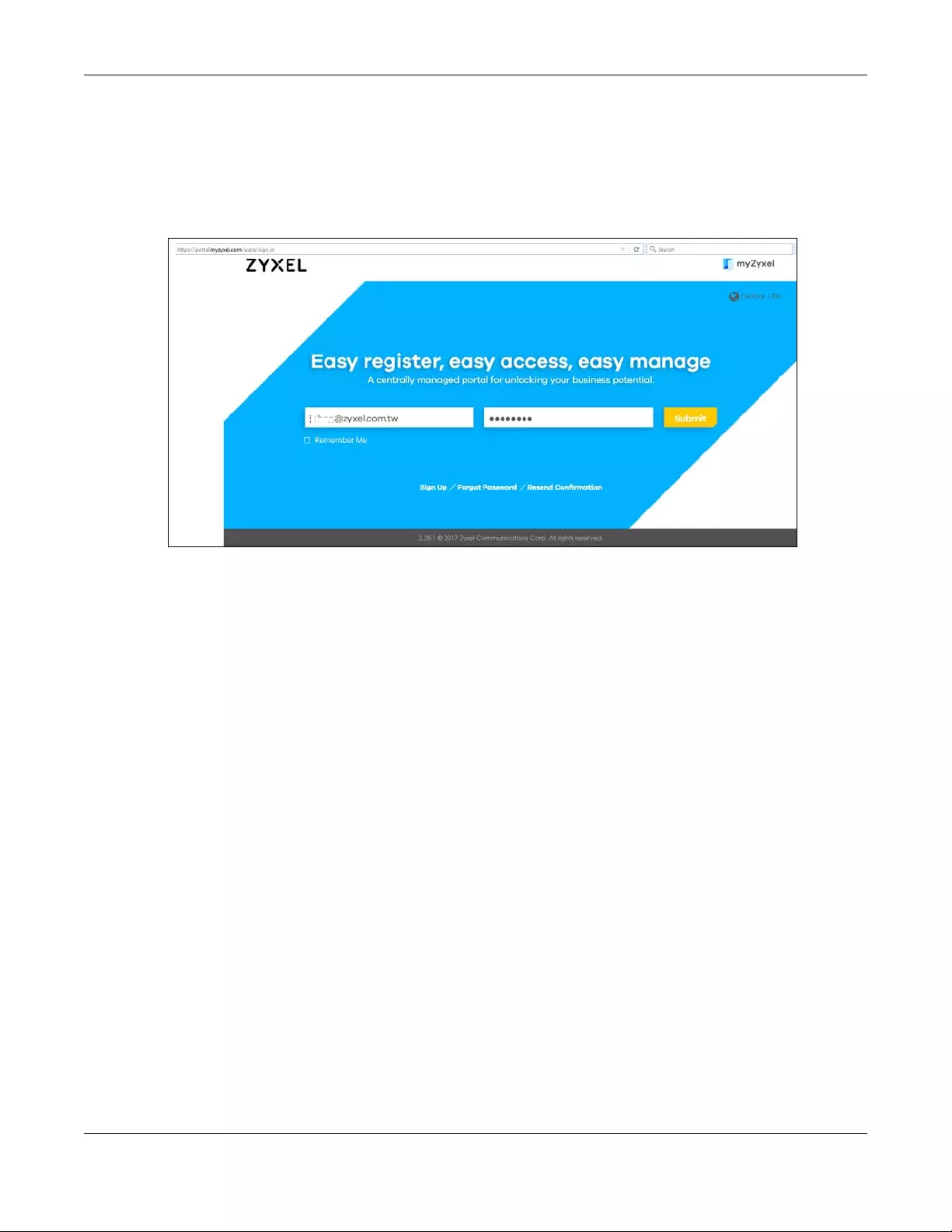
Chapter 1 Introduction
USG/ZyWALL User’s Guide
26
Note: You need to create a myZyxel.com account at portal.myzyxel.com before you can
register your device and activate the services at myZyxel.com.
You may need your Zyxel Device’s serial number and LAN MAC address to register it at
myZyxel.com. See the label at the back of the Zyxel Device’s for details.
Figure 1 myZyxel Login
1.2.1 Grace Period
SecuReporter and UTM licenses have a 15-day grace period after a license expires. Services will
continue to work in this period during which you will receive notifications to renew your license(s). New
license(s) are valid for 1 year from the date of purchase.
1.2.2 Applications
These are some Zyxel Device application scenarios.
Security Router
Security includes a Stateful Packet Inspection (SPI) firewall, and UTM (Unified Threat Management). All
models need a license to use UTM (Unified Threat Management) features.
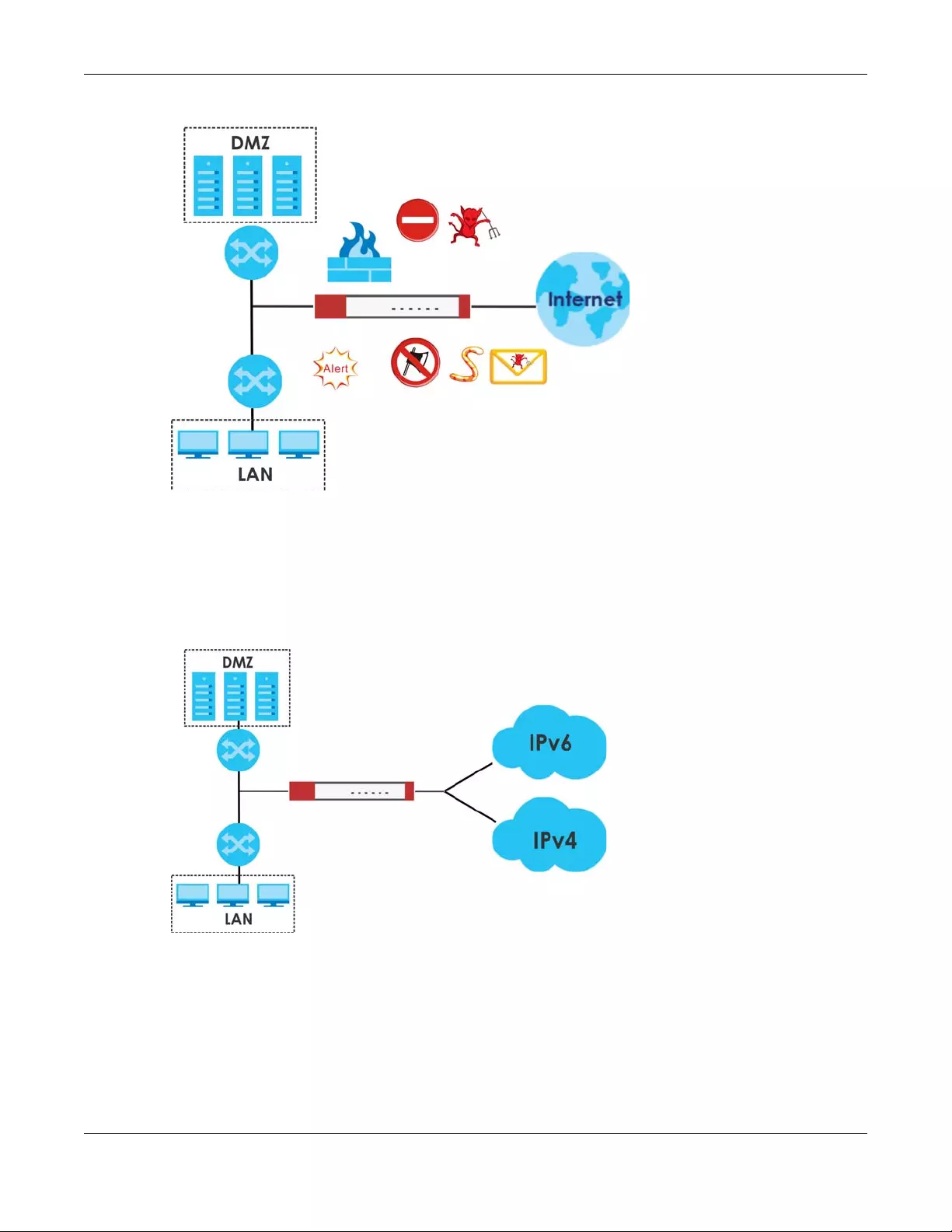
Chapter 1 Introduction
USG/ZyWALL User’s Guide
27
Figure 2 Applications: Security Router Applications: Security Router
IPv6 Routing
The Zyxel Device supports IPv6 Ethernet, PPP, VLAN, and bridge routing. You may also create IPv6 policy
routes and IPv6 objects. The Zyxel Device can also route IPv6 packets through IPv4 networks using
different tunneling methods.
Figure 3 Applications: IPv6 Routing
VPN Connectivity
Set up VPN tunnels with other companies, branch offices, telecommuters, and business travelers to
provide secure access to your network. You can also purchase the Zyxel Device OTPv2 One-Time
Password System for strong two-factor authentication for Web Configurator, Web access, SSL VPN, and
Zyxel IPSec VPN client user logins. AS is an Authentication Server in the below figure.
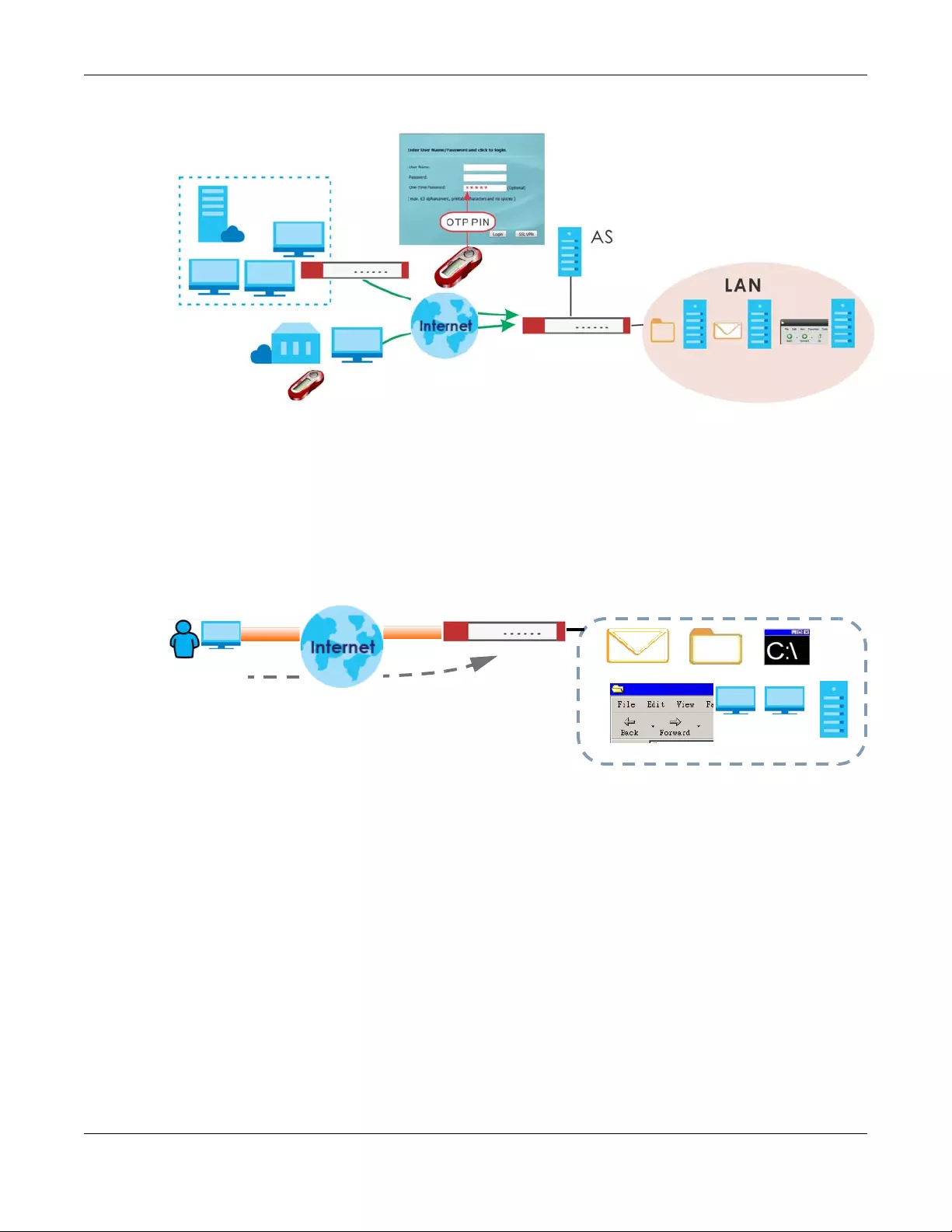
Chapter 1 Introduction
USG/ZyWALL User’s Guide
28
Figure 4 Applications: VPN Connectivity
SSL VPN Network Access
SSL VPN lets remote users use their web browsers for a very easy-to-use VPN solution. A user just browses
to the Zyxel Device’s web address and enters his user name and password to securely connect to the
Zyxel Device’s network. Here full tunnel mode creates a virtual connection for a remote user and gives
him a private IP address in the same subnet as the local network so he can access network resources in
the same way as if he were part of the internal network.
Figure 5 SSL VPN With Full Tunnel Mode
User-Aware Access Control
Set up security policies to restrict access to sensitive information and shared resources based on the user
who is trying to access it. In the following figure user A can access both the Internet and an internal file
server. User B has a lower level of access and can only access the Internet. User C is not even logged in,
so and cannot access either the Internet or the file server.
O T P PIN
Web Mail File Share
Web-based Application
https://
Application Server
Non-Web
LAN (192.168.1.X)
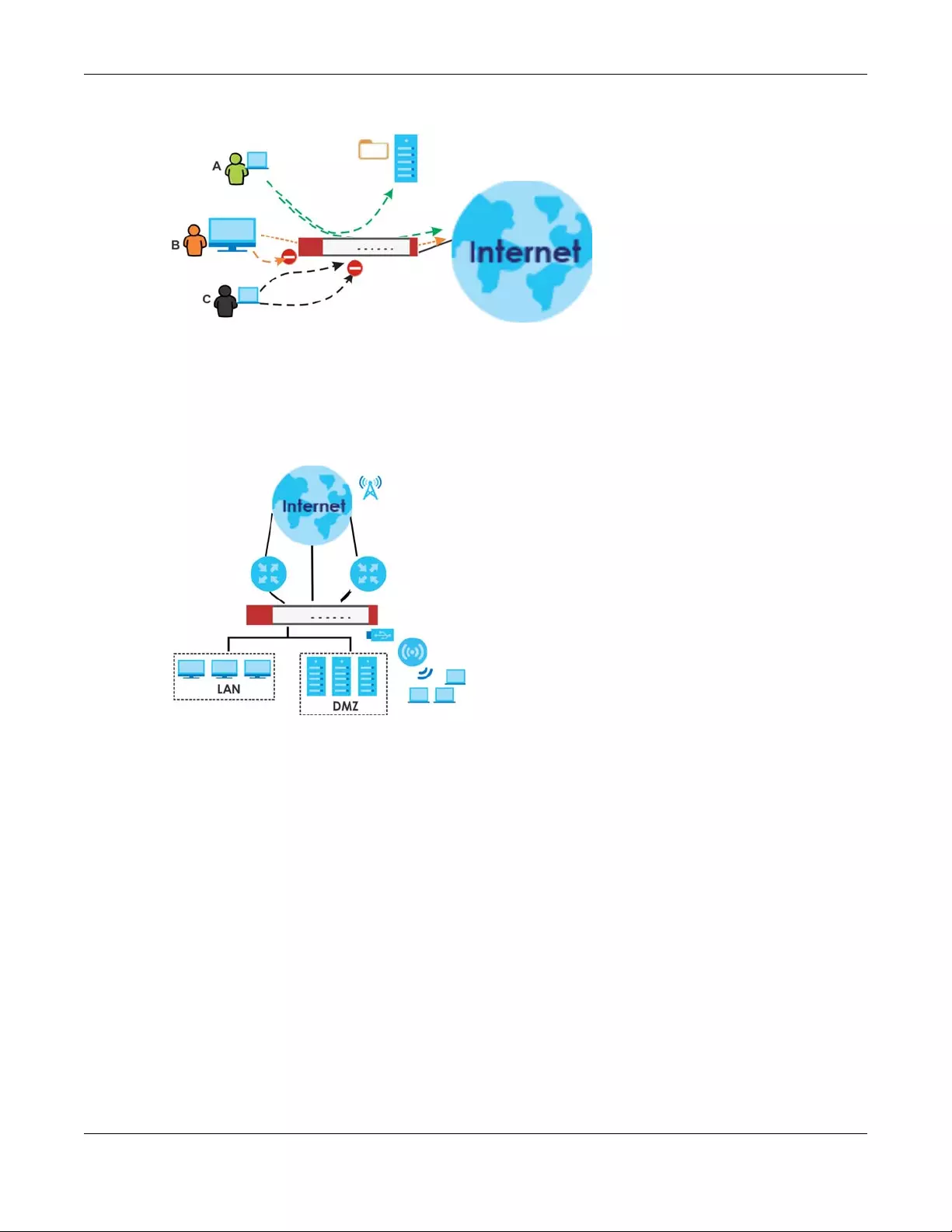
Chapter 1 Introduction
USG/ZyWALL User’s Guide
29
Figure 6 Applications: User-Aware Access Control
Load Balancing
Set up multiple connections to the Internet on the same port, or different ports, including cellular
interfaces. In either case, you can balance the traffic loads between them.
Figure 7 Applications: Multiple WAN Interfaces
1.3 Management Overview
You can manage the Zyxel Device in the following ways.
Web Configurator
The Web Configurator allows easy Zyxel Device setup and management using an Internet browser. This
User’s Guide provides information about the Web Configurator.
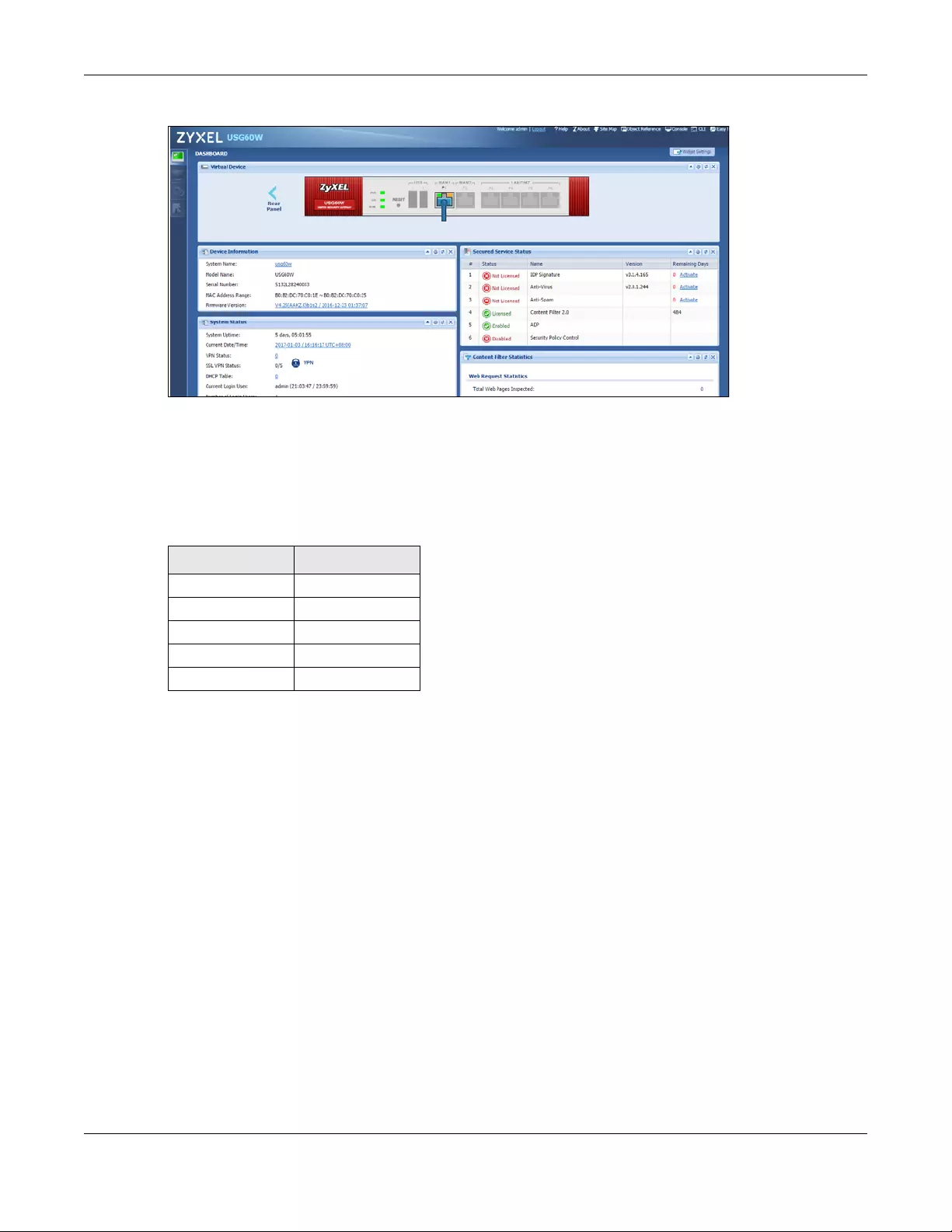
Chapter 1 Introduction
USG/ZyWALL User’s Guide
30
Figure 8 Managing the Zyxel Device: Web Configurator
Command-Line Interface (CLI)
The CLI allows you to use text-based commands to configure the Zyxel Device. Access it using remote
management (for example, SSH or Telnet) or via the physical or Web Configurator console port. See the
Command Reference Guide for CLI details. The default settings for the console port are:
FTP
Use File Transfer Protocol for firmware upgrades and configuration backup/restore.
SNMP
The device can be monitored and/or managed by an SNMP manager. See Section 44.11 on page 872.
Cloud CNM
Use the Cloud CNM screens (see Section 29.1 on page 539) to enable and configure management of
the Zyxel Device by a Central Network Management system and collect logs from the Zyxel Device in
order to monitor network activities and alert on potential threats, both internal and external.
1.4 Web Configurator
In order to use the Web Configurator, you must:
Table 2 Console Port Default Settings
SETTING VALUE
Speed 115200 bps
Data Bits 8
Parity None
Stop Bit 1
Flow Control Off
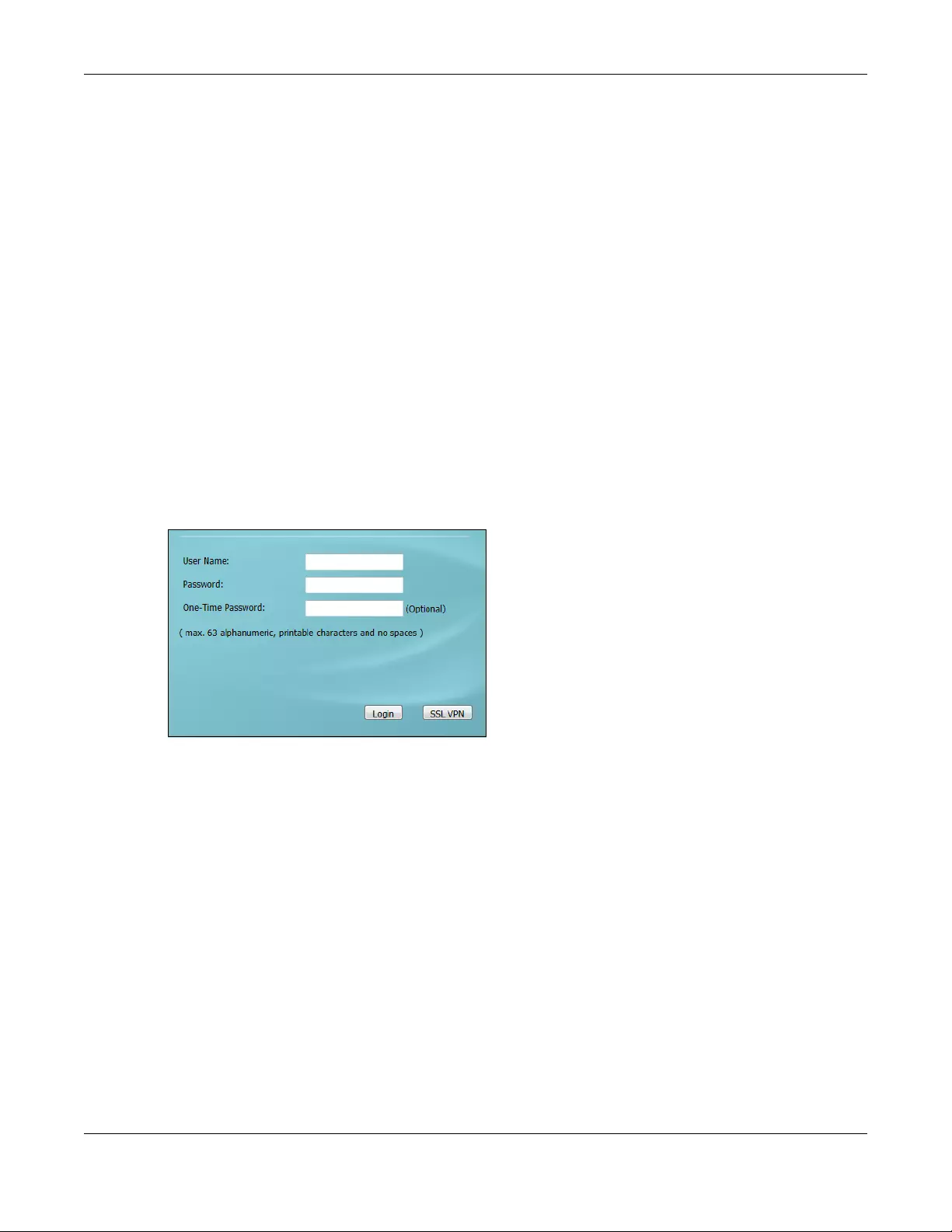
Chapter 1 Introduction
USG/ZyWALL User’s Guide
31
• Use one of the following web browser versions or later:
• Internet Explorer 10.x, 11.x
• Chrome latest version (45 or above)
• Firefox latest version (45 or above)
• Safari latest version (9.0 or above)
• Allow pop-up windows (blocked by default in Windows XP Service Pack 2)
• Enable JavaScripts, Java permissions, and cookies
The recommended screen resolution is 1024 x 768 pixels.
Note: Most screen shots in this guide come from the USG110 and USG60W. Screen shots for
other models may vary a little.
1.4.1 Web Configurator Access
1Make sure your Zyxel Device hardware is properly connected. See the Quick Start Guide.
2In your browser go to http://192.168.1.1. By default, the Zyxel Device automatically routes this request to
its HTTPS server, and it is recommended to keep this setting. The Login screen appears.
3Type the user name (default: “admin”) and password (default: “1234”).
If you have a OTP (One-Time Password) token generate a number and enter it in the One-Time
Password field. The number is only good for one login. You must use the token to generate a new
number the next time you log in.
4Click Login. After you log in for the first time using the default user name and password, you must
change the default admin password in the Update Admin Info screen. Type a new password of up to 63
printable characters without spaces, then click Apply.
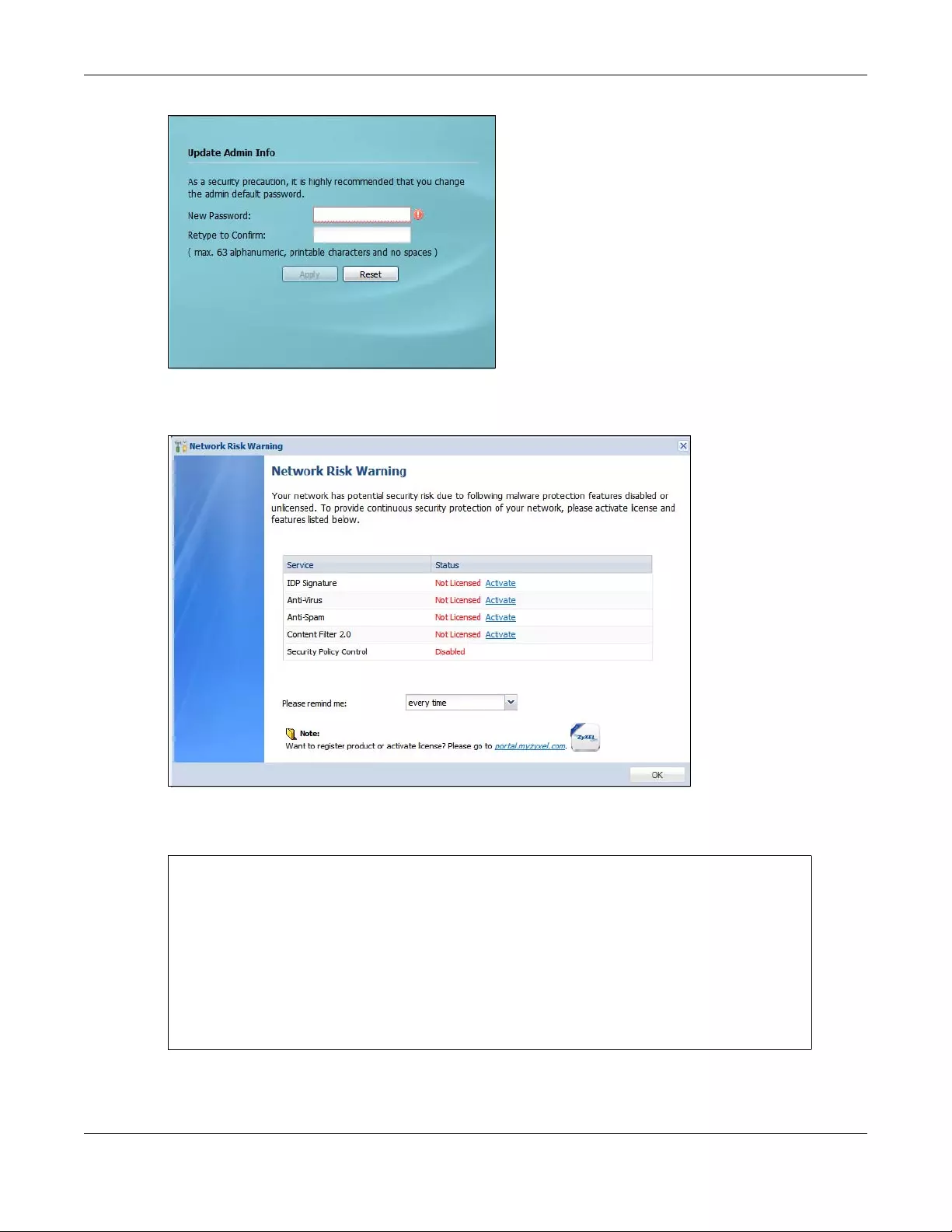
Chapter 1 Introduction
USG/ZyWALL User’s Guide
32
5The Network Risk Warning screen displays any unregistered or disabled security services. Select how
often to display the screen and click OK.
If you select Never and you later want to bring this screen back, use these commands (note the space
before the underscore).
See the Command Line Interface (CLI) Reference Guide (RG) for details on all supported commands.
Router> enable
Router#
Router# configure terminal
Router(config)#
Router(config)# service-register _setremind
after-10-days
after-180-days
after-30-days
every-time
never
Router(config)# service-register _setremind every-time
Router(config)#
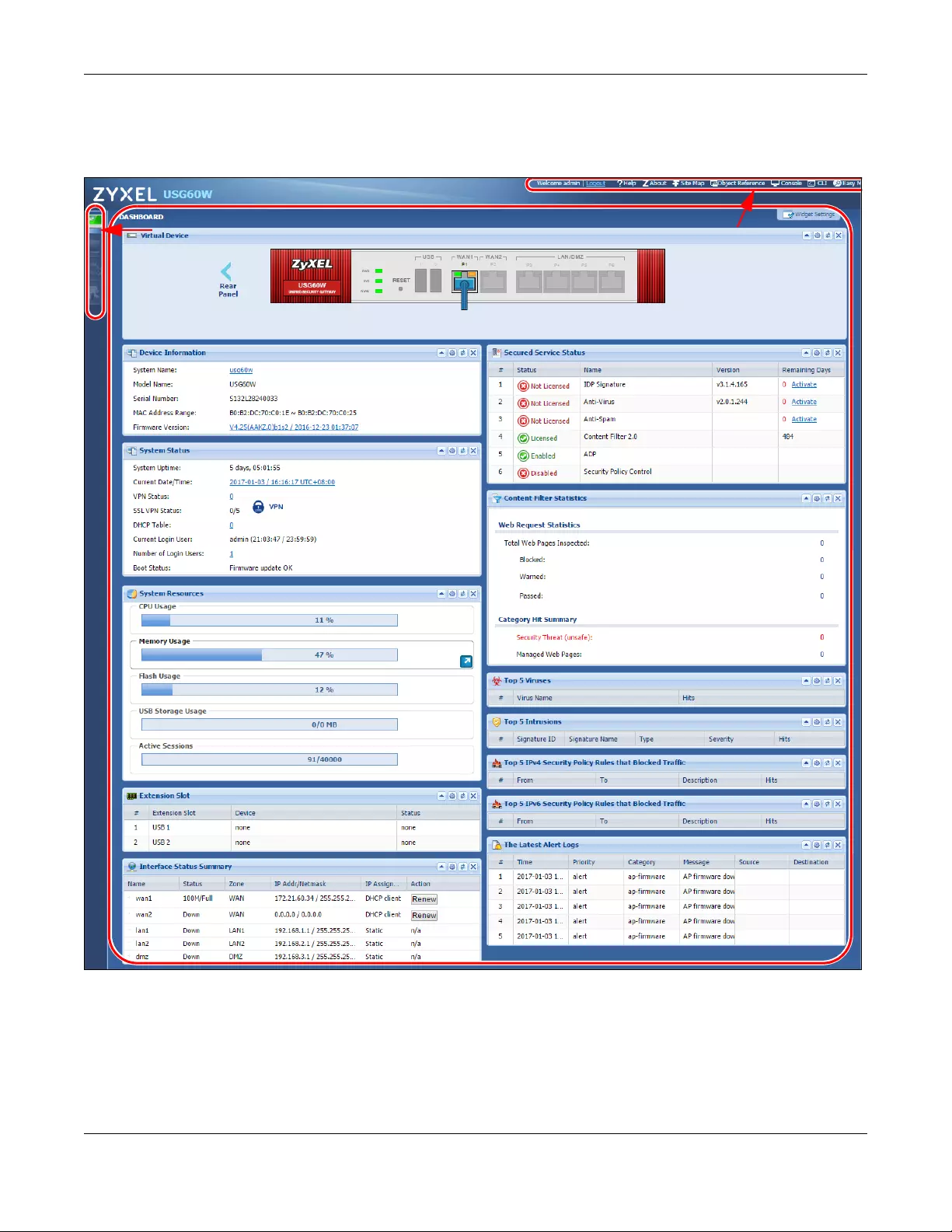
Chapter 1 Introduction
USG/ZyWALL User’s Guide
33
6Follow the directions in the Update Admin Info screen. If you change the default password, the Login
screen appears after you click Apply. If you click Ignore, the Installation Setup Wizard opens if the
ZyWALL is using its default configuration; otherwise the dashboard appears.
1.4.2 Web Configurator Screens Overview
The Web Configurator screen is divided into these parts (as illustrated on page 33):
•A - title bar
•B - navigation panel
A
C
B
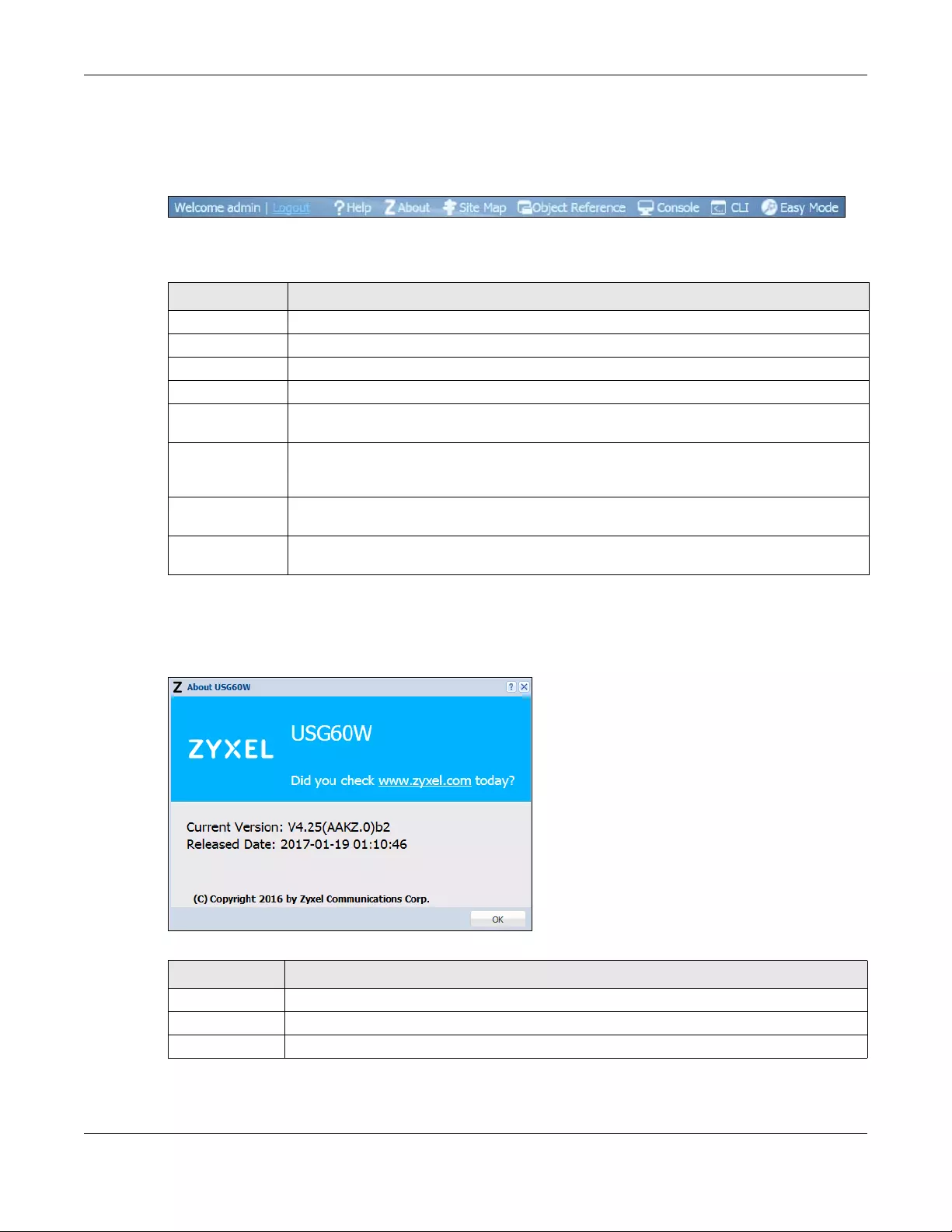
Chapter 1 Introduction
USG/ZyWALL User’s Guide
34
•C - main window
Title Bar
Figure 9 Title Bar
The title bar icons in the upper right corner provide the following functions.
About
Click About to display basic information about the Zyxel Device.
Figure 10 About
Table 3 Title Bar: Web Configurator Icons
LABEL DESCRIPTION
Logout Click this to log out of the Web Configurator.
Help Click this to open the help page for the current screen.
About Click this to display basic information about the Zyxel Device.
Site Map Click this to see an overview of links to the Web Configurator screens.
Object
Reference
Click this to check which configuration items reference an object.
Console Click this to open a Java-based console window from which you can run command line
interface (CLI) commands. You will be prompted to enter your user name and password. See
the Command Reference Guide for information about the commands.
CLI Click this to open a popup window that displays the CLI commands sent by the Web
Configurator to the Zyxel Device.
Easy Mode Click this to switch from Expert Mode to Easy Mode, which offers wizards to configure the Zyxel
Device.
Table 4 About
LABEL DESCRIPTION
Current Version This shows the firmware version of the Zyxel Device.
Released Date This shows the date (yyyy-mm-dd) and time (hh:mm:ss) when the firmware was released.
OK Click this to close the screen.
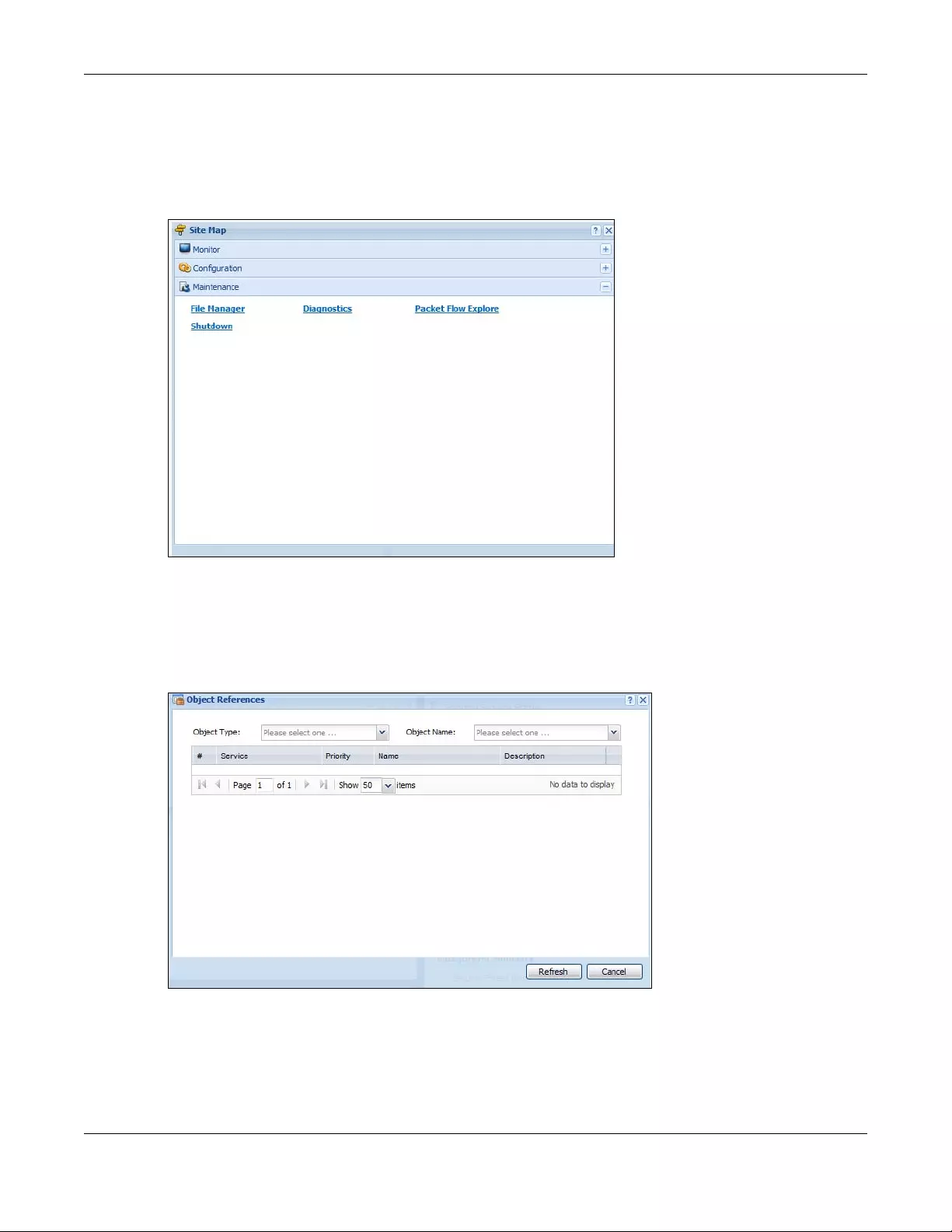
Chapter 1 Introduction
USG/ZyWALL User’s Guide
35
Site Map
Click Site MAP to see an overview of links to the Web Configurator screens. Click a screen’s link to go to
that screen.
Figure 11 Site Map
Object Reference
Click Object Reference to open the Object Reference screen. Select the type of object and the
individual object and click Refresh to show which configuration settings reference the object.
Figure 12 Object Reference
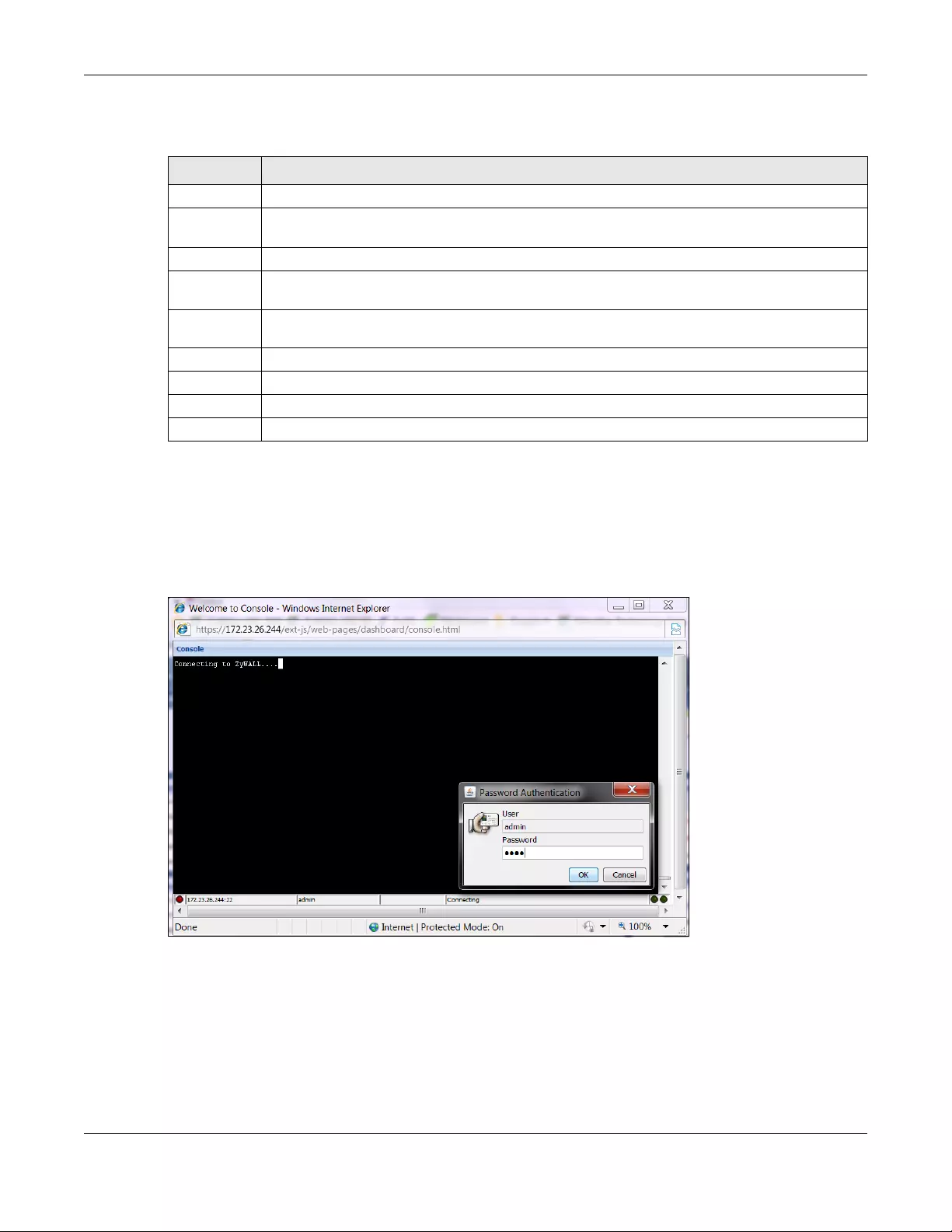
Chapter 1 Introduction
USG/ZyWALL User’s Guide
36
The fields vary with the type of object. This table describes labels that can appear in this screen.
Console
Click Console to open a Java-based console window from which you can run CLI commands. You will
be prompted to enter your user name and password. See the Command Reference Guide for
information about the commands.
Figure 13 Console Window
CLI Messages
Click CLI to look at the CLI commands sent by the Web Configurator. Open the pop-up window and
then click some menus in the Web Configurator to display the corresponding commands.
Table 5 Object References
LABEL DESCRIPTION
Object Type Select the object type to display the services available.
Object
Name
This identifies the object for which the configuration settings that use it are displayed. Click the
object’s name to display the object’s configuration screen in the main window.
# This field is a sequential value, and it is not associated with any entry.
Service This is the type of setting that references the selected object. Click a service’s name to display the
service’s configuration screen in the main window.
Priority If it is applicable, this field lists the referencing configuration item’s position in its list, otherwise N/A
displays.
Name This field identifies the configuration item that references the object.
Description If the referencing configuration item has a description configured, it displays here.
Refresh Click this to update the information in this screen.
Cancel Click Cancel to close the screen.
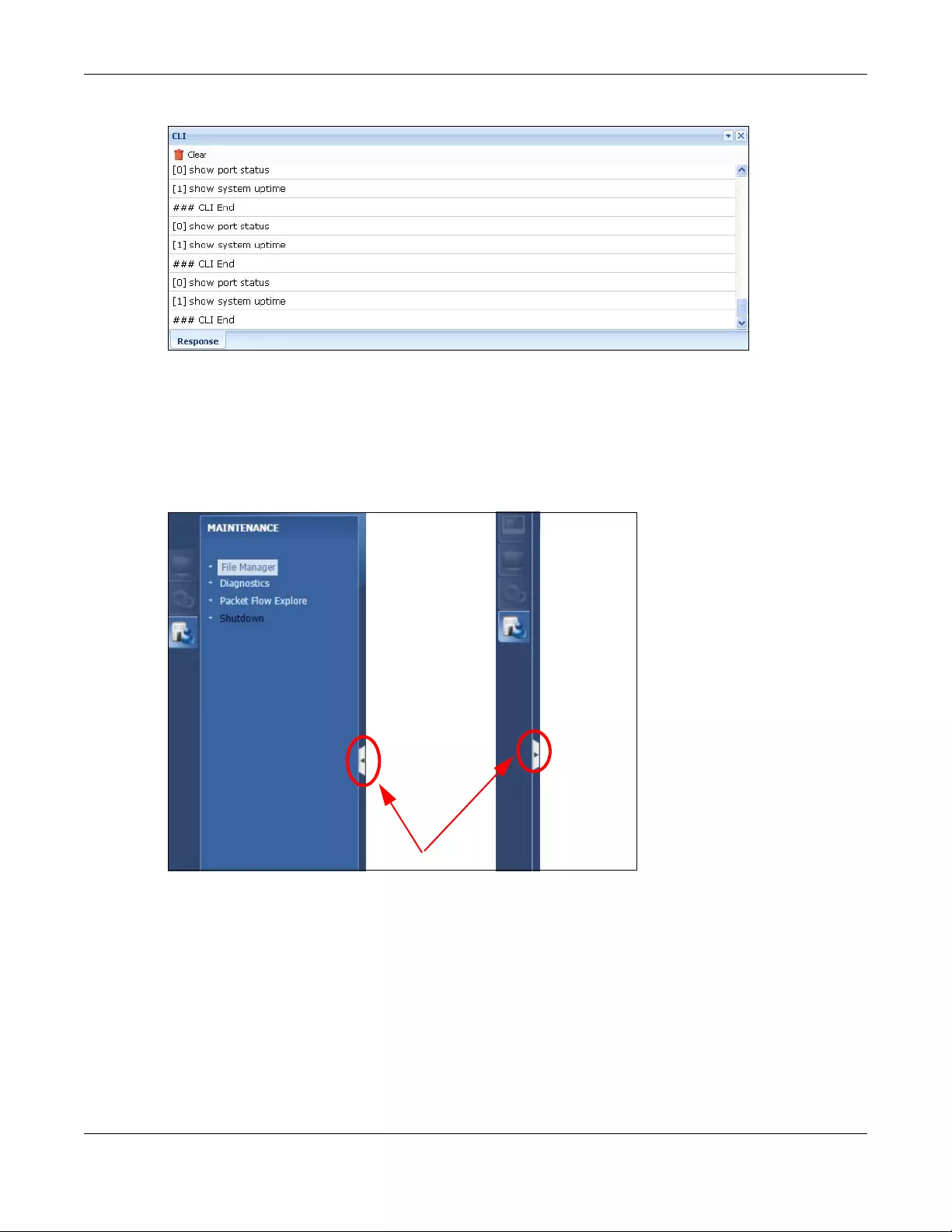
Chapter 1 Introduction
USG/ZyWALL User’s Guide
37
Figure 14 CLI Messages
1.4.3 Navigation Panel
Use the navigation panel menu items to open status and configuration screens. Click the arrow in the
middle of the right edge of the navigation panel to hide the panel or drag to resize it. The following
sections introduce the Zyxel Device’s navigation panel menus and their screens.
Figure 15 Navigation Panel
Dashboard
The dashboard displays general device information, system status, system resource usage, licensed
service status, and interface status in widgets that you can re-arrange to suit your needs. See the Web
Help for details on the dashboard.
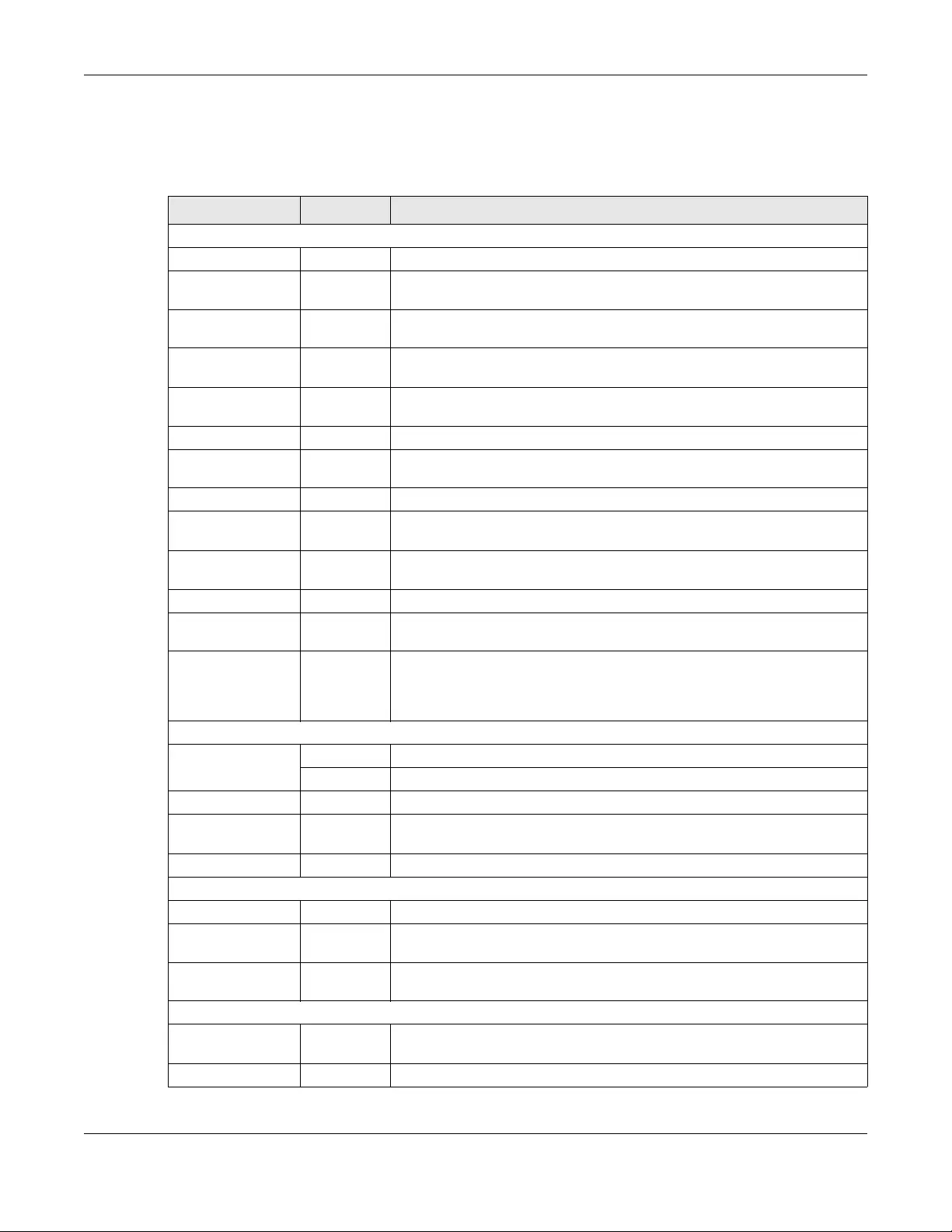
Chapter 1 Introduction
USG/ZyWALL User’s Guide
38
Monitor Menu
The monitor menu screens display status and statistics information.
Table 6 Monitor Menu Screens Summary
FOLDER OR LINK TAB FUNCTION
System Status
Port Statistics Port Statistics Displays packet statistics for each physical port.
Interface Status Interface
Summary
Displays general interface information and packet statistics.
Traffic Statistics Traffic
Statistics
Collect and display traffic statistics.
Session Monitor Session
Monitor
Displays the status of all current sessions.
IGMP Statistics IGMP
Statistics
Collect and display IGMP statistics.
DDNS Status DDNS Status Displays the status of the Zyxel Device’s DDNS domain names.
IP/MAC Binding IP/MAC
Binding
Lists the devices that have received an IP address from Zyxel Device
interfaces using IP/MAC binding.
Login Users Login Users Lists the users currently logged into the Zyxel Device.
Dynamic Guest Dynamic
Guest
List the dynamic guest accounts in the Zyxel Device’s local database.
Cellular Status Cellular
Status
Displays details about the Zyxel Device’s mobile broadband connection
status.
UPnP Port Status Port Statistics Displays details about UPnP connections going through the Zyxel Device.
USB Storage Storage
Information
Displays details about USB device connected to the Zyxel Device.
Ethernet
Neighbor Ethernet
Neighbor
View and manage the Zyxel Device’s neighboring devices via Smart
Connect (Layer Link Discovery Protocol (LLDP)). Use the Zyxel One Network
(ZON) utility to view and manage the Zyxel Device’s neighboring devices via
the Zyxel Discovery Protocol (ZDP).
Wireless
AP Information AP List Lists APs managed by the Zyxel Device.
Radio List Lists wireless details of APs managed by the Zyxel Device.
Station Info Station List Lists wireless clients associated with the APs managed by the Zyxel Device.
Detected
Device Detected
Device
Display information about suspected rogue APs.
Printer Status Printer Status Display information about the connected statement printers.
VPN Monitor
IPSec IPSec Displays and manages the active IPSec SAs.
SSL SSL Lists users currently logged into the VPN SSL client portal. You can also log out
individual users and delete related session information.
L2TP over IPSec L2TP over
IPSec
Displays details about current L2TP sessions.
UTM Statistics
App Patrol AppPatrol
Statistics
Displays application patrol statistics.
Content Filter Report Collect and display content filter statistics
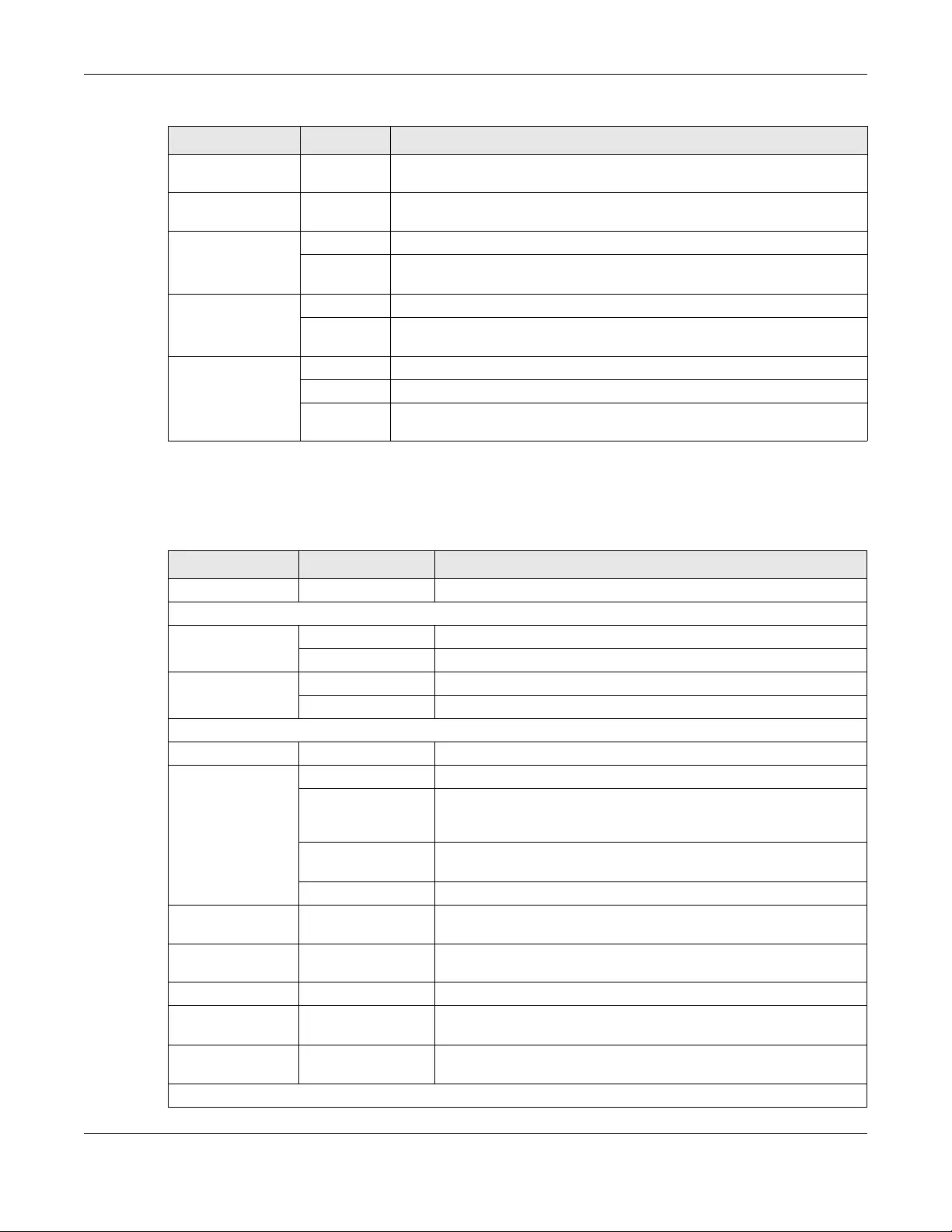
Chapter 1 Introduction
USG/ZyWALL User’s Guide
39
Configuration Menu
Use the configuration menu screens to configure the Zyxel Device’s features.
IDP IDP Collect and display statistics on the intrusions that the Zyxel Device has
detected.
Anti-Virus Anti-Virus Collect and display statistics on the viruses that the Zyxel Device has
detected.
Anti-Spam Report Collect and display spam statistics.
Status Displays how many mail sessions the ZyWALL is currently checking and DNSBL
(Domain Name Service-based spam Black List) statistics.
SSL Inspection Report Collect and display SSL Inspection statistics.
Certificate
Cache List
Displays traffic to destination servers using certificates.
Log View Log Lists log entries.
View AP Log Lists AP log entries.
Dynamic
Users Log
Display the Zyxel Device’s dynamic guest account log messages.
Table 7 Configuration Menu Screens Summary
FOLDER OR LINK TAB FUNCTION
Quick Setup Quickly configure WAN interfaces or VPN connections.
Licensing
Registration Registration Register the device and activate trial services.
Service View the licensed service status and upgrade licensed services.
Signature
Update Anti-Virus Update anti-virus signatures immediately or by a schedule.
IDP/AppPatrol Update IDP signatures immediately or by a schedule.
Wireless
Controller Configuration Configure manual or automatic controller registration.
AP
Management Mgnt AP List Edit or remove entries in the lists of APs managed by the Zyxel Device.
AP Policy Configure the AP controller’s IP address on the managed APs and
determine the action the managed APs take if the current AP
controller fails.
AP Group Create groups of APs, define their radio, VLAN, port and load
balancing settings.
Firmware Update the firmware on APs connected to your Zyxel Device.
MON Profile Rogue/Friendly AP
List
Configure how the Zyxel Device monitors rogue APs.
Load Balancing Load Balancing Configure load balancing for traffic moving to and from wireless
clients.
DCS DCS Configure dynamic wireless channel selection.
Auto Healing Auto Healing Enable auto healing to extend the wireless service coverage area of
the managed APs when one of the APs fails.
RTLS Real Time Location
System
Use the managed APs as part of an Ekahau RTLS to track the location
of Ekahau Wi-Fi tags.
Network
Table 6 Monitor Menu Screens Summary (continued)
FOLDER OR LINK TAB FUNCTION
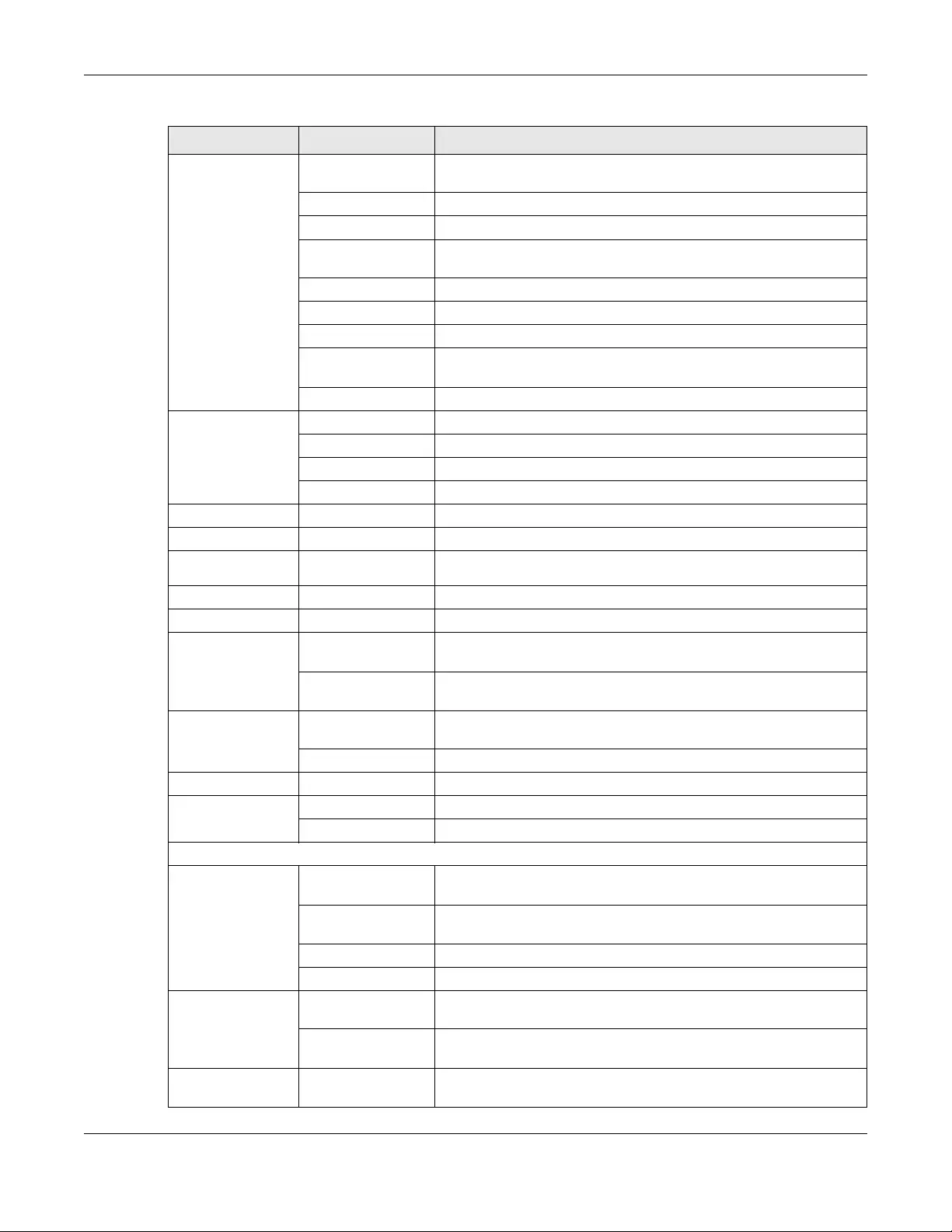
Chapter 1 Introduction
USG/ZyWALL User’s Guide
40
Interface Port Role Use this screen to set the Zyxel Device’s flexible ports such as LAN, OPT,
WLAN, or DMZ.
Ethernet Manage Ethernet interfaces and virtual Ethernet interfaces.
PPP Create and manage PPPoE and PPTP interfaces.
Cellular Configure a cellular Internet connection for an installed mobile
broadband card.
Tunnel Configure tunneling between IPv4 and IPv6 networks.
VLAN Create and manage VLAN interfaces and virtual VLAN interfaces.
Bridge Create and manage bridges and virtual bridge interfaces.
VTI Configure IP address assignment and interface parameters for VTI
(Virtual Tunnel Interface).
Trunk Create and manage trunks (groups of interfaces) for load balancing.
Routing Policy Route Create and manage routing policies.
Static Route Create and manage IP static routing information.
RIP Configure device-level RIP settings.
OSPF Configure device-level OSPF settings, including areas and virtual links.
DDNS DDNS Define and manage the Zyxel Device’s DDNS domain names.
NAT NAT Set up and manage port forwarding rules.
Redirect
Service Redirect Service Set up and manage HTTP and SMTP redirection rules.
ALG ALG Configure SIP, H.323, and FTP pass-through settings.
UPnP UPnP Configure interfaces that allow UPnP and NAT-PMP connections.
IP/MAC Binding Summary Configure IP to MAC address bindings for devices connected to each
supported interface.
Exempt List Configure ranges of IP addresses to which the Zyxel Device does not
apply IP/MAC binding.
Layer 2 Isolation General Enable layer-2 isolation on the Zyxel Device and the internal
interface(s).
White List Enable and configure the white list.
DNS Inbound LB DNS Load Balancing Configure DNS Load Balancing.
Web
Authentication
Web Authentication Define a web portal and exempt services from authentication.
SSO Configure the Zyxel Device to work with a Single Sign On agent.
Hotspot
Billing General Configure the general billing settings, such as the accounting
method.
Billing Profile Configure the billing profiles for the web-based account generator
and each button on the connected statement printer.
Discount Configure discount price plans.
Payment Service Enable online payment service and configure the service pages.
Printer
Manager General Setting Configure the printer list, enable printer management and customize
the account printout.
Printer Manager Detect the connected statement printers, change their IP addresses
and/or add them to the managed printer list.
Free Time Free Time Allow users to get a free account for Internet surfing during the
specified time period.
Table 7 Configuration Menu Screens Summary (continued)
FOLDER OR LINK TAB FUNCTION
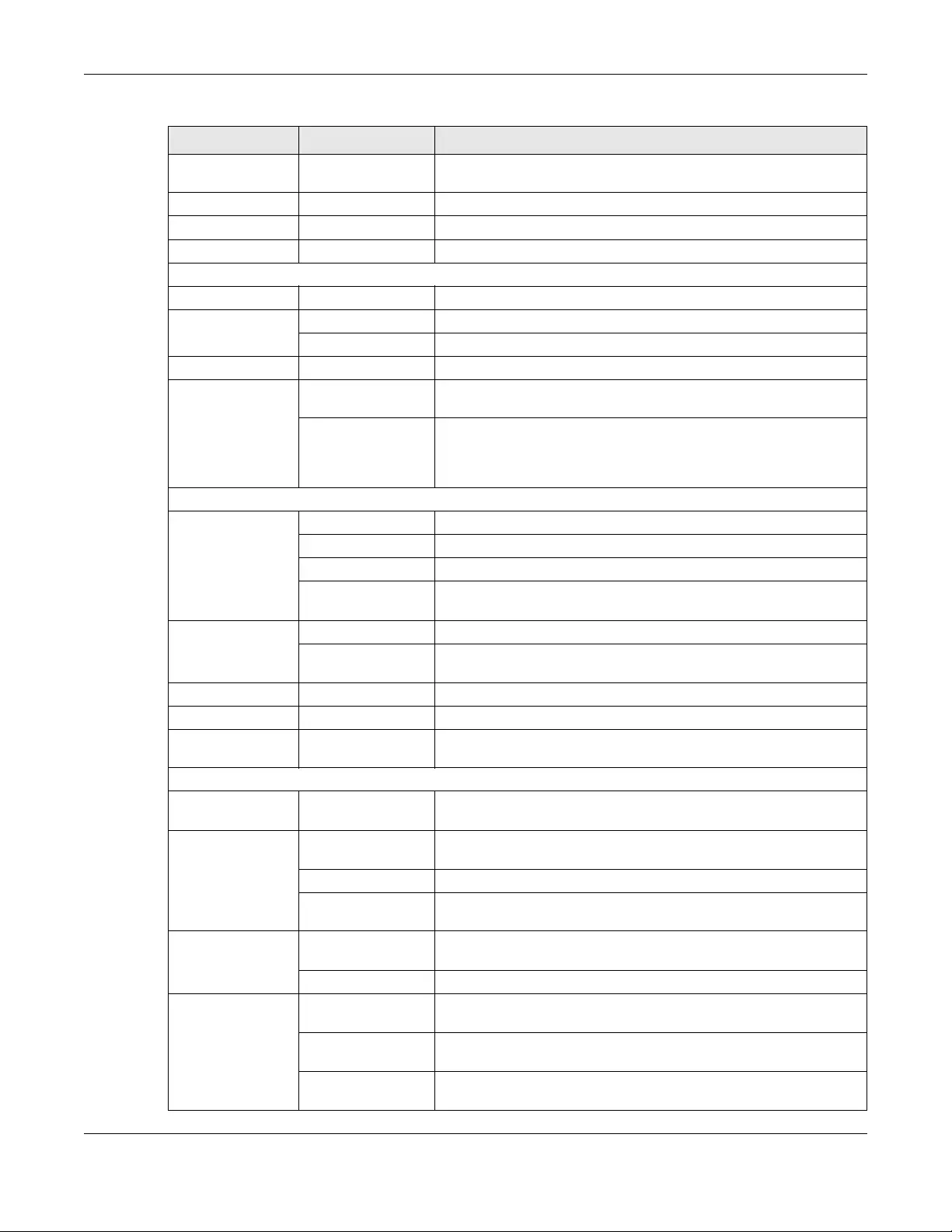
Chapter 1 Introduction
USG/ZyWALL User’s Guide
41
SMS SMS Enable the SMS service to send dynamic guest account information in
text messages.
IPnP IPnP Enable IPnP on the Zyxel Device and the internal interface(s).
Walled Garden Walled Garden Create walled garden links that display in the login screen.
Advertisement Advertisement Enable and set advertisement links.
Security Policy
Policy Control Policy Create and manage level-3 traffic rules and apply UTM profiles.
ADP General Display and manage ADP bindings.
Profile Create and manage ADP profiles.
Session Control Session Control Limit the number of concurrent client NAT/security policy sessions.
Cloud CNM SecuManager Enable and configure management of the Zyxel Device by a Central
Network Management system.
SecuReporter Enable SecuReporter logging and access the SecuReporter security
analytics portal that collects and analyzes logs from your Zyxel Device
in order to identify anomalies, alert on potential internal / external
threats, and report on network usage.
VPN
IPSec VPN VPN Connection Configure IPSec tunnels.
VPN Gateway Configure IKE tunnels.
Concentrator Combine IPSec VPN connections into a single secure network
Configuration
Provisioning
Set who can retrieve VPN rule settings from the Zyxel Device using the
Zyxel Device IPSec VPN Client.
SSL VPN Access Privilege Configure SSL VPN access rights for users and groups.
Global Setting Configure the Zyxel Device’s SSL VPN settings that apply to all
connections.
L2TP VPN L2TP VPN Configure L2TP over IPSec tunnels.
BWM BWM Enable and configure bandwidth management rules.
App Patrol General Enable or disable traffic management by application and see
registration and signature information.
UTM Profile
AppPatrol Profile Manage different types of traffic in this screen. Create App Patrol
template(s) of settings to apply to a traffic flow using a security policy.
Content Filter Profile Create and manage the detailed filtering rules for content filtering
profiles and then apply to a traffic flow using a security policy.
Trusted Web Sites Create a list of allowed web sites that bypass content filtering policies.
Forbidden Web Sites Create a list of web sites to block regardless of content filtering
policies.
IDP Profile Create IDP template(s) of settings to apply to a traffic flow using a
security policy.
Custom Signatures Create, import, or export custom signatures.
Anti-Virus Profile Create anti-virus template(s) of settings to apply to a traffic flow using
a security policy.
Black/White List Set up a black list to identify files with virus file patterns and a white list
to identify files that should not be checked for AV.
Signature Search for signatures by signature name or attributes and configure
how the Zyxel Device uses them.
Table 7 Configuration Menu Screens Summary (continued)
FOLDER OR LINK TAB FUNCTION
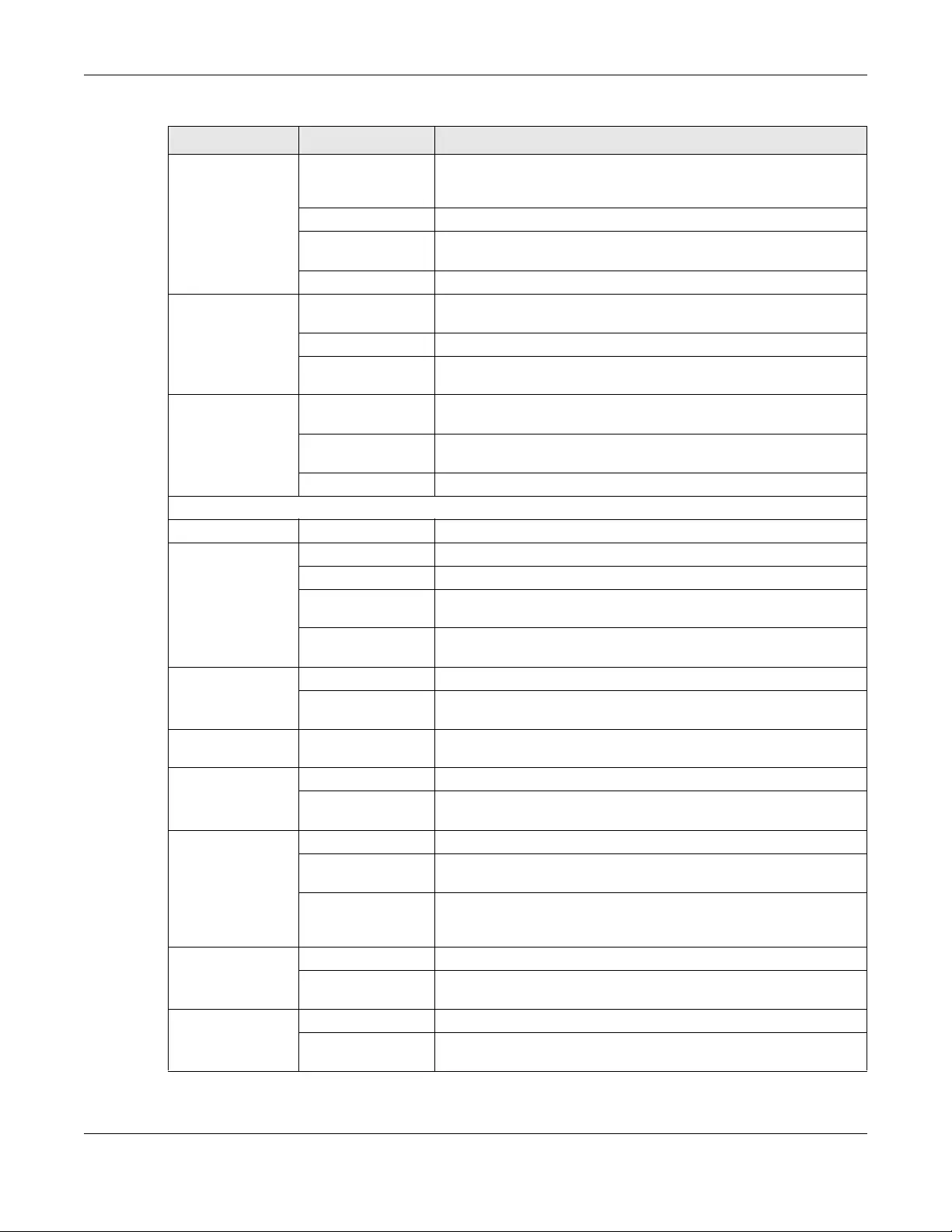
Chapter 1 Introduction
USG/ZyWALL User’s Guide
42
Anti-Spam Profile Turn anti-spam on or off and manage anti-spam policies. Create anti-
spam template(s) of settings to apply to a traffic flow using a security
policy.
Mail Scan Configure e-mail scanning details.
Black/White List Set up a black list to identify spam and a white list to identify
legitimate e-mail.
DNSBL Have the ZyWALL check e-mail against DNS Black Lists.
SSL Inspection Profile Decrypt HTTPS traffic for UTM inspection. Create SSL Inspection
template(s) of settings to apply to a traffic flow using a security policy.
Exclude List Configure services to be excluded from SSL Inspection.
Certificate Update Use this screen to update the latest certificates of servers using SSL
connections to the Zyxel Device network.
Device HA General Configure Device HA global settings, and see the status of each
interface monitored by Device HA.
Device HA Pro Configure Device HA Pro global, monitored interfaces and
synchronization settings.
Device HA Configure active-passive mode Device HA.
Object
Zone Zone Configure zone template(s) used to define various policies.
User/Group User Create and manage users.
Group Create and manage groups of users.
Setting Manage default settings for all users, general settings for user sessions,
and rules to force user authentication.
MAC Address Configure the MAC addresses of wireless clients for MAC
authentication using the local user database.
AP Profile Radio Create template(s) of radio settings to apply to policies as an object.
SSID Create template(s) of wireless settings to apply to radio profiles or
policies as an object.
MON Profile MON Profile Create and manage rogue AP monitoring files that can be
associated with different APs.
Application Application Create template(s) of services to apply to policies as an object.
Application Group Create and manage groups of applications to apply to policies as a
single object.
Address/Geo IP Address Create and manage host, range, and network (subnet) addresses.
Address Group Create and manage groups of addresses to apply to policies as a
single objects.
Geo IP Update the database of country-to-IP address mappings and
manually configure country-to-IP address mappings for geographic
address objects that can be used in security policies.
Service Service Create and manage TCP and UDP services.
Service Group Create and manage groups of services to apply to policies as a single
object.
Schedule Schedule Create one-time and recurring schedules.
Schedule Group Create and manage groups of schedules to apply to policies as a
single object.
Table 7 Configuration Menu Screens Summary (continued)
FOLDER OR LINK TAB FUNCTION
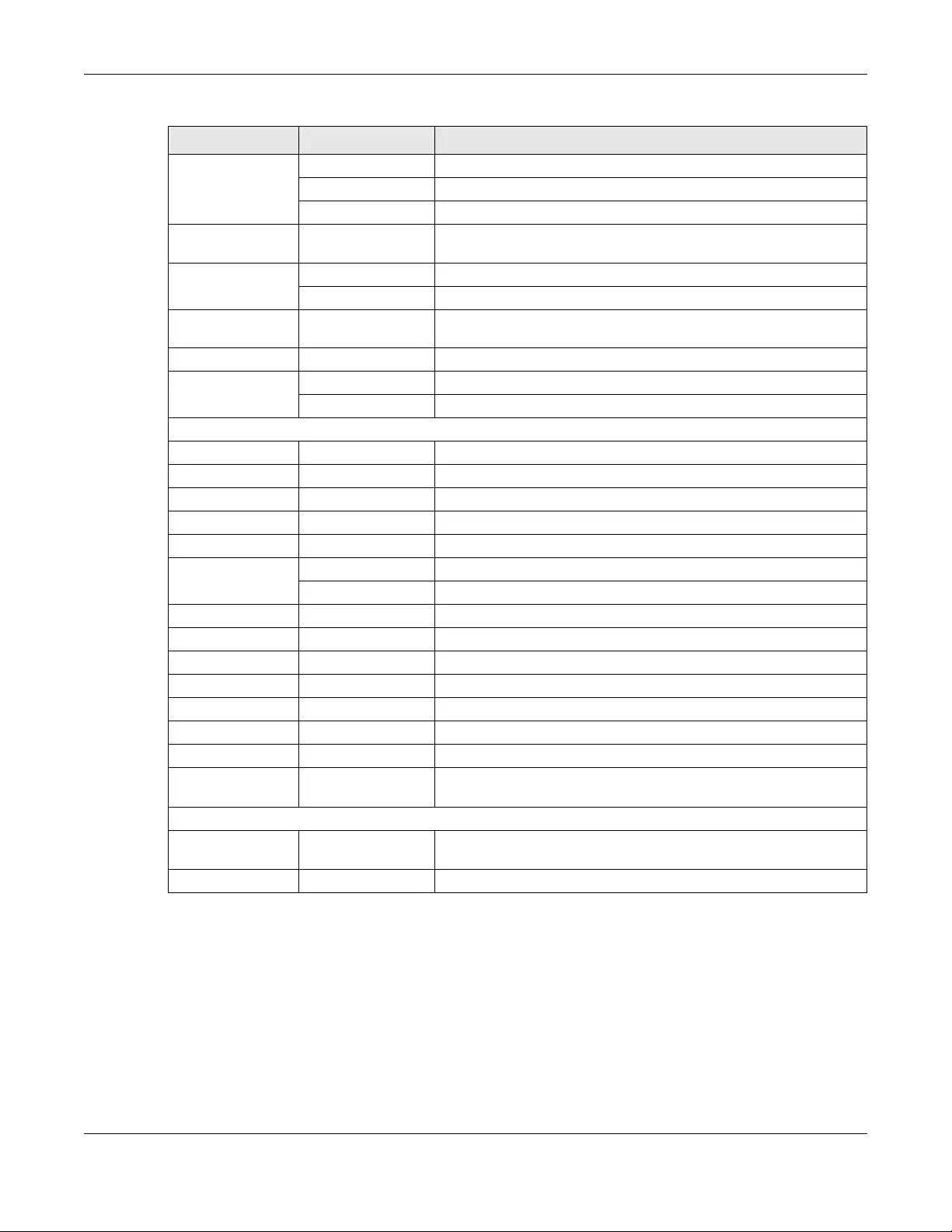
Chapter 1 Introduction
USG/ZyWALL User’s Guide
43
AAA Server Active Directory Configure the Active Directory settings.
LDAP Configure the LDAP settings.
RADIUS Configure the RADIUS settings.
Auth. Method Authentication
Method
Create and manage ways of authenticating users.
Certificate My Certificates Create and manage the Zyxel Device’s certificates.
Trusted Certificates Import and manage certificates from trusted sources.
ISP Account ISP Account Create and manage ISP account information for PPPoE/PPTP
interfaces.
SSL Application SSL Application Create SSL web application or file sharing objects to apply to policies.
DHCPv6 Request Configure IPv6 DHCP request type and interface information.
Lease Configure IPv6 DHCP lease type and interface information.
System
Host Name Host Name Configure the system and domain name for the Zyxel Device.
USB Storage Settings Configure the settings for the connected USB devices.
Date/Time Date/Time Configure the current date, time, and time zone in the Zyxel Device.
Console Speed Console Speed Set the console speed.
DNS DNS Configure the DNS server and address records for the Zyxel Device.
WWW Service Control Configure HTTP, HTTPS, and general authentication.
Login Page Configure how the login and access user screens look.
SSH SSH Configure SSH server and SSH service settings.
TELNET TELNET Configure telnet server settings for the Zyxel Device.
FTP FTP Configure FTP server settings.
SNMP SNMP Configure SNMP communities and services.
Auth. Server Auth. Server Configure the Zyxel Device to act as a RADIUS server.
Language Language Select the Web Configurator language.
IPv6 IPv6 Enable IPv6 globally on the Zyxel Device here.
ZON ZON Use the Zyxel One Network (ZON) utility to view and manage the Zyxel
Device’s neighboring devices via the Zyxel Discovery Protocol (ZDP).
Log & Report
Email Daily
Report Email Daily Report Configure where and how to send daily reports and what reports to
send.
Log Settings Log Settings Configure the system log, e-mail logs, and remote syslog servers.
Table 7 Configuration Menu Screens Summary (continued)
FOLDER OR LINK TAB FUNCTION
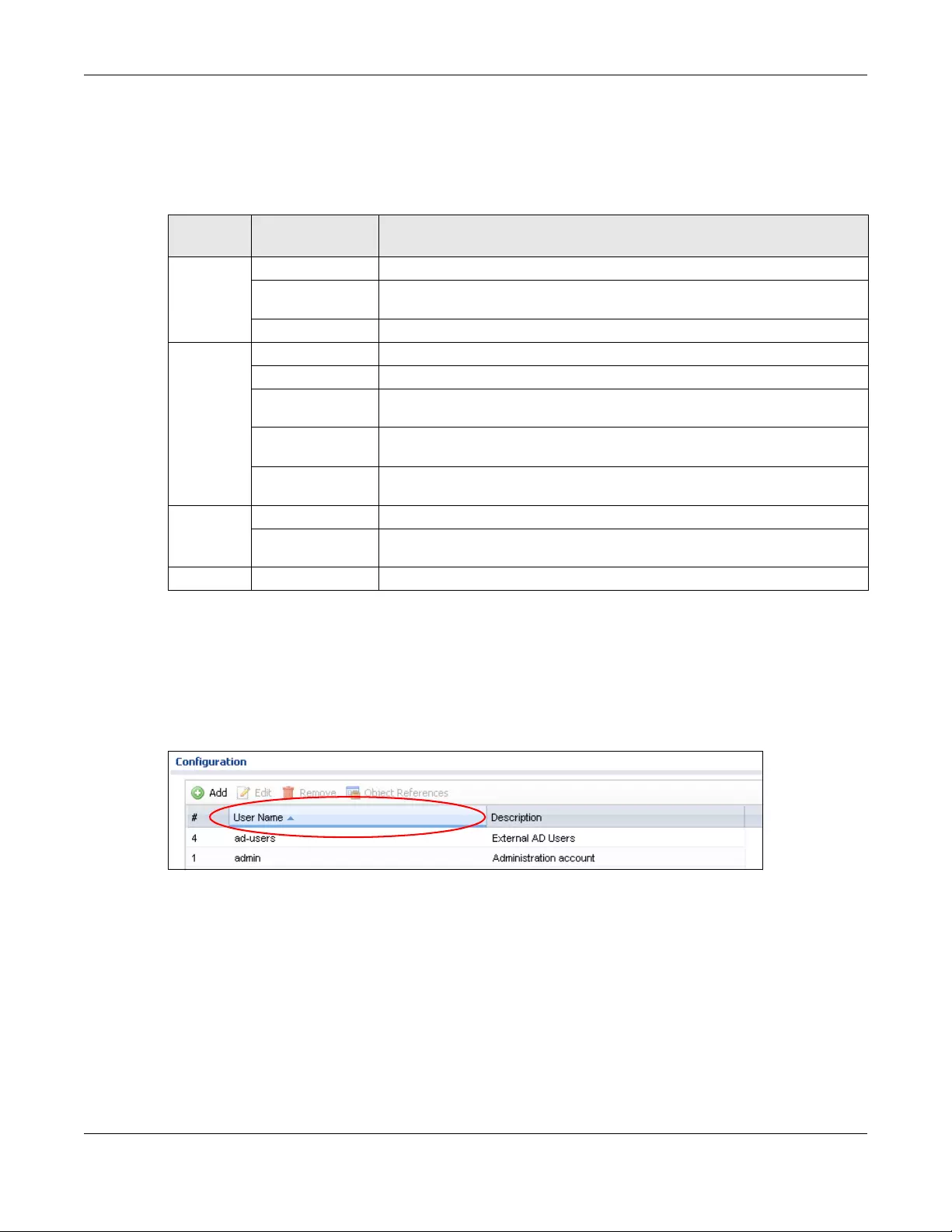
Chapter 1 Introduction
USG/ZyWALL User’s Guide
44
Maintenance Menu
Use the maintenance menu screens to manage configuration and firmware files, run diagnostics, and
reboot or shut down the Zyxel Device.
1.4.4 Tables and Lists
Web Configurator tables and lists are flexible with several options for how to display their entries.
Click a column heading to sort the table’s entries according to that column’s criteria.
Figure 16 Sorting Table Entries by a Column’s Criteria
Click the down arrow next to a column heading for more options about how to display the entries. The
options available vary depending on the type of fields in the column. Here are some examples of what
you can do:
• Sort in ascending or descending (reverse) alphabetical order
• Select which columns to display
•Group entries by field
•Show entries in groups
• Filter by mathematical operators (<, >, or =) or searching for text
Table 8 Maintenance Menu Screens Summary
FOLDER
OR LINK TAB FUNCTION
File
Manager
Configuration File Manage and upload configuration files for the Zyxel Device.
Firmware
Management
View the current firmware version and upload firmware. Reboot with your
choice of firmware.
Shell Script Manage and run shell script files for the Zyxel Device.
Diagnostics Diagnostics Collect diagnostic information.
Packet Capture Capture packets for analysis.
System Log Connect a USB device to the Zyxel Device and archive the Zyxel Device system
logs to it here.
Network Tool Identify problems with the connections. You can use Ping or Traceroute to help
you identify problems.
Wireless Frame
Capture
Capture wireless frames from APs for analysis.
Packet
Flow
Explore
Routing Status Check how the Zyxel Device determines where to route a packet.
SNAT Status View a clear picture on how the Zyxel Device converts a packet’s source IP
address and check the related settings.
Shutdown Shutdown Turn off the Zyxel Device.
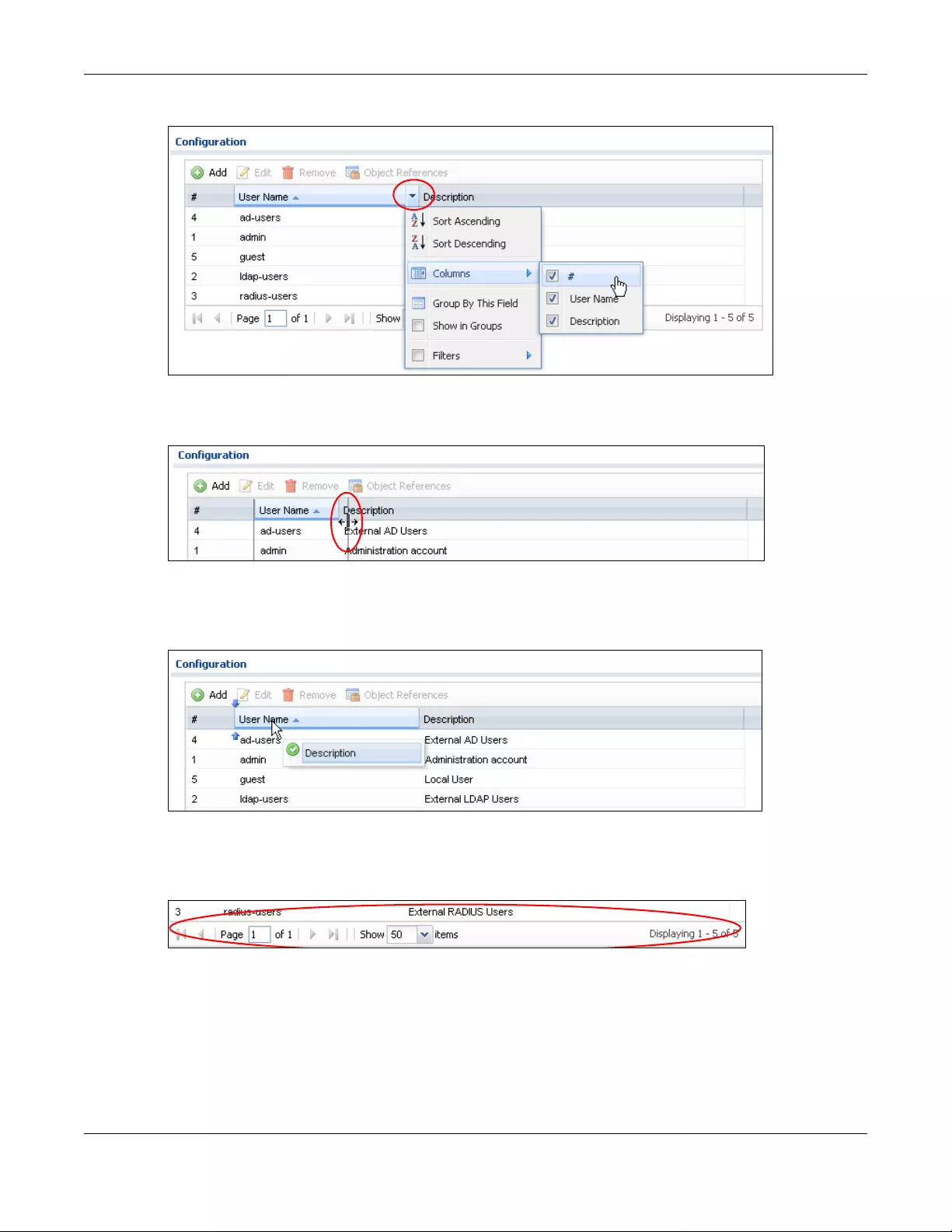
Chapter 1 Introduction
USG/ZyWALL User’s Guide
45
Figure 17 Common Table Column Options
Select a column heading cell’s right border and drag to re-size the column.
Figure 18 Resizing a Table Column
Select a column heading and drag and drop it to change the column order. A green check mark
displays next to the column’s title when you drag the column to a valid new location.
Figure 19 Moving Columns
Use the icons and fields at the bottom of the table to navigate to different pages of entries and control
how many entries display at a time.
Figure 20 Navigating Pages of Table Entries
The tables have icons for working with table entries. You can often use the [Shift] or [Ctrl] key to select
multiple entries to remove, activate, or deactivate.
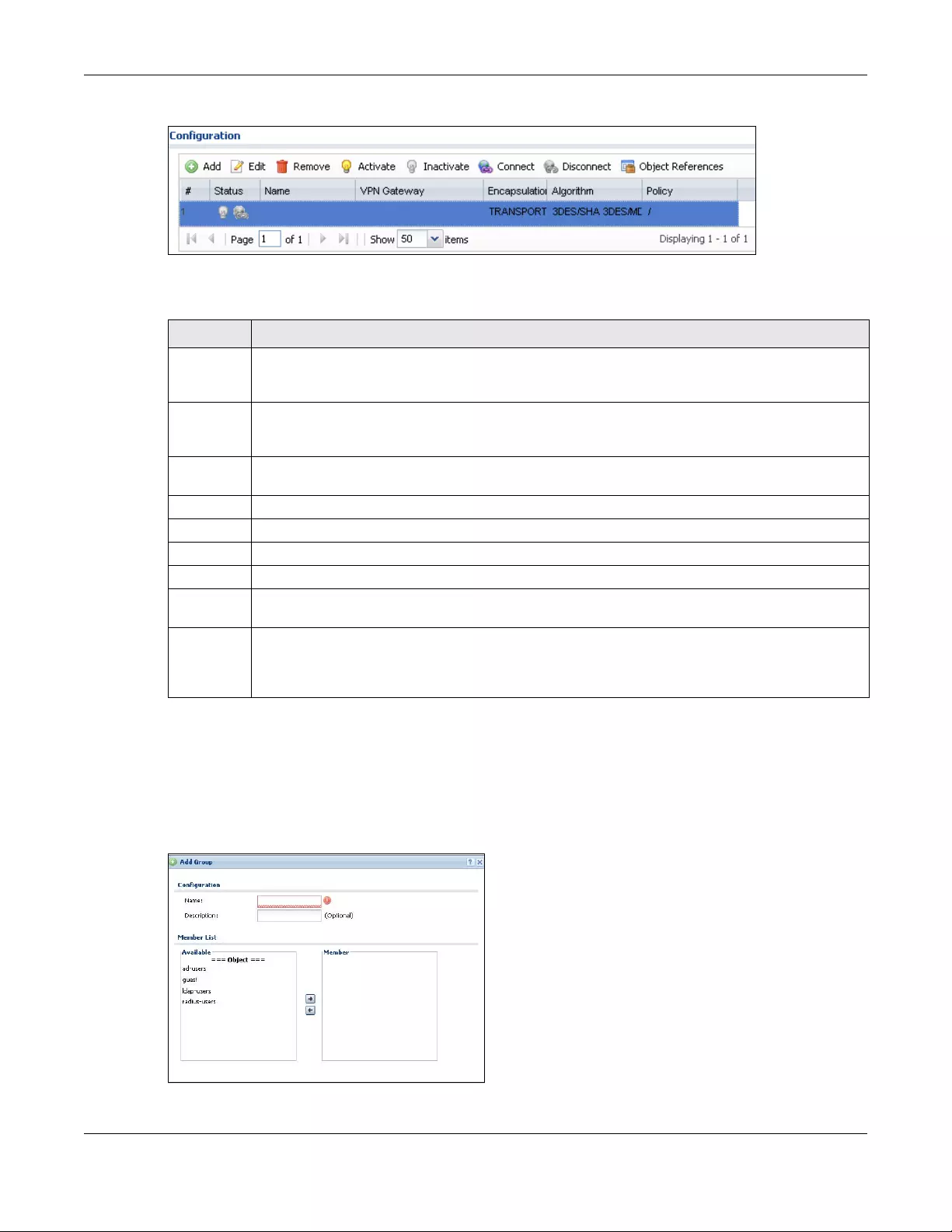
Chapter 1 Introduction
USG/ZyWALL User’s Guide
46
Figure 21 Common Table Icons
Here are descriptions for the most common table icons.
Working with Lists
When a list of available entries displays next to a list of selected entries, you can often just double-click
an entry to move it from one list to the other. In some lists you can also use the [Shift] or [Ctrl] key to
select multiple entries, and then use the arrow button to move them to the other list.
Figure 22 Working with Lists
Table 9 Common Table Icons
LABEL DESCRIPTION
Add Click this to create a new entry. For features where the entry’s position in the numbered list is
important (features where the Zyxel Device applies the table’s entries in order like the security policy
for example), you can select an entry and click Add to create a new entry after the selected entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the entry’s
settings. In some tables you can just click a table entry and edit it directly in the table. For those types
of tables small red triangles display for table entries with changes that you have not yet applied.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove it
before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Connect To connect an entry, select it and click Connect.
Disconnect To disconnect an entry, select it and click Disconnect.
Object
References
Select an entry and click Object References to check which settings use the entry.
Move To change an entry’s position in a numbered list, select it and click Move to display a field to type a
number for where you want to put that entry and press [ENTER] to move the entry to the number that
you typed. For example, if you type 6, the entry you are moving becomes number 6 and the previous
entry 6 (if there is one) gets pushed up (or down) one.

USG/ZyWALL User’s Guide
47
CHAPTER 2
Initial Setup Wizard
2.1 Initial Setup Wizard Screens
When you log into the Web Configurator for the first time or when you reset the Zyxel Device to its
default configuration, the Initial Setup Wizard screen displays. This wizard helps you configure Internet
connection settings and activate subscription services.
The following models have Easy Mode wizards. Initial setup wizards for these models have a different
style to the other models.
• USG20-VPN
• USG20W-VPN
•USG40
• USG40W
•USG60
• USG60W
Note: For Zyxel Devices that already have firmware version 4.25, you have to register your
Zyxel Device and activate the corresponding service at myZyxel.com (through your
Zyxel Device).
This chapter provides information on configuring the Web Configurator's Initial Setup Wizard. See the
feature-specific chapters in this User’s Guide for background information.
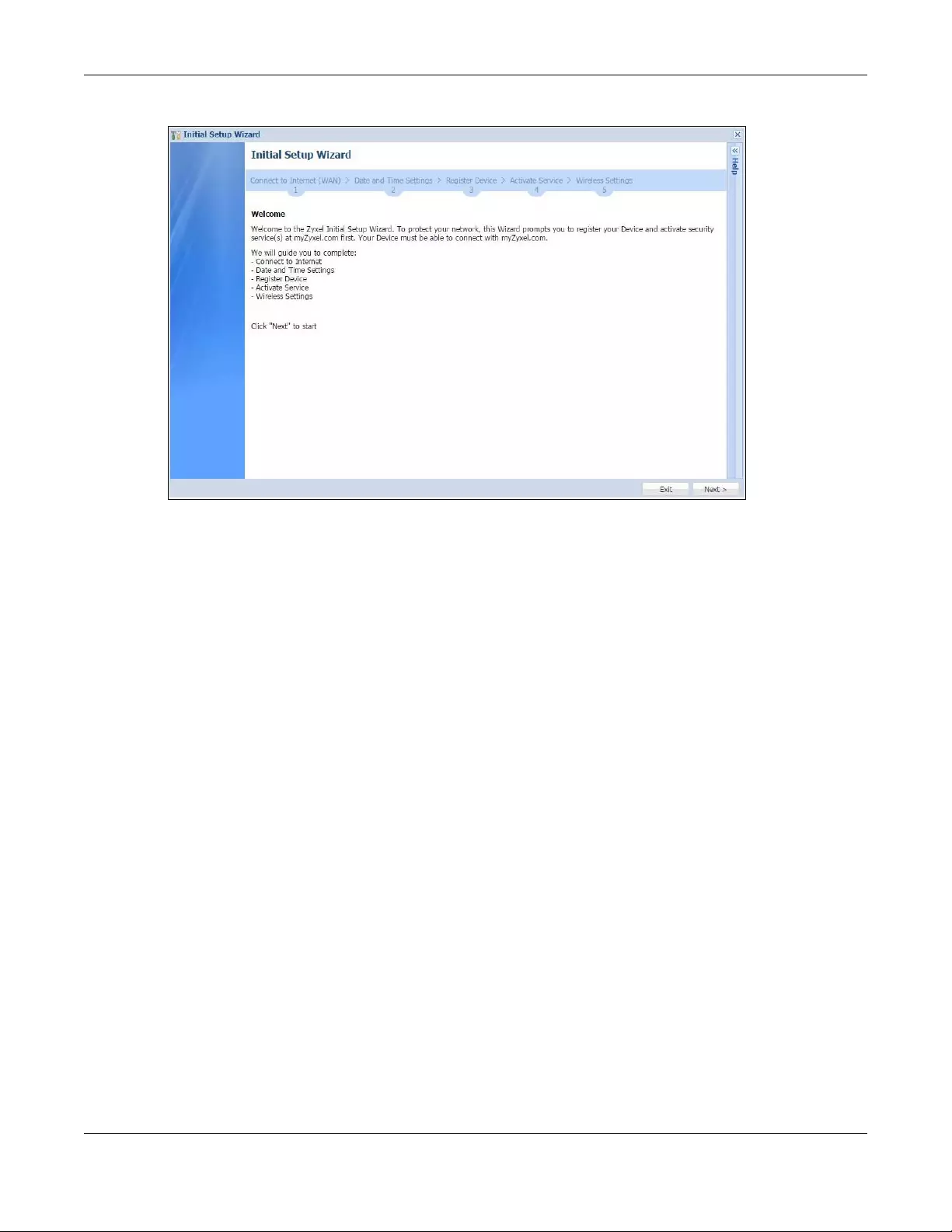
Chapter 2 Initial Setup Wizard
USG/ZyWALL User’s Guide
48
Figure 23 Initial Setup Wizard
• Click the double arrow in the upper right corner to display or hide the help.
• Click Logout to exit the Initial Setup Wizard or click Next to continue the wizard.
2.1.1 Internet Access Setup - WAN Interface
Use this screen to set how many WAN interfaces to configure and the first WAN interface’s type of
encapsulation and method of IP address assignment.
The screens vary depending on the encapsulation type. Refer to information provided by your ISP to
know what to enter in each field. Leave a field blank if you don’t have that information.
Note: Enter the Internet access information exactly as your ISP gave it to you.
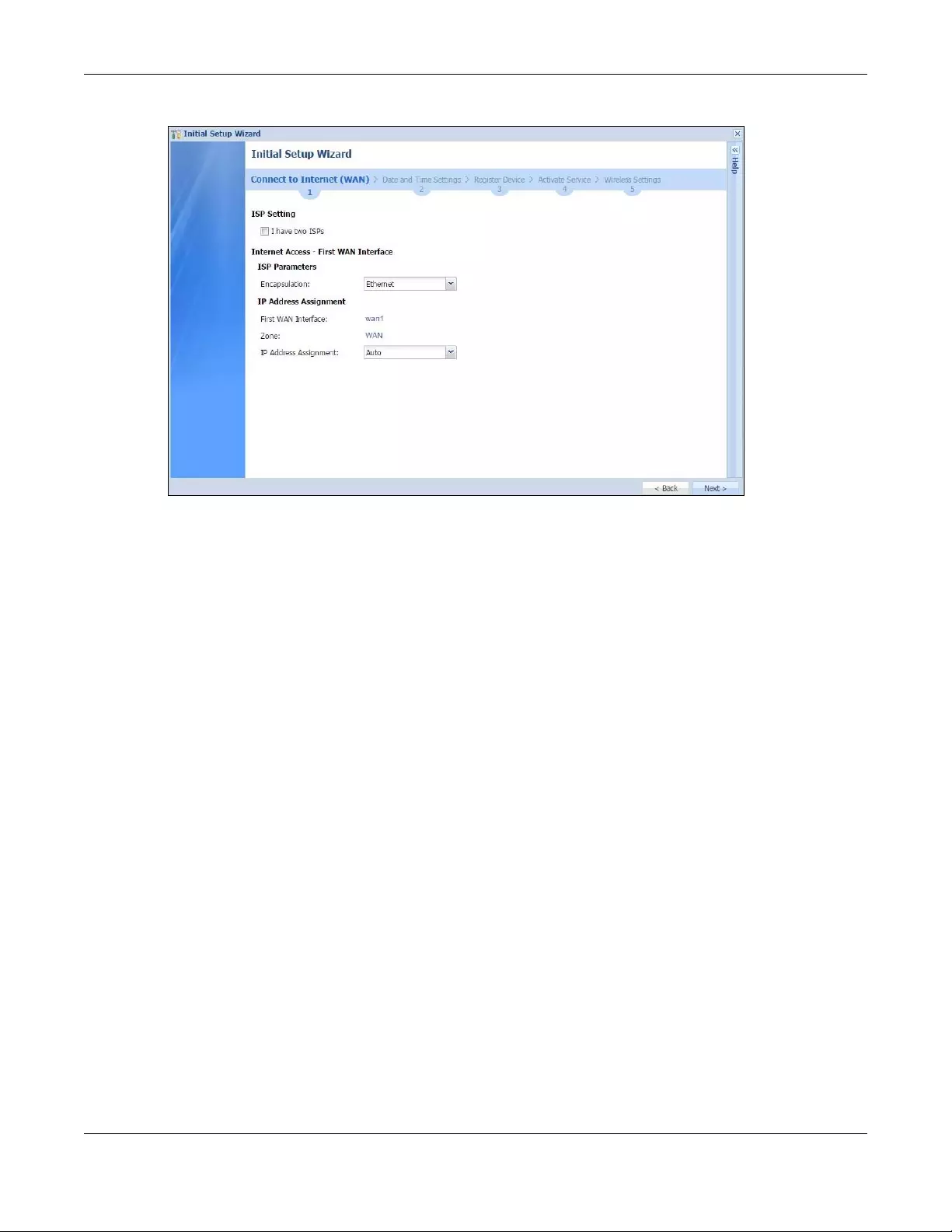
Chapter 2 Initial Setup Wizard
USG/ZyWALL User’s Guide
49
Figure 24 Internet Access
•I have two ISPs: Select this option to configure two Internet connections. Leave it cleared to configure
just one. This option appears when you are configuring the first WAN interface.
•Encapsulation: Choose the Ethernet option when the WAN port is used as a regular Ethernet. Choose
PPPoE, PPTP or L2TP for a dial-up connection according to the information from your ISP.
•WAN Interface: This is the interface you are configuring for Internet access.
•Zone: This is the security zone to which this interface and Internet connection belong.
•IP Address Assignment: Select Auto if your ISP did not assign you a fixed IP address.
Select Static if the ISP assigned a fixed IP address.
2.1.2 Internet Access: Ethernet
This screen is read-only if you set the previous screen’s IP Address Assignment field to Auto. If you set the
previous screen’s IP Address Assignment field to Static, use this screen to configure your IP address
settings.
Note: Enter the Internet access information exactly as given to you by your ISP or network
administrator.
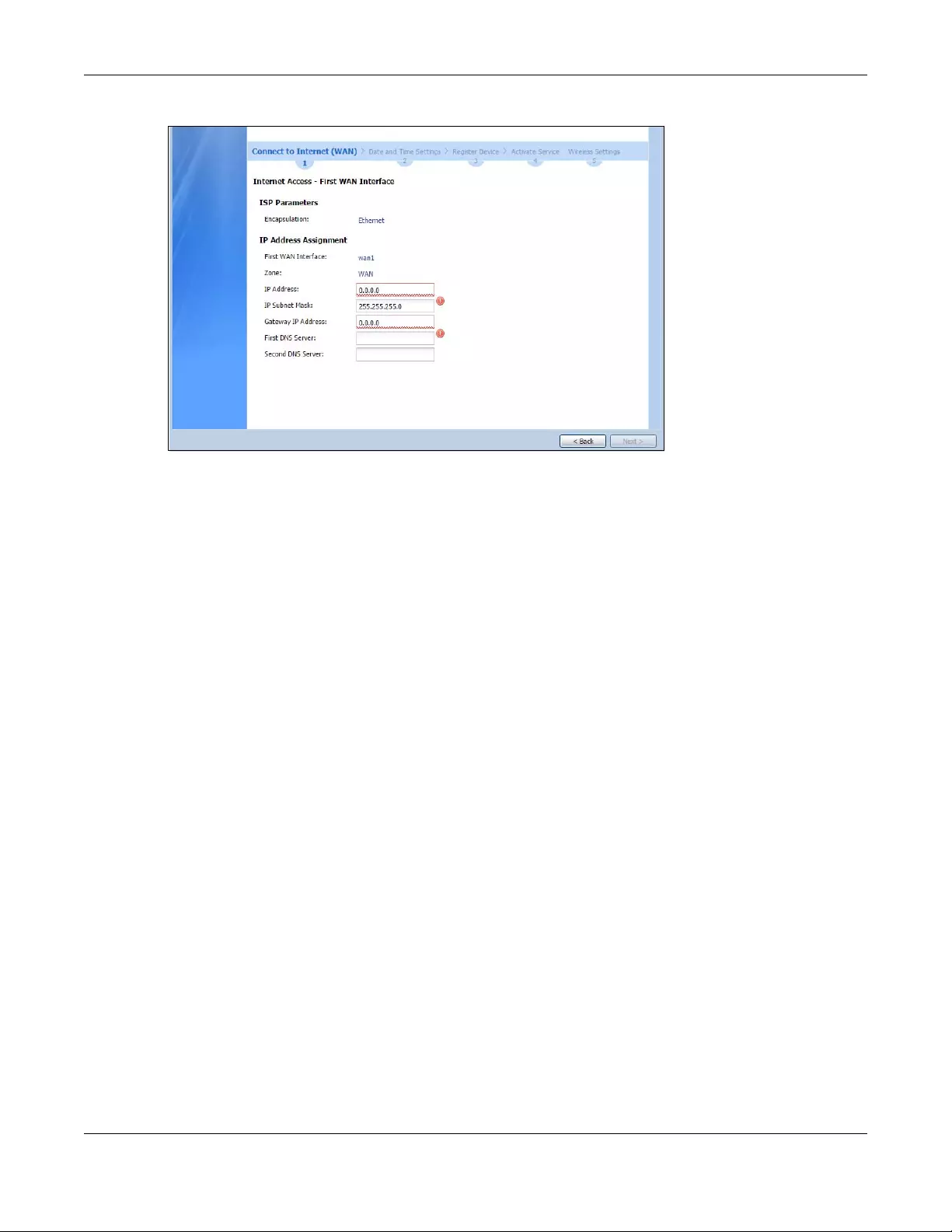
Chapter 2 Initial Setup Wizard
USG/ZyWALL User’s Guide
50
Figure 25 Internet Access: Ethernet Encapsulation
•Encapsulation: This displays the type of Internet connection you are configuring.
•First WAN Interface: This is the number of the interface that will connect with your ISP.
•Zone: This is the security zone to which this interface and Internet connection will belong.
•IP Address: Enter your (static) public IP address. Auto displays if you selected Auto as the IP Address
Assignment in the previous screen.
The following fields display if you selected static IP address assignment.
•IP Subnet Mask: Enter the subnet mask for this WAN connection's IP address.
•Gateway IP Address: Enter the IP address of the router through which this WAN connection will send
traffic (the default gateway).
•First / Second DNS Server: These fields display if you selected static IP address assignment. The Domain
Name System (DNS) maps a domain name to an IP address and vice versa. Enter a DNS server's IP
address(es). The DNS server is extremely important because without it, you must know the IP address
of a computer before you can access it. The Zyxel Device uses these (in the order you specify here) to
resolve domain names for VPN, DDNS and the time server. Leave the field as 0.0.0.0 if you do not want
to configure DNS servers.
2.1.3 Internet Access: PPPoE
Note: Enter the Internet access information exactly as given to you by your ISP.
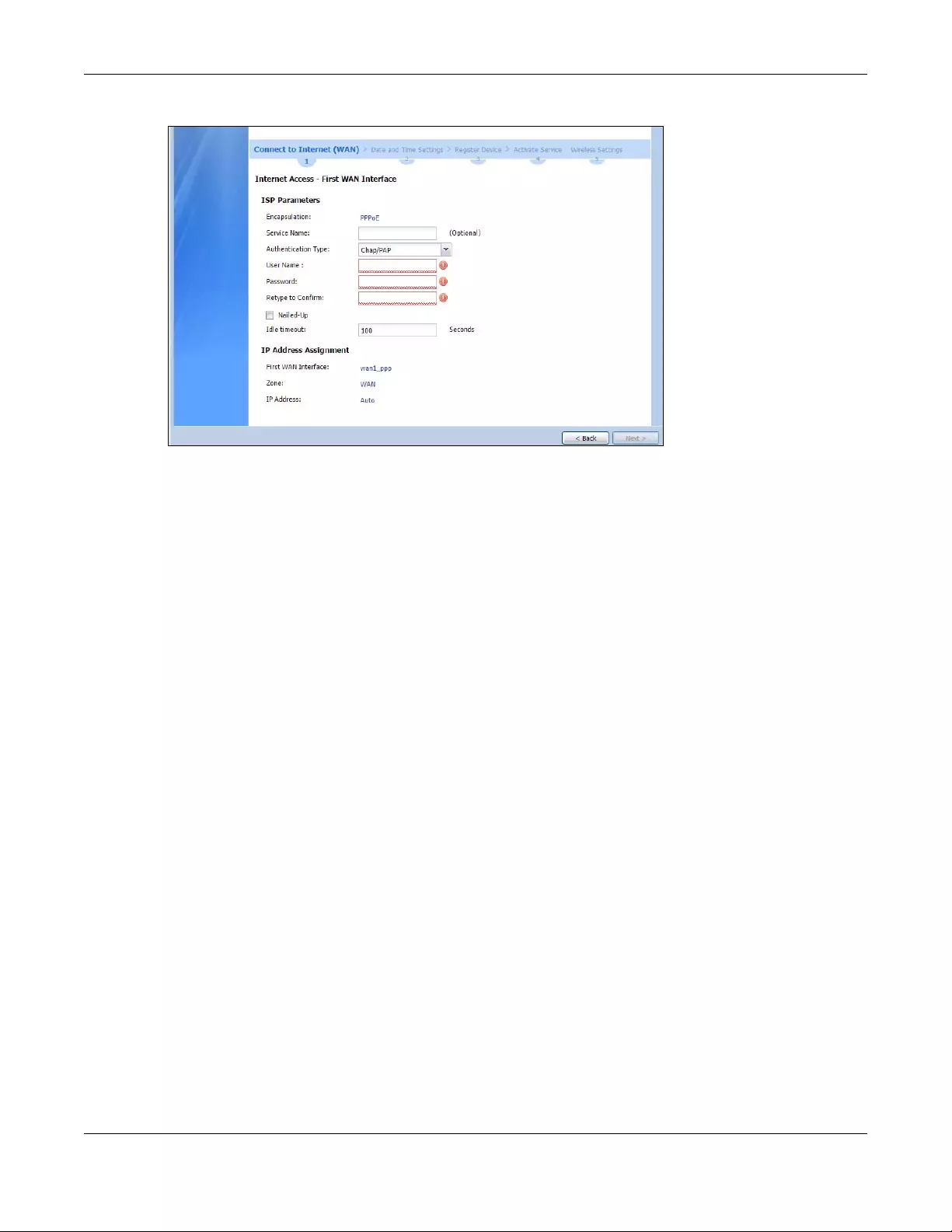
Chapter 2 Initial Setup Wizard
USG/ZyWALL User’s Guide
51
Figure 26 Internet Access: PPPoE Encapsulation
2.1.3.1 ISP Parameters
• Type the PPPoE Service Name from your service provider. PPPoE uses a service name to identify and
reach the PPPoE server. You can use alphanumeric and -_@$./ characters, and it can be up to 64
characters long.
•Authentication Type - Select an authentication protocol for outgoing connection requests. Options
are:
•CHAP/PAP - Your Zyxel Device accepts either CHAP or PAP when requested by the remote node.
•CHAP - Your Zyxel Device accepts CHAP only.
•PAP - Your Zyxel Device accepts PAP only.
•MSCHAP - Your Zyxel Device accepts MSCHAP only.
•MSCHAP-V2 - Your Zyxel Device accepts MSCHAP-V2 only.
• Type the User Name given to you by your ISP. You can use alphanumeric and -_@$./ characters, and
it can be up to 31 characters long.
•Type the Password associated with the user name. Use up to 64 ASCII characters except the [] and ?.
This field can be blank.
•Select Nailed-Up if you do not want the connection to time out. Otherwise, type the Idle Timeout in
seconds that elapses before the router automatically disconnects from the PPPoE server.
2.1.3.2 WAN IP Address Assignments
•WAN Interface: This is the name of the interface that will connect with your ISP.
•Zone: This is the security zone to which this interface and Internet connection will belong.
•IP Address: Enter your (static) public IP address. Auto displays if you selected Auto as the IP Address
Assignment in the previous screen.
•First / Second DNS Server: These fields display if you selected static IP address assignment. The Domain
Name System (DNS) maps a domain name to an IP address and vice versa. Enter a DNS server's IP
address(es). The DNS server is extremely important because without it, you must know the IP address
of a computer before you can access it. The Zyxel Device uses these (in the order you specify here) to
resolve domain names for VPN, DDNS and the time server. Leave the field as 0.0.0.0 if you do not want
to configure DNS servers. If you do not configure a DNS server, you must know the IP address of a
machine in order to access it.
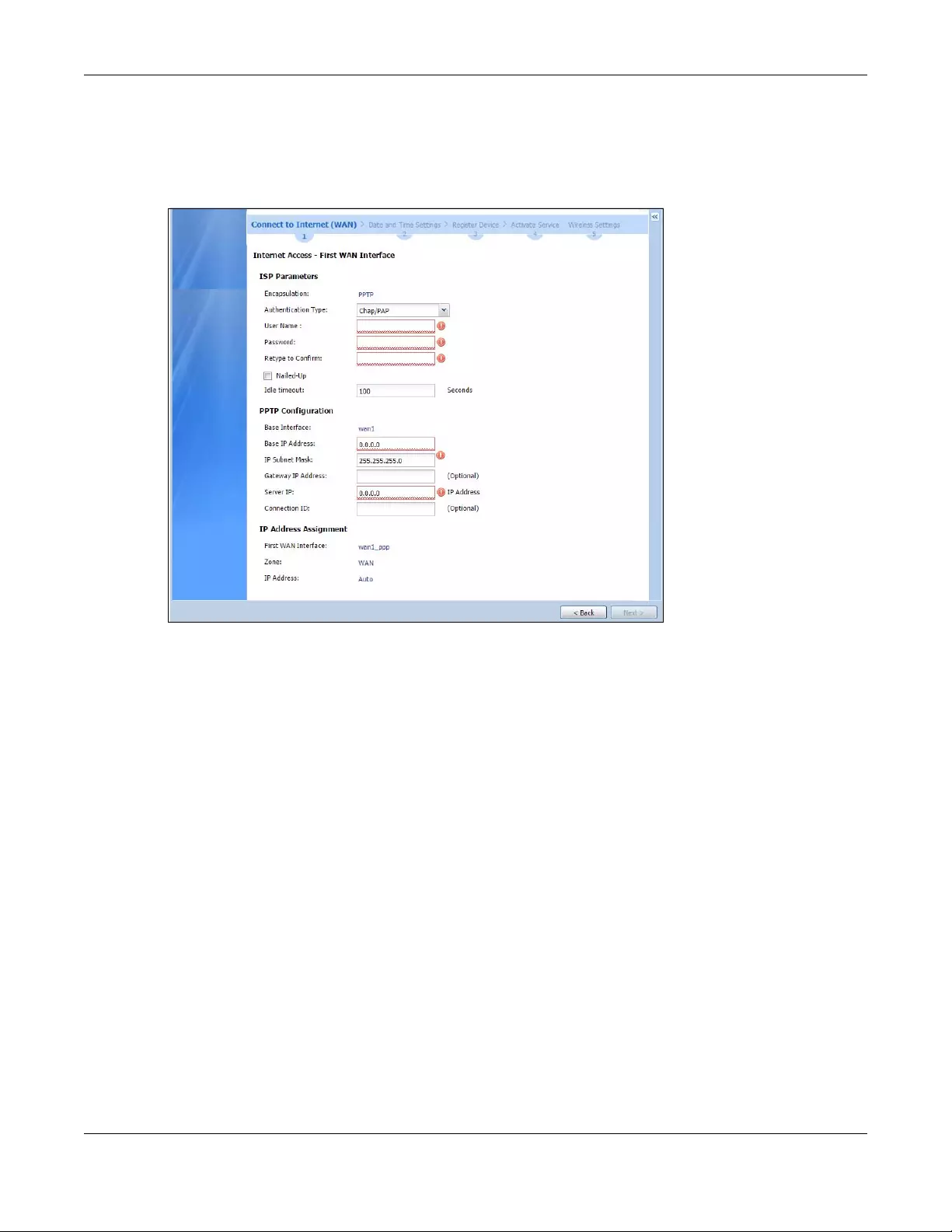
Chapter 2 Initial Setup Wizard
USG/ZyWALL User’s Guide
52
2.1.4 Internet Access: PPTP
Note: Enter the Internet access information exactly as given to you by your ISP.
Figure 27 Internet Access: PPTP Encapsulation
2.1.4.1 ISP Parameters
•Authentication Type - Select an authentication protocol for outgoing calls. Options are:
•CHAP/PAP - Your Zyxel Device accepts either CHAP or PAP when requested by the remote node.
•CHAP - Your Zyxel Device accepts CHAP only.
•PAP - Your Zyxel Device accepts PAP only.
•MSCHAP - Your Zyxel Device accepts MSCHAP only.
•MSCHAP-V2 - Your Zyxel Device accepts MSCHAP-V2 only.
• Type the User Name given to you by your ISP. You can use alphanumeric and -_@$./ characters, and
it can be up to 31 characters long.
•Type the Password associated with the user name. Use up to 64 ASCII characters except the [] and ?.
This field can be blank. Re-type your password in the next field to confirm it.
•Select Nailed-Up if you do not want the connection to time out. Otherwise, type the Idle Timeout in
seconds that elapses before the router automatically disconnects from the PPTP server.
2.1.4.2 PPTP Configuration
•Base Interface: This identifies the Ethernet interface you configure to connect with a modem or router.
•Type a Base IP Address (static) assigned to you by your ISP.
• Type the IP Subnet Mask assigned to you by your ISP (if given).
•Server IP: Type the IP address of the PPTP server.
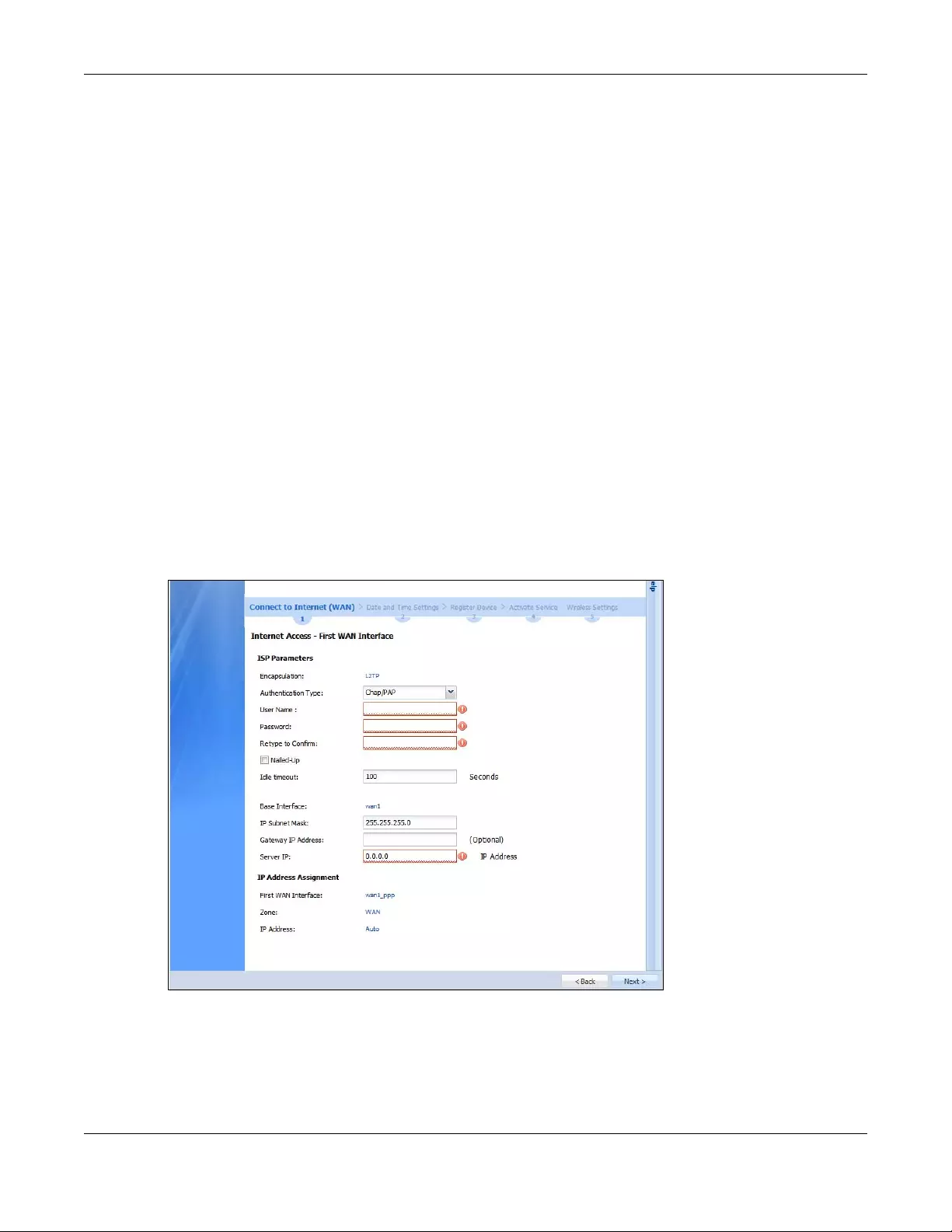
Chapter 2 Initial Setup Wizard
USG/ZyWALL User’s Guide
53
•Type a Connection ID or connection name. It must follow the “c:id” and “n:name” format. For
example, C:12 or N:My ISP. This field is optional and depends on the requirements of your broadband
modem or router. You can use alphanumeric and -_: characters, and it can be up to 31 characters
long.
2.1.4.3 WAN IP Address Assignments
•First WAN Interface: This is the connection type on the interface you are configuring to connect with
your ISP.
•Zone This is the security zone to which this interface and Internet connection will belong.
•IP Address: Enter your (static) public IP address. Auto displays if you selected Auto as the IP Address
Assignment in the previous screen.
•First / Second DNS Server: These fields display if you selected static IP address assignment. The Domain
Name System (DNS) maps a domain name to an IP address and vice versa. Enter a DNS server's IP
address(es). The DNS server is extremely important because without it, you must know the IP address
of a computer before you can access it. The Zyxel Device uses these (in the order you specify here) to
resolve domain names for VPN, DDNS and the time server. Leave the field as 0.0.0.0 if you do not want
to configure DNS servers.
2.1.5 Internet Access: L2TP
Note: Enter the Internet access information exactly as given to you by your ISP or network
administrator.
Figure 28 Internet Access: L2TP Encapsulation
2.1.5.1 ISP Parameters
•Authentication Type - Select an authentication protocol for outgoing connection requests. Options
are:
•CHAP/PAP - Your Zyxel Device accepts either CHAP or PAP when requested by the remote node.
•CHAP - Your Zyxel Device accepts CHAP only.
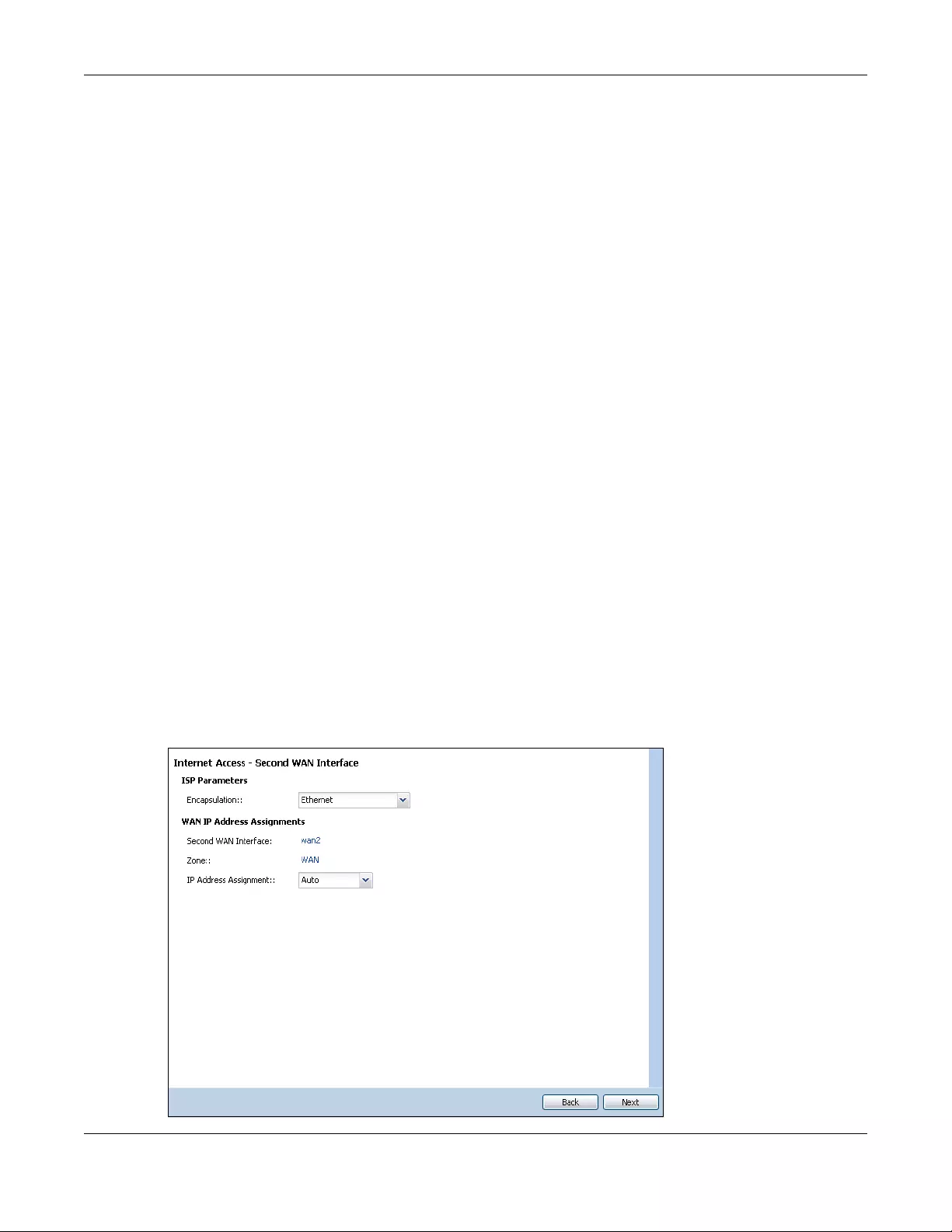
Chapter 2 Initial Setup Wizard
USG/ZyWALL User’s Guide
54
•PAP - Your Zyxel Device accepts PAP only.
•MSCHAP - Your Zyxel Device accepts MSCHAP only.
•MSCHAP-V2 - Your Zyxel Device accepts MSCHAP-V2 only.
• Type the User Name given to you by your ISP. You can use alphanumeric and -_@$./ characters, and
it can be up to 31 characters long.
•Type the Password associated with the user name. Use up to 64 ASCII characters except the [] and ?.
This field can be blank.
•Select Nailed-Up if you do not want the connection to time out. Otherwise, type the Idle Timeout in
seconds that elapses before the router automatically disconnects from the PPPoE server.
2.1.5.2 L2TP Configuration
•Base Interface: This identifies the Ethernet interface you configure to connect with a modem or router.
•IP Subnet Mask: Enter the subnet mask for this WAN connection's IP address.
•Gateway IP Address: Enter the IP address of the router through which this WAN connection will send
traffic (the default gateway).
•Server IP: Type the IP address of the L2TP server.
2.1.5.3 WAN IP Address Assignments
•WAN Interface: This is the name of the interface that will connect with your ISP.
•Zone: This is the security zone to which this interface and Internet connection will belong.
•IP Address: Enter your (static) public IP address. Auto displays if you selected Auto as the IP Address
Assignment in the previous screen.
2.1.6 Internet Access Setup - Second WAN Interface
If you selected I have two ISPs, after you configure the First WAN Interface, you can configure the
Second WAN Interface. The screens for configuring the second WAN interface are similar to the first (see
Section 2.1.1 on page 48).
Figure 29 Internet Access: Step 3: Second WAN Interface
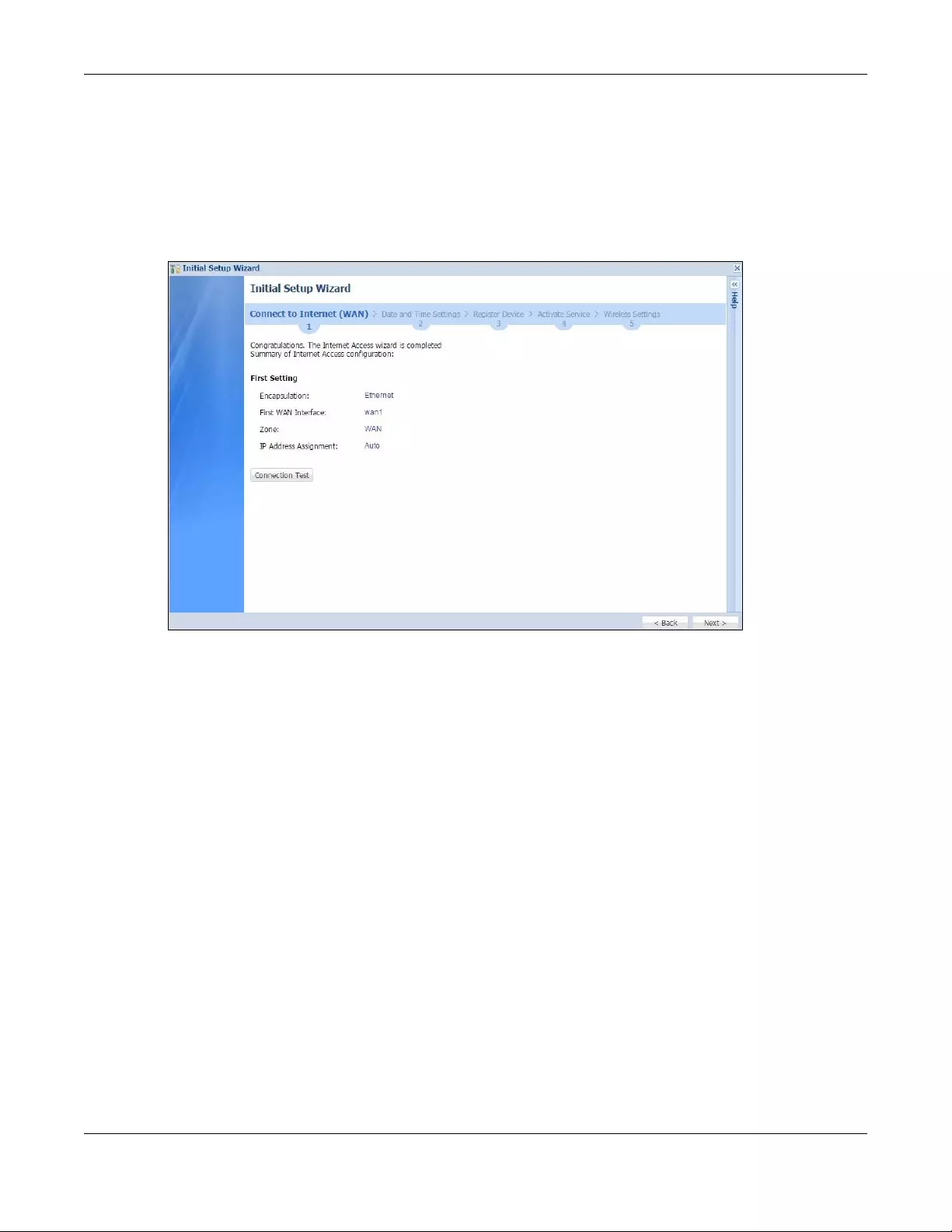
Chapter 2 Initial Setup Wizard
USG/ZyWALL User’s Guide
55
2.1.7 Internet Access: Finish
You have set up your Zyxel Device to access the Internet. A screen displays with your settings. Click
Connection Test to check that you can access the Internet. If you cannot, click Back and confirm that
you entered the settings correctly. If you have, check that you got the correct settings from your ISP or
network administrator.
Figure 30 Internet Access: Finish
2.1.8 Date and Time Settings
It’s important to have correct date and time values in the logs. The Zyxel Device can automatically
update the time and date by detecting your time zone and whether Daylight Savings is in effect in that
time zone.
If your Zyxel Device cannot get the correct date and time, it may not able to connect to a time server.
Check that the Zyxel Device has Internet access, then click Sync. Now.
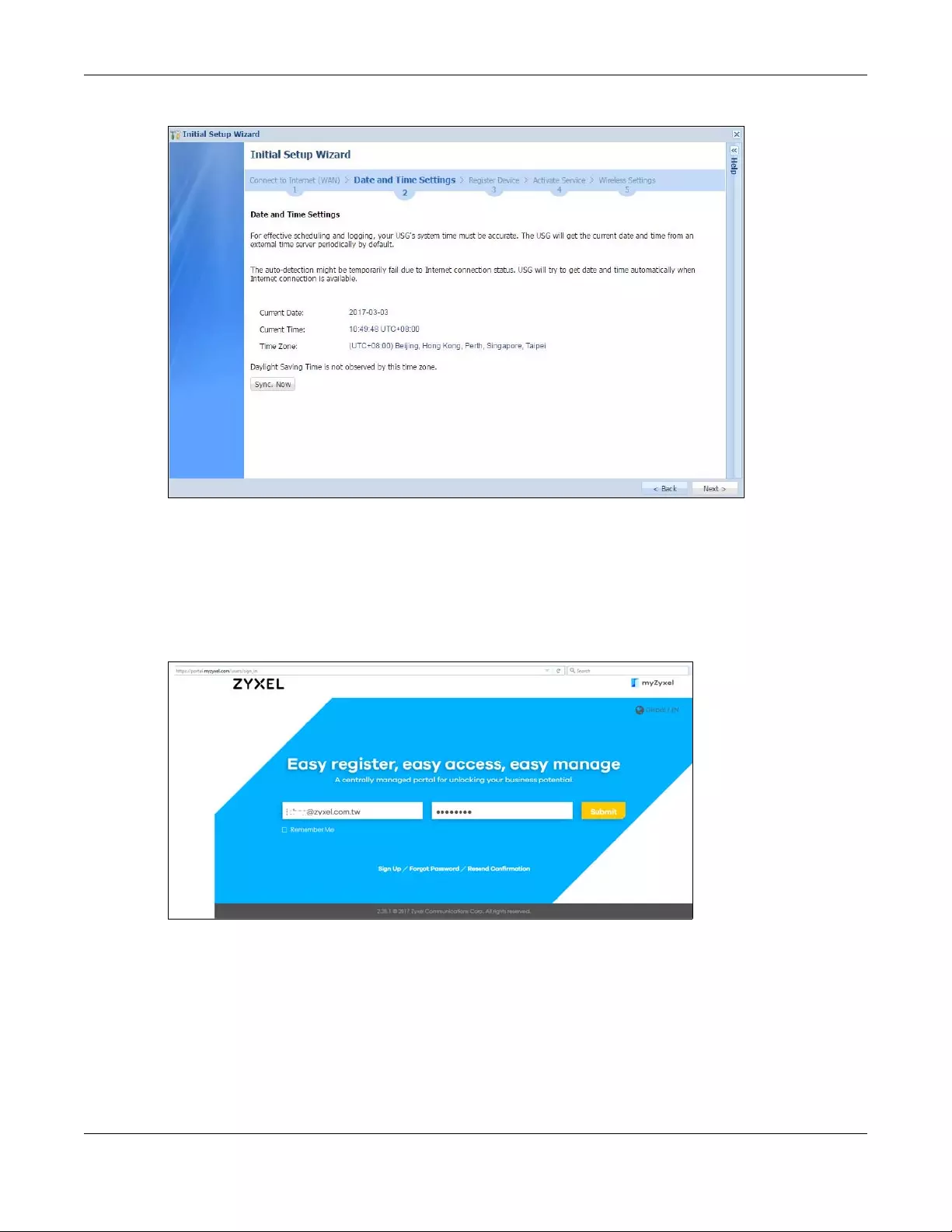
Chapter 2 Initial Setup Wizard
USG/ZyWALL User’s Guide
56
Figure 31 Date and Time Settings
2.1.9 Register Device
Click the Register button in this screen to register your device at portal.myzyxel.com.
Note: The Zyxel Device must be connected to the Internet in order to register.
Figure 32 myZyxel Login
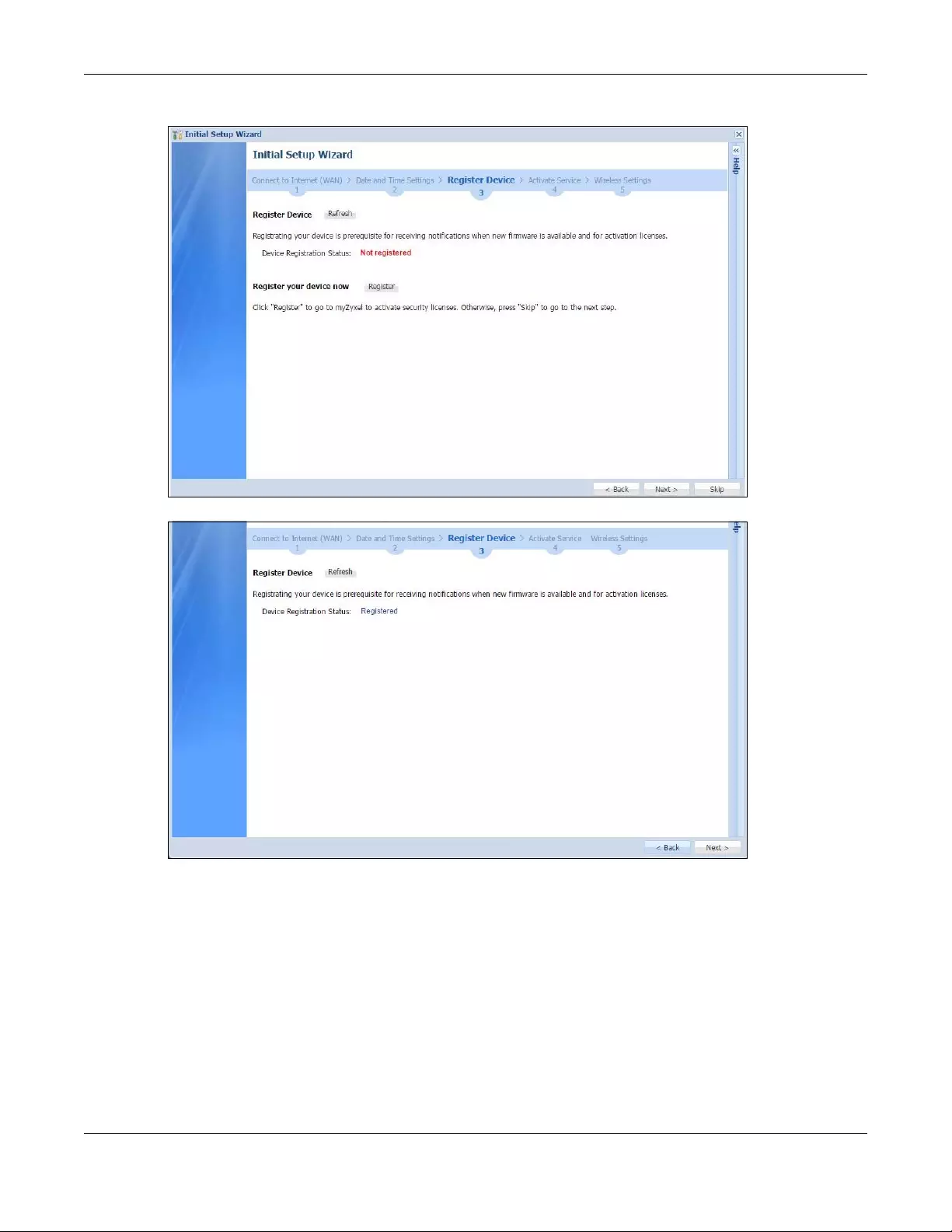
Chapter 2 Initial Setup Wizard
USG/ZyWALL User’s Guide
57
Figure 33 Register Device
Figure 34 Registered Device
You may need the Zyxel Device’s serial number and LAN MAC address to register it at myZyxel.com if
you have not already done so. Refer to the label at the back of the Zyxel Device’s for details. Use the
Configuration > Licensing > Registration screen to update your Zyxel Device registration status.
2.1.10 Activate Service
After you register your Zyxel Device, you can register for the services supported by your model. Examples
of services are:
• Content Filter (to block websites by category, such as Gambling)
• IDP (to recognize and drop traffic with Intrusion, Detection & Protection attack patterns)
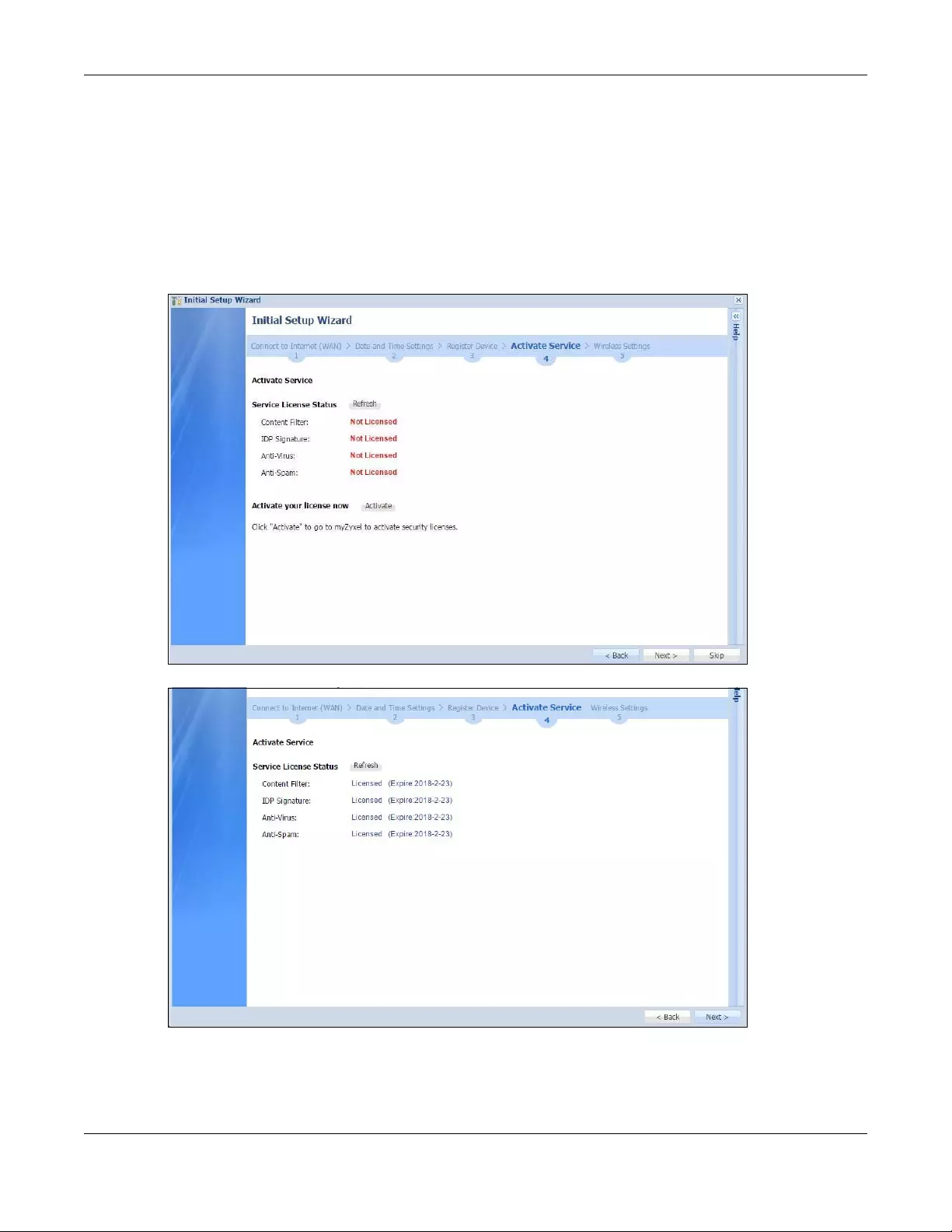
Chapter 2 Initial Setup Wizard
USG/ZyWALL User’s Guide
58
• Anti-Virus (to detect virus patterns in files)
• Anti-Spam (to mark or discard unsolicited commercial or junk e-mail suspect of being sent by
spammers).
Click Refresh and wait a few moments for the registration information to update in this screen. If the
page does not refresh, make sure the Internet connection is working and click Refresh again. To check
your Internet connection, try to access the Internet from a computer connected to a LAN port on the
Zyxel Device. If you cannot, then check your Internet access settings on the Zyxel Device
Figure 35 Activate Service
Figure 36 Activated Service
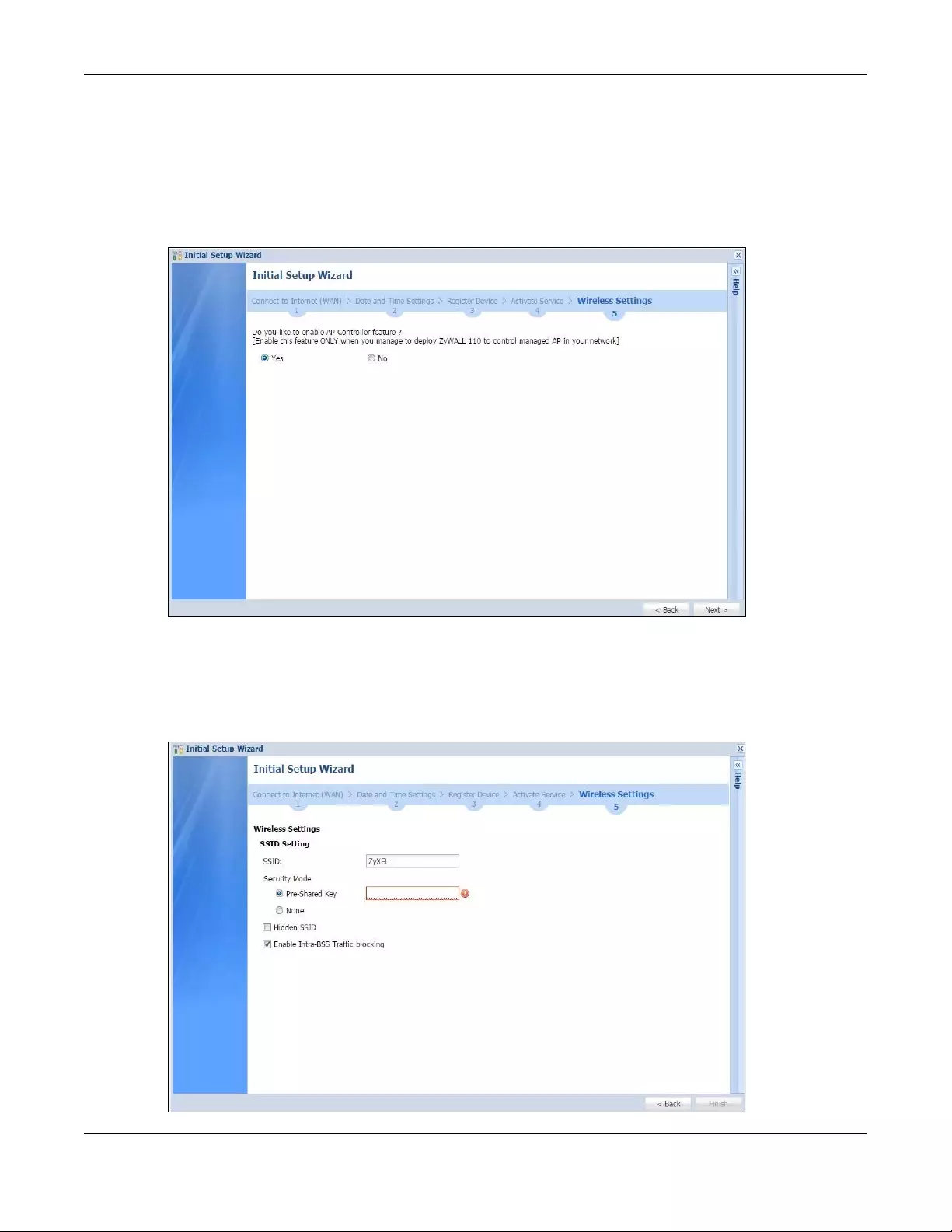
Chapter 2 Initial Setup Wizard
USG/ZyWALL User’s Guide
59
2.1.11 Wireless Settings: AP Controller
The Zyxel Device can act as an AP Controller that can manage APs in the same network as the Zyxel
Device. Select Yes if you want your Zyxel Device to manage APs in your network; otherwise select No.
• USG20-VPN and USG20W-VPN do not support the AP controller function.
Figure 37 Wireless Settings: AP Controller
2.1.12 Wireless Settings: SSID & Security
Configure SSID and wireless security in this screen.
Figure 38 Wireless Settings: SSID & Security

Chapter 2 Initial Setup Wizard
USG/ZyWALL User’s Guide
60
SSID Setting
•SSID - Enter a descriptive name of up to 32 printable characters for the wireless LAN.
•Security Mode - Select Pre-Shared Key to add security on this wireless network. Otherwise, select None
to allow any wireless client to associate this network without authentication.
•Pre-Shared Key - Enter a pre-shared key of between 8 and 63 case-sensitive ASCII characters
(including spaces and symbols) or 64 hexadecimal characters.
•Hidden SSID - Select this option if you want to hide the SSID in the outgoing beacon frame. A wireless
client then cannot obtain the SSID through scanning using a site survey tool.
•Enable Intra-BSS Traffic Blocking - Select this option if you want to prevent crossover traffic from within
the same SSID. Wireless clients can still access the wired network but cannot communicate with each
other.
For Built-in Wireless AP Only
•Bridged to: Zyxel Devices with W in the model name have a built-in AP. Select an interface to bridge
with the built-in AP wireless network. Devices connected to this interface will then be in the same
broadcast domain as devices in the AP wireless network.
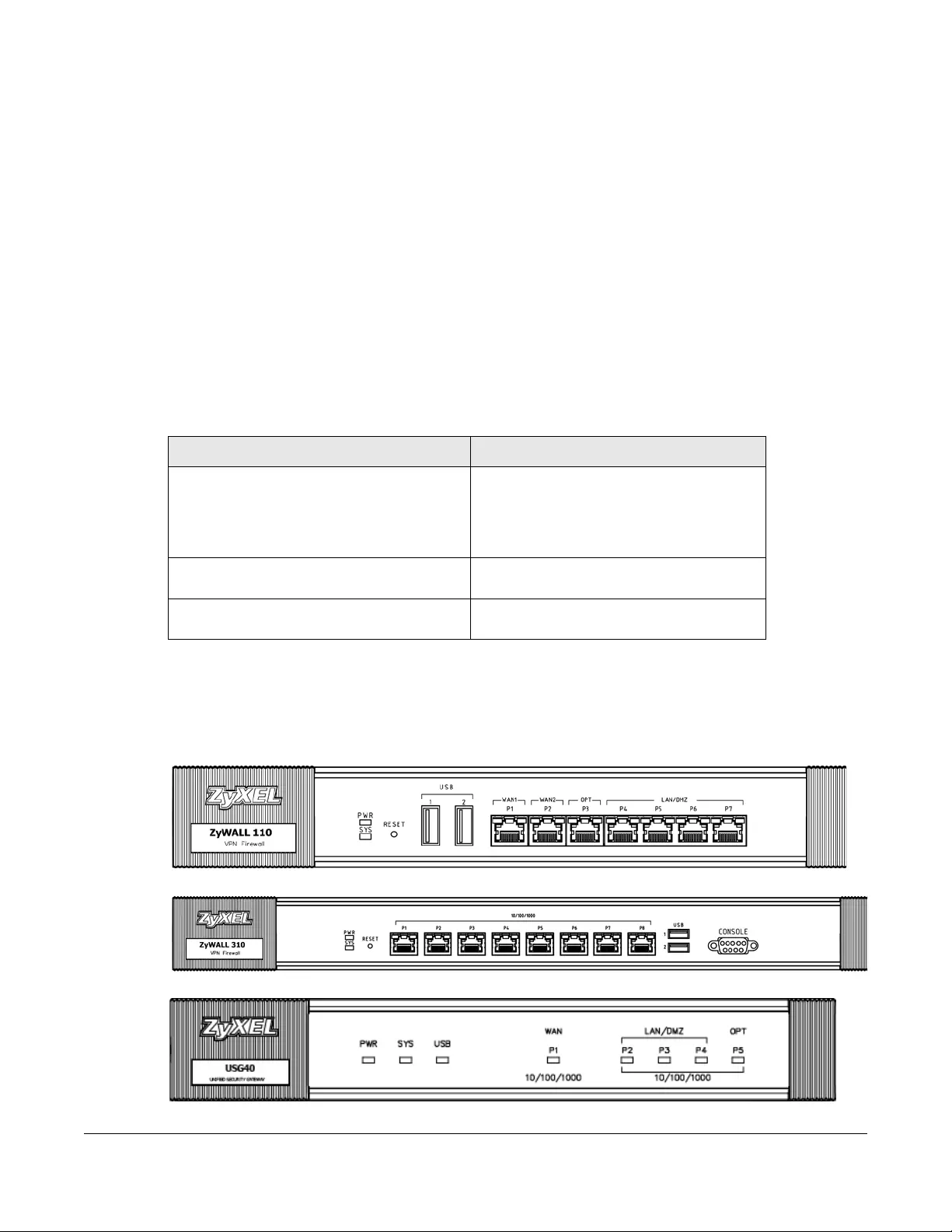
USG/ZyWALL User’s Guide
61
CHAPTER 3
Hardware, Interfaces and
Zones
3.1 Hardware Overview
This table is an overview of the different housings in the series.
3.1.1 Front Panels
The LED indicators are located on the front panel.
Figure 39 ZyWALL 110 / USG110 / USG210 Front Panel
Figure 40 ZyWALL 310 / ZyWALL 1100 / USG310 / USG1100 / USG1900 Front Panel
Figure 41 USG40 Front Panel
Table 10 Housing Comparison
MODELS WITH SAME HARDWARE MODELS WITH SAME HARDWARE
• ZyWALL 110
• USG110
• USG210
• ZyWALL 310
• ZyWALL 1100
•USG310
• USG1100
• USG1900
•USG40
• USG40W (with two antennas)
•USG60
• USG60W (with four antennas)
• USG20-VPN
• USG20W-VPN (with three antennas)
• USG2200-VPN
•
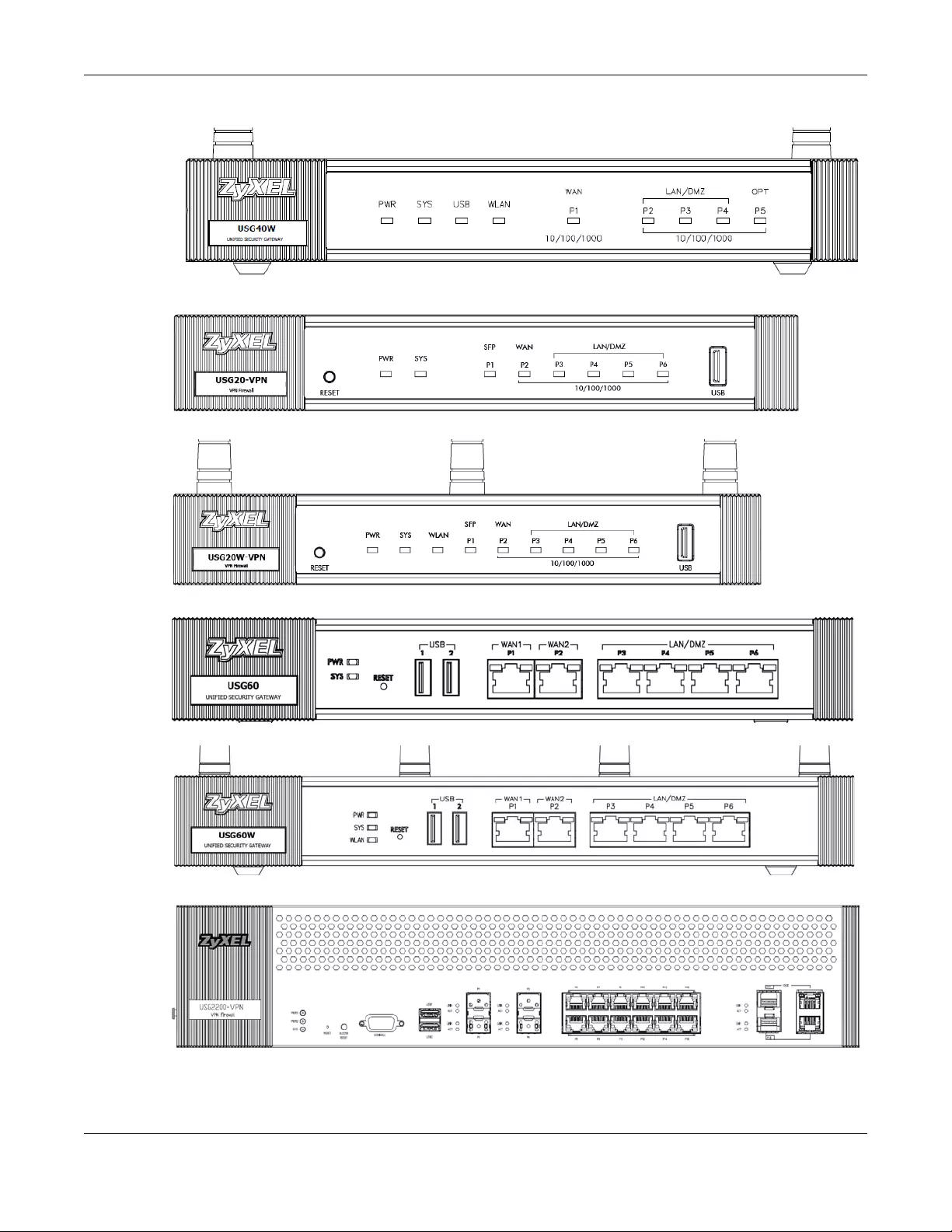
Chapter 3 Hardware, Interfaces and Zones
USG/ZyWALL User’s Guide
62
Figure 42 USG40W Front Panel
Figure 43 USG20-VPN Front Panel
Figure 44 USG20W-VPN / VPN20W Front Panel
Figure 45 USG60 Front Panel
Figure 46 USG60W Front Panel
Figure 47 USG2200-VPN Front Panel
Chapter 3 Hardware, Interfaces and Zones
USG/ZyWALL User’s Guide
63
The following table describes the LEDs.
The following table describes the USG2200-VPN and VPN3000 LEDs.
Table 11 LED Descriptions
LED COLOR STATUS DESCRIPTION
PWR Off The Zyxel Device is turned off.
Green On The Zyxel Device is turned on.
Red On There is a hardware component failure. Shut down the device, wait for a few
minutes and then restart the device. If the LED turns red again, then please
contact your vendor.
SYS Green Off The Zyxel Device is not ready or has failed.
On The Zyxel Device is ready and running.
Blinking The Zyxel Device is booting.
Red On The Zyxel Device encountered an error or has failed.
USB Green Off No device is connected to the Zyxel Device’s USB port or the connected device
is not supported by the Zyxel Device.
On A mobile broadband USB card or USB storage device is connected to the USB
port.
Orange On Connected to a mobile broadband network through the connected mobile
broadband USB card.
P1, P2... Green Off There is no traffic on this port.
Blinking The Zyxel Device is sending or receiving packets on this port.
Orange Off There is no connection on this port.
On This port has a successful link.
Table 12 USG2200-VPN LED Descriptions
LED COLOR STATUS DESCRIPTION
PWR1, 2 Off The Zyxel Device is turned off.
Green On The Zyxel Device is turned on.
Red On There is a hardware component failure. Shut down the device, wait for a few
minutes and then restart the device. If the LED turns red again, then please
contact your vendor.
SYS Green Off The Zyxel Device is not ready or has failed.
On The Zyxel Device is ready and running.
Blinking The Zyxel Device is booting.
Red On The Zyxel Device encountered an error or has failed.
P1-P4
(SFP) Link
Green Off There is no connection on this port.
On This port has a successful 100Mbps link.
Orange Off There is no connection on this port.
On This port has a successful 1000Mbps link.
P1-P4
(SFP) ACT
Green Off There is no traffic on this port.
On The Zyxel Device is sending or receiving packets on this port.
Chapter 3 Hardware, Interfaces and Zones
USG/ZyWALL User’s Guide
64
The following table describes the ports on the front panel.
The following table describes the ports on the USG2200-VPN front panel.
P5-P16
(WAN/
LAN))
Green Off There is no connection on this port.
On This port has a successful 10/100Mbps link.
Blinking The Zyxel Device is sending or receiving packets on this port.
Orange Off There is no connection on this port.
On This port has a successful 1000Mbps link.
Blinking The Zyxel Device is sending or receiving packets on this port.
P17-P18
(SFP+)
Link
Blue Off There is no connection on this port.
On This port has a successful 10Gbps link.
P17-P18
(SFP+)
ACT
Green Off There is no traffic on this port.
Blinking The Zyxel Device is sending or receiving packets on this port.
P17-P18
(10GE)
Link
Blue Off There is no connection on this port.
On This port has a successful 10Gbps link.
P17-P18
(10GE)
ACT
Green Off There is no traffic on this port.
Blinking The Zyxel Device is sending or receiving packets on this port.
Table 13 Front Panel Ports
LABEL DESCRIPTION
RESET Press the button in for about 5 seconds (or until the SYS LED starts to blink), then release it to
return the Zyxel Device to the factory defaults (password is 1234, LAN IP address 192.168.1.1
etc.)
CONSOLE You can use the console port to manage the Zyxel Device using CLI commands. You will be
prompted to enter your user name and password. See the Command Reference Guide for
more information about the CLI.
When configuring using the console port, you need a computer equipped with
communications software configured to the following parameters:
• Speed 115200 bps
• Data Bits 8
•Parity None
•Stop Bit 1
• Flow Control Off
USB Connect a storage device for system logs (see Maintenance > Diagnostics > System Log) and
storage (see Configuration > System > USB Storage).
P1 ~ P6 These are 1G RJ-45 Ethernet ports.
Table 14 USG2200-VPN Front Panel Ports
LABEL DESCRIPTION
RESET Press the button in for about 5 seconds (or until the SYS LED starts to blink), then release it to
return the Zyxel Device to the factory defaults (password is 1234, LAN IP address 192.168.1.1
etc.)
BUZZER RESET The buzzer alarms when a power module fails. Use this to mute the buzzer alarm.
Table 12 USG2200-VPN LED Descriptions (continued)
LED COLOR STATUS DESCRIPTION
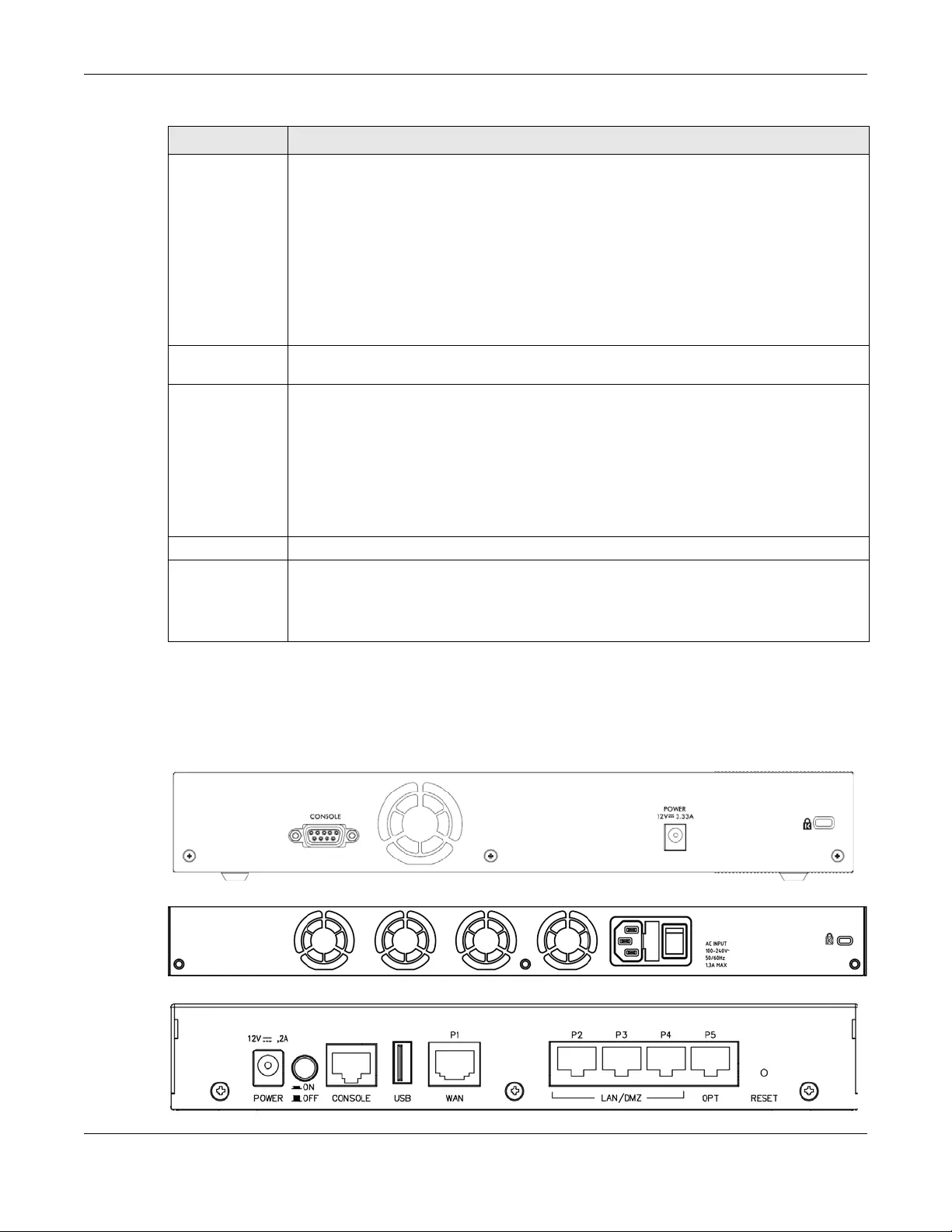
Chapter 3 Hardware, Interfaces and Zones
USG/ZyWALL User’s Guide
65
3.1.2 Rear Panels
The connection ports are located on the rear panel.
Figure 48 ZyWALL 110 / USG110 / USG210 Rear Panel
Figure 49 ZyWALL 310 / ZyWALL 1100 / USG310 / USG1100 / USG1900 Rear Panel
Figure 50 USG40 / USG40W Rear Panel
CONSOLE You can use the console port to manage the Zyxel Device using CLI commands. You will be
prompted to enter your user name and password. See the Command Reference Guide for
more information about the CLI.
When configuring using the console port, you need a computer equipped with
communications software configured to the following parameters:
• Speed 115200 bps
• Data Bits 8
•Parity None
•Stop Bit 1
• Flow Control Off
USB Connect a storage device for system logs (see Maintenance > Diagnostics > System Log) and
storage (see Configuration > System > USB Storage).
P1 ~ P4 These are SFP (1G) ports. These are compatible 1G transceiver modules (at the time of writing):
• SFP-1000T
•SFP-SX-D
• SFP-LX-10-D
• SFP-BX1310-10-D
• SFP-BX1490-10-D
• SFP-LHX1310-40-D
•SFP-ZX-80-D
P5 ~ P16 These are 1G RJ-45 Ethernet ports.
P17 ~ P18 These are 10G combo (SFP+ & RJ-45) ports. These are compatible 10G transceiver modules (at
the time of writing:)
• SFP10G-SR
• SFP10G-LR
Table 14 USG2200-VPN Front Panel Ports (continued)
LABEL DESCRIPTION
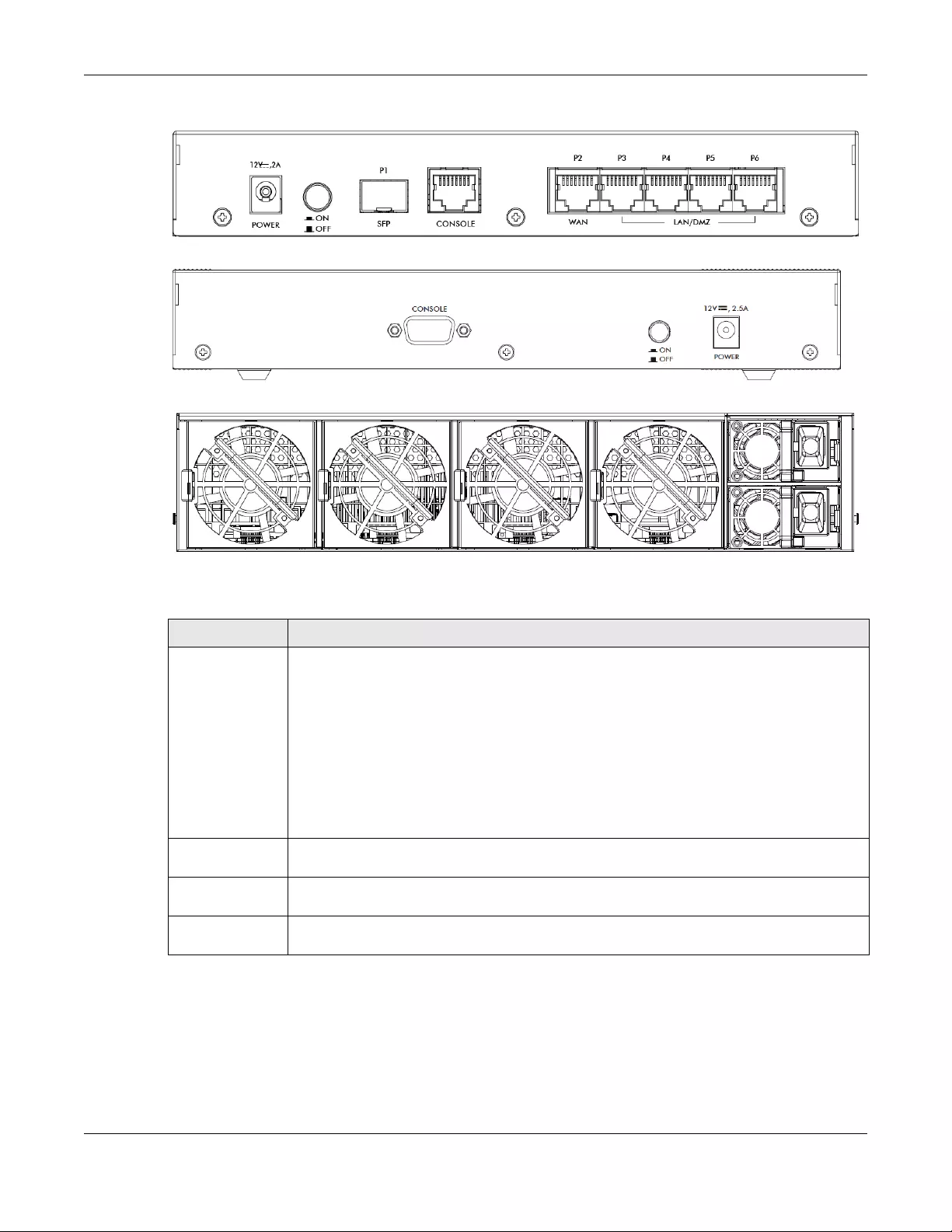
Chapter 3 Hardware, Interfaces and Zones
USG/ZyWALL User’s Guide
66
Figure 51 USG20-VPN / USG20W-VPN Rear Panel
Figure 52 USG60 / USG60W Rear Panel
Figure 53 USG2200-VPN Rear Panel
The following table describes the items on the rear panel.
Note: Use an 8-wire Ethernet cable to run your Gigabit Ethernet connection at 1000 Mbps.
Using a 4-wire Ethernet cable limits your connection to 100 Mbps. Note that the
connection speed also depends on what the Ethernet device at the other end can
support.
Table 15 Rear Panel Items
LABEL DESCRIPTION
Console You can use the console port to manage the Zyxel Device using CLI commands. You will be
prompted to enter your user name and password. See the Command Reference Guide for
more information about the CLI.
When configuring using the console port, you need a computer equipped with
communications software configured to the following parameters:
• Speed 115200 bps
• Data Bits 8
•Parity None
•Stop Bit 1
• Flow Control Off
Power Use the included power cord to connect the power socket to a power outlet. Turn the power
switch on if your Zyxel Device has a power switch.
Lock Attach a lock-and-cable from the Kensington lock (the small, metal-reinforced, oval hole) to a
permanent object, such as a pole, to secure the Zyxel Device in place.
Fan The fans are for cooling the Zyxel Device. Make sure they are not obstructed to allow maximum
ventilation.
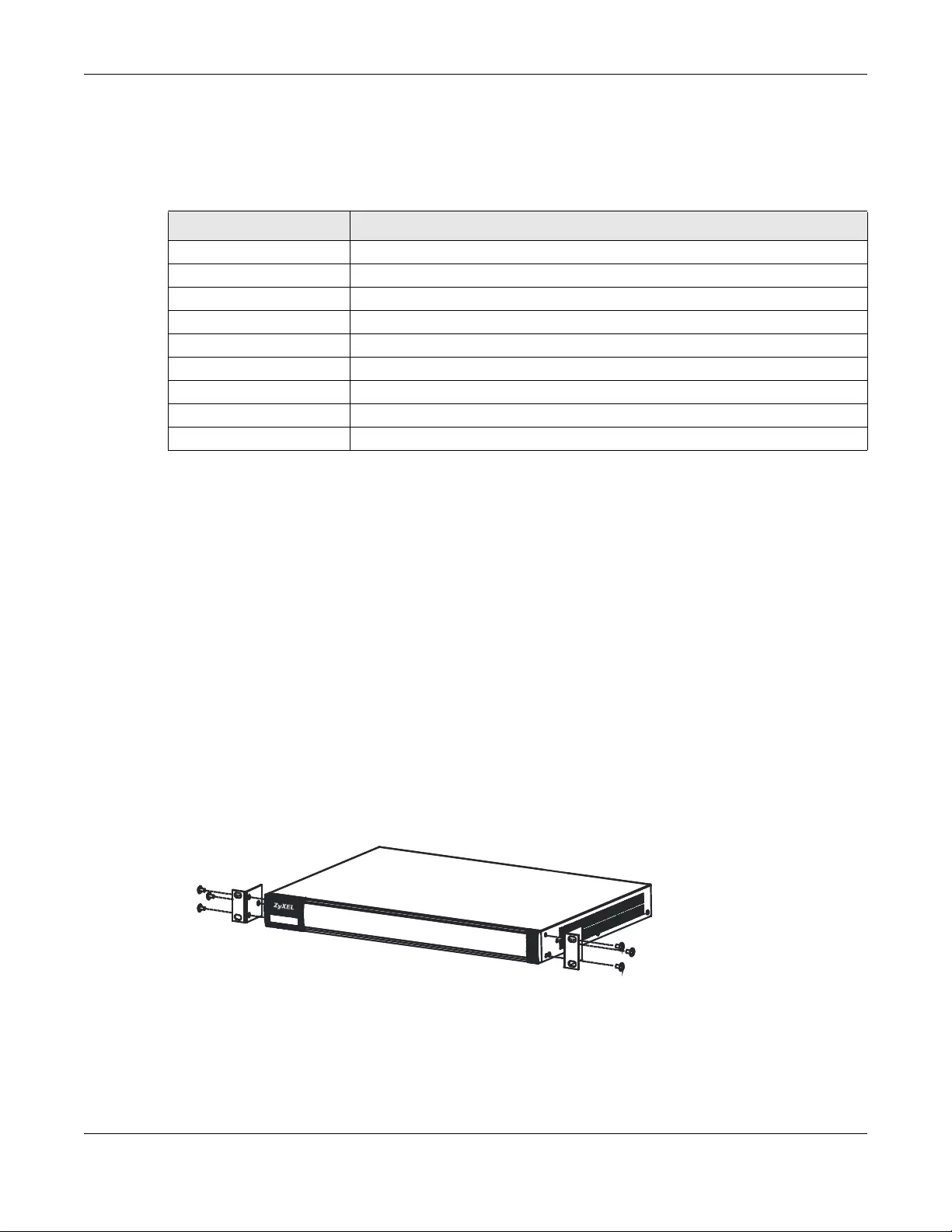
Chapter 3 Hardware, Interfaces and Zones
USG/ZyWALL User’s Guide
67
3.2 Mounting
Some models can be mounted in a rack, and some can be mounted on a wall.
3.2.1 Rack-mounting
See Table 16 on page 67 for the Zyxel Device models that can be rack mounted. Use the following steps
to mount the Zyxel Device on an EIA standard size, 19-inch rack or in a wiring closet with other
equipment using a rack-mounting kit. Make sure the rack will safely support the combined weight of all
the equipment it contains and that the position of the ZyWALL does not make the rack unstable or top-
heavy. Take all necessary precautions to anchor the rack securely before installing the unit.
Note: Leave 10 cm of clearance at the sides and 20 cm in the rear.
Use a #2 Phillips screwdriver to install the screws.
Note: Failure to use the proper screws may damage the unit.
1Align one bracket with the holes on one side of the Zyxel Device and secure it with the included bracket
screws (smaller than the rack-mounting screws).
2Attach the other bracket in a similar fashion.
3After attaching both mounting brackets, position the Zyxel Device in the rack and match up the bracket
holes with the rack holes. Secure the Zyxel Device to the rack with the rack-mounting screws.
Table 16 Mounting Method
RACK-MOUNTING WALL-MOUNTING
•ZyWALL 110 •USG40
•ZyWALL 310 •USG40W
•ZyWALL 1100 •USG60
•USG110 •USG60W
• USG210 • USG20-VPN
•USG310 •USG20W-VPN
• USG1100 •
• USG1900 •
• USG2200-VPN •
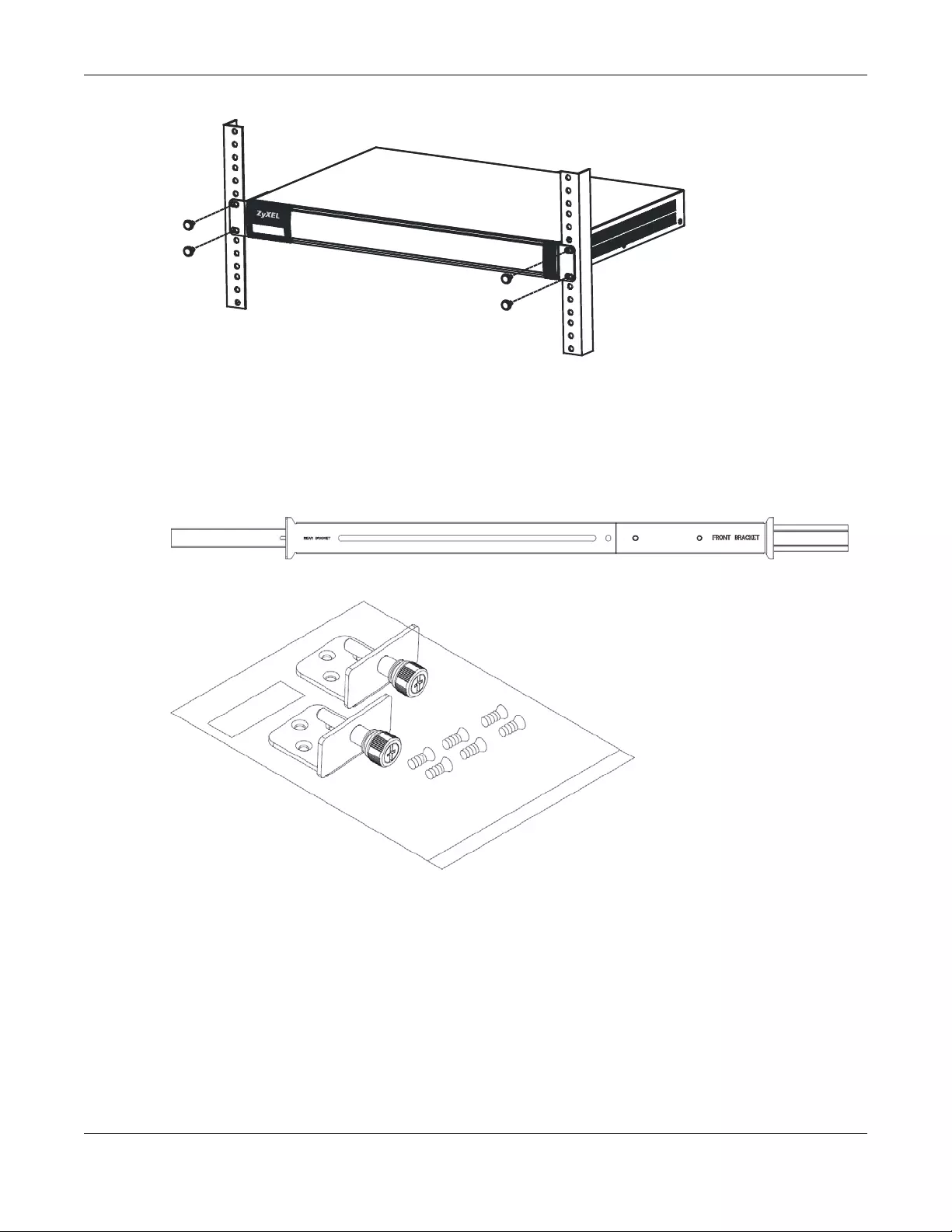
Chapter 3 Hardware, Interfaces and Zones
USG/ZyWALL User’s Guide
68
3.2.2 USG2200-VPN Rack Mounting
3.2.2.1 Installation Requirements
• Two front mounting brackets (short) and two rear mounting brackets (long).
• Two railings (inner and outer)
• Front Brackets & M3 Screws
• Rack M6 Screws and Nuts
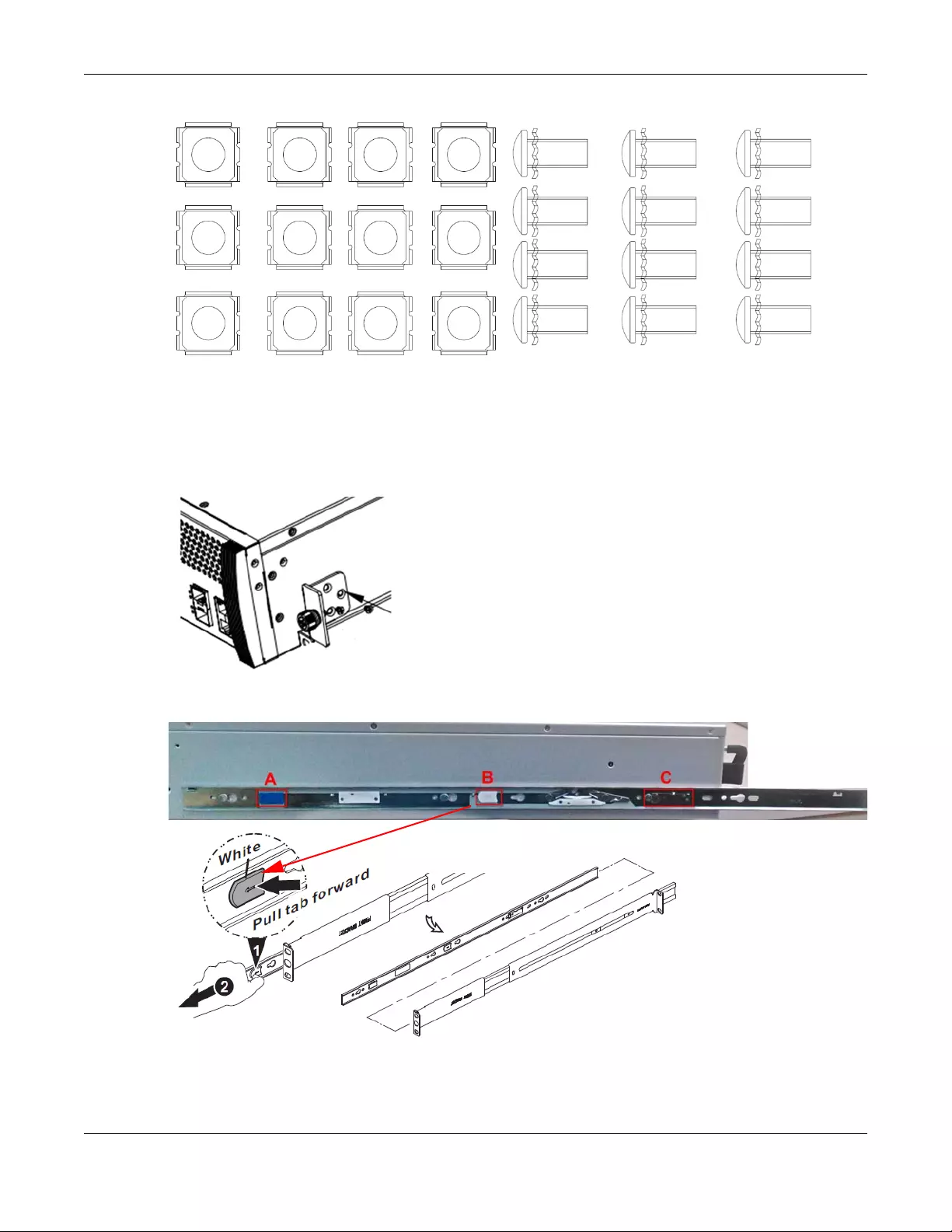
Chapter 3 Hardware, Interfaces and Zones
USG/ZyWALL User’s Guide
69
Note: Failure to use the proper screws may damage the unit.
3.2.2.2 Procedure
1Connect the front brackets to the USG2200-VPN using the M3 bracket screws.
2To separate the inner and outer railings, press tab B (white) and slide out the outer railing.
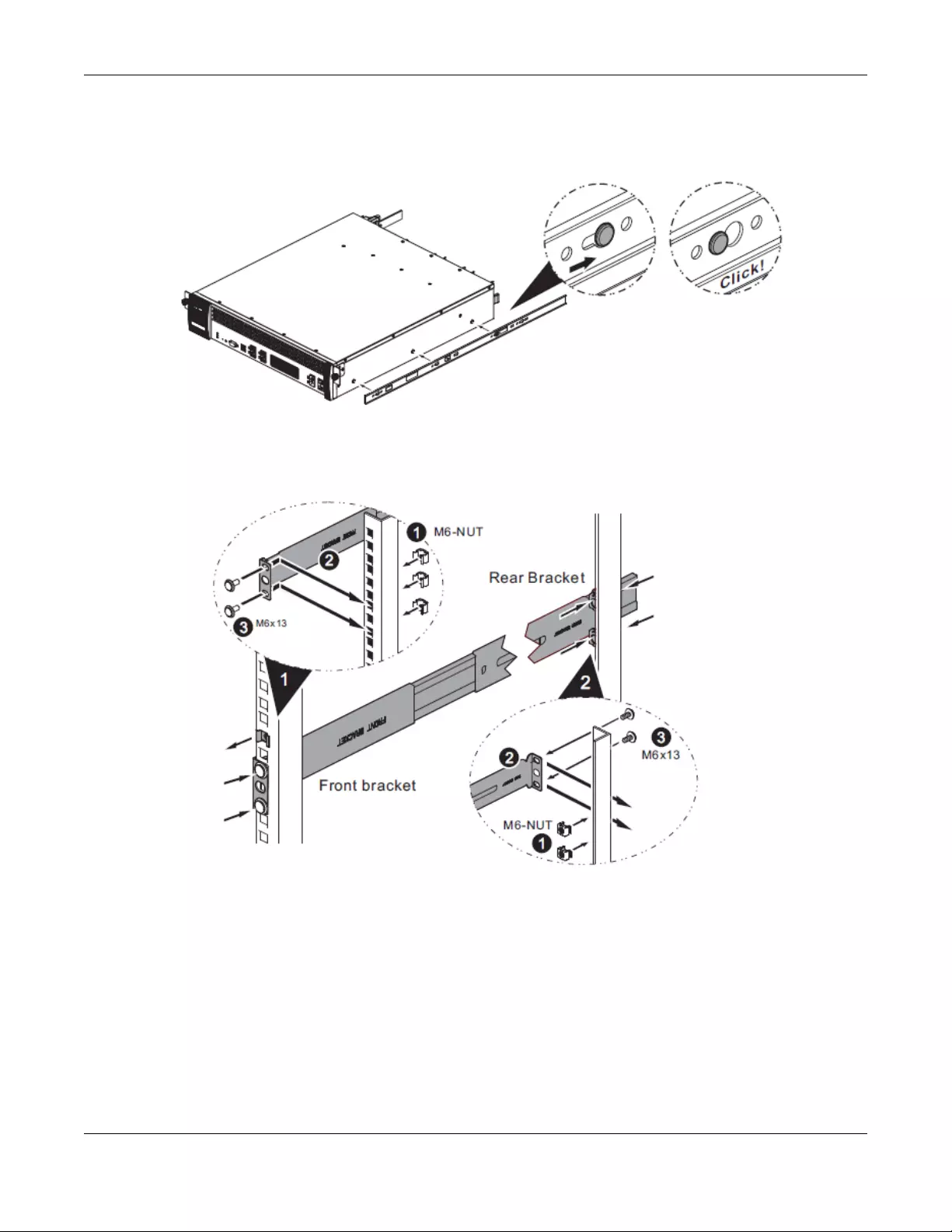
Chapter 3 Hardware, Interfaces and Zones
USG/ZyWALL User’s Guide
70
3Connect the inner railing to the USG2200-VPN as shown. Align the holes on the inner rail with the screws
on the side of the USG2200-VPN and slide until it clicks in place. Do the same for the other inner rail on
the other side of the USG2200-VPN. (Use tab C to remove the inner rail from the USG2200-VPN.)
4Connect the front of an outer railing to the front of the rack using the M6 rack screws. Similarly, connect
the rear of an outer railing to the back of the rack using the rack screws. Repeat for the second outer rail
on the other side of the rack.
5Carefully lift the USG2200-VPN with the inner rails attached and slide it onto the outer rails of the rack.
Use the blue tab (A in step 2 above) to slide the USG2200-VPN along the inner rail. Secure the USG2200-
VPN in the rack using the front bracket screws.
Precautions
• Make sure the rack will safely support the combined weight of all the equipment it contains.
• Make sure the position of the USG2200-VPN does not make the rack unstable or top-heavy. Take all
necessary precautions to anchor the rack securely before installing the unit.
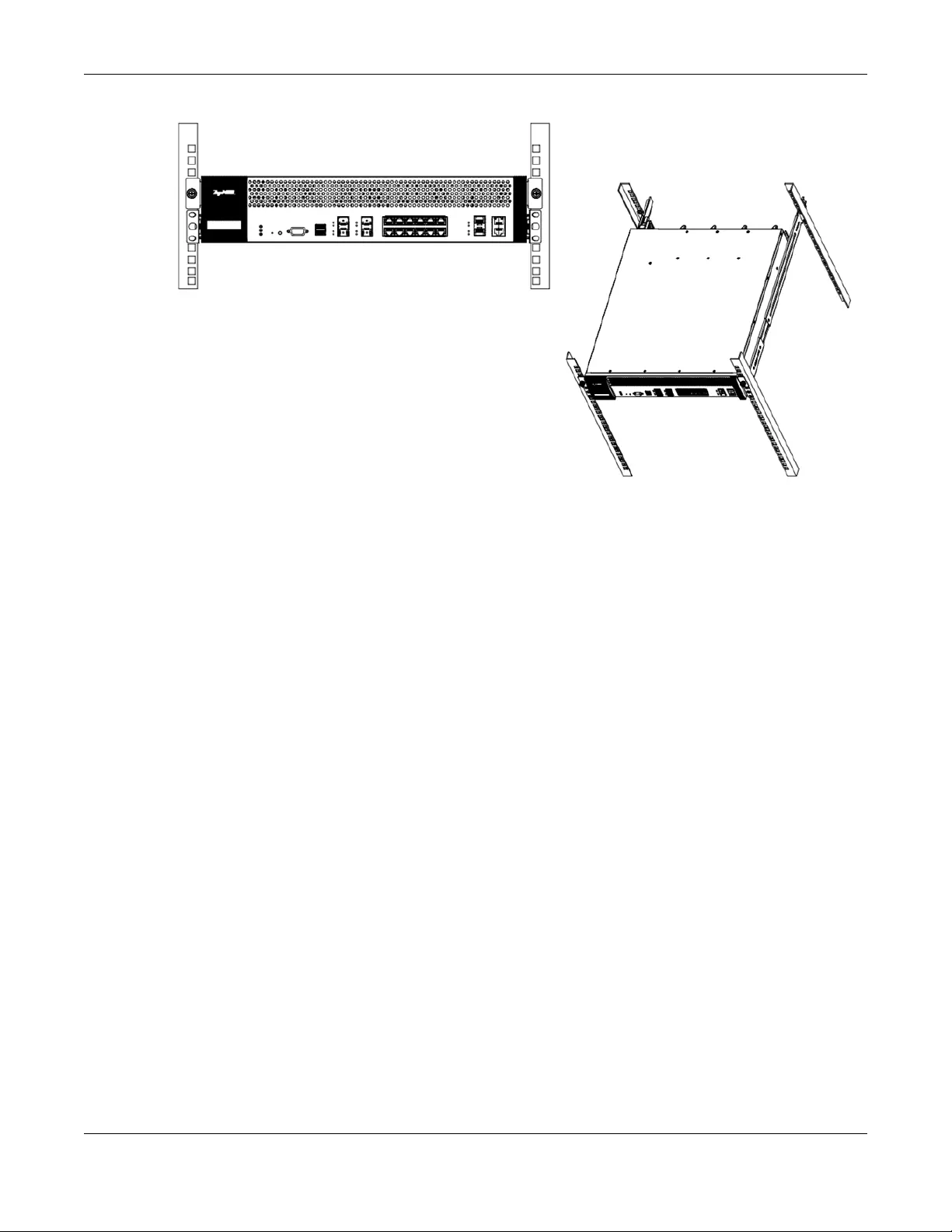
Chapter 3 Hardware, Interfaces and Zones
USG/ZyWALL User’s Guide
71
3.2.3 Wall-mounting
See Table 16 on page 67 for the Zyxel Device models that can be wall-mounted. Do the following to
attach your Zyxel Device to a wall.
1Drill two holes 3 mm ~ 4 mm (0.12" ~ 0.16") wide, 20 mm ~ 30 mm (0.79” ~ 1.18”) deep and 150 mm apart,
into a wall. Place two screw anchors in the holes.
2Screw two screws with 6 mm ~ 8 mm (0.24" ~ 0.31") wide heads into the screw anchors. Do not screw the
screws all the way in to the wall; leave a small gap between the head of the screw and the wall.
The gap must be big enough for the screw heads to slide into the screw slots and the connection cables
to run down the back of the Zyxel Device.
Note: Make sure the screws are securely fixed to the wall and strong enough to hold the
weight of the Zyxel Device with the connection cables.
3Use the holes on the bottom of the Zyxel Device to hang the Zyxel Device on the screws.
Wall-mount the Zyxel Device horizontally. The Zyxel Device's side
panels with ventilation slots should not be facing up or down as this
position is less safe.
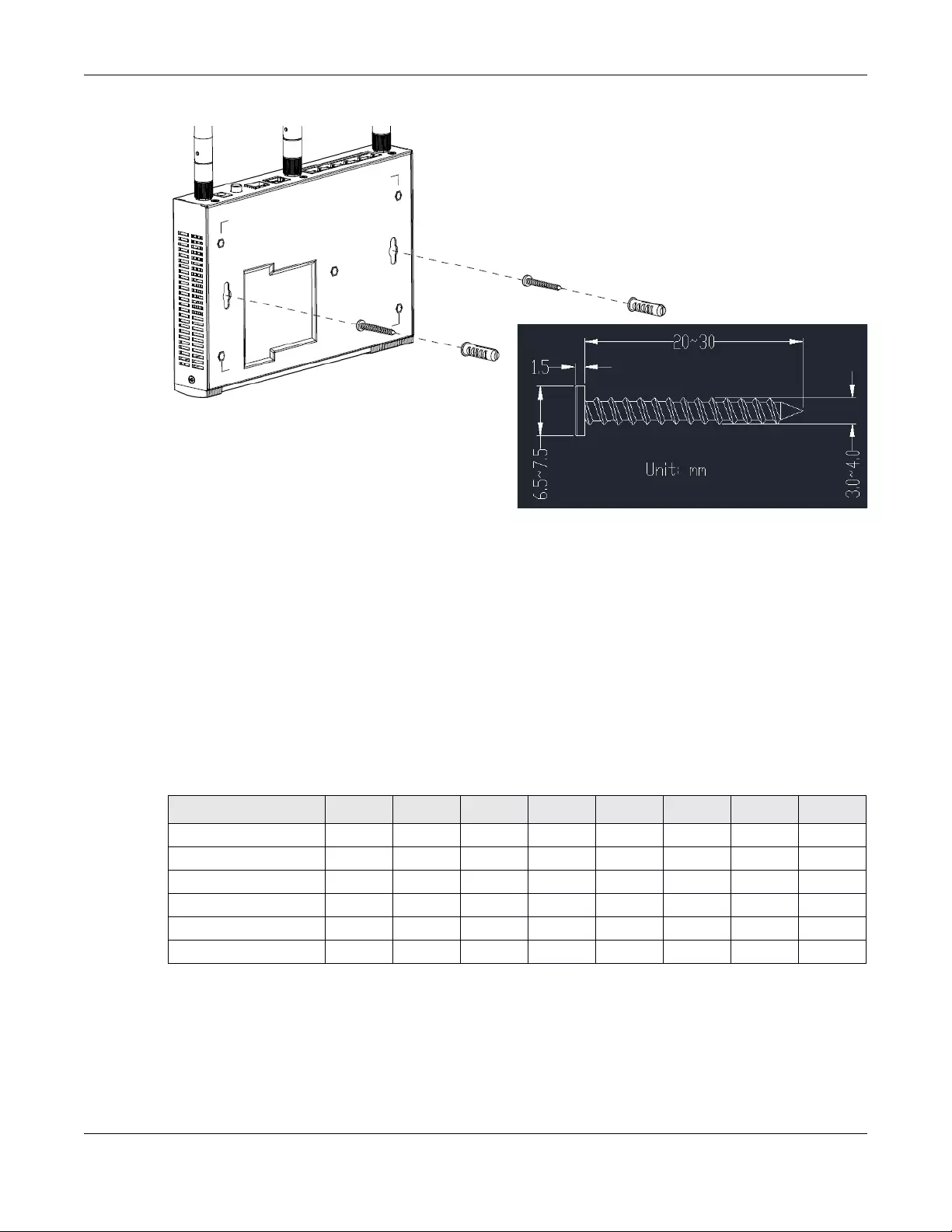
Chapter 3 Hardware, Interfaces and Zones
USG/ZyWALL User’s Guide
72
Figure 54 Wall Mounting
3.3 Default Zones, Interfaces, and Ports
The default configurations for zones, interfaces, and ports are as follows. References to interfaces may
be generic rather than the specific name used in your model. For example, this guide may use “the
WAN interface” rather than “wan1” or “wan2”, “ge2” or” ge3”.
An OPT (optional) Ethernet port can be configured as an additional WAN port, LAN, WLAN, or DMZ port.
The following table shows the default physical port and interface mapping for each model at the time
of writing.
Screw Specifications
Table 17 Default Physical Port - Interface Mapping
PORT / INTERFACE P1 P2 P3 P4 P5 P6 P7 P8
• USG40 wan1 lan1 lan1 lan1 opt
• USG40W wan1 lan1 lan1 lan1 opt
• USG20-VPN sfp wan lan1 lan1 lan1 lan1
• USG20W-VPN sfp wan lan1 lan1 lan1 lan1
• USG60 wan1 wan2 lan1 lan1 lan1 lan1
• USG60W wan1 wan2 lan1 lan1 lan1 lan1
Chapter 3 Hardware, Interfaces and Zones
USG/ZyWALL User’s Guide
73
The following table shows the default interface and zone mapping for each model at the time of
writing.
•ZyWALL 110
• USG110
• USG210
wan1 wan2 opt lan1 lan1 lan1 dmz
•ZyWALL 310
• ZyWALL 1100
• USG310
• USG1100
• USG1900
• USG2200-VPN
ge1 ge2 ge3 ge4 ge5 ge6 ge7 ge8
Table 18 Default Zone - Interface Mapping
ZONE / INTERFACE WAN LAN1 LAN2 DMZ OPT NO
DEFAULT
ZONE
•USG40 WAN1
WAN1_PPP
LAN1 LAN2 DMZ OPT
OPT_PPP
• USG40W WAN1
WAN1_PPP
LAN1 LAN2 DMZ OPT
OPT_PPP
• USG20-VPN
• USG20W-VPN
WAN
WAN_PPP
OPT
OPT_PPP
LAN1 LAN2 DMZ
•USG60 WAN1
WAN1_PPP
WAN2
WAN2_PPP
LAN1 LAN2 DMZ
• USG60W WAN1
WAN1_PPP
WAN2
WAN2_PPP
LAN1 LAN2 DMZ
•ZyWALL 110
• USG110
• USG210
WAN1
WAN1_PPP
WAN2
WAN2_PPP
LAN1 LAN2 DMZ OPT
OPT_PPP
•ZyWALL 310
• ZyWALL 1100
• USG310
• USG1100
• USG1900
GE1
GE1_PPP
GE2
GE2_PPP
GE3 GE4 GE5 GE3_PPP
GE4_PPP
GE5_PPP
G6
GE6_PPP
G7
GE7_PPP
G8
GE8_PPP
Table 17 Default Physical Port - Interface Mapping (continued)
PORT / INTERFACE P1 P2 P3 P4 P5 P6 P7 P8
Chapter 3 Hardware, Interfaces and Zones
USG/ZyWALL User’s Guide
74
3.4 Stopping the Zyxel Device
Always use Maintenance > Shutdown > Shutdown or the shutdown command before you turn off the
Zyxel Device or remove the power. Not doing so can cause the firmware to become corrupt.
Table 19 Default Zone - Interface Mapping USG2200-VPN
ZONE / INTERFACE WAN LAN1 LAN2 DMZ 10G NO
DEFAULT
ZONE
• USG2200-VPN GE5, GE5_PPP
GE6, GE6_PPP
GE7 GE8 GE9, GE10 TE17, TE17_PPP
TE18, TE18_PPP
GE1, GE1_PPP
GE2, GE2_PPP
GE3, GE3_PPP
GE4, GE4_PPP
GE7_PPP
GE8_PPP
GE9_PPP
GE10_PPP
GE11,
GE11_PPP
GE12,
GE12_PPP
GE13,
GE13_PPP
GE14,
GE14_PPP
GE15,
GE15_PPP
GE16,
GE16_PPP
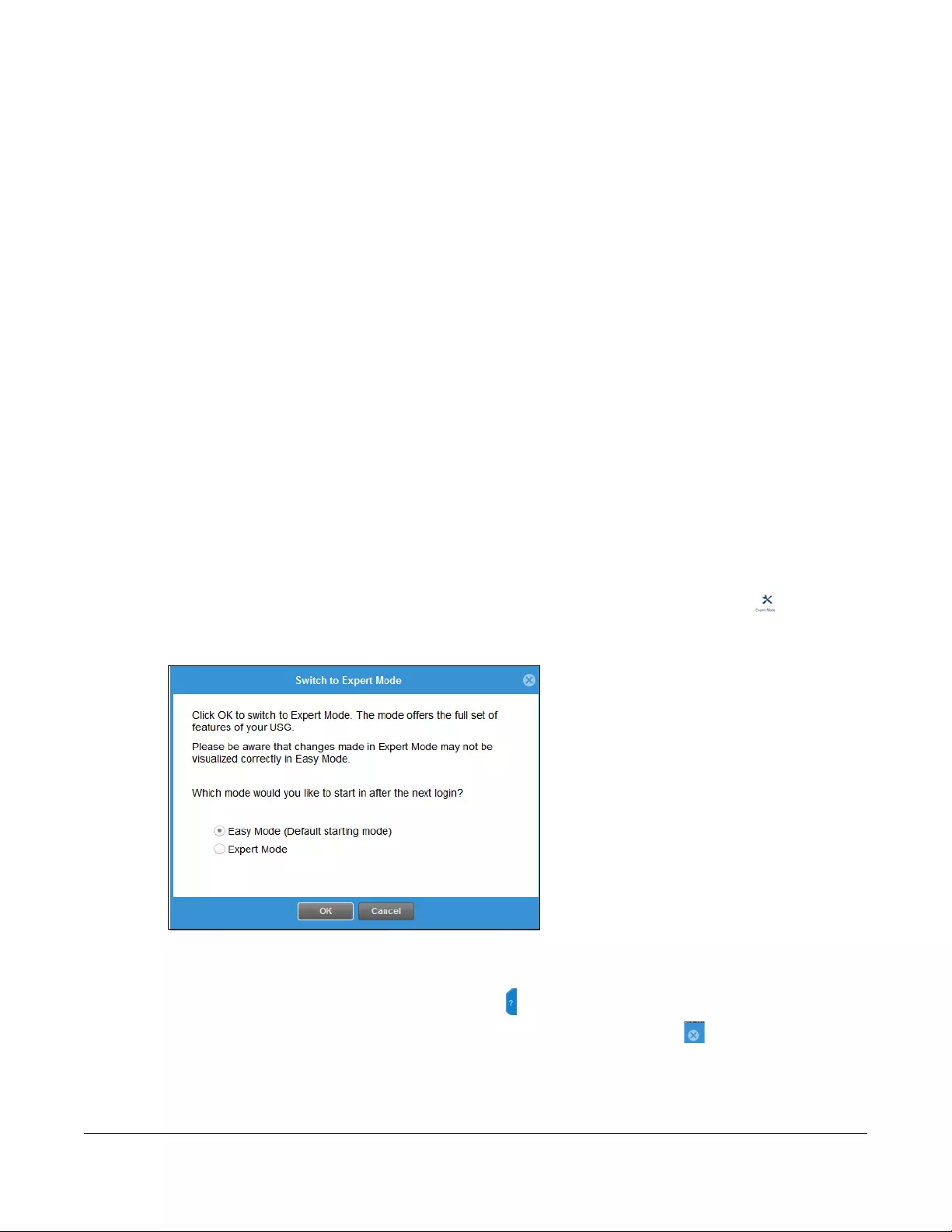
USG/ZyWALL User’s Guide
75
CHAPTER 4
Easy Mode
4.1 Overview
Welcome to the Easy Mode screens. This mode contains wizards that help you configure the Zyxel
Device, links to portals and the advanced menus in Expert Mode.
The following models have Easy Mode wizards.
Use the Easy Mode screens if you have a relatively simple network environment with one WAN (WAN1)
and one LAN (LAN1) connections. If your Zyxel Device has two WAN ports, use WAN1 as the WAN
connection. If you use WAN2 as the WAN connection or want to use both WAN ports, then please use
the Expert Mode screens.
If you prefer to start directly with the advanced screens, then simply click Expert Mode and select
the Expert Mode option.
Figure 55 Switch Modes
4.1.1 Wizards and Links
In the wizards, click the question mark on the right to display or hide the help. Click Next > to continue
to the following screen, < Back to return to the previous screen and Exit or X (top right) to close the
wizard screen without saving any changes.
The following are the Easy Mode wizards and links.
• USG20-VPN • USG20W-VPN
• USG40 • USG40W
• USG60 • USG60W
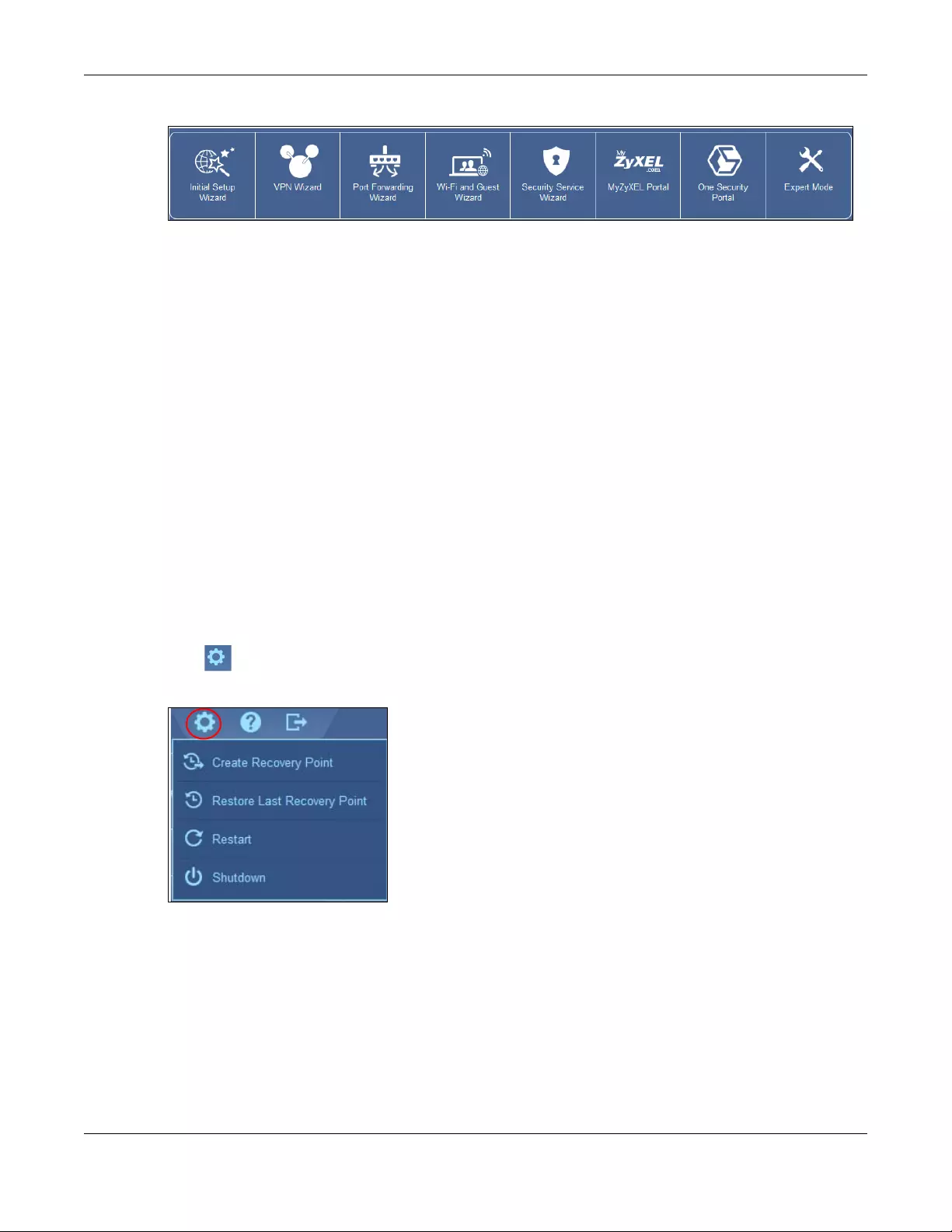
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
76
Figure 56 Easy Mode Wizards and Links
•Initial Setup Wizard for Internet access - you should have your Internet access account information at
hand
•VPN Wizard for a site-to-site tunnel between Zyxel Device networks, a tunnel from a remote client
using the Zyxel client VPN software to the Zyxel Device network, or a tunnel from a remote client using
other VPN software to the Zyxel Device network
•Port Forwarding Wizard to set up a server, such as a NAS in your network that you or other people can
access from outside the network
•Wi-Fi and Guest Wizard to set up a wireless name and security for normal and guest (Internet only)
wireless access to the Zyxel Device
•Security Service Wizard to configure subscriptions for content filtering, IDP, and anti-virus services.
There are also links to:
•MyZyxel Portal where you can subscribe for security services such as content filtering, IDP, and anti-
virus
•One Security Portal where you can get configuration walkthroughs, troubleshooting help and other
help on security services and VPN
•Expert Mode which contains all the advanced menus.
4.1.2 Easy Mode Settings
Click to display the Easy Mode Settings menu.
Figure 57 Easy Mode Settings
•Create Recovery Point - a recovery point is a point to which all the Zyxel Device’s configuration can
be reset to after you click Create Recovery Point. Choose this when you have some configurations
done and everything is working correctly.
•Restore Last Recovery Point - choose this if you have problems with recent configurations done on the
Zyxel Device and you want to return to a previous configuration point where everything was working
correctly. You will lose all configurations done after the restore point.
•Restart - reboot the Zyxel Device after upgrading new firmware. It may also be useful when
troubleshooting. Changes in the Web configurator are saved automatically and do not change
when you reboot. If you made changes in the CLI, however, you have to use the write command to
save the configuration before you reboot.

Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
77
•Shutdown - use this to safely turn off the Zyxel Device in preparation for disconnecting the power.
Shutdown writes all cached data to the local storage and stops the system processes. It does not turn
off the power. Wait for the device to shut down before you manually turn off or remove the power.
4.1.3 Easy Mode Dashboard
Cloud Helper
Click the Cloud Helper icon to check if there is new firmware available at myZyxel.com.
If there is new firmware available at myZyxel.com, then the icon displays a red N . Click the icon
with the red N to display a What’s New pop-up screen. You need a Firmware Upgrade license to
upgrade the firmware. If you do not have a license, Upgrade Now is grayed out. If you have a license,
click Upgrade Now to directly upgrade firmware. The Zyxel Device will reboot automatically.
Figure 58 Cloud Helper - What’s New
The Easy Mode dashboard is shown next.
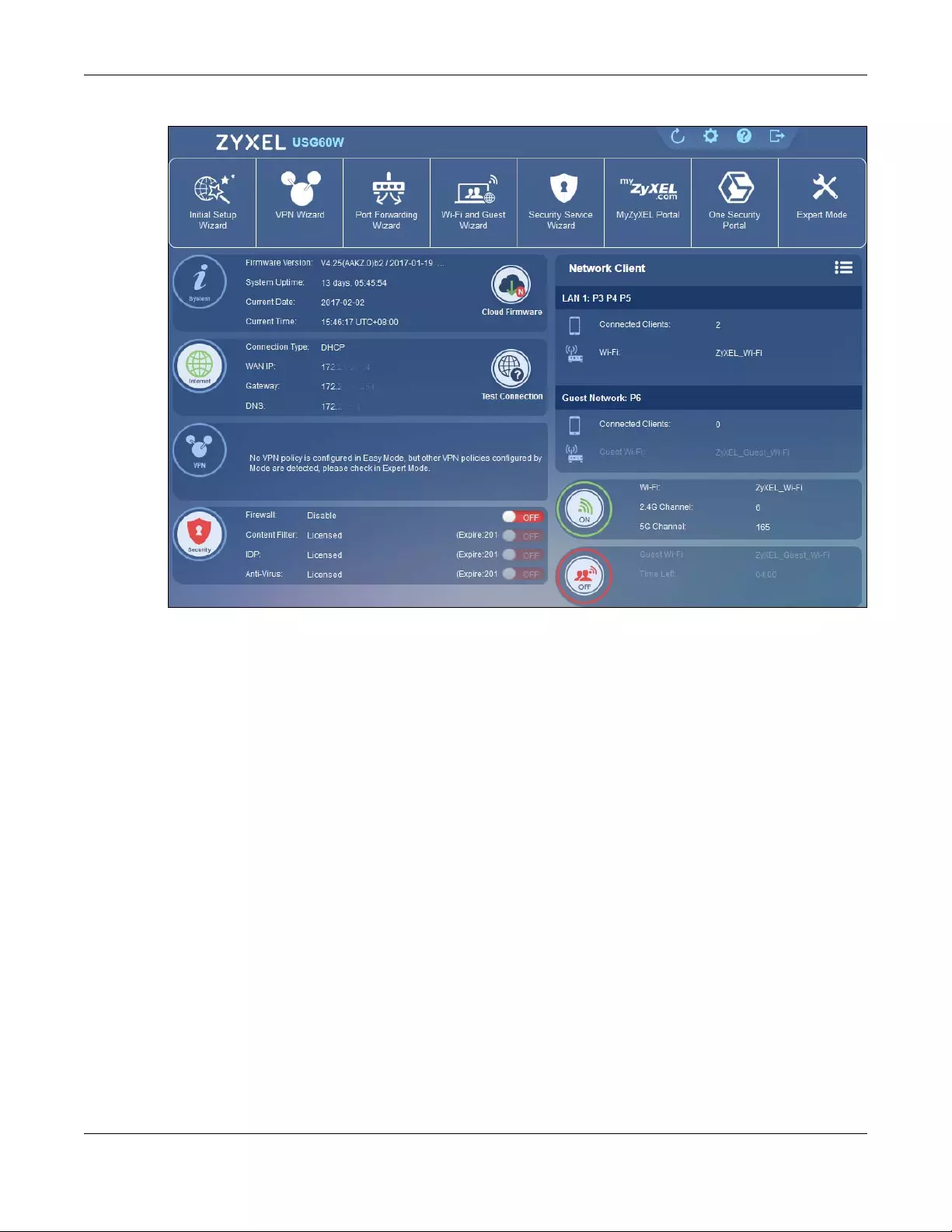
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
78
Figure 59 Easy Mode Dashboard
The Easy Mode dashboard contains the following.
•System information, such as firmware version, the length of time the Zyxel Device has been on, date
and time.
•Internet information such as Internet connection type, WAN IP address and a button to test the
connection.
•VPN tunnel information and a button to monitor and create VPN tunnels.
•Security information such as if the firewall is enabled and if supported security services are licensed.
You will be prompted to create a secure policy when a service is licensed and you turn it on in order
for the service to be used.
• Network Client
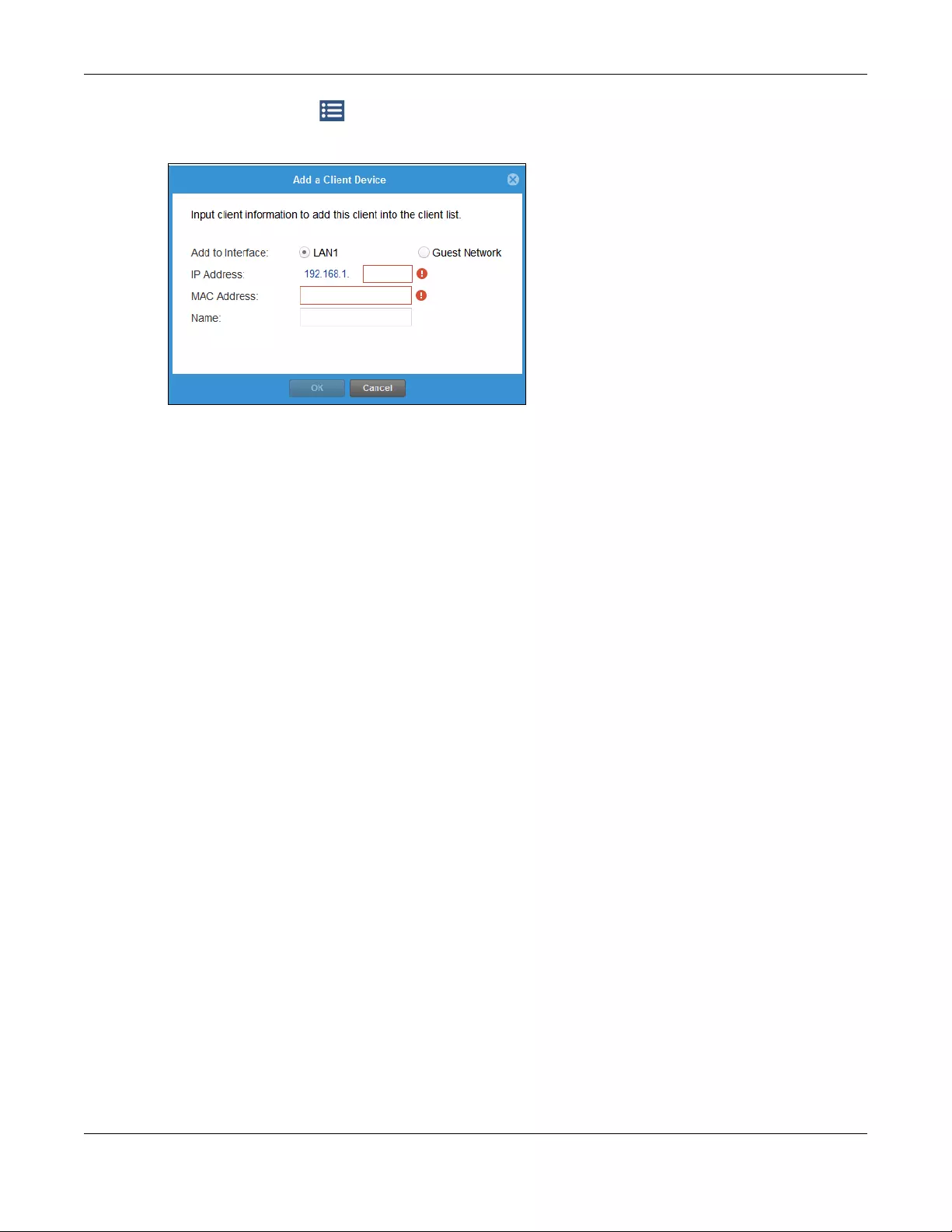
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
79
Click the settings icon to manage clients. Click + to add a new network client. In the pop-up
screen, you can add a new client by entering its interface (LAN1 or Guest), IP Address, MAC Address
and Name.
This is the information you see under Network Client:
•LAN information on wired and wireless connections to the Zyxel Device
•Guest Network information on guest wired and wireless connections to the Zyxel Device
•Wi-Fi button to change Wi-Fi channel
•Guest button turn the guest wireless network off or on.
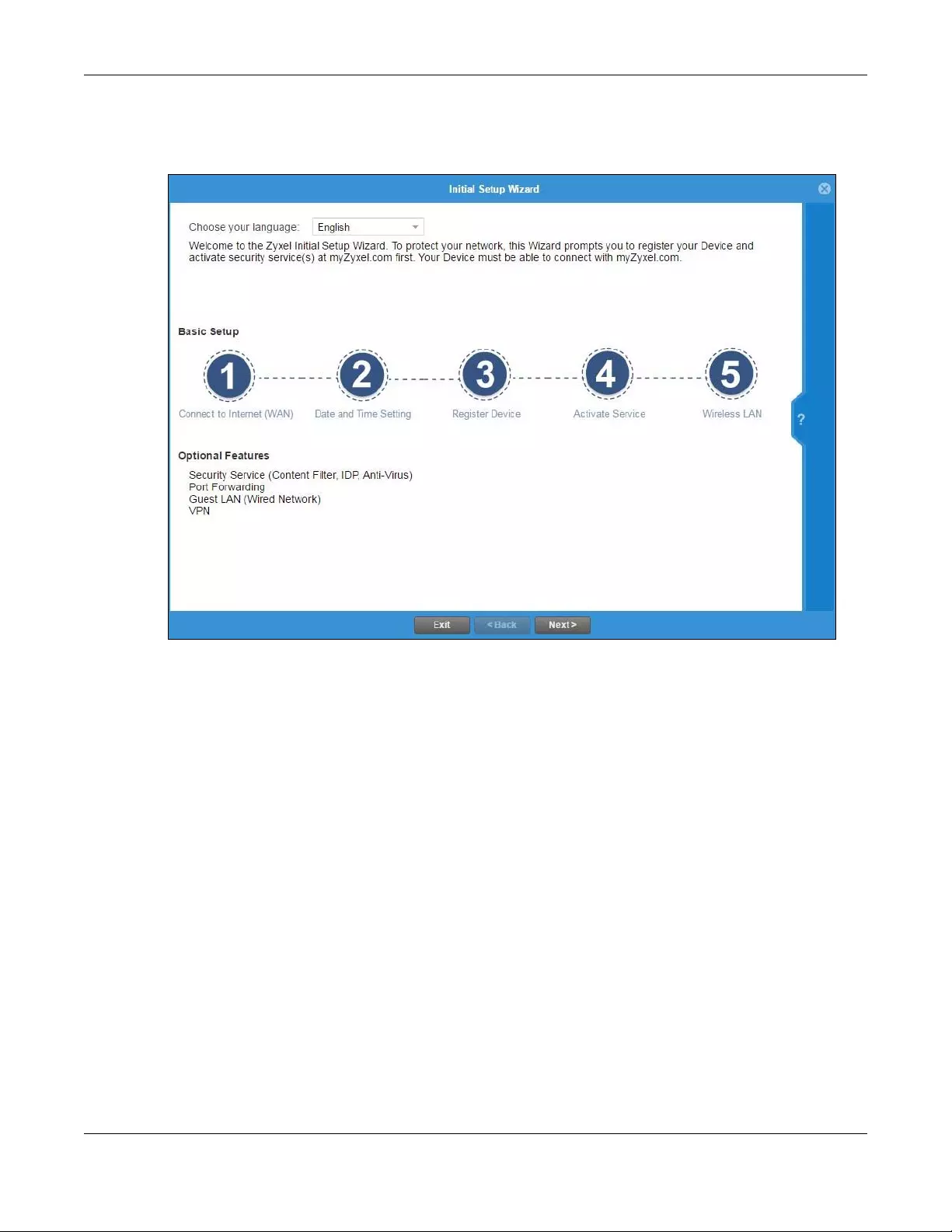
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
80
4.2 Initial Setup Wizard - Language and Overview
Figure 60 Initial Setup Wizard Language
Choose the language for the Easy Mode and Expert Mode screens.
• The initial wizard helps you set up basic options as shown in the screen. At the end, you will have the
choice of finishing the wizard or continuing the wizard to configure the optional features as listed. If
you choose to finish the wizard, you can configure the optional features later using their own
separate links in the Easy Mode main screen.
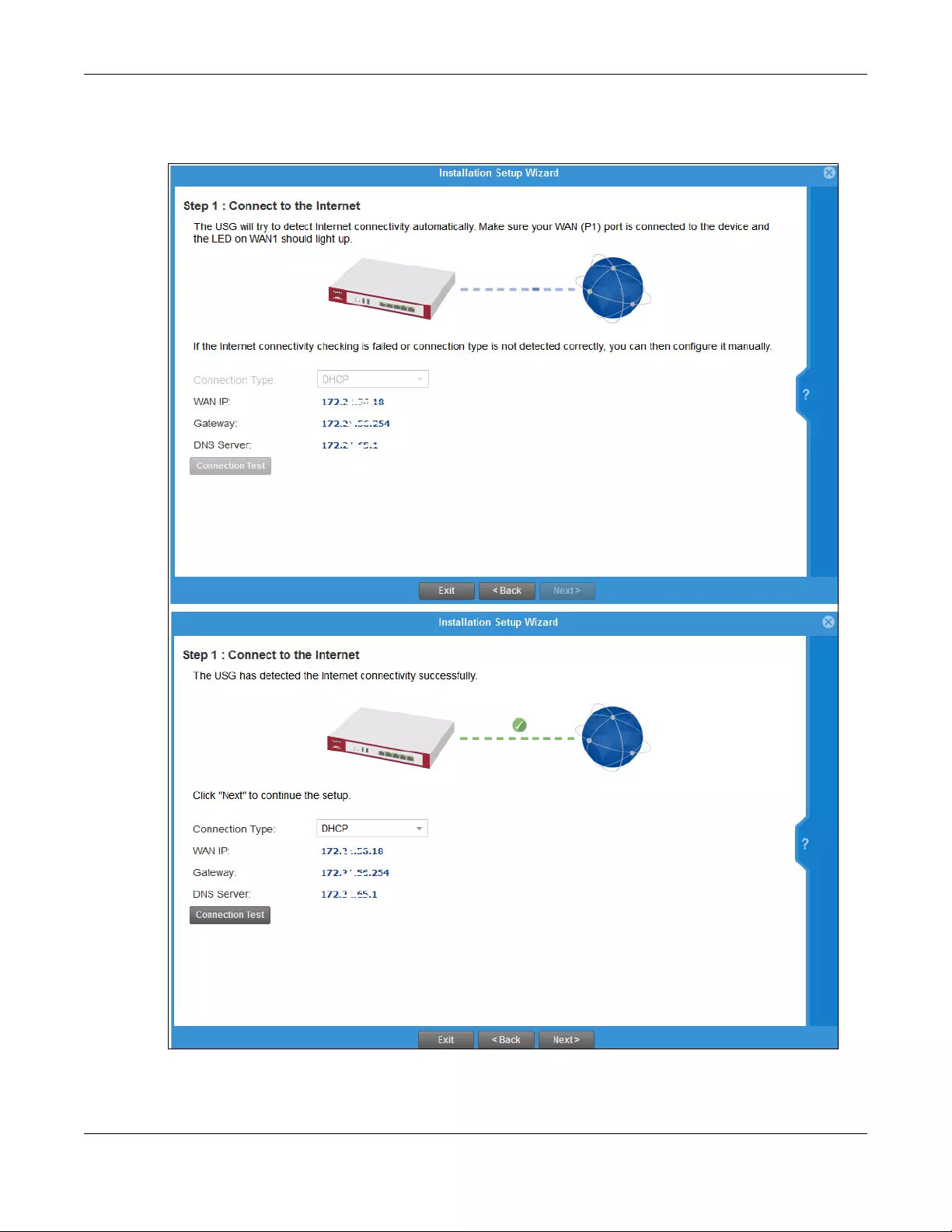
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
81
4.2.1 Initial Setup Wizard - Internet
Figure 61 Initial Setup Wizard Connect to Internet
This screen displays the Internet settings if the Zyxel Device can detect them automatically.

Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
82
If the Zyxel Device cannot detect the Internet settings automatically, then you have to enter them
manually.
• Choose DHCP if you were not given a specific IP address for the Zyxel Device. This allows the Zyxel
Device to be able to get one automatically.
• Choose Ethernet Fixed IP if you were given a specific IP address for the Zyxel Device.
• Choose PPPoE if you were given a PPPoE user name and password.
Note: Enter the Internet access information exactly as your ISP gave you.
4.2.2 Initial Setup Wizard - Internet Access Errors
These are some things you can do if you see Internet access error messages.
WAN 1 Down
Check that your cable connection from the WAN1 interface on the Zyxel Device is connected to the
device you’re using for Internet access such as a broadband router and that the router is turned on. The
LED of the WAN1 interface on the Zyxel Device should be orange.
PPPoE Error
Your Zyxel Device was not able to obtain an IP address. Check that your Internet access information
uses PPPoE as the WAN connection type. Re-enter your PPPoE user name and password exactly as
given. If it fails again, check with your Internet service provider for correct WAN settings and user
credentials.
DHCP Error
Your Zyxel Device was not able to obtain an IP address. Check that your Internet access information
uses DHCP as the WAN connection type. If it fails again, check with your Internet service provider for
correct WAN settings and user credentials.
Ethernet Fixed IP Error
Your Zyxel Device was not able to use the IP address entered. Check that you were given an IP address,
subnet mask and gateway address as part of your Internet access information. Re-enter your IP address,
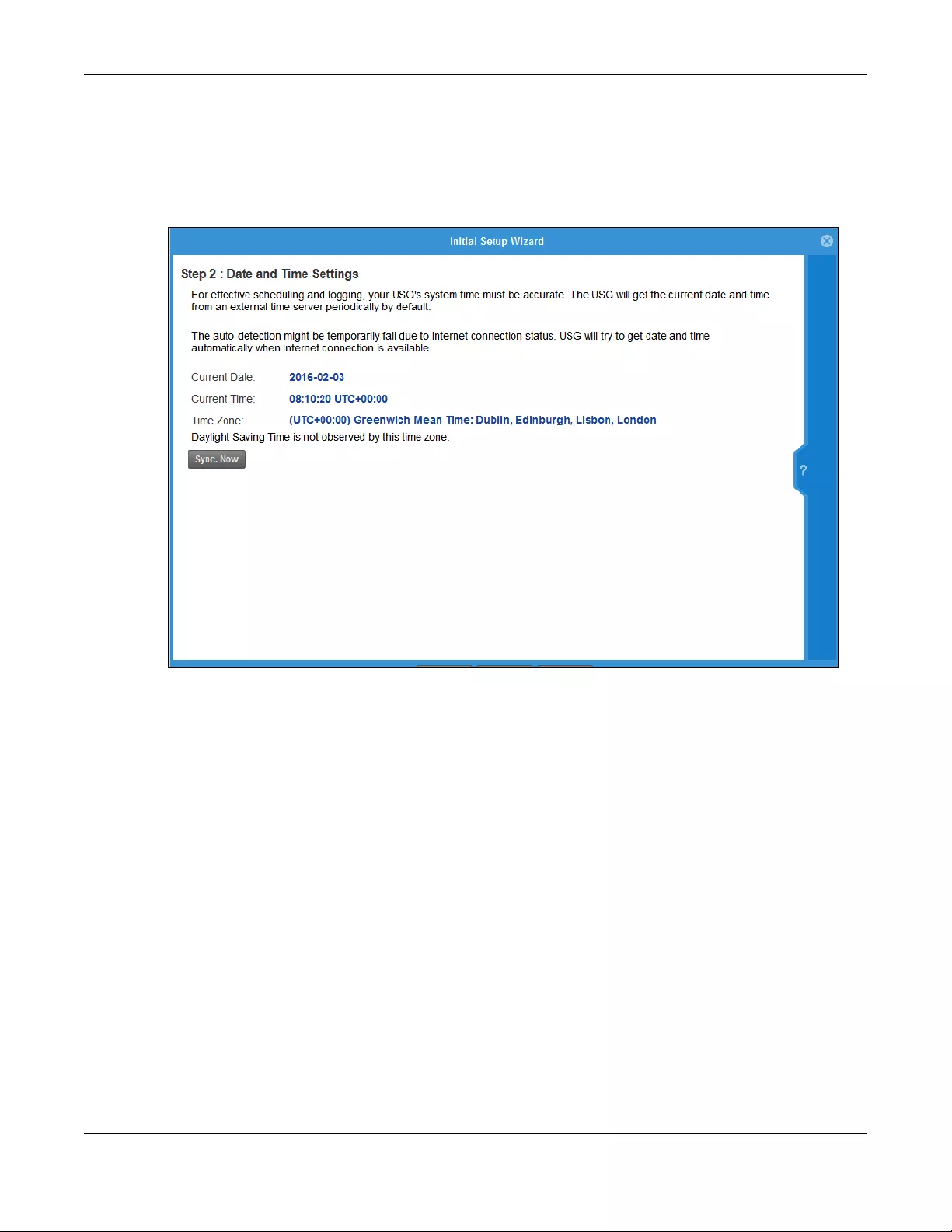
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
83
subnet mask and gateway address exactly as given. If it fails again, check with your Internet service
provider for correct IP address, subnet mask and gateway address and other WAN settings.
4.2.3 Initial Setup Wizard - Date and Time
Figure 62 Initial Setup Wizard Date and Time
It’s important to have correct date and time values in the logs. The Zyxel Device can automatically
update the time and date by detecting your time zone and whether Daylight Savings is in effect in that
time zone.
If your Zyxel Device cannot get the correct date and time, it may not able to connect to a time server.
Check that the Zyxel Device has Internet access, then click Synch Now.
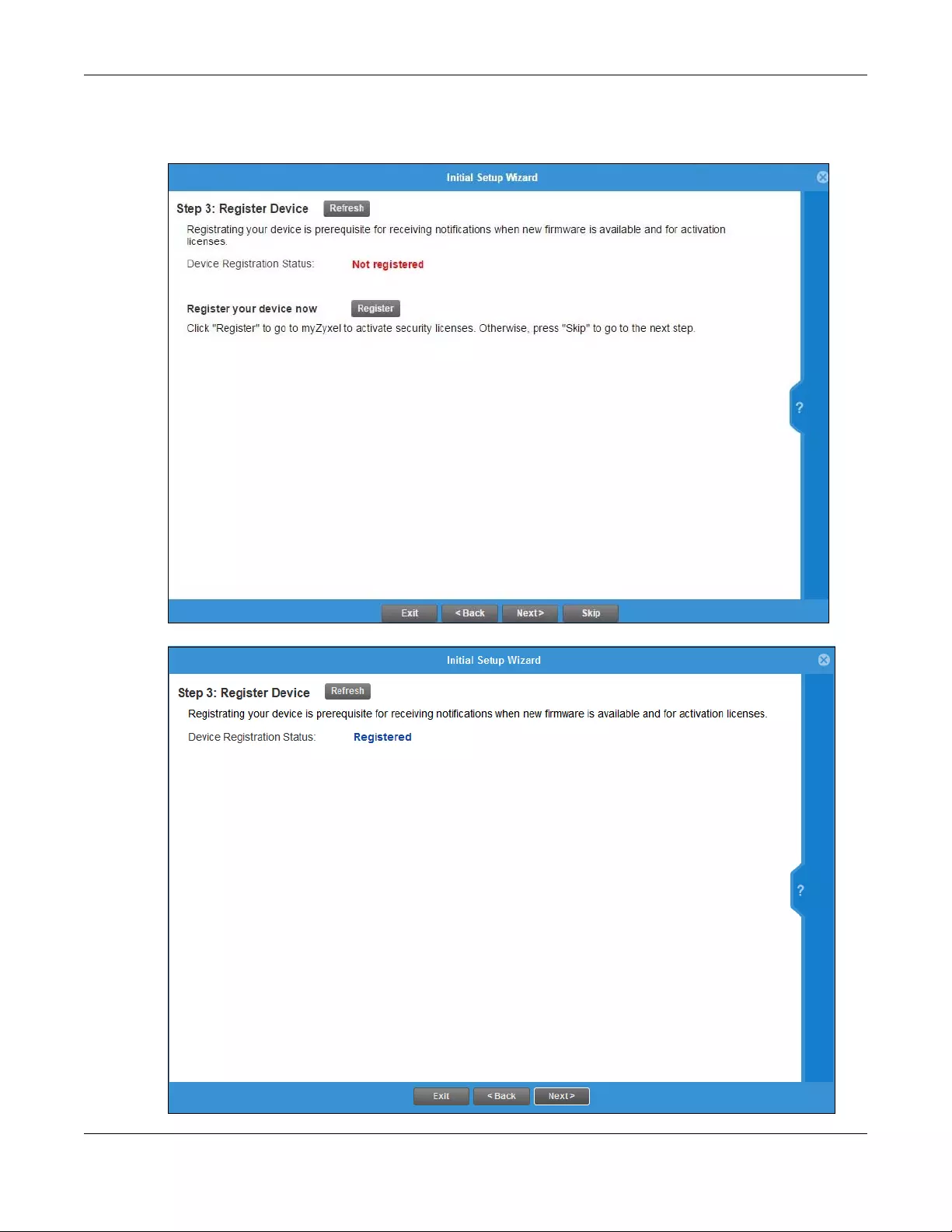
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
84
4.2.4 Initial Setup Wizard - Register Device
Figure 63 Initial Setup Wizard Non-Registered Device
Figure 64 Initial Setup Wizard Registered Device
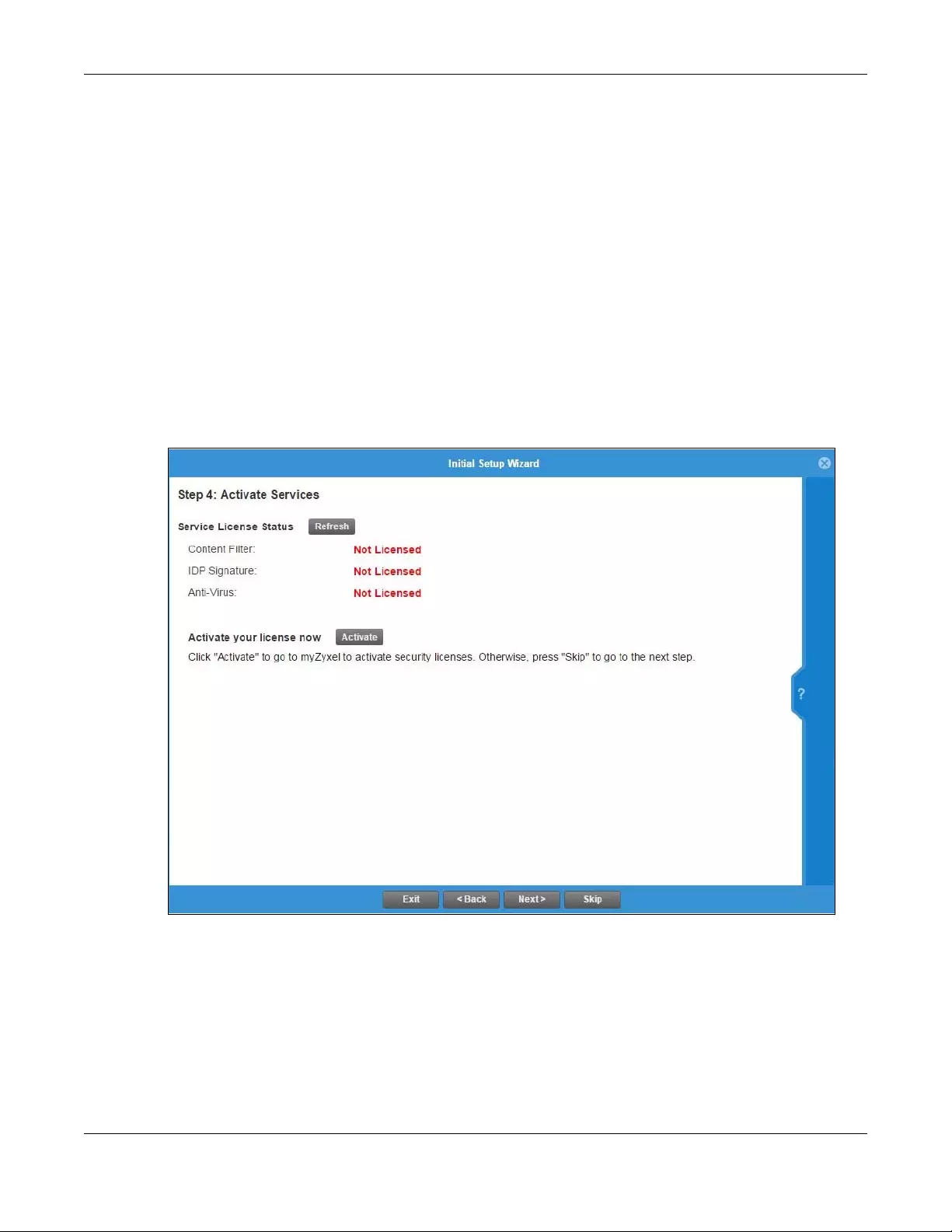
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
85
• For Zyxel Devices that already have firmware version 4.25 or later, you have to register your Zyxel
Device and activate the corresponding service at myZyxel.com (through your Zyxel Device).
• For Zyxel Devices upgrading to firmware version 4.25, you may skip registering your Zyxel Device and
activating the corresponding service at myZyxel.com. However, it is highly recommended to at least
register your Zyxel Device.
Click the Register button in this screen to register your device at portal.myzyxel.com. You need to create
a myZyxel.com account at portal.myzyxel.com before you can register your device and activate the
services at myZyxel.com.
When registering the Zyxel Device at myZyxel.com, if you are prompted for the Zyxel Device’s serial
number and LAN MAC address, see the label at the back of the Zyxel Device’s.
Note: The Zyxel Device must be connected to the Internet in order to register.
4.2.5 Initial Setup Wizard - Activate Services
Figure 65 Initial Setup Wizard Non-Activated Services
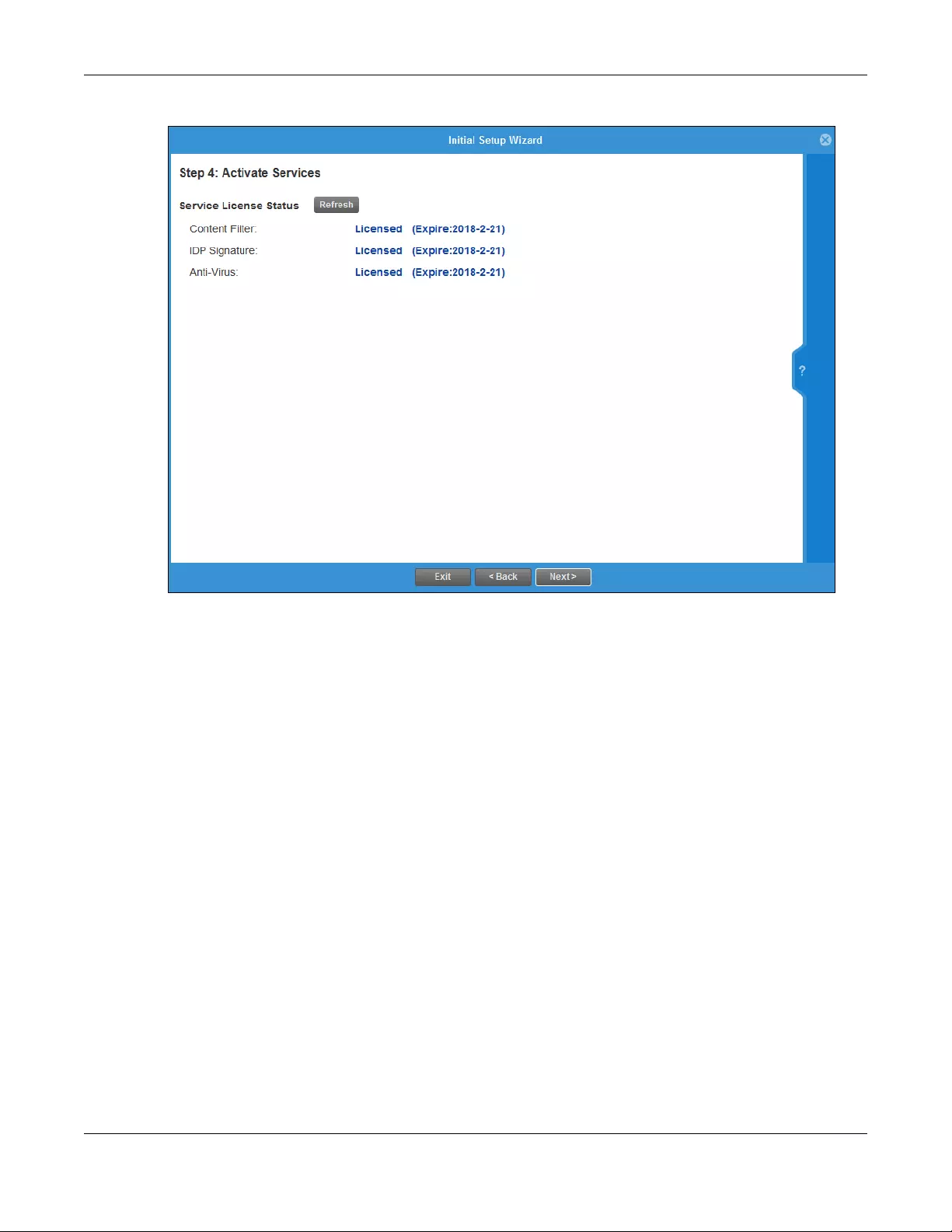
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
86
Figure 66 Initial Setup Wizard Activated Services
After you register your Zyxel Device, you can activate the services supported by your model if you have
service licenses. Examples of services are:
• Content Filter (to block websites by category, such as Gambling)
• IDP (to recognize and drop traffic with Intrusion, Detection & Protection attack patterns)
• Anti-Virus (to detect virus patterns in files)
• Anti-Spam (to mark or discard unsolicited commercial or junk e-mail suspect of being sent by
spammers).
Click Refresh and wait a few moments for the service information to update in this screen. If the page
does not refresh, make sure the Internet connection is working and click Refresh again. To check your
Internet connection, try to access the Internet from a computer connected to a LAN port on the Zyxel
Device. If you cannot, then check your Internet access settings on the Zyxel Device.
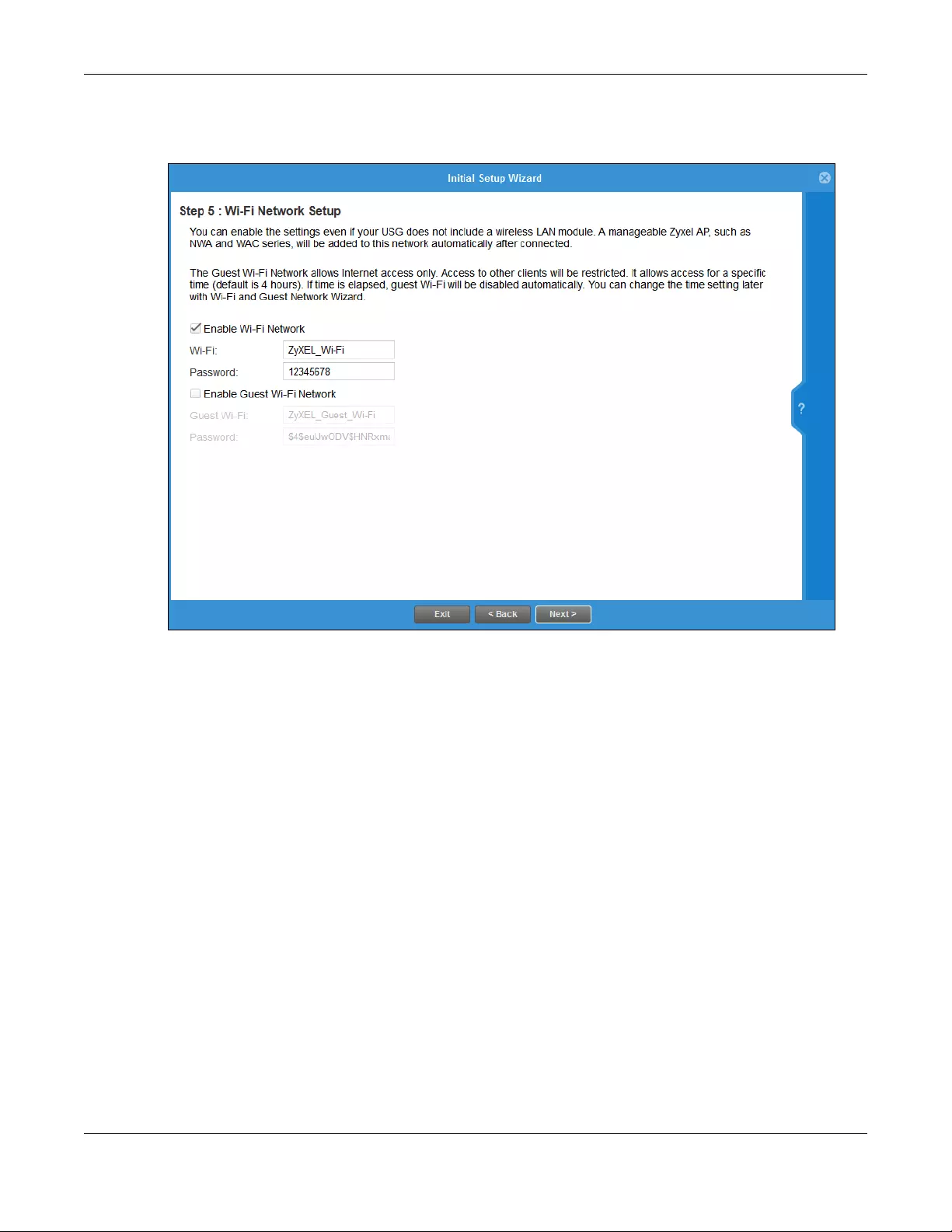
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
87
4.2.6 Initial Setup Wizard - Wi-Fi
Figure 67 Initial Setup Wizard Wi-Fi
Select Enable Wi-Fi Network if you want wireless devices to be able to wirelessly access the Zyxel Device
and all resources connected to the Zyxel Device. Configure a descriptive name of from 1 to 32 alpha-
numeric characters, hyphens or underscores (a-z A-Z 0-9 -_) for the wireless network name (Wi-Fi). Set a
Password of between 8 and 63 printable ASCII characters (including spaces and symbols) or 64
hexadecimal characters (0-9 a-f) that wireless users will have to enter for access to the Zyxel Device
wireless network.
Note: You must change the Password to continue.
Select Enable Guest Wi-Fi Network if you want wireless devices to only be able to wirelessly access the
Internet via the Zyxel Device for up to 4 hours. Configure a descriptive name of from 1 to 32 alpha-
numeric characters, hyphens or underscores (a-z A-Z 0-9 -_) for the wireless network name (Wi-Fi). Set a
Password of between 8 and 63 printable ASCII characters (including spaces and symbols) or 64
hexadecimal characters (0-9 a-f) that wireless users will have to enter for access to the Zyxel Device
Guest wireless network.
The Guest Wi-Fi Network allows Internet access only for up to 4 hours by default. Log in again if the time
has elapsed. You can change the default time for Guest Wi-Fi access in the Wi-Fi and Guest Wizard.
The Zyxel Device uses WPA2-PSK with AES encryption so wireless clients must be able to support AES
encryption to wirelessly connect to the Zyxel Device using WPA2-PSK.
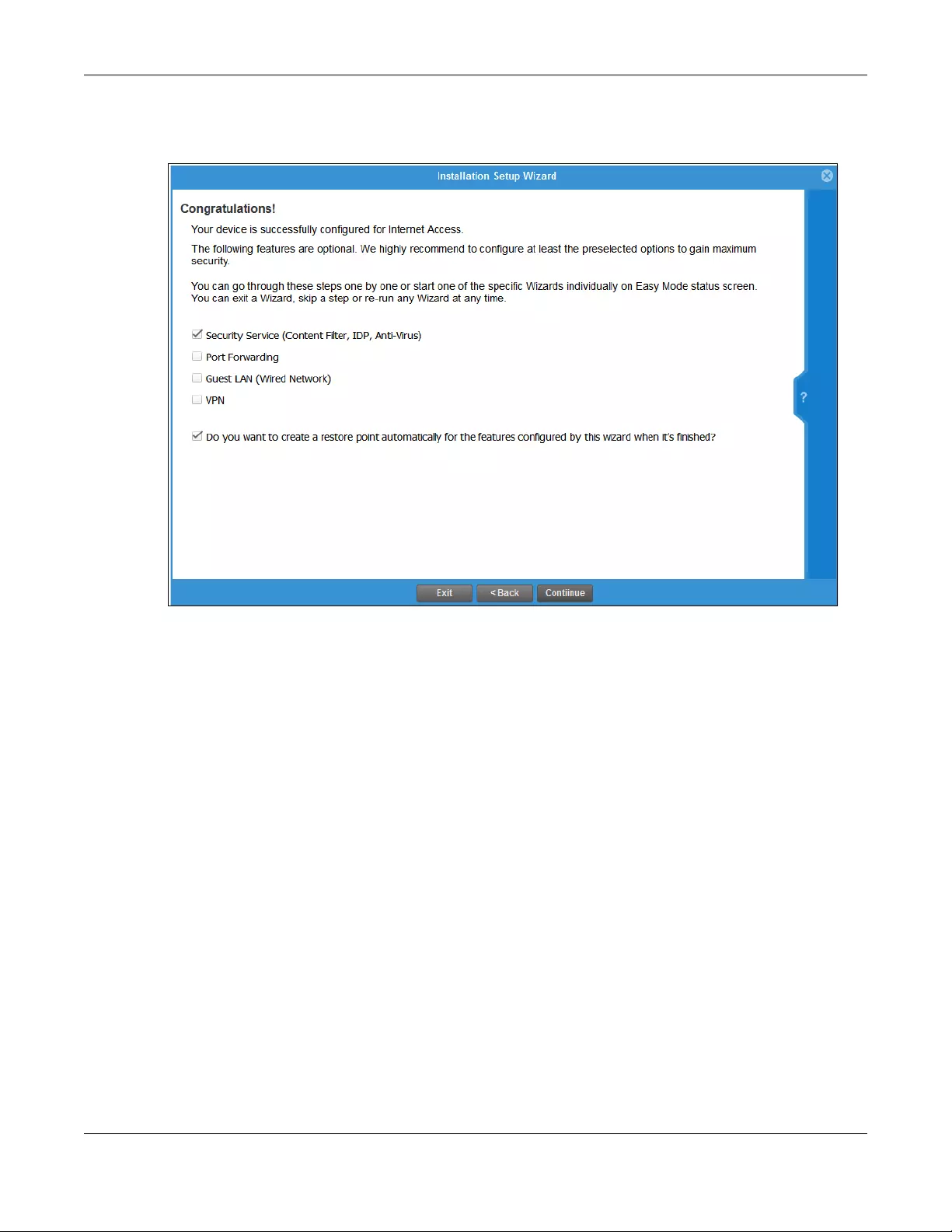
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
88
4.2.7 Initial Setup Wizard - Congratulations
Figure 68 Initial Setup Wizard Congratulations
This screen shows if your Internet access is successfully configured. You can save changes and exit the
Initial Wizard here by clearing Security Service, Port Forwarding, Guest LAN and VPN service selections
and clicking Finish. Alternatively, select desired security services to continue configuring them as part of
the Initial Wizard (Finish becomes Continue). If you want to configure these services later you can
access them from the tabs in the dashboard.
Select from the following to continue configuring in this screen:
•Security Service (Content Filter, IDP, Anti Virus) to configure subscriptions for these services
•Port Forwarding to set up a server in your network that people outside the network can access
•Guest LAN (Wired Network) to set up a guest network where users can access the Internet only from a
wired connection to the OPT port for a limited time
•VPN for a site-to-site tunnel between Zyxel Device networks, a tunnel from a remote client using the
Zyxel client VPN software to the Zyxel Device network, or a tunnel from a remote client using other
VPN software to the Zyxel Device network.
A restore point is a recovery point where you can reset the Zyxel Device’s configuration to if you have
problems later.
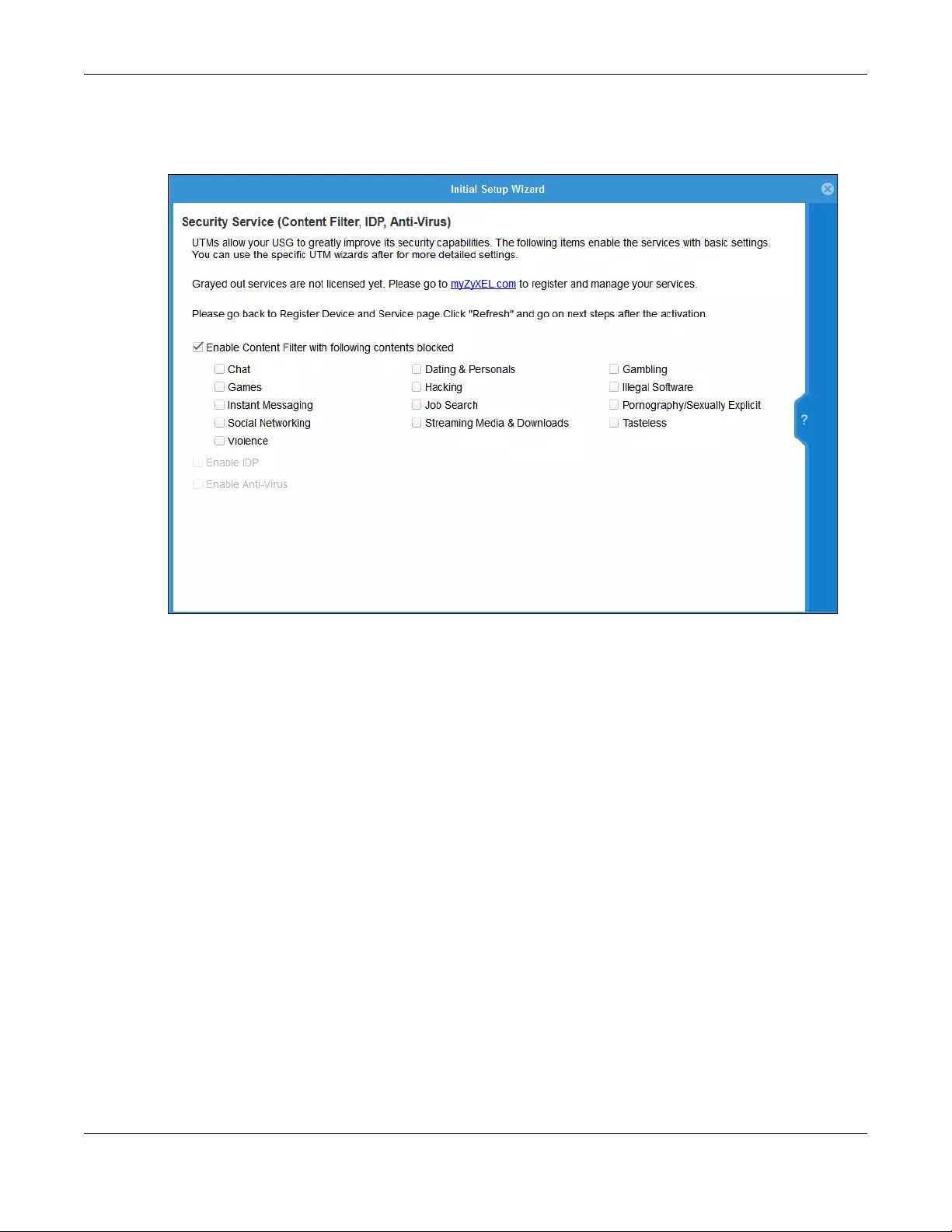
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
89
4.3 Initial Setup Wizard - Security Service
Figure 69 Initial Setup Wizard Security Service
Configure licensed (non-grayed-out) services in this screen. After you buy a license for a service, you
must activate it at myZyxel.com. Make sure the Zyxel Device Internet connection is working correctly.
Select Enable Content Filter to block websites by category, such as Chat websites. Note that if you select
Chat, the Content Filter blocks chat websites and not chat apps. Therefore, the Skype app can still be
used although the Skype website would be blocked. Select the categories you want to block.
•Chat: Sites that enable web-based exchange of real time messages through chat services or chat
rooms. For example, me.sohu.com, blufiles.storage.live.com.
•Dating & Personals: Sites that promote networking for interpersonal relationships such as dating and
marriage. Includes sites for match-making, online dating, spousal introduction. For example, www.i-
part.com.tw, www.imatchi.com.
•Gambling: Sites that offer or are related to online gambling, lottery, casinos and betting agencies
involving chance. For example, www.taiwanlottery.com.tw, www.i-win.com.tw, www.hkjc.com.
•Games: Sites relating to computer or other games, information about game producers, or how to
obtain cheat codes. Game-related publication sites. For example, www.gamer.com.tw,
www.wowtaiwan.com.tw, tw.lineage.gamania.com.
•Hacking: Sites that promote or give advice about how to gain unauthorized access to proprietary
computer systems, for the purpose of stealing information, perpetrating fraud, creating viruses, or
committing other illegal activity related to theft of digital information. For example,
www.hackbase.com, www.chinahacker.com.
•Illegal Software: Sites that illegally distribute software or copyrighted materials such as movies or
music, software cracks, illicit serial numbers, illegal license key generators. For example,
www.zhaokey.com.cn, www.tiansha.net.

Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
90
•Instant Messaging: Sites that enable logging in to instant messaging services such as ICQ, AOL Instant
Messenger, IRC, MSN, Jabber, Yahoo Messenger, and the like. For example, www.meebo.com,
www.aim.com, www. ebuddy.com.
•Job Search: Sites containing job listings, career information, assistance with job searches (such as
resume writing, interviewing tips, etc.), employment agencies or head hunters. For example,
www.104.com.tw, www.1111.com.tw, www.yes123.com.tw.
•Pornography/Sexually Explicit: Sites that contain explicit sexual content. Includes adult products such
as sex toys, CD-ROMs, and videos, adult services such as videoconferencing, escort services, and strip
clubs, erotic stories and textual descriptions of sexual acts. For example, www.dvd888.com,
www.18center.com, blog.sina.com.tw.
•Social Networking: Sites that enable social networking for online communities of various topics, for
friendship, dating, or professional reasons. For example, www.facebook.com, www.flickr.com,
www.groups.google.com.
•Streaming Media & Downloads: Sites that deliver streaming content, such as Internet radio, Internet TV
or MP3 and live or archived media download sites. Includes fan sites, or official sites run by musicians,
bands, or record labels. For example, www.youtube.com, pfp.sina.com.cn, my.xunlei.com.
•Tasteless: Sites with offensive or tasteless content such as bathroom humor or profanity. For example,
comedycentral.com, dilbert.com.
•Violence: Sites that contain images or text depicting or advocating physical assault against humans,
animals, or institutions. Sites of a particularly gruesome nature such as shocking depictions of blood or
wounds, or cruel animal treatment. For example, crimescene.com, deathnet.com,
michiganmilitia.com.
Select Enable IDP to drop traffic with recognized Intrusion, Detection & Protection attack patterns.
Select Enable Anti-Virus to detect virus patterns in files.
Use the Security Service Wizard if you need more detailed settings. Grayed-out services are not licensed
yet. Please go to portal.myzyxel.com to register and manage your services.
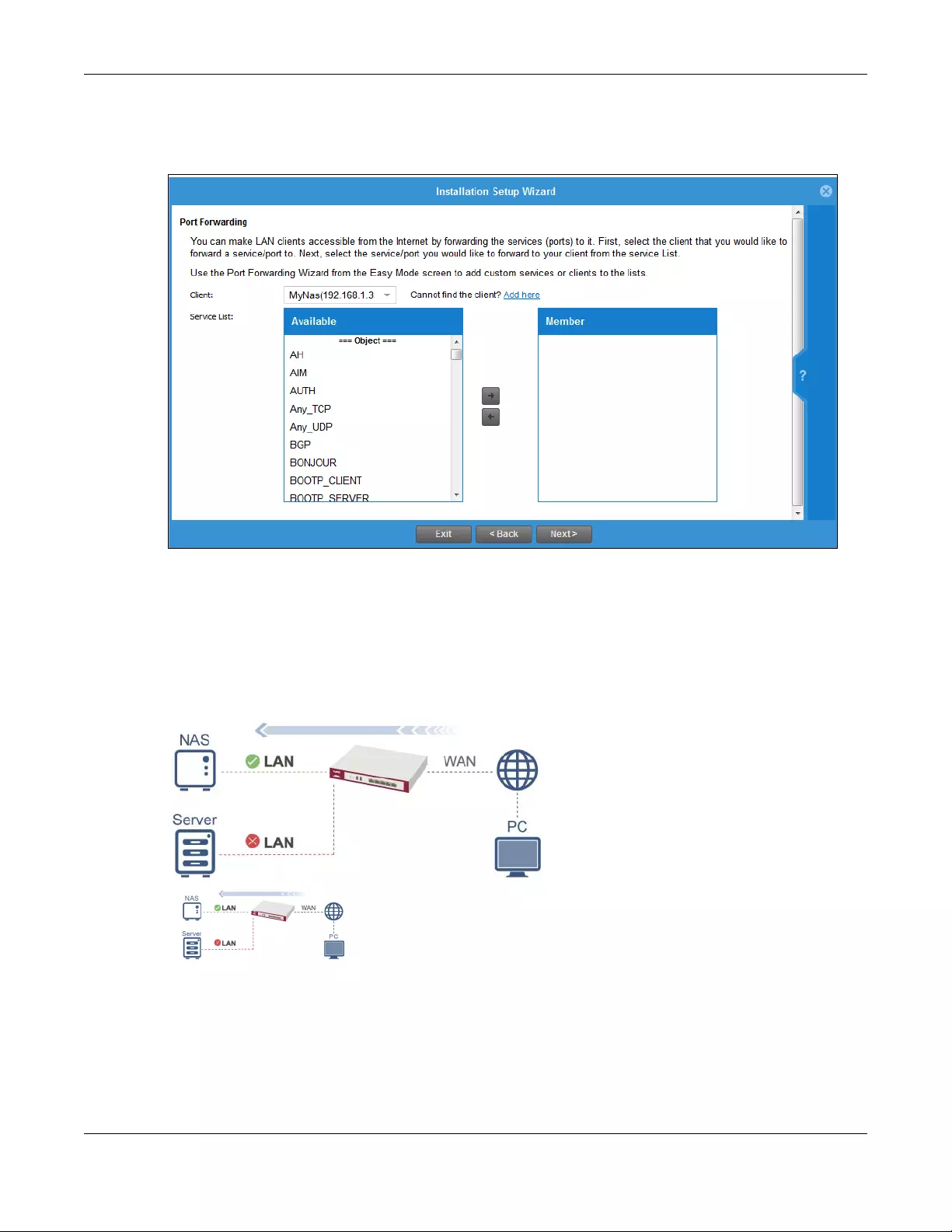
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
91
4.4 Initial Setup Wizard - Port Forwarding
Figure 70 Initial Setup Wizard Port Forwarding
NAT port forwarding allows the Zyxel Device to direct incoming traffic from the Internet to the correct
virtual server in your network. For example, if you have a NAS server in your network that you or other
people need access to from outside your network, select the IP address of the NAS from Client. Then,
select the service(s) that your NAS provides (for example FTP, HTTP, HTTPS) from the Available box and
use the right arrow to move each service to the Member box.
Even though the NAS is in your local network receiving the protection of the Zyxel Device, you can still
access that NAS using these services from anywhere outside your network.
Run the main Port Forwarding Wizard if you cannot see service you need in the list. In that wizard you
can define other services.
A client or device in your network acting as a server for forwarded services (for example, the NAS) needs
to have a static address. If the client selected does not have a static IP address, the IP address may
change when the client reboots, so the Zyxel Device may not be able to find it. If this happens, check
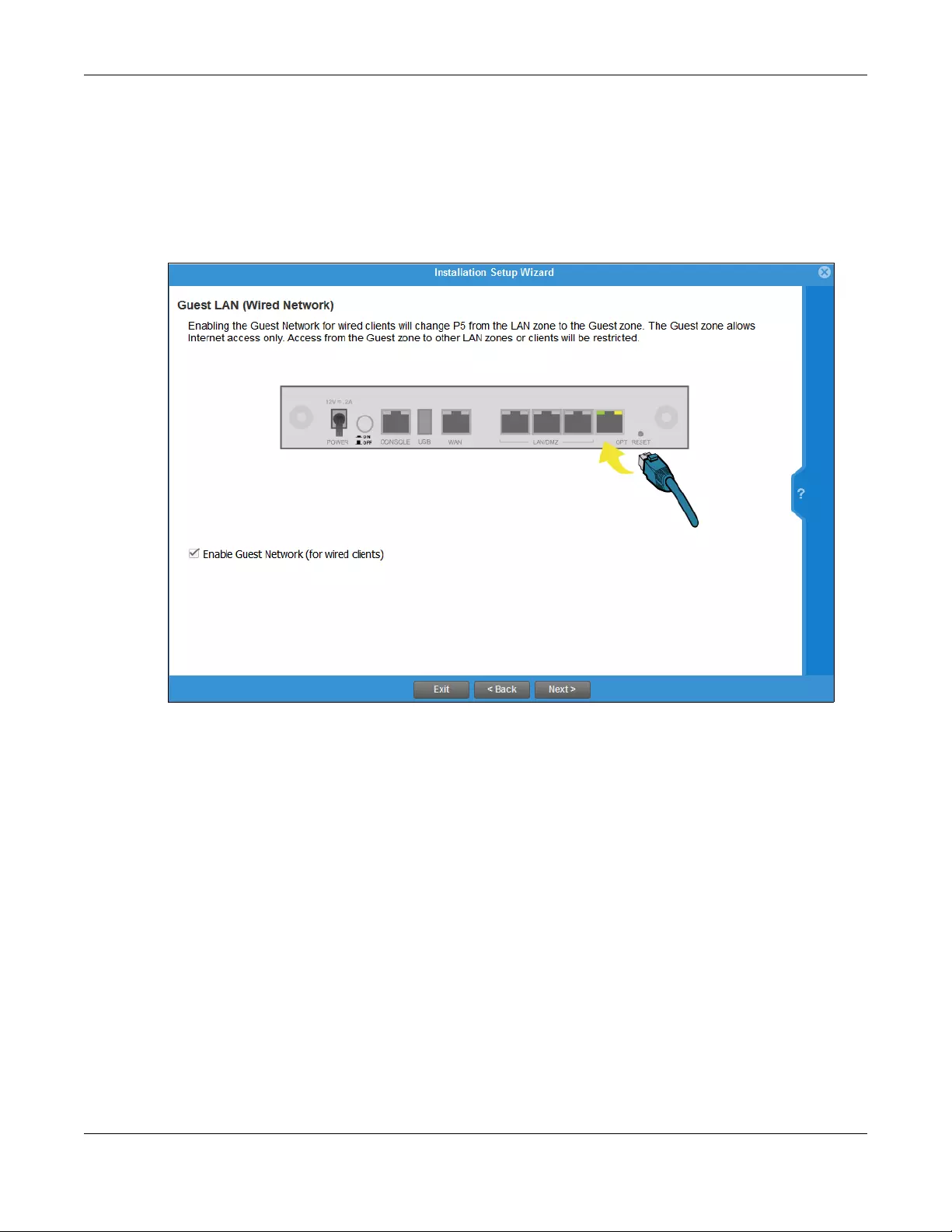
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
92
for the new IP address of the client. Then add the new IP address by clicking Add here and entering it in
the pop-up screen.
4.5 Initial Setup Wizard - Guest LAN
Figure 71 Initial Setup Wizard Guest LAN
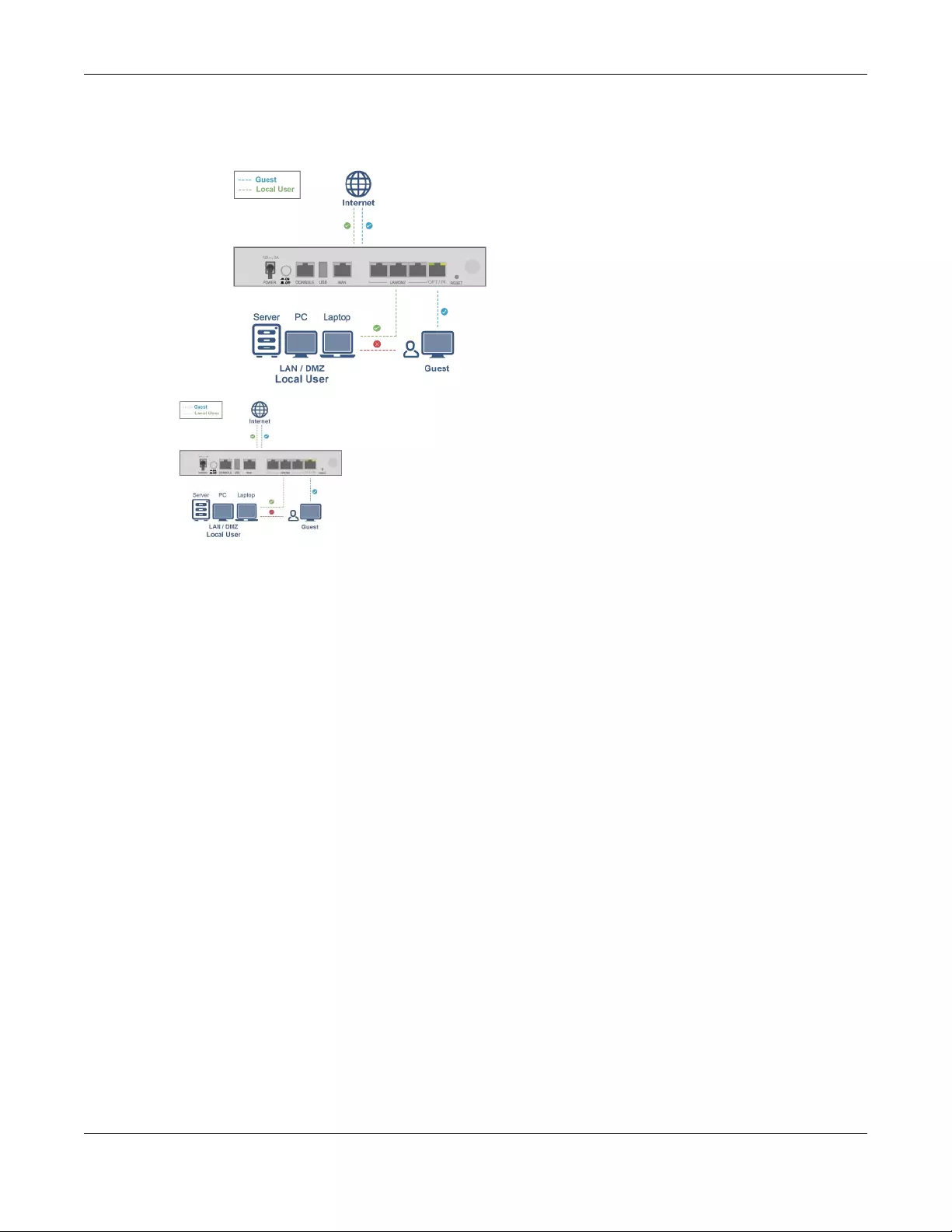
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
93
Select Enable Guest Network (for wired client s) to convert the OPT or P6 port (depending on your model)
to be a guest port and isolate it from the LAN/DMZ ports. Devices connected to the guest port are
allowed Internet access only and do not have access to networks connected to the other ports.
When the OPT or P6 port is not a guest port, then guest devices connected to that port can
communicate with all networks, including devices connected to the LAN/DMZ ports. If that is not your
intention, make sure Enable Guest Network (for wired clients) is selected and that guest devices are only
connected to the OPT or P6 port on the Zyxel Device.
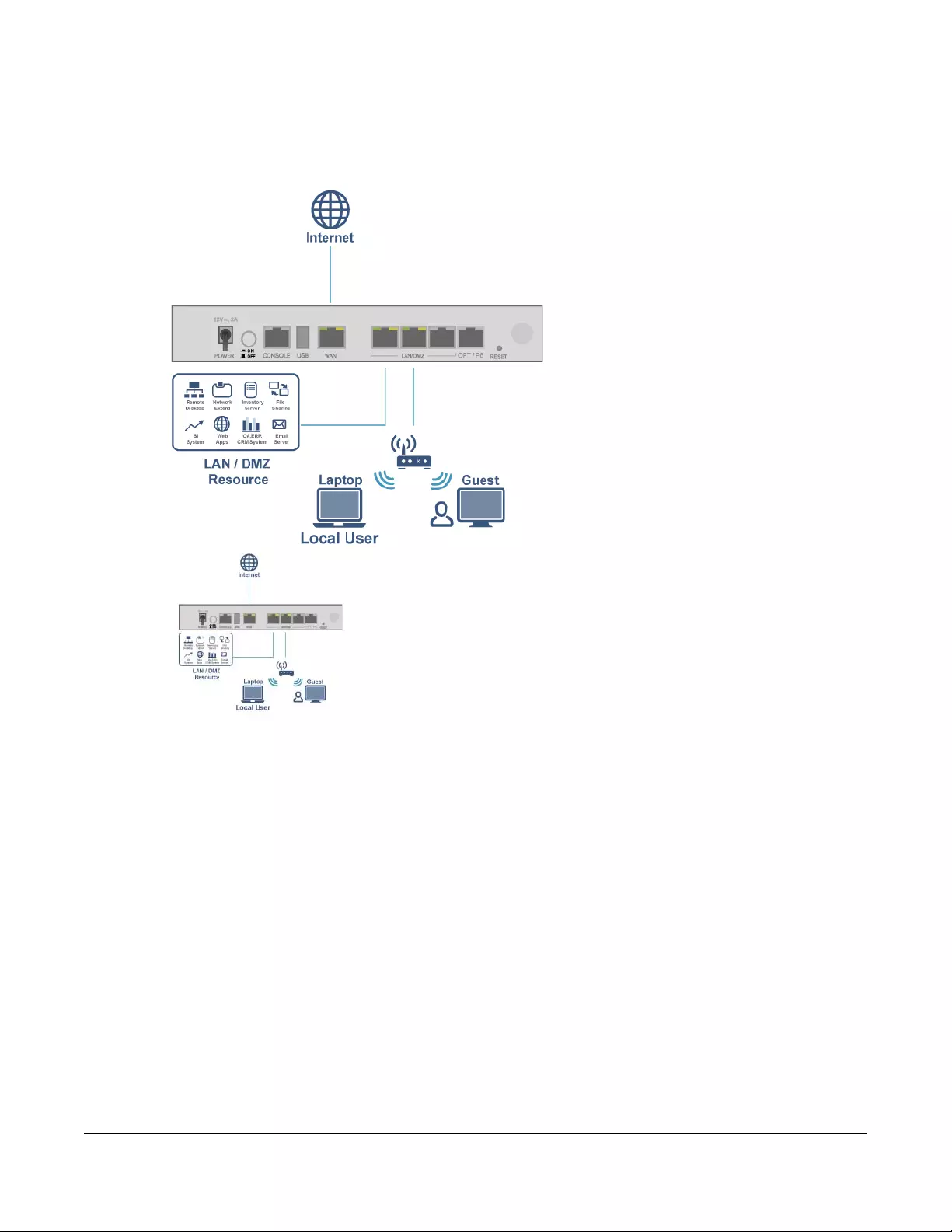
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
94
4.5.1 Connecting AP Scenarios
If you connect an AP to a LAN port, then users can use the AP’s SSID to wirelessly access all wired
resources connected to the LAN ports and Internet access.

Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
95
If you connect an AP to the Guest port, then users can use the AP’s SSID to wirelessly access all wired
resources connected to the Guest port (only) and Internet access. You must select both Enable Guest
Wi-Fi Network and Guest LAN (Wired Network).
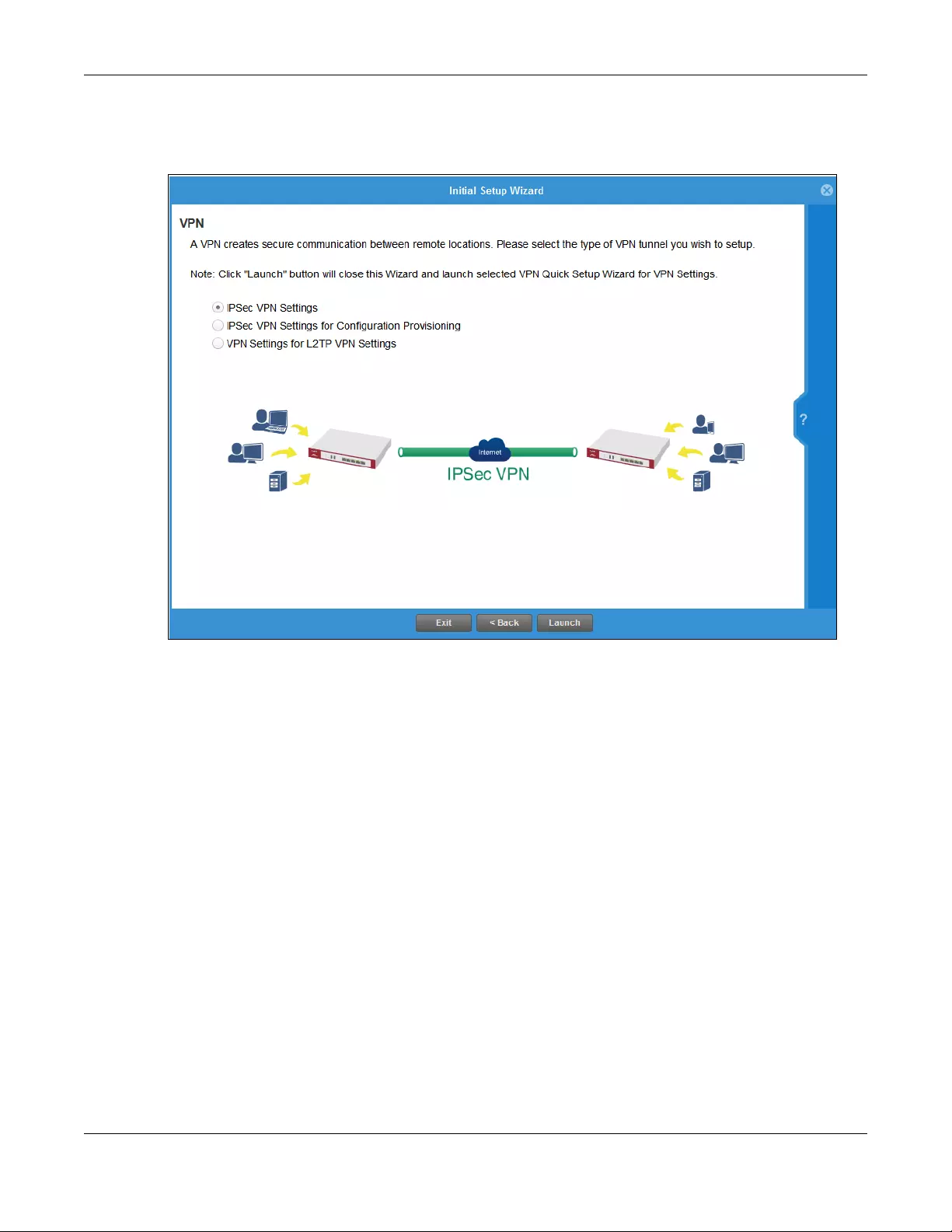
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
96
4.6 Initial Setup Wizard - VPN
Figure 72 Initial Setup Wizard VPN
A VPN is a secure, private connection between two end points. An end point could be a VPN gateway
like the Zyxel Device itself or a computer with VPN software installed. Select a VPN wizard type and click
Launch to begin that wizard and end the Initial Setup Wizard with changes saved. Click Exit to leave the
wizard with changes unsaved.
•Select IPSec VPN Settings to create a secure, private connection between two Zyxel Devices. Two
networks (sites) behind the Zyxel Devices can then communicate securely with each other.
Make sure that the settings on both Zyxel Devices are correct and reciprocal. What is a local setting
for one should be the equivalent remote setting on the other. Make sure the pre-shared key,
negotiation mode, encryption, authentication settings, DH key group and so on are the same on both
Zyxel Devices.
Make sure that both Zyxel Devices are able to communicate with each other. Try pinging one
gateway from a computer behind the other.
Make sure that there is not a firewall blocking VPN traffic in front of one of the Zyxel Devices.
•Select IPSec VPN Settings for Configuration Provisioning to create a secure, private connection
between a Zyxel Device and a computer with Zyxel client VPN software installed. See the client VPN
software’s help to see how to configure it. The computer with client VPN software installed and the
Zyxel Device can then communicate securely with each other.
Make sure the client VPN software is installed and configured correctly on the computer. See the
client VPN software’s help if anything is unclear.
Make sure the VPN settings such as the pre-shared key (or certificate), negotiation mode, encryption,
authentication settings, DH key group on the computer and the Zyxel Device are correct. Make sure
that the client is able to communicate with the Zyxel Device. Try pinging the Zyxel Device from the
client.
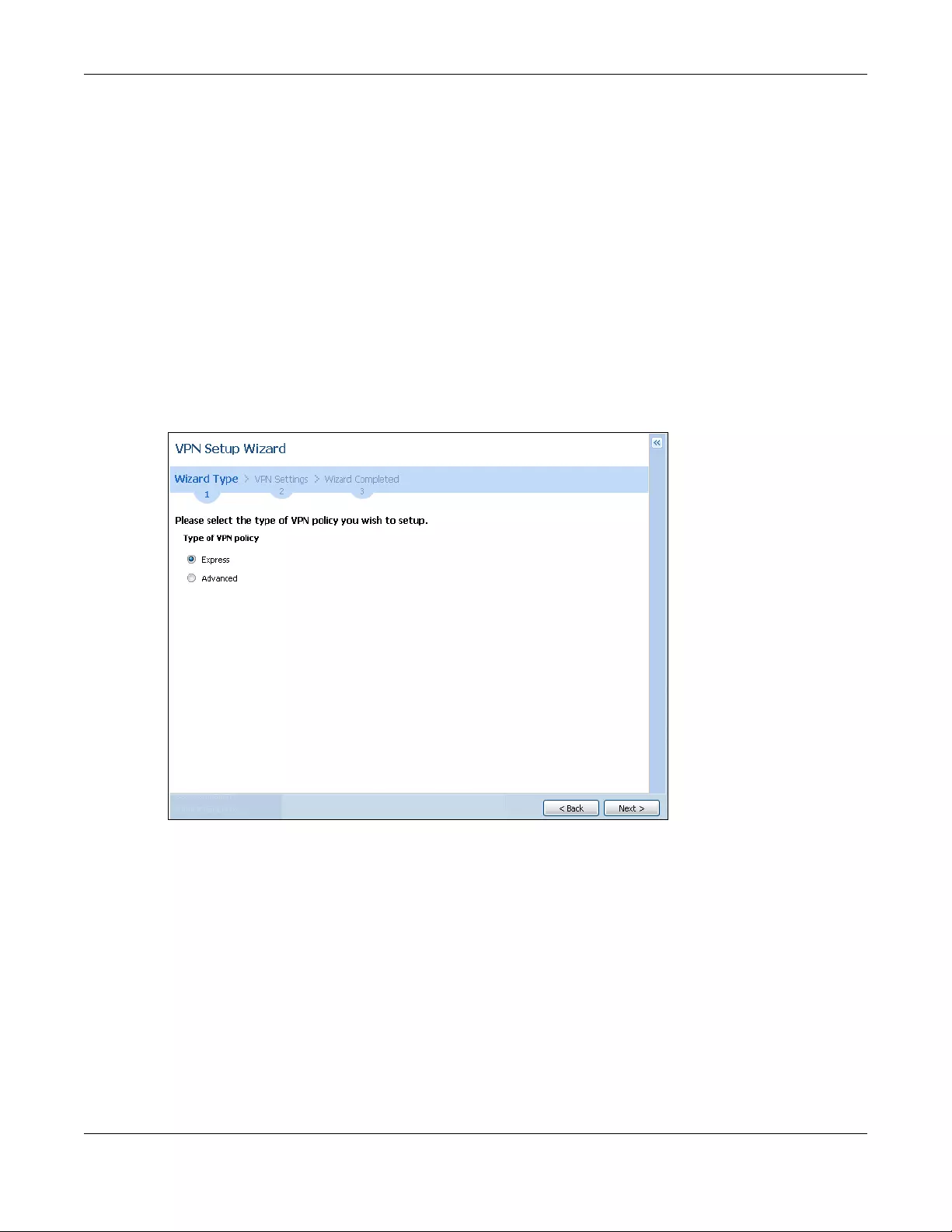
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
97
•Select VPN Settings for L2TP VPN Settings to create a secure, private connection between the Zyxel
Device and a computer with L2TP VPN software installed. Many computer operating systems come
with L2TP installed. See your computer’s help to see how to configure it. The L2TP computer and the
Zyxel Device will then communicate securely with each other.
Make sure that the computer with L2TP is able to communicate with the Zyxel Device. Try pinging the
Zyxel Device from the computer. Make sure that L2TP traffic is allowed through the WAN on the Zyxel
Device.
4.6.1 VPN Setup Wizard: Wizard Type
Choose Express to create a VPN rule with the default phase 1 and phase 2 settings to connect to
another ZLD-based Zyxel Device using a pre-shared key.
Choose Advanced to change the default settings and/or use certificates instead of a pre-shared key to
create a VPN rule to connect to another IPSec device.
Figure 73 VPN Setup Wizard: Wizard Type
4.6.2 VPN Express Wizard - Scenario
Click the Express radio button as shown in the previous figure to display the following screen.
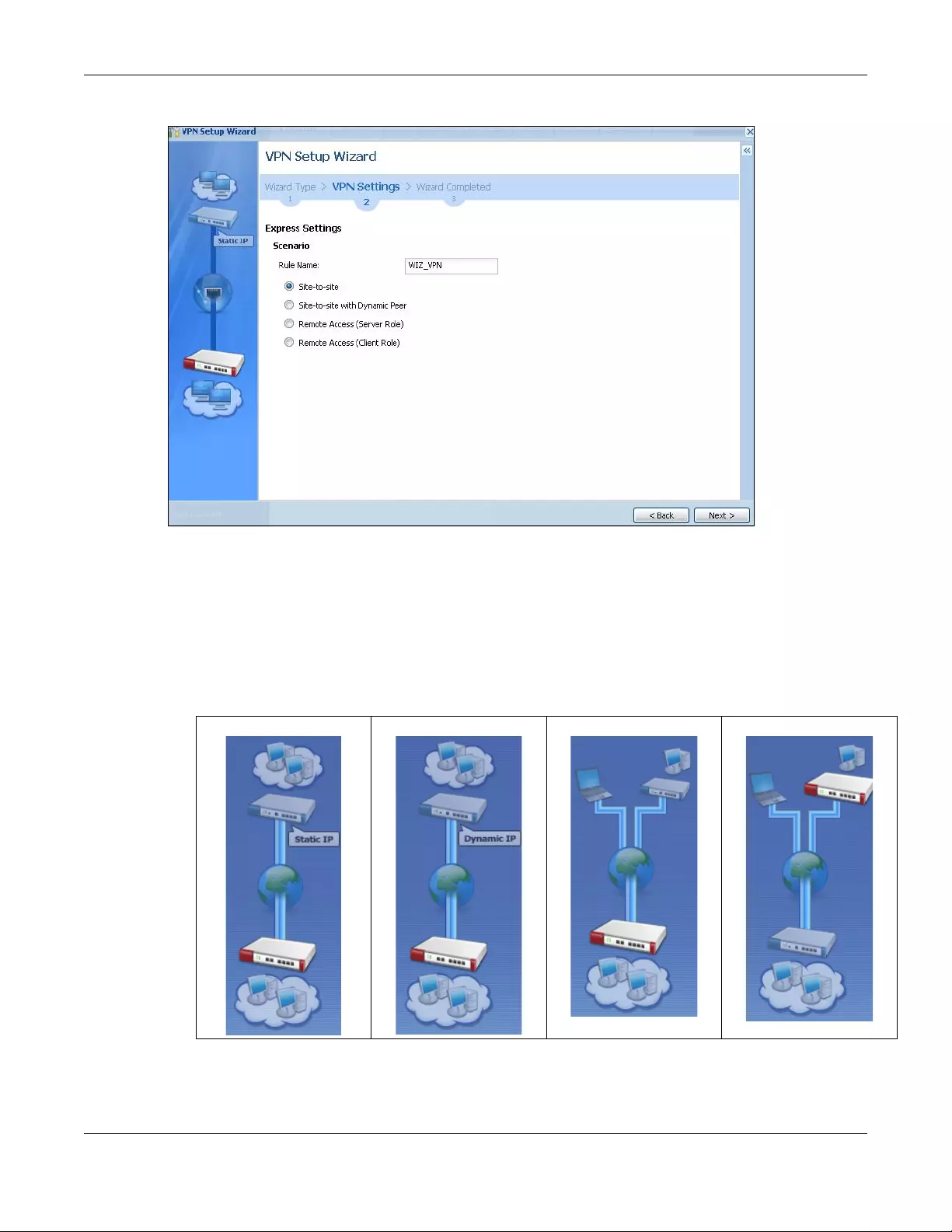
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
98
Figure 74 VPN Express Wizard: Scenario
Rule Name: Type the name used to identify this VPN connection (and VPN gateway). You may use 1-31
alphanumeric characters, underscores (_), or dashes (-), but the first character cannot be a number.
This value is case-sensitive.
Select the scenario that best describes your intended VPN connection. The figure on the left of the
screen changes to match the scenario you select.
•Site-to-site - choose this if the remote IPSec router has a static IP address or a domain name. This Zyxel
Device can initiate the VPN tunnel. The remote IPSec router can also initiate the VPN tunnel if this Zyxel
Device has a static IP address or a domain name.
SITE-TO-SITE SITE-TO-SITE WITH
DYNAMIC PEER REMOTE ACCESS
(SERVER ROLE) REMOTE ACCESS (CLIENT
ROLE)
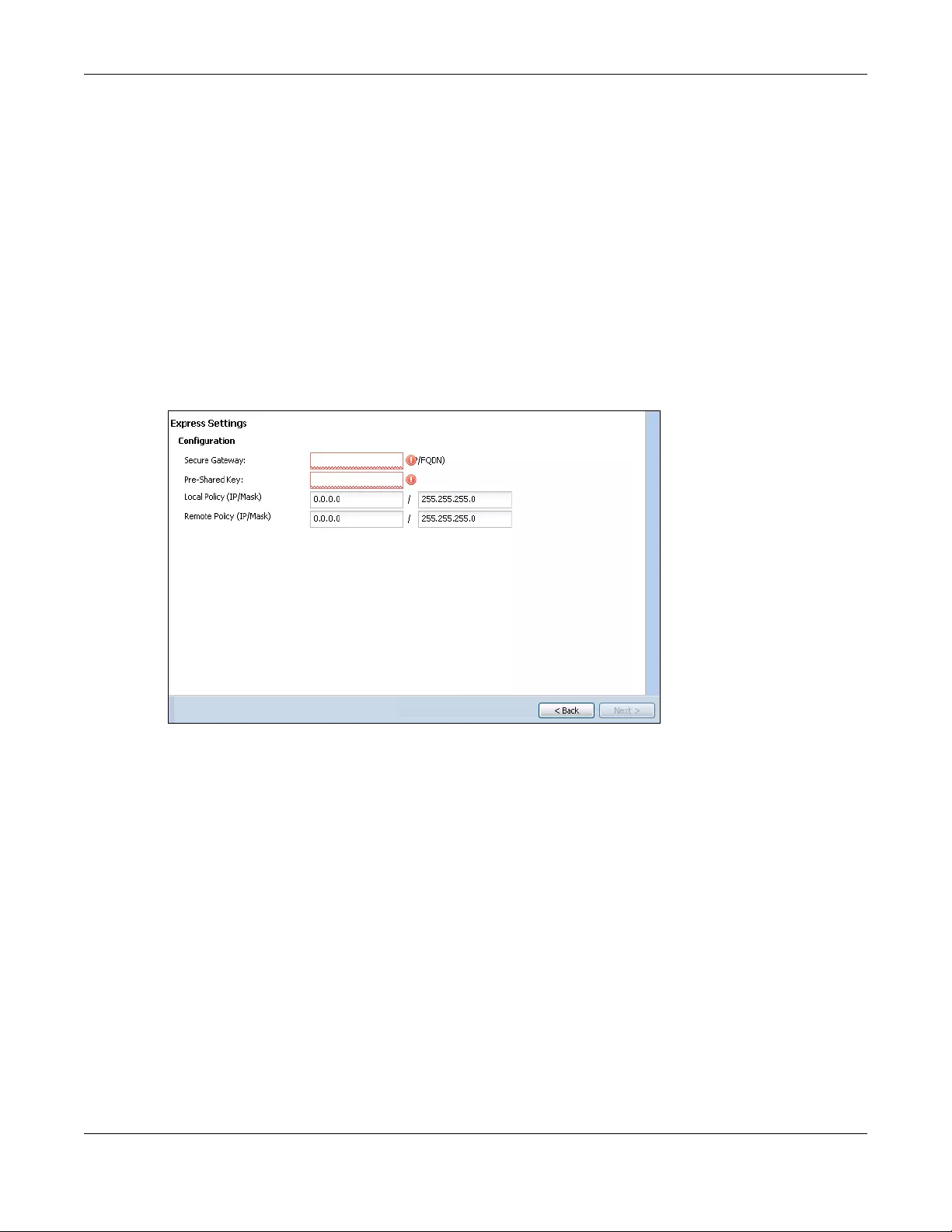
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
99
•Site-to-site with Dynamic Peer - choose this if the remote IPSec router has a dynamic IP address. You
don’t specify the remote IPSec router’s address, but you specify the remote policy (the addresses of
the devices behind the remote IPSec router). This Zyxel Device must have a static IP address or a
domain name. Only the remote IPSec router can initiate the VPN tunnel.
•Remote Access (Server Role) - choose this to allow incoming connections from IPSec VPN clients. The
clients have dynamic IP addresses and are also known as dial-in users. You don’t specify the
addresses of the client IPSec routers or the remote policy. This creates a dynamic IPSec VPN rule that
can let multiple clients connect. Only the clients can initiate the VPN tunnel.
•Remote Access (Client Role) - choose this to connect to an IPSec server. This Zyxel Device is the client
(dial-in user). Client role Zyxel Devices initiate IPSec VPN connections to a server role Zyxel Device. This
Zyxel Device can have a dynamic IP address. The IPSec server doesn’t configure this Zyxel Device’s IP
address or the addresses of the devices behind it. Only this Zyxel Device can initiate the VPN tunnel.
4.6.3 VPN Express Wizard - Configuration
Figure 75 VPN Express Wizard: Configuration
•Secure Gateway: Any displays in this field if it is not configurable for the chosen scenario. Otherwise,
enter the WAN IP address or domain name of the remote IPSec device (secure gateway) to identify
the remote IPSec router by its IP address or a domain name. Use 0.0.0.0 if the remote IPSec router has
a dynamic WAN IP address.
•Pre-Shared Key: Type the password. Both ends of the VPN tunnel must use the same password. Use 8
to 31 case-sensitive ASCII characters or 8 to 31 pairs of hexadecimal (“0-9”, “A-F”) characters.
Proceed a hexadecimal key with “0x”. You will receive a PYLD_MALFORMED (payload malformed)
packet if the same pre-shared key is not used on both ends.
•Local Policy (IP/Mask): Type the IP address of a computer on your network that can use the tunnel.
You can also specify a subnet. This must match the remote IP address configured on the remote IPSec
device.
•Remote Policy (IP/Mask): Any displays in this field if it is not configurable for the chosen scenario.
Otherwise, type the IP address of a computer behind the remote IPSec device. You can also specify
a subnet. This must match the local IP address configured on the remote IPSec device.
4.6.4 VPN Express Wizard - Summary
This screen provides a read-only summary of the VPN tunnel’s configuration and commands that you
can copy and paste into another ZLD-based Zyxel Device’s command line interface to configure it.
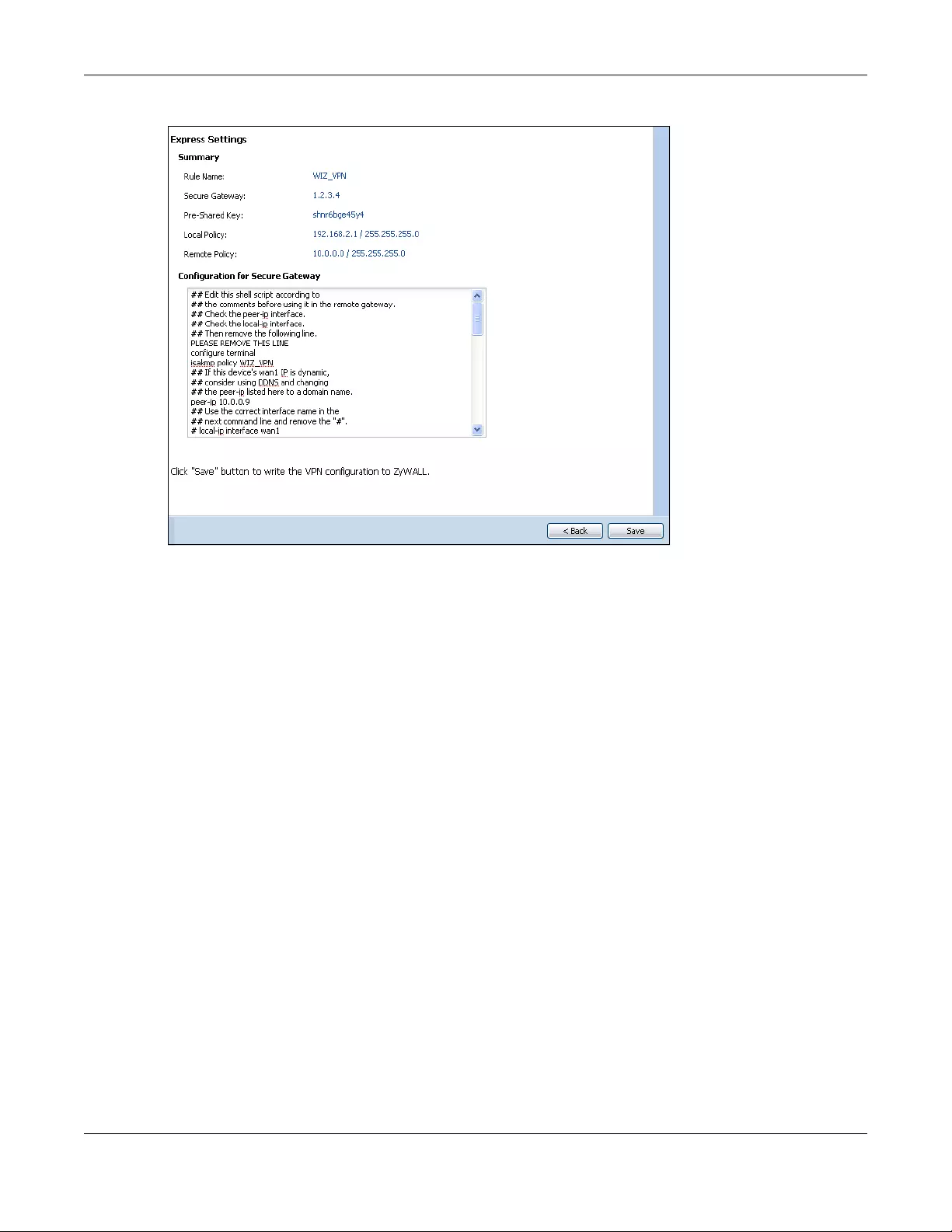
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
100
Figure 76 VPN Express Wizard: Summary
•Rule Name: Identifies the VPN gateway policy.
•Secure Gateway: IP address or domain name of the remote IPSec device. If this field displays Any,
only the remote IPSec device can initiate the VPN connection.
•Pre-Shared Key: VPN tunnel password. It identifies a communicating party during a phase 1 IKE
negotiation.
•Local Policy: IP address and subnet mask of the computers on the network behind your Zyxel Device
that can use the tunnel.
•Remote Policy: IP address and subnet mask of the computers on the network behind the remote
IPSec device that can use the tunnel. If this field displays Any, only the remote IPSec device can
initiate the VPN connection.
• Copy and paste the Configuration for Secure Gateway commands into another ZLD-based Zyxel
Device’s command line interface to configure it to serve as the other end of this VPN tunnel. You can
also use a text editor to save these commands as a shell script file with a “.zysh” filename extension.
Use the file manager to run the script in order to configure the VPN connection. See the commands
reference guide for details on the commands displayed in this list.
4.6.5 VPN Express Wizard - Finish
Now the rule is configured on the Zyxel Device. The Phase 1 rule settings appear in the VPN > IPSec VPN
> VPN Gateway screen and the Phase 2 rule settings appear in the VPN > IPSec VPN > VPN Connection
screen.
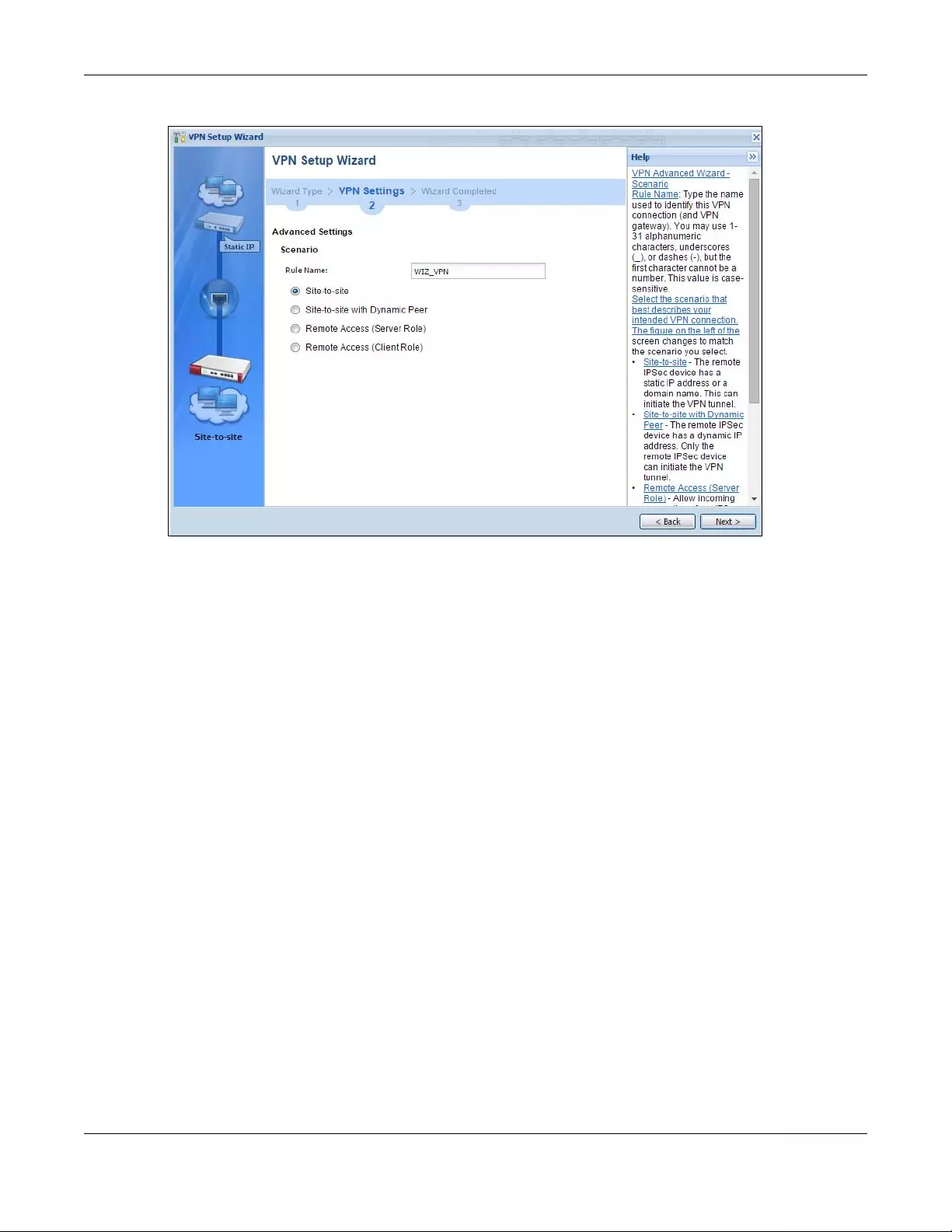
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
102
Figure 78 VPN Advanced Wizard: Scenario
Rule Name: Type the name used to identify this VPN connection (and VPN gateway). You may use 1-31
alphanumeric characters, underscores (_), or dashes (-), but the first character cannot be a number.
This value is case-sensitive.
Select the scenario that best describes your intended VPN connection. The figure on the left of the
screen changes to match the scenario you select.
•Site-to-site - The remote IPSec device has a static IP address or a domain name. This Zyxel Device can
initiate the VPN tunnel.
•Site-to-site with Dynamic Peer - The remote IPSec device has a dynamic IP address. Only the remote
IPSec device can initiate the VPN tunnel.
•Remote Access (Server Role) - Allow incoming connections from IPSec VPN clients. The clients have
dynamic IP addresses and are also known as dial-in users. Only the clients can initiate the VPN tunnel.
•Remote Access (Client Role) - Connect to an IPSec server. This Zyxel Device is the client (dial-in user)
and can initiate the VPN tunnel.
4.6.7 VPN Advanced Wizard - Phase 1 Settings
There are two phases to every IKE (Internet Key Exchange) negotiation – phase 1 (Authentication) and
phase 2 (Key Exchange). A phase 1 exchange establishes an IKE SA (Security Association).
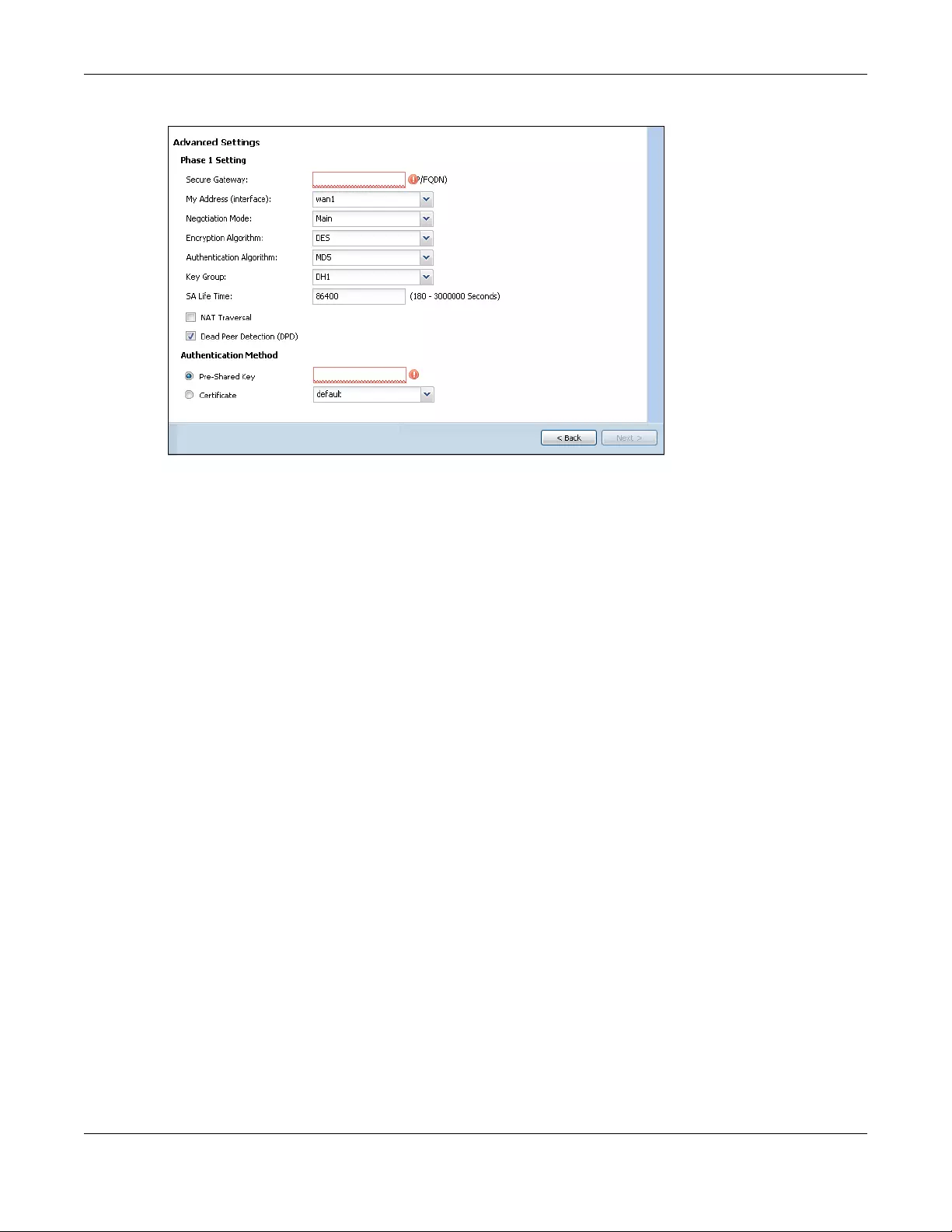
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
103
Figure 79 VPN Advanced Wizard: Phase 1 Settings
•Secure Gateway: Any displays in this field if it is not configurable for the chosen scenario. Otherwise,
enter the WAN IP address or domain name of the remote IPSec device (secure gateway) to identify
the remote IPSec device by its IP address or a domain name. Use 0.0.0.0 if the remote IPSec device
has a dynamic WAN IP address.
•My Address (interface): Select an interface from the drop-down list box to use on your Zyxel Device.
•Negotiation Mode: This displays Main or Aggressive:
•Main encrypts the ZyWALL/USG’s and remote IPSec router’s identities but takes more time to
establish the IKE SA
•Aggressive is faster but does not encrypt the identities.
The ZyWALL/USG and the remote IPSec router must use the same negotiation mode. Multiple SAs
connecting through a secure gateway must have the same negotiation mode.
•Encryption Algorithm: 3DES and AES use encryption. The longer the key, the higher the security (this
may affect throughput). Both sender and receiver must use the same secret key, which can be used
to encrypt and decrypt the message or to generate and verify a message authentication code. The
DES encryption algorithm uses a 56-bit key. Triple DES (3DES) is a variation on DES that uses a 168-bit
key. As a result, 3DES is more secure than DES. It also requires more processing power, resulting in
increased latency and decreased throughput. AES128 uses a 128-bit key and is faster than 3DES.
AES192 uses a 192-bit key, and AES256 uses a 256-bit key.
•Authentication Algorithm: MD5 gives minimal security and SHA512 gives the highest security. MD5
(Message Digest 5) and SHA (Secure Hash Algorithm) are hash algorithms used to authenticate
packet data. The stronger the algorithm the slower it is.
•Key Group: DH5 is more secure than DH1 or DH2 (although it may affect throughput). DH1 (default)
refers to Diffie-Hellman Group 1 a 768 bit random number. DH2 refers to Diffie-Hellman Group 2 a 1024
bit (1Kb) random number. DH5 refers to Diffie-Hellman Group 5 a 1536 bit random number.
•SA Life Time: Set how often the Zyxel Device renegotiates the IKE SA. A short SA life time increases
security, but renegotiation temporarily disconnects the VPN tunnel.
•NAT Traversal: Select this if the VPN tunnel must pass through NAT (there is a NAT router between the
IPSec devices).
Note: The remote IPSec device must also have NAT traversal enabled. See the help in the
main IPSec VPN screens for more information.
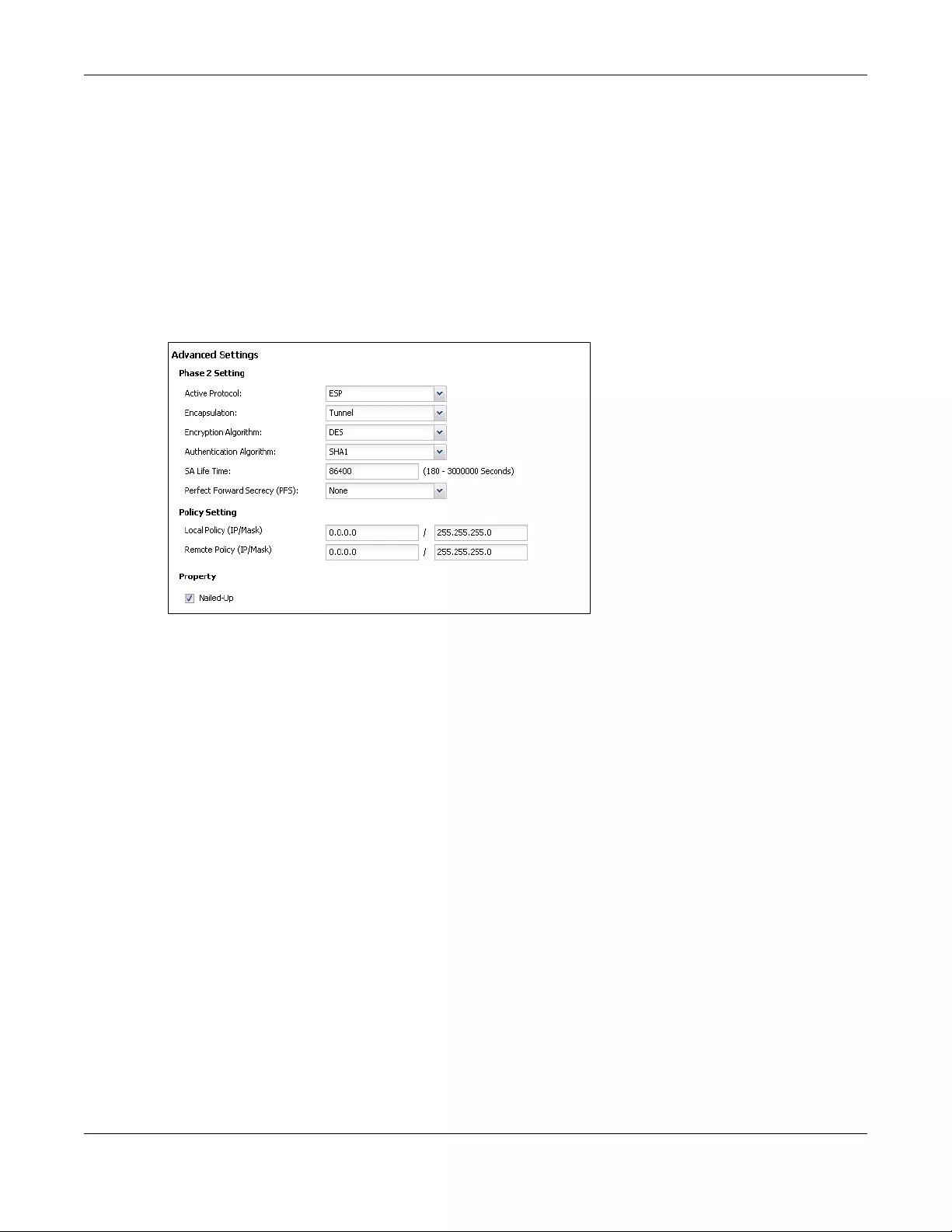
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
104
•Dead Peer Detection (DPD) has the Zyxel Device make sure the remote IPSec device is there before
transmitting data through the IKE SA. If there has been no traffic for at least 15 seconds, the Zyxel
Device sends a message to the remote IPSec device. If it responds, the Zyxel Device transmits the
data. If it does not respond, the Zyxel Device shuts down the IKE SA.
•Authentication Method: Select Pre-Shared Key to use a password or Certificate to use one of the Zyxel
Device’s certificates.
4.6.8 VPN Advanced Wizard - Phase 2
Phase 2 in an IKE uses the SA that was established in phase 1 to negotiate SAs for IPSec.
Figure 80 VPN Advanced Wizard: Phase 2 Settings
•Active Protocol: ESP is compatible with NAT, AH is not.
•Encapsulation: Tunnel is compatible with NAT, Transport is not.
•Encryption Algorithm: 3DES and AES use encryption. The longer the AES key, the higher the security
(this may affect throughput). Null uses no encryption.
•Authentication Algorithm: MD5 gives minimal security and SHA512 gives the highest security. MD5
(Message Digest 5) and SHA (Secure Hash Algorithm) are hash algorithms used to authenticate
packet data. The stronger the algorithm the slower it is.
•SA Life Time: Set how often the Zyxel Device renegotiates the IKE SA. A short SA life time increases
security, but renegotiation temporarily disconnects the VPN tunnel.
•Perfect Forward Secrecy (PFS): Disabling PFS allows faster IPSec setup, but is less secure. Select DH1,
DH2 or DH5 to enable PFS. DH5 is more secure than DH1 or DH2 (although it may affect throughput).
DH1 refers to Diffie-Hellman Group 1 a 768 bit random number. DH2 refers to Diffie-Hellman Group 2 a
1024 bit (1Kb) random number. DH5 refers to Diffie-Hellman Group 5 a 1536 bit random number (more
secure, yet slower).
•Local Policy (IP/Mask): Type the IP address of a computer on your network. You can also specify a
subnet. This must match the remote IP address configured on the remote IPSec device.
•Remote Policy (IP/Mask): Type the IP address of a computer behind the remote IPSec device. You
can also specify a subnet. This must match the local IP address configured on the remote IPSec
device.
•Nailed-Up: This displays for the site-to-site and remote access client role scenarios. Select this to have
the Zyxel Device automatically renegotiate the IPSec SA when the SA life time expires.
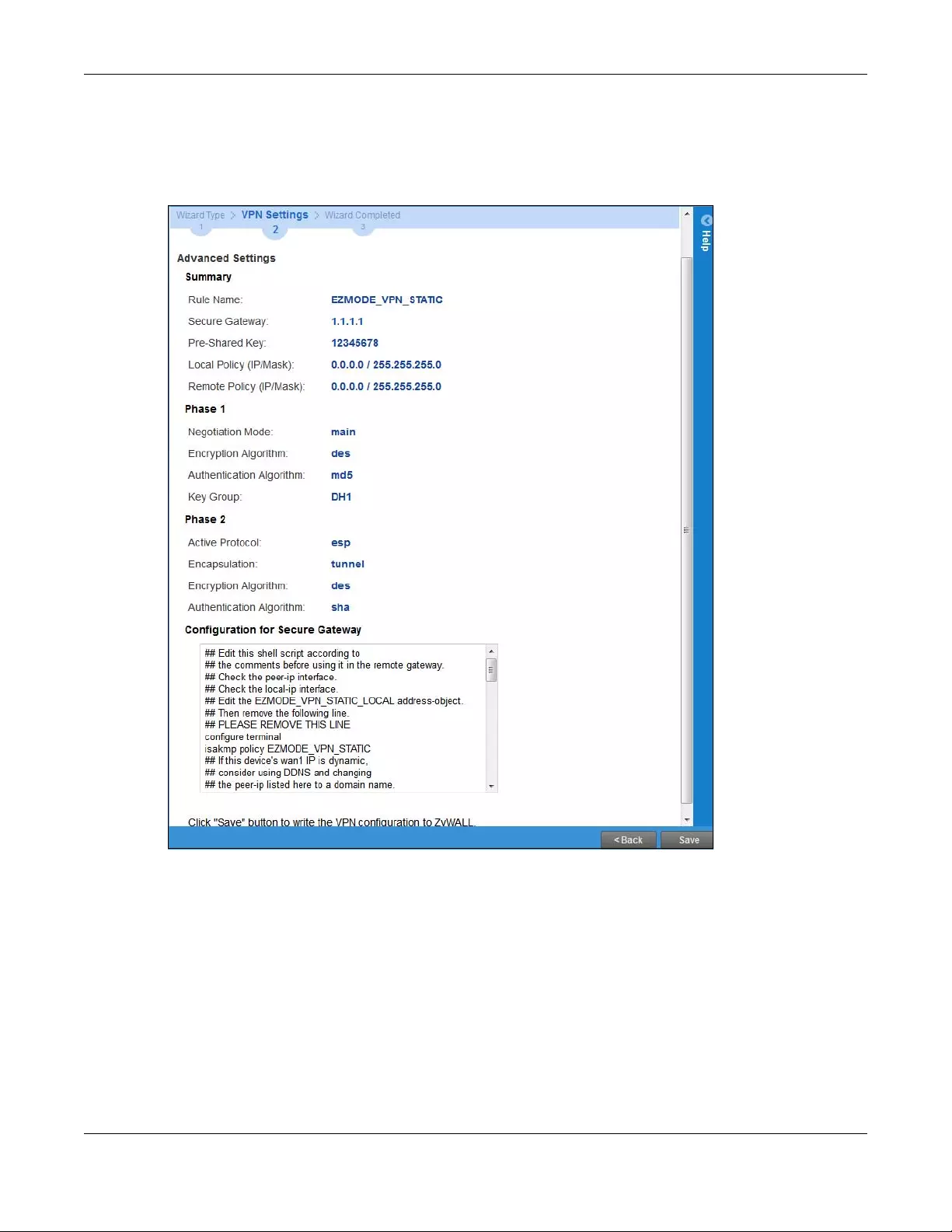
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
105
4.6.9 VPN Advanced Wizard - Summary
This is a read-only summary of the VPN tunnel settings.
Figure 81 VPN Advanced Wizard: Summary
•Rule Name: Identifies the VPN connection (and the VPN gateway).
•Secure Gateway: IP address or domain name of the remote IPSec device.
•Pre-Shared Key: VPN tunnel password.
•Certificate: The certificate the Zyxel Device uses to identify itself when setting up the VPN tunnel.
•Local Policy: IP address and subnet mask of the computers on the network behind your Zyxel Device
that can use the tunnel.
•Remote Policy: IP address and subnet mask of the computers on the network behind the remote
IPSec device that can use the tunnel.
• Copy and paste the Configuration for Remote Gateway commands into another ZLD-based Zyxel
Device’s command line interface.
• Click Save to save the VPN rule.
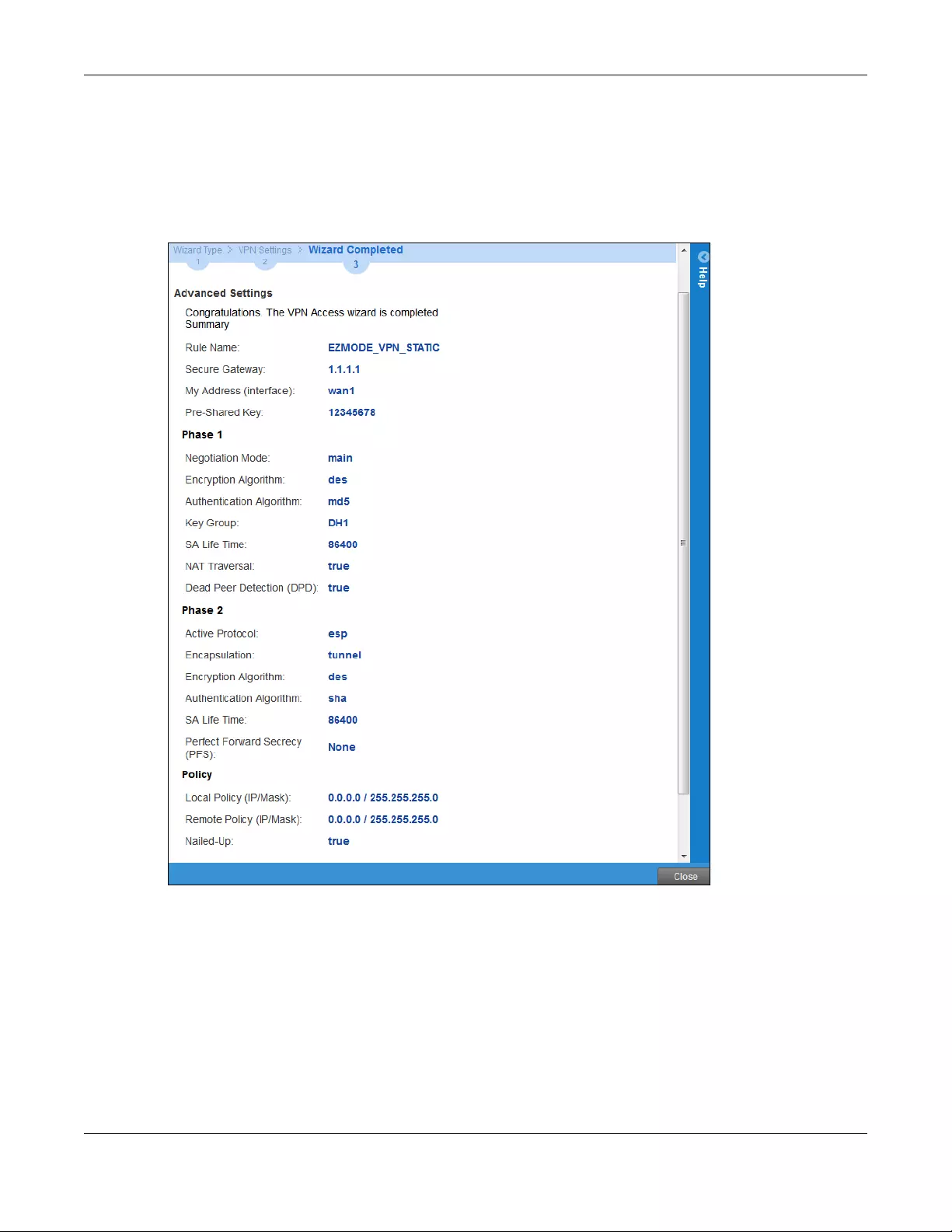
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
106
4.6.10 VPN Advanced Wizard - Finish
Now the rule is configured on the Zyxel Device. The Phase 1 rule settings appear in the VPN > IPSec VPN
> VPN Gateway screen and the Phase 2 rule settings appear in the VPN > IPSec VPN > VPN Connection
screen.
Figure 82 VPN Wizard: Finish
Click Close to exit the wizard.
4.7 VPN Settings for Configuration Provisioning Wizard:
Wizard Type
Use VPN Settings for Configuration Provisioning to set up a VPN rule that can be retrieved with the Zyxel
Device IPSec VPN Client.
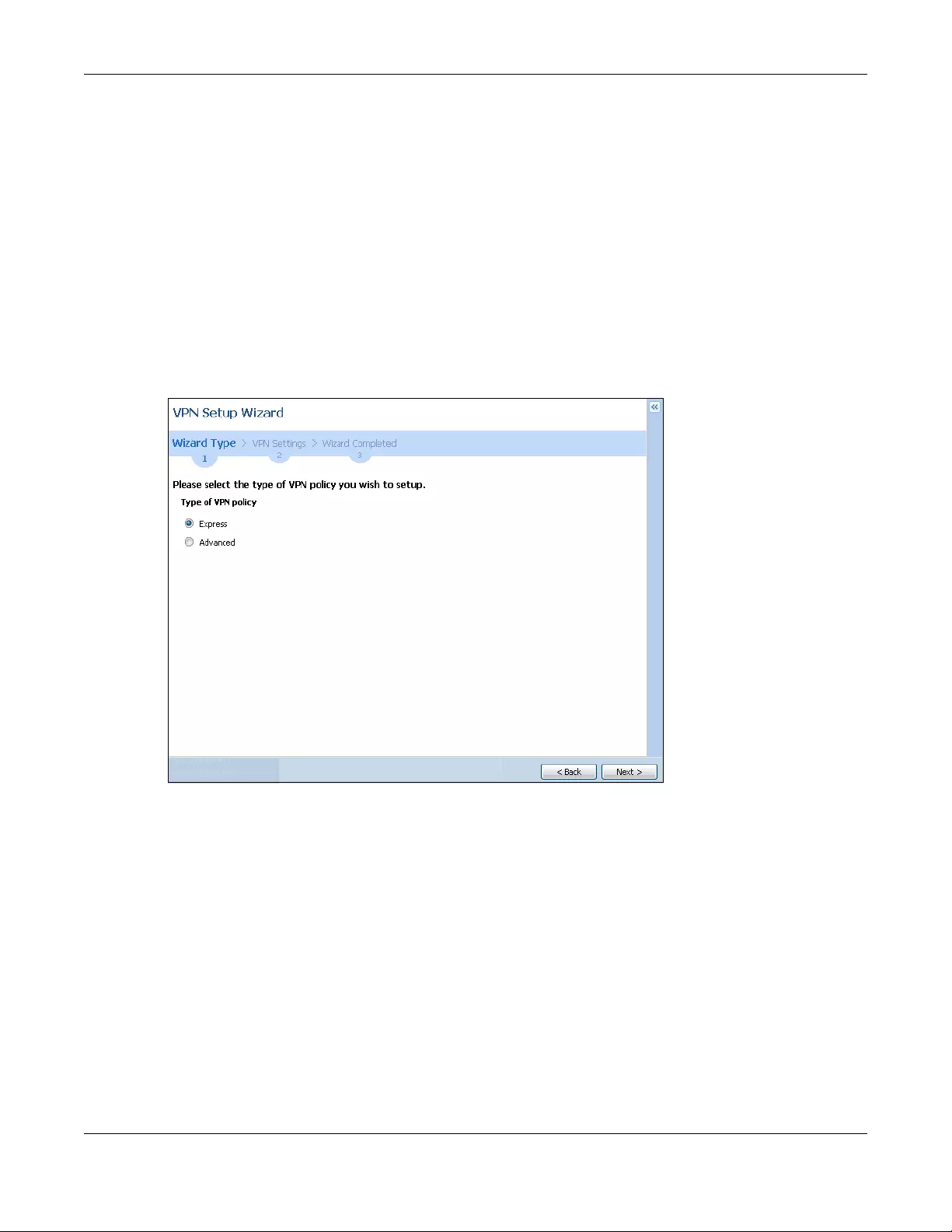
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
107
VPN rules for the Zyxel Device IPSec VPN Client have certain restrictions. They must not contain the
following settings:
•AH active protocol
•NULL encryption
•SHA512 authentication
• A subnet or range remote policy
Choose Express to create a VPN rule with the default phase 1 and phase 2 settings and to use a pre-
shared key.
Choose Advanced to change the default settings and/or use certificates instead of a pre-shared key in
the VPN rule.
Figure 83 VPN Settings for Configuration Provisioning Express Wizard: Wizard Type
4.7.1 Configuration Provisioning Express Wizard - VPN Settings
Click the Express radio button as shown in the previous screen to display the following screen.
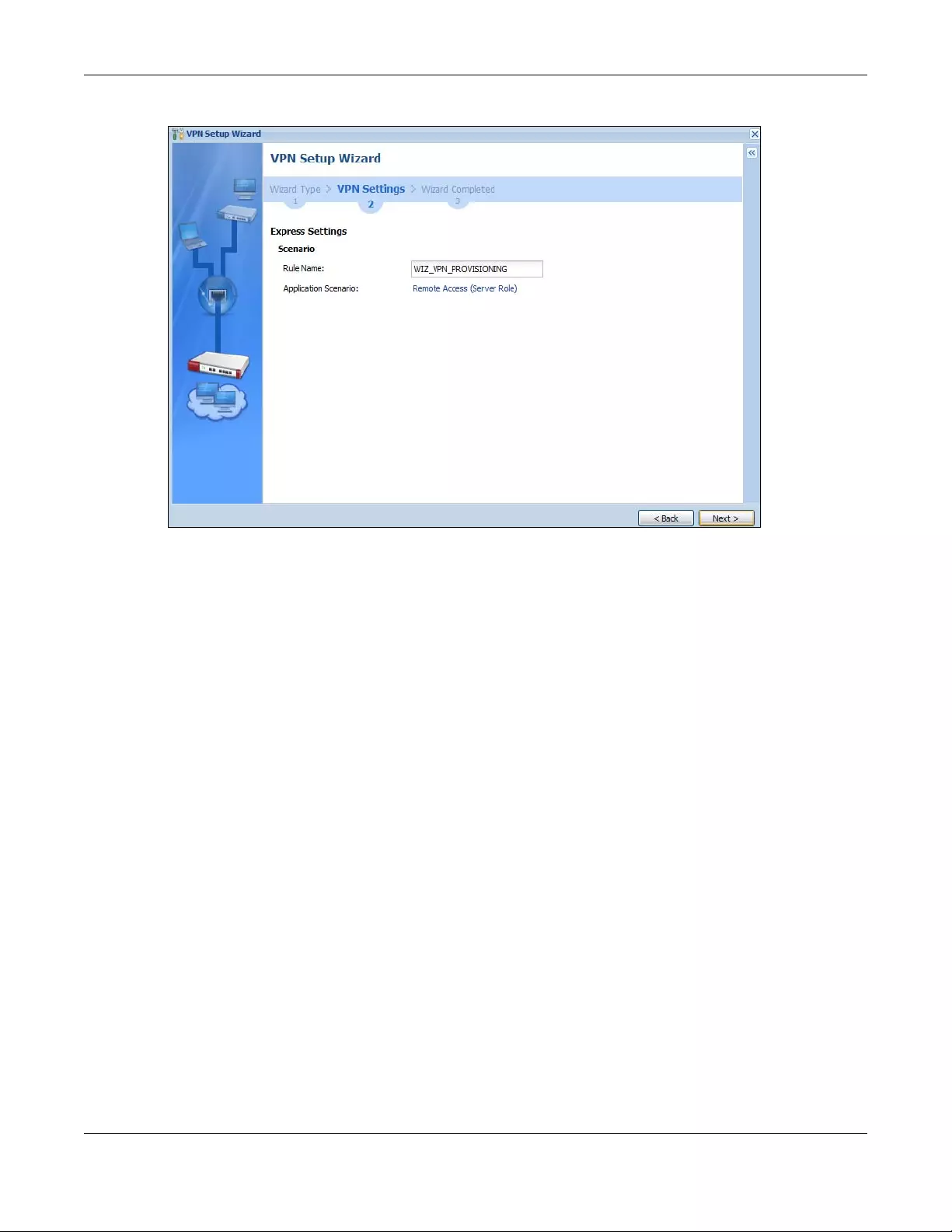
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
108
Figure 84 VPN for Configuration Provisioning Express Wizard: Settings Scenario
Rule Name: Type the name used to identify this VPN connection (and VPN gateway). You may use 1-31
alphanumeric characters, underscores (_), or dashes (-), but the first character cannot be a number.
This value is case-sensitive.
Application Scenario: Only the Remote Access (Server Role) is allowed in this wizard. It allows incoming
connections from the Zyxel Device IPSec VPN Client.
4.7.2 Configuration Provisioning VPN Express Wizard - Configuration
Click Next to continue the wizard.
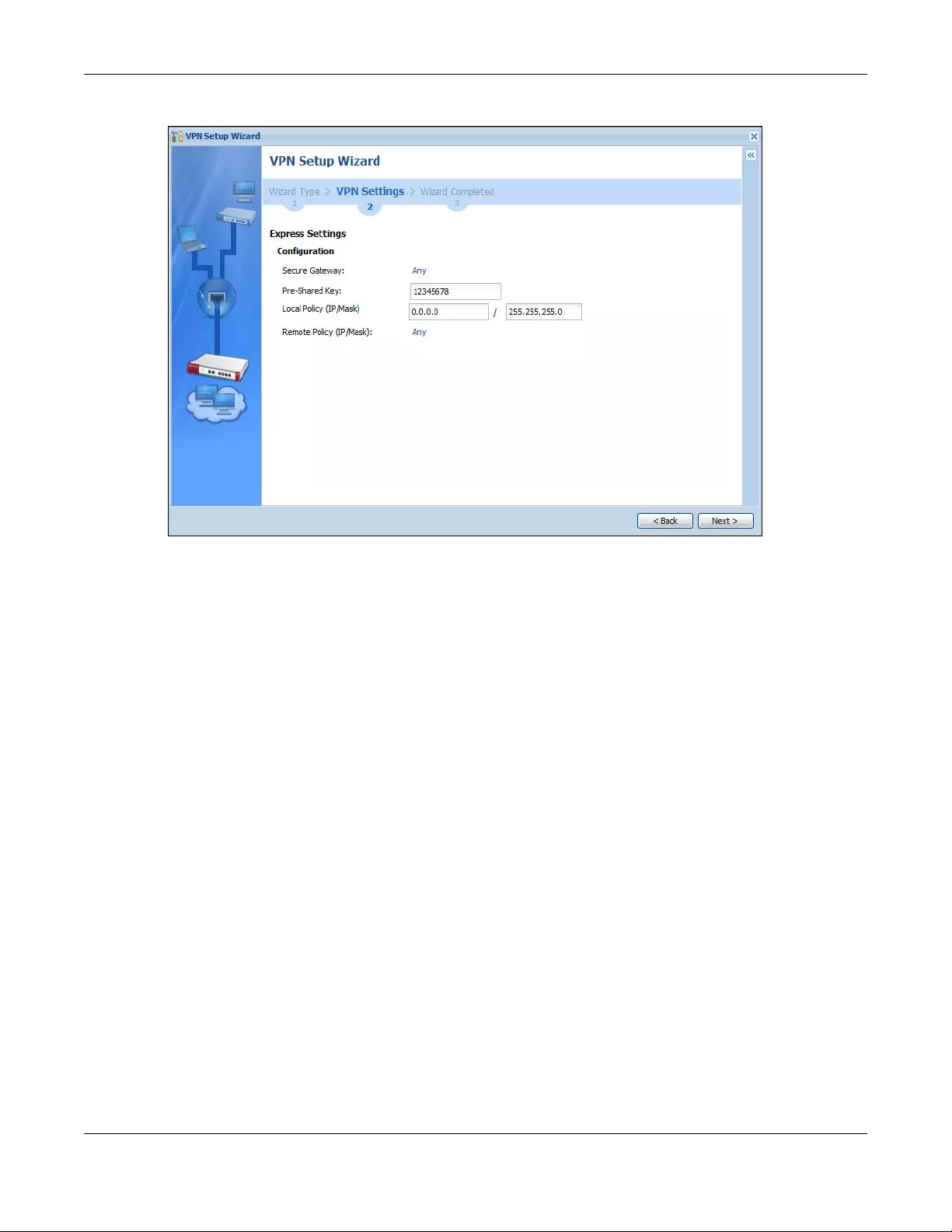
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
109
Figure 85 VPN for Configuration Provisioning Express Wizard: Configuration
•Secure Gateway: Any displays in this field because it is not configurable in this wizard. It allows
incoming connections from the Zyxel Device IPSec VPN Client.
•Pre-Shared Key: Type the password. Both ends of the VPN tunnel must use the same password. Use 8
to 31 case-sensitive ASCII characters or 8 to 31 pairs of hexadecimal (“0-9”, “A-F”) characters.
Proceed a hexadecimal key with “0x”. You will receive a PYLD_MALFORMED (payload malformed)
packet if the same pre-shared key is not used on both ends.
•Local Policy (IP/Mask): Type the IP address of a computer on your network. You can also specify a
subnet. This must match the remote IP address configured on the remote IPSec device.
•Remote Policy (IP/Mask): Any displays in this field because it is not configurable in this wizard.
4.7.3 VPN Settings for Configuration Provisioning Express Wizard - Summary
This screen has a read-only summary of the VPN tunnel’s configuration and commands you can copy
and paste into another ZLD-based Zyxel Device’s command line interface to configure it.
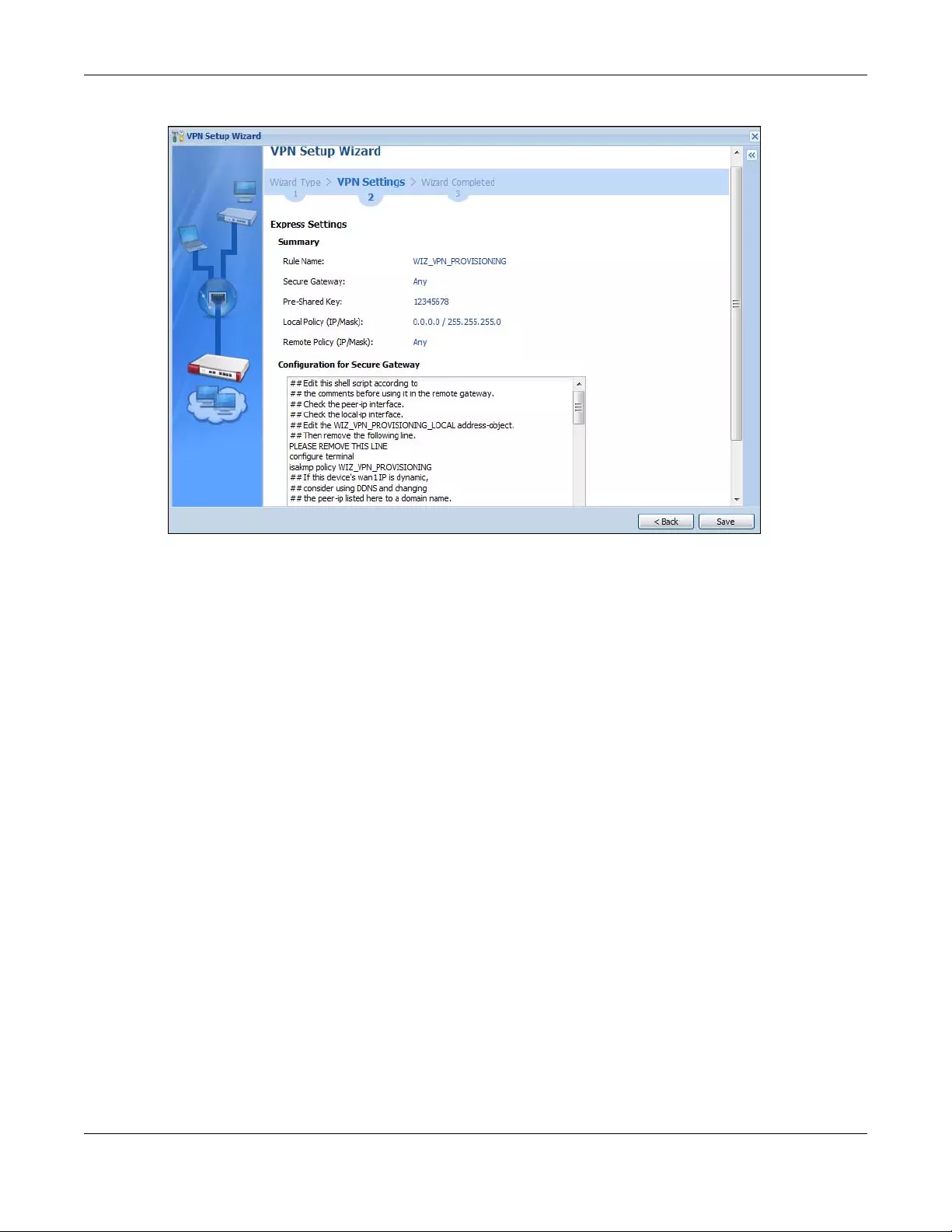
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
110
Figure 86 VPN for Configuration Provisioning Express Wizard: Summary
•Rule Name: Identifies the VPN gateway policy.
•Secure Gateway: Any displays in this field because it is not configurable in this wizard. It allows
incoming connections from the Zyxel Device IPSec VPN Client.
•Pre-Shared Key: VPN tunnel password. It identifies a communicating party during a phase 1 IKE
negotiation.
•Local Policy: (Static) IP address and subnet mask of the computers on the network behind your Zyxel
Device that can be accessed using the tunnel.
•Remote Policy: Any displays in this field because it is not configurable in this wizard.
• The Configuration for Secure Gateway displays the configuration that the Zyxel Device IPSec VPN
Client will get from the Zyxel Device.
• Click Save to save the VPN rule.
4.7.4 VPN Settings for Configuration Provisioning Express Wizard - Finish
Now the rule is configured on the Zyxel Device. The Phase 1 rule settings appear in the VPN > IPSec VPN
> VPN Gateway screen and the Phase 2 rule settings appear in the VPN > IPSec VPN > VPN Connection
screen. Enter the IP address of the Zyxel Device in the Zyxel Device IPSec VPN Client to get all these VPN
settings automatically from the Zyxel Device.
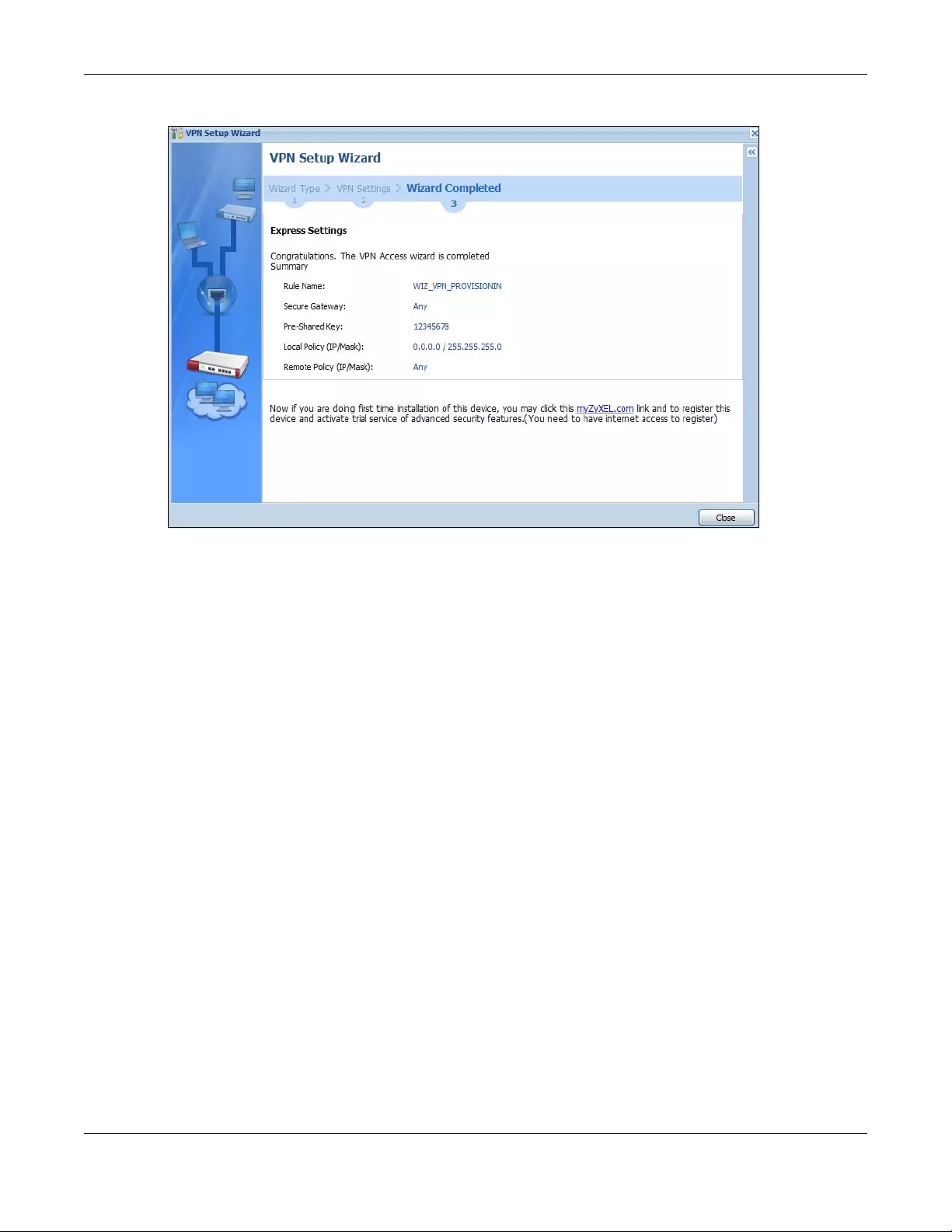
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
111
Figure 87 VPN for Configuration Provisioning Express Wizard: Finish
Click Close to exit the wizard.
4.7.5 VPN Settings for Configuration Provisioning Advanced Wizard -
Scenario
Click the Advanced radio button as shown in the screen shown in Figure 83 on page 107 to display the
following screen.
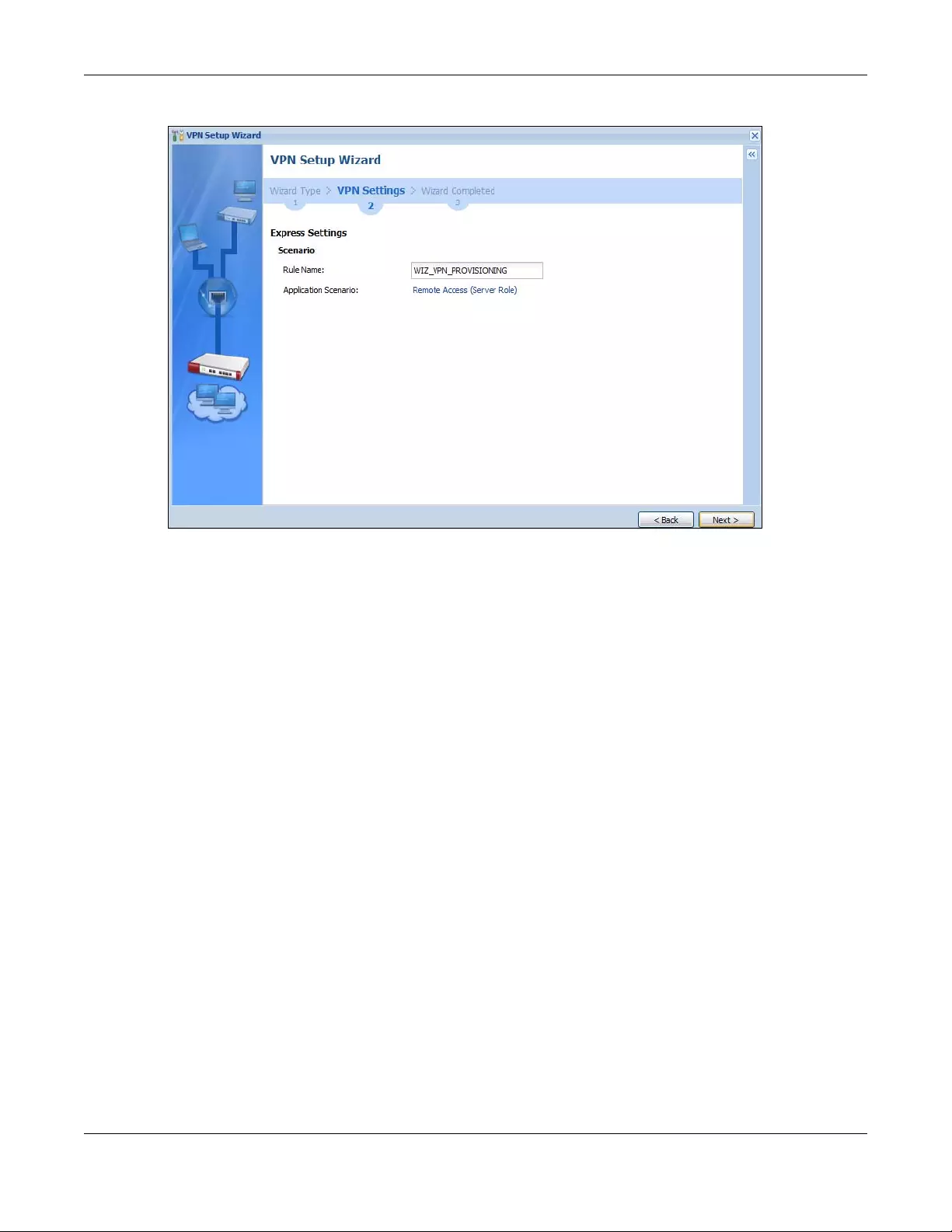
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
112
Figure 88 VPN for Configuration Provisioning Advanced Wizard: Scenario Settings
Rule Name: Type the name used to identify this VPN connection (and VPN gateway). You may use 1-31
alphanumeric characters, underscores (_), or dashes (-), but the first character cannot be a number.
This value is case-sensitive.
Application Scenario: Only the Remote Access (Server Role) is allowed in this wizard. It allows incoming
connections from the Zyxel Device IPSec VPN Client.
Click Next to continue the wizard.
4.7.6 VPN Settings for Configuration Provisioning Advanced Wizard - Phase
1 Settings
There are two phases to every IKE (Internet Key Exchange) negotiation – phase 1 (Authentication) and
phase 2 (Key Exchange). A phase 1 exchange establishes an IKE SA (Security Association).
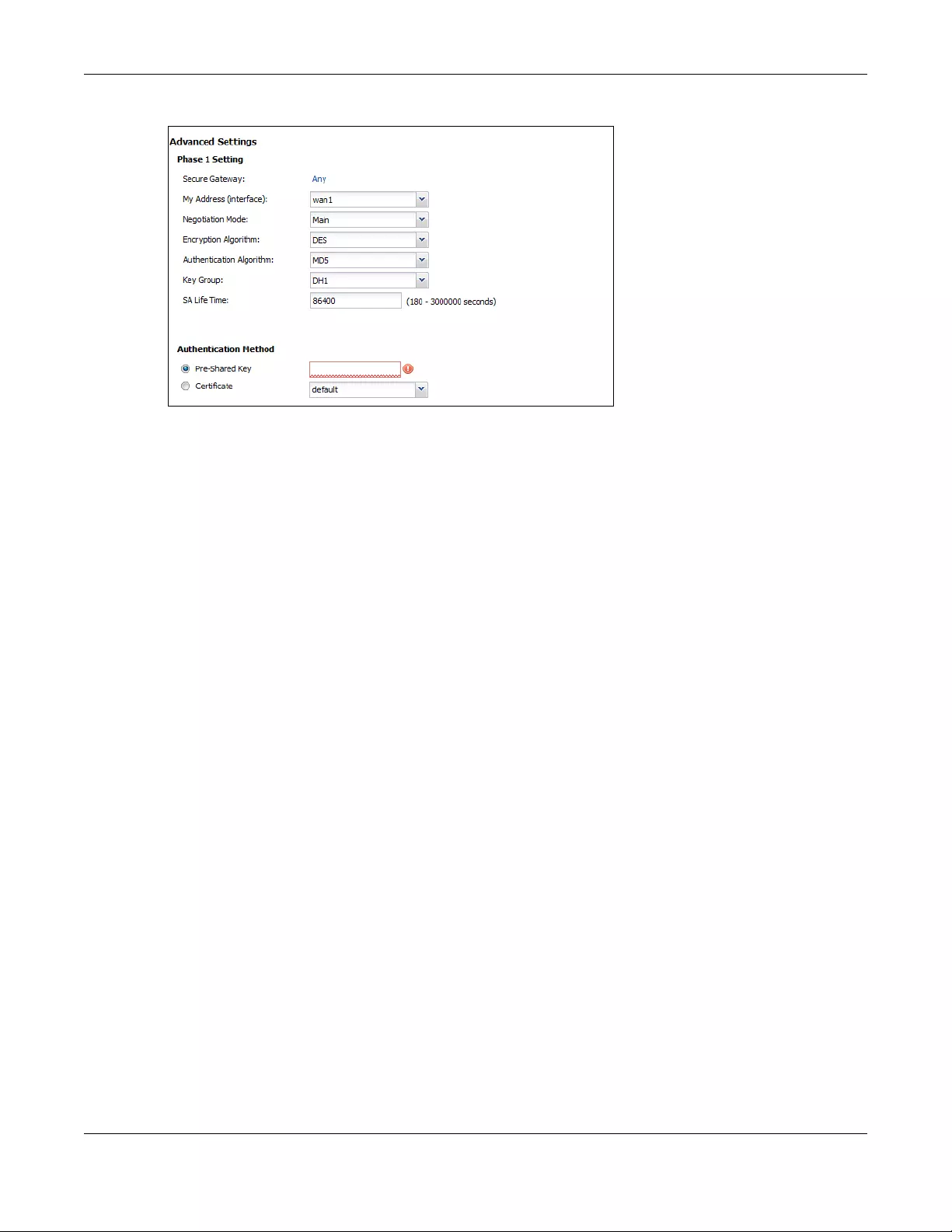
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
113
Figure 89 VPN for Configuration Provisioning Advanced Wizard: Phase 1 Settings
•Secure Gateway: Any displays in this field because it is not configurable in this wizard. It allows
incoming connections from the Zyxel Device IPSec VPN Client.
•My Address (interface): Select an interface from the drop-down list box to use on your Zyxel Device.
•Negotiation Mode: This displays Main or Aggressive:
•Main encrypts the ZyWALL/USG’s and remote IPSec router’s identities but takes more time to
establish the IKE SA
•Aggressive is faster but does not encrypt the identities.
The ZyWALL/USG and the remote IPSec router must use the same negotiation mode. Multiple SAs
connecting through a secure gateway must have the same negotiation mode.
•Encryption Algorithm: 3DES and AES use encryption. The longer the key, the higher the security (this
may affect throughput). Both sender and receiver must know the same secret key, which can be
used to encrypt and decrypt the message or to generate and verify a message authentication code.
The DES encryption algorithm uses a 56-bit key. Triple DES (3DES) is a variation on DES that uses a 168-
bit key. As a result, 3DES is more secure than DES. It also requires more processing power, resulting in
increased latency and decreased throughput. AES128 uses a 128-bit key and is faster than 3DES.
AES192 uses a 192-bit key and AES256 uses a 256-bit key.
•Authentication Algorithm: MD5 (Message Digest 5) and SHA (Secure Hash Algorithm) are hash
algorithms used to authenticate packet data. MD5 gives minimal security. SHA1 gives higher security
and SHA256 gives the highest security. The stronger the algorithm, the slower it is.
•Key Group: DH5 is more secure than DH1 or DH2 (although it may affect throughput). DH1 (default)
refers to Diffie-Hellman Group 1 a 768 bit random number. DH2 refers to Diffie-Hellman Group 2 a 1024
bit (1Kb) random number. DH5 refers to Diffie-Hellman Group 5 a 1536 bit random number.
•SA Life Time: Set how often the Zyxel Device renegotiates the IKE SA. A short SA life time increases
security, but renegotiation temporarily disconnects the VPN tunnel.
•Authentication Method: Select Pre-Shared Key to use a password or Certificate to use one of the Zyxel
Device’s certificates.
4.7.7 VPN Settings for Configuration Provisioning Advanced Wizard - Phase
2
Phase 2 in an IKE uses the SA that was established in phase 1 to negotiate SAs for IPSec.
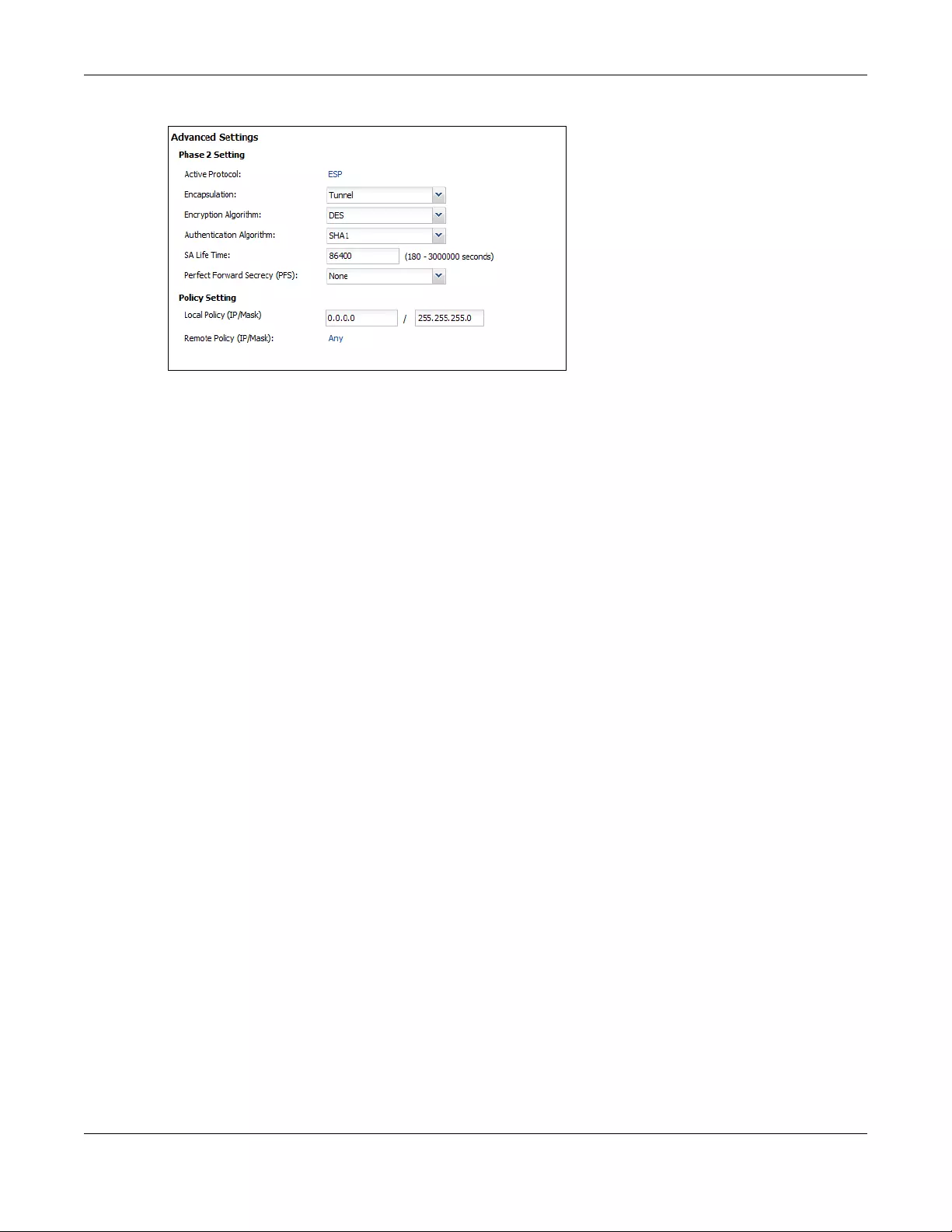
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
114
Figure 90 VPN for Configuration Provisioning Advanced Wizard: Phase 2 Settings
•Active Protocol: ESP is compatible with NAT. AH is not available in this wizard.
•Encapsulation: Tunnel is compatible with NAT, Transport is not.
•Encryption Algorithm: 3DES and AES use encryption. The longer the AES key, the higher the security
(this may affect throughput). Null uses no encryption.
•Authentication Algorithm: MD5 (Message Digest 5) and SHA (Secure Hash Algorithm) are hash
algorithms used to authenticate packet data. MD5 gives minimal security. SHA1 gives higher security
and SHA256 gives the highest security. The stronger the algorithm, the slower it is.
•SA Life Time: Set how often the Zyxel Device renegotiates the IKE SA. A short SA life time increases
security, but renegotiation temporarily disconnects the VPN tunnel.
•Perfect Forward Secrecy (PFS): Disabling PFS allows faster IPSec setup, but is less secure. Select DH1,
DH2 or DH5 to enable PFS. DH5 is more secure than DH1 or DH2 (although it may affect throughput).
DH1 refers to Diffie-Hellman Group 1 a 768 bit random number. DH2 refers to Diffie-Hellman Group 2 a
1024 bit (1Kb) random number. DH5 refers to Diffie-Hellman Group 5 a 1536 bit random number (more
secure, yet slower).
•Local Policy (IP/Mask): Type the IP address of a computer on your network. You can also specify a
subnet. This must match the remote IP address configured on the remote IPSec device.
•Remote Policy (IP/Mask): Any displays in this field because it is not configurable in this wizard.
•Nailed-Up: This displays for the site-to-site and remote access client role scenarios. Select this to have
the Zyxel Device automatically renegotiate the IPSec SA when the SA life time expires.
4.7.8 VPN Settings for Configuration Provisioning Advanced Wizard -
Summary
This is a read-only summary of the VPN tunnel settings.
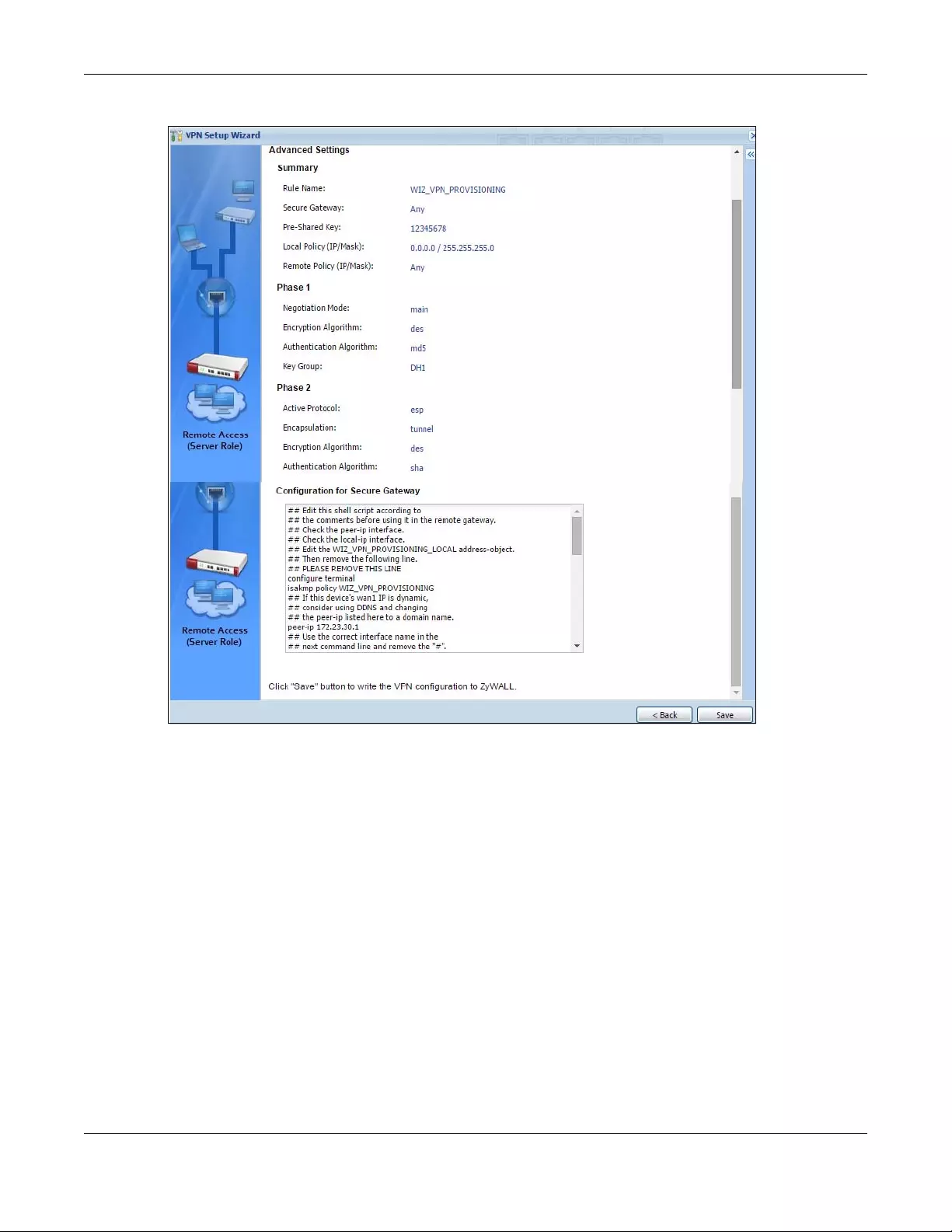
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
115
Figure 91 VPN for Configuration Provisioning Advanced Wizard: Summary
Summary
•Rule Name: Identifies the VPN connection (and the VPN gateway).
•Secure Gateway: Any displays in this field because it is not configurable in this wizard. It allows
incoming connections from the Zyxel Device IPSec VPN Client.
•Pre-Shared Key: VPN tunnel password.
•Local Policy: IP address and subnet mask of the computers on the network behind your Zyxel Device
that can use the tunnel.
•Remote Policy: Any displays in this field because it is not configurable in this wizard.
Phase 1
•Negotiation Mode: This displays Main or Aggressive:
•Main encrypts the ZyWALL/USG’s and remote IPSec router’s identities but takes more time to
establish the IKE SA
•Aggressive is faster but does not encrypt the identities.
The ZyWALL/USG and the remote IPSec router must use the same negotiation mode. Multiple SAs
connecting through a secure gateway must have the same negotiation mode.

Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
116
•Encryption Algorithm: This displays the encryption method used. The longer the key, the higher the
security, the lower the throughput (possibly).
•DES uses a 56-bit key.
•3DES uses a 168-bit key.
•AES128 uses a 128-bit key
•AES192 uses a 192-bit key
•AES256 uses a 256-bit key.
•Authentication Algorithm: This displays the authentication algorithm used. The stronger the algorithm,
the slower it is.
•MD5 gives minimal security.
•SHA1 gives higher security
•SHA256 gives the highest security.
•Key Group: This displays the Diffie-Hellman (DH) key group used. DH5 is more secure than DH1 or DH2
(although it may affect throughput).
•DH1 uses a 768 bit random number.
•DH2 uses a 1024 bit (1Kb) random number.
•DH5 uses a 1536 bit random number.
Phase 2
•Active Protocol: This displays ESP (compatible with NAT) or AH.
•Encapsulation: This displays Tunnel (compatible with NAT) or Transport.
•Encryption Algorithm: This displays the encryption method used. The longer the key, the higher the
security, the lower the throughput (possibly).
•DES uses a 56-bit key.
•3DES uses a 168-bit key.
•AES128 uses a 128-bit key
•AES192 uses a 192-bit key
•AES256 uses a 256-bit key.
•Null uses no encryption.
•Authentication Algorithm: This displays the authentication algorithm used. The stronger the algorithm,
the slower it is.
•MD5 gives minimal security.
•SHA1 gives higher security
•SHA256 gives the highest security.
The Configuration for Secure Gateway displays the configuration that the Zyxel Device IPSec VPN Client
will get from the Zyxel Device.
Click Save to save the VPN rule.
4.7.9 VPN Settings for Configuration Provisioning Advanced Wizard- Finish
Now the rule is configured on the Zyxel Device. The Phase 1 rule settings appear in the VPN > IPSec VPN
> VPN Gateway screen and the Phase 2 rule settings appear in the VPN > IPSec VPN > VPN Connection
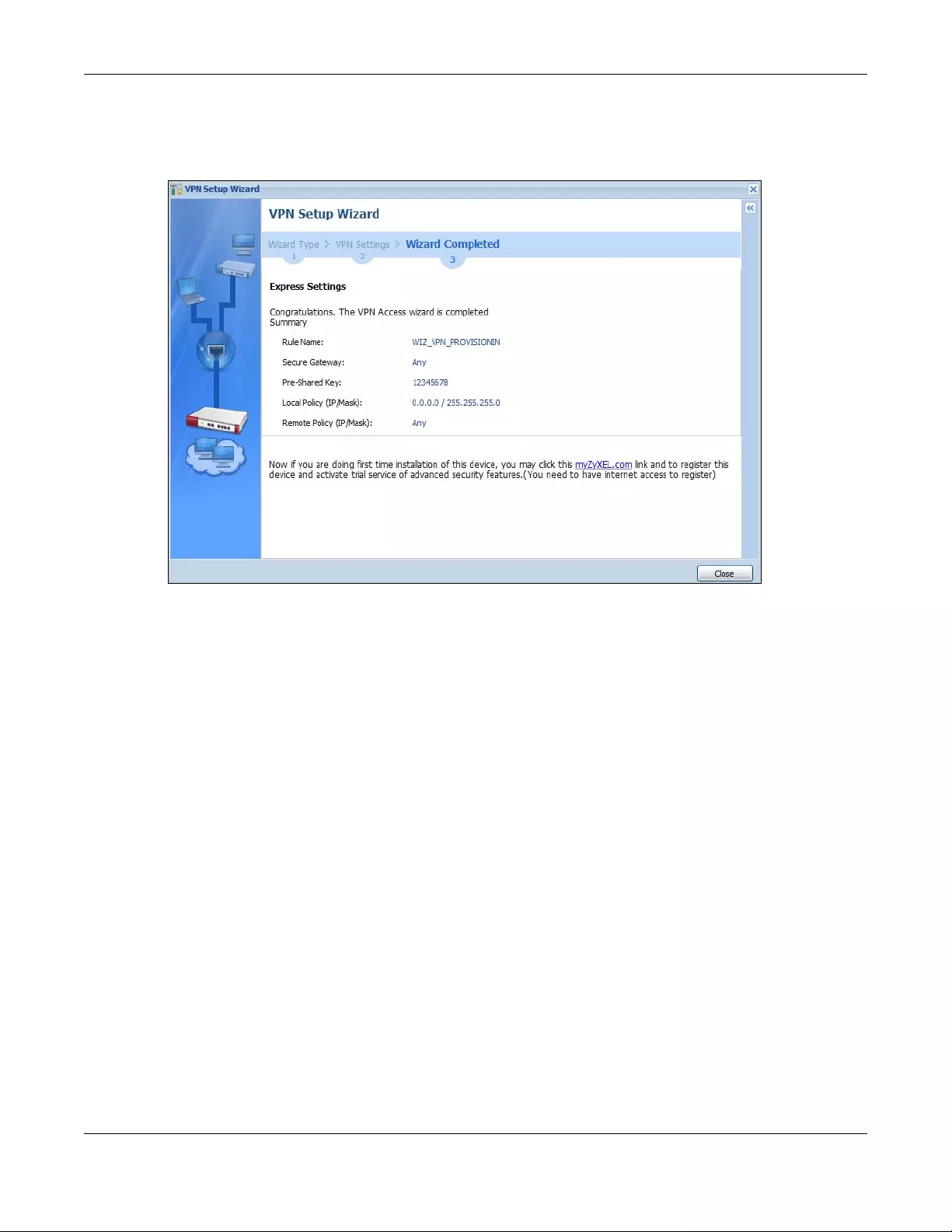
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
117
screen. Enter the IP address of the Zyxel Device in the Zyxel Device IPSec VPN Client to get all these VPN
settings automatically from the Zyxel Device.
Figure 92 VPN for Configuration Provisioning Advanced Wizard: Finish
Click Close to exit the wizard.
4.8 VPN Settings for L2TP VPN Settings Wizard
Use VPN Settings for L2TP VPN Settings to set up an L2TP VPN rule. Click Configuration > Quick Setup >
VPN Settings and select VPN Settings for L2TP VPN Settings to see the following screen.
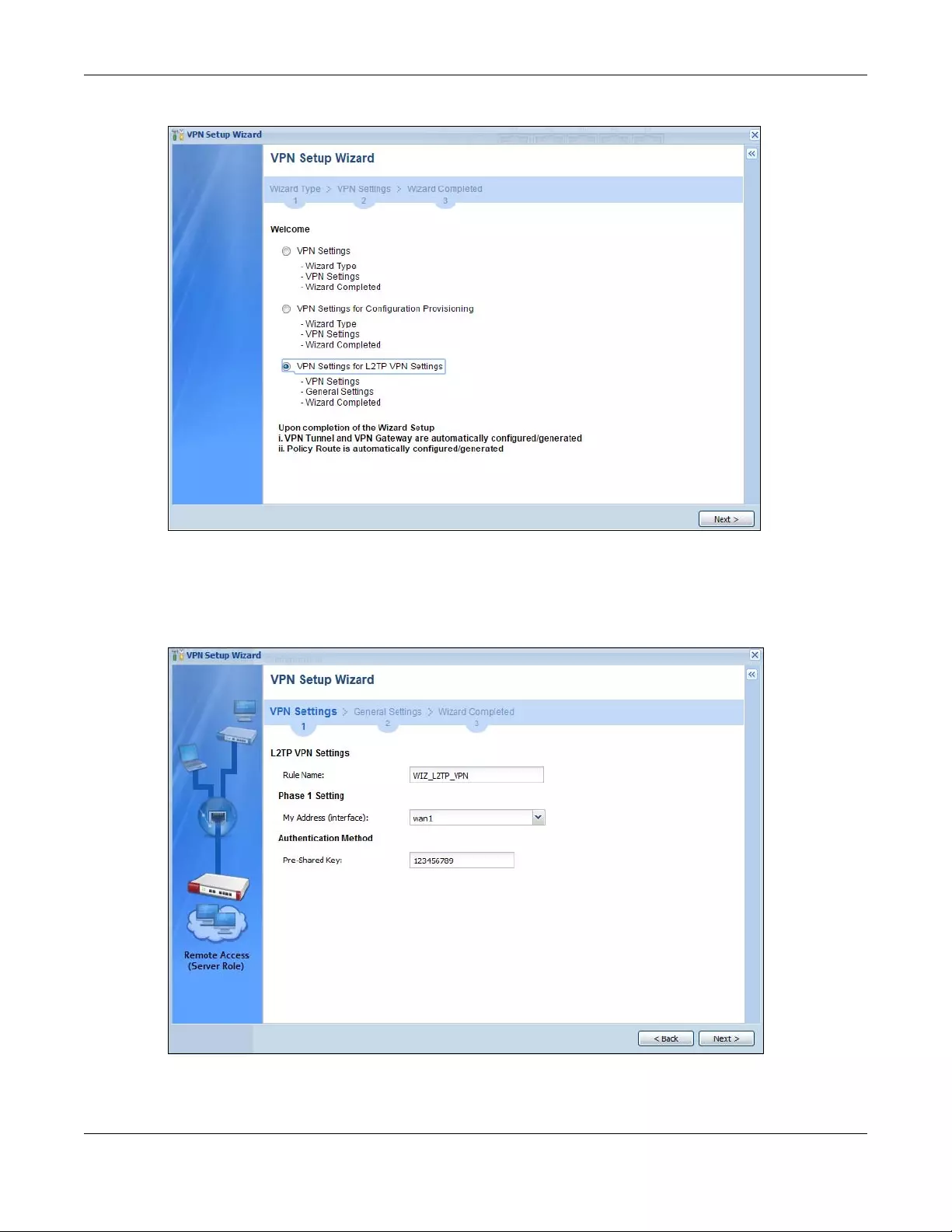
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
118
Figure 93 VPN Settings for L2TP VPN Settings Wizard: L2TP VPN Settings
Click Next to continue the wizard.
4.8.1 L2TP VPN Settings 1
Figure 94 VPN Settings for L2TP VPN Settings Wizard: L2TP VPN Settings
•Rule Name: Type the name used to identify this L2TP VPN connection (and L2TP VPN gateway). You
may use 1-31 alphanumeric characters, underscores (_), or dashes (-), but the first character cannot
be a number. This value is case-sensitive.
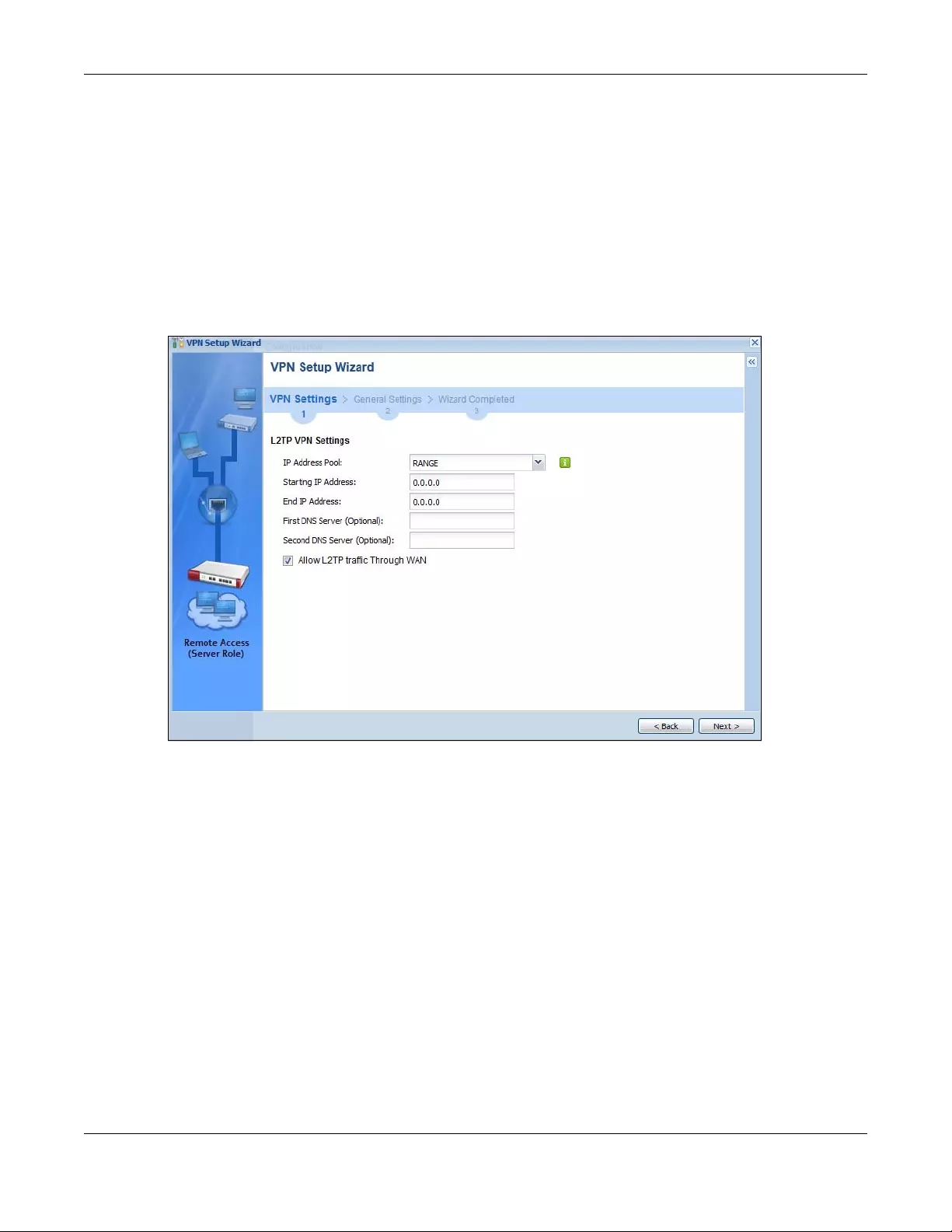
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
119
•My Address (interface): Select one of the interfaces from the pull down menu to apply the L2TP VPN
rule.
•Pre-Shared Key: Type the password. Both ends of the VPN tunnel must use the same password. Use 8
to 31 case-sensitive ASCII characters or 8 to 31 pairs of hexadecimal (“0-9”, “A-F”) characters.
Proceed a hexadecimal key with “0x”. You will receive a PYLD_MALFORMED (payload malformed)
packet if the same pre-shared key is not used on both ends.
Click Next to continue the wizard.
4.8.2 L2TP VPN Settings 2
Figure 95 VPN Settings for L2TP VPN Settings Wizard: L2TP VPN Settings
•IP Address Pool: Select Range or Subnet from the pull down menu. This IP address pool is used to
assign to the L2TP VPN clients.
•Starting IP Address: Enter the starting IP address in the field.
•End IP Address: Enter the ending IP address in the field.
•First DNS Server (Optional): Enter the first DNS server IP address in the field. Leave the filed as 0.0.0.0 if
you do not want to configure DNS servers. If you do not configure a DNS server you must know the IP
address of a machine in order to access it.
•Second DNS Server (Optional): Enter the second DNS server IP address in the field. Leave the filed as
0.0.0.0 if you do not want to configure DNS servers. If you do not configure a DNS server you must
know the IP address of a machine in order to access it.
•Allow L2TP traffic Through WAN: Select this check box to allow traffic from L2TP clients to go to the
Internet.
Click Next to continue the wizard.
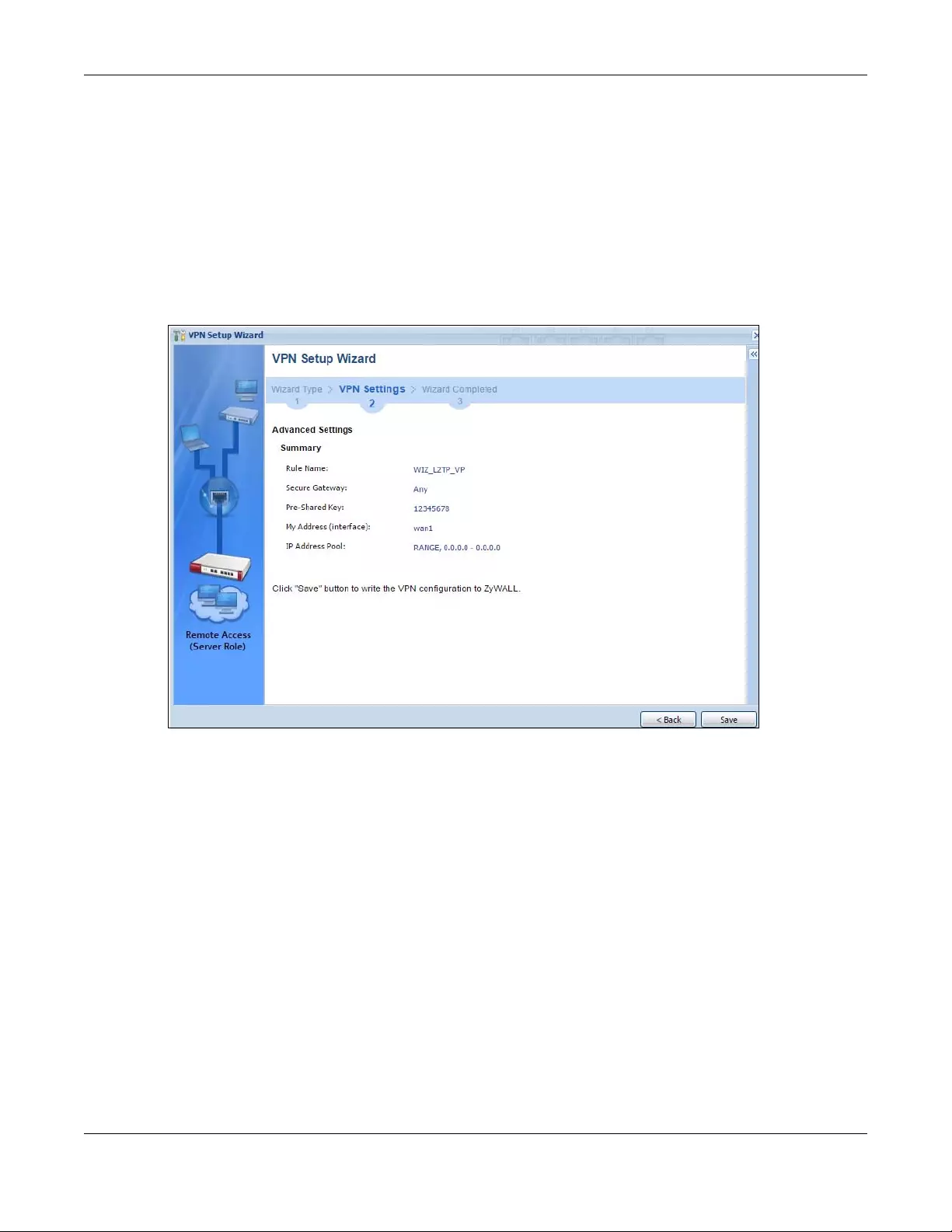
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
120
Note: DNS (Domain Name System) is for mapping a domain name to its corresponding IP
address and vice versa. The DNS server is extremely important because without it, you
must know the IP address of a computer before you can access it. The Zyxel Device
uses a system DNS server (in the order you specify here) to resolve domain names for
VPN, DDNS and the time server.
4.8.3 VPN Settings for L2TP VPN Setting Wizard - Summary
This is a read-only summary of the L2TP VPN settings.
Figure 96 VPN Settings for L2TP VPN Settings Advanced Settings Wizard: Summary
Summary
•Rule Name: Identifies the L2TP VPN connection (and the L2TP VPN gateway).
•Secure Gateway “Any” displays in this field because it is not configurable in this wizard. It allows
incoming connections from the L2TP VPN Client.
•Pre-Shared Key: L2TP VPN tunnel password.
•My Address (Interface): This displays the interface to use on your Zyxel Device for the L2TP tunnel.
•IP Address Pool: This displays the IP address pool used to assign to the L2TP VPN clients.
Click Save to complete the L2TP VPN Setting and the following screen will show.
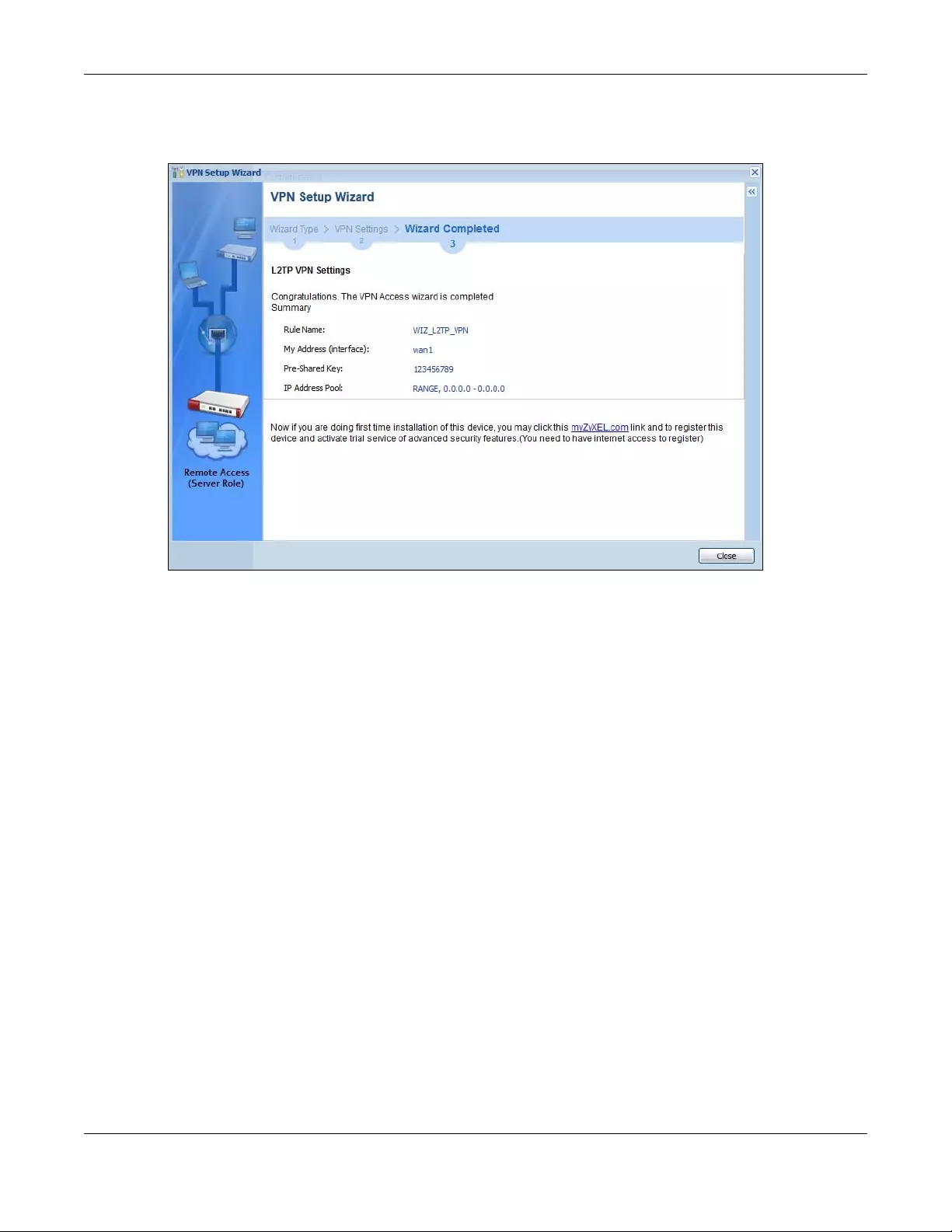
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
121
4.8.4 VPN Settings for L2TP VPN Setting Wizard Completed
Figure 97 VPN Settings for L2TP VPN Settings Wizard: Finish
Now the rule is configured on the Zyxel Device. The L2TP VPN rule settings appear in the VPN > L2TP VPN
screen and also in the VPN > IPSec VPN > VPN Connection and VPN Gateway screen.
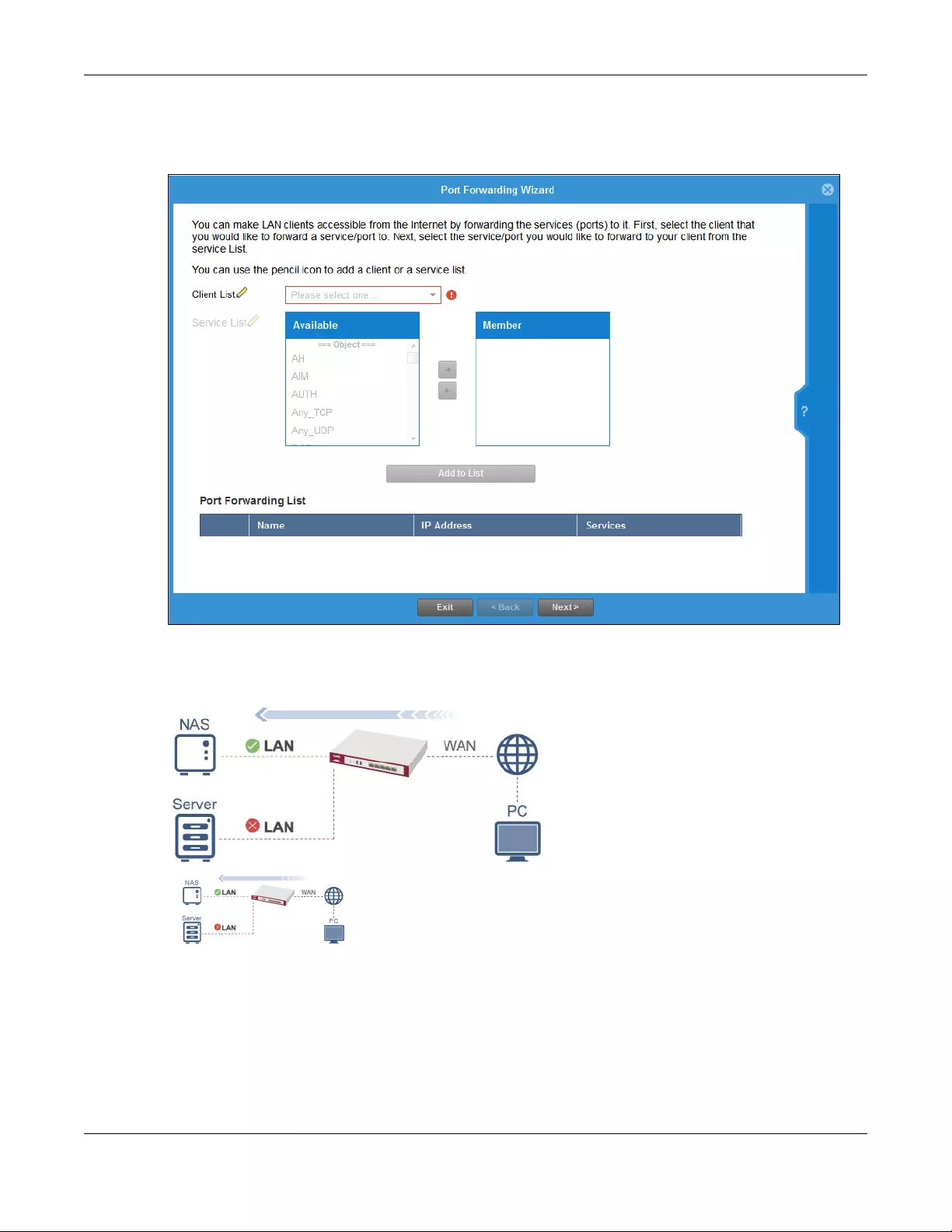
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
122
4.9 Port Forwarding
Figure 98 Port Forwarding > Wizard 1
NAT port forwarding allows the Zyxel Device to direct incoming traffic from the Internet to the correct
virtual server in your network. Even though the NAS is in your local network receiving the protection of
the Zyxel Device, you can still access that NAS using these services from anywhere outside your network.
For example, if you have a NAS server in your network that you or other people need access to from
outside your network, select the IP address of the NAS from Client. Then, select the service(s) that your
NAS provides (for example FTP, HTTP, HTTPS) from the Available box and use the right arrow to move
each service to the Member box.
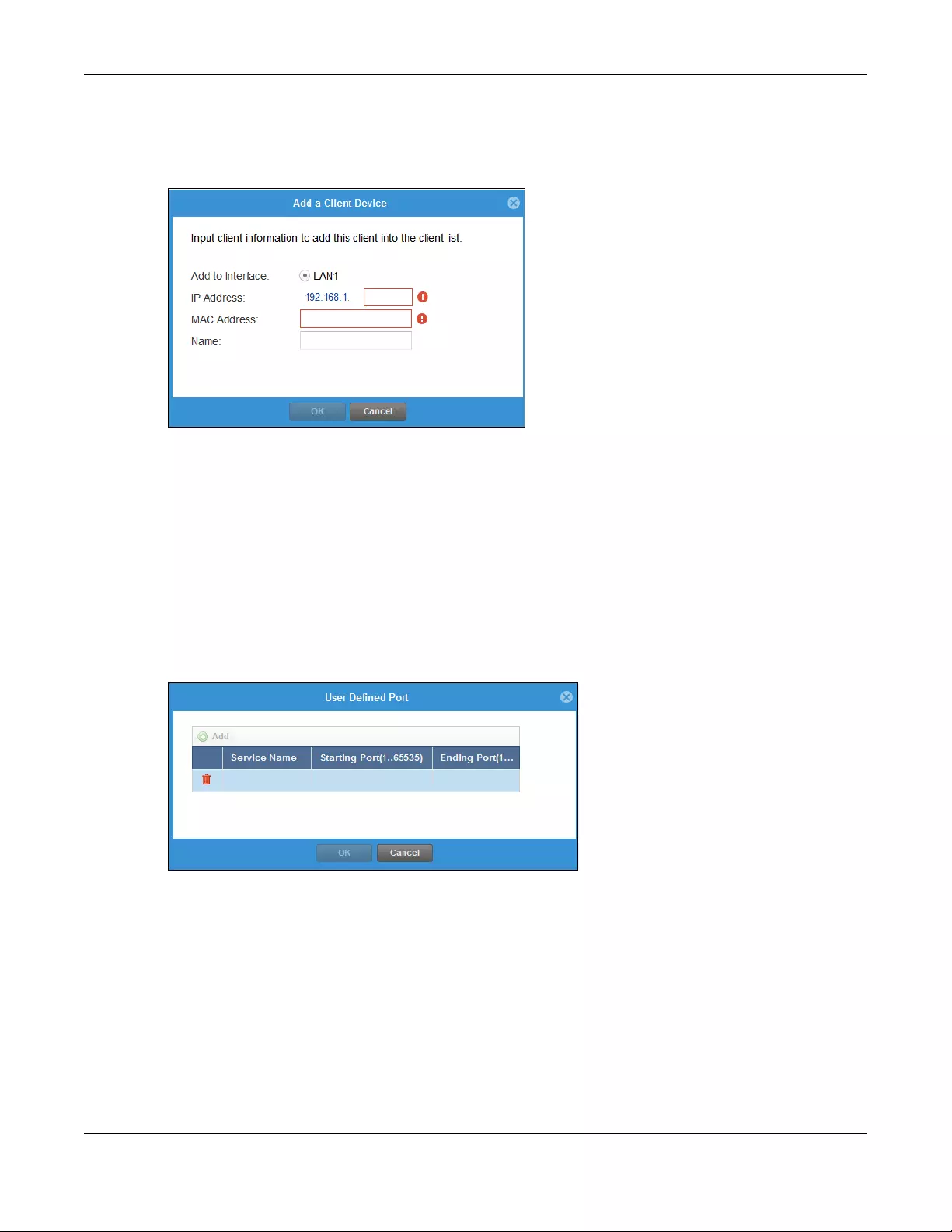
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
123
4.9.1 Port Fo rwarding > Add Client
Click the Edit icon next to Client List if you cannot see the client in the list. In the pop-up screen, you can
add a new client by entering its Name, IP Address and MAC Address.
A client or device in your network acting as a server for forwarded services (for example, the NAS) needs
to have a static address. If the client selected does not have a static IP address, the IP address may
change when the client reboots, so the Zyxel Device may not be able to find it. If this happens, check
for the new IP address of the client. Then add the new IP address by clicking the Edit icon next to Client
List and entering it in the pop-up screen.
4.9.2 Port Fo rwarding > Add Service
Click the Edit icon next to Service List if you cannot see the service in the list. In the pop-up screen, click
Add, then enter the service name and port range that defines the service. For example, if you have a
FileZilla Server in your network, then enter FileZilla Server as the Service Name, 14147 as the Starting Port
and 14147 as the Ending Port.
4.9.3 Port Forwarding > UPnP
The Zyxel Device supports both UPnP (Universal Plug and Play) and NAT-PMP (NAT Port Mapping
Protocol) to permit networking devices to discover each other and connect seamlessly. An enabled-
UPnP or NAT-PMP device can dynamically join a network, obtain an IP address, convey its capabilities
and learn about other devices on the network. If you have a service that requires UPnP or NAT-PMP,
such as a game server, then select Enable UPnP in this screen and click Refresh. All UPnP-enabled or
NAT-PMP-enabled devices may communicate freely with each other without additional configuration.
Do not select Enable UPnP if this is not your intention.
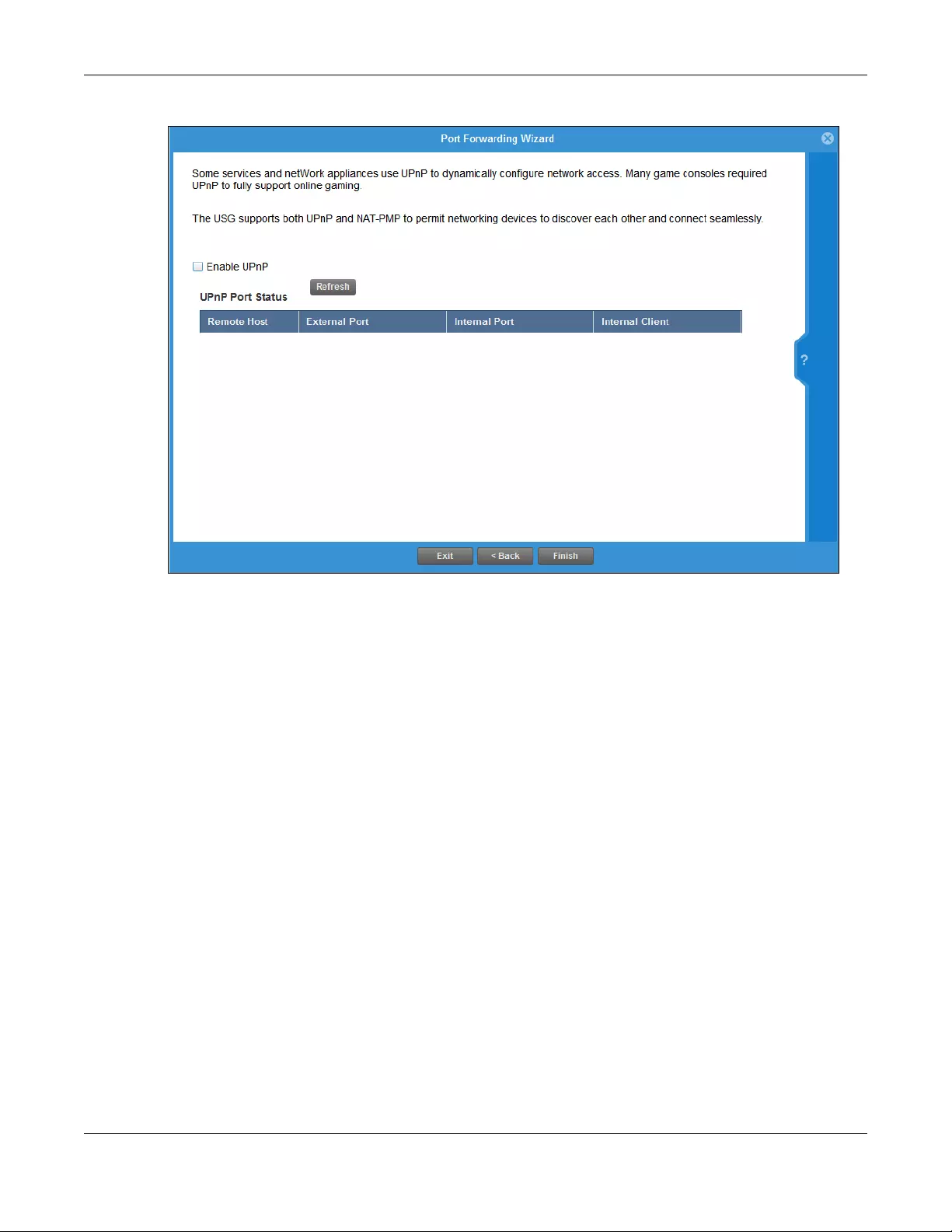
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
124
Click Finish to complete the Port Forwarding Wizard.
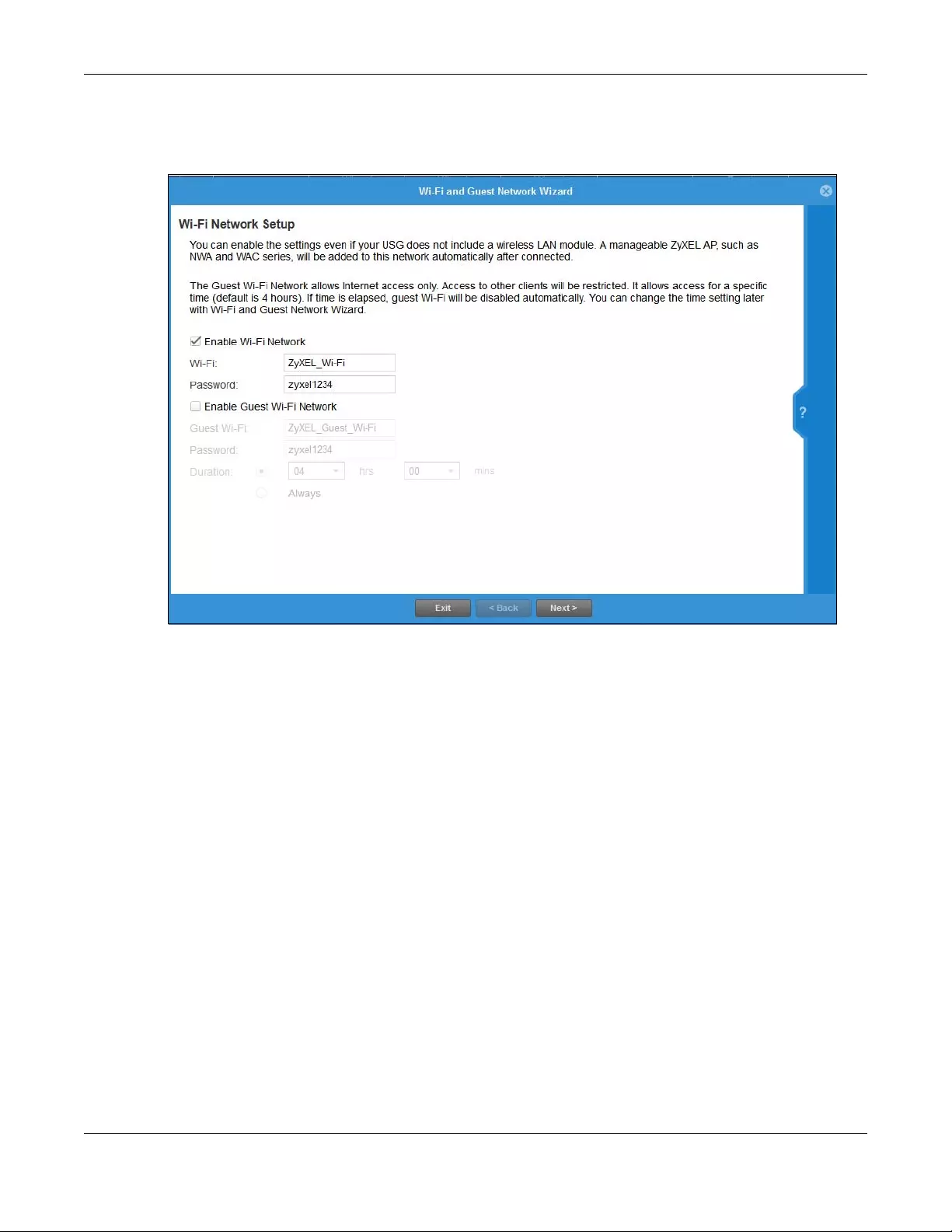
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
125
4.10 Wi-Fi and Guest Network Wizard
Figure 99 Wi-Fi and Guest Network Setup
Select Enable Wi-Fi Network if you want wireless devices to be able to wirelessly access the Zyxel Device
and all resources connected to the Zyxel Device. Configure a descriptive name of from 1 to 32 alpha-
numeric characters, hyphens or underscores (a-z A-Z 0-9 -_) for the wireless network name (Wi-Fi). Set a
Password of between 8 and 63 printable ASCII characters (including spaces and symbols) or 64
hexadecimal characters (0-9 a-f) that wireless users will have to enter for access to the Zyxel Device
wireless network.
Select Enable Guest Wi-Fi Network if you want wireless devices to only be able to wirelessly access the
Internet via the Zyxel Device for up to the period specified in Duration. Configure a descriptive name of
from 1 to 32 alpha-numeric characters, hyphens or underscores (a-z A-Z 0-9 -_) for the wireless network
name (Wi-Fi). Set a Password of between 8 and 63 printable ASCII characters (including spaces and
symbols) or 64 hexadecimal characters (0-9 a-f) that wireless users will have to enter for access to the
Zyxel Device Guest wireless network.
The Guest Wi-Fi Network allows Internet access for up to the period specified in Duration. Wireless users
will have to log in again if the time has elapsed.
The Zyxel Device uses WPA2-PSK with AES encryption so wireless clients must be able to support AES
encryption to wirelessly connect to the Zyxel Device using WPA2-PSK.
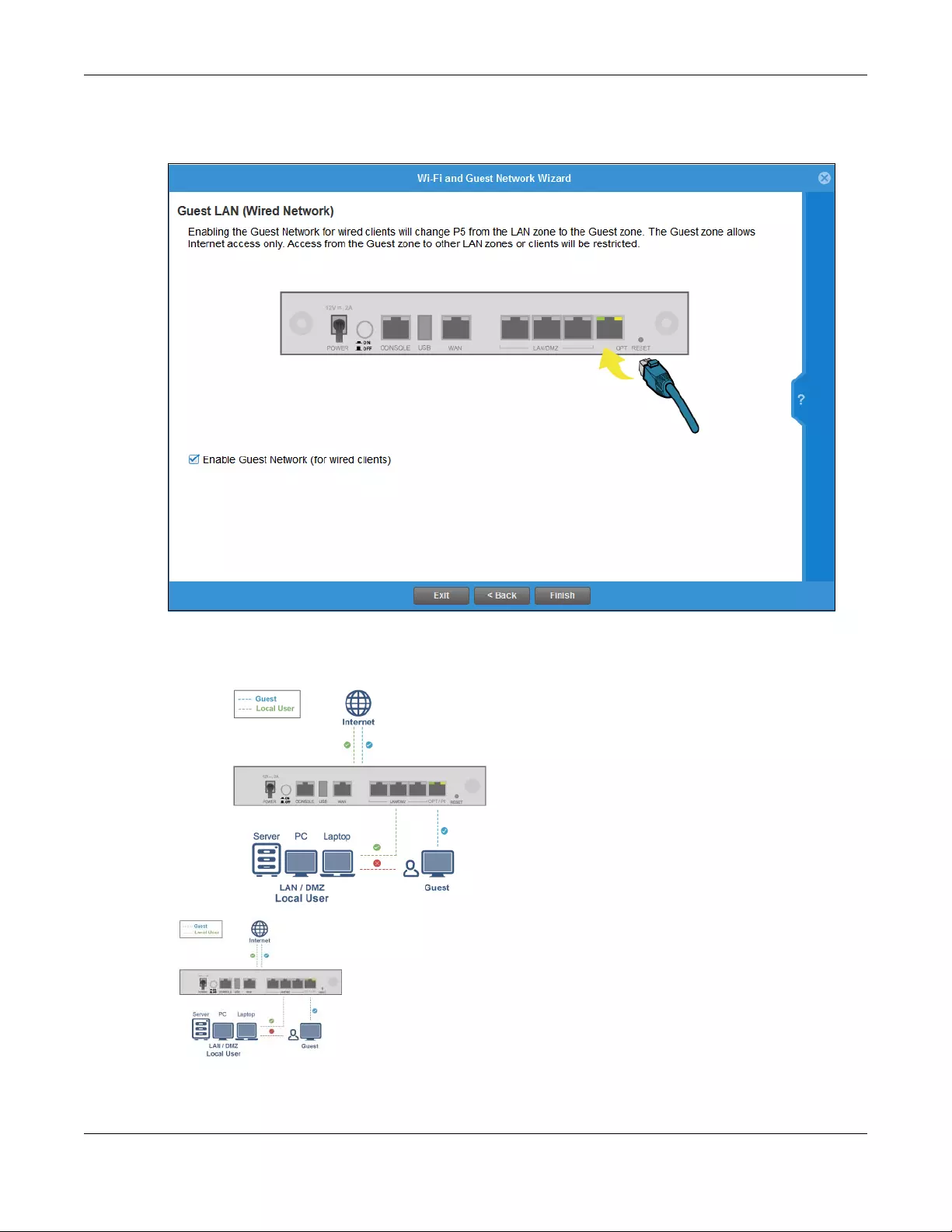
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
126
4.10.1 Guest LAN (Wired Network)
Figure 100 Wi-Fi and Guest Network Setup
Select Enable Guest Network (for wired client s) to convert the OPT or P6 port (depending on your model)
to be a guest port and isolate it from the LAN/DMZ ports. Devices connected to the guest port are
allowed Internet access only and do not have access to networks connected to the other ports.
When the OPT or P6 port is not a guest port, then guest devices connected to that port can communi-
cate with all networks, including devices connected to the LAN/DMZ ports. To avoid this, make sure
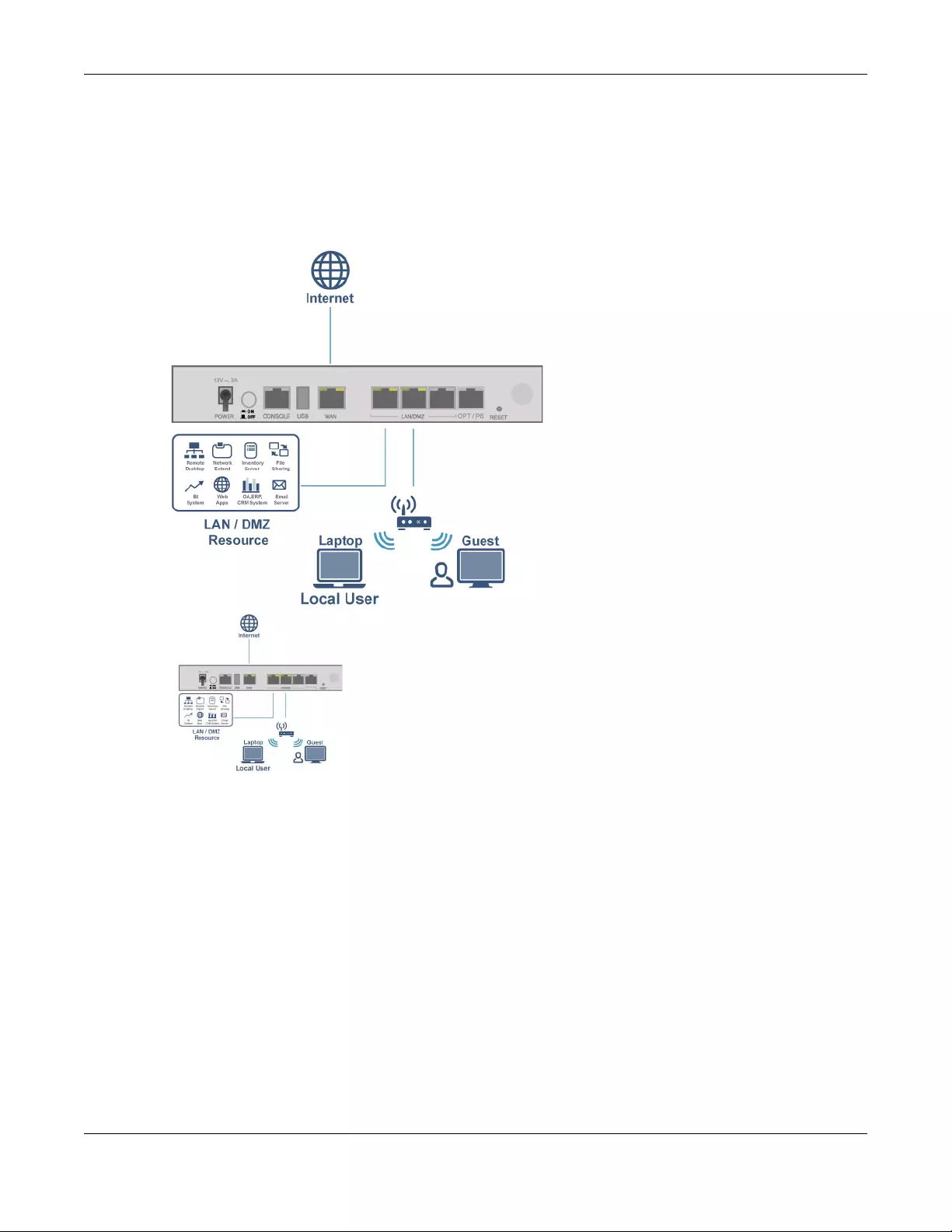
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
127
Enable Guest Network (for wired clients) is selected and that guest devices are only connected to the
OPT or P6 port on the Zyxel Device.
4.10.2 Connecting AP Scenarios
If you connect an AP to a LAN port, then users can use the AP’s SSID to wirelessly access all wired
resources connected to the LAN ports and Internet access.
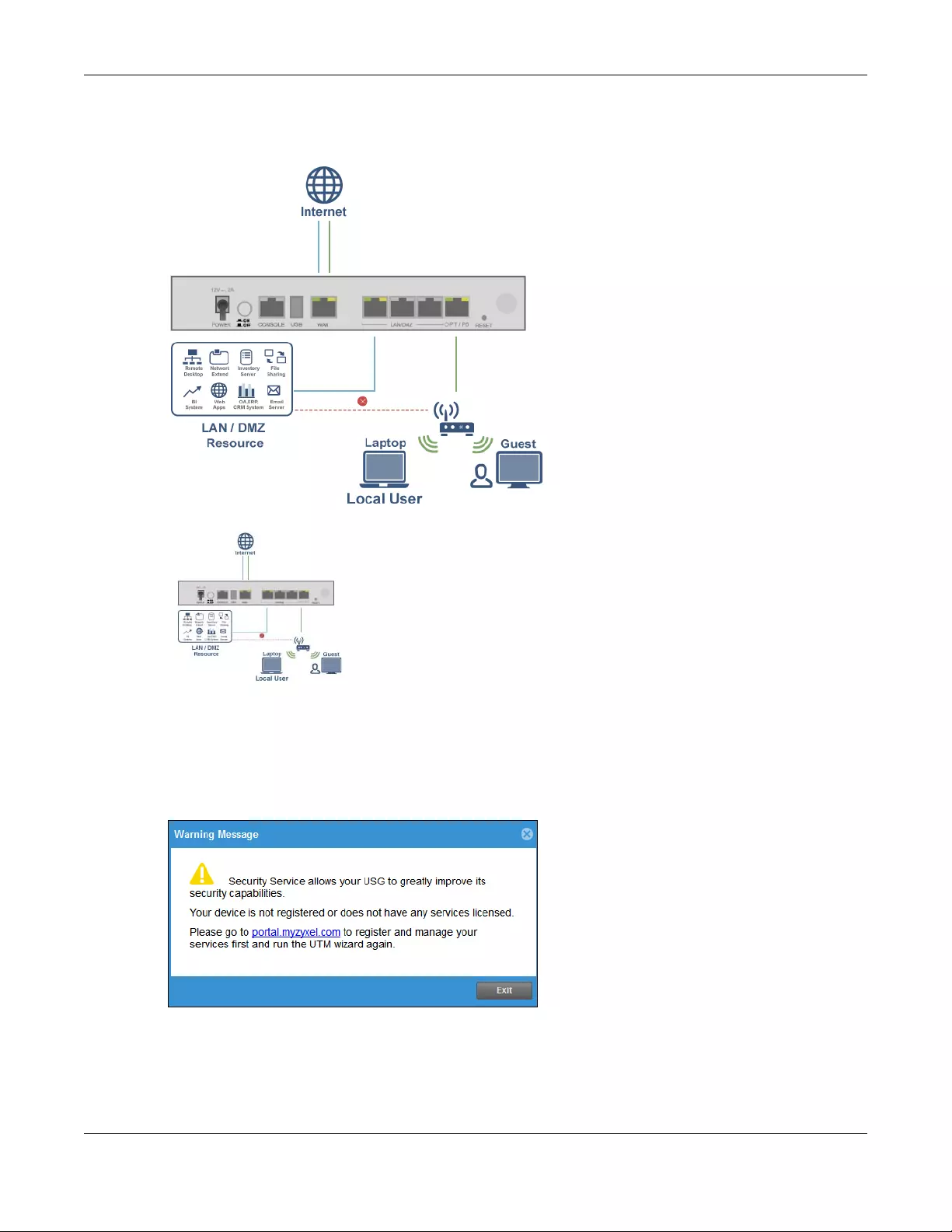
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
128
If you connect an AP to the Guest port, then users can use the AP’s SSID to wirelessly access all wired
resources connected to the Guest port (only) and Internet access. You must select both Enable Guest
Wi-Fi Network and Guest LAN (Wired Network).
4.11 Security Service Wizard
Figure 101 Register First
You must first register the Zyxel Device at portal.myzyxel.com and activate licenses for required services.
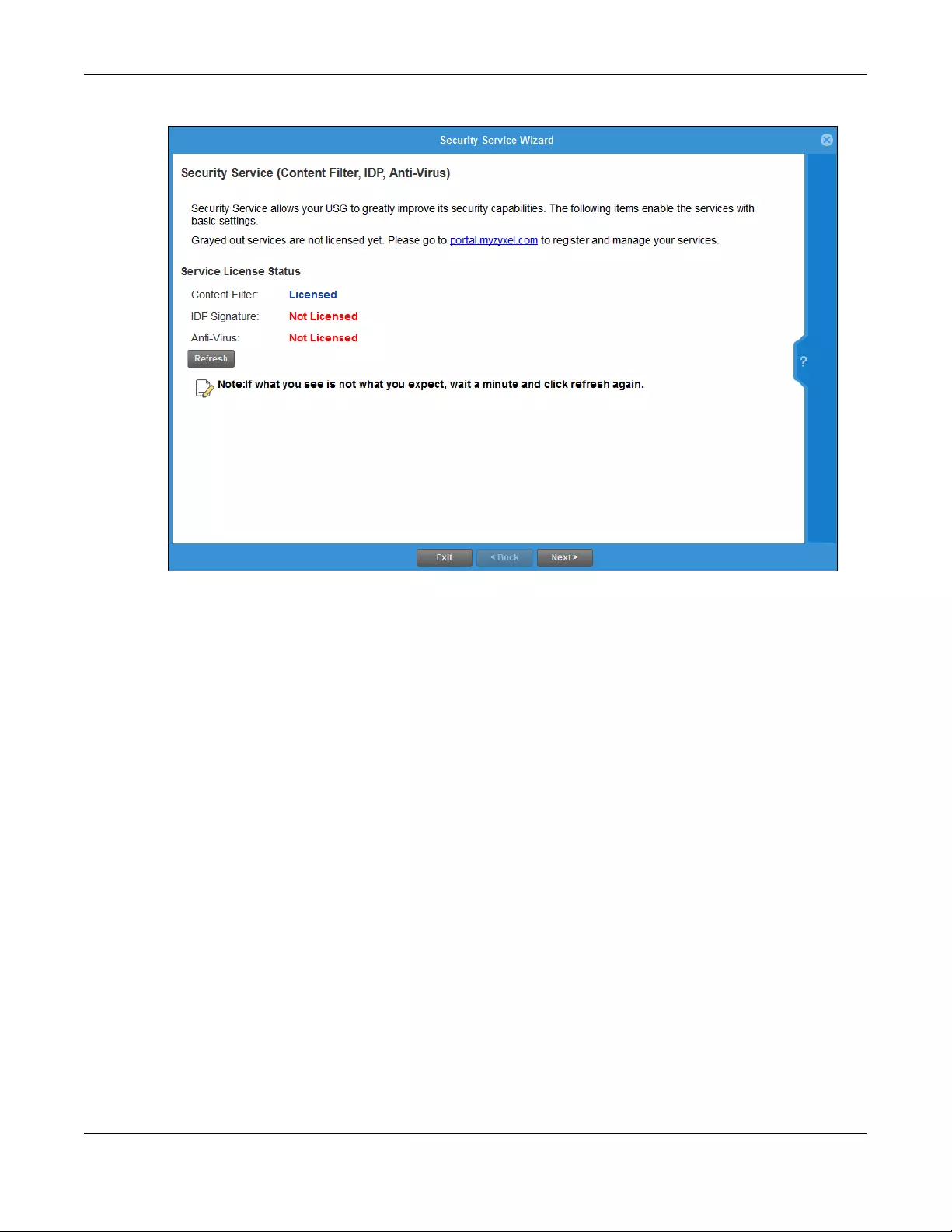
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
129
Figure 102 Security Service Wizard 1 - Service License Status
This screen shows if you have registered your Zyxel Device at portal.myZyxel.com. After you register your
Zyxel Device, you can register for the services supported by your model. For example, some models only
support content filtering.
• Content Filtering (to block websites by category, such as Gambling)
• IDP (to recognize and drop traffic with Intrusion, Detection & Protection attack patterns)
• Anti-Virus (to detect virus patterns in files)
Click Refresh and wait a few moments for the registration information to update in this screen. If the
page does not refresh, make sure the Internet connection is working and click Refresh again. To check
your Internet connection, try to access the Internet from a computer connected to a LAN port on the
Zyxel Device. If you cannot, then check your Internet access settings on the Zyxel Device.
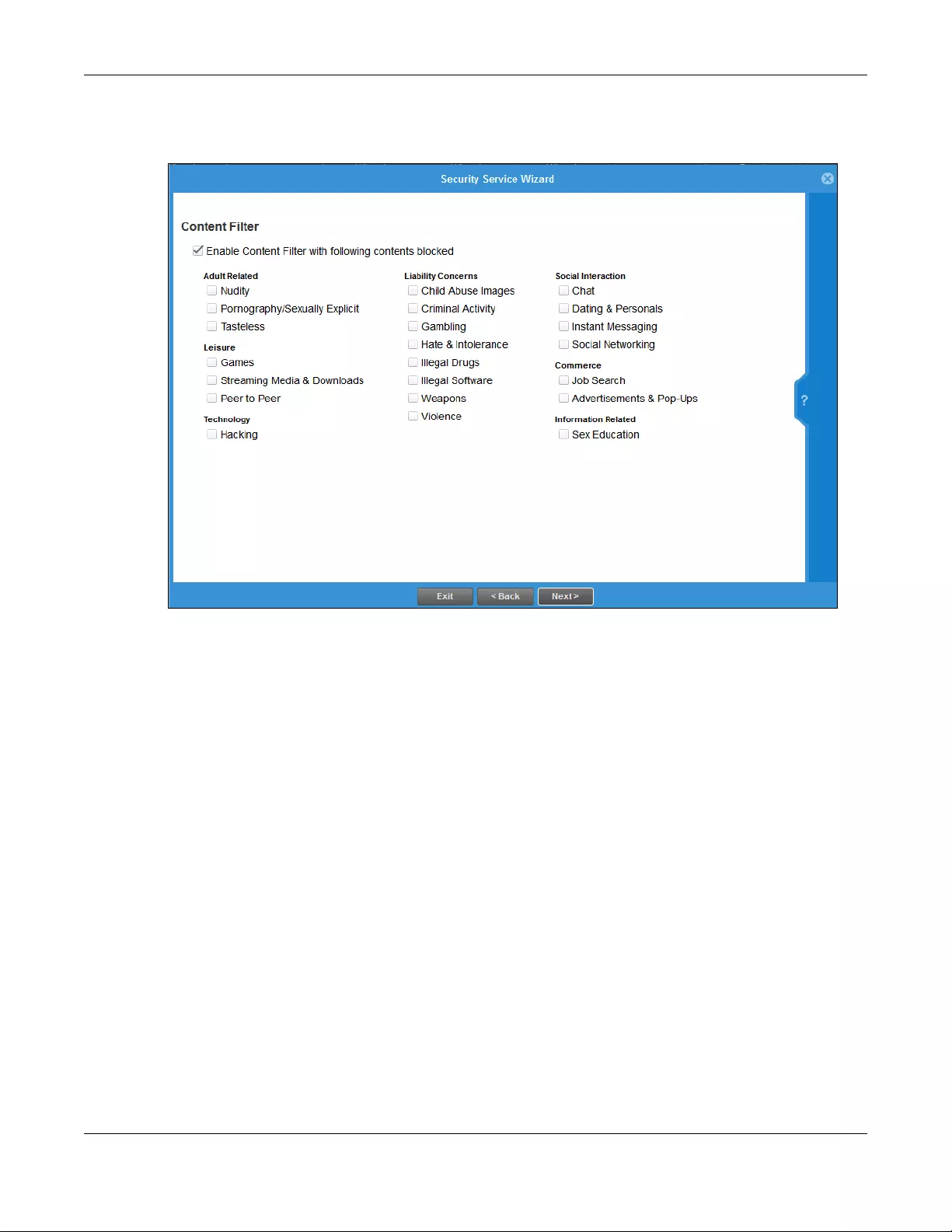
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
130
4.11.1 Security Service Wizard 2 - Content Filter Categories
Figure 103 Security Service Wizard 2 - Content Filter Categories
Configure licensed (non-grayed-out) services in this screen. After you buy a license for a service, you
must activate it at myZyxel.com. Make sure the Zyxel Device Internet connection is working correctly.
Select Enable Content Filter with following contents blocked to block websites by category, such as
Chat websites. Note that if you select Chat, the Content Filter blocks chat websites and not chat apps.
Therefore, the Skype app can still be used although the Skype website would be blocked. Select the
categories you want to block.
• Adult Related
• Nudity: Sites that contain full or partial nudity that are not necessarily overtly sexual in intent.
Includes sites that advertise or sell lingerie, intimate apparel, or swim wear. For example,
www.easyshop.com.tw, www.faster-swim.com.tw, image.baidu.com.
• Pornography/Sexually Explicit: Sites that contain explicit sexual content. Includes adult products
such as sex toys, CD-ROMs, and videos, adult services such as videoconferencing, escort services,
and strip clubs, erotic stories and textual descriptions of sexual acts. For example,
www.dvd888.com, www.18center.com, blog.sina.com.tw.
• Tasteless: Sites with offensive or tasteless content such as bathroom humor or profanity. For
example, comedycentral.com, dilbert.com.
•Leisure
• Games: Sites relating to computer or other games, information about game producers, or how to
obtain cheat codes. Game-related publication sites. For example, www.gamer.com.tw,
www.wowtaiwan.com.tw, tw.lineage.gamania.com.

Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
131
• Streaming Media & Downloads: Sites that deliver streaming content, such as Internet radio, Internet
TV or MP3 and live or archived media download sites. Includes fan sites, or official sites run by
musicians, bands, or record labels. For example, www.youtube.com, pfp.sina.com.cn,
my.xunlei.com.
• Peer to Peer: Sites that enable direct exchange of files between users without dependence on a
central server. For example, www.eyny.com.
• Technology
• Hacking: Sites that promote or give advice about how to gain unauthorized access to proprietary
computer systems, for the purpose of stealing information, perpetrating fraud, creating viruses, or
committing other illegal activity related to theft of digital information. For example,
www.hackbase.com, www.chinahacker.com.
• Liability Concerns
• Child Abuse Images: Sites that portray or discuss children in sexual or other abusive acts. For
example, a.uuzhijia.info.
• Criminal Activity: Sites that offer advice on how to commit illegal or criminal activities, or to avoid
detection. These can include how to commit murder, build bombs, pick locks, etc. Also includes
sites with information about illegal manipulation of electronic devices, hacking, fraud and illegal
distribution of software. For example, www.hackbase.com, jia.hackbase.com, ad.adver.com.tw.
• Gambling: Sites that offer or are related to online gambling, lottery, casinos and betting agencies
involving chance. For example, www.taiwanlottery.com.tw, www.i-win.com.tw, www.hkjc.com.
• Hate & Intolerance: Sites that promote a supremacist political agenda, encouraging oppression of
people or groups of people based on their race, religion, gender, age, disability, sexual orientation
or nationality. For example, www.racist-jokes.com, aryan-nations.org, whitepower.com.
• Illegal Drugs: Sites with information on the purchase, manufacture, and use of illegal or recreational
drugs and their paraphernalia, and misuse of prescription drugs and other compounds For
example, www.cannabis.net, www.amphetamines.com.
• Illegal Software: Sites that illegally distribute software or copyrighted materials such as movies or
music, software cracks, illicit serial numbers, illegal license key generators. For example,
www.zhaokey.com.cn, www.tiansha.net.
• Weapons: Sites that depict, sell, review or describe guns and weapons, including for sport. For
example, www.ak-47.net, warfare.ru.
• Violence: Sites that contain images or text depicting or advocating physical assault against
humans, animals, or institutions. Sites of a particularly gruesome nature such as shocking depictions
of blood or wounds, or cruel animal treatment. For example, crimescene.com, deathnet.com,
michiganmilitia.com.
• Social Interaction
• Chat: Sites that enable web-based exchange of real time messages through chat services or chat
rooms. For example, me.sohu.com, blufiles.storage.live.com.
• Dating & Personals: Sites that promote networking for interpersonal relationships such as dating and
marriage. Includes sites for match-making, online dating, spousal introduction. For example, www.i-
part.com.tw, www.imatchi.com.
• Instant Messaging: Sites that enable logging in to instant messaging services such as ICQ, AOL
Instant Messenger, IRC, MSN, Jabber, Yahoo Messenger, and the like. For example,
www.meebo.com, www.aim.com, www. ebuddy.com.
• Social Networking: Sites that enable social networking for online communities of various topics, for
friendship, dating, or professional reasons. For example, www.facebook.com, www.flickr.com,
www.groups.google.com.
•Commerce
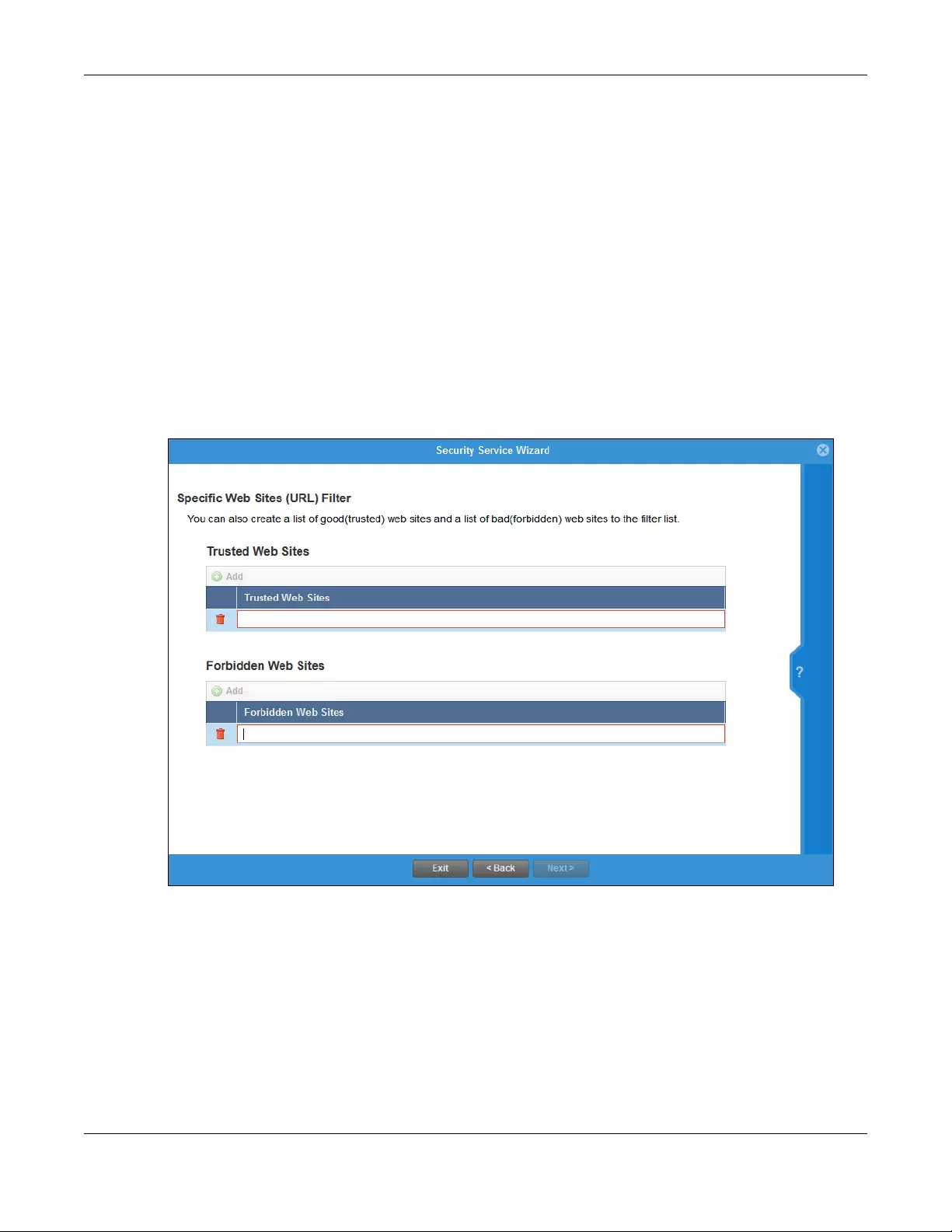
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
132
• Job Search: Sites containing job listings, career information, assistance with job searches (such as
resume writing, interviewing tips, etc.), employment agencies or head hunters. For example,
www.104.com.tw, www.1111.com.tw, www.yes123.com.tw.
• Advertisements & Pop-Ups: Sites that provide advertising graphics or other ad content files such as
banners and pop-ups. For example, pagead2.googlesyndication.com, ad.yieldmanager.com.
• Information Related
• Sex Education: Sites relating to sex education, including subjects such as respect for partner,
abortion, gay and lesbian lifestyle, contraceptives, sexually transmitted diseases, and pregnancy.
For example, apps.rockyou.com, www.howmama.com.tw, www.mombaby.com.tw.
Select Enable IDP to drop traffic with recognized Intrusion, Detection & Protection attack patterns.
Select Enable Anti-Virus to detect virus patterns in files.
4.11.2 Security Service Wizard 3 - Websites
Figure 104 Security Wizard 3 - Trusted and Forbidden Websites
Here, you can create a list of good (trusted) web site addresses and a list of bad (forbidden) web site
addresses. Click Add to create a new trusted or forbidden web site. Enter host names such as
www.good-site.com or www.bad-site.com into this text field. Do not enter the complete URL of the site –
that is, do not include “http://”. All sub-domains are allowed. For example, entering “*zyxel.com” also
allows or forbids “www.zyxel.com”, “partner.zyxel.com”, “press.zyxel.com”, and so on. You can also
enter just a top level domain. For example, enter “*.com” to allow or forbid all .com domains.
Use up to 127 characters (0-9a-z-). The casing does not matter. “*” can be used as a wild-card to match
any string. The entry must contain at least one period “.” or it will be invalid.
Click the trash can to remove a trusted or forbidden web site.
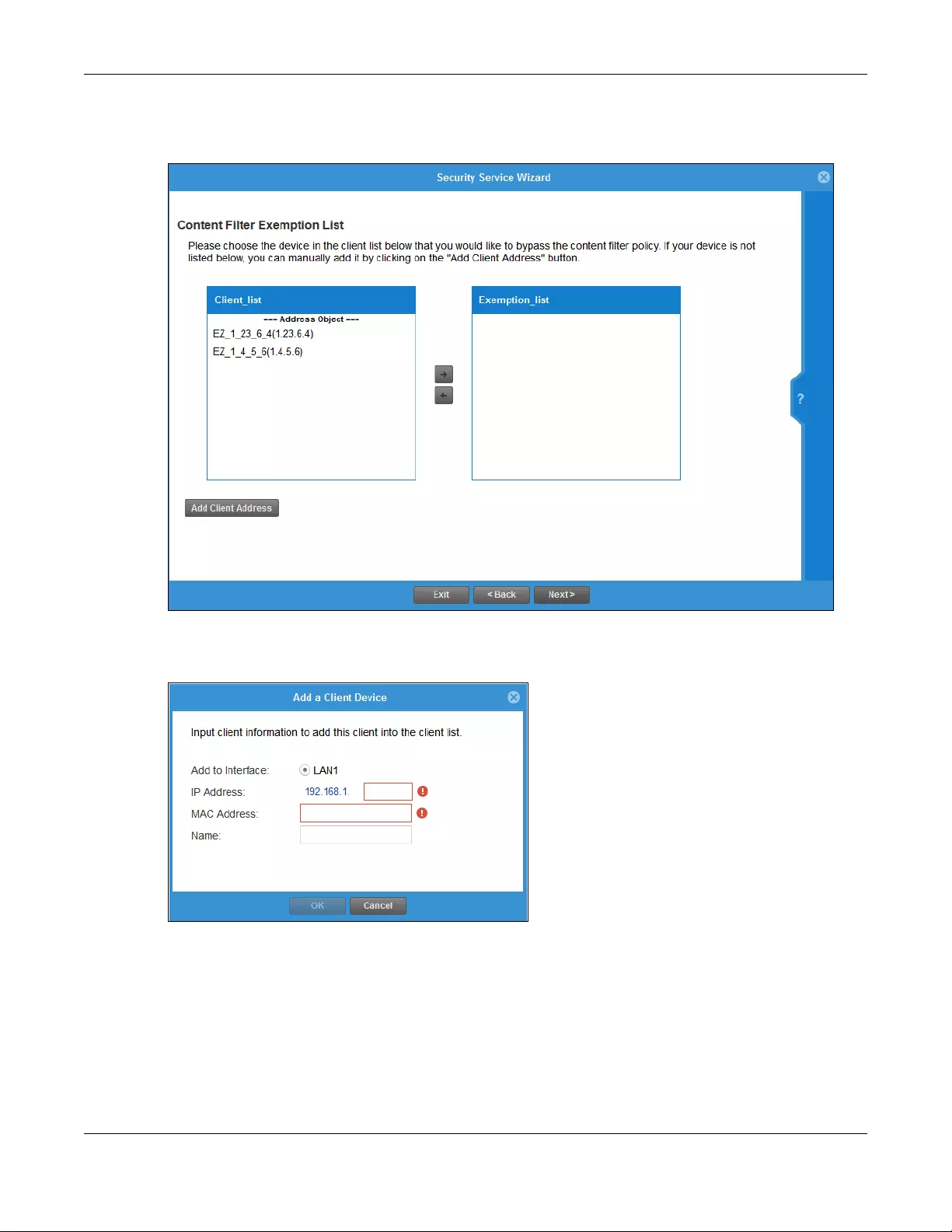
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
133
4.11.3 Security Service Wizard 4 - Exemptions
Figure 105 Security Wizard 4 - Exemptions
Select devices which are exempted from content file category and trusted/forbidden web site policies.
Click Add Client Address under Client List if you cannot see the client to exempt in the list. In the pop-up
screen, you can add a new client by entering its Name, IP Address and MAC Address.
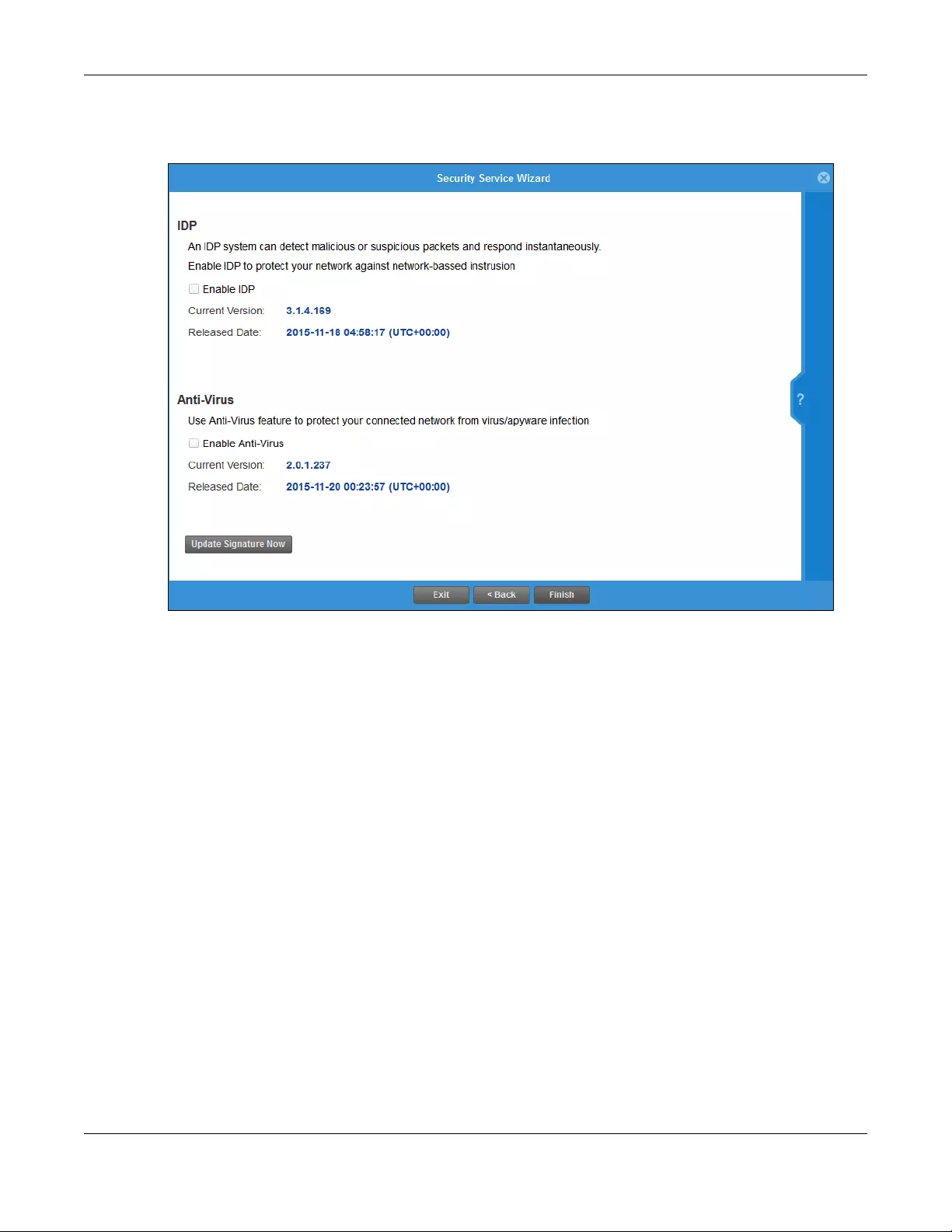
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
134
4.11.4 Security Service Wizard 5 - IDP/AV
Figure 106 Security Wizard 5 - IDP/AV
IDP (Intrusion, Detection and Prevention) consists of a set of signatures which examine packet content
for known malicious data. You need to subscribe for IDP service in order to be able to download new
signatures. It's important to keep the signatures up to date as new types of malicious data are
constantly evolving.
Use the Zyxel Device’s Anti-Virus (AV) feature to protect your connected network from virus/spyware
infection. A computer virus is a small program designed to corrupt and/or alter the operation of other
legitimate programs. A worm is a self-replicating virus that resides in active memory and duplicates itself.
Zyxel Device’s Anti-Virus consists of a set of signatures which examine packet content for known viruses
and worms. You need to subscribe for AV service in order to be able to download new signatures. It's
important to keep the signatures up to date as new viruses and worms are constantly evolving.
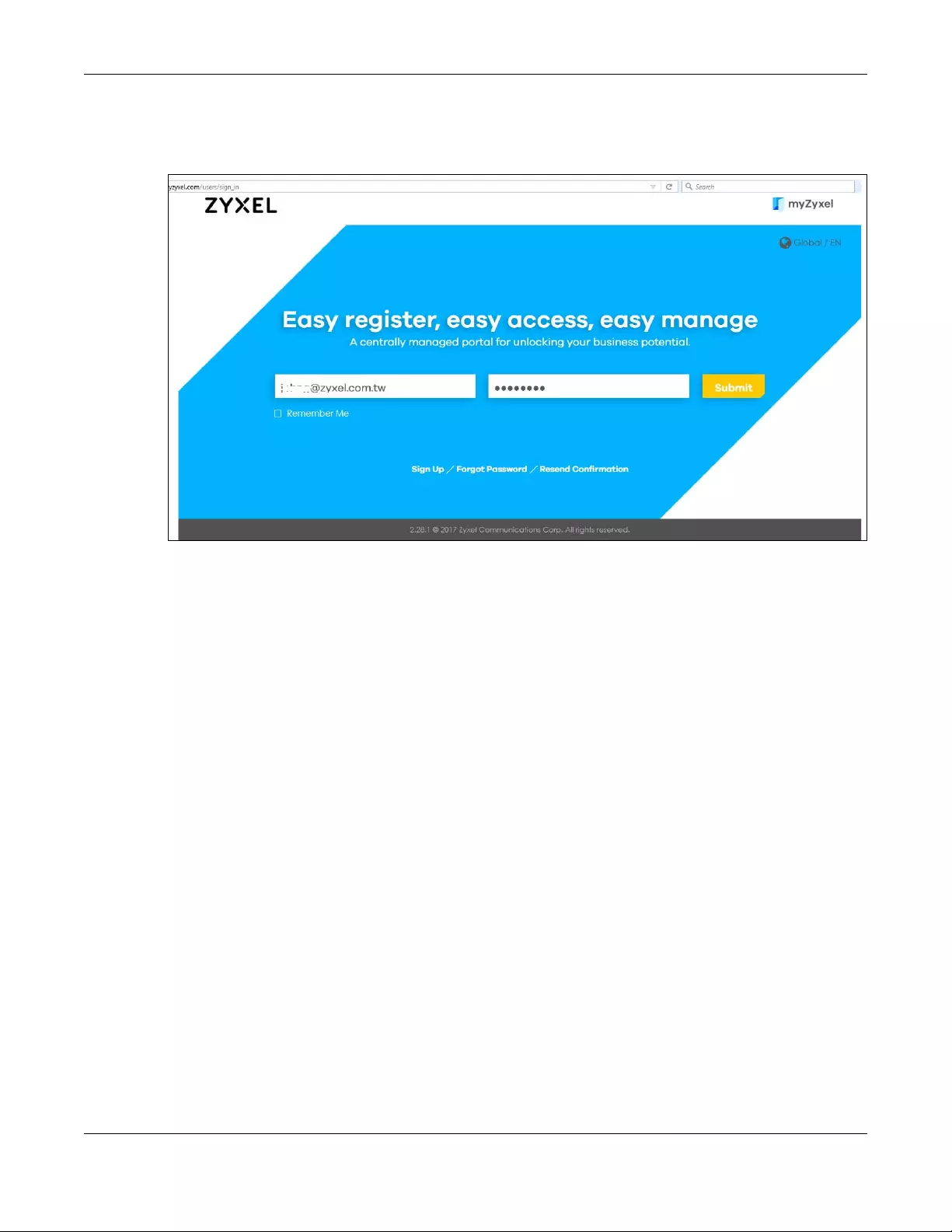
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
135
4.12 MyZyxel Portal
Figure 107 MyZyxel Portal
MyZyxel.com is Zyxel’s online services center where you can register your Zyxel Device and manage
subscription services available for the Zyxel Device. To update signature files or use a subscription
service, you have to register the Zyxel Device and activate the corresponding service at myZyxel.com
(through the Zyxel Device).
Use the MyZyxel Portal link to create an account at myZyxel.com.
Then, register your device. You may need your Zyxel Device’s serial number and LAN MAC address to
register it at myZyxel.com. Refer to the myZyxel.com web site’s on-line help for details.
To have the Zyxel Device use subscription services, please purchase an iCard and enter the license key
from it at MyZyxel Portal (through the Zyxel Device).
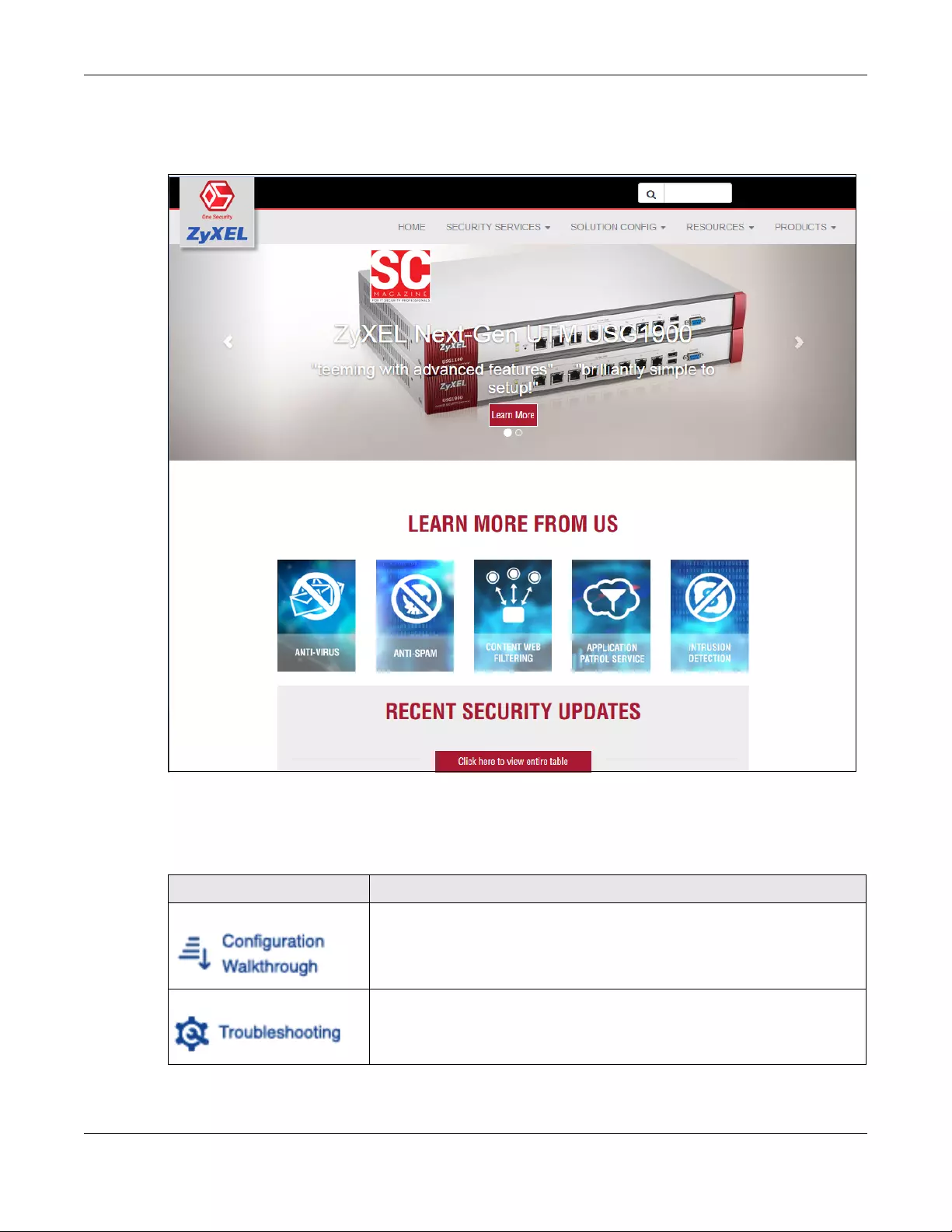
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
136
4.13 One Security Portal
Figure 108 One Security Portal
OneSecurity.com is a website with guidance on configuration walkthroughs, troubleshooting, and other
information. In the Zyxel Device advanced menus, you will see icons that link to OneSecurity
walkthroughs, troubleshooting and so on as shown in the following table.
Table 20 OneSecurity Links
ONESECURITY ICON SCREEN
Configuration Walkthrough
Click this icon to go to a series of screens that guide you how to configure the
feature. Note that the walkthroughs do not perform the actual configuring, but
just show you how to do it.
Troubleshooting
Click this icon to go to a series of screens that guide you how to fix problems with
the feature.
Chapter 4 Easy Mode
USG/ZyWALL User’s Guide
137
Application Patrol
Click this icon for more information on Application Patrol, which identifies traffic
that passes through the Zyxel Device, so you can decide what to do with specific
types of traffic. Traffic not recognized by application patrol is ignored.
Content Filter
Click this icon for more information on Content Filter, which controls access to
specific web sites or web content.
Intrusion Detection
Click this icon for more information on Intrusion Detection which can detect
malicious or suspicious packets used in network-based intrusions.
Anti-Virus
Click this icon for more information on Anti-Virus, which checks traffic flows
through your network for known virus and spyware signature patterns.
Anti-Spam
Click this icon for more information on Anti-Spam which can mark or discard
spam (unsolicited commercial or junk e-mail) and e-mail from certain servers
suspect of being used by spammers.
VPN Click this icon for more information on IPSec and SSL VPN. Internet Protocol
Security (IPSec) VPN connects IPSec routers or remote users using IPSec client
software. SSL VPN allows users to use a web browser for secure remote user login
without need of a VPN router or VPN client software.
Download VPN Client
Click this icon to download VPN client software.
Wireless AP Controller
Click this icon for more information on the Wireless AP Controller which sets how
the Zyxel Device allows APs to connect to the wireless network.
Table 20 OneSecurity Links (continued)
ONESECURITY ICON SCREEN

USG/ZyWALL User’s Guide
138
CHAPTER 5
Quick Setup Wizards
5.1 Quick Setup Overview
The Web Configurator's quick setup wizards help you configure Internet and VPN connection settings.
This chapter provides information on configuring the quick setup screens in the Web Configurator. See
the feature-specific chapters in this User’s Guide for background information.
In the Web Configurator, click Configuration > Quick Setup to open the first Quick Setup screen.
Figure 109 Quick Setup
• WAN Interface
Click this link to open a wizard to set up a WAN (Internet) connection. This wizard creates matching ISP
account settings in the Zyxel Device if you use PPPoE or PPTP. See Section 5.2 on page 139.
• VPN SETUP
Use VPN Setup to configure a VPN (Virtual Private Network) rule for a secure connection to another
computer or network. Use VPN Settings for Configuration Provisioning to set up a VPN rule that can be
retrieved with the Zyxel Device IPSec VPN Client. You only need to enter a user name, password and
the IP address of the Zyxel Device in the IPSec VPN Client to get all VPN settings automatically from
the Zyxel Device. See Section 5.3 on page 145.Use VPN Settings for L2TP VPN Settings to configure the
L2TP VPN for clients.
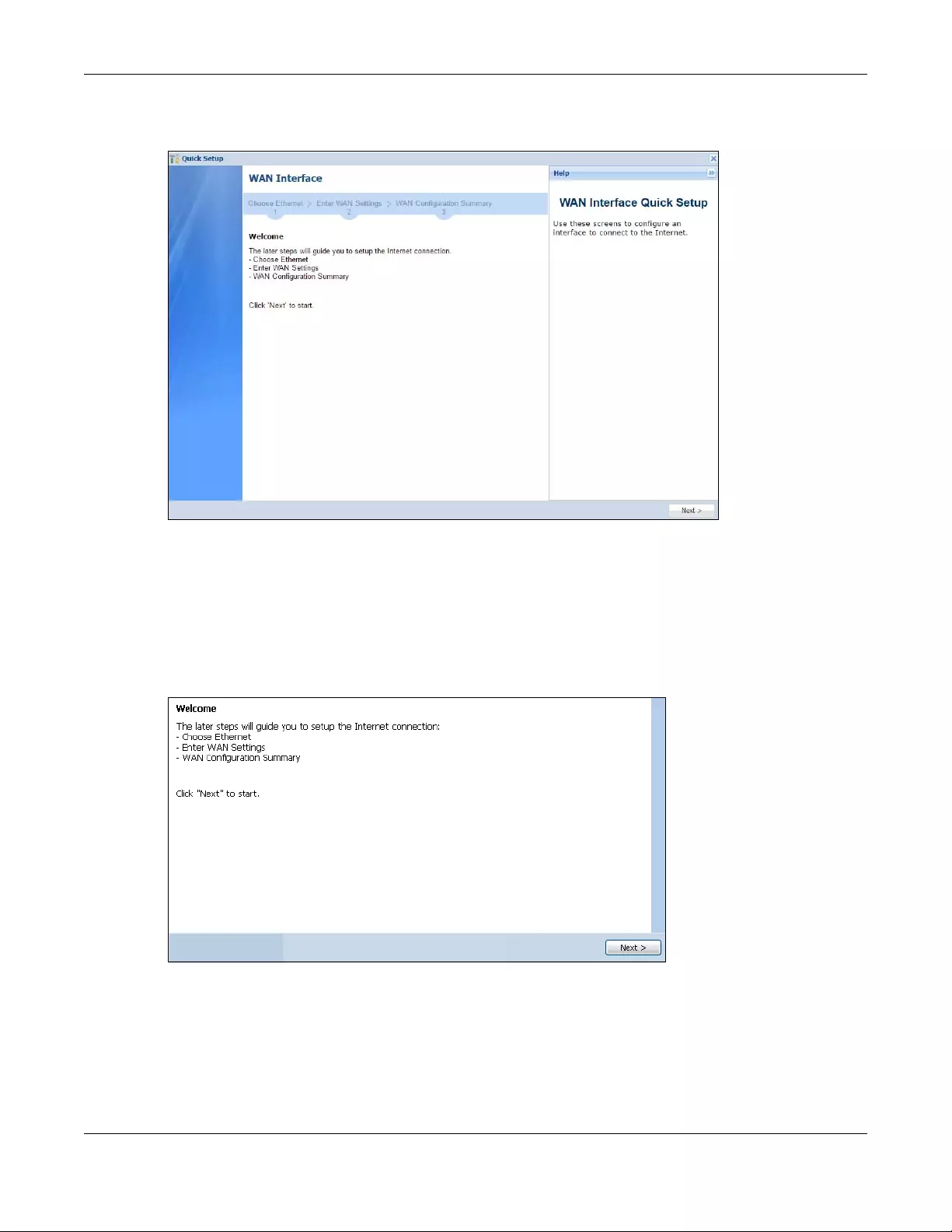
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
139
• Wizard Help
If the help does not automatically display when you run the wizard, click the arrow to display it.
5.2 WAN Interface Quick Setup
Click WAN Interface in the main Quick Setup screen to open the WAN Interface Quick Setup Wizard
Welcome screen. Use these screens to configure an interface to connect to the Internet. Click Next.
Figure 110 WAN Interface Quick Setup Wizard
5.2.1 Choose an Ethernet Interface
Select the Ethernet interface (names vary by model) that you want to configure for a WAN connection
and click Next.
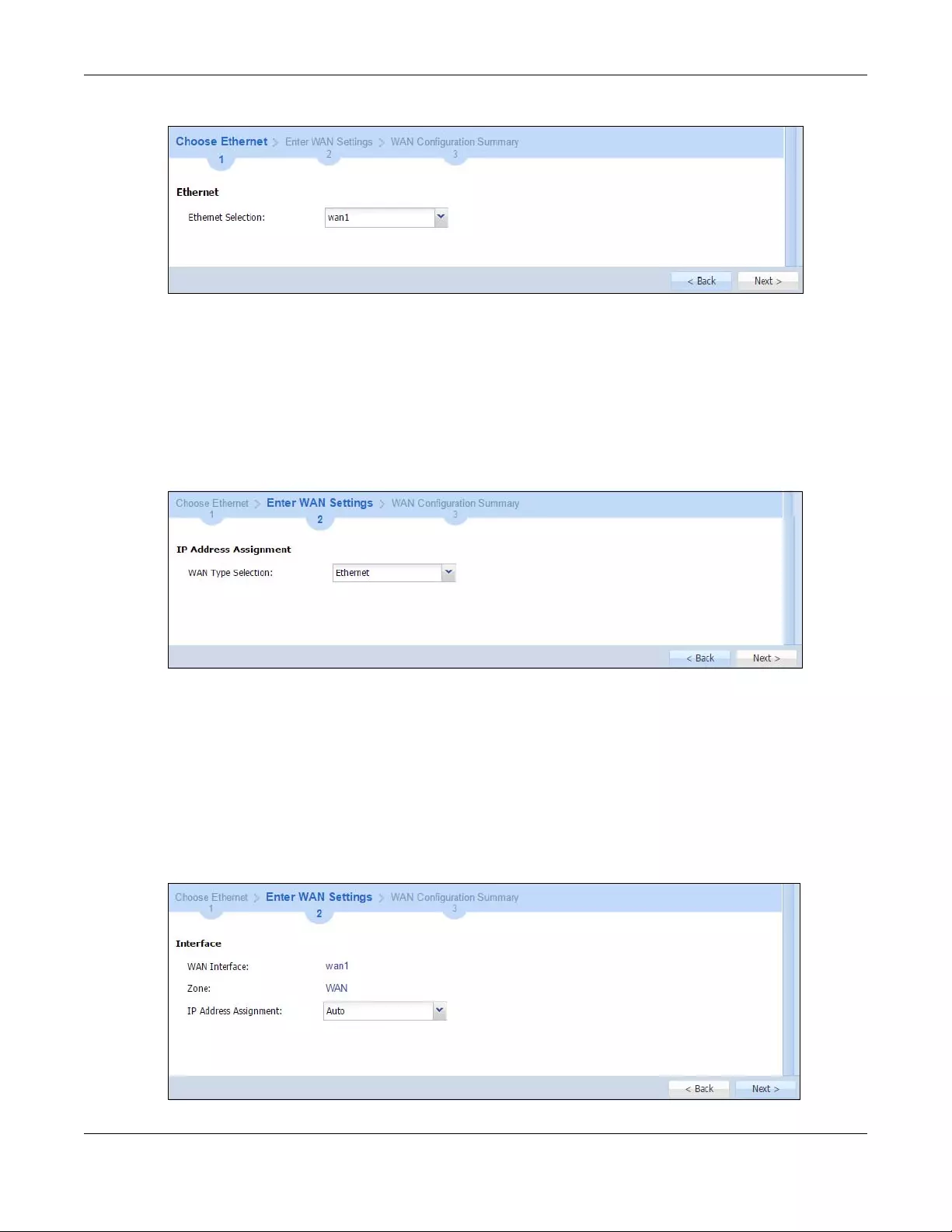
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
140
Figure 111 Choose an Ethernet Interface
5.2.2 Select WAN Type
WAN Type Selection: Select the type of encapsulation this connection is to use. Choose Ethernet when
the WAN port is used as a regular Ethernet.
Otherwise, choose PPPoE, PPTP or L2TP for a dial-up connection according to the information from your
ISP.
Figure 112 WAN Interface Setup: Step 2
The screens vary depending on what encapsulation type you use. Refer to information provided by your
ISP to know what to enter in each field. Leave a field blank if you don’t have that information.
Note: Enter the Internet access information exactly as your ISP gave it to you.
5.2.3 Configure WAN IP Settings
Use this screen to select whether the interface should use a fixed or dynamic IP address.
Figure 113 WAN Interface Setup: Step 2 Ethernet Dynamic IP
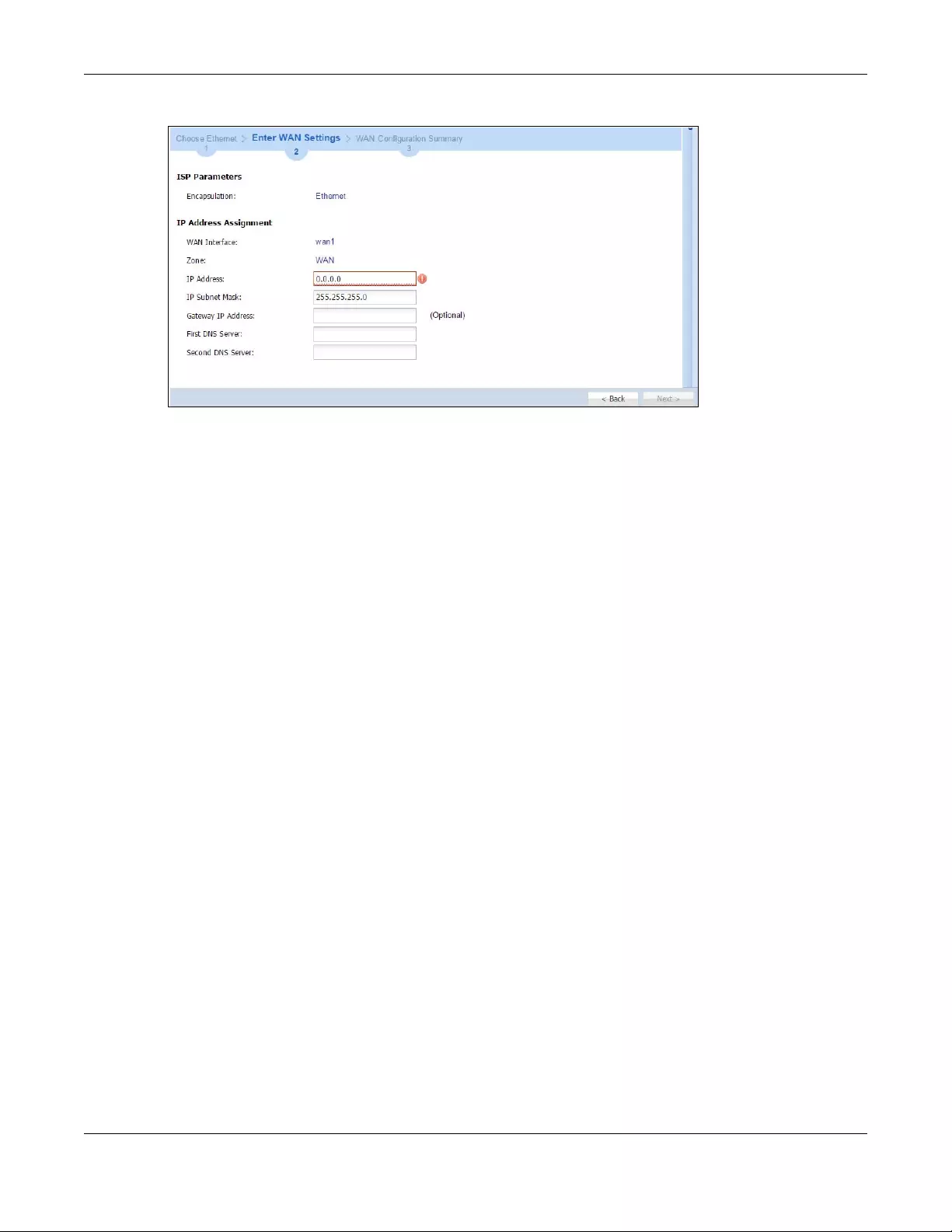
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
141
Figure 114 WAN Interface Setup: Step 2 Ethernet Static IP
•WAN Interface: This is the interface you are configuring for Internet access.
•Zone: This is the security zone to which this interface and Internet connection belong.
•IP Address Assignment: Select Auto If your ISP did not assign you a fixed IP address.
Select Static if you have a fixed IP address and enter the IP address, subnet mask, gateway IP address
(optional) and DNS server IP address(es).
5.2.4 ISP and WAN and ISP Connection Settings
Use this screen to configure the ISP and WAN interface settings. This screen is read-only if you select
Ethernet and set the IP Address Assignment to AutoStatic. If you set the IP Address Assignment to static
and/or select PPTP or PPPoE, enter the Internet access information exactly as your ISP gave it to you.
Note: Enter the Internet access information exactly as your ISP gave it to you.
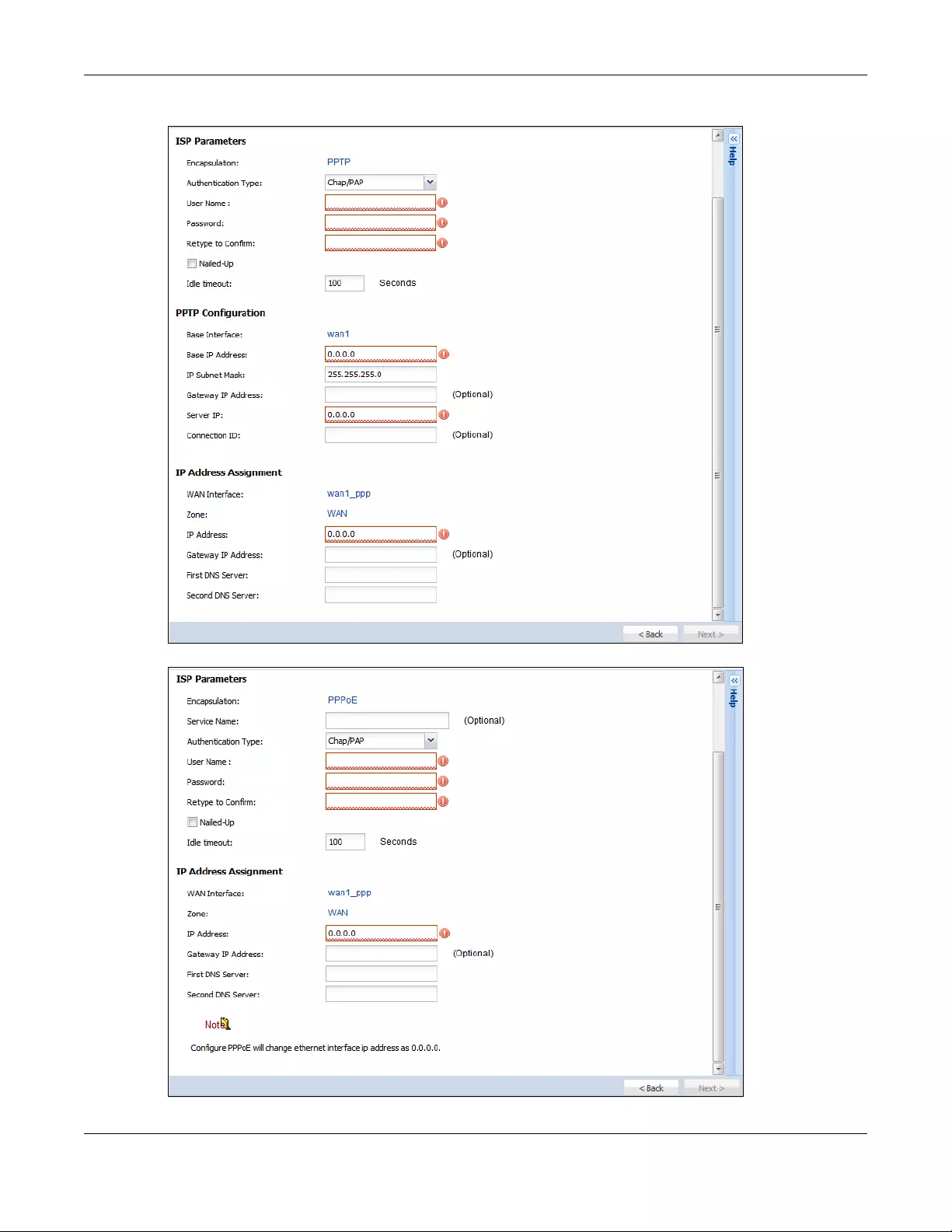
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
142
Figure 115 WAN and ISP Connection Settings: (PPTP)
Figure 116 WAN and ISP Connection Settings: (PPPoE)
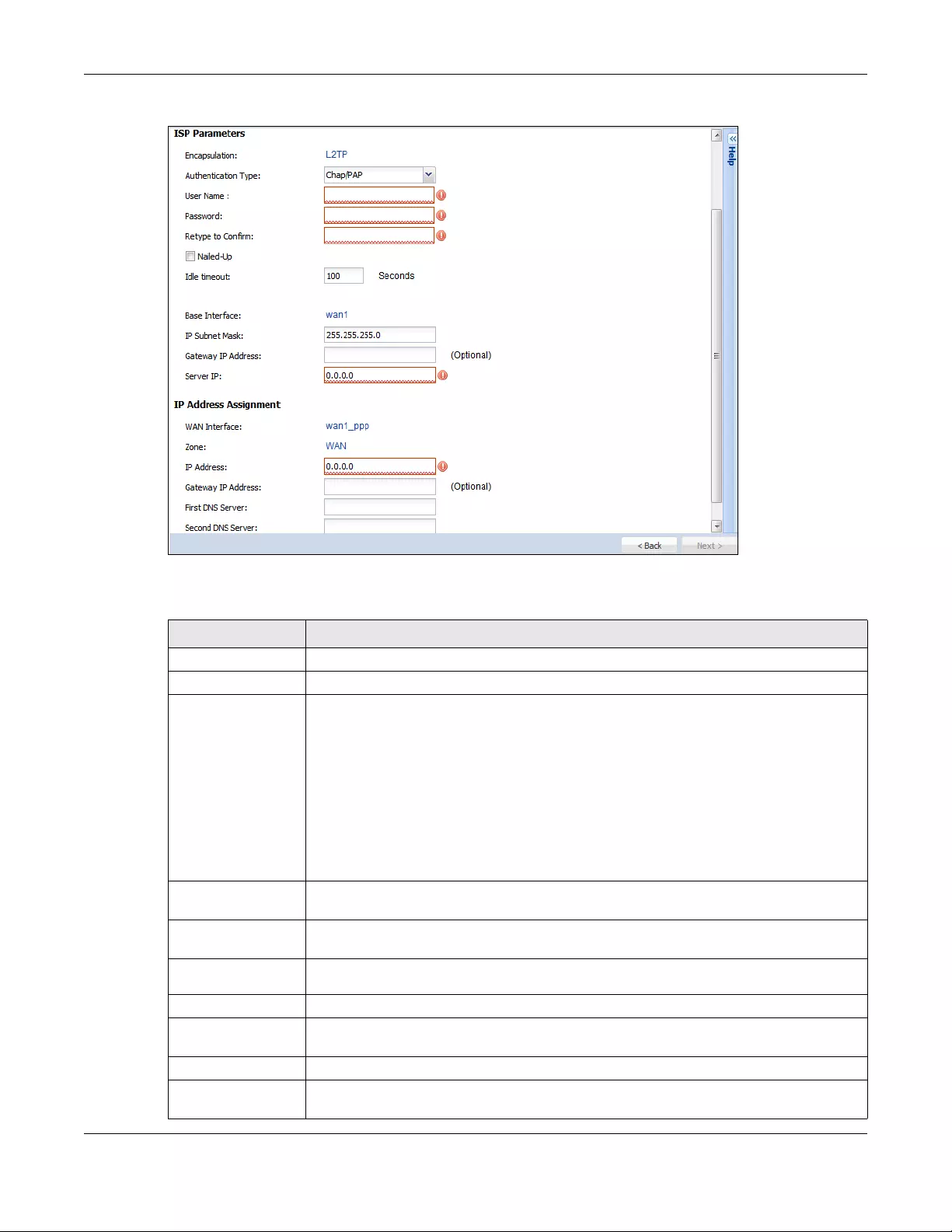
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
143
Figure 117 WAN and ISP Connection Settings: (L2TP)
The following table describes the labels in this screen.
Table 21 WAN and ISP Connection Settings
LABEL DESCRIPTION
ISP Parameter This section appears if the interface uses a PPPoE or PPTP Internet connection.
Encapsulation This displays the type of Internet connection you are configuring.
Authentication
Type Use the drop-down list box to select an authentication protocol for outgoing calls. Options
are:
CHAP/PAP - Your Zyxel Device accepts either CHAP or PAP when requested by this remote
node.
CHAP - Your Zyxel Device accepts CHAP only.
PAP - Your Zyxel Device accepts PAP only.
MSCHAP - Your Zyxel Device accepts MSCHAP only.
MSCHAP-V2 - Your Zyxel Device accepts MSCHAP-V2 only.
User Name Type the user name given to you by your ISP. You can use alphanumeric and -_@$./
characters, and it can be up to 31 characters long.
Password Type the password associated with the user name above. Use up to 64 ASCII characters
except the [] and ?. This field can be blank.
Retype to
Confirm Type your password again for confirmation.
Nailed-Up Select Nailed-Up if you do not want the connection to time out.
Idle Timeout Type the time in seconds that elapses before the router automatically disconnects from the
PPPoE server. 0 means no timeout.
PPTP Configuration This section only appears if the interface uses a PPPoE or PPTP Internet connection.
Base Interface This displays the identity of the Ethernet interface you configure to connect with a modem
or router.
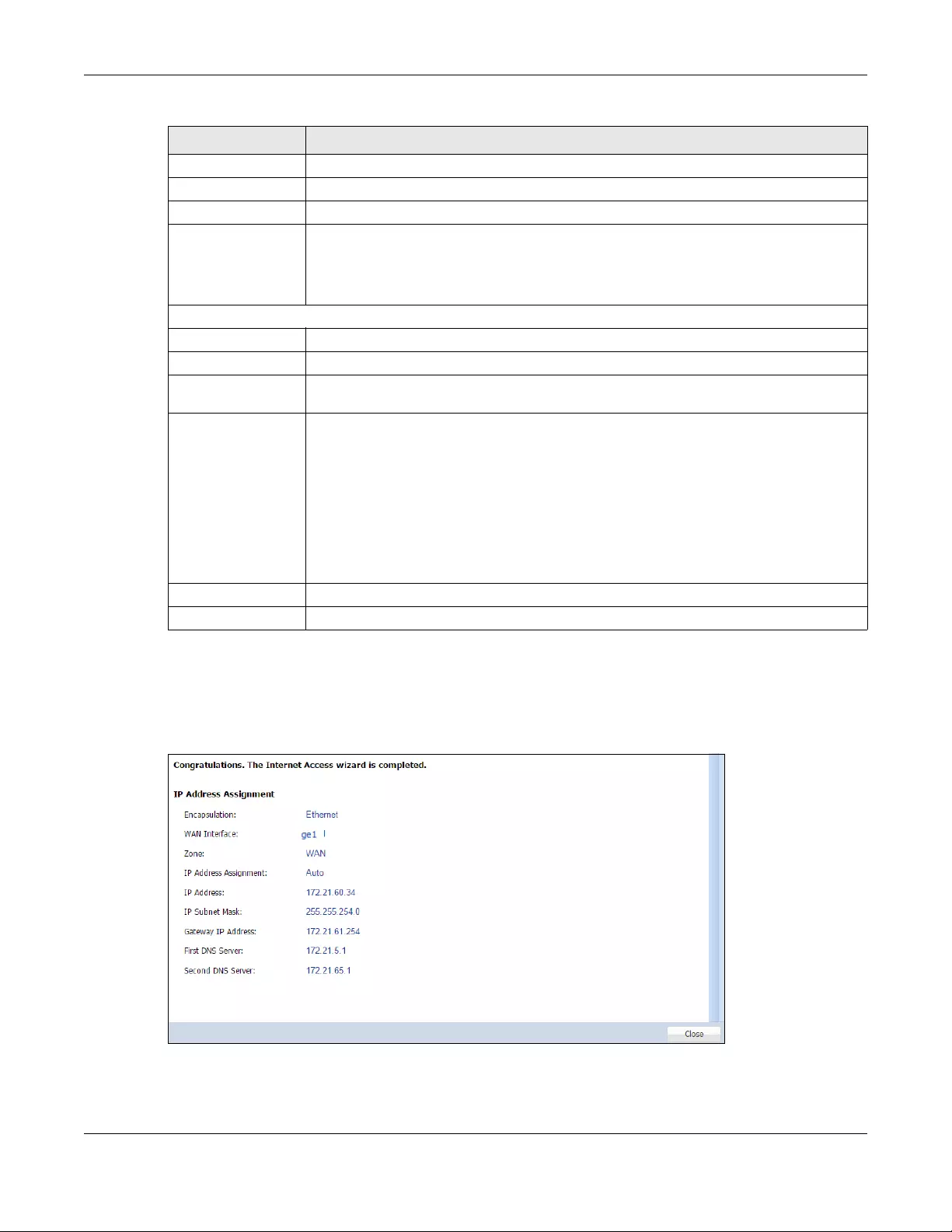
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
144
5.2.5 Quick Setup Interface Wizard: Summary
This screen displays an example WAN interface’s settings.
Figure 118 Interface Wizard: Summary WAN
Base IP Address Type the (static) IP address assigned to you by your ISP.
IP Subnet Mask Type the subnet mask assigned to you by your ISP (if given).
Server IP Type the IP address of the PPTP server.
Connection ID Enter the connection ID or connection name in this field. It must follow the "c:id" and
"n:name" format. For example, C:12 or N:My ISP.
This field is optional and depends on the requirements of your DSL modem.
You can use alphanumeric and -_: characters, and it can be up to 31 characters long.
WAN Interface Setup
WAN Interface This displays the identity of the interface you configure to connect with your ISP.
Zone This field displays to which security zone this interface and Internet connection will belong.
IP Address This field is read-only when the WAN interface uses a dynamic IP address. If your WAN
interface uses a static IP address, enter it in this field.
First DNS Server
Second DNS
Server
These fields only display for an interface with a static IP address. Enter the DNS server IP
address(es) in the field(s) to the right.
Leave the field as 0.0.0.0 if you do not want to configure DNS servers. If you do not configure
a DNS server, you must know the IP address of a machine in order to access it.
DNS (Domain Name System) is for mapping a domain name to its corresponding IP address
and vice versa. The DNS server is extremely important because without it, you must know the
IP address of a computer before you can access it. The Zyxel Device uses a system DNS
server (in the order you specify here) to resolve domain names for VPN, DDNS and the time
server.
Back Click Back to return to the previous screen.
Next Click Next to continue.
Table 21 WAN and ISP Connection Settings (continued)
LABEL DESCRIPTION
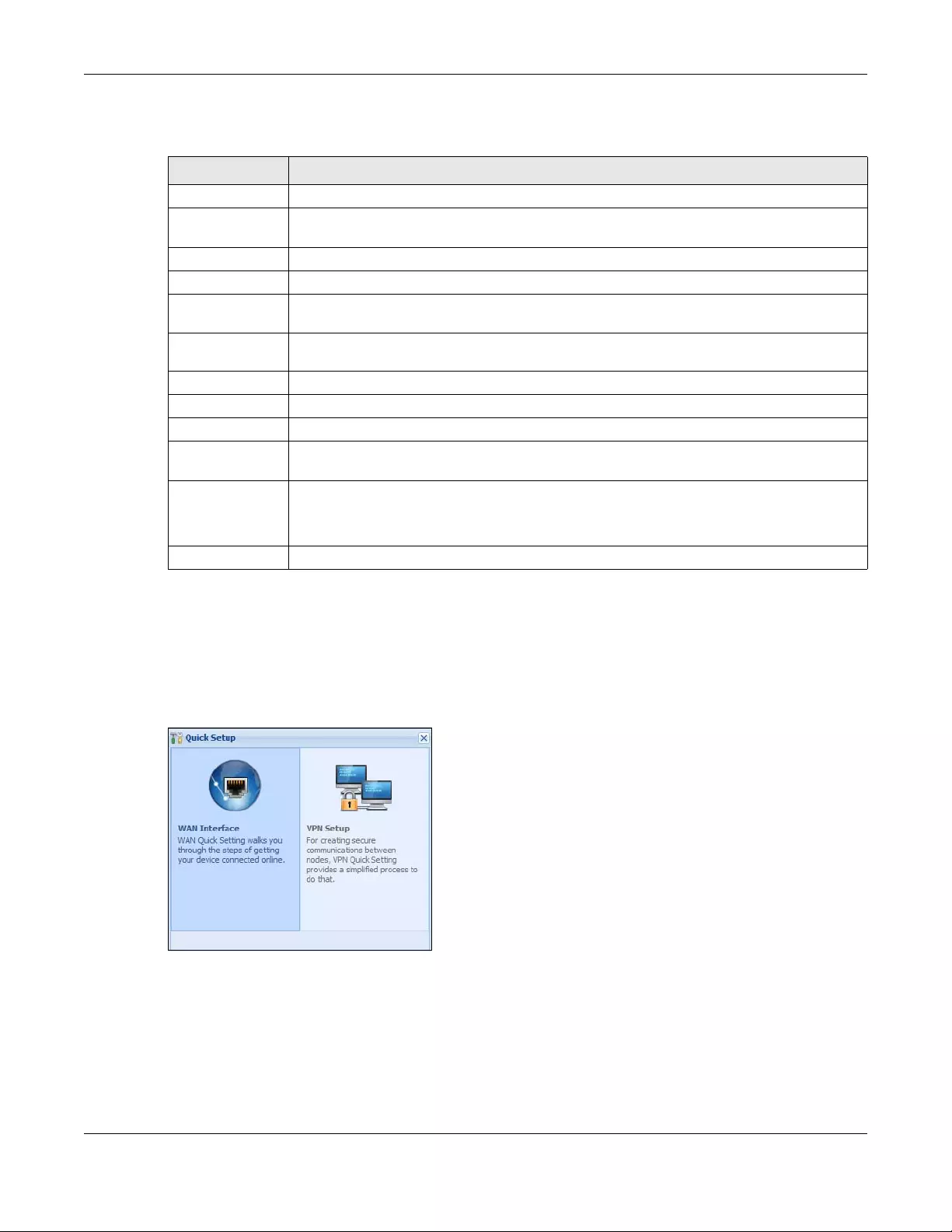
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
145
The following table describes the labels in this screen.
5.3 VPN Setup Wizard
Click VPN Setup in the main Quick Setup screen to open the VPN Setup Wizard Welcome screen.
Figure 119 VPN Setup Wizard
5.3.1 Welcome
Use wizards to create Virtual Private Network (VPN) rules. After you complete the wizard, the Phase 1 rule
settings appear in the VPN > IPSec VPN > VPN Gateway screen and the Phase 2 rule settings appear in
the VPN > IPSec VPN > VPN Connection screen.
•VPN Settings configures a VPN tunnel for a secure connection to another computer or network.
Table 22 Interface Wizard: Summary WAN
LABEL DESCRIPTION
Encapsulation This displays what encapsulation this interface uses to connect to the Internet.
Service Name This field only appears for a PPPoE interface. It displays the PPPoE service name specified in the
ISP account.
Server IP This field only appears for a PPTP interface. It displays the IP address of the PPTP server.
User Name This is the user name given to you by your ISP.
Nailed-Up If No displays the connection will not time out. Yes means the Zyxel Device uses the idle
timeout.
Idle Timeout This is how many seconds the connection can be idle before the router automatically
disconnects from the PPPoE server. 0 means no timeout.
Connection ID If you specified a connection ID, it displays here.
WAN Interface This identifies the interface you configure to connect with your ISP.
Zone This field displays to which security zone this interface and Internet connection will belong.
IP Address
Assignment
This field displays whether the WAN IP address is static or dynamic (Auto).
First DNS Server
Second DNS
Server
If the IP Address Assignment is Static, these fields display the DNS server IP address(es).
Close Click Close to exit the wizard.
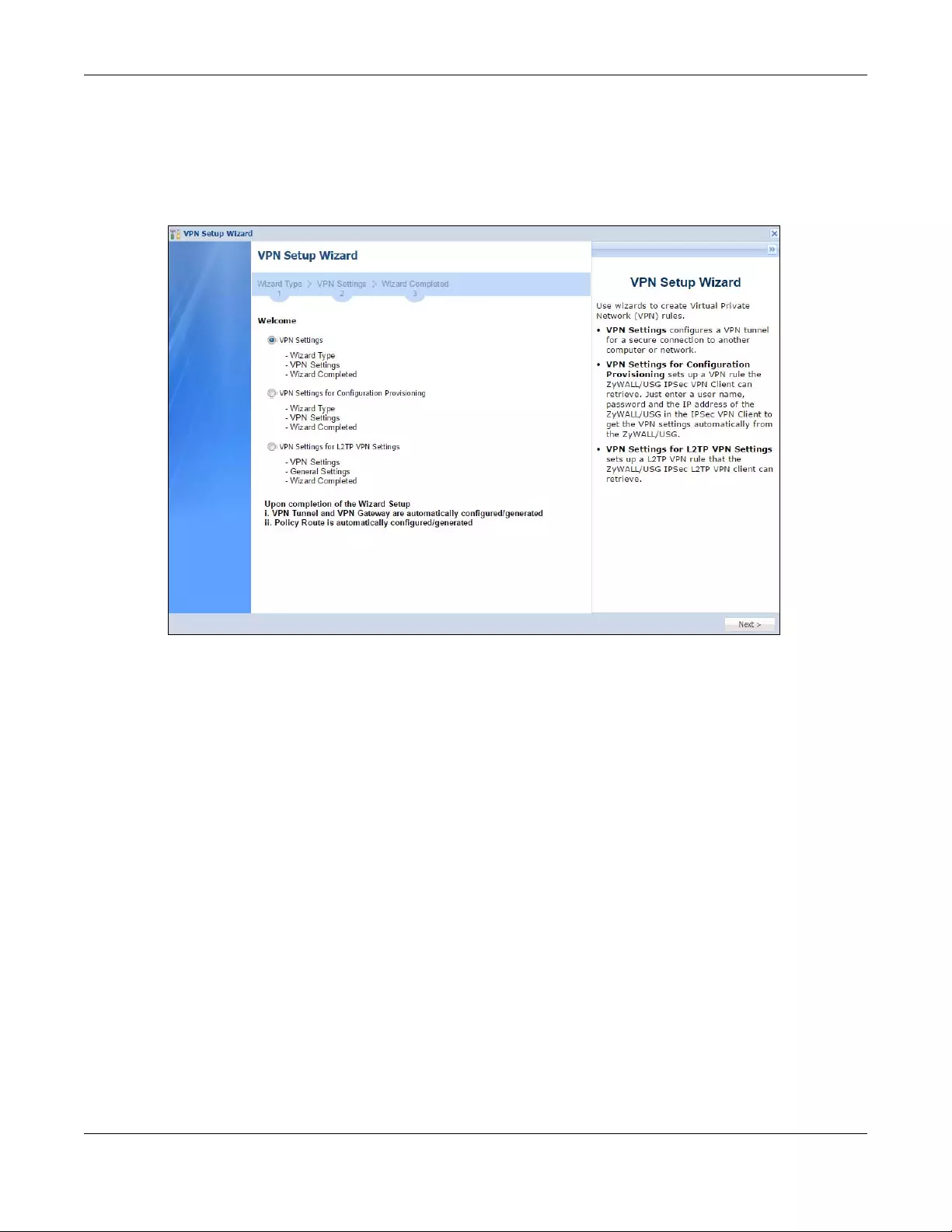
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
146
•VPN Settings for Configuration Provisioning sets up a VPN rule the Zyxel Device IPSec VPN Client can
retrieve. Just enter a user name, password and the IP address of the Zyxel Device in the IPSec VPN
Client to get the VPN settings automatically from the Zyxel Device.
•VPN Settings for L2TP VPN Settings sets up a L2TP VPN rule that the Zyxel Device IPSec L2TP VPN client
can retrieve.
Figure 120 VPN Setup Wizard Welcome
5.3.2 VPN Setup Wizard: Wizard Type
Choose Express to create a VPN rule with the default phase 1 and phase 2 settings to connect to
another ZLD-based Zyxel Device using a pre-shared key.
Choose Advanced to change the default settings and/or use certificates instead of a pre-shared key to
create a VPN rule to connect to another IPSec device.
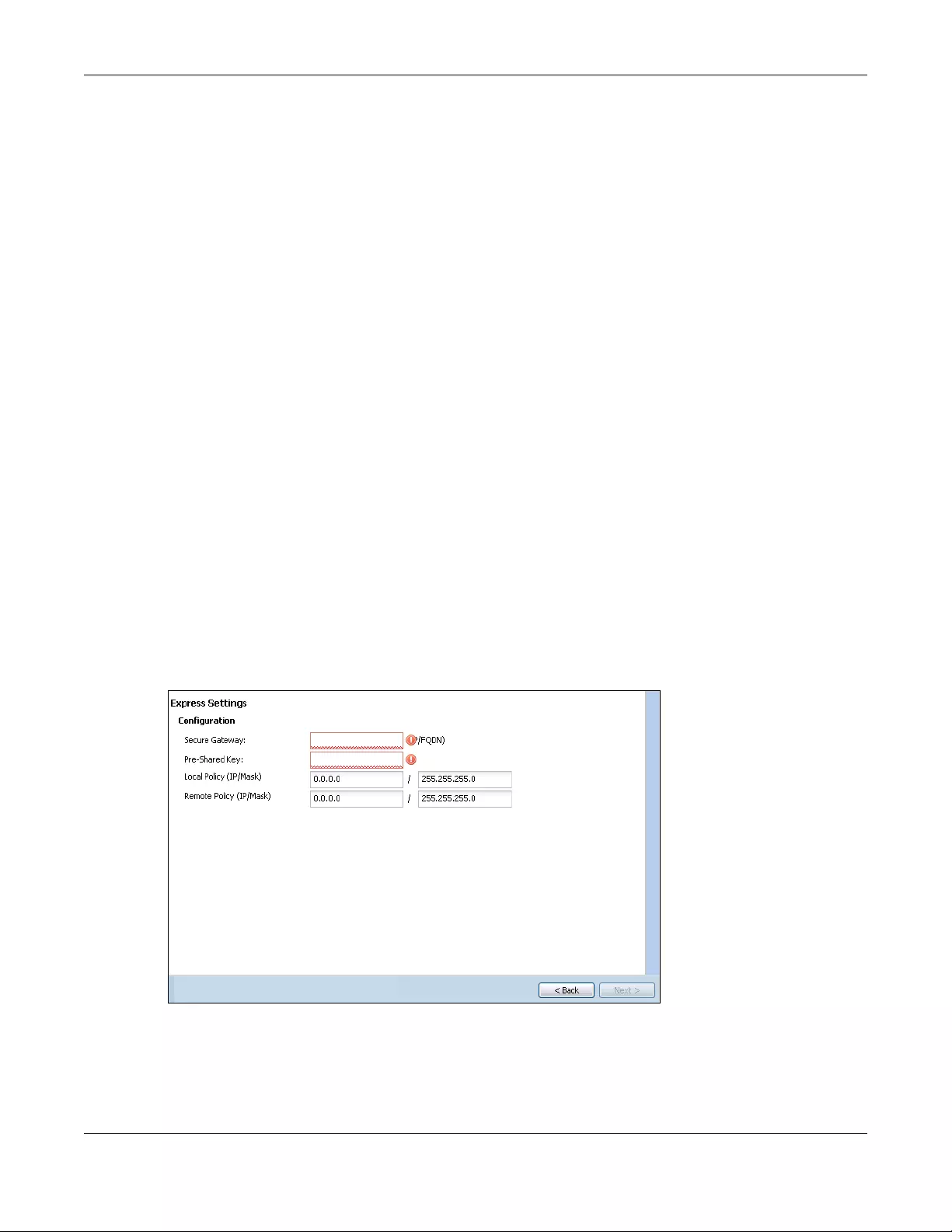
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
148
IKE (Internet Key Exchange) Version: IKEv1 and IKEv2
IKE (Internet Key Exchange) is a protocol used in security associations to send data securely. IKE uses
certificates or pre-shared keys for authentication and a Diffie–Hellman key exchange to set up a shared
session secret from which encryption keys are derived.
IKEv2 supports Extended Authentication Protocol (EAP) authentication, and IKEv1 supports X-Auth. EAP is
important when connecting to existing enterprise authentication systems.
Scenario
Rule Name: Type the name used to identify this VPN connection (and VPN gateway). You may use 1-31
alphanumeric characters, underscores (_), or dashes (-), but the first character cannot be a number.
This value is case-sensitive.
Select the scenario that best describes your intended VPN connection. The figure on the left of the
screen changes to match the scenario you select.
•Site-to-site - The remote IPSec device has a static IP address or a domain name. This Zyxel Device can
initiate the VPN tunnel.
•Site-to-site with Dynamic Peer - The remote IPSec device has a dynamic IP address. Only the remote
IPSec device can initiate the VPN tunnel.
•Remote Access (Server Role) - Allow incoming connections from IPSec VPN clients. The clients have
dynamic IP addresses and are also known as dial-in users. Only the clients can initiate the VPN tunnel.
•Remote Access (Client Role) - Connect to an IPSec server. This Zyxel Device is the client (dial-in user)
and can initiate the VPN tunnel.
5.3.4 VPN Express Wizard - Configuration
Figure 123 VPN Express Wizard: Configuration
•Secure Gateway: Any displays in this field if it is not configurable for the chosen scenario. Otherwise,
enter the WAN IP address or domain name of the remote IPSec device (secure gateway) to identify
the remote IPSec router by its IP address or a domain name. Use 0.0.0.0 if the remote IPSec router has
a dynamic WAN IP address.
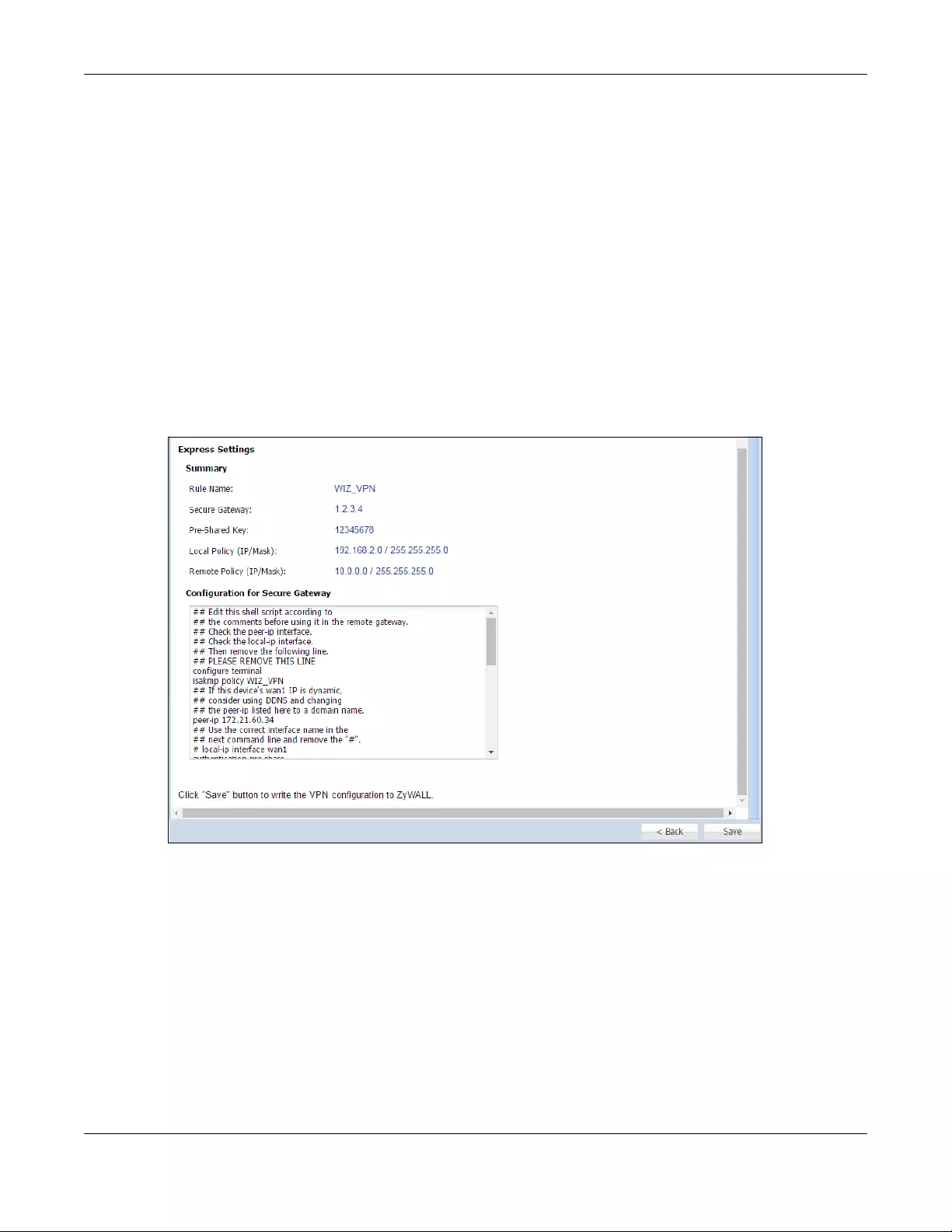
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
149
•Pre-Shared Key: Type the password. Both ends of the VPN tunnel must use the same password. Use 8
to 31 case-sensitive ASCII characters or 8 to 31 pairs of hexadecimal (“0-9”, “A-F”) characters.
Proceed a hexadecimal key with “0x”. You will receive a PYLD_MALFORMED (payload malformed)
packet if the same pre-shared key is not used on both ends.
•Local Policy (IP/Mask): Type the IP address of a computer on your network that can use the tunnel.
You can also specify a subnet. This must match the remote IP address configured on the remote IPSec
device.
•Remote Policy (IP/Mask): Any displays in this field if it is not configurable for the chosen scenario.
Otherwise, type the IP address of a computer behind the remote IPSec device. You can also specify
a subnet. This must match the local IP address configured on the remote IPSec device.
5.3.5 VPN Express Wizard - Summary
This screen provides a read-only summary of the VPN tunnel’s configuration and commands that you
can copy and paste into another ZLD-based Zyxel Device’s command line interface to configure it.
Figure 124 VPN Express Wizard: Summary
•Rule Name: Identifies the VPN gateway policy.
•Secure Gateway: IP address or domain name of the remote IPSec device. If this field displays Any,
only the remote IPSec device can initiate the VPN connection.
•Pre-Shared Key: VPN tunnel password. It identifies a communicating party during a phase 1 IKE
negotiation.
•Local Policy: IP address and subnet mask of the computers on the network behind your Zyxel Device
that can use the tunnel.
•Remote Policy: IP address and subnet mask of the computers on the network behind the remote
IPSec device that can use the tunnel. If this field displays Any, only the remote IPSec device can
initiate the VPN connection.
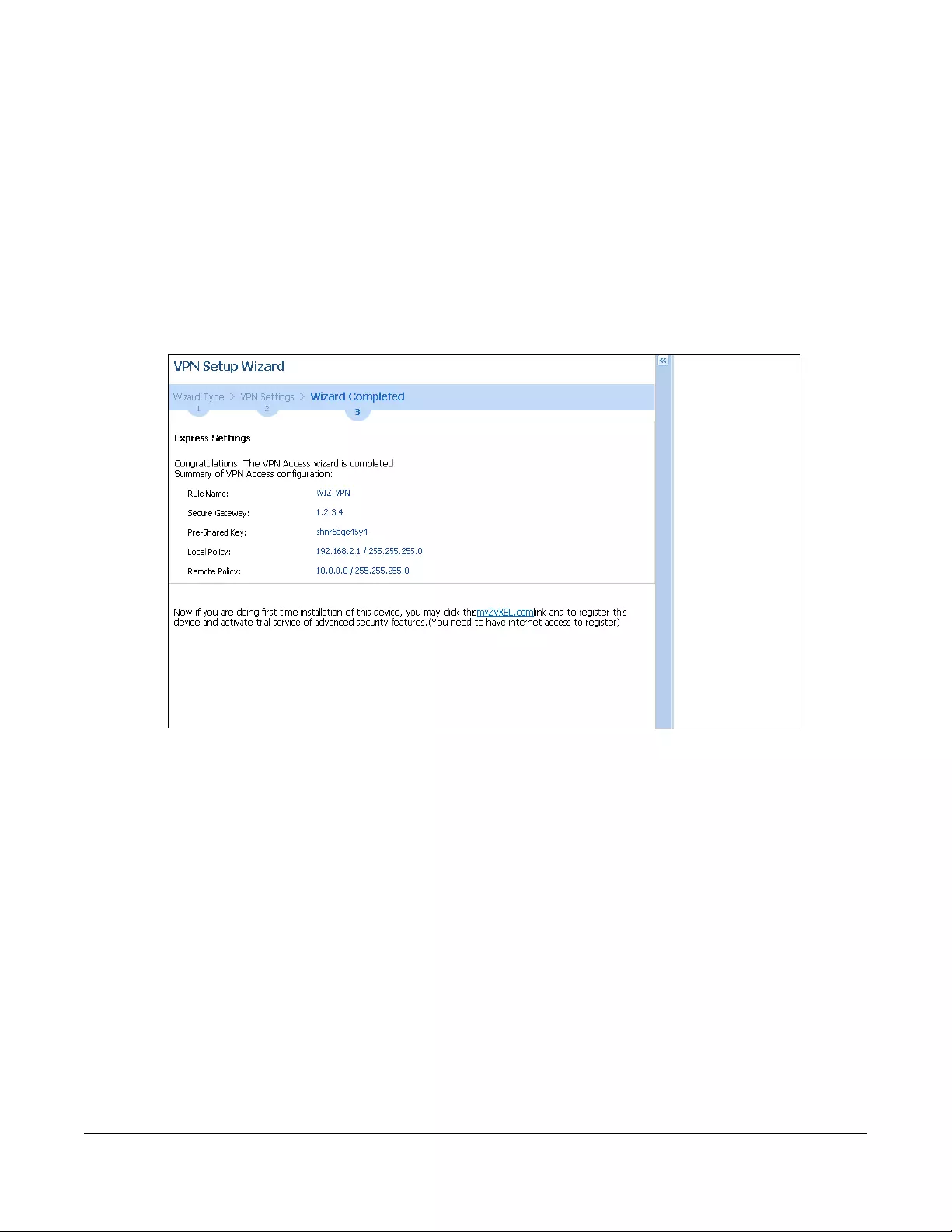
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
150
• Copy and paste the Configuration for Secure Gateway commands into another ZLD-based Zyxel
Device’s command line interface to configure it to serve as the other end of this VPN tunnel. You can
also use a text editor to save these commands as a shell script file with a “.zysh” filename extension.
Use the file manager to run the script in order to configure the VPN connection. See the commands
reference guide for details on the commands displayed in this list.
5.3.6 VPN Express Wizard - Finish
Now the rule is configured on the Zyxel Device. The Phase 1 rule settings appear in the VPN > IPSec VPN
> VPN Gateway screen and the Phase 2 rule settings appear in the VPN > IPSec VPN > VPN Connection
screen.
Figure 125 VPN Express Wizard: Finish
Click Close to exit the wizard.
5.3.7 VPN Advanced Wizard - Scenario
Click the Advanced radio button as shown in Figure 121 on page 147 to display the following screen.
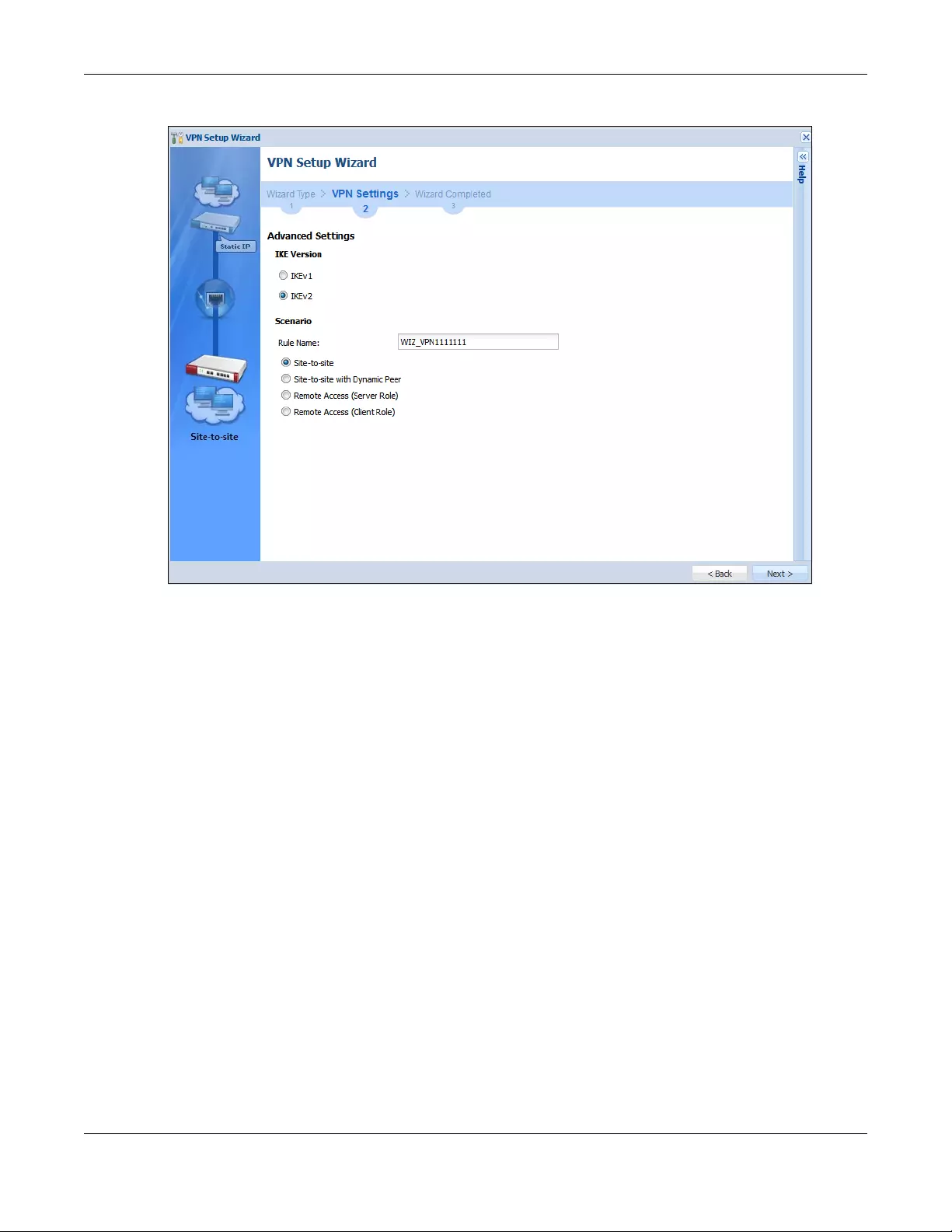
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
151
Figure 126 VPN Advanced Wizard: Scenario
IKE (Internet Key Exchange) Version: IKEv1 and IKEv2
IKE (Internet Key Exchange) is a protocol used in security associations to send data securely. IKE uses
certificates or pre-shared keys for authentication and a Diffie–Hellman key exchange to set up a shared
session secret from which encryption keys are derived.
IKEv2 supports Extended Authentication Protocol (EAP) authentication, and IKEv1 supports X-Auth. EAP is
important when connecting to existing enterprise authentication systems.
Scenario
Rule Name: Type the name used to identify this VPN connection (and VPN gateway). You may use 1-31
alphanumeric characters, underscores (_), or dashes (-), but the first character cannot be a number.
This value is case-sensitive.
Select the scenario that best describes your intended VPN connection. The figure on the left of the
screen changes to match the scenario you select.
•Site-to-site - The remote IPSec device has a static IP address or a domain name. This Zyxel Device can
initiate the VPN tunnel.
•Site-to-site with Dynamic Peer - The remote IPSec device has a dynamic IP address. Only the remote
IPSec device can initiate the VPN tunnel.
•Remote Access (Server Role) - Allow incoming connections from IPSec VPN clients. The clients have
dynamic IP addresses and are also known as dial-in users. Only the clients can initiate the VPN tunnel.
•Remote Access (Client Role) - Connect to an IPSec server. This Zyxel Device is the client (dial-in user)
and can initiate the VPN tunnel.
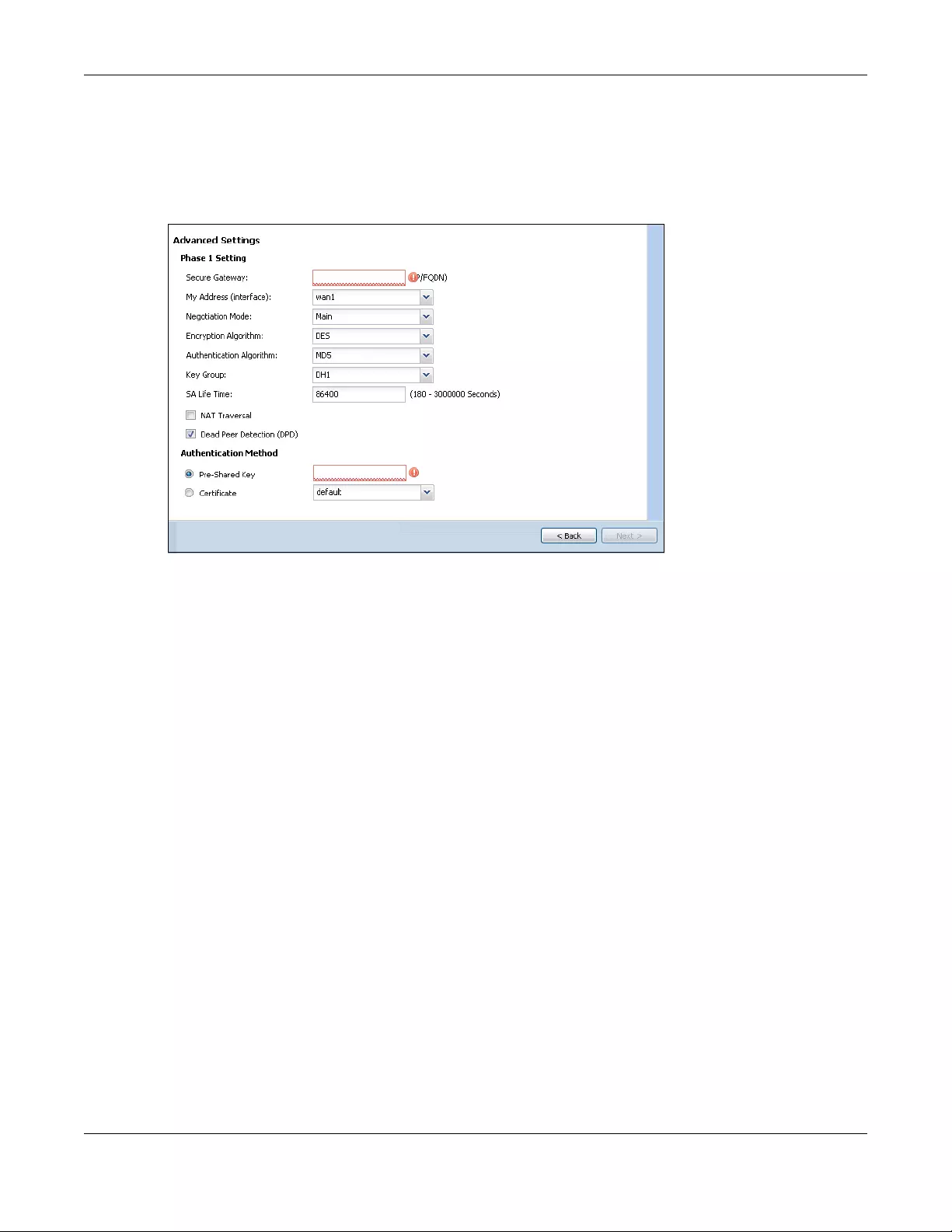
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
152
5.3.8 VPN Advanced Wizard - Phase 1 Settings
There are two phases to every IKE (Internet Key Exchange) negotiation – phase 1 (Authentication) and
phase 2 (Key Exchange). A phase 1 exchange establishes an IKE SA (Security Association).
Figure 127 VPN Advanced Wizard: Phase 1 Settings
•Secure Gateway: Any displays in this field if it is not configurable for the chosen scenario. Otherwise,
enter the WAN IP address or domain name of the remote IPSec device (secure gateway) to identify
the remote IPSec device by its IP address or a domain name. Use 0.0.0.0 if the remote IPSec device
has a dynamic WAN IP address.
•My Address (interface): Select an interface from the drop-down list box to use on your Zyxel Device.
•Negotiation Mode: This displays Main or Aggressive:
•Main encrypts the ZyWALL/USG’s and remote IPSec router’s identities but takes more time to
establish the IKE SA
•Aggressive is faster but does not encrypt the identities.
The ZyWALL/USG and the remote IPSec router must use the same negotiation mode. Multiple SAs
connecting through a secure gateway must have the same negotiation mode.
•Encryption Algorithm: 3DES and AES use encryption. The longer the key, the higher the security (this
may affect throughput). Both sender and receiver must use the same secret key, which can be used
to encrypt and decrypt the message or to generate and verify a message authentication code. The
DES encryption algorithm uses a 56-bit key. Triple DES (3DES) is a variation on DES that uses a 168-bit
key. As a result, 3DES is more secure than DES. It also requires more processing power, resulting in
increased latency and decreased throughput. AES128 uses a 128-bit key and is faster than 3DES.
AES192 uses a 192-bit key, and AES256 uses a 256-bit key.
•Authentication Algorithm: MD5 gives minimal security and SHA512 gives the highest security. MD5
(Message Digest 5) and SHA (Secure Hash Algorithm) are hash algorithms used to authenticate
packet data. The stronger the algorithm the slower it is.
•Key Group: DH5 is more secure than DH1 or DH2 (although it may affect throughput). DH1 (default)
refers to Diffie-Hellman Group 1 a 768 bit random number. DH2 refers to Diffie-Hellman Group 2 a 1024
bit (1Kb) random number. DH5 refers to Diffie-Hellman Group 5 a 1536 bit random number.
•SA Life Time: Set how often the Zyxel Device renegotiates the IKE SA. A short SA life time increases
security, but renegotiation temporarily disconnects the VPN tunnel.

Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
153
•NAT Traversal: Select this if the VPN tunnel must pass through NAT (there is a NAT router between the
IPSec devices).
Note: The remote IPSec device must also have NAT traversal enabled. See the help in the
main IPSec VPN screens for more information.
•Dead Peer Detection (DPD) has the Zyxel Device make sure the remote IPSec device is there before
transmitting data through the IKE SA. If there has been no traffic for at least 15 seconds, the Zyxel
Device sends a message to the remote IPSec device. If it responds, the Zyxel Device transmits the
data. If it does not respond, the Zyxel Device shuts down the IKE SA.
•Authentication Method: Select Pre-Shared Key to use a password or Certificate to use one of the Zyxel
Device’s certificates.
5.3.9 VPN Advanced Wizard - Phase 2
Phase 2 in an IKE uses the SA that was established in phase 1 to negotiate SAs for IPSec.
Figure 128 VPN Advanced Wizard: Phase 2 Settings
•Active Protocol: ESP is compatible with NAT, AH is not.
•Encapsulation: Tunnel is compatible with NAT, Transport is not.
•Encryption Algorithm: 3DES and AES use encryption. The longer the AES key, the higher the security
(this may affect throughput). Null uses no encryption.
•Authentication Algorithm: MD5 gives minimal security and SHA512 gives the highest security. MD5
(Message Digest 5) and SHA (Secure Hash Algorithm) are hash algorithms used to authenticate
packet data. The stronger the algorithm the slower it is.
•SA Life Time: Set how often the Zyxel Device renegotiates the IKE SA. A short SA life time increases
security, but renegotiation temporarily disconnects the VPN tunnel.
•Perfect Forward Secrecy (PFS): Disabling PFS allows faster IPSec setup, but is less secure. Select DH1,
DH2 or DH5 to enable PFS. DH5 is more secure than DH1 or DH2 (although it may affect throughput).
DH1 refers to Diffie-Hellman Group 1 a 768 bit random number. DH2 refers to Diffie-Hellman Group 2 a
1024 bit (1Kb) random number. DH5 refers to Diffie-Hellman Group 5 a 1536 bit random number (more
secure, yet slower).
•Local Policy (IP/Mask): Type the IP address of a computer on your network. You can also specify a
subnet. This must match the remote IP address configured on the remote IPSec device.
•Remote Policy (IP/Mask): Type the IP address of a computer behind the remote IPSec device. You
can also specify a subnet. This must match the local IP address configured on the remote IPSec
device.
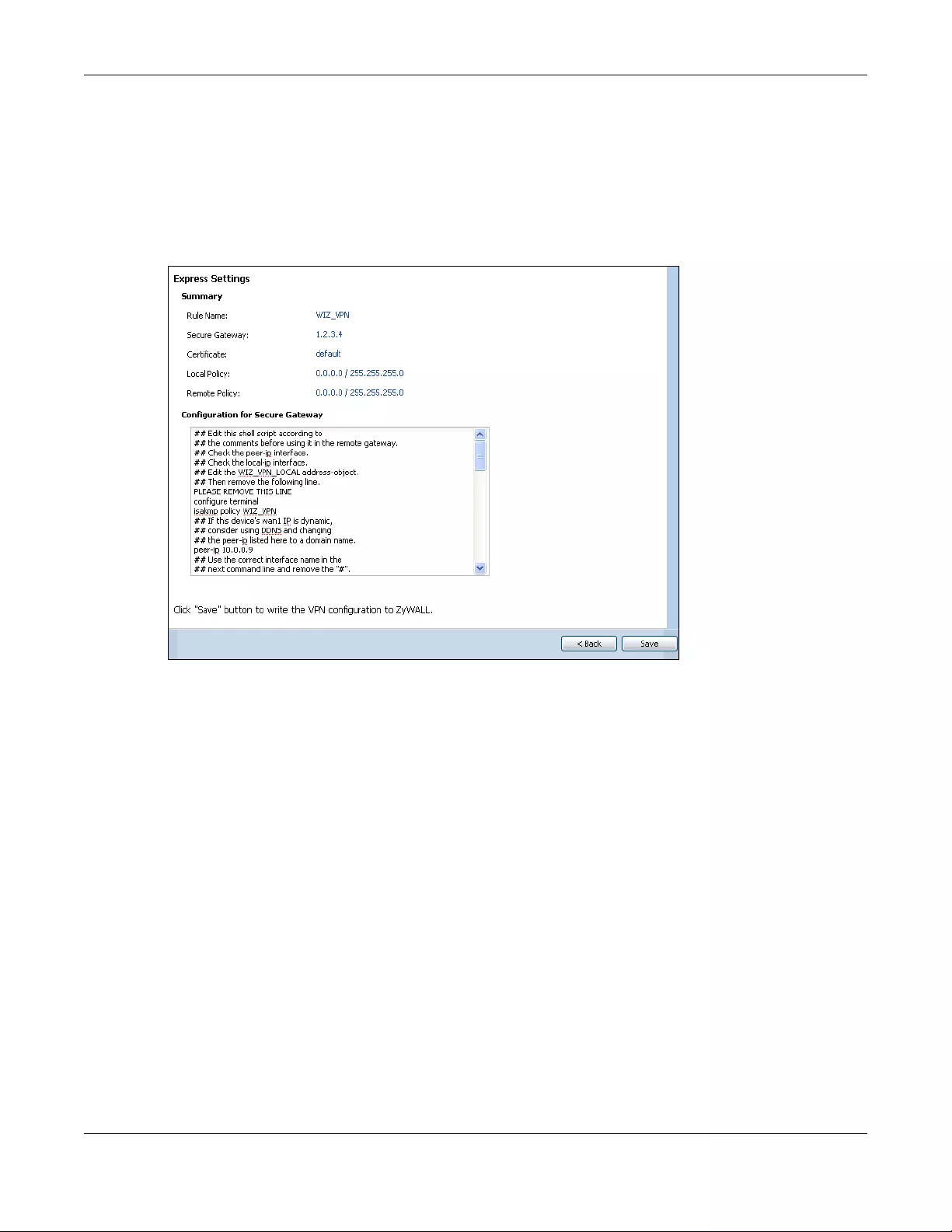
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
154
•Nailed-Up: This displays for the site-to-site and remote access client role scenarios. Select this to have
the Zyxel Device automatically renegotiate the IPSec SA when the SA life time expires.
5.3.10 VPN Advanced Wizard - Summary
This is a read-only summary of the VPN tunnel settings.
Figure 129 VPN Advanced Wizard: Summary
•Rule Name: Identifies the VPN connection (and the VPN gateway).
•Secure Gateway: IP address or domain name of the remote IPSec device.
•Pre-Shared Key: VPN tunnel password.
•Certificate: The certificate the Zyxel Device uses to identify itself when setting up the VPN tunnel.
•Local Policy: IP address and subnet mask of the computers on the network behind your Zyxel Device
that can use the tunnel.
•Remote Policy: IP address and subnet mask of the computers on the network behind the remote
IPSec device that can use the tunnel.
• Copy and paste the Configuration for Remote Gateway commands into another ZLD-based Zyxel
Device’s command line interface.
• Click Save to save the VPN rule.
5.3.11 VPN Advanced Wizard - Finish
Now the rule is configured on the Zyxel Device. The Phase 1 rule settings appear in the VPN > IPSec VPN
> VPN Gateway screen and the Phase 2 rule settings appear in the VPN > IPSec VPN > VPN Connection
screen.
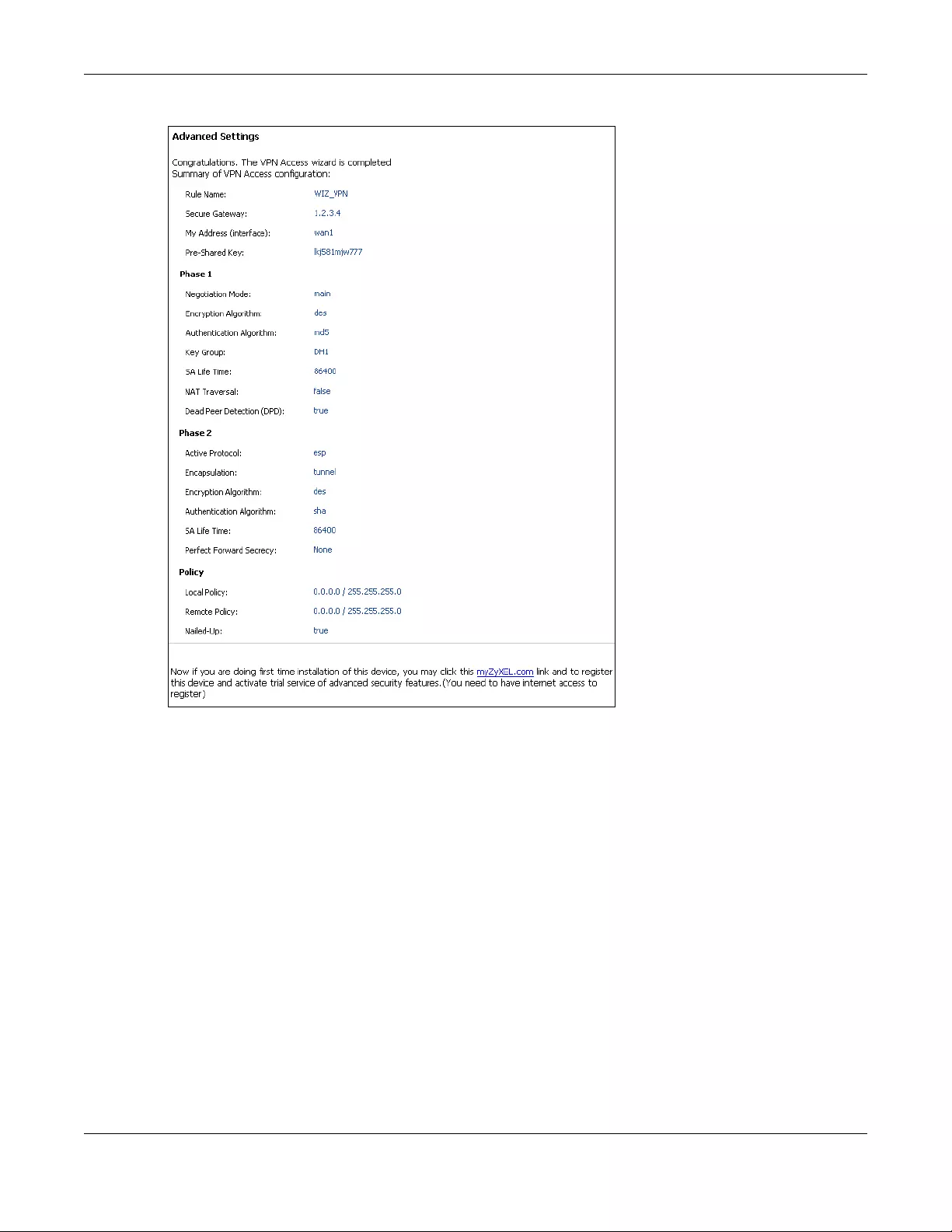
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
155
Figure 130 VPN Wizard: Finish
Click Close to exit the wizard.
5.4 VPN Settings for Configuration Provisioning Wizard:
Wizard Type
Use VPN Settings for Configuration Provisioning to set up a VPN rule that can be retrieved with the Zyxel
Device IPSec VPN Client.
VPN rules for the Zyxel Device IPSec VPN Client have certain restrictions. They must not contain the
following settings:
•AH active protocol
•NULL encryption
•SHA512 authentication
• A subnet or range remote policy
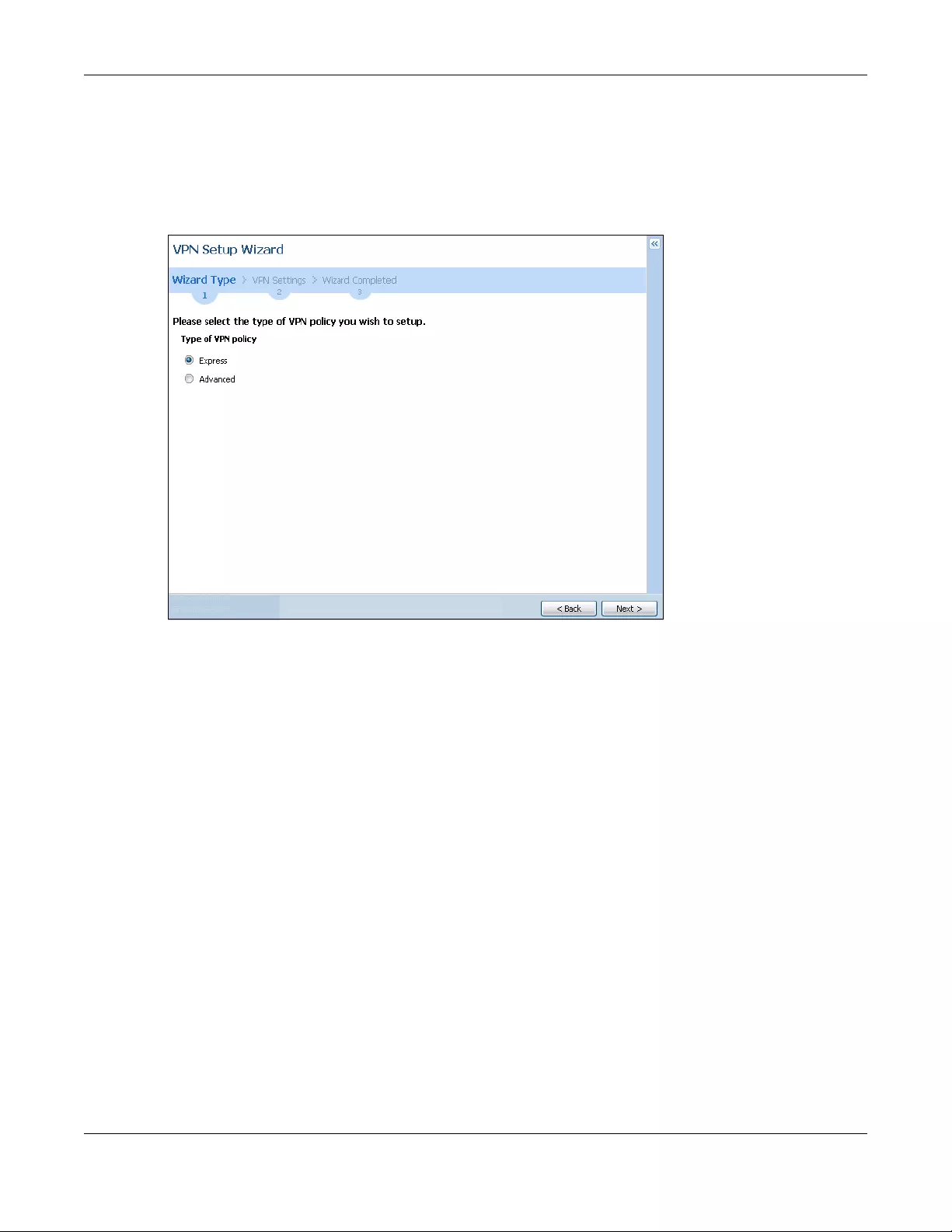
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
156
Choose Express to create a VPN rule with the default phase 1 and phase 2 settings and to use a pre-
shared key.
Choose Advanced to change the default settings and/or use certificates instead of a pre-shared key in
the VPN rule.
Figure 131 VPN Settings for Configuration Provisioning Express Wizard: Wizard Type
5.4.1 Configuration Provisioning Express Wizard - VPN Settings
Click the Express radio button as shown in the previous screen to display the following screen.
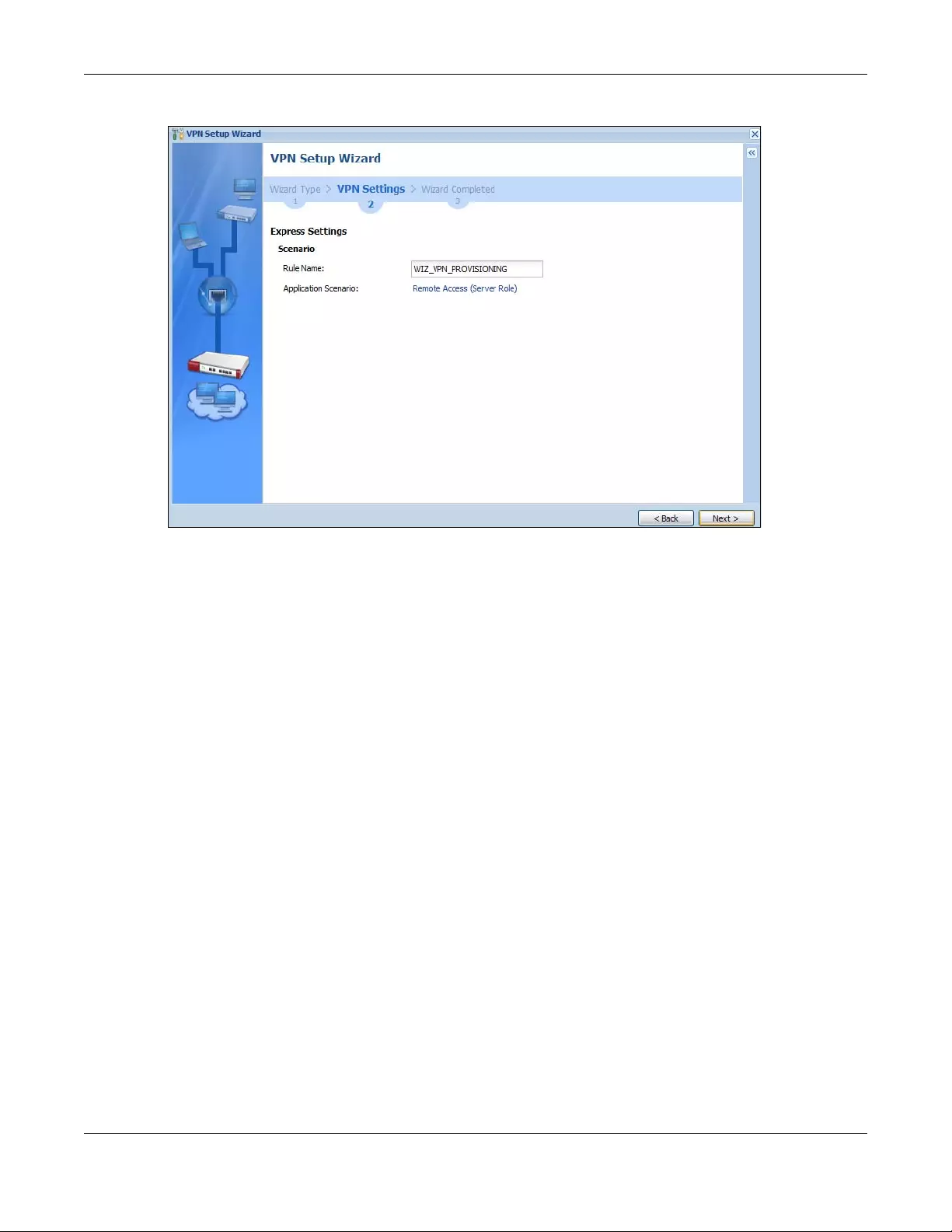
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
157
Figure 132 VPN for Configuration Provisioning Express Wizard: Settings Scenario
Rule Name: Type the name used to identify this VPN connection (and VPN gateway). You may use 1-31
alphanumeric characters, underscores (_), or dashes (-), but the first character cannot be a number.
This value is case-sensitive.
Application Scenario: Only the Remote Access (Server Role) is allowed in this wizard. It allows incoming
connections from the Zyxel Device IPSec VPN Client.
5.4.2 Configuration Provisioning VPN Express Wizard - Configuration
Click Next to continue the wizard.
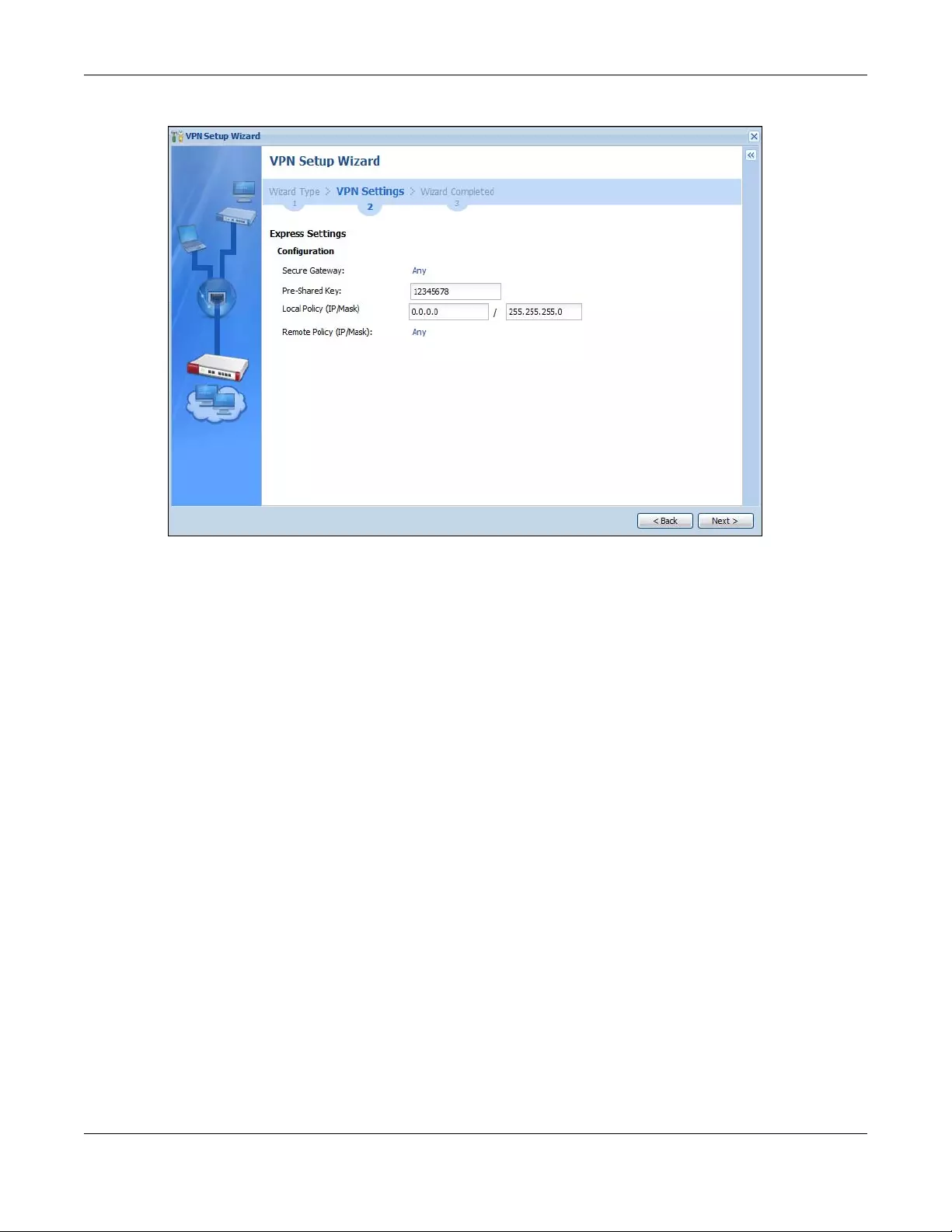
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
158
Figure 133 VPN for Configuration Provisioning Express Wizard: Configuration
•Secure Gateway: Any displays in this field because it is not configurable in this wizard. It allows
incoming connections from the Zyxel Device IPSec VPN Client.
•Pre-Shared Key: Type the password. Both ends of the VPN tunnel must use the same password. Use 8
to 31 case-sensitive ASCII characters or 8 to 31 pairs of hexadecimal (“0-9”, “A-F”) characters.
Proceed a hexadecimal key with “0x”. You will receive a PYLD_MALFORMED (payload malformed)
packet if the same pre-shared key is not used on both ends.
•Local Policy (IP/Mask): Type the IP address of a computer on your network. You can also specify a
subnet. This must match the remote IP address configured on the remote IPSec device.
•Remote Policy (IP/Mask): Any displays in this field because it is not configurable in this wizard.
5.4.3 VPN Settings for Configuration Provisioning Express Wizard - Summary
This screen has a read-only summary of the VPN tunnel’s configuration and commands you can copy
and paste into another ZLD-based Zyxel Device’s command line interface to configure it.
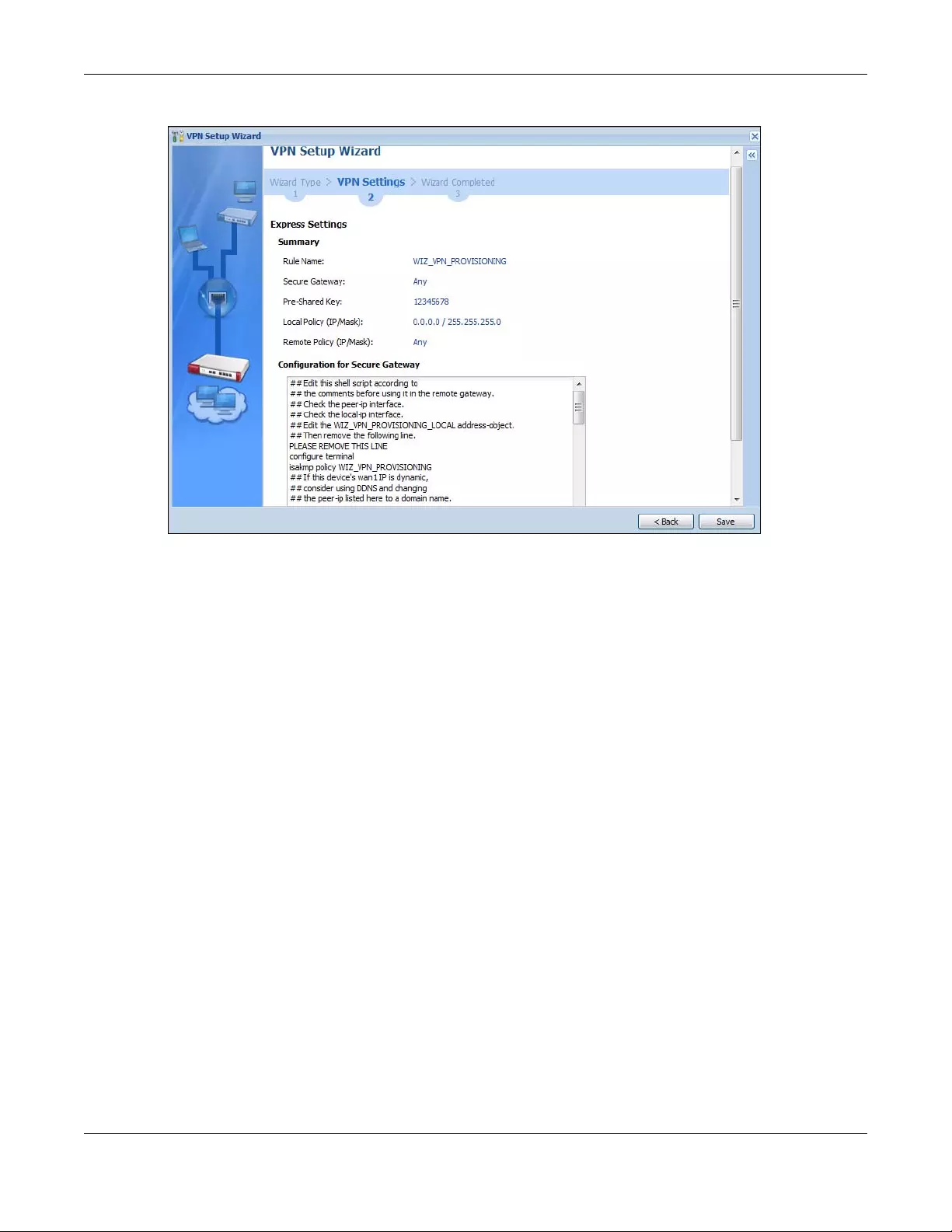
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
159
Figure 134 VPN for Configuration Provisioning Express Wizard: Summary
•Rule Name: Identifies the VPN gateway policy.
•Secure Gateway: Any displays in this field because it is not configurable in this wizard. It allows
incoming connections from the Zyxel Device IPSec VPN Client.
•Pre-Shared Key: VPN tunnel password. It identifies a communicating party during a phase 1 IKE
negotiation.
•Local Policy: (Static) IP address and subnet mask of the computers on the network behind your Zyxel
Device that can be accessed using the tunnel.
•Remote Policy: Any displays in this field because it is not configurable in this wizard.
• The Configuration for Secure Gateway displays the configuration that the Zyxel Device IPSec VPN
Client will get from the Zyxel Device.
• Click Save to save the VPN rule.
5.4.4 VPN Settings for Configuration Provisioning Express Wizard - Finish
Now the rule is configured on the Zyxel Device. The Phase 1 rule settings appear in the VPN > IPSec VPN
> VPN Gateway screen and the Phase 2 rule settings appear in the VPN > IPSec VPN > VPN Connection
screen. Enter the IP address of the Zyxel Device in the Zyxel Device IPSec VPN Client to get all these VPN
settings automatically from the Zyxel Device.
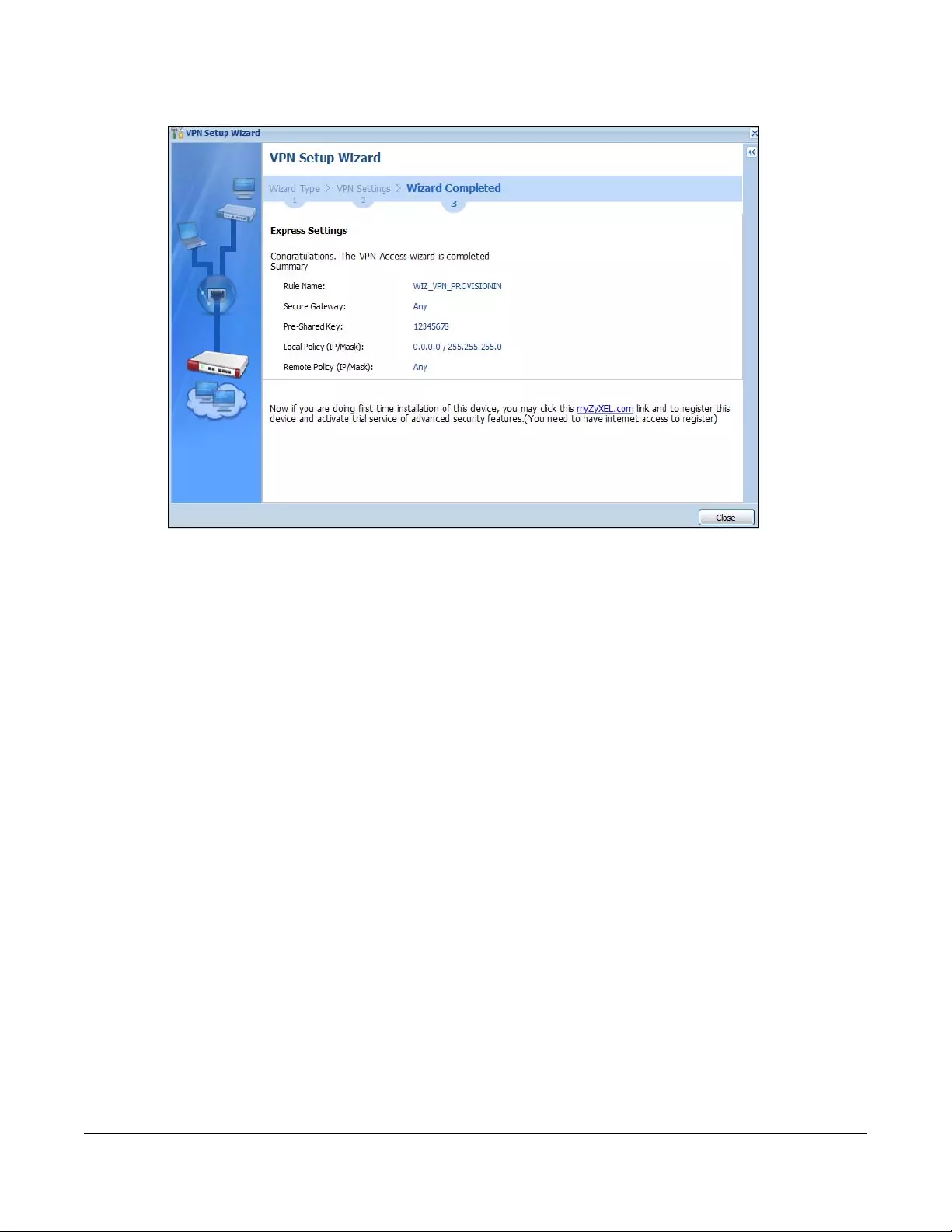
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
160
Figure 135 VPN for Configuration Provisioning Express Wizard: Finish
Click Close to exit the wizard.
5.4.5 VPN Settings for Configuration Provisioning Advanced Wizard -
Scenario
Click the Advanced radio button as shown in the screen shown in Figure 131 on page 156 to display the
following screen.
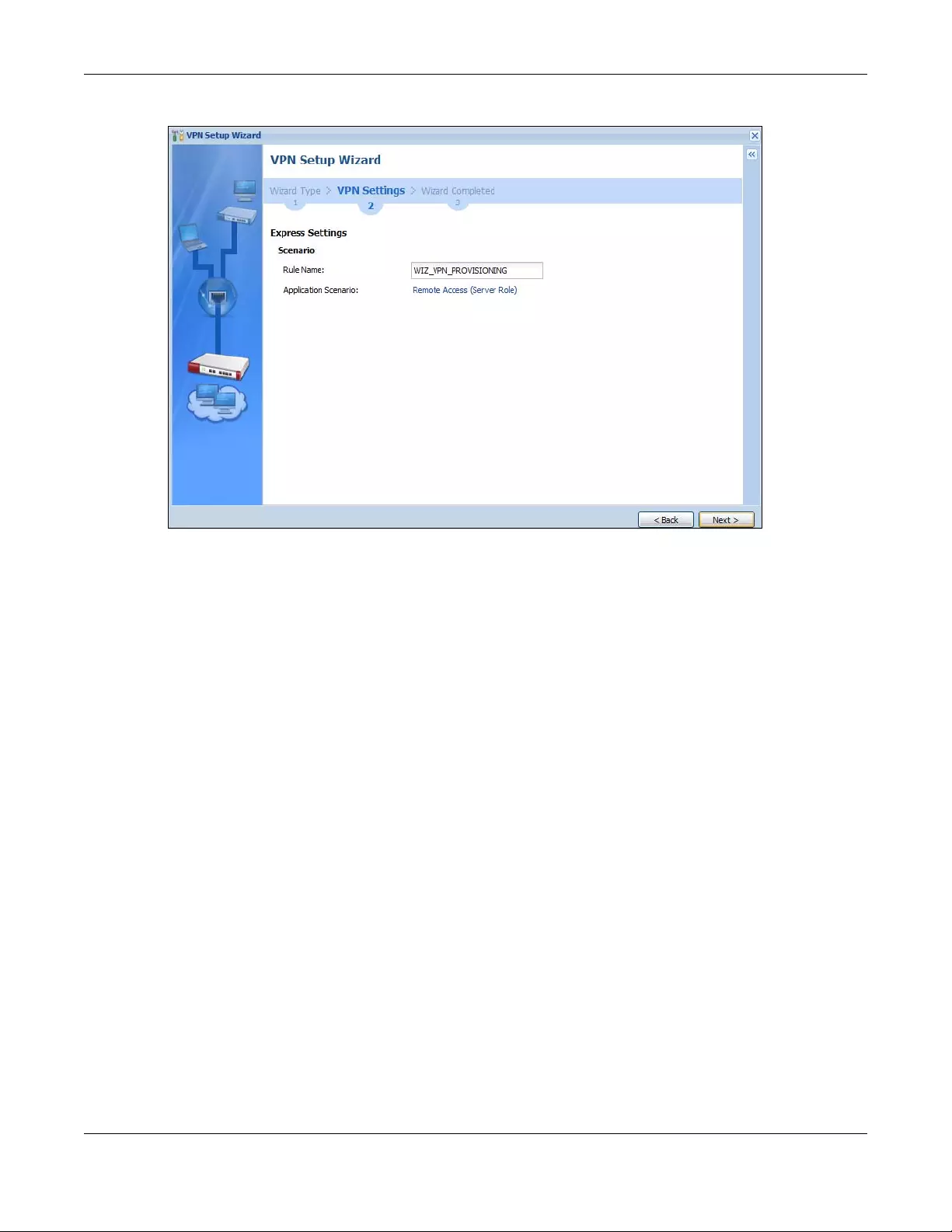
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
161
Figure 136 VPN for Configuration Provisioning Advanced Wizard: Scenario Settings
Rule Name: Type the name used to identify this VPN connection (and VPN gateway). You may use 1-31
alphanumeric characters, underscores (_), or dashes (-), but the first character cannot be a number.
This value is case-sensitive.
Application Scenario: Only the Remote Access (Server Role) is allowed in this wizard. It allows incoming
connections from the Zyxel Device IPSec VPN Client.
Click Next to continue the wizard.
5.4.6 VPN Settings for Configuration Provisioning Advanced Wizard - Phase
1 Settings
There are two phases to every IKE (Internet Key Exchange) negotiation – phase 1 (Authentication) and
phase 2 (Key Exchange). A phase 1 exchange establishes an IKE SA (Security Association).
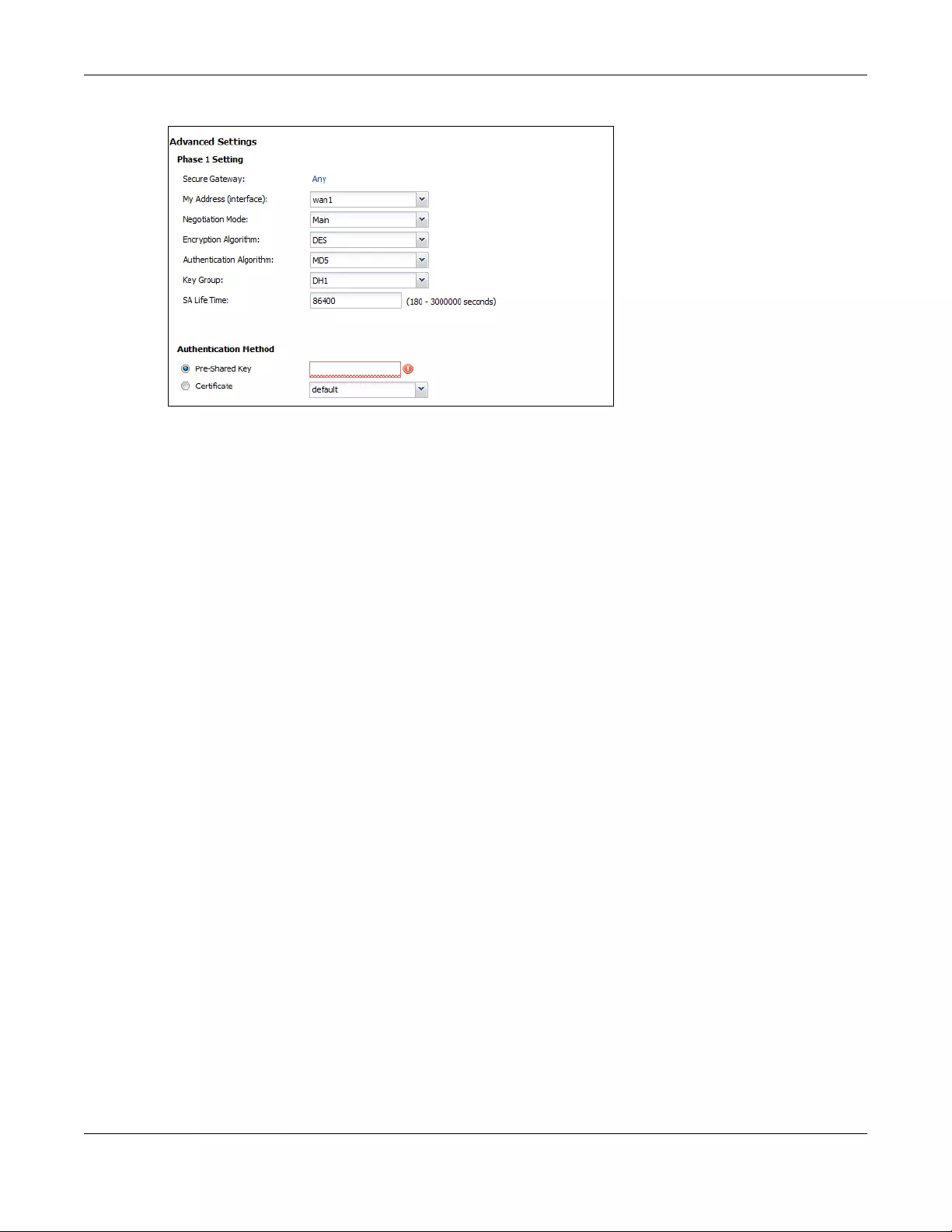
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
162
Figure 137 VPN for Configuration Provisioning Advanced Wizard: Phase 1 Settings
•Secure Gateway: Any displays in this field because it is not configurable in this wizard. It allows
incoming connections from the Zyxel Device IPSec VPN Client.
•My Address (interface): Select an interface from the drop-down list box to use on your Zyxel Device.
•Negotiation Mode: This displays Main or Aggressive:
•Main encrypts the ZyWALL/USG’s and remote IPSec router’s identities but takes more time to
establish the IKE SA
•Aggressive is faster but does not encrypt the identities.
The ZyWALL/USG and the remote IPSec router must use the same negotiation mode. Multiple SAs
connecting through a secure gateway must have the same negotiation mode.
•Encryption Algorithm: 3DES and AES use encryption. The longer the key, the higher the security (this
may affect throughput). Both sender and receiver must know the same secret key, which can be
used to encrypt and decrypt the message or to generate and verify a message authentication code.
The DES encryption algorithm uses a 56-bit key. Triple DES (3DES) is a variation on DES that uses a 168-
bit key. As a result, 3DES is more secure than DES. It also requires more processing power, resulting in
increased latency and decreased throughput. AES128 uses a 128-bit key and is faster than 3DES.
AES192 uses a 192-bit key and AES256 uses a 256-bit key.
•Authentication Algorithm: MD5 (Message Digest 5) and SHA (Secure Hash Algorithm) are hash
algorithms used to authenticate packet data. MD5 gives minimal security. SHA1 gives higher security
and SHA256 gives the highest security. The stronger the algorithm, the slower it is.
•Key Group: DH5 is more secure than DH1 or DH2 (although it may affect throughput). DH1 (default)
refers to Diffie-Hellman Group 1 a 768 bit random number. DH2 refers to Diffie-Hellman Group 2 a 1024
bit (1Kb) random number. DH5 refers to Diffie-Hellman Group 5 a 1536 bit random number.
•SA Life Time: Set how often the Zyxel Device renegotiates the IKE SA. A short SA life time increases
security, but renegotiation temporarily disconnects the VPN tunnel.
•Authentication Method: Select Pre-Shared Key to use a password or Certificate to use one of the Zyxel
Device’s certificates.
5.4.7 VPN Settings for Configuration Provisioning Advanced Wizard - Phase
2
Phase 2 in an IKE uses the SA that was established in phase 1 to negotiate SAs for IPSec.
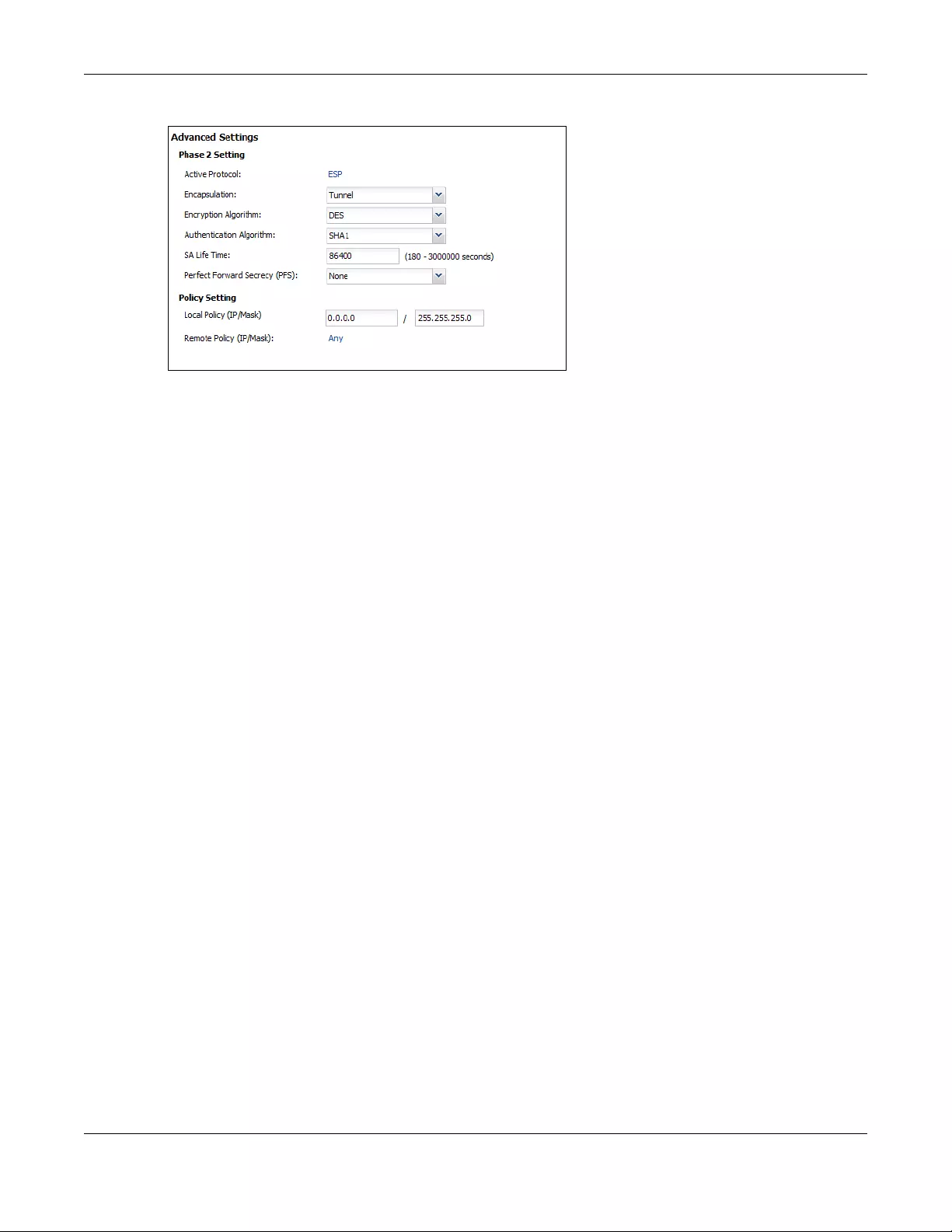
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
163
Figure 138 VPN for Configuration Provisioning Advanced Wizard: Phase 2 Settings
•Active Protocol: ESP is compatible with NAT. AH is not available in this wizard.
•Encapsulation: Tunnel is compatible with NAT, Transport is not.
•Encryption Algorithm: 3DES and AES use encryption. The longer the AES key, the higher the security
(this may affect throughput). Null uses no encryption.
•Authentication Algorithm: MD5 (Message Digest 5) and SHA (Secure Hash Algorithm) are hash
algorithms used to authenticate packet data. MD5 gives minimal security. SHA1 gives higher security
and SHA256 gives the highest security. The stronger the algorithm, the slower it is.
•SA Life Time: Set how often the Zyxel Device renegotiates the IKE SA. A short SA life time increases
security, but renegotiation temporarily disconnects the VPN tunnel.
•Perfect Forward Secrecy (PFS): Disabling PFS allows faster IPSec setup, but is less secure. Select DH1,
DH2 or DH5 to enable PFS. DH5 is more secure than DH1 or DH2 (although it may affect throughput).
DH1 refers to Diffie-Hellman Group 1 a 768 bit random number. DH2 refers to Diffie-Hellman Group 2 a
1024 bit (1Kb) random number. DH5 refers to Diffie-Hellman Group 5 a 1536 bit random number (more
secure, yet slower).
•Local Policy (IP/Mask): Type the IP address of a computer on your network. You can also specify a
subnet. This must match the remote IP address configured on the remote IPSec device.
•Remote Policy (IP/Mask): Any displays in this field because it is not configurable in this wizard.
•Nailed-Up: This displays for the site-to-site and remote access client role scenarios. Select this to have
the Zyxel Device automatically renegotiate the IPSec SA when the SA life time expires.
5.4.8 VPN Settings for Configuration Provisioning Advanced Wizard -
Summary
This is a read-only summary of the VPN tunnel settings.
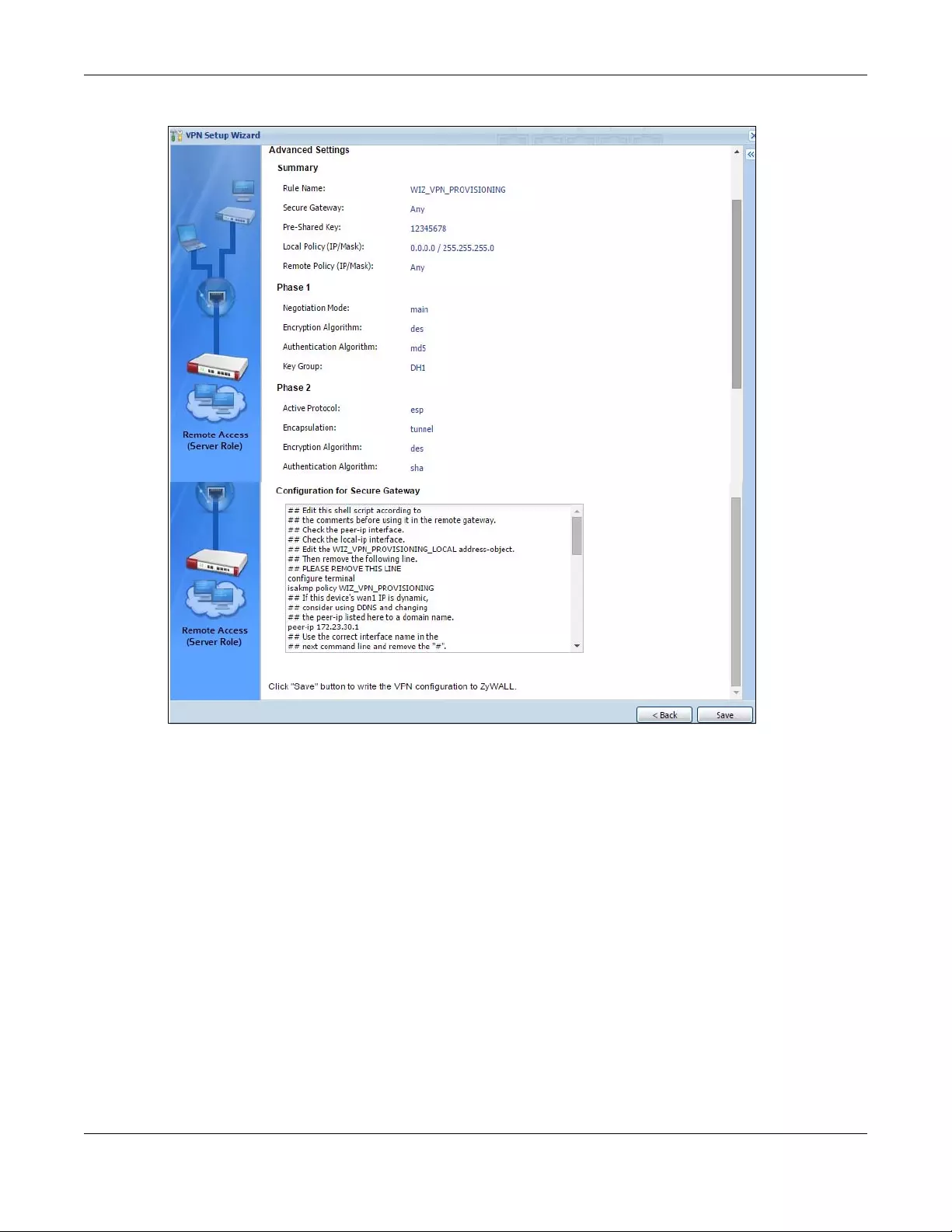
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
164
Figure 139 VPN for Configuration Provisioning Advanced Wizard: Summary
Summary
•Rule Name: Identifies the VPN connection (and the VPN gateway).
•Secure Gateway: Any displays in this field because it is not configurable in this wizard. It allows
incoming connections from the Zyxel Device IPSec VPN Client.
•Pre-Shared Key: VPN tunnel password.
•Local Policy: IP address and subnet mask of the computers on the network behind your Zyxel Device
that can use the tunnel.
•Remote Policy: Any displays in this field because it is not configurable in this wizard.
Phase 1
•Negotiation Mode: This displays Main or Aggressive:
•Main encrypts the ZyWALL/USG’s and remote IPSec router’s identities but takes more time to
establish the IKE SA
•Aggressive is faster but does not encrypt the identities.
The ZyWALL/USG and the remote IPSec router must use the same negotiation mode. Multiple SAs
connecting through a secure gateway must have the same negotiation mode.

Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
165
•Encryption Algorithm: This displays the encryption method used. The longer the key, the higher the
security, the lower the throughput (possibly).
•DES uses a 56-bit key.
•3DES uses a 168-bit key.
•AES128 uses a 128-bit key
•AES192 uses a 192-bit key
•AES256 uses a 256-bit key.
•Authentication Algorithm: This displays the authentication algorithm used. The stronger the algorithm,
the slower it is.
•MD5 gives minimal security.
•SHA1 gives higher security
•SHA256 gives the highest security.
•Key Group: This displays the Diffie-Hellman (DH) key group used. DH5 is more secure than DH1 or DH2
(although it may affect throughput).
•DH1 uses a 768 bit random number.
•DH2 uses a 1024 bit (1Kb) random number.
•DH5 uses a 1536 bit random number.
Phase 2
•Active Protocol: This displays ESP (compatible with NAT) or AH.
•Encapsulation: This displays Tunnel (compatible with NAT) or Transport.
•Encryption Algorithm: This displays the encryption method used. The longer the key, the higher the
security, the lower the throughput (possibly).
•DES uses a 56-bit key.
•3DES uses a 168-bit key.
•AES128 uses a 128-bit key
•AES192 uses a 192-bit key
•AES256 uses a 256-bit key.
•Null uses no encryption.
•Authentication Algorithm: This displays the authentication algorithm used. The stronger the algorithm,
the slower it is.
•MD5 gives minimal security.
•SHA1 gives higher security
•SHA256 gives the highest security.
The Configuration for Secure Gateway displays the configuration that the Zyxel Device IPSec VPN Client
will get from the Zyxel Device.
Click Save to save the VPN rule.
5.4.9 VPN Settings for Configuration Provisioning Advanced Wizard- Finish
Now the rule is configured on the Zyxel Device. The Phase 1 rule settings appear in the VPN > IPSec VPN
> VPN Gateway screen and the Phase 2 rule settings appear in the VPN > IPSec VPN > VPN Connection
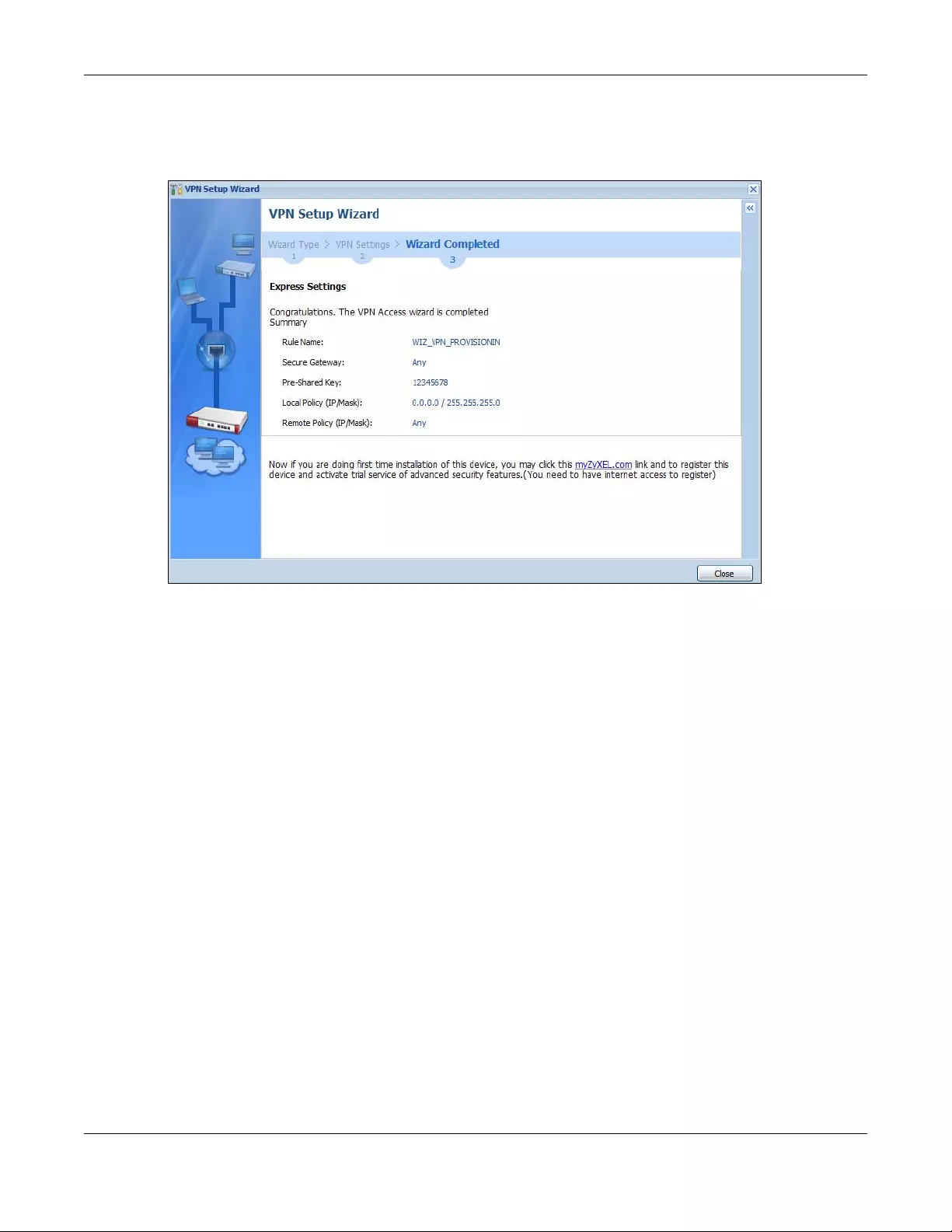
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
166
screen. Enter the IP address of the Zyxel Device in the Zyxel Device IPSec VPN Client to get all these VPN
settings automatically from the Zyxel Device.
Figure 140 VPN for Configuration Provisioning Advanced Wizard: Finish
Click Close to exit the wizard.
5.5 VPN Settings for L2TP VPN Settings Wizard
Use VPN Settings for L2TP VPN Settings to set up an L2TP VPN rule. Click Configuration > Quick Setup >
VPN Settings and select VPN Settings for L2TP VPN Settings to see the following screen.
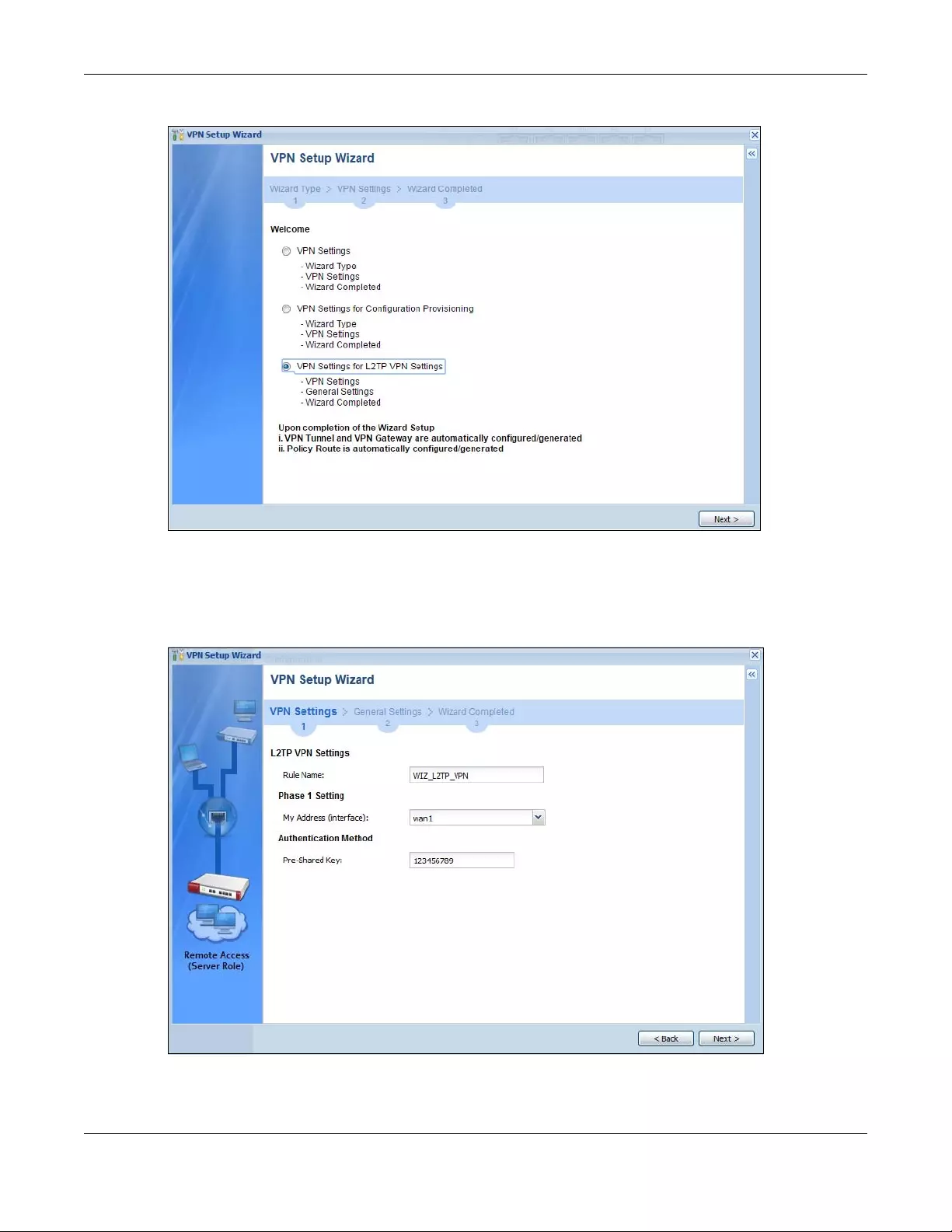
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
167
Figure 141 VPN Settings for L2TP VPN Settings Wizard: L2TP VPN Settings
Click Next to continue the wizard.
5.5.1 L2TP VPN Settings
Figure 142 VPN Settings for L2TP VPN Settings Wizard: L2TP VPN Settings
•Rule Name: Type the name used to identify this L2TP VPN connection (and L2TP VPN gateway). You
may use 1-31 alphanumeric characters, underscores (_), or dashes (-), but the first character cannot
be a number. This value is case-sensitive.
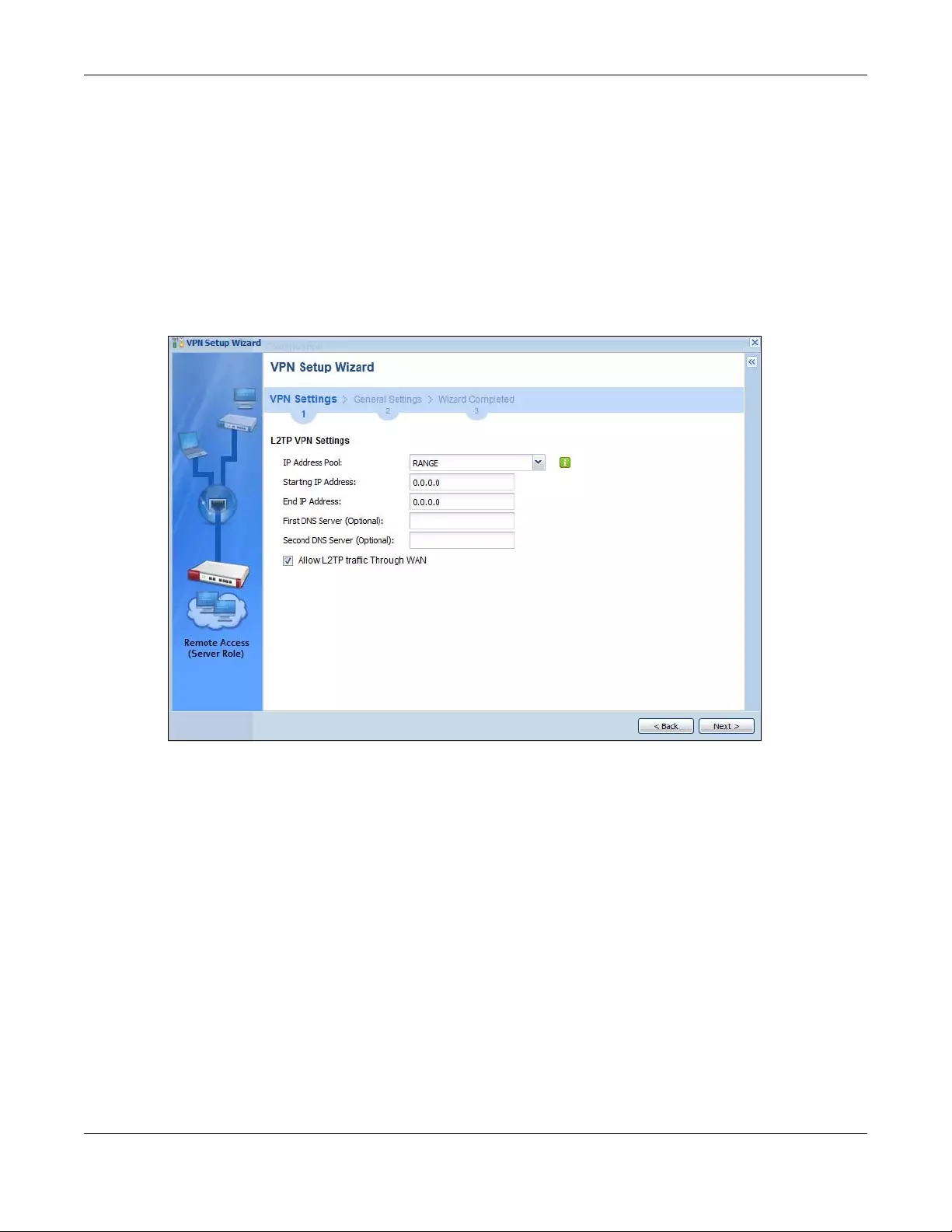
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
168
•My Address (interface): Select one of the interfaces from the pull down menu to apply the L2TP VPN
rule.
•Pre-Shared Key: Type the password. Both ends of the VPN tunnel must use the same password. Use 8
to 31 case-sensitive ASCII characters or 8 to 31 pairs of hexadecimal (“0-9”, “A-F”) characters.
Proceed a hexadecimal key with “0x”. You will receive a PYLD_MALFORMED (payload malformed)
packet if the same pre-shared key is not used on both ends.
Click Next to continue the wizard.
5.5.2 L2TP VPN Settings
Figure 143 VPN Settings for L2TP VPN Settings Wizard: L2TP VPN Settings
•IP Address Pool: Select Range or Subnet from the pull down menu. This IP address pool is used to
assign to the L2TP VPN clients.
•Starting IP Address: Enter the starting IP address in the field.
•End IP Address: Enter the ending IP address in the field.
•First DNS Server (Optional): Enter the first DNS server IP address in the field. Leave the filed as 0.0.0.0 if
you do not want to configure DNS servers. If you do not configure a DNS server you must know the IP
address of a machine in order to access it.
•Second DNS Server (Optional): Enter the second DNS server IP address in the field. Leave the filed as
0.0.0.0 if you do not want to configure DNS servers. If you do not configure a DNS server you must
know the IP address of a machine in order to access it.
•Allow L2TP traffic Through WAN: Select this check box to allow traffic from L2TP clients to go to the
Internet.
Click Next to continue the wizard.
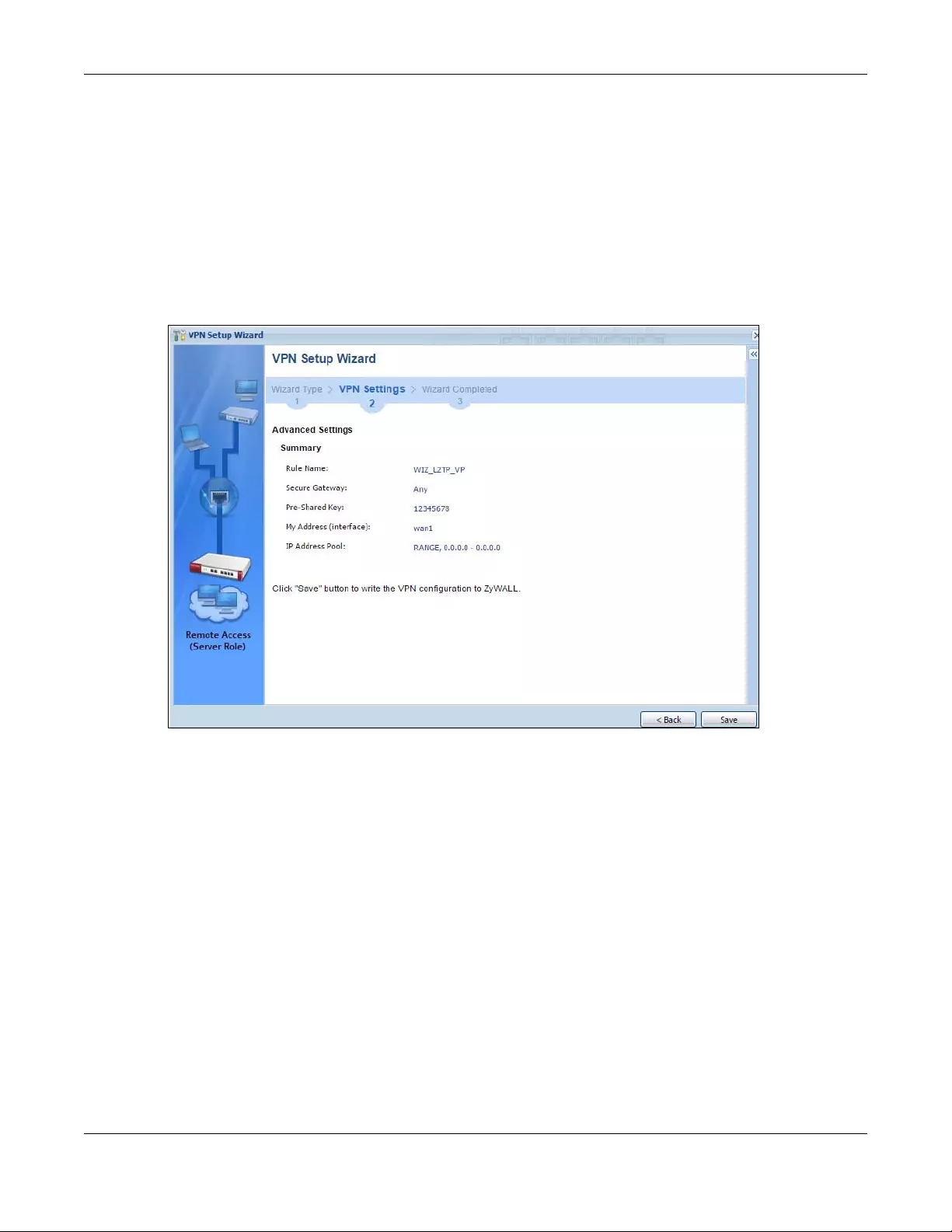
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
169
Note: DNS (Domain Name System) is for mapping a domain name to its corresponding IP
address and vice versa. The DNS server is extremely important because without it, you
must know the IP address of a computer before you can access it. The Zyxel Device
uses a system DNS server (in the order you specify here) to resolve domain names for
VPN, DDNS and the time server.
5.5.3 VPN Settings for L2TP VPN Setting Wizard - Summary
This is a read-only summary of the L2TP VPN settings.
Figure 144 VPN Settings for L2TP VPN Settings Advanced Settings Wizard: Summary
Summary
•Rule Name: Identifies the L2TP VPN connection (and the L2TP VPN gateway).
•Secure Gatewa “Any” displays in this field because it is not configurable in this wizard. It allows
incoming connections from the L2TP VPN Client.
•Pre-Shared Key: L2TP VPN tunnel password.
•My Address (Interface): This displays the interface to use on your Zyxel Device for the L2TP tunnel.
•IP Address Pool: This displays the IP address pool used to assign to the L2TP VPN clients.
Click Save to complete the L2TP VPN Setting and the following screen will show.
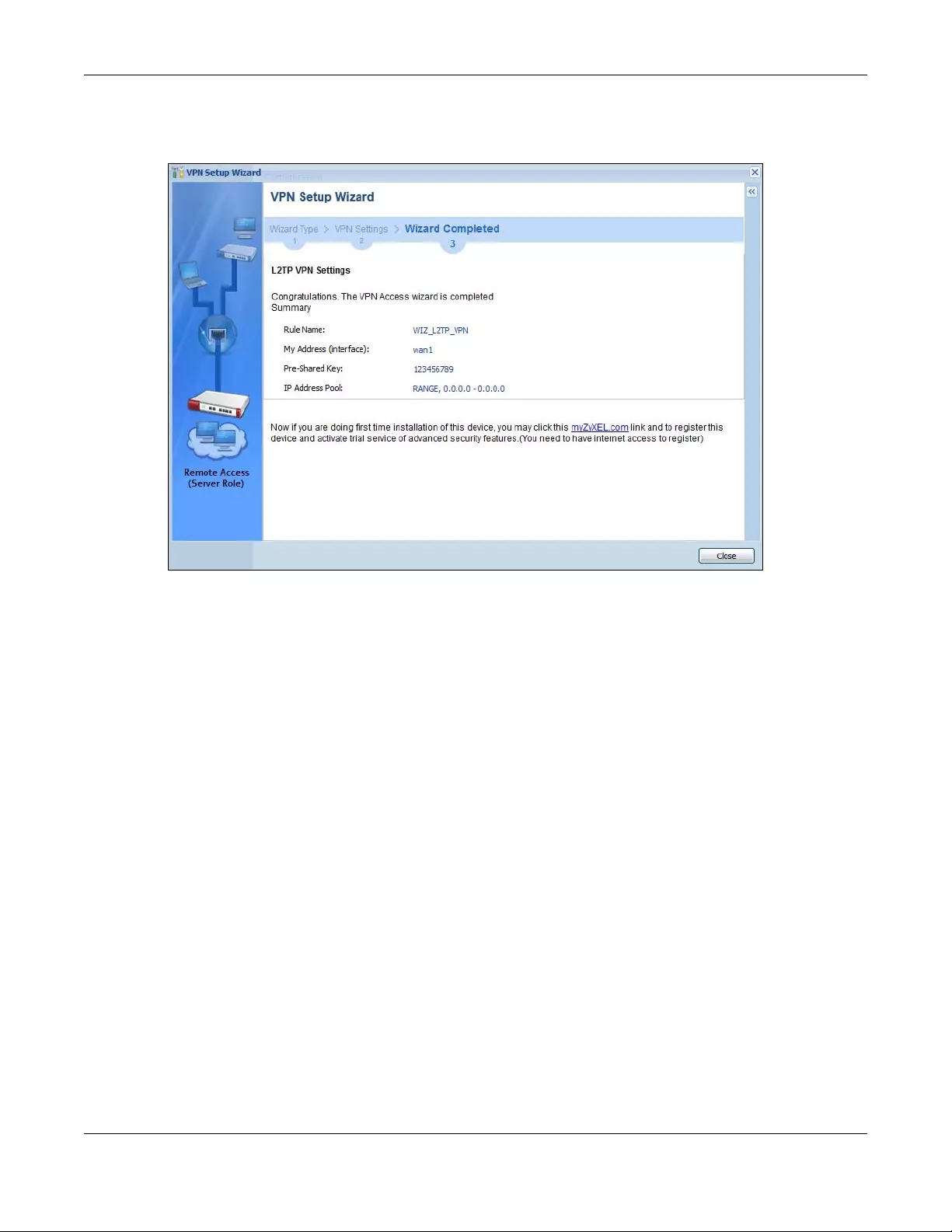
Chapter 5 Quick Setup Wizards
USG/ZyWALL User’s Guide
170
5.5.4 VPN Settings for L2TP VPN Setting Wizard Completed
Figure 145 VPN Settings for L2TP VPN Settings Wizard: Finish
Now the rule is configured on the Zyxel Device. The L2TP VPN rule settings appear in the VPN > L2TP VPN
screen and also in the VPN > IPSec VPN > VPN Connection and VPN Gateway screen.

USG/ZyWALL User’s Guide
171
CHAPTER 6
Dashboard
6.1 Overview
Use the Dashboard screens to check status information about the Zyxel Device.
6.1.1 What You Can Do in this Chapter
Use the main Dashboard screen to see the Zyxel Device’s general device information, system status,
system resource usage, licensed service status, and interface status. You can also display other status
screens for more information.
Use the Dashboard screens to view the following.
•Device Information Screen on page 173
•System Status Screen on page 174
•VPN Status Screen on page 175
•DHCP Table Screen on page 177
•Number of Login Users Screen on page 178
•System Resources Screen on page 178
•CPU Usage Screen on page 179
•Memory Usage Screen on page 180
•Active Sessions Screen on page 181
•Extension Slot Screen on page 182
•Interface Status Summary Screen on page 182
•Secured Service Status Screen on page 184
•Content Filter Statistics Screen on page 184
•Top 5 Viruses Screen on page 185
•Top 5 Intrusions Screen on page 186
•Top 5 IPv4/IPv6 Security Policy Rules that Blocked Traffic Screen on page 186
•The Latest Alert Logs Screen on page 187
6.2 Main Dashboard Screen
The Dashboard screen displays when you log into the Zyxel Device or click Dashboard in the navigation
panel. The dashboard displays general device information, system status, system resource usage,
licensed service status, and interface status in widgets that you can re-arrange to suit your needs. You
can also collapse, refresh, and close individual widgets.
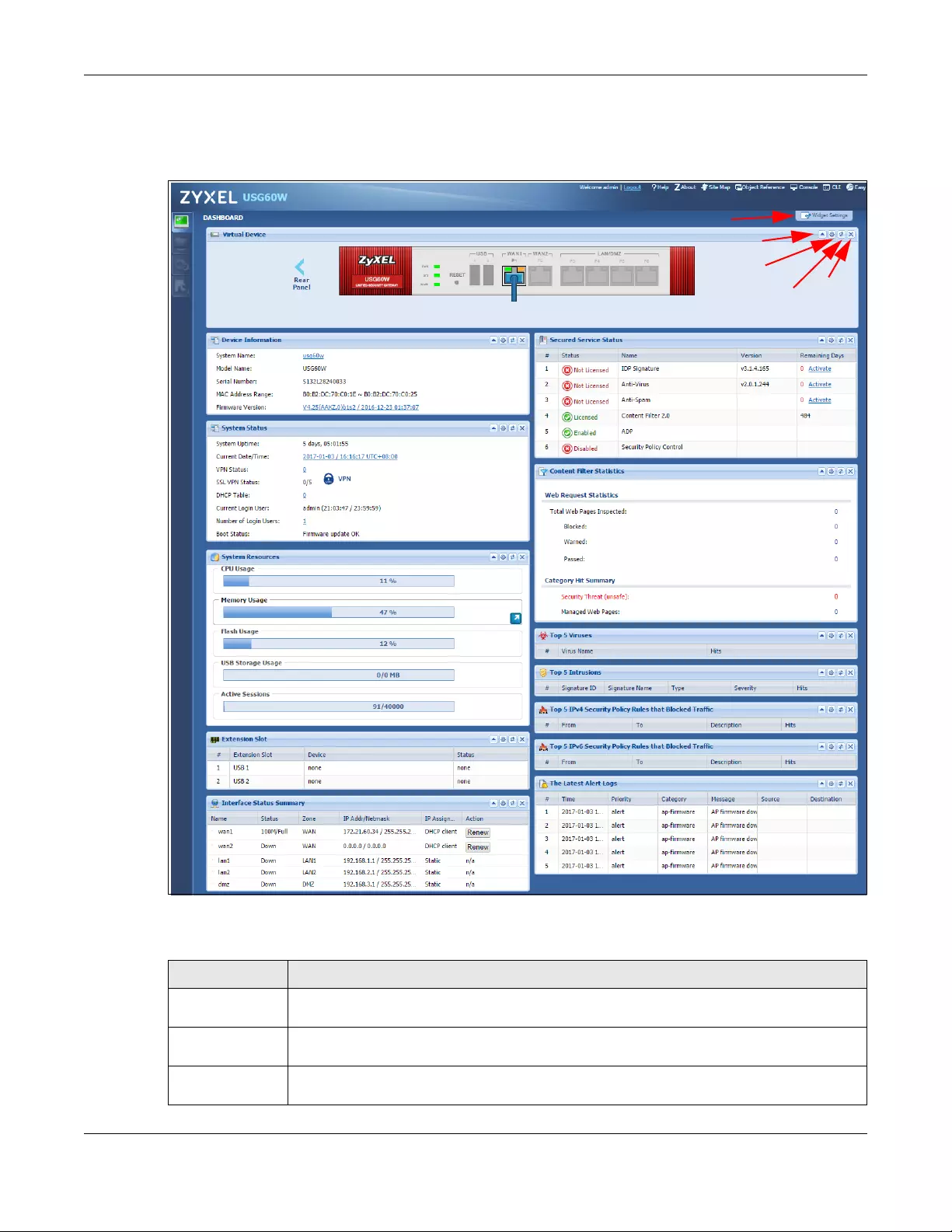
Chapter 6 Dashboard
USG/ZyWALL User’s Guide
172
Click on the icon to go to the OneSecurity.com website where there is guidance on configuration
walkthroughs, troubleshooting, and other information.
Figure 146 Dashboard
The following table describes the labels in this screen.
Table 23 Dashboard
LABEL DESCRIPTION
Widget Settings
(A)
Use this link to open or close widgets by selecting/clearing the associated checkbox.
Up Arrow (B) Click this to collapse a widget. It then becomes a down arrow. Click it again to enlarge the
widget again.
Refresh Time
Setting (C)
Set the interval for refreshing the information displayed in the widget.
AB
CDE
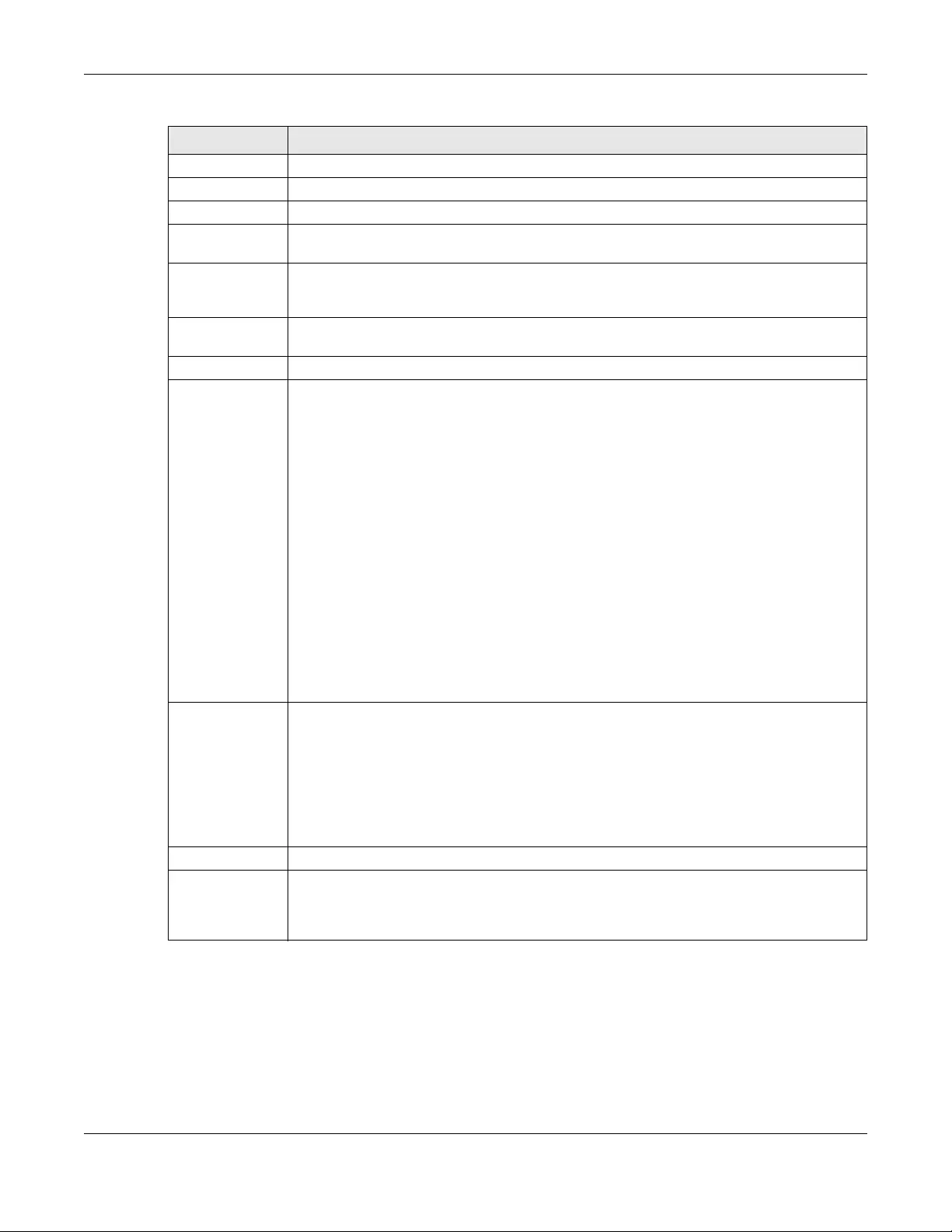
Chapter 6 Dashboard
USG/ZyWALL User’s Guide
173
6.2.1 Device Information Screen
The Device Information screen displays Zyxel Device’s system and model name, serial number, MAC
address and firmware version shown in the below screen.
Refresh Now (D) Click this to update the widget’s information immediately.
Close Widget (E) Click this to close the widget. Use Widget Settings to re-open it.
Virtual Device
Rear Panel Click this to view details about the Zyxel Device’s rear panel. Hover your cursor over a
connected interface or slot to display status details.
Front Panel Click this to view details about the status of the Zyxel Device’s front panel LEDs and
connections. See Section 3.1.1 on page 61 for LED descriptions. An unconnected interface or
slot appears grayed out.
The following front and rear panel labels display when you hover your cursor over a connected
interface or slot.
Name This field displays the name of each interface.
Status This field displays the current status of each interface or device installed in a slot. The possible
values depend on what type of interface it is.
Inactive - The Ethernet interface is disabled.
Down - The Ethernet interface does not have any physical ports associated with it or the
Ethernet interface is enabled but not connected.
Speed / Duplex - The Ethernet interface is enabled and connected. This field displays the port
speed and duplex setting (Full or Half).
The status for a WLAN card is none.
For cellular (mobile broadband) interfaces, see Section 10.6 on page 304 for the status that
can appear.
For the auxiliary interface:
Inactive - The auxiliary interface is disabled.
Connected - The auxiliary interface is enabled and connected.
Disconnected - The auxiliary interface is not connected.
HA Status This field displays the status of the interface in the virtual router.
Active - This interface is the master interface in the virtual router.
Stand-By - This interface is a backup interface in the virtual router.
Fault - This VRRP group is not functioning in the virtual router right now. For example, this might
happen if the interface is down.
n/a - Device HA is not active on the interface.
Zone This field displays the zone to which the interface is currently assigned.
IP Address/
Mask This field displays the current IP address and subnet mask assigned to the interface. If the
interface is a member of an active virtual router, this field displays the IP address it is currently
using. This is either the static IP address of the interface (if it is the master) or the management
IP address (if it is a backup).
Table 23 Dashboard (continued)
LABEL DESCRIPTION
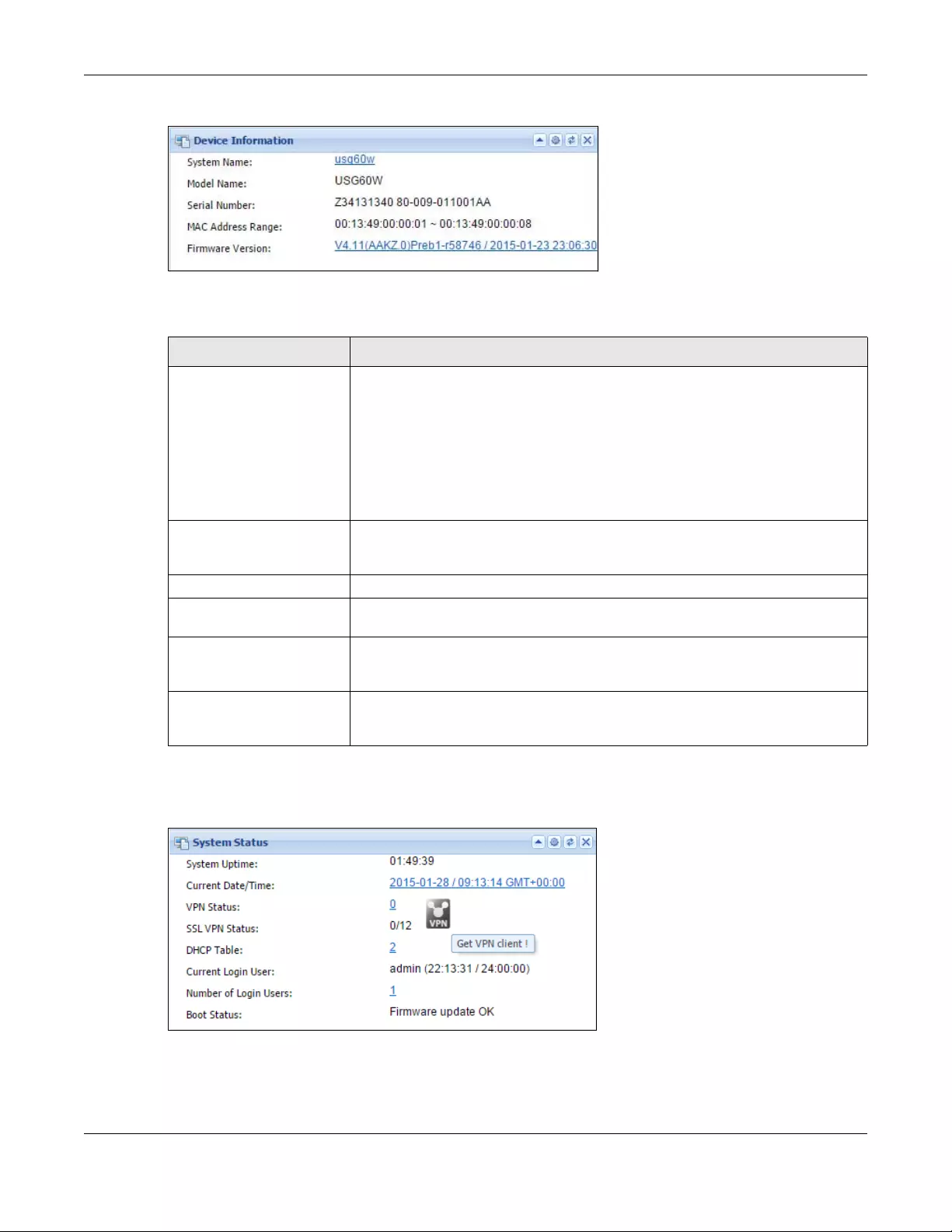
Chapter 6 Dashboard
USG/ZyWALL User’s Guide
174
Figure 147 Dashboard > Device Information (Example)
This table describes the fields in the above screen.
6.2.2 System Status Screen
Figure 148 Dashboard > System Status (Example)
Table 24 Dashboard > Device Information
LABEL DESCRIPTION
Device Information This identifies a device installed in one of the Zyxel Device’s extension slots, the
Security Extension Module slot, or USB ports. For an installed SEM (Security Extension
Module) card, this field displays what kind of SEM card is installed.
SEM-VPN - The VPN accelerator. The SEM-VPN provides 500 Mbps VPN throughput,
2,000 IPSec VPN tunnels, and 750 SSL VPN users.
SEM-DUAL - accelerator for both VPN and UTM. The SEM-DUAL provides the benefits
of the SEM-VPN and increases the maximum anti-virus and IDP traffic throughput
from 100 Mbps to 400 Mbps.
System Name This field displays the name used to identify the Zyxel Device on any network. Click
the link and open the Host Name screen where you can edit and make changes to
the system and domain name.
Model Name This field displays the model name of this Zyxel Device.
Serial Number This field displays the serial number of this Zyxel Device. The serial number is used for
device tracking and control.
MAC Address Range This field displays the MAC addresses used by the Zyxel Device. Each physical port
has one MAC address. The first MAC address is assigned to physical port 1, the
second MAC address is assigned to physical port 2, and so on.
Firmware Version This field displays the version number and date of the firmware the Zyxel Device is
currently running. Click the link to open the Firmware Package screen where you
can upload firmware.
Chapter 6 Dashboard
USG/ZyWALL User’s Guide
175
This table describes the fields in the above screen.
6.2.3 VPN Status Screen
Click on VPN Status link to look at the VPN tunnels that are currently established. The following screen will
show.
Table 25 Dashboard > System Status
LABEL DESCRIPTION
System Uptime This field displays how long the Zyxel Device has been running since it last restarted
or was turned on.
Current Date/Time This field displays the current date and time in the Zyxel Device. The format is yyyy-
mm-dd hh:mm:ss. Click on the link to see the Date/Time screen where you can make
edits and changes to the date, time and time zone information.
VPN Status Click on the link to look at the VPN tunnels that are currently established. See Section
6.2.3 on page 175. Click on the VPN icon to go to the Zyxel VPN Client product page
at the Zyxel website.
SSL VPN Status The first number is the actual number of VPN tunnels up and the second number is
the maximum number of SSL VPN tunnels allowed.
DHCP Table Click this to look at the IP addresses currently assigned to the Zyxel Device’s DHCP
clients and the IP addresses reserved for specific MAC addresses. See Section 6.2.4
on page 177.
Current Login User This field displays the user name used to log in to the current session, the amount of
reauthentication time remaining, and the amount of lease time remaining.
Number of Login Users This field displays the number of users currently logged in to the Zyxel Device. Click
the icon to pop-open a list of the users who are currently logged in to the Zyxel
Device.
Boot Status This field displays details about the Zyxel Device’s startup state.
OK - The Zyxel Device started up successfully.
Firmware update OK - A firmware update was successful.
Problematic configuration after firmware update - The application of the
configuration failed after a firmware upgrade.
System default configuration - The Zyxel Device successfully applied the system
default configuration. This occurs when the Zyxel Device starts for the first time or you
intentionally reset the Zyxel Device to the system default settings.
Fallback to lastgood configuration - The Zyxel Device was unable to apply the
startup-config.conf configuration file and fell back to the lastgood.conf
configuration file.
Fallback to system default configuration - The Zyxel Device was unable to apply the
lastgood.conf configuration file and fell back to the system default configuration file
(system-default.conf).
Booting in progress - The Zyxel Device is still applying the system configuration.
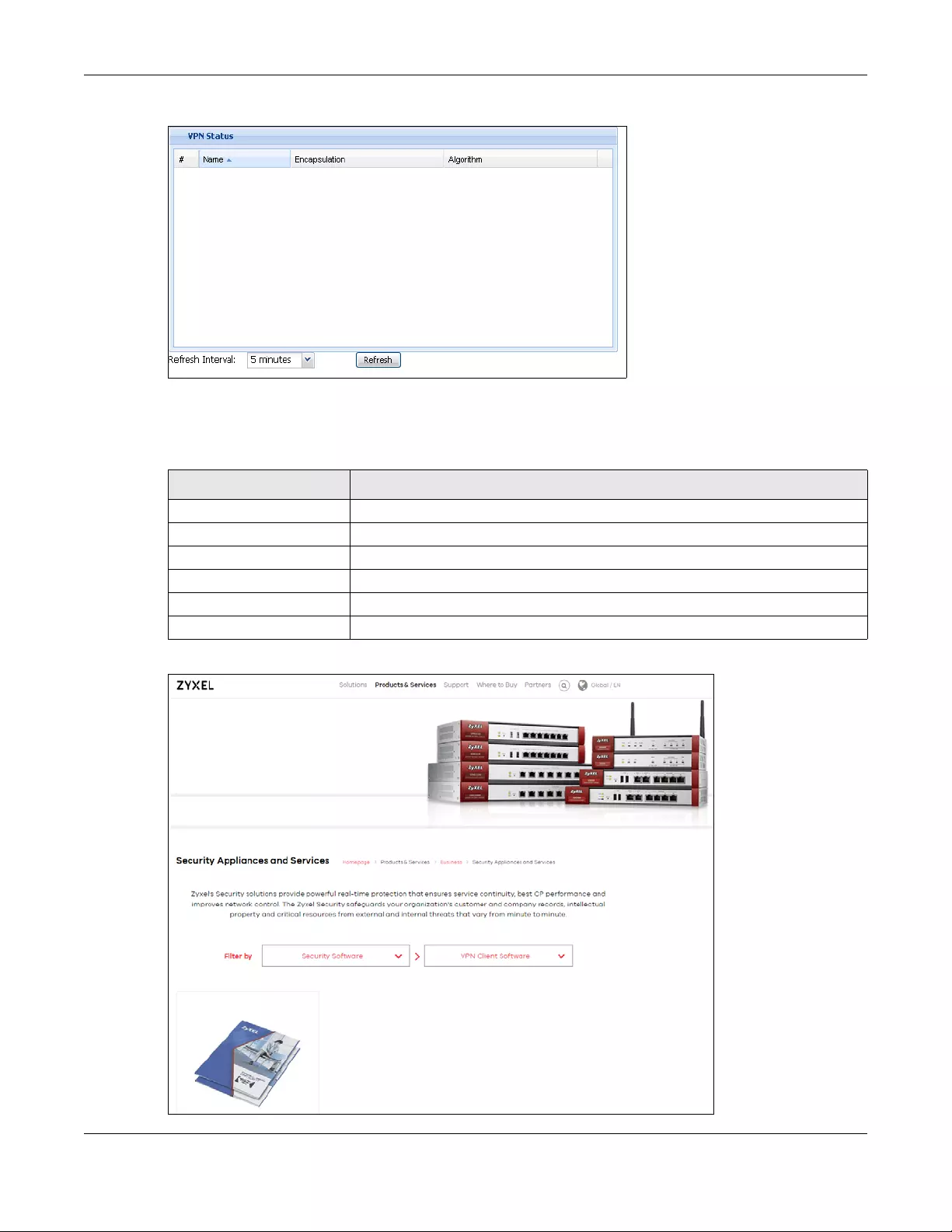
Chapter 6 Dashboard
USG/ZyWALL User’s Guide
176
Figure 149 Dashboard > System Status > VPN Status
This table describes the fields in the above screen.
Table 26 Dashboard > System Status > VPN Status
Zyxel VPN Client Product Page
LABLE DESCRIPTION
# This field is a sequential value, and it is not associated with a specific SA.
Name This field displays the name of the IPSec SA.
Encapsulation This field displays how the IPSec SA is encapsulated.
Algorithm This field displays the encryption and authentication algorithms used in the SA.
Refresh Interval Select how often you want this window to be updated automatically.
Refresh Now Click this to update the information in the window right away.
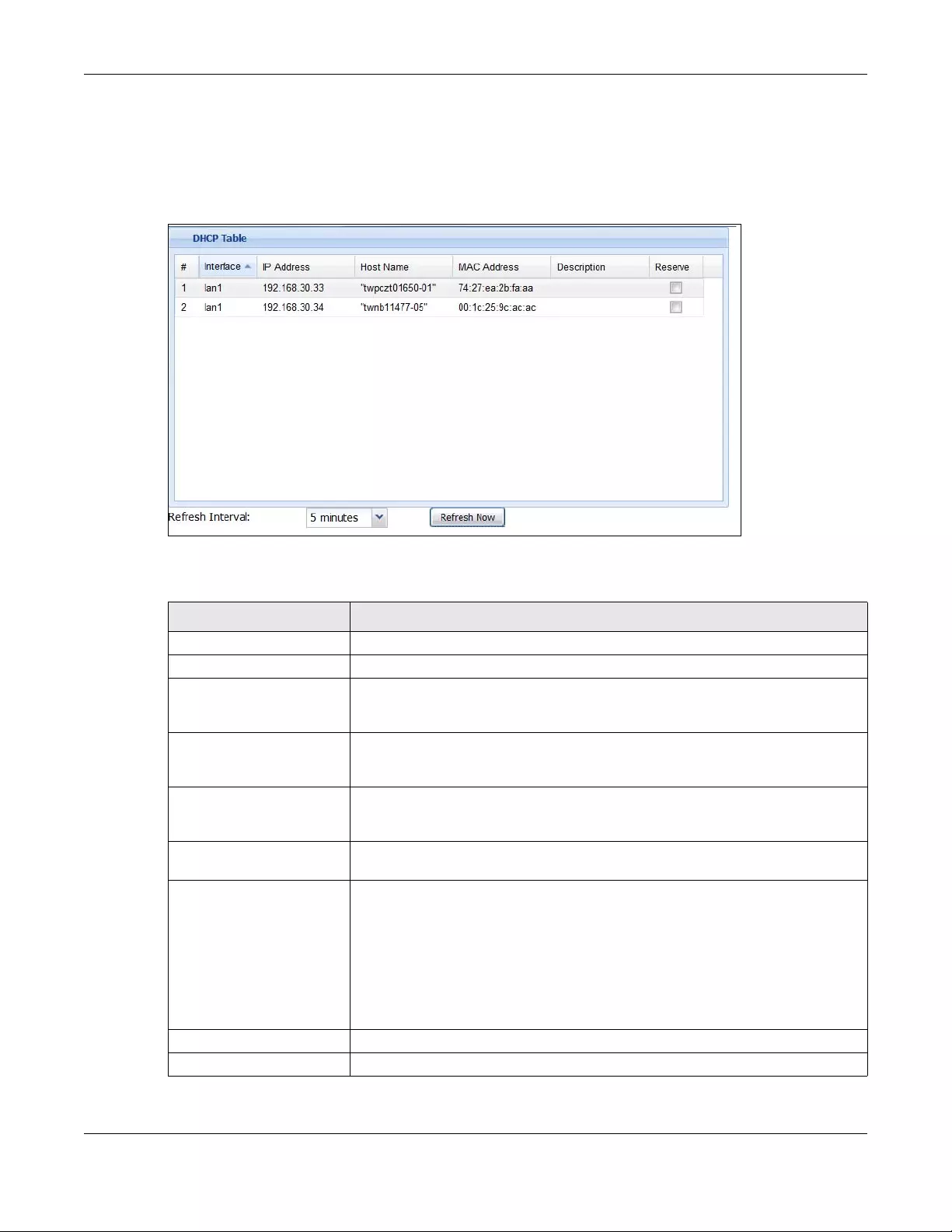
Chapter 6 Dashboard
USG/ZyWALL User’s Guide
177
6.2.4 DHCP Table Screen
Click on the DHCP Table link to look at the IP addresses currently assigned to DHCP clients and the IP
addresses reserved for specific MAC addresses. The following screen will show.
Figure 150 Dashboard > System Status > DHCP Table
This table describes the fields in the above screen.
Table 27 Dashboard > System Status > DHCP Table
LABEL DESCRIPTION
# This field is a sequential value, and it is not associated with a specific entry.
Interface This field identifies the interface that assigned an IP address to a DHCP client.
IP Address This field displays the IP address currently assigned to a DHCP client or reserved for a
specific MAC address. Click the column’s heading cell to sort the table entries by IP
address. Click the heading cell again to reverse the sort order.
Host Name This field displays the name used to identify this device on the network (the
computer name). The Zyxel Device learns these from the DHCP client requests.
“None” shows here for a static DHCP entry.
MAC Address This field displays the MAC address to which the IP address is currently assigned or for
which the IP address is reserved. Click the column’s heading cell to sort the table
entries by MAC address. Click the heading cell again to reverse the sort order.
Description For a static DHCP entry, the host name or the description you configured shows
here. This field is blank for dynamic DHCP entries.
Reserve If this field is selected, this entry is a static DHCP entry. The IP address is reserved for
the MAC address.
If this field is clear, this entry is a dynamic DHCP entry. The IP address is assigned to a
DHCP client.
To create a static DHCP entry using an existing dynamic DHCP entry, select this field,
and then click Apply.
To remove a static DHCP entry, clear this field, and then click Apply.
Refresh Interval Select how often you want this window to be updated automatically.
Refresh Now Click this to update the information in the window right away.
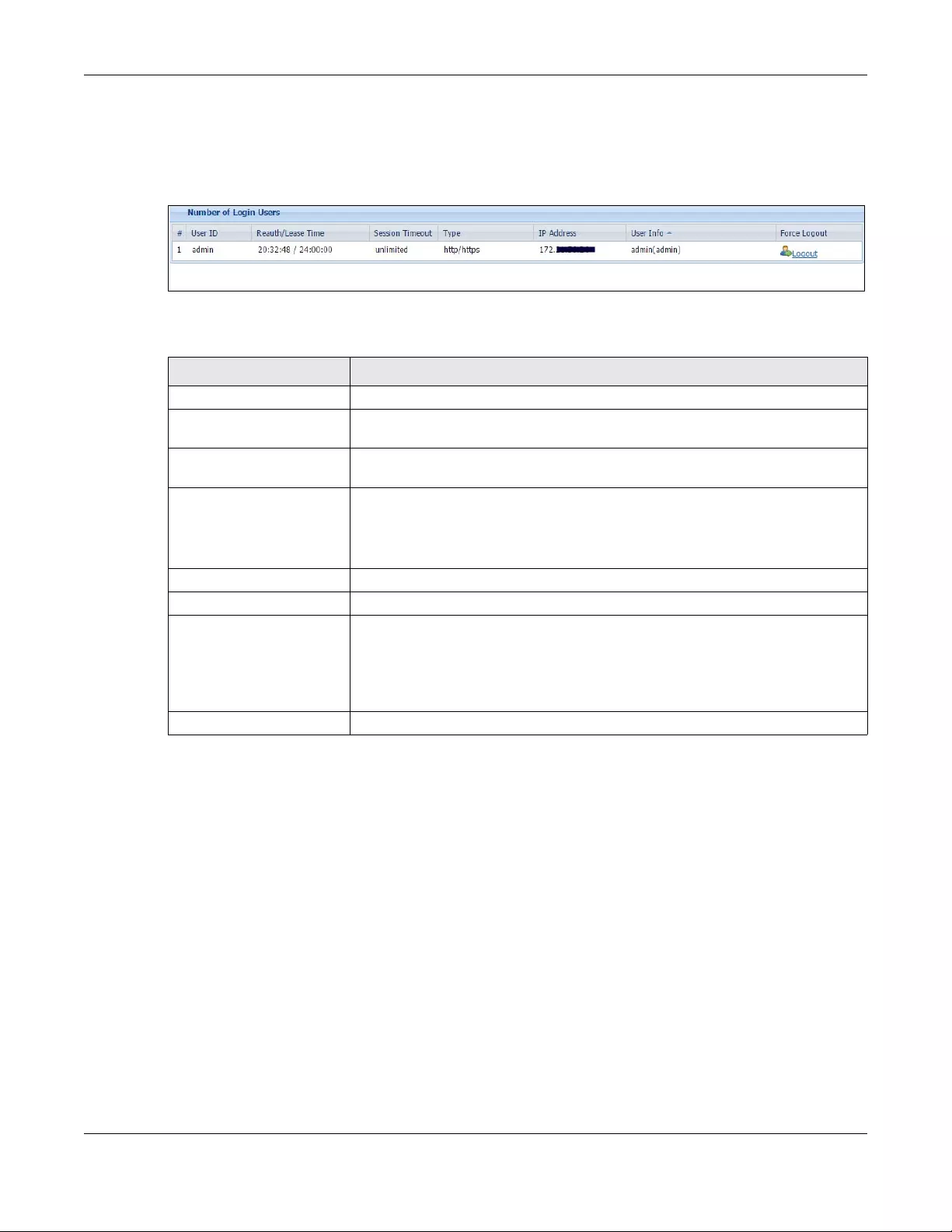
Chapter 6 Dashboard
USG/ZyWALL User’s Guide
178
6.2.5 Number of Login Users Screen
Click the Number of Login Users link to see the following screen.
Figure 151 Dashboard > System Status > Number of Login Users
This table describes the fields in the above screen.
6.2.6 System Resources Screen
Hover your mouse over an item and click the arrow on the right to see more details on that resource.
Table 28 Dashboard > System Status > Number of Login Users
LABEL DESCRIPTION
# This field is a sequential value and is not associated with any entry.
User ID This field displays the user name of each user who is currently logged in to the Zyxel
Device.
Reauth/Lease Time This field displays the amount of reauthentication time remaining and the amount of
lease time remaining for each user.
Session Timeout This field displays the total account of time the account (authenticated by an
external server) can use to log into the UAG or access the Internet through the Zyxel
Device.
This shows unlimited for an administrator account.
Type This field displays the way the user logged in to the Zyxel Device.
IP address This field displays the IP address of the computer used to log in to the Zyxel Device.
User Info This field displays the types of user accounts the Zyxel Device uses. If the user type is
ext-user (external user), this field will show its external-group information when you
move your mouse over it.
If the external user matches two external-group objects, both external-group object
names will be shown.
Force Logout Click this icon to end a user’s session.
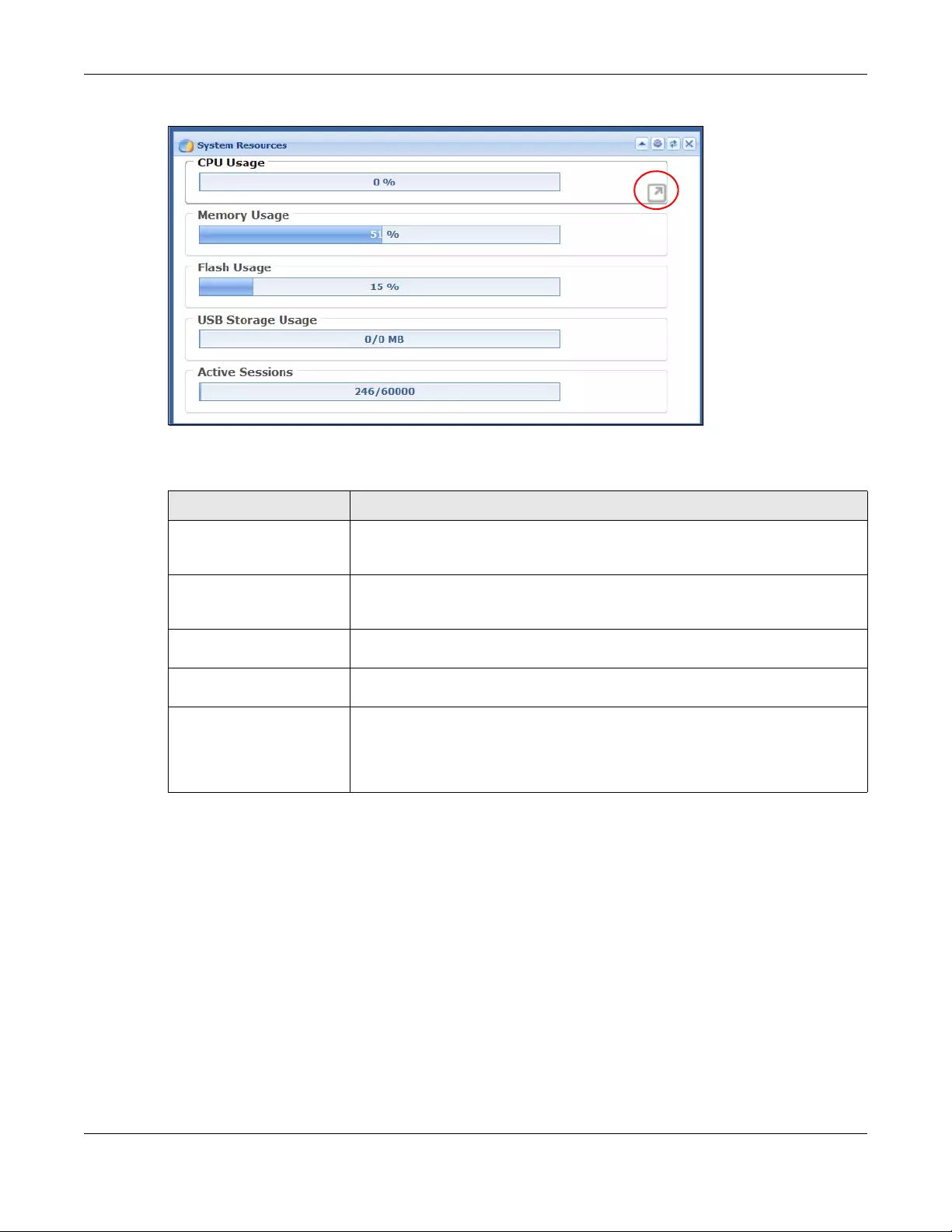
Chapter 6 Dashboard
USG/ZyWALL User’s Guide
179
Figure 152 Dashboard > System Resources
This table describes the fields in the above screen.
6.2.7 CPU Usage Screen
Use the below screen to look at a chart of the Zyxel Device’s recent CPU usage. To access this screen,
click CPU Usage in the dashboard.
Table 29 .Dashboard > System Resources
LABEL DESCRIPTION
CPU Usage This field displays what percentage of the Zyxel Device’s processing capability is
currently being used. Hover your cursor over this field to display the Show CPU Usage
icon that takes you to a chart of the Zyxel Device’s recent CPU usage.
Memory Usage This field displays what percentage of the Zyxel Device’s RAM is currently being used.
Hover your cursor over this field to display the Show Memory Usage icon that takes
you to a chart of the Zyxel Device’s recent memory usage.
Flash Usage This field displays what percentage of the Zyxel Device’s onboard flash memory is
currently being used.
USB Storage Usage This field shows how much storage in the USB device connected to the Zyxel Device
is in use.
Active Sessions This field shows how many sessions, established and non-established, that pass
through/from/to/within the ZyWALL. Hover your cursor over this field to display icons.
Click the Detail icon to go to the Session Monitor screen to see details about the
active sessions. Click the Show Active Sessions icon to display a chart of Zyxel
Device’s recent session usage.
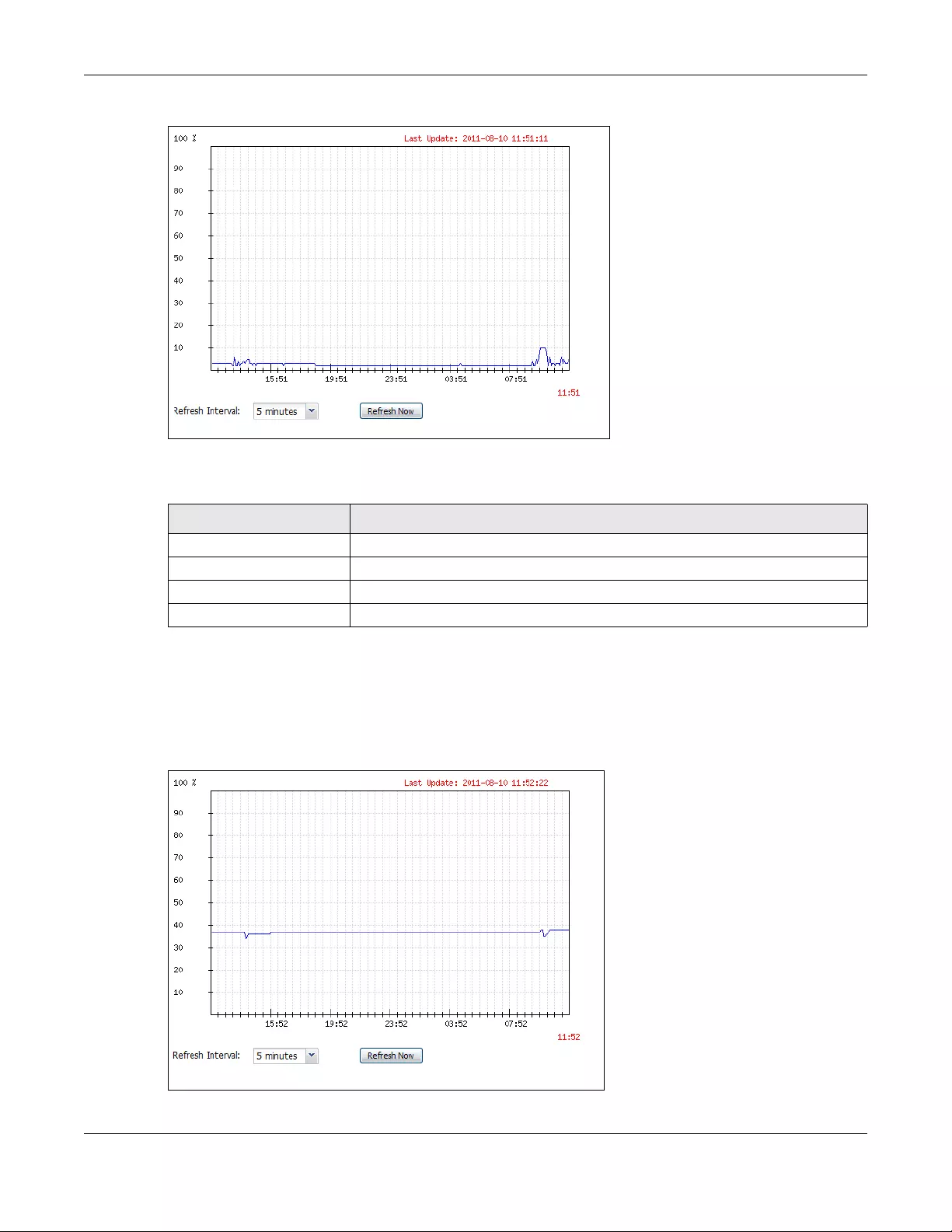
Chapter 6 Dashboard
USG/ZyWALL User’s Guide
180
Figure 153 Dashboard > CPU Usage screen
This table describes the fields in the above screen.
6.2.8 Memory Usage Screen
Use the below screen to look at a chart of the Zyxel Device’s recent memory (RAM) usage. To access
this screen, click Memory Usage in the dashboard.
Figure 154 Dashboard > Memory Usage screen
Table 30 Dashboard > CPU Usage
LABEL DESCRIPTION
The y-axis represents the percentage of CPU usage.
The x-axis shows the time period over which the CPU usage occurred
Refresh Interval Enter how often you want this window to be automatically updated.
Refresh Now Click this to update the information in the window right away.
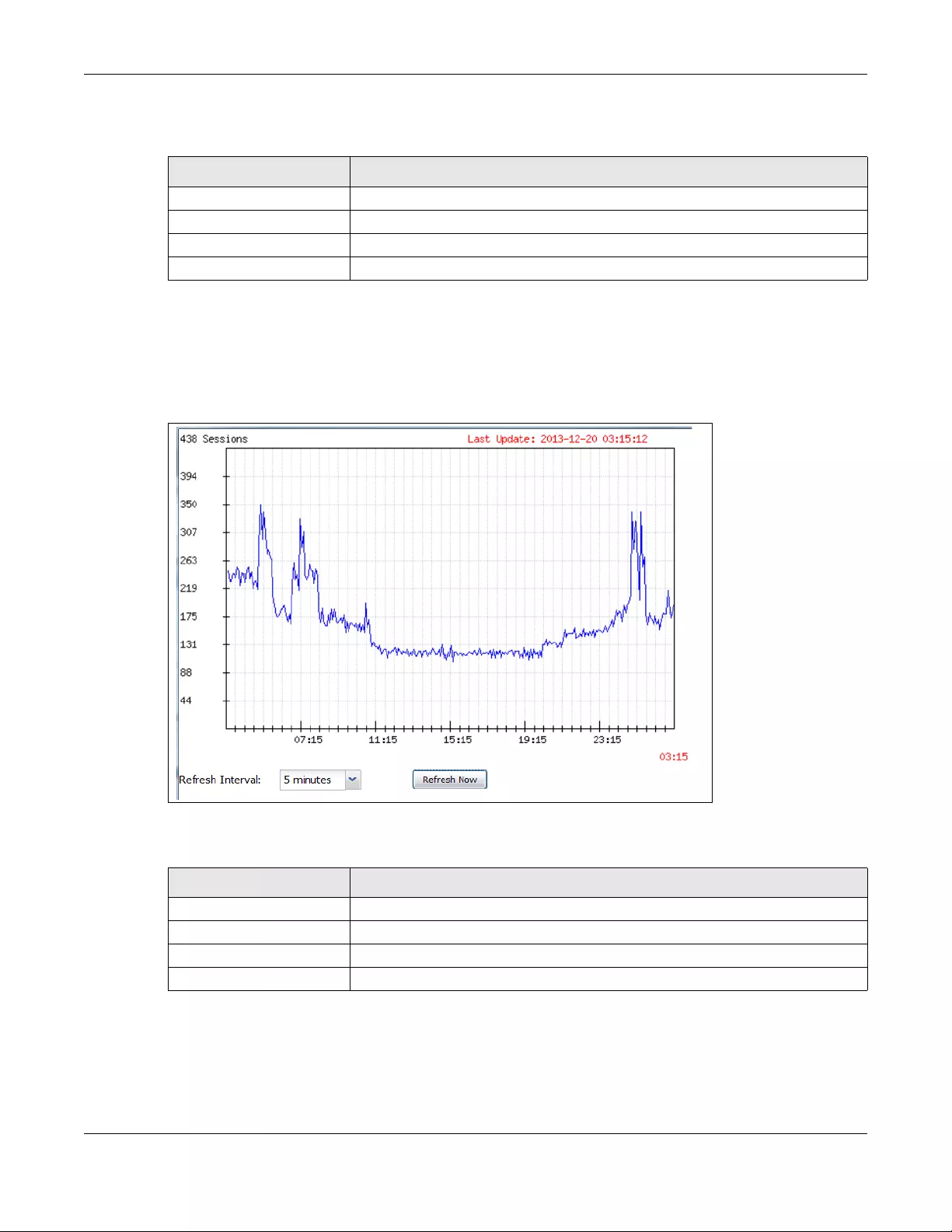
Chapter 6 Dashboard
USG/ZyWALL User’s Guide
181
This table describes the fields in the above screen.
6.2.9 Active Sessions Screen
To see the details of Active Sessions, move the cursor to the far right of the Active Sessions box and the
Detail and the Show Active Sessions icons appear. Click the Show Active Sessions icon.
Figure 155 Dashboard > Active Sessions > Show Active Sessions
This table describes the fields in the above screen.
Table 31 Dashboard > Memory Usage screen.
LABEL DESCRIPTION
The y-axis represents the percentage of RAM usage.
The x-axis shows the time period over which the RAM usage occurred
Refresh Interval Enter how often you want this window to be automatically updated.
Refresh Now Click this to update the information in the window right away.
Table 32 Dashboard > Active Sessions > Show Active Sessions
Sessions The y-axis represents the number of session.
The x-axis shows the time period over which the session usage occurred
Refresh Interval Enter how often you want this window to be automatically updated.
Refresh Now Click this to update the information in the window right away.
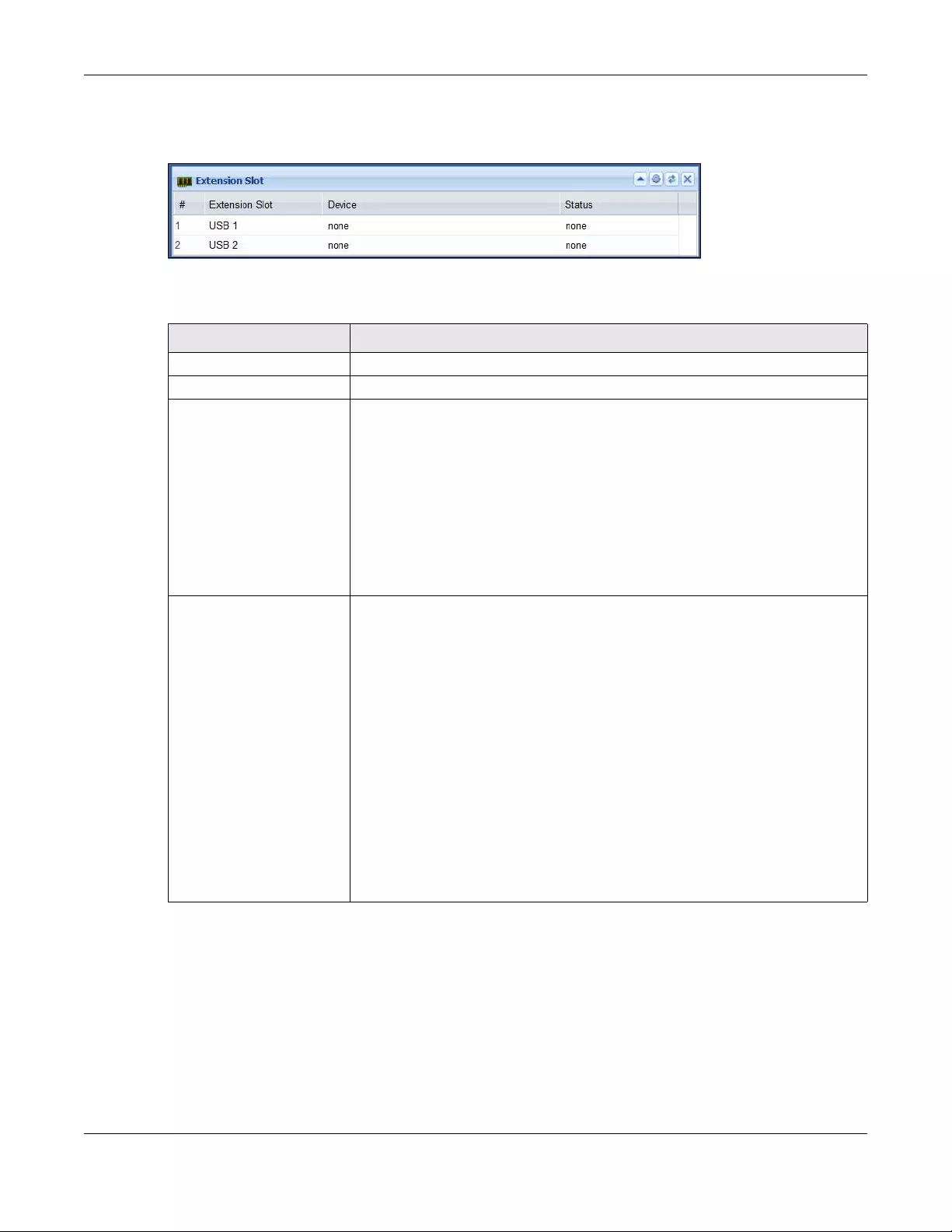
Chapter 6 Dashboard
USG/ZyWALL User’s Guide
182
6.2.10 Extension Slot Screen
Figure 156 Dashboard > Extension Slot
This table describes the fields in the above screen.
6.2.11 Interface Status Summary Screen
Interfaces per Zyxel Device model vary.
Table 33 Dashboard > Extension Slot
LABEL DESCRIPTION
# This is the index number of the entry.
Extension Slot This field displays the name of each extension slot.
Device This field displays the name of the device connected to the extension slot (or none if
no device is detected). For an installed SEM (Security Extension Module) card, this
field displays what kind of SEM card is installed.
SEM-VPN - VPN accelerator. The SEM-VPN provides 500 Mbps VPN throughput, 2,000
IPSec VPN tunnels, and 750 SSL VPN users.
SEM-DUAL - accelerator for both VPN and UTM. The SEM-DUAL provides the benefits
of the SEM-VPN and increases the maximum anti-virus and IDP traffic throughput
from 100 Mbps to 400 Mbps.
USB Flash Drive - Indicates a connected USB storage device and the drive’s storage
capacity.
Status The status for an installed 3G USB dongle is none. For cellular (mobile broadband)
interfaces, see Section 7.11 on page 204 for the status that can appear. For an
installed SEM (Security Extension Module) card, this field displays one of the
following:
Active - The SEM card is working properly.
Ready to activate - The SEM was inserted while the Zyxel Device was operating.
Restart the Zyxel Device to use the SEM.
Driver load failed - An error occurred during the Zyxel Device’s attempt to activate
the SEM card. Make sure the SEM is installed properly and the thumbscrews are
tightened. If this status still displays, contact your vendor.
For a USB storage device, this field displays one of the following:
Ready - A USB storage device connected to the Zyxel Device is ready for the Zyxel
Device to use.
Unused - The Zyxel Device is unable to mount a USB storage device connected to
the Zyxel Device.
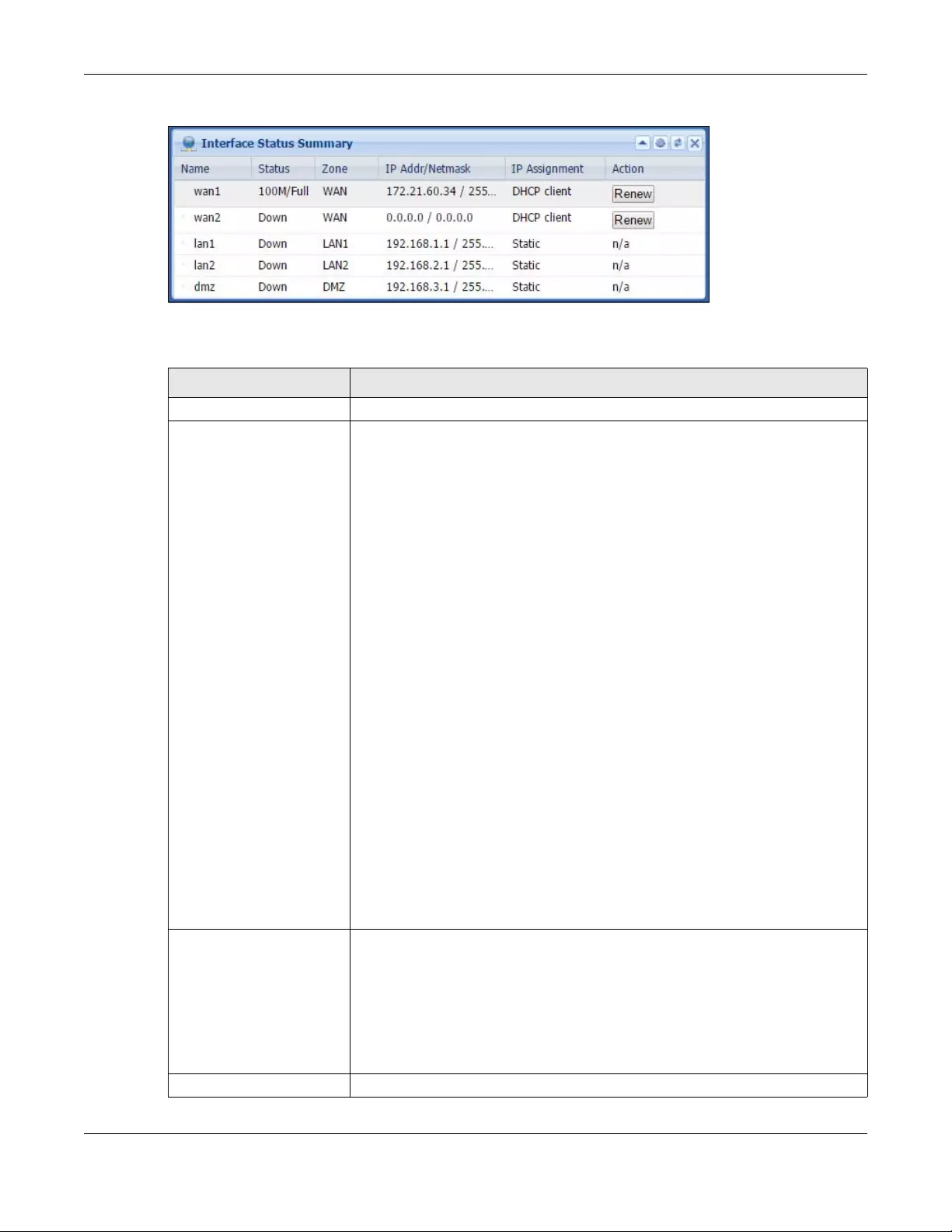
Chapter 6 Dashboard
USG/ZyWALL User’s Guide
183
Figure 157 Dashboard > Interface Status Summary
This table describes the fields in the above screen.
Table 34 Dashboard > Interface Status Summary
LABEL DESCRIPTION
Name This field displays the name of each interface.
Status This field displays the current status of each interface. The possible values depend on
what type of interface it is.
For Ethernet interfaces:
Inactive - The Ethernet interface is disabled.
Down - The Ethernet interface does not have any physical ports associated with it or
the Ethernet interface is enabled but not connected.
Speed / Duplex - The Ethernet interface is enabled and connected. This field displays
the port speed and duplex setting (Full or Half).
For cellular (mobile broadband) interfaces, see Section 7.11 on page 204 for the
status that can appear.
For the auxiliary interface:
Inactive - The auxiliary interface is disabled.
Connected - The auxiliary interface is enabled and connected.
Disconnected - The auxiliary interface is not connected.
For PPP interfaces:
Connected - The PPP interface is connected.
Disconnected - The PPP interface is not connected.
If the PPP interface is disabled, it does not appear in the list.
For WLAN interfaces:
Up - The WLAN interface is enabled.
Down - The WLAN interface is disabled.
HA Status This field displays the status of the interface in the virtual router.
Active - This interface is the master interface in the virtual router.
Stand-By - This interface is a backup interface in the virtual router.
Fault - This VRRP group is not functioning in the virtual router right now. For example,
this might happen if the interface is down.
n/a - Device HA is not active on the interface.
Zone This field displays the zone to which the interface is currently assigned.
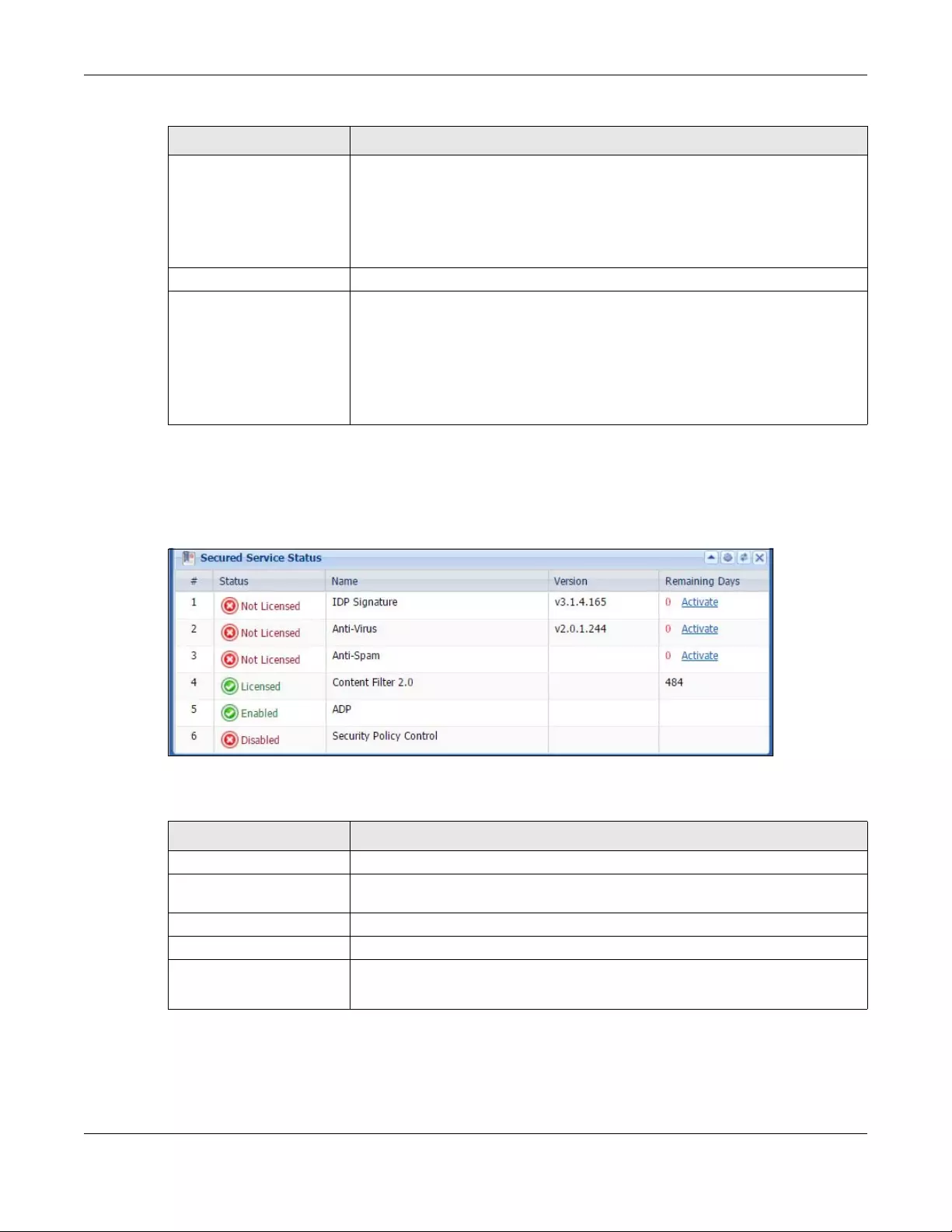
Chapter 6 Dashboard
USG/ZyWALL User’s Guide
184
6.2.12 Secured Service Status Screen
This part shows what Unified Threat Management (UTM) services are available and enabled.
Figure 158 Dashboard > Secured Service Status
This table describes the fields in the above screen.
6.2.13 Content Filter Statistics Screen
Configure Configuration > UTM Profile > Content Filter and then view results here.
IP Addr/Netmask This field displays the current IP address and subnet mask assigned to the interface. If
the IP address is 0.0.0.0/0.0.0.0, the interface is disabled or did not receive an IP
address and subnet mask via DHCP.
If this interface is a member of an active virtual router, this field displays the IP
address it is currently using. This is either the static IP address of the interface (if it is
the master) or the management IP address (if it is a backup).
IP Assignment This field displays the interface’s IP assignment. It will show DHCP or Static.
Action Use this field to get or to update the IP address for the interface.
Click Renew to send a new DHCP request to a DHCP server.
Click the Connect icon to have the Zyxel Device try to connect a PPPoE/PPTP
interface. If the interface cannot use one of these ways to get or to update its IP
address, this field displays n/a.
Click the Disconnect icon to stop a PPPoE/PPTP connection.
Table 34 Dashboard > Interface Status Summary
LABEL DESCRIPTION
Table 35 Dashboard > Secured Service Status
LABEL DESCRIPTION
# This field is a sequential value, and it is not associated with a specific status.
Status This field displays the status of the Zyxel Device’s secure services. It will show four
types of status, Licensed or Unlicensed or Disabled or Enabled.
Name This field displays the name of the service, for example Anti-Spam.
Version This field displays the version number of the services.
Remaining Days This field displays the number of days remaining before the license expires.
Click Activate to connect with the myZyxel.com server and activate the license.
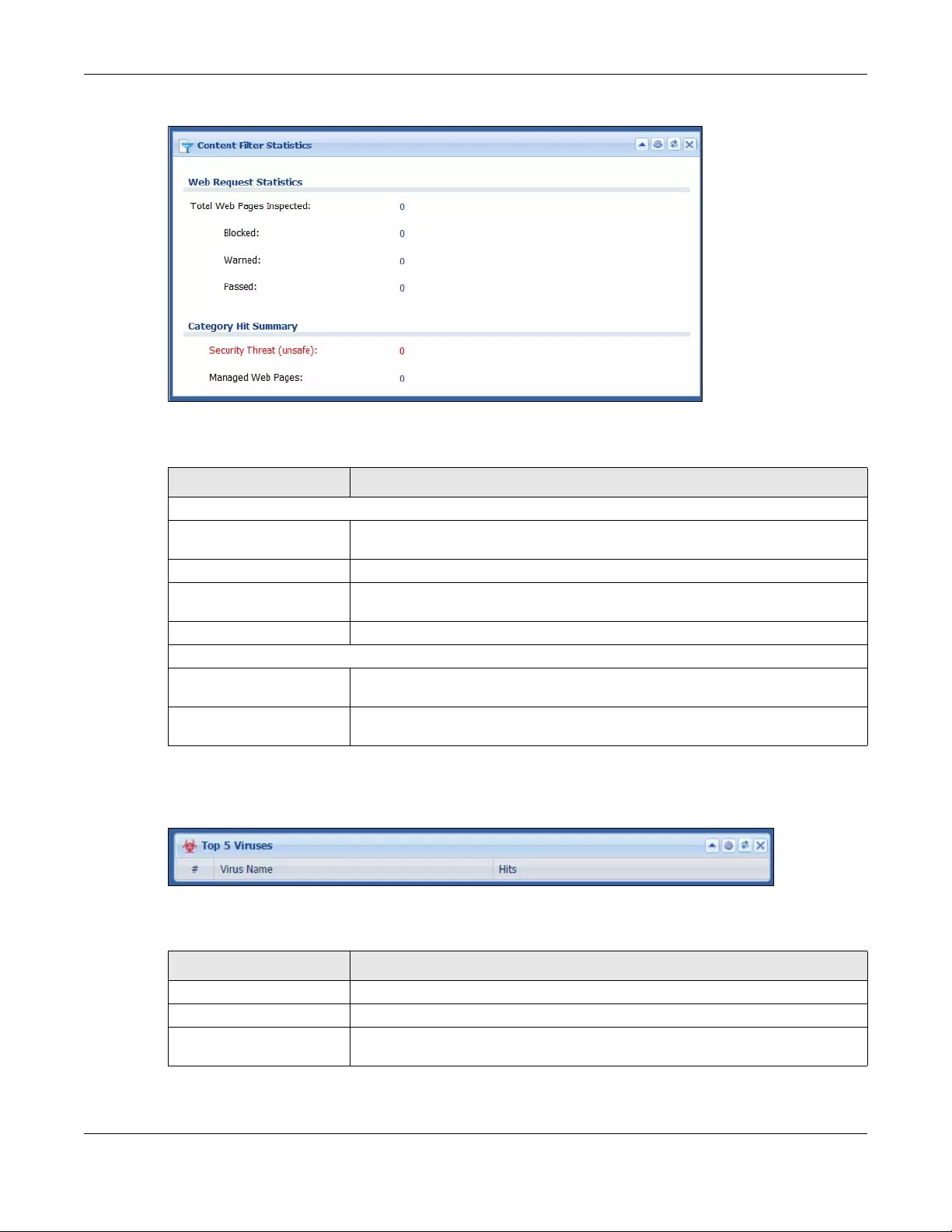
Chapter 6 Dashboard
USG/ZyWALL User’s Guide
185
Figure 159 Dashboard > Content Filter Statistics
This table describes the fields in the above screen.
6.2.14 Top 5 Viruses Screen
Figure 160 Dashboard > Top 5 Viruses
This table describes the fields in the above screen.
Table 36 Dashboard > Content Filter Statistics
LABEL DESCRIPTION
Web Request Statistics
Total Web Pages
Inspected This is the number of web pages the Zyxel Device has checked to see whether they
belong to the categories you selected in the content filter screen.
Blocked This is the number of web pages that the Zyxel Device blocked access.
Warned This is the number of web pages for which the Zyxel Device has displayed a warning
message to the access requesters.
Passed This is the number of web pages that the Zyxel Device allowed access.
Category Hit Summary
Security Threat (unsafe) This is the number of requested web pages that belong to the unsafe categories you
have selected in the content filter screen.
Managed Web pages This is the number of requested web pages that belong to the managed categories
you have selected in the content filter screen.
Table 37 Dashboard > Top 5 Viruses
LABEL DESCRIPTION
# This is the entry’s rank in the list of the most commonly detected viruses.
Virus Name This is the name of a detected virus.
Hits This is how many times the Zyxel Device has detected the event described in the
entry.
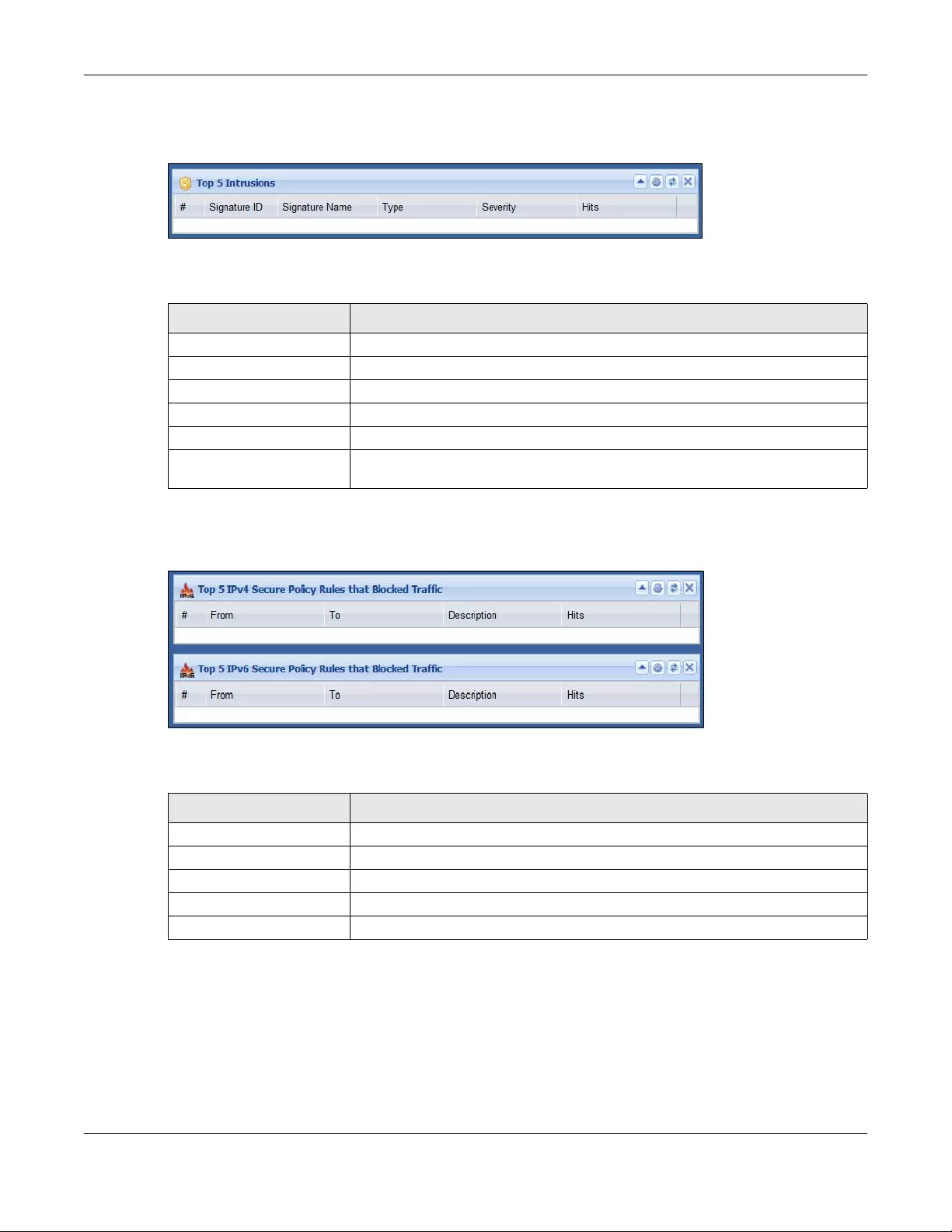
Chapter 6 Dashboard
USG/ZyWALL User’s Guide
186
6.2.15 Top 5 Intrusions Screen
Figure 161 Dashboard > Top 5 Intrusions
This table describes the fields in the above screen.
6.2.16 Top 5 IPv4/IPv6 Security Policy Rules that Blocked Traffic Screen
Figure 162 Dashboard > Top 5 IPv4/IPv6 Security Policy Rules that Blocked Traffic
This table describes the fields in the above screen.
Table 38 Dashboard > Top 5 Intrusions
LABEL DESCRIPTION
# This is the entry’s rank in the list of the most commonly triggered signature policies.
Signature ID This is the identification number of the signature.
Signature Name This is the name of the signature.
Type This is the type of the signature, for example Schedule.
Severity This is the level of threat that the intrusions may pose.
Hits This is how many times the Zyxel Device has detected the event described in the
entry.
Table 39 Dashboard > Top 5 IPv4/IPv6 Security Policy Rules that Blocked Traffic
LABEL DESCRIPTION
# This is the entry’s rank in the list of the most commonly triggered security policies.
From This shows the zone packets came from that the triggered security policy.
To This shows the zone packets went to that the triggered security policy.
Description This field displays the descriptive name (if any) of the triggered security policy.
Hits This field displays how many times the security policy was triggered.
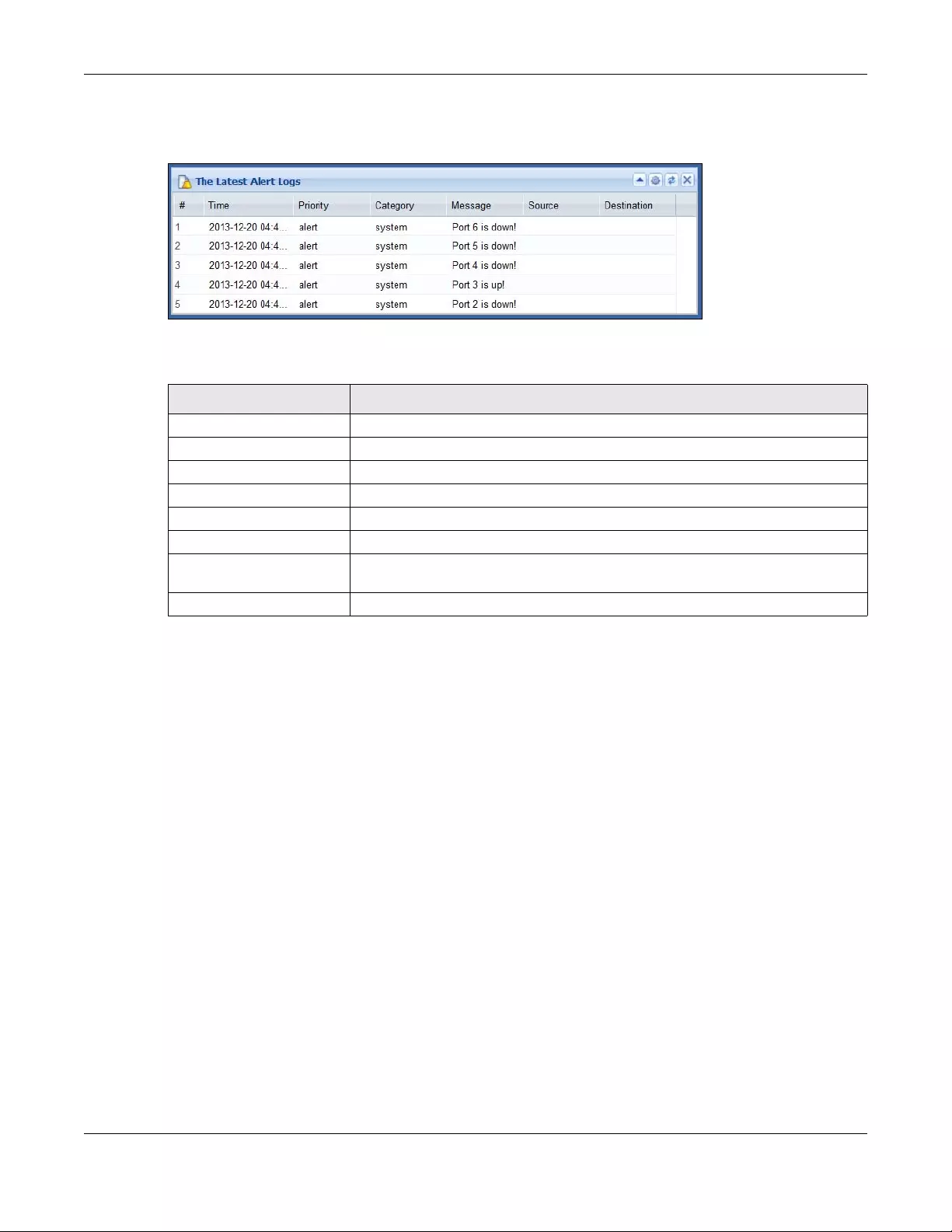
Chapter 6 Dashboard
USG/ZyWALL User’s Guide
187
6.2.17 The Latest Alert Logs Screen
Figure 163 Dashboard > The Latest Alert Logs
This table describes the fields in the above screen.
Table 40 Dashboard > The Latest Alert Logs
LABEL DESCRIPTION
# This is the entry’s rank in the list of alert logs.
Time This field displays the date and time the log was created.
Priority This field displays the severity of the log.
Category This field displays the type of log generated.
Message This field displays the actual log message.
Source This field displays the source address (if any) in the packet that generated the log.
Destination This field displays the destination address (if any) in the packet that generated the
log.
Source Interface This field displays the incoming interface of the packet that generated the log.
188
PART II
Technical Reference

USG/ZyWALL User’s Guide
189
CHAPTER 7
Monitor
7.1 Overview
Use the Monitor screens to check status and statistics information.
7.1.1 What You Can Do in this Chapter
Use the Monitor screens for the following.
• Use the System Status > Port Statistics screen (see Section 7.2 on page 190) to look at packet statistics
for each physical port.
• Use the System Status > Port Statistics > Graph View screen (see Section 7.2 on page 190) to look at a
line graph of packet statistics for each physical port.
• Use the System Status > Interface Status screen (Section 7.3 on page 192) to see all of the Zyxel
Device’s interfaces and their packet statistics.
• Use the System Status > Traffic Statistics screen (see Section 7.4 on page 195) to start or stop data
collection and view statistics.
• Use the System Status > Session Monitor screen (see Section 7.5 on page 198) to view sessions by user
or service.
• Use the System Status > IGMP Statistics screen (see Section 7.6 on page 199) to view multicasting
details.
• Use the System Status > DDNS Status screen (see Section 7.7 on page 200) to view the status of the
Zyxel Device’s DDNS domain names.
• Use the System Status > IP/MAC Binding screen (Section 7.8 on page 201) to view a list of devices that
have received an IP address from Zyxel Device interfaces with IP/MAC binding enabled.
• Use the System Status > Login Users screen (Section 7.9 on page 201) to look at a list of the users
currently logged into the Zyxel Device.
• Use the System Status > Dynamic Guest screen (see Section 7.10 on page 202) to look at a list of the
guest user accounts, which are created automatically and allowed to access the Zyxel Device’s
services for a certain period of time.
• Use the System Status > Cellular Status screen (Section 7.11 on page 204) to check your mobile
broadband connection status.
• Use the System Status > UPnP Port Status screen (see Section 7.12 on page 207) to look at a list of the
NAT port mapping rules that UPnP creates on the Zyxel Device.
• Use the System Status > USB Storage screen (Section 7.13 on page 208) to view information about a
connected USB storage device.
• Use the System Status > Ethernet Neighbor screen (Section 7.14 on page 209) to view and manage
the Zyxel Device’s neighboring devices via Layer Link Discovery Protocol (LLDP).
• Use the Wireless > AP Information screen (Section 7.15.1 on page 210) to view information on
connected APs.

Chapter 7 Monitor
USG/ZyWALL User’s Guide
190
• Use the Wireless > Station Info screen (Section 7.15.6 on page 218) to view information on connected
wireless stations.
• Use the Wireless > Detected Device screen (Section 7.15.6 on page 218) to view information about
suspected rogue APs.
• Use the Printer Status screen (see Section 7.16 on page 220) to view information about the connected
statement printers.
• Use the VPN Monitor > IPSec screen (Section 7.17 on page 221) to display and manage active IPSec
SAs.
• Use the VPN Monitor > SSL screen (see Section 7.18 on page 222) to list the users currently logged into
the VPN SSL client portal. You can also log out individual users and delete related session information.
• Use the VPN Monitor > L2TP over IPSec screen (see Section 7.19 on page 223) to display and manage
the Zyxel Device’s connected L2TP VPN sessions.
• Use the UTM Statistics > App Patrol screen (see Section 7.20 on page 223) to start or stop data
collection and view virus statistics
• Use the UTM Statistics > Content Filter screen (Section 7.21 on page 225) to start or stop data
collection and view content filter statistics.
• Use the UTM Statistics > IDP screen (Section 7.22 on page 226) to start or stop data collection and view
IDP statistics.
• Use the UTM Statistics > Anti-Virus screen (see Section 7.23 on page 228) to start or stop data
collection and view virus statistics.
• Use the UTM Statistics > Anti-Spam screen (Section 7.24 on page 230) to start or stop data collection
and view spam statistics.
• Use the UTM Statistics > Anti-Spam > Status screen (Section 7.24.2 on page 232) to see how many mail
sessions the Zyxel Device is currently checking and DNSBL statistics.
• Use the UTM Statistics > SSL Inspection screen (Section 7.25 on page 234) to see a report on SSL
Inspection and a certificate cache list.
• Use the Log > View Log screen (see Section 7.26.1 on page 236) to view the Zyxel Device’s current log
messages. You can change the way the log is displayed, you can e-mail the log, and you can also
clear the log in this screen.
• Use the Log > View AP Log screen (see Section 7.26.2 on page 238) to view the Zyxel Device’s current
wireless AP log messages.
• Use the Log > Dynamic Users Log screen (see Section 7.26.3 on page 240) to view the Zyxel Device’s
dynamic guest account log messages.
7.2 The Port Statistics Screen
Use this screen to look at packet statistics for each Gigabit Ethernet port. To access this screen, click
Monitor > System Status > Port Statistics.
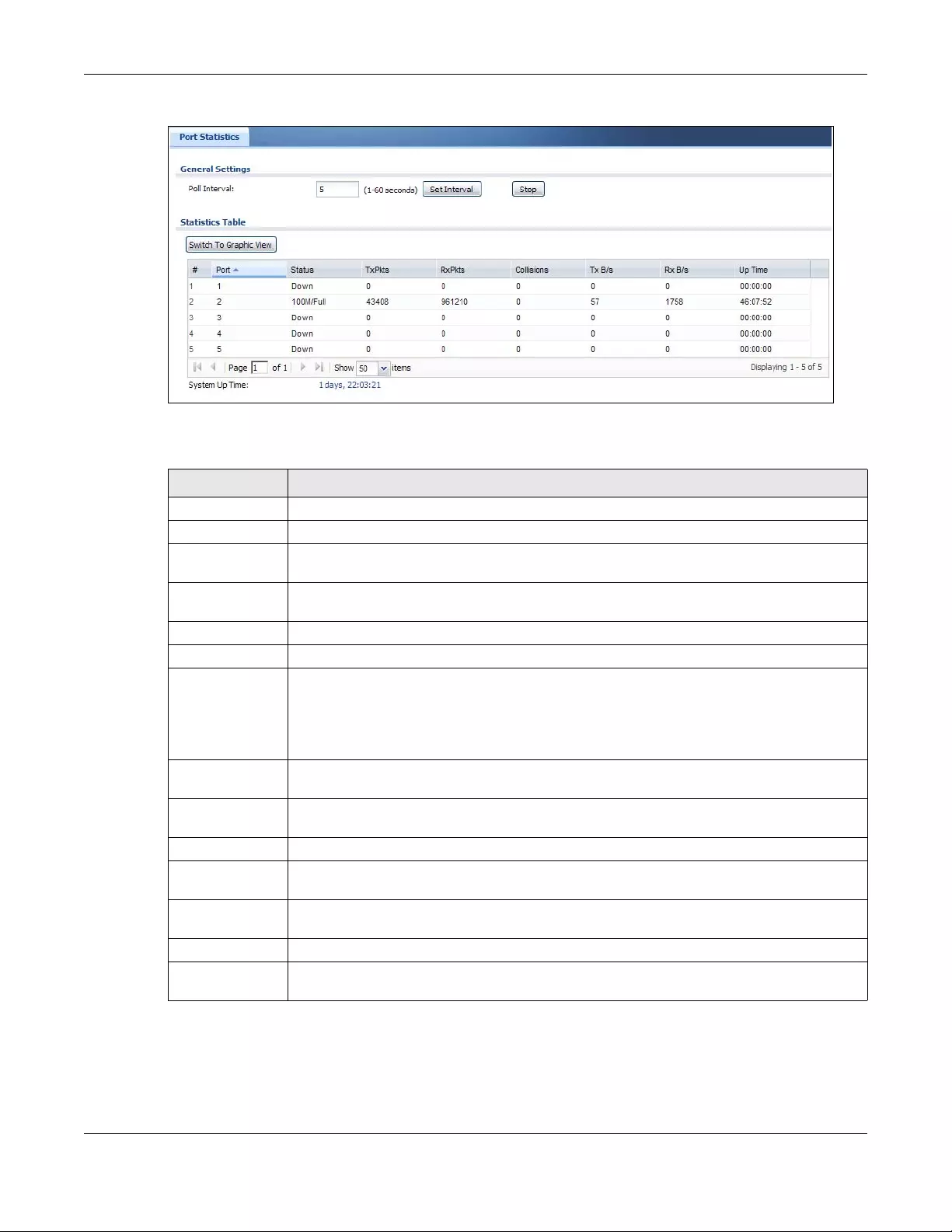
Chapter 7 Monitor
USG/ZyWALL User’s Guide
191
Figure 164 Monitor > System Status > Port Statistics
The following table describes the labels in this screen.
7.2.1 The Port Statistics Graph Screen
Use this screen to look at a line graph of packet statistics for each physical port. To access this screen,
click Port Statistics in the Status screen and then the Switch to Graphic View Button.
Table 41 Monitor > System Status > Port Statistics
LABEL DESCRIPTION
Poll Interval Enter how often you want this window to be updated automatically, and click Set Interval.
Set Interval Click this to set the Poll Interval the screen uses.
Stop Click this to stop the window from updating automatically. You can start it again by setting the
Poll Interval and clicking Set Interval.
Switch to Graphic
View
Click this to display the port statistics as a line graph.
# This field is a sequential value, and it is not associated with a specific port.
Port This field displays the physical port number.
Status This field displays the current status of the physical port.
Down - The physical port is not connected.
Speed / Duplex - The physical port is connected. This field displays the port speed and duplex
setting (Full or Half).
TxPkts This field displays the number of packets transmitted from the Zyxel Device on the physical port
since it was last connected.
RxPkts This field displays the number of packets received by the Zyxel Device on the physical port
since it was last connected.
Collisions This field displays the number of collisions on the physical port since it was last connected.
Tx B/s This field displays the transmission speed, in bytes per second, on the physical port in the one-
second interval before the screen updated.
Rx B/s This field displays the reception speed, in bytes per second, on the physical port in the one-
second interval before the screen updated.
Up Time This field displays how long the physical port has been connected.
System Up Time This field displays how long the Zyxel Device has been running since it last restarted or was
turned on.
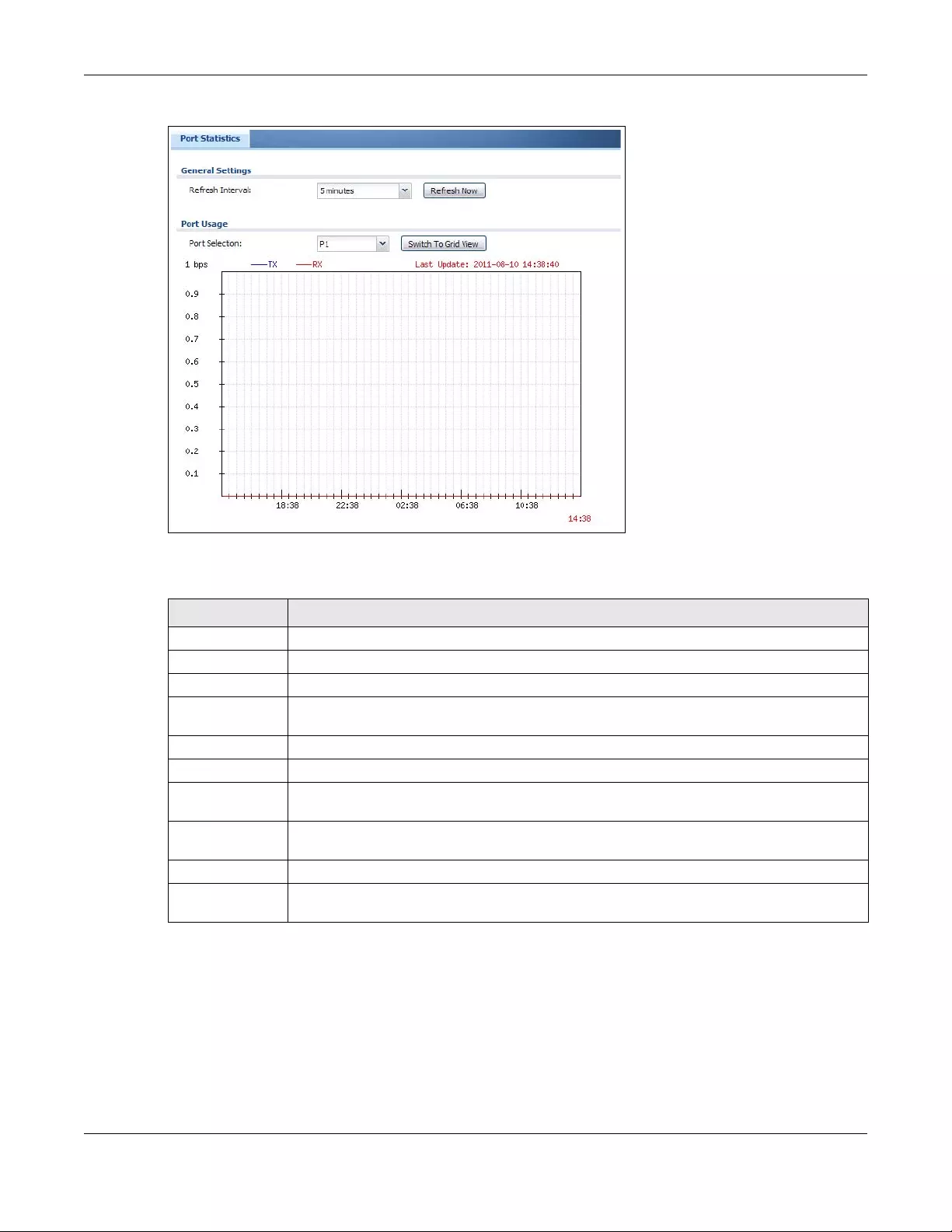
Chapter 7 Monitor
USG/ZyWALL User’s Guide
192
Figure 165 Monitor > System Status > Port Statistics > Switch to Graphic View
The following table describes the labels in this screen.
7.3 Interface Status Screen
This screen lists all of the Zyxel Device’s interfaces and gives packet statistics for them. Click Monitor >
System Status > Interface Status to access this screen.
Table 42 Monitor > System Status > Port Statistics > Switch to Graphic View
LABEL DESCRIPTION
Refresh Interval Enter how often you want this window to be automatically updated.
Refresh Now Click this to update the information in the window right away.
Port Selection Select the number of the physical port for which you want to display graphics.
Switch to Grid
View
Click this to display the port statistics as a table.
bps The y-axis represents the speed of transmission or reception.
time The x-axis shows the time period over which the transmission or reception occurred
TX This line represents traffic transmitted from the Zyxel Device on the physical port since it was last
connected.
RX This line represents the traffic received by the Zyxel Device on the physical port since it was last
connected.
Last Update This field displays the date and time the information in the window was last updated.
System Up Time This field displays how long the Zyxel Device has been running since it last restarted or was
turned on.
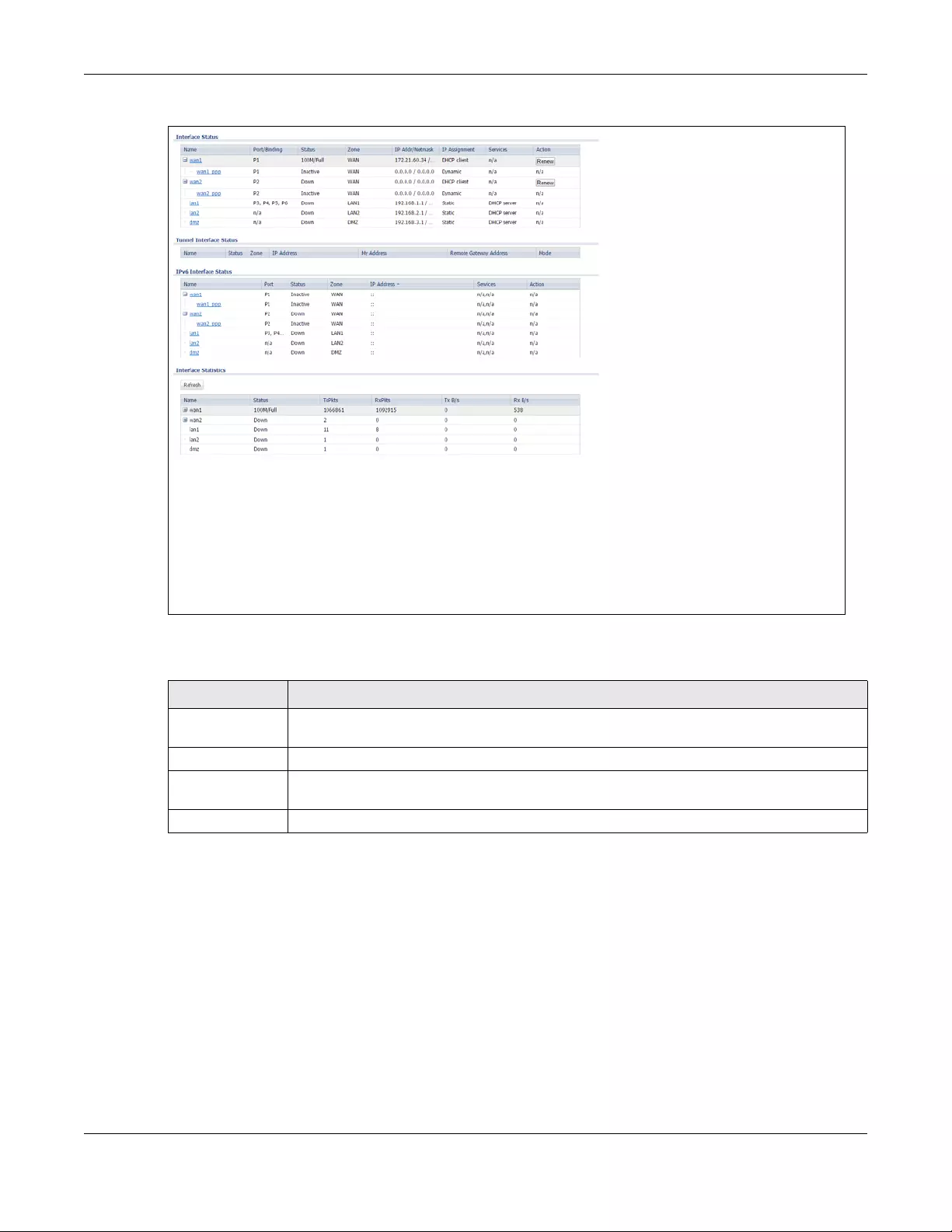
Chapter 7 Monitor
USG/ZyWALL User’s Guide
193
Figure 166 Monitor > System Status > Interface Status
Each field is described in the following table.
Table 43 Monitor > System Status > Interface Status
LABEL DESCRIPTION
Interface Status If an Ethernet interface does not have any physical ports associated with it, its entry is displayed
in light gray text.
Name This field displays the name of each interface. If there is an Expand icon (plus-sign) next to the
name, click this to look at the status of virtual interfaces on top of this interface.
Port This field displays the physical port number.
Chapter 7 Monitor
USG/ZyWALL User’s Guide
194
Status This field displays the current status of each interface. The possible values depend on what
type of interface it is.
For Ethernet interfaces:
•Inactive - The Ethernet interface is disabled.
•Down - The Ethernet interface does not have any physical ports associated with it or the
Ethernet interface is enabled but not connected.
•Speed / Duplex - The Ethernet interface is enabled and connected. This field displays the
port speed and duplex setting (Full or Half).
For cellular (mobile broadband) interfaces, see Section 7.13 on page 208 the Web Help for the
status that can appear.
For the auxiliary interface:
•Inactive - The auxiliary interface is disabled.
•Connected - The auxiliary interface is enabled and connected.
•Disconnected - The auxiliary interface is not connected.
For virtual interfaces, this field always displays Up. If the virtual interface is disabled, it does not
appear in the list.
For VLAN and bridge interfaces, this field always displays Up. If the VLAN or bridge interface is
disabled, it does not appear in the list.
For PPP interfaces:
•Connected - The PPP interface is connected.
•Disconnected - The PPP interface is not connected.
If the PPP interface is disabled, it does not appear in the list.
For WLAN interfaces:
•Up - The WLAN interface is enabled.
•Down - The WLAN interface is disabled.
HA Status This field displays the status of the interface in the virtual router.
•Active - This interface is the master interface in the virtual router.
•Stand-By - This interface is a backup interface in the virtual router.
•Fault - This VRRP group is not functioning in the virtual router right now. For example, this
might happen if the interface is down.
•n/a - Device HA is not active on the interface.
Zone This field displays the zone to which the interface is assigned.
IP Addr/Netmask This field displays the current IP address and subnet mask assigned to the interface. If the IP
address and subnet mask are 0.0.0.0, the interface is disabled or did not receive an IP address
and subnet mask via DHCP.
If this interface is a member of an active virtual router, this field displays the IP address it is
currently using. This is either the static IP address of the interface (if it is the master) or the
management IP address (if it is a backup).
IP Assignment This field displays how the interface gets its IP address.
•Static - This interface has a static IP address.
•DHCP Client - This interface gets its IP address from a DHCP server.
Services This field lists which services the interface provides to the network. Examples include DHCP
relay, DHCP server, DDNS, RIP, and OSPF. This field displays n/a if the interface does not provide
any services to the network.
Action Use this field to get or to update the IP address for the interface. Click Renew to send a new
DHCP request to a DHCP server. Click Connect to try to connect a PPPoE/PPTP interface. If the
interface cannot use one of these ways to get or to update its IP address, this field displays n/a.
Table 43 Monitor > System Status > Interface Status (continued)
LABEL DESCRIPTION
Chapter 7 Monitor
USG/ZyWALL User’s Guide
195
7.4 The Traffic Statistics Screen
Click Monitor > System Status > Traffic Statistics to display the Traffic Stat istics screen. This screen provides
basic information about the following for example:
• Most-visited Web sites and the number of times each one was visited. This count may not be accurate
in some cases because the Zyxel Device counts HTTP GET packets. Please see Table 44 on page 196
for more information.
• Most-used protocols or service ports and the amount of traffic on each one
• LAN IP with heaviest traffic and how much traffic has been sent to and from each one
Tunnel Interface
Status
This displays the details of the Zyxel Device’s configured tunnel interfaces.
Name This field displays the name of the interface.
Status The activate (light bulb) icon is lit when the entry is active and dimmed when the entry is
inactive.
Zone This field displays the zone to which the interface is assigned.
IP Address This is the IP address of the interface. If the interface is active (and connected), the Zyxel
Device tunnels local traffic sent to this IP address to the Remote Gateway Address.
My Address This is the interface or IP address uses to identify itself to the remote gateway. The Zyxel Device
uses this as the source for the packets it tunnels to the remote gateway.
Remote
Gateway
Address
This is the IP address or domain name of the remote gateway to which this interface tunnels
traffic.
Mode This field displays the tunnel mode that you are using.
Interface
Statistics
This table provides packet statistics for each interface.
Refresh Click this button to update the information in the screen.
Expand/Close Click this button to show or hide statistics for all the virtual interfaces on top of the Ethernet
interfaces.
Name This field displays the name of each interface. If there is a Expand icon (plus-sign) next to the
name, click this to look at the statistics for virtual interfaces on top of this interface.
Status This field displays the current status of the interface.
•Down - The interface is not connected.
•Speed / Duplex - The interface is connected. This field displays the port speed and duplex
setting (Full or Half).
This field displays Connected and the accumulated connection time (hh:mm:ss) when the PPP
interface is connected.
TxPkts This field displays the number of packets transmitted from the Zyxel Device on the interface
since it was last connected.
RxPkts This field displays the number of packets received by the Zyxel Device on the interface since it
was last connected.
Tx B/s This field displays the transmission speed, in bytes per second, on the interface in the one-
second interval before the screen updated.
Rx B/s This field displays the reception speed, in bytes per second, on the interface in the one-second
interval before the screen updated.
Table 43 Monitor > System Status > Interface Status (continued)
LABEL DESCRIPTION
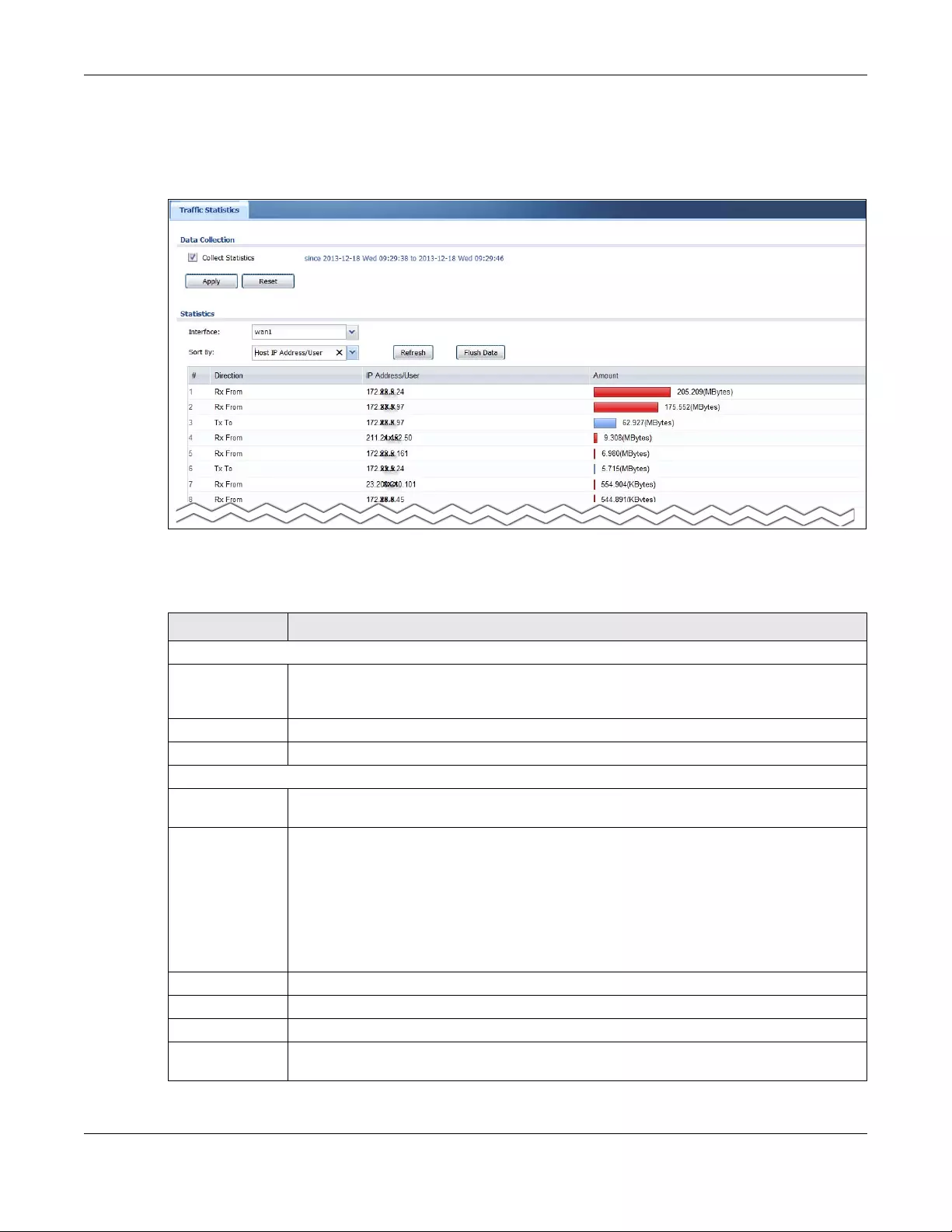
Chapter 7 Monitor
USG/ZyWALL User’s Guide
196
You use the Traffic Statistics screen to tell the Zyxel Device when to start and when to stop collecting
information for these reports. You cannot schedule data collection; you have to start and stop it
manually in the Traffic Statistics screen.
Figure 167 Monitor > System Status > Traffic Statistics
There is a limit on the number of records shown in the report. Please see Table 45 on page 197 for more
information. The following table describes the labels in this screen.
Table 44 Monitor > System Status > Traffic Statistics
LABEL DESCRIPTION
Data Collection
Collect Statistics Select this to have the Zyxel Device collect data for the report. If the Zyxel Device has already
been collecting data, the collection period displays to the right. The progress is not tracked
here real-time, but you can click the Refresh button to update it.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Statistics
Interface Select the interface from which to collect information. You can collect information from
Ethernet, VLAN, bridge and PPPoE/PPTP interfaces.
Sort By Select the type of report to display. Choices are:
•Host IP Address/User - displays the IP addresses or users with the most traffic and how much
traffic has been sent to and from each one.
•Service/Port - displays the most-used protocols or service ports and the amount of traffic for
each one.
•Web Site Hits - displays the most-visited Web sites and how many times each one has been
visited.
Each type of report has different information in the report (below).
Refresh Click this button to update the report display.
Flush Data Click this button to discard all of the screen’s statistics and update the report display.
These fields are available when the Traffic Type is Host IP Address/User.
# This field is the rank of each record. The IP addresses and users are sorted by the amount of
traffic.
Chapter 7 Monitor
USG/ZyWALL User’s Guide
197
The following table displays the maximum number of records shown in the report, the byte count limit,
and the hit count limit.
Direction This field indicates whether the IP address or user is sending or receiving traffic.
•Ingress- traffic is coming from the IP address or user to the Zyxel Device.
•Egress - traffic is going from the Zyxel Device to the IP address or user.
IP Address/User This field displays the IP address or user in this record. The maximum number of IP addresses or
users in this report is indicated in Table 45 on page 197.
Amount This field displays how much traffic was sent or received from the indicated IP address or user. If
the Direction is Ingress, a red bar is displayed; if the Direction is Egress, a blue bar is displayed.
The unit of measure is bytes, Kbytes, Mbytes or Gbytes, depending on the amount of traffic for
the particular IP address or user. The count starts over at zero if the number of bytes passes the
byte count limit. See Table 45 on page 197.
These fields are available when the Traffic Type is Service/Port.
# This field is the rank of each record. The protocols and service ports are sorted by the amount
of traffic.
Service/Port This field displays the service and port in this record. The maximum number of services and
service ports in this report is indicated in Table 45 on page 197.
Protocol This field indicates what protocol the service was using.
Direction This field indicates whether the indicated protocol or service port is sending or receiving traffic.
•Ingress - traffic is coming into the router through the interface
•Egress - traffic is going out from the router through the interface
Amount This field displays how much traffic was sent or received from the indicated service / port. If the
Direction is Ingress, a red bar is displayed; if the Direction is Egress, a blue bar is displayed. The
unit of measure is bytes, Kbytes, Mbytes, Gbytes, or Tbytes, depending on the amount of traffic
for the particular protocol or service port. The count starts over at zero if the number of bytes
passes the byte count limit. See Table 45 on page 197.
These fields are available when the Traffic Type is Web Site Hits.
# This field is the rank of each record. The domain names are sorted by the number of hits.
Web Site This field displays the domain names most often visited. The Zyxel Device counts each page
viewed on a Web site as another hit. The maximum number of domain names in this report is
indicated in Table 45 on page 197.
Hits This field displays how many hits the Web site received. The Zyxel Device counts hits by
counting HTTP GET packets. Many Web sites have HTTP GET references to other Web sites, and
the Zyxel Device counts these as hits too. The count starts over at zero if the number of hits
passes the hit count limit. See Table 45 on page 197.
Table 45 Maximum Values for Reports
LABEL DESCRIPTION
Maximum Number of Records 20
Byte Count Limit 264 bytes; this is just less than 17 million terabytes.
Hit Count Limit 264 hits; this is over 1.8 x 1019 hits.
Table 44 Monitor > System Status > Traffic Statistics (continued)
LABEL DESCRIPTION
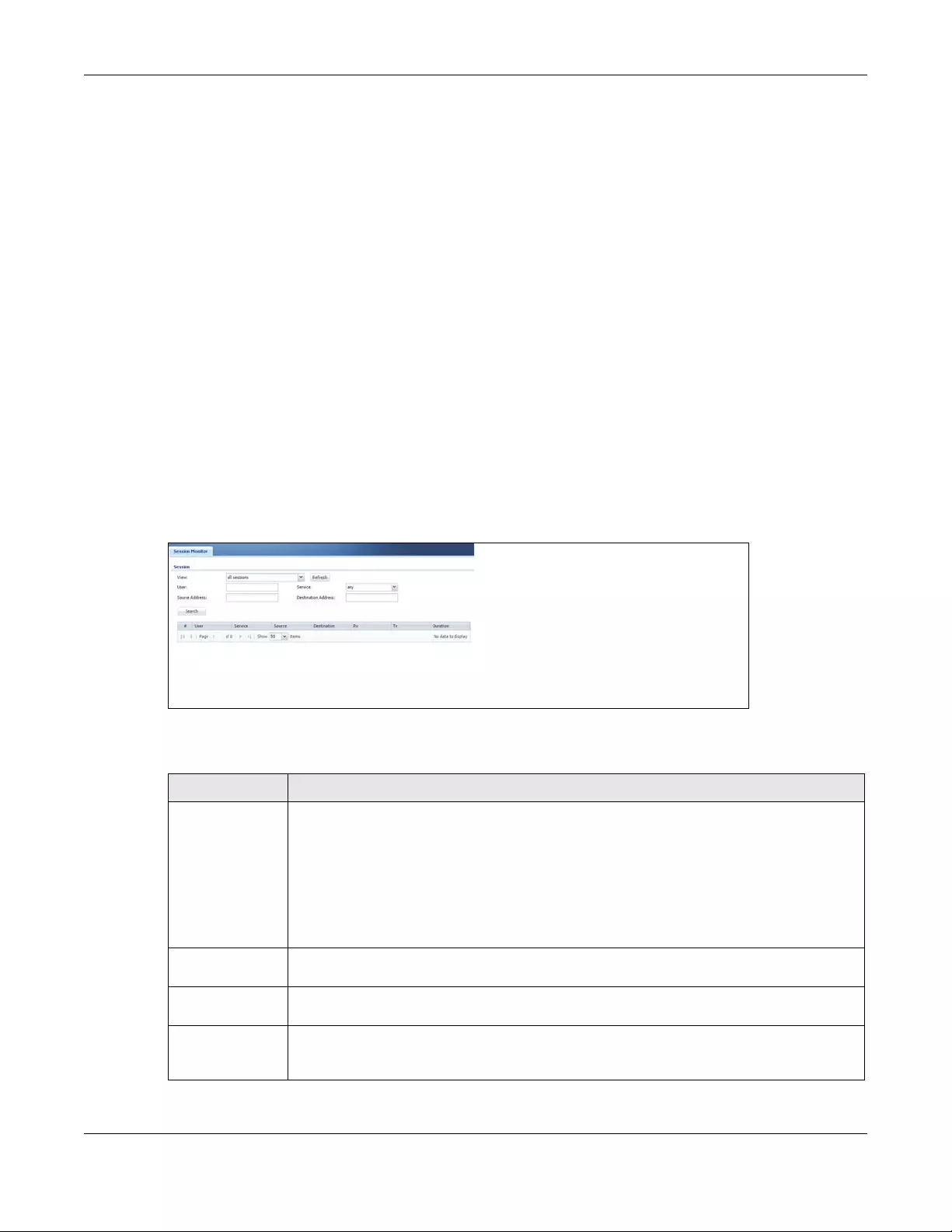
Chapter 7 Monitor
USG/ZyWALL User’s Guide
198
7.5 The Session Monitor Screen
The Session Monitor screen displays all established sessions that pass through the Zyxel Device for
debugging or statistical analysis. It is not possible to manage sessions in this screen. The following
information is displayed.
• User who started the session
• Protocol or service port used
• Source address
• Destination address
• Number of bytes received (so far)
• Number of bytes transmitted (so far)
• Duration (so far)
You can look at all established sessions that passed through the Zyxel Device by user, service, source IP
address, or destination IP address. You can also filter the information by user, protocol / service or service
group, source address, and/or destination address and view it by user.
Click Monitor > System Status > Session Monitor to display the following screen.
Figure 168 Monitor > System Status > Session Monitor
The following table describes the labels in this screen.
Table 46 Monitor > System Status > Session Monitor
LABEL DESCRIPTION
View Select how you want the established sessions that passed through the Zyxel Device to be
displayed. Choices are:
•sessions by users - display all active sessions grouped by user
•sessions by services - display all active sessions grouped by service or protocol
•sessions by source IP - display all active sessions grouped by source IP address
•sessions by destination IP - display all active sessions grouped by destination IP address
•all sessions - filter the active sessions by the User, Service, Source Address, and Destination
Address, and display each session individually (sorted by user).
Refresh Click this button to update the information on the screen. The screen also refreshes
automatically when you open and close the screen.
The User, Service, Source Address, and Destination Address fields display if you view all
sessions. Select your desired filter criteria and click the Refresh button to filter the list of sessions.
User This field displays when View is set to all sessions. Type the user whose sessions you want to
view. It is not possible to type part of the user name or use wildcards in this field; you must enter
the whole user name.
Chapter 7 Monitor
USG/ZyWALL User’s Guide
199
7.6 IGMP Statistics
The Internet Group Management Protocol (IGMP) Statistics is used by Zyxel Device IP hosts to inform
adjacent router about multicast group memberships. It can also be used for one-to-many networking
applications such as online streaming video and gaming, distribution of company newsletters, updating
address book of mobile computer users in the field allowing more efficient use of resources when
supporting these types of applications. Click Monitor > System Status > IGMP Statistics to open the
following screen.
Service This field displays when View is set to all sessions. Select the service or service group whose
sessions you want to view. The Zyxel Device identifies the service by comparing the protocol
and destination port of each packet to the protocol and port of each services that is defined.
Source This field displays when View is set to all sessions. Type the source IP address whose sessions you
want to view. You cannot include the source port.
Destination This field displays when View is set to all sessions. Type the destination IP address whose
sessions you want to view. You cannot include the destination port.
Rx This field displays the amount of information received by the source in the active session.
Tx This field displays the amount of information transmitted by the source in the active session.
Duration This field displays the length of the active session in seconds.
Active Sessions This is the total number of established sessions that passed through the ZyWALL which matched
the search criteria.
Show Select the number of active sessions displayed on each page. You can use the arrow keys on
the right to change pages.
# This field is the rank of each record. The names are sorted by the name of user in active
session. You can use the pull down menu on the right to choose sorting method.
User This field displays the user in each active session.
If you are looking at the sessions by users (or all sessions) report, click + or - to display or hide
details about a user’s sessions.
Service This field displays the protocol used in each active session.
If you are looking at the sessions by services report, click + or - to display or hide details about
a protocol’s sessions.
Source This field displays the source IP address and port in each active session.
If you are looking at the sessions by source IP report, click + or - to display or hide details about
a source IP address’s sessions.
Destination This field displays the destination IP address and port in each active session.
If you are looking at the sessions by destination IP report, click + or - to display or hide details
about a destination IP address’s sessions.
Rx This field displays the amount of information received by the source in the active session.
Tx This field displays the amount of information transmitted by the source in the active session.
Duration This field displays the length of the active session in seconds.
Table 46 Monitor > System Status > Session Monitor (continued)
LABEL DESCRIPTION
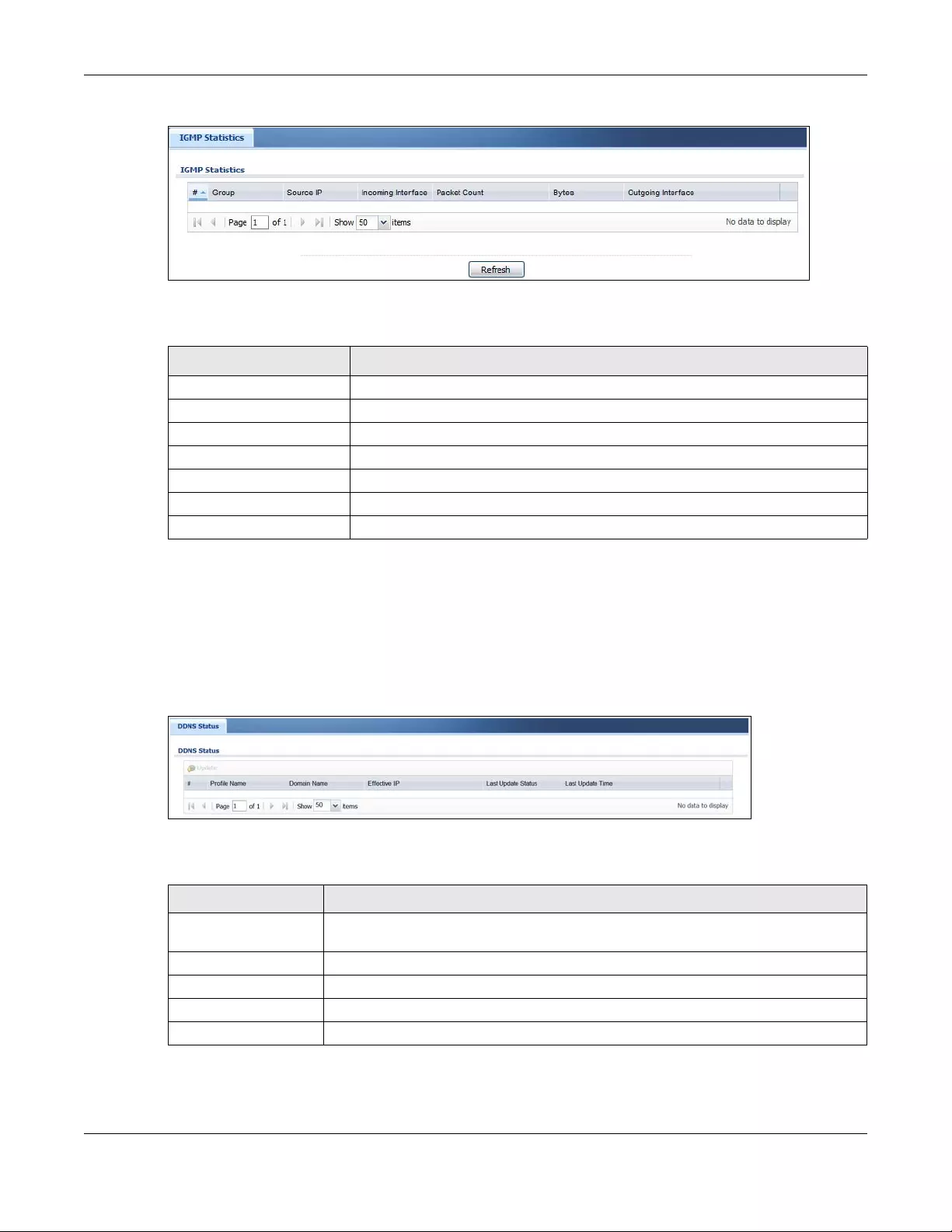
Chapter 7 Monitor
USG/ZyWALL User’s Guide
200
Figure 169 Monitor > System Status > IGMP Statistics
The following table describes the labels in this screen.
7.7 The DDNS Status Screen
The DDNS Status screen shows the status of the Zyxel Device’s DDNS domain names. Click Monitor >
System Status > DDNS Status to open the following screen.
Figure 170 Monitor > System Status > DDNS Status
The following table describes the labels in this screen.
Table 47 Monitor > System Status > IGMP Statistics
LABEL DESCRIPTION
# This field is a sequential value, and it is not associated with a specific I GMP Statistics.
Group This field displays the group of devices in the IGMP.
Source IP This field displays the host source IP information of the IGMP.
Incoming Interface This field displays the incoming interface that’s connected on the IGMP.
Packet Count This field displays the packet size of the data being transferred.
Bytes This field displays the size of the data being transferred in Byes.
Outgoing Interface This field displays the outgoing interface that’s connected on the IGMP.
Table 48 Monitor > System Status > DDNS Status
LABEL DESCRIPTION
Update Click this to have the Zyxel Device update the profile to the DDNS server. The Zyxel
Device attempts to resolve the IP address for the domain name.
# This field is a sequential value, and it is not associated with a specific DDNS server.
Profile Name This field displays the descriptive profile name for this entry.
Domain Name This field displays each domain name the Zyxel Device can route.
Effective IP This is the (resolved) IP address of the domain name.
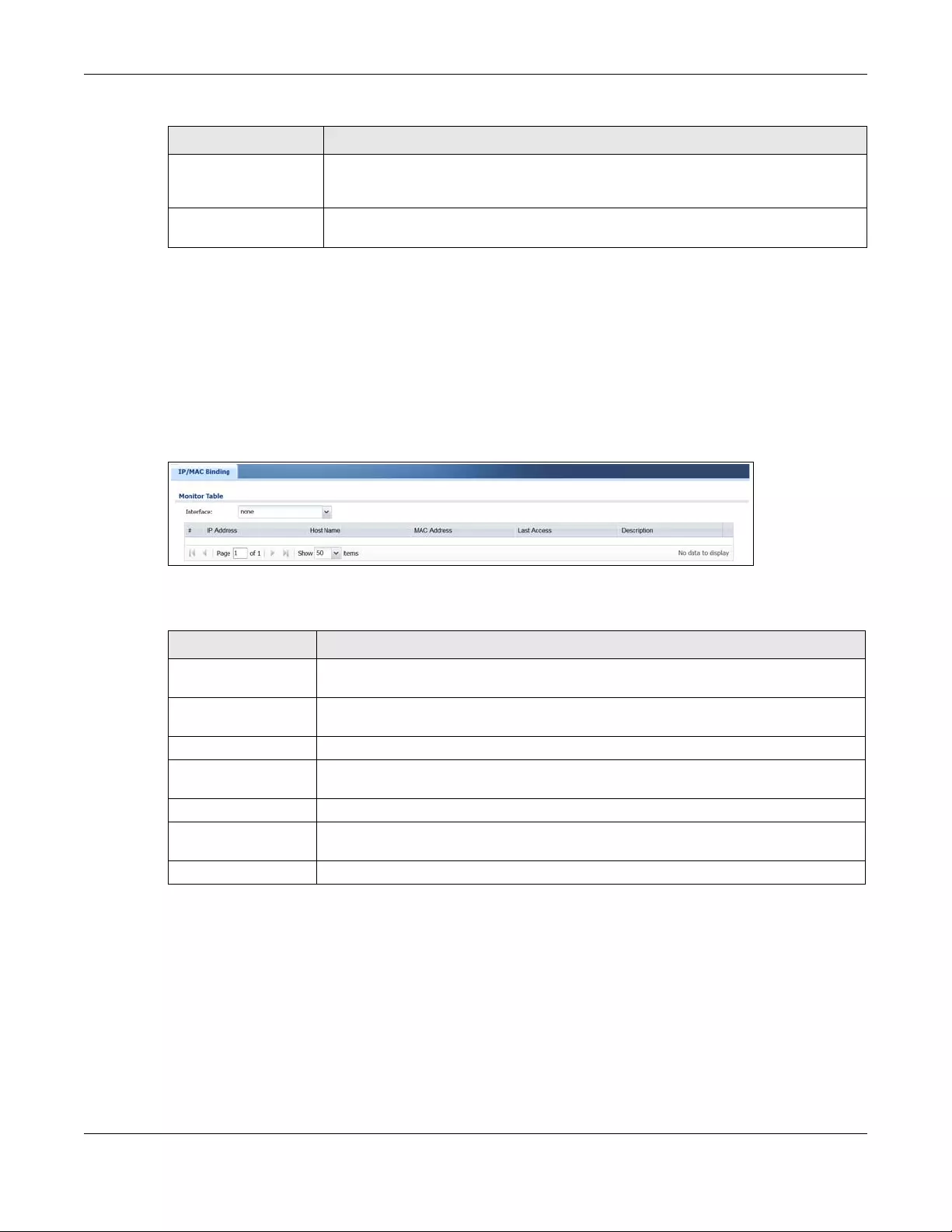
Chapter 7 Monitor
USG/ZyWALL User’s Guide
201
7.8 IP/MAC Binding
Click Monitor > System Status > IP/MAC Binding to open the IP/MAC Binding screen. This screen lists the
devices that have received an IP address from Zyxel Device interfaces with IP/MAC binding enabled
and have ever established a session with the Zyxel Device. Devices that have never established a
session with the Zyxel Device do not display in the list.
Figure 171 Monitor > System Status > IP/MAC Binding
The following table describes the labels in this screen.
7.9 The Login Users Screen
Use this screen to look at a list of the users currently logged into the Zyxel Device. To access this screen,
click Monitor > System Status > Login Users.
Last Update Status This shows whether the last attempt to resolve the IP address for the domain name was
successful or not. Updating means the Zyxel Device is currently attempting to resolve the
IP address for the domain name.
Last Update Time This shows when the last attempt to resolve the IP address for the domain name
occurred (in year-month-day hour:minute:second format).
Table 48 Monitor > System Status > DDNS Status (continued)
LABEL DESCRIPTION
Table 49 Monitor > System Status > IP/MAC Binding
LABEL DESCRIPTION
Interface Select a Zyxel Device interface that has IP/MAC binding enabled to show to which
devices it has assigned an IP address.
#This field is a sequential value, and it is not associated with a specific IP/MAC binding
entry.
IP Address This is the IP address that the Zyxel Device assigned to a device.
Host Name This field displays the name used to identify this device on the network (the computer
name). The Zyxel Device learns these from the DHCP client requests.
MAC Address This field displays the MAC address to which the IP address is currently assigned.
Last Access This is when the device last established a session with the Zyxel Device through this
interface.
Description This field displays the description of the IP/MAC binding.
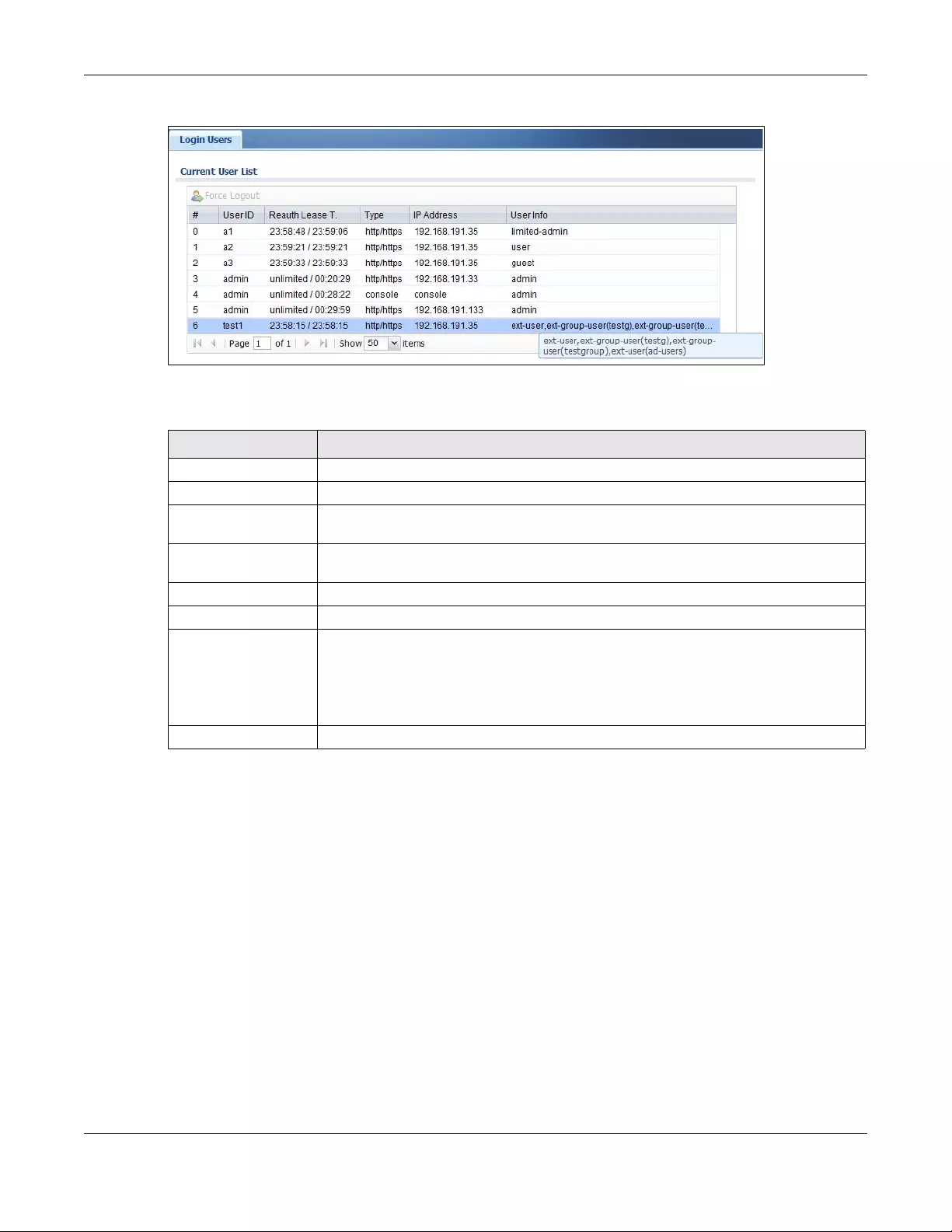
Chapter 7 Monitor
USG/ZyWALL User’s Guide
202
Figure 172 Monitor > System Status > Login Users
The following table describes the labels in this screen.
7.10 The Dynamic Guest Screen
Dynamic guest accounts can be automatically generated for guest users by using a connected
statement printer or the web configurator with the guest-manager account (see Chapter 21 on page
468 for more information). A dynamic guest account has a dynamically-created user name and
password. Guest users can log in with the dynamic guest accounts when connecting to an SSID for a
Table 50 Monitor > System Status > Login Users
LABEL DESCRIPTION
Force Logout Select a user ID and click this icon to end a user’s session.
# This field is a sequential value and is not associated with any entry.
User ID This field displays the user name of each user who is currently logged in to the Zyxel
Device.
Reauth Lease T. This field displays the amount of reauthentication time remaining and the amount of
lease time remaining for each user.
Type This field displays the way the user logged in to the Zyxel Device.
IP Address This field displays the IP address of the computer used to log in to the Zyxel Device.
User Info This field displays the types of user accounts the Zyxel Device uses. If the user type is ext-
user (external user), this field will show its external-group information when you move your
mouse over it.
If the external user matches two external-group objects, both external-group object
names will be shown.
Refresh Click this button to update the information in the screen.
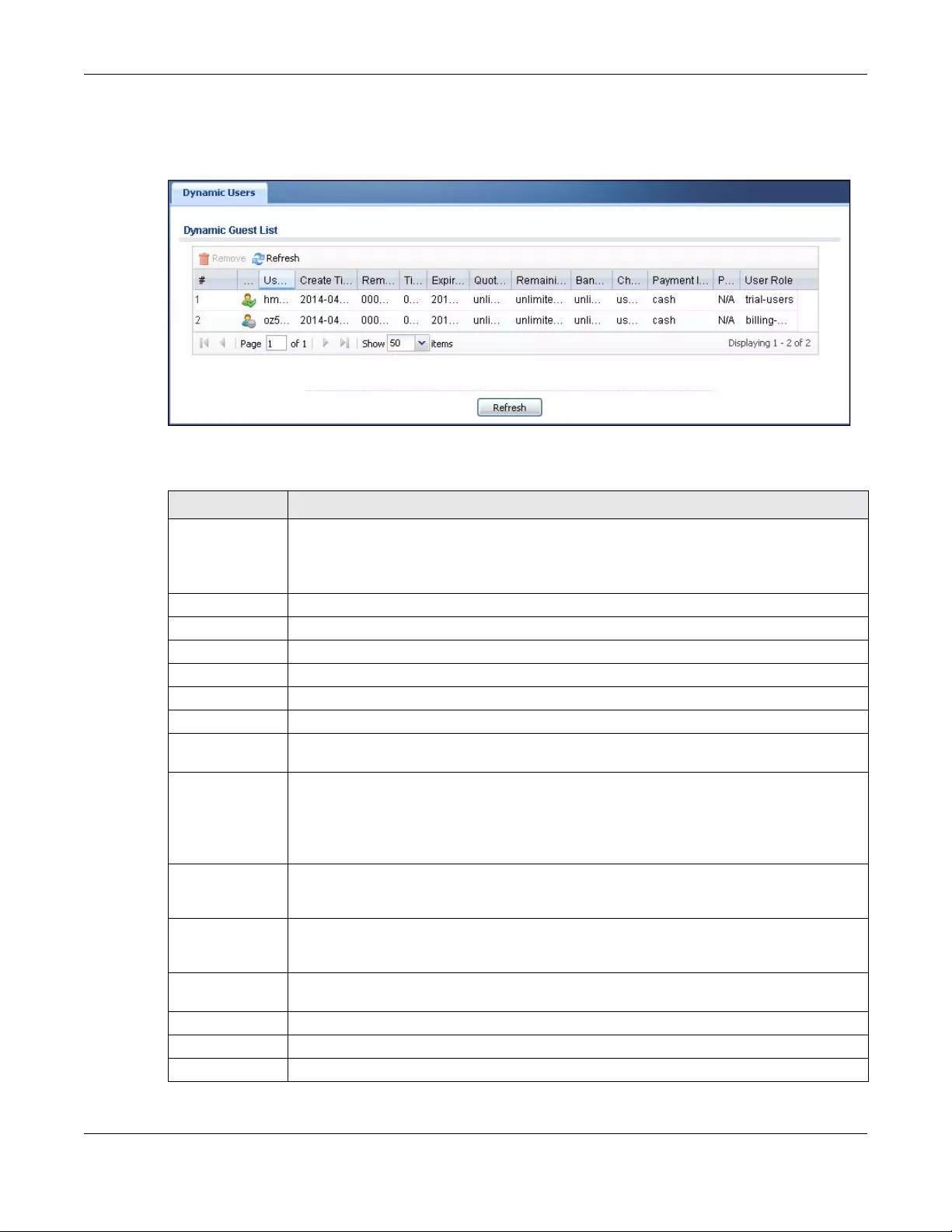
Chapter 7 Monitor
USG/ZyWALL User’s Guide
203
specified time unit. Use this screen to look at a list of dynamic guest user accounts on the Zyxel Device’s
local database. To access this screen, click Monitor > System Status > Dynamic Guest.
Figure 173 Monitor > System Status > Dynamic Guest
The following table describes the labels in this screen.
Table 51 Monitor > System Status > Dynamic Guest
LABEL DESCRIPTION
Remove Select an entry and click this button to remove it from the list.
Note: If you delete a valid user account which is in use, the Zyxel Device ends the
user session.
Refresh Click this button to update the information in the screen.
# This is the index number of the dynamic guest account in the list.
Status This field displays whether an account expires or not.
Username This field displays the user name of the account.
Create Time This field displays when the account was created.
Remaining Time This field displays the amount of Internet access time remaining for each account.
Time Period This field displays the total account of time the account can use to access the Internet through
the Zyxel Device.
Expiration Time This field displays the date and time the account becomes invalid.
Note: Once the time allocated to a dynamic account is used up or a dynamic
account remains un-used after the expiration time, the account is deleted
from the account list.
Quota (T/U/D) This field displays how much data in both directions (Total) or upstream data (Upload) and
downstream data (Download) can be transmitted through the WAN interface before the
account expires.
Remaining Quota
(T/U/D)
This field displays the remaining amount of data that can be transmitted or received by each
account. You can see the amount of either data in both directions (Total) or upstream data
(Upload) and downstream data (Download).
Bandwidth (U/D) This field displays the maximum upstream (Upload) and downstream (Download) bandwidth
allowed for the user account in kilobits per second.
Charge This field displays the total cost of the account.
Payment Info This field displays the method of payment for each account.
Phone Num This field displays the mobile phone number for the account.
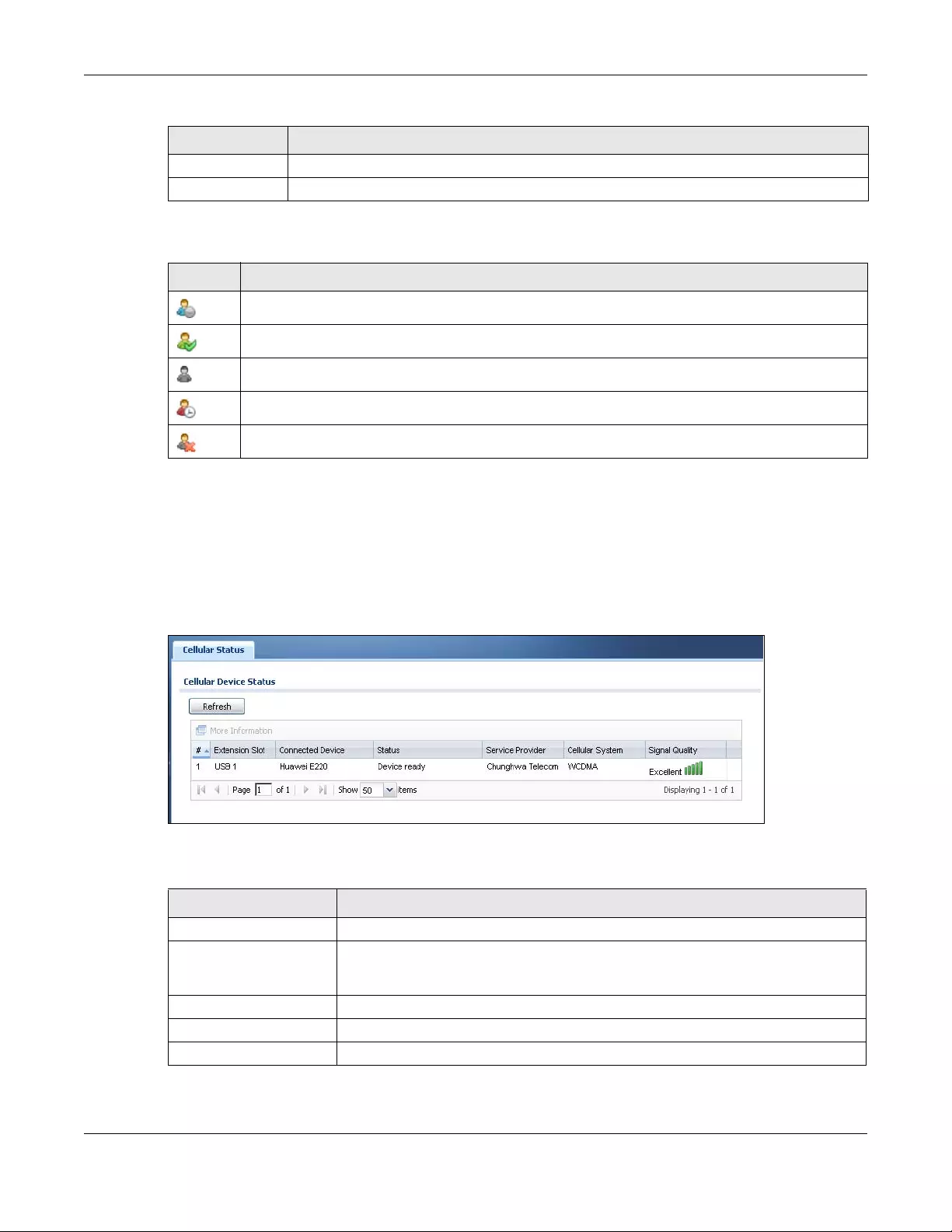
Chapter 7 Monitor
USG/ZyWALL User’s Guide
204
The following table describes the icons in this screen.
7.11 Cellular Status Screen
This screen displays your mobile broadband connection status. Click Monitor > System Status > Cellular
Status to display this screen.
Figure 174 Monitor > System Status > Cellular Status
The following table describes the labels in this screen.
User Role This field displays the role of the account.
Refresh Click this button to update the information in the screen.
Table 52 Monitor > System Status > Dynamic Guest Icons
LABEL DESCRIPTION
This guest account is un-used.
This guest account is in use and online.
This guest account has been used but is offline now.
This guest account expired.
This guest account has been deleted.
Table 51 Monitor > System Status > Dynamic Guest (continued)
LABEL DESCRIPTION
Table 53 Monitor > System Status > Cellular Status
LABEL DESCRIPTION
Refresh Click this button to update the information in the screen.
More Information Click this to display more information on your mobile broadband, such as the signal
strength, IMEA/ESN and IMSI. This is only available when the mobile broadband device
attached and activated on your Zyxel Device. Refer to Section 7.11.1 on page 206.
# This field is a sequential value, and it is not associated with any interface.
Extension Slot This field displays where the entry’s cellular card is located.
Connected Device This field displays the model name of the cellular card.
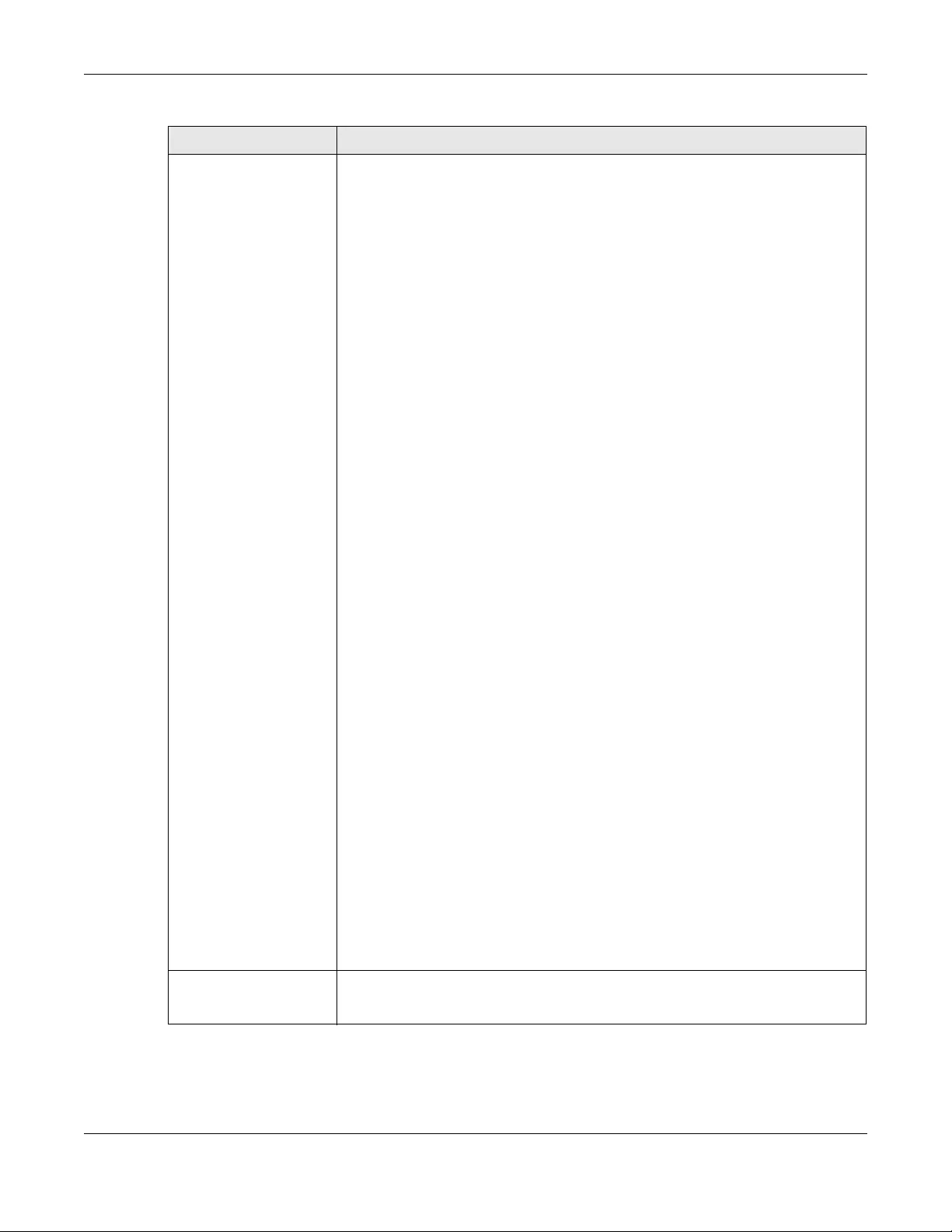
Chapter 7 Monitor
USG/ZyWALL User’s Guide
205
Status • No device - no mobile broadband device is connected to the Zyxel Device.
•No Service - no mobile broadband network is available in the area; you cannot
connect to the Internet.
•Limited Service - returned by the service provider in cases where the SIM card is
expired, the user failed to pay for the service and so on; you cannot connect to
the Internet.
•Device detected - displays when you connect a mobile broadband device.
•Device error - a mobile broadband device is connected but there is an error.
•Probe device fail - the Zyxel Device’s test of the mobile broadband device failed.
•Probe device ok - the Zyxel Device’s test of the mobile broadband device
succeeded.
•Init device fail - the Zyxel Device was not able to initialize the mobile broadband
device.
•Init device ok - the Zyxel Device initialized the mobile broadband card.
•Check lock fail - the Zyxel Device’s check of whether or not the mobile
broadband device is locked failed.
•Device locked - the mobile broadband device is locked.
•SIM error - there is a SIM card error on the mobile broadband device.
•SIM locked-PUK - the PUK is locked on the mobile broadband device’s SIM card.
•SIM locked-PIN - the PIN is locked on the mobile broadband device’s SIM card.
•Unlock PUK fail - Your attempt to unlock a WCDMA mobile broadband device’s
PUK failed because you entered an incorrect PUK.
•Unlock PIN fail - Your attempt to unlock a WCDMA mobile broadband device’s
PIN failed because you entered an incorrect PIN.
•Unlock device fail - Your attempt to unlock a CDMA2000 mobile broadband
device failed because you entered an incorrect device code.
•Device unlocked - You entered the correct device code and unlocked a
CDMA2000 mobile broadband device.
•Get dev-info fail - The Zyxel Device cannot get cellular device information.
•Get dev-info ok - The Zyxel Device succeeded in retrieving mobile broadband
device information.
•Searching network - The mobile broadband device is searching for a network.
•Get signal fail - The mobile broadband device cannot get a signal from a network.
•Network found - The mobile broadband device found a network.
•Apply config - The Zyxel Device is applying your configuration to the mobile
broadband device.
•Inactive - The mobile broadband interface is disabled.
•Active - The mobile broadband interface is enabled.
•Incorrect device - The connected mobile broadband device is not compatible
with the Zyxel Device.
•Correct device - The Zyxel Device detected a compatible mobile broadband
device.
•Set band fail - Applying your band selection was not successful.
•Set band ok - The Zyxel Device successfully applied your band selection.
•Set profile fail - Applying your ISP settings was not successful.
•Set profile ok - The Zyxel Device successfully applied your ISP settings.
•PPP fail - The Zyxel Device failed to create a PPP connection for the cellular
interface.
•Need auth-password - You need to enter the password for the mobile broadband
card in the cellular edit screen.
•Device ready - The Zyxel Device successfully applied all of your configuration and
you can use the mobile broadband connection.
Service Provider This displays the name of your network service provider. This shows Limited Service if
the service provider has stopped service to the mobile broadband card. For example
if the bill has not been paid or the account has expired.
Table 53 Monitor > System Status > Cellular Status (continued)
LABEL DESCRIPTION
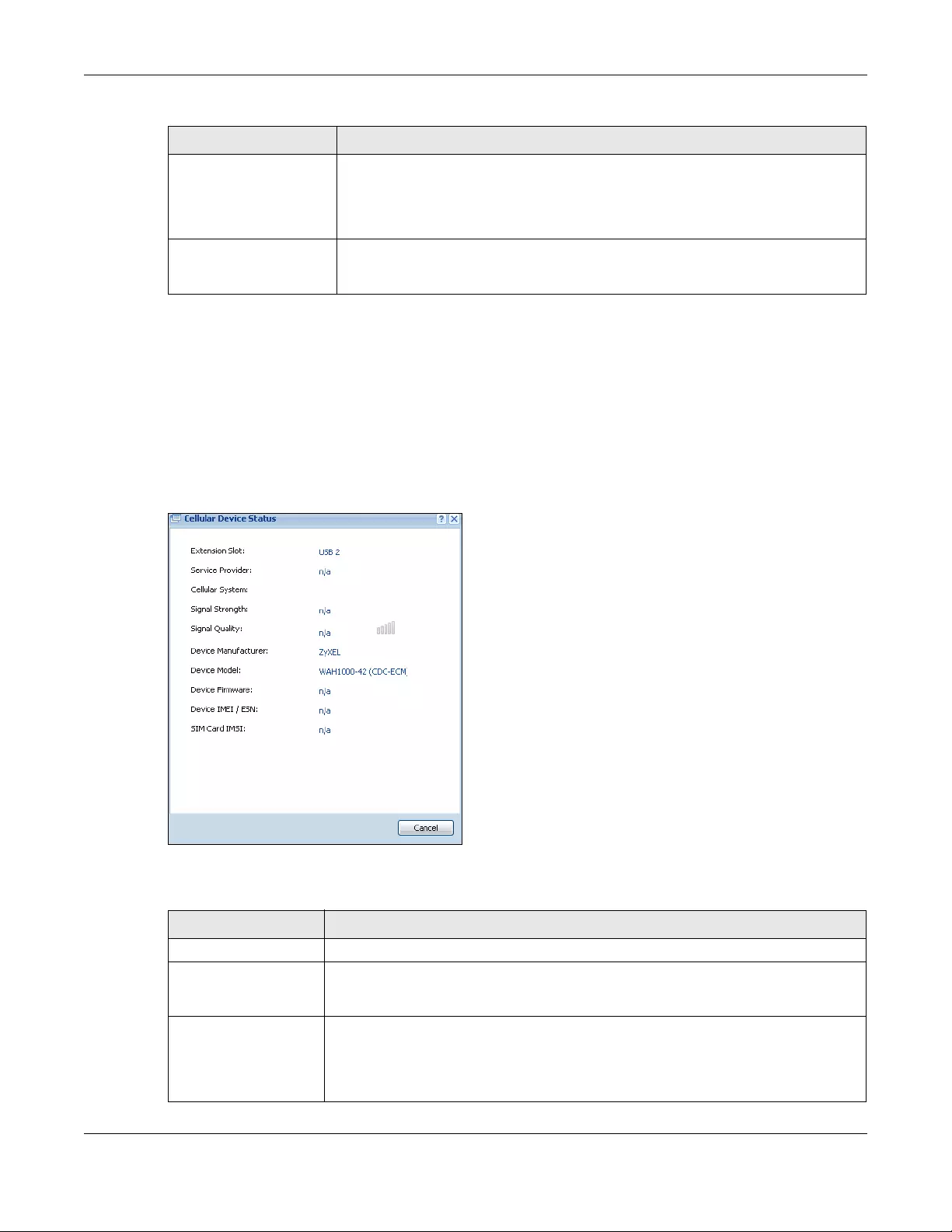
Chapter 7 Monitor
USG/ZyWALL User’s Guide
206
7.11.1 More Information
This screen displays more information on your mobile broadband, such as the signal strength, IMEA/ESN
and IMSI that helps identify your mobile broadband device and SIM card. Click Monitor > System Status
> More Information to display this screen.
Note: This screen is only available when the mobile broadband device is attached to and
activated on the Zyxel Device.
Figure 175 Monitor > System Status > More Information
The following table describes the labels in this screen.
Cellular System This field displays what type of cellular network the mobile broadband connection is
using. The network type varies depending on the mobile broadband card you inserted
and could be UMTS, UMTS/HSDPA, GPRS or EDGE when you insert a GSM mobile
broadband card, or 1xRTT, EVDO Rev.0 or EVDO Rev.A when you insert a CDMA
mobile broadband card.
Signal Quality This displays the strength of the signal. The signal strength mainly depends on the
antenna output power and the distance between your Zyxel Device and the service
provider’s base station.
Table 53 Monitor > System Status > Cellular Status (continued)
LABEL DESCRIPTION
Table 54 Monitor > System Status > More Information
LABEL DESCRIPTION
Extension Slot This field displays where the entry’s cellular card is located.
Service Provider This displays the name of your network service provider. This shows Limited Service if the
service provider has stopped service to the mobile broadband card. For example if the
bill has not been paid or the account has expired.
Cellular System This field displays what type of cellular network the mobile broadband connection is
using. The network type varies depending on the mobile broadband card you inserted
and could be UMTS, UMTS/HSDPA, GPRS or EDGE when you insert a GSM mobile
broadband card, or 1xRTT, EVDO Rev.0 or EVDO Rev.A when you insert a CDMA mobile
broadband card.
Chapter 7 Monitor
USG/ZyWALL User’s Guide
207
7.12 The UPnP Port Status Screen
Use this screen to look at the NAT port mapping rules that UPnP creates on the Zyxel Device. To access
this screen, click Monitor > System Status > UPnP Port Status.
Figure 176 Monitor > System Status > UPnP Port Status
The following table describes the labels in this screen.
Signal Strength This is the S ignal Quality measured in dBm.
Signal Quality This displays the strength of the signal. The signal strength mainly depends on the
antenna output power and the distance between your Zyxel Device and the service
provider’s base station.
Device Manufacturer This shows the name of the company that produced the mobile broadband device.
Device Model This field displays the model name of the cellular card.
Device Firmware This shows the software version of the mobile broadband device.
Device IMEI/ESN IMEI (International Mobile Equipment Identity) is a 15-digit code in decimal format that
identifies the mobile broadband device.
ESN (Electronic Serial Number) is an 8-digit code in hexadecimal format that identifies
the mobile broadband device.
SIM Card IMSI IMSI (International Mobile Subscriber Identity) is a 15-digit code that identifies the SIM
card.
Table 54 Monitor > System Status > More Information (continued)
LABEL DESCRIPTION
Table 55 Monitor > System Status > UPnP Port Status
LABEL DESCRIPTION
Remove Select an entry and click this button to remove it from the list.
# This is the index number of the UPnP-created NAT mapping rule entry.
Remote Host This field displays the source IP address (on the WAN) of inbound IP packets. Since this is often
a wild-card, the field may be blank.
When the field is blank, the Zyxel Device forwards all traffic sent to the External Port on the
WAN interface to the Internal Client on the Internal Port.
When this field displays an external IP address, the NAT rule has the Zyxel Device forward
inbound packets to the Internal Client from that IP address only.
Chapter 7 Monitor
USG/ZyWALL User’s Guide
208
7.13 USB Storage Screen
This screen displays information about a connected USB storage device. Click Monitor > System Status >
USB Storage to display this screen.
Figure 177 Monitor > System Status > USB Storage
The following table describes the labels in this screen.
External Port This field displays the port number that the Zyxel Device “listens” non the WAN port) for
connection requests destined for the NAT rule’s Internal Port and Internal Client. The Zyxel
Device forwards incoming packets (from the WAN) with this port number to the Internal Client
on the Internal Port (on the LAN). If the field displays “0”, the Zyxel Device ignores the Internal
Port value and forwards requests on all external port numbers (that are otherwise unmapped)
to the Internal Client.
Protocol This field displays the protocol of the NAT mapping rule (TCP or UDP).
Internal Port This field displays the port number on the Internal Client to which the Zyxel Device should
forward incoming connection requests.
Internal Client This field displays the DNS host name or IP address of a client on the LAN. Multiple NAT clients
can use a single port simultaneously if the internal client field is set to 255.255.255.255 for UDP
mappings.
Internal Client Type This field displays the type of the client application on the LAN.
Description This field displays a text explanation of the NAT mapping rule.
Delete All Click this to remove all mapping rules from the NAT table.
Refresh Click this button to update the information in the screen.
Table 55 Monitor > System Status > UPnP Port Status (continued)
LABEL DESCRIPTION
Table 56 Monitor > System Status > USB Storage
LABEL DESCRIPTION
Device description This is a basic description of the type of USB device.
Usage This field displays how much of the USB storage device’s capacity is currently being
used out of its total capacity and what percentage that makes.
Filesystem This field displays what file system the USB storage device is formatted with. This field
displays Unknown if the file system of the USB storage device is not supported by the
Zyxel Device, such as NTFS.
Speed This field displays the connection speed the USB storage device supports.
Chapter 7 Monitor
USG/ZyWALL User’s Guide
209
7.14 Ethernet Neighbor Screen
The Ethernet Neighbor screen allows you to view the Zyxel Device’s neighboring devices in one place.
It uses Smart Connect, that is Link Layer Discovery Protocol (LLDP) for discovering and configuring LLDP-
aware devices in the same broadcast domain as the Zyxel Device that you’re logged into using the
web configurator.
LLDP is a layer-2 protocol that allows a network device to advertise its identity and capabilities on the
local network. It also allows the device to maintain and store information from adjacent devices which
are directly connected to the network device. This helps you discover network changes and perform
necessary network reconfiguration and management.
Note: Enable Smart Connect in the System > ZON screen.
See also System > ZON for more information on the Zyxel One Network (ZON) utility that uses the Zyxel
Discovery Protocol (ZDP) for discovering and configuring ZDP-aware Zyxel devices in the same network
as the computer on which the ZON utility is installed.
Click Monitor > System Status > Ethernet Neighbor to see the following screen
Figure 178 Monitor > System Status > Ethernet Neighbor
Status Ready - you can have the Zyxel Device use the USB storage device.
Click Remove Now to stop the Zyxel Device from using the USB storage device so you
can remove it.
Unused - the connected USB storage device was manually unmounted by using the
Remove Now button or for some reason the Zyxel Device cannot mount it.
Click Use It to have the Zyxel Device mount a connected USB storage device. This
button is grayed out if the file system is not supported (unknown) by the Zyxel Device.
none - no USB storage device is connected.
Detail This field displays any other information the Zyxel Device retrieves from the USB storage
device.
•Deactivated - the use of a USB storage device is disabled (turned off) on the Zyxel
Device.
•OutofSpace - the available disk space is less than the disk space full threshold.
•Mounting - the Zyxel Device is mounting the USB storage device.
•Removing - the Zyxel Device is unmounting the USB storage device.
•none - the USB device is operating normally or not connected.
Table 56 Monitor > System Status > USB Storage (continued)
LABEL DESCRIPTION
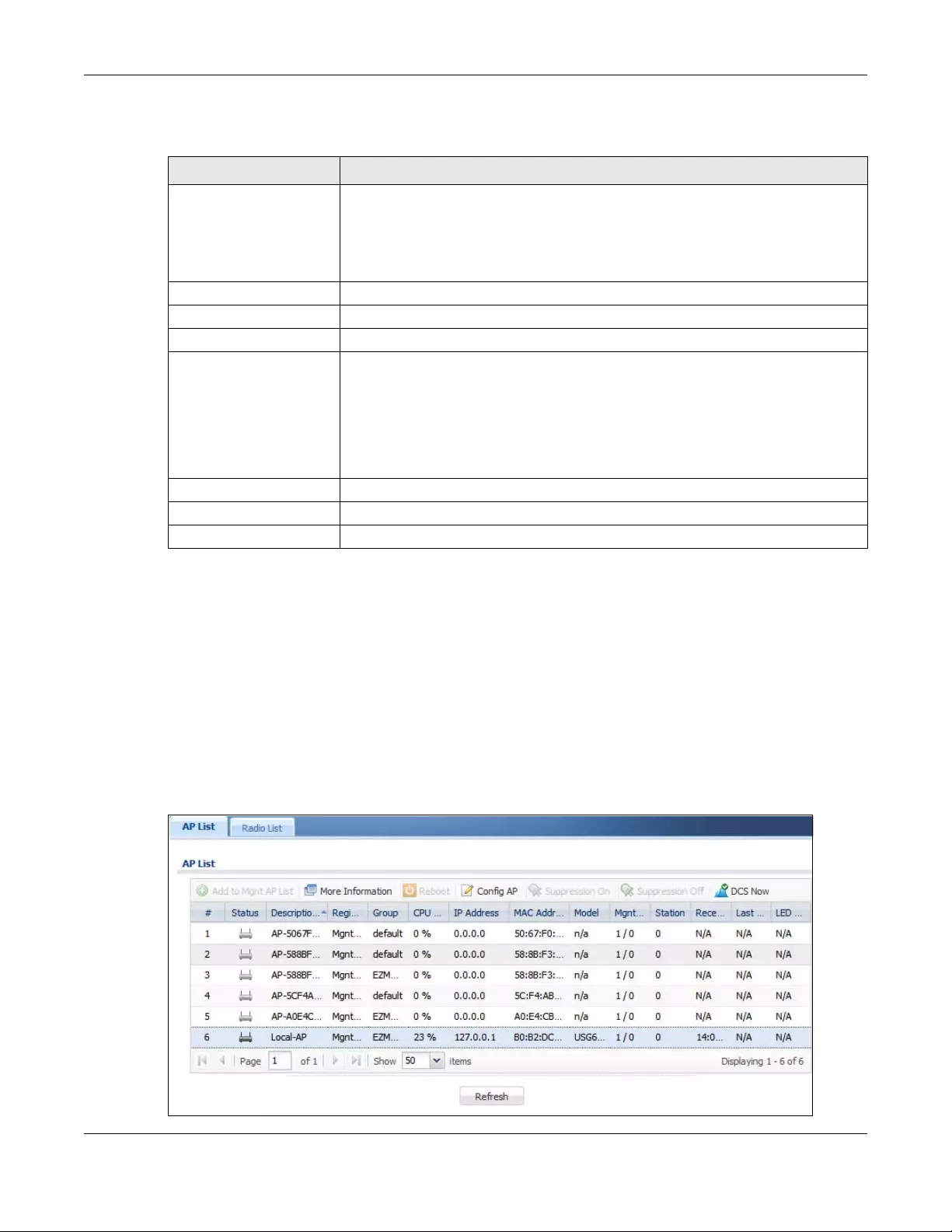
Chapter 7 Monitor
USG/ZyWALL User’s Guide
210
The following table describes the fields in the previous screen.
7.15 Wireless
Wireless contains AP information, Station Info and Detected Device menus.
7.15.1 Wireless AP Information: AP List
The AP Information menu contains AP List and Radio List screens. Click Monitor > Wireless > AP
Information to display the AP List screen.
Figure 179 Monitor > Wireless > AP List
Table 57 Monitor > System Status > Ethernet Neighbor
LABEL DESCRIPTION
Local Port (Description) This field displays the port of the Zyxel Device, on which the neighboring device is
discovered.
For Zyxel Devices that support Port Role, if ports 3 to 5 are grouped together and there
is a connection to P5 only, the Zyxel Device will display P3 as the interface port
number (even though there is no connection to that port).
Model Name This field displays the model name of the discovered device.
System Name This field displays the system name of the discovered device.
Firmware Version This field displays the firmware version of the discovered device.
Port (Description) This field displays the first internal port on the discovered device. Internal is an
interface type displayed in the Network > Interface > Ethernet > Edit screen. For
example, if P1 and P2 are WAN, P3 to P5 are LAN, and P6 is DMZ, then Zyxel Device will
display P3 as the first internal interface port number.
For Zyxel Devices that support Port Role, if ports 3 to 5 are grouped together and there
is a connection to P5 only, the Zyxel Device will display P3 as the first internal interface
port number (even though there is no connection to that port).
IP Address This field displays the IP address of the discovered device.
MAC Address This field displays the MAC address of the discovered device.
Refresh Click this button to update the information in the screen.
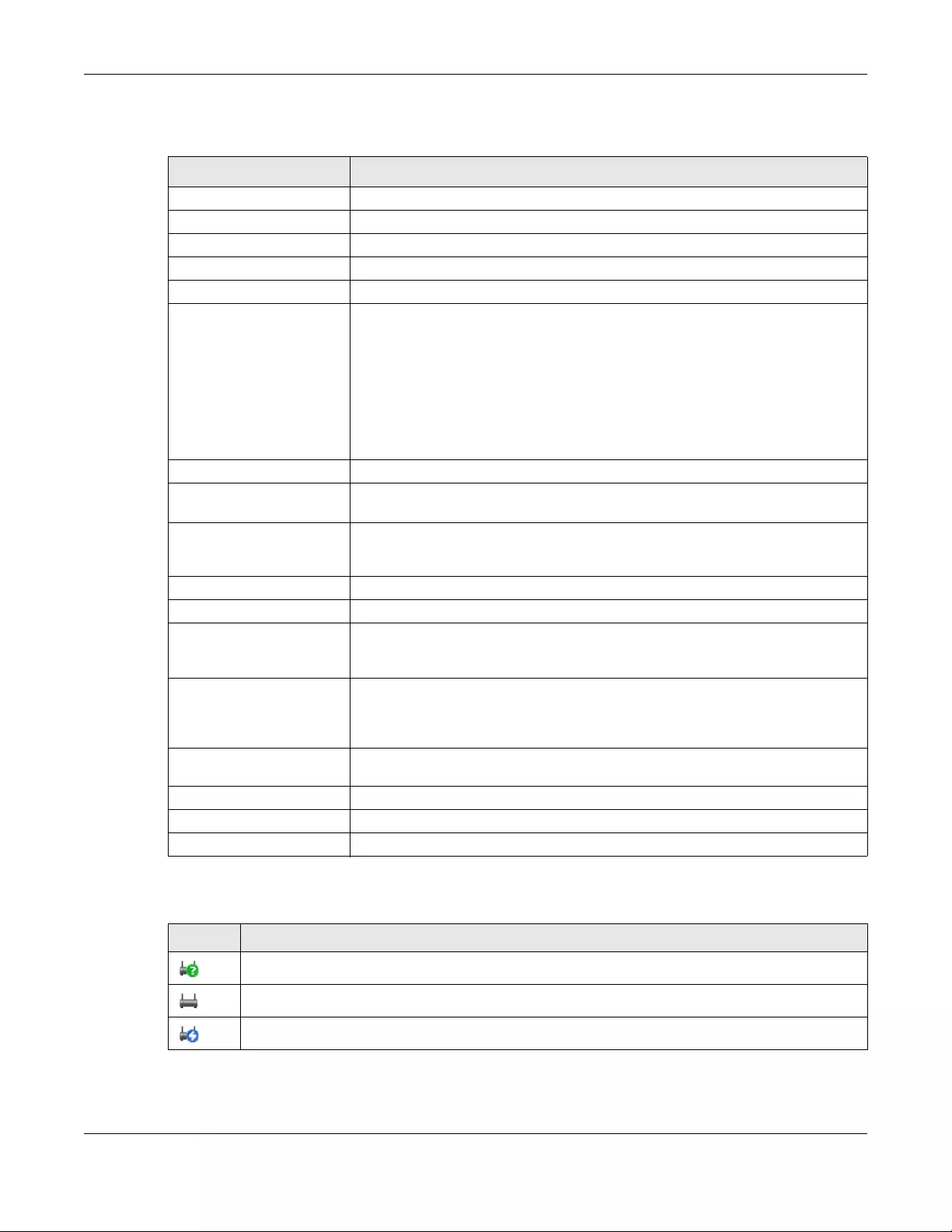
Chapter 7 Monitor
USG/ZyWALL User’s Guide
211
The following table describes the labels in this screen.
The following table describes the icons in this screen.
Table 58 Monitor > Wireless > AP Information
LABEL DESCRIPTION
Add to Mgnt AP List Click this to add new Access Points
More Information Click this icon to see AP Information and Station count.
Reboot Select an AP and click this button to force it to restart.
Suppression On Click this button to turn suppression on.
Suppression Off Click this button to turn suppression off.
DCS Now Select one or multiple APs and click this button to use DCS (Dynamic Channel
Selection) to allow the AP to automatically find a less-used channel in an
environment where there are many APs and there may be interference.
Note: You should have enabled DCS in the applied AP radio profile before
the APs can use DCS.
Note: DCS is not supported on the radio which is working in repeater AP
mode.
# This field is a sequential value, and it is not associated with a specific AP.
Status This field displays the on-line or off-line status of the AP, move the cursor to the AP
icon and a status pop up message will appear.
Registration This field displays the registration information of the AP. You can set the AP’s
registration at Configuration > Wireless > Controller screen. APs must be connected
to the Zyxel Device by a wired connection or network.
IP Address This field displays the IP address of the AP.
MAC Address This field displays the MAC address of the AP.
Model This field displays the AP’s hardware model information. It displays N/A (not
applicable) only when the AP disconnects from the Zyxel Device and the
information is unavailable as a result.
Mgnt. VLAN ID (AC/AP) This displays the Access Controller (the Zyxel Device) and runtime management
VLAN ID setting for the AP. VLAN Conflict displays if the AP’s management VLAN ID
does not match the Mgmnt. VLAN ID(AC). This field displays n/a if the Zyxel Device
cannot get VLAN information from the AP.
Description This field displays the AP’s description, which you can configure by selecting the AP’s
entry and clicking the Edit button.
Station This field displays the station count information.
Recent On-Line This field displays the latest date and time that the AP was logged on.
Last Off-Line This field displays the date and time that the AP was last logged out.
Table 59 Monitor > Wireless > AP Information > AP List Icons
LABEL DESCRIPTION
This AP is not on the management list.
This AP is on the management list and online.
This AP is in the process of having its firmware updated.
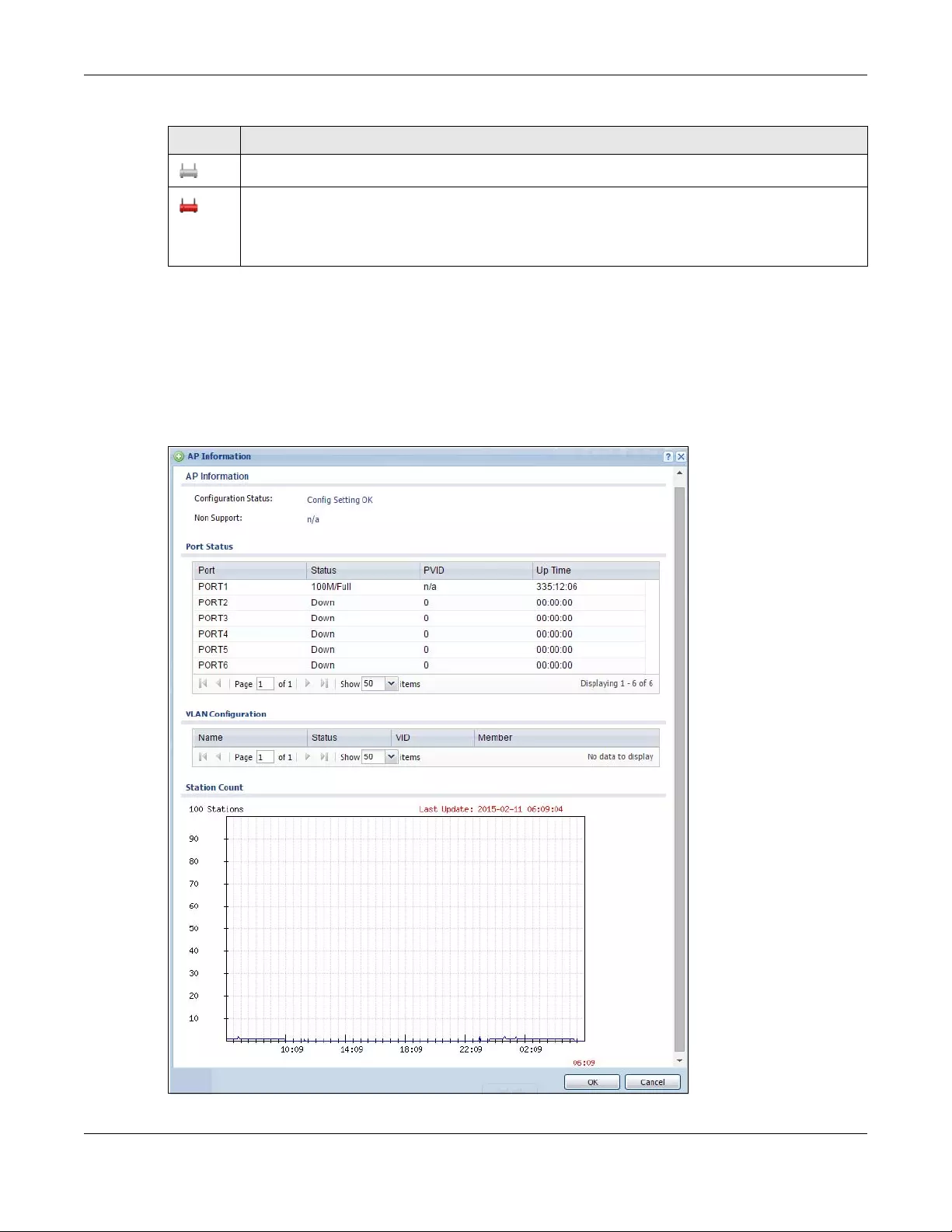
Chapter 7 Monitor
USG/ZyWALL User’s Guide
212
7.15.2 AP List More Information
Use this screen to look at station statistics for the connected AP. To access this screen, select an entry
and click the More Information button in the AP List screen. Use this screen to look at configuration
information, port status and station statistics for the connected AP. To access this screen, select an entry
and click the More Information button in the AP List screen.
Figure 180 Monitor > Wireless > AP Information > AP List > More Information
This AP is on the management list but offline.
This indicates one of the following cases:
• This AP has a runtime management VLAN ID setting that conflicts with the VLAN ID setting on the
Access Controller (the Zyxel Device).
• A setting the Zyxel Device assigns to this AP does not match the AP’s capability.
Table 59 Monitor > Wireless > AP Information > AP List Icons (continued)
LABEL DESCRIPTION
Chapter 7 Monitor
USG/ZyWALL User’s Guide
213
The following table describes the labels in this screen.
Table 60 Monitor > Wireless > AP Information > AP List > More Information
LABEL DESCRIPTION
Configuration
Status
This displays whether or not any of the AP’s configuration is in conflict with the Zyxel Device’s
settings for the AP.
Non Support If any of the AP’s configuration conflicts with the Zyxel Device’s settings for the AP, this field
displays which configuration conflicts. It displays n/a if none of the AP’s configuration
conflicts with the Zyxel Device’s settings for the AP.
Port Status
Port This shows the name of the physical Ethernet port on the Zyxel Device.
Status This field displays the current status of each physical port on the AP.
Down - The port is not connected.
Speed / Duplex - The port is connected. This field displays the port speed and duplex setting
(Full or Half).
PVID This shows the port’s PVID.
A PVID (Port VLAN ID) is a tag that adds to incoming untagged frames received on a port so
that the frames are forwarded to the VLAN group that the tag defines.
Up Time This field displays how long the physical port has been connected.
VLAN
Configuration
Name This shows the name of the VLAN.
Status This displays whether or not the VLAN is activated.
VID This shows the VLAN ID number.
Member This field displays the Ethernet port(s) that is a member of this VLAN.
Station Count
The y-axis represents the number of connected stations.
The x-axis shows the time over which a station was connected.
Last Update This field displays the date and time the information in the window was last updated.
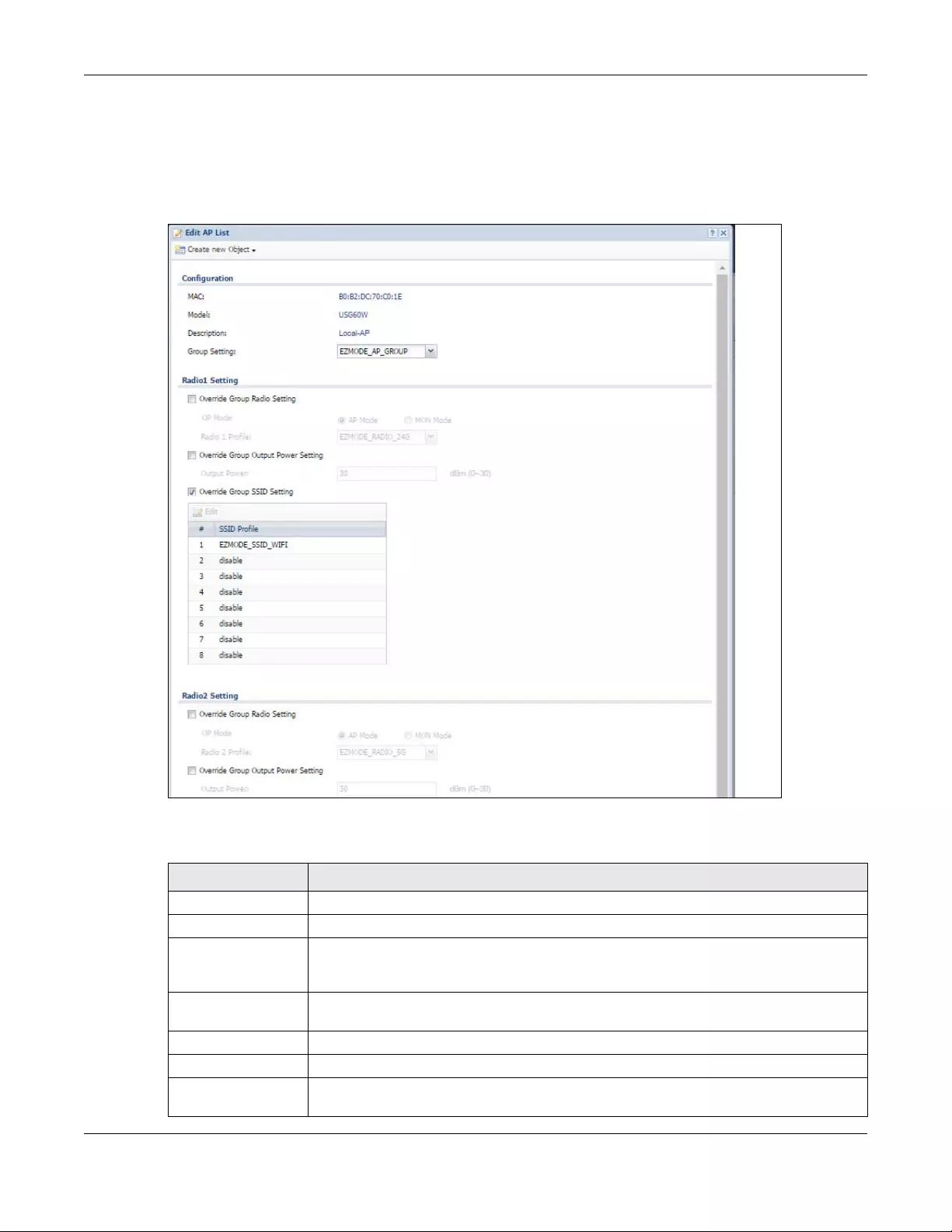
Chapter 7 Monitor
USG/ZyWALL User’s Guide
214
7.15.3 Config AP
Select an AP and click the Config AP button in the Monitor > Wireless > AP List table to display this
screen.
Figure 181 Monitor > Wireless > AP List > Config AP
Each field is described in the following table.
Table 61 Monitor > Wireless > AP List > Config AP
LABEL DESCRIPTION
Create new Object Use this menu to create a new Radio Profile object to associate with this AP.
MAC This displays the MAC address of the selected AP.
Model This field displays the AP’s hardware model information. It displays N/A (not applicable) only
when the AP disconnects from the Zyxel Device and the information is unavailable as a
result.
Description Enter a description for this AP. You can use up to 31 characters, spaces and underscores
allowed.
Group Setting Select an AP group to which you want this AP to belong.
Radio 1/2 Setting
Override Group
Radio Setting
Select this option to overwrite the AP radio settings with the settings you configure here.
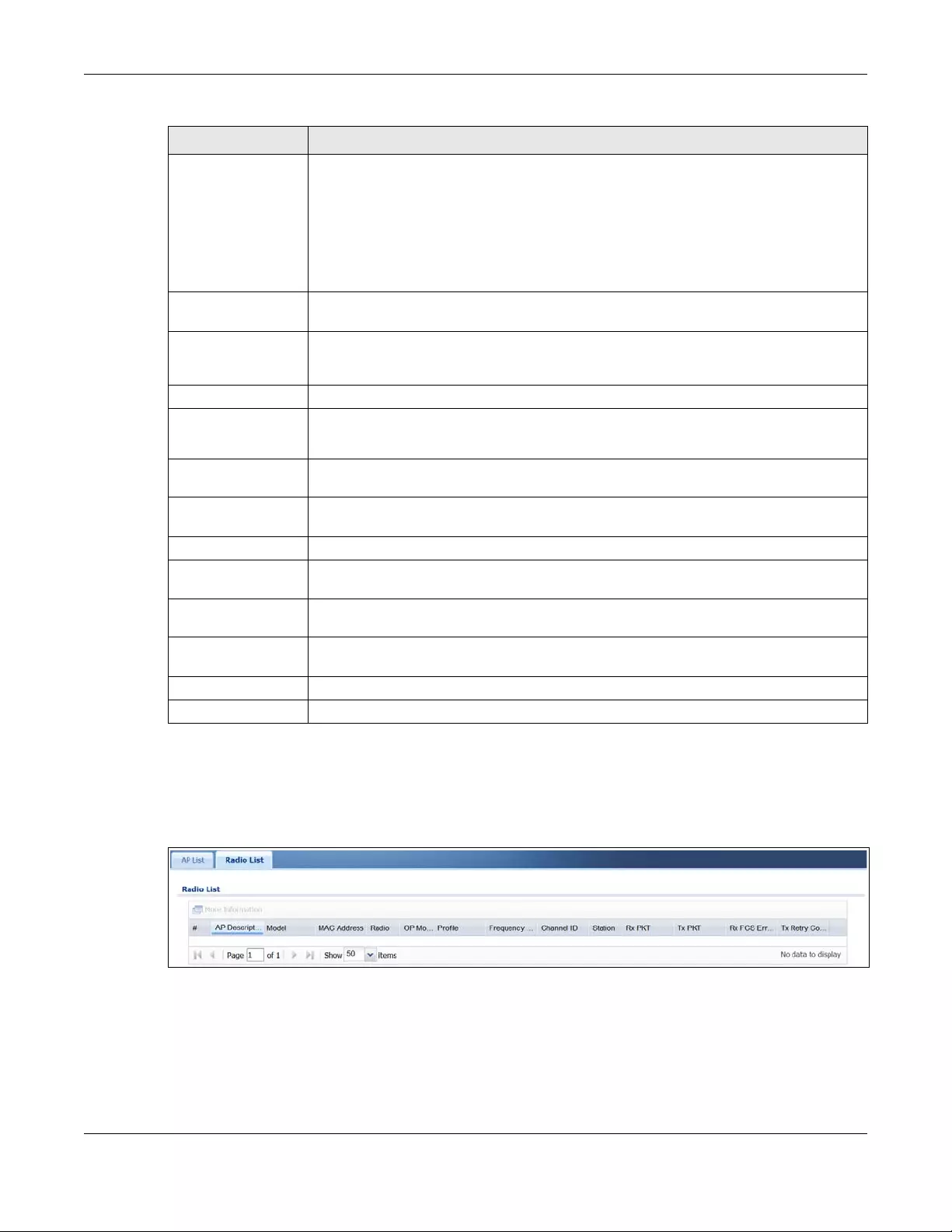
Chapter 7 Monitor
USG/ZyWALL User’s Guide
215
7.15.4 Wireless AP Information: Radio List
Click Monitor > Wireless > AP Information > Radio List to display the Radio List screen.
Figure 182 Monitor > Wireless > Radio List
Radio 1/2 OP Mode Select the operating mode for radio 1 or radio 2.
AP Mode means the AP can receive connections from wireless clients and pass their data
traffic through to the Zyxel Device to be managed (or subsequently passed on to an
upstream gateway for managing).
MON Mode means the AP monitors the broadcast area for other APs, then passes their
information on to the Zyxel Device where it can be determined if those APs are friendly or
rogue. If an AP is set to this mode it cannot receive connections from wireless clients.
Radio 1/2 Profile Select a profile from the list. If no profile exists, you can create a new one through the
Create new Object menu.
Override Group
Output Power
Setting
Select this option to overwrite the AP output power setting with the setting you configure
here.
Output Power Set the output power of the AP.
Override Group SSID
Setting
Select this option to overwrite the AP SSID profile setting with the setting you configure here.
This section allows you to associate an SSID profile with the radio.
Edit Select an SSID and click this button to reassign it. The selected SSID becomes editable
immediately upon clicking.
#This is the index number of the SSID profile. You can associate up to eight SSID profiles with
an AP radio.
SSID Profile Indicates which SSID profile is associated with this radio profile.
Force Overwrite
VLAN Config
Select this to have the Zyxel Device change the AP’s management VLAN to match the
configuration in this screen.
Management VLAN
ID
Enter a VLAN ID for this AP.
As Native VLAN Select this option to treat this VLAN ID as a VLAN created on the Zyxel Device and not one
assigned to it from outside the network.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to close the window with changes unsaved.
Table 61 Monitor > Wireless > AP List > Config AP (continued)
LABEL DESCRIPTION
Chapter 7 Monitor
USG/ZyWALL User’s Guide
216
The following table describes the labels in this screen.
Table 62 Monitor > Wireless > Radio List
LABEL DESCRIPTION
More Information Click this icon to see the traffic statistics, station count, SSID, Security Mode and
VLAN ID information on the AP.
# This field is a sequential value, and it is not associated with a specific radio.
AP Description Enter a description for this AP. You can use up to 31 characters, spaces and
underscores allowed.
Model This field displays the AP’s hardware model information. It displays N/A (not
applicable) only when the AP disconnects from the Zyxel Device and the
information is unavailable as a result.
MAC Address This field displays the MAC address of the AP.
Radio This field displays the Radio number. For example 1.
OP Mode This field displays the operating mode of the AP. It displays n/a for the profile for a
radio not using an AP profile.
AP Mode means the AP can receive connections from wireless clients and pass their
data traffic through to the Zyxel Device to be managed (or subsequently passed on
to an upstream gateway for managing).
Profile This field displays the AP Profile for the Radio. It displays n/A for the radio profile not
using an AP profile. It displays default if using a default profile.
Frequency Band This field displays the WLAN frequency band using the IEEE 802.11 a/b/g/n standard
of 2.4 or 5 GHz.
Channel ID This field displays the WLAN channels using the IEEE 802.11 protocols.
Station This field displays the station count information.
Rx PKT This field displays the data packets of incoming traffic on the AP.
Tx PKT This field displays the data packet of outgoing traffic on the AP.
Rx FCS Error Count This field displays the erroneous data packet count received and detected by
Frame Check Sequence (FCS)
Tx Retry Count This field displays the data packet count that were transmitted for retry.
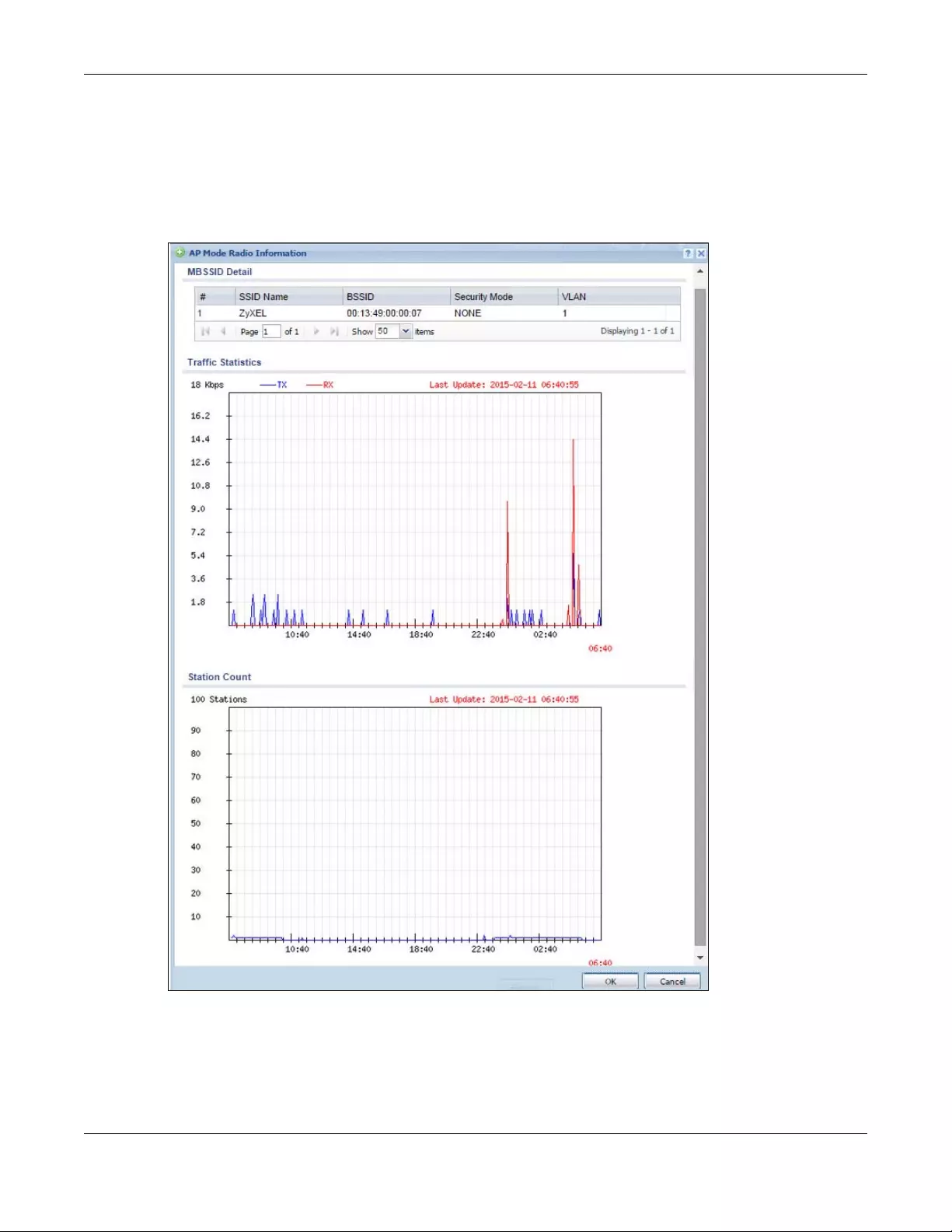
Chapter 7 Monitor
USG/ZyWALL User’s Guide
217
7.15.5 Radio List More Information
This screen allows you to view detailed information about a selected radio’s SSID(s), wireless traffic and
wireless clients for the preceding 24 hours. To access this window, select an entry and click the More
Information button in the Radio List screen.
Figure 183 Monitor > Wireless > AP Information > Radio List > More Information
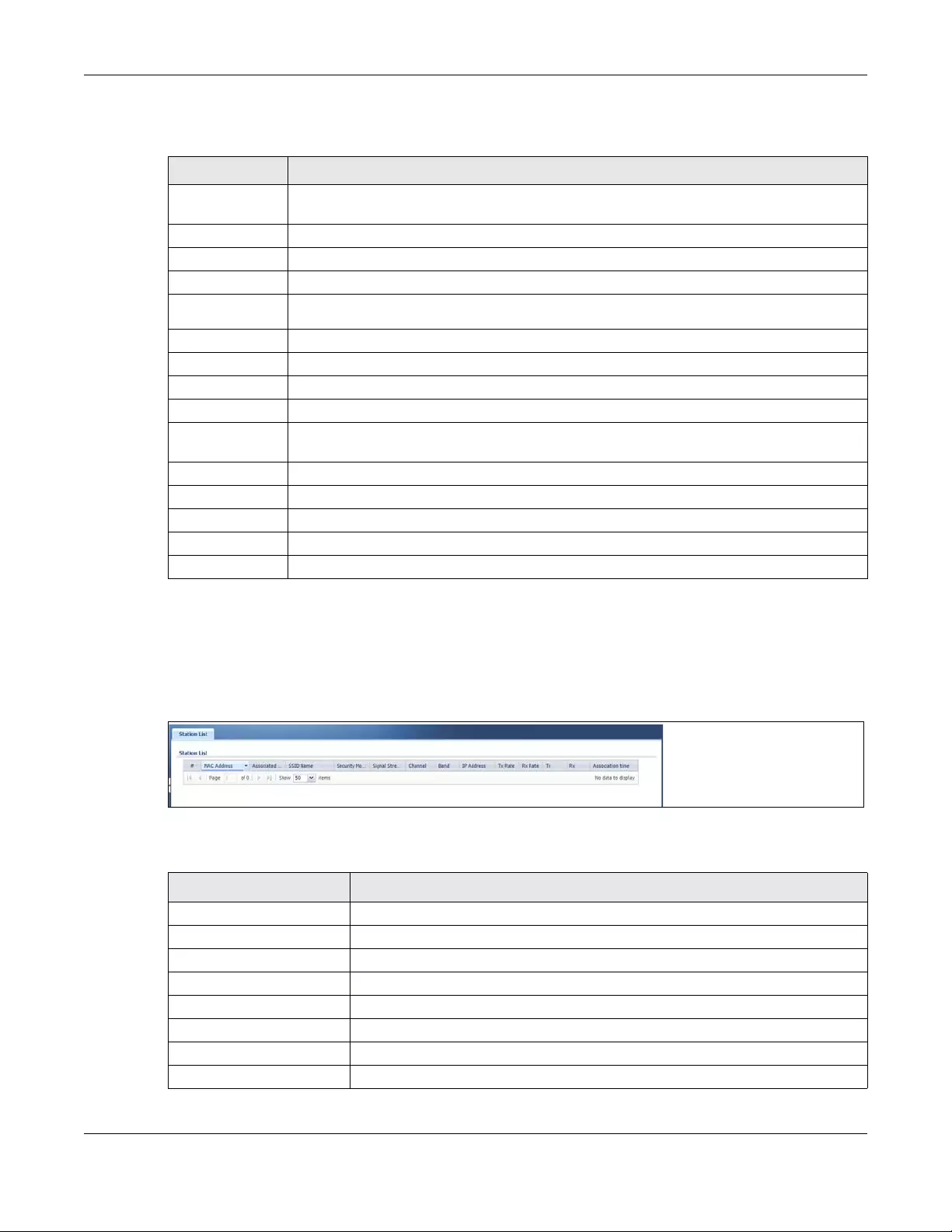
Chapter 7 Monitor
USG/ZyWALL User’s Guide
218
The following table describes the labels in this screen.
7.15.6 Wireless Station Info
This screen displays information about connected wireless stations. Click Monitor > Wireless > Station
Information to display this screen.
Figure 184 Monitor > Wireless > Station List
The following table describes the labels in this screen.
Table 63 Monitor > Wireless > AP Info > Radio List > More Information
LABEL DESCRIPTION
MBSSID Detail This list shows information about the SSID(s) that is associated with the radio over the preceding
24 hours.
# This is the items sequential number in the list. It has no bearing on the actual data in this list.
SSID Name This displays an SSID associated with this radio. There can be up to eight maximum.
BSSID This displays the MAC address associated with the SSID.
Security
Mode This displays the security mode in which the SSID is operating.
VLAN This displays the VLAN ID associated with the SSID.
Traffic Statistics This graph displays the overall traffic information about the radio over the preceding 24 hours.
y-axis This axis represents the amount of data moved across this radio in megabytes per second.
x-axis This axis represents the amount of time over which the data moved across this radio.
Station Count This graph displays information about all the wireless clients that have connected to the radio
over the preceding 24 hours.
y-axis The y-axis represents the number of connected wireless clients.
x-axis The x-axis shows the time over which a wireless client was connected.
Last Update This field displays the date and time the information in the window was last updated.
OK Click this to close this window.
Cancel Click this to close this window.
Table 64 Monitor > Wireless > Station List
LABEL DESCRIPTION
# This field is a sequential value, and it is not associated with a specific station.
MAC Address This field displays the MAC address of the station.
Associated AP This field displays the APs that are associated with the station.
SSID Name This field displays the SSID names of the station.
Security Mode This field displays the security mode the station is using.
Signal Strength This field displays the signal strength of the station.
IP Address This field displays the IP address of the station.
Tx Rate This field displays the transmit data rate of the station.
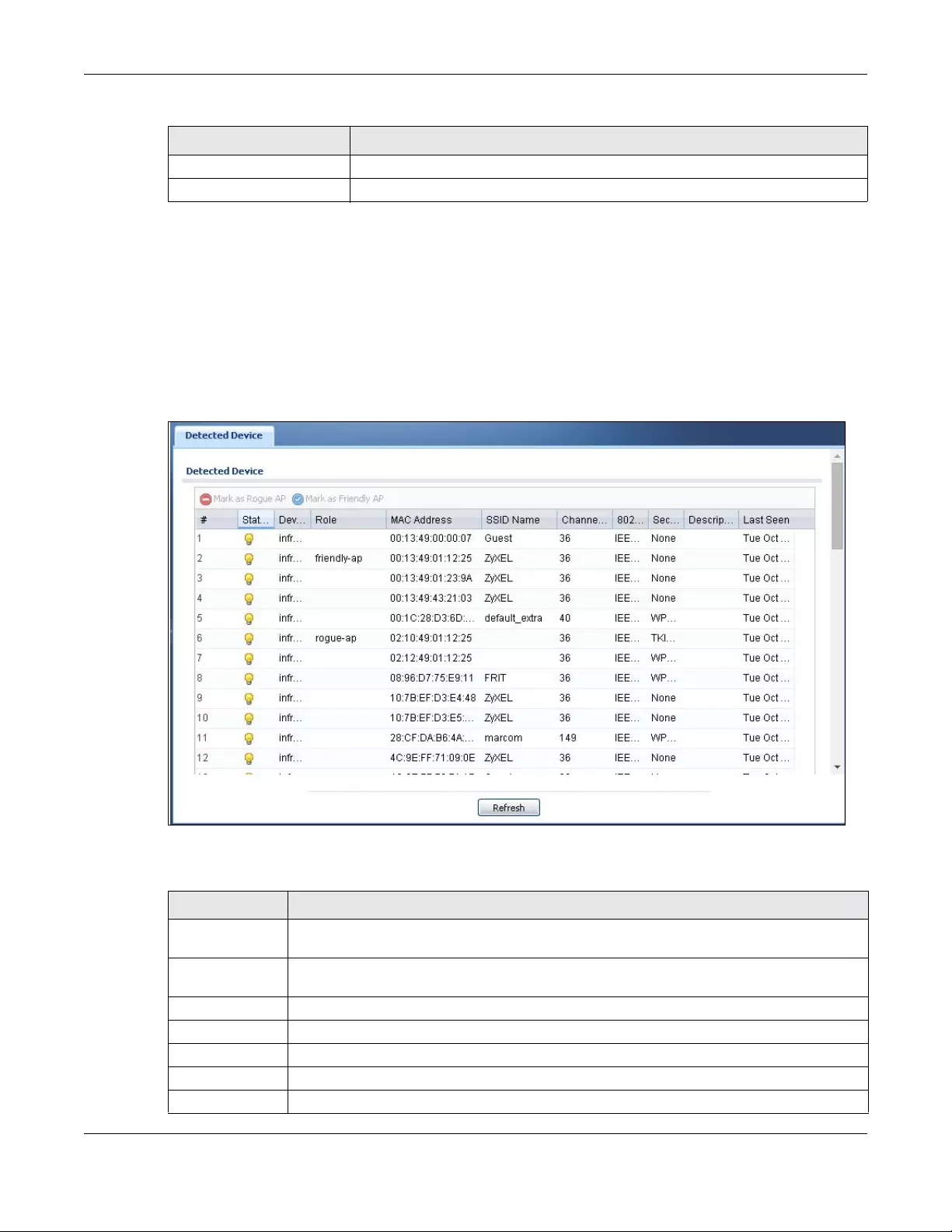
Chapter 7 Monitor
USG/ZyWALL User’s Guide
219
7.15.7 Detected Device
Use this screen to view information about wireless devices detected by the AP. Click Monitor > Wireless >
Detected Device to access this screen.
Note: At least one radio of the APs connected to the Zyxel Device must be set to monitor
mode (in the Configuration > Wireless > AP Management screen) in order to detect
other wireless devices in its vicinity.
Figure 185 Monitor > Wireless > Detected Device
The following table describes the labels in this screen.
Rx Rate This field displays the receive data rate of the station.
Association Time This field displays the time duration the station was online and offline.
Table 64 Monitor > Wireless > Station List
LABEL DESCRIPTION
Table 65 Monitor > Wireless > Detected Device
LABEL DESCRIPTION
Mark as Rogue
AP
Click this button to mark the selected AP as a rogue AP. A rogue AP can be contained in the
Configuration > Wireless > MON Mode screen.
Mark as Friendly
AP
Click this button to mark the selected AP as a friendly AP. For more on managing friendly APs,
see the Configuration > Wireless > MON Mode screen.
# This is the station’s index number in this list.
Status This indicates the detected device’s status.
Device This indicates the detected device’s network type (such as infrastructure or ad-hoc).
Role This indicates the detected device’s role (such as friendly or rogue).
MAC Address This indicates the detected device’s MAC address.
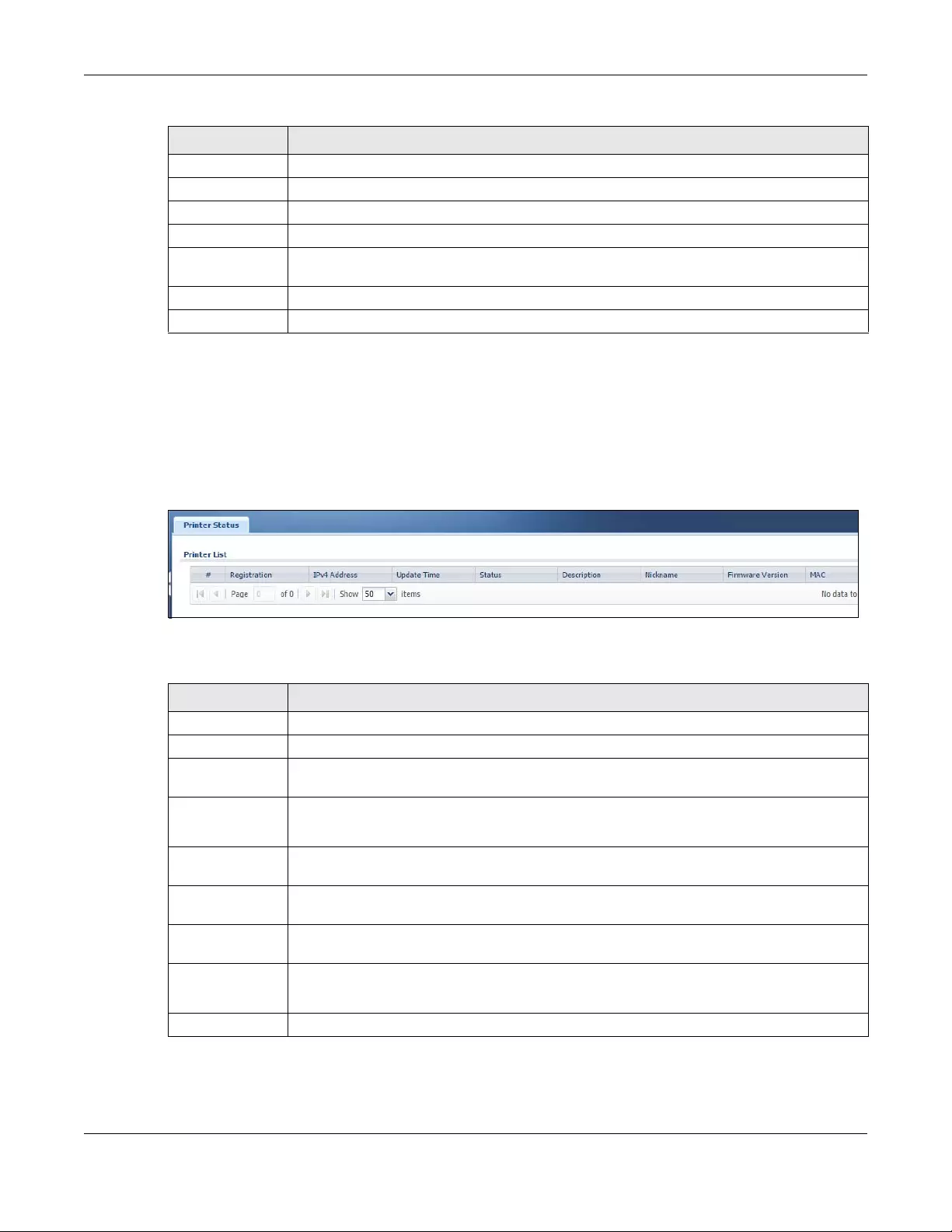
Chapter 7 Monitor
USG/ZyWALL User’s Guide
220
7.16 The Printer Status Screen
This screen displays information about the connected statement printer, such as SP350E. Click Monitor >
Printer Status to display this screen.
Figure 186 Monitor > Printer Status
The following table describes the labels in this screen.
SSID Name This indicates the detected device’s SSID.
Channel ID This indicates the detected device’s channel ID.
802.11 Mode This indicates the 802.11 mode (a/b/g/n) transmitted by the detected device.
Security This indicates the encryption method (if any) used by the detected device.
Description This displays the detected device’s description. For more on managing friendly and rogue APs,
see the Configuration > Wireless > MON Mode screen.
Last Seen This indicates the last time the device was detected by the Zyxel Device.
Refresh Click this to refresh the items displayed on this page.
Table 65 Monitor > Wireless > Detected Device (continued)
LABEL DESCRIPTION
Table 66 Monitor > Printer Status
LABEL DESCRIPTION
# This is the index number of the printer in the list.
Registration This field shows that the printer is added to the managed printer list (Mgnt Printer).
IPv4 Address This field displays the IP address of the printer that you configured in the Configuration > Hotspot
> Printer Manager > General: Add screen.
Update Time This field displays the date and time the Zyxel Device last synchronized with the printer.
This shows n/a when the printer status is sync fail.
Status This field displays whether the Zyxel Device can connect to the printer and update the printer
information.
Description This field displays the descriptive name of the printer that you configured in the Configuration >
Hotspot > Printer Manager > General: Add screen.
Nickname This field displays the nickname of the printer that you configured in the Configuration > Hotspot
> Printer Manager > General: Edit screen.
Firmware Version This field displays the model number and firmware version of the printer.
This shows n/a when the printer status is sync fail.
MAC This field displays the MAC address of the printer.
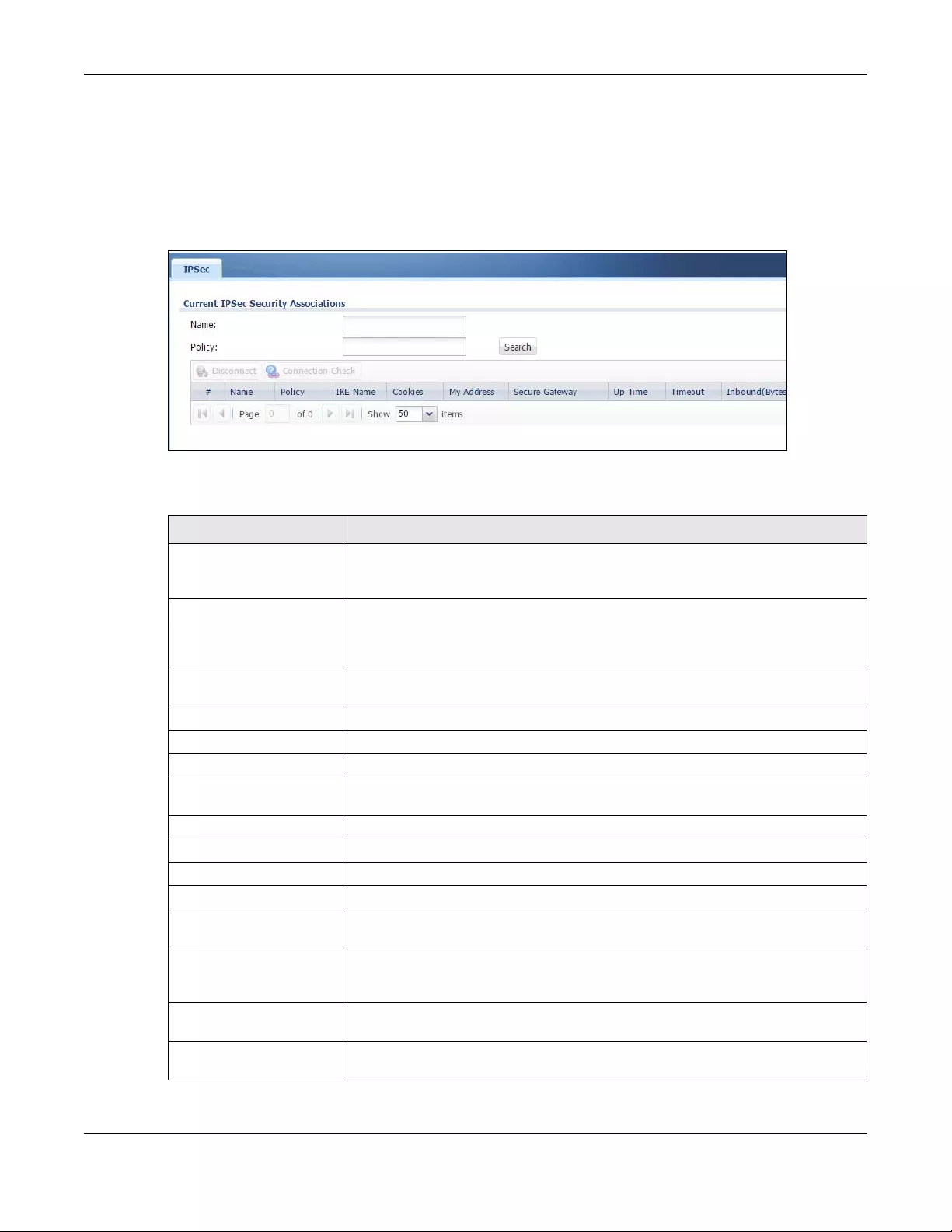
Chapter 7 Monitor
USG/ZyWALL User’s Guide
221
7.17 The IPSec Monitor Screen
You can use the IPSec Monitor screen to display and to manage active IPSec To access this screen, click
Monitor > VPN Monitor > IPSec. The following screen appears. SAs. Click a column’s heading cell to sort
the table entries by that column’s criteria. Click the heading cell again to reverse the sort order.
Figure 187 Monitor > VPN Monitor > IPSec
Each field is described in the following table.
Table 67 Monitor > VPN Monitor > IPSec
LABEL DESCRIPTION
Name Type the name of a IPSec SA here and click Search to find it (if it is associated). You
can use a keyword or regular expression. Use up to 30 alphanumeric and _+-
.()!$*^:?|{}[]<>/ characters. See Section 7.17.1 on page 222 for more details.
Policy Type the IP address(es) or names of the local and remote policies for an IPSec SA
and click Search to find it. You can use a keyword or regular expression. Use up to 30
alphanumeric and _+-.()!$*^:?|{}[]<>/ characters. See Section 7.17.1 on page 222
for more details.
Search Click this button to search for an IPSec SA that matches the information you
specified above.
Disconnect Select an IPSec SA and click this button to disconnect it.
# This field is a sequential value, and it is not associated with a specific SA.
Name This field displays the name of the IPSec SA.
Policy This field displays the content of the local and remote policies for this IPSec SA. The IP
addresses, not the address objects, are displayed.
IKE Name This field displays the Internet Key Exchange (IKE) name.
Cookies This field displays the cookies information that initiates the IKE.
My Address This field displays the IP address of local computer.
Secure Gateway This field displays the secure gateway information.
Up Time This field displays how many seconds the IPSec SA has been active. This field displays
N/A if the IPSec SA uses manual keys.
Timeout This field displays how many seconds remain in the SA life time, before the Zyxel
Device automatically disconnects the IPSec SA. This field displays N/A if the IPSec SA
uses manual keys.
Inbound (Bytes) This field displays the amount of traffic that has gone through the IPSec SA from the
remote IPSec router to the Zyxel Device since the IPSec SA was established.
Outbound (Bytes) This field displays the amount of traffic that has gone through the IPSec SA from the
Zyxel Device to the remote IPSec router since the IPSec SA was established.
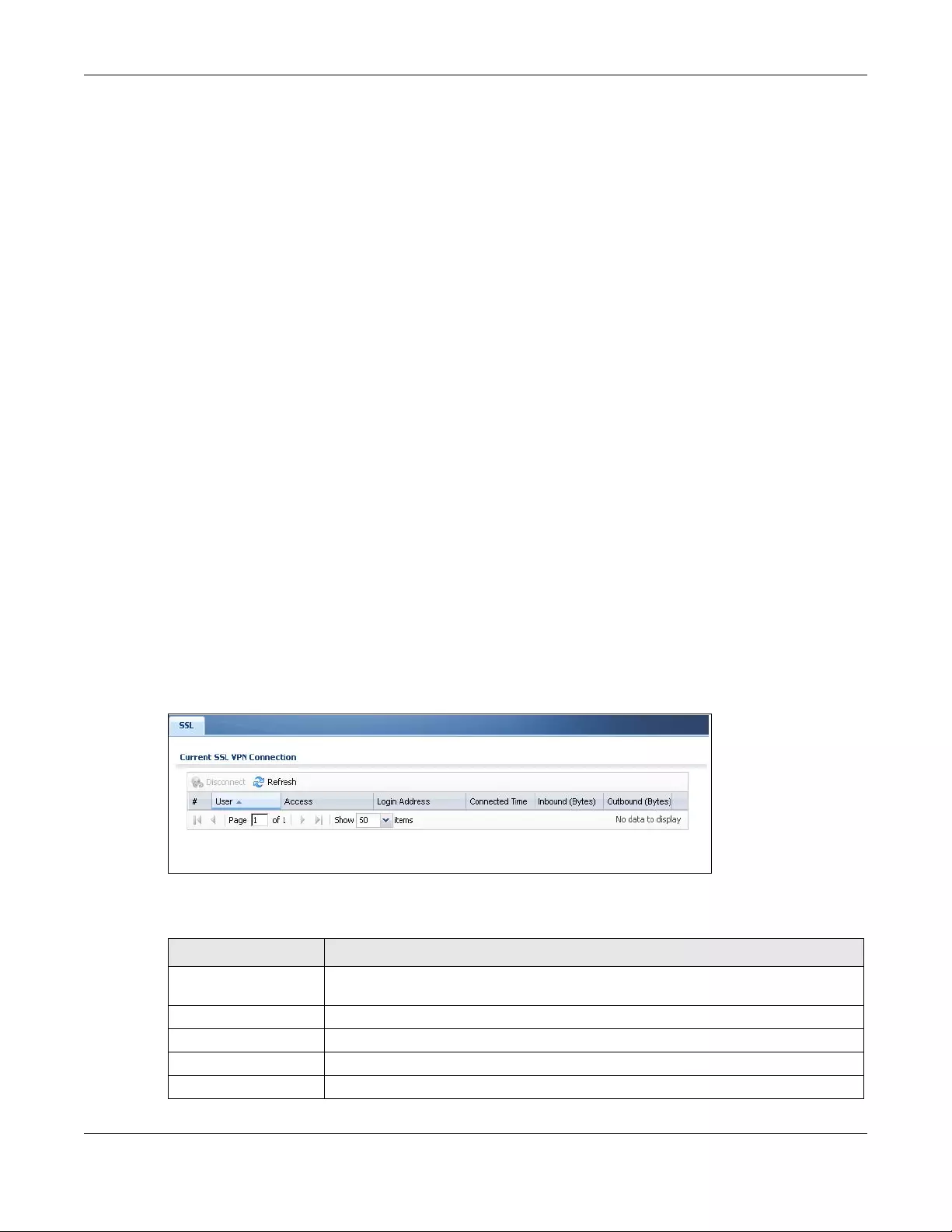
Chapter 7 Monitor
USG/ZyWALL User’s Guide
222
7.17.1 Regular Expressions in Searching IPSec SAs
A question mark (?) lets a single character in the VPN connection or policy name vary. For example, use
“a?c” (without the quotation marks) to specify abc, acc and so on.
Wildcards (*) let multiple VPN connection or policy names match the pattern. For example, use “*abc”
(without the quotation marks) to specify any VPN connection or policy name that ends with “abc”. A
VPN connection named “testabc” would match. There could be any number (of any type) of
characters in front of the “abc” at the end and the VPN connection or policy name would still match. A
VPN connection or policy name named “testacc” for example would not match.
A * in the middle of a VPN connection or policy name has the Zyxel Device check the beginning and
end and ignore the middle. For example, with “abc*123”, any VPN connection or policy name starting
with “abc” and ending in “123” matches, no matter how many characters are in between.
The whole VPN connection or policy name has to match if you do not use a question mark or asterisk.
7.18 The SSL Screen
The Zyxel Device keeps track of the users who are currently logged into the VPN SSL client. Click Monitor
> VPN Monitor > SSL to display the user list.
Use this screen to do the following:
• View a list of active SSL VPN connections.
• Log out individual users and delete related session information.
Once a user logs out, the corresponding entry is removed from the screen.
Figure 188 Monitor > VPN Monitor > SSL
The following table describes the labels in this screen.
Table 68 Monitor > VPN Monitor > SSL
LABEL DESCRIPTION
Disconnect Select a connection and click this button to terminate the user’s connection and delete
corresponding session information from the Zyxel Device.
Refresh Click Refresh to update this screen.
# This field is a sequential value, and it is not associated with a specific SSL.
User This field displays the account user name used to establish this SSL VPN connection.
Access This field displays the name of the SSL VPN application the user is accessing.
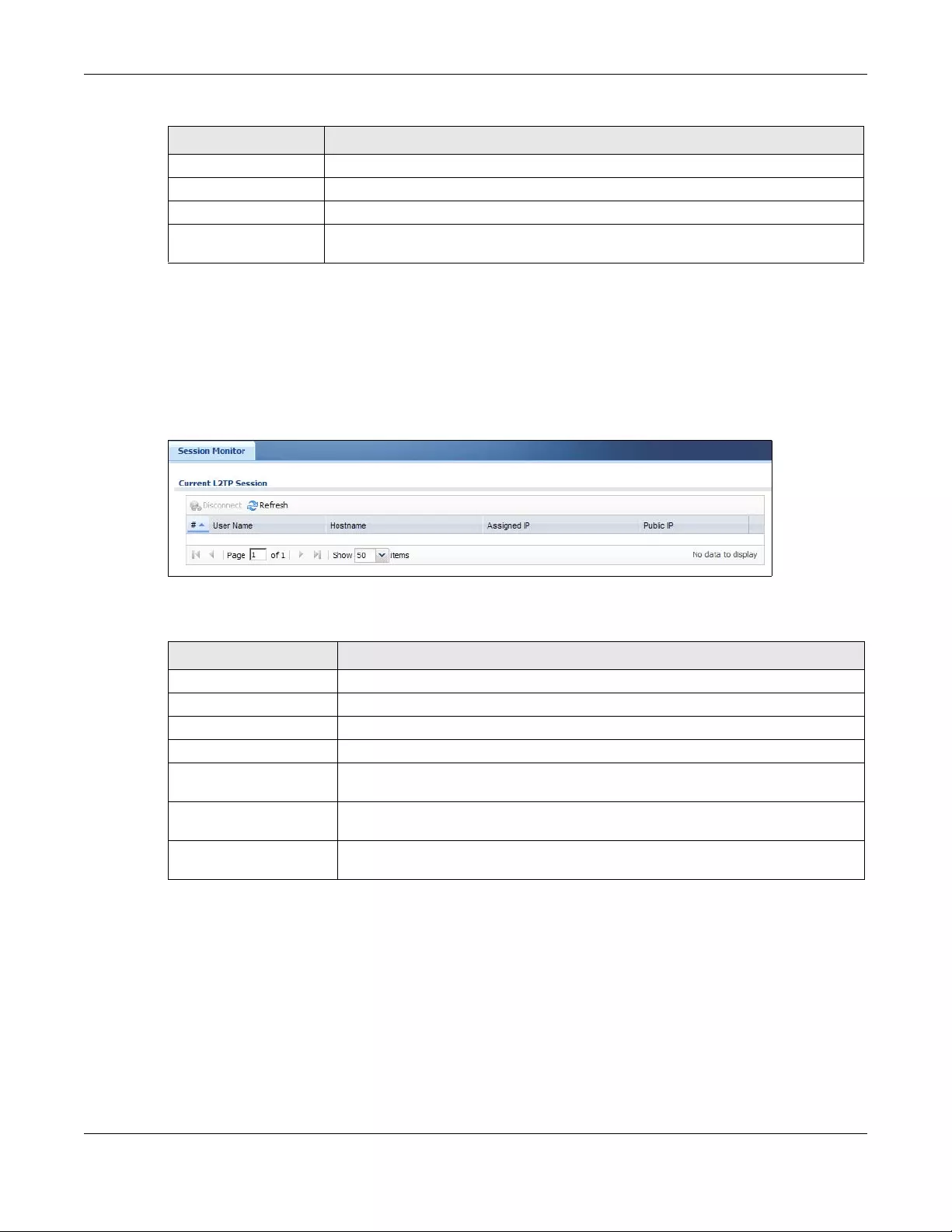
Chapter 7 Monitor
USG/ZyWALL User’s Guide
223
7.19 The L2TP over IPSec Session Monitor Screen
Click Monitor > VPN Monitor > L2TP over IPSec to open the following screen. Use this screen to display
and manage the Zyxel Device’s connected L2TP VPN sessions.
Figure 189 Monitor > VPN Monitor > L2TP over IPSec
The following table describes the fields in this screen.
7.20 The App Patrol Screen
Application patrol provides a convenient way to manage the use of various applications on the
network. It manages general protocols (for example, HTTP and FTP) and instant messenger (IM), peer-to-
peer (P2P), Voice over IP (VoIP), and streaming (RSTP) applications. You can even control the use of a
particular application’s individual features (like text messaging, voice, video conferencing, and file
transfers).
Login Address This field displays the IP address the user used to establish this SSL VPN connection.
Connected Time This field displays the time this connection was established.
Inbound (Bytes) This field displays the number of bytes received by the Zyxel Device on this connection.
Outbound (Bytes) This field displays the number of bytes transmitted by the Zyxel Device on this
connection.
Table 68 Monitor > VPN Monitor > SSL (continued)
LABEL DESCRIPTION
Table 69 Monitor > VPN Monitor > L2TP over IPSec
LABEL DESCRIPTION
Disconnect Select a connection and click this button to disconnect it.
Refresh Click Refresh to update this screen.
# This field is a sequential value, and it is not associated with a specific L2TP VPN session.
User Name This field displays the remote user’s user name.
Hostname This field displays the name of the computer that has this L2TP VPN connection with
the Zyxel Device.
Assigned IP This field displays the IP address that the Zyxel Device assigned for the remote user’s
computer to use within the L2TP VPN tunnel.
Public IP This field displays the public IP address that the remote user is using to connect to the
Internet.
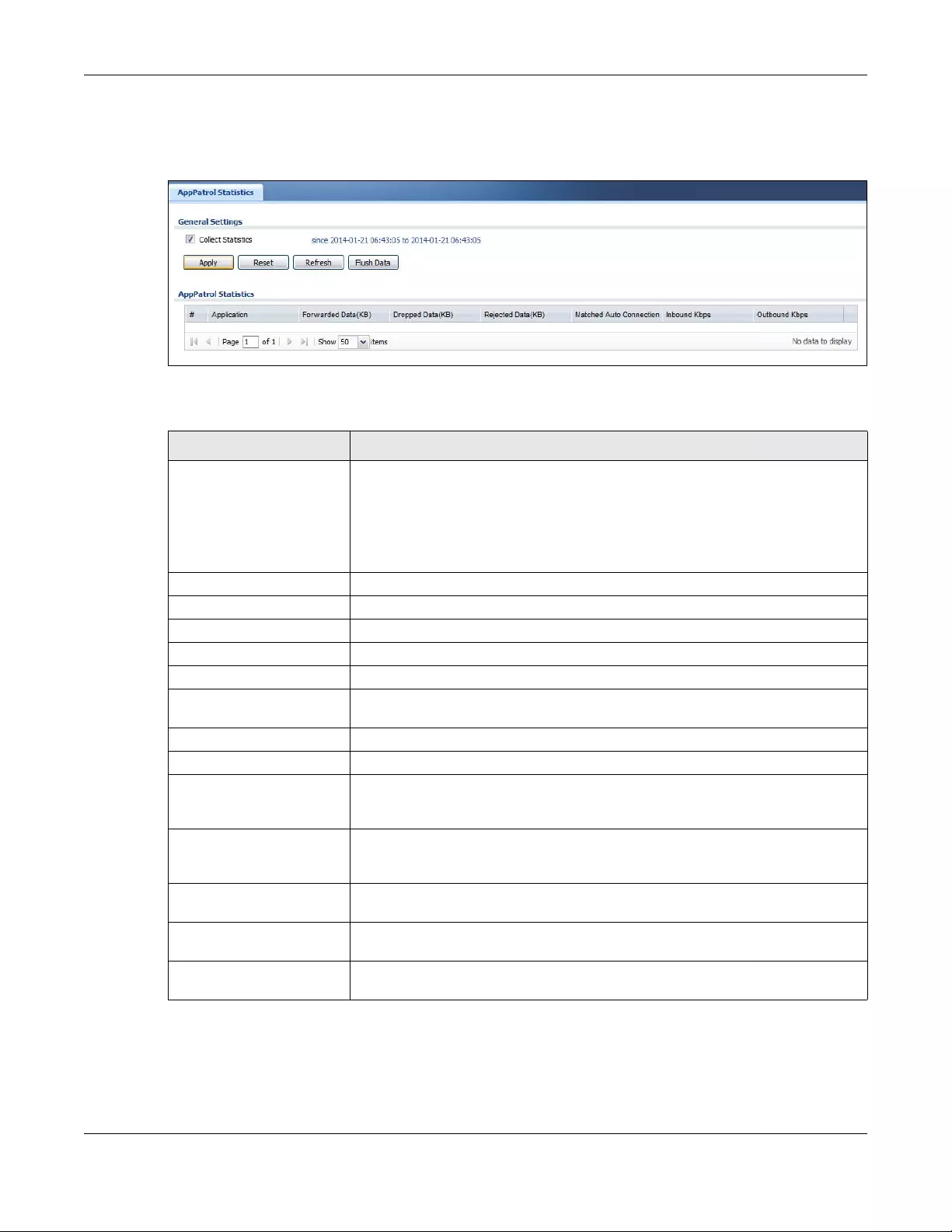
Chapter 7 Monitor
USG/ZyWALL User’s Guide
224
Click Monitor > UTM Statistics > App Patrol to display the following screen. This screen displays
Application Patrol statistics based on the App Patrol profiles bound to Security Policy profiles.
Figure 190 Monitor > UTM Statistics > App Patrol
The following table describes the labels in this screen.
Table 70 Monitor > UTM Statistics > App Patrol
LABEL DESCRIPTION
Collect Statistics Select this check box to have the Zyxel Device collect app patrol statistics.
The collection starting time displays after you click Apply. All of the statistics in this
screen are for the time period starting at the time displayed here. The format is year,
month, day and hour, minute, second. All of the statistics are erased if you restart the
Zyxel Device or click Flush Data. Collecting starts over and a new collection start
time displays.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Refresh Click this button to update the report display.
Flush Data Click this button to discard all of the screen’s statistics and update the report display.
App Patrol Statistics
# This field is a sequential value, and it is not associated with a specific App Patrol
session.
Application This is the protocol.
Forwarded Data (KB) This is how much of the application’s traffic the Zyxel Device has sent (in kilobytes).
Dropped Data (KB) This is how much of the application’s traffic the Zyxel Device has discarded without
notifying the client (in kilobytes). This traffic was dropped because it matched an
application policy set to “drop”.
Rejected Data (KB) This is how much of the application’s traffic the Zyxel Device has discarded and
notified the client that the traffic was rejected (in kilobytes). This traffic was rejected
because it matched an application policy set to “reject”.
Matched Auto
Connection This is how much of the application’s traffic the Zyxel Device identified by examining
the IP payload.
Inbound Kbps This field displays the amount of the application’s traffic that has gone to the ZyWALL
(in kilo bits per second).
Outbound Kbps This field displays the amount of the application’s traffic that has gone from the
ZyWALL (in kilo bits per second).
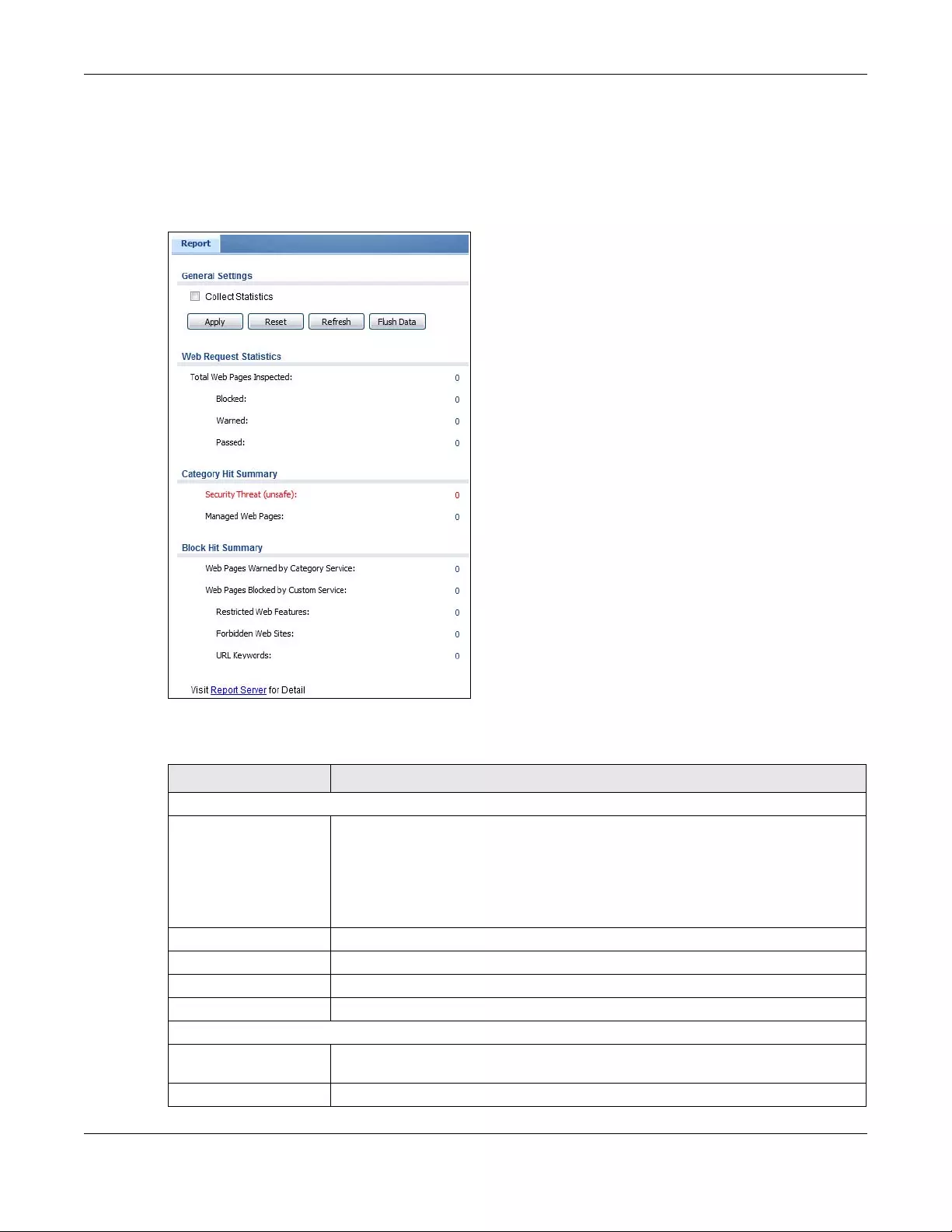
Chapter 7 Monitor
USG/ZyWALL User’s Guide
225
7.21 The Content Filter Screen
Click Monitor > UTM Statistics > Content Filter to display the following screen. This screen displays content
filter statistics.
Figure 191 Monitor > UTM Statistics > Content Filter
The following table describes the labels in this screen.
Table 71 Monitor > UTM Statistics > Content Filter
LABEL DESCRIPTION
General Settings
Collect Statistics Select this check box to have the Zyxel Device collect content filtering statistics.
The collection starting time displays after you click Apply. All of the statistics in this
screen are for the time period starting at the time displayed here. The format is year,
month, day and hour, minute, second. All of the statistics are erased if you restart the
Zyxel Device or click Flush Data. Collecting starts over and a new collection start time
displays.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Refresh Click this button to update the report display.
Flush Data Click this button to discard all of the screen’s statistics and update the report display.
Web Request Statistics
Total Web Pages
Inspected
This field displays the number of web pages that the Zyxel Device’s content filter feature
has checked.
Blocked This is the number of web pages that the Zyxel Device blocked access.
Chapter 7 Monitor
USG/ZyWALL User’s Guide
226
7.22 The IDP Screen
Click Monitor > UTM Statistics > IDP to display the following screen. This screen displays IDP (Intrusion
Detection and Prevention) statistics.
Warned This is the number of web pages for which the Zyxel Device displayed a warning
message to the access requesters.
Passed This is the number of web pages to which the Zyxel Device allowed access.
Category Hit Summary
Security Threat (unsafe) This is the number of requested web pages that the Zyxel Device’s content filtering
service identified as posing a threat to users.
Managed Web Pages This is the number of requested web pages that the Zyxel Device’s content filtering
service identified as belonging to a category that was selected to be managed.
Block Hit Summary
Web Pages Warned by
Category Service
This is the number of web pages that matched an external database content filtering
category selected in the Zyxel Device and for which the Zyxel Device displayed a
warning before allowing users access.
Web Pages Blocked by
Custom Service
This is the number of web pages to which the Zyxel Device did not allow access due to
the content filtering custom service configuration.
Restricted Web
Features This is the number of web pages to which the ZyWALL limited access or removed
cookies due to the content filtering custom service's restricted web features
configuration.
Forbidden Web Sites This is the number of web pages to which the Zyxel Device did not allow access
because they matched the content filtering custom service’s forbidden web sites list.
URL Keywords This is the number of web pages to which the Zyxel Device did not allow access
because they contained one of the content filtering custom service’s list of forbidden
keywords.
Web Pages Blocked
Without Policy
This is the number of web pages to which the Zyxel Device did not allow access
because they were not rated by the external database content filtering service.
Report Server Click this link to go to http://www.myZyxel.com where you can view content filtering
reports after you have activated the category-based content filtering subscription
service.
Table 71 Monitor > UTM Statistics > Content Filter (continued)
LABEL DESCRIPTION
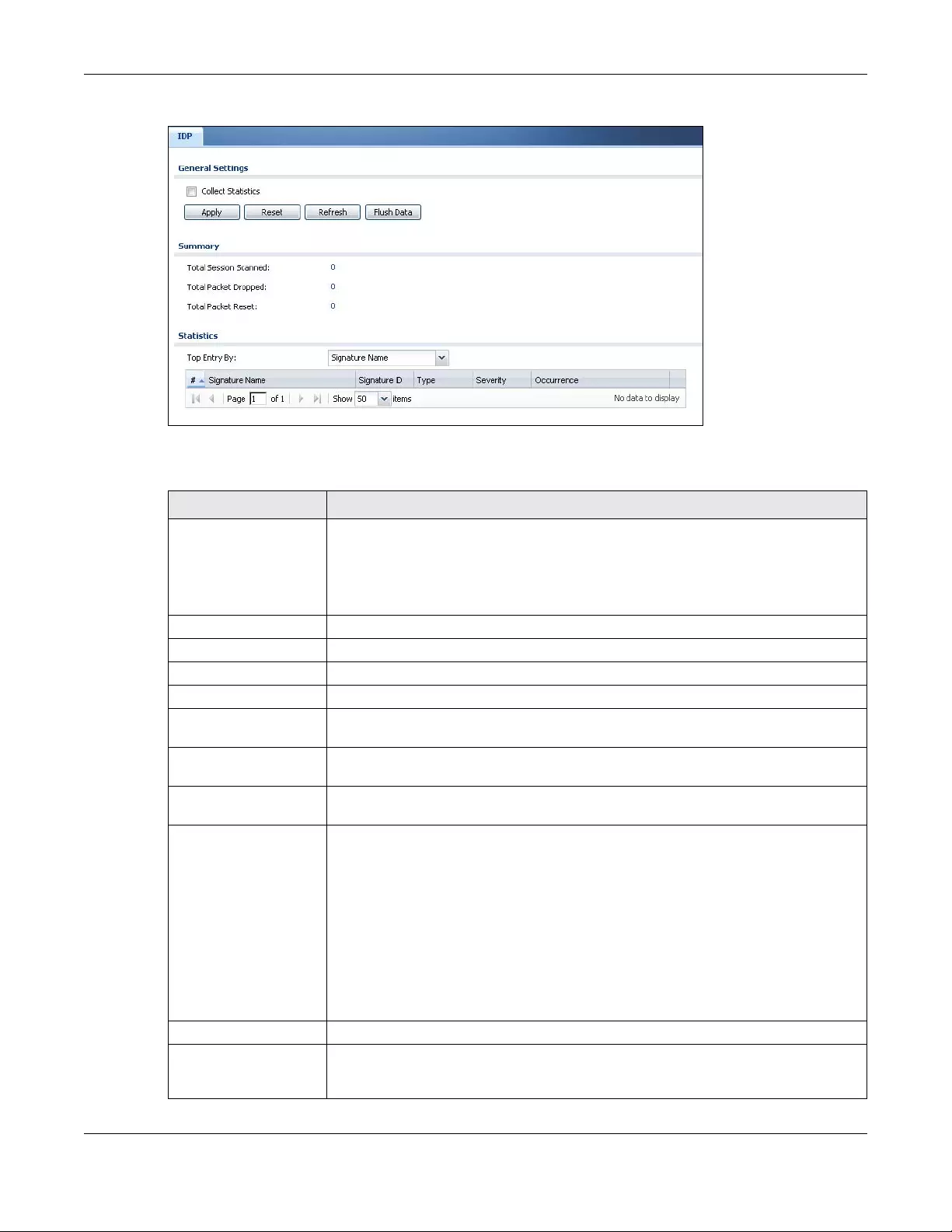
Chapter 7 Monitor
USG/ZyWALL User’s Guide
227
Figure 192 Monitor > UTM Statistics > IDP: Signature Name
The following table describes the labels in this screen.
Table 72 Monitor > UTM Statistics > IDP
LABEL DESCRIPTION
Collect Statistics Select this check box to have the Zyxel Device collect IDP statistics.
The collection starting time displays after you click Apply. All of the statistics in this screen
are for the time period starting at the time displayed here. The format is year, month,
day and hour, minute, second. All of the statistics are erased if you restart the Zyxel
Device or click Flush Data. Collecting starts over and a new collection start time displays.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Refresh Click this button to update the report display.
Flush Data Click this button to discard all of the screen’s statistics and update the report display.
Total Session Scanned This field displays the number of sessions that the Zyxel Device has checked for intrusion
characteristics.
Total Packet Dropped The Zyxel Device can detect and drop malicious packets from network traffic. This field
displays the number of packets that the Zyxel Device has dropped.
Total Packet Reset The Zyxel Device can detect and drop malicious packets from network traffic. This field
displays the number of packets that the Zyxel Device has reset.
Top Entries By Use this field to have the following (read-only) table display the top IDP log entries by
Signature Name, Source or Destination. This table displays the most common, recent IDP
logs. See the log screen for less common IDP logs or use a syslog server to record all IDP
logs.
Select Signature Name to list the most common signatures that the Zyxel Device has
detected.
Select Source to list the source IP addresses from which the Zyxel Device has detected
the most intrusion attempts.
Select Destination to list the most common destination IP addresses for intrusion attempts
that the Zyxel Device has detected.
#This field displays the entry’s rank in the list of the top entries.
Signature Name This column displays when you display the entries by Signature Name. The signature
name identifies the type of intrusion pattern. Click the hyperlink for more detailed
information on the intrusion.
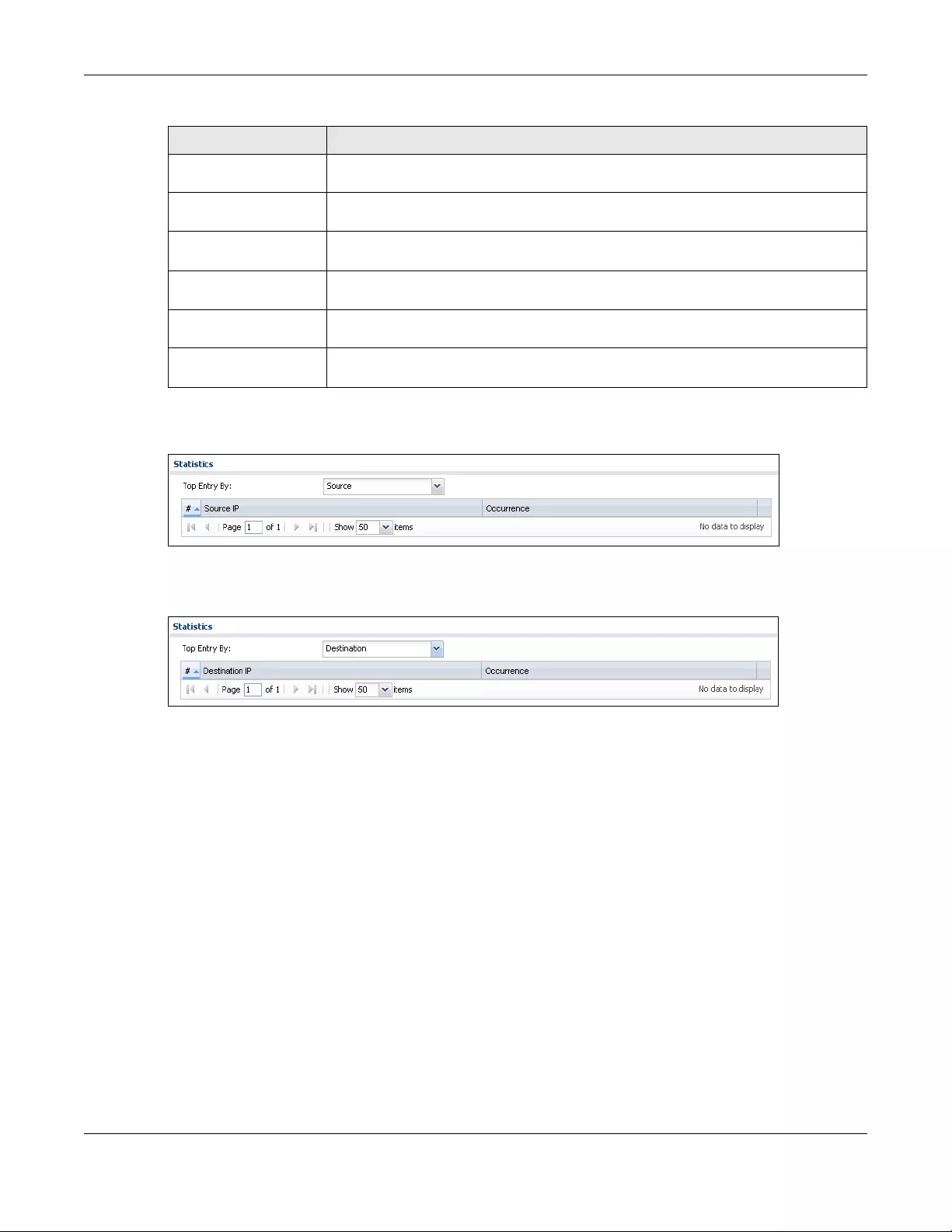
Chapter 7 Monitor
USG/ZyWALL User’s Guide
228
The statistics display as follows when you display the top entries by source.
Figure 193 Monitor > UTM Statistics > IDP: Source
The statistics display as follows when you display the top entries by destination.
Figure 194 Monitor > UTM Statistics > IDP: Destination
7.23 The Anti-Virus Screen
Click Monitor > UTM Statistics > Anti-Virus to display the following screen. This screen displays anti-virus
statistics.
Signature ID This column displays when you display the entries by Signature Name. The signature ID is
a unique value given to each intrusion detected.
Type This column displays when you display the entries by Signature Name. It shows the
categories of intrusions.
Severity This column displays when you display the entries by Signature Name. It shows the level
of threat that the intrusions may pose.
Source IP This column displays when you display the entries by Source. It shows the source IP
address of the intrusion attempts.
Destination IP This column displays when you display the entries by Destination. It shows the destination
IP address at which intrusion attempts were targeted.
Occurrences This field displays how many times the Zyxel Device has detected the event described in
the entry.
Table 72 Monitor > UTM Statistics > IDP (continued)
LABEL DESCRIPTION
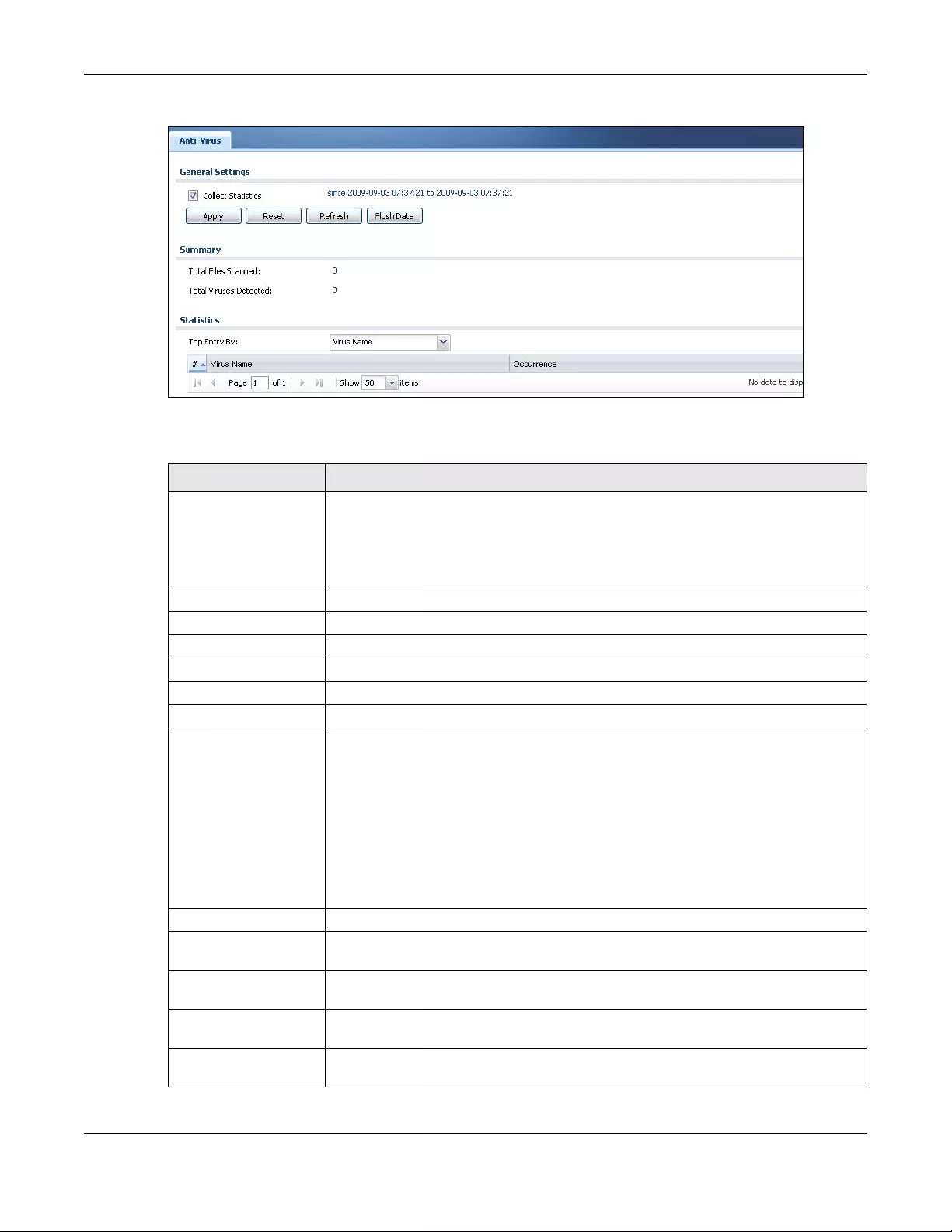
Chapter 7 Monitor
USG/ZyWALL User’s Guide
229
Figure 195 Monitor > UTM Statistics > Anti-Virus: Virus Name
The following table describes the labels in this screen.
Table 73 Monitor > UTM Statistics > Anti-Virus
LABEL DESCRIPTION
Collect Statistics Select this check box to have the Zyxel Device collect anti-virus statistics.
The collection starting time displays after you click Apply. All of the statistics in this screen
are for the time period starting at the time displayed here. The format is year, month, day
and hour, minute, second. All of the statistics are erased if you restart the Zyxel Device or
click Flush Data. Collecting starts over and a new collection start time displays.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Refresh Click this button to update the report display.
Flush Data Click this button to discard all of the screen’s statistics and update the report display.
Total Viruses Detected This field displays the number of different viruses that the Zyxel Device has detected.
Infected Files Detected This field displays the number of files in which the Zyxel Device has detected a virus.
Top Entries By Use this field to have the following (read-only) table display the top anti-virus log entries
by Virus Name, Source IP or Destination IP. This table displays the most common, recent
virus logs. See the log screen for less common virus logs or use a syslog server to record all
virus logs.
Select Virus Name to list the most common viruses that the Zyxel Device has detected.
Select Source IP to list the source IP addresses from which the Zyxel Device has detected
the most virus-infected files.
Select Destination IP to list the most common destination IP addresses for virus-infected
files that Zyxel Device has detected.
#This field displays the entry’s rank in the list of the top entries.
Virus name This column displays when you display the entries by Virus Name. This displays the name
of a detected virus.
Source IP This column displays when you display the entries by Source. It shows the source IP
address of virus-infected files that the Zyxel Device has detected.
Destination IP This column displays when you display the entries by Destination. It shows the destination
IP address of virus-infected files that the Zyxel Device has detected.
Occurrences This field displays how many times the Zyxel Device has detected the event described in
the entry.
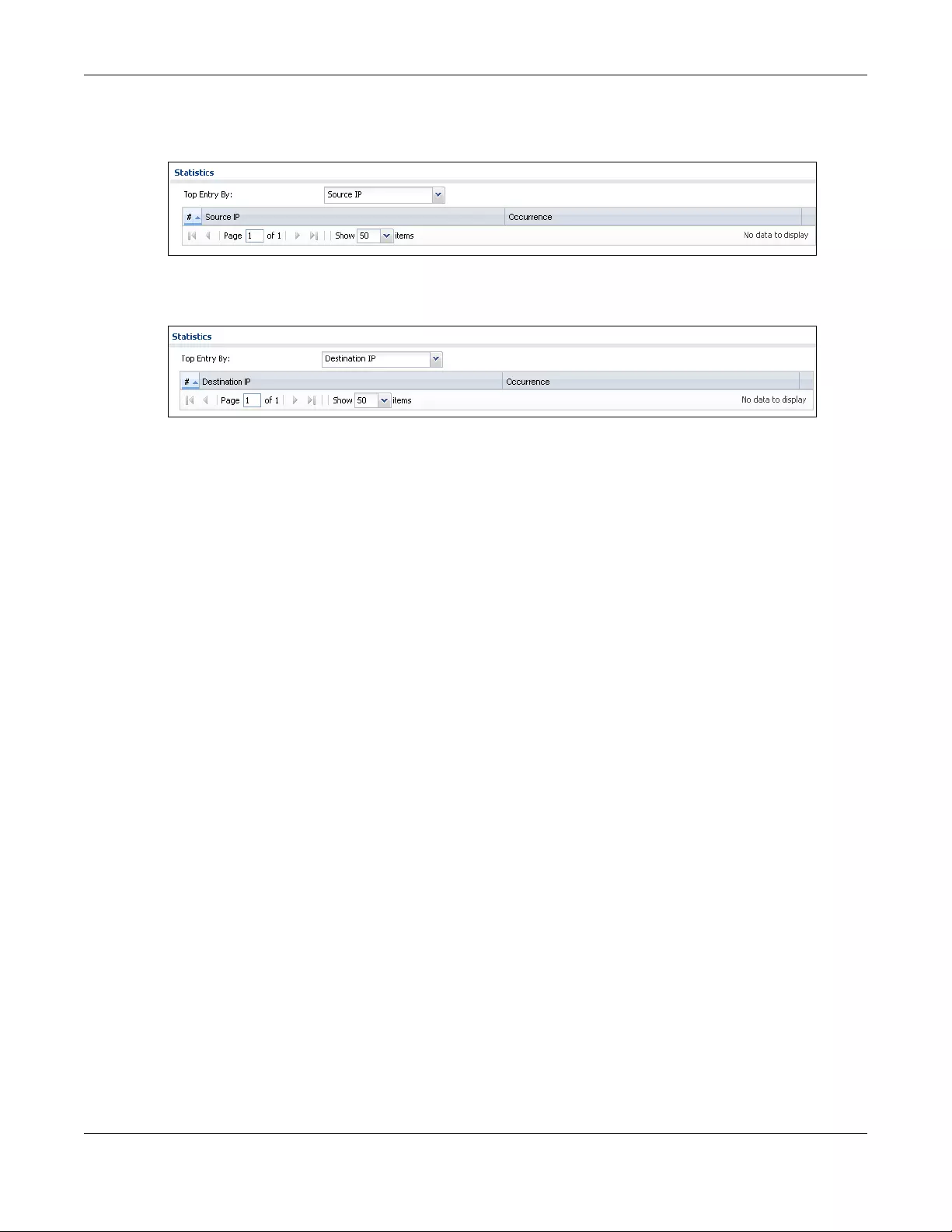
Chapter 7 Monitor
USG/ZyWALL User’s Guide
230
The statistics display as follows when you display the top entries by source.
Figure 196 Monitor > UTM Statistics > Anti-Virus: Source IP
The statistics display as follows when you display the top entries by destination.
Figure 197 Monitor > UTM Statistics > Anti-Virus: Destination IP
7.24 The Anti-Spam Screens
The Anti-Spam menu contains the Report and Status screens.
7.24.1 Anti-Spam Report
Click Monitor > UTM Statistics > Anti-Spam to display the following screen. This screen displays spam
statistics.
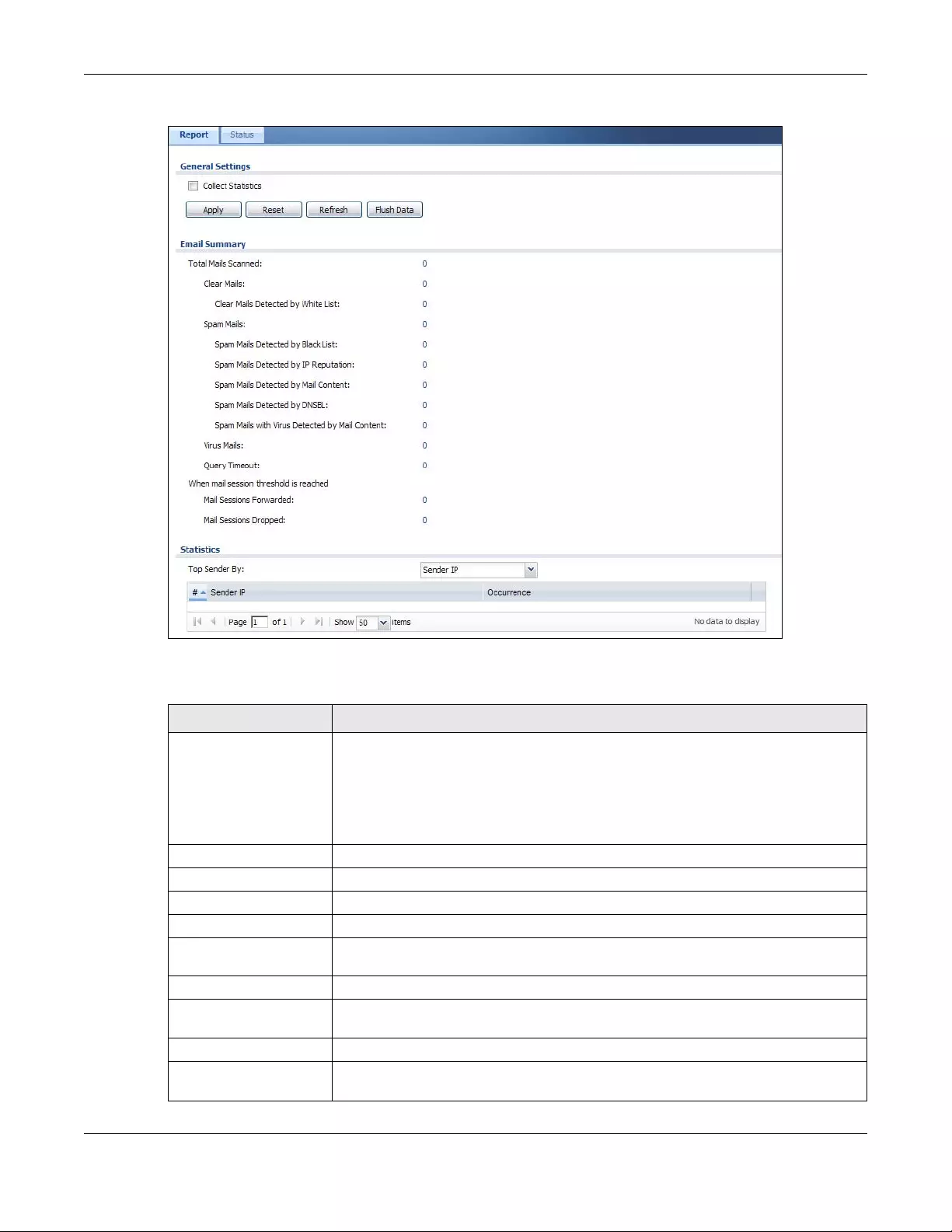
Chapter 7 Monitor
USG/ZyWALL User’s Guide
231
Figure 198 Monitor > UTM Statistics > Anti-Spam
The following table describes the labels in this screen.
Table 74 Monitor > UTM Statistics > Anti-Spam
LABEL DESCRIPTION
Collect Statistics Select this check box to have the Zyxel Device collect anti-spam statistics.
The collection starting time displays after you click Apply. All of the statistics in this
screen are for the time period starting at the time displayed here. The format is year,
month, day and hour, minute, second. All of the statistics are erased if you restart the
Zyxel Device or click Flush Data. Collecting starts over and a new collection start time
displays.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Refresh Click this button to update the report display.
Flush Data Click this button to discard all of the screen’s statistics and update the report display.
Total Mails Scanned This field displays the number of e-mails that the Zyxel Device’s anti-spam feature has
checked.
Clear Mails This is the number of e-mails that the Zyxel Device has determined to not be spam.
Clear Mails Detected by
Whitelist
This is the number of e-mails that matched an entry in the Zyxel Device’s anti-spam
white list.
Spam Mails This is the number of e-mails that the Zyxel Device has determined to be spam.
Spam Mails Detected by
Black List
This is the number of e-mails that matched an entry in the Zyxel Device’s anti-spam
black list.
Chapter 7 Monitor
USG/ZyWALL User’s Guide
232
7.24.2 The Anti-Spam Status Screen
Click Monitor > UTM Statistics > Anti-Spam > Status to display the Anti-Spam Status screen.
Use the Anti-Spam Status screen to see how many e-mail sessions the anti-spam feature is scanning and
statistics for the DNSBLs.
Spam Mails Detected by
IP Reputation
This is the number of e-mails that the Zyxel Device has determined to be spam by IP
Reputation. Spam or Unwanted Bulk Email is determined by the sender’s IP address.
Spam Mails Detected by
Mail Content
This is the number of e-mails that the Zyxel Device has determined to have malicious
contents.
Spam Mails Detected by
DNSBL
The Zyxel Device can check the sender and relay IP addresses in an e-mail’s header
against DNS (Domain Name Service)-based spam Black Lists (DNSBLs). This is the
number of e-mails that had a sender or relay IP address in the header which matched
one of the DNSBLs that the Zyxel Device uses.
Spam Mails with Virus
Detected by Mail
Content
This is the number of e-mails that the Zyxel Device has determined to have malicious
contents and attached with virus.
Virus Mails This is the number of e-mails that the Zyxel Device has determined to be attached with
virus.
Query Timeout This is how many queries that were sent to the Zyxel Device’s configured list of DNSBL
domains or Mail Scan services and did not receive a response in time.
Mail Sessions Forwarded This is how many e-mail sessions the Zyxel Device allowed because they exceeded the
maximum number of e-mail sessions that the anti-spam feature can check at a time.
You can see the Zyxel Device’s threshold of concurrent e-mail sessions in the Anti-Spam
> Status screen.
Use the Anti-Spam > General screen to set whether the Zyxel Device forwards or drops
sessions that exceed this threshold.
Mail Sessions Dropped This is how many e-mail sessions the Zyxel Device dropped because they exceeded the
maximum number of e-mail sessions that the anti-spam feature can check at a time.
You can see the Zyxel Device’s threshold of concurrent e-mail sessions in the Anti-Spam
> Status screen.
Use the Anti-Spam > General screen to set whether the Zyxel Device forwards or drops
sessions that exceed this threshold.
Top Sender By Use this field to list the top e-mail or IP addresses from which the Zyxel Device has
detected the most spam.
Select Sender IP to list the source IP addresses from which the Zyxel Device has
detected the most spam.
Select Sender Email Address to list the top e-mail addresses from which the Zyxel
Device has detected the most spam.
#This field displays the entry’s rank in the list of the top entries.
Sender IP This column displays when you display the entries by Sender IP. It shows the source IP
address of spam e-mails that the Zyxel Device has detected.
Sender Email Address This column displays when you display the entries by Sender Email Address. This column
displays the e-mail addresses from which the Zyxel Device has detected the most
spam.
Occurrence This field displays how many spam e-mails the Zyxel Device detected from the sender.
Table 74 Monitor > UTM Statistics > Anti-Spam (continued)
LABEL DESCRIPTION
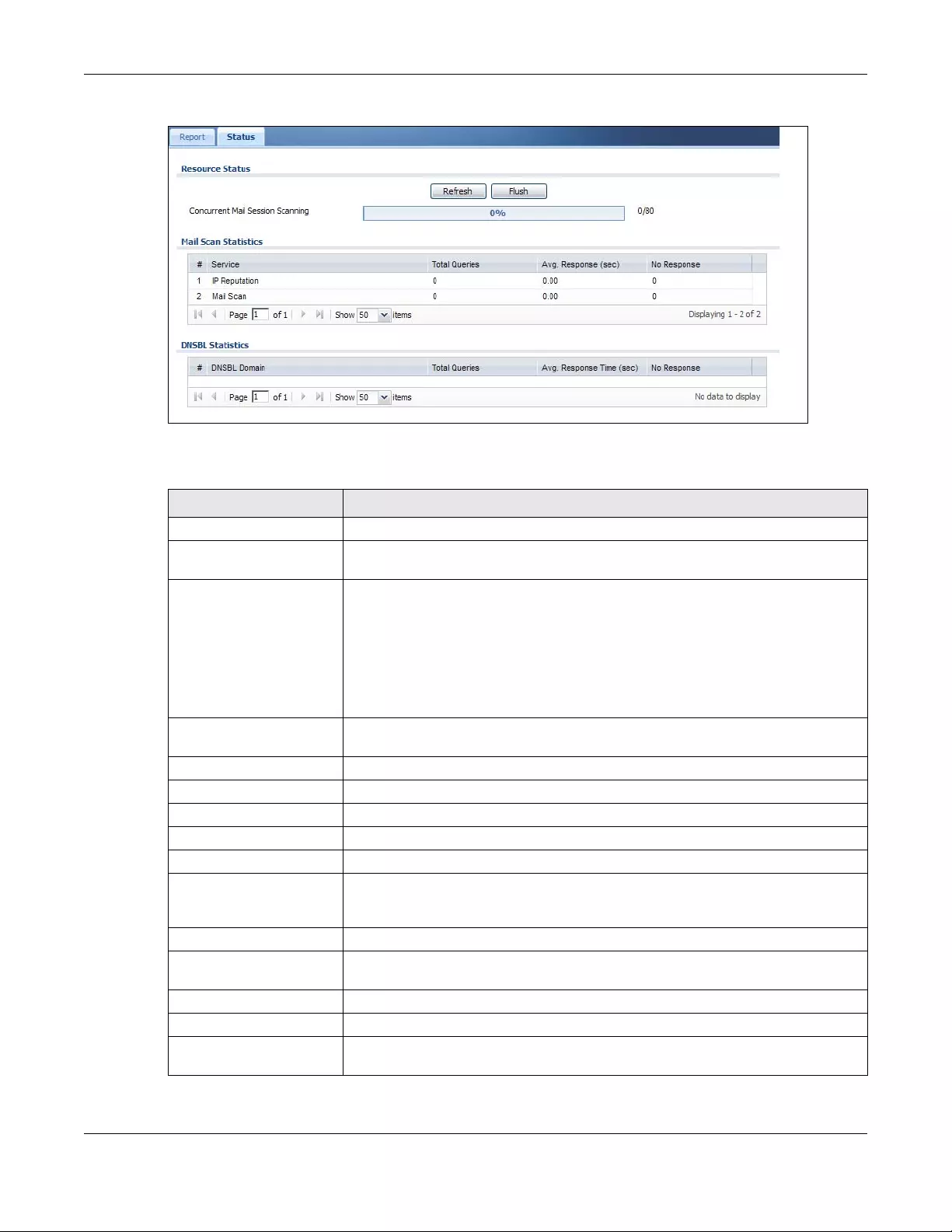
Chapter 7 Monitor
USG/ZyWALL User’s Guide
233
Figure 199 Monitor > UTM Statistics > Anti-Spam > Status
The following table describes the labels in this screen.
Table 75 Monitor > UTM Statistics > Anti-Spam > Status
LABEL DESCRIPTION
Refresh Click this button to update the information displayed on this screen.
Flush Click this button to clear the DNSBL statistics. This also clears the concurrent mail
session scanning bar’s historical high.
Concurrent Mail Session
Scanning
The darker shaded part of the bar shows how much of the Zyxel Device’s total spam
checking capability is currently being used.
The lighter shaded part of the bar and the pop-up show the historical high.
The first number to the right of the bar is how many e-mail sessions the Zyxel Device is
presently checking for spam. The second number is the maximum number of e-mail
sessions that the Zyxel Device can check at once. An e-mail session is when an e-mail
client and e-mail server (or two e-mail servers) connect through the Zyxel Device.
Mail Scan Statistics These are the statistics for the service the Zyxel Device uses. These statistics are for
when the Zyxel Device actually queries the service servers.
#This is the entry’s index number in the list.
Service This displays the name of the service.
Total Queries This is the total number of queries the Zyxel Device has sent to this service.
Avg. Response Time (sec) This is the average for how long it takes to receive a reply from this service.
No Response This is how many queries the Zyxel Device sent to this service without receiving a reply.
DNSBL Statistics These are the statistics for the DNSBL the Zyxel Device uses. These statistics are for
when the Zyxel Device actually queries the DNSBL servers. Matches for DNSBL
responses stored in the cache do not affect these statistics.
#This is the entry’s index number in the list.
DNSBL Domain These are the DNSBLs the Zyxel Device uses to check sender and relay IP addresses in
e-mails.
Total Queries This is the total number of DNS queries the Zyxel Device has sent to this DNSBL.
Avg. Response Time (sec) This is the average for how long it takes to receive a reply from this DNSBL.
No Response This is how many DNS queries the Zyxel Device sent to this DNSBL without receiving a
reply.
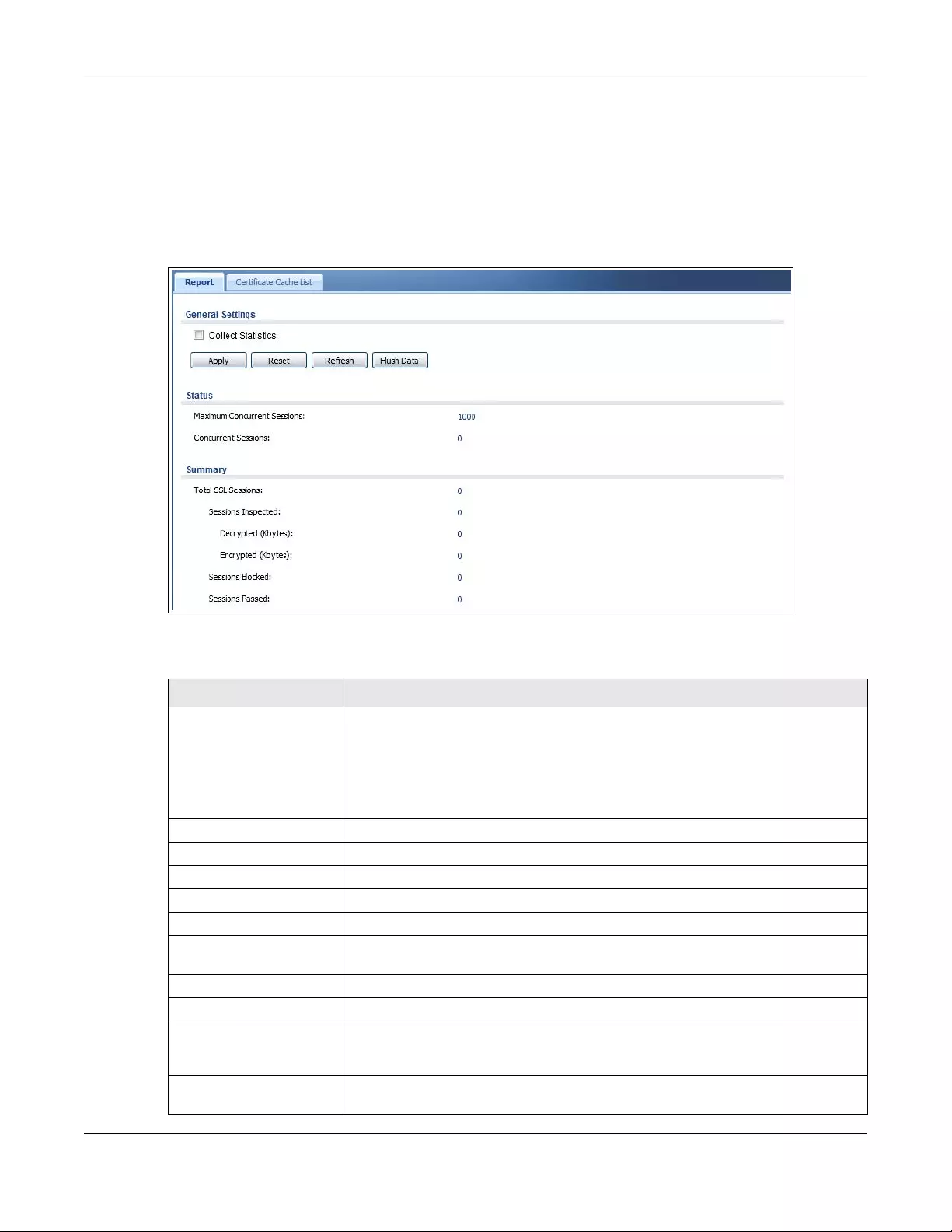
Chapter 7 Monitor
USG/ZyWALL User’s Guide
234
7.25 The SSL Inspection Screens
The Zyxel Device uses SSL Inspection to decrypt SSL traffic, sends it to the UTM engines for inspection,
then encrypts traffic that passes inspection and forwards it.
Click Monitor > UTM Statistics > SSL Inspection > Report to display the following screen.
Figure 200 Monitor > UTM Statistics > SSL Inspection > Report
The following table describes the labels in this screen.
Table 76 Monitor > UTM Statistics > SSL Inspection > Report
LABEL DESCRIPTION
Collect Statistics Select this check box to have the Zyxel Device collect SSL Inspection statistics.
The collection starting time displays after you click Apply. All of the statistics in this
screen are for the time period starting at the time displayed here. The format is year,
month, day and hour, minute, second. All of the statistics are erased if you restart the
Zyxel Device or click Flush Data. Collecting starts over and a new collection start time
displays.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Refresh Click this button to update the report display.
Flush Data Click this button to discard all of the screen’s statistics and update the report display.
Status
Maximum Concurrent
Sessions This shows the maximum number of simultaneous SSL Inspection sessions allowed for
your Zyxel Device model.
Concurrent Sessions This shows the actual number of simultaneous SSL Inspection sessions in progress.
Summary
Total SSL Sessions This is the total of SSL sessions inspected and number of sessions blocked and number
of sessions passed since data was last flushed or the Zyxel Device last rebooted after
Collect Statistics was enabled.
Sessions Inspected This shows the total number of SSL sessions inspected since data was last flushed or the
Zyxel Device last rebooted after Collect Statistics was enabled
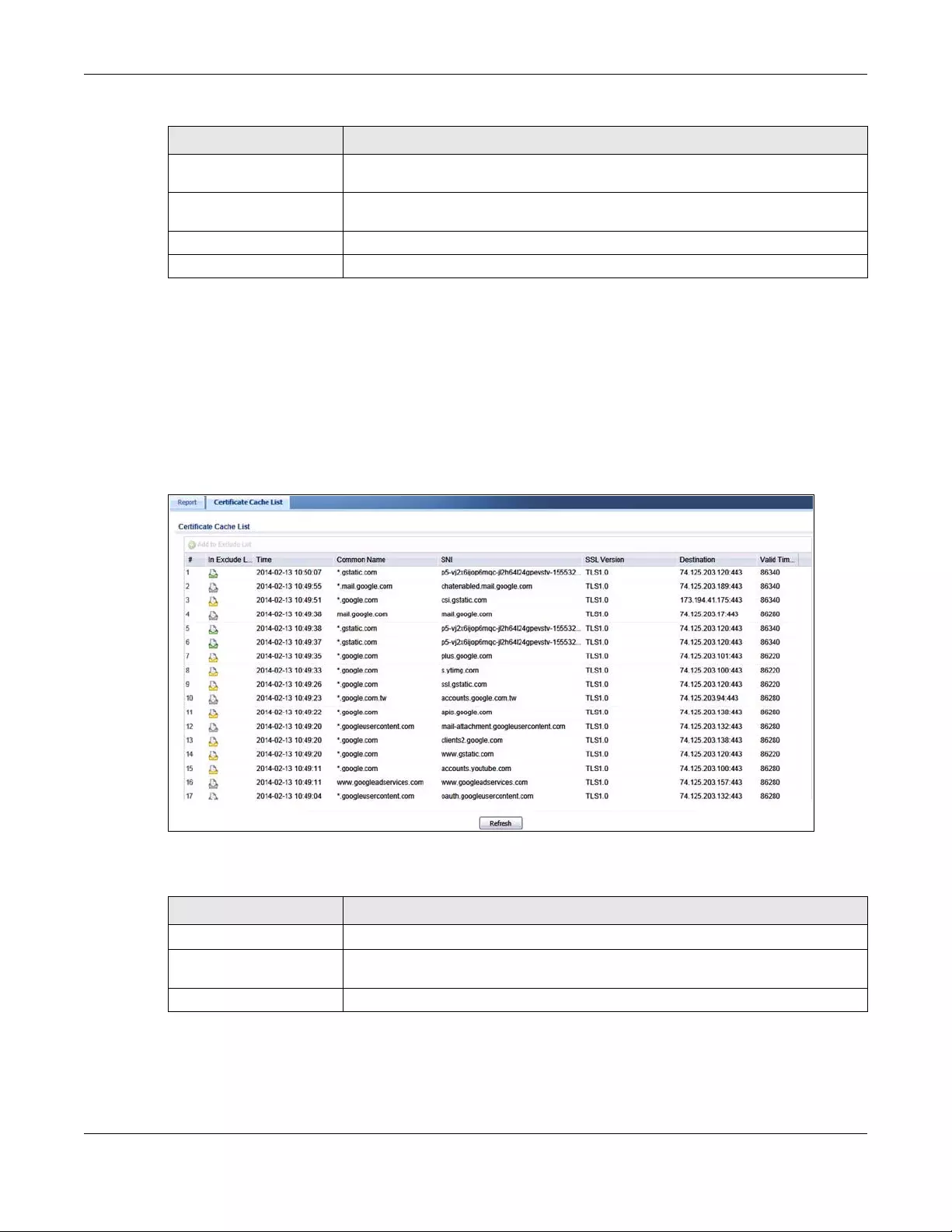
Chapter 7 Monitor
USG/ZyWALL User’s Guide
235
7.25.1 Certificate Cache List
SSL traffic to a server to be excluded from SSL Inspection is identified by its certificate. Traffic in an
Exclude List is not intercepted by SSL Inspection.
Click Monitor > UTM Statistics > SSL Inspection > Certificate Cache List to display a screen that shows
details on SSL traffic going to servers identified by its certificate and an option to add that traffic to the
Exclude List.
Figure 201 Monitor > UTM Statistics > SSL Inspection > Certificate Cache List
The following table describes the labels in this screen.
Decrypted (Kbytes) This shows the number of kilobytes (KB) of data that was decrypted for UTM
inspection.
Encrypted (Kbytes) This shows the number of kilobytes (KB) of data that was re-encrypted after UTM
inspection and then forwarded.
Sessions Blocked This shows the number of SSL sessions blocked.
Sessions Passed This shows the number of SSL sessions passed.
Table 76 Monitor > UTM Statistics > SSL Inspection > Report (continued)
LABEL DESCRIPTION
Table 77 Monitor > UTM Statistics > SSL Inspection > Certificate Cache List
LABEL DESCRIPTION
Certificate Cache List
Add to Exclude list Select and item in the list and click this icon to add the common name (CN) to the
Exclude List.
# This field is a sequential value, and it is not associated with a specific entry.
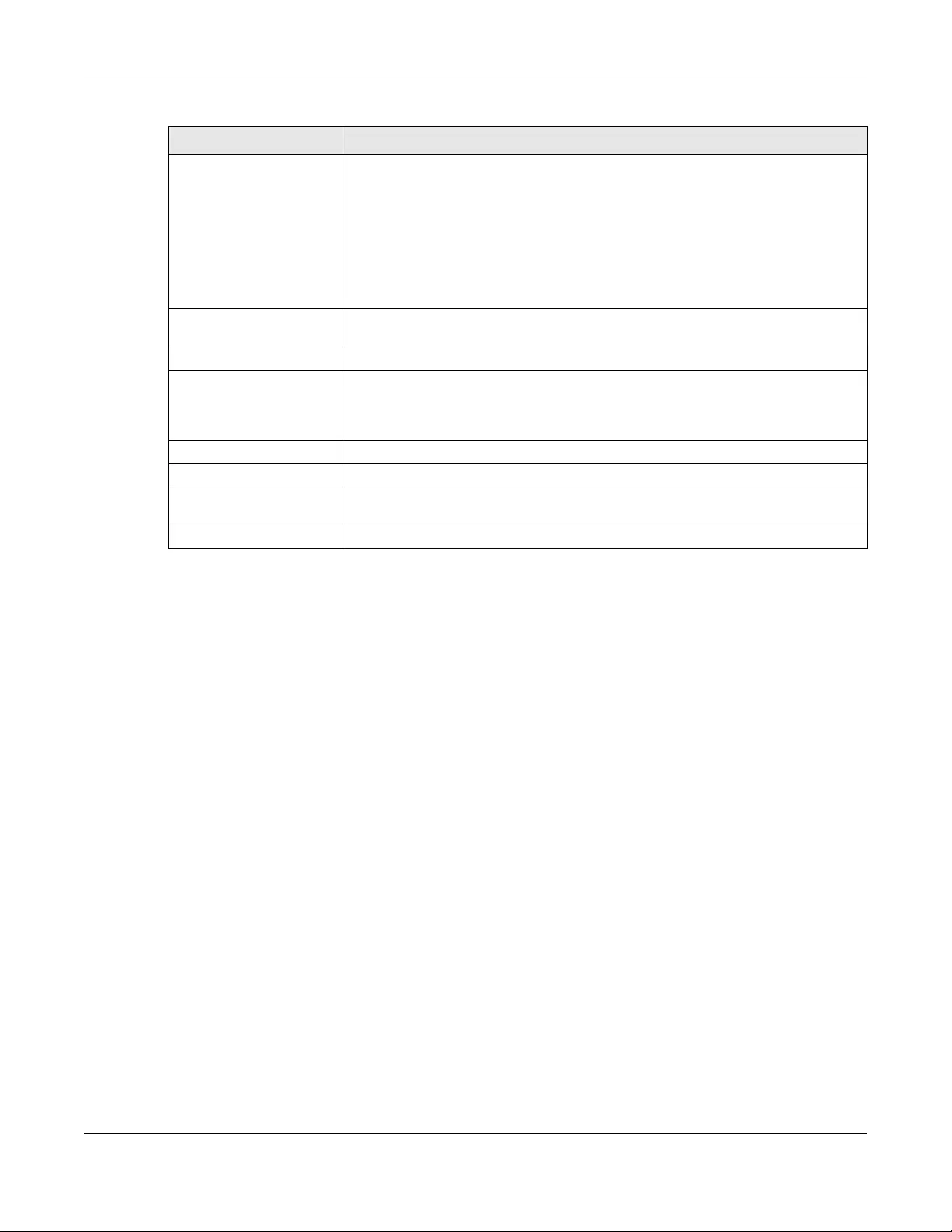
Chapter 7 Monitor
USG/ZyWALL User’s Guide
236
7.26 Log Screens
Log messages are stored in two separate logs, one for regular log messages and one for debugging
messages. In the regular log, you can look at all the log messages by selecting All Logs, or you can
select a specific category of log messages (for example, security policy or user). You can also look at
the debugging log by selecting Debug Log. All debugging messages have the same priority.
7.26.1 View Log
To access this screen, click Monitor > Log. The log is displayed in the following screen.
Note: When a log reaches the maximum number of log messages, new log messages
automatically overwrite existing log messages, starting with the oldest existing log
message first.
• The maximum possible number of log messages in the Zyxel Device varies by model.
Events that generate an alert (as well as a log message) display in red. Regular logs display in black.
Click a column’s heading cell to sort the table entries by that column’s criteria. Click the heading cell
again to reverse the sort order. The Web Configurator saves the filter settings if you leave the View Log
screen and return to it later.
In Exclude List If any one of common name, DNS name, email address or IP address of the
certificate is in the Ex cl ude Li s t, then traffic to the server identified by the certificate is
excluded from inspection.
The icons here are defined as follows:
• Gray: The identity of the certificate is not in the Exclude List
• Green: The common name of the certificate is in the Exclude List
• Yellow: The common name of certificate is not in the Exclude List but one of the
DNS name, email address or IP address is.
Time This is the latest date (yyyy-mm-dd) and time (hh-mm-ss) that the record in the
certificate cache list was met.
Common Name This displays the common name in the certificate of the SSL traffic destination server.
SNI Server Name Indication (SNI) is the domain name entered in the browser, FTP client,
etc. to begin the SSL session with the server. It allows multiple SSL sessions to the same
IP address and port number with different certificates from different SNI. This field
displays the SNI for this SSL session.
SSL Version This field shows the SSL version. SSLv3/TLS1.0 is currently supported
Destination This displays the IP address and port number of the SSL traffic destination server.
Valid Time This displays the cache item expiry time in seconds. The cache item is deleted when
the remaining time expires.
Refresh Click this button to update the information in the screen.
Table 77 Monitor > UTM Statistics > SSL Inspection > Certificate Cache List (continued)
LABEL DESCRIPTION
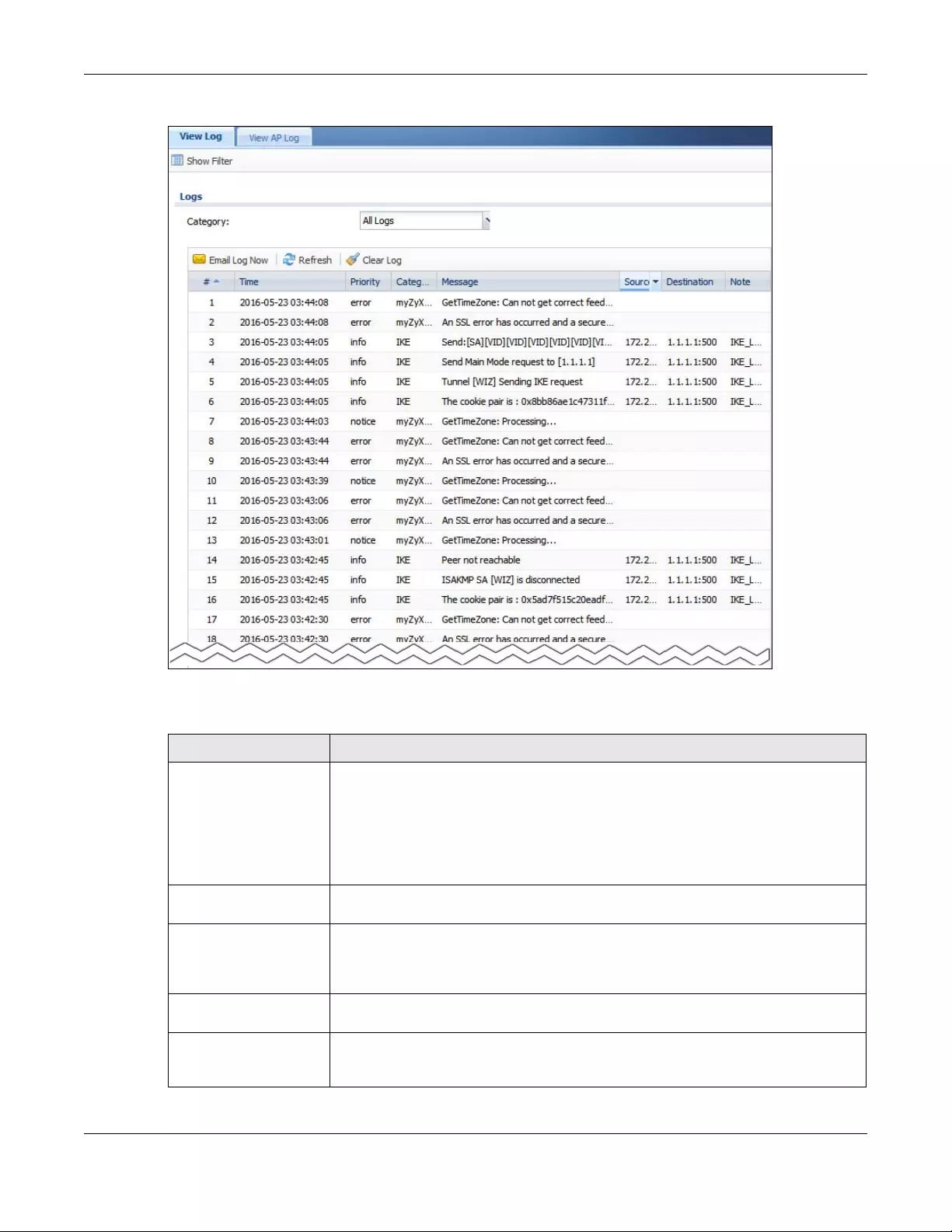
Chapter 7 Monitor
USG/ZyWALL User’s Guide
237
Figure 202 Monitor > Log > View Log
The following table describes the labels in this screen.
Table 78 Monitor > Log > View Log
LABEL DESCRIPTION
Show (Hide) Filter Click this button to show or hide the filter settings.
If the filter settings are hidden, the Category, Email Log Now, Refresh, and Clear Log
fields are available.
If the filter settings are shown, the Category, Priority, Source Address, Destination
Address, Source Interface, De stination Interface , Service, Keyword, and Search fields
are available.
Category Select the type of log message(s) you want to view. You can also view All Logs at one
time, or you can view the Debug Log.
Priority This displays when you show the filter. Select the priority of log messages to display. The
log displays the log messages with this priority or higher. Choices are: any, emerg, alert,
crit, error, warn, notice, and info, from highest priority to lowest priority. This field is read-
only if the Category is Debug Log.
Category This field displays the log that generated the log message. It is the same value used in
the Category field above.
Message This field displays the reason the log message was generated. The text “[count=x]”,
where x is a number, appears at the end of the Message field if log consolidation is
turned on and multiple entries were aggregated to generate into this one.
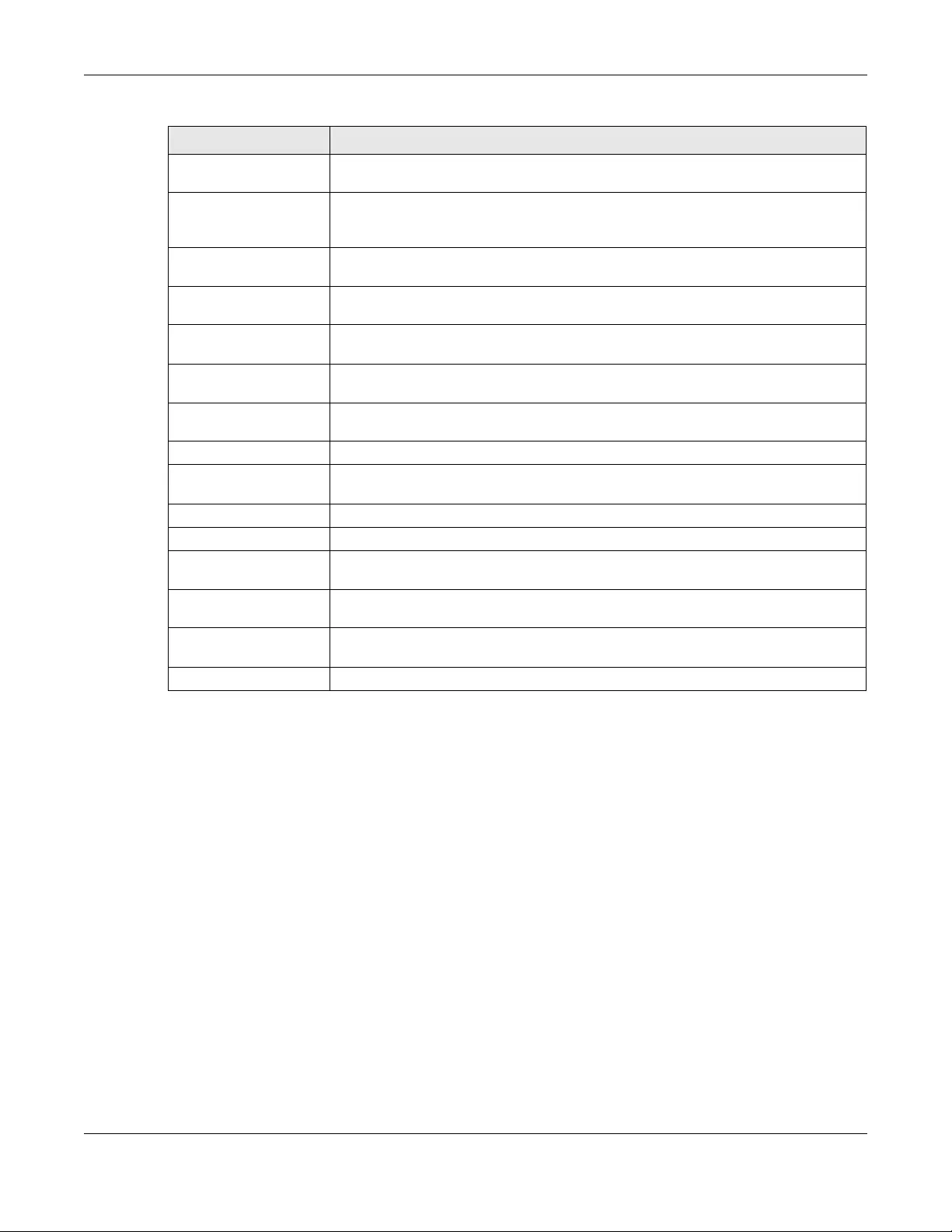
Chapter 7 Monitor
USG/ZyWALL User’s Guide
238
7.26.2 View AP Log
Click on Monitor > Log > View AP Log to open the following screen.
Source Address This displays when you show the filter. Type the source IP address of the incoming
packet that generated the log message. Do not include the port in this filter.
Destination Address This displays when you show the filter. Type the IP address of the destination of the
incoming packet when the log message was generated. Do not include the port in this
filter.
Source Interface This displays when you show the filter. Type the source interface of the incoming packet
that generated the log message.
Destination Interface This displays when you show the filter. Type the interface of the destination of the
incoming packet when the log message was generated.
Protocol This displays when you show the filter. Select a service protocol whose log messages
you would like to see.
Search This displays when you show the filter. Click this button to update the log using the
current filter settings.
Email Log Now Click this button to send log message(s) to the Active e-mail address(es) specified in the
Send Log To field on the Log Settings page.
Refresh Click this button to update the information in the screen.
Clear Log Click this button to clear the whole log, regardless of what is currently displayed on the
screen.
# This field is a sequential value, and it is not associated with a specific log message.
Time This field displays the time the log message was recorded.
Priority This field displays the priority of the log message. It has the same range of values as the
Priority field above.
Source This field displays the source IP address and the port number in the event that
generated the log message.
Destination This field displays the destination IP address and the port number of the event that
generated the log message.
Note This field displays any additional information about the log message.
Table 78 Monitor > Log > View Log (continued)
LABEL DESCRIPTION
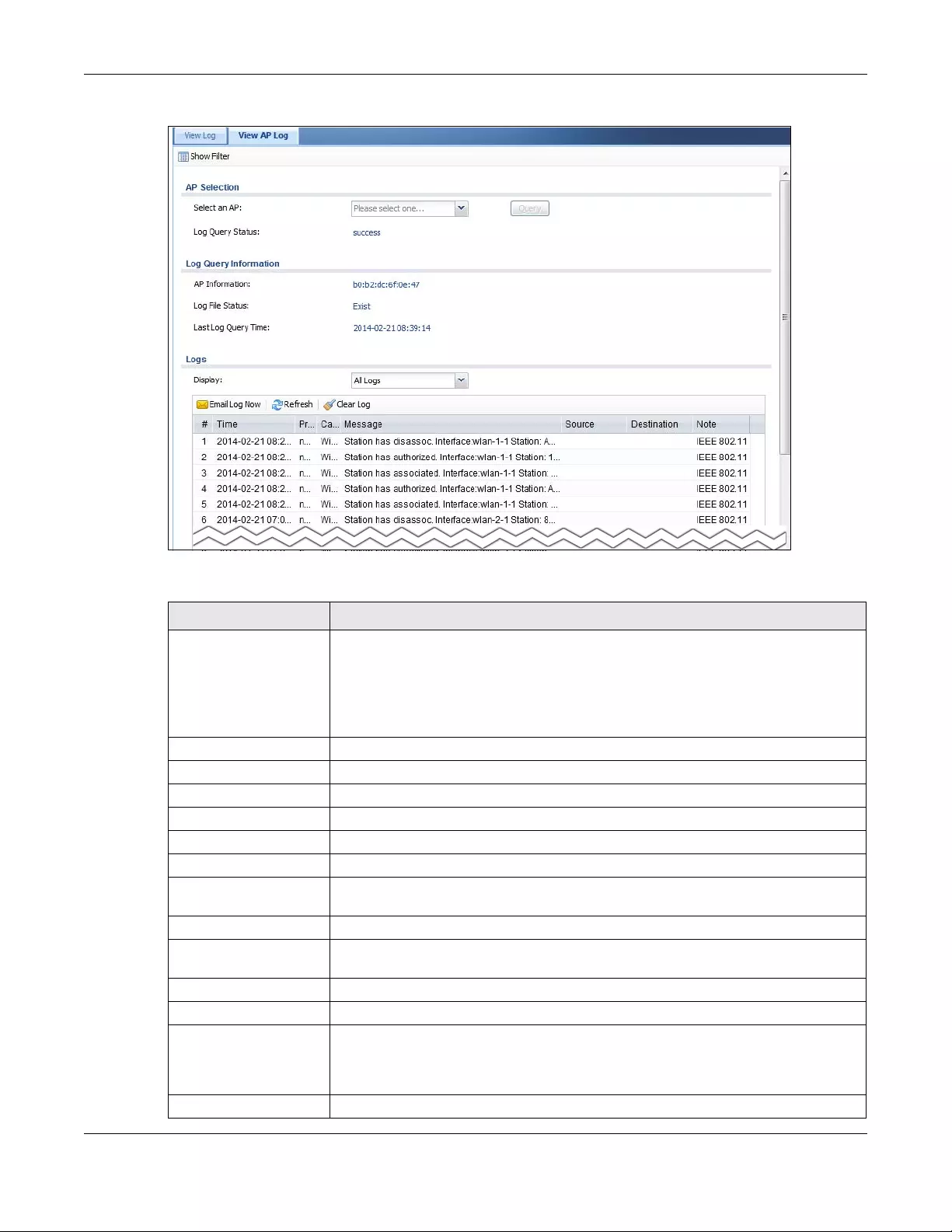
Chapter 7 Monitor
USG/ZyWALL User’s Guide
239
Figure 203 Monitor > Log > View AP Log
The following table describes the labels in this screen.
LABEL DESCRIPTION
Show Filter Click this button to show or hide the filter settings.
If the filter settings are hidden, the Display, Email Log Now, Refresh, and Clear Log fields
are available.
If the filter settings are shown, the Display, Priority, Source Address, Destination Address,
Service, Keyword, and Search fields are available.
Select an AP Click the pull down menu to choose an AP.
Query Click Query to create a Query log.
Log Query Status The field displays the
AP Information This field displays the AP information. N/A is displayed when
Log File Status This field displays how many logs are available. It will display Empty if there’s none.
Last Log Query Time This field displays the most recent time a log query was solicited.
Display Select the category of log message(s) you want to view. You can also view All Logs at
one time, or you can view the Debug Log.
Source Address Type the IP address of the source AP.
Source Interface Select the interface of the source AP from the pull down menu. Choose Any to search
all interface.
Service Select a policy service available from Zyxel Device from the pull down menu.
Protocol Select the protocol of the AP from the pull down menu.
Priority This displays when you show the filter. Select the priority of log messages to display. The
log displays the log messages with this priority or higher. Choices are: any, emerg, alert,
crit, error, warn, notice, and info, from highest priority to lowest priority. This field is read-
only if the Category is Debug Log.
Destination Address Type the IP ad re ss of the destination.
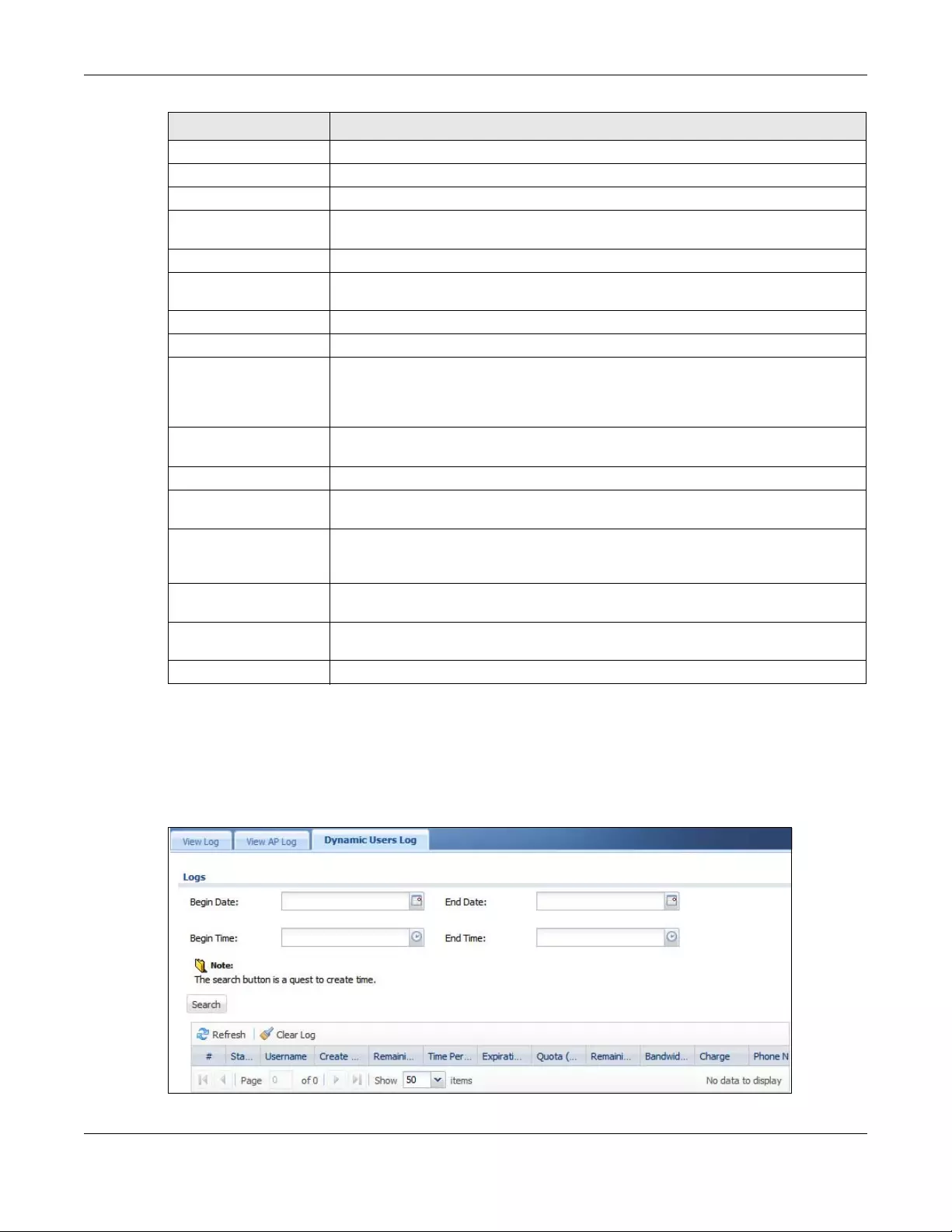
Chapter 7 Monitor
USG/ZyWALL User’s Guide
240
7.26.3 Dynamic Users Log
Use this screen to view the Zyxel Device’s dynamic guest account log messages. Click Monitor > Log >
Dynamic Users Log to access this screen.
Figure 204 Monitor > Log > Dynamic Users Log
Destination Interface Select the destination interface from the pull down menu.
Keyword Type a keyword of the policy service available from Zyxel Device to search for a log.
Search Click this to start the search.
Email Log Now Click this button to send log message(s) to the Active e-mail address(es) specified in the
Send Log To field on the Log Settings page.
Refresh Click this button to update the information in the screen.
Clear Log Click this button to clear the whole log, regardless of what is currently displayed on the
screen.
#This field is a sequential value, and it is not associated with a specific log message.
Time This field displays the time the log message was recorded.
Priority This displays when you show the filter. Select the priority of log messages to display. The
log displays the log messages with this priority or higher. Choices are: any, emerg, alert,
crit, error, warn, notice, and info, from highest priority to lowest priority. This field is read-
only if the Category is Debug Log.
Category This field displays the log that generated the log message. It is the same value used in
the Display and (other) Category fields.
Message This field displays the message of the log.
Source Address This displays when you show the filter. Type the source IP address of the incoming
packet that generated the log message. Do not include the port in this filter.
Destination Address This displays when you show the filter. Type the IP address of the destination of the
incoming packet when the log message was generated. Do not include the port in this
filter.
Source Interface This displays when you show the filter. Select the source interface of the packet that
generated the log message.
Destination Interface This displays when you show the filter. Select the destination interface of the packet that
generated the log message.
Note This field displays any additional information about the log message.
LABEL DESCRIPTION
Chapter 7 Monitor
USG/ZyWALL User’s Guide
241
The following table describes the labels in this screen.
Table 79 Monitor > Log > Dynamic Users Log
LABEL DESCRIPTION
Begin/End Date Select the first and last dates to specify a time period. The Zyxel Device displays log messages
only for the accounts created during the specified time period after you click Search.
Begin/End Time Select the begin time of the first date and the end time of the last date to specify a time
period. The Zyxel Device displays log messages only for the accounts created during the
specified time period after you click Search.
Search Click this button to update the information on the screen using the filter criteria in the date and
time fields.
Refresh Click this button to update the information in the screen.
Clear Log Click this button to delete the log messages for invalid accounts.
# This is the index number of the dynamic guest account in the list.
Status This field displays whether an account expires or not.
Username This field displays the user name of the account.
Create Time This field displays when the account was created.
Remaining Time This field displays the amount of Internet access time remaining for each account.
Time Period This field displays the total account of time the account can use to access the Internet through
the Zyxel Device.
Expiration Time This field displays the date and time the account becomes invalid.
Note: Once the time allocated to a dynamic account is used up or a dynamic
account remains un-used after the expiration time, the account is deleted
from the account list.
Quota (T/U/D) This field displays how much data in both directions (Total) or upstream data (Upload) and
downstream data (Download) can be transmitted through the WAN interface before the
account expires.
Remaining Quota
(T/U/D)
This field displays the remaining amount of data that can be transmitted or received by each
account. You can see the amount of either data in both directions (Total) or upstream data
(Upload) and downstream data (Download).
Bandwidth (U/D) This field displays the maximum upstream (Upload) and downstream (Download) bandwidth
allowed for the user account in kilobits per second.
Charge This field displays the total cost of the account.
Payment Info This field displays the method of payment for each account.
Phone Num This field displays the telephone number for the user account.

USG/ZyWALL User’s Guide
242
CHAPTER 8
Licensing
8.1 Registration Overview
Use the Configuration > Licensing > Registration screens to register your Zyxel Device and manage its
service subscriptions.
• Use the Registration screen (see Section 8.1.2 on page 242) to refresh Zyxel Device registration, go to
portal.myzyxel.com to register your Zyxel Device and activate a service, such as content filtering.
• Use the Service screen (see Section 8.1.3 on page 243) to display the status of your service
registrations and upgrade licenses.
Note: ZyWALL models need a license for UTM (Unified Threat management) functionality.
8.1.1 What you Need to Know
This section introduces the topics covered in this chapter.
Subscription Services Available
See Configuration > Licen sing > Registration > Service for the subscription services that your Zyxel Device
supports.
ZyWALL models need a license for UTM (Unified Threat Management) functionality - see Section 1.1 on
page 24 for details.
You can purchase an iCard and enter its license key at myZyxel.com to have a Zyxel Device use UTM
services or use more counts of a service or extend a service. See the respective chapters in this guide for
more information about UTM features.
8.1.2 Registration Screen
Click the link in this screen to register your Zyxel Device at myZyxel.com. Then click Refresh in this screen
and wait a few moments for the registration information to update. If the page does not refresh, make
sure the Internet connection is working and click Refresh again. The Zyxel Device should already have
Internet access and be able to access myZyxel.com. Click Configuration > Licensing > Registration in the
navigation panel to open the screen as shown next.
Click on the icon to go to the OneSecurity.com website where there is guidance on configuration
walkthrough and other information.
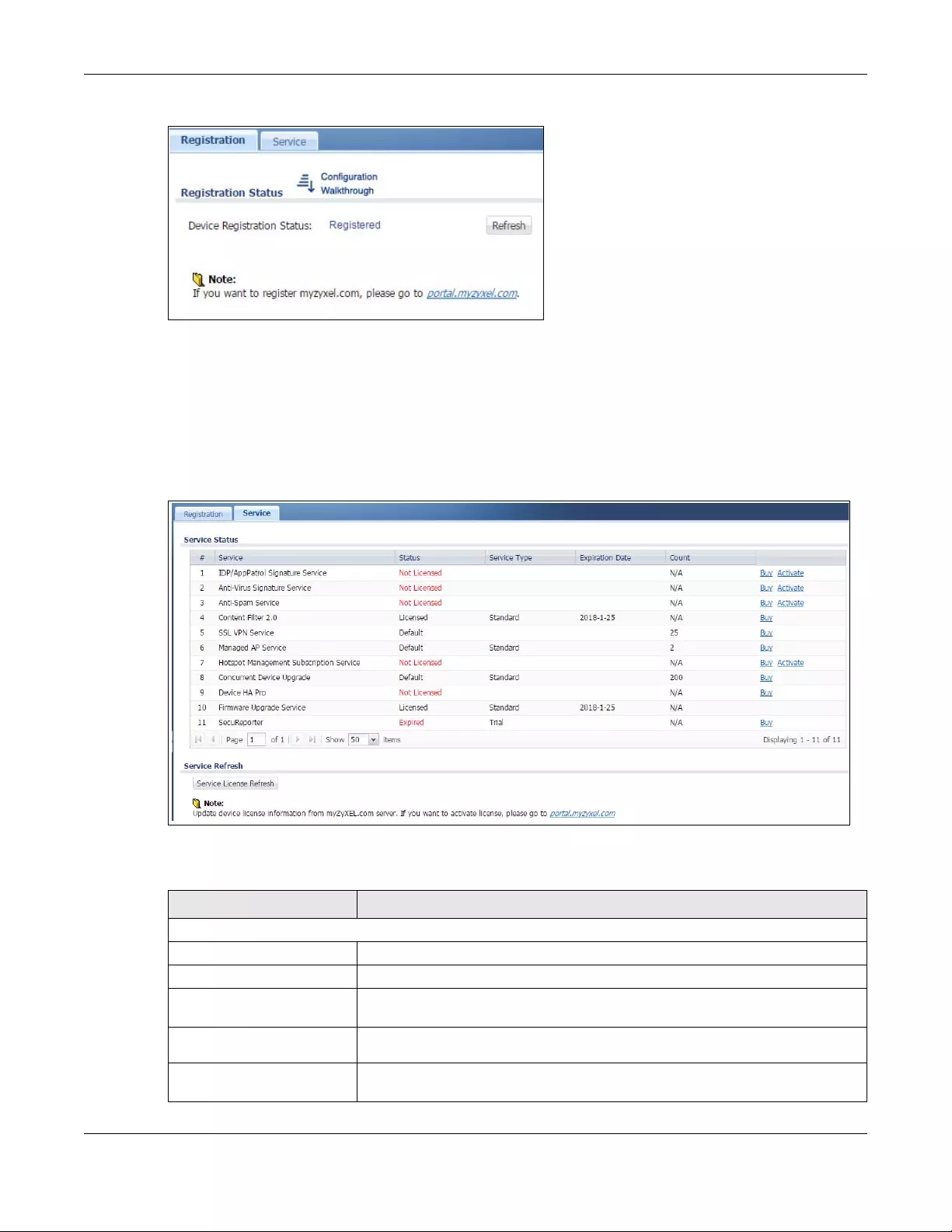
Chapter 8 Licensing
USG/ZyWALL User’s Guide
243
Figure 205 Configuration > Licensing > Registration
8.1.3 Service Screen
Use this screen to display the status of your service registrations and upgrade licenses. To activate or
extend a standard service subscription, purchase an iCard and click Activate to go to a screen to enter
the iCard’s PIN number (license key). Click Config uration > Licensing > Registration > Service to open the
screen as shown next.
Figure 206 Configuration > Licensing > Registration > Service
The following table describes the labels in this screen.
Table 80 Configuration > Licensing > Registration > Service
LABEL DESCRIPTION
License Status
# This is the entry’s position in the list.
Service This lists the services that available on the Zyxel Device.
IDP/AppPatrol Signature
Service This is a license for signatures for Intrusion Detection and Prevention attacks and
Application Patrol inspection.
Anti-Virus Signature
Service This is a license for signatures to detect virus patterns in files.
Anti-Spam Service This is a license for signatures to recognize unsolicited commercial or junk e-mail
suspect of being sent by spammers
Chapter 8 Licensing
USG/ZyWALL User’s Guide
244
Content Filter 2.0 This is a license to a database that can block websites by category, such as
Gambling.
SSL VPN Service This is a license to create more SSL VPN than the default for your Zyxel Device.
Managed AP Service This is a license to manage more APs than the default for your Zyxel Device when
the AP controller is enabled.
Hotspot Management
Subscription Service This is a license to manage hotspot functions such as:
• Billing
• Printer Manager
•Free Time
•SMS
•IPnP
•Walled Garden
•Advertisement
Concurrent Device
Upgrade This is a license for the number of users that can log in and use the Hotspot at one
time.
Device HA Pro This is a license for professional High Availability (HA) that lets a backup Zyxel
Device automatically take over if the master Zyxel Device fails.
Firmware Upgrade
Service This is a license to get Cloud Helper notifications when new firmware is available, At
the time of writing, it is free when you register your Zyxel Device.
SecuReporter This is a license that allows SecuReporter to collect and analyze logs from your Zyxel
Device in order to identify anomalies, alert on potential internal / external threats,
and report on network usage.
Status This field displays whether a service is activated (Licensed) or not (Not Licensed) or
expired (Expired). It also displays the remaining Grace Period if your license has
expired.
Service Type This field displays whether you applied for a trial application (Trial) or registered a
service with your iCard’s PIN number (Standard). This field is blank when a service is
not activated. For an anti-virus service subscription this field also displays the type
of anti-virus engine.
Expiration Date This field displays the date your service license expires or the date the grace period
expires if the license has already expired.
You can continue to use IDP/AppPatrol, Anti-Virus (AV), Content Filter, Anti-Spam
(AS) during the grace period. After the grace period expires, you cannot use these
functions except for the AV and AS Black/White lists.
Count This field displays how many instances of a service you can use with your current
license. N/A means a count does not apply to this service.
If you need a license or a trial license has expired, click Buy to buy a new one. If a
Standard license has expired, click Renew to extend the license.
Then click Activate to connect with the myZyxel.com server to activate the new
license.
Service License Refresh Click this button to renew service license information (such as the registration status
and expiration day).
Note: It is recommended you use this button after you register for a new
service.
Table 80 Configuration > Licensing > Registration > Service (continued)
LABEL DESCRIPTION
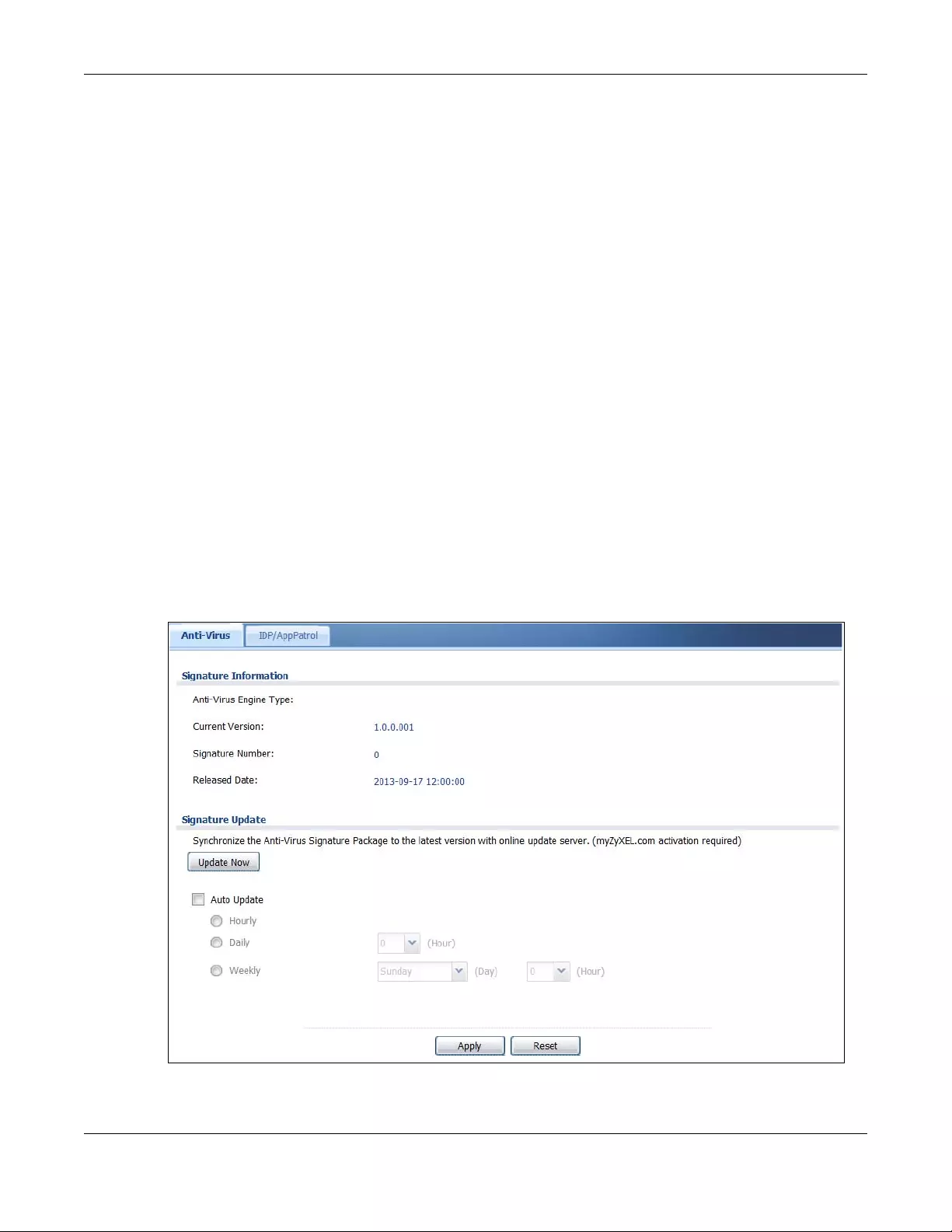
Chapter 8 Licensing
USG/ZyWALL User’s Guide
245
8.2 Signature Update
This section shows you how to update the Zyxel Device’s signature packages.
• Use the Configuration > Licensing > Signature Update > Anti-virus screen (Section 8.2.2 on page 245)
to update the anti-virus signatures.
• Use the Configuration > Licensing > Signature Update > IDP/AppPatrol screen (Section 8.2.3 on page
246) to update the signatures used for IDP and application patrol.
8.2.1 What you Need to Know
• You need a valid service registration to update the anti-virus signatures and the IDP/AppPatrol
signatures.
• You do not need a service registration to update the system-protection signatures.
• Schedule signature updates for a day and time when your network is least busy to minimize disruption
to your network.
• Your custom signature configurations are not over-written when you download new signatures.
Note: The Zyxel Device does not have to reboot when you upload new signatures.
8.2.2 The Anti-Virus Update Screen
Click Configuration > Licensing > Signature Update > Anti-Virus to display the following screen.
Figure 207 Configuration > Licensing > Signature Update >Anti-Virus
Chapter 8 Licensing
USG/ZyWALL User’s Guide
246
The following table describes the labels in this screen.
8.2.3 The IDP/AppPatrol Update Screen
Click Configuration > Licensing > Signature Update > IDP/AppPatrol to display the following screen.
The Zyxel Device comes with signatures for the IDP and application patrol features. These signatures are
continually updated as new attack types evolve. New signatures can be downloaded to the Zyxel
Device periodically if you have subscribed for the IDP/AppPatrol signatures service.
You need to create an account at myZyxel.com, register your Zyxel Device and then subscribe for IDP
service in order to be able to download new packet inspection signatures from myZyxel.com (see the
Registration screens). Use the Update IDP /AppPatrol screen to schedule or immediately download IDP
signatures.
Table 81 Configuration > Licensing > Signature Update >Anti-Virus
LABEL DESCRIPTION
Signature Information The following fields display information on the current signature set that the Zyxel
Device is using.
Anti-Virus Engine
Type This field displays the anti-virus engine used by the Zyxel Device. Update to the latest
signatures and firmware for the best AV protection.
Current Version This field displays the anti-virus signatures version number currently used by the Zyxel
Device. This number gets larger as new signatures are added.
Signature Number This field displays the number of signatures in this set.
Released Date This field displays the date and time the set was released.
Signature Update Use these fields to have the Zyxel Device check for new signatures at myZyxel.com. If
new signatures are found, they are then downloaded to the Zyxel Device.
Update Now Click this button to have the Zyxel Device check for new signatures immediately. If
there are new ones, the Zyxel Device will then download them.
Auto Update Select this check box to have the Zyxel Device automatically check for new signatures
regularly at the time and day specified.
You should select a time when your network is not busy for minimal interruption.
Hourly Select this option to have the Zyxel Device check for new signatures every hour.
Daily Select this option to have the Zyxel Device check for new signatures every day at the
specified time. The time format is the 24 hour clock, so ‘23’ means 11 PM for example.
Weekly Select this option to have the Zyxel Device check for new signatures once a week on
the day and at the time specified.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
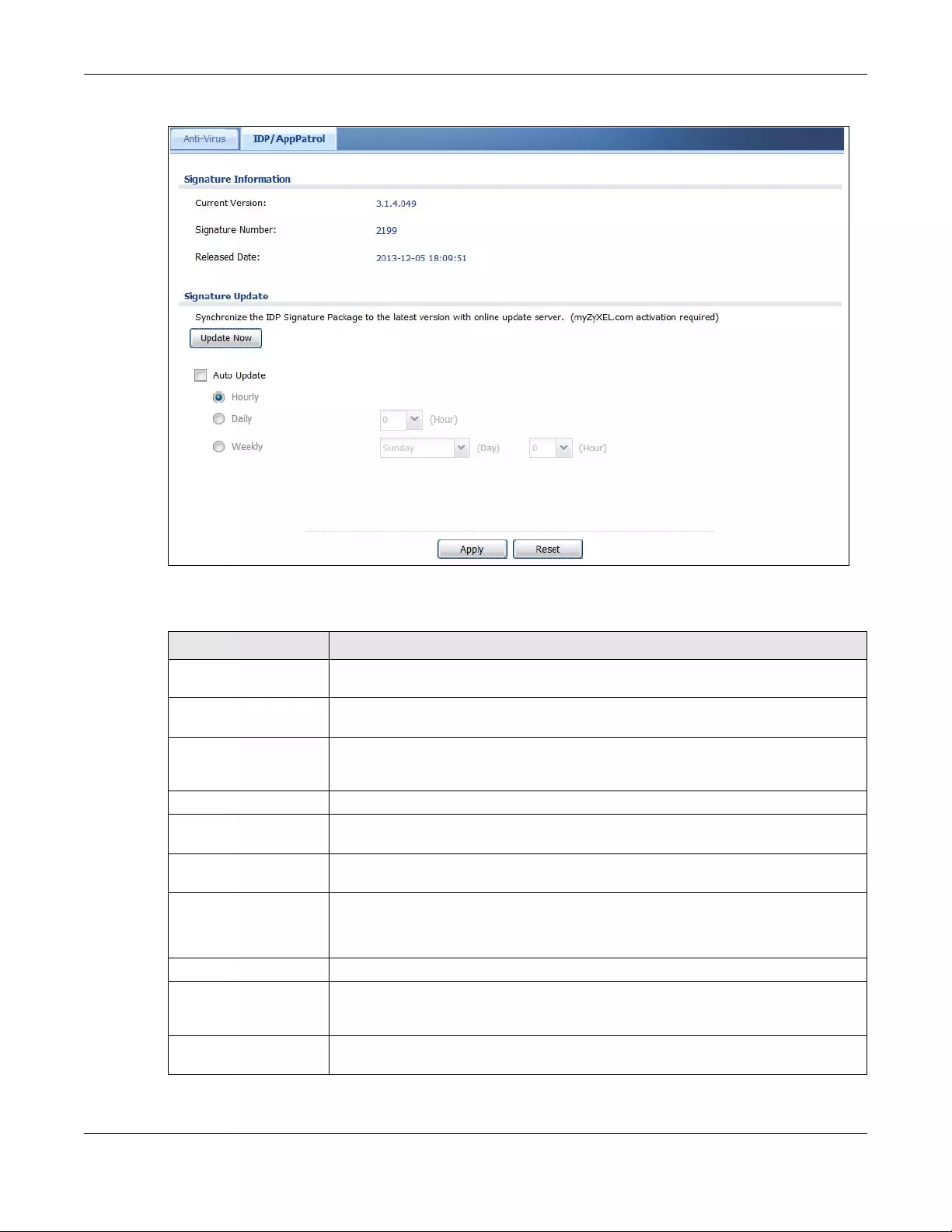
Chapter 8 Licensing
USG/ZyWALL User’s Guide
247
Figure 208 Configuration > Licensing > Signature Update > IDP/AppPatrol
The following table describes the fields in this screen.
Table 82 Configuration > Licensing > Signature Update > IDP/AppPatrol
LABEL DESCRIPTION
Signature Information The following fields display information on the current signature set that the Zyxel Device
is using.
Current Version This field displays the IDP signature and anomaly rule set version number. This number
gets larger as the set is enhanced.
Signature Number This field displays the number of IDP signatures in this set. This number usually gets larger
as the set is enhanced. Older signatures and rules may be removed if they are no
longer applicable or have been supplanted by newer ones.
Released Date This field displays the date and time the set was released.
Signature Update Use these fields to have the Zyxel Device check for new IDP signatures at myZyxel.com.
If new signatures are found, they are then downloaded to the Zyxel Device.
Update Now Click this button to have the Zyxel Device check for new IDP signatures immediately. If
there are new ones, the Zyxel Device will then download them.
Auto Update Select this check box to have the Zyxel Device automatically check for new IDP
signatures regularly at the time and day specified.
You should select a time when your network is not busy for minimal interruption.
Hourly Select this option to have the Zyxel Device check for new IDP signatures every hour.
Daily Select this option to have the Zyxel Device check for new IDP signatures everyday at
the specified time. The time format is the 24 hour clock, so ‘23’ means 11 PM for
example.
Weekly Select this option to have the Zyxel Device check for new IDP signatures once a week
on the day and at the time specified.
Chapter 8 Licensing
USG/ZyWALL User’s Guide
248
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
Table 82 Configuration > Licensing > Signature Update > IDP/AppPatrol (continued)
LABEL DESCRIPTION
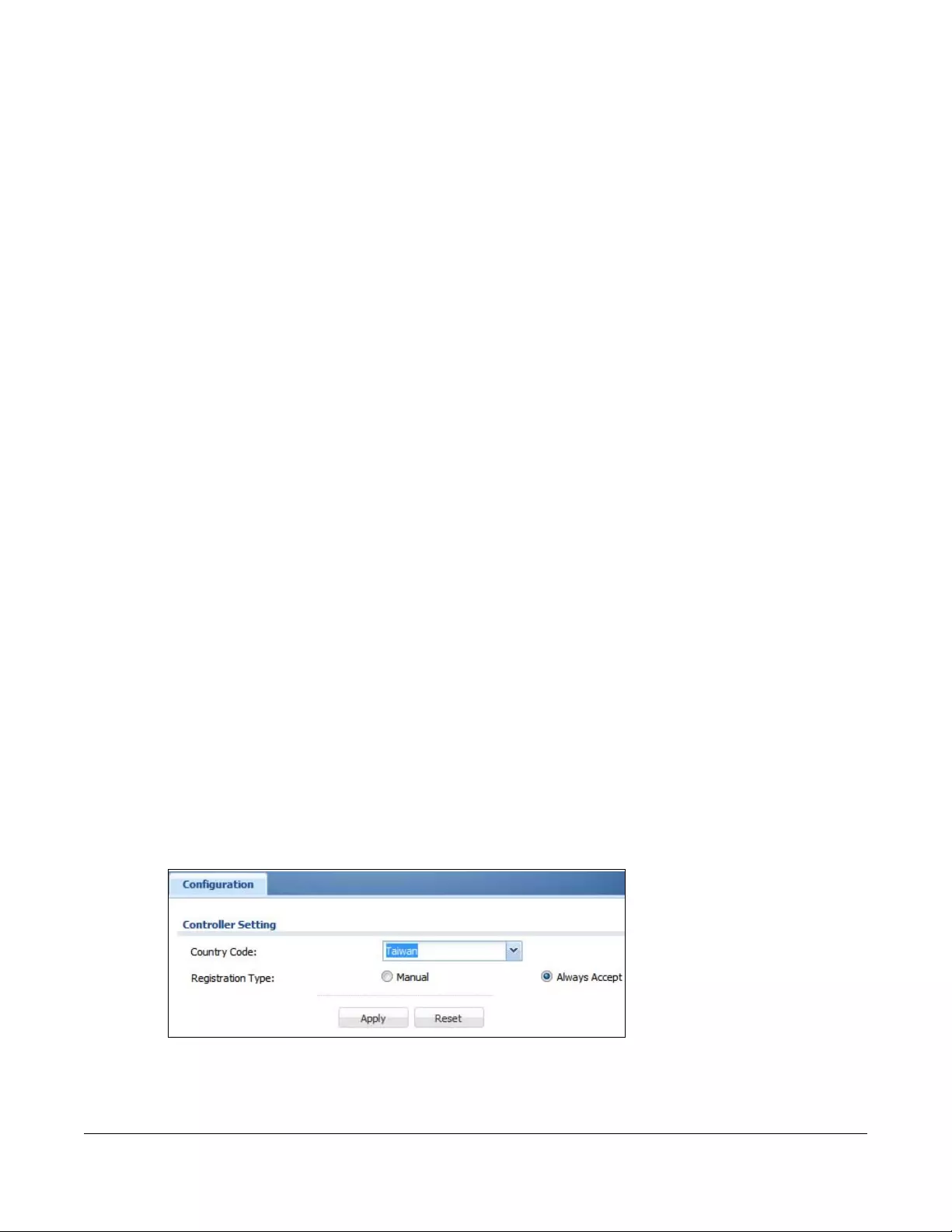
USG/ZyWALL User’s Guide
249
CHAPTER 9
Wireless
9.1 Overview
Use the Wireless screens to configure how the Zyxel Device manages supported Access Points (APs).
Supported APs should be in managed mode. See the product page Licenses tab for a list of supported
APs.
Note: USG20-VPN and USG20W-VPN do not support the AP controller function.
9.1.1 What You Can Do in this Chapter
• Use the Controller screen (Section 9.2 on page 249) to set how the Zyxel Device allows new APs to
connect to the network and set the country code of APs that are connected to the Zyxel Device.
• Use the AP Management screens (Section 9.3 on page 250) to manage all of the APs connected to
the Zyxel Device.
• Use the MON Mode screen (Section 9.4 on page 261) to assign APs either to the rogue AP list or the
friendly AP list.
• Use the Auto Healing screen (Section 9.5 on page 263) to extend the wireless service coverage area
of the managed APs when one of the APs fails.
• Use the RTLS screen (Section 9.6 on page 264) to allow managed APs with battery-powered Wi-Fi tags
be part of Ekahau RTLS (Real Time Location Service). RTLS can track the location of APs managed by
the Zyxel Device to create maps, alerts, and reports.
9.2 Controller Screen
Use this screen to set how the Zyxel Device allows new APs to connect to the network. Click
Configuration > Wireless > Controller to access this screen.
Figure 209 Configuration > Wireless > Controller
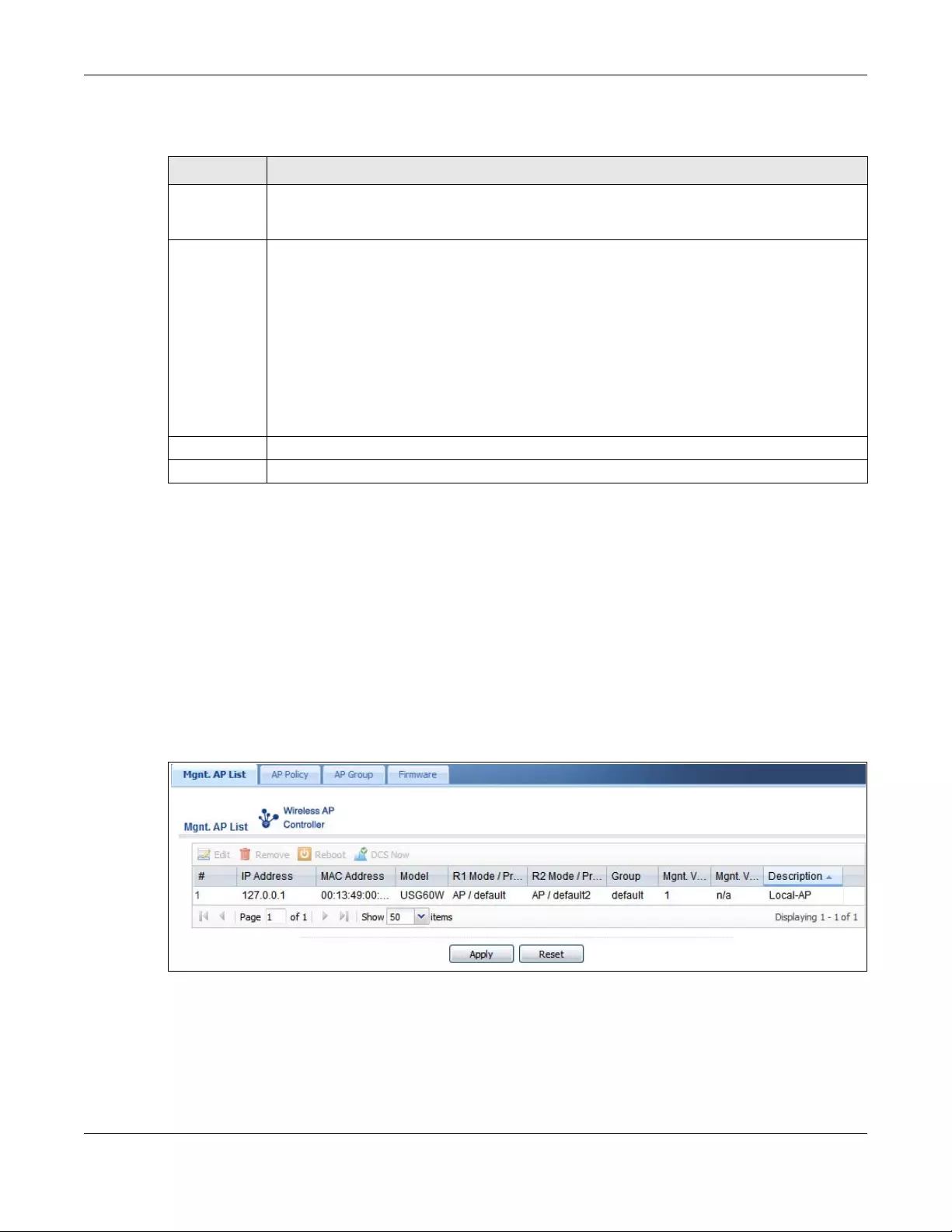
Chapter 9 Wireless
USG/ZyWALL User’s Guide
250
Each field is described in the following table.
9.3 AP Management Screens
Use these screens to manage all of the APs connected to the Zyxel Device. Click Configuration >
Wireless > AP Management to access these screens.
Click on the icon to go to the OneSecurity.com website where there is guidance on configuration
walkthroughs and other information.
9.3.1 Mgnt. AP List
Figure 210 Configuration > Wireless > AP Management > Mgnt. AP List
Table 83 Configuration > Wireless > Controller
LABEL DESCRIPTION
Country Code Select the country code of APs that are connected to the Zyxel Device to be the same as where
the Zyxel Device is located/installed. The available channels vary depending on the country you
selected.
Registration
Type
Select Manual to add each AP to the Zyxel Device for management, or Always Accept to
automatically add APs to the Zyxel Device for management.
If you select Manual, then go to Monitor > Wireless > AP Information > AP List, select an AP to be
managed and then click Add to Mgnt AP List. That AP will then appear in Configuration > Wireless
> Controller > Mgnt. AP List.
Note: Select the Manual option for managing a specific set of APs. This is
recommended as the registration mechanism cannot automatically differentiate
between friendly and rogue APs.
APs must be connected to the Zyxel Device by a wired connection or network.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Chapter 9 Wireless
USG/ZyWALL User’s Guide
251
Each field is described in the following table.
Table 84 Configuration > Wireless > AP Management > Mgnt. AP List
LABEL DESCRIPTION
Edit Select an AP and click this button to edit its properties.
Remove Select an AP and click this button to remove it from the list.
Note: If in the Configuration > Wireless > Controller screen you set the Registration
Type to Always Accept, then as soon as you remove an AP from this list it
reconnects.
Reboot Select an AP and click this button to force it to restart.
DCS Now Select one or multiple APs and click this button to use DCS (Dynamic Channel Selection) to
allow the AP to automatically find a less-used channel in an environment where there are
many APs and there may be interference.
Note: You should have enabled DCS in the applied AP radio profile before the
APs can use DCS.
Note: DCS is not supported on the radio which is working in repeater AP mode.
# This field is a sequential value, and it is not associated with any entry.
IP Address This field displays the IP address of the AP.
MAC Address This field displays the MAC address of the AP.
Model This field displays the AP’s hardware model information. It displays N/A (not applicable) only
when the AP disconnects from the Zyxel Device and the information is unavailable as a
result.
R1 Mode / Profile This field displays the operating mode (AP) and AP profile name for Radio 1. It displays n/a
for the profile for a radio not using an AP profile.
Mgnt. VLAN ID(AC) This displays the Access Controller (the Zyxel Device) management VLAN ID setting for the
AP.
Mgnt. VLAN ID(AP) This displays the runtime management VLAN ID setting on the AP. VLAN Conflict displays if
the AP’s management VLAN ID does not match the Mgnt. VLAN ID(AC). This field displays n/
a if the Zyxel Device cannot get VLAN information from the AP.
Description This field displays the AP’s description, which you can configure by selecting the AP’s entry
and clicking the Edit button.
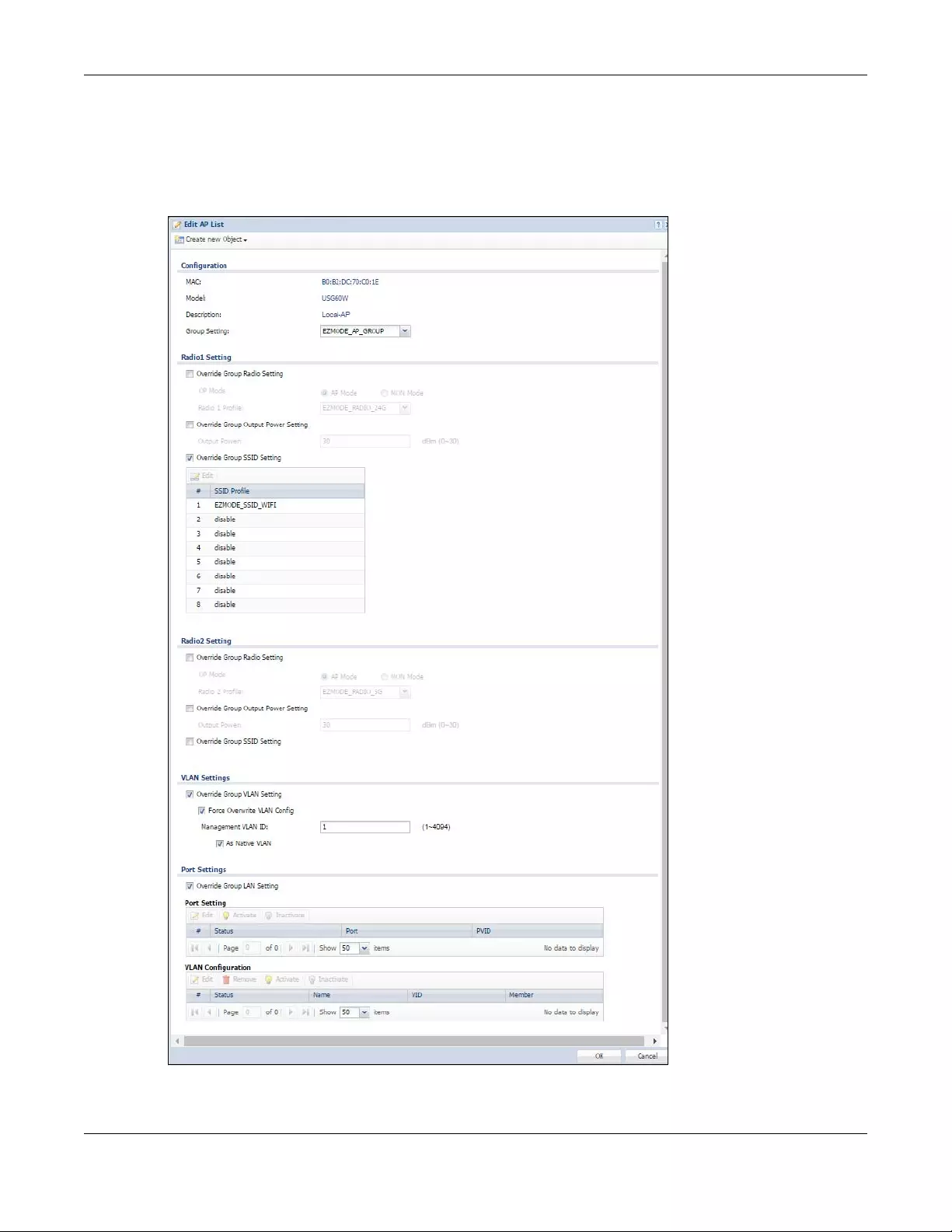
Chapter 9 Wireless
USG/ZyWALL User’s Guide
252
9.3.1.1 Edit AP List
Select an AP and click the Edit button in the Configuration > Wireless > AP Mana gement table to display
this screen.
Figure 211 Configuration > Wireless > AP Management > Mgnt. AP List > Edit AP List
Chapter 9 Wireless
USG/ZyWALL User’s Guide
253
Each field is described in the following table.
Table 85 Configuration > Wireless > AP Management > Mgnt. AP List > Edit AP List
LABEL DESCRIPTION
Create new Object Use this menu to create a new Radio Profile object to associate with this AP.
MAC This displays the MAC address of the selected AP.
Model This field displays the AP’s hardware model information. It displays N/A (not applicable) only
when the AP disconnects from the Zyxel Device and the information is unavailable as a
result.
Description Enter a description for this AP. You can use up to 31 characters, spaces and underscores
allowed.
Group Setting Select an AP group to which you want this AP to belong.
Radio 1/2 Setting
Override Group
Radio Setting
Select this option to overwrite the AP radio settings with the settings you configure here.
Radio 1/2 OP Mode Select the operating mode for radio 1 or radio 2.
AP Mode means the AP can receive connections from wireless clients and pass their data
traffic through to the Zyxel Device to be managed (or subsequently passed on to an
upstream gateway for managing).
MON Mode means the AP monitors the broadcast area for other APs, then passes their
information on to the Zyxel Device where it can be determined if those APs are friendly or
rogue. If an AP is set to this mode it cannot receive connections from wireless clients.
Radio 1/2 Profile Select a profile from the list. If no profile exists, you can create a new one through the
Create new Object menu.
Override Group
Output Power
Setting
Select this option to overwrite the AP output power setting with the setting you configure
here.
Output Power Set the output power of the AP.
Override Group SSID
Setting
Select this option to overwrite the AP SSID profile setting with the setting you configure here.
This section allows you to associate an SSID profile with the radio.
Edit Select an SSID and click this button to reassign it. The selected SSID becomes editable
immediately upon clicking.
#This is the index number of the SSID profile. You can associate up to eight SSID profiles with
an AP radio.
SSID Profile Indicates which SSID profile is associated with this radio profile.
Force Overwrite
VLAN Config
Select this to have the Zyxel Device change the AP’s management VLAN to match the
configuration in this screen.
Management VLAN
ID
Enter a VLAN ID for this AP.
As Native VLAN Select this option to treat this VLAN ID as a VLAN created on the Zyxel Device and not one
assigned to it from outside the network.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to close the window with changes unsaved.
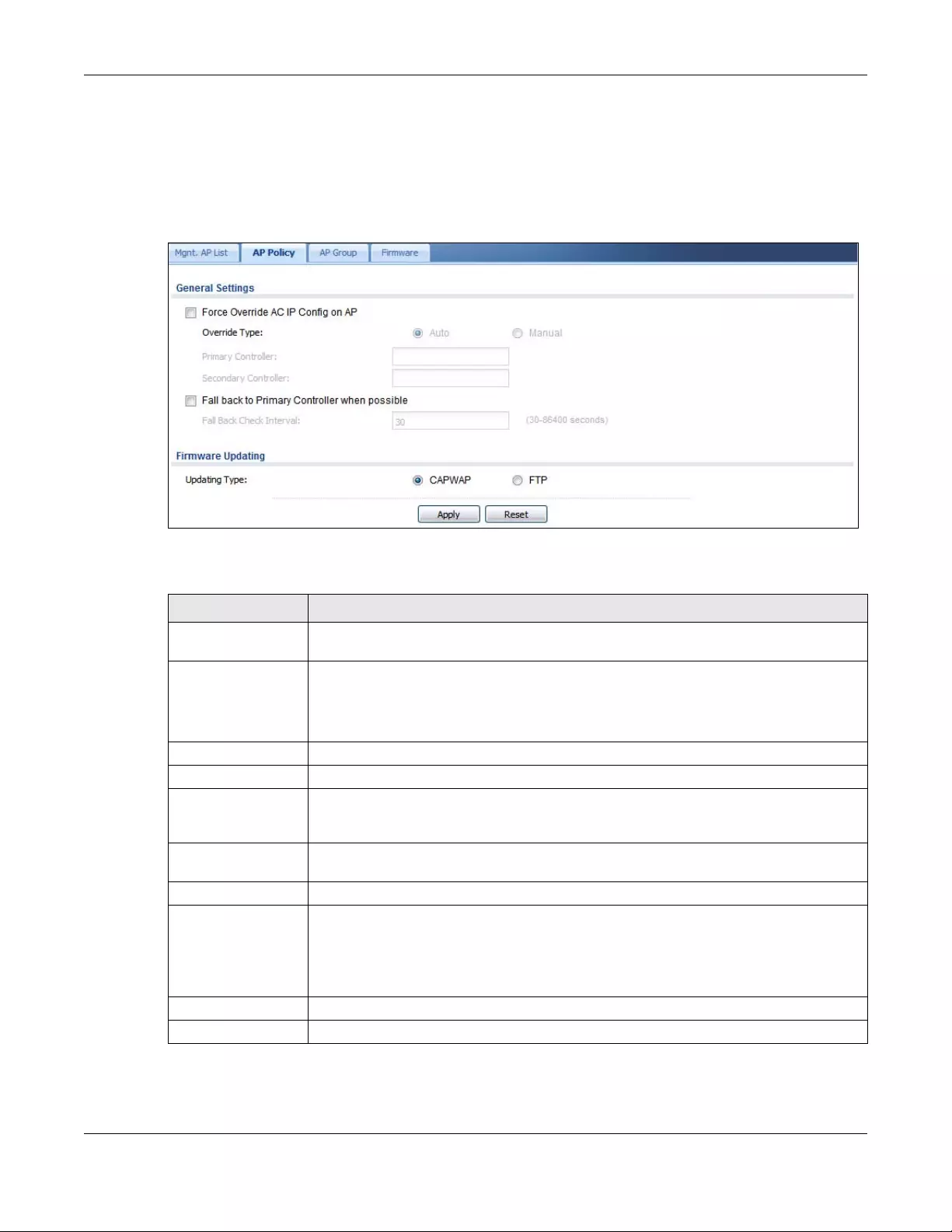
Chapter 9 Wireless
USG/ZyWALL User’s Guide
254
9.3.2 AP Policy
Use this screen to configure the AP controller’s IP address on the managed APs and determine the
action the managed APs take if the current AP controller fails. Click Configuration > Wireless > AP
Management > AP Policy to access this screen.
Figure 212 Configuration > Wireless > AP Management > AP Policy
Each field is described in the following table.
Table 86 Configuration > Wireless > AP Management > AP Policy
LABEL DESCRIPTION
Force Override AC IP
Config on AP
Select this to have the Zyxel Device change the AP controller’s IP address on the managed
AP(s) to match the configuration in this screen.
Override Type Select Auto to have the managed AP(s) automatically send broadcast packets to find any
other available AP controllers.
Select Manual to replace the AP controller’s IP address configured on the managed AP(s)
with the one(s) you specified below.
Primary Controller Specify the IP address of the primary AP controller if you set Override Type to Manual.
Secondary Controller Specify the IP address of the secondary AP controller if you set Override Type to Manual.
Fall back to Primary
Controller when
possible
Select this option to have the managed AP(s) change back to associate with the primary
AP controller as soon as the primary AP controller is available.
Fall Back Check
Interval
Set how often the managed AP(s) check whether the primary AP controller is available.
Firmware Updating
Updating Type Specify how you want the Zyxel Device to upgrade AP firmware.
Select CAPWAP to have the Zyxel Device use CAPWAP (Control and Provisioning of Wireless
Access Points protocol) to update firmware on the managed APs.
Select FTP to have the Zyxel Device use FTP to update firmware on the managed APs.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
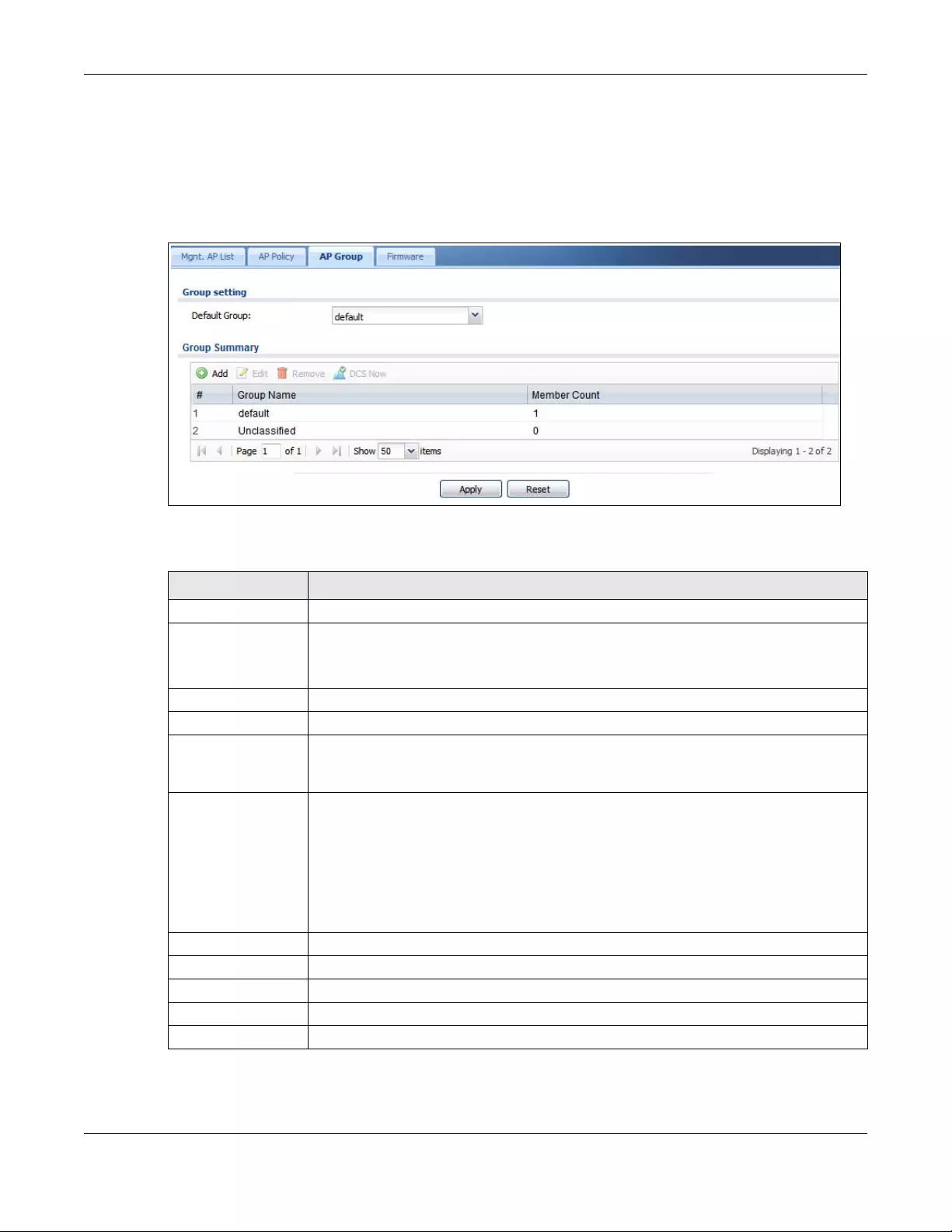
Chapter 9 Wireless
USG/ZyWALL User’s Guide
255
9.3.3 AP Group
Use this screen to configure AP groups, which define the radio, port, VLAN and load balancing settings
and apply the settings to all APs in the group. An AP can belong to one AP group at a time. Click
Configuration > Wireless > AP Management > AP Group to access this screen.
Figure 213 Configuration > Wireless > AP Management > AP Group
Each field is described in the following table.
Table 87 Configuration > Wireless > AP Management > AP Group
LABEL DESCRIPTION
Group Setting
Default Group Select a group that is used as the default group.
Any AP that is not configured to associate with a specific AP group belongs to the default
group automatically.
Group Summary
Edit Select an entry and click this button to edit its properties.
Remove Select an entry and click this button to remove it from the list.
Note: You cannot remove a group with which an AP is associated.
DCS Now Select one or multiple groups and click this button to use DCS (Dynamic Channel Selection)
to allow the APs in the group(s) to automatically find a less-used channel in an environment
where there are many APs and there may be interference.
Note: You should have enabled DCS in the applied AP radio profile before the
APs can use DCS.
Note: DCS is not supported on the radio which is working in repeater AP mode.
# This is the index number of the group in the list.
Group Name This is the name of the group.
Member Count This is the total number of APs which belong to this group.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
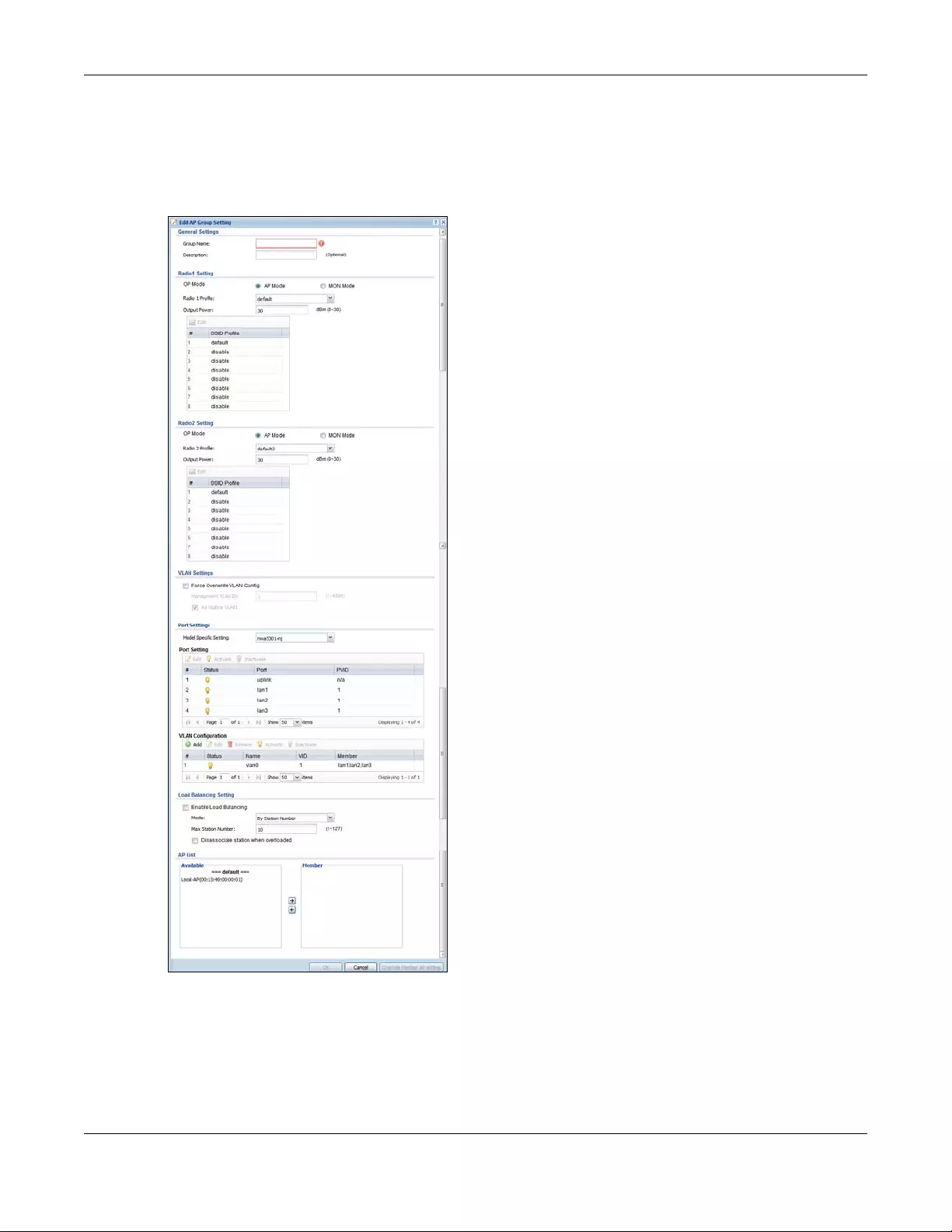
Chapter 9 Wireless
USG/ZyWALL User’s Guide
256
9.3.3.1 Add/Edit AP Group
Click Add or select an AP group and click the Edit button in the Configuration > Wireless > AP
Management > AP Group table to display this screen.
Figure 214 Configuration > Wireless > AP Management > AP Group > Add/Edit
Chapter 9 Wireless
USG/ZyWALL User’s Guide
257
Each field is described in the following table.
Table 88 Configuration > Wireless > AP Management > AP Group > Add/Edit
LABEL DESCRIPTION
General Settings
Group Name Enter a name for this group. You can use up to 31 alphanumeric characters. Dashes and
underscores are also allowed. The name should start with a letter.
Description Enter a description for this group. You can use up to 31 characters, spaces and underscores
allowed.
Radio 1/2 Setting
OP Mode Select the operating mode for radio 1 or radio 2.
AP Mode means the AP can receive connections from wireless clients and pass their data
traffic through to the Zyxel Device to be managed (or subsequently passed on to an
upstream gateway for managing).
MON Mode means the AP monitors the broadcast area for other APs, then passes their
information on to the Zyxel Device where it can be determined if those APs are friendly or
rogue. If an AP is set to this mode it cannot receive connections from wireless clients.
Radio 1/2 Profile Select a radio profile from the list. Use Object > AP Profile > Radio to create new profiles.
Output Power Set the maximum output power of the AP.
If there is a high density of APs in an area, decrease the output power of the managed AP
to reduce interference with other APs.
Note: Reducing the output power also reduces the Zyxel Device’s effective
broadcast radius.
Edit Select an SSID and click this button to reassign it. The selected SSID becomes editable
immediately upon clicking.
#This is the index number of the SSID profile. You can associate up to eight SSID profiles with
an AP radio.
SSID Profile Indicates which SSID profile is associated with this radio profile.
VLAN Settings
Force Overwrite
VLAN Config
Select this to have the Zyxel Device change the AP’s management VLAN to match the
configuration in this screen.
Management VLAN
ID
Enter a VLAN ID for this AP.
As Native VLAN Select this option to treat this VLAN ID as a VLAN created on the Zyxel Device and not one
assigned to it from outside the network.
Port Settings
Model Specific
Setting
Select the model of the managed AP to display the model-specific port and VLAN settings
in the tables below.
Port Setting You can activate or deactivate a non-uplink port.
# This is the port’s index number in this list.
Status This displays whether or not the port is activated.
Port This shows the name of the physical Ethernet port on the managed AP.
PVID This shows the port’s PVID.
A PVID (Port VLAN ID) is a tag that adds to incoming untagged frames received on a port
so that the frames are forwarded to the VLAN group that the tag defines.
VLAN Configuration Use Add to create a new VLAN Configuration. Select a VLAN Configuration first to use the
Edit, Remove, Activate and Inactivate buttons.
# This is the VLAN’s index number in this list.
Chapter 9 Wireless
USG/ZyWALL User’s Guide
258
Status This displays whether or not the VLAN is activated.
Name This shows the name of the VLAN.
VID This shows the VLAN ID number.
Member This field displays the Ethernet port(s) that is a member of this VLAN.
Load Balancing
Setting
Enable Load
Balancing
Select this to enable load balancing on the Zyxel Device.
Use this section to configure wireless network traffic load balancing between the managed
APs in this group.
Note: Load balancing is not supported on the radio which is working in root AP or
repeater AP mode.
Mode Select a mode by which load balancing is carried out.
Select By Station Number to balance network traffic based on the number of specified
stations connected to an AP.
Select By Traffic Level to balance network traffic based on the volume generated by the
stations connected to an AP.
Select By Smart Classroom to balance network traffic based on the number of specified
stations connected to an AP. The AP ignores association request and authentication
request packets from any new station when the maximum number of stations is reached.
If you select By Station Number or By Traffic Level, once the threshold is crossed (either the
maximum station numbers or with network traffic), the AP delays association request and
authentication request packets from any new station that attempts to make a connection.
This allows the station to automatically attempt to connect to another, less burdened AP if
one is available.
Max Station
Number Enter the threshold number of stations at which an AP begins load balancing its
connections.
Traffic Level Select the threshold traffic level at which the AP begins load balancing its connections
(Low, Medium, High).
The maximum bandwidth allowed for each level is:
•Low - 11 Mbps,
•Medium - 23 Mbps
•High - 35M bps
Disassociate
station when
overloaded
This function is enabled by default and the disassociation priority is always Signal Strength
when you set Mode to By Smart Classroom.
Select this option to disassociate wireless clients connected to the AP when it becomes
overloaded. If you do not enable this option, then the AP simply delays the connection until
it can afford the bandwidth it requires, or it transfers the connection to another AP within its
broadcast radius.
The disassociation priority is determined automatically by the Zyxel Device and is as follows:
•Idle Timeout - Devices that have been idle the longest will be disassociated first. If none
of the connected devices are idle, then the priority shifts to Signal Strength.
•Signal Strength - Devices with the weakest signal strength will be disassociated first.
Note: If you enable this function, you should ensure that there are multiple APs
within the broadcast radius that can accept any rejected or kicked wireless
clients; otherwise, a wireless client attempting to connect to an overloaded
AP will be kicked continuously and never be allowed to connect.
Table 88 Configuration > Wireless > AP Management > AP Group > Add/Edit (continued)
LABEL DESCRIPTION
Chapter 9 Wireless
USG/ZyWALL User’s Guide
259
9.3.4 Firmware
The Zyxel Device stores an AP firmware in order to manage supported APs. This screen allows the Zyxel
Device to check for and download new AP firmware when it becomes available on the firmware server.
All APs managed by the Zyxel Device must have the same firmware version as the AP firmware on the
Zyxel Device.
When an AP connects to the Zyxel Device wireless controller, the Zyxel Device will check if the AP has
the same firmware version as the AP firmware on the Zyxel Device. If yes, then the Zyxel Device can
manage it. If no, then the AP must upgrade (or downgrade) its firmware to be the same version as the
AP firmware on the Zyxel Device (and reboot).
The Zyxel Device should always have the latest AP firmware so that:
• APs don’t have to downgrade firmware in order to be managed
• All new APs are supported.
Use Check to see if the Zyxel Device has the latest AP firmware. Use Apply to have the Zyxel Device
download the latest AP firmware (see More Details for more information on the firmware) from the
firmware server. If the Zyxel Device does not have enough space for the latest AP firmware, then the
Zyxel Device will delete an existing firmware that no AP is using before downloading the new AP
firmware.
AP List
Available This lists the APs that do not belong to this group. Select the APs that you want to add to the
group you are editing, and click the right arrow button to add them.
Member This lists the APs that belong to this group. Select any APs that you want to remove from the
group, and click the left arrow button to remove them.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to close the window with changes unsaved.
Override Member AP
Setting
Click this button to overwrite the settings of all managed APs in this group with the settings
you configure here. All Override Group check boxes on the AP Management > Mgnt. AP List
> Edit AP List screen for the APs in this group will be deselected.
Table 88 Configuration > Wireless > AP Management > AP Group > Add/Edit (continued)
LABEL DESCRIPTION
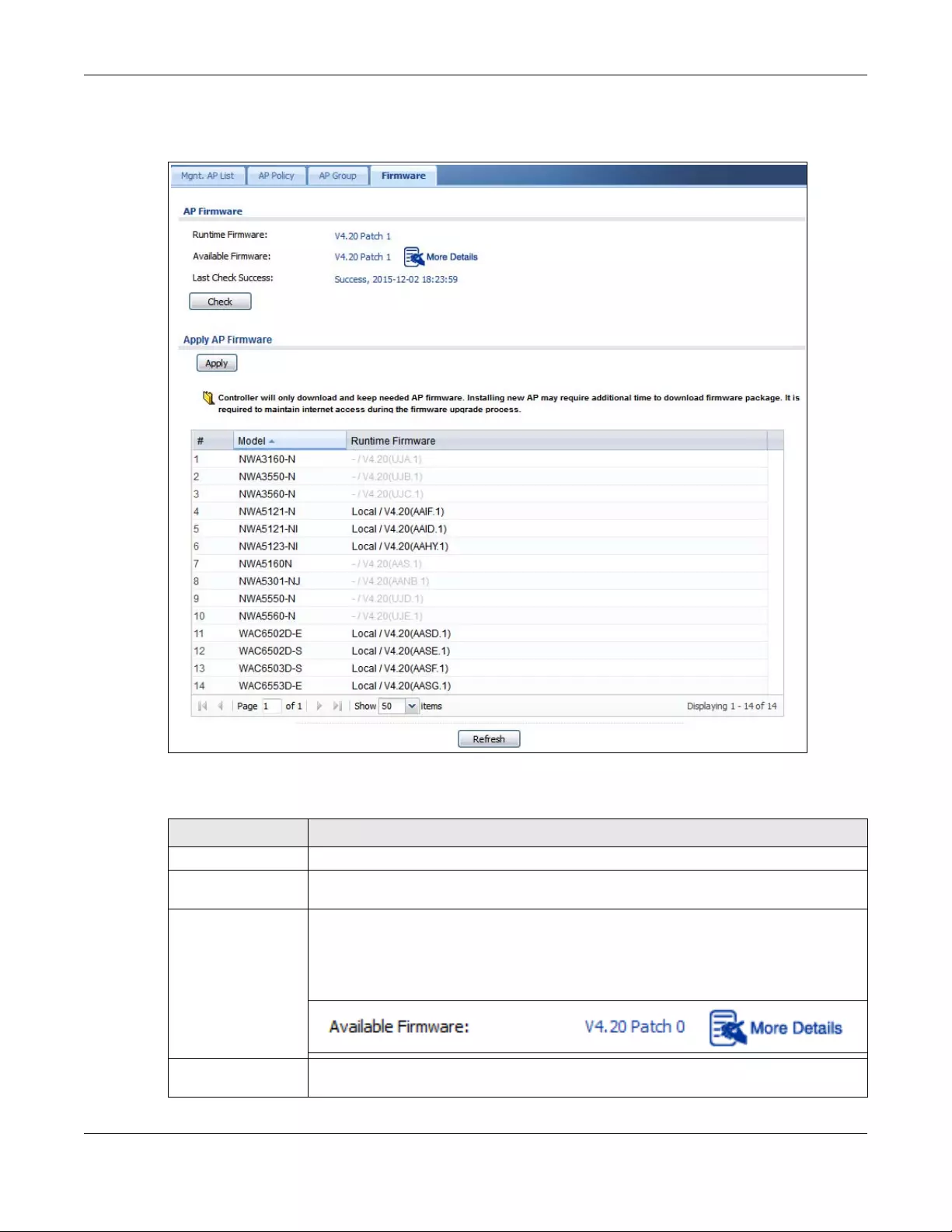
Chapter 9 Wireless
USG/ZyWALL User’s Guide
260
Click Configuration > Wireless > AP Management > Firmware to access this screen.
Figure 215 Configuration > Wireless > AP Management > Firmware
Each field is described in the following table.
Table 89 Configuration > Wireless > AP Management > Firmware
LABEL DESCRIPTION
AP Firmware
Runtime Firmware This displays the current AP firmware version on the Zyxel Device. The Zyxel Device must
have the latest AP firmware to manage all supported APs.
Available Firmware This field displays if there is a later AP firmware version available on the firmware server. It
displays N/A if the Zyxel Device cannot connect with the firmware server. Check that the
Zyxel Device has Internet access if N/A displays and then click the Check button below.
If a newer Zyxel Device AP firmware is available, its version number and a More Details icon
displays here.
Check Click this button to have the Zyxel Device display the latest AP firmware version available on
the firmware server.
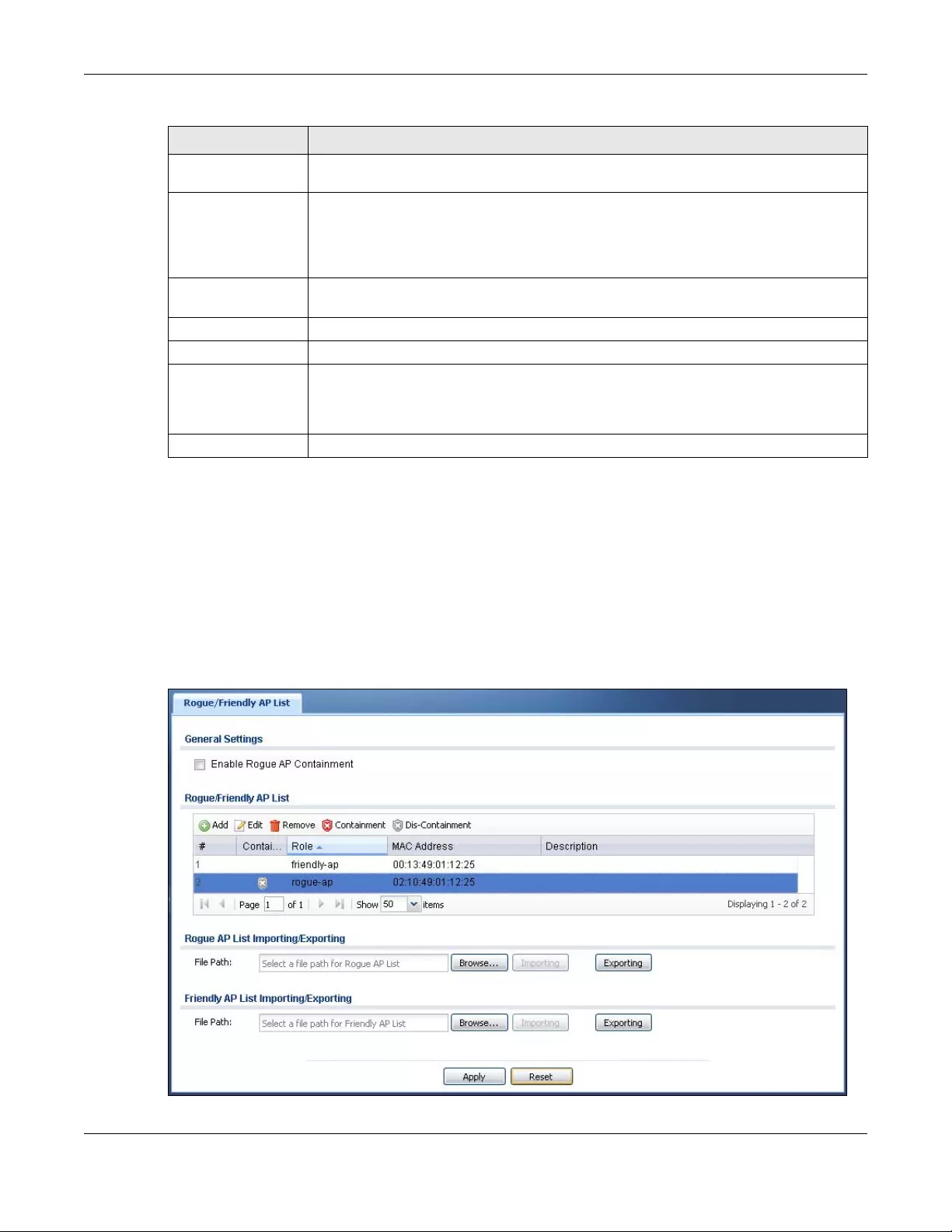
Chapter 9 Wireless
USG/ZyWALL User’s Guide
261
9.4 MON Mode
Use this screen to assign APs either to the rogue AP list or the friendly AP list. A rogue AP is a wireless
access point operating in a network’s coverage area that is not under the control of the network
administrator, and which can potentially open up holes in a network’s security.
Click Configuration > Wireless > MON Mode to access this screen.
Figure 216 Configuration > Wireless > MON Mode
Last Check Success This displays the date and time the last check for new firmware was made and whether the
check is in progress (checking), was successful (success), or has failed (fail).
Apply AP Firmware Due to space limitations, the Zyxel Device only downloads and keeps AP firmware for APs it
is currently managing. If you connect a new AP to the Zyxel Device, the Zyxel Device may
need to download a new AP firmware. Please wait while downloading new firmware as the
speed depends on your Internet connection speed. Make sure to maintain the Internet
connection while downloading new firmware.
Apply Click this to download newer Available Firmware from the firmware server and update the
Runtime Firmware version.
# This is an index number of a managed AP.
Model This displays the name of all manageable AP models.
Runtime Firmware This displays the firmware version that the managed AP must have in order to be managed
by the Zyxel Device. Firmware for APs that the Zyxel Device already has displays in bold;
firmware that the Zyxel Device doesn’t have or is still downloading is grayed out. Firmware
that is in the download queue will show To be downloaded.
Refresh Click this to update the model firmware table.
Table 89 Configuration > Wireless > AP Management > Firmware (continued)
LABEL DESCRIPTION
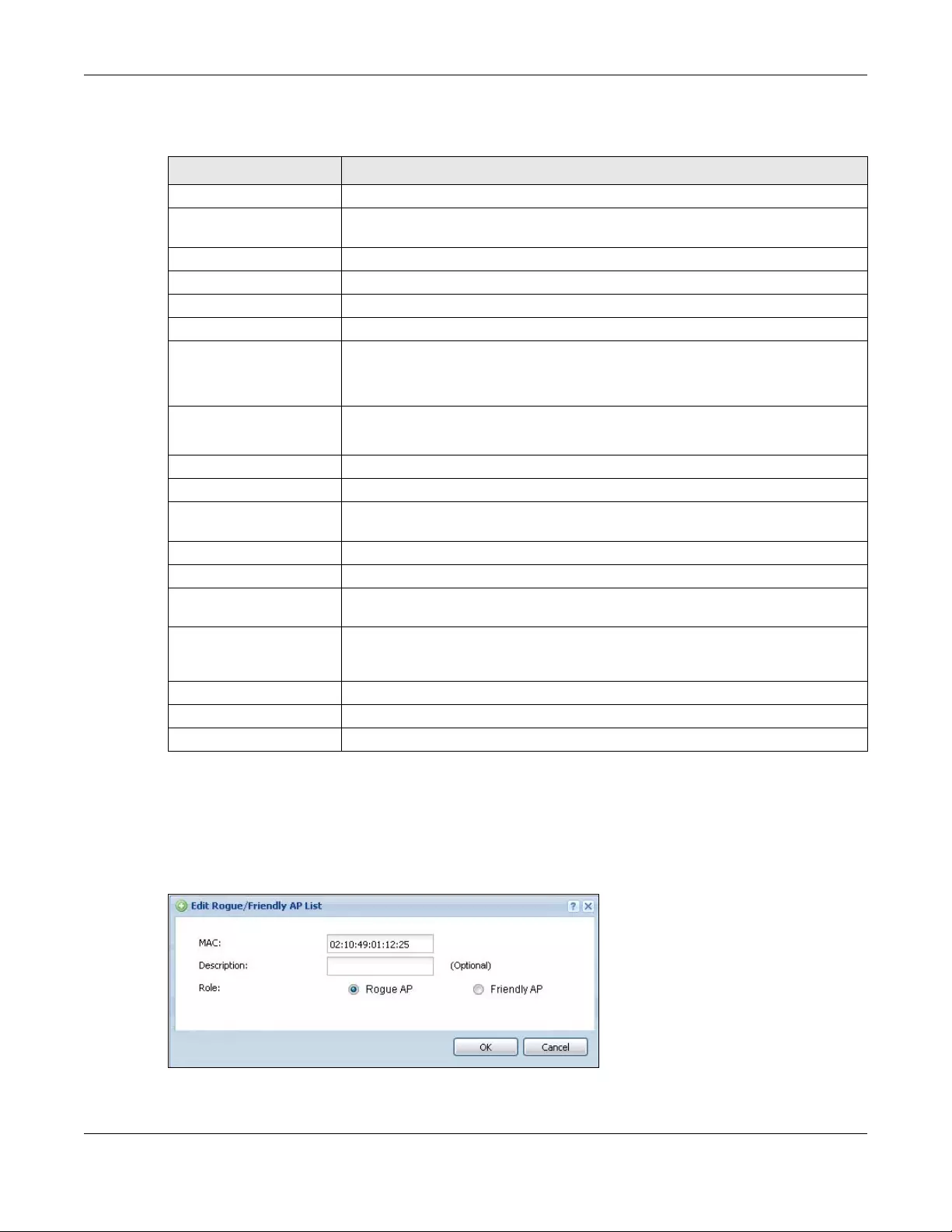
Chapter 9 Wireless
USG/ZyWALL User’s Guide
262
Each field is described in the following table.
9.4.1 Add/Edit Rogue /Friendly List
Select an AP and click the Edit button in the Configuration > Wireless > MON Mode table to display this
screen.
Figure 217 Configuration > Wireless > MON Mode > Add/Edit Rogue/Friendly
Table 90 Configuration > Wireless > MON Mode
LABEL DESCRIPTION
General Settings
Enable Rogue AP
Containment
Select this to enable rogue AP containment.
Rogue/Friendly AP List
Add Click this button to add an AP to the list and assign it either friendly or rogue status.
Edit Select an AP in the list to edit and reassign its status.
Remove Select an AP in the list to remove.
Containment Click this button to quarantine the selected AP.
A quarantined AP cannot grant access to any network services. Any stations that
attempt to connect to a quarantined AP are disconnected automatically.
Dis-Containment Click this button to take the selected AP out of quarantine.
An unquarantined AP has normal access to the network.
# This field is a sequential value, and it is not associated with any interface.
Containment This field indicates the selected AP’s containment status.
Role This field indicates whether the selected AP is a rogue-ap or a friendly-ap. To change
the AP’s role, click the Edit button.
MAC Address This field indicates the AP’s radio MAC address.
Description This field displays the AP’s description. You can modify this by clicking the Edit button.
Rogue/Friendly AP List
Importing/Exporting
These controls allow you to export the current list of rogue and friendly APs or import
existing lists.
File Path / Browse /
Importing Enter the file name and path of the list you want to import or click the Browse button
to locate it. Once the File Path field has been populated, click Importing to bring the
list into the Zyxel Device.
Exporting Click this button to export the current list of either rogue APs or friendly APS.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
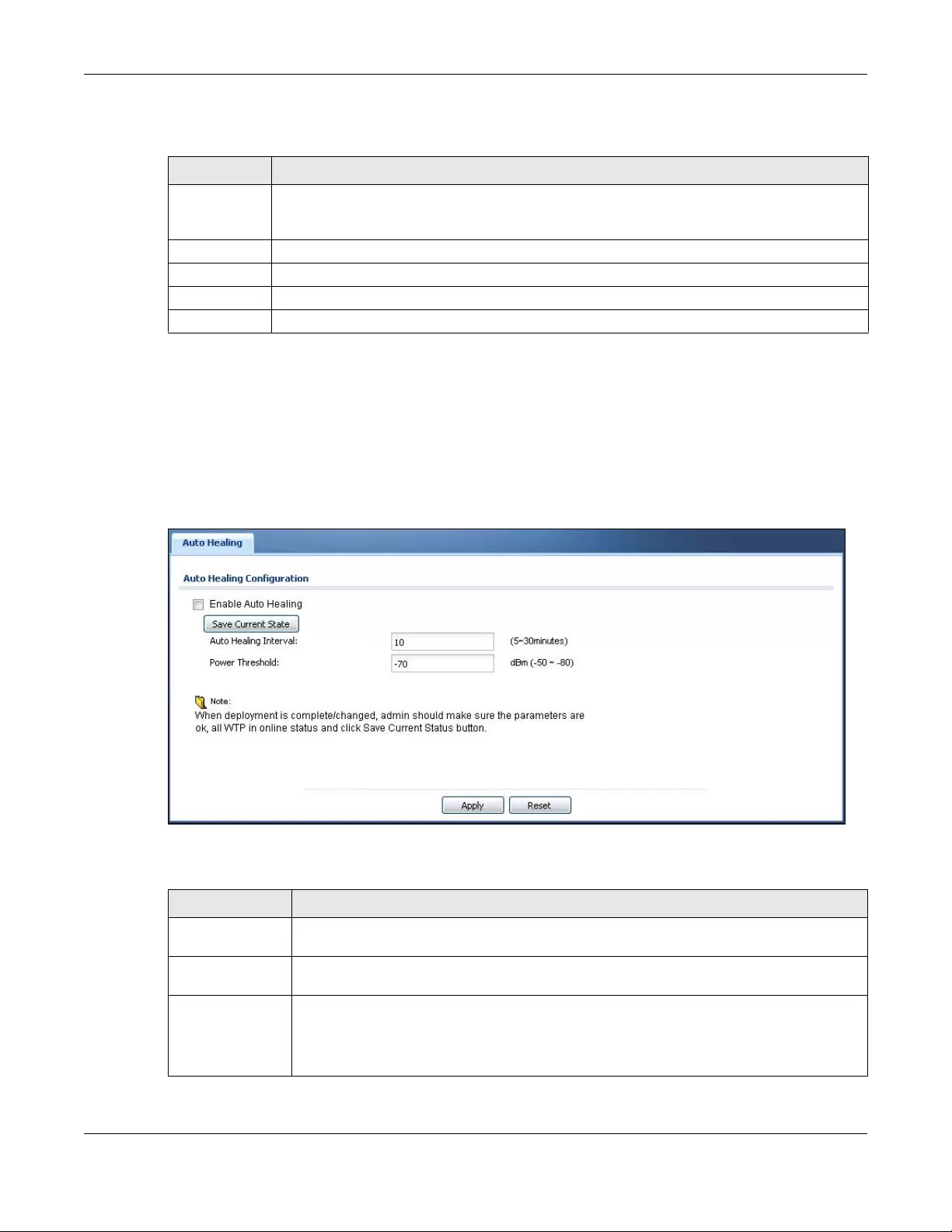
Chapter 9 Wireless
USG/ZyWALL User’s Guide
263
Each field is described in the following table.
9.5 Auto Healing
Use this screen to enable auto healing, which allows you to extend the wireless service coverage area
of the managed APs when one of the APs fails. Click Configuration > Wireless > Auto Healing to access
this screen.
Figure 218 Configuration > Wireless > Auto Healing
Each field is described in the following table.
Table 91 Configuration > Wireless > MON Mode > Add/Edit Rogue/Friendly
LABEL DESCRIPTION
MAC Enter the MAC address of the AP you want to add to the list. A MAC address is a unique hardware
identifier in the following hexadecimal format: xx:xx:xx:xx:xx:xx where xx is a hexadecimal number
separated by colons.
Description Enter up to 60 characters for the AP’s description. Spaces and underscores are allowed.
Role Select either Rogue AP or Friendly AP for the AP’s role.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to close the window with changes unsaved.
Table 92 Configuration > Wireless > Auto Healing
LABEL DESCRIPTION
Enable Auto
Healing
Select this option to turn on the auto healing feature.
Save Current
State
Click this button to have all manged APs immediately scan their neighborhoods three times in
a row and update their neighbor lists to the AP controller (Zyxel Device).
Auto Healing
Interval
Set the time interval (in minutes) at which the managed APs scan their neighborhoods and
report the status of neighbor APs to the AP controller (Zyxel Device).
An AP is considered “failed” if the AP controller obtains the same scan result that the AP is
missing from the neighbor list of other APs three times.
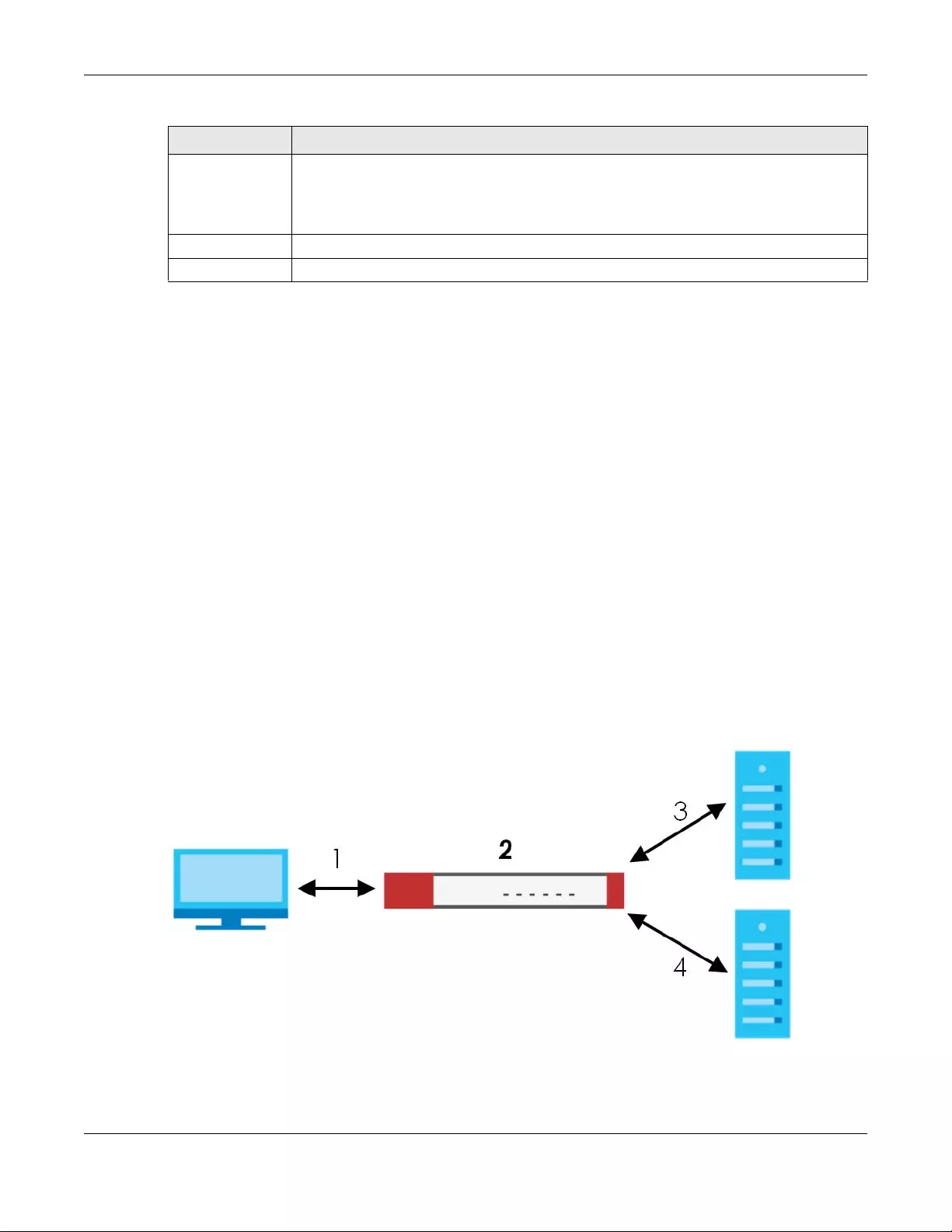
Chapter 9 Wireless
USG/ZyWALL User’s Guide
264
9.6 RTLS Overview
Ekahau RTLS (Real Time Location Service) tracks battery-powered Wi-Fi tags attached to APs managed
by the Zyxel Device to create maps, alerts, and reports.
The Ekahau RTLS Controller is the centerpiece of the RTLS system. This server software runs on a Windows
computer to track and locate Ekahau tags from Wi-Fi signal strength measurements. Use the Zyxel
Device with the Ekahau RTLS system to take signal strength measurements at the APs (Integrated
Approach / Blink Mode).
The following example shows the Ekahau RTLS Integrated Approach (Blink Mode).
1The Wi-Fi tag sends blink packets at specified intervals (or triggered by something like motion or button
presses).
2The APs pick up the blink packets, measure the signal strength, and send it to the Zyxel Device.
3The Zyxel Device forwards the signal measurements to the Ekahau RTLS Controller.
4The Ekahau RTLS Controller calculates the tag positions.
Figure 219 RTLS Example
Power Threshold Set the power level (in dBm) to which the neighbor APs of the failed AP increase their output
power in order to extend their wireless service coverage areas.
When the failed AP is working again, its neighbor APs return their output power to the original
level.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 92 Configuration > Wireless > Auto Healing (continued)
LABEL DESCRIPTION
Chapter 9 Wireless
USG/ZyWALL User’s Guide
265
9.6.1 What You Can Do in this Chapter
Use the RTLS screen (Section 9.6.3 on page 265) to use the managed APs as part of an Ekahau RTLS (Real
Time Location Service) to track the location of Ekahau Wi-Fi tags.
9.6.2 Before You Begin
You need:
• At least three APs managed by the Zyxel Device (the more APs the better since it increases the
amount of information the Ekahau RTLS Controller has for calculating the location of the tags)
• IP addresses for the Ekahau Wi-Fi tags
• A dedicated RTLS SSID is recommended
• Ekahau RTLS Controller in blink mode with TZSP Updater enabled
• Security policies to allow RTLS traffic if the Zyxel Device security policy control is enabled or the Ekahau
RTLS Controller is behind a firewall.
For example, if the Ekahau RTLS Controller is behind a firewall, open ports 8550, 8553, and 8569 to allow
traffic the APs send to reach the Ekahau RTLS Controller.
The following table lists default port numbers and types of packets RTLS uses.
9.6.3 Configuring RTLS
Click Configura tion > Wireless > RTLS to open this screen. Use this screen to turn RTLS (Real Time Location
System) on or off and specify the IP address and server port of the Ekahau RTLS Controller.
Table 93 RTLS Traffic Port Numbers
PORT NUMBER TYPE DESCRIPTION
8548 TCP Ekahau T201 location update.
8549 UDP Ekahau T201 location update.
8550 TCP Ekahau T201 tag maintenance protocol and Ekahau RTLS Controller user interface.
8552 UDP Ekahau Location Protocol
8553 UDP Ekahau Maintenance Protocol
8554 UDP Ekahau T301 firmware update.
8560 TCP Ekahau Vision web interface
8562 UDP Ekahau T301W firmware update.
8569 UDP Ekahau TZSP Listener Port
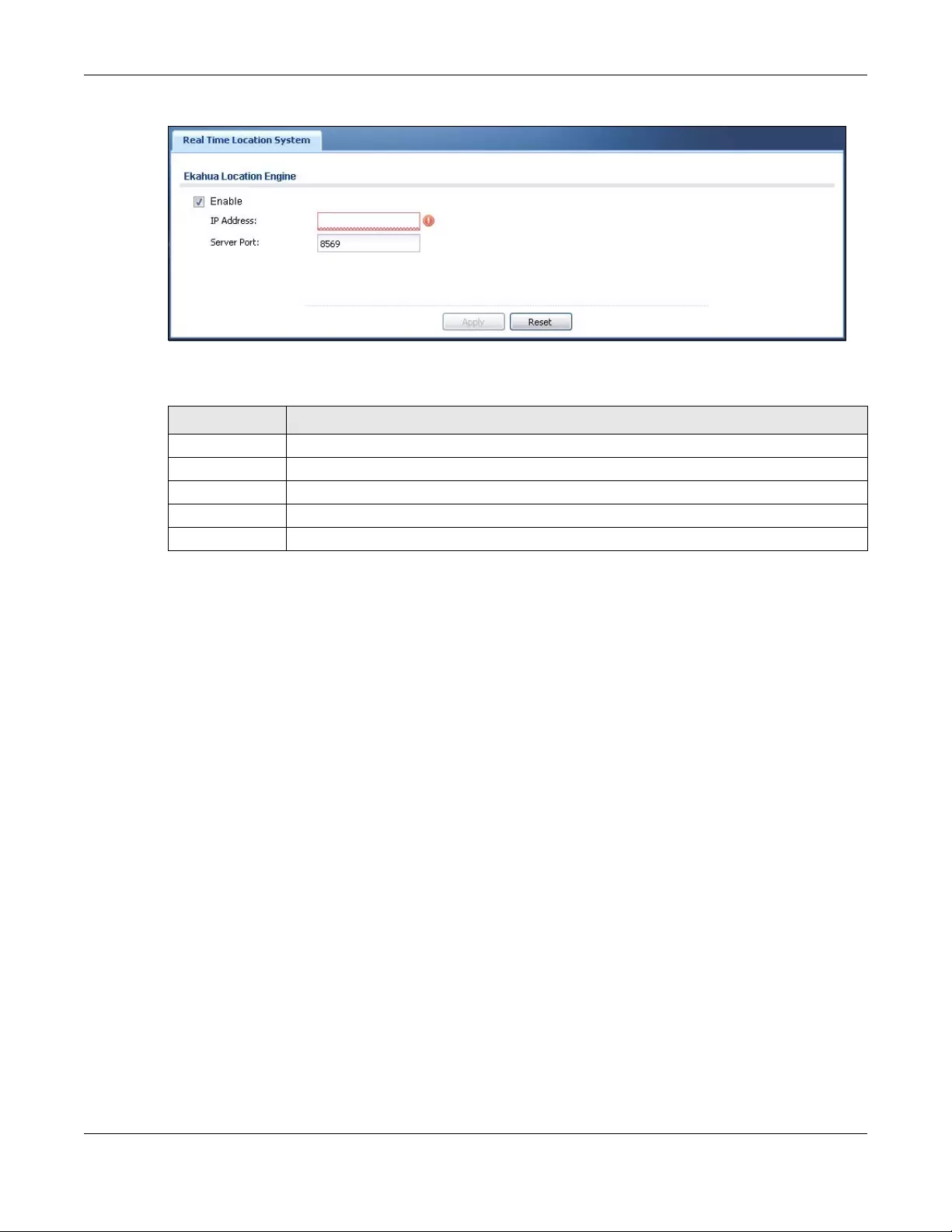
Chapter 9 Wireless
USG/ZyWALL User’s Guide
266
Figure 220 Configuration > Wireless > RTLS
The following table describes the labels in this screen.
9.7 Technical Reference
The following section contains additional technical information about wireless features.
9.7.1 Dynamic Channel Selection
When numerous APs broadcast within a given area, they introduce the possibility of heightened radio
interference, especially if some or all of them are broadcasting on the same radio channel. If the
interference becomes too great, then the network administrator must open his AP configuration options
and manually change the channel to one that no other AP is using (or at least a channel that has a
lower level of interference) in order to give the connected stations a minimum degree of interference.
Dynamic channel selection frees the network administrator from this task by letting the AP do it
automatically. The AP can scan the area around it looking for the channel with the least amount of
interference.
In the 2.4 GHz spectrum, each channel from 1 to 13 is broken up into discrete 22 MHz segments that are
spaced 5 MHz apart. Channel 1 is centered on 2.412 GHz while channel 13 is centered on 2.472 GHz.
Table 94 Configuration > Wireless > RTLS
LABEL DESCRIPTION
Enable Select this to use Wi-Fi to track the location of Ekahau Wi-Fi tags.
IP Address Specify the IP address of the Ekahau RTLS Controller.
Server Port Specify the server port number of the Ekahau RTLS Controller.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
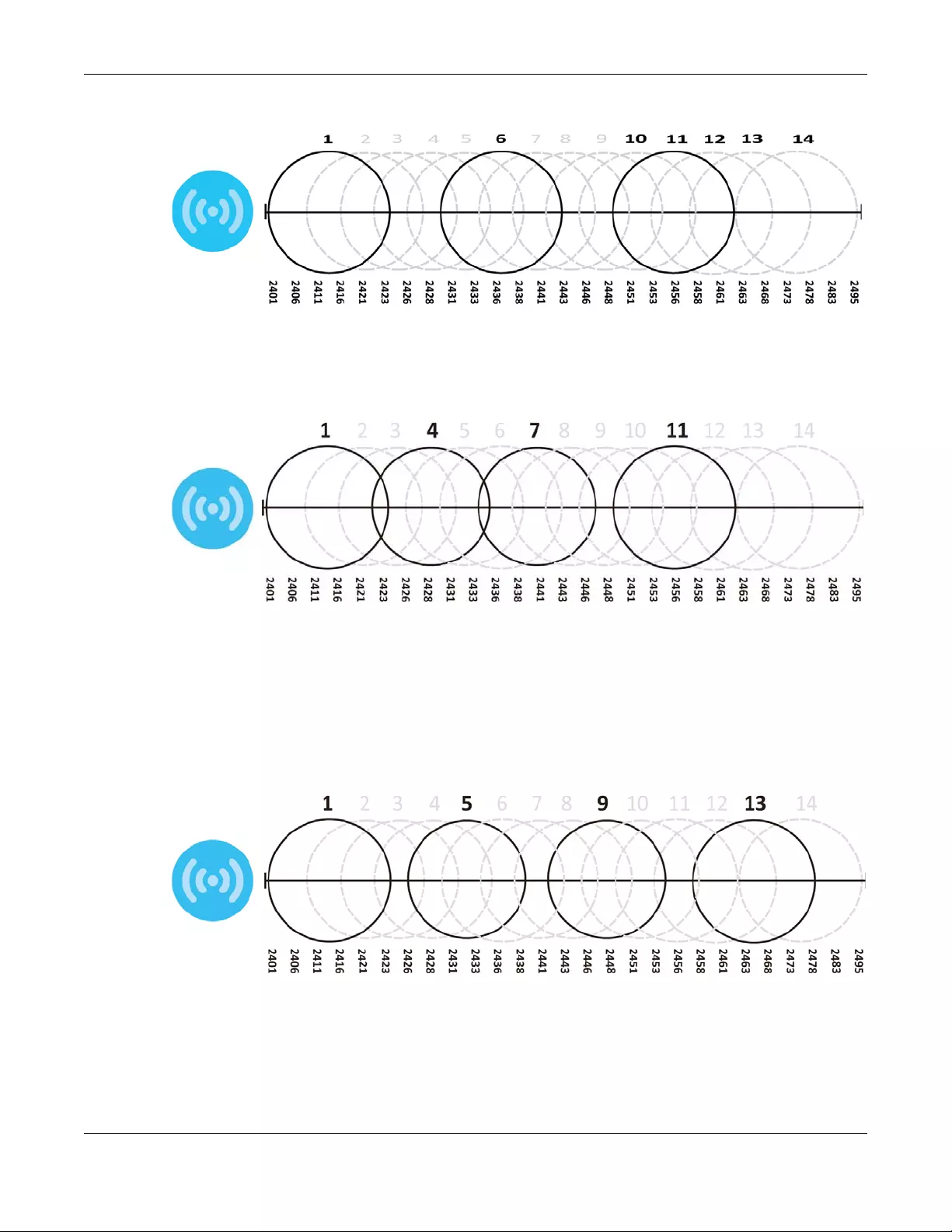
Chapter 9 Wireless
USG/ZyWALL User’s Guide
267
Figure 221 An Example Three-Channel Deployment
Three channels are situated in such a way as to create almost no interference with one another if used
exclusively: 1, 6 and 11. When an AP broadcasts on any of these three channels, it should not interfere
with neighboring APs as long as they are also limited to same trio.
Figure 222 An Example Four-Channel Deployment
However, some regions require the use of other channels and often use a safety scheme with the
following four channels: 1, 4, 7 and 11. While they are situated sufficiently close to both each other and
the three so-called “safe” channels (1,6 and 11) that interference becomes inevitable, the severity of it is
dependent upon other factors: proximity to the affected AP, signal strength, activity, and so on.
Finally, there is an alternative four channel scheme for ETSI, consisting of channels 1, 5, 9, 13. This offers
significantly less overlap that the other one.
Figure 223 An Alternative Four-Channel Deployment
9.7.2 Load Balancing
Because there is a hard upper limit on an AP’s wireless bandwidth, load balancing can be crucial in
areas crowded with wireless users. Rather than let every user connect and subsequently dilute the

Chapter 9 Wireless
USG/ZyWALL User’s Guide
268
available bandwidth to the point where each connecting device receives a meager trickle, the load
balanced AP instead limits the incoming connections as a means to maintain bandwidth integrity.
There are two kinds of wireless load balancing available on the Zyxel Device:
Load balancing by station number limits the number of devices allowed to connect to your AP. If you
know exactly how many stations you want to let connect, choose this option.
For example, if your company’s graphic design team has their own AP and they have 10 computers,
you can load balance for 10. Later, if someone from the sales department visits the graphic design
team’s offices for a meeting and he tries to access the network, his computer’s connection is delayed,
giving it the opportunity to connect to a different, neighboring AP. If he still connects to the AP
regardless of the delay, then the AP may boot other people who are already connected in order to
associate with the new connection.
Load balancing by traffic level limits the number of connections to the AP based on maximum
bandwidth available. If you are uncertain as to the exact number of wireless connections you will have
then choose this option. By setting a maximum bandwidth cap, you allow any number of devices to
connect as long as their total bandwidth usage does not exceed the configured bandwidth cap
associated with this setting. Once the cap is hit, any new connections are rejected or delayed provided
that there are other APs in range.
Imagine a coffee shop in a crowded business district that offers free wireless connectivity to its
customers. The coffee shop owner can’t possibly know how many connections his AP will have at any
given moment. As such, he decides to put a limit on the bandwidth that is available to his customers but
not on the actual number of connections he allows. This means anyone can connect to his wireless
network as long as the AP has the bandwidth to spare. If too many people connect and the AP hits its
bandwidth cap then all new connections must basically wait for their turn or get shunted to the nearest
identical AP.

USG/ZyWALL User’s Guide
269
CHAPTER 10
Interfaces
10.1 Interface Overview
Use the Interface screens to configure the Zyxel Device’s interfaces. You can also create interfaces on
top of other interfaces.
•Ports are the physical ports to which you connect cables.
•Interfaces are used within the system operationally. You use them in configuring various features. An
interface also describes a network that is directly connected to the Zyxel Device. For example, You
connect the LAN network to the LAN interface.
•Zones are groups of interfaces used to ease security policy configuration.
10.1.1 What You Can Do in this Chapter
• Use the Port Role screen (Section 10.2 on page 274) to create port groups and to assign physical ports
and port groups to Ethernet interfaces.
• Use the Ethernet screens (Section 10.4 on page 276) to configure the Ethernet interfaces. Ethernet
interfaces are the foundation for defining other interfaces and network policies. RIP and OSPF are also
configured in these interfaces.
• Use the Virtual Interface screen (Section 10.4.2 on page 293) to create virtual interfaces on top of
Ethernet interfaces to tell the Zyxel Device where to route packets. You can create virtual Ethernet
interfaces, virtual VLAN interfaces, and virtual bridge interfaces.
• Use the PPP screens (Section 10.5 on page 297) for PPPoE, PPTP or L2TP Internet connections.
• Use the Cellular screens (Section 10.6 on page 304) to configure settings for interfaces for Internet
connections through an installed mobile broadband card.
• Use the Tunnel screens (Section 10.7 on page 313) to configure tunnel interfaces to be used in
Generic Routing Encapsulation (GRE), IPv6 in IPv4, and 6to4 tunnels.
• Use the VLAN screens (Section 10.8 on page 319) to divide the physical network into multiple logical
networks. VLAN interfaces receive and send tagged frames. The Zyxel Device automatically adds or
removes the tags as needed. Each VLAN can only be associated with one Ethernet interface.
• Use the Bridge screens (Section 10.9 on page 333) to combine two or more network segments into a
single network.
• Use the LAG screens (Section 10.10 on page 344) to combine multiple physical Ethernet interfaces
into a single logical interface.
• Use the VTI screens (Section 10.11 on page 352) to encrypt or decrypt IPv4 traffic from or to the
interface according to the IP routing table.
• Use the Trunk screens (Section 10.12 on page 355) to configure load balancing.
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
270
10.1.2 What You Need to Know
Interface Characteristics
Interfaces generally have the following characteristics (although not all characteristics apply to each
type of interface).
• An interface is a logical entity through which (layer-3) packets pass.
• An interface is bound to a physical port or another interface.
• Many interfaces can share the same physical port.
• An interface belongs to at most one zone.
• Many interfaces can belong to the same zone.
• Layer-3 virtualization (IP alias, for example) is a kind of interface.
Types of Interfaces
You can create several types of interfaces in the Zyxel Device.
• Setting interfaces to the same port role forms a port group. Port groups creates a hardware
connection between physical ports at the layer-2 (data link, MAC address) level. Port groups are
created when you use the Interface > Port Roles or Interface > Port Groups screen to set multiple
physical ports to be part of the same interface.
•Ethernet interfaces are the foundation for defining other interfaces and network policies. RIP and
OSPF are also configured in these interfaces.
•Tunnel interfaces send IPv4 or IPv6 packets from one network to a specific network through the
Internet or a public network.
•VLAN interfaces receive and send tagged frames. The Zyxel Device automatically adds or removes
the tags as needed. Each VLAN can only be associated with one Ethernet interface.
•Bridge interfaces create a software connection between Ethernet or VLAN interfaces at the layer-2
(data link, MAC address) level. Unlike port groups, bridge interfaces can take advantage of some
security features in the Zyxel Device. You can also assign an IP address and subnet mask to the
bridge.
•PPP interfaces support Point-to-Point Protocols (PPP). ISP accounts are required for PPPoE/PPTP/L2TP
interfaces.
•Cellular interfaces are for mobile broadband WAN connections via a connected mobile broadband
device.
•Virtual interfaces provide additional routing information in the Zyxel Device. There are three types:
virtual Ethernet interfaces, virtual VLAN interfaces, and virtual bridge interfaces.
•Trunk interfaces manage load balancing between interfaces.
Port groups and trunks have a lot of characteristics that are specific to each type of interface. The other
types of interfaces--Ethernet, PPP, cellular, VLAN, bridge, and virtual--have a lot of similar characteristics.
These characteristics are listed in the following table and discussed in more detail below.
Table 95 Ethernet, PPP, Cellular, VLAN, Bridge, and Virtual Interface Characteristics
CHARACTERISTICS ETHERNET ETHERNET PPP CELLULAR VLAN BRIDGE VIRTUAL
Name* wan1, wan2 lan1, lan2,
dmz
pppxcellularx vlanxbrx**
Configurable Zone No No Yes Yes Yes Yes No
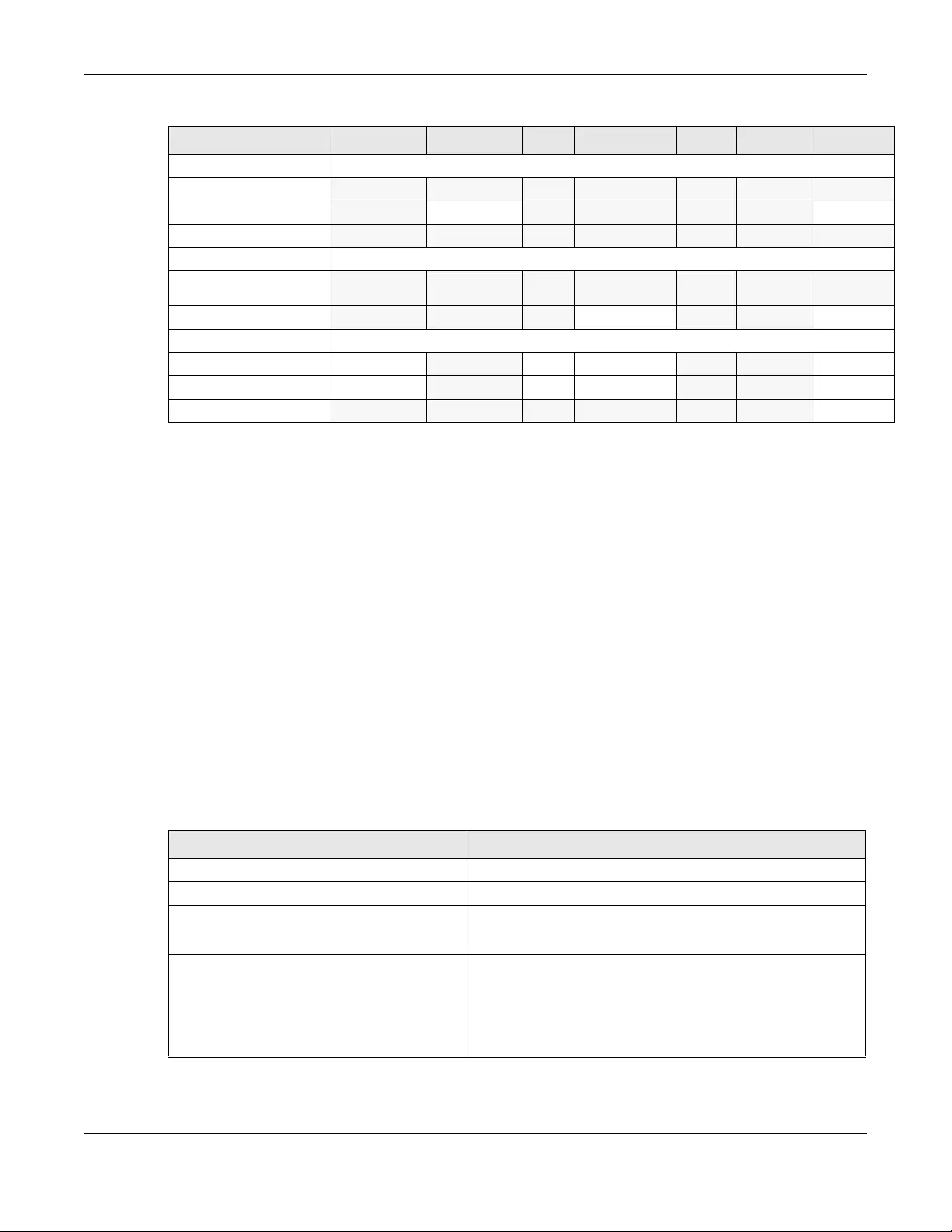
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
271
Note: - * The format of interface names other than the Ethernet and ppp interface names is
strict. Each name consists of 2-4 letters (interface type), followed by a number (x). For
most interfaces, x is limited by the maximum number of the type of interface. For VLAN
interfaces, x is defined by the number you enter in the VLAN name field. For example,
Ethernet interface names are wan1, wan2, lan1, lan2, dmz; VLAN interfaces are vlan0,
vlan1, vlan2,...; and so on.
** - The names of virtual interfaces are derived from the interfaces on which they are
created. For example, virtual interfaces created on Ethernet interface wan1 are called
wan1:1, wan1:2, and so on. Virtual interfaces created on VLAN interface vlan2 are
called vlan2:1, vlan2:2, and so on. You cannot specify the number after the colon(:) in
the Web Configurator; it is a sequential number. You can specify the number after the
colon if you use the CLI to set up a virtual interface.
Relationships Between Interfaces
In the Zyxel Device, interfaces are usually created on top of other interfaces. Only Ethernet interfaces
are created directly on top of the physical ports or port groups. The relationships between interfaces are
explained in the following table.
IP Address Assignment
Static IP address Yes Yes Yes Yes Yes Yes Yes
DHCP client Yes No Yes Yes Yes Yes No
Routing metric Yes Yes Yes Yes Yes Yes Yes
Interface Parameters
Bandwidth
restrictions Yes Yes Yes Yes Yes Yes Yes
Packet size (MTU) Yes Yes Yes Yes Yes Yes No
DHCP
DHCP server No Yes No No Yes Yes No
DHCP relay No Yes No No Yes Yes No
Connectivity Check Yes No Yes Yes Yes Yes No
Table 96 Relationships Between Different Types of Interfaces
INTERFACE REQUIRED PORT / INTERFACE
Ethernet interface physical port
VLAN interface Ethernet interface
bridge interface Ethernet interface*
VLAN interface*
PPP interface Ethernet interface*
VLAN interface*
bridge interface
WAN1, WAN2, OPT*
Table 95 Ethernet, PPP, Cellular, VLAN, Bridge, and Virtual Interface Characteristics (continued)
CHARACTERISTICS ETHERNET ETHERNET PPP CELLULAR VLAN BRIDGE VIRTUAL
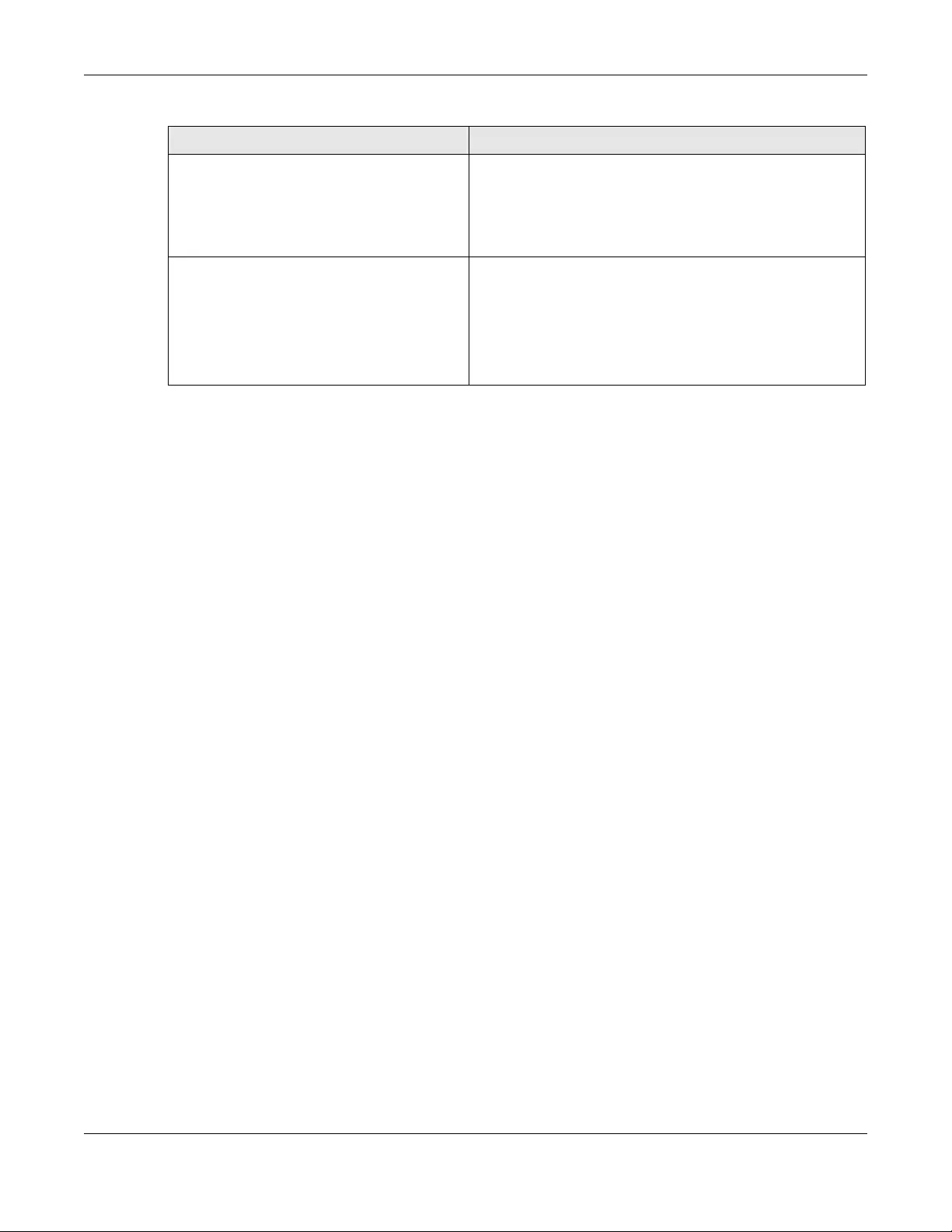
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
272
Note: * You cannot set up a PPP interface, virtual Ethernet interface or virtual VLAN interface
if the underlying interface is a member of a bridge. You also cannot add an Ethernet
interface or VLAN interface to a bridge if the member interface has a virtual interface
or PPP interface on top of it.
IPv6 Overview
IPv6 (Internet Protocol version 6), is designed to enhance IP address size and features. The increase in
IPv6 address size to 128 bits (from the 32-bit IPv4 address) allows up to 3.4 x 1038 IP addresses.
IPv6 Addressing
An 128-bit IPv6 address is written as eight 16-bit hexadecimal blocks separated by colons (:). This is an
example IPv6 address 2001:0db8:1a2b:0015:0000:0000:1a2f:0000.
IPv6 addresses can be abbreviated in two ways:
• Leading zeros in a block can be omitted. So 2001:0db8:1a2b:0015:0000:0000:1a2f:0000 can be
written as 2001:db8:1a2b:15:0:0:1a2f:0.
• Any number of consecutive blocks of zeros can be replaced by a double colon. A double colon can
only appear once in an IPv6 address. So 2001:0db8:0000:0000:1a2f:0000:0000:0015 can be
written as 2001:0db8::1a2f:0000:0000:0015, 2001:0db8:0000:0000:1a2f::0015,
2001:db8::1a2f:0:0:15 or 2001:db8:0:0:1a2f::15.
Prefix and Prefix Length
Similar to an IPv4 subnet mask, IPv6 uses an address prefix to represent the network address. An IPv6
prefix length specifies how many most significant bits (start from the left) in the address compose the
network address. The prefix length is written as “/x” where x is a number. For example,
2001:db8:1a2b:15::1a2f:0/32
means that the first 32 bits (2001:db8) from the left is the network prefix.
virtual interface
(virtual Ethernet interface)
(virtual VLAN interface)
(virtual bridge interface)
Ethernet interface*
VLAN interface*
bridge interface
trunk Ethernet interface
Cellular interface
VLAN interface
bridge interface
PPP interface
Table 96 Relationships Between Different Types of Interfaces (continued)
INTERFACE REQUIRED PORT / INTERFACE

Chapter 10 Interfaces
USG/ZyWALL User’s Guide
273
Link-local Address
A link-local address uniquely identifies a device on the local network (the LAN). It is similar to a “private IP
address” in IPv4. You can have the same link-local address on multiple interfaces on a device. A link-
local unicast address has a predefined prefix of fe80::/10. The link-local unicast address format is as
follows.
Subnet Masking
Both an IPv6 address and IPv6 subnet mask compose of 128-bit binary digits, which are divided into
eight 16-bit blocks and written in hexadecimal notation. Hexadecimal uses four bits for each character
(1 ~ 10, A ~ F). Each block’s 16 bits are then represented by four hexadecimal characters. For example,
FFFF:FFFF:FFFF:FFFF:FC00:0000:0000:0000.
Stateless Autoconfiguration
With stateless autoconfiguration in IPv6, addresses can be uniquely and automatically generated.
Unlike DHCPv6 (Dynamic Host Configuration Protocol version six) which is used in IPv6 stateful
autoconfiguration, the owner and status of addresses don’t need to be maintained by a DHCP server.
Every IPv6 device is able to generate its own and unique IP address automatically when IPv6 is initiated
on its interface. It combines the prefix and the interface ID (generated from its own Ethernet MAC
address) to form a complete IPv6 address.
When IPv6 is enabled on a device, its interface automatically generates a link-local address (beginning
with fe80).
When the Zyxel Device’s WAN interface is connected to an ISP with a router and the Zyxel Device is set
to automatically obtain an IPv6 network prefix from the router for the interface, it generates another
address which combines its interface ID and global and subnet information advertised from the router.
(In IPv6, all network interfaces can be associated with several addresses.) This is a routable global IP
address.
Prefix Delegation
Prefix delegation enables an IPv6 router (the Zyxel Device) to use the IPv6 prefix (network address)
received from the ISP (or a connected uplink router) for its LAN. The Zyxel Device uses the received IPv6
prefix (for example, 2001:db2::/48) to generate its LAN IP address. Through sending Router
Advertisements (RAs) regularly by multicast, the router passes the IPv6 prefix information to its LAN hosts.
The hosts then can use the prefix to generate their IPv6 addresses.
IPv6 Router Advertisement
An IPv6 router sends router advertisement messages periodically to advertise its presence and other
parameters to the hosts in the same network.
Table 97 Link-local Unicast Address Format
1111 1110 10 0 Interface ID
10 bits 54 bits 64 bits
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
274
DHCPv6
The Dynamic Host Configuration Protocol for IPv6 (DHCPv6, RFC 3315) is a server-client protocol that
allows a DHCP server to assign and pass IPv6 network addresses, prefixes and other configuration
information to DHCP clients. DHCPv6 servers and clients exchange DHCP messages using UDP.
Each DHCP client and server has a unique DHCP Unique IDentifier (DUID), which is used for identification
when they are exchanging DHCPv6 messages. The DUID is generated from the MAC address, time,
vendor assigned ID and/or the vendor's private enterprise number registered with the IANA. It should not
change over time even after you reboot the device.
10.1.3 What You Need to Do First
For IPv6 settings, go to the Configuration > System > IPv6 screen to enable IPv6 support on the Zyxel
Device first.
10.2 Port Role
To access this screen, click Configuration > Network > Interface > Port Role. Use the Port Role screen to
set the Zyxel Device’s flexible ports as part of the lan1, lan2, ext-wlan, ext-lan or dmz interfaces. This
creates a hardware connection between the physical ports at the layer-2 (data link, MAC address)
level. This provides wire-speed throughput but no security.
The following table shows the models that support port role at the time of writing.
Note the following if you are configuring from a computer connected to a lan1, lan2, ext-wlan, ext-lan
or dmz port and change the port's role:
• A port's IP address varies as its role changes, make sure your computer's IP address is in the same
subnet as the Zyxel Device's lan1, lan2, ext-wlan, ext-lan or dmz IP address.
• Use the appropriate lan1, lan2, ext-wlan, ext-lan or dmz IP address to access the Zyxel Device.
Table 98 Models with Port Role
MODEL WITH PORT ROLE MODEL WITH PORT ROLE
ZyWALL 110 USG60W
USG40 USG110
USG40W USG210
USG60
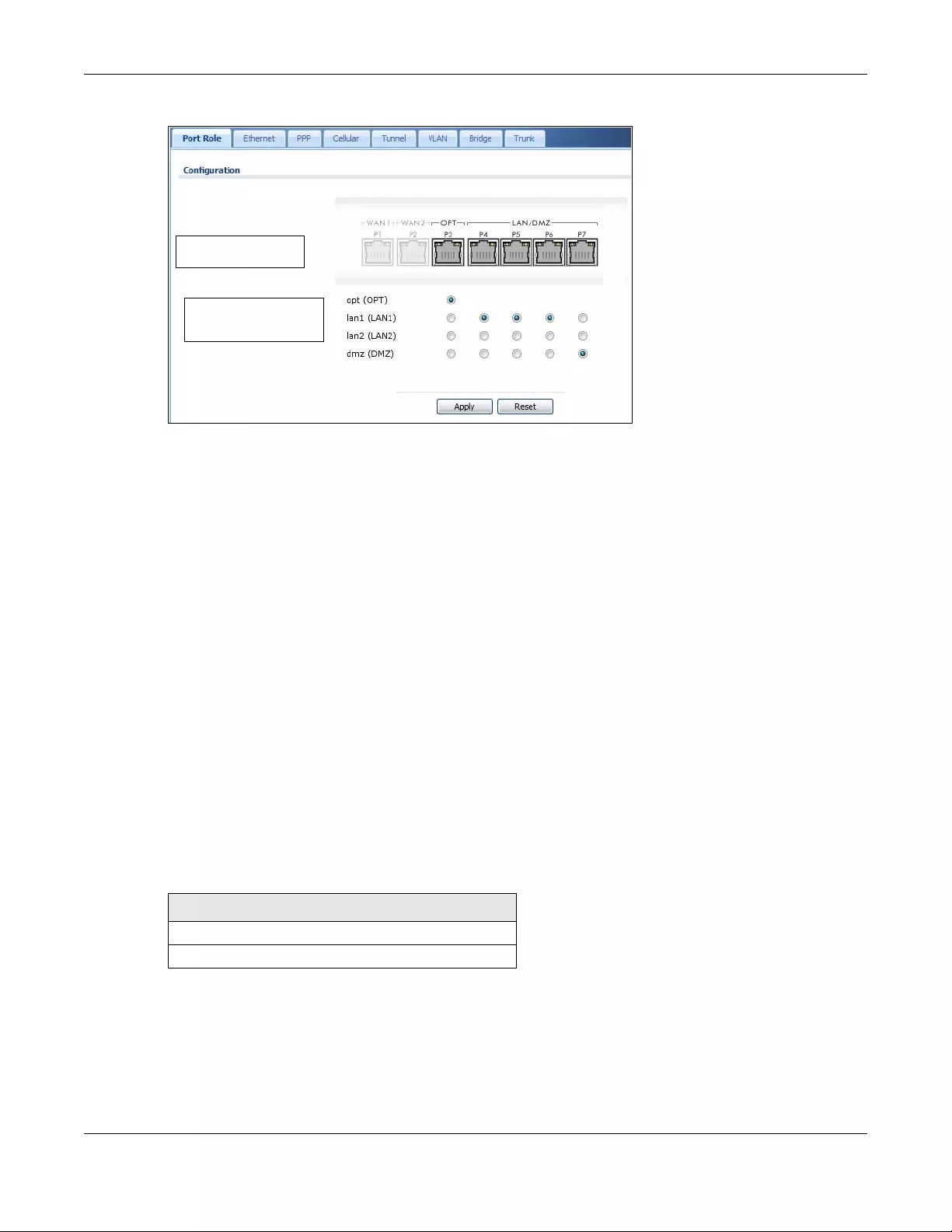
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
275
Figure 224 Configuration > Network > Interface > Port Role
The physical Ethernet ports are shown at the top and the Ethernet interfaces and zones are shown at the
bottom of the screen. Use the radio buttons to select for which interface (network) you want to use
each physical port. For example, select a port’s LAN radio button to use the port as part of the LAN
interface. The port will use the Zyxel Device’s LAN IP address and MAC address.
When you assign more than one physical port to a network, you create a port group. Port groups have
the following characteristics:
• There is a layer-2 Ethernet switch between physical ports in the port group. This provides wire-speed
throughput but no security.
• It can increase the bandwidth between the port group and other interfaces.
• The port group uses a single MAC address.
Click Apply to save your changes and apply them to the Zyxel Device.
Click Reset to change the port groups to their current configuration (last-saved values).
10.3 Port Group
The following table shows the models that support port group at the time of writing.
Physical Ports
Default
interface (ZONE)
Table 99 Models with Port Group
MODELS WITH PORT GROUP
USG2200-VPN
VPN3000
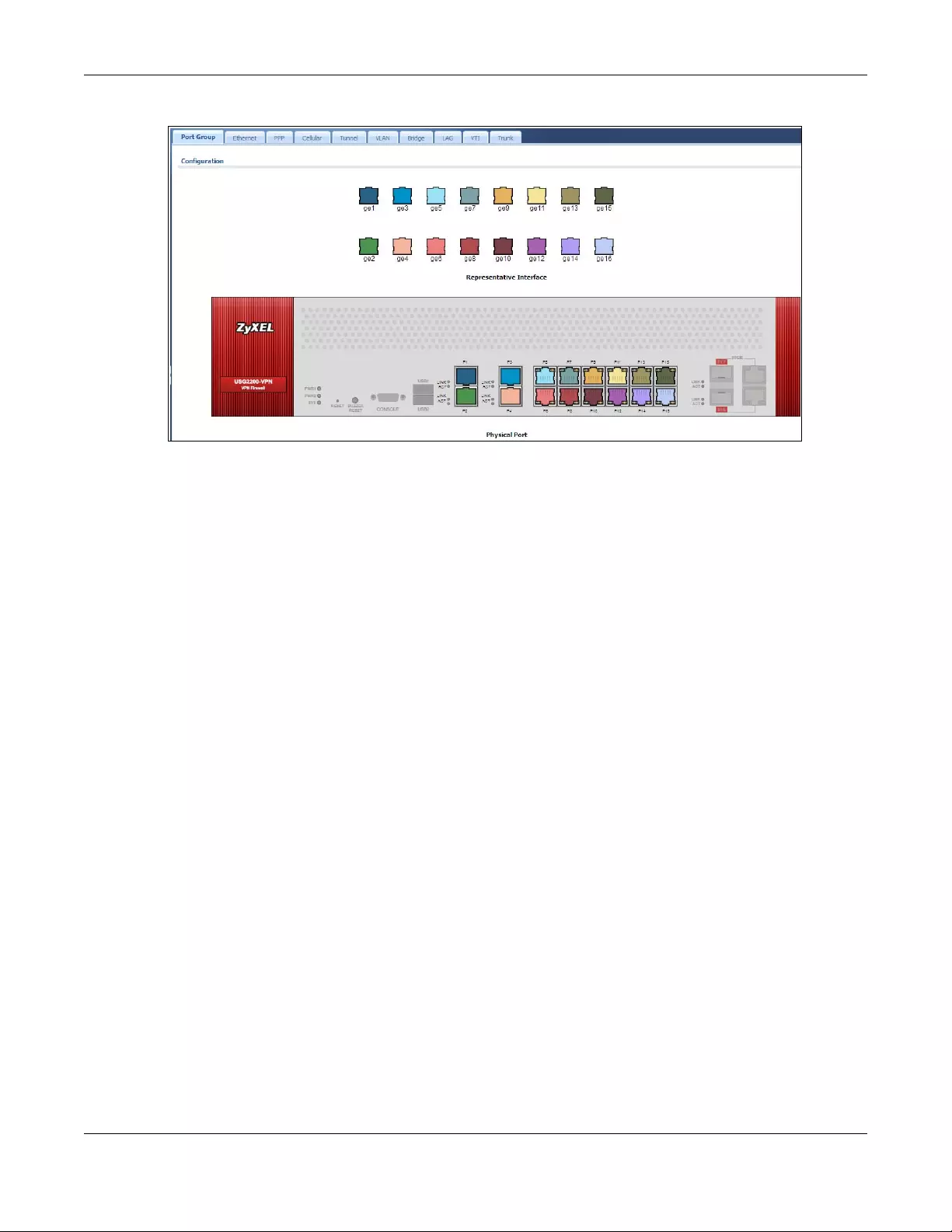
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
276
Figure 225 Configuration > Network > Interface > Port Group (USG2200-VPN / VPN3000)
The representative interfaces are shown at the top of the screen and the physical ports are shown at the
bottom. You can set port grouping for ports 1~16. Ports 1~4 are 1G fiber ports and ports 5~16 are 1G
Ethernet ports. Select a physical port using the mouse, hold, and drag it to a representative interface.
Dragging ports (one-by-one) to the same representative interface creates a port group.
Port groups have the following characteristics:
• There is a layer-2 Ethernet switch between physical ports in the port group. This provides wire-speed
throughput but no security.
• It can increase the bandwidth between the port group and other interfaces.
• The port group uses a single MAC address.
10.4 Ethernet Summary Screen
This screen lists every Ethernet interface and virtual interface created on top of Ethernet interfaces. If you
enabled IPv6 in the Configuration > System > IPv6 screen, you can also configure Ethernet interfaces
used for your IPv6 networks on this screen. To access this screen, click Configuration > Network >
Interface > Ethernet.
Unlike other types of interfaces, you cannot create new Ethernet interfaces nor can you delete any of
them. If an Ethernet interface does not have any physical ports assigned to it, the Ethernet interface is
effectively removed from the Zyxel Device, but you can still configure it.
Ethernet interfaces are similar to other types of interfaces in many ways. They have an IP address, subnet
mask, and gateway used to make routing decisions. They restrict the amount of bandwidth and packet
size. They can provide DHCP services, and they can verify the gateway is available.
Use Ethernet interfaces to control which physical ports exchange routing information with other routers
and how much information is exchanged through each one. The more routing information is
exchanged, the more efficient the routers should be. However, the routers also generate more network
traffic, and some routing protocols require a significant amount of configuration and management. The
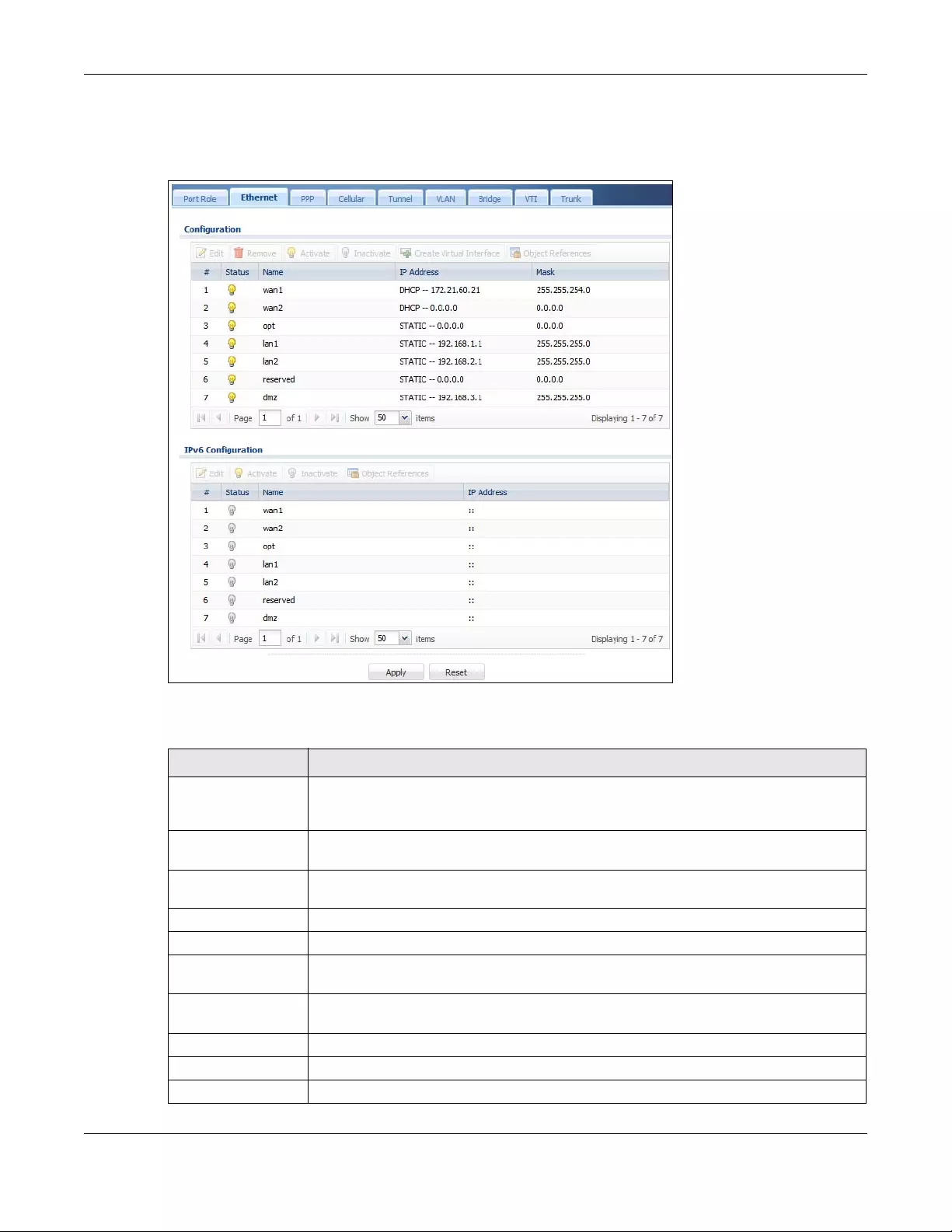
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
277
Zyxel Device supports two routing protocols, RIP and OSPF. See Chapter 11 on page 378 for background
information about these routing protocols.
Figure 226 Configuration > Network > Interface > Ethernet
Each field is described in the following table.
Table 100 Configuration > Network > Interface > Ethernet
LABEL DESCRIPTION
Configuration / IPv6
Configuration
Use the Configuration section for IPv4 network settings. Use the IPv6 Configuration section
for IPv6 network settings if you connect your Zyxel Device to an IPv6 network. Both sections
have similar fields as described below.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove a virtual interface, select it and click Remove. The Zyxel Device confirms you
want to remove it before doing so.
Activate To turn on an interface, select it and click Activate.
Inactivate To turn off an interface, select it and click Inactivate.
Create Virtual
Interface
To open the screen where you can create a virtual Ethernet interface, select an Ethernet
interface and click Create Virtual Interface.
Object References Select an entry and click Object Reference to open a screen that shows which settings use
the entry. See Section 10.4.4 on page 294 for an example.
# This field is a sequential value, and it is not associated with any interface.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
Name This field displays the name of the interface.
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
278
10.4.1 Ethernet Edit
The Ethernet Edit screen lets you configure IP address assignment, interface parameters, RIP settings,
OSPF settings, DHCP settings, connectivity check, and MAC address settings. To access this screen, click
an Edit icon in the Ethernet Summary screen. (See Section 10.4 on page 276.)
The OPT interface’s Edit > Configuration screen is shown here as an example. The screens for other
interfaces are similar and contain a subset to the OPT interface screen’s fields.
Note: If you create IP address objects based on an interface’s IP address, subnet, or gateway,
the Zyxel Device automatically updates every rule or setting that uses the object
whenever the interface’s IP address settings change. For example, if you change the
VLAN's IP address, the Zyxel Device automatically updates the corresponding
interface-based, LAN subnet address object.
With RIP, you can use Ethernet interfaces to do the following things.
• Enable and disable RIP in the underlying physical port or port group.
• Select which direction(s) routing information is exchanged - The Zyxel Device can receive routing
information, send routing information, or do both.
• Select which version of RIP to support in each direction - The Zyxel Device supports RIP-1, RIP-2, and
both versions.
• Select the broadcasting method used by RIP-2 packets - The Zyxel Device can use subnet
broadcasting or multicasting.
With OSPF, you can use Ethernet interfaces to do the following things.
• Enable and disable OSPF in the underlying physical port or port group.
• Select the area to which the interface belongs.
• Override the default link cost and authentication method for the selected area.
• Select in which direction(s) routing information is exchanged - The Zyxel Device can receive routing
information, send routing information, or do both.
IP Address This field displays the current IP address of the interface. If the IP address is 0.0.0.0 (in the IPv4
network) or :: (in the IPv6 network), the interface does not have an IP address yet.
In the IPv4 network, this screen also shows whether the IP address is a static IP address
(STATIC) or dynamically assigned (DHCP). IP addresses are always static in virtual interfaces.
In the IPv6 network, this screen also shows whether the IP address is a static IP address
(STATIC), link-local IP address (LINK LOCAL), dynamically assigned (DHCP), or an IPv6
StateLess Address AutoConfiguration IP address (SLAAC). See Section 10.1.2 on page 270
for more information about IPv6.
Mask This field displays the interface’s subnet mask in dot decimal notation.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 100 Configuration > Network > Interface > Ethernet (continued)
LABEL DESCRIPTION

Chapter 10 Interfaces
USG/ZyWALL User’s Guide
279
Set the priority used to identify the DR or BDR if one does not exist.
IGMP Proxy
Internet Group Management Protocol (IGMP) proxy is used for multicast routing. IGMP proxy enables the Zyxel
Device to issue IGMP host messages on behalf of hosts that the Zyxel Device discovered on its IGMP-enabled
interfaces. The Zyxel Device acts as a proxy for its hosts. Refer to the following figure.
• DS: Downstream traffic
• US: Upstream traffic
•R: Router
• MS: Multicast Server
• Enable IGMP Upstream (US) on the Zyxel Device interface that connects to a router (R) running IGMP
that is closer to the multicast server (MS).
• Enable IGMP Downstream on the Zyxel Device interface which connects to the multicast hosts.
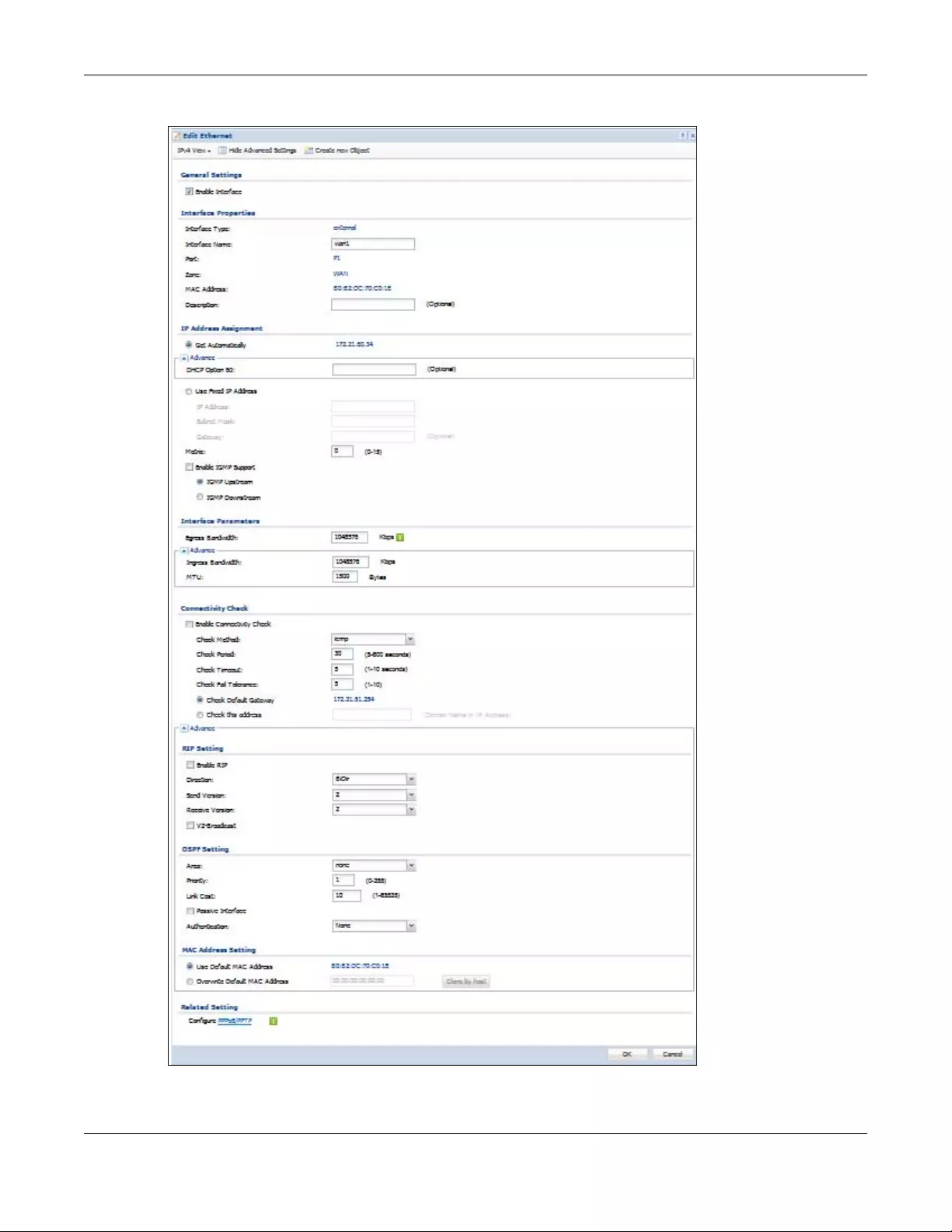
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
280
Figure 227 Configuration > Network > Interface > Ethernet > Edit (External Type)
Configuration > Network > Interface > Ethernet > Edit (External Type
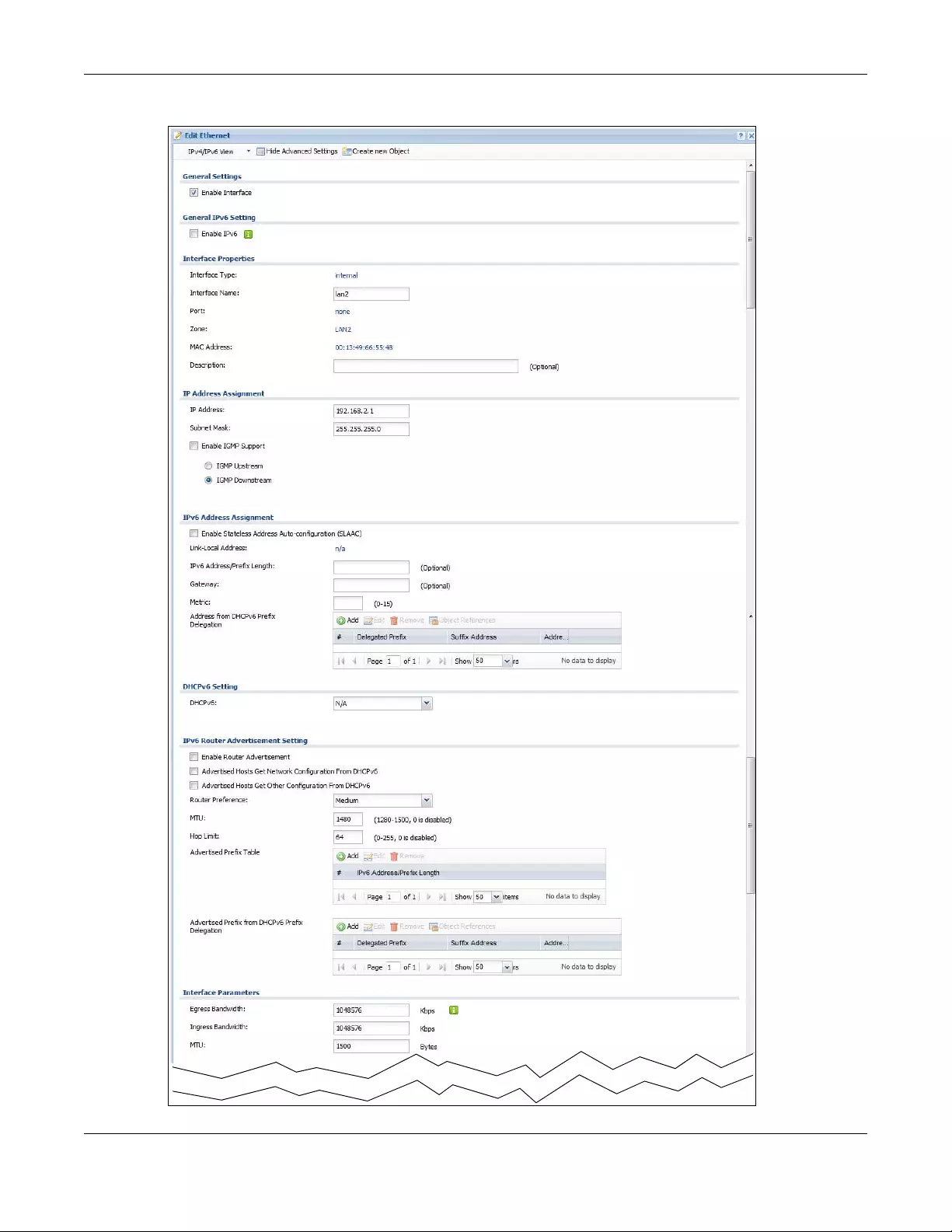
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
281
Figure 228 Configuration > Network > Interface > Ethernet > Edit (Internal Type)
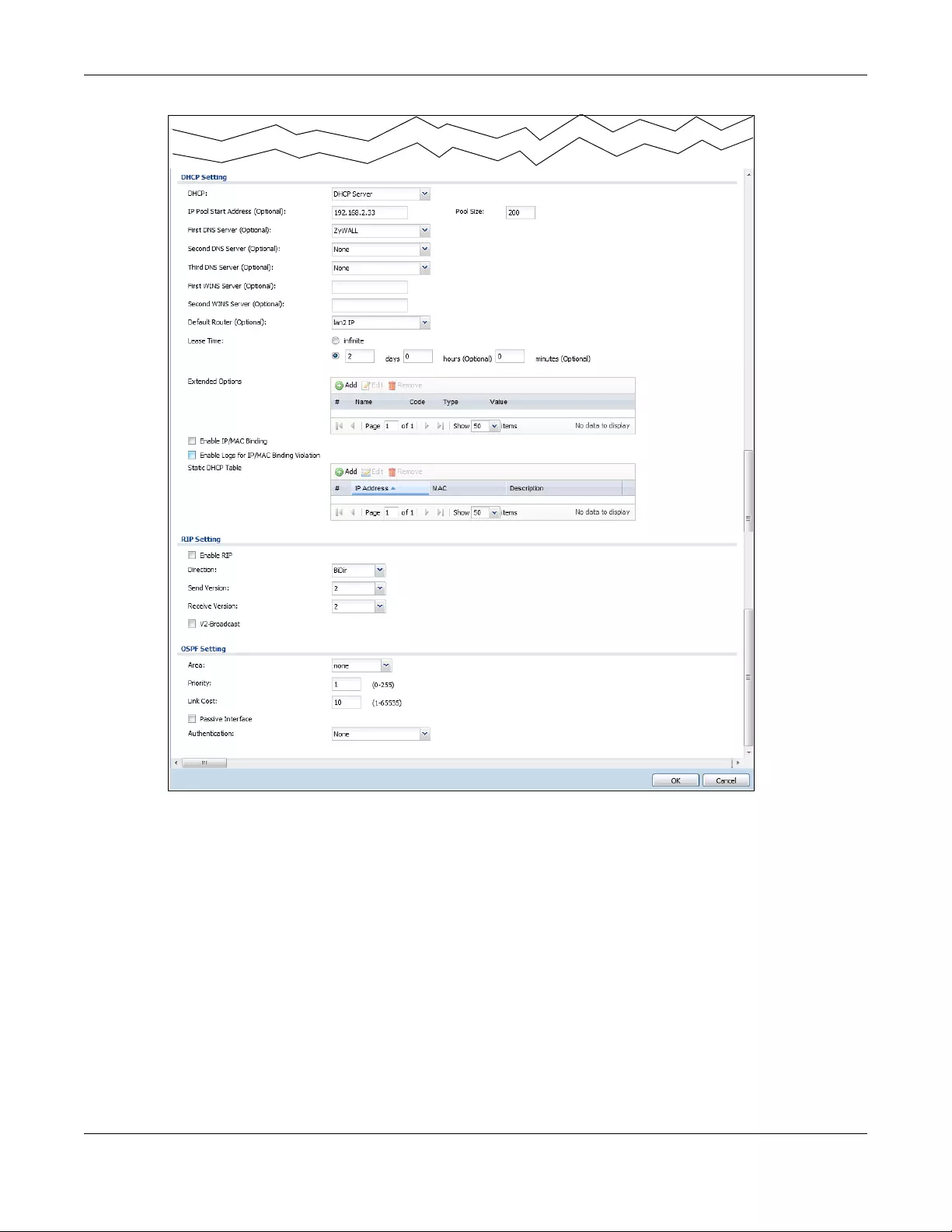
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
282
Configuration > Network > Interface > Ethernet > Edit (Internal Type)
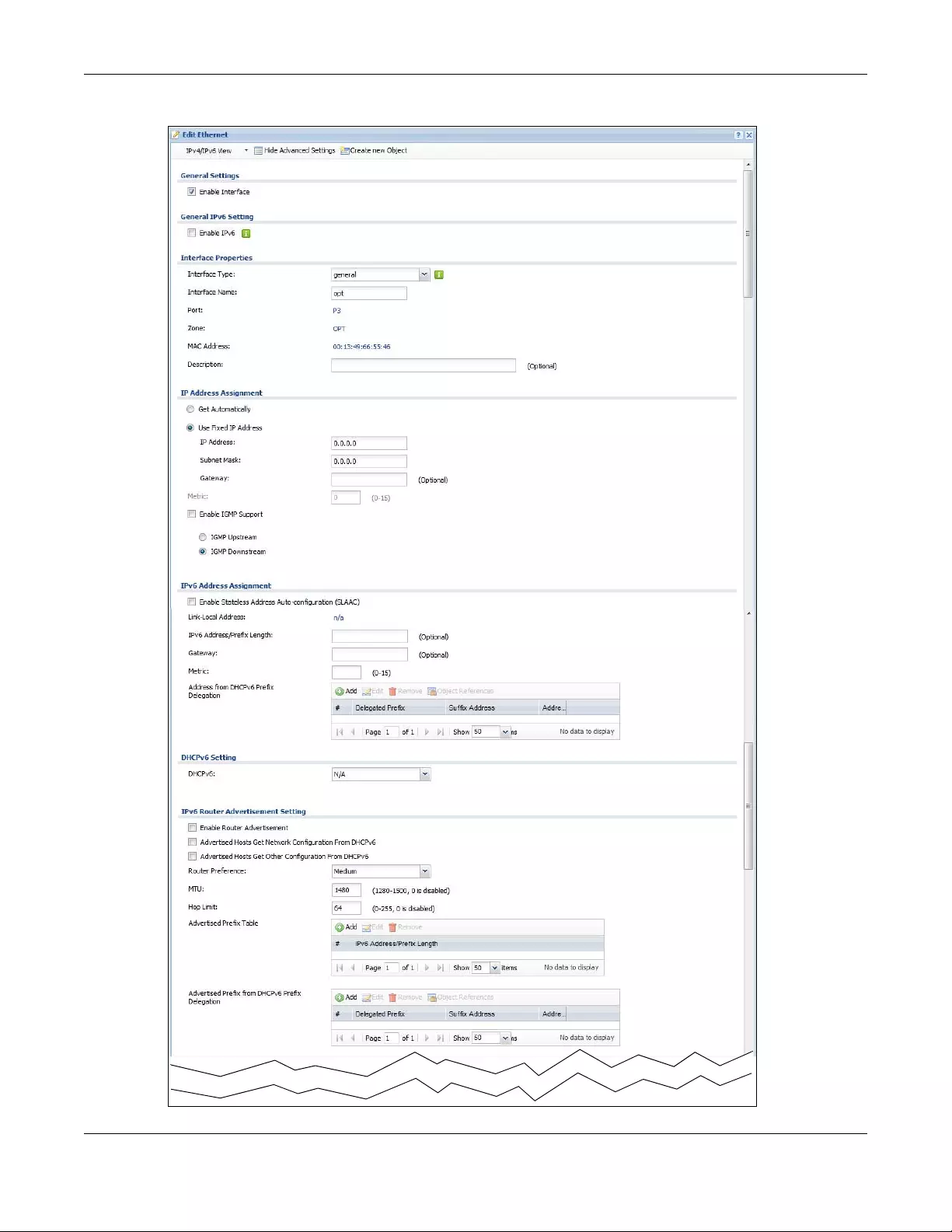
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
283
Figure 229 Configuration > Network > Interface > Ethernet > Edit (OPT)
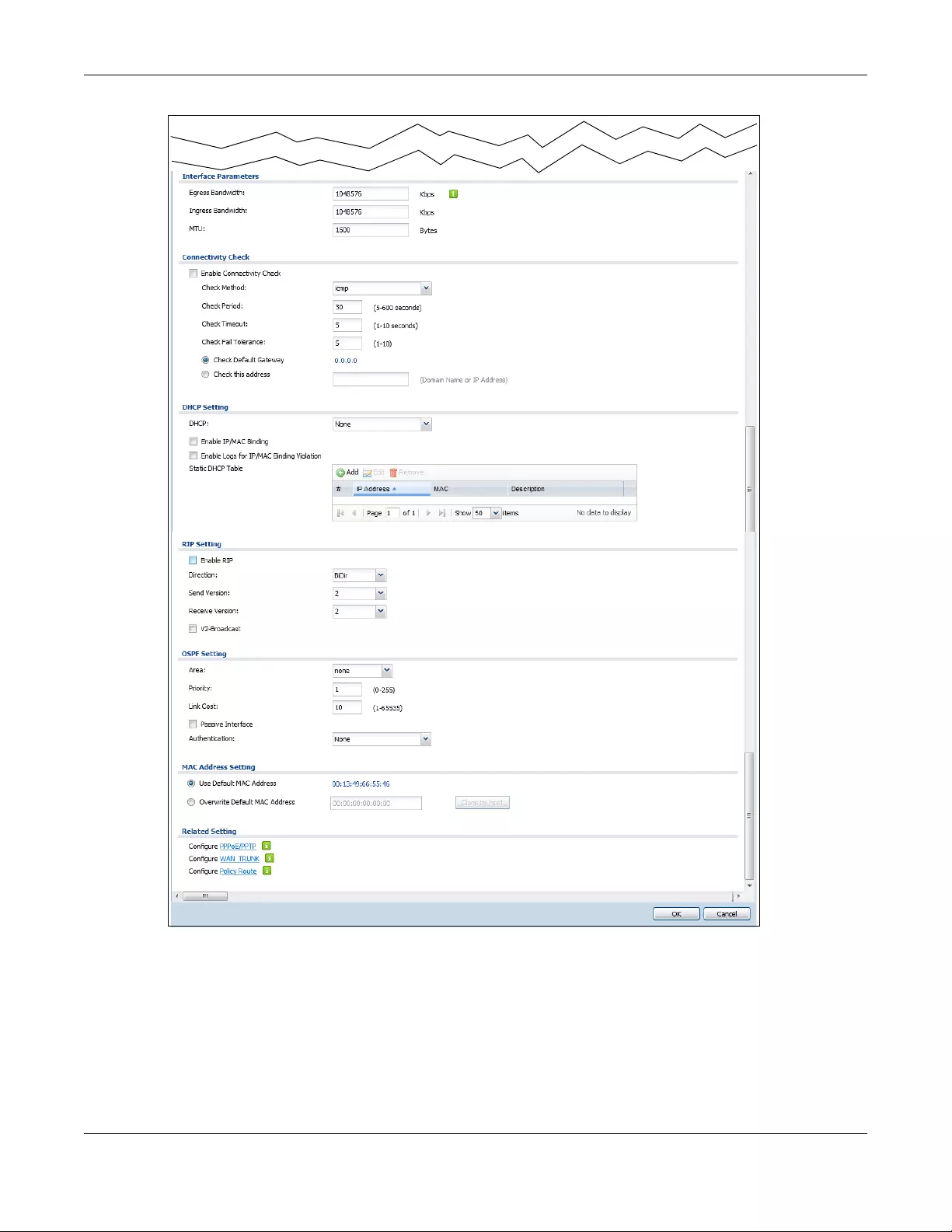
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
284
Configuration > Network > Interface > Ethernet > Edit (OPT)
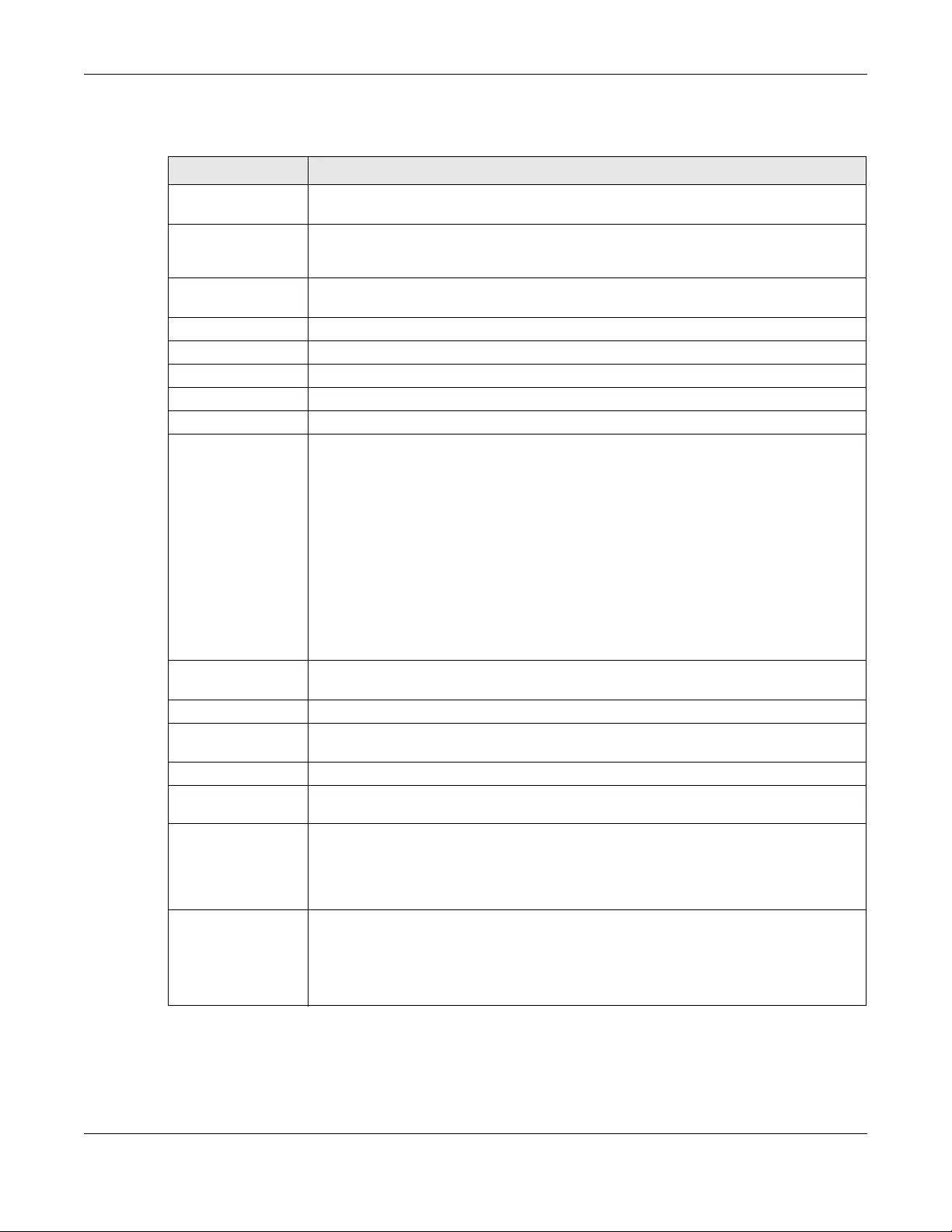
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
285
This screen’s fields are described in the table below.
Table 101 Configuration > Network > Interface > Ethernet > Edit
LABEL DESCRIPTION
IPv4/IPv6 View / IPv4
View / IPv6 View
Use this button to display both IPv4 and IPv6, IPv4-only, or IPv6-only configuration fields.
Show Advanced
Settings / Hide
Advanced Settings
Click this button to display a greater or lesser number of configuration fields.
Create New Object Click this button to create a DHCPv6 lease or DHCPv6 request object that you may use for
the DHCPv6 settings in this screen.
General Settings
Enable Interface Select this to enable this interface. Clear this to disable this interface.
General IPv6 Setting
Enable IPv6 Select this to enable IPv6 on this interface. Otherwise, clear this to disable it.
Interface Properties
Interface Type This field is configurable for the OPT interface only. Select to which type of network you will
connect this interface. When you select internal or external the rest of the screen’s options
automatically adjust to correspond. The Zyxel Device automatically adds default route and
SNAT settings for traffic it routes from internal interfaces to external interfaces; for example
LAN to WAN traffic.
internal is for connecting to a local network. Other corresponding configuration options:
DHCP server and DHCP relay. The Zyxel Device automatically adds default SNAT settings for
traffic flowing from this interface to an external interface.
external is for connecting to an external network (like the Internet). The Zyxel Device
automatically adds this interface to the default WAN trunk.
For general, the rest of the screen’s options do not automatically adjust and you must
manually configure a policy route to add routing and SNAT settings for the interface.
Interface Name Specify a name for the interface. It can use alphanumeric characters, hyphens, and
underscores, and it can be up to 11 characters long.
Port This is the name of the Ethernet interface’s physical port.
Zone Select the zone to which this interface is to belong. You use zones to apply security settings
such as security policy, IDP, remote management, anti-virus, and application patrol.
MAC Address This field is read-only. This is the MAC address that the Ethernet interface uses.
Description Enter a description of this interface. It is not used elsewhere. You can use alphanumeric and
()+/:=?!*#@$_%- characters, and it can be up to 60 characters long.
IP Address
Assignment
These IP address fields configure an IPv4 IP address on the interface itself. If you change this
IP address on the interface, you may also need to change a related address object for the
network connected to the interface. For example, if you use this screen to change the IP
address of your LAN interface, you should also change the corresponding LAN subnet
address object.
Get
Automatically This option appears when Interface Type is external or general. Select this to make the
interface a DHCP client and automatically get the IP address, subnet mask, and gateway
address from a DHCP server.
You should not select this if the interface is assigned to a VRRP group. See Chapter 42 on
page 718.
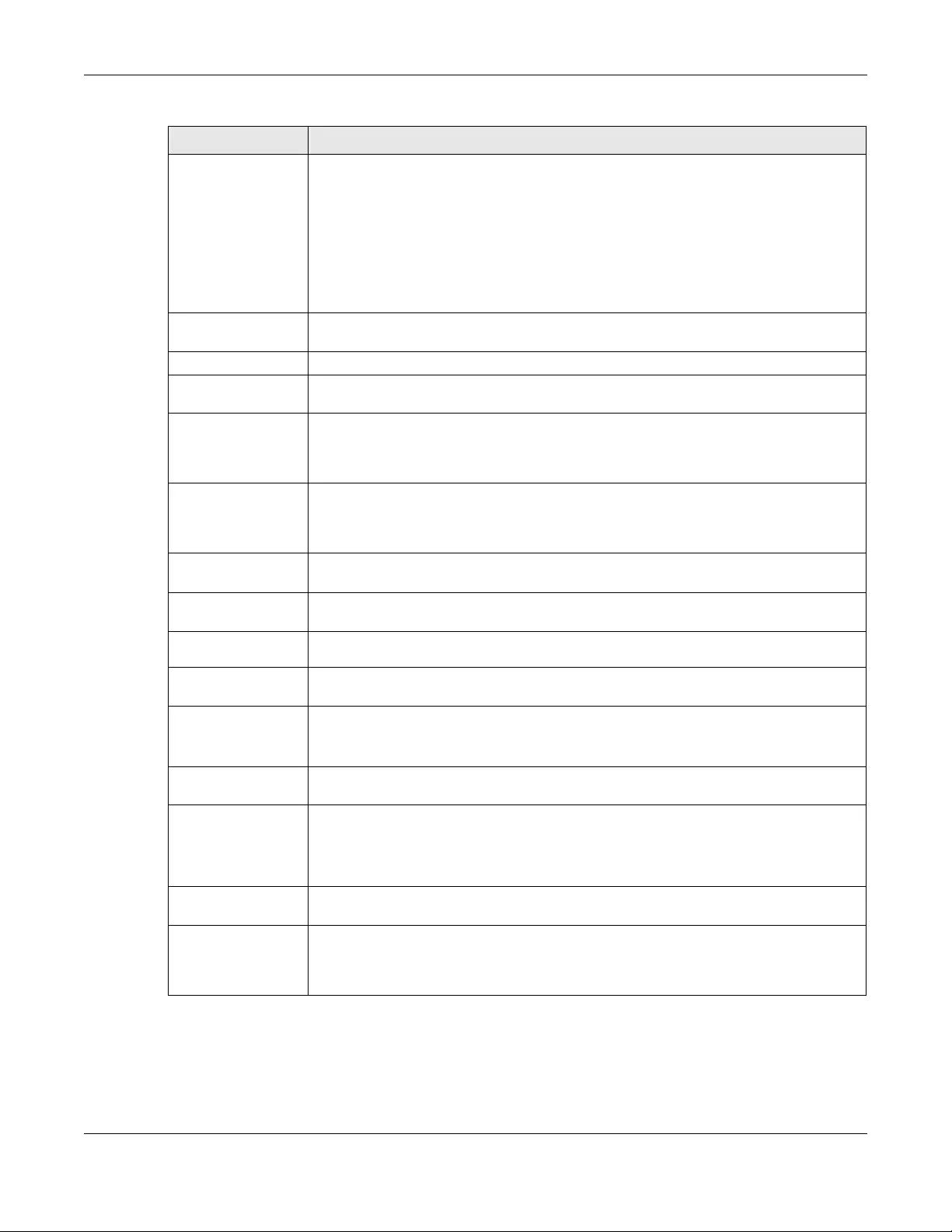
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
286
DHCP Option 60 This is available for external interfaces. DHCP Option 60 is used by the Zyxel Device for
identification to the DHCP server using the VCI (Vendor Class Identifier) on the DHCP server.
The Zyxel Device adds it in the initial DHCP discovery message that a DHCP client
broadcasts in search of an IP address. The DHCP server can assign different IP addresses or
options to clients with the specific VCI or reject the request from clients without the specific
VCI.
Type a string using up to 64 of these characters [a-zA-Z0-9!\"#$%&\'()*+,-./
:;<=>?@\[\\\]^_`{|}~] to identify this Zyxel Device to the DHCP server. For example, Zyxel-
TW.
Use Fixed IP
Address This option appears when Interface Type is external or general. Select this if you want to
specify the IP address, subnet mask, and gateway manually.
IP Address Enter the IP address for this interface.
Subnet Mask Enter the subnet mask of this interface in dot decimal notation. The subnet mask indicates
what part of the IP address is the same for all computers in the network.
Gateway This option appears when Interface Type is external or general. Enter the IP address of the
gateway. The Zyxel Device sends packets to the gateway when it does not know how to
route the packet to its destination. The gateway should be on the same network as the
interface.
Metric This option appears when Interface Type is external or general. Enter the priority of the
gateway (if any) on this interface. The Zyxel Device decides which gateway to use based
on this priority. The lower the number, the higher the priority. If two or more gateways have
the same priority, the Zyxel Device uses the one that was configured first.
Enable IGMP Support Select this to allow the Zyxel Device to act as an IGMP proxy for hosts connected on the
IGMP downstream interface.
IGMP Upstream Enable IGMP Upstream on the interface which connects to a router running IGMP that is
closer to the multicast server.
IGMP
Downstream Enable IGMP Downstream on the interface which connects to the multicast hosts.
IPv6 Address
Assignment
These IP address fields configure an IPv6 IP address on the interface itself.
Enable Stateless
Address Auto-
configuration
(SLAAC)
Select this to enable IPv6 stateless auto-configuration on this interface. The interface will
generate an IPv6 IP address itself from a prefix obtained from an IPv6 router in the network.
Link-Local
address This displays the IPv6 link-local address and the network prefix that the Zyxel Device
generates itself for the interface.
IPv6 Address/
Prefix Length Enter the IPv6 address and the prefix length for this interface if you want to use a static IP
address. This field is optional.
The prefix length indicates what the left-most part of the IP address is the same for all
computers in the network, that is, the network address.
Gateway Enter the IPv6 address of the default outgoing gateway using colon (:) hexadecimal
notation.
Metric Enter the priority of the gateway (if any) on this interface. The Zyxel Device decides which
gateway to use based on this priority. The lower the number, the higher the priority. If two or
more gateways have the same priority, the Zyxel Device uses the one that was configured
first.
Table 101 Configuration > Network > Interface > Ethernet > Edit (continued)
LABEL DESCRIPTION
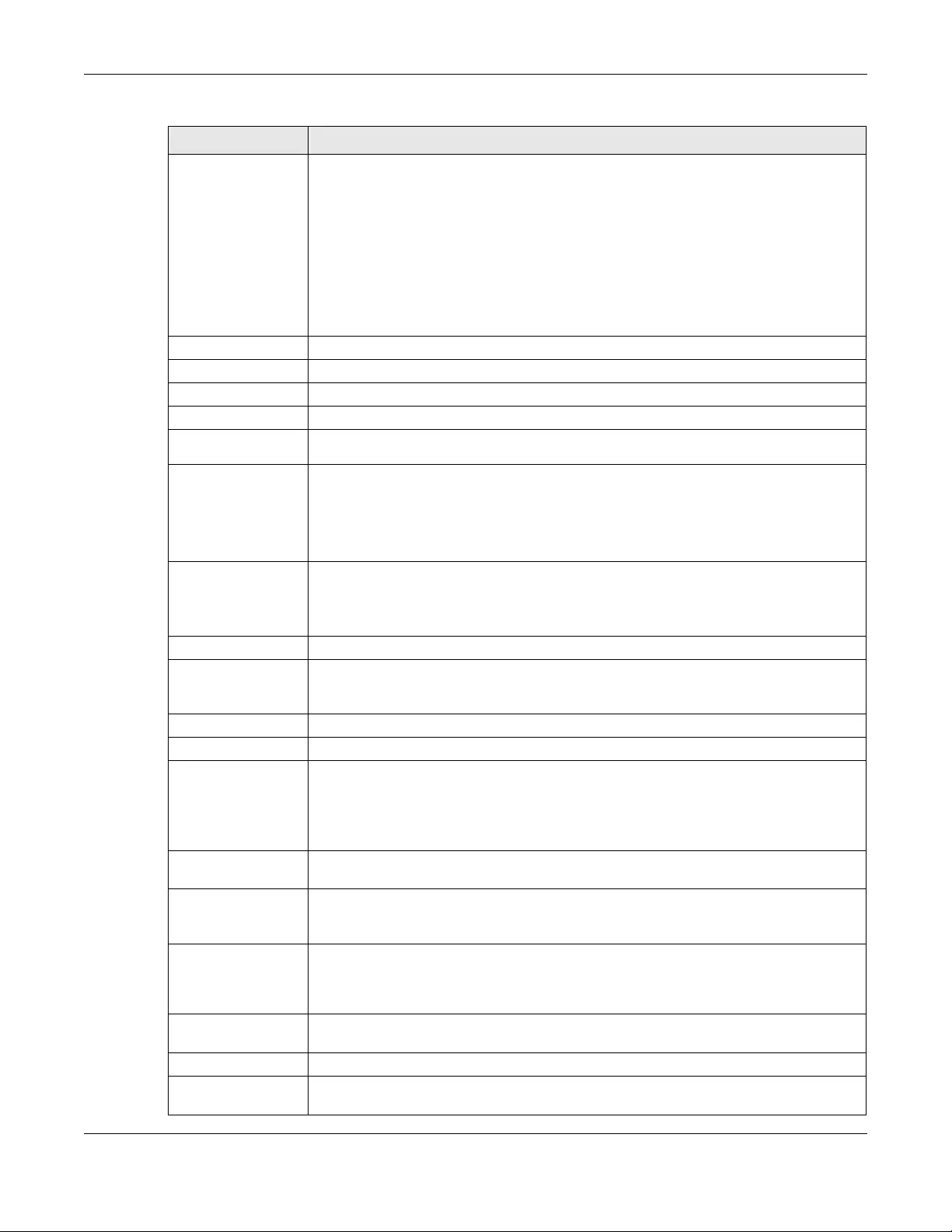
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
287
Address from
DHCPv6 Prefix
Delegation
Use this table to have the Zyxel Device obtain an IPv6 prefix from the ISP or a connected
uplink router for an internal network, such as the LAN or DMZ. You have to also enter a suffix
address which is appended to the delegated prefix to form an address for this interface.
See Prefix Delegation on page 273 for more information.
To use prefix delegation, you must:
• Create at least one DHCPv6 request object before configuring this table.
• The external interface must be a DHCPv6 client. You must configure the DHCPv6
request options using a DHCPv6 request object with the type of prefix-delegation.
• Assign the prefix delegation to an internal interface and enable router advertisement
on that interface.
Add Click this to create an entry.
Edit Select an entry and click this to change the settings.
Remove Select an entry and click this to delete it from this table.
# This field is a sequential value, and it is not associated with any entry.
Delegated
Prefix Select the DHCPv6 request object to use from the drop-down list.
Suffix
Address Enter the ending part of the IPv6 address, a slash (/), and the prefix length. The Zyxel Device
will append it to the delegated prefix.
For example, you got a delegated prefix of 2003:1234:5678/48. You want to configure an IP
address of 2003:1234:5678:1111::1/128 for this interface, then enter ::1111:0:0:0:1/128 in this
field.
Address This field displays the combined IPv6 IP address for this interface.
Note: This field displays the combined address after you click OK and reopen this
screen.
DHCPv6 Setting
DUID This field displays the DHCP Unique IDentifier (DUID) of the interface, which is unique and
used for identification purposes when the interface is exchanging DHCPv6 messages with
others. See DHCPv6 on page 274 for more information.
DUID as MAC Select this if you want the DUID is generated from the interface’s default MAC address.
Customized DUID If you want to use a customized DUID, enter it here for the interface.
Enable Rapid
Commit Select this to shorten the DHCPv6 message exchange process from four to two steps. This
function helps reduce heavy network traffic load.
Note: Make sure you also enable this option in the DHCPv6 clients to make rapid
commit work.
Information
Refresh Time Enter the number of seconds a DHCPv6 client should wait before refreshing information
retrieved from DHCPv6.
Request Address This field is available if you set this interface to DHCPv6 Client. Select this to get an IPv6 IP
address for this interface from the DHCP server. Clear this to not get any IP address
information through DHCPv6.
DHCPv6 Request
Options /
DHCPv6 Lease
Options
If this interface is a DHCPv6 client, use this section to configure DHCPv6 request settings that
determine what additional information to get from the DHCPv6 server. If the interface is a
DHCPv6 server, use this section to configure DHCPv6 lease settings that determine what
additional information to offer to the DHCPv6 clients.
Add Click this to create an entry in this table. See Section 10.4.5 on page 295 for more
information.
Remove Select an entry and click this to delete it from this table.
Object
Reference Select an entry and click Object Reference to open a screen that shows which settings use
the entry. See Section 10.4.4 on page 294 for an example.
Table 101 Configuration > Network > Interface > Ethernet > Edit (continued)
LABEL DESCRIPTION
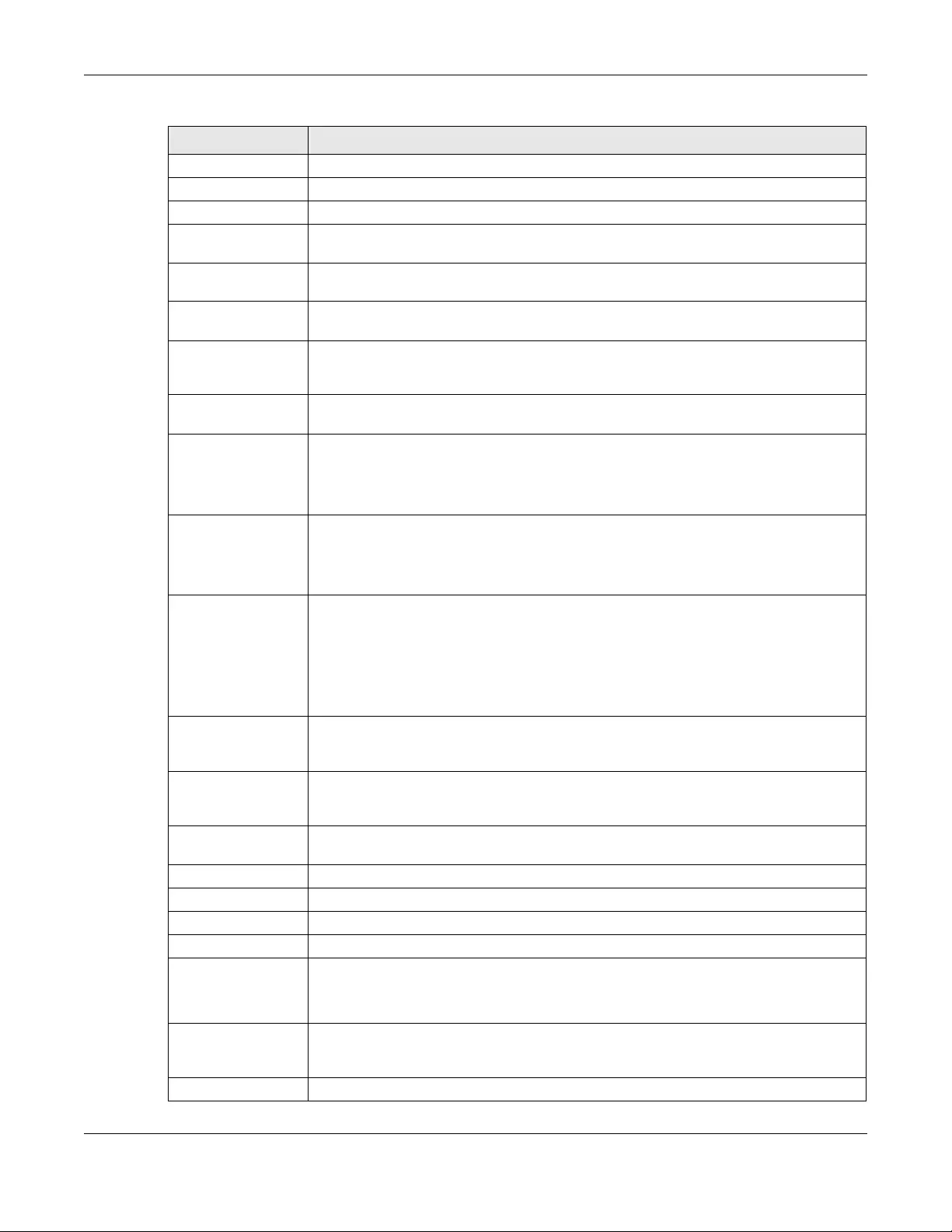
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
288
# This field is a sequential value, and it is not associated with any entry.
Name This field displays the name of the DHCPv6 request or lease object.
Type This field displays the type of the object.
Value This field displays the IPv6 prefix that the Zyxel Device obtained from an uplink router (Server
is selected) or will advertise to its clients (Client is selected).
Interface When Relay is selected, select this check box and an interface from the drop-down list if
you want to use it as the relay server.
Relay Server When Relay is selected, select this check box and enter the IP address of a DHCPv6 server
as the relay server.
IPv6 Router
Advertisement
Setting
Enable Router
Advertisement Select this to enable this interface to send router advertisement messages periodically. See
IPv6 Router Advertisement on page 273 for more information.
Advertised Hosts
Get Network
Configuration
From DHCPv6
Select this to have the Zyxel Device indicate to hosts to obtain network settings (such as
prefix and DNS settings) through DHCPv6.
Clear this to have the Zyxel Device indicate to hosts that DHCPv6 is not available and they
should use the prefix in the router advertisement message.
Advertised Hosts
Get Other
Configuration
From DHCPv6
Select this to have the Zyxel Device indicate to hosts to obtain DNS information through
DHCPv6.
Clear this to have the Zyxel Device indicate to hosts that DNS information is not available in
this network.
Router
Preference Select the router preference (Low, Medium or High) for the interface. The interface sends
this preference in the router advertisements to tell hosts what preference they should use
for the Zyxel Device. This helps hosts to choose their default router especially when there
are multiple IPv6 router in the network.
Note: Make sure the hosts also support router preference to make this function
work.
MTU The Maximum Transmission Unit. Type the maximum size of each IPv6 data packet, in bytes,
that can move through this interface. If a larger packet arrives, the Zyxel Device discards
the packet and sends an error message to the sender to inform this.
Hop Limit Enter the maximum number of network segments that a packet can cross before reaching
the destination. When forwarding an IPv6 packet, IPv6 routers are required to decrease the
Hop Limit by 1 and to discard the IPv6 packet when the Hop Limit is 0.
Advertised Prefix
Table Configure this table only if you want the Zyxel Device to advertise a fixed prefix to the
network.
Add Click this to create an IPv6 prefix address.
Edit Select an entry in this table and click this to modify it.
Remove Select an entry in this table and click this to delete it.
# This field is a sequential value, and it is not associated with any entry.
IPv6
Address/
Prefix Length
Enter the IPv6 network prefix address and the prefix length.
The prefix length indicates what the left-most part of the IP address is the same for all
computers in the network, that is, the network address.
Advertised Prefix
from DHCPv6
Prefix Delegation
This table is available when the Interface Type is internal. Use this table to configure the
network prefix if you want to use a delegated prefix as the beginning part of the network
prefix.
Add Click this to create an entry in this table.
Table 101 Configuration > Network > Interface > Ethernet > Edit (continued)
LABEL DESCRIPTION
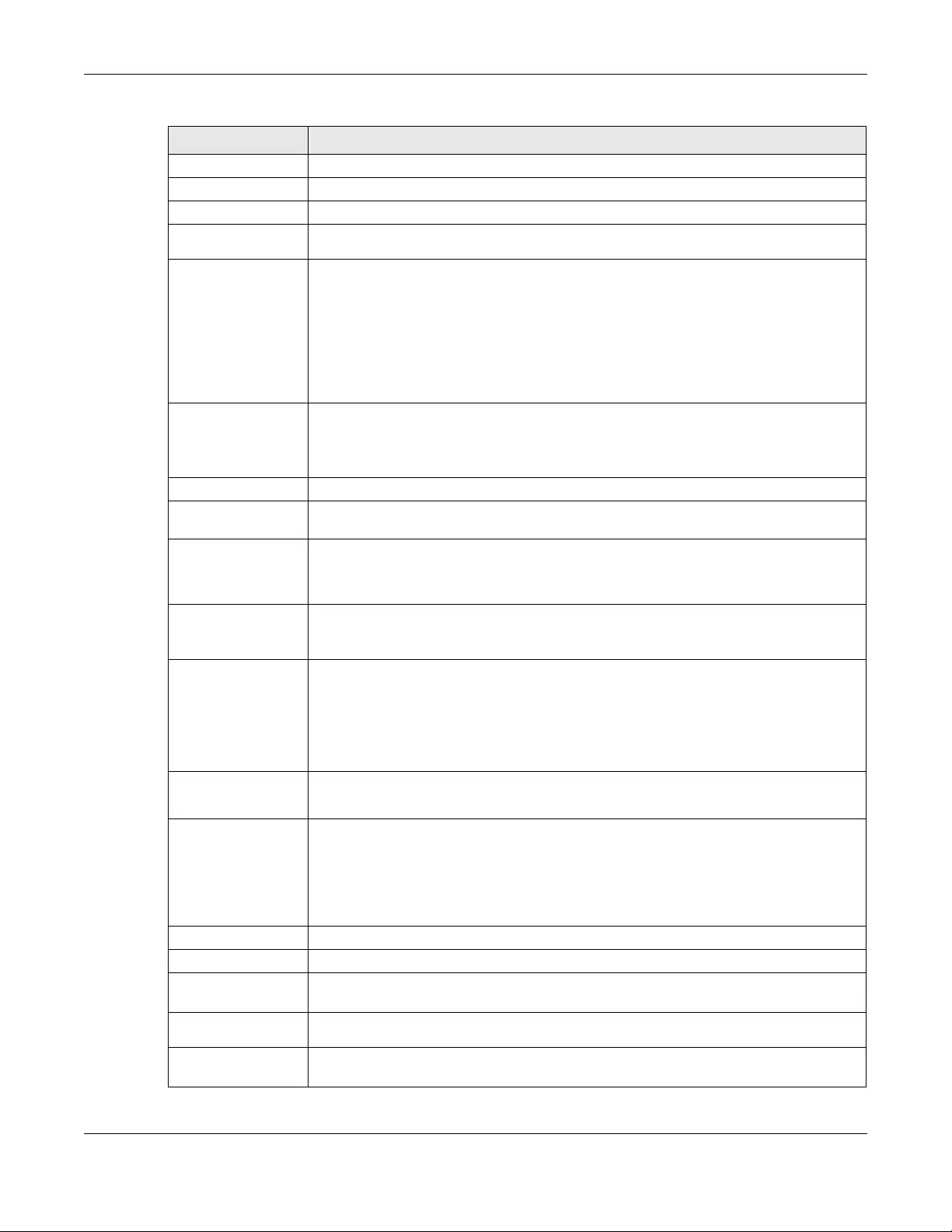
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
289
Edit Select an entry in this table and click this to modify it.
Remove Select an entry in this table and click this to delete it.
# This field is a sequential value, and it is not associated with any entry.
Delegated
Prefix Select the DHCPv6 request object to use for generating the network prefix for the network.
Suffix
Address Enter the ending part of the IPv6 network address plus a slash (/) and the prefix length. The
Zyxel Device will append it to the selected delegated prefix. The combined address is the
network prefix for the network.
For example, you got a delegated prefix of 2003:1234:5678/48. You want to divide it into
2003:1234:5678:1111/64 for this interface and 2003:1234:5678:2222/64 for another interface.
You can use ::1111/64 and ::2222/64 for the suffix address respectively. But if you do not
want to divide the delegated prefix into subnetworks, enter ::0/48 here, which keeps the
same prefix length (/48) as the delegated prefix.
Address This is the final network prefix combined by the delegated prefix and the suffix.
Note: This field displays the combined address after you click OK and reopen this
screen.
Interface Parameters
Egress Bandwidth Enter the maximum amount of traffic, in kilobits per second, the Zyxel Device can send
through the interface to the network. Allowed values are 0 - 1048576.
Ingress
Bandwidth This is reserved for future use.
Enter the maximum amount of traffic, in kilobits per second, the Zyxel Device can receive
from the network through the interface. Allowed values are 0 - 1048576.
MTU Maximum Transmission Unit. Type the maximum size of each data packet, in bytes, that can
move through this interface. If a larger packet arrives, the Zyxel Device divides it into smaller
fragments. Allowed values are 576 - 1500. Usually, this value is 1500.
Connectivity Check These fields appear when Interface Properties is External or General.
The interface can regularly check the connection to the gateway you specified to make
sure it is still available. You specify how often the interface checks the connection, how
long to wait for a response before the attempt is a failure, and how many consecutive
failures are required before the Zyxel Device stops routing to the gateway. The Zyxel Device
resumes routing to the gateway the first time the gateway passes the connectivity check.
Enable
Connectivity
Check
Select this to turn on the connection check.
Check Method Select the method that the gateway allows.
Select icmp to have the Zyxel Device regularly ping the gateway you specify to make sure
it is still available.
Select tcp to have the Zyxel Device regularly perform a TCP handshake with the gateway
you specify to make sure it is still available.
Check Period Enter the number of seconds between connection check attempts.
Check Timeout Enter the number of seconds to wait for a response before the attempt is a failure.
Check Fail
Tolerance Enter the number of consecutive failures before the Zyxel Device stops routing through the
gateway.
Check Default
Gateway Select this to use the default gateway for the connectivity check.
Check this
address Select this to specify a domain name or IP address for the connectivity check. Enter that
domain name or IP address in the field next to it.
Table 101 Configuration > Network > Interface > Ethernet > Edit (continued)
LABEL DESCRIPTION
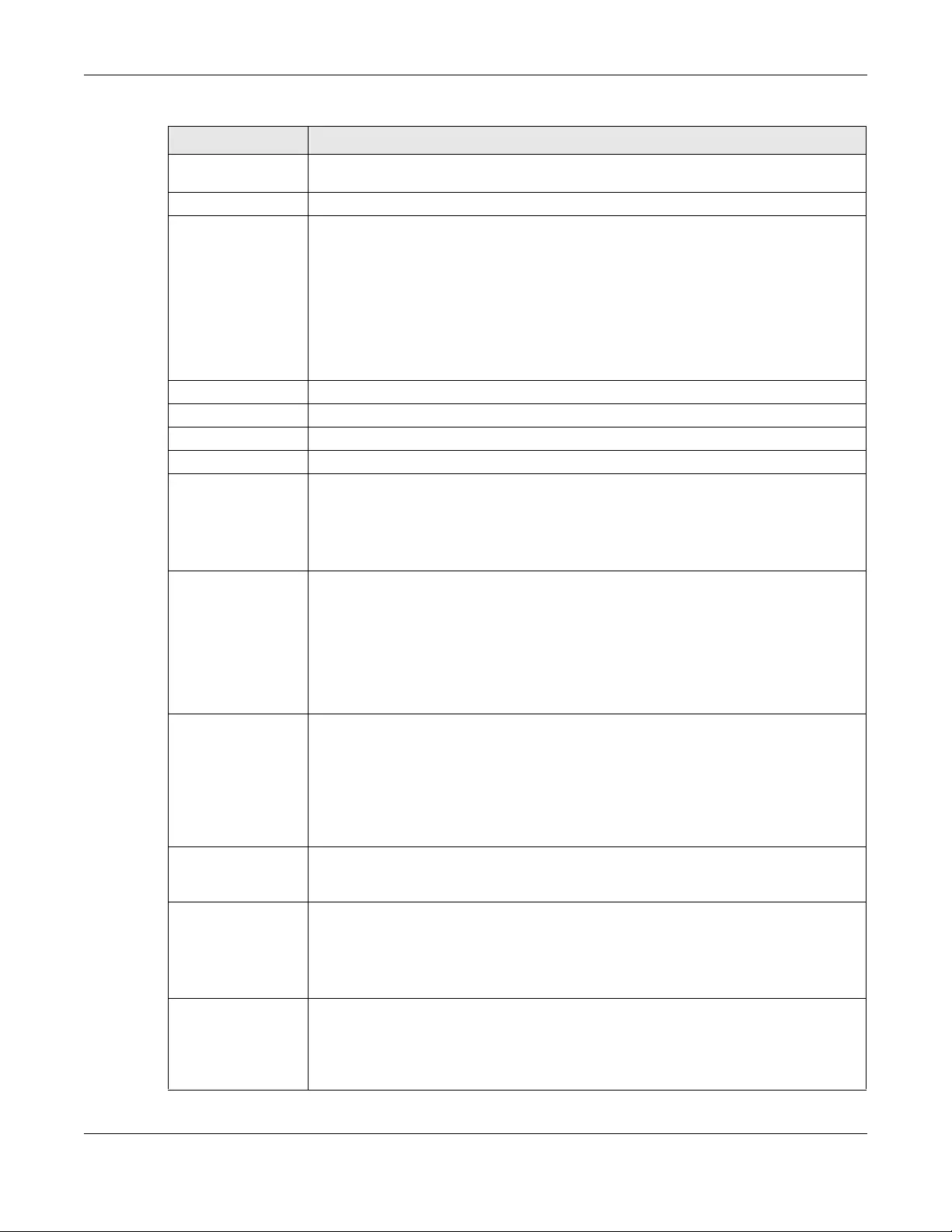
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
290
Check Port This field only displays when you set the Check Method to tcp. Specify the port number to
use for a TCP connectivity check.
DHCP Setting This section appears when Interface Type is internal or general.
DHCP Select what type of DHCP service the Zyxel Device provides to the network. Choices are:
None - the Zyxel Device does not provide any DHCP services. There is already a DHCP
server on the network.
DHCP Relay - the Zyxel Device routes DHCP requests to one or more DHCP servers you
specify. The DHCP server(s) may be on another network.
DHCP Server - the Zyxel Device assigns IP addresses and provides subnet mask, gateway,
and DNS server information to the network. The Zyxel Device is the DHCP server for the
network.
These fields appear if the Zyxel Device is a DHCP Relay.
Relay Server 1 Enter the IP address of a DHCP server for the network.
Relay Server 2 This field is optional. Enter the IP address of another DHCP server for the network.
These fields appear if the Zyxel Device is a DHCP Server.
IP Pool Start
Address Enter the IP address from which the Zyxel Device begins allocating IP addresses. If you want
to assign a static IP address to a specific computer, use the Static DHCP Table.
If this field is blank, the Pool Size must also be blank. In this case, the Zyxel Device can assign
every IP address allowed by the interface’s IP address and subnet mask, except for the first
address (network address), last address (broadcast address) and the interface’s IP address.
Pool Size Enter the number of IP addresses to allocate. This number must be at least one and is
limited by the interface’s Subnet Mask. For example, if the Subnet Mask is 255.255.255.0 and
IP Pool Start Address is 10.10.10.10, the Zyxel Device can allocate 10.10.10.10 to
10.10.10.254, or 245 IP addresses.
If this field is blank, the IP Pool Start Address must also be blank. In this case, the Zyxel Device
can assign every IP address allowed by the interface’s IP address and subnet mask, except
for the first address (network address), last address (broadcast address) and the interface’s
IP address.
First DNS Server,
Second DNS
Server, Third DNS
Server
Specify the IP addresses up to three DNS servers for the DHCP clients to use. Use one of the
following ways to specify these IP addresses.
Custom Defined - enter a static IP address.
From ISP - select the DNS server that another interface received from its DHCP server.
Zyxel Device - the DHCP clients use the IP address of this interface and the Zyxel Device
works as a DNS relay.
First WINS Server,
Second WINS
Server
Type the IP address of the WINS (Windows Internet Naming Service) server that you want to
send to the DHCP clients. The WINS server keeps a mapping table of the computer names
on your network and the IP addresses that they are currently using.
Default Router If you set this interface to DHCP Server, you can select to use either the interface’s IP
address or another IP address as the default router. This default router will become the
DHCP clients’ default gateway.
To use another IP address as the default router, select Custom Defined and enter the IP
address.
Lease time Specify how long each computer can use the information (especially the IP address)
before it has to request the information again. Choices are:
infinite - select this if IP addresses never expire.
days, hours, and minutes - select this to enter how long IP addresses are valid.
Table 101 Configuration > Network > Interface > Ethernet > Edit (continued)
LABEL DESCRIPTION
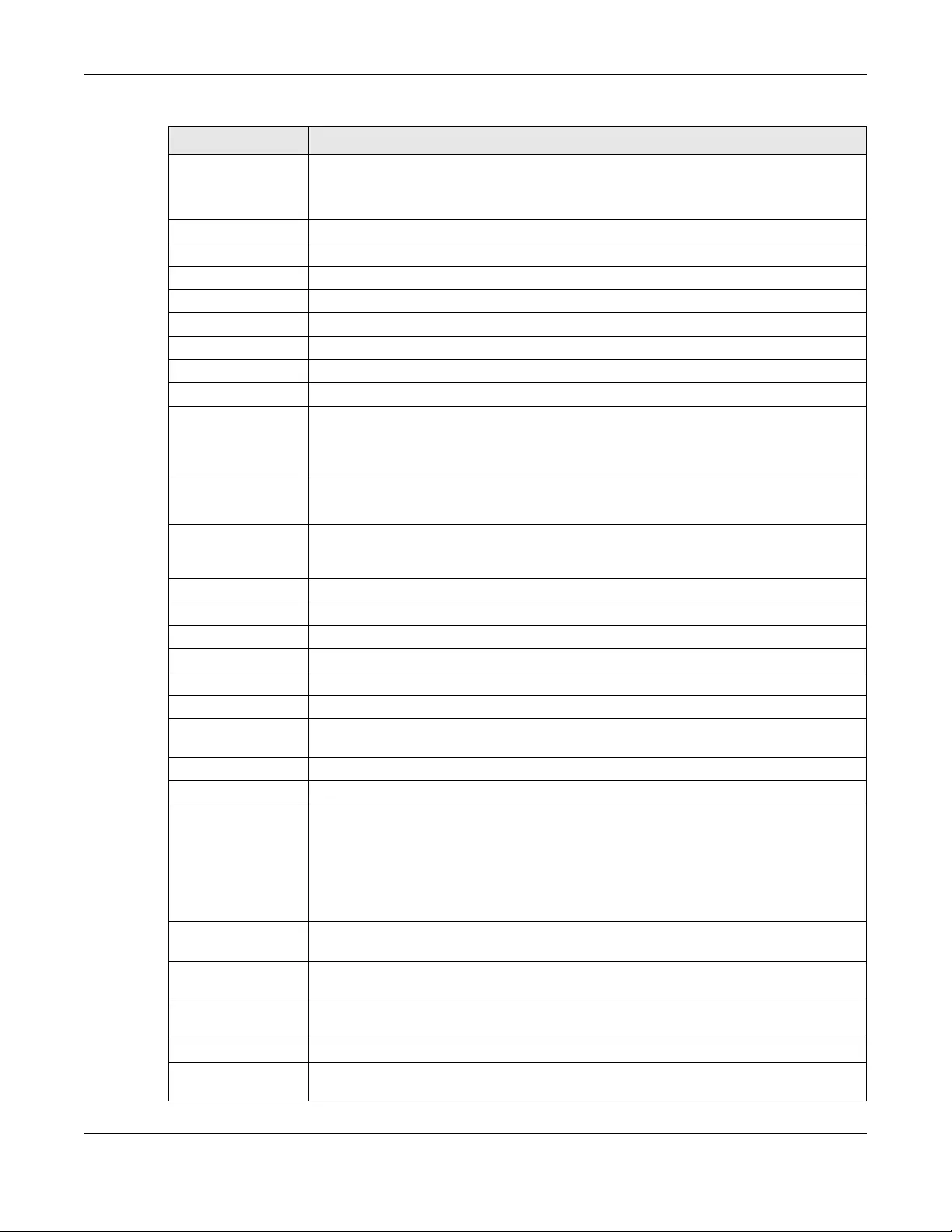
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
291
Extended
Options This table is available if you selected DHCP server.
Configure this table if you want to send more information to DHCP clients through DHCP
packets.
Add Click this to create an entry in this table. See Section 10.4.6 on page 295.
Edit Select an entry in this table and click this to modify it.
Remove Select an entry in this table and click this to delete it.
# This field is a sequential value, and it is not associated with any entry.
Name This is the name of the DHCP option.
Code This is the code number of the DHCP option.
Type This is the type of the set value for the DHCP option.
Value This is the value set for the DHCP option.
Enable IP/MAC
Binding Select this option to have this interface enforce links between specific IP addresses and
specific MAC addresses. This stops anyone else from manually using a bound IP address on
another device connected to this interface. Use this to make use only the intended users
get to use specific IP addresses.
Enable Logs for
IP/MAC Binding
Violation
Select this option to have the Zyxel Device generate a log if a device connected to this
interface attempts to use an IP address that is bound to another device’s MAC address.
Static DHCP
Table Configure a list of static IP addresses the Zyxel Device assigns to computers connected to
the interface. Otherwise, the Zyxel Device assigns an IP address dynamically using the
interface’s IP Pool Start Address and Pool Size.
Add Click this to create a new entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
# This field is a sequential value, and it is not associated with a specific entry.
IP Address Enter the IP address to assign to a device with this entry’s MAC address.
MAC Enter the MAC address to which to assign this entry’s IP address.
Description Enter a description to help identify this static DHCP entry. You can use alphanumeric and
()+/:=?!*#@$_%- characters, and it can be up to 60 characters long.
RIP Setting See Section 11.6 on page 379 for more information about RIP.
Enable RIP Select this to enable RIP in this interface.
Direction This field is effective when RIP is enabled. Select the RIP direction from the drop-down list
box.
BiDir - This interface sends and receives routing information.
In-Only - This interface receives routing information.
Out-Only - This interface sends routing information.
Send Version This field is effective when RIP is enabled. Select the RIP version(s) used for sending RIP
packets. Choices are 1, 2, and 1 and 2.
Receive Version This field is effective when RIP is enabled. Select the RIP version(s) used for receiving RIP
packets. Choices are 1, 2, and 1 and 2.
V2-Broadcast This field is effective when RIP is enabled. Select this to send RIP-2 packets using subnet
broadcasting; otherwise, the Zyxel Device uses multicasting.
OSPF Setting See Section 11.7 on page 381 for more information about OSPF.
Area Select the area in which this interface belongs. Select None to disable OSPF in this
interface.
Table 101 Configuration > Network > Interface > Ethernet > Edit (continued)
LABEL DESCRIPTION
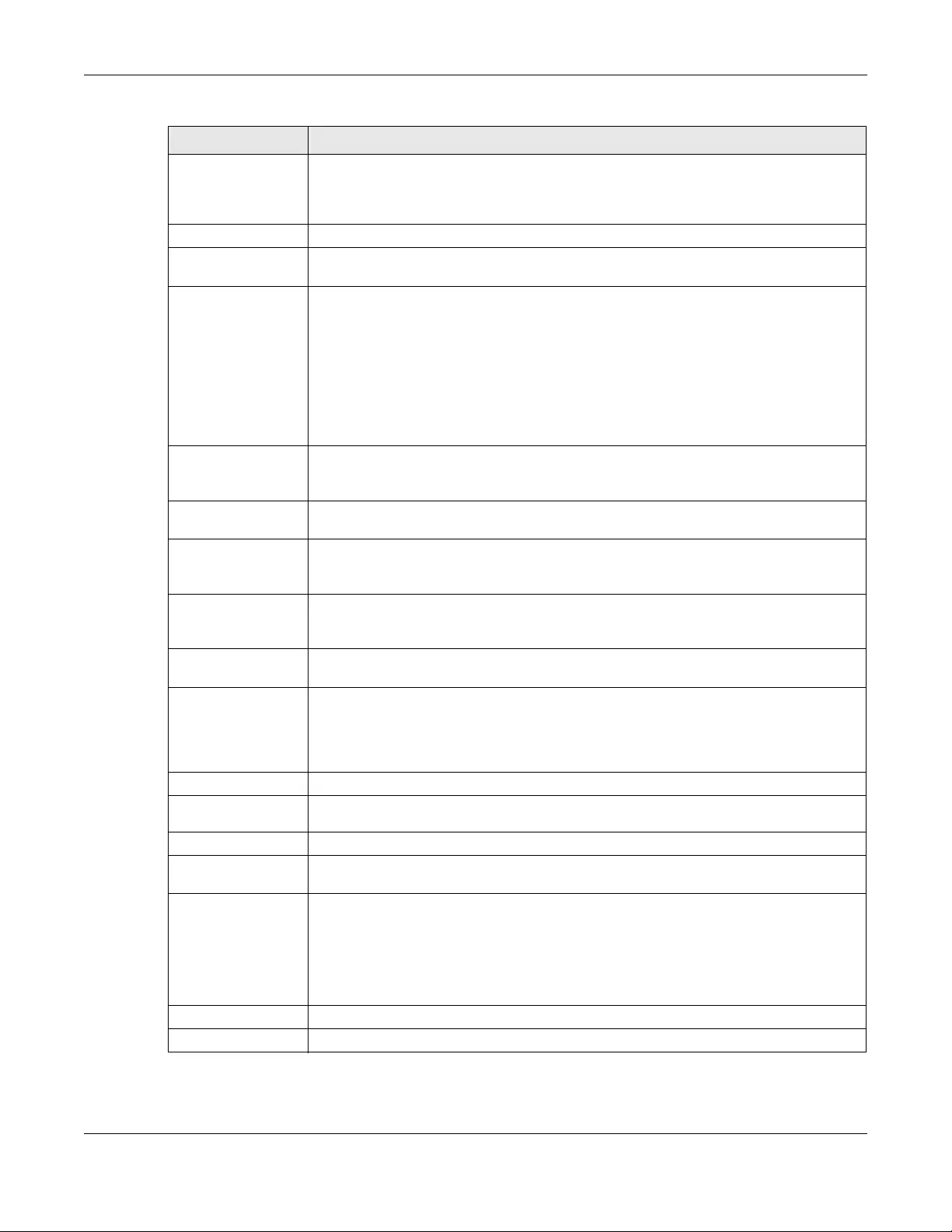
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
292
Priority Enter the priority (between 0 and 255) of this interface when the area is looking for a
Designated Router (DR) or Backup Designated Router (BDR). The highest-priority interface
identifies the DR, and the second-highest-priority interface identifies the BDR. Set the priority
to zero if the interface can not be the DR or BDR.
Link Cost Enter the cost (between 1 and 65,535) to route packets through this interface.
Passive Interface Select this to stop forwarding OSPF routing information from the selected interface. As a
result, this interface only receives routing information.
Authentication Select an authentication method, or disable authentication. To exchange OSPF routing
information with peer border routers, you must use the same authentication method that
they use. Choices are:
Same-as-Area - use the default authentication method in the area
None - disable authentication
Text - authenticate OSPF routing information using a plain-text password
MD5 - authenticate OSPF routing information using MD5 encryption
Text
Authentication
Key
This field is available if the Authentication is Text. Type the password for text authentication.
The key can consist of alphanumeric characters and the underscore, and it can be up to
16 characters long.
MD5
Authentication ID This field is available if the Authentication is MD5. Type the ID for MD5 authentication. The ID
can be between 1 and 255.
MD5
Authentication
Key
This field is available if the Authentication is MD5. Type the password for MD5
authentication. The password can consist of alphanumeric characters and the underscore,
and it can be up to 16 characters long.
MAC Address Setting This section appears when Interface Properties is External or General. Have the interface
use either the factory assigned default MAC address, a manually specified MAC address,
or clone the MAC address of another device or computer.
Use Default MAC
Address Select this option to have the interface use the factory assigned default MAC address. By
default, the Zyxel Device uses the factory assigned MAC address to identify itself.
Overwrite
Default MAC
Address
Select this option to have the interface use a different MAC address. Either enter the MAC
address in the fields or click Clone by host and enter the IP address of the device or
computer whose MAC you are cloning. Once it is successfully configured, the address will
be copied to the configuration file. It will not change unless you change the setting or
upload a different configuration file.
Related Setting
Configure
PPPoE/PPTP Click PPPoE/PPTP if this interface’s Internet connection uses PPPoE or PPTP or L2TP.
Configure VLAN Click VLAN if you want to configure a VLAN interface for this Ethernet interface.
Configure WAN
TRUNK Click WAN TRUNK to go to a screen where you can set this interface to be part of a WAN
trunk for load balancing.
Configure Policy
Route Click Policy Route to go to the policy route summary screen where you can manually
associate traffic with this interface.
You must manually configure a policy route to add routing and SNAT settings for an
interface with the Interface Type set to general. You can also configure a policy route to
override the default routing and SNAT behavior for an interface with an Interface Type of
internal or external.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 101 Configuration > Network > Interface > Ethernet > Edit (continued)
LABEL DESCRIPTION
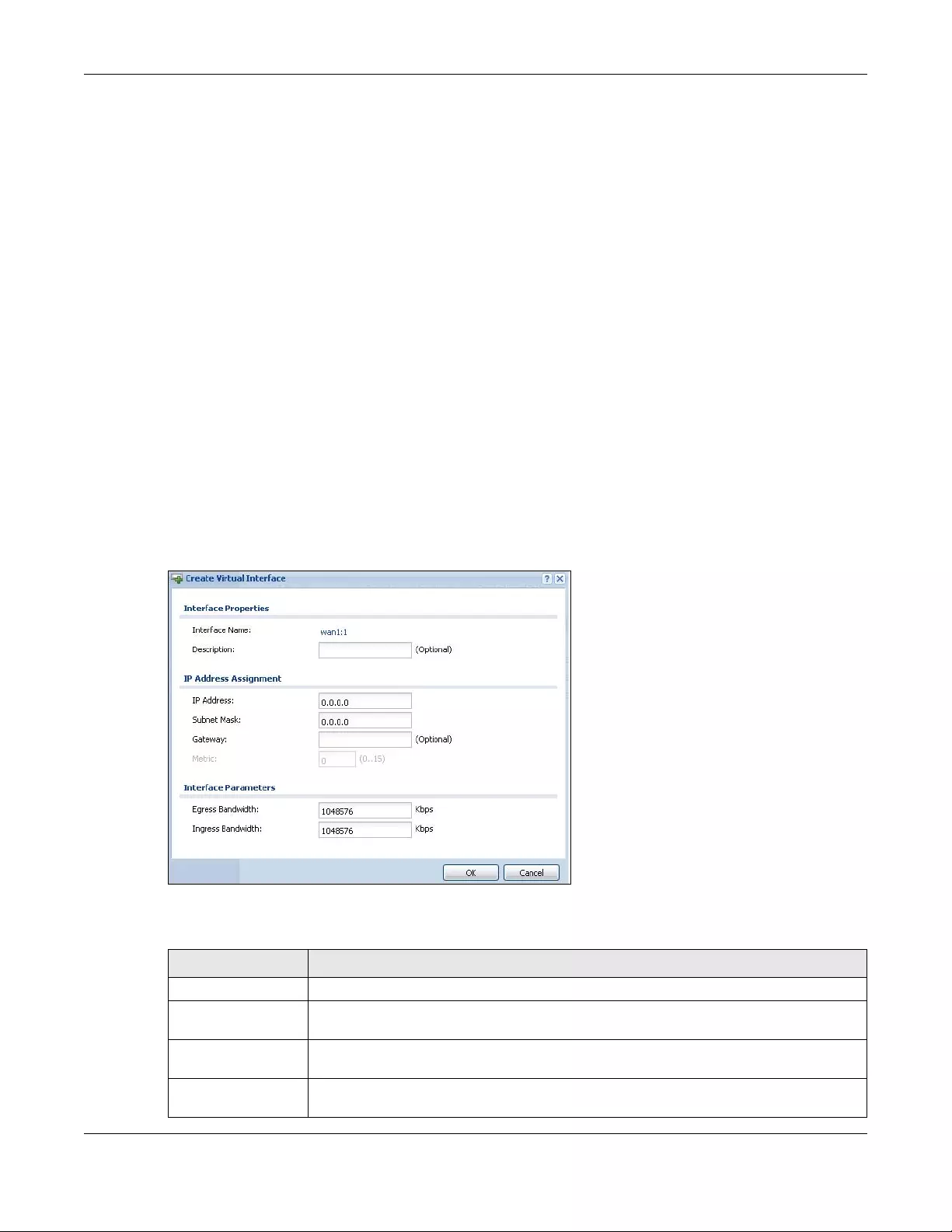
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
293
10.4.2 Virtual Interfaces
Use virtual interfaces to tell the Zyxel Device where to route packets. Virtual interfaces can also be used
in VPN gateways (see Chapter 30 on page 545) and VRRP groups (see Chapter 42 on page 718).
Virtual interfaces can be created on top of Ethernet interfaces, VLAN interfaces, or bridge interfaces.
Virtual VLAN interfaces recognize and use the same VLAN ID. Otherwise, there is no difference between
each type of virtual interface. Network policies (for example, security policies) that apply to the
underlying interface automatically apply to the virtual interface as well.
Like other interfaces, virtual interfaces have an IP address, subnet mask, and gateway used to make
routing decisions. However, you have to manually specify the IP address and subnet mask; virtual
interfaces cannot be DHCP clients. Like other interfaces, you can restrict bandwidth through virtual
interfaces, but you cannot change the MTU. The virtual interface uses the same MTU that the underlying
interface uses. Unlike other interfaces, virtual interfaces do not provide DHCP services, and they do not
verify that the gateway is available.
10.4.3 Virtual Interfaces Add/Edit
This screen lets you configure IP address assignment and interface parameters for virtual interfaces. To
access this screen, click the Create Virtual Interface icon in the Ethernet, VLAN, or bridge interface
summary screen.
Figure 230 Configuration > Network > Interface > Create Virtual Interface
Each field is described in the table below.
Table 102 Configuration > Network > Interface > Create Virtual Interface
LABEL DESCRIPTION
Interface Properties
Interface Name This field is read-only. It displays the name of the virtual interface, which is automatically
derived from the underlying Ethernet interface, VLAN interface, or bridge interface.
Description Enter a description of this interface. It is not used elsewhere. You can use alphanumeric and
()+/:=?!*#@$_%- characters, and it can be up to 60 characters long.
IP Address
Assignment
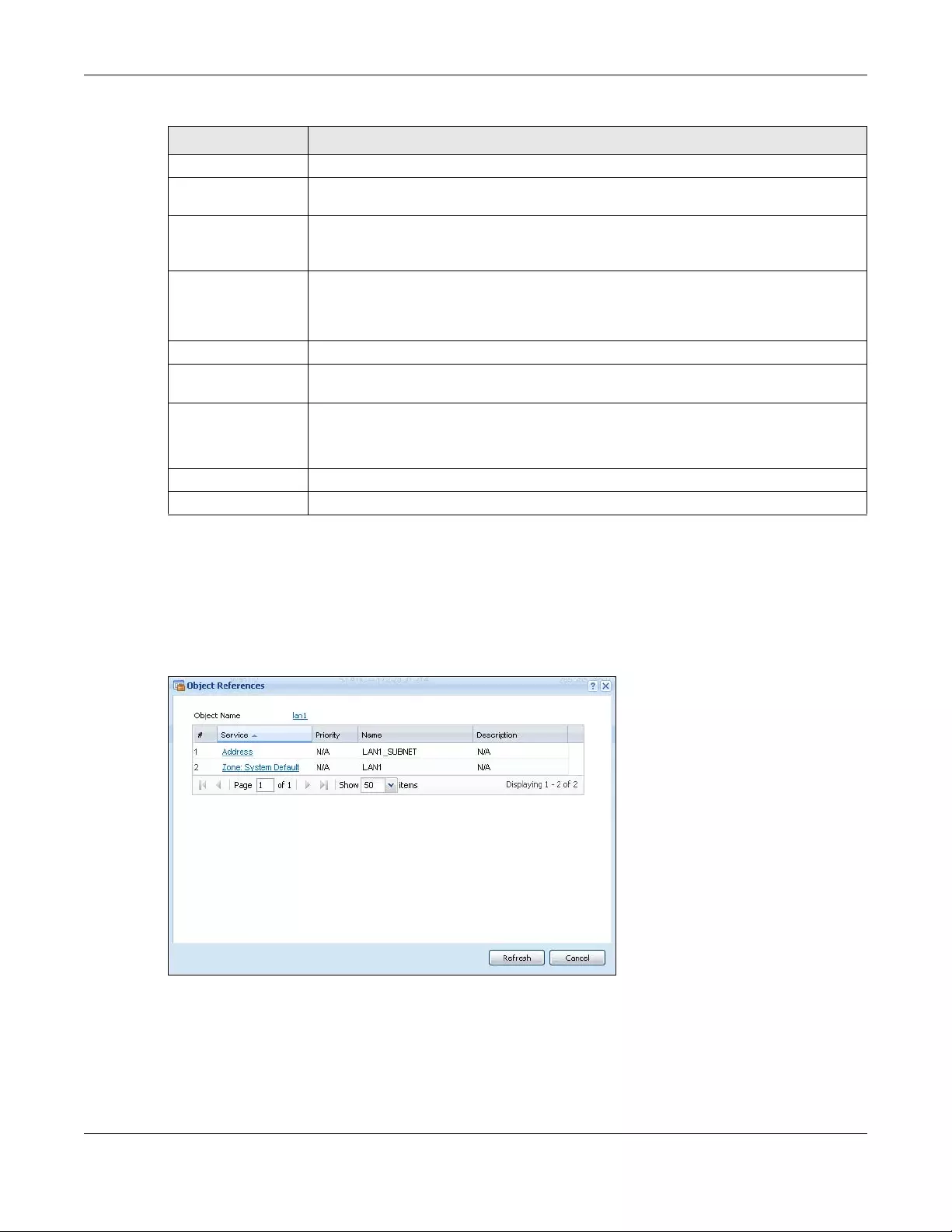
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
294
10.4.4 Object References
When a configuration screen includes an Object Reference icon, select a configuration object and
click Object Reference to open the Object References screen. This screen displays which configuration
settings reference the selected object. The fields shown vary with the type of object.
Figure 231 Object References
IP Address Enter the IP address for this interface.
Subnet Mask Enter the subnet mask of this interface in dot decimal notation. The subnet mask indicates
what part of the IP address is the same for all computers in the network.
Gateway Enter the IP address of the gateway. The Zyxel Device sends packets to the gateway when
it does not know how to route the packet to its destination. The gateway should be on the
same network as the interface.
Metric Enter the priority of the gateway (if any) on this interface. The Zyxel Device decides which
gateway to use based on this priority. The lower the number, the higher the priority. If two or
more gateways have the same priority, the Zyxel Device uses the one that was configured
first.
Interface Parameters
Egress Bandwidth Enter the maximum amount of traffic, in kilobits per second, the Zyxel Device can send
through the interface to the network. Allowed values are 0 - 1048576.
Ingress
Bandwidth This is reserved for future use.
Enter the maximum amount of traffic, in kilobits per second, the Zyxel Device can receive
from the network through the interface. Allowed values are 0 - 1048576.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 102 Configuration > Network > Interface > Create Virtual Interface (continued)
LABEL DESCRIPTION
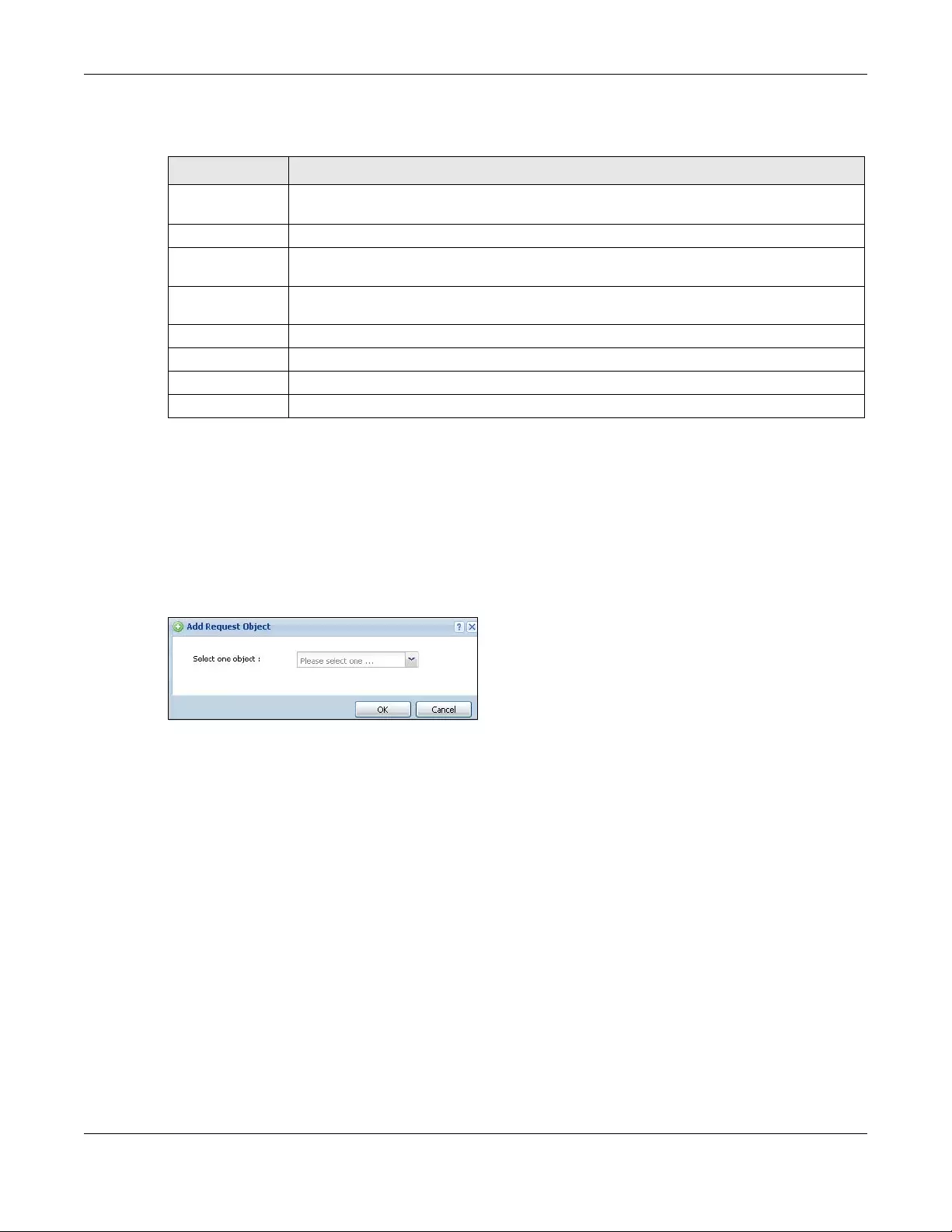
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
295
The following table describes labels that can appear in this screen.
10.4.5 Add/Edit DHCPv6 Request/Release Options
When you configure an interface as a DHCPv6 server or client, you can additionally add DHCPv6
request or lease options which have the Zyxel Device to add more information in the DHCPv6 packets.
To open the screen, click Configuration > Network > Interface > Ethernet > Edit, select DHCPv6 Server or
DHCPv6 Client in the DHCPv6 Setting section, and then click Add in the DHCPv6 Request Options or
DHCPv6 Lease Options table.
Figure 232 Configuration > Network > Interface > Ethernet > Edit > Add DHCPv6 Request/Lease Options
Select a DHCPv6 request or lease object in the Select one object field and click OK to save it. Click
Cancel to exit without saving the setting.
10.4.6 Add/Edit DHCP Extended Options
When you configure an interface as a DHCPv4 server, you can additionally add DHCP extended
options which have the Zyxel Device to add more information in the DHCP packets. The available fields
vary depending on the DHCP option you select in this screen. To open the screen, click Configuration >
Network > Interface > Ethernet > Edit, select DHCP Server in the DHCP Setting section, and then click Add
or Edit in the Extended Options table.
Table 103 Object References
LABEL DESCRIPTION
Object Name This identifies the object for which the configuration settings that use it are displayed. Click the
object’s name to display the object’s configuration screen in the main window.
# This field is a sequential value, and it is not associated with any entry.
Service This is the type of setting that references the selected object. Click a service’s name to display
the service’s configuration screen in the main window.
Priority If it is applicable, this field lists the referencing configuration item’s position in its list, otherwise
N/A displays.
Name This field identifies the configuration item that references the object.
Description If the referencing configuration item has a description configured, it displays here.
Refresh Click this to update the information in this screen.
Cancel Click Cancel to close the screen.
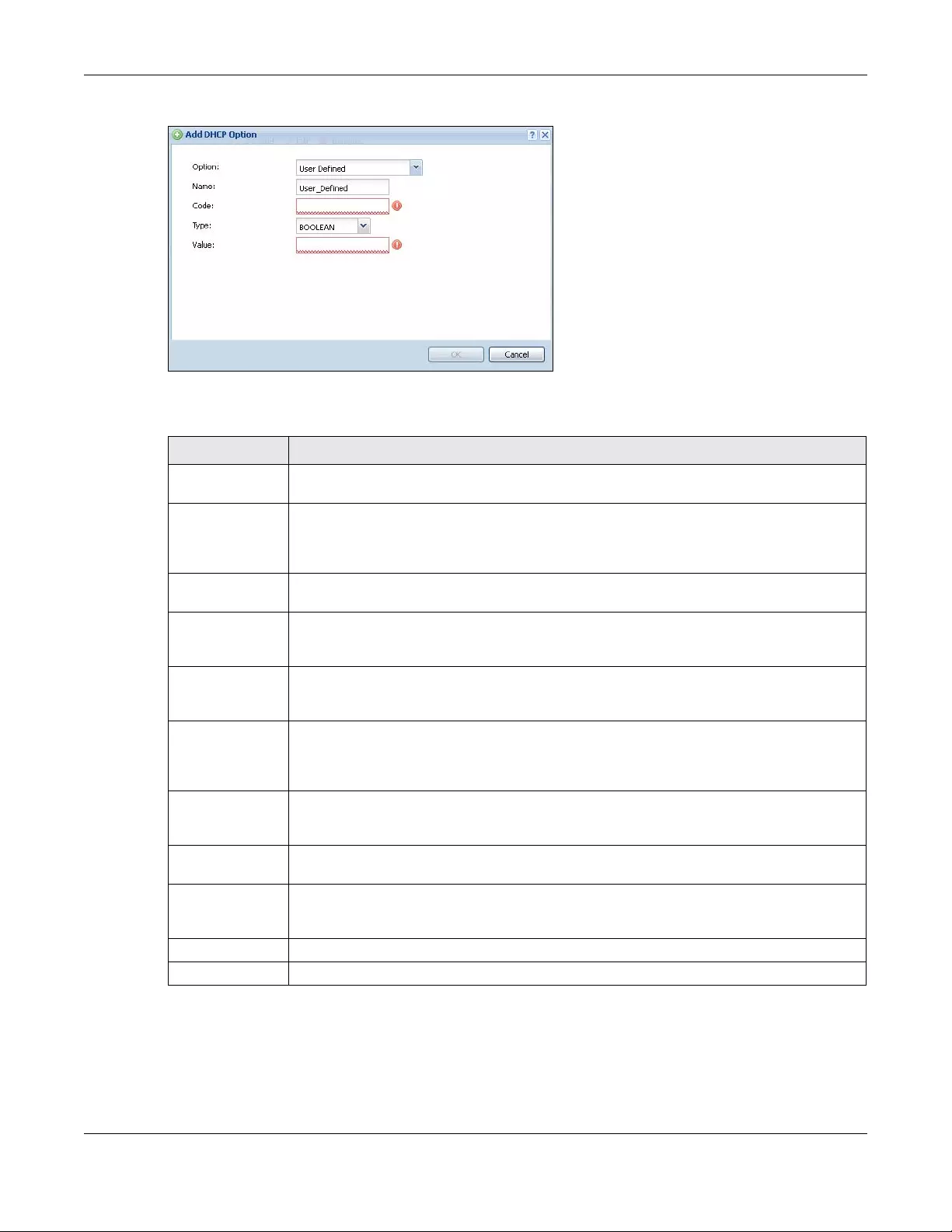
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
296
Figure 233 Configuration > Network > Interface > Ethernet > Edit > Add/Edit Extended Options
The following table describes labels that can appear in this screen.
Table 104 Configuration > Network > Interface > Ethernet > Edit > Add/Edit Extended Options
LABEL DESCRIPTION
Option Select which DHCP option that you want to add in the DHCP packets sent through the
interface. See the next table for more information.
Name This field displays the name of the selected DHCP option. If you selected User Defined in the
Option field, enter a descriptive name to identify the DHCP option. You can enter up to 16
characters (“a-z”, “A-Z, “0-9”, “-”, and “_”) with no spaces allowed. The first character must be
alphabetical (a-z, A-Z).
Code This field displays the code number of the selected DHCP option. If you selected User Defined
in the Option field, enter a number for the option. This field is mandatory.
Type This is the type of the selected DHCP option. If you selected User Defined in the Option field,
select an appropriate type for the value that you will enter in the next field. Only advanced
users should configure User Defined. Misconfiguration could result in interface lockout.
Value Enter the value for the selected DHCP option. For example, if you selected TFTP Server Name
(66) and the type is TEXT, enter the DNS domain name of a TFTP server here. This field is
mandatory.
First IP Address,
Second IP
Address, Third IP
Address
If you selected Time Server (4), NTP Server (41), SIP Server (120), CAPWAP AC (138), or TFTP
Server (150), you have to enter at least one IP address of the corresponding servers in these
fields. The servers should be listed in order of your preference.
First Enterprise ID,
Second Enterprise
ID
If you selected VIVC (124) or VIVS (125), you have to enter at least one vendor’s 32-bit
enterprise number in these fields. An enterprise number is a unique number that identifies a
company.
First Class, Second
Class
If you selected VIVC (124), enter the details of the hardware configuration of the host on
which the client is running, or of industry consortium compliance.
First Information,
Second
Information
If you selected VIVS (125), enter additional information for the corresponding enterprise
number in these fields.
OK Click this to close this screen and update the settings to the previous Edit screen.
Cancel Click Cancel to close the screen.
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
297
The following table lists the available DHCP extended options (defined in RFCs) on the Zyxel Device. See
RFCs for more information.
10.5 PPP Interfaces
Use PPPoE/PPTP/L2TP interfaces to connect to your ISP. This way, you do not have to install or manage
PPPoE/PPTP/L2TP software on each computer in the network.
Figure 234 Example: PPPoE/PPTP/L2TP Interfaces
Table 105 DHCP Extended Options
OPTION NAME CODE DESCRIPTION
Time Offset 2 This option specifies the offset of the client's subnet in seconds from Coordinated
Universal Time (UTC).
Time Server 4 This option specifies a list of Time servers available to the client.
NTP Server 42 This option specifies a list of the NTP servers available to the client by IP address.
TFTP Server Name 66 This option is used to identify a TFTP server when the “sname” field in the DHCP
header has been used for DHCP options. The minimum length of the value is 1.
Bootfile 67 This option is used to identify a bootfile when the “file” field in the DHCP header
has been used for DHCP options. The minimum length of the value is 1.
SIP Server 120 This option carries either an IPv4 address or a DNS domain name to be used by
the SIP client to locate a SIP server.
VIVC 124 Vendor-Identifying Vendor Class option
A DHCP client may use this option to unambiguously identify the vendor that
manufactured the hardware on which the client is running, the software in use, or
an industry consortium to which the vendor belongs.
VIVS 125 Vendor-Identifying Vendor-Specific option
DHCP clients and servers may use this option to exchange vendor-specific
information.
CAPWAP AC 138 CAPWAP Access Controller addresses option
The Control And Provisioning of Wireless Access Points Protocol allows a Wireless
Termination Point (WTP) to use DHCP to discover the Access Controllers to which it
is to connect. This option carries a list of IPv4 addresses indicating one or more
CAPWAP ACs available to the WTP.
TFTP Server 150 The option contains one or more IPv4 addresses that the client may use. The
current use of this option is for downloading configuration from a VoIP server via
TFTP; however, the option may be used for purposes other than contacting a
VoIP configuration server.
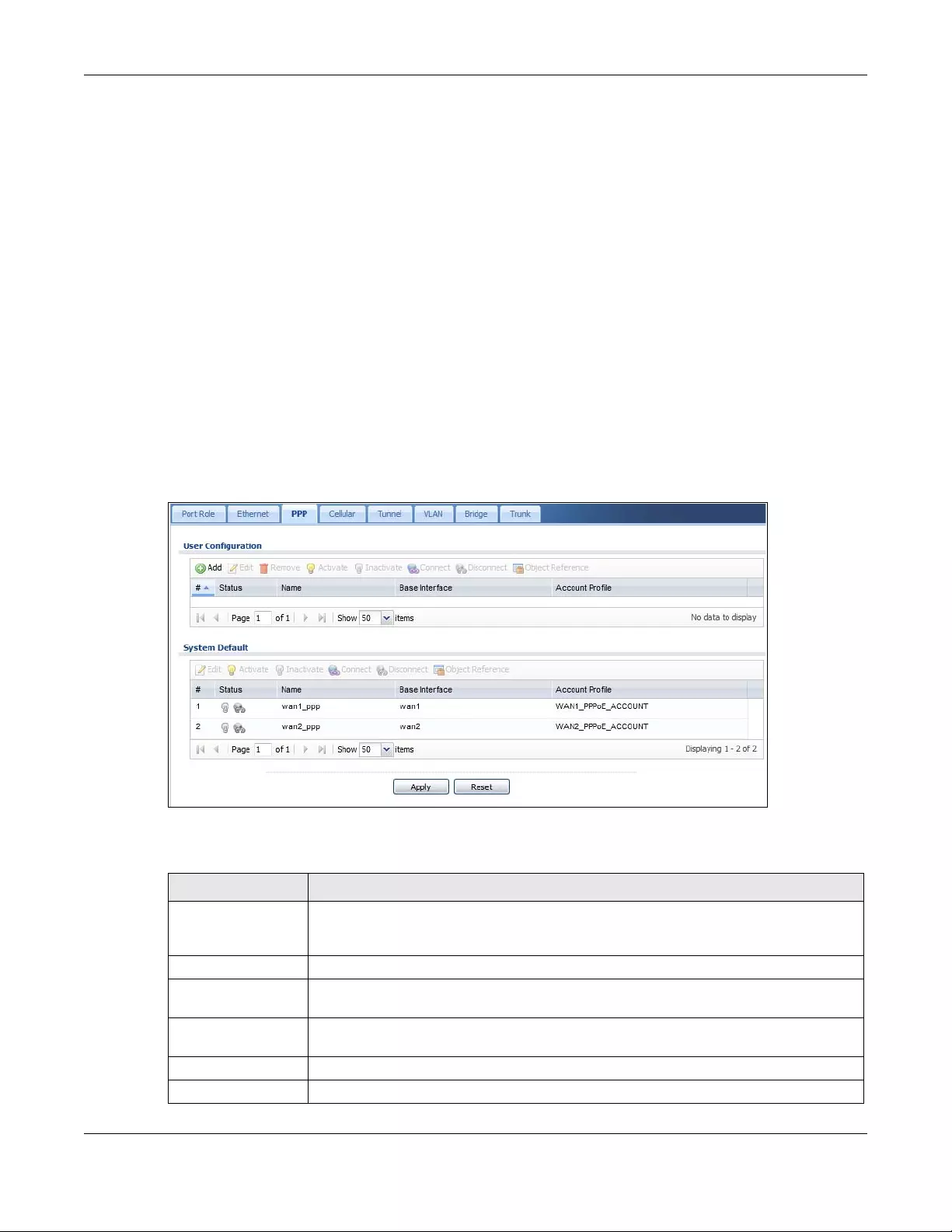
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
298
PPPoE/PPTP/L2TP interfaces are similar to other interfaces in some ways. They have an IP address, subnet
mask, and gateway used to make routing decisions; they restrict bandwidth and packet size; and they
can verify the gateway is available. There are two main differences between PPPoE/PPTP/L2TP
interfaces and other interfaces.
• You must also configure an ISP account object for the PPPoE/PPTP/L2TP interface to use.
Each ISP account specifies the protocol (PPPoE or PPTP or L2TP), as well as your ISP account
information. If you change ISPs later, you only have to create a new ISP account, not a new PPPoE/
PPTP/L2TP interface. You should not have to change any network policies.
• You do not set up the subnet mask or gateway.
PPPoE/PPTP/L2TP interfaces are interfaces between the Zyxel Device and only one computer.
Therefore, the subnet mask is always 255.255.255.255. In addition, the Zyxel Device always treats the
ISP as a gateway.
10.5.1 PPP Interface Summary
This screen lists every PPPoE/PPTP/L2TP interface. To access this screen, click Configuration > Network >
Interface > PPP.
Figure 235 Configuration > Network > Interface > PPP
Each field is described in the table below.
Table 106 Configuration > Network > Interface > PPP
LABEL DESCRIPTION
User Configuration /
System Default
The Zyxel Device comes with the (non-removable) System Default PPP interfaces pre-
configured. You can create (and delete) User Configuration PPP interfaces. System Default
PPP interfaces vary by model.
Add Click this to create a new user-configured PPP interface.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove a user-configured PPP interface, select it and click Remove. The Zyxel Device
confirms you want to remove it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
299
10.5.2 PPP Interface Add or Edit
Note: You have to set up an ISP account before you create a PPPoE/PPTP/L2TP interface.
This screen lets you configure a PPPoE or PPTP or L2TP interface. If you enabled IPv6 in the Configuration
> System > IPv6 screen, you can also configure PPP interfaces used for your IPv6 networks on this screen.
To access this screen, click the Add icon or an Edit icon in the PPP Interface screen.
Connect To connect an interface, select it and click Connect. You might use this in testing the
interface or to manually establish the connection for a Dial-on-Demand PPPoE/PPTP
interface.
Disconnect To disconnect an interface, select it and click Disconnect. You might use this in testing the
interface.
Object References Select an entry and click Object Reference to open a screen that shows which settings use
the entry. See Section 10.4.4 on page 294 for an example.
# This field is a sequential value, and it is not associated with any interface.
Status The activate (light bulb) icon is lit when the entry is active and dimmed when the entry is
inactive.
The connect icon is lit when the interface is connected and dimmed when it is
disconnected.
Name This field displays the name of the interface.
Base Interface This field displays the interface on the top of which the PPPoE/PPTP/L2TP interface is.
Account Profile This field displays the ISP account used by this PPPoE/PPTP interface.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 106 Configuration > Network > Interface > PPP (continued)
LABEL DESCRIPTION
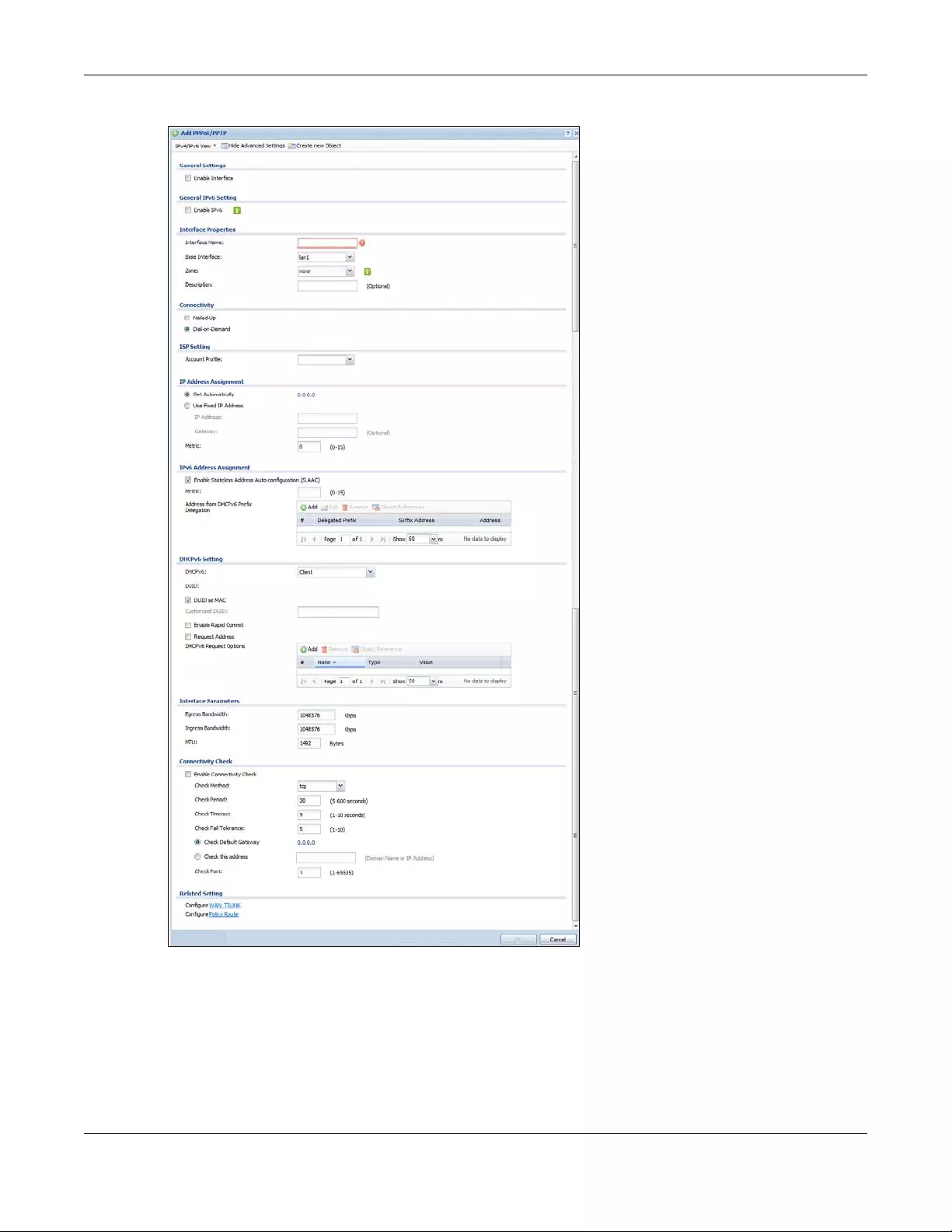
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
300
Figure 236 Configuration > Network > Interface > PPP > Add
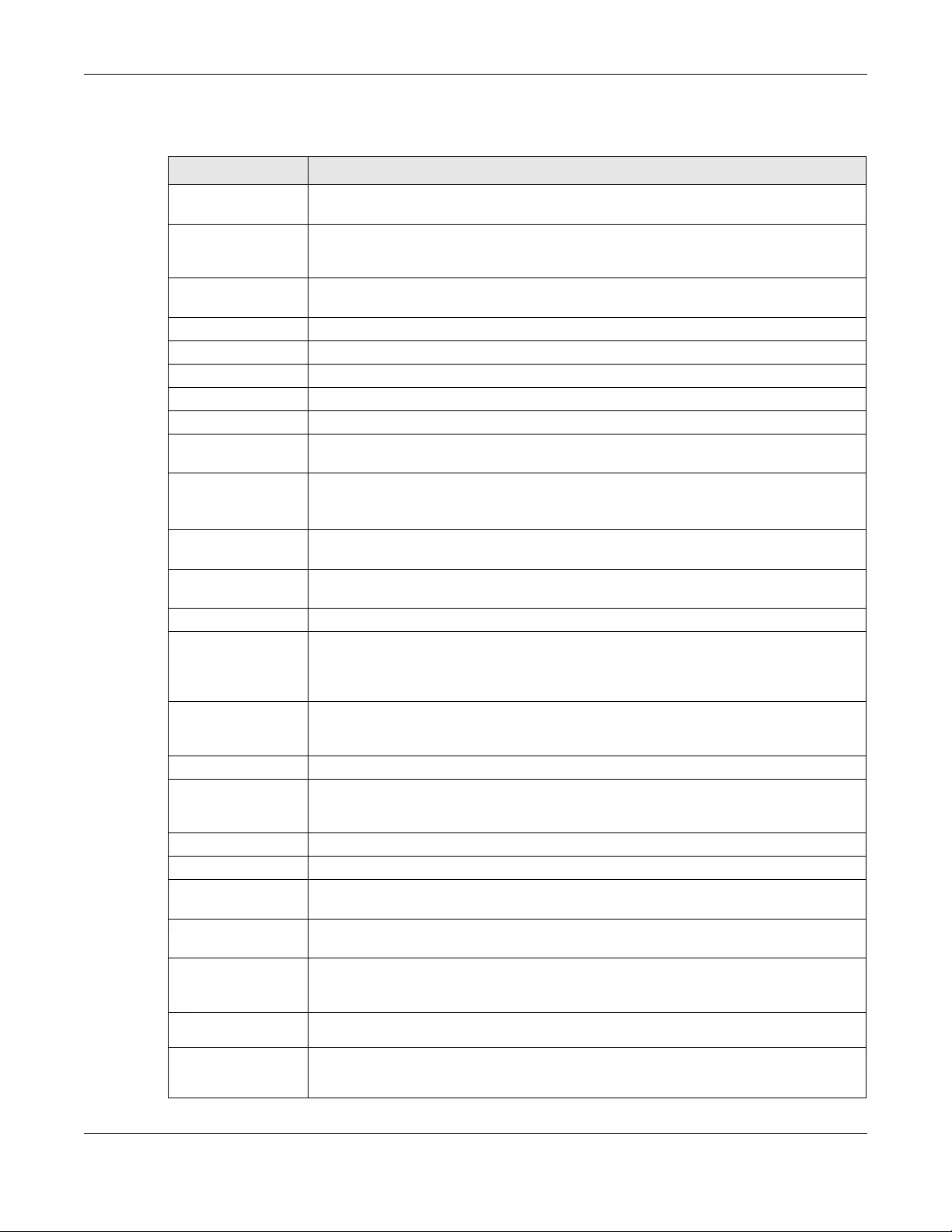
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
301
Each field is explained in the following table.
Table 107 Configuration > Network > Interface > PPP > Add
LABEL DESCRIPTION
IPv4/IPv6 View / IPv4
View / IPv6 View
Use this button to display both IPv4 and IPv6, IPv4-only, or IPv6-only configuration fields.
Show Advanced
Settings / Hide
Advanced Settings
Click this button to display a greater or lesser number of configuration fields.
Create New Object Click this button to create an ISP Account or a DHCPv6 request object that you may use for
the ISP or DHCPv6 settings in this screen.
General Settings
Enable Interface Select this to enable this interface. Clear this to disable this interface.
General IPv6 Setting
Enable IPv6 Select this to enable IPv6 on this interface. Otherwise, clear this to disable it.
Interface Properties
Interface Name Specify a name for the interface. It can use alphanumeric characters, hyphens, and
underscores, and it can be up to 11 characters long.
Base Interface Select the interface upon which this PPP interface is built.
Note: Multiple PPP interfaces can use the same base interface.
Zone Select the zone to which this PPP interface belongs. The zone determines the security
settings the Zyxel Device uses for the interface.
Description Enter a description of this interface. It is not used elsewhere. You can use alphanumeric and
()+/:=?!*#@$_%- characters, and it can be up to 60 characters long.
Connectivity
Nailed-Up Select this if the PPPoE/PPTP/L2TP connection should always be up. Clear this to have the
Zyxel Device establish the PPPoE/PPTP/L2TP connection only when there is traffic. You might
use this option if a lot of traffic needs to go through the interface or it does not cost extra to
keep the connection up all the time.
Dial-on-Demand Select this to have the Zyxel Device establish the PPPoE/PPTP/L2TP connection only when
there is traffic. You might use this option if there is little traffic through the interface or if it
costs money to keep the connection available.
ISP Setting
Account Profile Select the ISP account that this PPPoE/PPTP/L2TP interface uses. The drop-down box lists ISP
accounts by name. Use Create new Object if you need to configure a new ISP account
(see Chapter 43 on page 819 for details).
Protocol This field is read-only. It displays the protocol specified in the ISP account.
User Name This field is read-only. It displays the user name for the ISP account.
Service Name This field is read-only. It displays the PPPoE service name specified in the ISP account. This
field is blank if the ISP account uses PPTP.
IP Address
Assignment
Click Show Advanced Settings to display more settings. Click Hide Advanced Settings to
display fewer settings.
Get
Automatically Select this if this interface is a DHCP client. In this case, the DHCP server configures the IP
address automatically. The subnet mask and gateway are always defined automatically in
PPPoE/PPTP/L2TP interfaces.
Use Fixed IP
Address Select this if you want to specify the IP address manually.
IP Address This field is enabled if you select Use Fixed IP Address.
Enter the IP address for this interface.
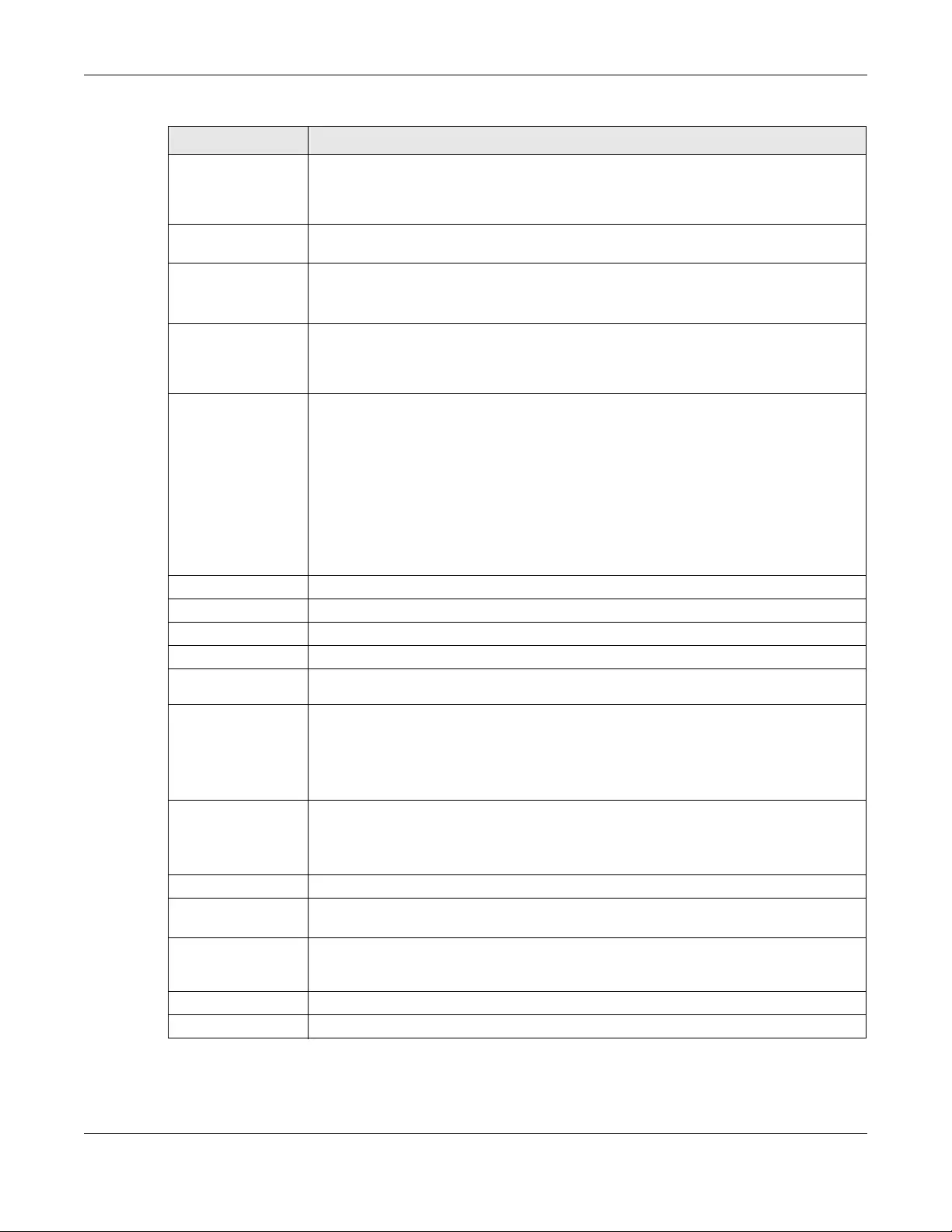
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
302
Metric Enter the priority of the gateway (the ISP) on this interface. The Zyxel Device decides which
gateway to use based on this priority. The lower the number, the higher the priority. If two or
more gateways have the same priority, the Zyxel Device uses the one that was configured
first.
IPv6 Address
Assignment
These IP address fields configure an IPv6 IP address on the interface itself.
Enable Stateless
Address Auto-
configuration
(SLAAC)
Select this to enable IPv6 stateless auto-configuration on this interface. The interface will
generate an IPv6 IP address itself from a prefix obtained from an IPv6 router in the network.
Metric Enter the priority of the gateway (if any) on this interface. The Zyxel Device decides which
gateway to use based on this priority. The lower the number, the higher the priority. If two or
more gateways have the same priority, the Zyxel Device uses the one that was configured
first.
Address from
DHCPv6 Prefix
Delegation
Use this table to have the Zyxel Device obtain an IPv6 prefix from the ISP or a connected
uplink router for an internal network, such as the LAN or DMZ. You have to also enter a suffix
address which is appended to the delegated prefix to form an address for this interface.
See Prefix Delegation on page 273 for more information.
To use prefix delegation, you must:
• Create at least one DHCPv6 request object before configuring this table.
• The external interface must be a DHCPv6 client. You must configure the DHCPv6
request options using a DHCPv6 request object with the type of prefix-delegation.
• Assign the prefix delegation to an internal interface and enable router advertisement
on that interface.
Add Click this to create an entry.
Edit Select an entry and click this to change the settings.
Remove Select an entry and click this to delete it from this table.
# This field is a sequential value, and it is not associated with any entry.
Delegated
Prefix Select the DHCPv6 request object to use from the drop-down list.
Suffix
Address Enter the ending part of the IPv6 address, a slash (/), and the prefix length. The Zyxel Device
will append it to the delegated prefix.
For example, you got a delegated prefix of 2003:1234:5678/48. You want to configure an IP
address of 2003:1234:5678:1111::1/128 for this interface, then enter ::1111:0:0:0:1/128 in this
field.
Address This field displays the combined IPv6 IP address for this interface.
Note: This field displays the combined address after you click OK and reopen this
screen.
DHCPv6 Setting
DHCPv6 Select Client to obtain an IP address and DNS information from the service provider for the
interface. Otherwise, select N/A to disable the function.
DUID This field displays the DHCP Unique IDentifier (DUID) of the interface, which is unique and
used for identification purposes when the interface is exchanging DHCPv6 messages with
others. See DHCPv6 on page 274 for more information.
DUID as MAC Select this if you want the DUID is generated from the interface’s default MAC address.
Customized DUID If you want to use a customized DUID, enter it here for the interface.
Table 107 Configuration > Network > Interface > PPP > Add (continued)
LABEL DESCRIPTION
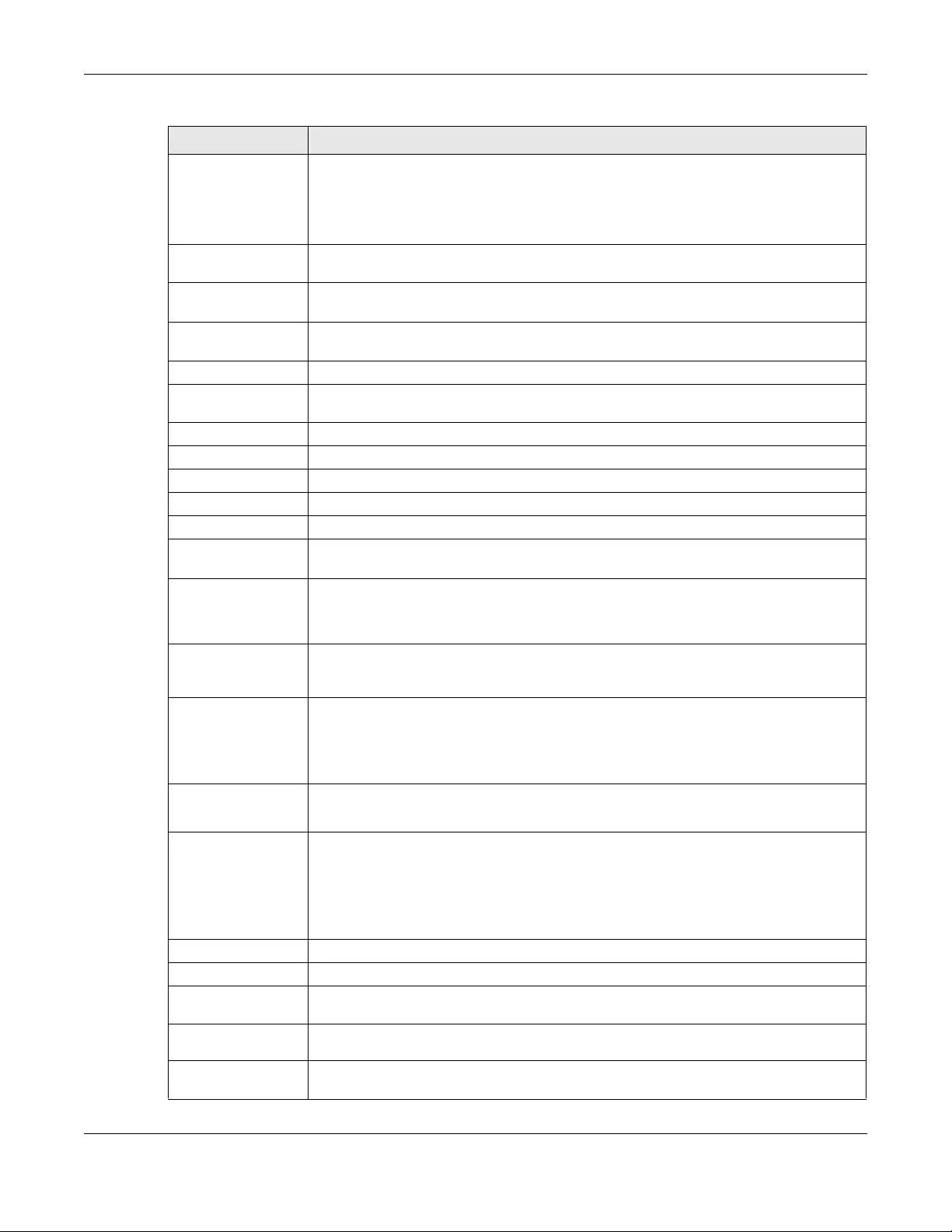
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
303
Enable Rapid
Commit Select this to shorten the DHCPv6 message exchange process from four to two steps. This
function helps reduce heavy network traffic load.
Note: Make sure you also enable this option in the DHCPv6 clients to make rapid
commit work.
Request Address Select this to get an IPv6 IP address for this interface from the DHCP server. Clear this to not
get any IP address information through DHCPv6.
DHCPv6 Request
Options Use this section to configure DHCPv6 request settings that determine what additional
information to get from the DHCPv6 server.
Add Click this to create an entry in this table. See Section 10.4.6 on page 295 for more
information.
Remove Select an entry and click this to delete it from this table.
Object
Reference Select an entry and click Object Reference to open a screen that shows which settings use
the entry. See Section 10.4.4 on page 294 for an example.
# This field is a sequential value, and it is not associated with any entry.
Name This field displays the name of the DHCPv6 request object.
Type This field displays the type of the object.
Value This field displays the IPv6 prefix that the Zyxel Device will advertise to its clients.
Interface Parameters
Egress Bandwidth Enter the maximum amount of traffic, in kilobits per second, the Zyxel Device can send
through the interface to the network. Allowed values are 0 - 1048576.
Ingress
Bandwidth This is reserved for future use.
Enter the maximum amount of traffic, in kilobits per second, the Zyxel Device can receive
from the network through the interface. Allowed values are 0 - 1048576.
MTU Maximum Transmission Unit. Type the maximum size of each data packet, in bytes, that can
move through this interface. If a larger packet arrives, the Zyxel Device divides it into smaller
fragments. Allowed values are 576 - 1492. Usually, this value is 1492.
Connectivity Check The interface can regularly check the connection to the gateway you specified to make
sure it is still available. You specify how often the interface checks the connection, how
long to wait for a response before the attempt is a failure, and how many consecutive
failures are required before the Zyxel Device stops routing to the gateway. The Zyxel Device
resumes routing to the gateway the first time the gateway passes the connectivity check.
Enable
Connectivity
Check
Select this to turn on the connection check.
Check Method Select the method that the gateway allows.
Select icmp to have the Zyxel Device regularly ping the gateway you specify to make sure
it is still available.
Select tcp to have the Zyxel Device regularly perform a TCP handshake with the gateway
you specify to make sure it is still available.
Check Period Enter the number of seconds between connection check attempts.
Check Timeout Enter the number of seconds to wait for a response before the attempt is a failure.
Check Fail
Tolerance Enter the number of consecutive failures before the Zyxel Device stops routing through the
gateway.
Check Default
Gateway Select this to use the default gateway for the connectivity check.
Check this
address Select this to specify a domain name or IP address for the connectivity check. Enter that
domain name or IP address in the field next to it.
Table 107 Configuration > Network > Interface > PPP > Add (continued)
LABEL DESCRIPTION
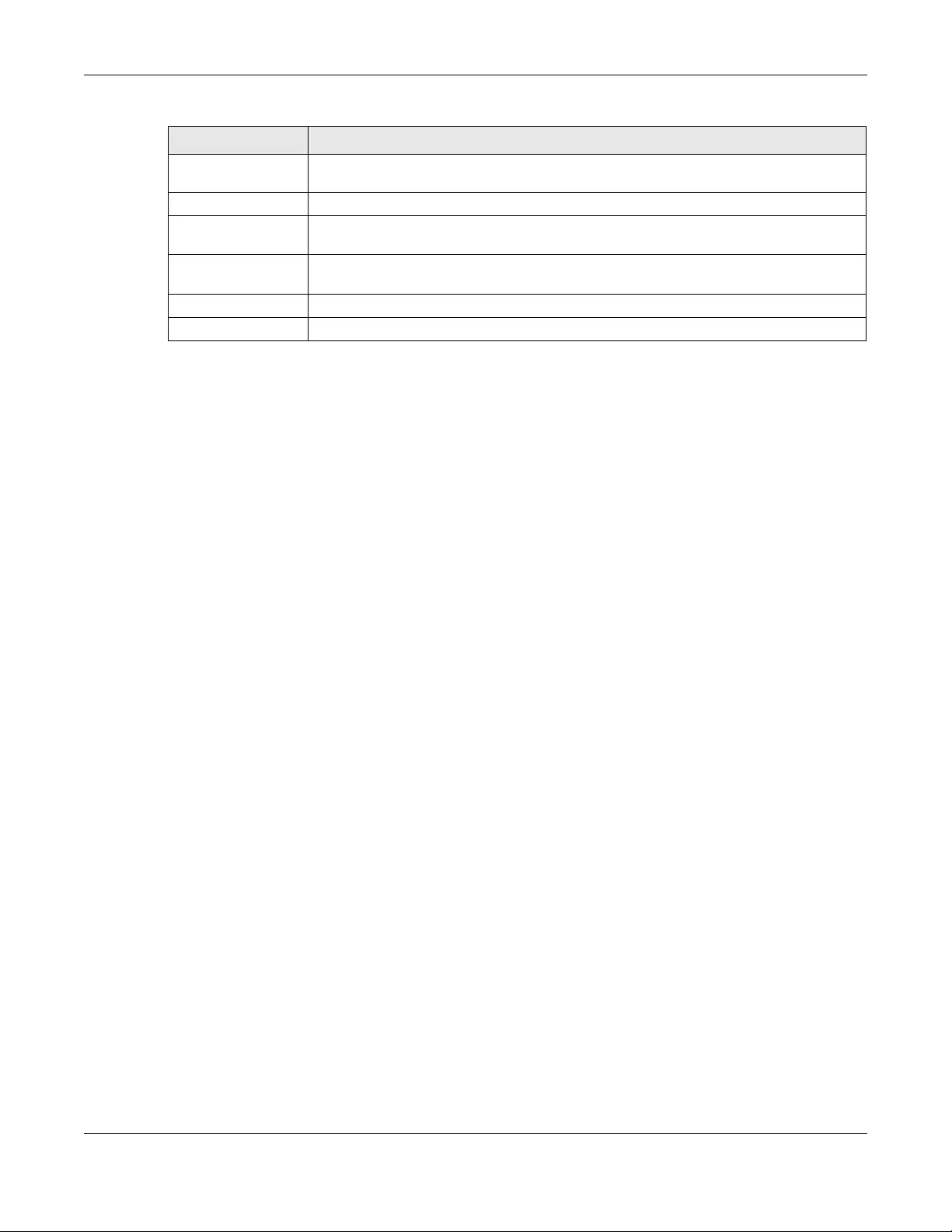
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
304
10.6 Cellular Configuration Screen
Mobile broadband is a digital, packet-switched wireless technology. Bandwidth usage is optimized as
multiple users share the same channel and bandwidth is only allocated to users when they send data. It
allows fast transfer of voice and non-voice data and provides broadband Internet access to mobile
devices.
Note: The actual data rate you obtain varies depending on the mobile broadband device
you use, the signal strength to the service provider’s base station, and so on.
You can configure how the Zyxel Device’s mobile broadband device connects to a network (refer to
Section 10.6.1 on page 307):
• You can set the mobile broadband device to connect only to the home network, which is the
network to which you are originally subscribed.
• You can set the mobile broadband device to connect to other networks if the signal strength of the
home network is too low or it is unavailable.
3G
3G (Third Generation) is a digital, packet-switched wireless technology. Bandwidth usage is optimized as
multiple users share the same channel and bandwidth is only allocated to users when they send data. It
allows fast transfer of voice and non-voice data and provides broadband Internet access to mobile
devices.
4G
4G is the fourth generation of the mobile telecommunications technology and a successor of 3G. Both
the WiMAX and Long Term Evolution (LTE) standards are the 4G candidate systems. 4G only supports all-
IP-based packet-switched telephony services and is required to offer Gigabit speed access.
Note: The actual data rate you obtain varies depending on your mobile environment. The
environmental factors may include the number of mobile devices which are currently
connected to the mobile network, the signal strength to the mobile network, and so on.
Check Port This field only displays when you set the Check Method to tcp. Specify the port number to
use for a TCP connectivity check.
Related Setting
Configure WAN
TRUNK Click WAN TRUNK to go to a screen where you can configure the interface as part of a
WAN trunk for load balancing.
Policy Route Click Policy Route to go to the screen where you can manually configure a policy route to
associate traffic with this interface.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 107 Configuration > Network > Interface > PPP > Add (continued)
LABEL DESCRIPTION
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
305
See the following table for a comparison between 2G, 2.5G, 2.75G, 3G and 4G wireless technologies.
To change your mobile broadband WAN settings, click Configuration > Network > Interface > Cellular.
Note: Install (or connect) a compatible mobile broadband USB device to use a cellular
connection.
Note: The WAN IP addresses of a Zyxel Device with multiple WAN interfaces must be on
different subnets.
Table 108 2G, 2.5G, 2.75G, 3G, 3.5G and 4G Wireless Technologies
NAME TYPE MOBILE PHONE AND DATA STANDARDS DATA
SPEED
GSM-BASED CDMA-BASED
2G Circuit-
switched
GSM (Global System for Mobile
Communications), Personal Handy-
phone System (PHS), etc.
Interim Standard 95 (IS-95), the first CDMA-based
digital cellular standard pioneered by Qualcomm.
The brand name for IS-95 is cdmaOne. IS-95 is also
known as TIA-EIA-95.
Slow
2.5G Packet-
switched
GPRS (General Packet Radio Services),
High-Speed Circuit-Switched Data
(HSCSD), etc.
CDMA2000 is a hybrid 2.5G / 3G protocol of mobile
telecommunications standards that use CDMA, a
multiple access scheme for digital radio.
CDMA2000 1xRTT (1 times Radio Transmission
Technology) is the core CDMA2000 wireless air
interface standard. It is also known as 1x, 1xRTT, or IS-
2000 and considered to be a 2.5G or 2.75G
technology.
2.75G Packet-
switched
Enhanced Data rates for GSM Evolution
(EDGE), Enhanced GPRS (EGPRS), etc.
3G Packet-
switched
UMTS (Universal Mobile
Telecommunications System), a third-
generation (3G) wireless standard
defined in ITU specification, is sometimes
marketed as 3GSM. The UMTS uses GSM
infrastructures and W-CDMA (Wideband
Code Division Multiple Access) as the air
interface. The International
Telecommunication Union (ITU) is an
international organization within which
governments and the private sector
coordinate global telecom networks
and services.
CDMA2000 EV-DO (Evolution-Data Optimized,
originally 1x Evolution-Data Only), also referred to as
EV-DO, EVDO, or just EV, is an evolution of
CDMA2000 1xRTT and enables high-speed wireless
connectivity. It is also denoted as IS-856 or High
Data Rate (HDR).
3.5G Packet-
switched
HSDPA (High-Speed Downlink Packet
Access) is a mobile telephony protocol,
used for UMTS-based 3G networks and
allows for higher data transfer speeds.
4G/LTE Packet-
switched
The LTE (Long Term Evolution) standard is
based on the GSM and UMTS network
technologies. Fast
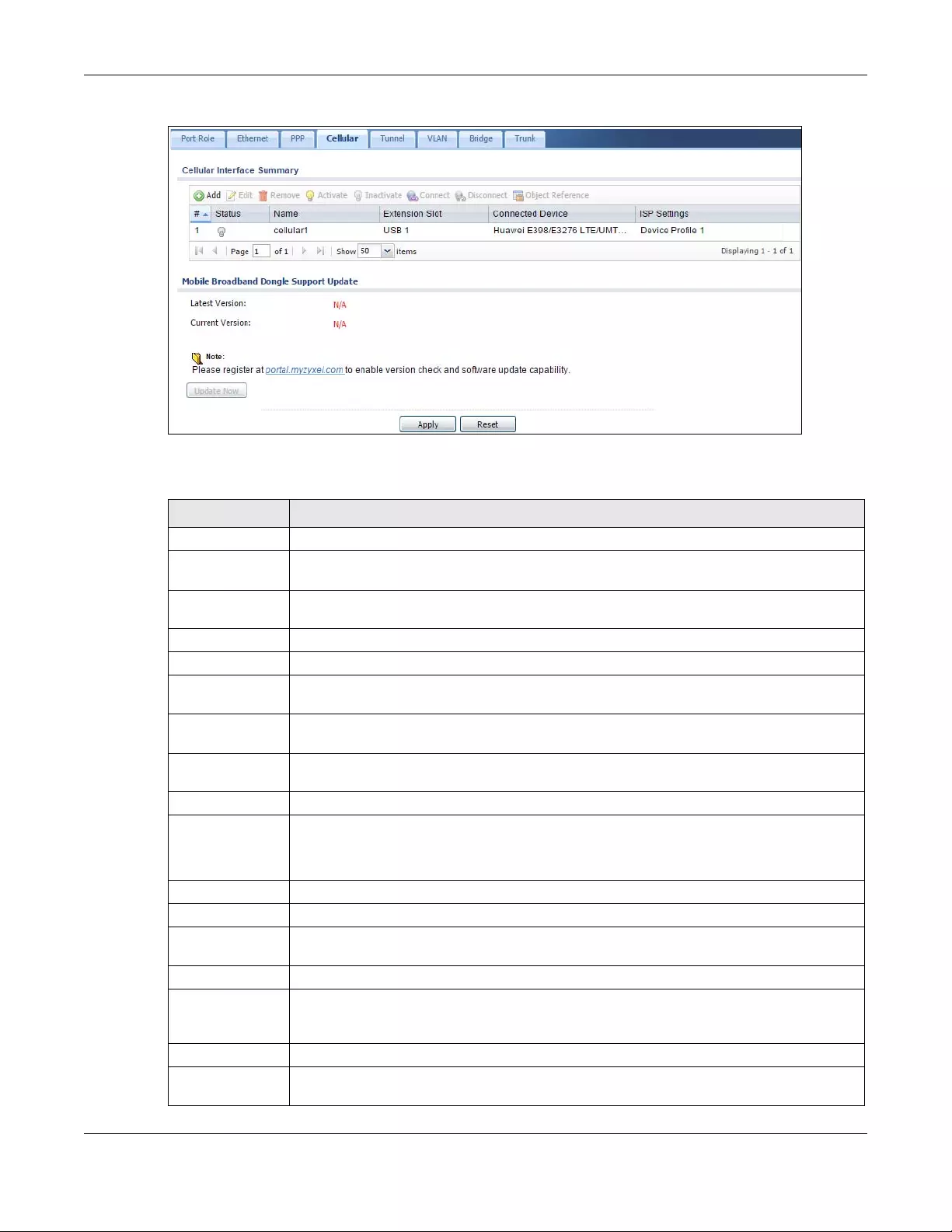
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
306
Figure 237 Configuration > Network > Interface > Cellular
The following table describes the labels in this screen.
Table 109 Configuration > Network > Interface > Cellular
LABEL DESCRIPTION
Add Click this to create a new cellular interface.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Connect To connect an interface, select it and click Connect. You might use this in testing the interface
or to manually establish the connection.
Disconnect To disconnect an interface, select it and click Disconnect. You might use this in testing the
interface.
Object
References
Select an entry and click Object Reference to open a screen that shows which settings use
the entry. See Section 10.4.4 on page 294 for an example.
# This field is a sequential value, and it is not associated with any interface.
Status The activate (light bulb) icon is lit when the entry is active and dimmed when the entry is
inactive.
The connect icon is lit when the interface is connected and dimmed when it is disconnected.
Name This field displays the name of the interface.
Extension Slot This field displays where the entry’s cellular card is located.
Connected
Device
This field displays the name of the cellular card.
ISP Settings This field displays the profile of ISP settings that this cellular interface is set to use.
Mobile
Broadband
Dongle Support
You should have registered your Zyxel Device at myzyxel.com. Myzyxel.com hosts a list of
supported mobile broadband dongle devices. You should have an Internet connection to
access this website.
Latest Version This displays the latest supported mobile broadband dongle list version number.
Current
Version This displays the currently supported (by the Zyxel Device) mobile broadband dongle list
version number.
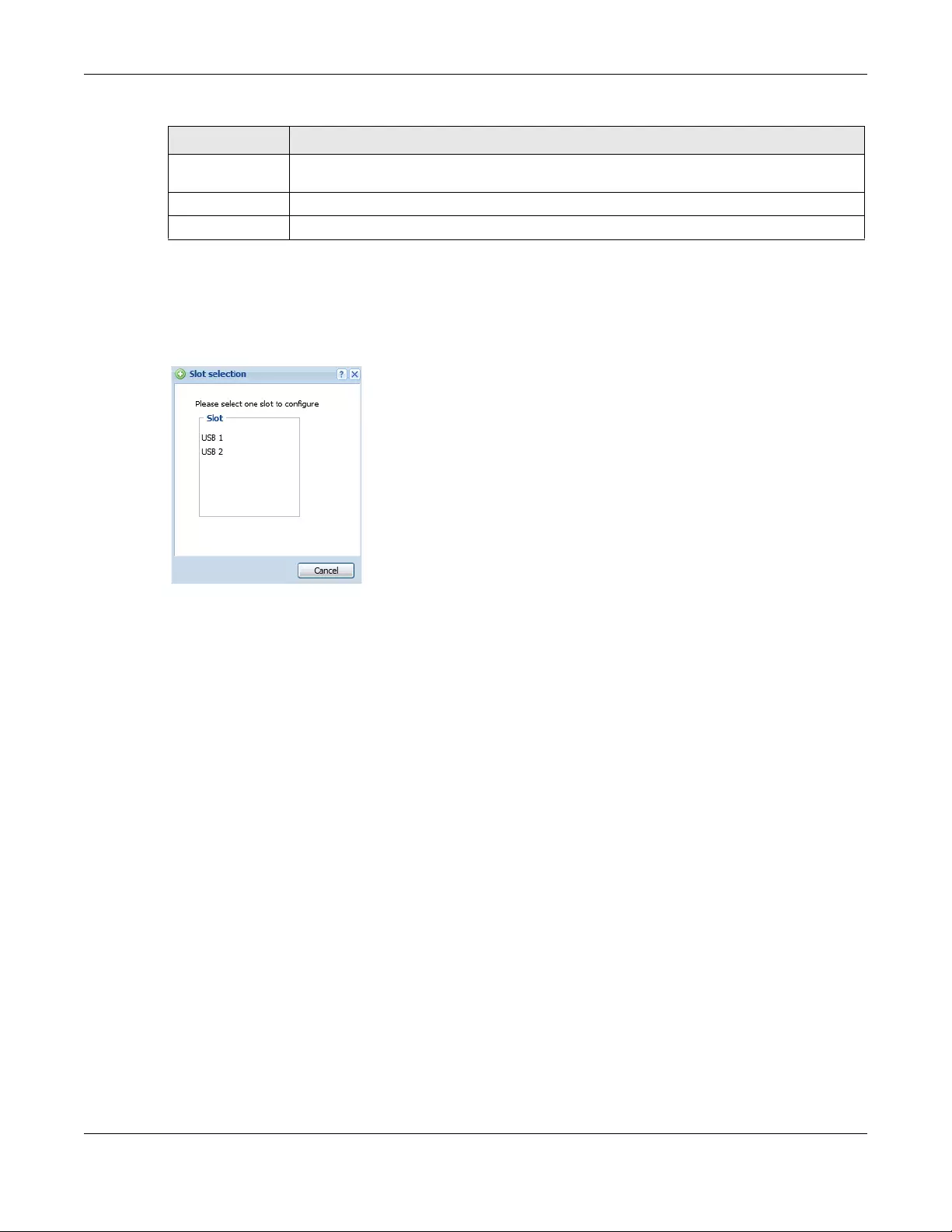
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
307
10.6.1 Cellular Choose Slot
To change your mobile broadband settings, click Configuration > Network > Interface > Cellular > Add
(or Edit). In the pop-up window that displays, select the slot that contains the mobile broadband device,
then the Add Cellular configuration screen displays.
10.6.2 Add / Edit Cellular Configuration
This screen displays after you select the slot that contains the mobile broadband device in the previous
pop-up window.
Update Now If the latest version number is greater than the current version number, then click this button to
download the latest list of supported mobile broadband dongle devices to the Zyxel Device.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 109 Configuration > Network > Interface > Cellular (continued)
LABEL DESCRIPTION
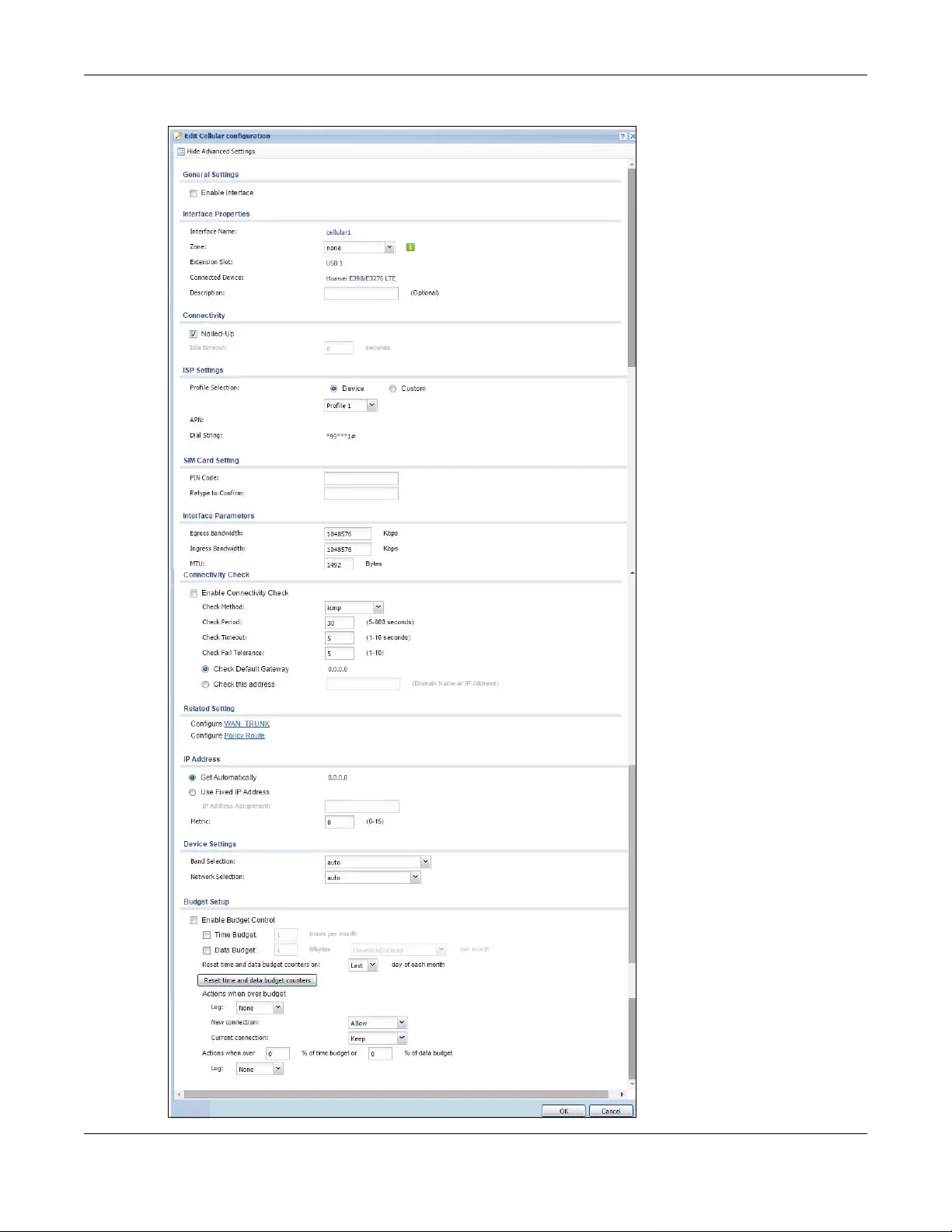
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
308
Figure 238 Configuration > Network > Interface > Cellular > Add / Edit
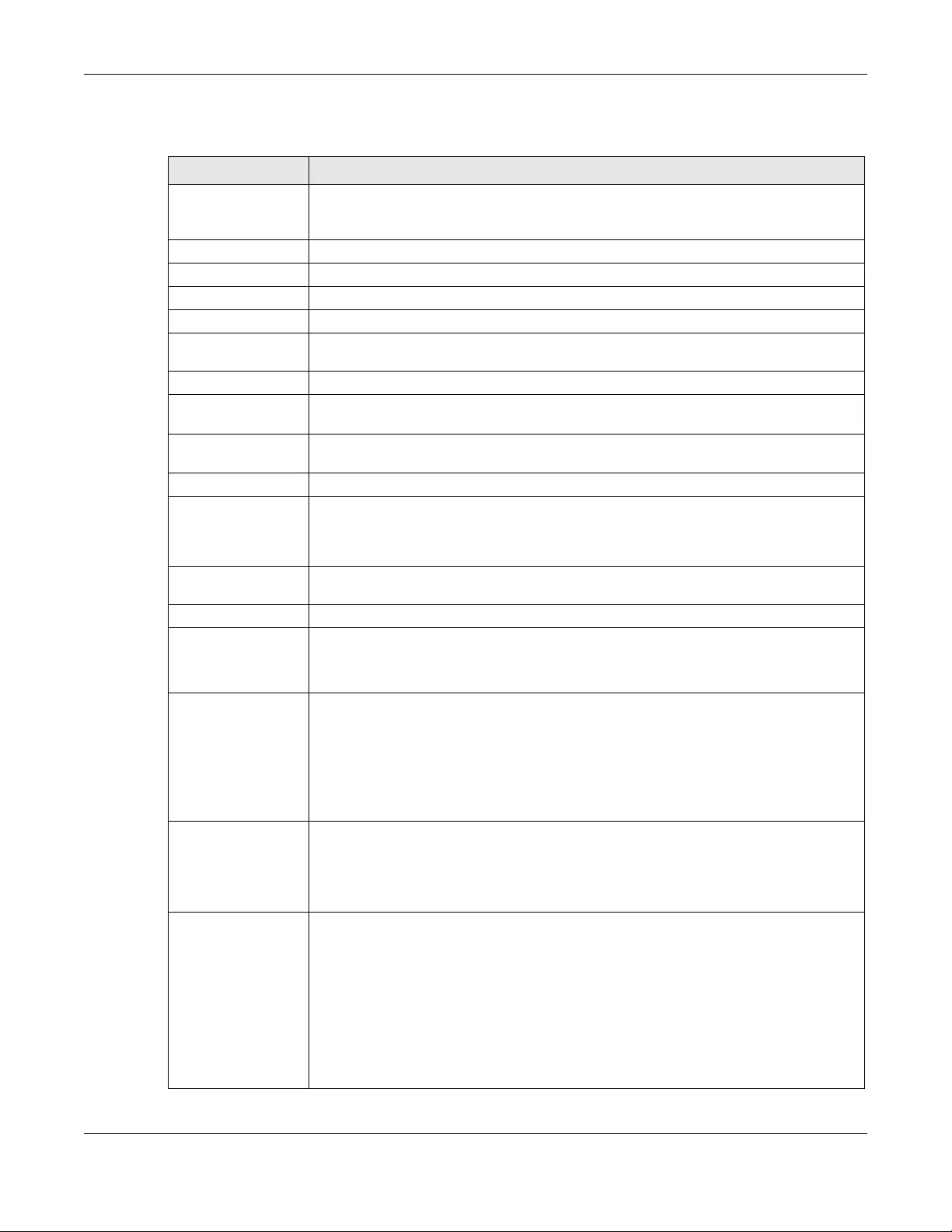
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
309
The following table describes the labels in this screen.
Table 110 Configuration > Network > Interface > Cellular > Add / Edit
LABEL DESCRIPTION
Show Advanced
Settings / Hide
Advanced Settings
Click this button to display a greater or lesser number of configuration fields.
General Settings
Enable Interface Select this option to turn on this interface.
Interface Properties
Interface Name Select a name for the interface.
Zone Select the zone to which you want the cellular interface to belong. The zone determines
the security settings the Zyxel Device uses for the interface.
Extension Slot This is the USB slot that you are configuring for use with a mobile broadband card.
Connected
Device This displays the manufacturer and model name of your mobile broadband card if you
inserted one in the Zyxel Device. Otherwise, it displays none.
Description Enter a description of this interface. It is not used elsewhere. You can use alphanumeric
and ()+/:=?!*#@$_%- characters, and it can be up to 60 characters long.
Connectivity
Nailed-Up Select this if the connection should always be up. Clear this to have the Zyxel Device to
establish the connection only when there is traffic. You might not nail up the connection if
there is little traffic through the interface or if it costs money to keep the connection
available.
Idle timeout This value specifies the time in seconds (0~360) that elapses before the Zyxel Device
automatically disconnects from the ISP’s server. Zero disables the idle timeout.
ISP Settings
Profile Selection Select Device to use one of the mobile broadband device’s profiles of device settings.
Then select the profile (use Profile 1 unless your ISP instructed you to do otherwise).
Select Custom to configure your device settings yourself.
APN This field is read-only if you selected Device in the profile selection. Select Custom in the
profile selection to be able to manually input the APN (Access Point Name) provided by
your service provider. This field applies with a GSM or HSDPA mobile broadband card. Enter
the APN from your service provider. Connections with different APNs may provide different
services (such as Internet access or MMS (Multi-Media Messaging Service)) and charge
method.
You can enter up to 63 ASCII printable characters. Spaces are allowed.
Dial String Enter the dial string if your ISP provides a string, which would include the APN, to initialize
the mobile broadband card.
You can enter up to 63 ASCII printable characters. Spaces are allowed.
This field is available only when you insert a GSM mobile broadband card.
Authentication
Type The Zyxel Device supports PAP (Password Authentication Protocol) and CHAP (Challenge
Handshake Authentication Protocol). CHAP is more secure than PAP; however, PAP is
readily available on more platforms.
Use the drop-down list box to select an authentication protocol for outgoing calls. Options
are:
None: No authentication for outgoing calls.
CHAP - Your Zyxel Device accepts CHAP requests only.
PAP - Your Zyxel Device accepts PAP requests only.
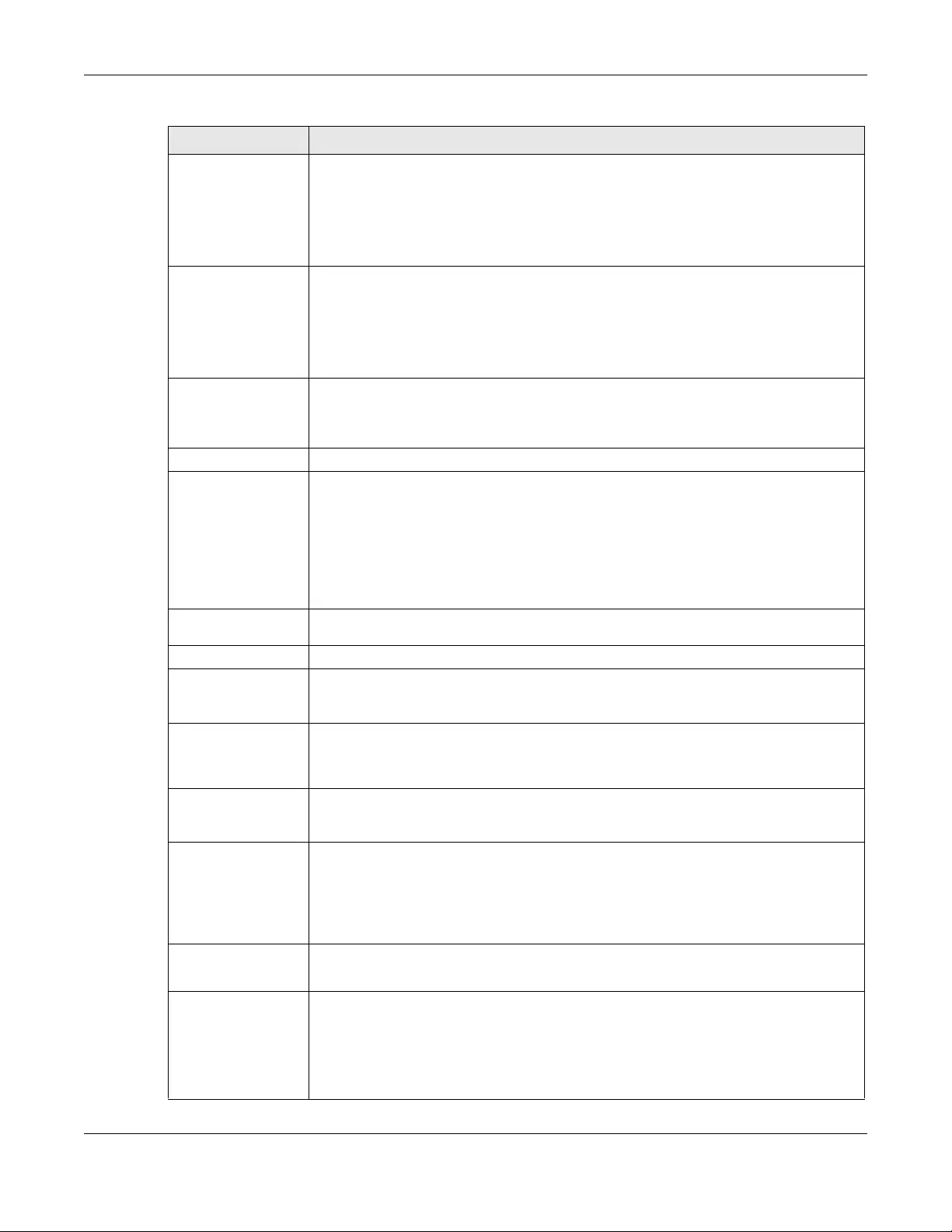
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
310
User Name This field displays when you select an authentication type other than None. This field is
read-only if you selected Device in the profile selection. If this field is configurable, enter
the user name for this mobile broadband card exactly as the service provider gave it to
you.
You can use 1 ~ 64 alphanumeric and #:%-_@$./ characters. The first character must be
alphanumeric or -_@$./. Spaces are not allowed.
Password This field displays when you select an authentication type other than None. This field is
read-only if you selected Device in the profile selection and the password is included in the
mobile broadband card’s profile. If this field is configurable, enter the password for this SIM
card exactly as the service provider gave it to you.
You can use 0 ~ 63 alphanumeric and `~!@#$%^&*()_-+={}|;:'<,>./ characters.
Spaces are not allowed.
Retype to
Confirm This field displays when you select an authentication type other than None. This field is
read-only if you selected Device in the profile selection and the password is included in the
mobile broadband card’s profile. If this field is configurable, re-enter the password for this
SIM card exactly as the service provider gave it to you.
SIM Card Setting
PIN Code This field displays with a GSM or HSDPA mobile broadband card. A PIN (Personal
Identification Number) code is a key to a mobile broadband card. Without the PIN code,
you cannot use the mobile broadband card.
Enter the 4-digit PIN code (0000 for example) provided by your ISP. If you enter the PIN
code incorrectly, the mobile broadband card may be blocked by your ISP and you
cannot use the account to access the Internet.
If your ISP disabled PIN code authentication, enter an arbitrary number.
Retype to
Confirm Type the PIN code again to confirm it.
Interface Parameters
Egress Bandwidth Enter the maximum amount of traffic, in kilobits per second, the Zyxel Device can send
through the interface to the network. Allowed values are 0 - 1048576. This setting is used in
WAN load balancing and bandwidth management.
Ingress
Bandwidth This is reserved for future use.
Enter the maximum amount of traffic, in kilobits per second, the Zyxel Device can receive
from the network through the interface. Allowed values are 0 - 1048576.
MTU Maximum Transmission Unit. Type the maximum size of each data packet, in bytes, that
can move through this interface. If a larger packet arrives, the Zyxel Device divides it into
smaller fragments. Allowed values are 576 - 1492. Usually, this value is 1492.
Connectivity Check The interface can regularly check the connection to the gateway you specified to make
sure it is still available. You specify how often the interface checks the connection, how
long to wait for a response before the attempt is a failure, and how many consecutive
failures are required before the Zyxel Device stops routing to the gateway. The Zyxel
Device resumes routing to the gateway the first time the gateway passes the connectivity
check.
Enable
Connectivity
Check
Select this to turn on the connection check.
Check Method Select the method that the gateway allows.
Select icmp to have the Zyxel Device regularly ping the gateway you specify to make sure
it is still available.
Select tcp to have the Zyxel Device regularly perform a TCP handshake with the gateway
you specify to make sure it is still available.
Table 110 Configuration > Network > Interface > Cellular > Add / Edit (continued)
LABEL DESCRIPTION
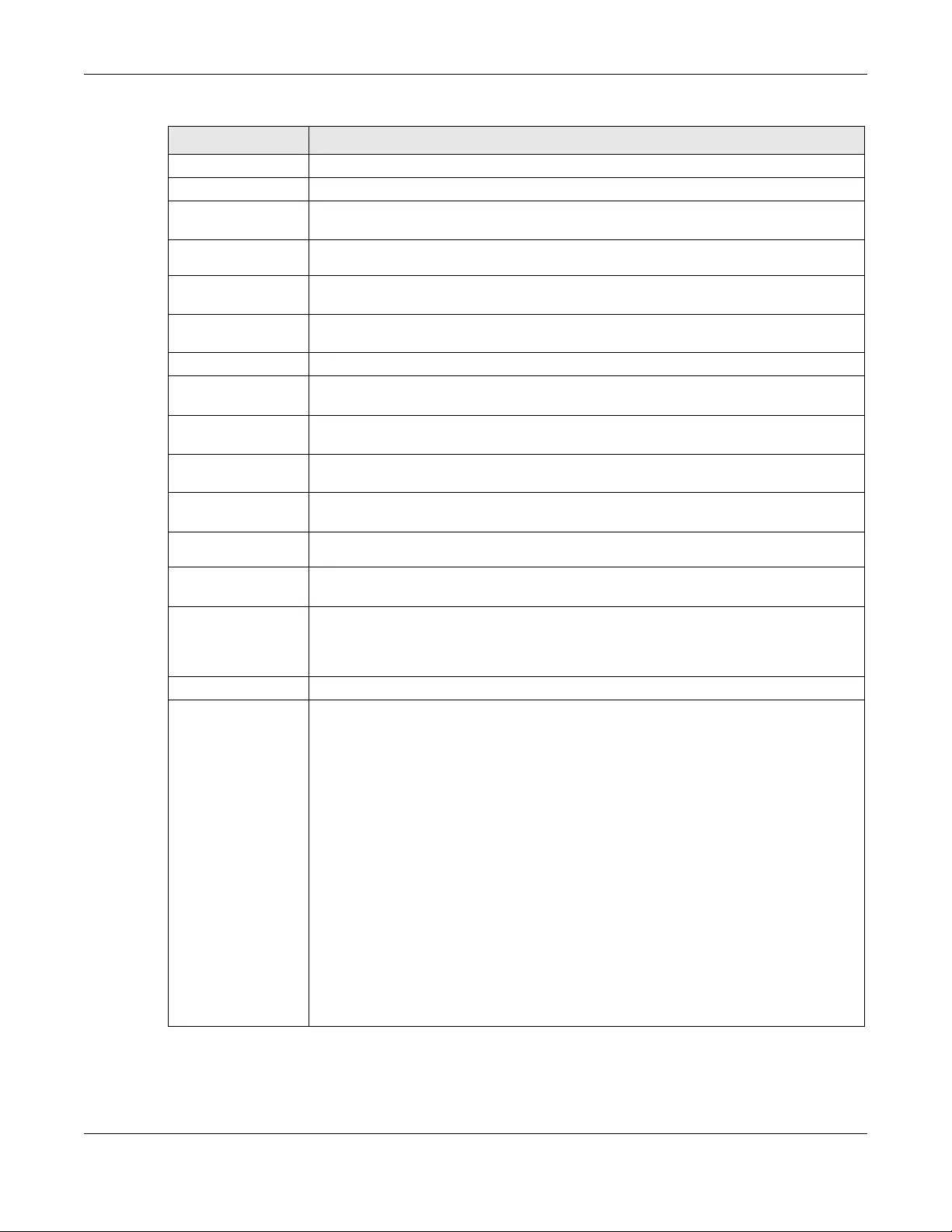
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
311
Check Period Enter the number of seconds between connection check attempts.
Check Timeout Enter the number of seconds to wait for a response before the attempt is a failure.
Check Fail
Tolerance Enter the number of consecutive failures before the Zyxel Device stops routing through the
gateway.
Check Default
Gateway Select this to use the default gateway for the connectivity check.
Check this
address Select this to specify a domain name or IP address for the connectivity check. Enter that
domain name or IP address in the field next to it.
Check Port This field only displays when you set the Check Method to tcp. Specify the port number to
use for a TCP connectivity check.
Related Setting
Configure WAN
TRUNK Click WAN TRUNK to go to a screen where you can configure the interface as part of a
WAN trunk for load balancing.
Configure Policy
Route Click Policy Route to go to the policy route summary screen where you can configure a
policy route to override the default routing and SNAT behavior for the interface.
IP Address
Assignment
Get
Automatically Select this option If your ISP did not assign you a fixed IP address. This is the default
selection.
Use Fixed IP
Address Select this option If the ISP assigned a fixed IP address.
IP Address
Assignment Enter the cellular interface’s WAN IP address in this field if you selected Use Fixed IP
Address.
Metric Enter the priority of the gateway (if any) on this interface. The Zyxel Device decides which
gateway to use based on this priority. The lower the number, the higher the priority. If two
or more gateways have the same priority, the Zyxel Device uses the one that was
configured first.
Device Settings
Band Selection This field appears if you selected a mobile broadband device that allows you to select the
type of network to use. Select the type of mobile broadband service for your mobile
broadband connection. If you are unsure what to select, check with your mobile
broadband service provider to find the mobile broadband service available to you in your
region.
Select auto to have the card connect to an available network. Choose this option if you
do not know what networks are available.
You may want to manually specify the type of network to use if you are charged differently
for different types of network or you only have one type of network available to you.
Select GPRS / EDGE (GSM) only to have this interface only use a 2.5G or 2.75G network
(respectively). If you only have a GSM network available to you, you may want to select
this so the Zyxel Device does not spend time looking for a WCDMA network.
Select UMTS / HSDPA (WCDMA) only to have this interface only use a 3G or 3.5G network
(respectively). You may want to do this if you want to make sure the interface does not use
the GSM network.
Select LTE only to have this interface only use a 4G LTE network. This option only appears
when a USG dongle for 4G technology is inserted.
Table 110 Configuration > Network > Interface > Cellular > Add / Edit (continued)
LABEL DESCRIPTION
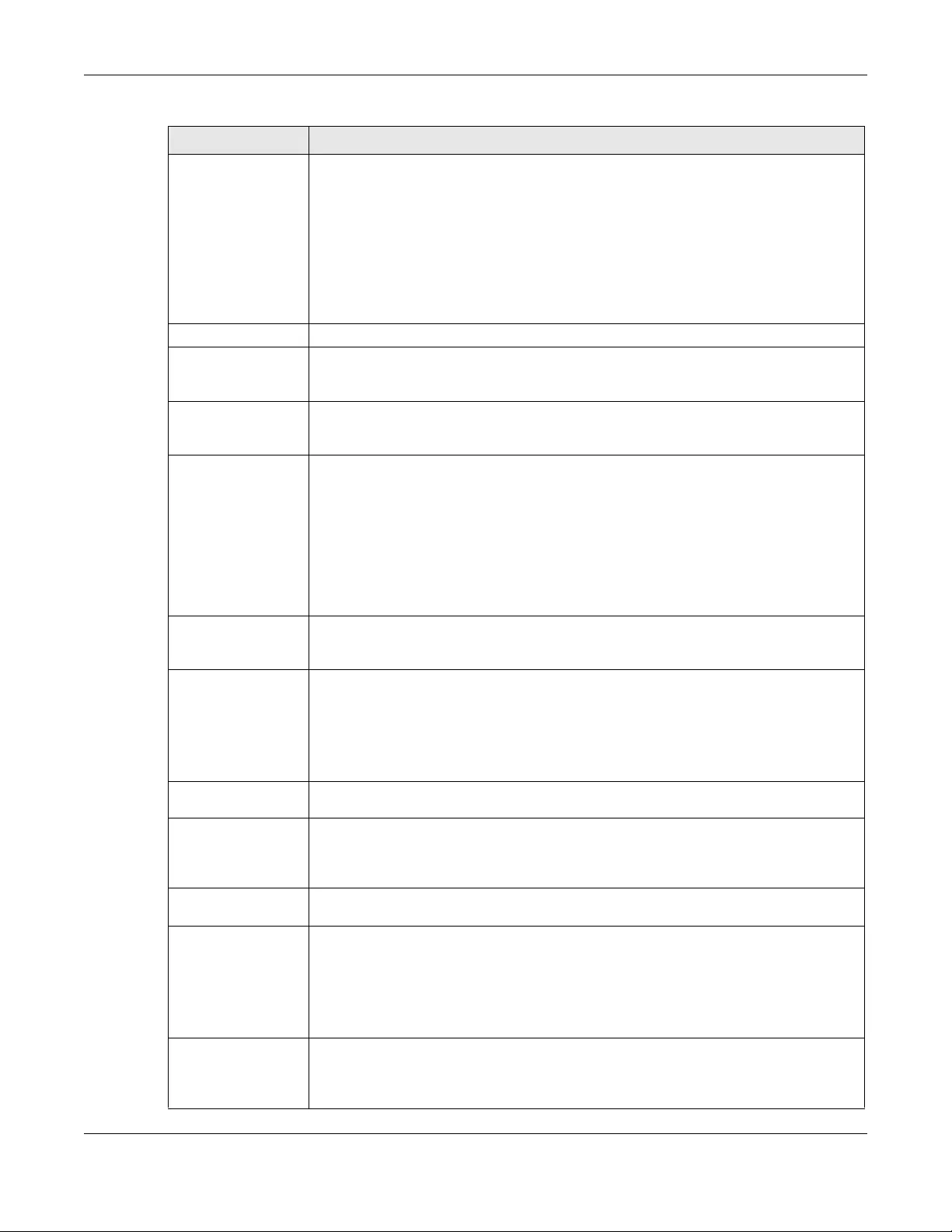
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
312
Network
Selection Home network is the network to which you are originally subscribed.
Select Home to have the mobile broadband device connect only to the home network. If
the home network is down, the Zyxel Device’s mobile broadband Internet connection is
also unavailable.
Select Auto (Default) to allow the mobile broadband device to connect to a network to
which you are not subscribed when necessary, for example when the home network is
down or another mobile broadband base station's signal is stronger. This is recommended
if you need continuous Internet connectivity. If you select this, you may be charged using
the rate of a different network.
Budget Setup
Enable Budget
Control Select this to set a monthly limit for the user account of the installed mobile broadband
card. You can set a limit on the total traffic and/or call time. The Zyxel Device takes the
actions you specified when a limit is exceeded during the month.
Time Budget Select this and specify the amount of time (in hours) that the mobile broadband
connection can be used within one month. If you change the value after you configure
and enable budget control, the Zyxel Device resets the statistics.
Data Budget Select this and specify how much downstream and/or upstream data (in Mega bytes) can
be transmitted via the mobile broadband connection within one month.
Select Download to set a limit on the downstream traffic (from the ISP to the Zyxel Device).
Select Upload to set a limit on the upstream traffic (from the Zyxel Device to the ISP).
Select Download/Upload to set a limit on the total traffic in both directions.
If you change the value after you configure and enable budget control, the Zyxel Device
resets the statistics.
Reset time and
data budget
counters on
Select the date on which the Zyxel Device resets the budget every month. If the date you
selected is not available in a month, such as 30th or 31st, the Zyxel Device resets the
budget on the last day of the month.
Reset time and
data budget
counters
This button is available only when you enable budget control in this screen.
Click this button to reset the time and data budgets immediately. The count starts over
with the mobile broadband connection’s full configured monthly time and data budgets.
This does not affect the normal monthly budget restart; so if you configured the time and
data budget counters to reset on the second day of the month and you use this button on
the first, the time and data budget counters will still reset on the second.
Actions when
over budget Specify the actions the Zyxel Device takes when the time or data limit is exceeded.
Log Select None to not create a log, Log to create a log, or Log-alert to create an alert log. If
you select Log or Log-alert you can also select recurring every to have the Zyxel Device
send a log or alert for this event periodically. Specify how often (from 1 to 65535 minutes) to
send the log or alert.
New connection Select Allow to permit new mobile broadband connections or Disallow to drop/block new
mobile broadband connections.
Current
connection Select Keep to maintain an existing mobile broadband connection or Drop to disconnect
it. You cannot set New connection to Allow and Current connection to Drop at the same
time.
If you set New connection to Disallow and Current connection to Keep, the Zyxel Device
allows you to transmit data using the current connection, but you cannot build a new
connection if the existing connection is disconnected.
Actions when over %
of time budget or %
of data budget
Specify the actions the Zyxel Device takes when the specified percentage of time budget
or data limit is exceeded. Enter a number from 1 to 99 in the percentage fields. If you
change the value after you configure and enable budget control, the Zyxel Device resets
the statistics.
Table 110 Configuration > Network > Interface > Cellular > Add / Edit (continued)
LABEL DESCRIPTION
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
313
10.7 Tunnel Interfaces
The Zyxel Device uses tunnel interfaces in Generic Routing Encapsulation (GRE), IPv6 in IPv4, and 6to4
tunnels.
GRE Tunneling
GRE tunnels encapsulate a wide variety of network layer protocol packet types inside IP tunnels. A GRE
tunnel serves as a virtual point-to-point link between the Zyxel Device and another router over an IPv4
network. At the time of writing, the Zyxel Device only supports GRE tunneling in IPv4 networks.
Figure 239 GRE Tunnel Example
IPv6 Over IPv4 Tunnels
To route traffic between two IPv6 networks over an IPv4 network, an IPv6 over IPv4 tunnel has to be
used.
Figure 240 IPv6 over IPv4 Network
On the Zyxel Device, you can either set up a manual IPv6-in-IPv4 tunnel or an automatic 6to4 tunnel. The
following describes each method:
Log Select None to not create a log when the Zyxel Device takes this action, Log to create a
log, or Log-alert to create an alert log. If you select Log or Log-alert you can also select
recurring every to have the Zyxel Device send a log or alert for this event periodically.
Specify how often (from 1 to 65535 minutes) to send the log or alert.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 110 Configuration > Network > Interface > Cellular > Add / Edit (continued)
LABEL DESCRIPTION

Chapter 10 Interfaces
USG/ZyWALL User’s Guide
314
IPv6-in-IPv4 Tunneling
Use this mode on the WAN of the Zyxel Device if
• your Zyxel Device has a public IPv4 IP address given from your ISP,
and
• you want to transmit your IPv6 packets to one and only one remote site whose LAN network is also an
IPv6 network.
With this mode, the Zyxel Device encapsulates IPv6 packets within IPv4 packets across the Internet. You
must know the WAN IP address of the remote gateway device. This mode is normally used for a site-to-
site application such as two branch offices.
Figure 241 IPv6-in-IPv4 Tunnel
In the Zyxel Device, you must also manually configure a policy route for an IPv6-in-IPv4 tunnel to make
the tunnel work.
6to4 Tunneling
This mode also enables IPv6 packets to cross IPv4 networks. Unlike IPv6-in-IPv4 tunneling, you do not
need to configure a policy route for a 6to4 tunnel. Through your properly pre-configuring the destination
router’s IP address in the IP address assignments to hosts, the Zyxel Device can automatically forward
6to4 packets to the destination they want to go. A 6to4 relay router is required to route 6to4 packets to
a native IPv6 network if the packet’s destination do not match your specified criteria.
In this mode, the Zyxel Device should get a public IPv4 address for the WAN. The Zyxel Device adds an
IPv4 IP header to an IPv6 packet when transmitting the packet to the Internet. In reverse, the Zyxel
Device removes the IPv4 header from an IPv6 packet when receiving it from the Internet.
An IPv6 address using the 6to4 mode consists of an IPv4 address, the format is as the following:
2002:[a public IPv4 address in hexadecimal]::/48
For example, a public IPv4 address is 202.156.30.41. The converted hexadecimal IP string is ca.9c.1Ee.29.
The IPv6 address prefix becomes 2002:ca9c:1e29::/48.
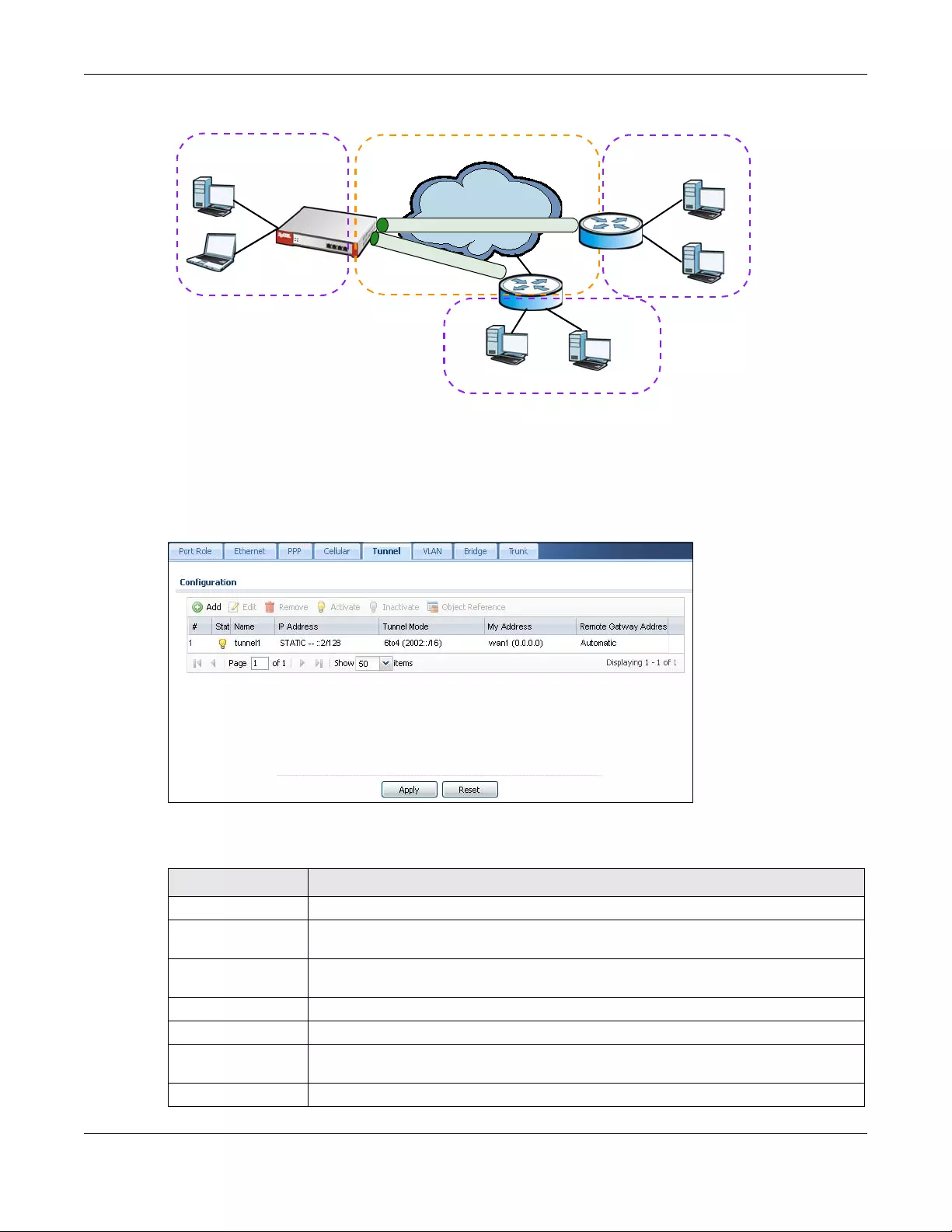
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
315
Figure 242 6to4 Tunnel
10.7.1 Configuring a Tunnel
This screen lists the Zyxel Device’s configured tunnel interfaces. To access this screen, click Network >
Interface > Tunnel.
Figure 243 Network > Interface > Tunnel
Each field is explained in the following table.
Internet
IPv6
IPv4
IPv6
IPv6
Table 111 Network > Interface > Tunnel
LABEL DESCRIPTION
Add Click this to create a new GRE tunnel interface.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Object References Select an entry and click Object Reference to open a screen that shows which settings use
the entry. See Section 10.4.4 on page 294 for an example.
# This field is a sequential value, and it is not associated with any interface.
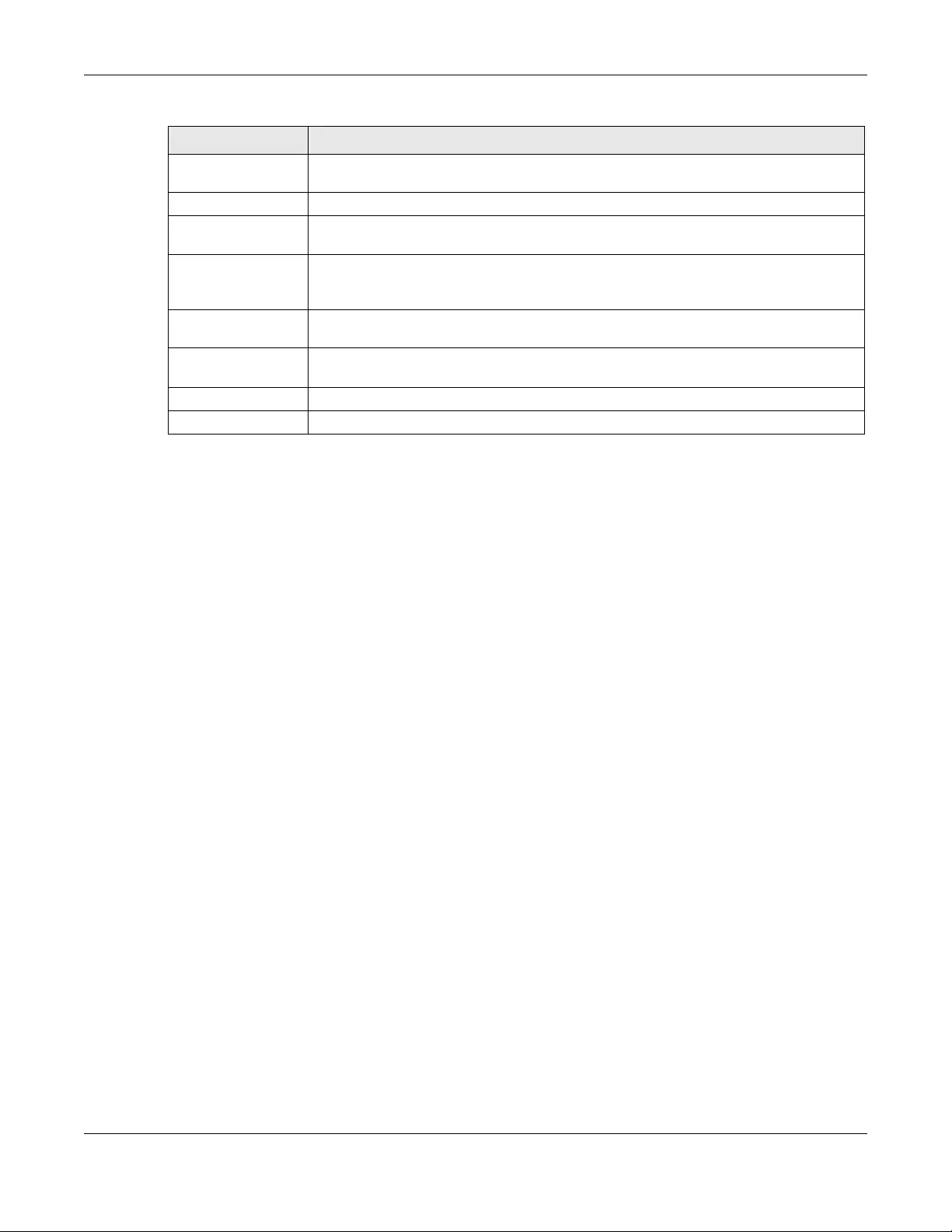
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
316
10.7.2 Tunnel Add or Edit Screen
This screen lets you configure a tunnel interface. Click Configuration > Network > Interface > Tunnel >
Add (or Edit) to open the following screen.
Status The activate (light bulb) icon is lit when the entry is active and dimmed when the entry is
inactive.
Name This field displays the name of the interface.
IP Address This is the IP address of the interface. If the interface is active (and connected), the Zyxel
Device tunnels local traffic sent to this IP address to the Remote Gateway Address.
Tunnel Mode This is the tunnel mode of the interface (GRE, IPv6-in-IPv4 or 6to4). This field also displays the
interface’s IPv4 IP address and subnet mask if it is a GRE tunnel. Otherwise, it displays the
interface’s IPv6 IP address and prefix length.
My Address This is the interface or IP address uses to identify itself to the remote gateway. The Zyxel
Device uses this as the source for the packets it tunnels to the remote gateway.
Remote Gateway
Address
This is the IP address or domain name of the remote gateway to which this interface tunnels
traffic.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to begin configuring this screen afresh.
Table 111 Network > Interface > Tunnel (continued)
LABEL DESCRIPTION
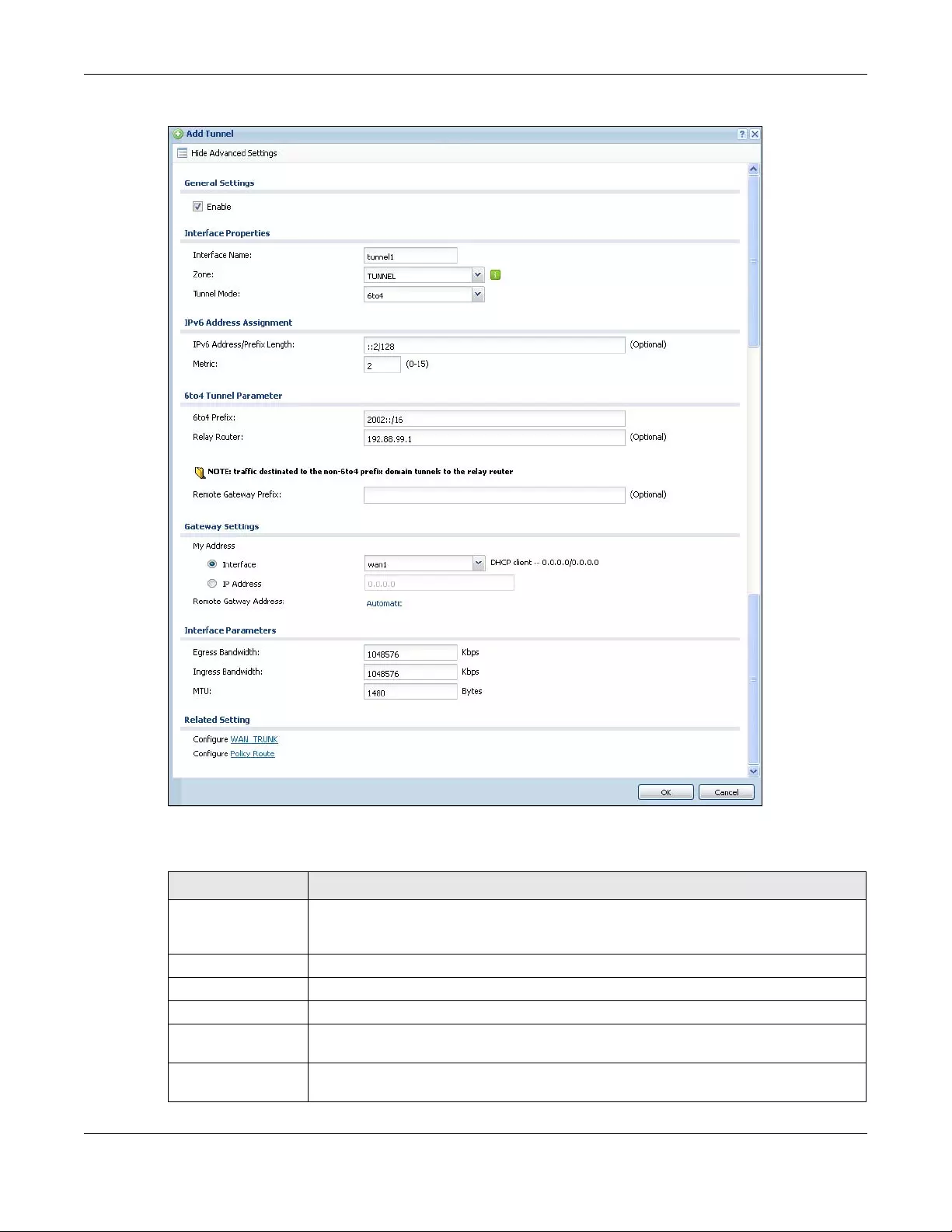
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
317
Figure 244 Network > Interface > Tunnel > Add/Edit
Each field is explained in the following table.
Table 112 Network > Interface > Tunnel > Add/Edit
LABEL DESCRIPTION
Show Advanced
Settings / Hide
Advanced Settings
Click this button to display a greater or lesser number of configuration fields.
General Settings
Enable Select this to enable this interface. Clear this to disable this interface.
Interface Properties
Interface Name This field is read-only if you are editing an existing tunnel interface. Enter the name of the
tunnel interface. The format is tunnelx, where x is 0 - 3. For example, tunnel0.
Zone Use this field to select the zone to which this interface belongs. This controls what security
settings the Zyxel Device applies to this interface.
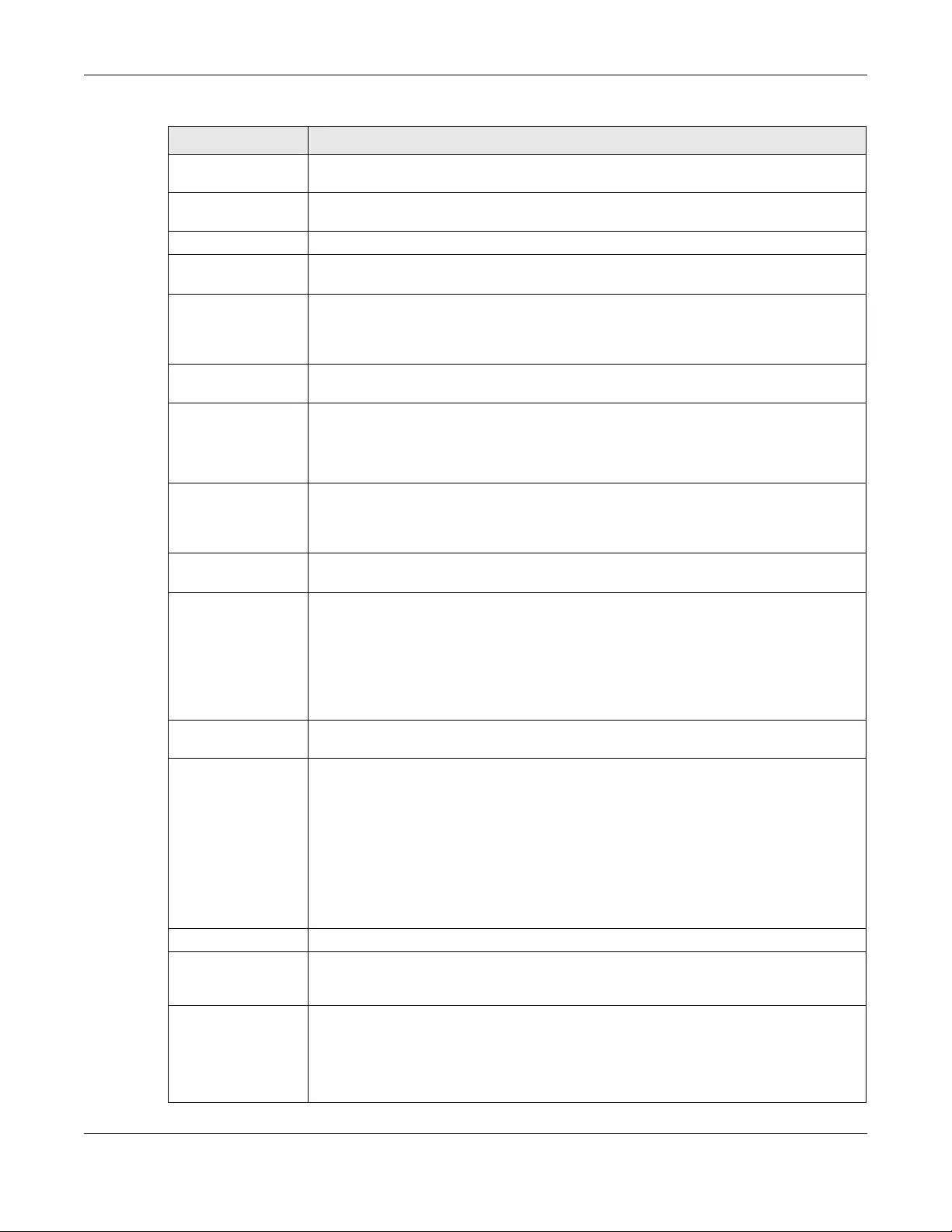
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
318
Tunnel Mode Select the tunneling protocol of the interface (GRE, IPv6-in-IPv4 or 6to4). See Section 10.7
on page 313 for more information.
IP Address
Assignment
This section is available if you are configuring a GRE tunnel.
IP Address Enter the IP address for this interface.
Subnet Mask Enter the subnet mask of this interface in dot decimal notation. The subnet mask indicates
what part of the IP address is the same for all computers in the network.
Metric Enter the priority of the gateway (if any) on this interface. The Zyxel Device decides which
gateway to use based on this priority. The lower the number, the higher the priority. If two or
more gateways have the same priority, the Zyxel Device uses the one that was configured
first.
IPv6 Address
Assignment
This section is available if you are configuring an IPv6-in-IPv4 or a 6to4 tunnel.
IPv6 Address/
Prefix Length Enter the IPv6 address and the prefix length for this interface if you want to use a static IP
address. This field is optional.
The prefix length indicates what the left-most part of the IP address is the same for all
computers in the network, that is, the network address.
Metric Enter the priority of the gateway (if any) on this interface. The Zyxel Device decides which
gateway to use based on this priority. The lower the number, the higher the priority. If two or
more gateways have the same priority, the Zyxel Device uses the one that was configured
first.
6to4 Tunnel
Parameter
This section is available if you are configuring a 6to4 tunnel which encapsulates IPv6 to IPv4
packets.
6to4 Prefix Enter the IPv6 prefix of a destination network. The Zyxel Device forwards IPv6 packets to the
hosts in the matched network.
If you enter a prefix starting with 2002, the Zyxel Device will forward the matched packets to
the IPv4 IP address converted from the packets’ destination address. The IPv4 IP address
can be converted from the next 32 bits after the prefix you specified in this field. See 6to4
Tunneling on page 314 for an example. The Zyxel Device forwards the unmatched packets
to the specified Relay Router.
Relay Router Enter the IPv4 address of a 6to4 relay router which helps forward packets between 6to4
networks and native IPv6 networks.
Remote
Gateway Prefix Enter the IPv4 network address and network bits of a remote 6to4 gateway, for example,
14.15.0.0/16.
This field works if you enter a 6to4 Prefix not starting with 2002 (2003 for example). The Zyxel
Device forwards the matched packets to a remote gateway with the network address you
specify here, and the bits converted after the 6to4 Prefix in the packets.
For example, you configure the 6to4 prefix to 2003:A0B::/32 and the remote gateway prefix
to 14.15.0.0/16. If a packet’s destination is 2003:A0B:1011:5::8, the Zyxel Device forwards the
packet to 14.15.16.17, where the network address is 14.15.0.0 and the host address is the
remain bits converted from 1011 after the packet’s 6to4 prefix (2003:A0B).
Gateway Settings
My Address Specify the interface or IP address to use as the source address for the packets this
interface tunnels to the remote gateway. The remote gateway sends traffic to this interface
or IP address.
Remote
Gateway
Address
Enter the IP address or domain name of the remote gateway to which this interface tunnels
traffic.
Automatic displays in this field if you are configuring a 6to4 tunnel. It means the 6to4 tunnel
will help forward packets to the corresponding remote gateway automatically by looking
at the packet’s destination address.
Table 112 Network > Interface > Tunnel > Add/Edit (continued)
LABEL DESCRIPTION
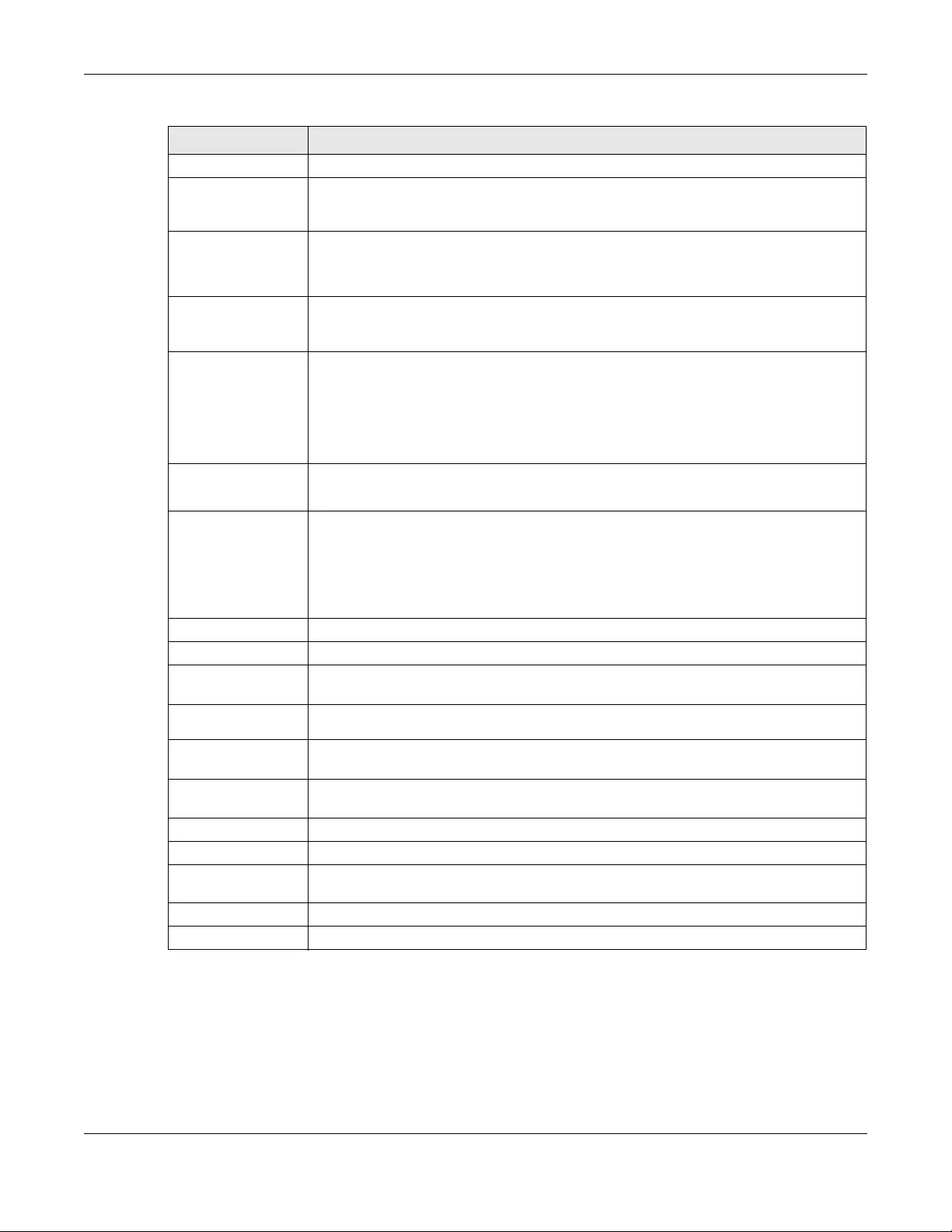
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
319
10.8 VLAN Interfaces
A Virtual Local Area Network (VLAN) divides a physical network into multiple logical networks. The
standard is defined in IEEE 802.1q.
Interface Parameters
Egress Bandwidth Enter the maximum amount of traffic, in kilobits per second, the Zyxel Device can send
through the interface to the network. Allowed values are 0 - 1048576. This setting is used in
WAN load balancing and bandwidth management.
Ingress
Bandwidth This is reserved for future use.
Enter the maximum amount of traffic, in kilobits per second, the Zyxel Device can receive
from the network through the interface. Allowed values are 0 - 1048576.
MTU Maximum Transmission Unit. Type the maximum size of each data packet, in bytes, that can
move through this interface. If a larger packet arrives, the Zyxel Device divides it into smaller
fragments. Allowed values are 576 - 1500. Usually, this value is 1500.
Connectivity Check This section is available if you are configuring a GRE tunnel.
The interface can regularly check the connection to the gateway you specified to make
sure it is still available. You specify how often the interface checks the connection, how
long to wait for a response before the attempt is a failure, and how many consecutive
failures are required before the Zyxel Device stops routing to the gateway. The Zyxel Device
resumes routing to the gateway the first time the gateway passes the connectivity check.
Enable
Connectivity
Check
Select this to turn on the connection check.
Check Method Select the method that the gateway allows.
Select icmp to have the Zyxel Device regularly ping the gateway you specify to make sure
it is still available.
Select tcp to have the Zyxel Device regularly perform a TCP handshake with the gateway
you specify to make sure it is still available.
Check Period Enter the number of seconds between connection check attempts.
Check Timeout Enter the number of seconds to wait for a response before the attempt is a failure.
Check Fail
Tolerance Enter the number of consecutive failures before the Zyxel Device stops routing through the
gateway.
Check Default
Gateway Select this to use the default gateway for the connectivity check.
Check this
address Select this to specify a domain name or IP address for the connectivity check. Enter that
domain name or IP address in the field next to it.
Check Port This field displays when you set the Check Method to tcp. Specify the port number to use for
a TCP connectivity check.
Related Setting
WAN TRUNK Click this link to go to a screen where you can configure WAN trunk load balancing.
Policy Route Click this link to go to the screen where you can manually configure a policy route to
associate traffic with this interface.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 112 Network > Interface > Tunnel > Add/Edit (continued)
LABEL DESCRIPTION
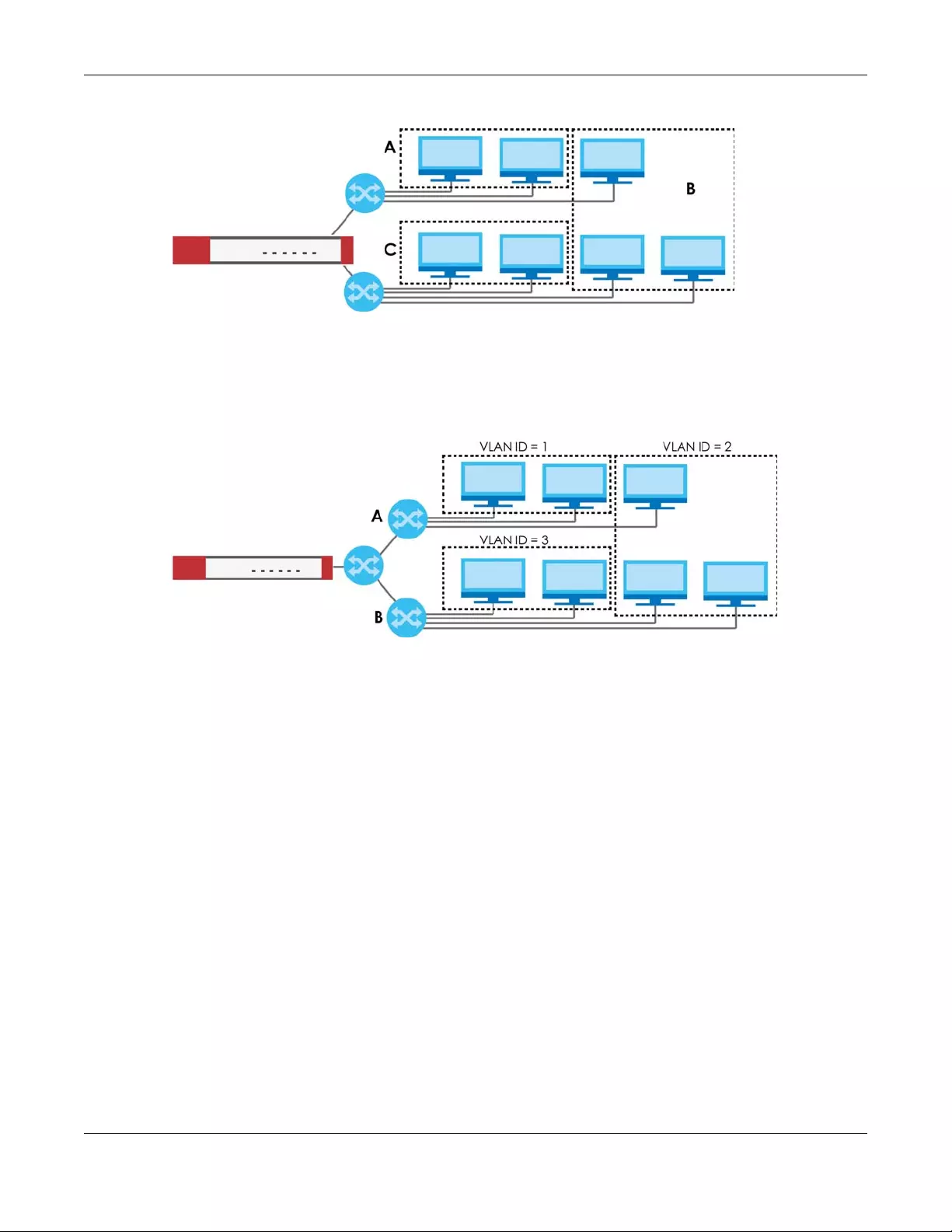
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
320
Figure 245 Example: Before VLAN
In this example, there are two physical networks and three departments A, B, and C. The physical
networks are connected to hubs, and the hubs are connected to the router.
Alternatively, you can divide the physical networks into three VLANs.
Figure 246 Example: After VLAN
Each VLAN is a separate network with separate IP addresses, subnet masks, and gateways. Each VLAN
also has a unique identification number (ID). The ID is a 12-bit value that is stored in the MAC header. The
VLANs are connected to switches, and the switches are connected to the router. (If one switch has
enough connections for the entire network, the network does not need switches A and B.)
• Traffic inside each VLAN is layer-2 communication (data link layer, MAC addresses). It is handled by
the switches. As a result, the new switch is required to handle traffic inside VLAN 2. Traffic is only
broadcast inside each VLAN, not each physical network.
• Traffic between VLANs (or between a VLAN and another type of network) is layer-3 communication
(network layer, IP addresses). It is handled by the router.
This approach provides a few advantages.
• Increased performance - In VLAN 2, the extra switch should route traffic inside the sales department
faster than the router does. In addition, broadcasts are limited to smaller, more logical groups of users.
• Higher security - If each computer has a separate physical connection to the switch, then broadcast
traffic in each VLAN is never sent to computers in another VLAN.
• Better manageability - You can align network policies more appropriately for users. For example, you
can create different content filtering rules for each VLAN (each department in the example above),
and you can set different bandwidth limits for each VLAN. These rules are also independent of the
physical network, so you can change the physical network without changing policies.
In this example, the new switch handles the following types of traffic:
• Inside VLAN 2.
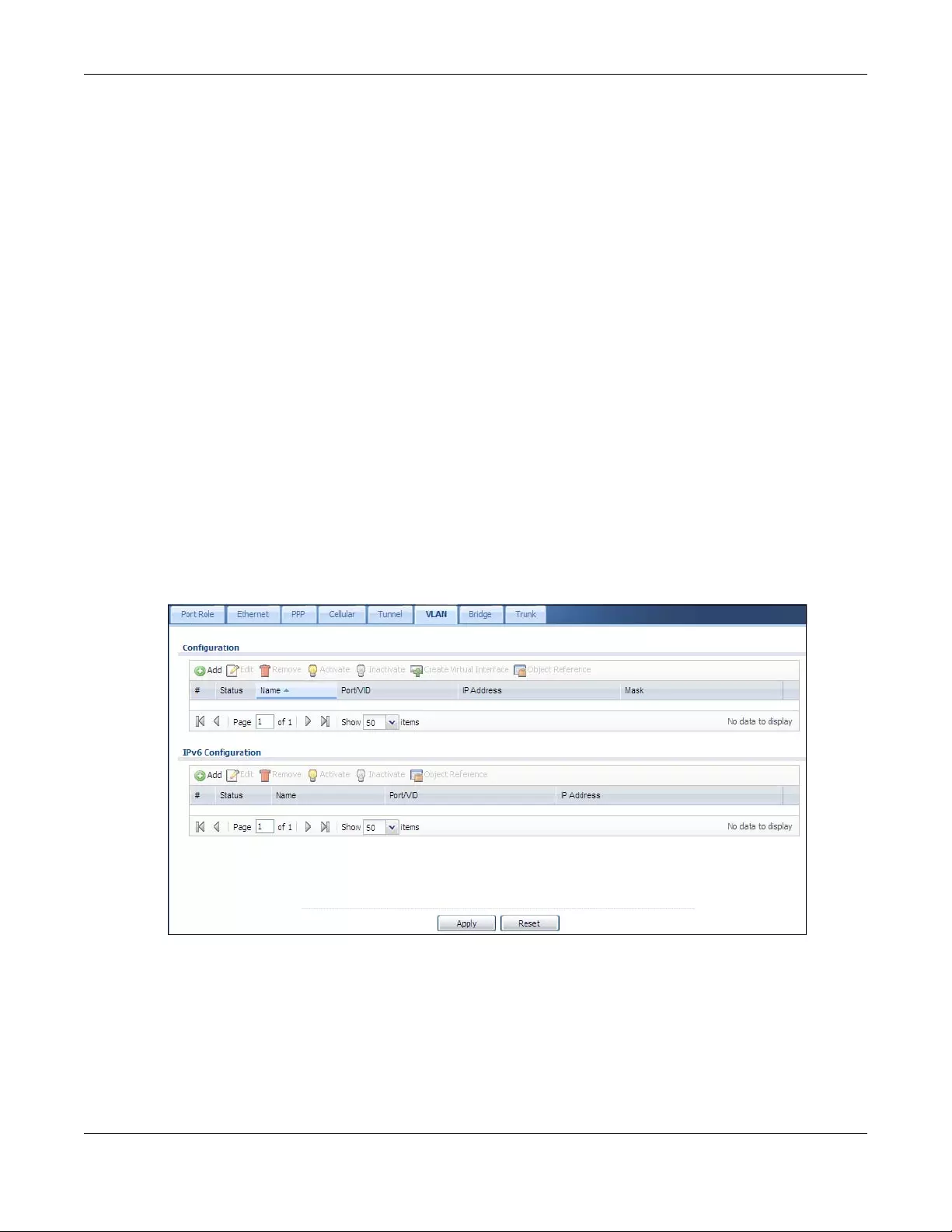
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
321
• Between the router and VLAN 1.
• Between the router and VLAN 2.
• Between the router and VLAN 3.
VLAN Interfaces Overview
In the Zyxel Device, each VLAN is called a VLAN interface. As a router, the Zyxel Device routes traffic
between VLAN interfaces, but it does not route traffic within a VLAN interface. All traffic for each VLAN
interface can go through only one Ethernet interface, though each Ethernet interface can have one or
more VLAN interfaces.
Note: Each VLAN interface is created on top of only one Ethernet interface.
Otherwise, VLAN interfaces are similar to other interfaces in many ways. They have an IP address, subnet
mask, and gateway used to make routing decisions. They restrict bandwidth and packet size. They can
provide DHCP services, and they can verify the gateway is available.
10.8.1 VLAN Summary Screen
This screen lists every VLAN interface and virtual interface created on top of VLAN interfaces. If you
enabled IPv6 in the Configuration > System > IPv6 screen, you can also configure VLAN interfaces used
for your IPv6 networks on this screen. To access this screen, click Configuration > Network > Interface >
VLAN.
Figure 247 Configuration > Network > Interface > VLAN
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
322
Each field is explained in the following table.
10.8.2 VLAN Add/Edit
Select an existing entry in the previous screen and click Edit or click Add to create a new entry. The
following screen appears.
Table 113 Configuration > Network > Interface > VLAN
LABEL DESCRIPTION
Configuration
/ IPv6
Configuration
Use the Configuration section for IPv4 network settings. Use the IPv6 Configuration section for IPv6
network settings if you connect your Zyxel Device to an IPv6 network. Both sections have similar
fields as described below.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the entry’s
settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove it
before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Create Virtual
Interface
To open the screen where you can create a virtual interface, select an interface and click Create
Virtual Interface.
Object
References
Select an entry and click Object Reference to open a screen that shows which settings use the
entry. See Section 10.4.4 on page 294 for an example.
# This field is a sequential value, and it is not associated with any interface.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
Name This field displays the name of the interface.
Port/VID For VLAN interfaces, this field displays
• the Ethernet interface on which the VLAN interface is created
• the VLAN ID
For virtual interfaces, this field is blank.
IP Address This field displays the current IP address of the interface. If the IP address is 0.0.0.0, the interface
does not have an IP address yet.
This screen also shows whether the IP address is a static IP address (STATIC) or dynamically
assigned (DHCP). IP addresses are always static in virtual interfaces.
Mask This field displays the interface’s subnet mask in dot decimal notation.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
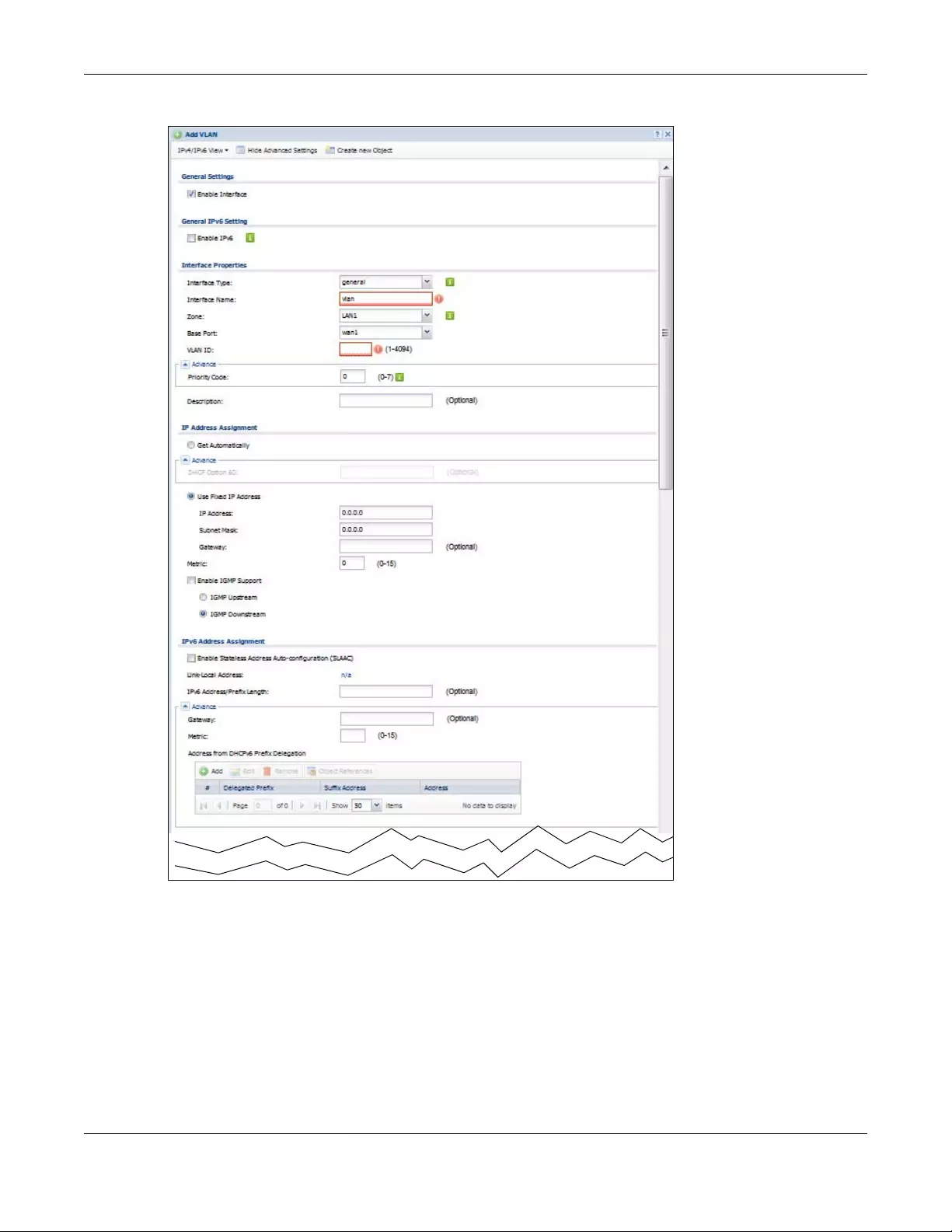
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
323
Figure 248 Configuration > Network > Interface > VLAN > Add /Edit
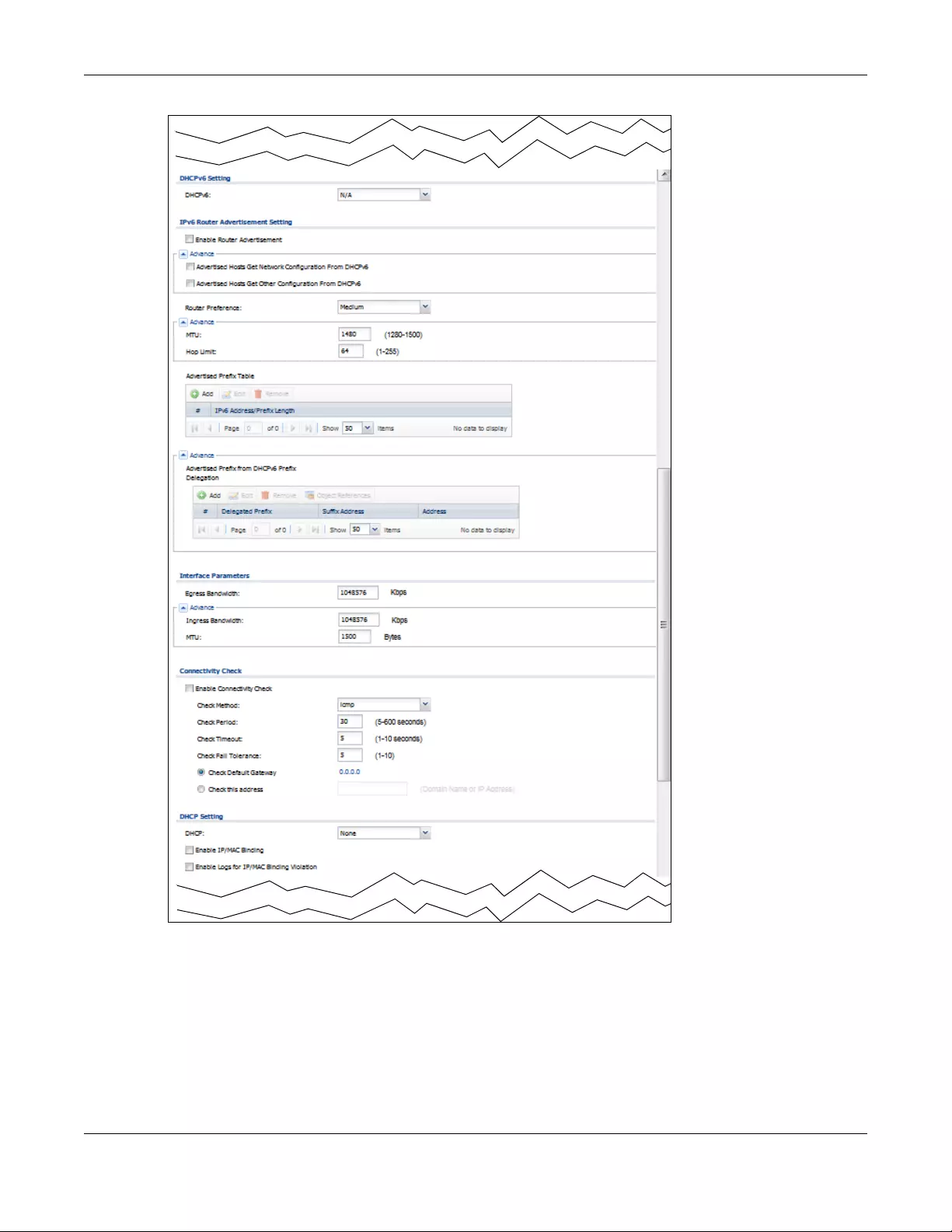
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
324
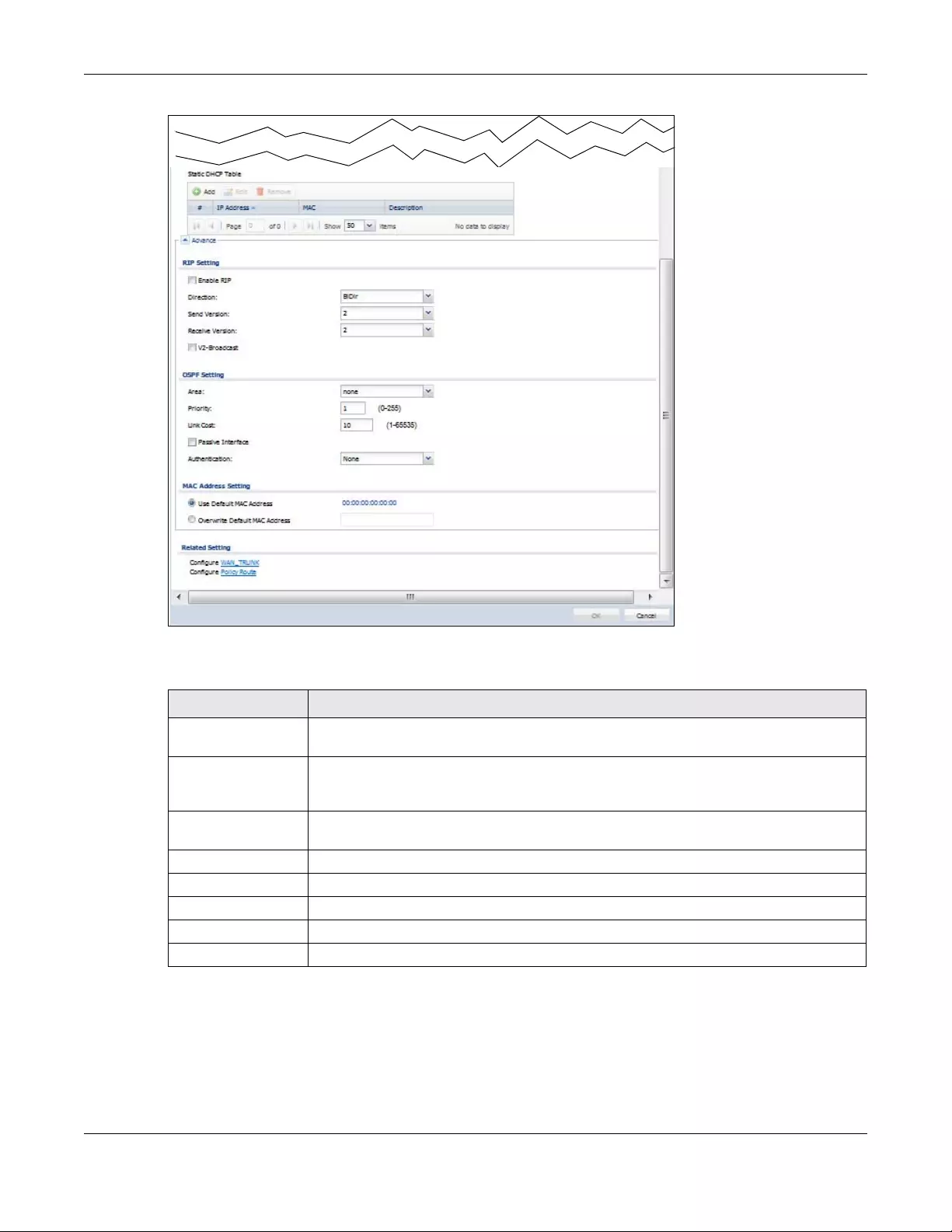
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
325
Each field is explained in the following table.
Table 114 Configuration > Network > Interface > VLAN > Add / Edit
LABEL DESCRIPTION
IPv4/IPv6 View / IPv4
View / IPv6 View
Use this button to display both IPv4 and IPv6, IPv4-only, or IPv6-only configuration fields.
Show Advanced
Settings / Hide
Advanced Settings
Click this button to display a greater or lesser number of configuration fields.
Create New Object Click this button to create a DHCPv6 lease or DHCPv6 request object that you may use for
the DHCPv6 settings in this screen.
General Settings
Enable Interface Select this to turn this interface on. Clear this to disable this interface.
General IPv6 Setting
Enable IPv6 Select this to enable IPv6 on this interface. Otherwise, clear this to disable it.
Interface Properties
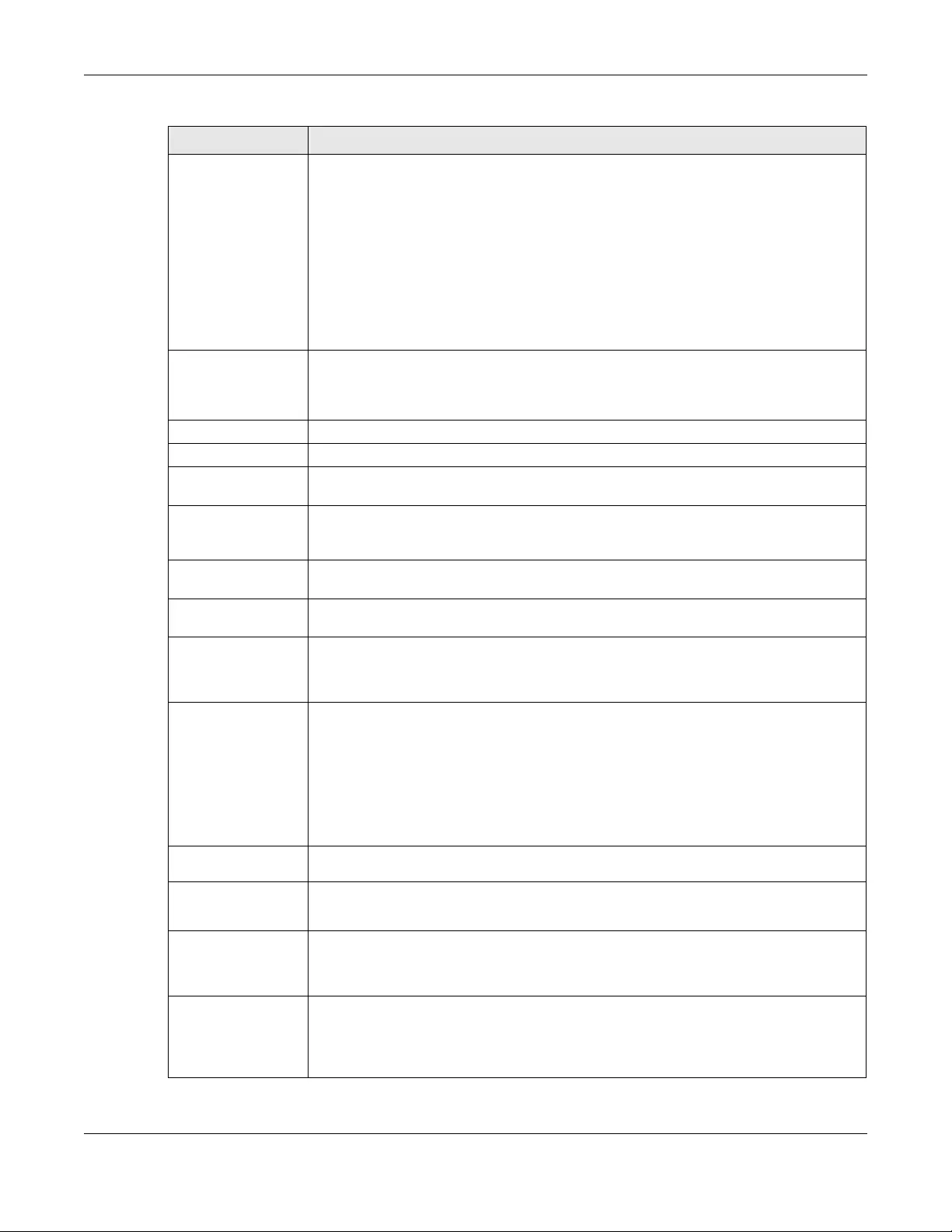
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
326
Interface Type Select one of the following option depending on the type of network to which the Zyxel
Device is connected or if you want to additionally manually configure some related
settings.
internal is for connecting to a local network. Other corresponding configuration options:
DHCP server and DHCP relay. The Zyxel Device automatically adds default SNAT settings for
traffic flowing from this interface to an external interface.
external is for connecting to an external network (like the Internet). The Zyxel Device
automatically adds this interface to the default WAN trunk.
For general, the rest of the screen’s options do not automatically adjust and you must
manually configure a policy route to add routing and SNAT settings for the interface.
Interface Name This field is read-only if you are editing an existing VLAN interface. Enter the number of the
VLAN interface. You can use a number from 0~4094. For example, use vlan0, vlan8, and so
on. The total number of VLANs you can configure on the Zyxel Device depends on the
model.
Zone Select the zone to which the VLAN interface belongs.
Base Port Select the Ethernet interface on which the VLAN interface runs.
VLAN ID Enter the VLAN ID. This 12-bit number uniquely identifies each VLAN. Allowed values are 1 -
4094. (0 and 4095 are reserved.)
Priority Code This is a 3-bit field within a 802.1Q VLAN tag that’s used to prioritize associated outgoing
VLAN traffic. “0” is the lowest priority level and “7” is the highest. See Table 235 on page 621.
The setting configured in Configuration > BWM overwrites the priority setting here.
Description Enter a description of this interface. It is not used elsewhere. You can use alphanumeric and
()+/:=?!*#@$_%- characters, and it can be up to 60 characters long.
IP Address
Assignment
Get
Automatically Select this if this interface is a DHCP client. In this case, the DHCP server configures the IP
address, subnet mask, and gateway automatically.
You should not select this if the interface is assigned to a VRRP group.
DHCP Option 60 DHCP Option 60 is used by the Zyxel Device for identification to the DHCP server using the
VCI (Vendor Class Identifier) on the DHCP server. The Zyxel Device adds it in the initial DHCP
discovery message that a DHCP client broadcasts in search of an IP address. The DHCP
server can assign different IP addresses or options to clients with the specific VCI or reject
the request from clients without the specific VCI.
Type a string using up to 64 of these characters [a-zA-Z0-9!\"#$%&\'()*+,-./
:;<=>?@\[\\\]^_`{|}~] to identify this Zyxel Device to the DHCP server. For example, Zyxel-
TW.
Use Fixed IP
Address Select this if you want to specify the IP address, subnet mask, and gateway manually.
IP Address This field is enabled if you select Use Fixed IP Address.
Enter the IP address for this interface.
Subnet Mask This field is enabled if you select Use Fixed IP Address.
Enter the subnet mask of this interface in dot decimal notation. The subnet mask indicates
what part of the IP address is the same for all computers in the network.
Gateway This field is enabled if you select Use Fixed IP Address.
Enter the IP address of the gateway. The Zyxel Device sends packets to the gateway when
it does not know how to route the packet to its destination. The gateway should be on the
same network as the interface.
Table 114 Configuration > Network > Interface > VLAN > Add / Edit (continued)
LABEL DESCRIPTION
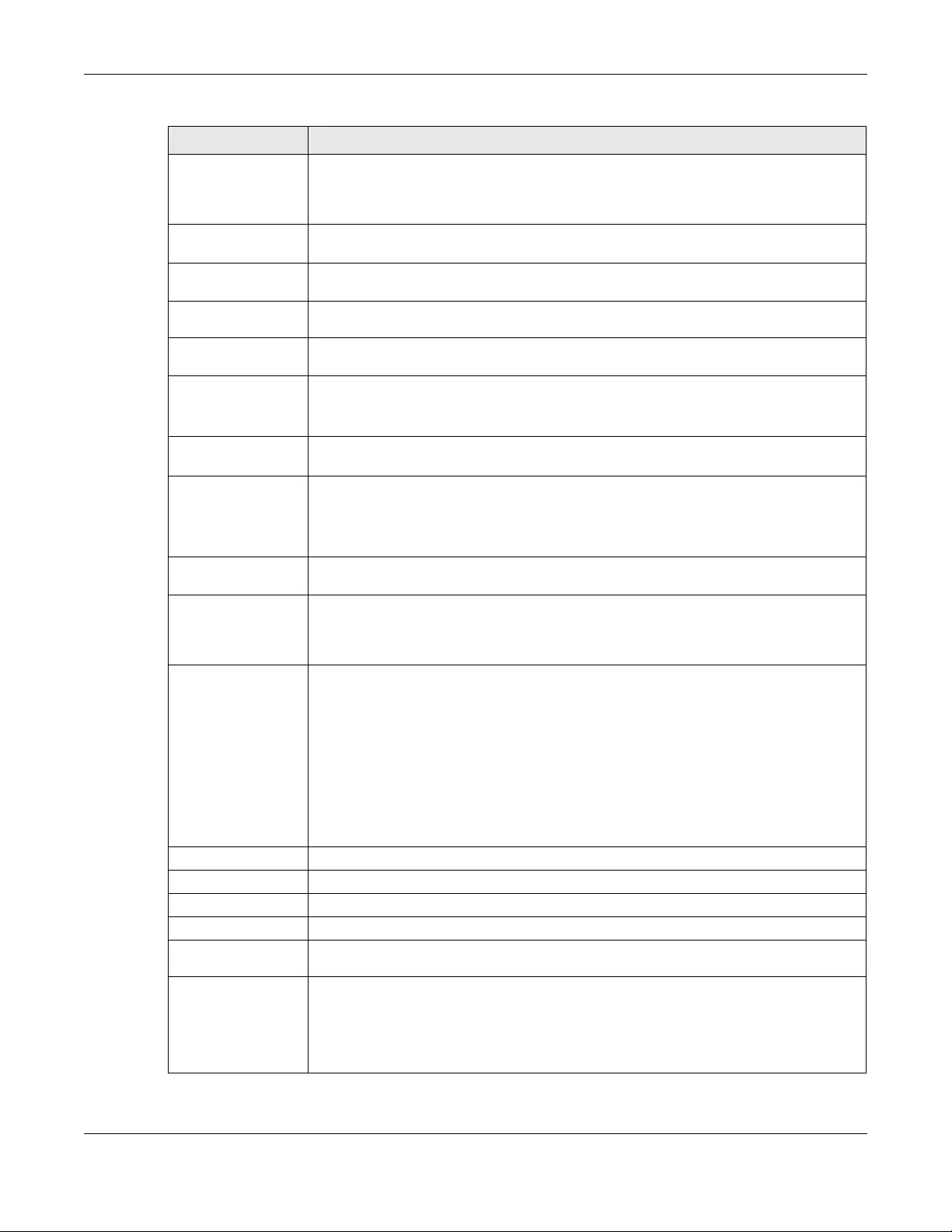
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
327
Metric Enter the priority of the gateway (if any) on this interface. The Zyxel Device decides which
gateway to use based on this priority. The lower the number, the higher the priority. If two or
more gateways have the same priority, the Zyxel Device uses the one that was configured
first.
Enable IGMP Support Select this to allow the Zyxel Device to act as an IGMP proxy for hosts connected on the
IGMP downstream interface.
IGMP Upstream Enable IGMP Upstream on the interface which connects to a router running IGMP that is
closer to the multicast server.
IGMP
Downstream Enable IGMP Downstream on the interface which connects to the multicast hosts.
IPv6 Address
Assignment
These IP address fields configure an IPv6 IP address on the interface itself.
Enable Stateless
Address Auto-
configuration
(SLAAC)
Select this to enable IPv6 stateless auto-configuration on this interface. The interface will
generate an IPv6 IP address itself from a prefix obtained from an IPv6 router in the network.
Link-Local
address This displays the IPv6 link-local address and the network prefix that the Zyxel Device
generates itself for the interface.
IPv6 Address/
Prefix Length Enter the IPv6 address and the prefix length for this interface if you want to configure a
static IP address for this interface. This field is optional.
The prefix length indicates what the left-most part of the IP address is the same for all
computers in the network, that is, the network address.
Gateway Enter the IPv6 address of the default outgoing gateway using colon (:) hexadecimal
notation.
Metric Enter the priority of the gateway (if any) on this interface. The Zyxel Device decides which
gateway to use based on this priority. The lower the number, the higher the priority. If two or
more gateways have the same priority, the Zyxel Device uses the one that was configured
first.
Address from
DHCPv6 Prefix
Delegation
Use this table to have the Zyxel Device obtain an IPv6 prefix from the ISP or a connected
uplink router for an internal network, such as the LAN or DMZ. You have to also enter a suffix
address which is appended to the delegated prefix to form an address for this interface.
See Prefix Delegation on page 273 for more information.
To use prefix delegation, you must:
• Create at least one DHCPv6 request object before configuring this table.
• The external interface must be a DHCPv6 client. You must configure the DHCPv6
request options using a DHCPv6 request object with the type of prefix-delegation.
• Assign the prefix delegation to an internal interface and enable router advertisement
on that interface.
Add Click this to create an entry.
Edit Select an entry and click this to change the settings.
Remove Select an entry and click this to delete it from this table.
# This field is a sequential value, and it is not associated with any entry.
Delegated
Prefix Select the DHCPv6 request object to use from the drop-down list.
Suffix
Address Enter the ending part of the IPv6 address, a slash (/), and the prefix length. The Zyxel Device
will append it to the delegated prefix.
For example, you got a delegated prefix of 2003:1234:5678/48. You want to configure an IP
address of 2003:1234:5678:1111::1/128 for this interface, then enter ::1111:0:0:0:1/128 in this
field.
Table 114 Configuration > Network > Interface > VLAN > Add / Edit (continued)
LABEL DESCRIPTION
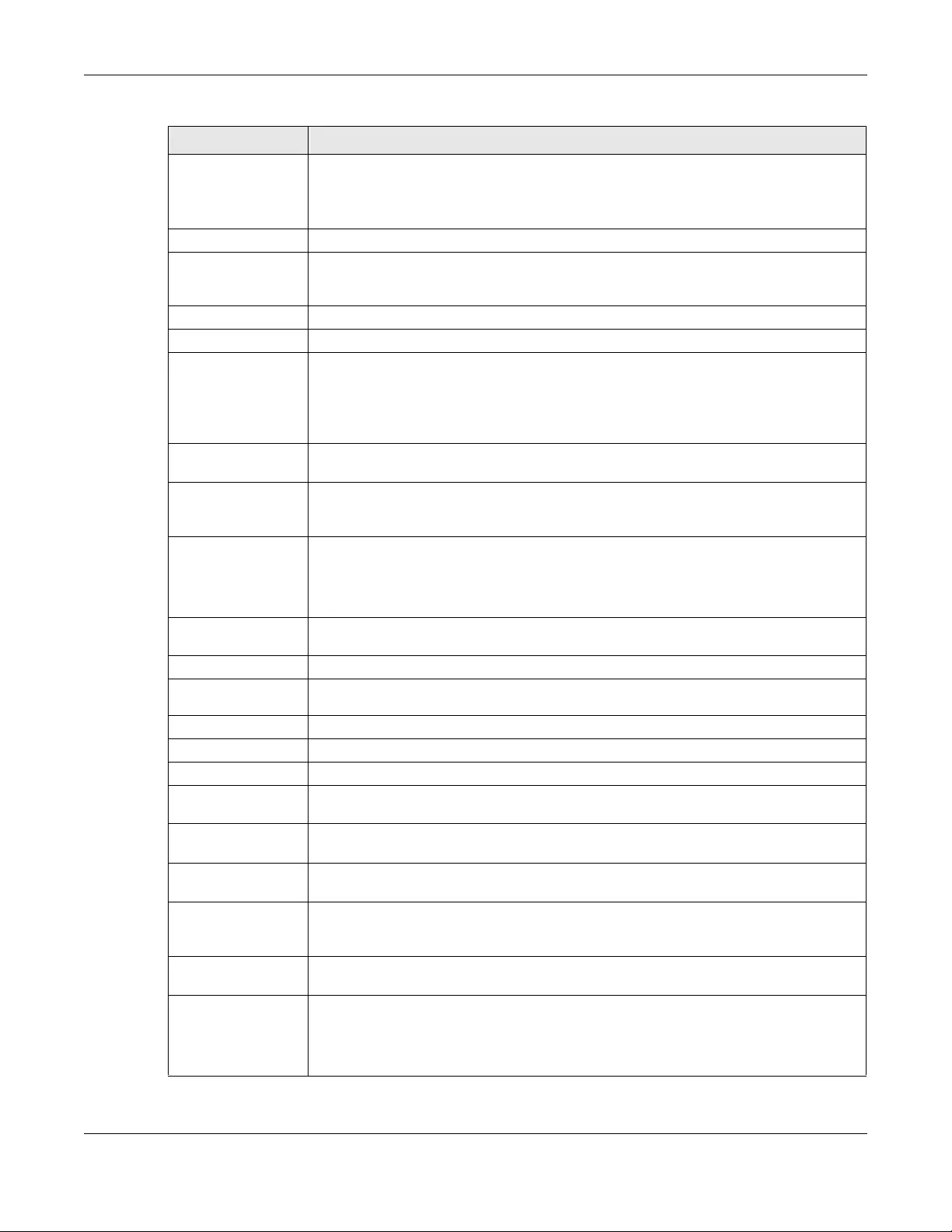
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
328
Address This field displays the combined IPv6 IP address for this interface.
Note: This field displays the combined address after you click OK and reopen this
screen.
DHCPv6 Setting
DUID This field displays the DHCP Unique IDentifier (DUID) of the interface, which is unique and
used for identification purposes when the interface is exchanging DHCPv6 messages with
others. See DHCPv6 on page 274 for more information.
DUID as MAC Select this to have the DUID generated from the interface’s default MAC address.
Customized DUID If you want to use a customized DUID, enter it here for the interface.
Enable Rapid
Commit Select this to shorten the DHCPv6 message exchange process from four to two steps. This
function helps reduce heavy network traffic load.
Note: Make sure you also enable this option in the DHCPv6 clients to make rapid
commit work.
Information
Refresh Time Enter the number of seconds a DHCPv6 client should wait before refreshing information
retrieved from DHCPv6.
Request Address This field is available if you set this interface to DHCPv6 Client. Select this to get an IPv6 IP
address for this interface from the DHCP server. Clear this to not get any IP address
information through DHCPv6.
DHCPv6 Request
Options /
DHCPv6 Lease
Options
If this interface is a DHCPv6 client, use this section to configure DHCPv6 request settings that
determine what additional information to get from the DHCPv6 server.
If this interface is a DHCPv6 server, use this section to configure DHCPv6 lease settings that
determine what to offer to the DHCPv6 clients.
Add Click this to create an entry in this table. See Section 10.4.5 on page 295 for more
information.
Remove Select an entry and click this to change the settings.
Object
Reference Select an entry and click this to delete it from this table.
# This field is a sequential value, and it is not associated with any entry.
Name This field displays the name of the DHCPv6 request or lease object.
Type This field displays the type of the object.
Value This field displays the IPv6 prefix that the Zyxel Device obtained from an uplink router (Server
is selected) or will advertise to its clients (Client is selected).
Interface When Relay is selected, select this check box and an interface from the drop-down list if
you want to use it as the relay server.
Relay Server When Relay is selected, select this check box and enter the IP address of a DHCPv6 server
as the relay server.
IPv6 Router
Advertisement
Setting
Enable Router
Advertisement Select this to enable this interface to send router advertisement messages periodically. See
IPv6 Router Advertisement on page 273 for more information.
Advertised Hosts
Get Network
Configuration
From DHCPv6
Select this to have the Zyxel Device indicate to hosts to obtain network settings (such as
prefix and DNS settings) through DHCPv6.
Clear this to have the Zyxel Device indicate to hosts that DHCPv6 is not available and they
should use the prefix in the router advertisement message.
Table 114 Configuration > Network > Interface > VLAN > Add / Edit (continued)
LABEL DESCRIPTION
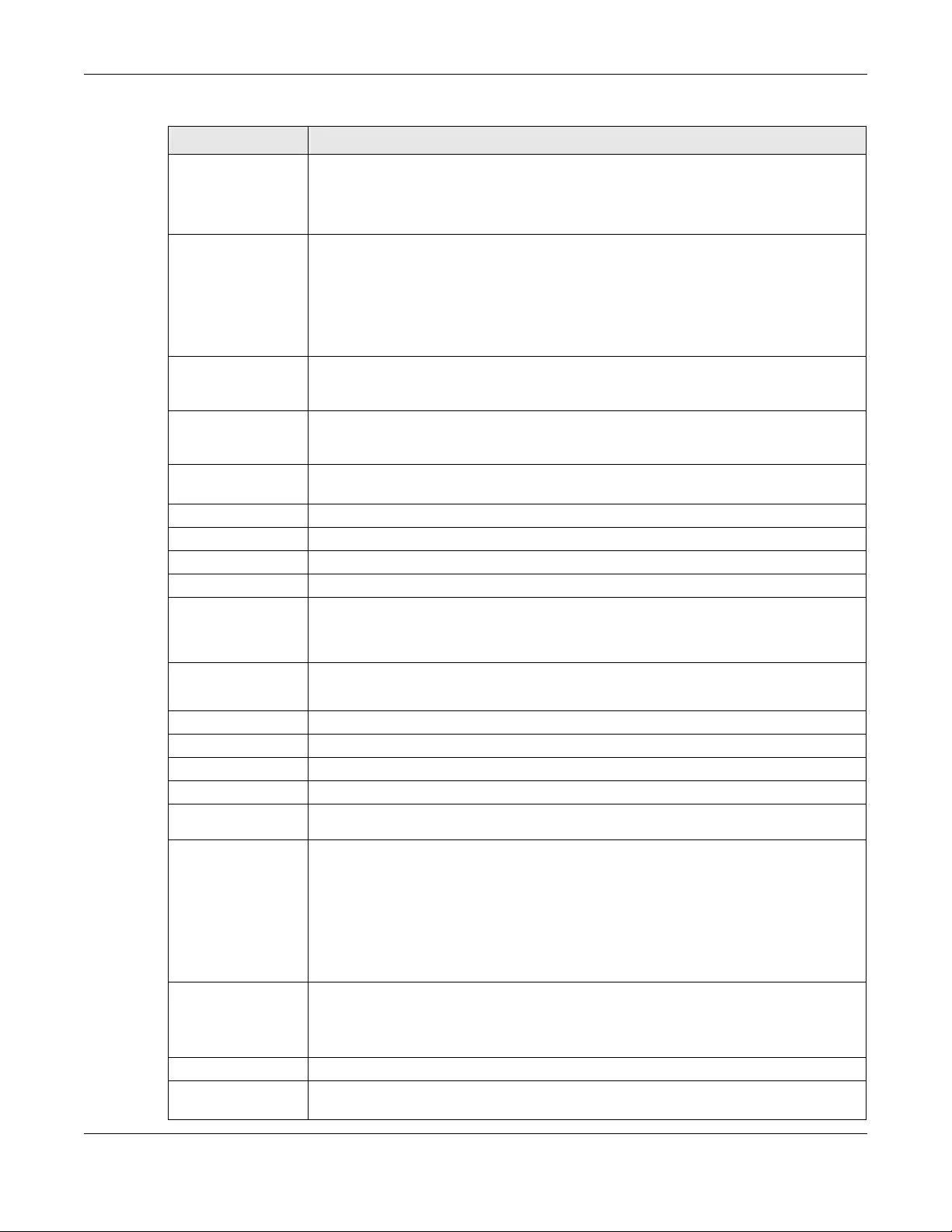
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
329
Advertised Hosts
Get Other
Configuration
From DHCPv6
Select this to have the Zyxel Device indicate to hosts to obtain DNS information through
DHCPv6.
Clear this to have the Zyxel Device indicate to hosts that DNS information is not available in
this network.
Router
Preference Select the router preference (Low, Medium or High) for the interface. The interface sends
this preference in the router advertisements to tell hosts what preference they should use
for the Zyxel Device. This helps hosts to choose their default router especially when there
are multiple IPv6 router in the network.
Note: Make sure the hosts also support router preference to make this function
work.
MTU The Maximum Transmission Unit. Type the maximum size of each IPv6 data packet, in bytes,
that can move through this interface. If a larger packet arrives, the Zyxel Device divides it
into smaller fragments.
Hop Limit Enter the maximum number of network segments that a packet can cross before reaching
the destination. When forwarding an IPv6 packet, IPv6 routers are required to decrease the
Hop Limit by 1 and to discard the IPv6 packet when the Hop Limit is 0.
Advertised Prefix
Table Configure this table only if you want the Zyxel Device to advertise a fixed prefix to the
network.
Add Click this to create an IPv6 prefix address.
Edit Select an entry in this table and click this to modify it.
Remove Select an entry in this table and click this to delete it.
# This field is a sequential value, and it is not associated with any entry.
IPv6
Address/
Prefix Length
Enter the IPv6 network prefix address and the prefix length.
The prefix length indicates what the left-most part of the IP address is the same for all
computers in the network, that is, the network address.
Advertised Prefix
from DHCPv6
Prefix Delegation
Use this table to configure the network prefix if you want to use a delegated prefix as the
beginning part of the network prefix.
Add Click this to create an entry in this table.
Edit Select an entry in this table and click this to modify it.
Remove Select an entry in this table and click this to delete it.
# This field is a sequential value, and it is not associated with any entry.
Delegated
Prefix Select the DHCPv6 request object to use for generating the network prefix for the network.
Suffix
Address Enter the ending part of the IPv6 network address plus a slash (/) and the prefix length. The
Zyxel Device will append it to the selected delegated prefix. The combined address is the
network prefix for the network.
For example, you got a delegated prefix of 2003:1234:5678/48. You want to divide it into
2003:1234:5678:1111/64 for this interface and 2003:1234:5678:2222/64 for another interface.
You can use ::1111/64 and ::2222/64 for the suffix address respectively. But if you do not
want to divide the delegated prefix into subnetworks, enter ::0/48 here, which keeps the
same prefix length (/48) as the delegated prefix.
Address This is the final network prefix combined by the delegated prefix and the suffix.
Note: This field displays the combined address after you click OK and reopen this
screen.
Interface Parameters
Egress Bandwidth Enter the maximum amount of traffic, in kilobits per second, the Zyxel Device can send
through the interface to the network. Allowed values are 0 - 1048576.
Table 114 Configuration > Network > Interface > VLAN > Add / Edit (continued)
LABEL DESCRIPTION
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
330
Ingress
Bandwidth This is reserved for future use.
Enter the maximum amount of traffic, in kilobits per second, the Zyxel Device can receive
from the network through the interface. Allowed values are 0 - 1048576.
MTU Maximum Transmission Unit. Type the maximum size of each data packet, in bytes, that can
move through this interface. If a larger packet arrives, the Zyxel Device divides it into smaller
fragments. Allowed values are 576 - 1500. Usually, this value is 1500.
Connectivity Check The Zyxel Device can regularly check the connection to the gateway you specified to
make sure it is still available. You specify how often to check the connection, how long to
wait for a response before the attempt is a failure, and how many consecutive failures are
required before the Zyxel Device stops routing to the gateway. The Zyxel Device resumes
routing to the gateway the first time the gateway passes the connectivity check.
Enable
Connectivity
Check
Select this to turn on the connection check.
Check Method Select the method that the gateway allows.
Select icmp to have the Zyxel Device regularly ping the gateway you specify to make sure
it is still available.
Select tcp to have the Zyxel Device regularly perform a TCP handshake with the gateway
you specify to make sure it is still available.
Check Period Enter the number of seconds between connection check attempts.
Check Timeout Enter the number of seconds to wait for a response before the attempt is a failure.
Check Fail
Tolerance Enter the number of consecutive failures before the Zyxel Device stops routing through the
gateway.
Check Default
Gateway Select this to use the default gateway for the connectivity check.
Check this
address Select this to specify a domain name or IP address for the connectivity check. Enter that
domain name or IP address in the field next to it.
Check Port This field only displays when you set the Check Method to tcp. Specify the port number to
use for a TCP connectivity check.
DHCP Setting The DHCP settings are available for the OPT, LAN and DMZ interfaces.
DHCP Select what type of DHCP service the Zyxel Device provides to the network. Choices are:
None - the Zyxel Device does not provide any DHCP services. There is already a DHCP
server on the network.
DHCP Relay - the Zyxel Device routes DHCP requests to one or more DHCP servers you
specify. The DHCP server(s) may be on another network.
DHCP Server - the Zyxel Device assigns IP addresses and provides subnet mask, gateway,
and DNS server information to the network. The Zyxel Device is the DHCP server for the
network.
These fields appear if the Zyxel Device is a DHCP Relay.
Relay Server 1 Enter the IP address of a DHCP server for the network.
Relay Server 2 This field is optional. Enter the IP address of another DHCP server for the network.
These fields appear if the Zyxel Device is a DHCP Server.
IP Pool Start
Address Enter the IP address from which the Zyxel Device begins allocating IP addresses. If you want
to assign a static IP address to a specific computer, click Add Static DHCP.
If this field is blank, the Pool Size must also be blank. In this case, the Zyxel Device can assign
every IP address allowed by the interface’s IP address and subnet mask, except for the first
address (network address), last address (broadcast address) and the interface’s IP address.
Table 114 Configuration > Network > Interface > VLAN > Add / Edit (continued)
LABEL DESCRIPTION
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
331
Pool Size Enter the number of IP addresses to allocate. This number must be at least one and is
limited by the interface’s Subnet Mask. For example, if the Subnet Mask is 255.255.255.0 and
IP Pool Start Address is 10.10.10.10, the Zyxel Device can allocate 10.10.10.10 to
10.10.10.254, or 245 IP addresses.
If this field is blank, the IP Pool Start Address must also be blank. In this case, the Zyxel Device
can assign every IP address allowed by the interface’s IP address and subnet mask, except
for the first address (network address), last address (broadcast address) and the interface’s
IP address.
First DNS Server
Second DNS
Server
Third DNS Server
Specify the IP addresses up to three DNS servers for the DHCP clients to use. Use one of the
following ways to specify these IP addresses.
Custom Defined - enter a static IP address.
From ISP - select the DNS server that another interface received from its DHCP server.
Zyxel Device - the DHCP clients use the IP address of this interface and the Zyxel Device
works as a DNS relay.
First WINS Server,
Second WINS
Server
Type the IP address of the WINS (Windows Internet Naming Service) server that you want to
send to the DHCP clients. The WINS server keeps a mapping table of the computer names
on your network and the IP addresses that they are currently using.
Default Router If you set this interface to DHCP Server, you can select to use either the interface’s IP
address or another IP address as the default router. This default router will become the
DHCP clients’ default gateway.
To use another IP address as the default router, select Custom Defined and enter the IP
address.
Lease time Specify how long each computer can use the information (especially the IP address)
before it has to request the information again. Choices are:
infinite - select this if IP addresses never expire
days, hours, and minutes - select this to enter how long IP addresses are valid. The default is
2 days.
Extended
Options This table is available if you selected DHCP server.
Configure this table if you want to send more information to DHCP clients through DHCP
packets.
Add Click this to create an entry in this table. See Section 10.4.6 on page 295.
Edit Select an entry in this table and click this to modify it.
Remove Select an entry in this table and click this to delete it.
# This field is a sequential value, and it is not associated with any entry.
Name This is the option’s name.
Code This is the option’s code number.
Type This is the option’s type.
Value This is the option’s value.
Enable IP/MAC
Binding Select this option to have the Zyxel Device enforce links between specific IP addresses and
specific MAC addresses for this VLAN. This stops anyone else from manually using a bound
IP address on another device connected to this interface. Use this to make use only the
intended users get to use specific IP addresses.
Enable Logs for
IP/MAC Binding
Violation
Select this option to have the Zyxel Device generate a log if a device connected to this
VLAN attempts to use an IP address that is bound to another device’s MAC address.
Static DHCP
Table Configure a list of static IP addresses the Zyxel Device assigns to computers connected to
the interface. Otherwise, the Zyxel Device assigns an IP address dynamically using the
interface’s IP Pool Start Address and Pool Size.
Table 114 Configuration > Network > Interface > VLAN > Add / Edit (continued)
LABEL DESCRIPTION
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
332
Add Click this to create a new entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
# This field is a sequential value, and it is not associated with a specific entry.
IP Address Enter the IP address to assign to a device with this entry’s MAC address.
MAC Address Enter the MAC address to which to assign this entry’s IP address.
Description Enter a description to help identify this static DHCP entry. You can use alphanumeric and
()+/:=?!*#@$_%- characters, and it can be up to 60 characters long.
RIP Setting See Section 11.6 on page 379 for more information about RIP.
Enable RIP Select this to enable RIP on this interface.
Direction This field is effective when RIP is enabled. Select the RIP direction from the drop-down list
box.
BiDir - This interface sends and receives routing information.
In-Only - This interface receives routing information.
Out-Only - This interface sends routing information.
Send Version This field is effective when RIP is enabled. Select the RIP version(s) used for sending RIP
packets. Choices are 1, 2, and 1 and 2.
Receive Version This field is effective when RIP is enabled. Select the RIP version(s) used for receiving RIP
packets. Choices are 1, 2, and 1 and 2.
V2-Broadcast This field is effective when RIP is enabled. Select this to send RIP-2 packets using subnet
broadcasting; otherwise, the Zyxel Device uses multicasting.
OSPF Setting See Section 11.7 on page 381 for more information about OSPF.
Area Select the area in which this interface belongs. Select None to disable OSPF in this
interface.
Priority Enter the priority (between 0 and 255) of this interface when the area is looking for a
Designated Router (DR) or Backup Designated Router (BDR). The highest-priority interface
identifies the DR, and the second-highest-priority interface identifies the BDR. Set the priority
to zero if the interface can not be the DR or BDR.
Link Cost Enter the cost (between 1 and 65,535) to route packets through this interface.
Passive Interface Select this to stop forwarding OSPF routing information from the selected interface. As a
result, this interface only receives routing information.
Authentication Select an authentication method, or disable authentication. To exchange OSPF routing
information with peer border routers, you must use the same authentication method that
they use. Choices are:
Same-as-Area - use the default authentication method in the area
None - disable authentication
Text - authenticate OSPF routing information using a plain-text password
MD5 - authenticate OSPF routing information using MD5 encryption
Text
Authentication
Key
This field is available if the Authentication is Text. Type the password for text authentication.
The key can consist of alphanumeric characters and the underscore, and it can be up to
16 characters long.
MD5
Authentication ID This field is available if the Authentication is MD5. Type the ID for MD5 authentication. The ID
can be between 1 and 255.
MD5
Authentication
Key
This field is available if the Authentication is MD5. Type the password for MD5
authentication. The password can consist of alphanumeric characters and the underscore,
and it can be up to 16 characters long.
Table 114 Configuration > Network > Interface > VLAN > Add / Edit (continued)
LABEL DESCRIPTION
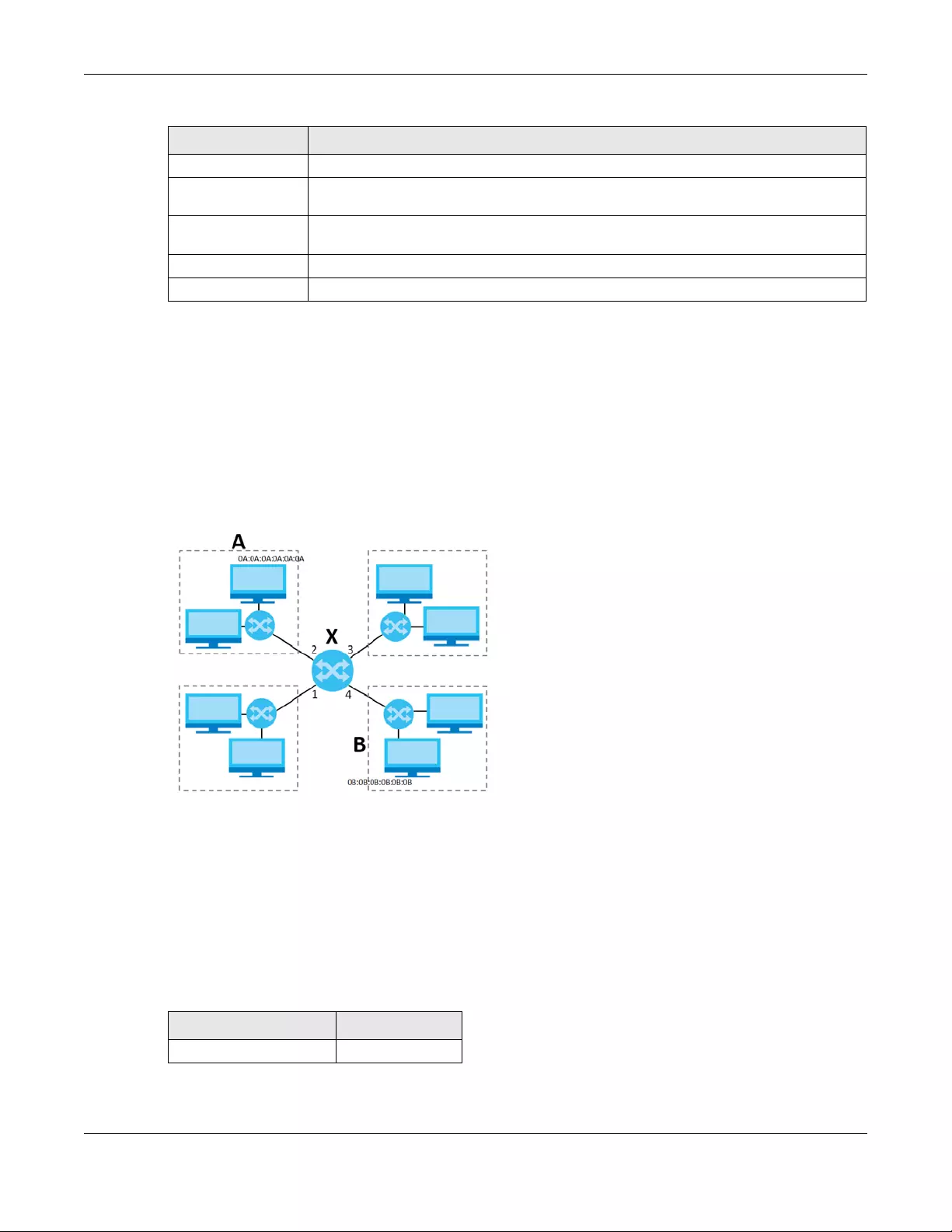
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
333
10.9 Bridge Interfaces
This section introduces bridges and bridge interfaces and then explains the screens for bridge interfaces.
Bridge Overview
A bridge creates a connection between two or more network segments at the layer-2 (MAC address)
level. In the following example, bridge X connects four network segments.
When the bridge receives a packet, the bridge records the source MAC address and the port on which
it was received in a table. It also looks up the destination MAC address in the table. If the bridge knows
on which port the destination MAC address is located, it sends the packet to that port. If the destination
MAC address is not in the table, the bridge broadcasts the packet on every port (except the one on
which it was received).
In the example above, computer A sends a packet to computer B. Bridge X records the source address
0A:0A:0A:0A:0A:0A and port 2 in the table. It also looks up 0B:0B:0B:0B:0B:0B in the table. There is no entry
yet, so the bridge broadcasts the packet on ports 1, 3, and 4.
Related Setting
Configure WAN
TRUNK Click WAN TRUNK to go to a screen where you can set this VLAN to be part of a WAN trunk
for load balancing.
Configure Policy
Route Click Policy Route to go to the screen where you can manually configure a policy route to
associate traffic with this VLAN.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 114 Configuration > Network > Interface > VLAN > Add / Edit (continued)
LABEL DESCRIPTION
Table 115 Example: Bridge Table After Computer A Sends a Packet to Computer B
MAC ADDRESS PORT
0A:0A:0A:0A:0A:0A 2
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
334
If computer B responds to computer A, bridge X records the source address 0B:0B:0B:0B:0B:0B and port 4
in the table. It also looks up 0A:0A:0A:0A:0A:0A in the table and sends the packet to port 2 accordingly.
Bridge Interface Overview
A bridge interface creates a software bridge between the members of the bridge interface. It also
becomes the Zyxel Device’s interface for the resulting network.
Unlike the device-wide bridge mode in ZyNOS-based Zyxel Devices, this Zyxel Device can bridge traffic
between some interfaces while it routes traffic for other interfaces. The bridge interfaces also support
more functions, like interface bandwidth parameters, DHCP settings, and connectivity check. To use the
whole Zyxel Device as a transparent bridge, add all of the Zyxel Device’s interfaces to a bridge
interface.
A bridge interface may consist of the following members:
• Zero or one VLAN interfaces (and any associated virtual VLAN interfaces)
• Any number of Ethernet interfaces (and any associated virtual Ethernet interfaces)
When you create a bridge interface, the Zyxel Device removes the members’ entries from the routing
table and adds the bridge interface’s entries to the routing table. For example, this table shows the
routing table before and after you create bridge interface br0 (250.250.250.0/23) between lan1 and
vlan1.
In this example, virtual Ethernet interface lan1:1 is also removed from the routing table when lan1 is
added to br0. Virtual interfaces are automatically added to or remove from a bridge interface when
the underlying interface is added or removed.
10.9.1 Bridge Summary
This screen lists every bridge interface and virtual interface created on top of bridge interfaces. If you
enabled IPv6 in the Configuration > System > IPv6 screen, you can also configure bridge interfaces used
for your IPv6 network on this screen. To access this screen, click Configuration > Network > Interface >
Bridge.
Table 116 Example: Bridge Table After Computer B Responds to Computer A
MAC ADDRESS PORT
0A:0A:0A:0A:0A:0A 2
0B:0B:0B:0B:0B:0B 4
Table 117 Example: Routing Table Before and After Bridge Interface br0 Is Created
IP ADDRESS(ES) DESTINATION IP ADDRESS(ES) DESTINATION
210.210.210.0/24 lan1 221.221.221.0/24 vlan0
210.211.1.0/24 lan1:1 230.230.230.192/26 wan2
221.221.221.0/24 vlan0 241.241.241.241/32 dmz
222.222.222.0/24 vlan1 242.242.242.242/32 dmz
230.230.230.192/26 wan2 250.250.250.0/23 br0
241.241.241.241/32 dmz
242.242.242.242/32 dmz
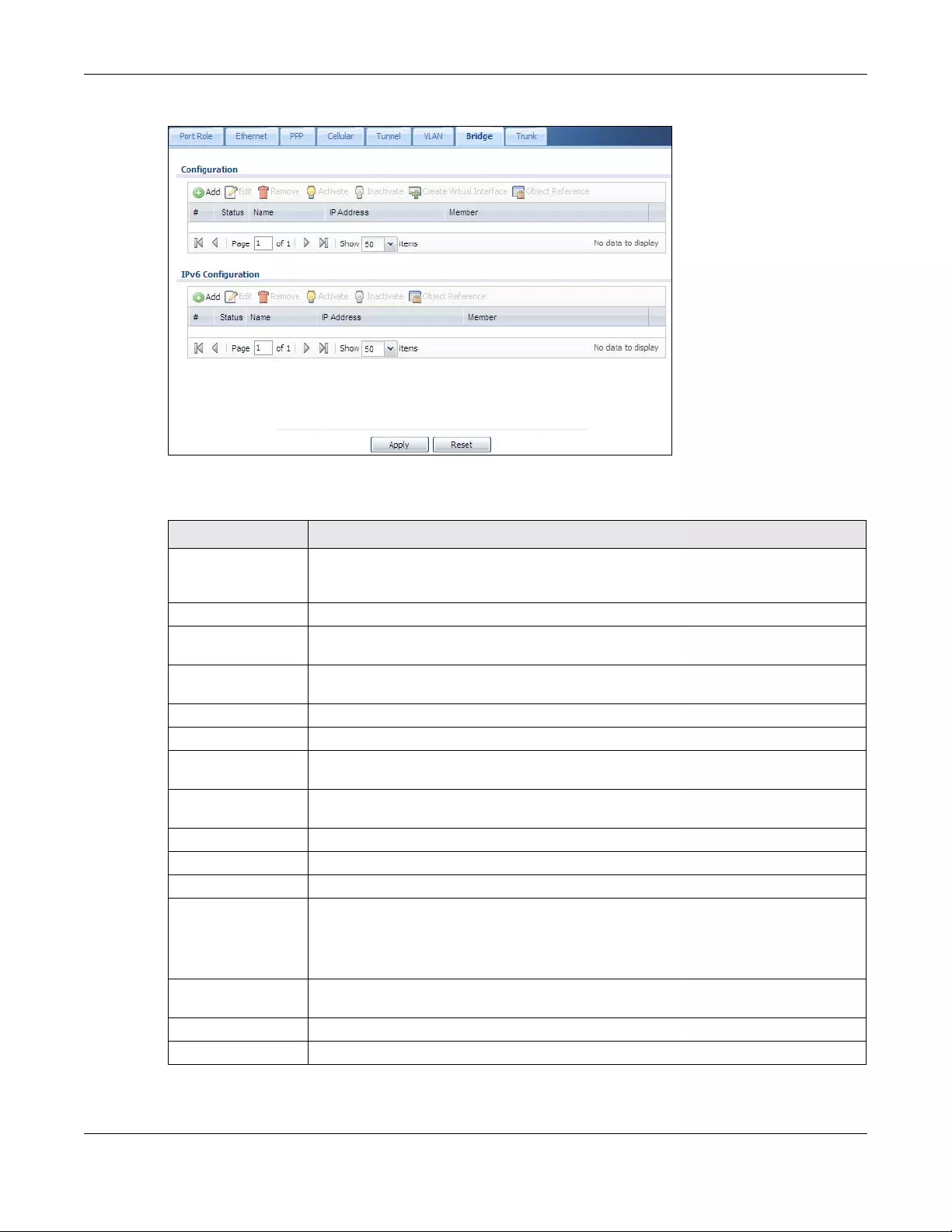
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
335
Figure 249 Configuration > Network > Interface > Bridge
Each field is described in the following table.
Table 118 Configuration > Network > Interface > Bridge
LABEL DESCRIPTION
Configuration / IPv6
Configuration
Use the Configuration section for IPv4 network settings. Use the IPv6 Configuration section
for IPv6 network settings if you connect your Zyxel Device to an IPv6 network. Both sections
have similar fields as described below.
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Create Virtual
Interface
To open the screen where you can create a virtual interface, select an interface and click
Create Virtual Interface.
Object References Select an entry and click Object Reference to open a screen that shows which settings use
the entry. See Section 10.4.4 on page 294 for an example.
# This field is a sequential value, and it is not associated with any interface.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
Name This field displays the name of the interface.
IP Address This field displays the current IP address of the interface. If the IP address is 0.0.0.0, the
interface does not have an IP address yet.
This screen also shows whether the IP address is a static IP address (STATIC) or dynamically
assigned (DHCP). IP addresses are always static in virtual interfaces.
Member This field displays the Ethernet interfaces and VLAN interfaces in the bridge interface. It is
blank for virtual interfaces.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
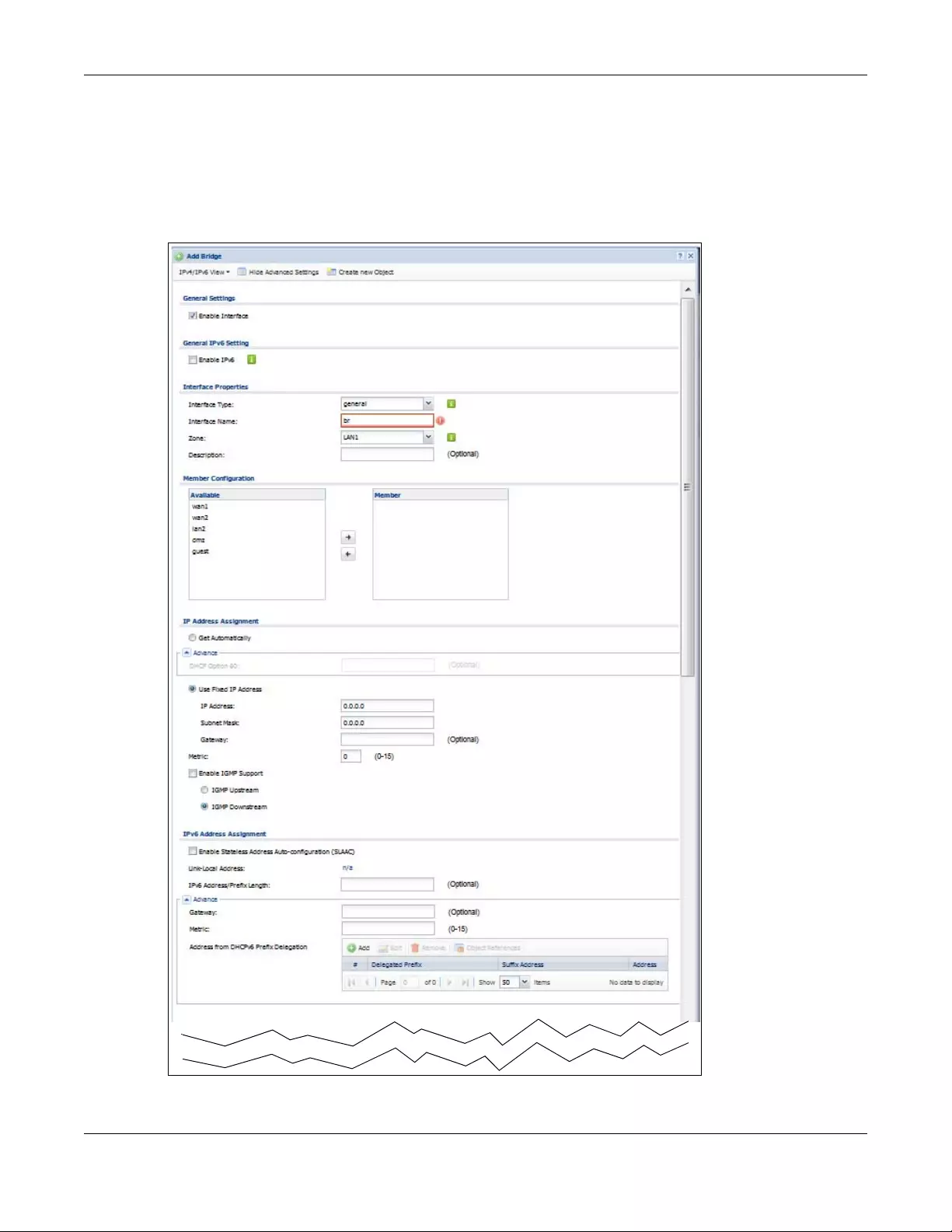
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
336
10.9.2 Bridge Add/Edit
This screen lets you configure IP address assignment, interface bandwidth parameters, DHCP settings,
and connectivity check for each bridge interface. To access this screen, click the Add or Edit icon in the
Bridge Summary screen. The following screen appears.
Figure 250 Configuration > Network > Interface > Bridge > Add / Edit
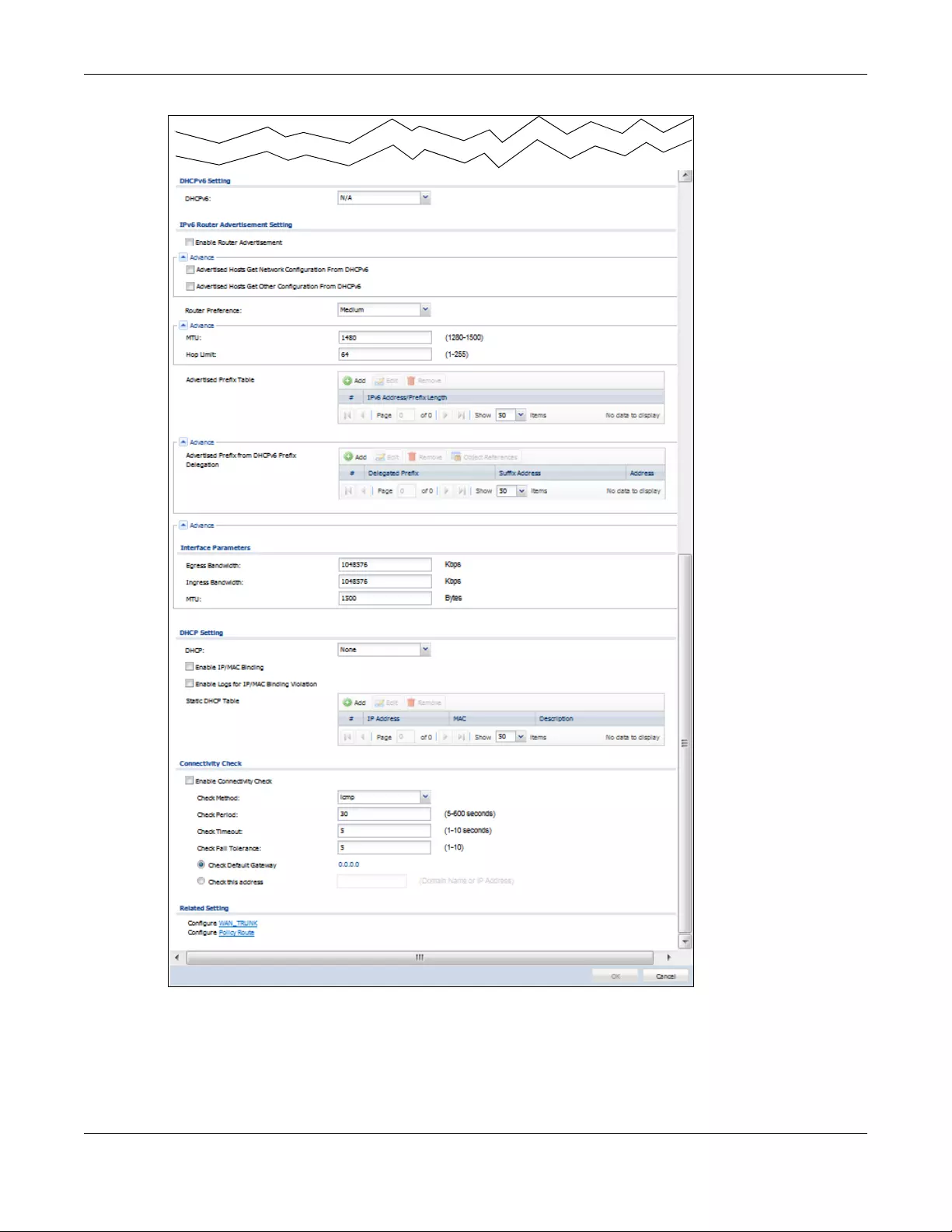
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
337
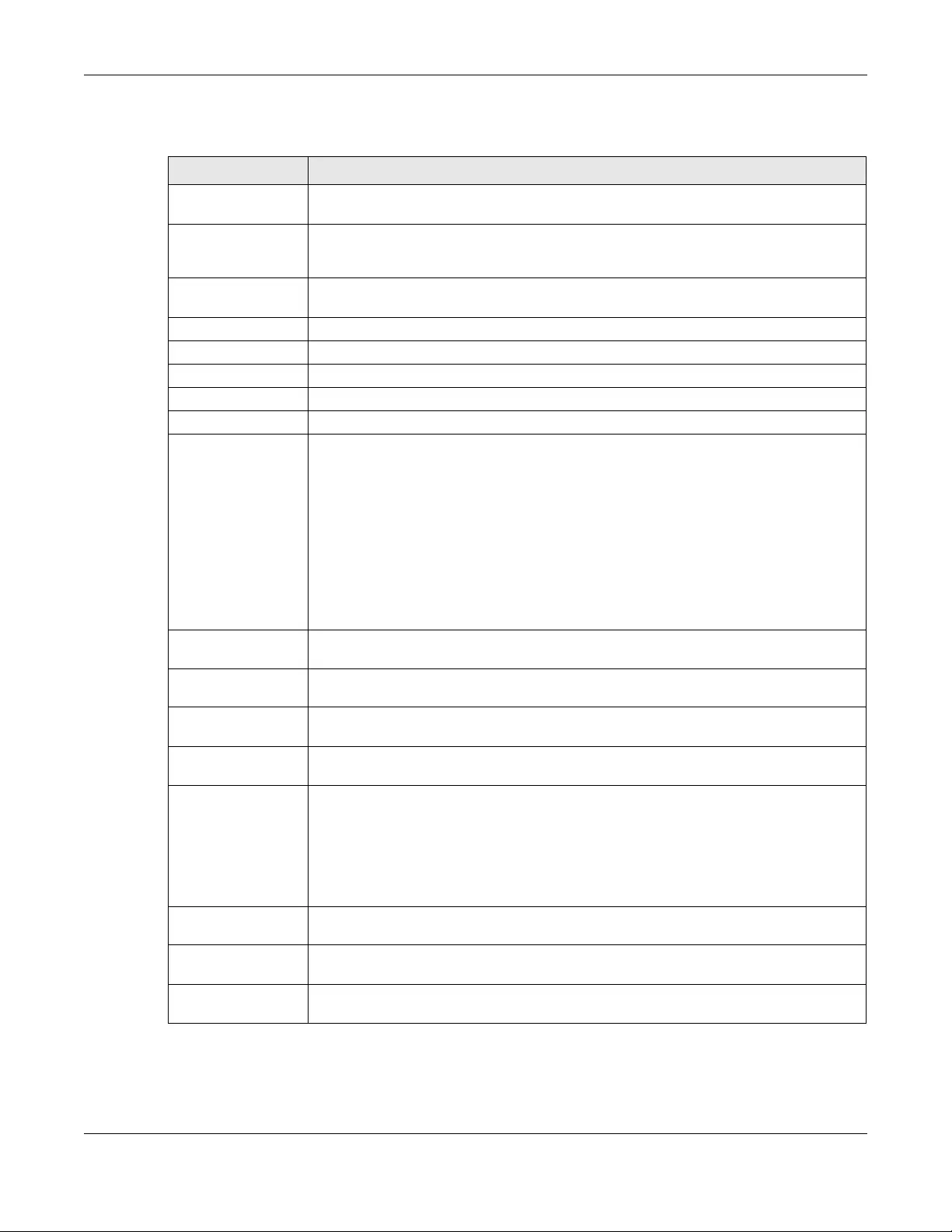
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
338
Each field is described in the table below.
Table 119 Configuration > Network > Interface > Bridge > Add / Edit
LABEL DESCRIPTION
IPv4/IPv6 View / IPv4
View / IPv6 View
Use this button to display both IPv4 and IPv6, IPv4-only, or IPv6-only configuration fields.
Show Advanced
Settings / Hide
Advanced Settings
Click this button to display a greater or lesser number of configuration fields.
Create New Object Click this button to create a DHCPv6 lease or DHCPv6 request object that you may use for
the DHCPv6 settings in this screen.
General Settings
Enable Interface Select this to enable this interface. Clear this to disable this interface.
General IPv6 Setting
Enable IPv6 Select this to enable IPv6 on this interface. Otherwise, clear this to disable it.
Interface Properties
Interface Type Select one of the following option depending on the type of network to which the Zyxel
Device is connected or if you want to additionally manually configure some related
settings.
internal is for connecting to a local network. Other corresponding configuration options:
DHCP server and DHCP relay. The Zyxel Device automatically adds default SNAT settings for
traffic flowing from this interface to an external interface.
external is for connecting to an external network (like the Internet). The Zyxel Device
automatically adds this interface to the default WAN trunk.
For general, the rest of the screen’s options do not automatically adjust and you must
manually configure a policy route to add routing and SNAT settings for the interface.
Interface Name This field is read-only if you are editing the interface. Enter the name of the bridge interface.
The format is brx, where x is 0 - 11. For example, br0, br3, and so on.
Zone Select the zone to which the interface is to belong. You use zones to apply security settings
such as security policy, IDP, remote management, anti-virus, and application patrol.
Description Enter a description of this interface. It is not used elsewhere. You can use alphanumeric and
()+/:=?!*#@$_%- characters, and it can be up to 60 characters long.
Member
Configuration
Available This field displays Ethernet interfaces and VLAN interfaces that can become part of the
bridge interface. An interface is not available in the following situations:
• There is a virtual interface on top of it
• It is already used in a different bridge interface
Select one, and click the >> arrow to add it to the bridge interface. Each bridge interface
can only have one VLAN interface.
Member This field displays the interfaces that are part of the bridge interface. Select one, and click
the << arrow to remove it from the bridge interface.
IP Address
Assignment
Get
Automatically Select this if this interface is a DHCP client. In this case, the DHCP server configures the IP
address, subnet mask, and gateway automatically.
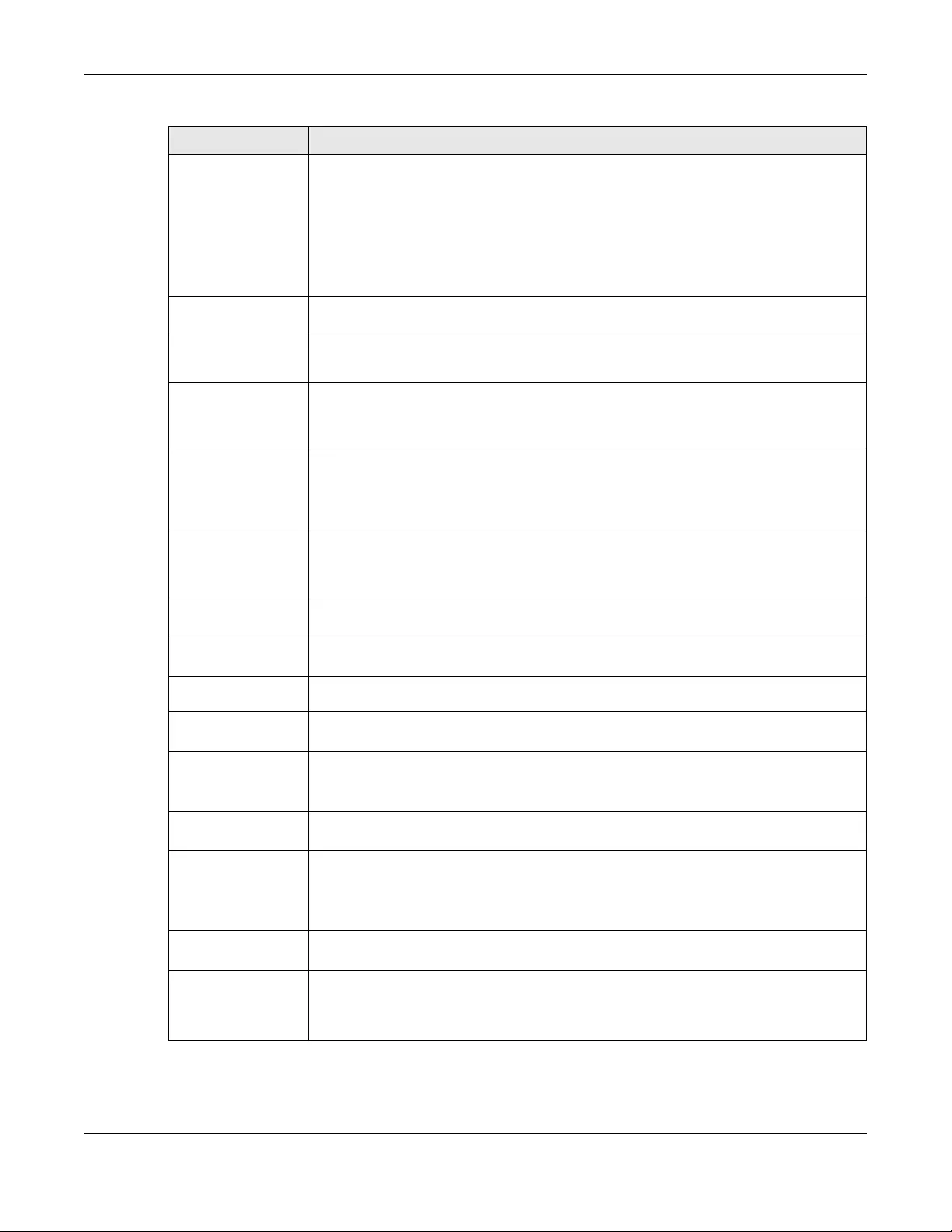
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
339
DHCP Option 60 DHCP Option 60 is used by the Zyxel Device for identification to the DHCP server using the
VCI (Vendor Class Identifier) on the DHCP server. The Zyxel Device adds it in the initial DHCP
discovery message that a DHCP client broadcasts in search of an IP address. The DHCP
server can assign different IP addresses or options to clients with the specific VCI or reject
the request from clients without the specific VCI.
Type a string using up to 64 of these characters [a-zA-Z0-9!\"#$%&\'()*+,-./
:;<=>?@\[\\\]^_`{|}~] to identify this Zyxel Device to the DHCP server. For example, Zyxel-
TW.
Use Fixed IP
Address Select this if you want to specify the IP address, subnet mask, and gateway manually.
IP Address This field is enabled if you select Use Fixed IP Address.
Enter the IP address for this interface.
Subnet Mask This field is enabled if you select Use Fixed IP Address.
Enter the subnet mask of this interface in dot decimal notation. The subnet mask indicates
what part of the IP address is the same for all computers in the network.
Gateway This field is enabled if you select Use Fixed IP Address.
Enter the IP address of the gateway. The Zyxel Device sends packets to the gateway when
it does not know how to route the packet to its destination. The gateway should be on the
same network as the interface.
Metric Enter the priority of the gateway (if any) on this interface. The Zyxel Device decides which
gateway to use based on this priority. The lower the number, the higher the priority. If two or
more gateways have the same priority, the Zyxel Device uses the one that was configured
first.
Enable IGMP Support Select this to allow the Zyxel Device to act as an IGMP proxy for hosts connected on the
IGMP downstream interface.
IGMP Upstream Enable IGMP Upstream on the interface which connects to a router running IGMP that is
closer to the multicast server.
IGMP
Downstream Enable IGMP Downstream on the interface which connects to the multicast hosts.
IPv6 Address
Assignment
These IP address fields configure an IPv6 IP address on the interface itself.
Enable Stateless
Address Auto-
configuration
(SLAAC)
Select this to enable IPv6 stateless auto-configuration on this interface. The interface will
generate an IPv6 IP address itself from a prefix obtained from an IPv6 router in the network.
Link-Local
address This displays the IPv6 link-local address and the network prefix that the Zyxel Device
generates itself for the interface.
IPv6 Address/
Prefix Length Enter the IPv6 address and the prefix length for this interface if you want to use a static IP
address. This field is optional.
The prefix length indicates what the left-most part of the IP address is the same for all
computers in the network, that is, the network address.
Gateway Enter the IPv6 address of the default outgoing gateway using colon (:) hexadecimal
notation.
Metric Enter the priority of the gateway (if any) on this interface. The Zyxel Device decides which
gateway to use based on this priority. The lower the number, the higher the priority. If two or
more gateways have the same priority, the Zyxel Device uses the one that was configured
first.
Table 119 Configuration > Network > Interface > Bridge > Add / Edit (continued)
LABEL DESCRIPTION
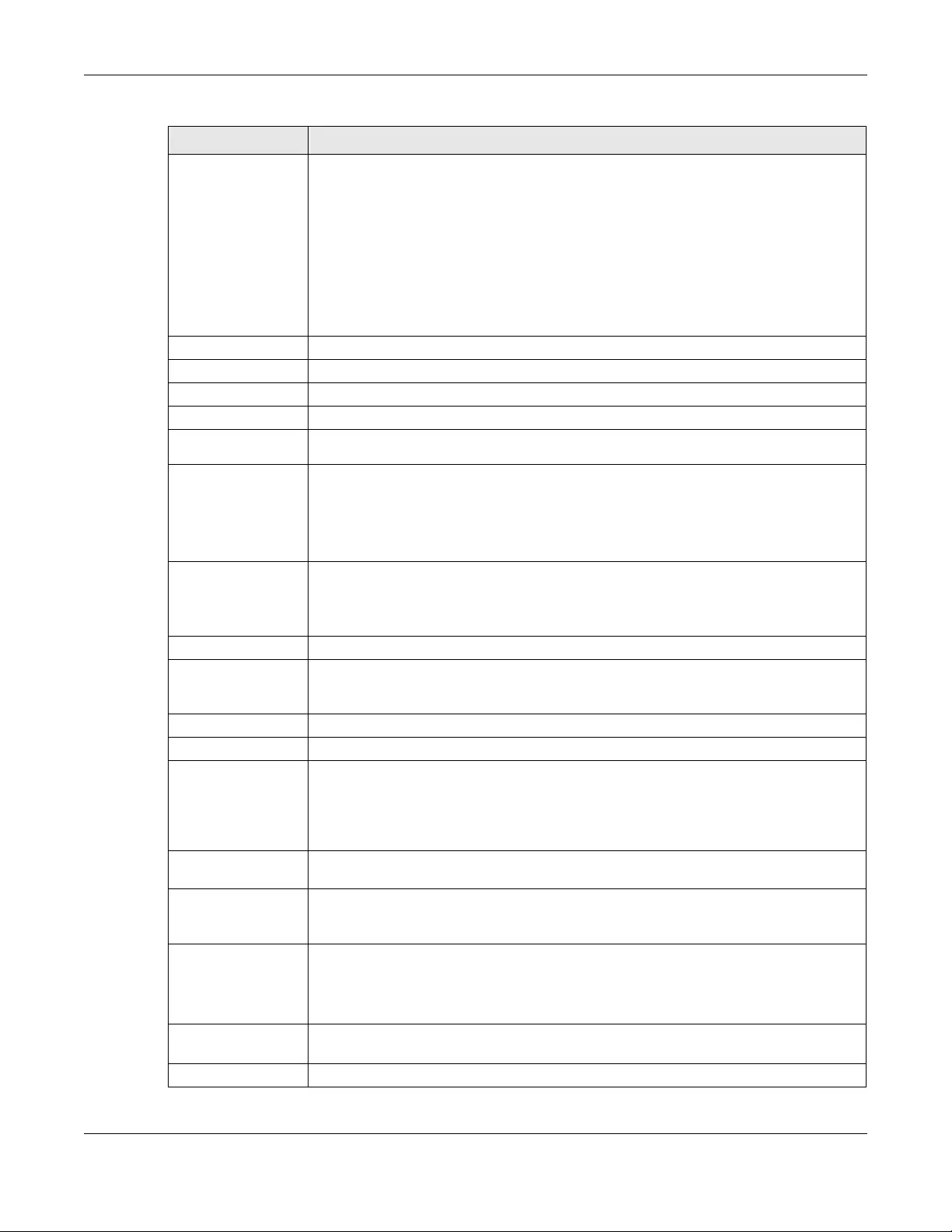
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
340
Address from
DHCPv6 Prefix
Delegation
Use this table to have the Zyxel Device obtain an IPv6 prefix from the ISP or a connected
uplink router for an internal network, such as the LAN or DMZ. You have to also enter a suffix
address which is appended to the delegated prefix to form an address for this interface.
See Prefix Delegation on page 273 for more information.
To use prefix delegation, you must:
• Create at least one DHCPv6 request object before configuring this table.
• The external interface must be a DHCPv6 client. You must configure the DHCPv6
request options using a DHCPv6 request object with the type of prefix-delegation.
• Assign the prefix delegation to an internal interface and enable router advertisement
on that interface.
Add Click this to create an entry.
Edit Select an entry and click this to change the settings.
Remove Select an entry and click this to delete it from this table.
# This field is a sequential value, and it is not associated with any entry.
Delegated
Prefix Select the DHCPv6 request object to use from the drop-down list.
Suffix
Address Enter the ending part of the IPv6 address, a slash (/), and the prefix length. The Zyxel Device
will append it to the delegated prefix.
For example, you got a delegated prefix of 2003:1234:5678/48. You want to configure an IP
address of 2003:1234:5678:1111:1/128 for this interface, then enter ::1111:0:0:0:1/128 in this
field.
Address This field displays the combined IPv6 IP address for this interface.
Note: This field displays the combined address after you click OK and reopen this
screen.
DHCPv6 Setting
DUID This field displays the DHCP Unique IDentifier (DUID) of the interface, which is unique and
used for identification purposes when the interface is exchanging DHCPv6 messages with
others. See DHCPv6 on page 274 for more information.
DUID as MAC Select this if you want the DUID is generated from the interface’s default MAC address.
Customized DUID If you want to use a customized DUID, enter it here for the interface.
Enable Rapid
Commit Select this to shorten the DHCPv6 message exchange process from four to two steps. This
function helps reduce heavy network traffic load.
Note: Make sure you also enable this option in the DHCPv6 clients to make rapid
commit work.
Information
Refresh Time Enter the number of seconds a DHCPv6 client should wait before refreshing information
retrieved from DHCPv6.
Request Address This field is available if you set this interface to DHCPv6 Client. Select this to get an IPv6 IP
address for this interface from the DHCP server. Clear this to not get any IP address
information through DHCPv6.
DHCPv6 Request
Options /
DHCPv6 Lease
Options
If this interface is a DHCPv6 client, use this section to configure DHCPv6 request settings that
determine what additional information to get from the DHCPv6 server.
If the interface is a DHCPv6 server, use this section to configure DHCPv6 lease settings that
determine what to offer to the DHCPv6 clients.
Add Click this to create an entry in this table. See Section 10.4.5 on page 295 for more
information.
Remove Select an entry and click this to change the settings.
Table 119 Configuration > Network > Interface > Bridge > Add / Edit (continued)
LABEL DESCRIPTION
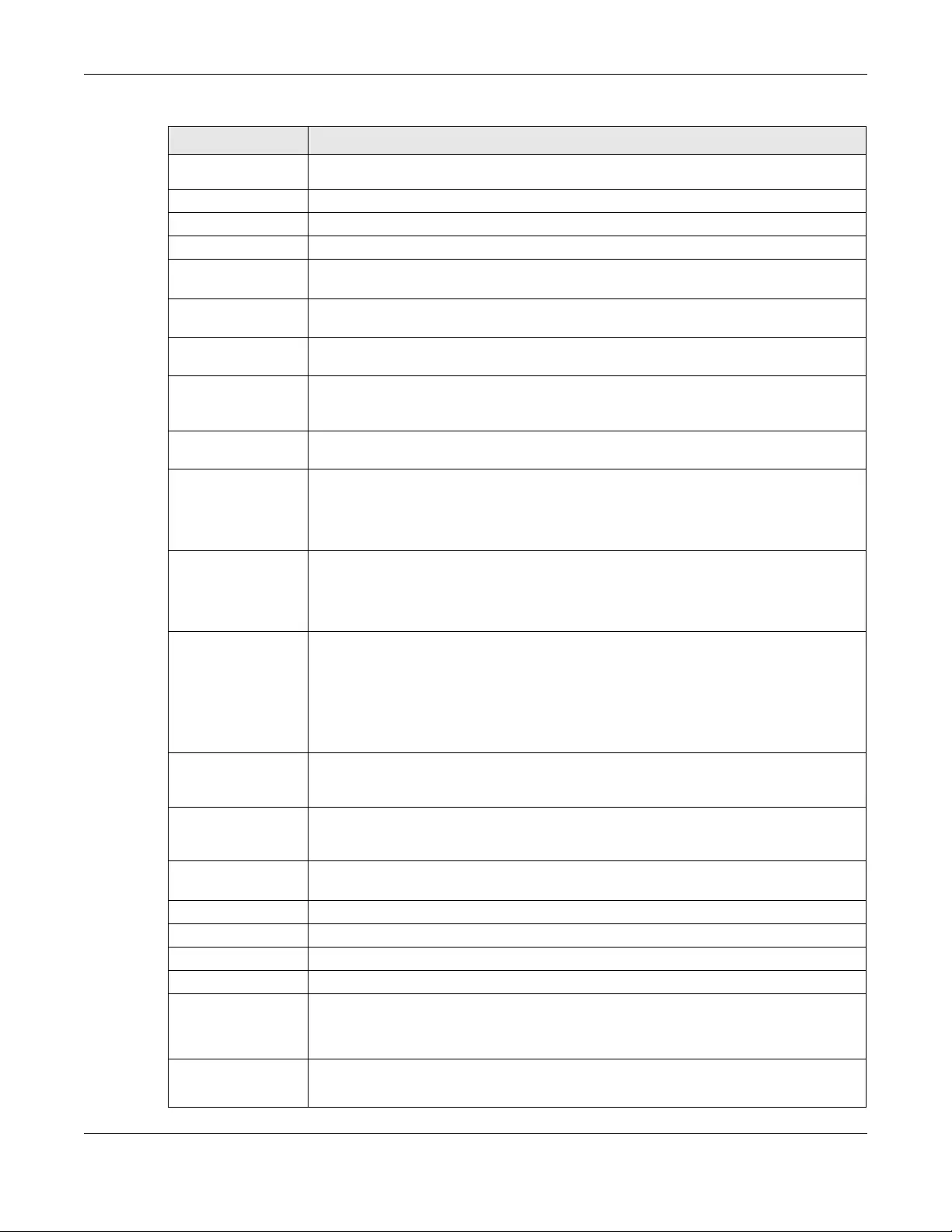
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
341
Object
Reference Select an entry and click this to delete it from this table.
# This field is a sequential value, and it is not associated with any entry.
Name This field displays the name of the DHCPv6 request or lease object.
Type This field displays the type of the object.
Value This field displays the IPv6 prefix that the Zyxel Device obtained from an uplink router (Server
is selected) or will advertise to its clients (Client is selected).
Interface When Relay is selected, select this check box and an interface from the drop-down list if
you want to use it as the relay server.
Relay Server When Relay is selected, select this check box and enter the IP address of a DHCPv6 server
as the relay server.
IPv6 Router
Advertisement
Setting
Enable Router
Advertisement Select this to enable this interface to send router advertisement messages periodically. See
IPv6 Router Advertisement on page 273 for more information.
Advertised Hosts
Get Network
Configuration
From DHCPv6
Select this to have the Zyxel Device indicate to hosts to obtain network settings (such as
prefix and DNS settings) through DHCPv6.
Clear this to have the Zyxel Device indicate to hosts that DHCPv6 is not available and they
should use the prefix in the router advertisement message.
Advertised Hosts
Get Other
Configuration
From DHCPv6
Select this to have the Zyxel Device indicate to hosts to obtain DNS information through
DHCPv6.
Clear this to have the Zyxel Device indicate to hosts that DNS information is not available in
this network.
Router
Preference Select the router preference (Low, Medium or High) for the interface. The interface sends
this preference in the router advertisements to tell hosts what preference they should use
for the Zyxel Device. This helps hosts to choose their default router especially when there
are multiple IPv6 router in the network.
Note: Make sure the hosts also support router preference to make this function
work.
MTU The Maximum Transmission Unit. Type the maximum size of each IPv6 data packet, in bytes,
that can move through this interface. If a larger packet arrives, the Zyxel Device divides it
into smaller fragments.
Hop Limit Enter the maximum number of network segments that a packet can cross before reaching
the destination. When forwarding an IPv6 packet, IPv6 routers are required to decrease the
Hop Limit by 1 and to discard the IPv6 packet when the Hop Limit is 0.
Advertised Prefix
Table Configure this table only if you want the Zyxel Device to advertise a fixed prefix to the
network.
Add Click this to create an IPv6 prefix address.
Edit Select an entry in this table and click this to modify it.
Remove Select an entry in this table and click this to delete it.
# This field is a sequential value, and it is not associated with any entry.
IPv6
Address/
Prefix Length
Enter the IPv6 network prefix address and the prefix length.
The prefix length indicates what the left-most part of the IP address is the same for all
computers in the network, that is, the network address.
Advertised Prefix
from DHCPv6
Prefix Delegation
Use this table to configure the network prefix if you want to use a delegated prefix as the
beginning part of the network prefix.
Table 119 Configuration > Network > Interface > Bridge > Add / Edit (continued)
LABEL DESCRIPTION
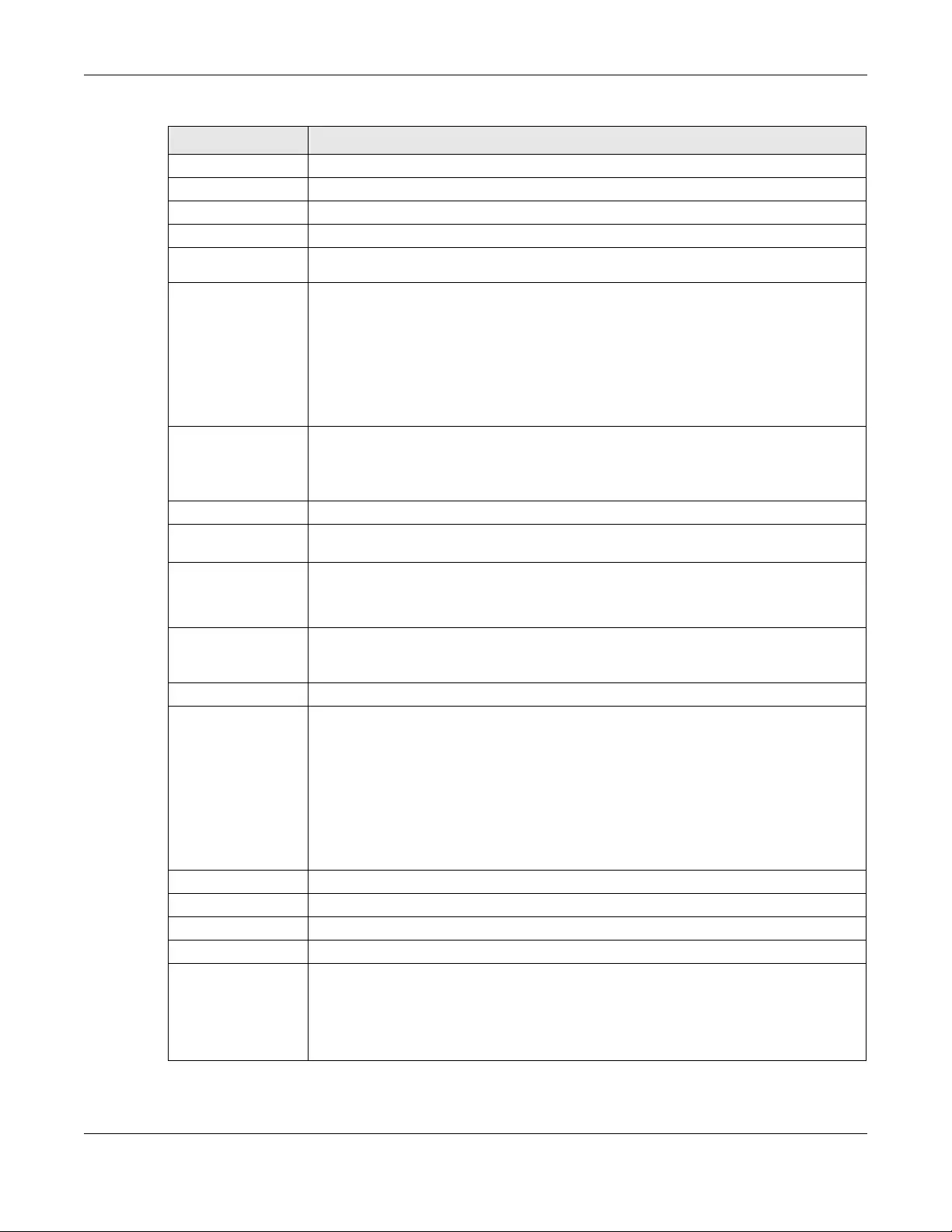
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
342
Add Click this to create an entry in this table.
Edit Select an entry in this table and click this to modify it.
Remove Select an entry in this table and click this to delete it.
# This field is a sequential value, and it is not associated with any entry.
Delegated
Prefix Select the DHCPv6 request object to use for generating the network prefix for the network.
Suffix
Address Enter the ending part of the IPv6 network address plus a slash (/) and the prefix length. The
Zyxel Device will append it to the selected delegated prefix. The combined address is the
network prefix for the network.
For example, you got a delegated prefix of 2003:1234:5678/48. You want to divide it into
2003:1234:5678:1111/64 for this interface and 2003:1234:5678:2222/64 for another interface.
You can use ::1111/64 and ::2222/64 for the suffix address respectively. But if you do not
want to divide the delegated prefix into subnetworks, enter ::0/48 here, which keeps the
same prefix length (/48) as the delegated prefix.
Address This is the final network prefix combined by the selected delegated prefix and the suffix.
Note: This field displays the combined address after you click OK and reopen this
screen.
Interface Parameters
Egress Bandwidth Enter the maximum amount of traffic, in kilobits per second, the Zyxel Device can send
through the interface to the network. Allowed values are 0 - 1048576.
Ingress
Bandwidth This is reserved for future use.
Enter the maximum amount of traffic, in kilobits per second, the Zyxel Device can receive
from the network through the interface. Allowed values are 0 - 1048576.
MTU Maximum Transmission Unit. Type the maximum size of each data packet, in bytes, that can
move through this interface. If a larger packet arrives, the Zyxel Device divides it into smaller
fragments. Allowed values are 576 - 1500. Usually, this value is 1500.
DHCP Setting
DHCP Select what type of DHCP service the Zyxel Device provides to the network. Choices are:
None - the Zyxel Device does not provide any DHCP services. There is already a DHCP
server on the network.
DHCP Relay - the Zyxel Device routes DHCP requests to one or more DHCP servers you
specify. The DHCP server(s) may be on another network.
DHCP Server - the Zyxel Device assigns IP addresses and provides subnet mask, gateway,
and DNS server information to the network. The Zyxel Device is the DHCP server for the
network.
These fields appear if the Zyxel Device is a DHCP Relay.
Relay Server 1 Enter the IP address of a DHCP server for the network.
Relay Server 2 This field is optional. Enter the IP address of another DHCP server for the network.
These fields appear if the Zyxel Device is a DHCP Server.
IP Pool Start
Address Enter the IP address from which the Zyxel Device begins allocating IP addresses. If you want
to assign a static IP address to a specific computer, click Add Static DHCP.
If this field is blank, the Pool Size must also be blank. In this case, the Zyxel Device can assign
every IP address allowed by the interface’s IP address and subnet mask, except for the first
address (network address), last address (broadcast address) and the interface’s IP address.
Table 119 Configuration > Network > Interface > Bridge > Add / Edit (continued)
LABEL DESCRIPTION
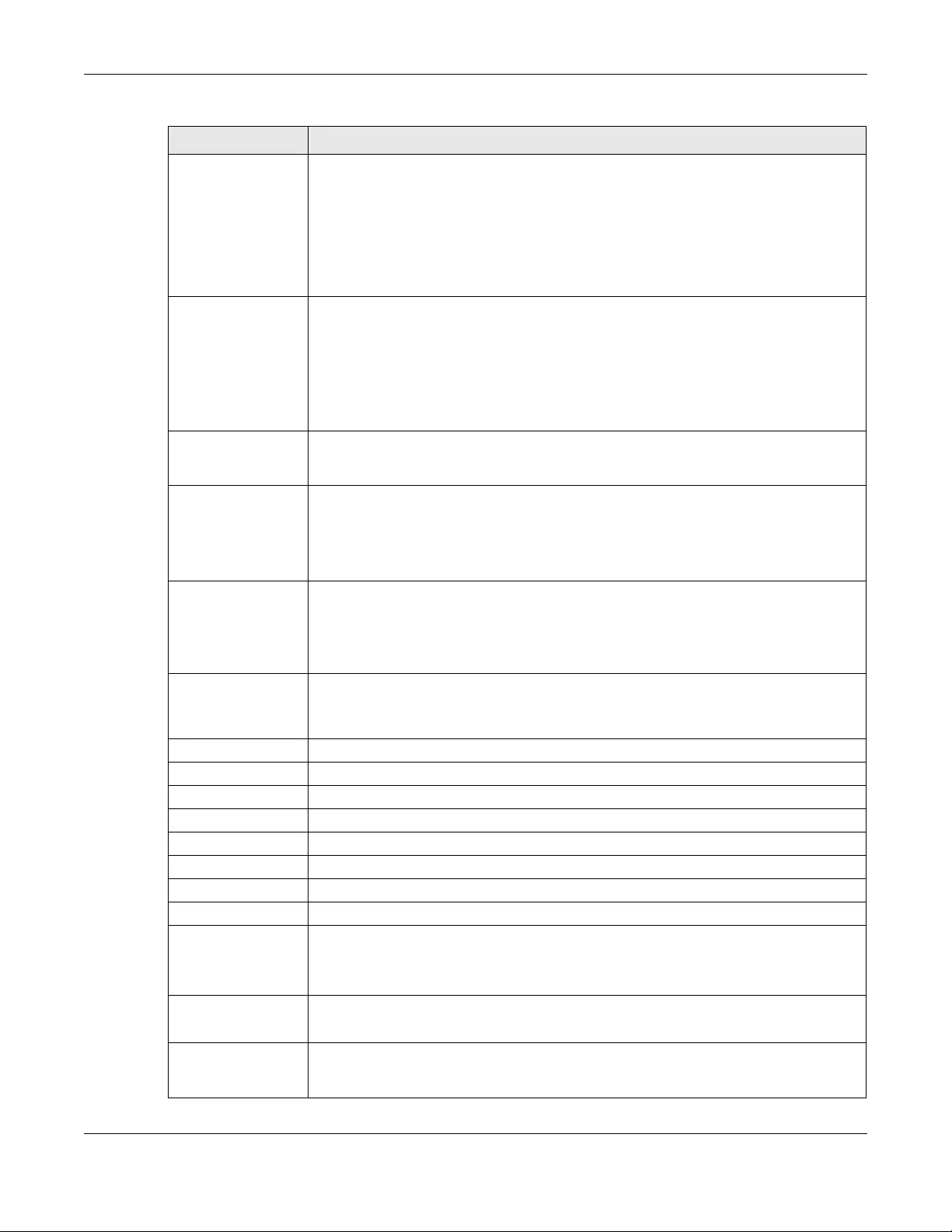
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
343
Pool Size Enter the number of IP addresses to allocate. This number must be at least one and is
limited by the interface’s Subnet Mask. For example, if the Subnet Mask is 255.255.255.0 and
IP Pool Start Address is 10.10.10.10, the Zyxel Device can allocate 10.10.10.10 to
10.10.10.254, or 245 IP addresses.
If this field is blank, the IP Pool Start Address must also be blank. In this case, the Zyxel Device
can assign every IP address allowed by the interface’s IP address and subnet mask, except
for the first address (network address), last address (broadcast address) and the interface’s
IP address.
First DNS Server
Second DNS
Server
Third DNS Server
Specify the IP addresses up to three DNS servers for the DHCP clients to use. Use one of the
following ways to specify these IP addresses.
Custom Defined - enter a static IP address.
From ISP - select the DNS server that another interface received from its DHCP server.
Zyxel Device - the DHCP clients use the IP address of this interface and the Zyxel Device
works as a DNS relay.
First WINS Server,
Second WINS
Server
Type the IP address of the WINS (Windows Internet Naming Service) server that you want to
send to the DHCP clients. The WINS server keeps a mapping table of the computer names
on your network and the IP addresses that they are currently using.
Default Router If you set this interface to DHCP Server, you can select to use either the interface’s IP
address or another IP address as the default router. This default router will become the
DHCP clients’ default gateway.
To use another IP address as the default router, select Custom Defined and enter the IP
address.
Lease time Specify how long each computer can use the information (especially the IP address)
before it has to request the information again. Choices are:
infinite - select this if IP addresses never expire
days, hours, and minutes - select this to enter how long IP addresses are valid.
Extended
Options This table is available if you selected DHCP server.
Configure this table if you want to send more information to DHCP clients through DHCP
packets.
Add Click this to create an entry in this table. See Section 10.4.6 on page 295.
Edit Select an entry in this table and click this to modify it.
Remove Select an entry in this table and click this to delete it.
# This field is a sequential value, and it is not associated with any entry.
Name This is the option’s name.
Code This is the option’s code number.
Type This is the option’s type.
Value This is the option’s value.
Enable IP/MAC
Binding Select this option to have this interface enforce links between specific IP addresses and
specific MAC addresses. This stops anyone else from manually using a bound IP address on
another device connected to this interface. Use this to make use only the intended users
get to use specific IP addresses.
Enable Logs for
IP/MAC Binding
Violation
Select this option to have the Zyxel Device generate a log if a device connected to this
interface attempts to use an IP address that is bound to another device’s MAC address.
Static DHCP
Table Configure a list of static IP addresses the Zyxel Device assigns to computers connected to
the interface. Otherwise, the Zyxel Device assigns an IP address dynamically using the
interface’s IP Pool Start Address and Pool Size.
Table 119 Configuration > Network > Interface > Bridge > Add / Edit (continued)
LABEL DESCRIPTION
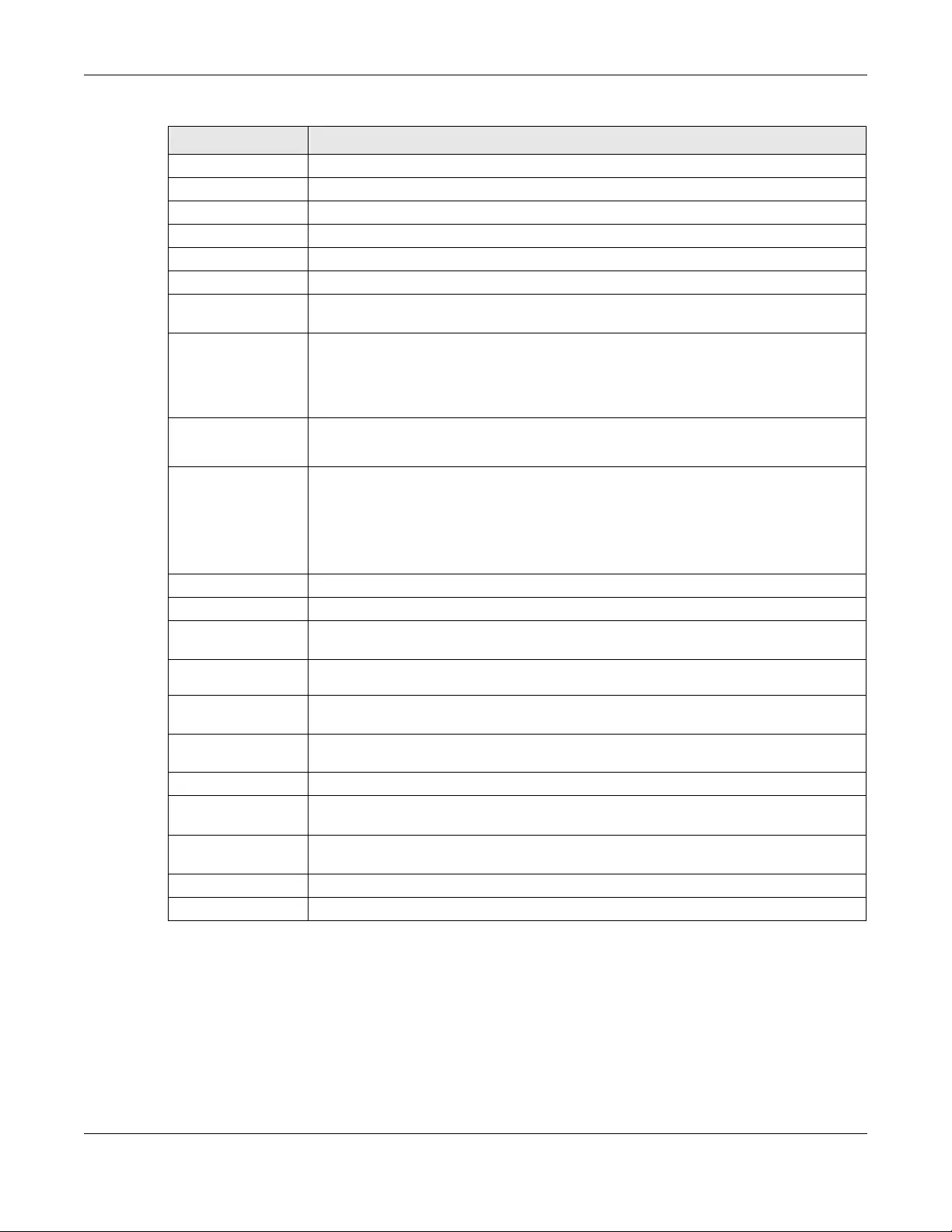
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
344
10.10 LAG
Link Aggregation Group (LAG) is a way to combine multiple physical Ethernet interfaces into a single
logical interface. This increases uplink bandwidth. It also increases availability as even if a member link
goes down, LAG can continue to transmit and receive traffic over the remaining links.
Add Click this to create a new entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
# This field is a sequential value, and it is not associated with a specific entry.
IP Address Enter the IP address to assign to a device with this entry’s MAC address.
MAC Address Enter the MAC address to which to assign this entry’s IP address.
Description Enter a description to help identify this static DHCP entry. You can use alphanumeric and
()+/:=?!*#@$_%- characters, and it can be up to 60 characters long.
Connectivity Check The interface can regularly check the connection to the gateway you specified to make
sure it is still available. You specify how often the interface checks the connection, how
long to wait for a response before the attempt is a failure, and how many consecutive
failures are required before the Zyxel Device stops routing to the gateway. The Zyxel Device
resumes routing to the gateway the first time the gateway passes the connectivity check.
Enable
Connectivity
Check
Select this to turn on the connection check.
Check Method Select the method that the gateway allows.
Select icmp to have the Zyxel Device regularly ping the gateway you specify to make sure
it is still available.
Select tcp to have the Zyxel Device regularly perform a TCP handshake with the gateway
you specify to make sure it is still available.
Check Period Enter the number of seconds between connection check attempts.
Check Timeout Enter the number of seconds to wait for a response before the attempt is a failure.
Check Fail
Tolerance Enter the number of consecutive failures before the Zyxel Device stops routing through the
gateway.
Check Default
Gateway Select this to use the default gateway for the connectivity check.
Check this
address Select this to specify a domain name or IP address for the connectivity check. Enter that
domain name or IP address in the field next to it.
Check Port This field only displays when you set the Check Method to tcp. Specify the port number to
use for a TCP connectivity check.
Related Setting
Configure WAN
TRUNK Click WAN TRUNK to go to a screen where you can configure the interface as part of a
WAN trunk for load balancing.
Configure Policy
Route Click Policy Route to go to the screen where you can manually configure a policy route to
associate traffic with this bridge interface.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 119 Configuration > Network > Interface > Bridge > Add / Edit (continued)
LABEL DESCRIPTION
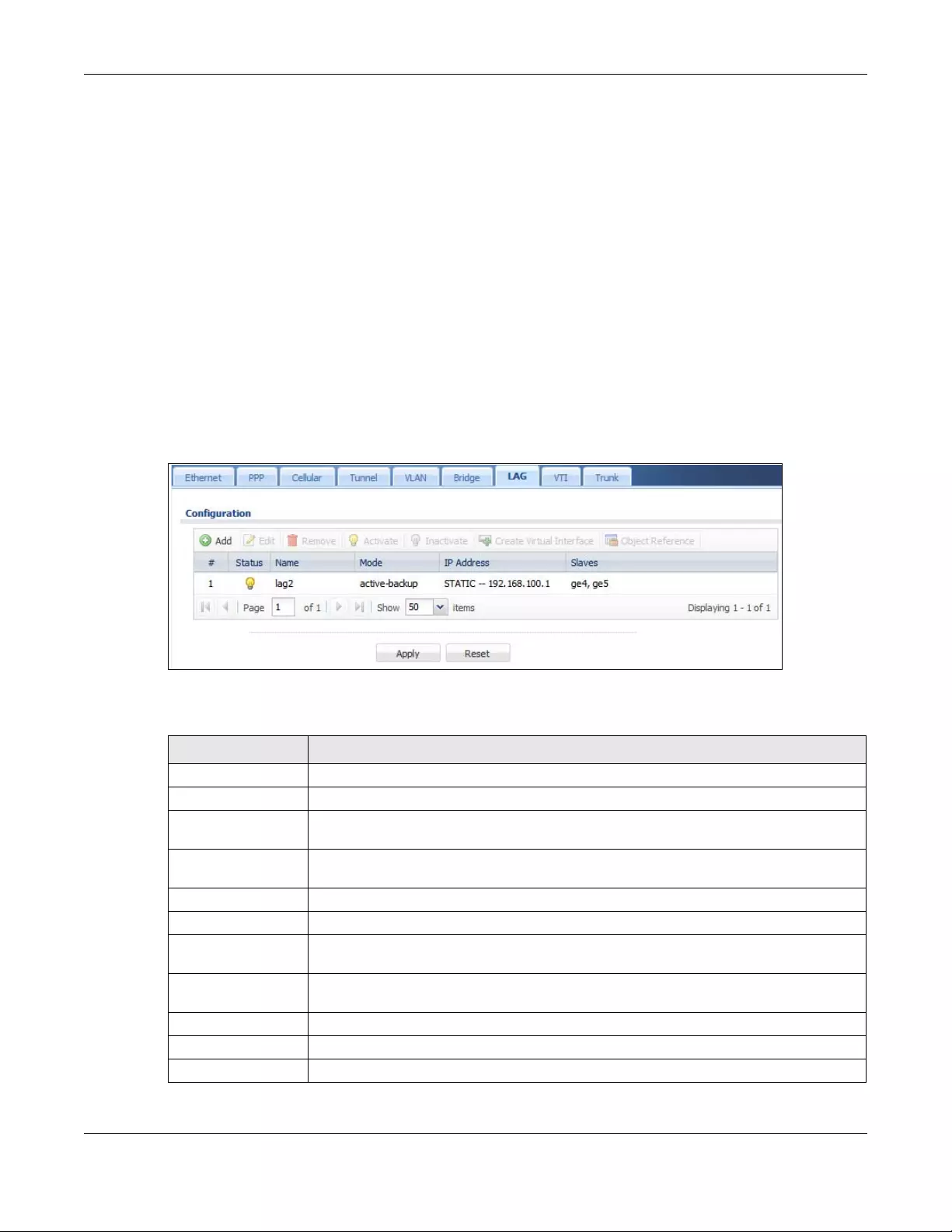
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
345
To configure LAG, configure a link number and specify the member ports in the link. All ports must have
the same speed and be in full-duplex mode. You must configure the LAG on both sides of the link and
you must set the interfaces on either side of the link to be the same speed.
At the time of writing, up to 4 ports can be grouped into a LAG and up to 4 LAGs can be configured on
a Zyxel Device.
The following models support Link Aggregation Group (LAG):
10.10.1 LAG Summary Screen
This screen lists every LAG created on the Zyxel Device. To access this screen, click Configuration >
Network > Interface > LAG.
Figure 251 Configuration > Network > Interface > LAG
Each field is described in the following table.
• ZyWALL 310 • USG310 • ZyWALL 1100
• USG1100 • USG1900 • USG2200-VPN
Table 120 Configuration > Network > Interface > LAG
LABEL DESCRIPTION
Configuration
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Create Virtual
Interface
To open the screen where you can create a virtual interface, select an interface and click
Create Virtual Interface.
Object References Select an entry and click Object Reference to open a screen that shows which settings use
the entry.
# This field is a sequential value, and it is not associated with any interface.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
Name This field displays the name of the LAG interface.
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
346
10.10.2 LAG Add/Edit
This screen lets you configure Interface and LAG parameters for each LAG interface. To access this
screen, click the Add or Edit icon in the LAG screen. The following screen appears.
Mode Mode refers to whether the LAG is acting as follows:
•active-backup where only one slave in the LAG interface is active and another slave
becomes active only if the active slave fails.
•802.3ad (IEEE 802.3ad Dynamic link aggregation) where Link Aggregation Control
Protocol (LACP) negotiates automatic combining of links and balances the traffic load
across the LAG link by sending LACP packets to the directly connected device that
also implements LACP. The slaves must have the same speed and duplex settings.
•balance-alb (adaptive load balancing) where traffic is distributed according to the
current load on each slave by ARP negotiation. Incoming traffic is received by the
current slave. If the receiving slave fails, another slave takes over the MAC address of
the failed receiving slave.
IP Address This field displays the current IP address of the LAG interface. If the IP address is 0.0.0.0, the
interface does not have an IP address yet.
This screen also shows whether the IP address is a static IP address (STATIC) or dynamically
assigned (DHCP). IP addresses are always static in virtual interfaces.
Slaves A slave is a physical Ethernet interface that is a member of a LAG. Slaves do not have an IP
Address and in some cases share the same MAC address. This field displays the member
Ethernet interfaces and VLAN interfaces in the LAG. It is blank for virtual interfaces.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 120 Configuration > Network > Interface > LAG (continued)
LABEL DESCRIPTION
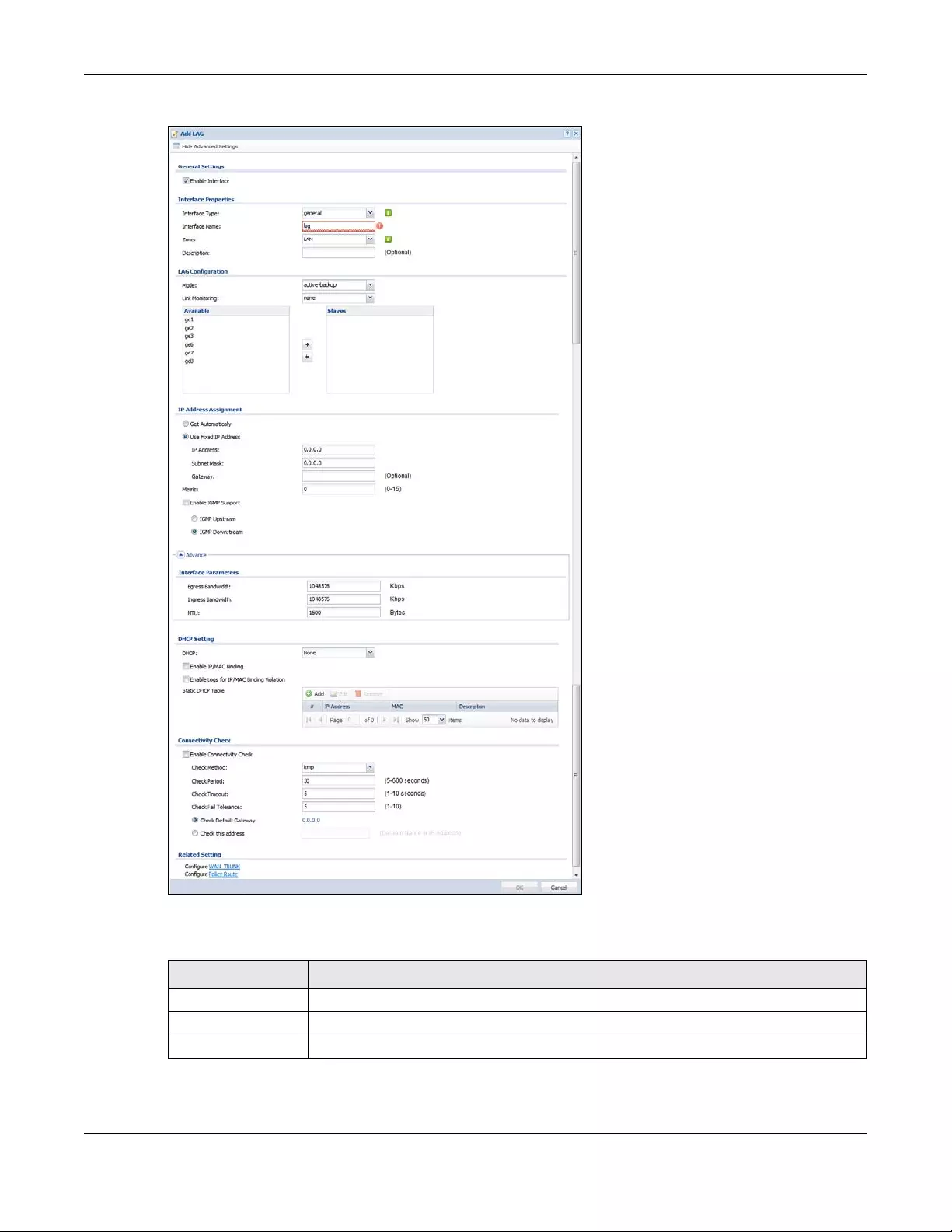
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
347
Figure 252 Configuration > Network > Interface > LAG > Add
Each field is described in the following table.
Table 121 Configuration > Network > Interface > LAG > Add
LABEL DESCRIPTION
General Settings
Enable Interface Select this to enable this interface. Clear this to disable this interface.
Interface Properties
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
348
Interface Type Select one of the following option depending on the type of network to which the Zyxel
Device is connected or if you want to additionally manually configure some related
settings.
internal is for connecting to a local network. Other corresponding configuration options:
DHCP server and DHCP relay. The Zyxel Device automatically adds default SNAT settings for
traffic flowing from this interface to an external interface.
external is for connecting to an external network (like the Internet). The Zyxel Device
automatically adds this interface to the default WAN trunk.
For general, the rest of the screen’s options do not automatically adjust and you must
manually configure a policy route to add routing and SNAT settings for the interface.
Interface Name This field is read-only if you are editing the interface. Enter the name of the LAG interface.
The format is lagx, where x is 0 - 3. For example, lag0, lag1, and so on.
Zone Select the zone to which the interface is to belong. You use zones to apply security settings
such as security policy, IDP, remote management, anti-virus, and application patrol.
Description Enter a description of this interface. It is not used elsewhere. You can use alphanumeric and
()+/:=?!*#@$_%- characters, and it can be up to 60 characters long.
LAG Configuration
Mode Select a Mode for this LAG interface. Choices are as follows:
•active-backup where only one slave in the LAG interface is active and another slave
becomes active only if the active slave fails.
•802.3ad (IEEE 802.3ad Dynamic link aggregation) where Link Aggregation Control
Protocol (LACP) negotiates automatic combining of links and balances the traffic load
across the LAG link by sending LACP packets to the directly connected device that
also implements LACP. The slaves must have the same speed and duplex settings.
•balance-alb (adaptive load balancing) where traffic is distributed according to the
current load on each slave by ARP negotiation. Incoming traffic is received by the
current slave. If the receiving slave fails, another slave takes over the MAC address of
the failed receiving slave.
Link Monitoring Select from none, mii or arp. none means no link monitoring is done.
mii monitoring monitors the state of the local interface; it can’t tell if the link can transmit or
receive packets.
arp monitoring sends ARP queries and uses the reply to know if the link is up and that traffic
is flowing over the link.
Miimom This field displays for mii Link Monitoring. Set the link check interval in milliseconds that the
system polls the Media Independent Interface (MII) to get status.
Updelay This field displays for mii Link Monitoring. Set the waiting time in milliseconds to confirm the
slave interface status is up.
Downdelay This field displays for mii Link Monitoring. Set the waiting time in milliseconds to confirm the
slave interface status is down.
Xmit Hash Policy This field displays in 802.3ad Mode. This field sets the algorithm for slave selection according
to the selected TCP/IP layer.
LACP Rate This field displays in 802.3ad Mode. Select the preferred LACPDU packet transmission rate
(slow/fast) to request from 802.3ad partner.
ARP Interval This field displays for arp Link Monitoring. Select the frequency of ARP requests sent to
confirm a that slave interface is up.
ARP IP Target This field displays for arp Link Monitoring. Set the IP address of the link to send ARP queries.
Table 121 Configuration > Network > Interface > LAG > Add (continued)
LABEL DESCRIPTION
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
349
Available This field displays Ethernet interfaces and VLAN interfaces that can become part of the LAG
interface. An interface is not available in the following situations:
• There is a virtual interface on top of it
• It is already used in a different LAG interface
Select one, and click the >> arrow to add it to the LAG interface. Each LAG interface can
only have one VLAN interface.
Slaves A slave is a physical Ethernet interface that is a member of a LAG. This field displays the
interfaces that are part of the LAG interface. Select one, and click the << arrow to remove
it from the LAG interface.
IP Address
Assignment
Get
Automatically Select this if this interface is a DHCP client. In this case, the DHCP server configures the IP
address, subnet mask, and gateway automatically.
Use Fixed IP
Address Select this if you want to specify the IP address, subnet mask, and gateway manually.
IP Address This field is enabled if you select Use Fixed IP Address.
Enter the IP address for this interface.
Subnet Mask This field is enabled if you select Use Fixed IP Address.
Enter the subnet mask of this interface in dot decimal notation. The subnet mask indicates
what part of the IP address is the same for all computers in the network.
Gateway This field is enabled if you select Use Fixed IP Address.
Enter the IP address of the gateway. The Zyxel Device sends packets to the gateway when
it does not know how to route the packet to its destination. The gateway should be on the
same network as the interface.
Metric Enter the priority of the gateway (if any) on this interface. The Zyxel Device decides which
gateway to use based on this priority. The lower the number, the higher the priority. If two or
more gateways have the same priority, the Zyxel Device uses the one that was configured
first.
Enable IGMP Support Select this to allow the Zyxel Device to act as an IGMP proxy for hosts connected on the
IGMP downstream interface.
IGMP Upstream Enable IGMP Upstream on the interface which connects to a router running IGMP that is
closer to the multicast server.
IGMP
Downstream Enable IGMP Downstream on the interface which connects to the multicast hosts.
DHCP Setting
DHCP Select what type of DHCP service the Zyxel Device provides to the network. Choices are:
None - the Zyxel Device does not provide any DHCP services. There is already a DHCP
server on the network.
DHCP Relay - the Zyxel Device routes DHCP requests to one or more DHCP servers you
specify. The DHCP server(s) may be on another network.
DHCP Server - the Zyxel Device assigns IP addresses and provides subnet mask, gateway,
and DNS server information to the network. The Zyxel Device is the DHCP server for the
network.
These fields appear if the Zyxel Device is a DHCP Relay.
Relay Server 1 Enter the IP address of a DHCP server for the network.
Relay Server 2 This field is optional. Enter the IP address of another DHCP server for the network.
These fields appear if the Zyxel Device is a DHCP Server.
Table 121 Configuration > Network > Interface > LAG > Add (continued)
LABEL DESCRIPTION
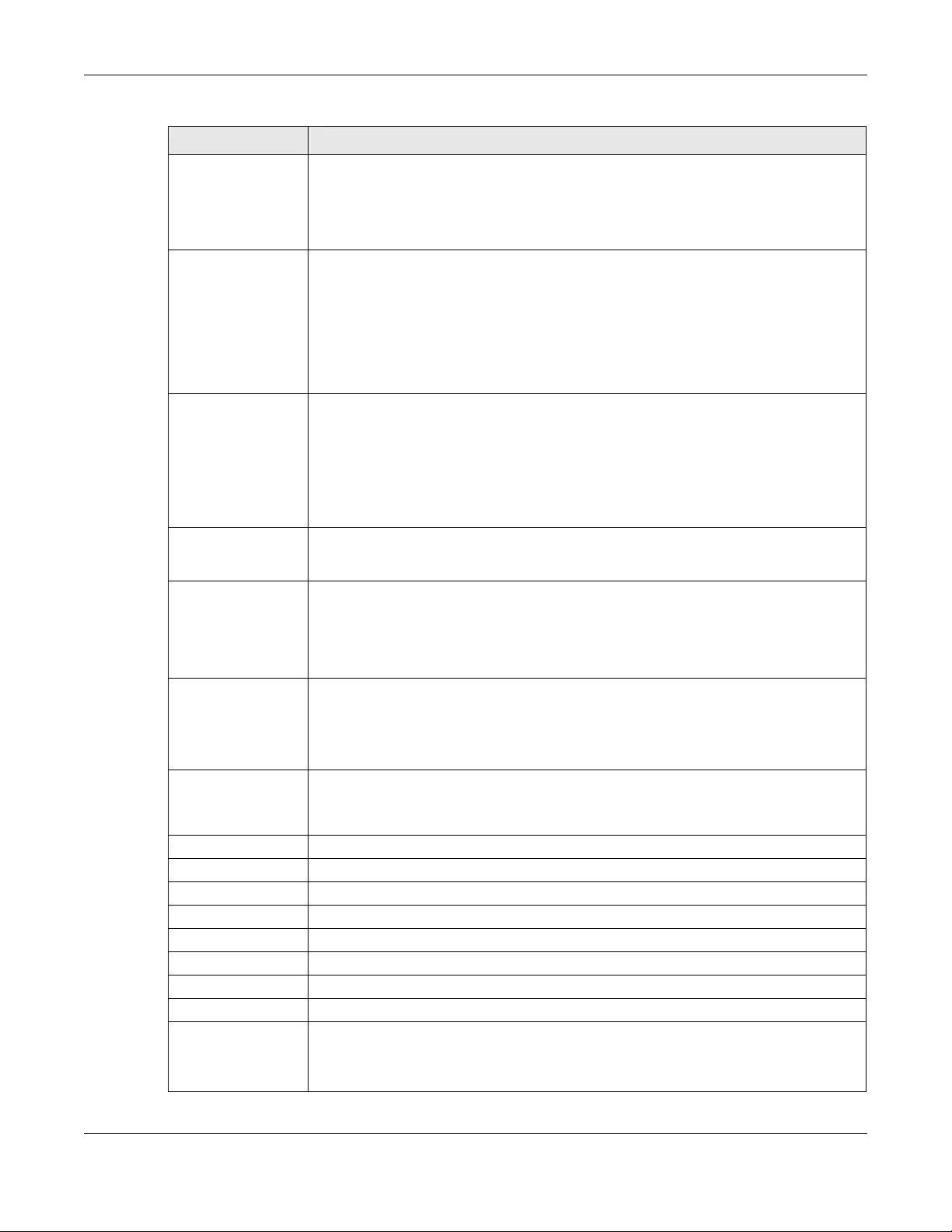
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
350
IP Pool Start
Address Enter the IP address from which the Zyxel Device begins allocating IP addresses. If you want
to assign a static IP address to a specific computer, click Add Static DHCP.
If this field is blank, the Pool S ize must also be blank. In this case, the Zyxel Device can assign
every IP address allowed by the interface’s IP address and subnet mask, except for the first
address (network address), last address (broadcast address) and the interface’s IP address.
Pool Size Enter the number of IP addresses to allocate. This number must be at least one and is
limited by the interface’s Subnet Mask. For example, if the Subnet Mask is 255.255.255.0 and
IP Pool Start Address is 10.10.10.10, the Zyxel Device can allocate 10.10.10.10 to
10.10.10.254, or 245 IP addresses.
If this field is blank, the IP Pool Start Addres s must also be blank. In this case, the Zyxel Device
can assign every IP address allowed by the interface’s IP address and subnet mask, except
for the first address (network address), last address (broadcast address) and the interface’s
IP address.
First DNS Server
Second DNS
Server
Third DNS Server
Specify the IP addresses up to three DNS servers for the DHCP clients to use. Use one of the
following ways to specify these IP addresses.
Custom Defined - enter a static IP address.
From ISP - select the DNS server that another interface received from its DHCP server.
Zyxel Device - the DHCP clients use the IP address of this interface and the Zyxel Device
works as a DNS relay.
First WINS Server,
Second WINS
Server
Type the IP address of the WINS (Windows Internet Naming Service) server that you want to
send to the DHCP clients. The WINS server keeps a mapping table of the computer names
on your network and the IP addresses that they are currently using.
Default Router If you set this interface to DHCP Server, you can select to use either the interface’s IP
address or another IP address as the default router. This default router will become the
DHCP clients’ default gateway.
To use another IP address as the default router, select Custom Defined and enter the IP
address.
Lease time Specify how long each computer can use the information (especially the IP address)
before it has to request the information again. Choices are:
infinite - select this if IP addresses never expire
days, hours, and minutes - select this to enter how long IP addresses are valid.
Extended
Options This table is available if you selected DHCP server.
Configure this table if you want to send more information to DHCP clients through DHCP
packets.
Add Click this to create an entry in this table. See Section 10.4.6 on page 295.
Edit Select an entry in this table and click this to modify it.
Remove Select an entry in this table and click this to delete it.
# This field is a sequential value, and it is not associated with any entry.
Name This is the option’s name.
Code This is the option’s code number.
Type This is the option’s type.
Value This is the option’s value.
Enable IP/MAC
Binding Select this option to have this interface enforce links between specific IP addresses and
specific MAC addresses. This stops anyone else from manually using a bound IP address on
another device connected to this interface. Use this to make use only the intended users
get to use specific IP addresses.
Table 121 Configuration > Network > Interface > LAG > Add (continued)
LABEL DESCRIPTION
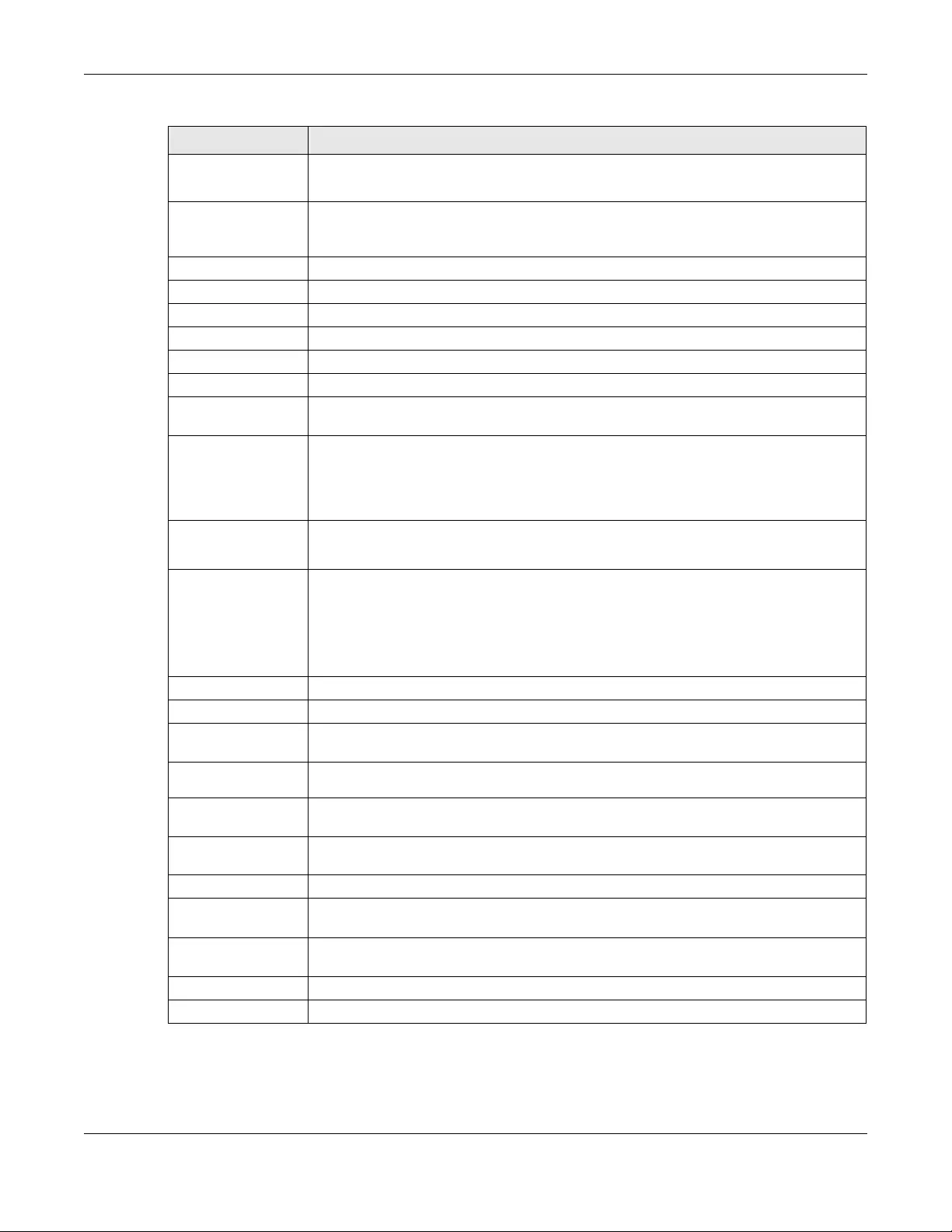
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
351
Enable Logs for
IP/MAC Binding
Violation
Select this option to have the Zyxel Device generate a log if a device connected to this
interface attempts to use an IP address that is bound to another device’s MAC address.
Static DHCP
Table Configure a list of static IP addresses the Zyxel Device assigns to computers connected to
the interface. Otherwise, the Zyxel Device assigns an IP address dynamically using the
interface’s IP Pool Start Address and Pool Size.
Add Click this to create a new entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
# This field is a sequential value, and it is not associated with a specific entry.
IP Address Enter the IP address to assign to a device with this entry’s MAC address.
MAC Address Enter the MAC address to which to assign this entry’s IP address.
Description Enter a description to help identify this static DHCP entry. You can use alphanumeric and
()+/:=?!*#@$_%- characters, and it can be up to 60 characters long.
Connectivity Check The interface can regularly check the connection to the gateway you specified to make
sure it is still available. You specify how often the interface checks the connection, how
long to wait for a response before the attempt is a failure, and how many consecutive
failures are required before the Zyxel Device stops routing to the gateway. The Zyxel Device
resumes routing to the gateway the first time the gateway passes the connectivity check.
Enable
Connectivity
Check
Select this to turn on the connection check.
Check Method Select the method that the gateway allows.
Select icmp to have the Zyxel Device regularly ping the gateway you specify to make sure
it is still available.
Select tcp to have the Zyxel Device regularly perform a TCP handshake with the gateway
you specify to make sure it is still available.
Check Period Enter the number of seconds between connection check attempts.
Check Timeout Enter the number of seconds to wait for a response before the attempt is a failure.
Check Fail
Tolerance Enter the number of consecutive failures before the Zyxel Device stops routing through the
gateway.
Check Default
Gateway Select this to use the default gateway for the connectivity check.
Check this
address Select this to specify a domain name or IP address for the connectivity check. Enter that
domain name or IP address in the field next to it.
Check Port This field only displays when you set the Check Method to tcp. Specify the port number to
use for a TCP connectivity check.
Related Setting
Configure WAN
TRUNK Click WAN TRUNK to go to a screen where you can configure the interface as part of a
WAN trunk for load balancing.
Configure Policy
Route Click Policy Route to go to the screen where you can manually configure a policy route to
associate traffic with this bridge interface.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 121 Configuration > Network > Interface > LAG > Add (continued)
LABEL DESCRIPTION
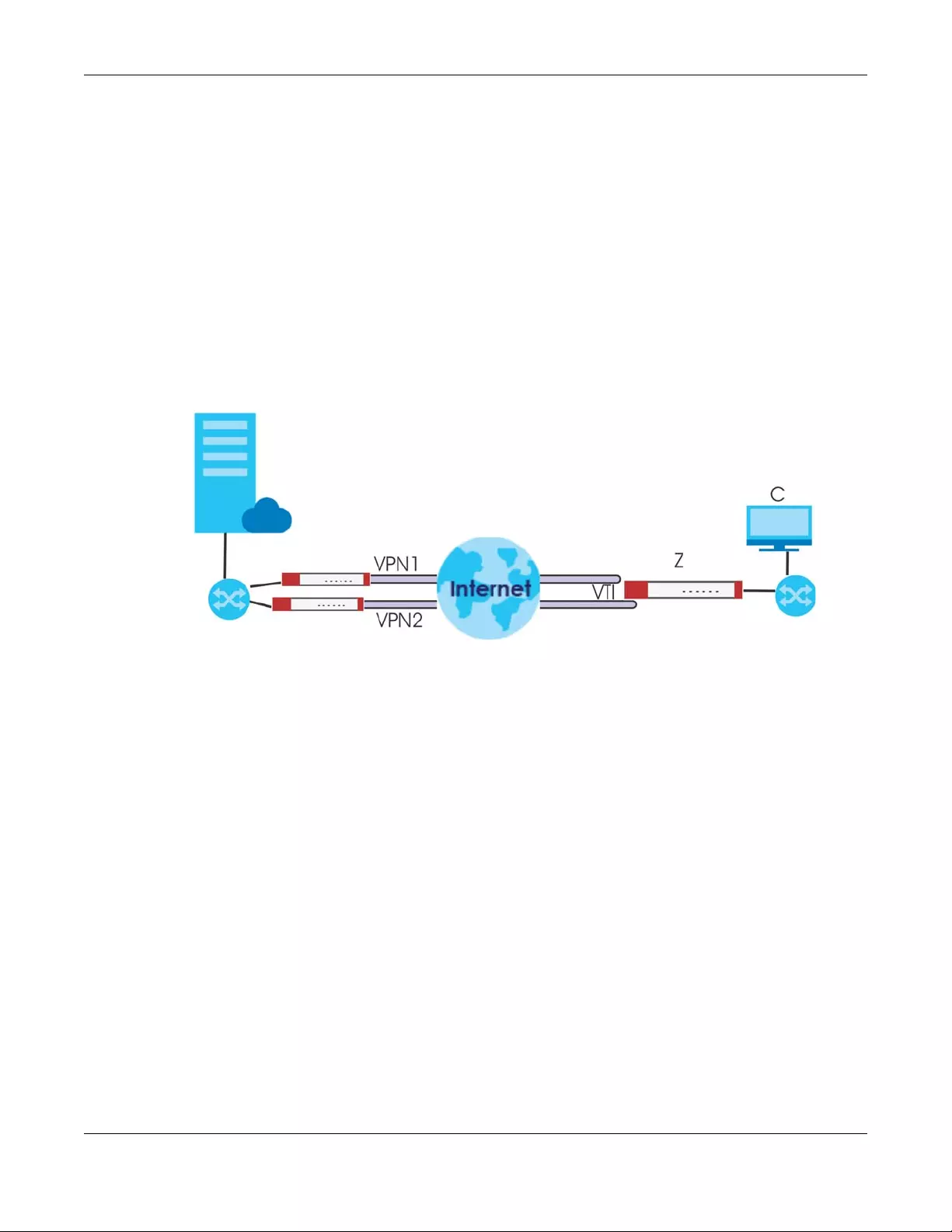
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
352
10.11 VTI
IPSec VPN Tunnel Interface (VTI) encrypts or decrypts IPv4 traffic from or to the interface according to
the IP routing table.
VTI allows static routes to send traffic over the VPN. The IPSec tunnel endpoint is associated with an
actual (virtual) interface. Therefore many interface capabilities such as Policy Route, Static Route, Trunk,
and BWM can be applied to the IPSec tunnel as soon as the tunnel is active
IPSec VTIs simplifies network management and load balancing. Create a trunk using VPN tunnel
interfaces for load balancing. In the following example configure VPN tunnels with static IP addresses or
DNS on both Zyxel Devices (or IPSec routers at the end of the tunnel). Also configure VTI and a trunk on
both Zyxel Devices.
Figure 253 VTI and Trunk for VPN Load Balancing
10.11.1 Restrictions for IPSec Virtual Tunnel Interface
• IPv4 traffic only
• IPSec tunnel mode only. A shared keyword must not be configured when using tunnel mode.
• With a VTI VPN you do not add local or remote LANs to your VPN configuration.
• For a VTI VPN you should only have one local and one remote WAN.
• A dynamic peer is not supported
• The IPSec VTI is limited to IP unicast and multicast traffic only.
10.11.2 VTI Screen
To access this screen, click Configuration > Network > Interface > VTI.
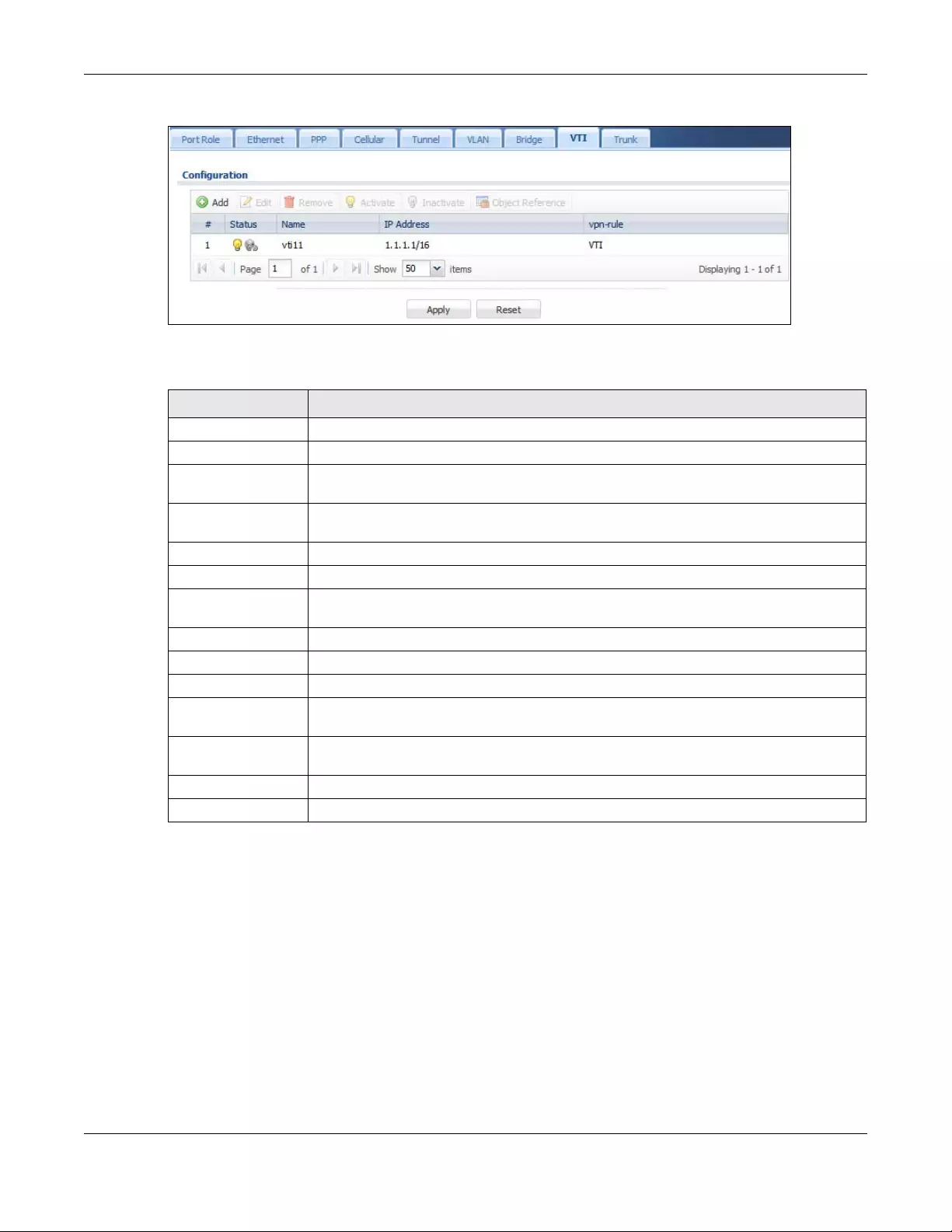
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
353
Figure 254 Configuration > Network > Interface > VTI
The following table describes the fields in this screen.
10.11.3 VTI Add/Edit
This screen lets you configure IP address assignment and interface parameters for VTI.
Note: You should have created a VPN tunnel for a Vpn Tunnel Interface scenario first.
To access this screen, click the Add or Edit icon in Network > Interface > VTI. The following screen
appears.
Table 122 Configuration > Network > Interface > VTI
LABEL DESCRIPTION
Configuration
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Object References Select an entry and click Object Reference to open a screen that shows which settings use
the entry.
# This field is a sequential value, and it is not associated with any interface.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
Name This field displays the name of the LAG interface.
IP Address This field displays the current IP address of the virtual interface and subnet mask in bits. If the
IP address is 0.0.0.0, the interface does not have an IP address yet.
vpn-rule This shows the name of the associated IPSec VPN rule with Vpn Tunnel Interface application
scenario.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
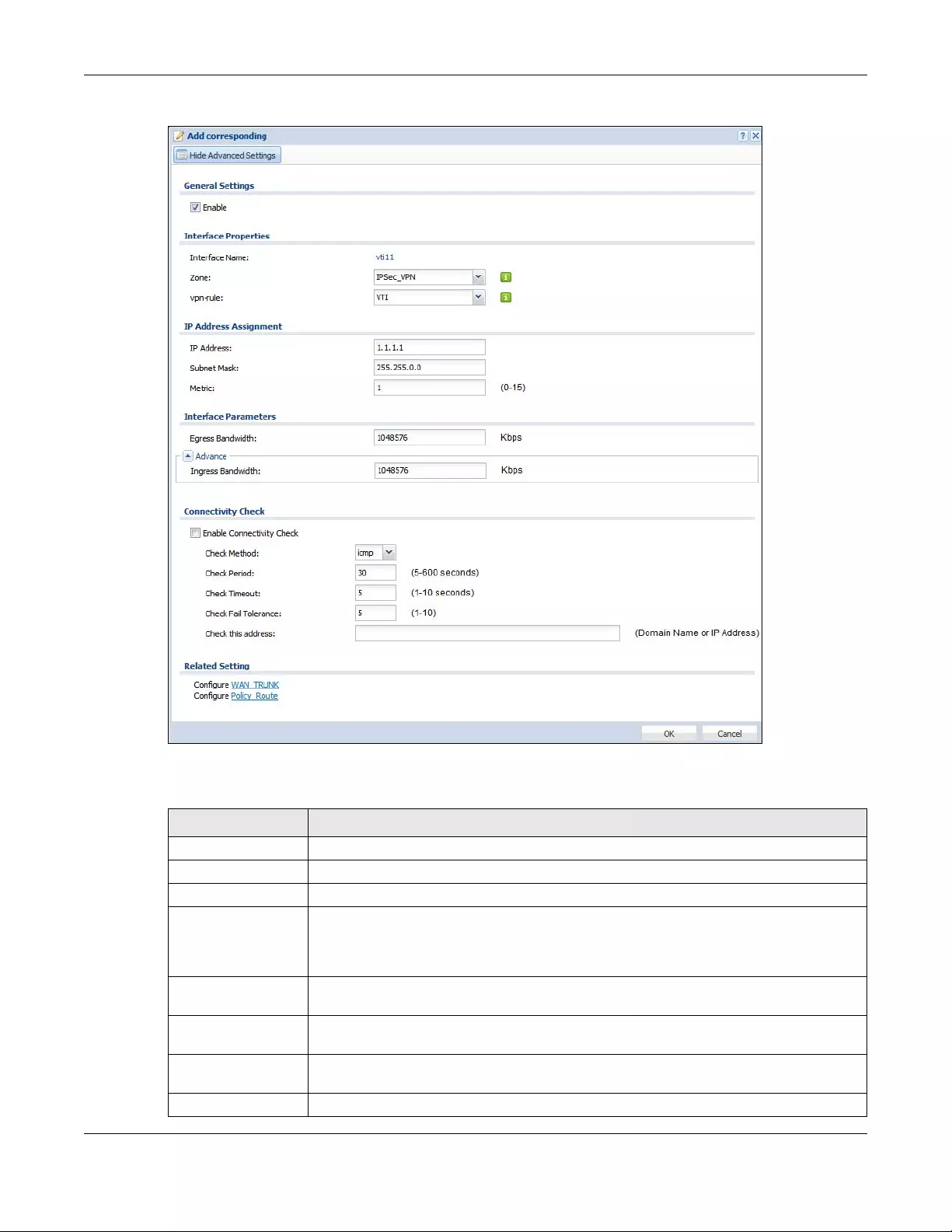
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
354
Figure 255 Configuration > Network > Interface > VTI > Add
Each field is described in the table below.
Table 123 Configuration > Network > Interface > VTI > Add
LABEL DESCRIPTION
General Settings
Enable Select this to enable VTI. Clear this to disable it.
Interface Properties
Interface Name This field is read-only if you are editing an existing VPN tunnel interface. For a new VPN
tunnel interface, enter the name of the VPN tunnel interface in vtix format, where x is a
number from 0 to the maximum number of VPN connections allowed for this model. For
example, enter vti10.
Zone Select a zone. Make sure that the zone you select does not have traffic blocked by a
security feature such as a security policy.
vpn-rule You should have created a VPN tunnel first for a Vpn Tunnel Interface scenario. Select one
of the Vpn Tunnel Interface scenario rules that you created.
IP Address
Assignment
IP Address Enter the IP address for this interface.
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
355
10.12 Trunk Overview
Use trunks for WAN traffic load balancing to increase overall network throughput and reliability. Load
balancing divides traffic loads between multiple interfaces. This allows you to improve quality of service
and maximize bandwidth utilization for multiple ISP links.
Maybe you have two Internet connections with different bandwidths. You could set up a trunk that uses
spillover or weighted round robin load balancing so time-sensitive traffic (like video) usually goes
Subnet Mask Enter the subnet mask of this interface in dot decimal notation. The subnet mask indicates
what part of the IP address is the same for all computers in the network.
Gateway Enter the IP address of the gateway. The Zyxel Device sends packets to the gateway when
it does not know how to route the packet to its destination. The gateway should be on the
same network as the interface.
Metric Enter the priority of the gateway (if any) on this interface. The Zyxel Device decides which
gateway to use based on this priority. The lower the number, the higher the priority. If two or
more gateways have the same priority, the Zyxel Device uses the one that was configured
first.
Interface Parameters
Egress Bandwidth Enter the maximum amount of traffic, in kilobits per second, the Zyxel Device can send
through the interface to the network. Allowed values are 0 - 1048576.
Ingress
Bandwidth This is reserved for future use.
Enter the maximum amount of traffic, in kilobits per second, the Zyxel Device can receive
from the network through the interface. Allowed values are 0 - 1048576.
Connectivity Check These fields appear when you select a vpn-rule.
The interface can regularly check the connection to the gateway you specified to make
sure it is still available. You specify how often the interface checks the connection, how
long to wait for a response before the attempt is a failure, and how many consecutive
failures are required before the Zyxel Device stops routing to the gateway. The Zyxel Device
resumes routing to the gateway the first time the gateway passes the connectivity check.
Enable
Connectivity
Check
Select this to turn on the connection check.
Check Method Select the method that the gateway allows.
Select icmp to have the Zyxel Device regularly ping the gateway you specify to make sure
it is still available.
Select tcp to have the Zyxel Device regularly perform a TCP handshake with the gateway
you specify to make sure it is still available.
Check Period Enter the number of seconds between connection check attempts.
Check Timeout Enter the number of seconds to wait for a response before the attempt is a failure.
Check Fail
Tolerance Enter the number of consecutive failures before the Zyxel Device stops routing through the
gateway.
Check this
address Select this to specify a domain name or IP address for the connectivity check. Enter that
domain name or IP address in the field next to it.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 123 Configuration > Network > Interface > VTI > Add (continued)
LABEL DESCRIPTION

Chapter 10 Interfaces
USG/ZyWALL User’s Guide
356
through the higher-bandwidth interface. For other traffic, you might want to use least load first load
balancing to even out the distribution of the traffic load.
Suppose ISP A has better connections to Europe while ISP B has better connections to Australia. You
could use policy routes and trunks to have traffic for your European branch office primarily use ISP A and
traffic for your Australian branch office primarily use ISP B.
Or maybe one of the Zyxel Device's interfaces is connected to an ISP that is also your Voice over IP
(VoIP) service provider. You can use policy routing to send the VoIP traffic through a trunk with the
interface connected to the VoIP service provider set to active and another interface (connected to
another ISP) set to passive. This way VoIP traffic goes through the interface connected to the VoIP
service provider whenever the interface’s connection is up.
• Use the Trunk summary screen (Section 10.13 on page 358) to view the list of configured trunks and
which load balancing algorithm each trunk uses.
• Use the Add Trunk screen (Section 10.13.1 on page 360) to configure the member interfaces for a
trunk and the load balancing algorithm the trunk uses.
• Use the Add System Default screen (Section 10.13.2 on page 362) to configure the load balancing
algorithm for the system default trunk.
10.12.1 What You Need to Know
• Add WAN interfaces to trunks to have multiple connections share the traffic load.
• If one WAN interface’s connection goes down, the Zyxel Device sends traffic through another
member of the trunk.
• For example, you connect one WAN interface to one ISP and connect a second WAN interface to a
second ISP. The Zyxel Device balances the WAN traffic load between the connections. If one
interface's connection goes down, the Zyxel Device can automatically send its traffic through
another interface.
You can also use trunks with policy routing to send specific traffic types through the best WAN interface
for that type of traffic.
• If that interface’s connection goes down, the Zyxel Device can still send its traffic through another
interface.
• You can define multiple trunks for the same physical interfaces.
1LAN user A logs into server B on the Internet. The Zyxel Device uses wan1 to send the request to server B.
2The Zyxel Device is using active/active load balancing. So when LAN user A tries to access something on
the server, the request goes out through wan2.
3The server finds that the request comes from wan2’s IP address instead of wan1’s IP address and rejects
the request.
If link sticking had been configured, the Zyxel Device would have still used wan1 to send LAN user A’s
request to the server and server would have given the user A access.
Load Balancing Algorithms
The following sections describe the load balancing algorithms the Zyxel Device can use to decide which
interface the traffic (from the LAN) should use for a session. In the load balancing section, a session may
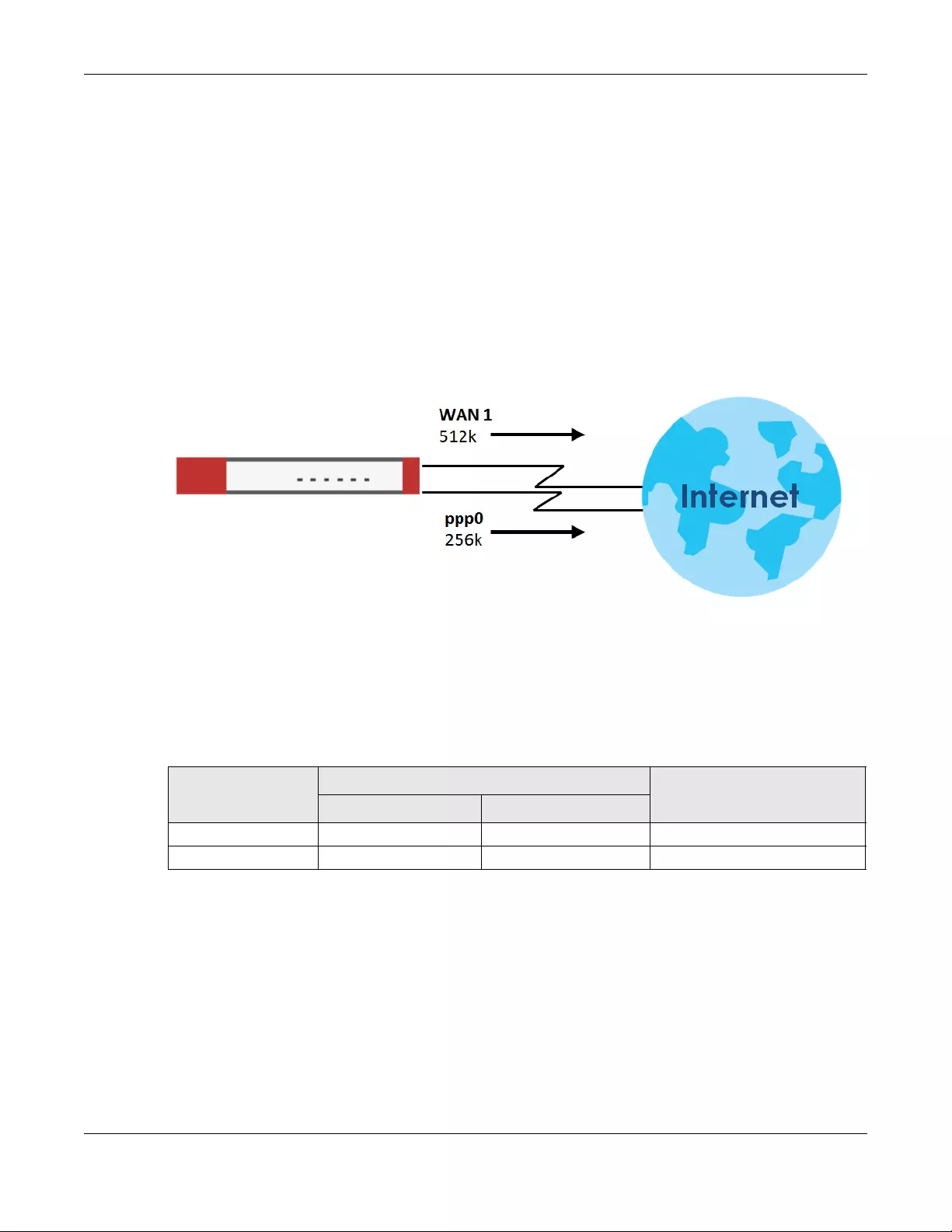
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
357
refer to normal connection-oriented, UDP or SNMP2 traffic. The available bandwidth you configure on
the Zyxel Device refers to the actual bandwidth provided by the ISP and the measured bandwidth refers
to the bandwidth an interface is currently using.
Least Load First
The least load first algorithm uses the current (or recent) outbound bandwidth utilization of each trunk
member interface as the load balancing index(es) when making decisions about to which interface a
new session is to be distributed. The outbound bandwidth utilization is defined as the measured
outbound throughput over the available outbound bandwidth.
Here the Zyxel Device has two WAN interfaces connected to the Internet. The configured available
outbound bandwidths for WAN 1 and WAN 2 are 512K and 256K respectively.
Figure 256 Load Balancing Least Load First Example
The outbound bandwidth utilization is used as the load balancing index. In this example, the measured
(current) outbound throughput of WAN 1 is 412K and WAN 2 is 198K. The Zyxel Device calculates the
load balancing index as shown in the table below.
Since WAN 2 has a smaller load balancing index (meaning that it is less utilized than WAN 1), the Zyxel
Device will send the subsequent new session traffic through WAN 2.
Weighted Round Robin
Round Robin scheduling services queues on a rotating basis and is activated only when an interface has
more traffic than it can handle. A queue is given an amount of bandwidth irrespective of the incoming
traffic on that interface. This queue then moves to the back of the list. The next queue is given an equal
amount of bandwidth, and then moves to the end of the list; and so on, depending on the number of
queues being used. This works in a looping fashion until a queue is empty.
The Weighted Round Robin (WRR) algorithm is best suited for situations when the bandwidths set for the
two WAN interfaces are different. Similar to the Round Robin (RR) algorithm, the Weighted Round Robin
(WRR) algorithm sets the Zyxel Device to send traffic through each WAN interface in turn. In addition, the
Table 124 Least Load First Example
INTERFACE OUTBOUND LOAD BALANCING INDEX
(M/A)
AVAILABLE (A) MEASURED (M)
WAN 1 512 K 412 K 0.8
WAN 2 256 K 198 K 0.77
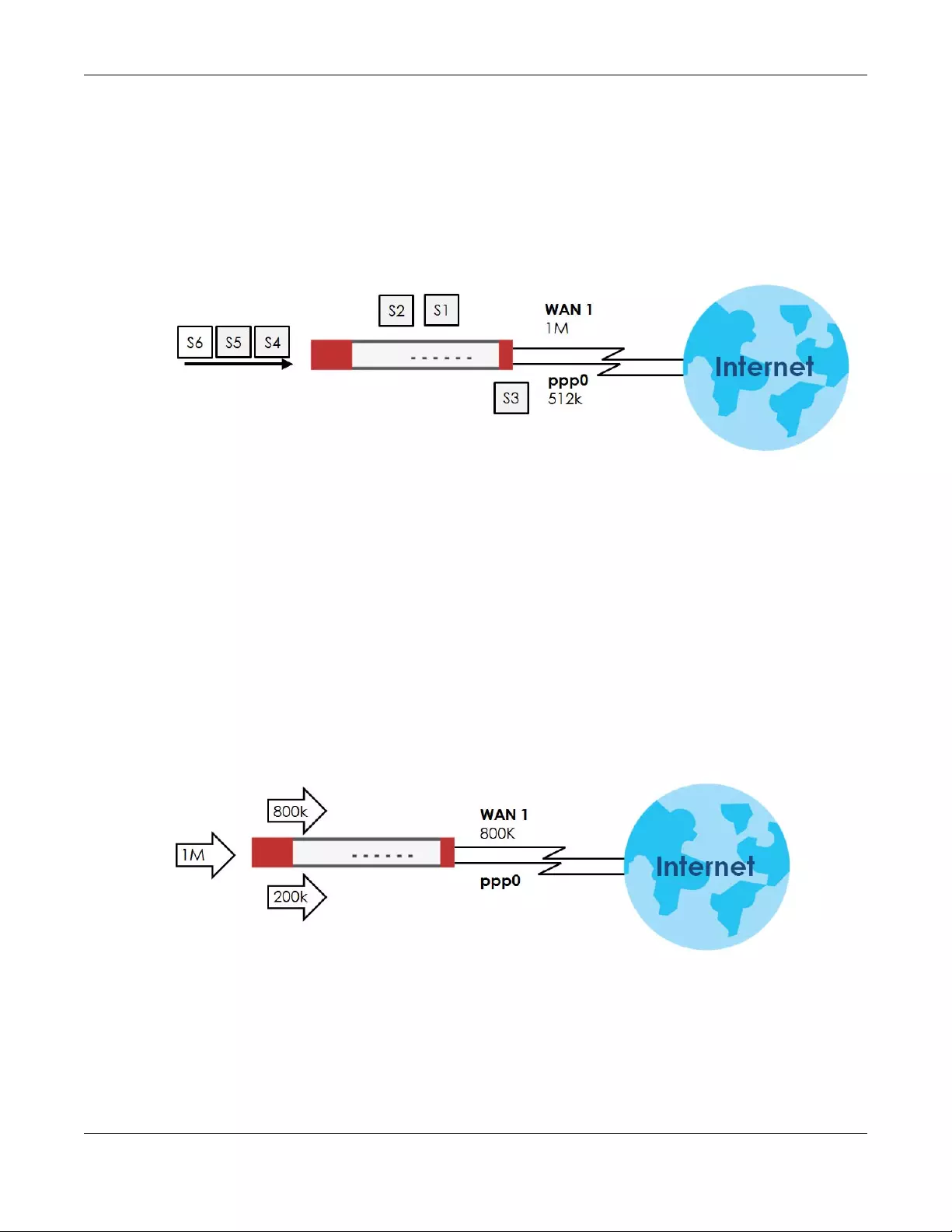
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
358
WAN interfaces are assigned weights. An interface with a larger weight gets more chances to transmit
traffic than an interface with a smaller weight.
For example, in the figure below, the configured available bandwidth of WAN1 is 1M and WAN2 is 512K.
You can set the Zyxel Device to distribute the network traffic between the two interfaces by setting the
weight of wan1 and wan2 to 2 and 1 respectively. The Zyxel Device assigns the traffic of two sessions to
wan1 and one session's traffic to wan2 in each round of 3 new sessions.
Figure 257 Weighted Round Robin Algorithm Example
Spillover
The spillover load balancing algorithm sends network traffic to the first interface in the trunk member list
until the interface’s maximum allowable load is reached, then sends the excess network traffic of new
sessions to the next interface in the trunk member list. This continues as long as there are more member
interfaces and traffic to be sent through them.
Suppose the first trunk member interface uses an unlimited access Internet connection and the second
is billed by usage. Spillover load balancing only uses the second interface when the traffic load exceeds
the threshold on the first interface. This fully utilizes the bandwidth of the first interface to reduce Internet
usage fees and avoid overloading the interface.
In this example figure, the upper threshold of the first interface is set to 800K. The Zyxel Device sends
network traffic of new sessions that exceed this limit to the secondary WAN interface.
Figure 258 Spillover Algorithm Example
10.13 The Trunk Summary Screen
Click Configuration > Network > Interface > Trunk to open the Trunk screen. The Trunk Summary screen
lists the configured trunks and the load balancing algorithm that each is configured to use.
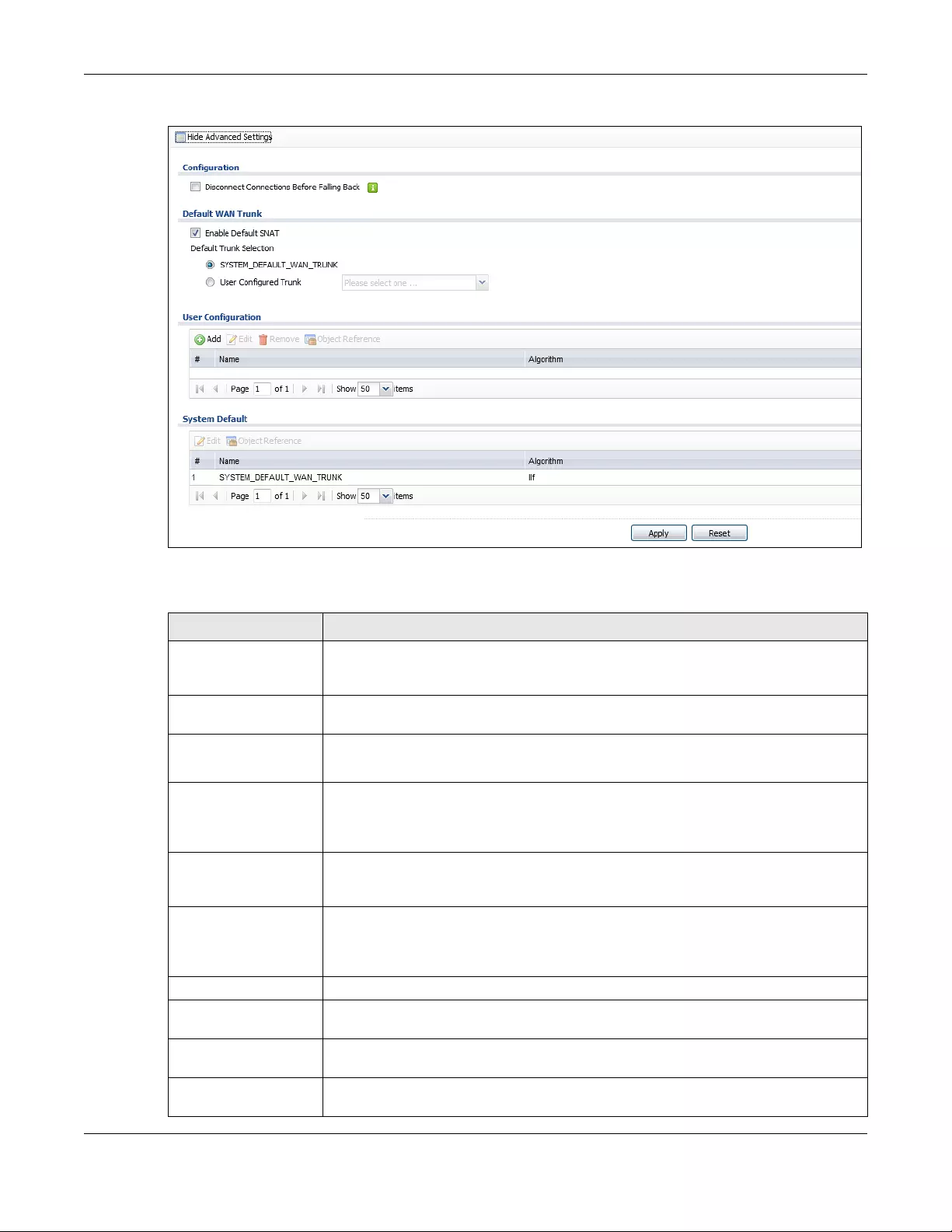
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
359
Figure 259 Configuration > Network > Interface > Trunk
The following table describes the items in this screen.
Table 125 Configuration > Network > Interface > Trunk
LABEL DESCRIPTION
Show Advanced
Settings / Hide
Advanced Settings
Click this button to display a greater or lesser number of configuration fields.
Configuration Configure what to do with existing passive mode interface connections when an
interface set to active mode in the same trunk comes back up.
Disconnect
Connections Before
Falling Back
Select this to terminate existing connections on an interface which is set to passive mode
when any interface set to active mode in the same trunk comes back up.
Enable Default SNAT Select this to have the Zyxel Device use the IP address of the outgoing interface as the
source IP address of the packets it sends out through its WAN trunks. The Zyxel Device
automatically adds SNAT settings for traffic it routes from internal interfaces to external
interfaces.
Default Trunk Selection Select whether the Zyxel Device is to use the default system WAN trunk or one of the user
configured WAN trunks as the default trunk for routing traffic from internal interfaces to
external interfaces.
User Configuration /
System Default
The Zyxel Device automatically adds all external interfaces into the pre-configured
system default SYSTEM_DEFAULT_WAN_TRUNK. You cannot delete it. You can create your
own User Configuration trunks and customize the algorithm, member interfaces and the
active/passive mode.
Add Click this to create a new user-configured trunk.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify
the entry’s settings.
Remove To remove a user-configured trunk, select it and click Remove. The Zyxel Device confirms
you want to remove it before doing so.
Object References Select an entry and click Object References to open a screen that shows which settings
use the entry. See Section 10.4.4 on page 294 for an example.
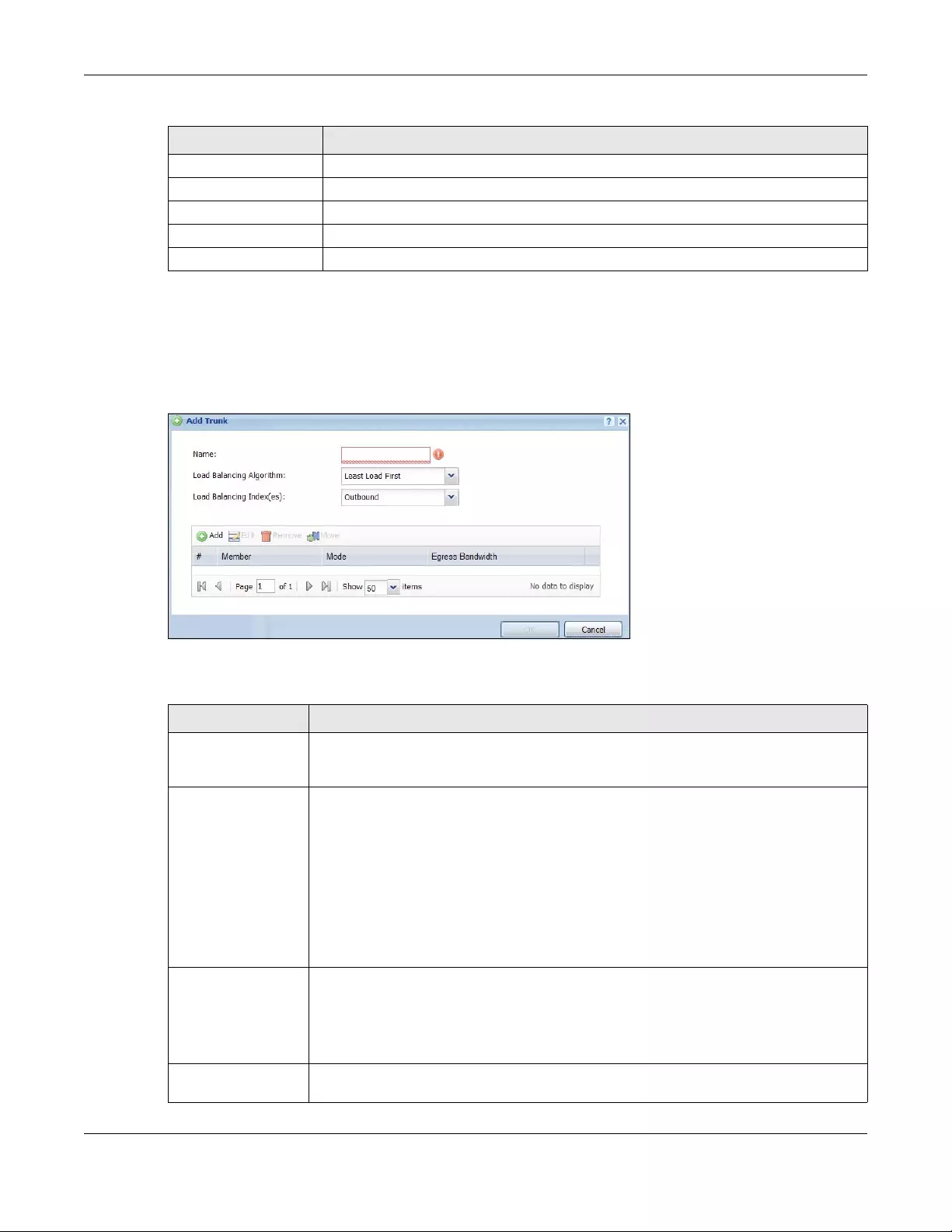
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
360
10.13.1 Configuring a User-Defined Trunk
Click Configuration > Network > Interface > Trunk, in the User Configuration table click the Add (or Edit)
icon to open the following screen. Use this screen to create or edit a WAN trunk entry.
Figure 260 Configuration > Network > Interface > Trunk > Add (or Edit)
Each field is described in the table below.
# This field is a sequential value, and it is not associated with any interface.
Name This field displays the label that you specified to identify the trunk.
Algorithm This field displays the load balancing method the trunk is set to use.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
Table 125 Configuration > Network > Interface > Trunk (continued)
LABEL DESCRIPTION
Table 126 Configuration > Network > Interface > Trunk > Add (or Edit)
LABEL DESCRIPTION
Name This is read-only if you are editing an existing trunk. When adding a new trunk, enter a
descriptive name for this trunk. You may use 1-31 alphanumeric characters, underscores
(_), or dashes (-), but the first character cannot be a number. This value is case-sensitive.
Load Balancing
Algorithm
Select a load balancing method to use from the drop-down list box.
Select Weighted Round Robin to balance the traffic load between interfaces based on
their respective weights. An interface with a larger weight gets more chances to transmit
traffic than an interface with a smaller weight. For example, if the weight ratio of wan1 and
wan2 interfaces is 2:1, the Zyxel Device chooses wan1 for 2 sessions’ traffic and wan2 for 1
session’s traffic in each round of 3 new sessions.
Select Least Load First to send new session traffic through the least utilized trunk member.
Select Spillover to send network traffic through the first interface in the group member list
until there is enough traffic that the second interface needs to be used (and so on).
Load Balancing
Index(es)
This field is available if you selected to use the Least Load First or Spillover method.
Select Outbound, Inbound, or Outbound + Inbound to set the traffic to which the Zyxel
Device applies the load balancing method. Outbound means the traffic traveling from an
internal interface (ex. LAN) to an external interface (ex. WAN). Inbound means the
opposite.
The table lists the trunk’s member interfaces. You can add, edit, remove, or move entries for
user configured trunks.
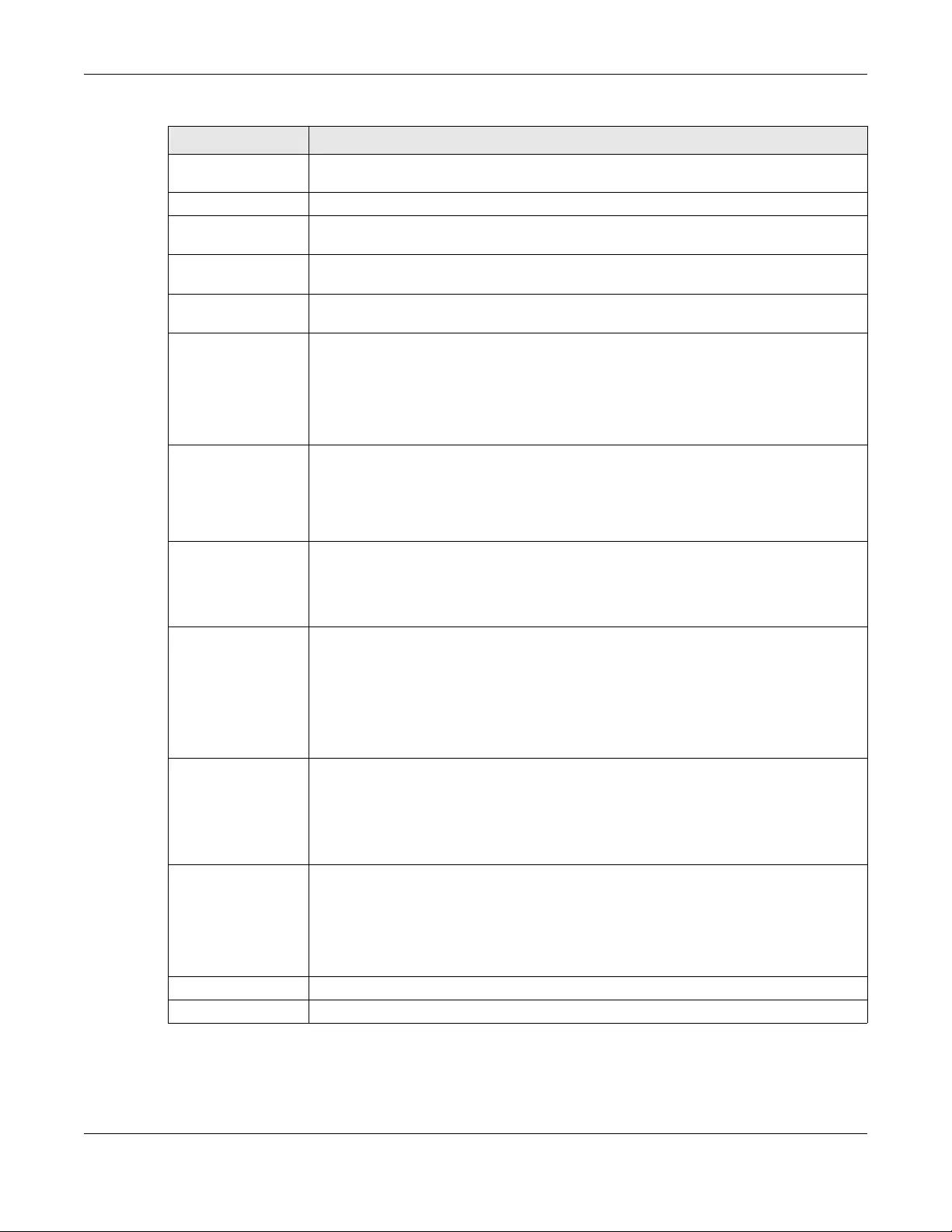
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
361
Add Click this to add a member interface to the trunk. Select an interface and click Add to add
a new member interface after the selected member interface.
Edit Select an entry and click Edit to modify the entry’s settings.
Remove To remove a member interface, select it and click Remove. The Zyxel Device confirms you
want to remove it before doing so.
Move To move an interface to a different number in the list, click the Move icon. In the field that
appears, specify the number to which you want to move the interface.
# This column displays the priorities of the group’s interfaces. The order of the interfaces in the
list is important since they are used in the order they are listed.
Member Click this table cell and select an interface to be a group member.
If you select an interface that is part of another Ethernet interface, the Zyxel Device does
not send traffic through the interface as part of the trunk. For example, if you have physical
port 5 in the ge2 representative interface, you must select interface ge2 in order to send
traffic through port 5 as part of the trunk. If you select interface ge5 as a member here, the
Zyxel Device will not send traffic through port 5 as part of the trunk.
Mode Click this table cell and select Active to have the Zyxel Device always attempt to use this
connection.
Select Passive to have the Zyxel Device only use this connection when all of the
connections set to active are down. You can only set one of a group’s interfaces to passive
mode.
Weight This field displays with the weighted round robin load balancing algorithm. Specify the
weight (1~10) for the interface. The weights of the different member interfaces form a ratio.
This ratio determines how much traffic the Zyxel Device assigns to each member interface.
The higher an interface’s weight is (relative to the weights of the interfaces), the more
sessions that interface should handle.
Ingress Bandwidth This is reserved for future use.
This field displays with the least load first load balancing algorithm. It displays the maximum
number of kilobits of data the Zyxel Device is to allow to come in through the interface per
second.
Note: You can configure the bandwidth of an interface in the corresponding
interface edit screen.
Egress Bandwidth This field displays with the least load first or spillover load balancing algorithm. It displays the
maximum number of kilobits of data the Zyxel Device is to send out through the interface
per second.
Note: You can configure the bandwidth of an interface in the corresponding
interface edit screen.
Spillover This field displays with the spillover load balancing algorithm. Specify the maximum
bandwidth of traffic in kilobits per second (1~1048576) to send out through the interface
before using another interface. When this spillover bandwidth limit is exceeded, the Zyxel
Device sends new session traffic through the next interface. The traffic of existing sessions
still goes through the interface on which they started.
The Zyxel Device uses the group member interfaces in the order that they are listed.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 126 Configuration > Network > Interface > Trunk > Add (or Edit) (continued)
LABEL DESCRIPTION
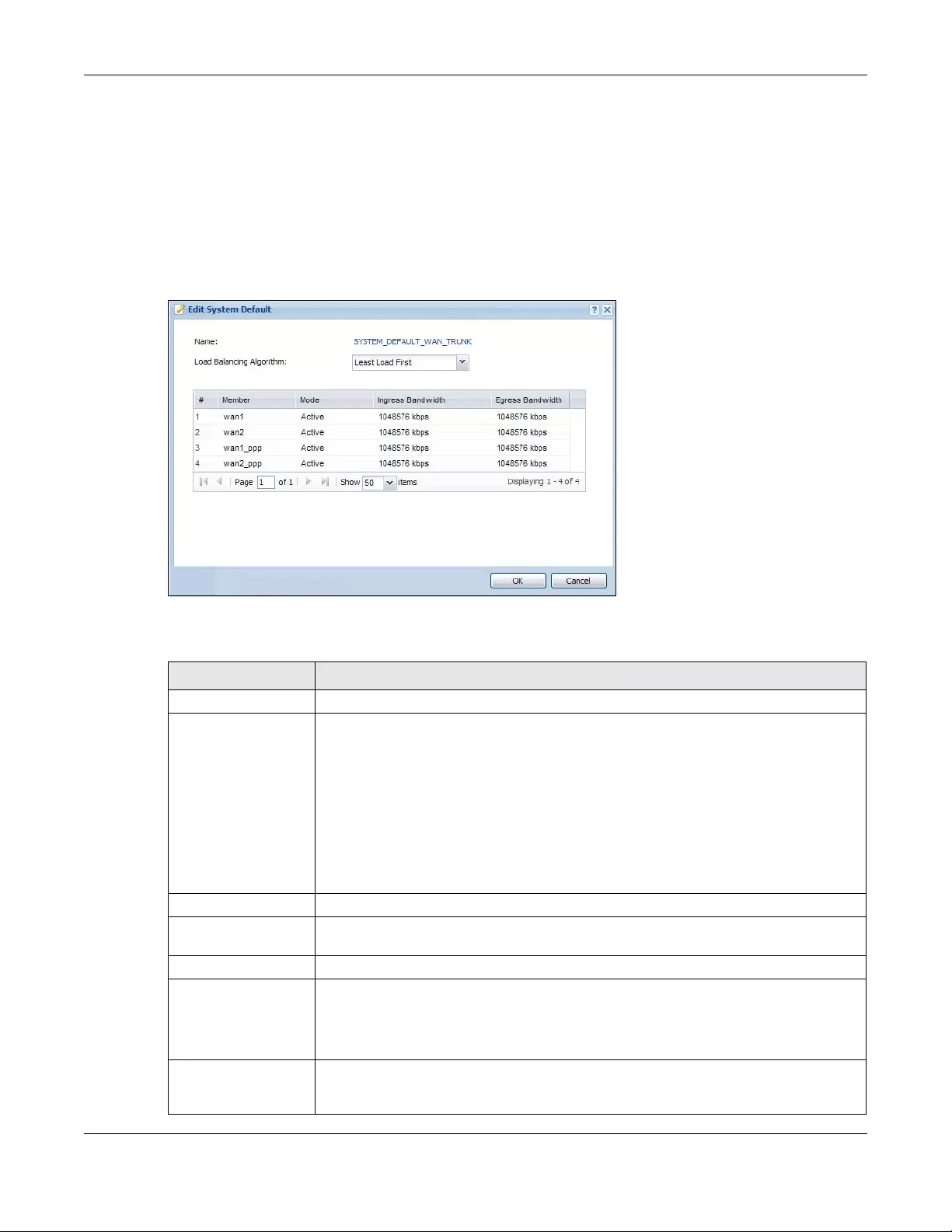
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
362
10.13.2 Configuring the System Default Trunk
In the Configuration > Network > Interface > Trunk screen and the System Default section, select the
default trunk entry and click Edit to open the following screen. Use this screen to change the load
balancing algorithm and view the bandwidth allocations for each member interface.
Note: The available bandwidth is allocated to each member interface equally and is not
allowed to be changed for the default trunk.
Figure 261 Configuration > Network > Interface > Trunk > Edit (System Default)
Each field is described in the table below.
Table 127 Configuration > Network > Interface > Trunk > Edit (System Default)
LABEL DESCRIPTION
Name This field displays the name of the selected system default trunk.
Load Balancing
Algorithm
Select the load balancing method to use for the trunk.
Select Weighted Round Robin to balance the traffic load between interfaces based on
their respective weights. An interface with a larger weight gets more chances to transmit
traffic than an interface with a smaller weight. For example, if the weight ratio of wan1
and wan2 interfaces is 2:1, the Zyxel Device chooses wan1 for 2 sessions’ traffic and wan2
for 1 session’s traffic in each round of 3 new sessions.
Select Least Load First to send new session traffic through the least utilized trunk member.
Select Spillover to send network traffic through the first interface in the group member list
until there is enough traffic that the second interface needs to be used (and so on).
The table lists the trunk’s member interfaces. This table is read-only.
# This column displays the priorities of the group’s interfaces. The order of the interfaces in
the list is important since they are used in the order they are listed.
Member This column displays the name of the member interfaces.
Mode This field displays Active if the Zyxel Device always attempt to use this connection.
This field displays Passive if the Zyxel Device only use this connection when all of the
connections set to active are down. Only one of a group’s interfaces can be set to
passive mode.
Weight This field displays with the weighted round robin load balancing algorithm. Specify the
weight (1~10) for the interface. The weights of the different member interfaces form a
ratio. s
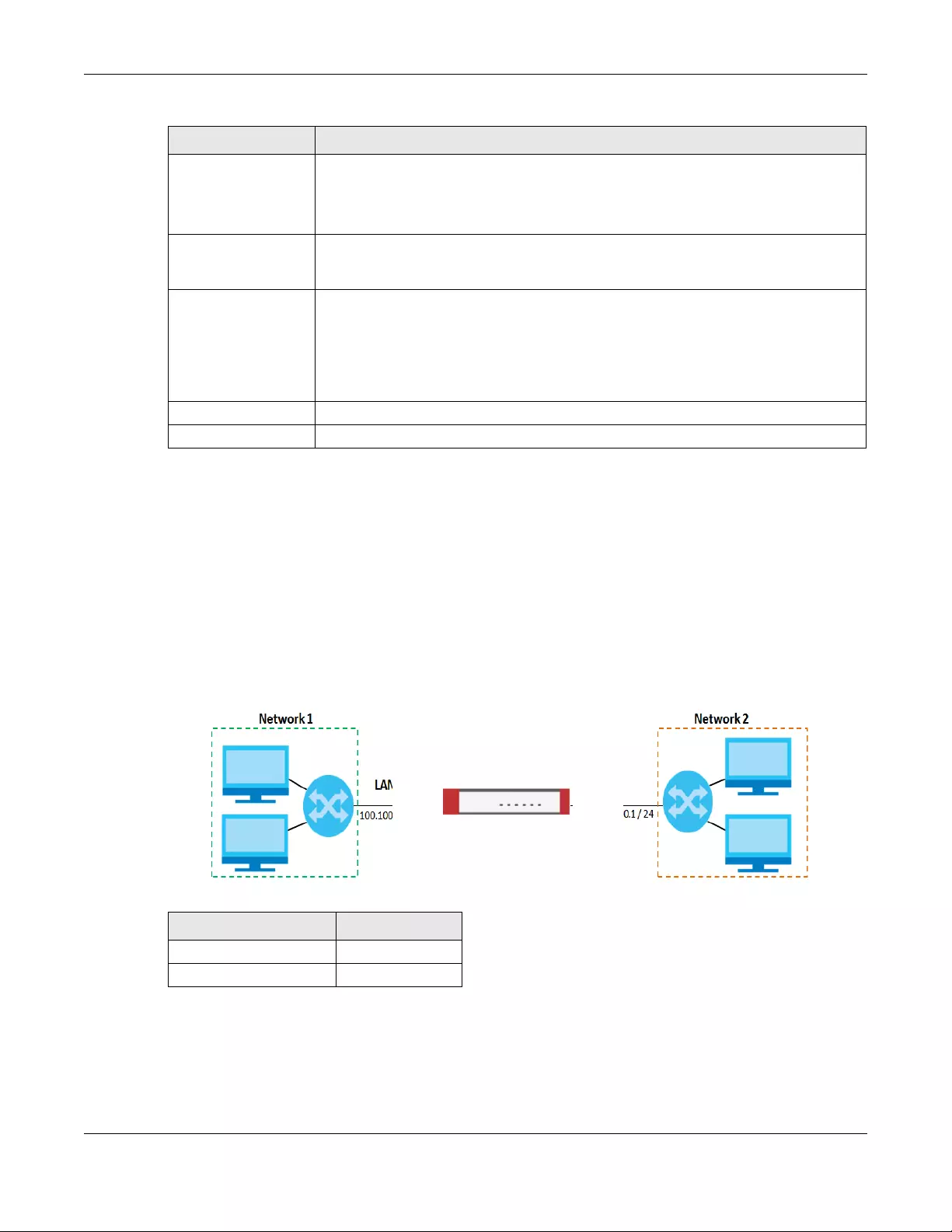
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
363
10.14 Interface Technical Reference
Here is more detailed information about interfaces on the Zyxel Device.
IP Address Assignment
Most interfaces have an IP address and a subnet mask. This information is used to create an entry in the
routing table.
Figure 262 Example: Entry in the Routing Table Derived from Interfaces
For example, if the Zyxel Device gets a packet with a destination address of 100.100.25.25, it routes the
packet to interface lan1. If the Zyxel Device gets a packet with a destination address of 200.200.200.200,
it routes the packet to interface wan1.
Ingress Bandwidth This is reserved for future use.
This field displays with the least load first load balancing algorithm. It displays the
maximum number of kilobits of data the Zyxel Device is to allow to come in through the
interface per second.
Egress Bandwidth This field displays with the least load first or spillover load balancing algorithm. It displays
the maximum number of kilobits of data the Zyxel Device is to send out through the
interface per second.
Spillover This field displays with the spillover load balancing algorithm. Specify the maximum
bandwidth of traffic in kilobits per second (1~1048576) to send out through the interface
before using another interface. When this spillover bandwidth limit is exceeded, the Zyxel
Device sends new session traffic through the next interface. The traffic of existing sessions
still goes through the interface on which they started.
The Zyxel Device uses the group member interfaces in the order that they are listed.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 127 Configuration > Network > Interface > Trunk > Edit (System Default) (continued)
LABEL DESCRIPTION
Table 128 Example: Routing Table Entries for Interfaces
IP ADDRESS(ES) DESTINATION
100.100.1.1/16 lan1
200.200.200.1/24 wan1
lan1 wan1
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
364
In most interfaces, you can enter the IP address and subnet mask manually. In PPPoE/PPTP/L2TP
interfaces, however, the subnet mask is always 255.255.255.255 because it is a point-to-point interface.
For these interfaces, you can only enter the IP address.
In many interfaces, you can also let the IP address and subnet mask be assigned by an external DHCP
server on the network. In this case, the interface is a DHCP client. Virtual interfaces, however, cannot be
DHCP clients. You have to assign the IP address and subnet mask manually.
In general, the IP address and subnet mask of each interface should not overlap, though it is possible for
this to happen with DHCP clients.
In the example above, if the Zyxel Device gets a packet with a destination address of 5.5.5.5, it might
not find any entries in the routing table. In this case, the packet is dropped. However, if there is a default
router to which the Zyxel Device should send this packet, you can specify it as a gateway in one of the
interfaces. For example, if there is a default router at 200.200.200.100, you can create a gateway at
200.200.200.100 on ge2. In this case, the Zyxel Device creates the following entry in the routing table.
The gateway is an optional setting for each interface. If there is more than one gateway, the Zyxel
Device uses the gateway with the lowest metric, or cost. If two or more gateways have the same metric,
the Zyxel Device uses the one that was set up first (the first entry in the routing table). In PPPoE/PPTP/L2TP
interfaces, the other computer is the gateway for the interface by default. In this case, you should
specify the metric.
If the interface gets its IP address and subnet mask from a DHCP server, the DHCP server also specifies
the gateway, if any.
Interface Parameters
The Zyxel Device restricts the amount of traffic into and out of the Zyxel Device through each interface.
• Egress bandwidth sets the amount of traffic the Zyxel Device sends out through the interface to the
network.
• Ingress bandwidth sets the amount of traffic the Zyxel Device allows in through the interface from the
network.At the time of writing, the Zyxel Device does not support ingress bandwidth management.
If you set the bandwidth restrictions very high, you effectively remove the restrictions.
The Zyxel Device also restricts the size of each data packet. The maximum number of bytes in each
packet is called the maximum transmission unit (MTU). If a packet is larger than the MTU, the Zyxel
Device divides it into smaller fragments. Each fragment is sent separately, and the original packet is re-
assembled later. The smaller the MTU, the more fragments sent, and the more work required to re-
assemble packets correctly. On the other hand, some communication channels, such as Ethernet over
ATM, might not be able to handle large data packets.
DHCP Settings
Dynamic Host Configuration Protocol (DHCP, RFC 2131, RFC 2132) provides a way to automatically set
up and maintain IP addresses, subnet masks, gateways, and some network information (such as the IP
Table 129 Example: Routing Table Entry for a Gateway
IP ADDRESS(ES) DESTINATION
0.0.0.0/0 200.200.200.100
Chapter 10 Interfaces
USG/ZyWALL User’s Guide
365
addresses of DNS servers) on computers in the network. This reduces the amount of manual
configuration you have to do and usually uses available IP addresses more efficiently.
In DHCP, every network has at least one DHCP server. When a computer (a DHCP client) joins the
network, it submits a DHCP request. The DHCP servers get the request; assign an IP address; and provide
the IP address, subnet mask, gateway, and available network information to the DHCP client. When the
DHCP client leaves the network, the DHCP servers can assign its IP address to another DHCP client.
In the Zyxel Device, some interfaces can provide DHCP services to the network. In this case, the
interface can be a DHCP relay or a DHCP server.
As a DHCP relay, the interface routes DHCP requests to DHCP servers on different networks. You can
specify more than one DHCP server. If you do, the interface routes DHCP requests to all of them. It is
possible for an interface to be a DHCP relay and a DHCP client simultaneously.
As a DHCP server, the interface provides the following information to DHCP clients.
• IP address - If the DHCP client’s MAC address is in the Zyxel Device’s static DHCP table, the interface
assigns the corresponding IP address. If not, the interface assigns IP addresses from a pool, defined by
the starting address of the pool and the pool size.
The Zyxel Device cannot assign the first address (network address) or the last address (broadcast
address) in the subnet defined by the interface’s IP address and subnet mask. For example, in the first
entry, if the subnet mask is 255.255.255.0, the Zyxel Device cannot assign 50.50.50.0 or 50.50.50.255. If
the subnet mask is 255.255.0.0, the Zyxel Device cannot assign 50.50.0.0 or 50.50.255.255. Otherwise, it
can assign every IP address in the range, except the interface’s IP address.
If you do not specify the starting address or the pool size, the interface the maximum range of IP
addresses allowed by the interface’s IP address and subnet mask. For example, if the interface’s IP
address is 9.9.9.1 and subnet mask is 255.255.255.0, the starting IP address in the pool is 9.9.9.2, and the
pool size is 253.
• Subnet mask - The interface provides the same subnet mask you specify for the interface. See IP
Address Assignment on page 363.
• Gateway - The interface provides the same gateway you specify for the interface. See IP Address
Assignment on page 363.
• DNS servers - The interface provides IP addresses for up to three DNS servers that provide DNS services
for DHCP clients. You can specify each IP address manually (for example, a company’s own DNS
server), or you can refer to DNS servers that other interfaces received from DHCP servers (for example,
a DNS server at an ISP). These other interfaces have to be DHCP clients.
It is not possible for an interface to be the DHCP server and a DHCP client simultaneously.
WINS
WINS (Windows Internet Naming Service) is a Windows implementation of NetBIOS Name Server (NBNS)
on Windows. It keeps track of NetBIOS computer names. It stores a mapping table of your network’s
computer names and IP addresses. The table is dynamically updated for IP addresses assigned by
Table 130 Example: Assigning IP Addresses from a Pool
START IP ADDRESS POOL SIZE RANGE OF ASSIGNED IP ADDRESS
50.50.50.33 5 50.50.50.33 - 50.50.50.37
75.75.75.1 200 75.75.75.1 - 75.75.75.200
99.99.1.1 1023 99.99.1.1 - 99.99.4.255
120.120.120.100 100 120.120.120.100 - 120.120.120.199

Chapter 10 Interfaces
USG/ZyWALL User’s Guide
366
DHCP. This helps reduce broadcast traffic since computers can query the server instead of
broadcasting a request for a computer name’s IP address. In this way WINS is similar to DNS, although
WINS does not use a hierarchy (unlike DNS). A network can have more than one WINS server. Samba
can also serve as a WINS server.
PPPoE/PPTP/L2TP Overview
Point-to-Point Protocol over Ethernet (PPPoE, RFC 2516) and Point-to-Point Tunneling Protocol (PPTP, RFC
2637) are usually used to connect two computers over phone lines or broadband connections. PPPoE is
often used with cable modems and DSL connections. It provides the following advantages:
• The access and authentication method works with existing systems, including RADIUS.
• You can access one of several network services. This makes it easier for the service provider to offer
the service
• PPPoE does not usually require any special configuration of the modem.
PPTP is used to set up virtual private networks (VPN) in unsecured TCP/IP environments. It sets up two
sessions.
1The first one runs on TCP port 1723. It is used to start and manage the second one.
2The second one uses Generic Routing Encapsulation (GRE, RFC 2890) to transfer information between
the computers.
PPTP is convenient and easy-to-use, but you have to make sure that firewalls support both PPTP sessions.
Layer 2 Tunneling Protocol (L2TP) was taken from PPTP of Microsoft and Cisco’s L2F (Layer 2 Forwarding
technology), so LT2P combines PPTP’s control and runs over a faster transport protocol, UDP, although it
may be a bit more complicated to set up.
It supports up to 256 bit session keys using the IPSec protocol. When security is a priority, L2TP is a good
option as it requires certificates unlike PPTP.
It uses the following ports: UDP 500, Protocol 50, UDP 1701 and UDP 4500.

USG/ZyWALL User’s Guide
367
CHAPTER 11
Routing
11.1 Policy and Static Routes Overview
Use policy routes and static routes to override the Zyxel Device’s default routing behavior in order to
send packets through the appropriate interface or VPN tunnel.
For example, the next figure shows a computer (A) connected to the Zyxel Device’s LAN interface. The
Zyxel Device routes most traffic from A to the Internet through the Zyxel Device’s default gateway (R1).
You create one policy route to connect to services offered by your ISP behind router R2. You create
another policy route to communicate with a separate network behind another router (R3) connected
to the LAN.
Figure 263 Example of Policy Routing Topology
Note: You can generally just use policy routes. You only need to use static routes if you have a
large network with multiple routers where you use RIP or OSPF to propagate routing
information to other routers.
11.1.1 What You Can Do in this Chapter
• Use the Policy Route screens (see Section 11.2 on page 369) to list and configure policy routes.
• Use the Static Route screens (see Section 11.3 on page 376) to list and configure static routes.

Chapter 11 Routing
USG/ZyWALL User’s Guide
368
11.1.2 What You Need to Know
Policy Routing
Traditionally, routing is based on the destination address only and the Zyxel Device takes the shortest
path to forward a packet. IP Policy Routing (IPPR) provides a mechanism to override the default routing
behavior and alter the packet forwarding based on the policy defined by the network administrator.
Policy-based routing is applied to incoming packets on a per interface basis, prior to the normal routing.
How You Can Use Policy Routing
• Source-Based Routing – Network administrators can use policy-based routing to direct traffic from
different users through different connections.
• Bandwidth Shaping – You can allocate bandwidth to traffic that matches routing policies and
prioritize traffic (however the application patrol’s bandwidth management is more flexible and
recommended for TCP and UDP traffic). You can also use policy routes to manage other types of
traffic (like ICMP traffic) and send traffic through VPN tunnels.
Note: Bandwidth management in policy routes has priority over application patrol bandwidth
management.
• Cost Savings – IPPR allows organizations to distribute interactive traffic on high-bandwidth, high-cost
paths while using low-cost paths for batch traffic.
• Load Sharing – Network administrators can use IPPR to distribute traffic among multiple paths.
• NAT - The Zyxel Device performs NAT by default for traffic going to or from the WAN interfaces. A
routing policy’s SNAT allows network administrators to have traffic received on a specified interface
use a specified IP address as the source IP address.
Note: The Zyxel Device automatically uses SNAT for traffic it routes from internal interfaces to
external interfaces. For example LAN to WAN traffic.
Static Routes
The Zyxel Device usually uses the default gateway to route outbound traffic from computers on the LAN
to the Internet. To have the Zyxel Device send data to devices not reachable through the default
gateway, use static routes. Configure static routes if you need to use RIP or OSPF to propagate the
routing information to other routers. See Chapter 11 on page 378 for more on RIP and OSPF.
Policy Routes Versus Static Routes
• Policy routes are more flexible than static routes. You can select more criteria for the traffic to match
and can also use schedules, NAT, and bandwidth management.
• Policy routes are only used within the Zyxel Device itself. Static routes can be propagated to other
routers using RIP or OSPF.
• Policy routes take priority over static routes. If you need to use a routing policy on the Zyxel Device
and propagate it to other routers, you could configure a policy route and an equivalent static route.
DiffServ
QoS is used to prioritize source-to-destination traffic flows. All packets in the same flow are given the
same priority. CoS (class of service) is a way of managing traffic in a network by grouping similar types of
Chapter 11 Routing
USG/ZyWALL User’s Guide
369
traffic together and treating each type as a class. You can use CoS to give different priorities to different
packet types.
DiffServ (Differentiated Services) is a class of service (CoS) model that marks packets so that they
receive specific per-hop treatment at DiffServ-compliant network devices along the route based on the
application types and traffic flow. Packets are marked with DiffServ Code Points (DSCPs) indicating the
level of service desired. This allows the intermediary DiffServ-compliant network devices to handle the
packets differently depending on the code points without the need to negotiate paths or remember
state information for every flow. In addition, applications do not have to request a particular service or
give advanced notice of where the traffic is going.
DSCP Marking and Per-Hop Behavior
DiffServ defines a new DS (Differentiated Services) field to replace the Type of Service (TOS) field in the IP
header. The DS field contains a 2-bit unused field and a 6-bit DSCP field which can define up to 64
service levels. The following figure illustrates the DS field.
DSCP is backward compatible with the three precedence bits in the ToS octet so that non-DiffServ
compliant, ToS-enabled network device will not conflict with the DSCP mapping.
The DSCP value determines the forwarding behavior, the PHB (Per-Hop Behavior), that each packet
gets across the DiffServ network. Based on the marking rule, different kinds of traffic can be marked for
different kinds of forwarding. Resources can then be allocated according to the DSCP values and the
configured policies.
11.2 Policy Route Screen
Click Configuration > Network > Routing to open the Policy Route screen. Use this screen to see the
configured policy routes and turn policy routing based bandwidth management on or off.
A policy route defines the matching criteria and the action to take when a packet meets the criteria.
The action is taken only when all the criteria are met. The criteria can include the user name, source
address and incoming interface, destination address, schedule, IP protocol (ICMP, UDP, TCP, etc.) and
port.
The actions that can be taken include:
• Routing the packet to a different gateway, outgoing interface, VPN tunnel, or trunk.
• Limiting the amount of bandwidth available and setting a priority for traffic.
IPPR follows the existing packet filtering facility of RAS in style and in implementation.
If you enabled IPv6 in the Configuration > System > IPv6 screen, you can also configure policy routes
used for your IPv6 networks on this screen.
Click on the icons to go to the OneSecurity.com website where there is guidance on configuration
walkthroughs, troubleshooting, and other information.
DSCP (6 bits) Unused (2 bits)
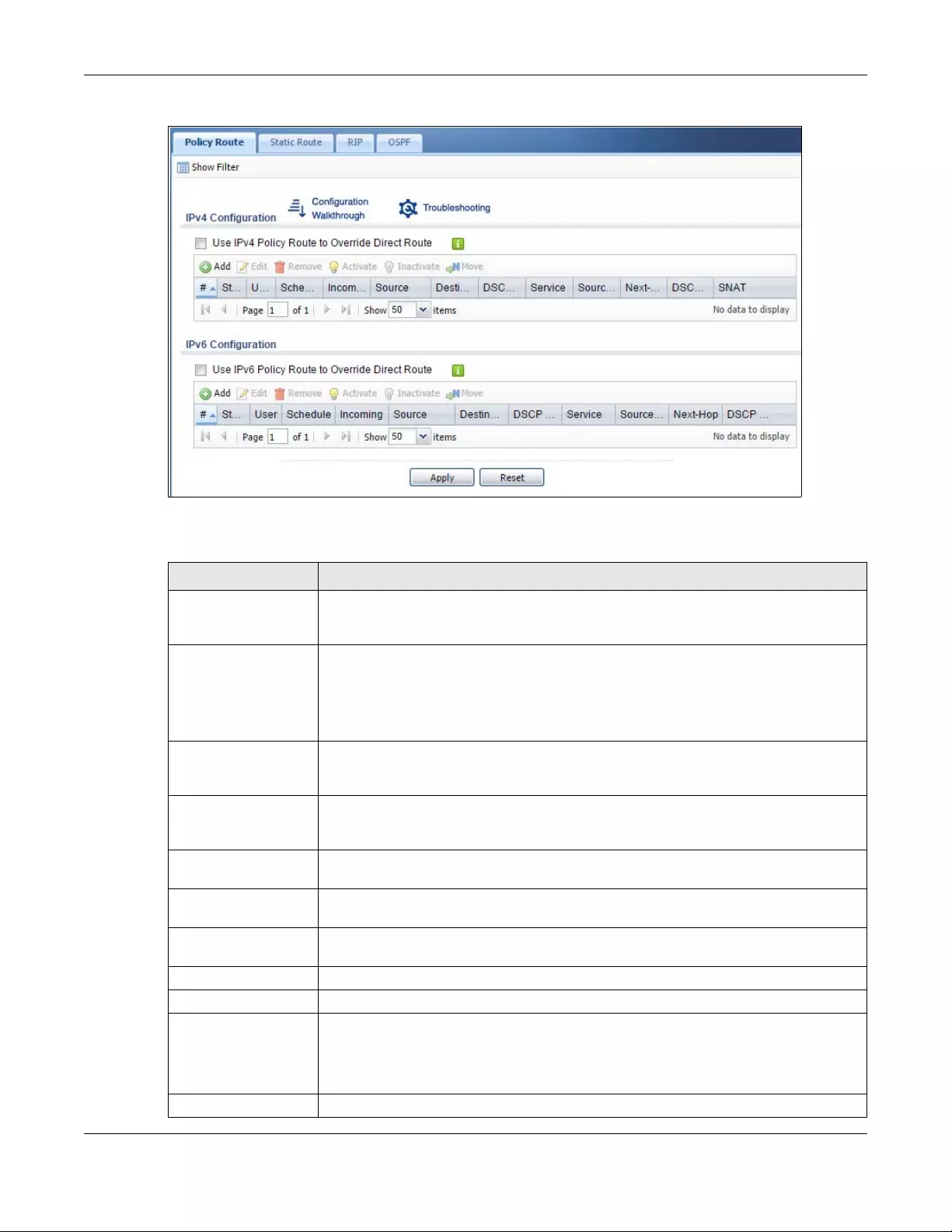
Chapter 11 Routing
USG/ZyWALL User’s Guide
370
Figure 264 Configuration > Network > Routing > Policy Route
The following table describes the labels in this screen.
Table 131 Configuration > Network > Routing > Policy Route
LABEL DESCRIPTION
Show Advanced
Settings / Hide
Advanced Settings
Click this button to display a greater or lesser number of configuration fields.
Enable BWM This is a global setting for enabling or disabling bandwidth management on the Zyxel
Device. You must enable this setting to have individual policy routes or application patrol
policies apply bandwidth management.
This same setting also appears in the AppPatrol > General screen. Enabling or disabling it
in one screen also enables or disables it in the other screen.
IPv4 Configuration /
IPv6 Configuration
Use the IPv4 Configuration section for IPv4 network settings. Use the IPv6 Configuration
section for IPv6 network settings if you connect your Zyxel Device to an IPv6 network. Both
sections have similar fields as described below.
Use IPv4/IPv6 Policy
Route to Override
Direct Route
Select this to have the Zyxel Device forward packets that match a policy route according
to the policy route instead of sending the packets directly to a connected network.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after
the selected entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify
the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Move To change a rule’s position in the numbered list, select the rule and click Move to display
a field to type a number for where you want to put that rule and press [ENTER] to move
the rule to the number that you typed.
The ordering of your rules is important as they are applied in order of their numbering.
#This is the number of an individual policy route.
Chapter 11 Routing
USG/ZyWALL User’s Guide
371
11.2.1 Policy Route Edit Screen
Click Configuration > Network > Routing to open the Policy Route screen. Then click the Add or Edit icon
in the IPv4 Configuration or IPv6 Configuration section. The Add Policy Route or Policy Route Edit screen
opens. Use this screen to configure or edit a policy route. Both IPv4 and IPv6 policy route have similar
settings except the Address Translation (SNAT) settings.
Status This icon is lit when the entry is active, red when the next hop’s connection is down, and
dimmed when the entry is inactive.
User This is the name of the user (group) object from which the packets are sent. any means all
users.
Schedule This is the name of the schedule object. none means the route is active at all times if
enabled.
Incoming This is the interface on which the packets are received.
Source This is the name of the source IP address (group) object. any means all IP addresses.
Destination This is the name of the destination IP address (group) object. any means all IP addresses.
DSCP Code This is the DSCP value of incoming packets to which this policy route applies.
any means all DSCP values or no DSCP marker.
default means traffic with a DSCP value of 0. This is usually best effort traffic
The “af” entries stand for Assured Forwarding. The number following the “af” identifies one
of four classes and one of three drop preferences. See Assured Forwarding (AF) PHB for
DiffServ on page 378 for more details.
Service This is the name of the service object. any means all services.
Source Port This is the name of a service object. The Zyxel Device applies the policy route to the
packets sent from the corresponding service port. any means all service ports.
Next-Hop This is the next hop to which packets are directed. It helps forward packets to their
destinations and can be a router, VPN tunnel, outgoing interface or trunk.
DSCP Marking This is how the Zyxel Device handles the DSCP value of the outgoing packets that match
this route. If this field displays a DSCP value, the Zyxel Device applies that DSCP value to
the route’s outgoing packets.
preserve means the Zyxel Device does not modify the DSCP value of the route’s outgoing
packets.
default means the Zyxel Device sets the DSCP value of the route’s outgoing packets to 0.
The “af” choices stand for Assured Forwarding. The number following the “af” identifies
one of four classes and one of three drop preferences. See Assured Forwarding (AF) PHB
for DiffServ on page 378 for more details.
SNAT This is the source IP address that the route uses.
It displays none if the Zyxel Device does not perform NAT for this route.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 131 Configuration > Network > Routing > Policy Route (continued)
LABEL DESCRIPTION
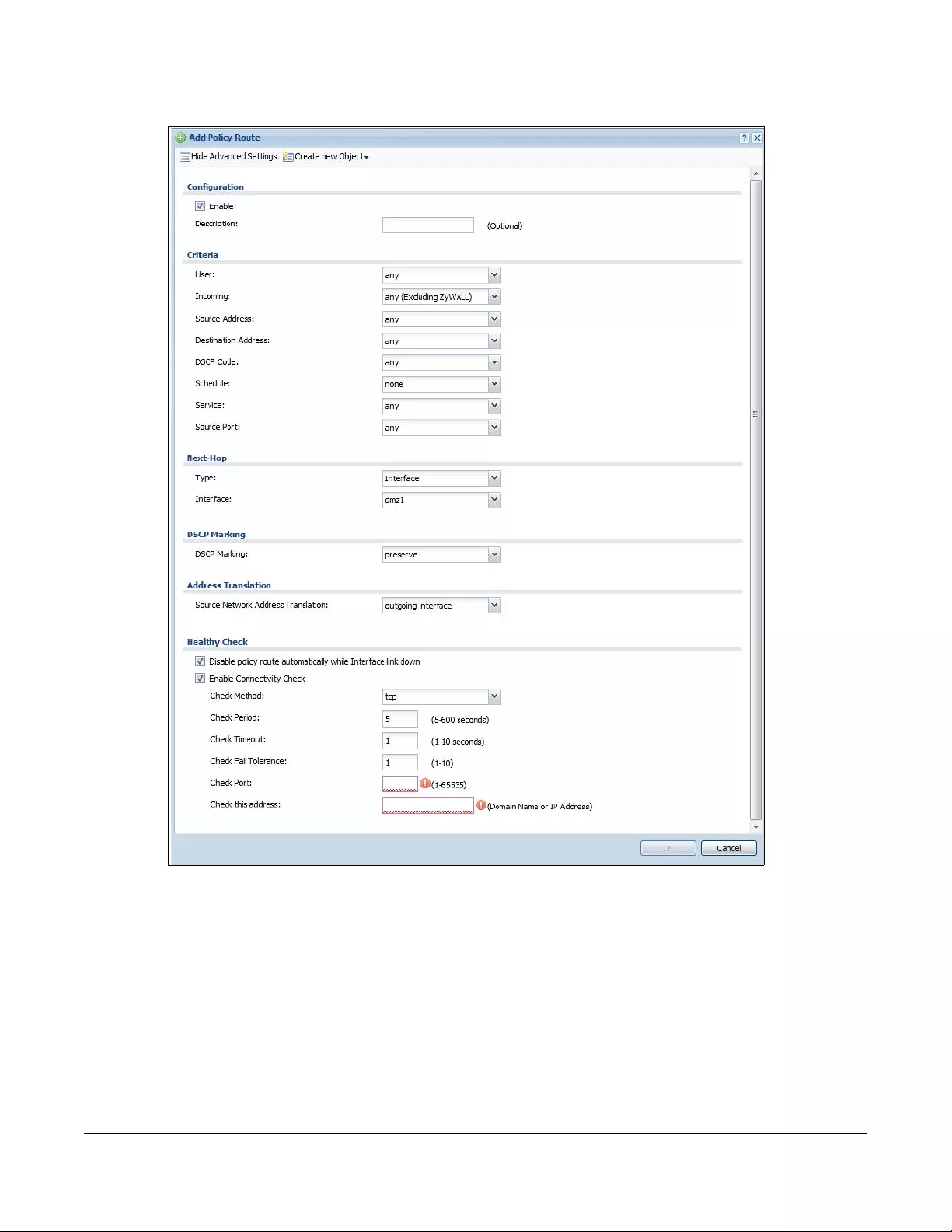
Chapter 11 Routing
USG/ZyWALL User’s Guide
372
Figure 265 Configuration > Network > Routing > Policy Route > Add/Edit (IPv4 Configuration)
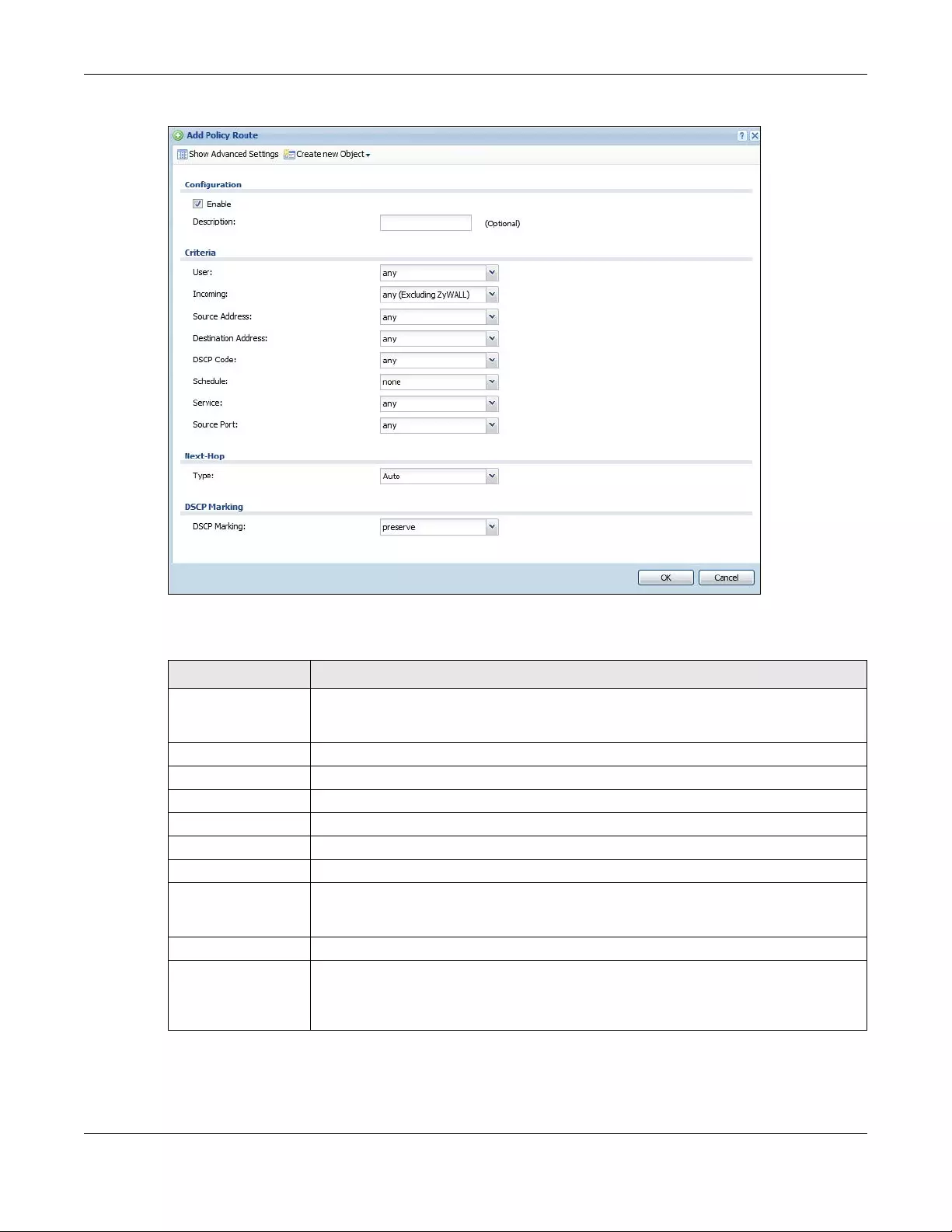
Chapter 11 Routing
USG/ZyWALL User’s Guide
373
Figure 266 Configuration > Network > Routing > Policy Route > Add/Edit (IPv6 Configuration)
The following table describes the labels in this screen.
Table 132 Configuration > Network > Routing > Policy Route > Add/Edit
LABEL DESCRIPTION
Show Advanced
Settings / Hide
Advanced Settings
Click this button to display a greater or lesser number of configuration fields.
Create new Object Use this to configure any new settings objects that you need to use in this screen.
Configuration
Enable Select this to activate the policy.
Description Enter a descriptive name of up to 31 printable ASCII characters for the policy.
Criteria
User Select a user name or user group from which the packets are sent.
Incoming Select where the packets are coming from; any, an interface, a tunnel, an SSL VPN, or the
Zyxel Device itself. For an interface, a tunnel, or an SSL VPN, you also need to select the
individual interface, VPN tunnel, or SSL VPN connection.
Source Address Select a source IP address object from which the packets are sent.
Destination Address Select a destination IP address object to which the traffic is being sent. If the next hop is a
dynamic VPN tunnel and you enable Auto Destination Address, the Zyxel Device uses the
local network of the peer router that initiated an incoming dynamic IPSec tunnel as the
destination address of the policy instead of your configuration here.
Chapter 11 Routing
USG/ZyWALL User’s Guide
374
DSCP Code Select a DSCP code point value of incoming packets to which this policy route applies or
select User Define to specify another DSCP code point. The lower the number the higher
the priority with the exception of 0 which is usually given only best-effort treatment.
any means all DSCP value or no DSCP marker.
default means traffic with a DSCP value of 0. This is usually best effort traffic
The “af” choices stand for Assured Forwarding. The number following the “af” identifies one
of four classes and one of three drop preferences. See Assured Forwarding (AF) PHB for
DiffServ on page 378 for more details.
User-Defined
DSCP Code Use this field to specify a custom DSCP code point when you select User Define in the
previous field.
Schedule Select a schedule to control when the policy route is active. none means the route is active
at all times if enabled.
Service Select a service or service group to identify the type of traffic to which this policy route
applies.
Source Port Select a service or service group to identify the source port of packets to which the policy
route applies.
Next-Hop
Type Select Auto to have the Zyxel Device use the routing table to find a next-hop and forward
the matched packets automatically.
Select Gateway to route the matched packets to the next-hop router or switch you
specified in the Gateway field. You have to set up the next-hop router or switch as a HOST
address object first.
Select VPN Tunnel to route the matched packets via the specified VPN tunnel.
Select Trunk to route the matched packets through the interfaces in the trunk group based
on the load balancing algorithm.
Select Interface to route the matched packets through the specified outgoing interface to
a gateway (which is connected to the interface).
Gateway This field displays when you select Gateway in the Type field. Select a HOST address object.
The gateway is an immediate neighbor of your Zyxel Device that will forward the packet to
the destination. The gateway must be a router or switch on the same segment as your Zyxel
Device's interface(s).
VPN Tunnel This field displays when you select VPN Tunnel in the Type field. Select a VPN tunnel through
which the packets are sent to the remote network that is connected to the Zyxel Device
directly.
Auto Destination
Address This field displays when you select VPN Tunnel in the Type field. Select this to have the Zyxel
Device use the local network of the peer router that initiated an incoming dynamic IPSec
tunnel as the destination address of the policy.
Leave this cleared if you want to manually specify the destination address.
Trunk This field displays when you select Trunk in the Type field. Select a trunk group to have the
Zyxel Device send the packets via the interfaces in the group.
Interface This field displays when you select Interface in the Type field. Select an interface to have
the Zyxel Device send traffic that matches the policy route through the specified interface.
Table 132 Configuration > Network > Routing > Policy Route > Add/Edit (continued)
LABEL DESCRIPTION
Chapter 11 Routing
USG/ZyWALL User’s Guide
375
DSCP Marking Set how the Zyxel Device handles the DSCP value of the outgoing packets that match this
route.
Select one of the pre-defined DSCP values to apply or select User Define to specify another
DSCP value. The “af” choices stand for Assured Forwarding. The number following the “af”
identifies one of four classes and one of three drop preferences. See Assured Forwarding
(AF) PHB for DiffServ on page 378 for more details.
Select preserve to have the Zyxel Device keep the packets’ original DSCP value.
Select default to have the Zyxel Device set the DSCP value of the packets to 0.
User-Defined
DSCP Code Use this field to specify a custom DSCP value.
Address Translation Use this section to configure NAT for the policy route. This section does not apply to policy
routes that use a VPN tunnel as the next hop.
Source Network
Address Translation
Select none to not use NAT for the route.
Select outgoing-interface to use the IP address of the outgoing interface as the source IP
address of the packets that matches this route.
To use SNAT for a virtual interface that is in the same WAN trunk as the physical interface to
which the virtual interface is bound, the virtual interface and physical interface must be in
different subnets.
Otherwise, select a pre-defined address (group) to use as the source IP address(es) of the
packets that match this route.
Use Create n ew Object if you need to configure a new address (group) to use as the
source IP address(es) of the packets that match this route.
Healthy Check Use this part of the screen to configure a route connectivity check and disable the policy if
the interface is down.
Disable policy route
automatically while
Interface link down
Select this to disable the policy if the interface is down or disabled. This is available for
Interface and Trunk in the Type field above.
Enable Connectivity
Check
Select this to turn on the connection check. This is available for Interface and Gateway in
the Type field above.
Check Method: Select the method that the gateway allows.
Select icmp to have the Zyxel Device regularly ping the gateway you specify to make sure
it is still available.
Select tcp to have the Zyxel Device regularly perform a TCP handshake with the gateway
you specify to make sure it is still available.
Check Period: Enter the number of seconds between connection check attempts (5-600 seconds).
Check Timeout: Enter the number of seconds to wait for a response before the attempt is a failure (1-10
seconds).
Check Fail Tolerance: Enter the number of consecutive failures before the Zyxel Device stops routing using this
policy (1-10).
Check Port: This field only displays when you set the Check Method to tcp. Specify the port number to
use for a TCP connectivity check (1-65535).
Check this address: Select this to specify a domain name or IP address for the connectivity check. Enter that
domain name or IP address in the field next to it.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 132 Configuration > Network > Routing > Policy Route > Add/Edit (continued)
LABEL DESCRIPTION
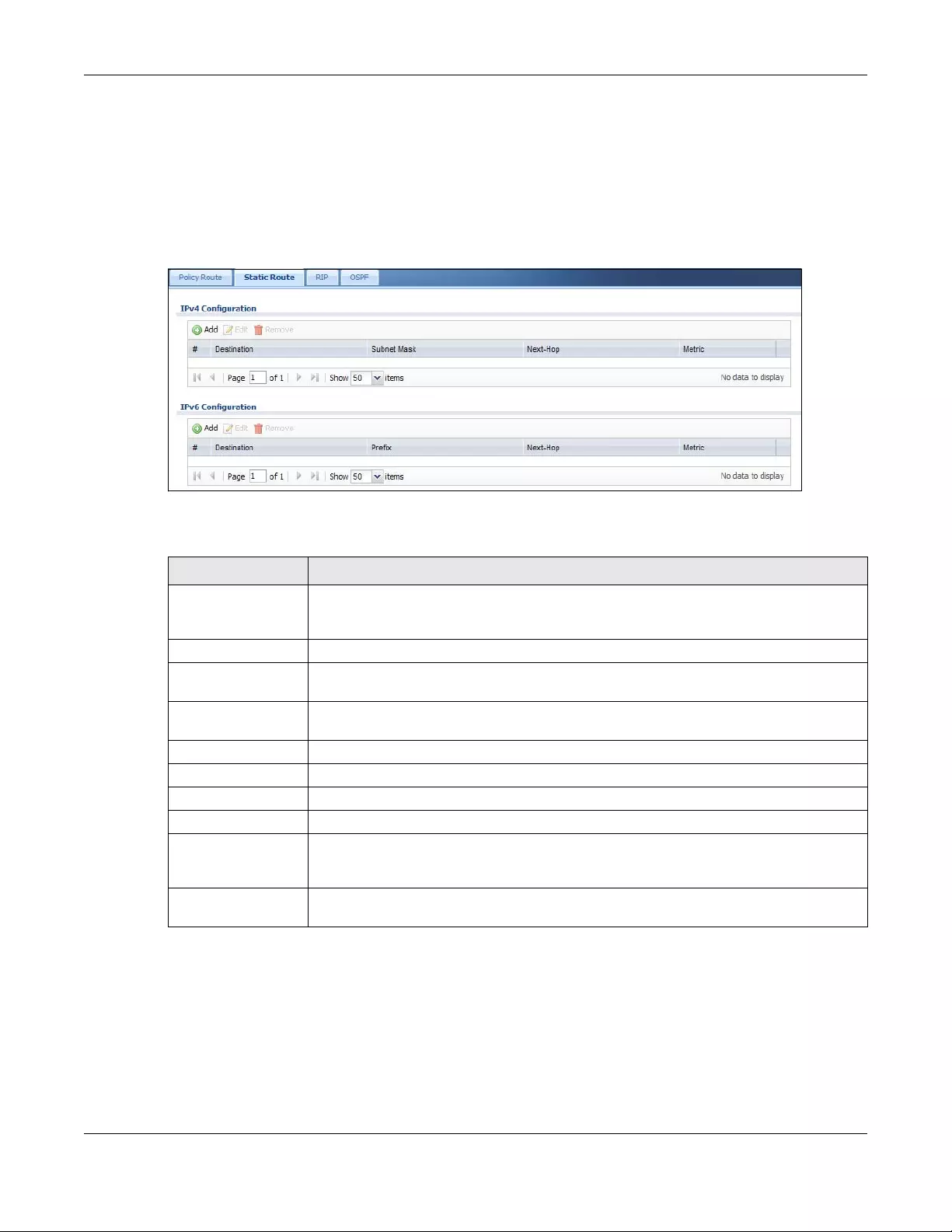
Chapter 11 Routing
USG/ZyWALL User’s Guide
376
11.3 IP Static Route Screen
Click Configuration > Network > Routing > Static Route to open the Static Route screen. This screen
displays the configured static routes. Configure static routes to be able to use RIP or OSPF to propagate
the routing information to other routers. If you enabled IPv6 in the Configuration > System > IPv6 screen,
you can also configure static routes used for your IPv6 networks on this screen.
Figure 267 Configuration > Network > Routing > Static Route
The following table describes the labels in this screen.
11.3.1 Static Route Add/Edit Screen
Select a static route index number and click Add or Edit. The screen shown next appears. Use this screen
to configure the required information for a static route.
Table 133 Configuration > Network > Routing > Static Route
LABEL DESCRIPTION
IPv4 Configuration /
IPv6 Configuration
Use the IPv4 Configuration section for IPv4 network settings. Use the IPv6 Configuration
section for IPv6 network settings if you connect your Zyxel Device to an IPv6 network. Both
sections have similar fields as described below.
Add Click this to create a new static route.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so.
#This is the number of an individual static route.
Destination This is the destination IP address.
Subnet Mask This is the IP subnet mask.
Prefix This is the IPv6 prefix for the destination IP address.
Next-Hop This is the IP address of the next-hop gateway or the interface through which the traffic is
routed. The gateway is a router or switch on the same segment as your Zyxel Device's
interface(s). The gateway helps forward packets to their destinations.
Metric This is the route’s priority among the Zyxel Device’s routes. The smaller the number, the
higher priority the route has.
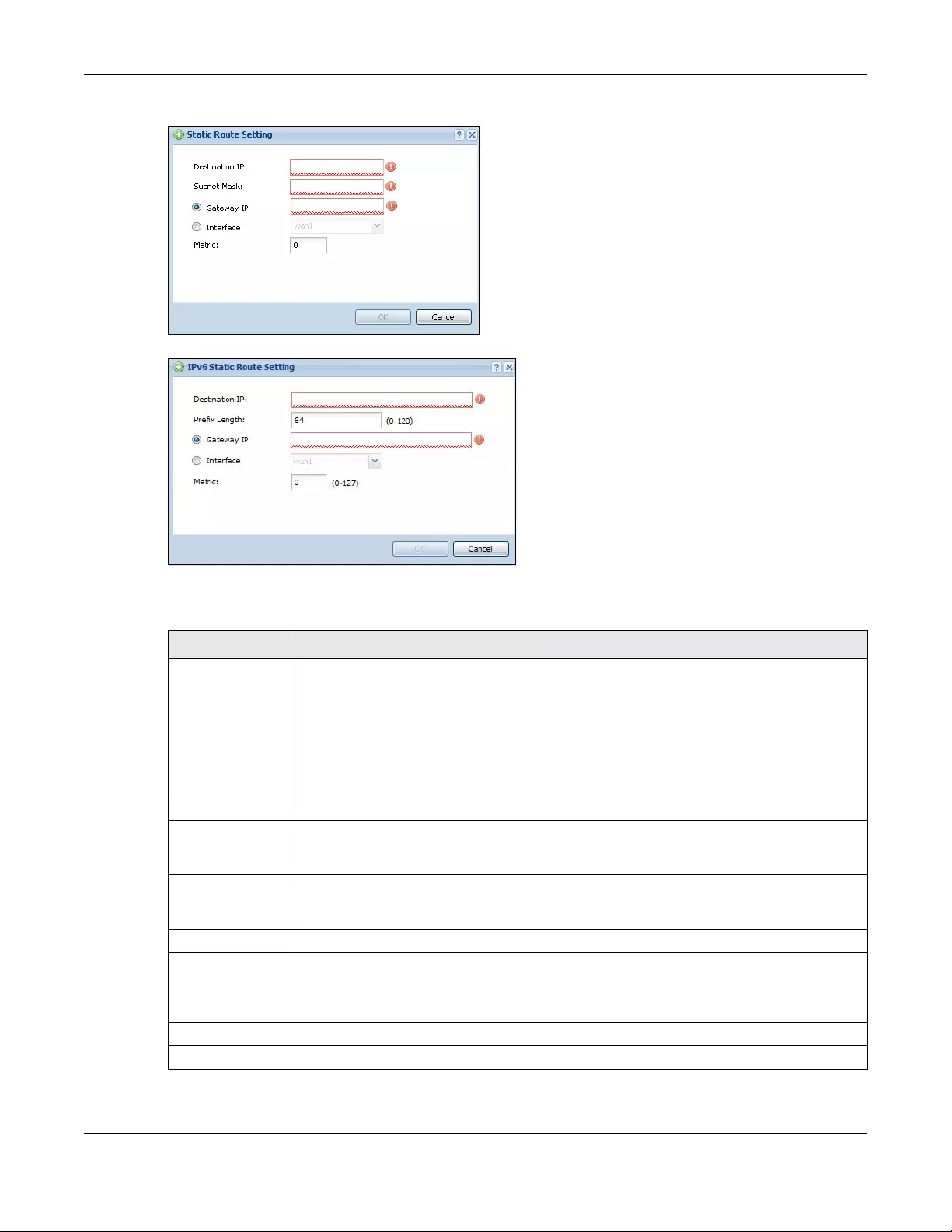
Chapter 11 Routing
USG/ZyWALL User’s Guide
377
Figure 268 Configuration > Network > Routing > Static Route > Add (IPv4 Configuration)
Figure 269 Configuration > Network > Routing > Static Route > Add (IPv6 Configuration)
The following table describes the labels in this screen.
Table 134 Configuration > Network > Routing > Static Route > Add
LABEL DESCRIPTION
Destination IP This parameter specifies the IP network address of the final destination. Routing is always
based on network number.
If you need to specify a route to a single host, enter the specific IP address here and use a
subnet mask of 255.255.255.255 (for IPv4) in the Subnet Mask field or a prefix of 128 (for IPv6) in
the Prefix Length field to force the network number to be identical to the host ID.
For IPv6, if you want to send all traffic to the gateway or interface specified in the Gateway IP
or Interface field, enter :: in this field and 0 in the Prefix Length field.
Subnet Mask Enter the IP subnet mask here.
Prefix Length Enter the number of left-most digits in the destination IP address, which indicates the network
prefix. Enter :: in the Destination IP field and 0 in this field if you want to send all traffic to the
gateway or interface specified in the Gateway IP or Interface field.
Gateway IP Select the radio button and enter the IP address of the next-hop gateway. The gateway is a
router or switch on the same segment as your Zyxel Device's interface(s). The gateway helps
forward packets to their destinations.
Interface Select the radio button and a predefined interface through which the traffic is sent.
Metric Metric represents the “cost” of transmission for routing purposes. IP routing uses hop count as
the measurement of cost, with a minimum of 1 for directly connected networks. Enter a
number that approximates the cost for this link. The number need not be precise, but it must
be 0~127. In practice, 2 or 3 is usually a good number.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.

Chapter 11 Routing
USG/ZyWALL User’s Guide
378
11.4 Policy Routing Technical Reference
Here is more detailed information about some of the features you can configure in policy routing.
NAT and SNAT
NAT (Network Address Translation - NAT, RFC 1631) is the translation of the IP address in a packet in one
network to a different IP address in another network. Use SNAT (Source NAT) to change the source IP
address in one network to a different IP address in another network.
Assured Forwarding (AF) PHB for DiffServ
Assured Forwarding (AF) behavior is defined in RFC 2597. The AF behavior group defines four AF classes.
Inside each class, packets are given a high, medium or low drop precedence. The drop precedence
determines the probability that routers in the network will drop packets when congestion occurs. If
congestion occurs between classes, the traffic in the higher class (smaller numbered class) is generally
given priority. Combining the classes and drop precedence produces the following twelve DSCP
encodings from AF11 through AF43. The decimal equivalent is listed in brackets.
Maximize Bandwidth Usage
The maximize bandwidth usage option allows the Zyxel Device to divide up any available bandwidth on
the interface (including unallocated bandwidth and any allocated bandwidth that a policy route is not
using) among the policy routes that require more bandwidth.
When you enable maximize bandwidth usage, the Zyxel Device first makes sure that each policy route
gets up to its bandwidth allotment. Next, the Zyxel Device divides up an interface’s available bandwidth
(bandwidth that is unbudgeted or unused by the policy routes) depending on how many policy routes
require more bandwidth and on their priority levels. When only one policy route requires more
bandwidth, the Zyxel Device gives the extra bandwidth to that policy route.
When multiple policy routes require more bandwidth, the Zyxel Device gives the highest priority policy
routes the available bandwidth first (as much as they require, if there is enough available bandwidth),
and then to lower priority policy routes if there is still bandwidth available. The Zyxel Device distributes
the available bandwidth equally among policy routes with the same priority level.
11.5 Routing Protocols Overview
Routing protocols give the Zyxel Device routing information about the network from other routers. The
Zyxel Device stores this routing information in the routing table it uses to make routing decisions. In turn,
the Zyxel Device can also use routing protocols to propagate routing information to other routers.
Table 135 Assured Forwarding (AF) Behavior Group
CLASS 1 CLASS 2 CLASS 3 CLASS 4
Low Drop Precedence AF11 (10) AF21 (18) AF31 (26) AF41 (34)
Medium Drop Precedence AF12 (12) AF22 (20) AF32 (28) AF42 (36)
High Drop Precedence AF13 (14) AF23 (22) AF33 (30) AF43 (38)
Chapter 11 Routing
USG/ZyWALL User’s Guide
379
Routing protocols are usually only used in networks using multiple routers like campuses or large
enterprises.
• Use the RIP screen (see Section 11.6 on page 379) to configure the Zyxel Device to use RIP to receive
and/or send routing information.
• Use the OSPF screen (see Section 11.7 on page 381) to configure general OSPF settings and manage
OSPF areas.
• Use the OSPF Area Add/Edit screen (see Section 11.7.2 on page 385) to create or edit an OSPF area.
11.5.1 What You Need to Know
The Zyxel Device supports two standards, RIP and OSPF, for routing protocols. RIP and OSPF are
compared here and discussed further in the rest of the chapter.
Finding Out More
See Section 11.8 on page 388 for background information on routing protocols.
11.6 The RIP Screen
RIP (Routing Information Protocol, RFC 1058 and RFC 1389) allows a device to exchange routing
information with other routers. RIP is a vector-space routing protocol, and, like most such protocols, it
uses hop count to decide which route is the shortest. Unfortunately, it also broadcasts its routes
asynchronously to the network and converges slowly. Therefore, RIP is more suitable for small networks
(up to 15 routers).
• In the Zyxel Device, you can configure two sets of RIP settings before you can use it in an interface.
•First, the Authentication field specifies how to verify that the routing information that is received is the
same routing information that is sent. This is discussed in more detail in Authentication Types on page
388.
• Second, the Zyxel Device can also redistribute routing information from non-RIP networks, specifically
OSPF networks and static routes, to the RIP network. Costs might be calculated differently, however,
so you use the Metric field to specify the cost in RIP terms.
• RIP uses UDP port 520.
Use the RIP screen to specify the authentication method and maintain the policies for redistribution.
Click Configuration > Network > Routing > RIP to open the following screen.
Table 136 RIP vs. OSPF
RIP OSPF
Network Size Small (with up to 15 routers) Large
Metric Hop count Bandwidth, hop count, throughput, round trip time and
reliability.
Convergence Slow Fast
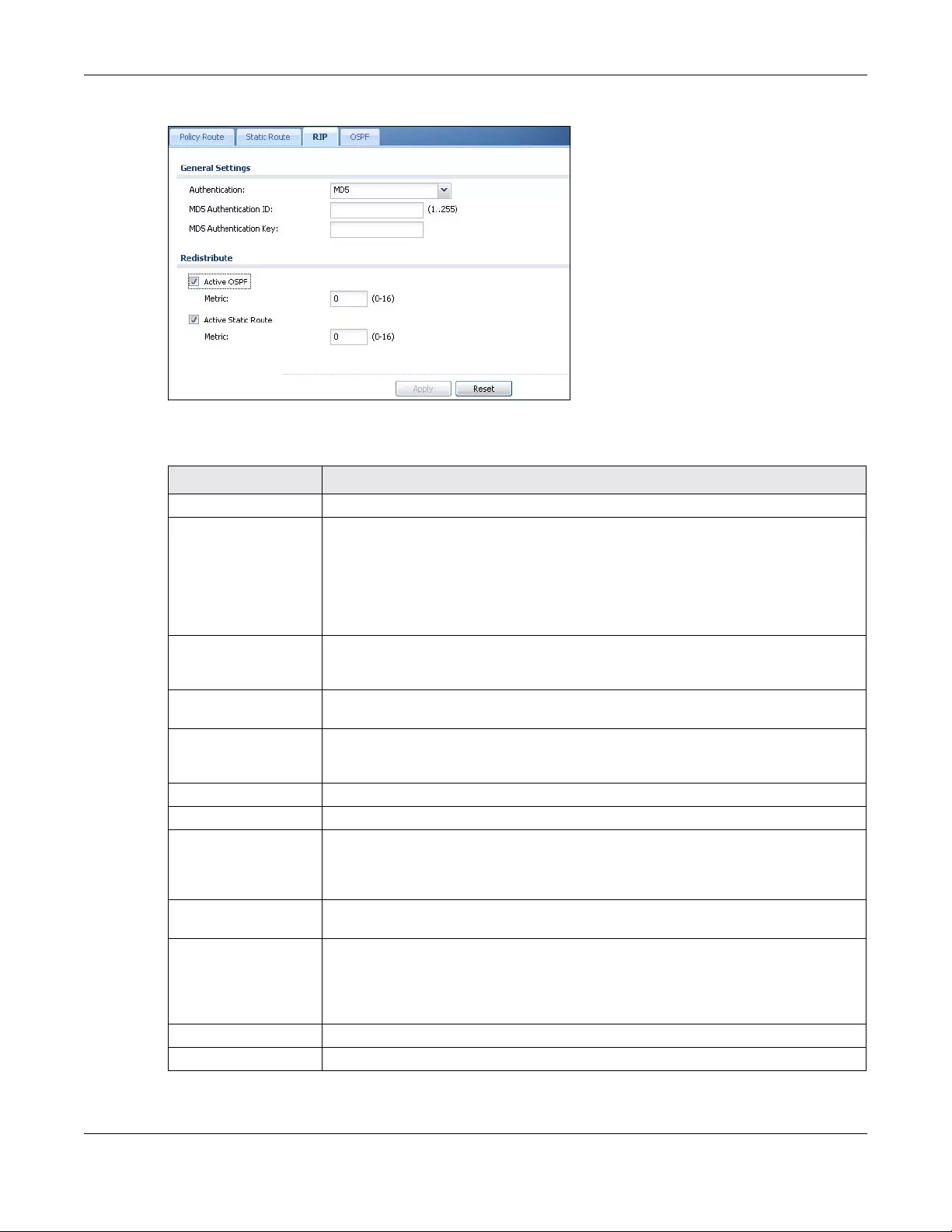
Chapter 11 Routing
USG/ZyWALL User’s Guide
380
Figure 270 Configuration > Network > Routing > RIP
The following table describes the labels in this screen.
Table 137 Configuration > Network > Routing Protocol > RIP
LABEL DESCRIPTION
Authentication
Authentication Select the authentication method used in the RIP network. This authentication protects
the integrity, but not the confidentiality, of routing updates.
None uses no authentication.
Text uses a plain text password that is sent over the network (not very secure).
MD5 uses an MD5 password and authentication ID (most secure).
Text Authentication
Key This field is available if the Authentication is Text. Type the password for text
authentication. The key can consist of alphanumeric characters and the underscore,
and it can be up to 16 characters long.
MD5
Authentication ID This field is available if the Authentication is MD5. Type the ID for MD5 authentication. The
ID can be between 1 and 255.
MD5
Authentication Key This field is available if the Authentication is MD5. Type the password for MD5
authentication. The password can consist of alphanumeric characters and the
underscore, and it can be up to 16 characters long.
Redistribute
Active OSPF Select this to use RIP to advertise routes that were learned through OSPF.
Metric Type the cost for routes provided by OSPF. The metric represents the “cost” of
transmission for routing purposes. RIP routing uses hop count as the measurement of cost,
with 1 usually used for directly connected networks. The number does not have to be
precise, but it must be between 0 and 16. In practice, 2 or 3 is usually used.
Active Static Route Select this to use RIP to advertise routes that were learned through the static route
configuration.
Metric Type the cost for routes provided by the static route configuration. The metric represents
the “cost” of transmission for routing purposes. RIP routing uses hop count as the
measurement of cost, with 1 usually used for directly connected networks. The number
does not have to be precise, but it must be between 0 and 16. In practice, 2 or 3 is
usually used.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.

Chapter 11 Routing
USG/ZyWALL User’s Guide
381
11.7 The OSPF Screen
OSPF (Open Shortest Path First, RFC 2328) is a link-state protocol designed to distribute routing
information within a group of networks, called an Autonomous System (AS). OSPF offers some
advantages over vector-space routing protocols like RIP.
• OSPF supports variable-length subnet masks, which can be set up to use available IP addresses more
efficiently.
• OSPF filters and summarizes routing information, which reduces the size of routing tables throughout
the network.
• OSPF responds to changes in the network, such as the loss of a router, more quickly.
• OSPF considers several factors, including bandwidth, hop count, throughput, round trip time, and
reliability, when it calculates the shortest path.
• OSPF converges more quickly than RIP.
Naturally, OSPF is also more complicated than RIP, so OSPF is usually more suitable for large networks.
OSPF uses IP protocol 89.
OSPF Areas
An OSPF Autonomous System (AS) is divided into one or more areas. Each area represents a group of
adjacent networks and is identified by a 32-bit ID. In OSPF, this number may be expressed as an integer
or as an IP address.
There are several types of areas.
• The backbone is the transit area that routes packets between other areas. All other areas are
connected to the backbone.
• A normal area is a group of adjacent networks. A normal area has routing information about the
OSPF AS, any networks outside the OSPF AS to which it is directly connected, and any networks
outside the OSPF AS that provide routing information to any area in the OSPF AS.
• A stub area has routing information about the OSPF AS. It does not have any routing information
about any networks outside the OSPF AS, including networks to which it is directly connected. It relies
on a default route to send information outside the OSPF AS.
• A Not So Stubby Area (NSSA, RFC 1587) has routing information about the OSPF AS and networks
outside the OSPF AS to which the NSSA is directly connected. It does not have any routing information
about other networks outside the OSPF AS.
Each type of area is illustrated in the following figure.
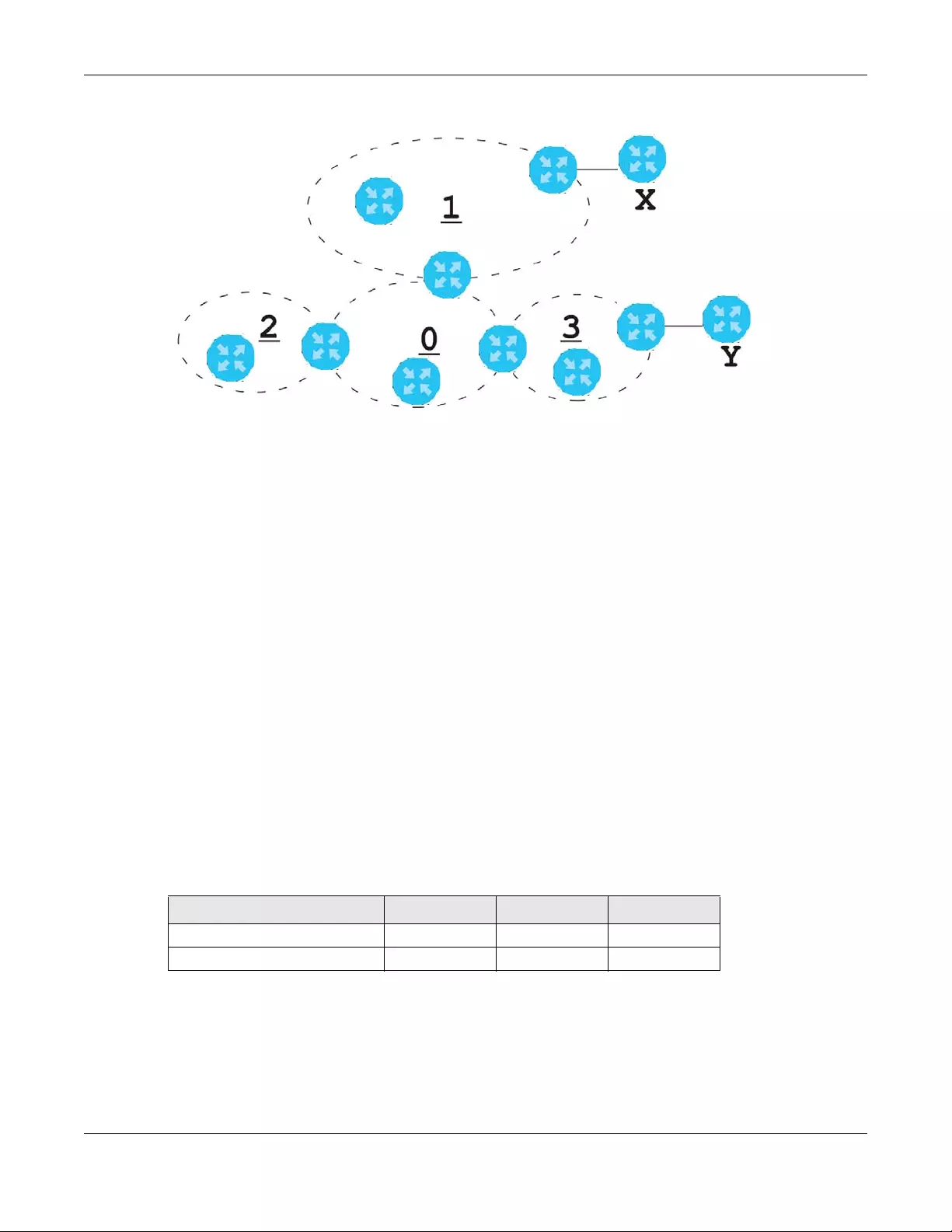
Chapter 11 Routing
USG/ZyWALL User’s Guide
382
Figure 271 OSPF: Types of Areas
This OSPF AS consists of four areas, areas 0-3. Area 0 is always the backbone. In this example, areas 1, 2,
and 3 are all connected to it. Area 1 is a normal area. It has routing information about the OSPF AS and
networks X and Y. Area 2 is a stub area. It has routing information about the OSPF AS, but it depends on
a default route to send information to networks X and Y. Area 3 is a NSSA. It has routing information
about the OSPF AS and network Y but not about network X.
OSPF Routers
Every router in the same area has the same routing information. They do this by exchanging Hello
messages to confirm which neighbor (layer-3) devices exist, and then they exchange database
descriptions (DDs) to create a synchronized link-state database. The link-state database contains
records of router IDs, their associated links and path costs. The link-state database is then constantly
updated through Link State Advertisements (LSA). Each router uses the link state database and the
Dijkstra algorithm to compute the least cost paths to network destinations.
Like areas, each router has a unique 32-bit ID in the OSPF AS, and there are several types of routers.
Each type is really just a different role, and it is possible for one router to play multiple roles at one time.
• An internal router (IR) only exchanges routing information with other routers in the same area.
• An Area Border Router (ABR) connects two or more areas. It is a member of all the areas to which it is
connected, and it filters, summarizes, and exchanges routing information between them.
• An Autonomous System Boundary Router (ASBR) exchanges routing information with routers in
networks outside the OSPF AS. This is called redistribution in OSPF.
• A backbone router (BR) has at least one interface with area 0. By default, every router in area 0 is a
backbone router, and so is every ABR.
Each type of router is illustrated in the following example.
Table 138 OSPF: Redistribution from Other Sources to Each Type of Area
SOURCE \ TYPE OF AREA NORMAL NSSA STUB
Static routes Yes Yes No
RIP Yes Yes Yes
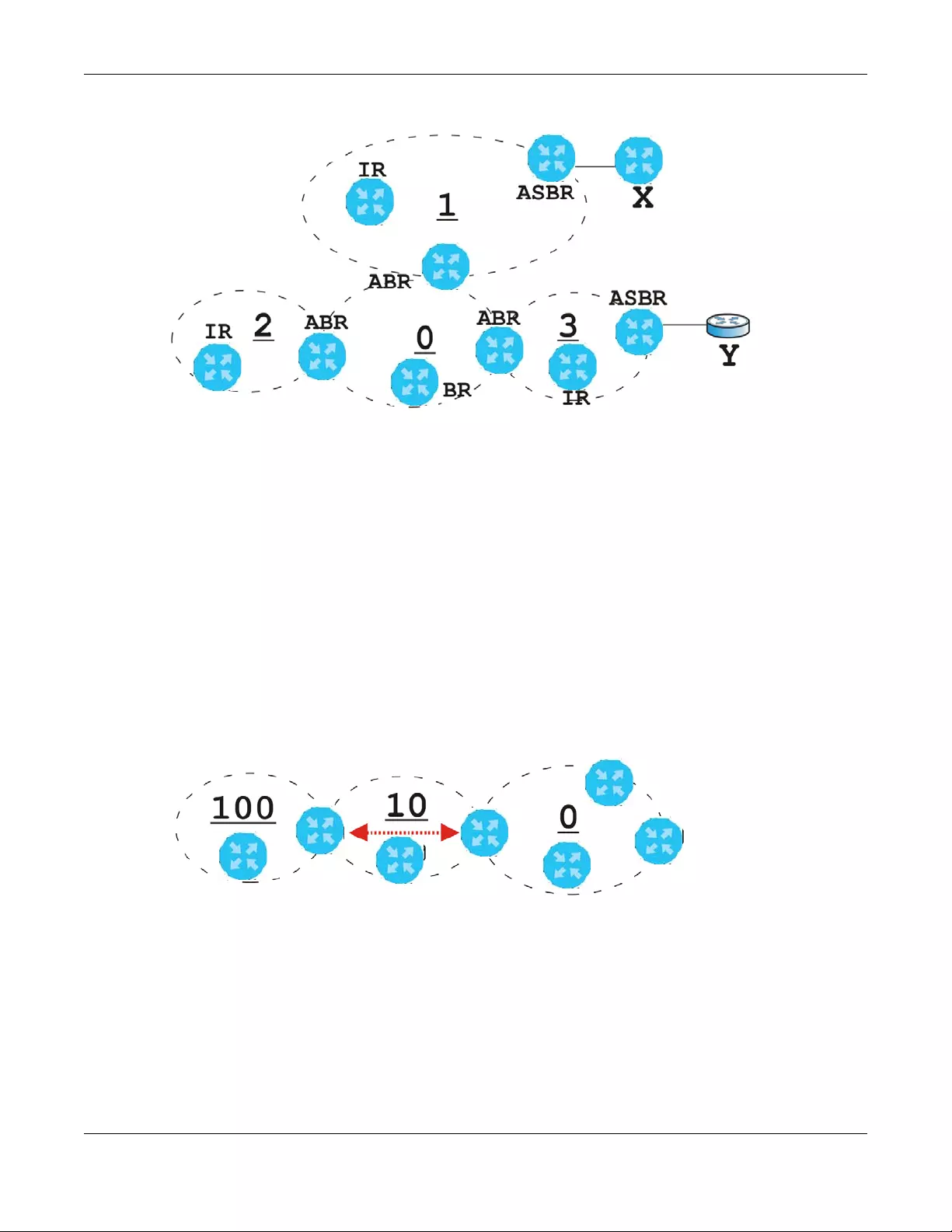
Chapter 11 Routing
USG/ZyWALL User’s Guide
383
Figure 272 OSPF: Types of Routers
In order to reduce the amount of traffic between routers, a group of routers that are directly connected
to each other selects a designated router (DR) and a backup designated router (BDR). All of the routers
only exchange information with the DR and the BDR, instead of exchanging information with all of the
other routers in the group. The DR and BDR are selected by priority; if two routers have the same priority,
the highest router ID is used.
The DR and BDR are selected in each group of routers that are directly connected to each other. If a
router is directly connected to several groups, it might be a DR in one group, a BDR in another group,
and neither in a third group all at the same time.
Virtual Links
In some OSPF AS, it is not possible for an area to be directly connected to the backbone. In this case,
you can create a virtual link through an intermediate area to logically connect the area to the
backbone. This is illustrated in the following example.
Figure 273 OSPF: Virtual Link
In this example, area 100 does not have a direct connection to the backbone. As a result, you should
set up a virtual link on both ABR in area 10. The virtual link becomes the connection between area 100
and the backbone.
You cannot create a virtual link to a router in a different area.
OSPF Configuration
Follow these steps when you configure OSPF on the Zyxel Device.
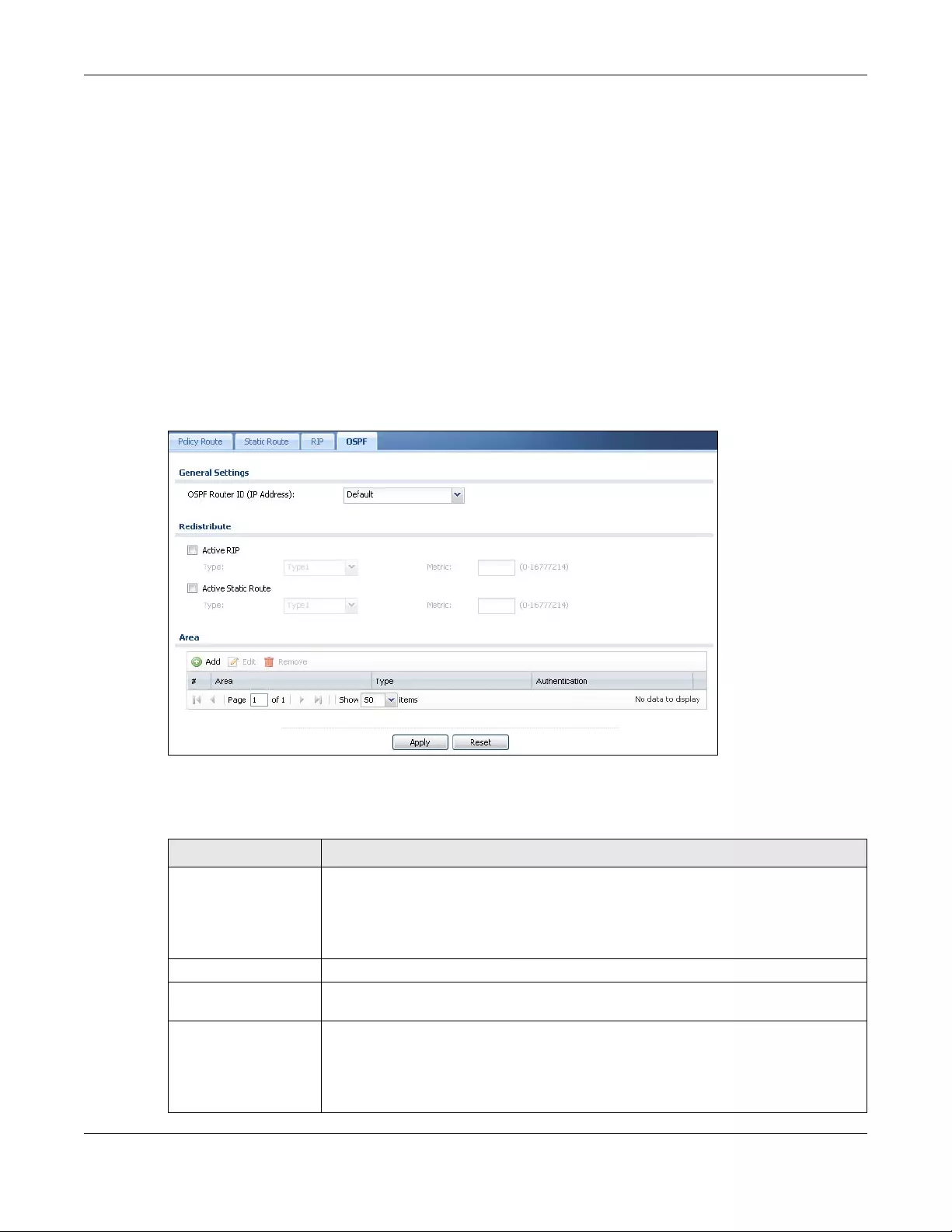
Chapter 11 Routing
USG/ZyWALL User’s Guide
384
1Enable OSPF.
2Set up the OSPF areas.
3Configure the appropriate interfaces. See Section 10.4.1 on page 278.
4Set up virtual links, as needed.
11.7.1 Configuring the OSPF Screen
Use the first OSPF screen to specify the OSPF router the Zyxel Device uses in the OSPF AS and maintain
the policies for redistribution. In addition, it provides a summary of OSPF areas, allows you to remove
them, and opens the OSPF Add/Edit screen to add or edit them.
Click Configuration > Network > Routing > OSPF to open the following screen.
Figure 274 Configuration > Network > Routing > OSPF
The following table describes the labels in this screen. See Section 11.7.2 on page 385 for more
information as well.
Table 139 Configuration > Network > Routing Protocol > OSPF
LABEL DESCRIPTION
OSPF Router ID Select the 32-bit ID the Zyxel Device uses in the OSPF AS.
Default - the first available interface IP address is the Zyxel Device’s ID.
User Defined - enter the ID (in IP address format) in the field that appears when you select
User Define.
Redistribute
Active RIP Select this to advertise routes that were learned from RIP. The Zyxel Device advertises
routes learned from RIP to Normal and NSSA areas but not to Stub areas.
Type Select how OSPF calculates the cost associated with routing information from RIP.
Choices are: Type 1 and Type 2.
Type 1 - cost = OSPF AS cost + external cost (Metric)
Type 2 - cost = external cost (Metric); the OSPF AS cost is ignored.
Chapter 11 Routing
USG/ZyWALL User’s Guide
385
11.7.2 OSPF Area Add/Edit Screen
The OSPF Area Add/Edit screen allows you to create a new area or edit an existing one. To access this
screen, go to the OSPF summary screen (see Section 11.7 on page 381), and click either the Add icon or
an Edit icon.
Metric Type the external cost for routes provided by RIP. The metric represents the “cost” of
transmission for routing purposes. The way this is used depends on the Type field. This
value is usually the average cost in the OSPF AS, and it can be between 1 and 16777214.
Active Static Route Select this to advertise routes that were learned from static routes. The Zyxel Device
advertises routes learned from static routes to all types of areas.
Type Select how OSPF calculates the cost associated with routing information from static
routes. Choices are: Type 1 and Type 2.
Type 1 - cost = OSPF AS cost + external cost (Metric)
Type 2 - cost = external cost (Metric); the OSPF AS cost is ignored.
Metric Type the external cost for routes provided by static routes. The metric represents the
“cost” of transmission for routing purposes. The way this is used depends on the Type field.
This value is usually the average cost in the OSPF AS, and it can be between 1 and
16777214.
Area This section displays information about OSPF areas in the Zyxel Device.
Add Click this to create a new OSPF area.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify
the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so.
# This field is a sequential value, and it is not associated with a specific area.
Area This field displays the 32-bit ID for each area in IP address format.
Type This field displays the type of area. This type is different from the Type field above.
Authentication This field displays the default authentication method in the area.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
Table 139 Configuration > Network > Routing Protocol > OSPF (continued)
LABEL DESCRIPTION
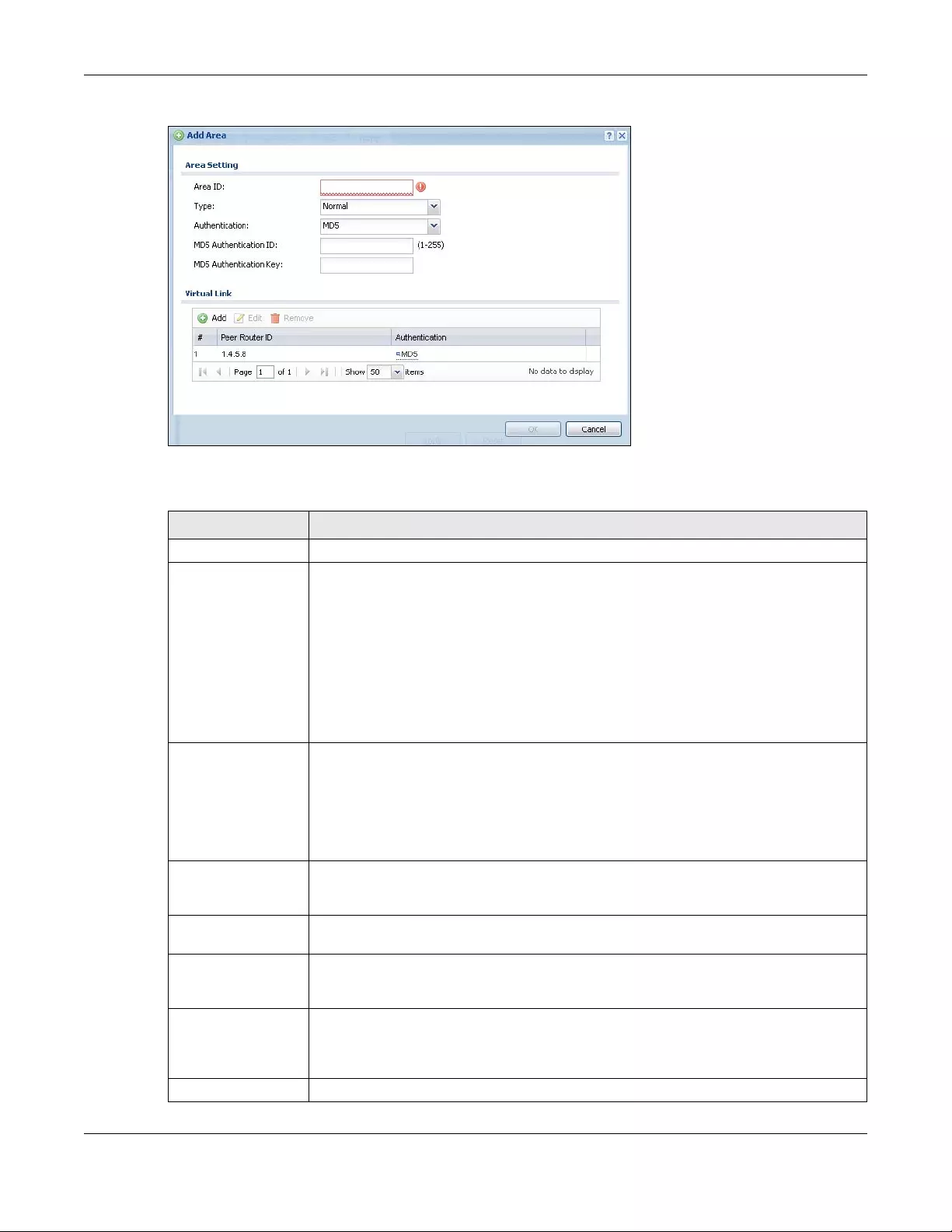
Chapter 11 Routing
USG/ZyWALL User’s Guide
386
Figure 275 Configuration > Network > Routing > OSPF > Add
The following table describes the labels in this screen.
Table 140 Configuration > Network > Routing > OSPF > Add
LABEL DESCRIPTION
Area ID Type the unique, 32-bit identifier for the area in IP address format.
Type Select the type of OSPF area.
Normal - This area is a normal area. It has routing information about the OSPF AS and about
networks outside the OSPF AS.
Stub - This area is an stub area. It has routing information about the OSPF AS but not about
networks outside the OSPF AS. It depends on a default route to send information outside
the OSPF AS.
NSSA - This area is a Not So Stubby Area (NSSA), per RFC 1587. It has routing information
about the OSPF AS and networks that are outside the OSPF AS and are directly connected
to the NSSA. It does not have information about other networks outside the OSPF AS.
Authentication Select the default authentication method used in the area. This authentication protects the
integrity, but not the confidentiality, of routing updates.
None uses no authentication.
Text uses a plain text password that is sent over the network (not very secure).
MD5 uses an MD5 password and authentication ID (most secure).
Text Authentication
Key
This field is available if the Authentication is Text. Type the password for text authentication.
The key can consist of alphanumeric characters and the underscore, and it can be up to
16 characters long.
MD5 Authentication
ID
This field is available if the Authentication is MD5. Type the default ID for MD5 authentication
in the area. The ID can be between 1 and 255.
MD5 Authentication
Key
This field is available if the Authentication is MD5. Type the default password for MD5
authentication in the area. The password can consist of alphanumeric characters and the
underscore, and it can be up to 16 characters long.
Virtual Link This section is displayed if the Type is Normal. Create a virtual link if you want to connect a
different area (that does not have a direct connection to the backbone) to the backbone.
You should set up the virtual link on the ABR that is connected to the other area and on the
ABR that is connected to the backbone.
Add Click this to create a new virtual link.
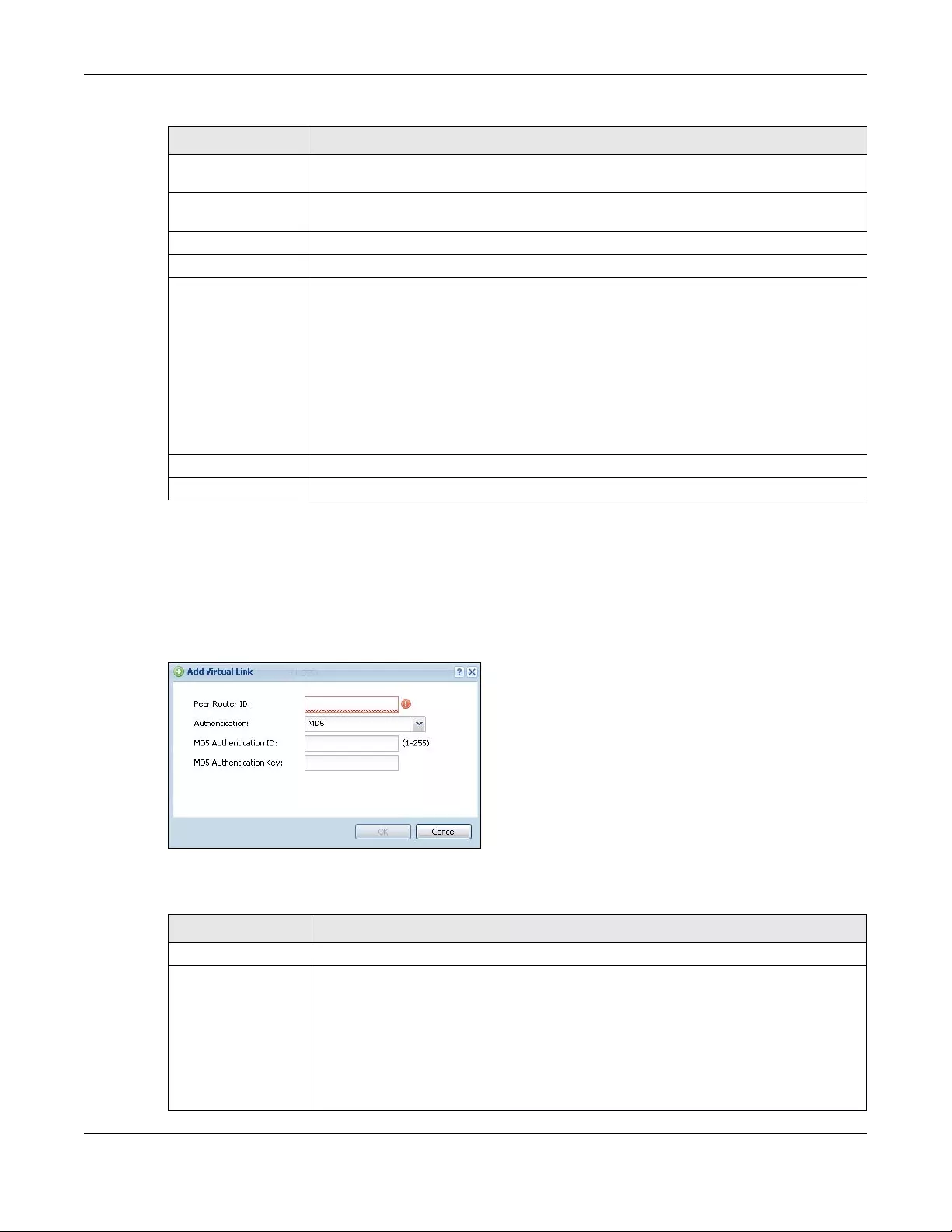
Chapter 11 Routing
USG/ZyWALL User’s Guide
387
11.7.3 Virtual Link Add/Edit Screen
The Virtual Link Add/Edit screen allows you to create a new virtual link or edit an existing one. When the
OSPF add or edit screen (see Section 11.7.2 on page 385) has the Type set to Normal, a Virtual Link table
displays. Click either the Add icon or an entry and the Edit icon to display a screen like the following.
Figure 276 Configuration > Network > Routing > OSPF > Add > Add
The following table describes the labels in this screen.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so.
# This field is a sequential value, and it is not associated with a specific area.
Peer Router ID This is the 32-bit ID (in IP address format) of the other ABR in the virtual link.
Authentication This is the authentication method the virtual link uses. This authentication protects the
integrity, but not the confidentiality, of routing updates.
None uses no authentication.
Text uses a plain text password that is sent over the network (not very secure). Hover your
cursor over this label to display the password.
MD5 uses an MD5 password and authentication ID (most secure). Hover your cursor over
this label to display the authentication ID and key.
Same as Area has the virtual link also use the Authentication settings above.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 140 Configuration > Network > Routing > OSPF > Add (continued)
LABEL DESCRIPTION
Table 141 Configuration > Network > Routing > OSPF > Add > Add
LABEL DESCRIPTION
Peer Router ID Enter the 32-bit ID (in IP address format) of the other ABR in the virtual link.
Authentication Select the authentication method the virtual link uses. This authentication protects the
integrity, but not the confidentiality, of routing updates.
None uses no authentication.
Text uses a plain text password that is sent over the network (not very secure).
MD5 uses an MD5 password and authentication ID (most secure).
Same as Area has the virtual link also use the Authentication settings above.
Chapter 11 Routing
USG/ZyWALL User’s Guide
388
11.8 Routing Protocol Technical Reference
Here is more detailed information about RIP and OSPF.
Authentication Types
Authentication is used to guarantee the integrity, but not the confidentiality, of routing updates. The
transmitting router uses its key to encrypt the original message into a smaller message, and the smaller
message is transmitted with the original message. The receiving router uses its key to encrypt the
received message and then verifies that it matches the smaller message sent with it. If the received
message is verified, then the receiving router accepts the updated routing information. The transmitting
and receiving routers must have the same key.
The Zyxel Device supports three types of authentication for RIP and OSPF routing protocols:
•None - no authentication is used.
•Text – authentication using a plain text password, and the (unencrypted) password is sent over the
network. This method is usually used temporarily to prevent network problems.
•MD5 – authentication using an MD5 password and authentication ID.
MD5 is an authentication method that produces a 128-bit checksum, called a message-digest, for each
packet. It also includes an authentication ID, which can be set to any value between 1 and 255. The
Zyxel Device only accepts packets if these conditions are satisfied.
• The packet’s authentication ID is the same as the authentication ID of the interface that received it.
• The packet’s message-digest is the same as the one the Zyxel Device calculates using the MD5
password.
For RIP, authentication is not available in RIP version 1. In RIP version 2, you can only select one
authentication type for all interfaces. For OSPF, the Zyxel Device supports a default authentication type
by area. If you want to use this default in an interface or virtual link, you set the associated
Authentication Type field to Same as Area. As a result, you only have to update the authentication
information for the area to update the authentication type used by these interfaces and virtual links.
Alternatively, you can override the default in any interface or virtual link by selecting a specific
authentication method. Please see the respective interface sections for more information.
Text Authentication
Key
This field is available if the Authentication is Text. Type the password for text authentication.
The key can consist of alphanumeric characters and the underscore, and it can be up to
16 characters long.
MD5 Authentication
ID
This field is available if the Authentication is MD5. Type the default ID for MD5
authentication in the area. The ID can be between 1 and 255.
MD5 Authentication
Key
This field is available if the Authentication is MD5. Type the default password for MD5
authentication in the area. The password can consist of alphanumeric characters and the
underscore, and it can be up to 16 characters long.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 141 Configuration > Network > Routing > OSPF > Add > Add (continued)
LABEL DESCRIPTION
USG/ZyWALL User’s Guide
389
CHAPTER 12
DDNS
12.1 DDNS Overview
Dynamic DNS (DDNS) services let you use a domain name with a dynamic IP address.
12.1.1 What You Can Do in this Chapter
• Use the DDNS screen (see Section 12.2 on page 390) to view a list of the configured DDNS domain
names and their details.
• Use the DDNS Add/Edit screen (see Section 12.2.1 on page 391) to add a domain name to the Zyxel
Device or to edit the configuration of an existing domain name.
12.1.2 What You Need to Know
DNS maps a domain name to a corresponding IP address and vice versa. Similarly, Dynamic DNS (DDNS)
maps a domain name to a dynamic IP address. As a result, anyone can use the domain name to
contact you (in NetMeeting, CU-SeeMe, etc.) or to access your FTP server or Web site, regardless of the
current (dynamic) IP address.
Note: You must have a public WAN IP address to use Dynamic DNS.
You must set up a dynamic DNS account with a supported DNS service provider before you can use
Dynamic DNS services with the Zyxel Device. When registration is complete, the DNS service provider
gives you a password or key. At the time of writing, the Zyxel Device supports the following DNS service
providers. See the listed websites for details about the DNS services offered by each.
Note: Record your DDNS account’s user name, password, and domain name to use to
configure the Zyxel Device.
After you configure the Zyxel Device, it automatically sends updated IP addresses to the DDNS service
provider, which helps redirect traffic accordingly.
Table 142 DDNS Service Providers
PROVIDER SERVICE TYPES SUPPORTED WEBSITE
DynDNS Dynamic DNS, Static DNS, and Custom DNS www.dyndns.com
Dynu Basic, Premium www.dynu.com
No-IP No-IP www.no-ip.com
Peanut Hull Peanut Hull www.oray.cn
3322 3322 Dynamic DNS, 3322 Static DNS www.3322.org
Selfhost Selfhost selfhost.de
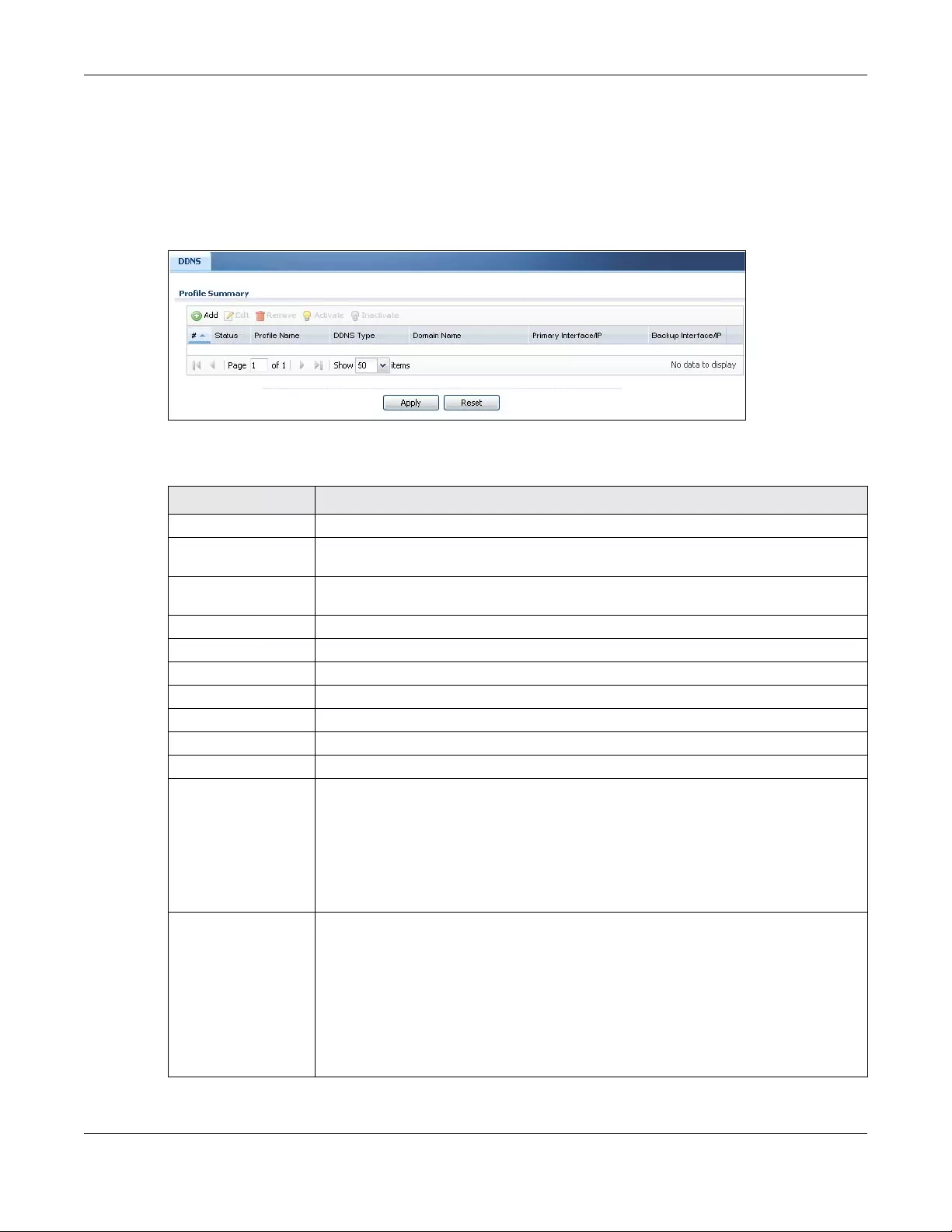
Chapter 12 DDNS
USG/ZyWALL User’s Guide
390
12.2 The DDNS Screen
The DDNS screen provides a summary of all DDNS domain names and their configuration. In addition,
this screen allows you to add new domain names, edit the configuration for existing domain names, and
delete domain names. Click Configuration > Network > DDNS to open the following screen.
Figure 277 Configuration > Network > DDNS
The following table describes the labels in this screen.
Table 143 Configuration > Network > DDNS
LABEL DESCRIPTION
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify
the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
#This is the number of an individual DDNS profile.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
Profile Name This field displays the descriptive profile name for this entry.
DDNS Type This field displays which DDNS service you are using.
Domain Name This field displays each domain name the Zyxel Device can route.
Primary Interface/IP This field displays the interface to use for updating the IP address mapped to the domain
name followed by how the Zyxel Device determines the IP address for the domain name.
from interface - The IP address comes from the specified interface.
auto detected -The DDNS server checks the source IP address of the packets from the
Zyxel Device for the IP address to use for the domain name.
custom - The IP address is static.
Backup Interface/IP This field displays the alternate interface to use for updating the IP address mapped to the
domain name followed by how the Zyxel Device determines the IP address for the domain
name. The Zyxel Device uses the backup interface and IP address when the primary
interface is disabled, its link is down or its connectivity check fails.
from interface - The IP address comes from the specified interface.
auto detected -The DDNS server checks the source IP address of the packets from the
Zyxel Device for the IP address to use for the domain name.
custom - The IP address is static.
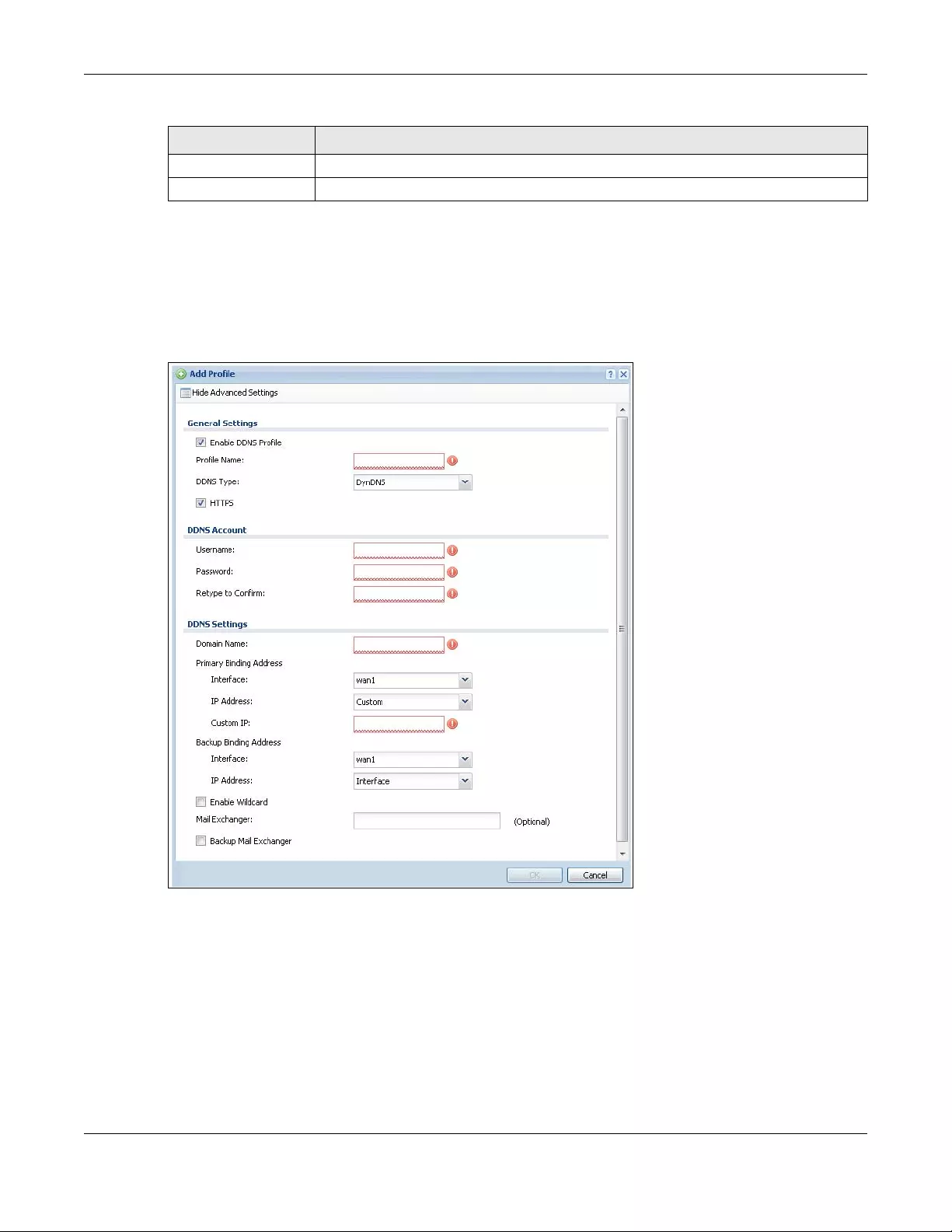
Chapter 12 DDNS
USG/ZyWALL User’s Guide
391
12.2.1 The Dynamic DNS Add/Edit Screen
The DDNS Add/Edit screen allows you to add a domain name to the Zyxel Device or to edit the
configuration of an existing domain name. Click Configuration > Network > DDNS and then an Add or
Edit icon to open this screen.
Figure 278 Configuration > Network > DDNS > Add
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
Table 143 Configuration > Network > DDNS (continued)
LABEL DESCRIPTION
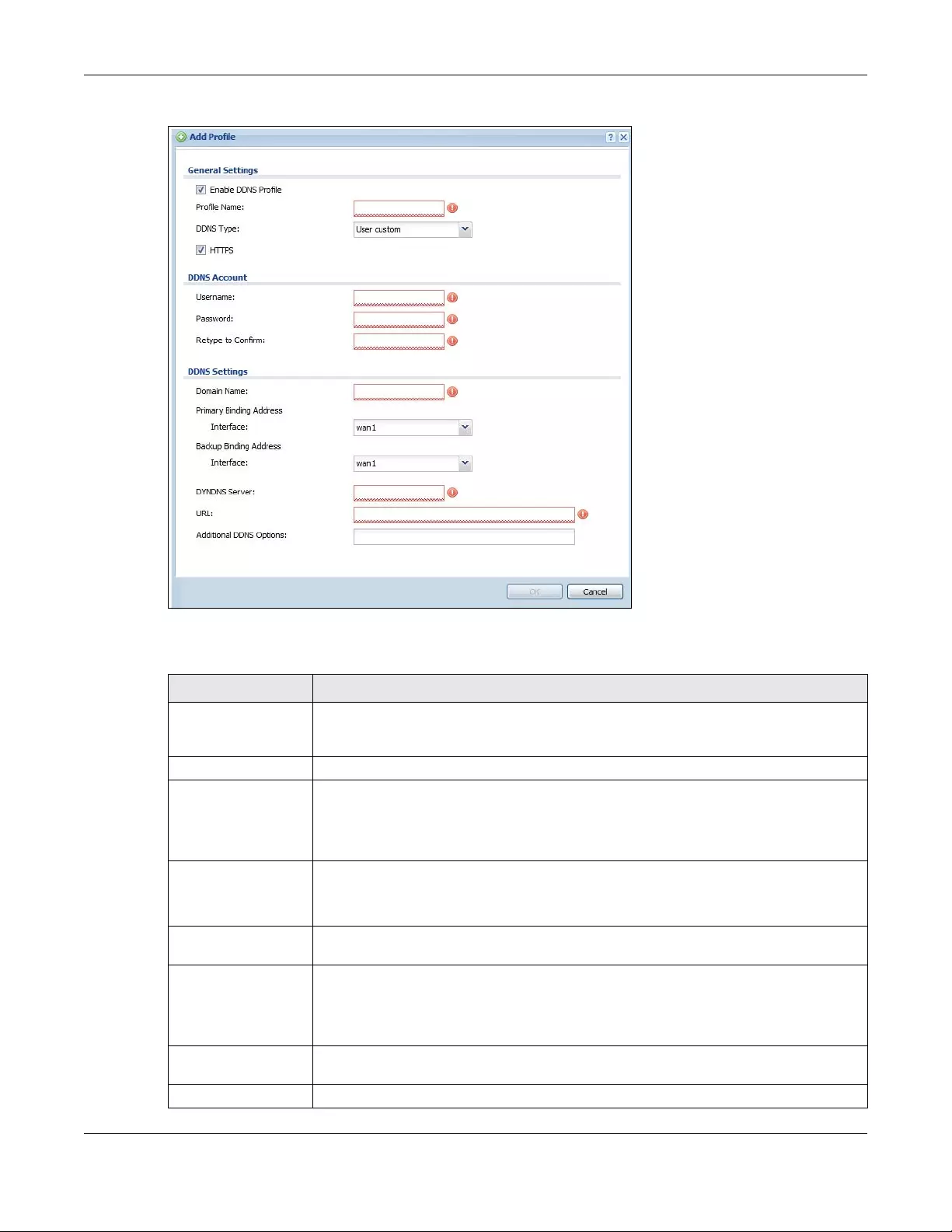
Chapter 12 DDNS
USG/ZyWALL User’s Guide
392
Figure 279 Configuration > Network > DDNS > Add - Custom
The following table describes the labels in this screen.
Table 144 Configuration > Network > DDNS > Add
LABEL DESCRIPTION
Show Advanced
Settings / Hide
Advanced Settings
Click this button to display a greater or lesser number of configuration fields.
Enable DDNS Profile Select this check box to use this DDNS entry.
Profile Name When you are adding a DDNS entry, type a descriptive name for this DDNS entry in the
Zyxel Device. You may use 1-31 alphanumeric characters, underscores(_), or dashes (-),
but the first character cannot be a number. This value is case-sensitive.
This field is read-only when you are editing an entry.
DDNS Type Select the type of DDNS service you are using.
Select User custom to create your own DDNS service and configure the DYNDNS Server,
URL, and Additional DDNS Options fields below.
HTTPS Select this to encrypt traffic using SSL (port 443), including traffic with username and
password, to the DDNS server. Not all DDNS providers support this option.
Username Type the user name used when you registered your domain name. You can use up to 31
alphanumeric characters and the underscore. Spaces are not allowed.
For a Dynu DDNS entry, this user name is the one you use for logging into the service, not
the name recorded in your personal information in the Dynu website.
Password Type the password provided by the DDNS provider. You can use up to 64 alphanumeric
characters and the underscore. Spaces are not allowed.
Retype to Confirm Type the password again to confirm it.
Chapter 12 DDNS
USG/ZyWALL User’s Guide
393
DDNS Settings
Domain name Type the domain name you registered. You can use up to 255 characters.
Primary Binding
Address
Use these fields to set how the Zyxel Device determines the IP address that is mapped to
your domain name in the DDNS server. The Zyxel Device uses the Backup Binding Address if
the interface specified by these settings is not available.
Interface Select the interface to use for updating the IP address mapped to the domain name.
Select Any to let the domain name be used with any interface.
IP Address The options available in this field vary by DDNS provider.
Interface -The Zyxel Device uses the IP address of the specified interface. This option
appears when you select a specific interface in the Primary Binding Address Interface
field.
Auto - If the interface has a dynamic IP address, the DDNS server checks the source IP
address of the packets from the Zyxel Device for the IP address to use for the domain
name. You may want to use this if there are one or more NAT routers between the Zyxel
Device and the DDNS server.
Note: The Zyxel Device may not determine the proper IP address if there is an
HTTP proxy server between the Zyxel Device and the DDNS server.
Custom - If you have a static IP address, you can select this to use it for the domain name.
The Zyxel Device still sends the static IP address to the DDNS server.
Custom IP This field is only available when the IP Address is Custom. Type the IP address to use for the
domain name.
Backup Binding
Address
Use these fields to set an alternate interface to map the domain name to when the
interface specified by the Primary Binding Interface settings is not available.
Interface Select the interface to use for updating the IP address mapped to the domain name.
Select Any to let the domain name be used with any interface. Select None to not use a
backup address.
IP Address The options available in this field vary by DDNS provider.
Interface -The Zyxel Device uses the IP address of the specified interface. This option
appears when you select a specific interface in the Backup Binding Address Interface
field.
Auto -The DDNS server checks the source IP address of the packets from the Zyxel Device
for the IP address to use for the domain name. You may want to use this if there are one or
more NAT routers between the Zyxel Device and the DDNS server.
Note: The Zyxel Device may not determine the proper IP address if there is an
HTTP proxy server between the Zyxel Device and the DDNS server.
Custom - If you have a static IP address, you can select this to use it for the domain name.
The Zyxel Device still sends the static IP address to the DDNS server.
Custom IP This field is only available when the IP Address is Custom. Type the IP address to use for the
domain name.
Enable Wildcard This option is only available with a DynDNS account.
Enable the wildcard feature to alias subdomains to be aliased to the same IP address as
your (dynamic) domain name. This feature is useful if you want to be able to use, for
example, www.yourhost.dyndns.org and still reach your hostname.
Table 144 Configuration > Network > DDNS > Add (continued)
LABEL DESCRIPTION
Chapter 12 DDNS
USG/ZyWALL User’s Guide
394
Mail Exchanger This option is only available with a DynDNS account.
DynDNS can route e-mail for your domain name to a mail server (called a mail
exchanger). For example, DynDNS routes e-mail for john-doe@yourhost.dyndns.org to the
host record specified as the mail exchanger.
If you are using this service, type the host record of your mail server here. Otherwise leave
the field blank.
See www.dyndns.org for more information about mail exchangers.
Backup Mail
Exchanger
This option is only available with a DynDNS account.
Select this check box if you are using DynDNS’s backup service for e-mail. With this service,
DynDNS holds onto your e-mail if your mail server is not available. Once your mail server is
available again, the DynDNS server delivers the mail to you. See www.dyndns.org for more
information about this service.
DYNDNS Server This field displays when you select User custom from the DDNS Type field above. Type the IP
address of the server that will host the DDSN service.
URL This field displays when you select User custom from the DDNS Type field above. Type the
URL that can be used to access the server that will host the DDSN service.
Additional DDNS
Options
This field displays when you select User custom from the DDNS Type field above. These are
the options supported at the time of writing:
• dyndns_system to specify the DYNDNS Server type - for example, dyndns@dyndns.org
• ip_server_name which should be the URL to get the server’s public IP address - for
example, http://myip.easylife.tw/
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 144 Configuration > Network > DDNS > Add (continued)
LABEL DESCRIPTION
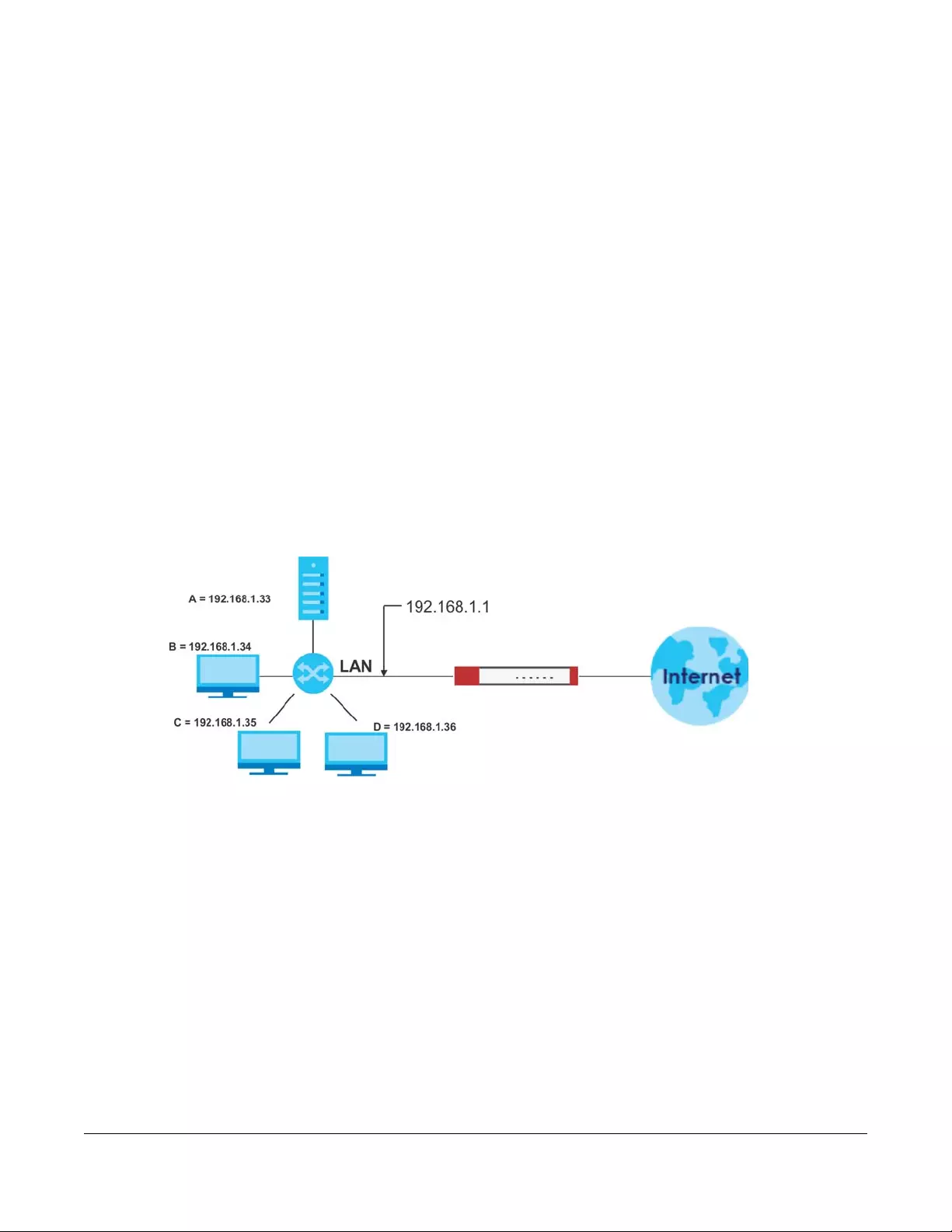
USG/ZyWALL User’s Guide
395
CHAPTER 13
NAT
13.1 NAT Overview
NAT (Network Address Translation - NAT, RFC 1631) is the translation of the IP address of a host in a
packet. For example, the source address of an outgoing packet, used within one network is changed to
a different IP address known within another network. Use Network Address Translation (NAT) to make
computers on a private network behind the Zyxel Device available outside the private network. If the
Zyxel Device has only one public IP address, you can make the computers in the private network
available by using ports to forward packets to the appropriate private IP address.
Suppose you want to assign ports 21-25 to one FTP, Telnet and SMTP server (A in the example), port 80 to
another (B in the example) and assign a default server IP address of 192.168.1.35 to a third (C in the
example). You assign the LAN IP addresses and the ISP assigns the WAN IP address. The NAT network
appears as a single host on the Internet.
Figure 280 Multiple Servers Behind NAT Example
13.1.1 What You Can Do in this Chapter
Use the NAT screens (see Section 13.2 on page 395) to view and manage the list of NAT rules and see
their configuration details. You can also create new NAT rules and edit or delete existing ones.
13.1.2 What You Need to Know
NAT is also known as virtual server, port forwarding, or port translation.
13.2 The NAT Screen
The NAT summary screen provides a summary of all NAT rules and their configuration. In addition, this
screen allows you to create new NAT rules and edit and delete existing NAT rules. To access this screen,
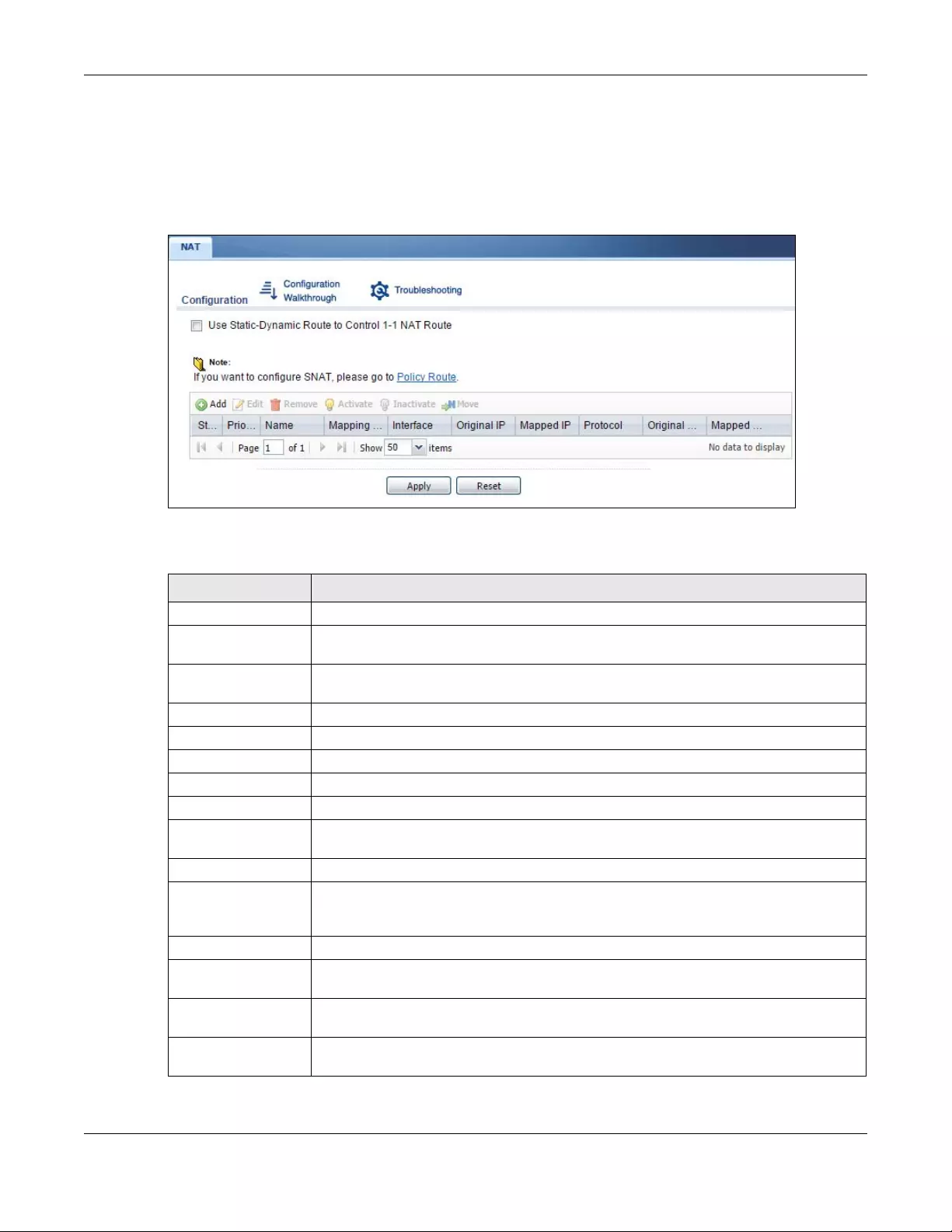
Chapter 13 NAT
USG/ZyWALL User’s Guide
396
login to the Web Configurator and click Configuration > Network > NAT. The following screen appears,
providing a summary of the existing NAT rules.
Click on the icons to go to the OneSecurity.com website where there is guidance on configuration
walkthroughs, troubleshooting, and other information.
Figure 281 Configuration > Network > NAT
The following table describes the labels in this screen.
Table 145 Configuration > Network > NAT
LABEL DESCRIPTION
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
# This field is a sequential value, and it is not associated with a specific entry.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
Name This field displays the name of the entry.
Mapping Type This field displays what kind of NAT this entry performs: Virtual Server, 1:1 NAT, or Many 1:1
NAT.
Interface This field displays the interface on which packets for the NAT entry are received.
Original IP This field displays the original destination IP address (or address object) of traffic that
matches this NAT entry. It displays any if there is no restriction on the original destination IP
address.
Mapped IP This field displays the new destination IP address for the packet.
Protocol This field displays the service used by the packets for this NAT entry. It displays any if there is
no restriction on the services.
Original Port This field displays the original destination port(s) of packets for the NAT entry. This field is
blank if there is no restriction on the original destination port.
Mapped Port This field displays the new destination port(s) for the packet. This field is blank if there is no
restriction on the original destination port.
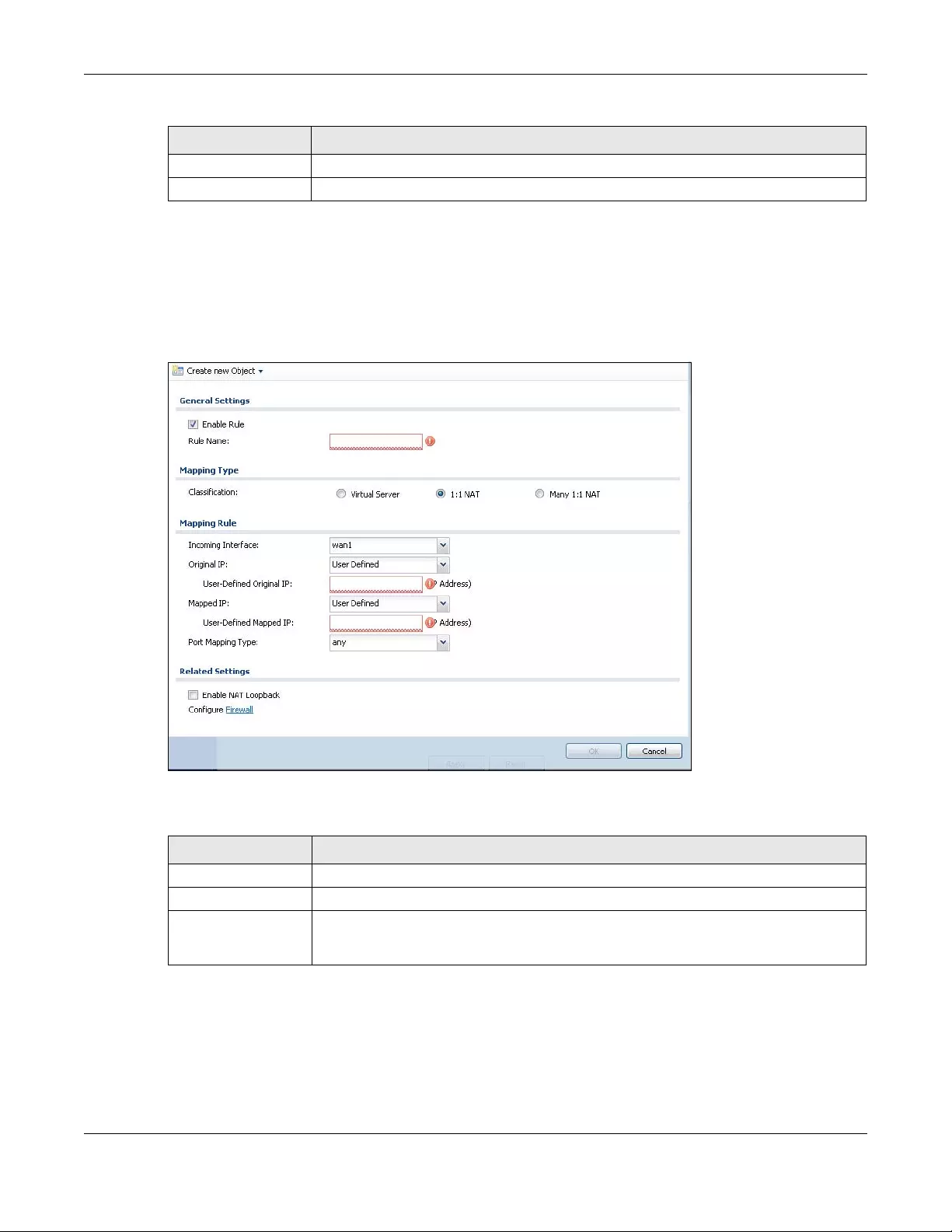
Chapter 13 NAT
USG/ZyWALL User’s Guide
397
13.2.1 The NAT Add/Edit Screen
The NAT Add/Edit screen lets you create new NAT rules and edit existing ones. To open this window,
open the NAT summary screen. (See Section 13.2 on page 395.) Then, click on an Add icon or Edit icon
to open the following screen.
Figure 282 Configuration > Network > NAT > Add
The following table describes the labels in this screen.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
Table 145 Configuration > Network > NAT (continued)
LABEL DESCRIPTION
Table 146 Configuration > Network > NAT > Add
LABEL DESCRIPTION
Create new Object Use to configure any new settings objects that you need to use in this screen.
Enable Rule Use this option to turn the NAT rule on or off.
Rule Name Type in the name of the NAT rule. The name is used to refer to the NAT rule. You may use 1-
31 alphanumeric characters, underscores(_), or dashes (-), but the first character cannot
be a number. This value is case-sensitive.
Chapter 13 NAT
USG/ZyWALL User’s Guide
398
Classification Select what kind of NAT this rule is to perform.
Virtual Server - This makes computers on a private network behind the Zyxel Device
available to a public network outside the Zyxel Device (like the Internet).
1:1 NAT - If the private network server will initiate sessions to the outside clients, select this to
have the Zyxel Device translate the source IP address of the server’s outgoing traffic to the
same public IP address that the outside clients use to access the server.
Many 1:1 NAT - If you have a range of private network servers that will initiate sessions to
the outside clients and a range of public IP addresses, select this to have the Zyxel Device
translate the source IP address of each server’s outgoing traffic to the same one of the
public IP addresses that the outside clients use to access the server. The private and public
ranges must have the same number of IP addresses.
One many 1:1 NAT rule works like multiple 1:1 NAT rules, but it eases configuration effort
since you only create one rule.
Incoming Interface Select the interface on which packets for the NAT rule must be received. It can be an
Ethernet, VLAN, bridge, or PPPoE/PPTP interface.
Original IP Specify the destination IP address of the packets received by this NAT rule’s specified
incoming interface.
any - Select this to use all of the incoming interface’s IP addresses including dynamic
addresses or those of any virtual interfaces built upon the selected incoming interface.
User Defined - Select this to manually enter an IP address in the User Defined field. For
example, you could enter a static public IP assigned by the ISP without having to create a
virtual interface for it.
Host address - select a host address object to use the IP address it specifies. The list also
includes address objects based on interface IPs. So for example you could select an
address object based on a WAN interface even if it has a dynamic IP address.
User Defined Original
IP
This field is available if Original IP is User Defined. Type the destination IP address that this
NAT rule supports.
Original IP Subnet/
Range
This field displays for Many 1:1 NAT. Select the destination IP address subnet or IP address
range that this NAT rule supports. The original and mapped IP address subnets or ranges
must have the same number of IP addresses.
Mapped IP Select to which translated destination IP address this NAT rule forwards packets.
User Def ined - this NAT rule supports a specific IP address, specified in the User Defined field.
HOST address - the drop-down box lists all the HOST address objects in the Zyxel Device. If
you select one of them, this NAT rule supports the IP address specified by the address
object.
User Defined Original
IP
This field is available if Mapped IP is User Define d. Type the translated destination IP address
that this NAT rule supports.
Mapped IP Subnet/
Range
This field displays for Many 1:1 NAT. Select to which translated destination IP address subnet
or IP address range this NAT rule forwards packets. The original and mapped IP address
subnets or ranges must have the same number of IP addresses.
Table 146 Configuration > Network > NAT > Add (continued)
LABEL DESCRIPTION
Chapter 13 NAT
USG/ZyWALL User’s Guide
399
Port Mapping Type Use the drop-down list box to select how many original destination ports this NAT rule
supports for the selected destination IP address (Original IP). Choices are:
Any - this NAT rule supports all the destination ports.
Port - this NAT rule supports one destination port.
Ports - this NAT rule supports a range of destination ports. You might use a range of
destination ports for unknown services or when one server supports more than one service.
Service - this NAT rule supports a service such as FTP (see Object > Service > Service)
Service-Group - this NAT rule supports a group of services such as all service objects related
to DNS (see Object > Service > Service Group)
Protocol Type This field is available if Mapping Type is Port or Ports. Select the protocol (TCP, UDP, or Any)
used by the service requesting the connection.
Original Port This field is available if Mapping Type is Port. Enter the original destination port this NAT rule
supports.
Mapped Port This field is available if Mapping Type is Port. Enter the translated destination port if this NAT
rule forwards the packet.
Original Start Port This field is available if Mapping Type is Ports. Enter the beginning of the range of original
destination ports this NAT rule supports.
Original End Port This field is available if Mapping Type is Ports. Enter the end of the range of original
destination ports this NAT rule supports.
Mapped Start Port This field is available if Mapping Type is Ports. Enter the beginning of the range of translated
destination ports if this NAT rule forwards the packet.
Mapped End Port This field is available if Mapping Type is Ports. Enter the end of the range of translated
destination ports if this NAT rule forwards the packet. The original port range and the
mapped port range must be the same size.
Enable NAT
Loopback
Enable NAT loopback to allow users connected to any interface (instead of just the
specified Incoming Interface) to use the NAT rule’s specified Original IP address to access
the Mapped IP device. For users connected to the same interface as the Mapped IP
device, the Zyxel Device uses that interface’s IP address as the source address for the
traffic it sends from the users to the Mapped IP device.
For example, if you configure a NAT rule to forward traffic from the WAN to a LAN server,
enabling NAT loopback allows users connected to other interfaces to also access the
server. For LAN users, the Zyxel Device uses the LAN interface’s IP address as the source
address for the traffic it sends to the LAN server. See NAT Loopback on page 400 for more
details.
If you do not enable NAT loopback, this NAT rule only applies to packets received on the
rule’s specified incoming interface.
Security Policy By default the security policy blocks incoming connections from external addresses. After
you configure your NAT rule settings, click the Security Policy link to configure a security
policy to allow the NAT rule’s traffic to come in.
The Zyxel Device checks NAT rules before it applies To-Zyxel Device security policies, so To-
Zyxel Device security policies, do not apply to traffic that is forwarded by NAT rules. The
Zyxel Device still checks other security policies, according to the source IP address and
mapped IP address.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to return to the NAT summary screen without creating the NAT rule (if it is new)
or saving any changes (if it already exists).
Table 146 Configuration > Network > NAT > Add (continued)
LABEL DESCRIPTION

Chapter 13 NAT
USG/ZyWALL User’s Guide
400
13.3 NAT Technical Reference
Here is more detailed information about NAT on the Zyxel Device.
NAT Loopback
Suppose an NAT 1:1 rule maps a public IP address to the private IP address of a LAN SMTP e-mail server
to give WAN users access. NAT loopback allows other users to also use the rule’s original IP to access the
mail server.
For example, a LAN user’s computer at IP address 192.168.1.89 queries a public DNS server to resolve the
SMTP server’s domain name (xxx.LAN-SMTP.com in this example) and gets the SMTP server’s mapped
public IP address of 1.1.1.1.
Figure 283 LAN Computer Queries a Public DNS Server
The LAN user’s computer then sends traffic to IP address 1.1.1.1. NAT loopback uses the IP address of the
Zyxel Device’s LAN interface (192.168.1.1) as the source address of the traffic going from the LAN users to
the LAN SMTP server.
192.168.1.21
xxx.LAN-SMTP.com =?
LAN
DNS
192.168.1.89
xxx.LAN-SMTP.com = 1.1.1.1
1.1.1.1

Chapter 13 NAT
USG/ZyWALL User’s Guide
401
Figure 284 LAN to LAN Traffic
The LAN SMTP server replies to the Zyxel Device’s LAN IP address and the Zyxel Device changes the
source address to 1.1.1.1 before sending it to the LAN user. The return traffic’s source matches the
original destination address (1.1.1.1). If the SMTP server replied directly to the LAN user without the traffic
going through NAT, the source would not match the original destination address which would cause the
LAN user’s computer to shut down the session.
Figure 285 LAN to LAN Return Traffic
192.168.1.21
LAN
192.168.1.89
Source 192.168.1.89
SMTP
NAT
Source 192.168.1.1
SMTP
192.168.1.21
LAN
192.168.1.89
Source 1.1.1.1
SMTP
NAT
Source 192.168.1.21
SMTP
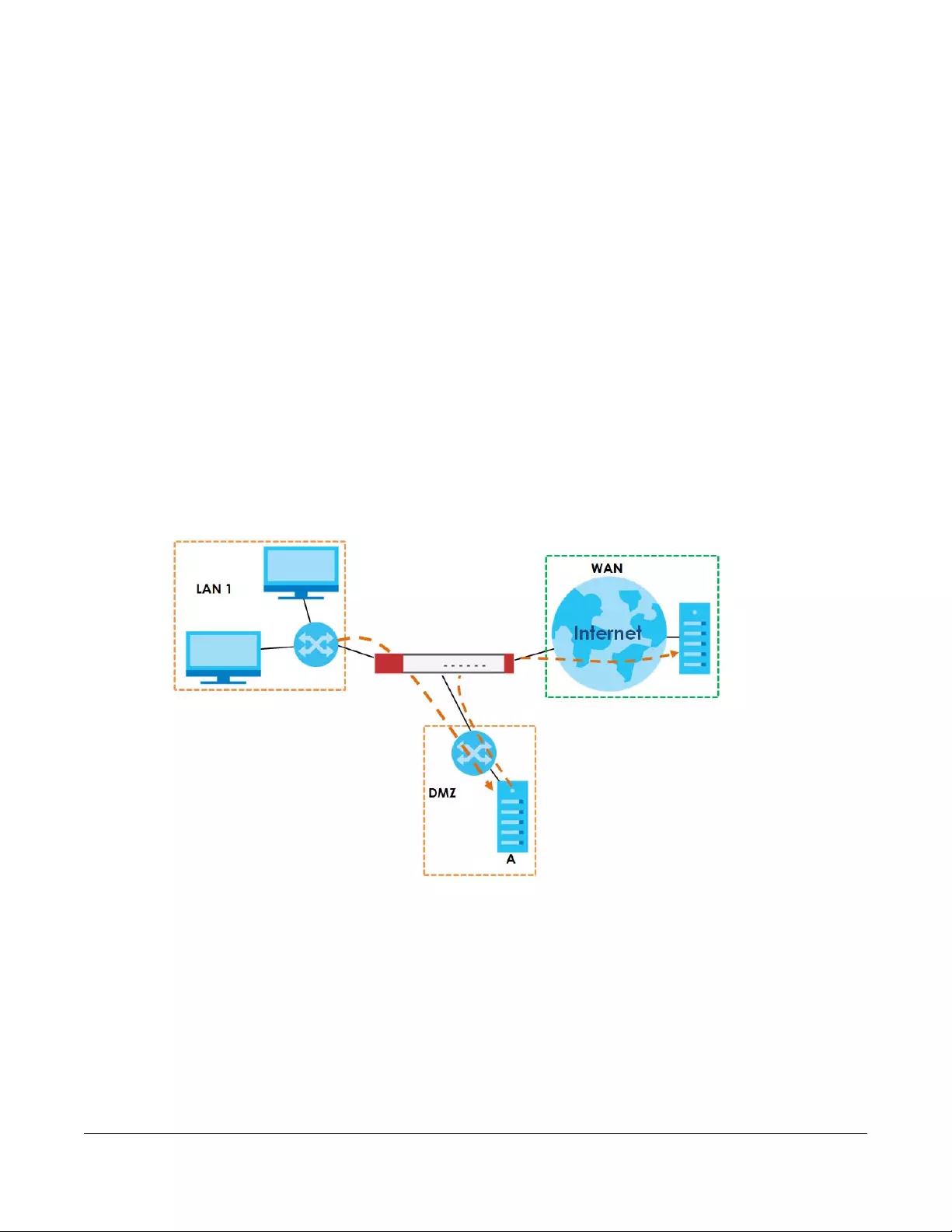
USG/ZyWALL User’s Guide
402
CHAPTER 14
Redirect Service
14.1 Overview
Redirect Service redirects HTTP and SMTP traffic.
14.1.1 HTTP Redirect
HTTP redirect forwards the client’s HTTP request (except HTTP traffic destined for the Zyxel Device) to a
web proxy server. In the following example, proxy server A is connected to the DMZ interface. When a
client connected to the LAN1 zone wants to open a web page, its HTTP request is redirected to proxy
server A first. If proxy server A cannot find the web page in its cache, a policy route allows it to access
the Internet to get them from a server. Proxy server A then forwards the response to the client.
Figure 286 HTTP Redirect Example
14.1.2 SMTP Redirect
SMTP redirect forwards the authenticated client’s SMTP message to a SMTP server, that handles all
outgoing e-mail messages. In the following example, SMTP server A is connected to the lan2 interface in
the LAN2 zone. When a client connected to the lan1 interface in the LAN1 zone logs into the Zyxel
Device and wants to send an e-mail, its SMTP message is redirected to SMTP server A. SMTP server A then
sends it to a mail server, where the message will be delivered to the recipient.
The Zyxel Device forwards SMTP traffic using TCP port 25.
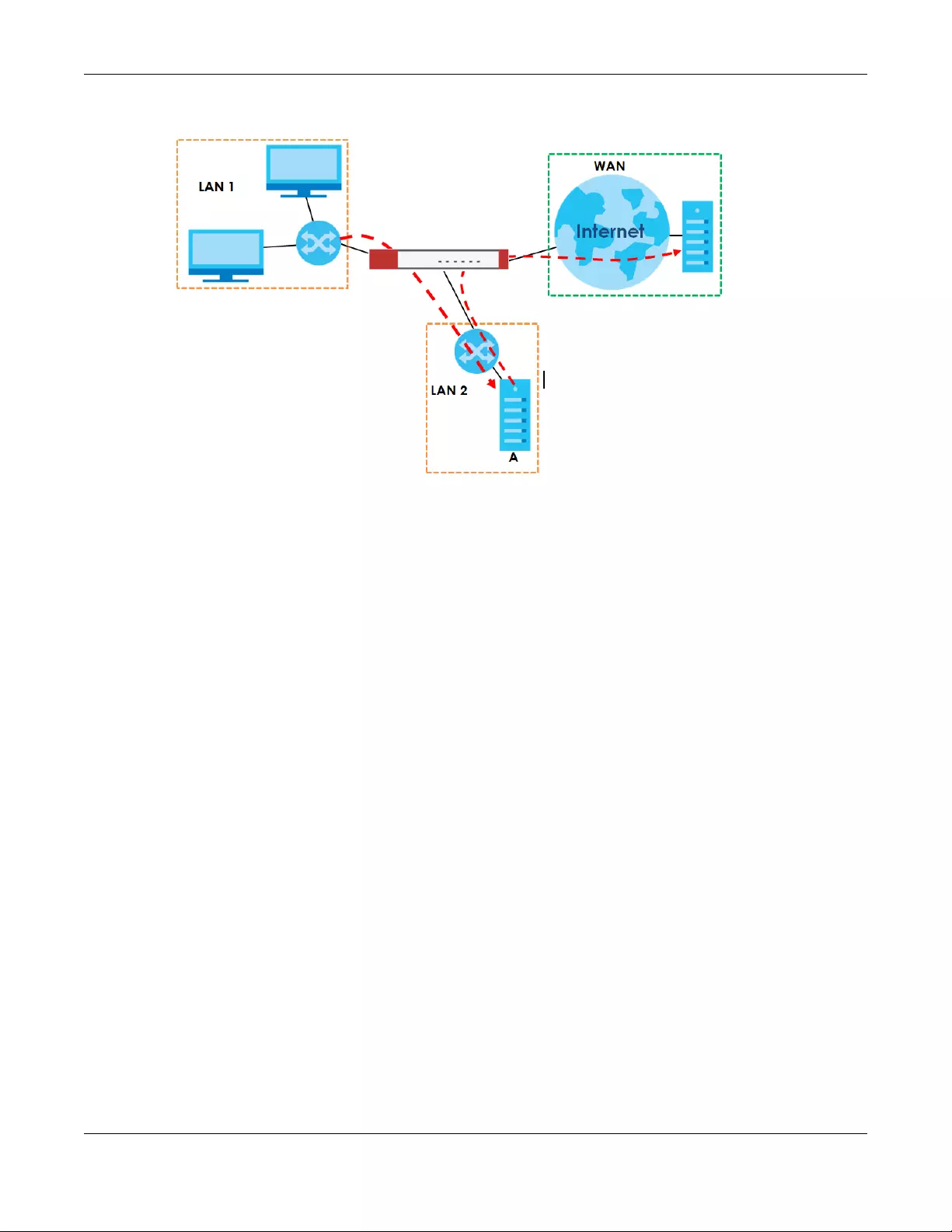
Chapter 14 Redirect Service
USG/ZyWALL User’s Guide
403
Figure 287 SMTP Redirect Example
14.1.3 What You Can Do in this Chapter
Use the Redirect Service screens (see Section 14.2 on page 405) to display and edit the HTTP and SMTP
redirect rules.
14.1.4 What You Need to Know
Web Proxy Server
A proxy server helps client devices make indirect requests to access the Internet or outside network
resources/services. A proxy server can act as a security policy or an ALG (application layer gateway)
between the private network and the Internet or other networks. It also keeps hackers from knowing
internal IP addresses.
A client connects to a web proxy server each time he/she wants to access the Internet. The web proxy
provides caching service to allow quick access and reduce network usage. The proxy checks its local
cache for the requested web resource first. If it is not found, the proxy gets it from the specified server
and forwards the response to the client.
HTTP Redirect, Security Policy and Policy Route
With HTTP redirect, the relevant packet flow for HTTP traffic is:
1Security Policy
2Application Patrol
3HTTP Redirect
4Policy Route

Chapter 14 Redirect Service
USG/ZyWALL User’s Guide
404
Even if you set a policy route to the same incoming interface and service as a HTTP redirect rule, the
Zyxel Device checks the HTTP redirect rules first and forwards HTTP traffic to a proxy server if matched.
You need to make sure there is no security policy blocking the HTTP requests from the client to the proxy
server.
You also need to manually configure a policy route to forward the HTTP traffic from the proxy server to
the Internet. To make the example in Figure 286 on page 402 work, make sure you have the following
settings.
For HTTP traffic between lan1 and dmz:
• a from LAN1 to DMZ security policy (default) to allow HTTP requests from lan1 to dmz. Responses to this
request are allowed automatically.
• a application patrol rule to allow HTTP traffic between lan1 and dmz.
• a HTTP redirect rule to forward HTTP traffic from lan1 to proxy server A.
For HTTP traffic between dmz and wan1:
• a from DMZ to WAN security policy (default) to allow HTTP requests from dmz to wan1. Responses to
these requests are allowed automatically.
• a application patrol rule to allow HTTP traffic between dmz and wan1.
• a policy route to forward HTTP traffic from proxy server A to the Internet.
SMTP
Simple Mail Transfer Protocol (SMTP) is the Internet’s message transport standard. It controls the sending
of e-mail messages between servers. E-mail clients (also called e-mail applications) then use mail server
protocols such as POP (Post Office Protocol) or IMAP (Internet Message Access Protocol) to retrieve e-
mail. E-mail clients also generally use SMTP to send messages to a mail server. The older POP2 requires
SMTP for sending messages while the newer POP3 can be used with or without it. This is why many e-mail
applications require you to specify both the SMTP server and the POP or IMAP server (even though they
may actually be the same server).
SMTP Redirect, Firewall and Policy Route
With SMTP redirect, the relevant packet flow for SMTP traffic is:
1Firewall
2SMTP Redirect
3Policy Route
Even if you set a policy route to the same incoming interface and service as a SMTP redirect rule, the
Zyxel Device checks the SMTP redirect rules first and forwards SMTP traffic to a SMTP server if matched.
You need to make sure there is no firewall rule(s) blocking the SMTP traffic from the client to the SMTP
server.
You also need to manually configure a policy route to forward the SMTP traffic from the SMTP server to
the Internet. To make the example in Figure 287 on page 403 work, make sure you have the following
settings.
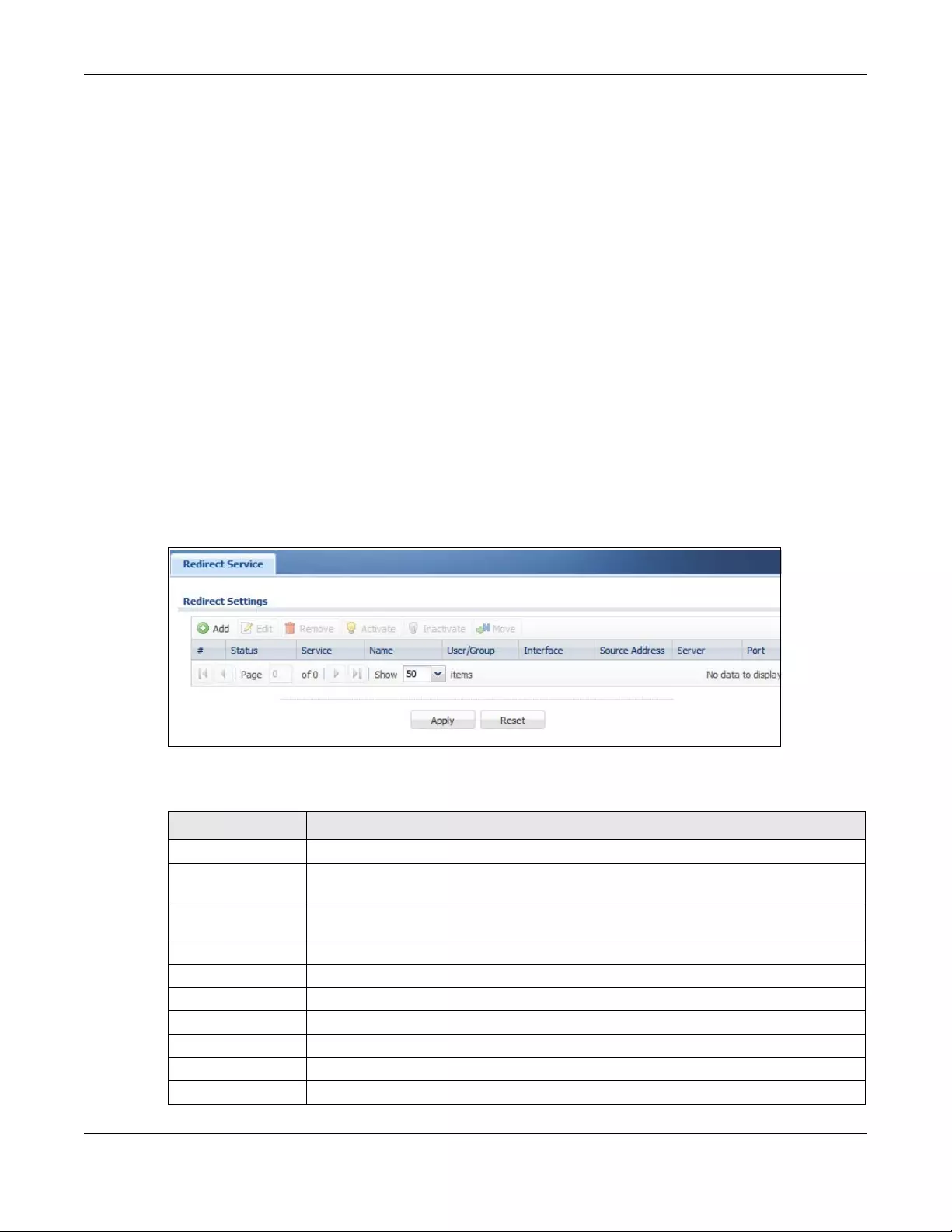
Chapter 14 Redirect Service
USG/ZyWALL User’s Guide
405
For SMTP traffic between lan1 and lan2:
• a from LAN1 to LAN2 firewall rule to allow SMTP messages from lan1 to lan2. Responses to this request
are allowed automatically.
• a SMTP redirect rule to forward SMTP traffic from lan1 to SMTP server A.
For SMTP traffic between lan2 and wan1:
• a from LAN2 to WAN firewall rule (default) to allow SMTP messages from lan2 to wan1. Responses to
these requests are allowed automatically.
• a policy route to forward SMTP messages from SMTP server A to the Internet.
14.2 The Redirect Service Screen
To configure redirection of a HTTP or SMTP request, click Configuration > Network > HTTP Redirect. This
screen displays the summary of the redirect rules.
Note: You can configure up to one HTTP redirect rule and one SMTP redirect rule for each
(incoming) interface.
Figure 288 Configuration > Network > Redirect Service
The following table describes the labels in this screen.
Table 147 Configuration > Network > Redirect Service
LABEL DESCRIPTION
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
# This field is a sequential value, and it is not associated with a specific entry.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
Service This is the name of the service: HTTP or SMTP.
Name This is the descriptive name of a rule.
User/Group This is the user account or user group name to which this rule is applied.
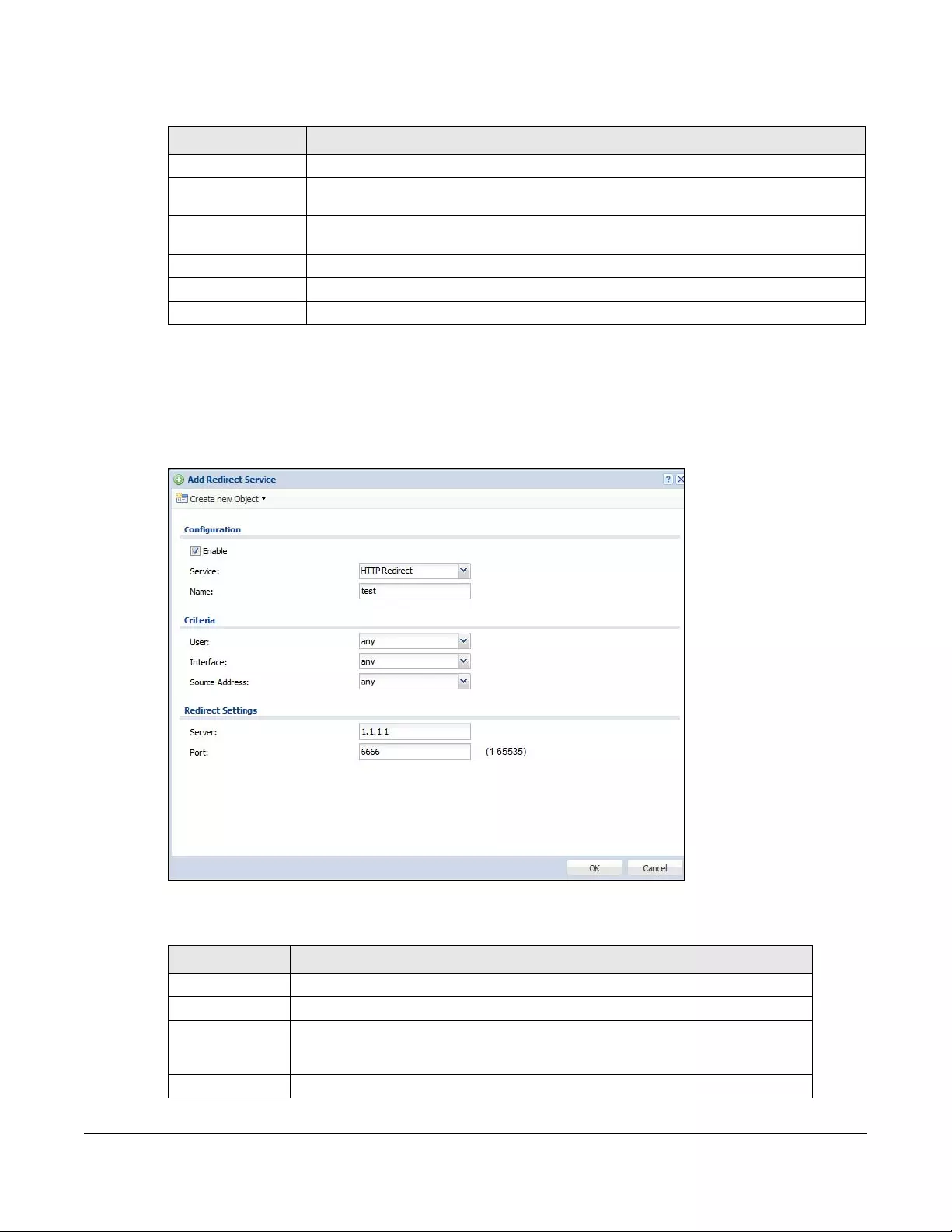
Chapter 14 Redirect Service
USG/ZyWALL User’s Guide
406
14.2.1 The Redirect Service Edit Screen
Click Network > Redirect Service to open the Redirect Service screen. Then click the Add or Edit icon to
open the Redirect Service Edit screen where you can configure the rule.
Figure 289 Network > Redirect Service > Edit
The following table describes the labels in this screen.
Interface This is the interface on which the request must be received.
Source Address This is the name of the source IP address object from which the traffic should be sent. If any
displays, the rule is effective for every source.
Server This is the IP address of the HTTP proxy server or the SMTP server to which the matched traffic
is forwarded.
Port This is the service port number used by the HTTP proxy server or SMTP server.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 147 Configuration > Network > Redirect Service (continued)
LABEL DESCRIPTION
Table 148 Network > Redirect Service > Edit
LABEL DESCRIPTION
Enable Use this option to turn the Redirect Service rule on or off.
Service Select the service to be redirected: HTTP Redirect or SMTP redirect.
Name Enter a name to identify this rule. You may use 1-31 alphanumeric characters,
underscores(_), or dashes (-), but the first character cannot be a number. This value
is case-sensitive.
Criteria
Chapter 14 Redirect Service
USG/ZyWALL User’s Guide
407
User Select the user account or user group name to which this rule is applied.
Interface Select the interface on which the request must be received for the Zyxel Device to
forward it to the specified server.
Source Address Select the name of the source IP address object from which the traffic should be
sent. Select any for the rule to be effective for every source.
Redirect Settings
Server Enter the IP address of the HTTP proxy or SMTP server.
Port Enter the port number that the HTTP proxy or SMTP server uses.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 148 Network > Redirect Service > Edit (continued)
LABEL DESCRIPTION
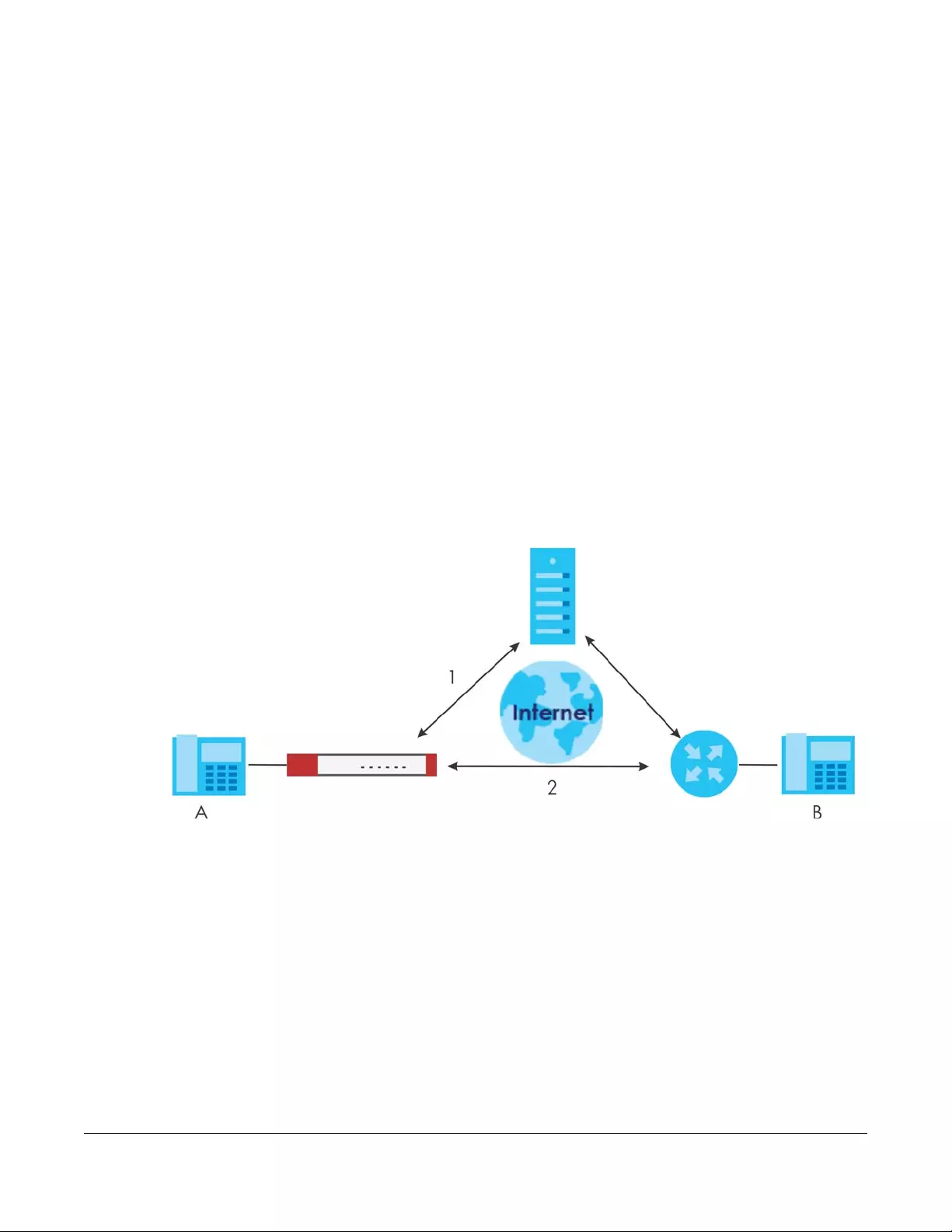
USG/ZyWALL User’s Guide
408
CHAPTER 15
ALG
15.1 ALG Overview
Application Layer Gateway (ALG) allows the following applications to operate properly through the
Zyxel Device’s NAT.
• SIP - Session Initiation Protocol (SIP) - An application-layer protocol that can be used to create voice
and multimedia sessions over Internet.
• H.323 - A teleconferencing protocol suite that provides audio, data and video conferencing.
• FTP - File Transfer Protocol - an Internet file transfer service.
The following example shows SIP signaling (1) and audio (2) sessions between SIP clients A and B and the
SIP server.
Figure 290 SIP ALG Example
The ALG feature is only needed for traffic that goes through the Zyxel Device’s NAT.
15.1.1 What You Need to Know
Application Layer Gateway (ALG), NAT and Security Policy
The Zyxel Device can function as an Application Layer Gateway (ALG) to allow certain NAT un-friendly
applications (such as SIP) to operate properly through the Zyxel Device’s NAT and security policy. The
Zyxel Device dynamically creates an implicit NAT session and security policy session for the application’s
traffic from the WAN to the LAN. The ALG on the Zyxel Device supports all of the Zyxel Device’s NAT
mapping types.
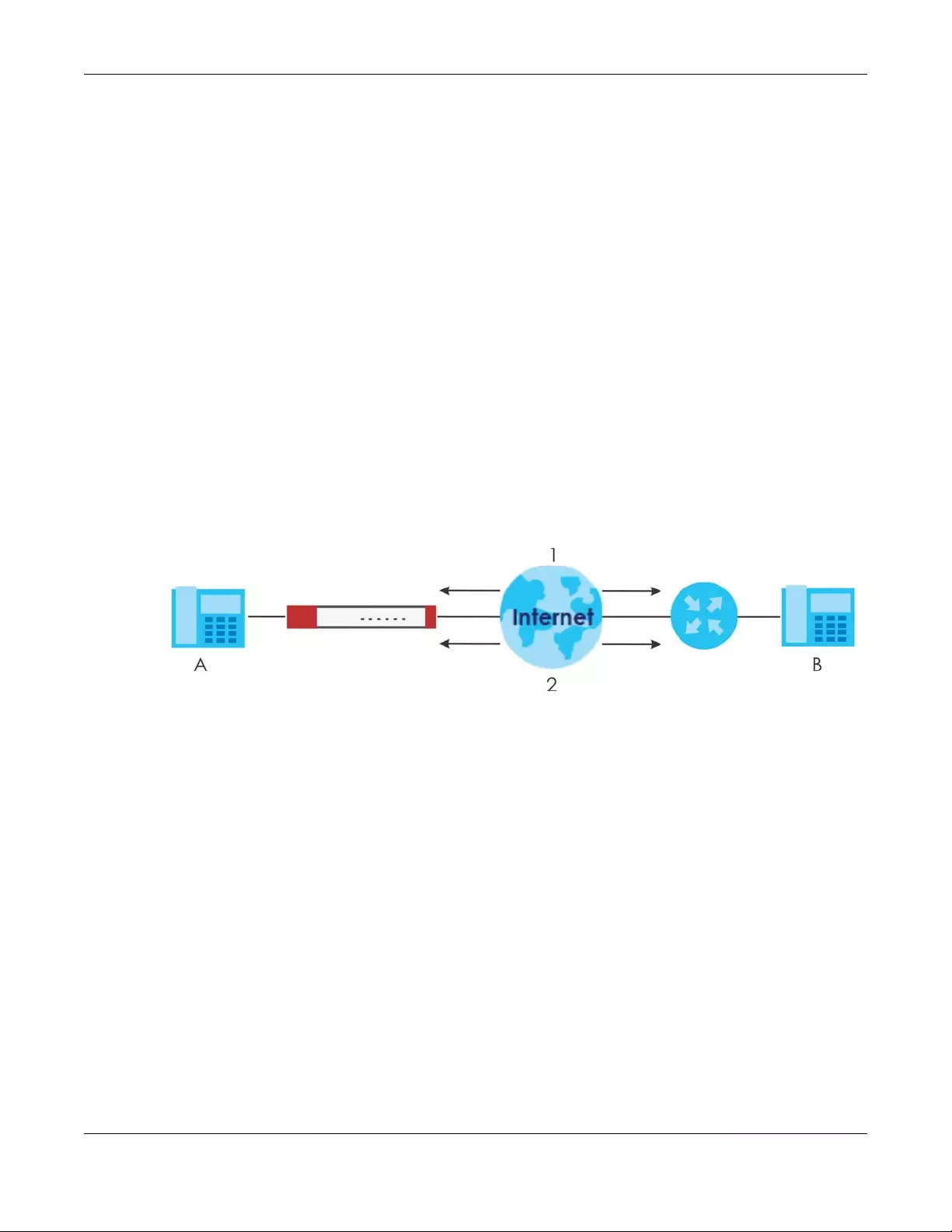
Chapter 15 ALG
USG/ZyWALL User’s Guide
409
FTP ALG
The FTP ALG allows TCP packets with a specified port destination to pass through. If the FTP server is
located on the LAN, you must also configure NAT (port forwarding) and security policies if you want to
allow access to the server from the WAN. Bandwidth management can be applied to FTP ALG traffic.
H.323 ALG
• The H.323 ALG supports peer-to-peer H.323 calls.
• The H.323 ALG handles H.323 calls that go through NAT or that the Zyxel Device routes. You can also
make other H.323 calls that do not go through NAT or routing. Examples would be calls between LAN
IP addresses that are on the same subnet.
• The H.323 ALG allows calls to go out through NAT. For example, you could make a call from a private
IP address on the LAN to a peer device on the WAN.
• The H.323 ALG operates on TCP packets with a specified port destination.
• Bandwidth management can be applied to H.323 ALG traffic.
• The Zyxel Device allows H.323 audio connections.
• The Zyxel Device can also apply bandwidth management to traffic that goes through the H.323 ALG.
The following example shows H.323 signaling (1) and audio (2) sessions between H.323 devices A and B.
Figure 291 H.323 ALG Example
SIP ALG
• SIP phones can be in any zone (including LAN, DMZ, WAN), and the SIP server and SIP clients can be in
the same network or different networks. The SIP server cannot be on the LAN. It must be on the WAN
or the DMZ.
• There should be only one SIP server (total) on the Zyxel Device’s private networks. Any other SIP servers
must be on the WAN. So for example you could have a Back-to-Back User Agent such as the IPPBX
x6004 or an asterisk PBX on the DMZ or on the LAN but not on both.
• Using the SIP ALG allows you to use bandwidth management on SIP traffic. Bandwidth management
can be applied to FTP ALG traffic. Use the option in the Configuration > BWM screen to configure the
highest bandwidth available for SIP traffic.
• The SIP ALG handles SIP calls that go through NAT or that the Zyxel Device routes. You can also make
other SIP calls that do not go through NAT or routing. Examples would be calls between LAN IP
addresses that are on the same subnet.
• The SIP ALG supports peer-to-peer SIP calls. The security policy (by default) allows peer to peer calls
from the LAN zone to go to the WAN zone and blocks peer to peer calls from the WAN zone to the
LAN zone.
• The SIP ALG allows UDP packets with a specified port destination to pass through.
• The Zyxel Device allows SIP audio connections.
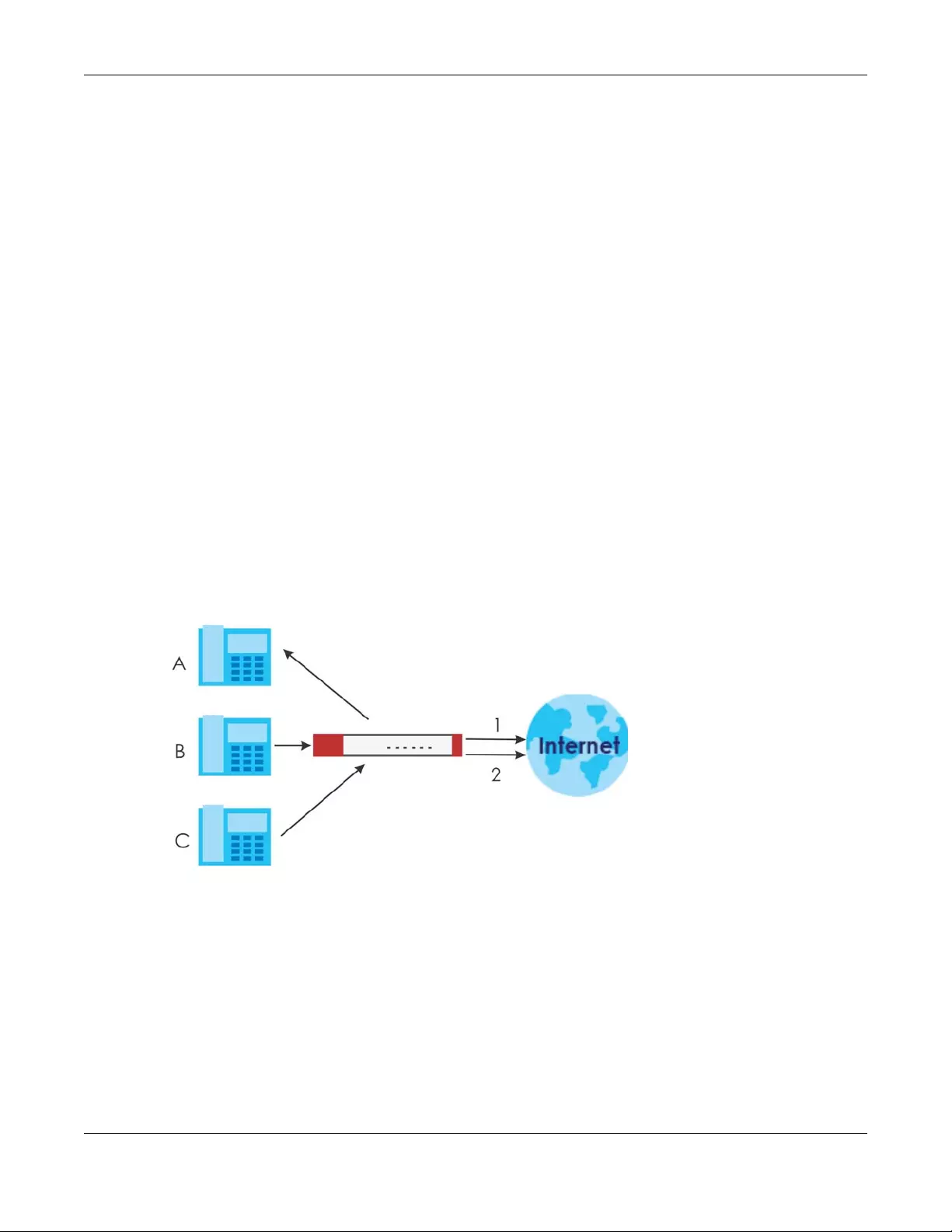
Chapter 15 ALG
USG/ZyWALL User’s Guide
410
• You do not need to use TURN (Traversal Using Relay NAT) for VoIP devices behind the Zyxel Device
when you enable the SIP ALG.
• Configuring the SIP ALG to use custom port numbers for SIP traffic also configures the application
patrol (see Chapter 36 on page 629) to use the same port numbers for SIP traffic. Likewise, configuring
the application patrol to use custom port numbers for SIP traffic also configures SIP ALG to use the
same port numbers for SIP traffic.
Peer-to-Peer Calls and the Zyxel Device
The Zyxel Device ALG can allow peer-to-peer VoIP calls for both H.323 and SIP. You must configure the
security policy and NAT (port forwarding) to allow incoming (peer-to-peer) calls from the WAN to a
private IP address on the LAN (or DMZ).
VoIP Calls from the WAN with Multiple Outgoing Calls
When you configure the security policy and NAT (port forwarding) to allow calls from the WAN to a
specific IP address on the LAN, you can also use policy routing to have H.323 (or SIP) calls from other LAN
or DMZ IP addresses go out through a different WAN IP address. The policy routing lets the Zyxel Device
correctly forward the return traffic for the calls initiated from the LAN IP addresses.
For example, you configure the security policy and NAT to allow LAN IP address A to receive calls from
the Internet through WAN IP address 1. You also use a policy route to have LAN IP address A make calls
out through WAN IP address 1. Configure another policy route to have H.323 (or SIP) calls from LAN IP
addresses B and C go out through WAN IP address 2. Even though only LAN IP address A can receive
incoming calls from the Internet, LAN IP addresses B and C can still make calls out to the Internet.
Figure 292 VoIP Calls from the WAN with Multiple Outgoing Calls
VoIP with Multiple WAN IP Addresses
With multiple WAN IP addresses on the Zyxel Device, you can configure different security policy and NAT
(port forwarding) rules to allow incoming calls from each WAN IP address to go to a specific IP address
on the LAN (or DMZ). Use policy routing to have the H.323 (or SIP) calls from each of those LAN or DMZ IP
addresses go out through the same WAN IP address that calls come in on. The policy routing lets the
Zyxel Device correctly forward the return traffic for the calls initiated from the LAN IP addresses.
For example, you configure security policy and NAT rules to allow LAN IP address A to receive calls
through public WAN IP address 1. You configure different security policy and port forwarding rules to
allow LAN IP address B to receive calls through public WAN IP address 2. You configure corresponding
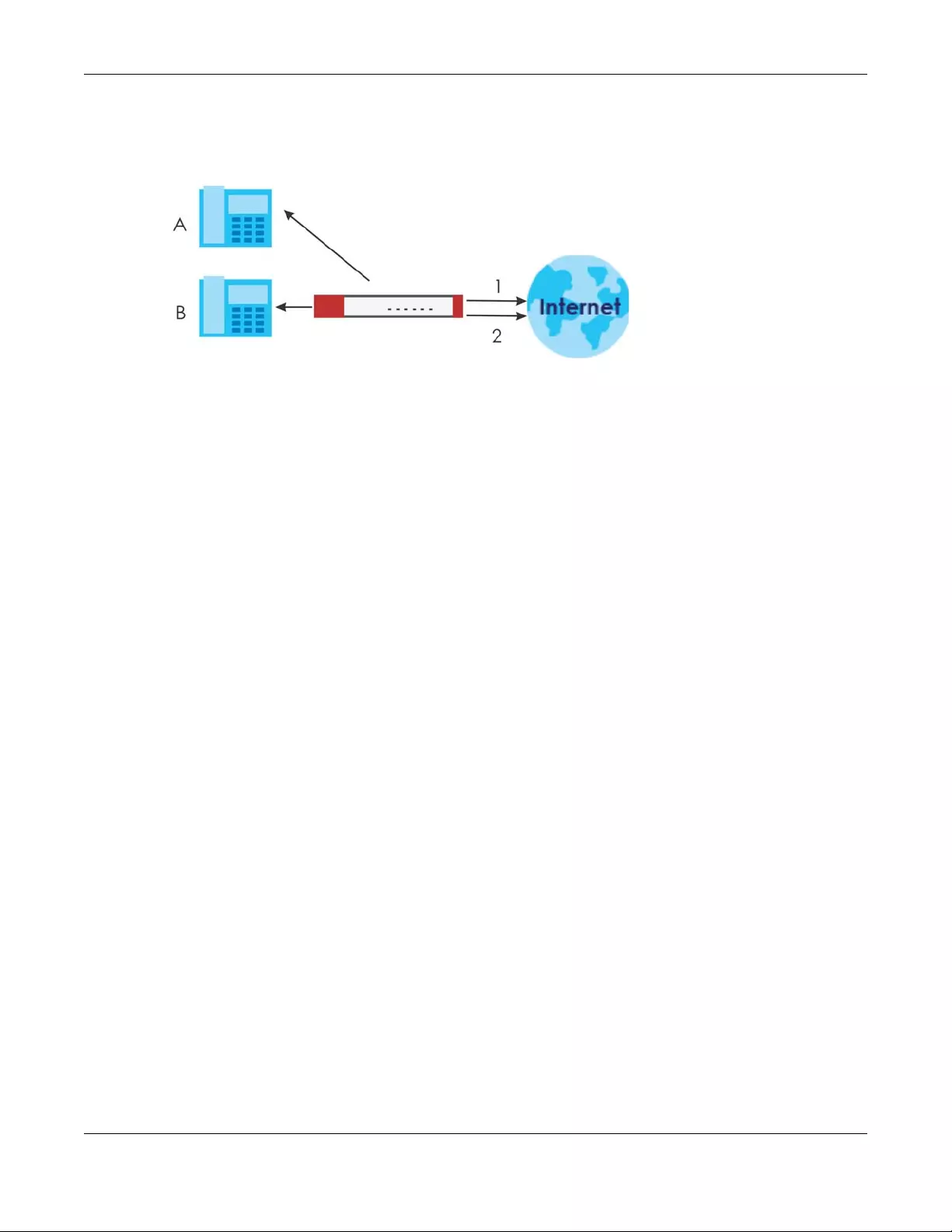
Chapter 15 ALG
USG/ZyWALL User’s Guide
411
policy routes to have calls from LAN IP address A go out through WAN IP address 1 and calls from LAN IP
address B go out through WAN IP address 2.
Figure 293 VoIP with Multiple WAN IP Addresses
15.1.2 Before You Begin
You must also configure the security policy and enable NAT in the Zyxel Device to allow sessions initiated
from the WAN.
15.2 The ALG Screen
Click Configuration > Network > ALG to open the ALG screen. Use this screen to turn ALGs off or on,
configure the port numbers to which they apply, and configure SIP ALG time outs.
Note: If the Zyxel Device provides an ALG for a service, you must enable the ALG in order to
use the application patrol on that service’s traffic.
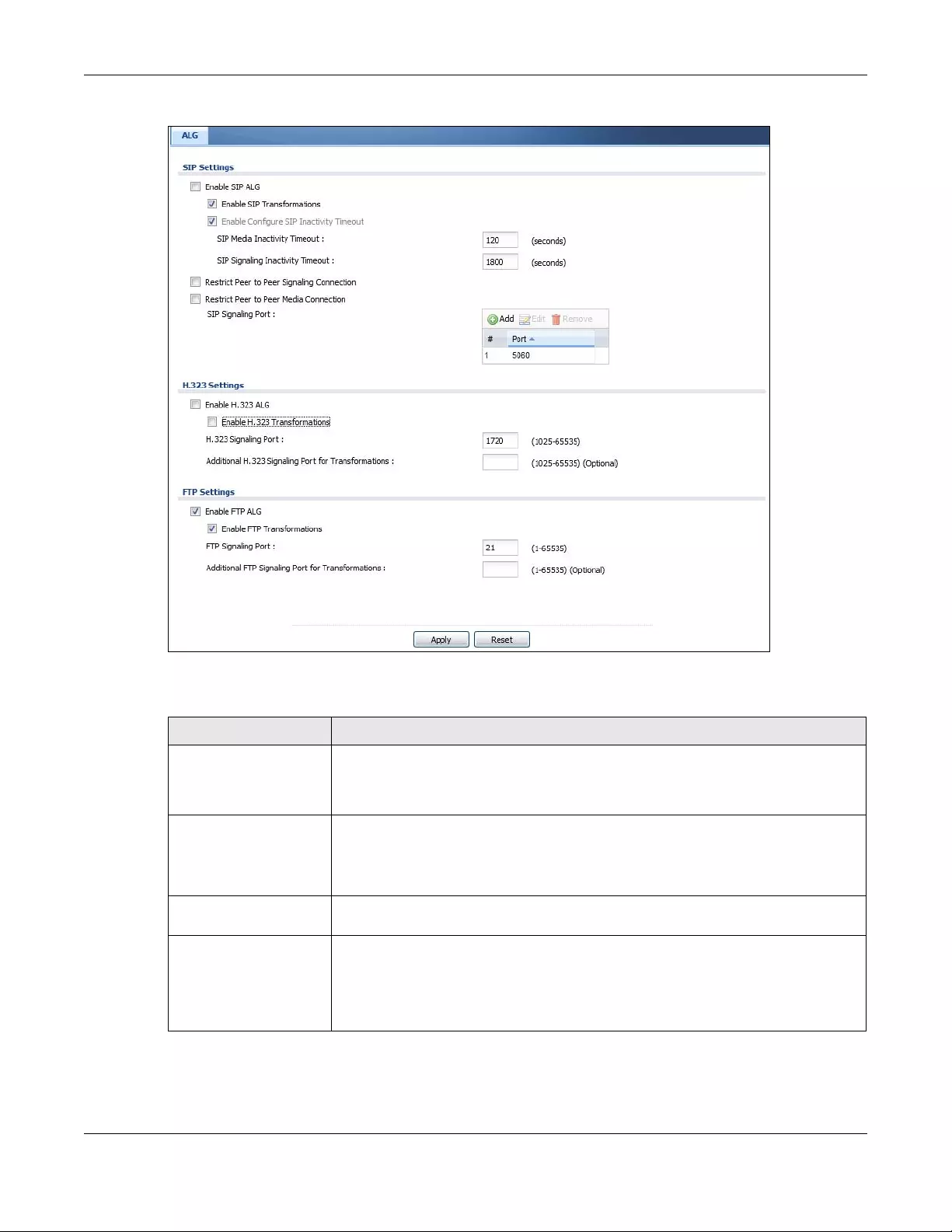
Chapter 15 ALG
USG/ZyWALL User’s Guide
412
Figure 294 Configuration > Network > ALG
The following table describes the labels in this screen.
Table 149 Configuration > Network > ALG
LABEL DESCRIPTION
Enable SIP ALG Turn on the SIP ALG to detect SIP traffic and help build SIP sessions through the Zyxel
Device’s NAT. Enabling the SIP ALG also allows you to use the application patrol to
detect SIP traffic and manage the SIP traffic’s bandwidth (see Chapter 36 on page
629).
Enable SIP
Transformations
Select this to have the Zyxel Device modify IP addresses and port numbers embedded
in the SIP data payload.
You do not need to use this if you have a SIP device or server that will modify IP
addresses and port numbers embedded in the SIP data payload.
Enable Configure SIP
Inactivity Timeout
Select this option to have the Zyxel Device apply SIP media and signaling inactivity time
out limits.
SIP Media Inactivity
Timeout
Use this field to set how many seconds (1~86400) the Zyxel Device will allow a SIP session
to remain idle (without voice traffic) before dropping it.
If no voice packets go through the SIP ALG before the timeout period expires, the Zyxel
Device deletes the audio session. You cannot hear anything and you will need to make
a new call to continue your conversation.
Chapter 15 ALG
USG/ZyWALL User’s Guide
413
SIP Signaling Inactivity
Timeout
Most SIP clients have an “expire” mechanism indicating the lifetime of signaling
sessions. The SIP user agent sends registration packets to the SIP server periodically and
keeps the session alive in the Zyxel Device.
If the SIP client does not have this mechanism and makes no calls during the Zyxel
Device SIP timeout, the Zyxel Device deletes the signaling session after the timeout
period. Enter the SIP signaling session timeout value (1~86400).
Restrict Peer to Peer
Signaling Connection
A signaling connection is used to set up the SIP connection.
Enable this if you want signaling connections to only arrive from the IP address(es) you
registered with. Signaling connections from other IP addresses will be dropped.
Restrict Peer to Peer
Media Connection
A media connection is the audio transfer in a SIP connection.
Enable this if you want media connections to only arrive from the IP address(es) you
registered with. Media connections from other IP addresses will be dropped.
You should disable this if have registered for cloud VoIP services.
SIP Signaling Port If you are using a custom UDP port number (not 5060) for SIP traffic, enter it here. Use the
Add icon to add fields if you are also using SIP on additional UDP port numbers.
Additional SIP Signaling
Port (UDP) for
Transformations
If you are also using SIP on an additional UDP port number, enter it here.
Enable H.323 ALG Turn on the H.323 ALG to detect H.323 traffic (used for audio communications) and
help build H.323 sessions through the Zyxel Device’s NAT. Enabling the H.323 ALG also
allows you to use the application patrol to detect H.323 traffic and manage the H.323
traffic’s bandwidth (see Chapter 36 on page 629).
Enable H.323
Transformations
Select this to have the Zyxel Device modify IP addresses and port numbers embedded
in the H.323 data payload.
You do not need to use this if you have a H.323 device or server that will modify IP
addresses and port numbers embedded in the H.323 data payload.
H.323 Signaling Port If you are using a custom TCP port number (not 1720) for H.323 traffic, enter it here.
Additional H.323
Signaling Port for
Transformations
If you are also using H.323 on an additional TCP port number, enter it here.
Enable FTP ALG Turn on the FTP ALG to detect FTP (File Transfer Program) traffic and help build FTP
sessions through the Zyxel Device’s NAT. Enabling the FTP ALG also allows you to use the
application patrol to detect FTP traffic and manage the FTP traffic’s bandwidth (see
Chapter 36 on page 629).
Enable FTP
Transformations
Select this option to have the Zyxel Device modify IP addresses and port numbers
embedded in the FTP data payload to match the Zyxel Device’s NAT environment.
Clear this option if you have an FTP device or server that will modify IP addresses and
port numbers embedded in the FTP data payload to match the Zyxel Device’s NAT
environment.
FTP Signaling Port If you are using a custom TCP port number (not 21) for FTP traffic, enter it here.
Additional FTP Signaling
Port for Transformations
If you are also using FTP on an additional TCP port number, enter it here.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 149 Configuration > Network > ALG (continued)
LABEL DESCRIPTION

Chapter 15 ALG
USG/ZyWALL User’s Guide
414
15.3 ALG Technical Reference
Here is more detailed information about the Application Layer Gateway.
ALG
Some applications cannot operate through NAT (are NAT unfriendly) because they embed IP addresses
and port numbers in their packets’ data payload. The Zyxel Device examines and uses IP address and
port number information embedded in the VoIP traffic’s data stream. When a device behind the Zyxel
Device uses an application for which the Zyxel Device has VoIP pass through enabled, the Zyxel Device
translates the device’s private IP address inside the data stream to a public IP address. It also records
session port numbers and allows the related sessions to go through the security policy so the
application’s traffic can come in from the WAN to the LAN.
ALG and Trunks
If you send your ALG-managed traffic through an interface trunk and all of the interfaces are set to
active, you can configure routing policies to specify which interface the ALG-managed traffic uses.
You could also have a trunk with one interface set to active and a second interface set to passive. The
Zyxel Device does not automatically change ALG-managed connections to the second (passive)
interface when the active interface’s connection goes down. When the active interface’s connection
fails, the client needs to re-initialize the connection through the second interface (that was set to
passive) in order to have the connection go through the second interface. VoIP clients usually re-register
automatically at set intervals or the users can manually force them to re-register.
FTP
File Transfer Protocol (FTP) is an Internet file transfer service that operates on the Internet and over TCP/IP
networks. A system running the FTP server accepts commands from a system running an FTP client. The
service allows users to send commands to the server for uploading and downloading files.
H.323
H.323 is a standard teleconferencing protocol suite that provides audio, data and video conferencing.
It allows for real-time point-to-point and multipoint communication between client computers over a
packet-based network that does not provide a guaranteed quality of service. NetMeeting uses H.323.
SIP
The Session Initiation Protocol (SIP) is an application-layer control (signaling) protocol that handles the
setting up, altering and tearing down of voice and multimedia sessions over the Internet. SIP is used in
VoIP (Voice over IP), the sending of voice signals over the Internet Protocol.
SIP signaling is separate from the media for which it handles sessions. The media that is exchanged
during the session can use a different path from that of the signaling. SIP handles telephone calls and
can interface with traditional circuit-switched telephone networks.

Chapter 15 ALG
USG/ZyWALL User’s Guide
415
RTP
When you make a VoIP call using H.323 or SIP, the RTP (Real time Transport Protocol) is used to handle
voice data transfer. See RFC 1889 for details on RTP.

USG/ZyWALL User’s Guide
416
CHAPTER 16
UPnP
16.1 UPnP and NAT-PMP Overview
The Zyxel Device supports both UPnP and NAT-PMP to permit networking devices to discover each other
and connect seamlessly.
Universal Plug and Play (UPnP) is a distributed, open networking standard that uses TCP/IP for simple
peer-to-peer network connectivity between devices. A UPnP device can dynamically join a network,
obtain an IP address, convey its capabilities and learn about other devices on the network. In turn, a
device can leave a network smoothly and automatically when it is no longer in use. A gateway that
supports UPnP is called Internet Gateway Device (IGD). The standardized Device Control Protocol (DCP)
is defined by the UPnP Forum for IGDs to configure port mapping automatically.
NAT Port Mapping Protocol (NAT-PMP), introduced by Apple and implemented in current Apple
products, is used as an alternative NAT traversal solution to the UPnP IGD protocol. NAT-PMP runs over
UDP port 5351. NAT-PMP is much simpler than UPnP IGD and mainly designed for small home networks. It
allows a client behind a NAT router to retrieve the router’s public IP address and port number and make
them known to the peer device with which it wants to communicate. The client can automatically
configure the NAT router to create a port mapping to allow the peer to contact it.
16.2 What You Need to Know
UPnP hardware is identified as an icon in the Network Connections folder (Windows XP). Each UPnP
compatible device installed on your network will appear as a separate icon. Selecting the icon of a
UPnP device will allow you to access the information and properties of that device.
16.2.1 NAT Traversal
UPnP NAT traversal automates the process of allowing an application to operate through NAT. UPnP
network devices can automatically configure network addressing, announce their presence in the
network to other UPnP devices and enable exchange of simple product and service descriptions. NAT
traversal allows the following:
• Dynamic port mapping
• Learning public IP addresses
• Assigning lease times to mappings
Windows Messenger is an example of an application that supports NAT traversal and UPnP.
See the NAT chapter for more information on NAT.
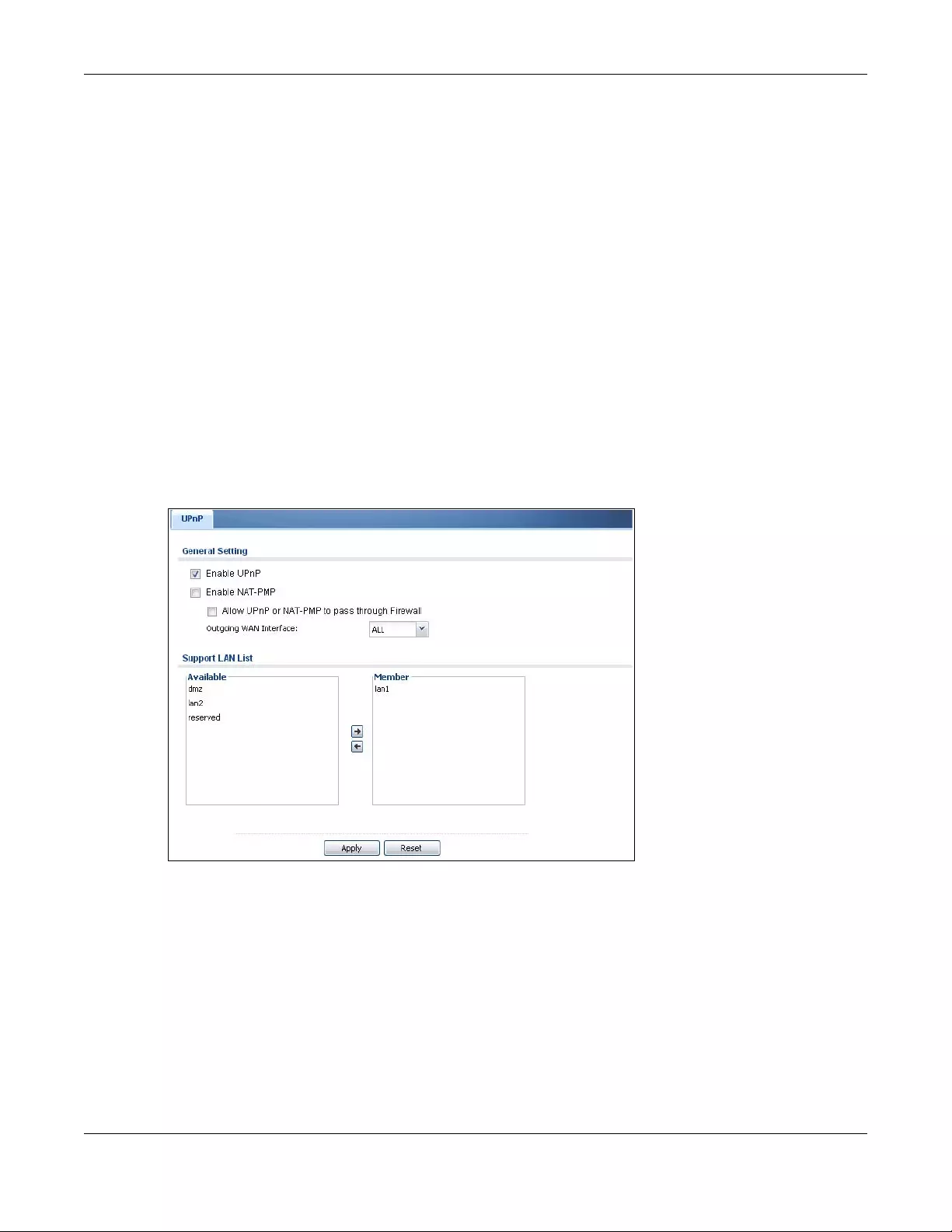
Chapter 16 UPnP
USG/ZyWALL User’s Guide
417
16.2.2 Cautions with UPnP and NAT-PMP
The automated nature of NAT traversal applications in establishing their own services and opening
security policy ports may present network security issues. Network information and configuration may
also be obtained and modified by users in some network environments.
When a UPnP or NAT-PMP device joins a network, it announces its presence with a multicast message.
For security reasons, the Zyxel Device allows multicast messages on the LAN only.
All UPnP-enabled or NAT-PMP-enabled devices may communicate freely with each other without
additional configuration. Disable UPnP or NAT-PMP if this is not your intention.
16.3 UPnP Screen
Use this screen to enable UPnP and NAT-PMP on your Zyxel Device.
Click Configuration > Network > UPnP to display the screen shown next.
Figure 295 Configuration > Network > UPnP
Chapter 16 UPnP
USG/ZyWALL User’s Guide
418
The following table describes the fields in this screen.
16.4 Technical Reference
The sections show examples of using UPnP.
16.4.1 Turning on UPnP in Windows 7 Example
This section shows you how to use the UPnP feature in Windows 7. UPnP server is installed in Windows 7.
Activate UPnP on the Zyxel Device.
Make sure the computer is connected to a LAN port of the Zyxel Device. Turn on your computer and the
Zyxel Device.
1Click the start icon, Control Panel and then the Network and Sharing Center.
Table 150 Configuration > Network > UPnP
LABEL DESCRIPTION
Enable UPnP Select this check box to activate UPnP on the Zyxel Device. Be aware that anyone could use
a UPnP application to open the web configurator's login screen without entering the Zyxel
Device's IP address (although you must still enter the password to access the web
configurator).
Enable NAT-PMP NAT Port Mapping Protocol (NAT-PMP) automates port forwarding to allow a computer in a
private network (behind the Zyxel Device) to automatically configure the Zyxel Device to
allow computers outside the private network to contact it.
Select this check box to activate NAT-PMP on the Zyxel Device. Be aware that anyone could
use a NAT-PMP application to open the web configurator's login screen without entering the
Zyxel Device's IP address (although you must still enter the password to access the web
configurator).
Allow UPnP or
NAT-PMP to pass
through Firewall
Select this check box to allow traffic from UPnP-enabled or NAT-PMP-enabled applications
to bypass the security policy.
Clear this check box to have the security policy block all UPnP or NAT-PMP application
packets (for example, MSN packets).
Outgoing WAN
Interface Select through which WAN interface(s) you want to send out traffic from UPnP-enabled or
NAT-PMP-enabled applications. If the WAN interface you select loses its connection, the
Zyxel Device attempts to use the other WAN interface. If the other WAN interface also does
not work, the Zyxel Device drops outgoing packets from UPnP-enabled or NAT-PMP-enabled
applications.
Support LAN List The Available list displays the name(s) of the internal interface(s) on which the Zyxel Device
supports UPnP and/or NAT-PMP.
To enable UPnP and/or NAT-PMP on an interface, you can double-click a single entry to
move it or use the [Shift] or [Ctrl] key to select multiple entries and click the right arrow button
to add to the Member list. To remove an interface, select the name(s) in the Member list and
click the left arrow button.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
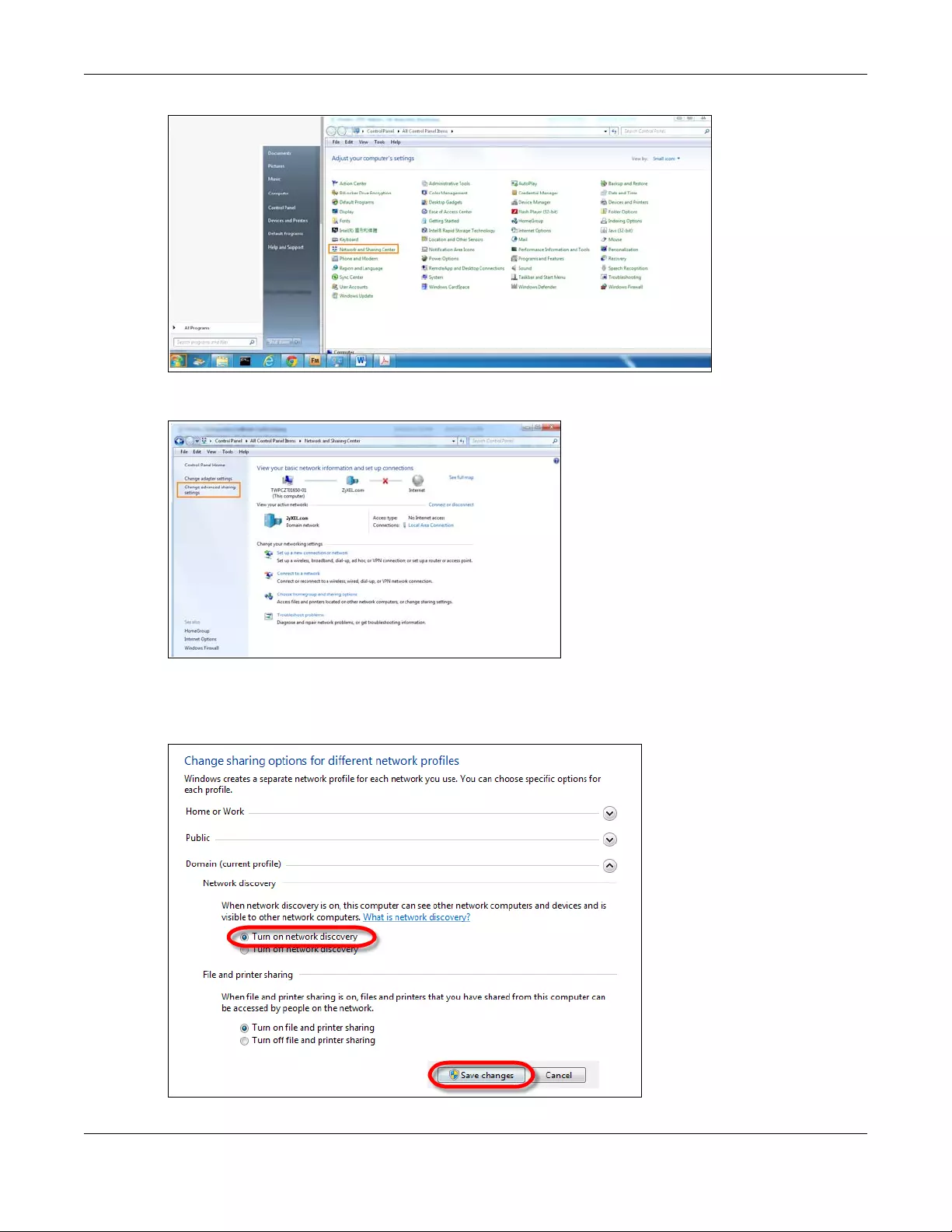
Chapter 16 UPnP
USG/ZyWALL User’s Guide
419
2Click Change Advanced Sharing Settings.
3Select Turn on network discovery and click Save Changes. Network discovery allows your computer to
find other computers and devices on the network and other computers on the network to find your
computer. This makes it easier to share files and printers.
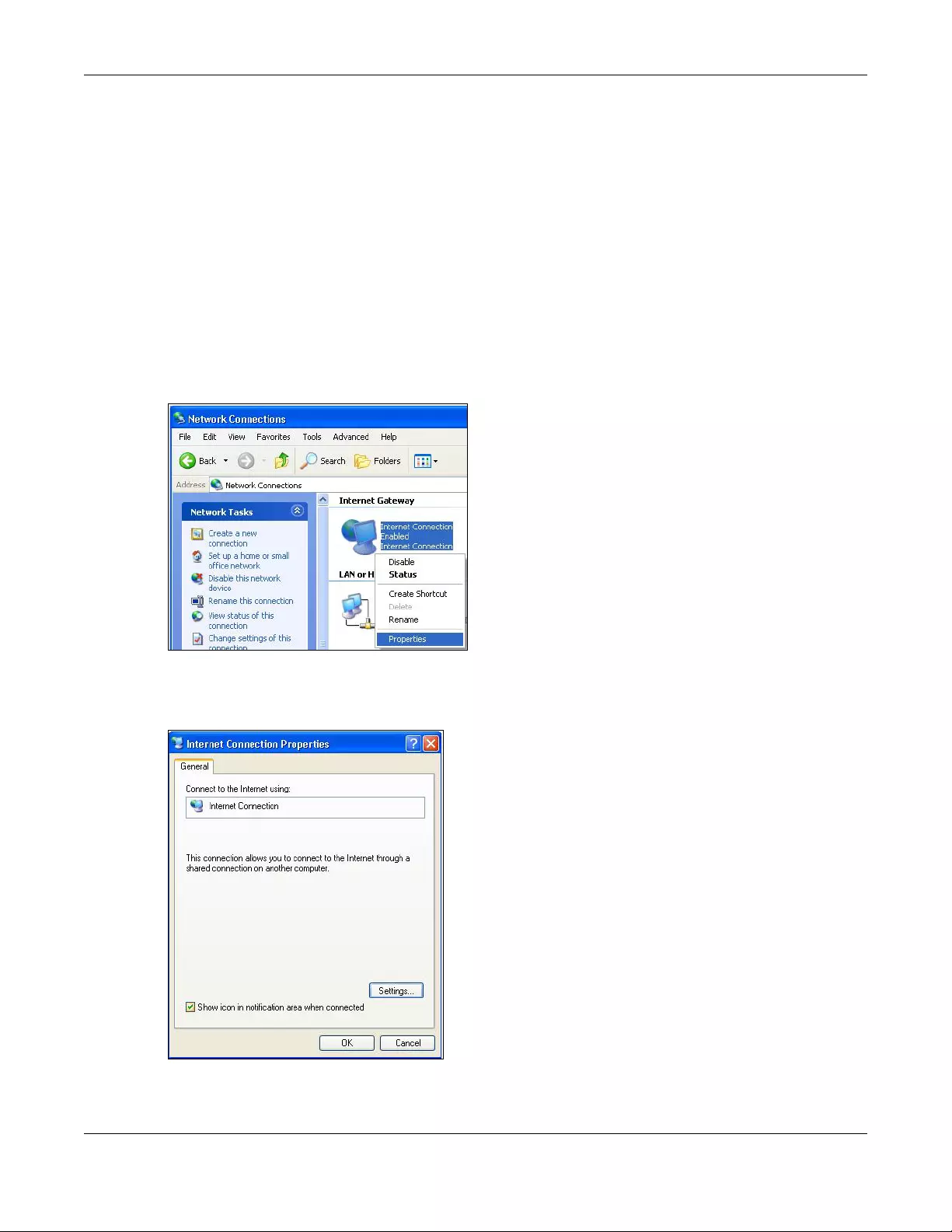
Chapter 16 UPnP
USG/ZyWALL User’s Guide
420
16.4.2 Using UPnP in Windows XP Example
This section shows you how to use the UPnP feature in Windows XP. You must already have UPnP installed
in Windows XP and UPnP activated on the Zyxel Device.
Make sure the computer is connected to a LAN port of the Zyxel Device. Turn on your computer and the
Zyxel Device.
16.4.2.1 Auto-discover Your UPnP-enabled Network Device
1Click start and Control Panel. Double-click Network Connections. An icon displays under Internet
Gateway.
2Right-click the icon and select Properties.
Figure 296 Network Connections
3In the Internet Connection Properties window, click Settings to see the port mappings there were
automatically created.
Figure 297 Internet Connection Properties
4You may edit or delete the port mappings or click Add to manually add port mappings.
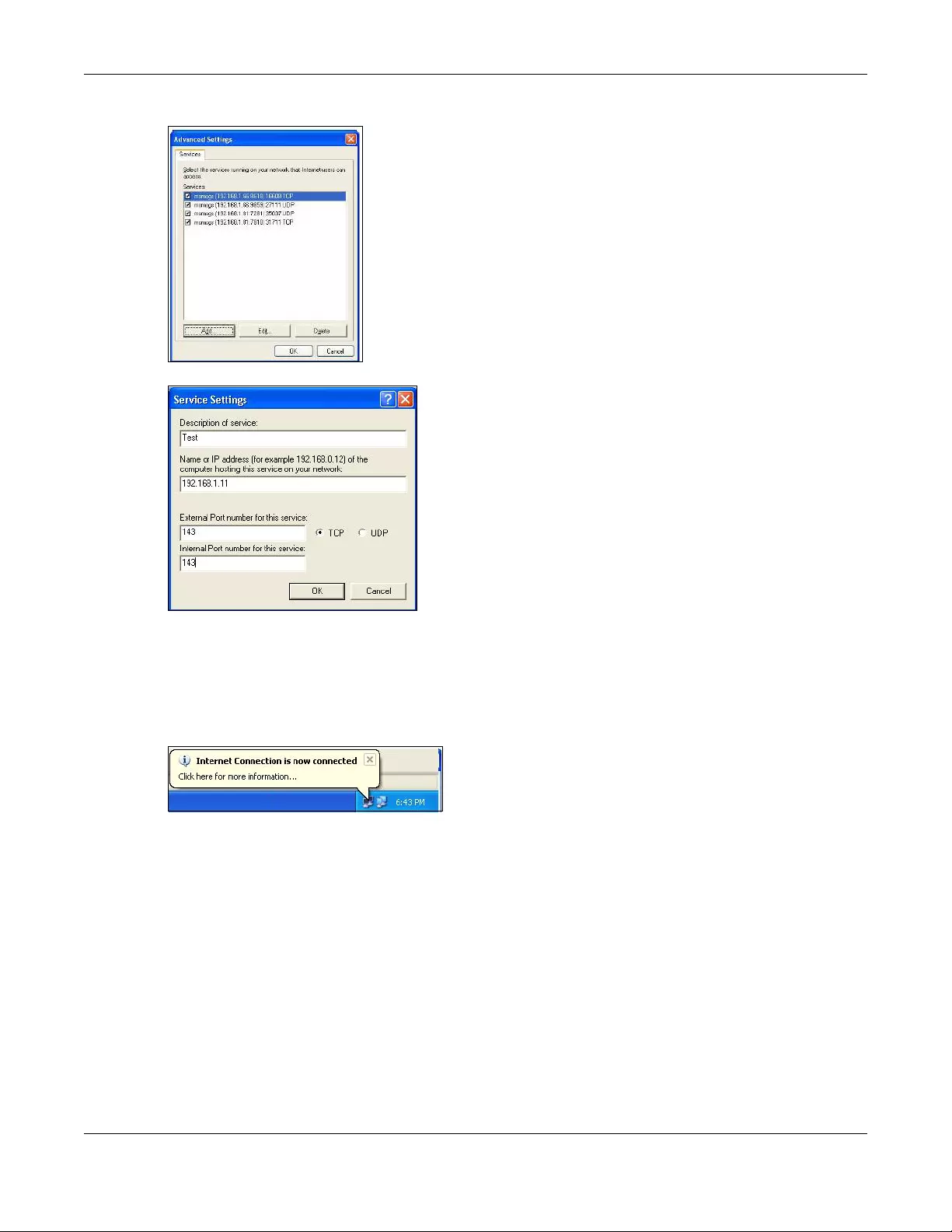
Chapter 16 UPnP
USG/ZyWALL User’s Guide
421
Figure 298 Internet Connection Properties: Advanced Settings
Figure 299 Internet Connection Properties: Advanced Settings: Add
Note: When the UPnP-enabled device is disconnected from your computer, all port
mappings will be deleted automatically.
5Select Show icon in notification area when connected option and click OK. An icon displays in the
system tray.
Figure 300 System Tray Icon
6Double-click on the icon to display your current Internet connection status.
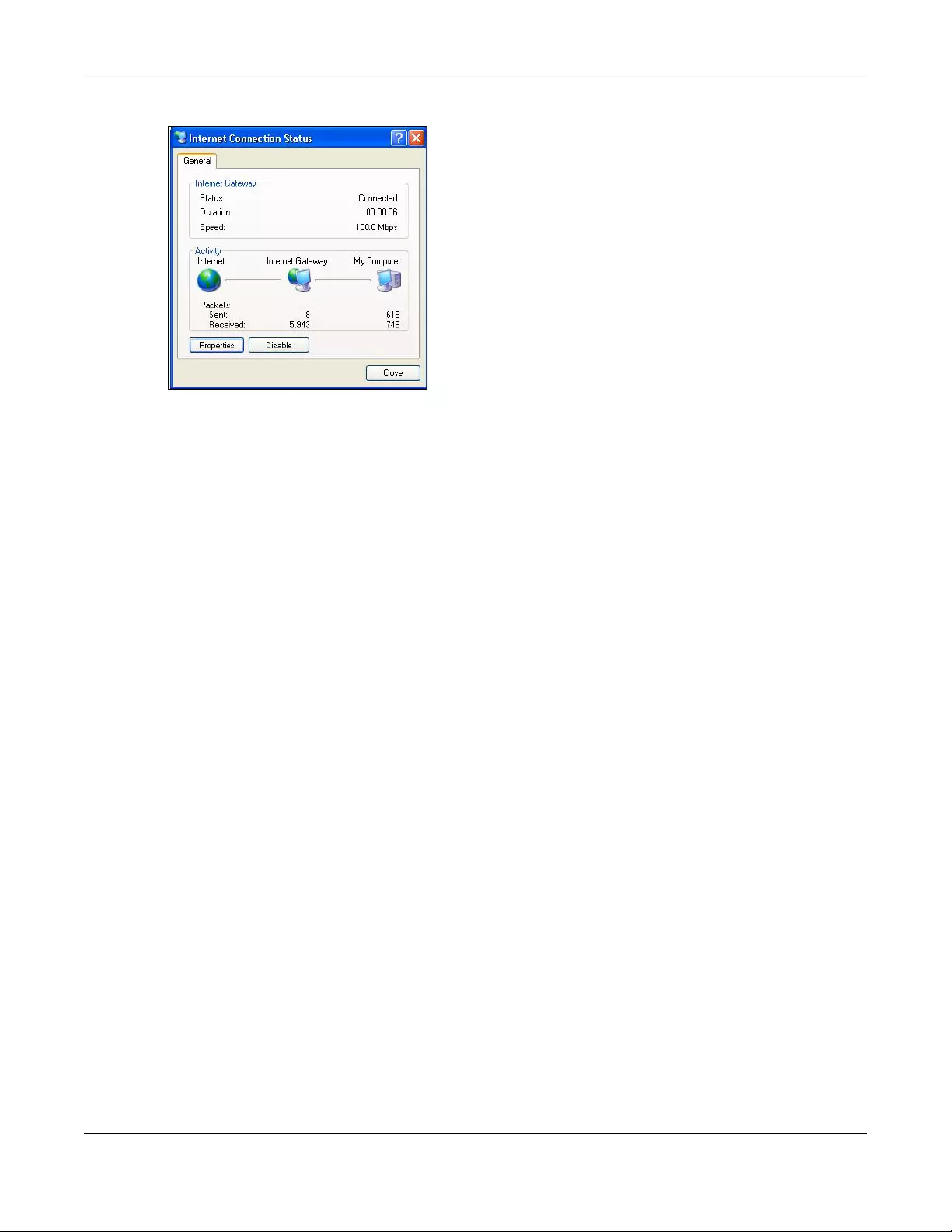
Chapter 16 UPnP
USG/ZyWALL User’s Guide
422
Figure 301 Internet Connection Status
16.4.3 Web Configurator Easy Access
With UPnP, you can access the web-based configurator on the Zyxel Device without finding out the IP
address of the Zyxel Device first. This comes helpful if you do not know the IP address of the Zyxel Device.
Follow the steps below to access the web configurator.
1Click Start and then Control Panel.
2Double-click Network Connections.
3Select My Network Places under Other Places.
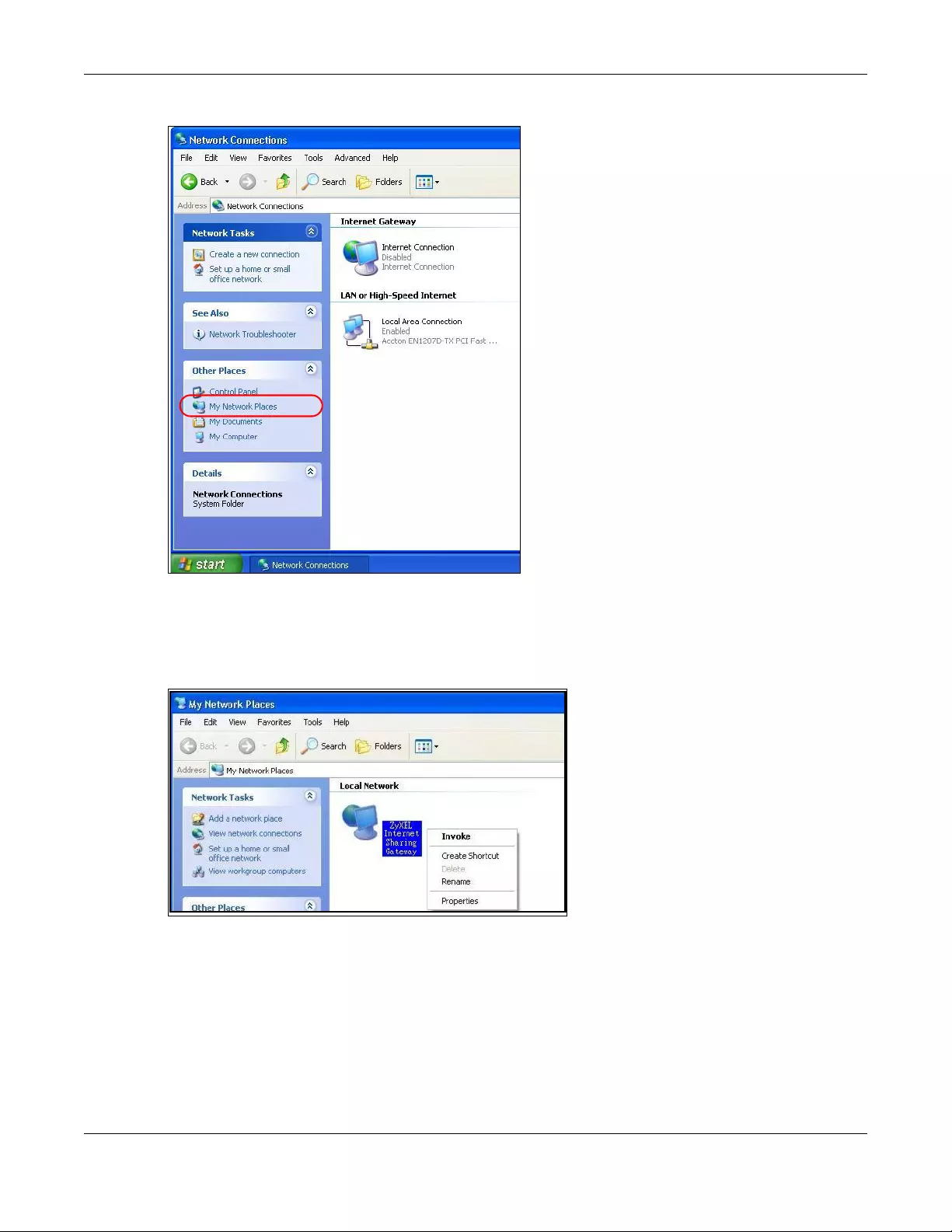
Chapter 16 UPnP
USG/ZyWALL User’s Guide
423
Figure 302 Network Connections
4An icon with the description for each UPnP-enabled device displays under Local Network.
5Right-click on the icon for your Zyxel Device and select Invoke. The web configurator login screen
displays.
Figure 303 Network Connections: My Network Places
6Right-click on the icon for your Zyxel Device and select Properties. A properties window displays with
basic information about the Zyxel Device.
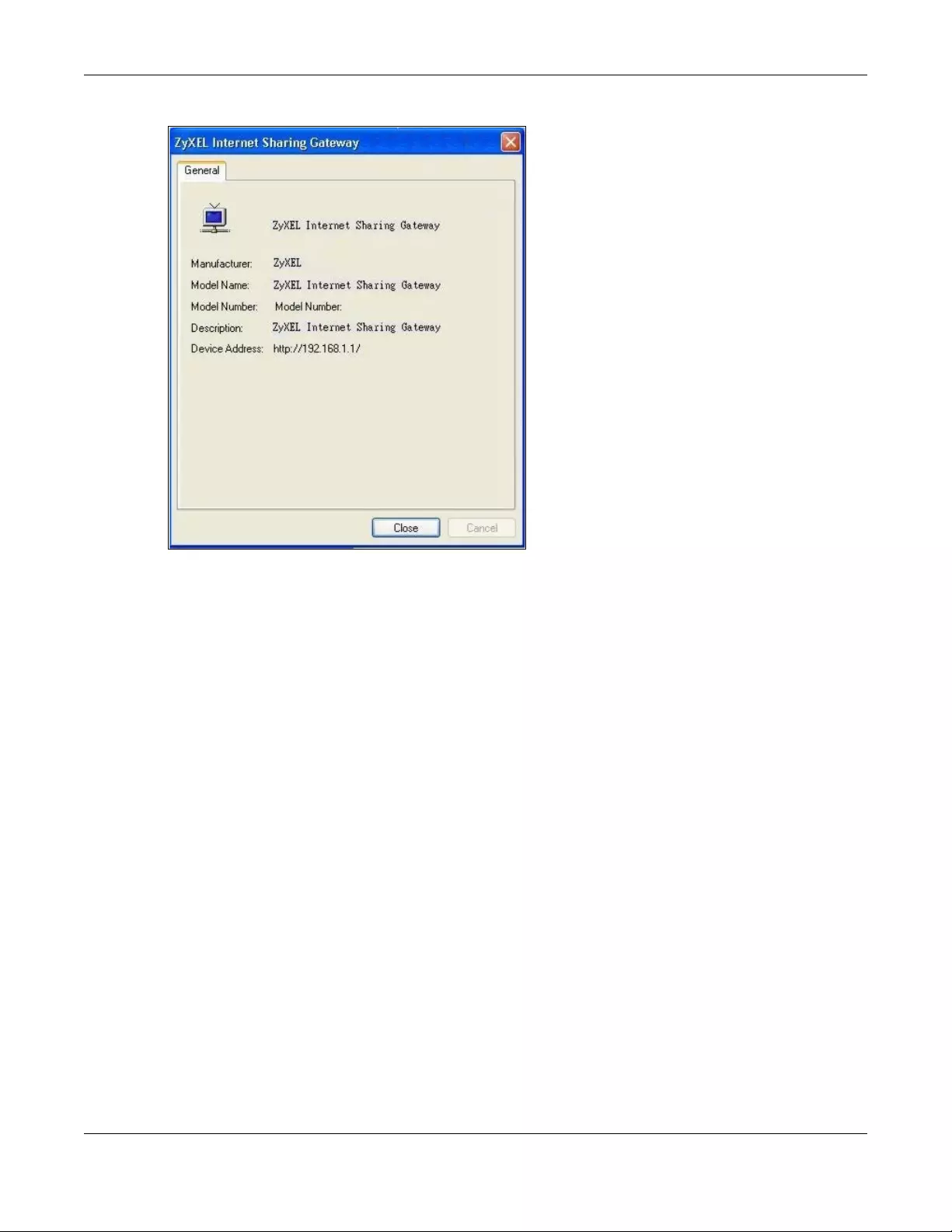
Chapter 16 UPnP
USG/ZyWALL User’s Guide
424
Figure 304 Network Connections: My Network Places: Properties: Example
USG/ZyWALL User’s Guide
425
CHAPTER 17
IP/MAC Binding
17.1 IP/MAC Binding Overview
IP address to MAC address binding helps ensure that only the intended devices get to use privileged IP
addresses. The Zyxel Device uses DHCP to assign IP addresses and records the MAC address it assigned
to each IP address. The Zyxel Device then checks incoming connection attempts against this list. A user
cannot manually assign another IP to his computer and use it to connect to the Zyxel Device.
Suppose you configure access privileges for IP address 192.168.1.27 and use static DHCP to assign it to
Tim’s computer’s MAC address of 12:34:56:78:90:AB. IP/MAC binding drops traffic from any computer
trying to use IP address 192.168.1.27 with another MAC address.
Figure 305 IP/MAC Binding Example
17.1.1 What You Can Do in this Chapter
• Use the Summary and Edit screens (Section 17.2 on page 426) to bind IP addresses to MAC addresses.
• Use the Exempt List screen (Section 17.3 on page 428) to configure ranges of IP addresses to which
the Zyxel Device does not apply IP/MAC binding.
17.1.2 What You Need to Know
DHCP
IP/MAC address bindings are based on the Zyxel Device’s dynamic and static DHCP entries.
MAC: 12:34:56:78:90:AB
Tim IP: 192.168.1.27
MAC: AB:CD:EF:12:34:56
Jim
IP: 192.168.1.27
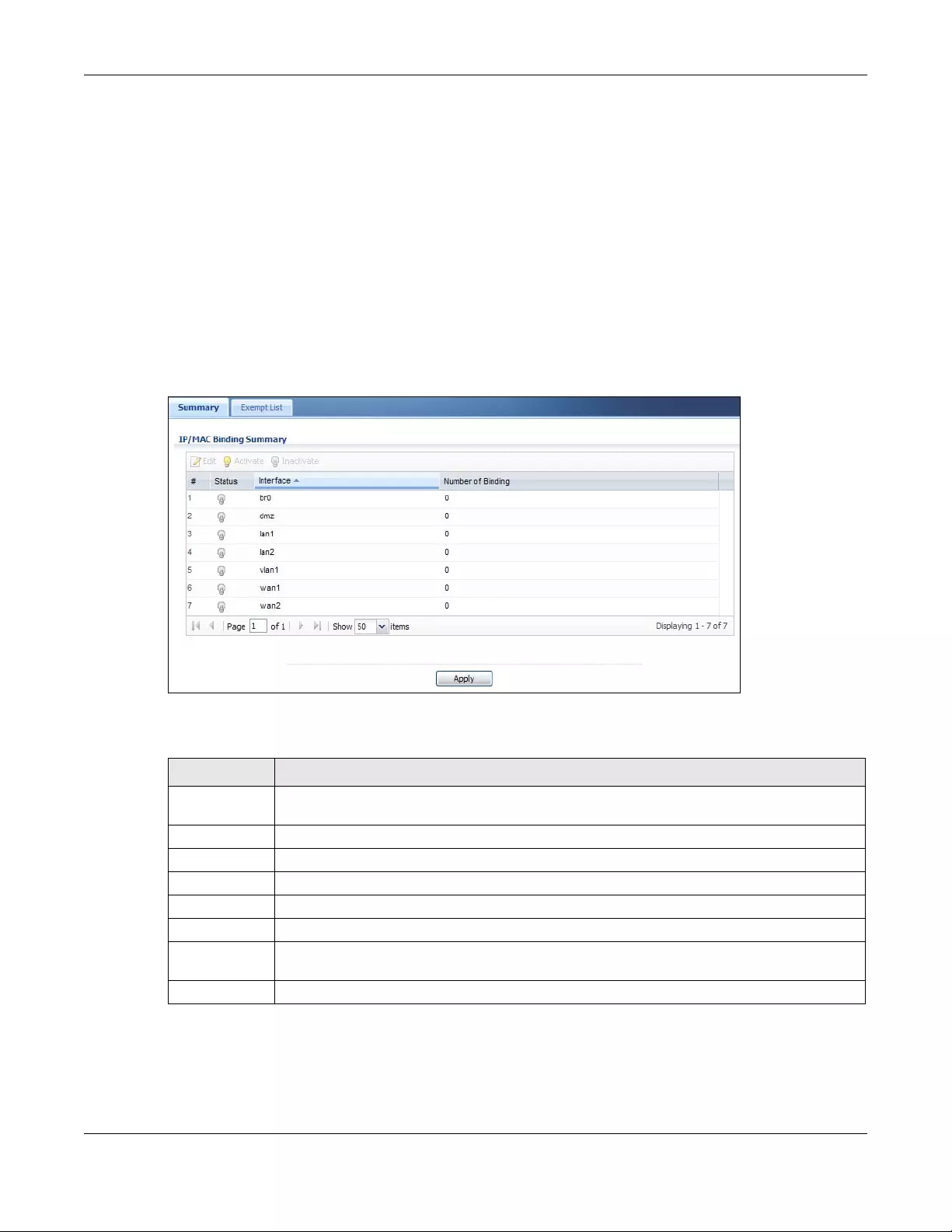
Chapter 17 IP/MAC Binding
USG/ZyWALL User’s Guide
426
Interfaces Used With IP/MAC Binding
IP/MAC address bindings are grouped by interface. You can use IP/MAC binding with Ethernet, bridge,
VLAN, and WLAN interfaces. You can also enable or disable IP/MAC binding and logging in an
interface’s configuration screen.
17.2 IP/MAC Binding Summary
Click Configuration > Network > IP/MAC Binding to open the IP/MAC Binding Summary screen. This
screen lists the total number of IP to MAC address bindings for devices connected to each supported
interface.
Figure 306 Configuration > Network > IP/MAC Binding > Summary
The following table describes the labels in this screen.
17.2.1 IP/MAC Binding Edit
Click Configuration > Network > IP/MAC Binding > Edit to open the IP/MAC Binding Edit screen. Use this
screen to configure an interface’s IP to MAC address binding settings.
Table 151 Configuration > Network > IP/MAC Binding > Summary
LABEL DESCRIPTION
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
# This field is a sequential value, and it is not associated with a specific entry.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
Interface This is the name of an interface that supports IP/MAC binding.
Number of
Binding
This field displays the interface’s total number of IP/MAC bindings and IP addresses that the
interface has assigned by DHCP.
Apply Click Apply to save your changes back to the Zyxel Device.
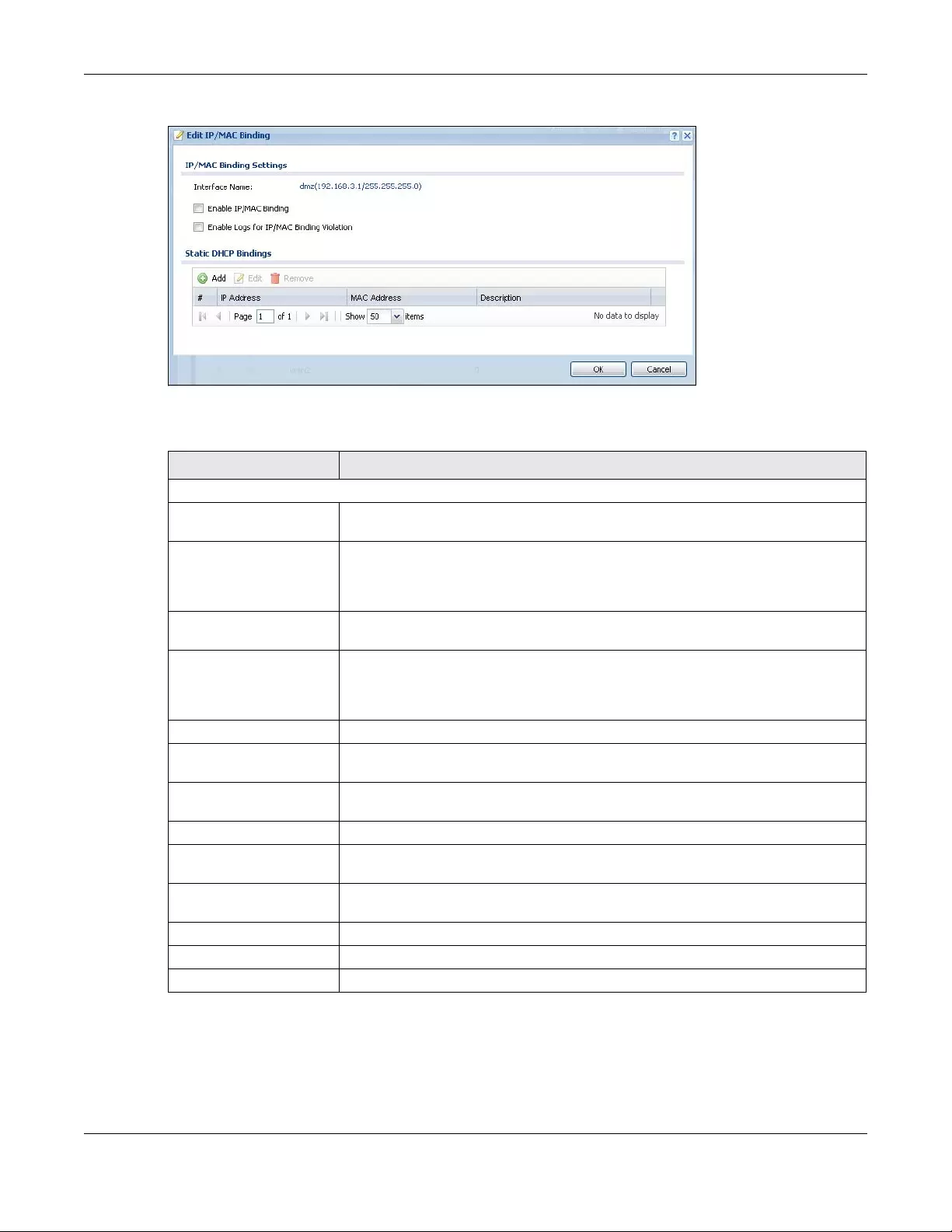
Chapter 17 IP/MAC Binding
USG/ZyWALL User’s Guide
427
Figure 307 Configuration > Network > IP/MAC Binding > Edit
The following table describes the labels in this screen.
17.2.2 Static DHCP Edit
Click Configuration > Network > IP/ MAC Binding > Edit to open the IP/MAC Binding Edit screen. Click the
Add or Edit icon to open the following screen. Use this screen to configure an interface’s IP to MAC
address binding settings.
Table 152 Configuration > Network > IP/MAC Binding > Edit
LABEL DESCRIPTION
IP/MAC Binding Settings
Interface Name This field displays the name of the interface within the Zyxel Device and the interface’s
IP address and subnet mask.
Enable IP/MAC
Binding Select this option to have this interface enforce links between specific IP addresses
and specific MAC addresses. This stops anyone else from manually using a bound IP
address on another device connected to this interface. Use this to make use only the
intended users get to use specific IP addresses.
Enable Logs for IP/
MAC Binding Violation Select this option to have the Zyxel Device generate a log if a device connected to
this interface attempts to use an IP address not assigned by the Zyxel Device.
Static DHCP Bindings This table lists the bound IP and MAC addresses. The Zyxel Device checks this table
when it assigns IP addresses. If the computer’s MAC address is in the table, the Zyxel
Device assigns the corresponding IP address. You can also access this table from the
interface’s edit screen.
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can
modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so.
#This is the index number of the static DHCP entry.
IP Address This is the IP address that the Zyxel Device assigns to a device with the entry’s MAC
address.
MAC Address This is the MAC address of the device to which the Zyxel Device assigns the entry’s IP
address.
Description This helps identify the entry.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
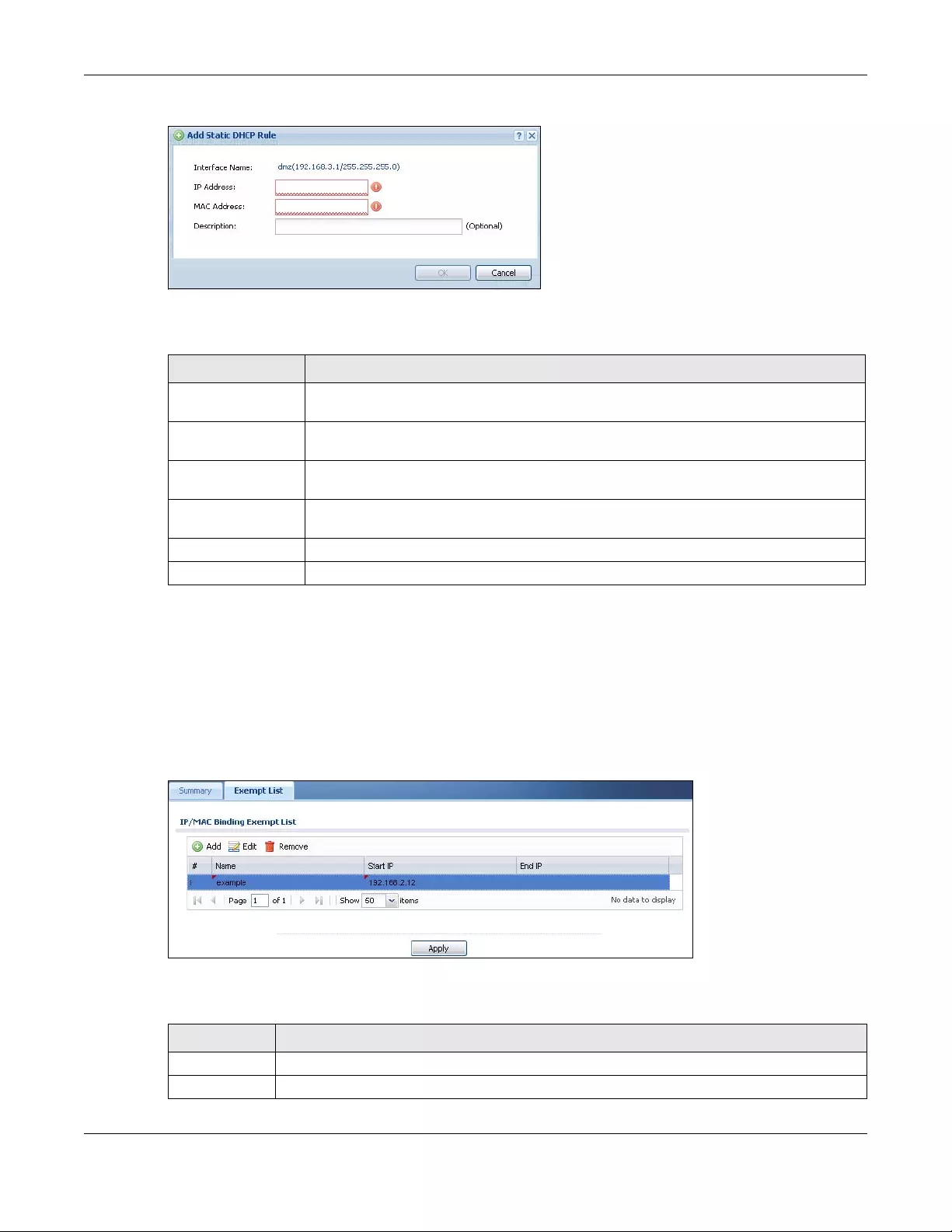
Chapter 17 IP/MAC Binding
USG/ZyWALL User’s Guide
428
Figure 308 Configuration > Network > IP/MAC Binding > Edit > Add
The following table describes the labels in this screen.
17.3 IP/MAC Binding Exempt List
Click Configuration > Network > IP/MAC Binding > Exempt List to open the IP/MAC Binding Exempt List
screen. Use this screen to configure ranges of IP addresses to which the Zyxel Device does not apply IP/
MAC binding.
Figure 309 Configuration > Network > IP/MAC Binding > Exempt List
The following table describes the labels in this screen.
Table 153 Configuration > Network > IP/MAC Binding > Edit > Add
LABEL DESCRIPTION
Interface Name This field displays the name of the interface within the Zyxel Device and the interface’s IP
address and subnet mask.
IP Address Enter the IP address that the Zyxel Device is to assign to a device with the entry’s MAC
address.
MAC Address Enter the MAC address of the device to which the Zyxel Device assigns the entry’s IP
address.
Description Enter up to 64 printable ASCII characters to help identify the entry. For example, you may
want to list the computer’s owner.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 154 Configuration > Network > IP/MAC Binding > Exempt List
LABEL DESCRIPTION
Add Click this to create a new entry.
Edit Click an entry or select it and click Edit to modify the entry’s settings.
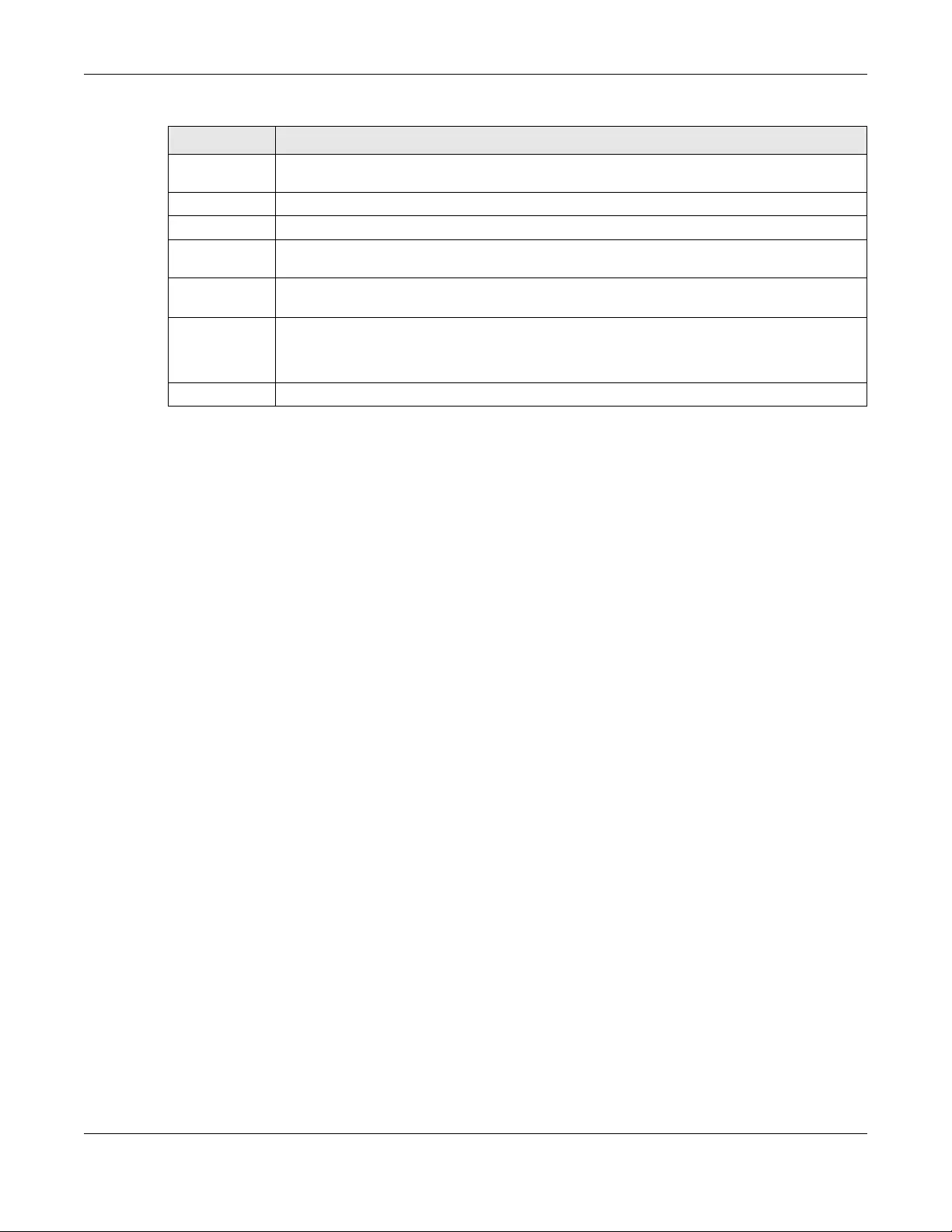
Chapter 17 IP/MAC Binding
USG/ZyWALL User’s Guide
429
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove it
before doing so.
#This is the index number of the IP/MAC binding list entry.
Name Enter a name to help identify this entry.
Start IP Enter the first IP address in a range of IP addresses for which the Zyxel Device does not apply IP/
MAC binding.
End IP Enter the last IP address in a range of IP addresses for which the Zyxel Device does not apply IP/
MAC binding.
Add icon Click the Add icon to add a new entry.
Click the Remove icon to delete an entry. A window displays asking you to confirm that you want
to delete it.
Apply Click Apply to save your changes back to the Zyxel Device.
Table 154 Configuration > Network > IP/MAC Binding > Exempt List (continued)
LABEL DESCRIPTION
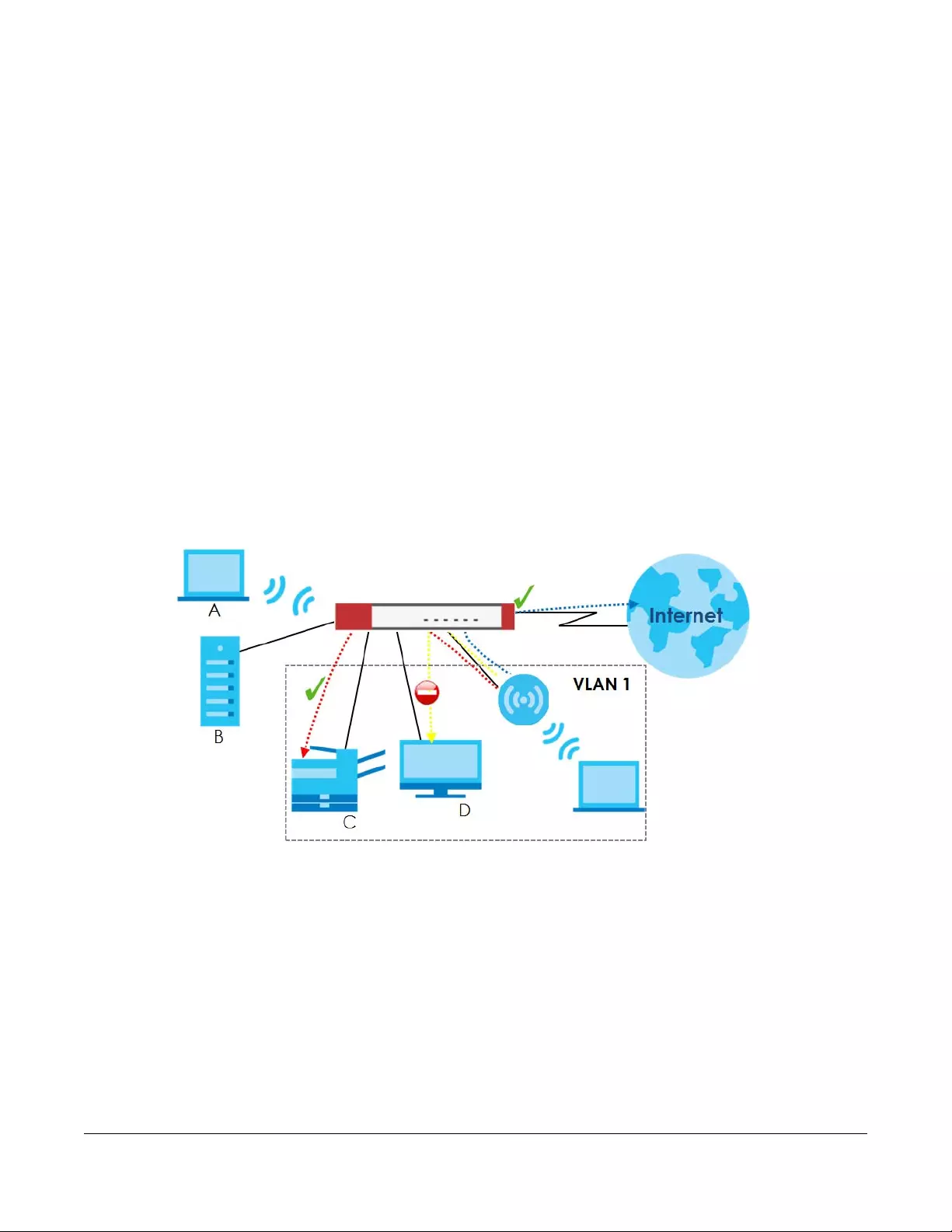
USG/ZyWALL User’s Guide
430
CHAPTER 18
Layer 2 Isolation
18.1 Overview
Layer-2 isolation is used to prevent connected devices from communicating with each other in the Zyxel
Device’s local network(s), except for the devices in the white list, when layer-2 isolation is enabled on
the Zyxel Device and the local interface(s).
Note: The security policy control must be enabled before you can use layer-2 isolation.
In the following example, layer-2 isolation is enabled on the Zyxel Device’s interface Vlan1. A printer, PC
and AP are in the Vlan1. The IP address of network printer (C) is added to the white list. With this setting,
the connected AP then cannot communicate with the PC (D), but can access the network printer (C),
server (B), wireless client (A) and the Internet.
Figure 310 Layer-2 Isolation Application
18.1.1 What You Can Do in this Chapter
• Use the General screen (Section 18.2 on page 430) to enable layer-2 isolation on the Zyxel Device
and the internal interface(s).
• Use the White List screen (Section 18.3 on page 431) to enable and configures the white list.
18.2 Layer-2 Isolation General Screen
This screen allows you to enable Layer-2 isolation on the Zyxel Device and specific internal interface(s).
To access this screen click Configuration > Network > Layer 2 Isolation.
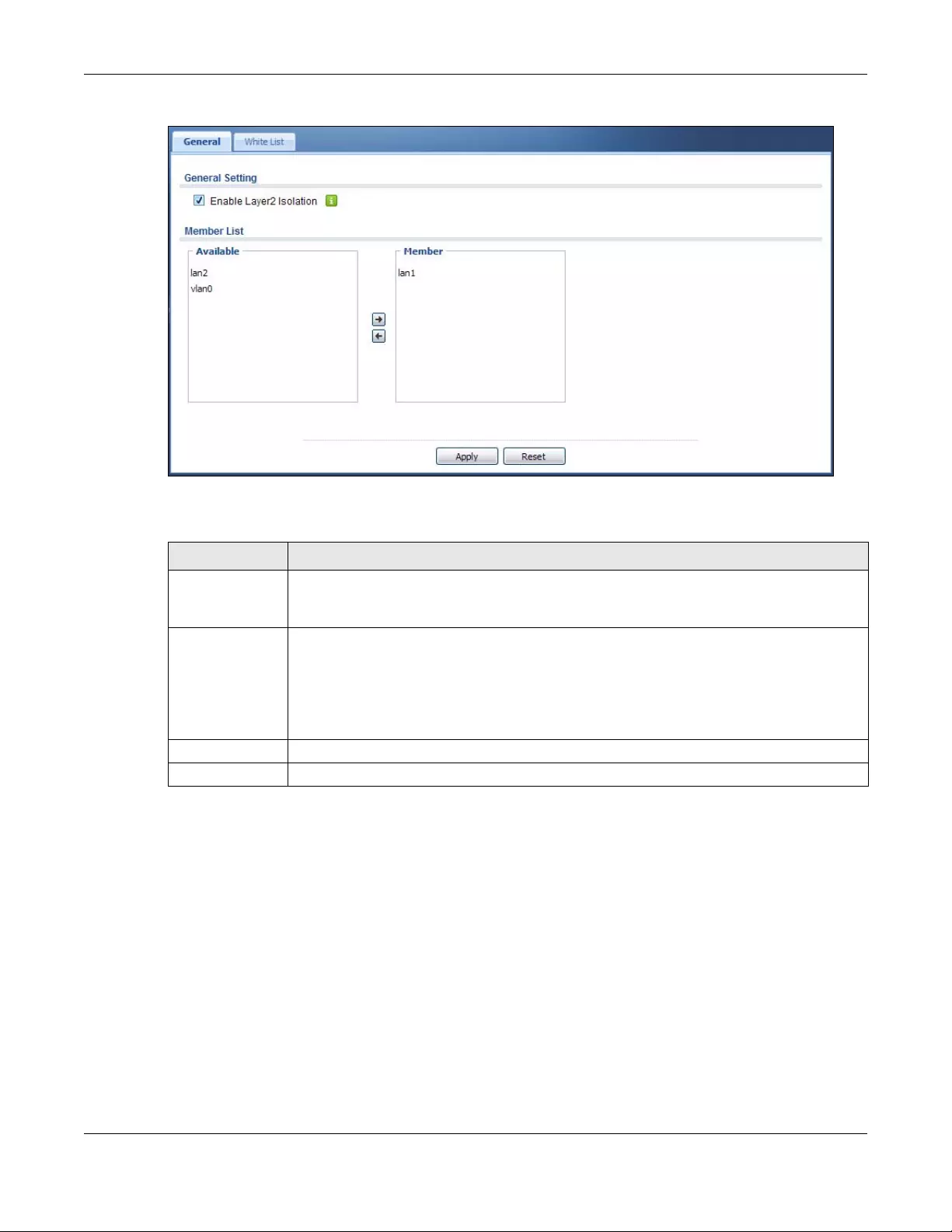
Chapter 18 Layer 2 Isolation
USG/ZyWALL User’s Guide
431
Figure 311 Configuration > Network > Layer 2 Isolation
The following table describes the labels in this screen.
18.3 White List Screen
IP addresses that are not listed in the white list are blocked from communicating with other devices in
the layer-2-isolation-enabled internal interface(s) except for broadcast packets.
To access this screen click Configuration > Network > Layer 2 Isolation > White List.
Table 155 Configuration > Network > Layer 2 Isolation
LABEL DESCRIPTION
Enable Layer2
Isolation
Select this option to turn on the layer-2 isolation feature on the Zyxel Device.
Note: You can enable this feature only when the security policy is enabled.
Member List The Available list displays the name(s) of the internal interface(s) on which you can enable
layer-2 isolation.
To enable layer-2 isolation on an interface, you can double-click a single entry to move it or use
the [Shift] or [Ctrl] key to select multiple entries and click the right arrow button to add to the
Member list. To remove an interface, select the name(s) in the Member list and click the left
arrow button.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
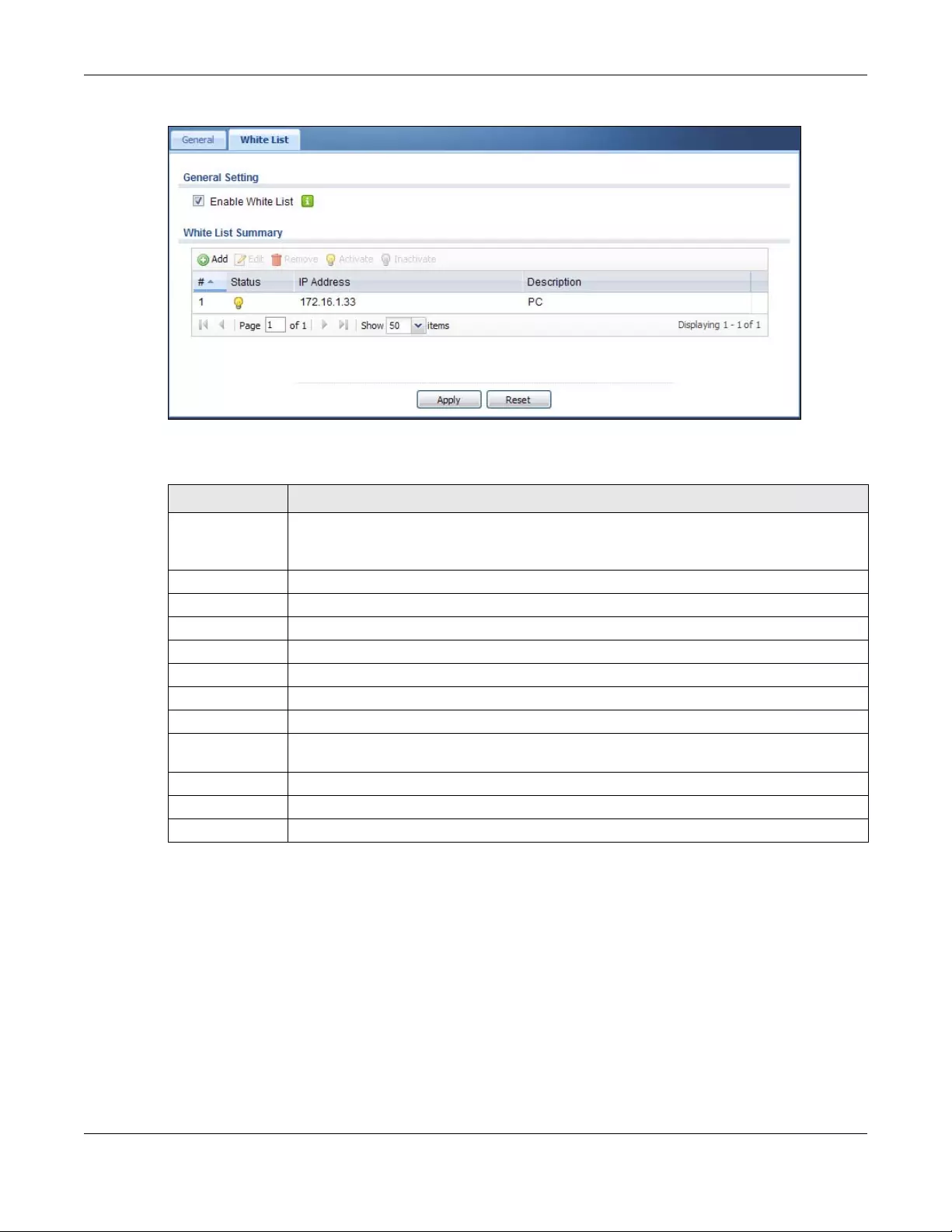
Chapter 18 Layer 2 Isolation
USG/ZyWALL User’s Guide
432
Figure 312 Configuration > Network > Layer 2 Isolation > White List
The following table describes the labels in this screen.
18.3.1 Add/Edit White List Rule
This screen allows you to create a new rule in the white list or edit an existing one. To access this screen,
click the Add button or select an entry from the list and click the Edit button.
Note: You can configure up to 100 white list rules on the Zyxel Device.
Note: You need to know the IP address of each connected device that you want to allow to
be accessed by other devices when layer-2 isolation is enabled.
Table 156 Configuration > Network > Layer 2 Isolation > White List
LABEL DESCRIPTION
Enable White List Select this option to turn on the white list on the Zyxel Device.
Note: You can enable this feature only when the security policy is enabled.
Add Click this to add a new rule.
Edit Click this to edit the selected rule.
Remove Click this to remove the selected rule.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
# This field is a sequential value, and it is not associated with a specific rule.
Status This icon is lit when the rule is active and dimmed when the rule is inactive.
IP Address This field displays the IP address of device that can be accessed by the devices connected to
an internal interface on which layer-2 isolation is enabled.
Description This field displays the description for the IP address in this rule.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
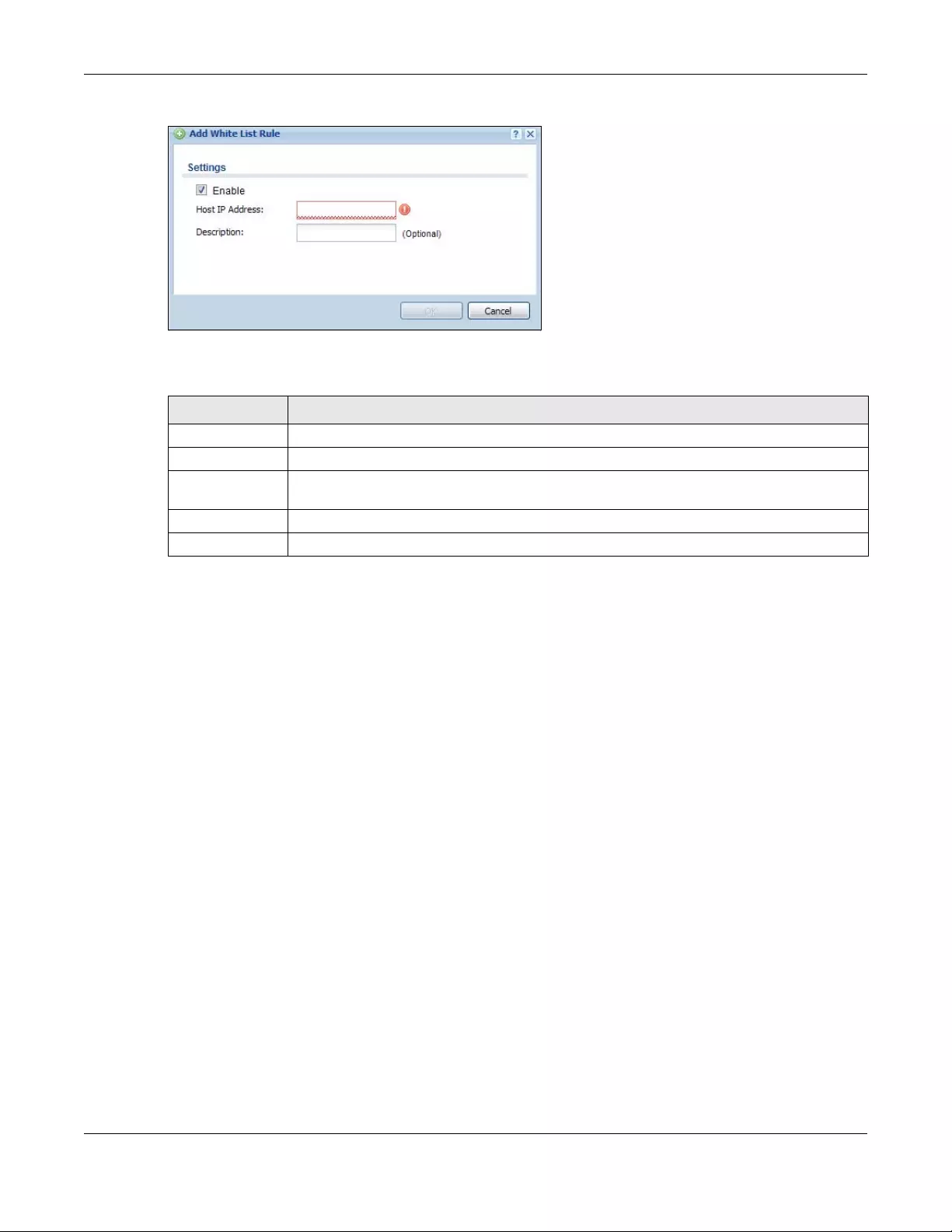
Chapter 18 Layer 2 Isolation
USG/ZyWALL User’s Guide
433
Figure 313 Configuration > Network > Layer 2 Isolation > White List > Add/Edit
The following table describes the labels in this screen.
Table 157 Configuration > Network > Layer 2 Isolation > White List > Add/Edit
LABEL DESCRIPTION
Enable Select this option to turn on the rule.
Host IP Address Enter an IPv4 address associated with this rule.
Description Specify a description for the IP address associated with this rule. Enter up to 60 characters,
spaces and underscores allowed.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
USG/ZyWALL User’s Guide
434
CHAPTER 19
DNS Inbound LB
19.1 DNS Inbound Load Balancing Overview
Inbound load balancing enables the Zyxel Device to respond to a DNS query message with a different
IP address for DNS name resolution. The Zyxel Device checks which member interface has the least load
and responds to the DNS query message with the interface’s IP address.
In the following figure, an Internet host (A) sends a DNS query message to the DNS server (D) in order to
resolve a domain name of www.example.com. DNS server D redirects it to the Zyxel Device (Z)’s WAN1
with an IP address of 1.1.1.1. The Zyxel Device receives the DNS query message and responds to it with
the WAN2’s IP address, 2.2.2.2, because the WAN2 has the least load at that moment.
Another Internet host (B) also sends a DNS query message to ask where www.example.com is. The Zyxel
Device responds to it with the WAN1’s IP address, 1.1.1.1, since WAN1 has the least load this time.
Figure 314 DNS Load Balancing Example
19.1.1 What You Can Do in this Chapter
• Use the Inbound LB screen (see Section 19.2 on page 435) to view a list of the configured DNS load
balancing rules.
• Use the Inbound LB Add/Edit screen (see Section 19.2.1 on page 436) to add or edit a DNS load
balancing rule.
Where is
www.example.com?
Ask 1.1.1.1.
A:
D:
A
D
1.1.1.1
2.2.2.2
W
Z
Where is
www.example.com?
It’s 2.2.2.2.
A:
Z:
1
2
3
B
D
1.1.1.1
2.2.2.2
W
Z
1
2
3
Where is
www.example.com?
Ask 1.1.1.1.
B:
D:
Where is
www.example.com?
It’s 1.1.1.1
B:
Z:
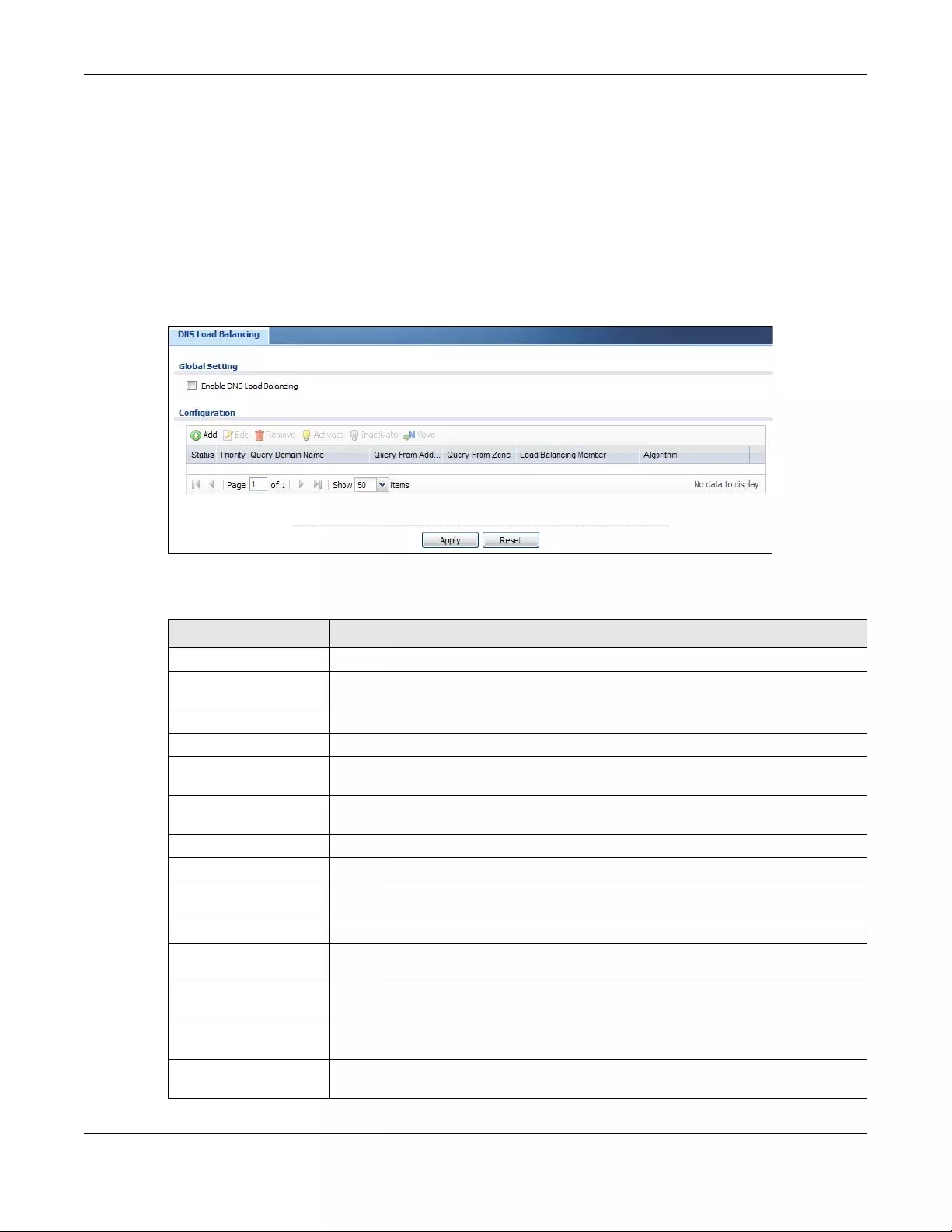
Chapter 19 DNS Inbound LB
USG/ZyWALL User’s Guide
435
19.2 The DNS Inbound LB Screen
The Inbound LB screen provides a summary of all DNS load balancing rules and the details. You can also
use this screen to add, edit, or remove the rules. Click Configuration > Network > Inb ound LB to open the
following screen.
Note: After you finish the inbound load balancing settings, go to security policy and NAT
screens to configure the corresponding rule and virtual server to allow the Internet users
to access your internal servers.
Figure 315 Configuration > Network > DNS Inbound LB
The following table describes the labels in this screen.
Table 158 Configuration > Network > DNS Inbound LB
LABEL DESCRIPTION
Global Setting
Enable DNS Load
Balancing
Select this to enable DNS load balancing.
Configuration
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify
the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Move To move an entry to a different number in the list, click the Move icon. In the field that
appears, specify the number to which you want to move the entry.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
Priority This field displays the order in which the Zyxel Device checks the member interfaces of
this DNS load balancing rule.
Query Domain Name This field displays the domain name for which the Zyxel Device manages load
balancing between the specified interfaces.
Query From Address This field displays the source IP address of the DNS query messages to which the Zyxel
Device applies the DNS load balancing rule.
Query From Zone The Zyxel Device applies the DNS load balancing rule to the query messages received
from this zone.
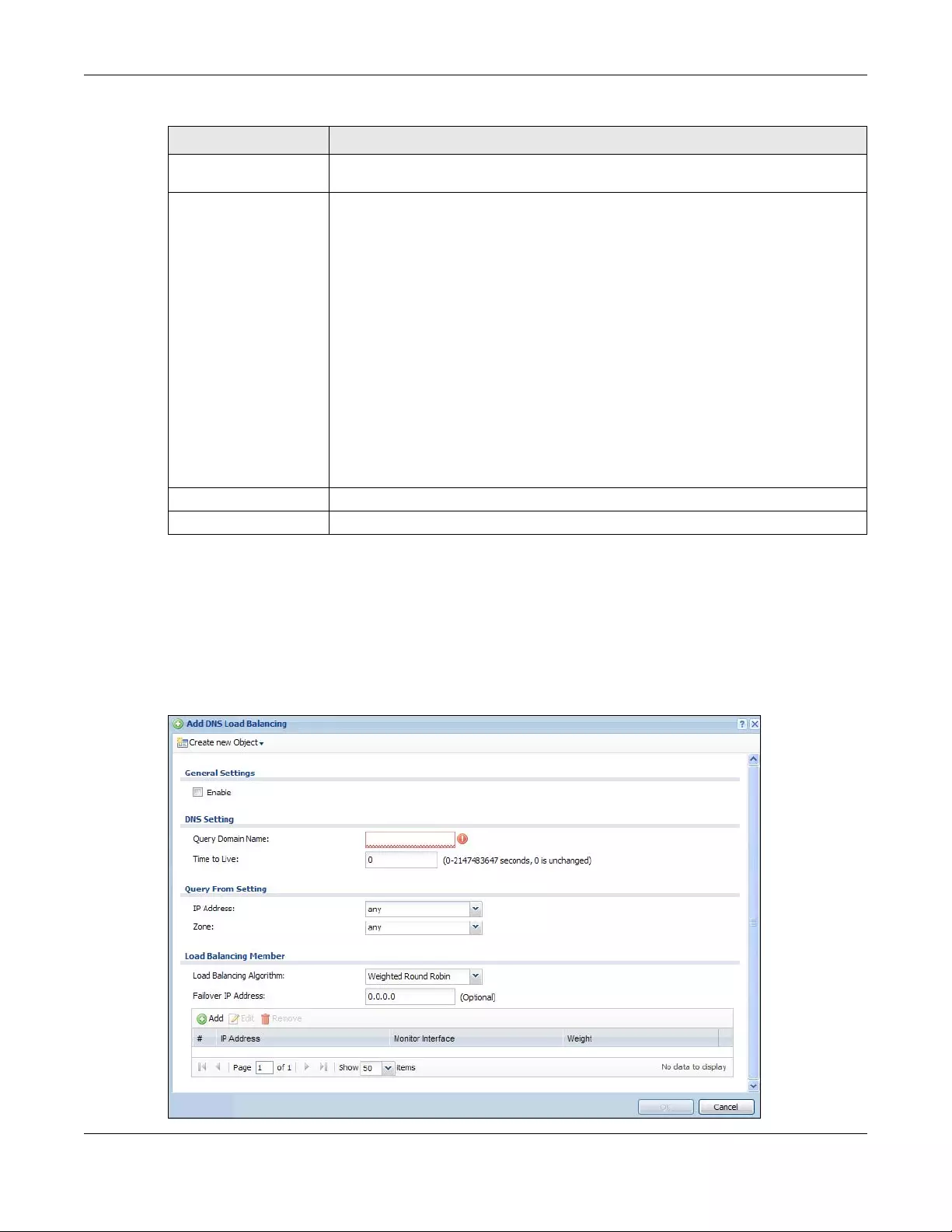
Chapter 19 DNS Inbound LB
USG/ZyWALL User’s Guide
436
19.2.1 The DNS Inbound LB Add/Edit Screen
The Add DNS Load Balancing screen allows you to add a domain name for which the Zyxel Device
manages load balancing between the specified interfaces. You can configure the Zyxel Device to
apply DNS load balancing to some specific hosts only by configuring the Query From settings. Click
Configuration > Network > Inbound LB and then the Add or Edit icon to open this screen.
Figure 316 Configuration > Network > DNS Inbound LB > Add
Load Balancing
Member
This field displays the member interfaces which the Zyxel Device manages for load
balancing.
Algorithm This field displays the load balancing method the Zyxel Device uses for this DNS load
balancing rule.
Weighted Round Robin - Each member interface is assigned a weight. An interface with
a larger weight gets more chances to transmit traffic than an interface with a smaller
weight. For example, if the weight ratio of wan1 and wan2 interfaces is 2:1, the Zyxel
Device chooses wan1 for 2 sessions’ traffic and wan2 for 1 session’s traffic in each round
of 3 new sessions.
Least Connection - The Zyxel Device chooses choose a member interface which is
handling the least number of sessions.
Least Load - Outbound - The Zyxel Device chooses a member interface which is
handling the least amount of outgoing traffic.
Least Load - Inbound - The Zyxel Device chooses a member interface which is handling
the least amount of incoming traffic.
Least Load - Total - The Zyxel Device chooses a member interface which is handling the
least amount of outgoing and incoming traffic.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
Table 158 Configuration > Network > DNS Inbound LB (continued)
LABEL DESCRIPTION
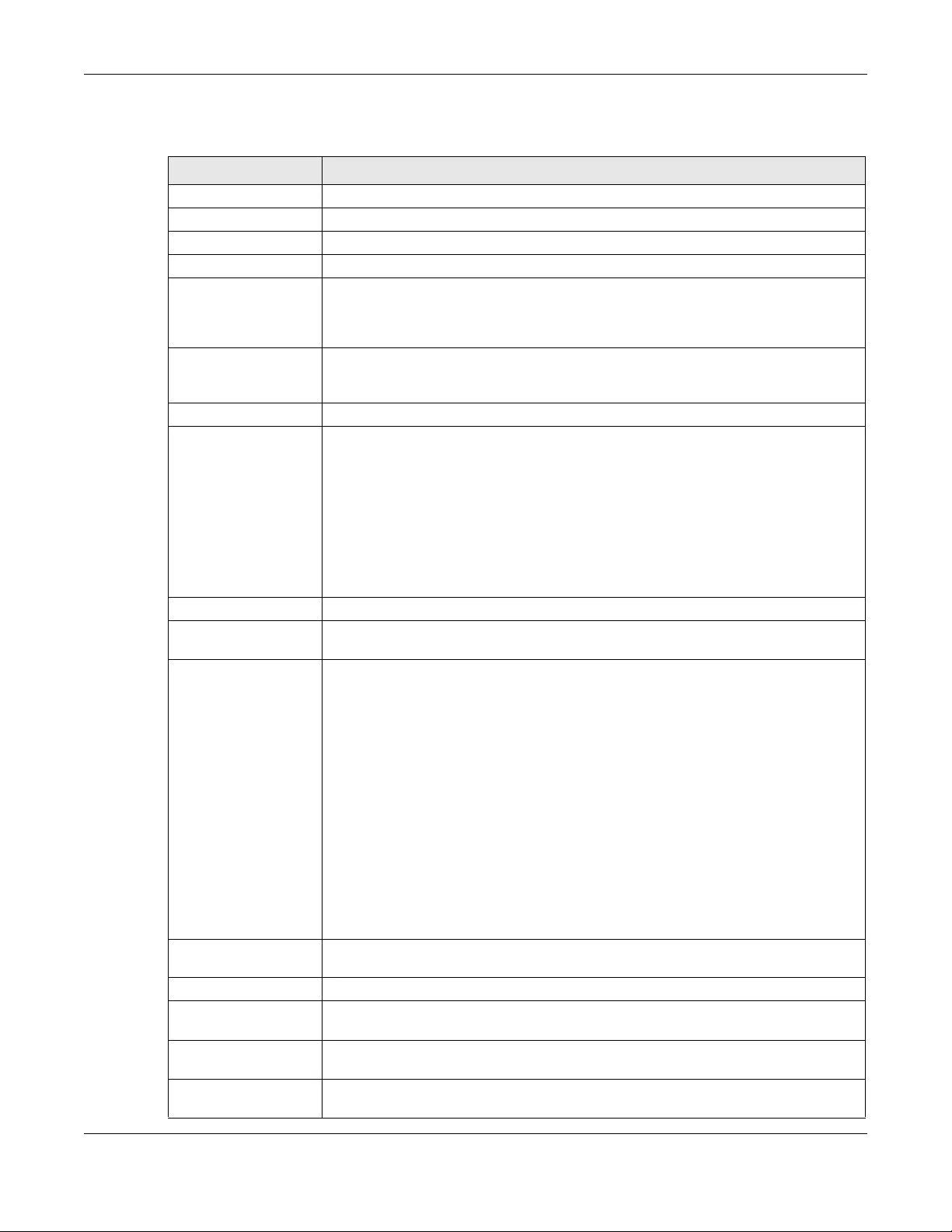
Chapter 19 DNS Inbound LB
USG/ZyWALL User’s Guide
437
The following table describes the labels in this screen.
Table 159 Configuration > Network > DNS Inbound LB > Add/Edit
LABEL DESCRIPTION
Create New Object Use this to configure any new setting objects that you need to use in this screen.
General Settings
Enable Select this to enable this DNS load balancing rule.
DNS Setting
Query Domain Name Type up to 255 characters for a domain name for which you want the Zyxel Device to
manage DNS load balancing. You can use a wildcard (*) to let multiple domains match
the name. For example, use *.example.com to specify any domain name that ends with
“example.com” would match.
Time to Live Enter the number of seconds the Zyxel Device recommends DNS request hosts to keep
the DNS entry in their caches before removing it. Enter 0 to have the Zyxel Device not
recommend this so the DNS request hosts will follow their DNS server’s TTL setting.
Query From Setting
IP Address Enter the IP address of a computer or a DNS server which makes the DNS queries upon
which to apply this rule.
DNS servers process client queries using recursion or iteration:
• In recursion, DNS servers make recursive queries on behalf of clients. So you have to
configure this field to the DNS server’s IP address when recursion is used.
• In iteration, a client asks the DNS server and expects the best and immediate answer
without the DNS server contacting other DNS servers. If the primary DNS server cannot
provide the best answer, the client makes iteration queries to other configured DNS
servers to resolve the name. You have to configure this field to the client’s IP address
when iteration is used.
Zone Select the zone of DNS query messages upon which to apply this rule.
Load Balancing
Member
Load Balancing
Algorithm
Select a load balancing method to use from the drop-down list box.
Select Weighted Round Robin to balance the traffic load between interfaces based on
their respective weights. An interface with a larger weight gets more chances to transmit
traffic than an interface with a smaller weight. For example, if the weight ratio of wan1
and wan2 interfaces is 2:1, the Zyxel Device chooses wan1 for 2 sessions’ traffic and
wan2 for every session’s traffic in each round of 3 new sessions.
Select Least Connection to have the Zyxel Device choose the member interface which is
handling the least number of sessions.
Select Least Load - Outbound to have the Zyxel Device choose the member interface
which is handling the least amount of outgoing traffic.
Select Least Load - Inbound to have the Zyxel Device choose the member interface
which is handling the least amount of incoming traffic.
Select Least Load - Total to have the Zyxel Device choose the member interface which is
handling the least amount of outgoing and incoming traffic.
Failover IP Address Enter an alternate IP address with which the Zyxel Device will respond to a DNS query
message when the load balancing algorithm cannot find any available interface.
Add Click this to create a new member interface for this rule.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify
the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so.
# This field displays the order in which the Zyxel Device checks this rule’s member
interfaces.
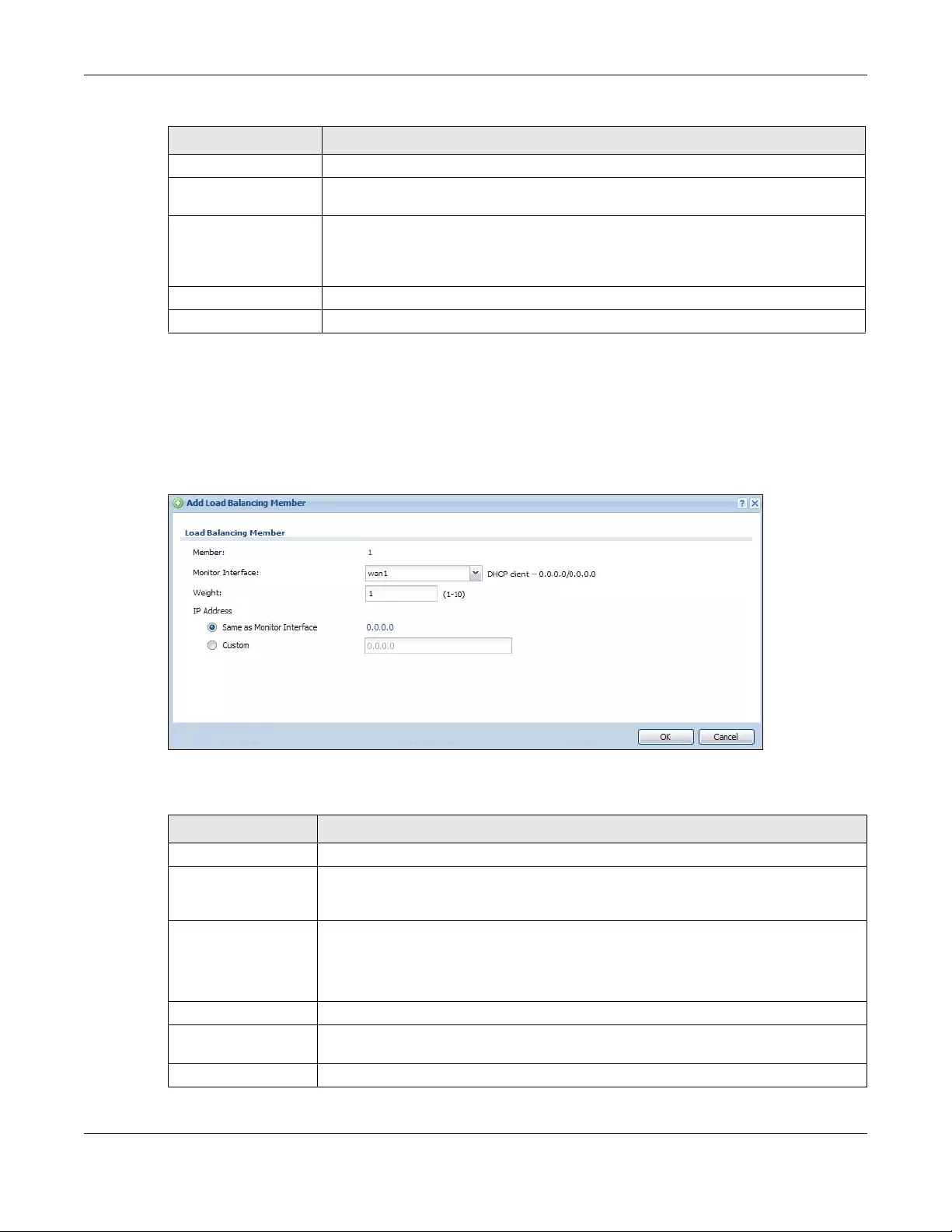
Chapter 19 DNS Inbound LB
USG/ZyWALL User’s Guide
438
19.2.2 The DNS Inbound LB Add/Edit Member Screen
The Add Load Balancing Member screen allows you to add a member interface for the DNS load
balancing rule. Click Configuration > Network > DNS Inbound LB > Add or Edit and then an Add or Edit
icon to open this screen.
Figure 317 Configuration > Network > DNS Inbound LB > Add/Edit > Add
The following table describes the labels in this screen.
IP Address This field displays the IP address of the member interface.
Monitor Interface This field displays the name of the member interface. The Zyxel Device manages load
balancing between the member interfaces.
Weight This field is available if you selected Weighted Round Robin as the load balancing
algorithm. This field displays the weight of the member interface. An interface with a
larger weight gets more chances to transmit traffic than an interface with a smaller
weight.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 159 Configuration > Network > DNS Inbound LB > Add/Edit (continued)
LABEL DESCRIPTION
Table 160 Configuration > Network > DNS Inbound LB > Add/Edit > Add/Edit
LABEL DESCRIPTION
Member The Zyxel Device checks each member interface’s loading in the order displayed here.
Monitor Interface Select an interface to associate it with the DNS load balancing rule. This field also displays
whether the IP address is a static IP address (Static), dynamically assigned (Dynamic) or
obtained from a DHCP server (DHCP Client), as well as the IP address and subnet mask.
Weight This field is available if you selected Weighted Round Robin for the load balancing
algorithm.
Specify the weight of the member interface. An interface with a larger weight gets more
chances to transmit traffic than an interface with a smaller weight.
IP Address
Same as Monitor
Interface
Select this to send the IP address displayed in the Monitor Interface field to the DNS query
senders.
Custom Select this and enter another IP address to send to the DNS query senders.
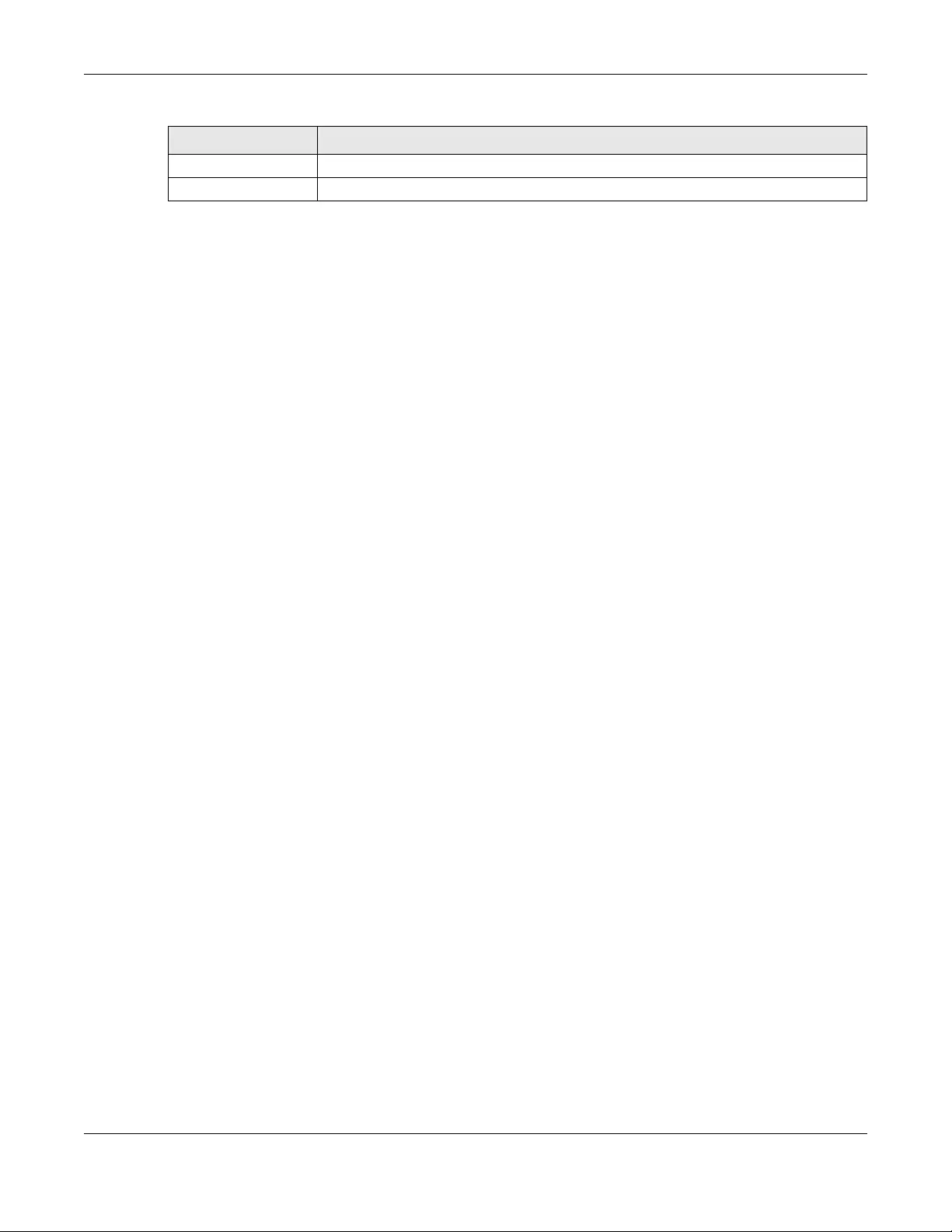
Chapter 19 DNS Inbound LB
USG/ZyWALL User’s Guide
439
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 160 Configuration > Network > DNS Inbound LB > Add/Edit > Add/Edit (continued)
LABEL DESCRIPTION

USG/ZyWALL User’s Guide
440
CHAPTER 20
Web Authentication
20.1 Web Auth Overview
Web authentication can intercept network traffic, according to the authentication policies, until the
user authenticates his or her connection, usually through a specifically designated login web page. This
means all web page requests can initially be redirected to a special web page that requires users to
authenticate their sessions. Once authentication is successful, they can then connect to the rest of the
network or Internet.
As soon as a user attempt to open a web page, the Zyxel Device reroutes his/her browser to a web
portal page that prompts him/her to log in.
Figure 318 Web Authentication Example
The web authentication page only appears once per authentication session. Unless a user session times
out or he/she closes the connection, he or she generally will not see it again during the same session.
20.1.1 What You Can Do in this Chapter
• Use the Configuration > Web Authentication screens (Section 20.2 on page 441) to create and
manage web authentication policies.
• Use the Configuration > Web Authentication > SSO screen (Section 20.3 on page 457) to configure
how the Zyxel Device communicates with a Single Sign-On agent.

Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
441
20.1.2 What You Need to Know
Single Sign-On
A SSO (Single Sign On) agent integrates Domain Controller and Zyxel Device authentication
mechanisms, so that users just need to log in once (single) to get access to permitted resources.
Forced User Authentication
Instead of making users for which user-aware policies have been configured go to the Zyxel Device
Login screen manually, you can configure the Zyxel Device to display the Login screen automatically
whenever it routes HTTP traffic for anyone who has not logged in yet.
Note: This works with HTTP traffic only. The Zyxel Device does not display the Login screen
when users attempt to send other kinds of traffic.
The Zyxel Device does not automatically route the request that prompted the login, however, so users
have to make this request again.
20.2 Web Authentication General Screen
The Web Authentication General screen displays the general web portal settings and web
authentication policies you have configured on the Zyxel Device. Use this screen to enable web
authentication on the Zyxel Device.
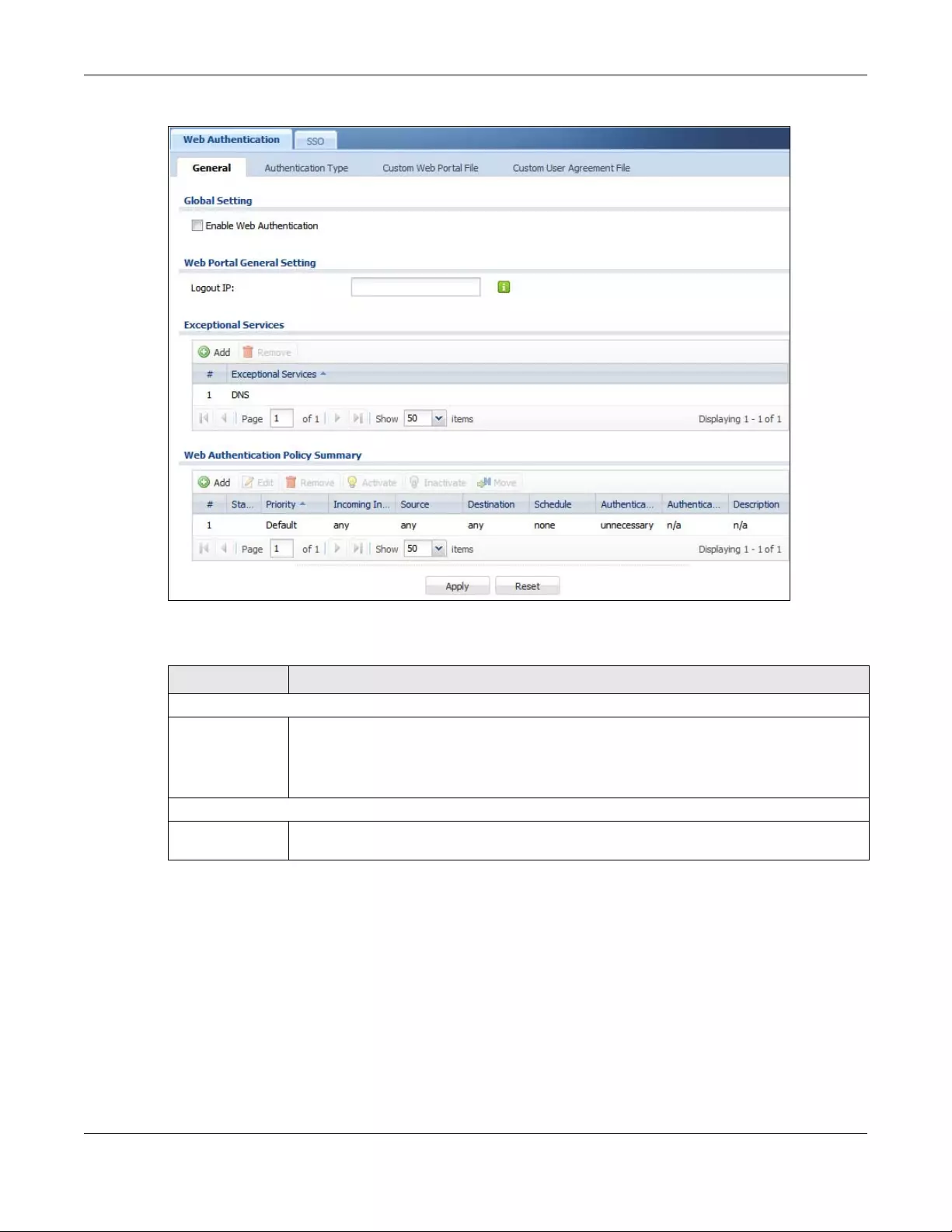
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
442
Figure 319 Configuration > Web Authentication > General
The following table gives an overview of the objects you can configure.
Table 161 Configuration > Web Authentication > General
LABEL DESCRIPTION
Global Setting
Enable Web
Authentication
Select the check box to turn on the web authentication feature. Otherwise, clear the check
box to turn it off.
Once enabled, all network traffic is blocked until a client authenticates with the Zyxel Device
through the specifically designated web portal or user agreement page.
Web Portal General Setting
Logout IP Specify an IP address that users can use to terminate their sessions manually by entering the IP
address in the address bar of the web browser.
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
443
Exceptional
Services
Use this table to list services that users can access without logging in.
Click Add to change the list’s membership. A screen appears. Available services appear on
the left. Select any services you want users to be able to access without logging in and click
the right arrow button to add them. The member services are on the right. Select any service
that you want to remove from the member list, and click the left arrow button to remove them.
Keeping DNS as a member allows users’ computers to resolve domain names into IP addresses.
Figure 320 Configuration > Web Authentication > Add Exceptional Service
In the table, select one or more entries and click Remove to delete it or them.
Web
Authentication
Policy Summary
Use this table to manage the Zyxel Device’s list of web authentication policies.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after the
selected entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Move To move an entry to a different number in the list, click the Move icon. In the field that appears,
specify the number to which you want to move the interface.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
Priority This is the position of the authentication policy in the list. The priority is important as the policies
are applied in order of priority. Default displays for the default authentication policy that the
Zyxel Device uses on traffic that does not match any exceptional service or other
authentication policy. You can edit the default rule but not delete it.
Incoming
Interface
This field displays the interface on which packets for this policy are received.
Source This displays the source address object to which this policy applies.
Destination This displays the destination address object to which this policy applies.
Schedule This field displays the schedule object that dictates when the policy applies. none means the
policy is active at all times if enabled.
Table 161 Configuration > Web Authentication > General (continued)
LABEL DESCRIPTION
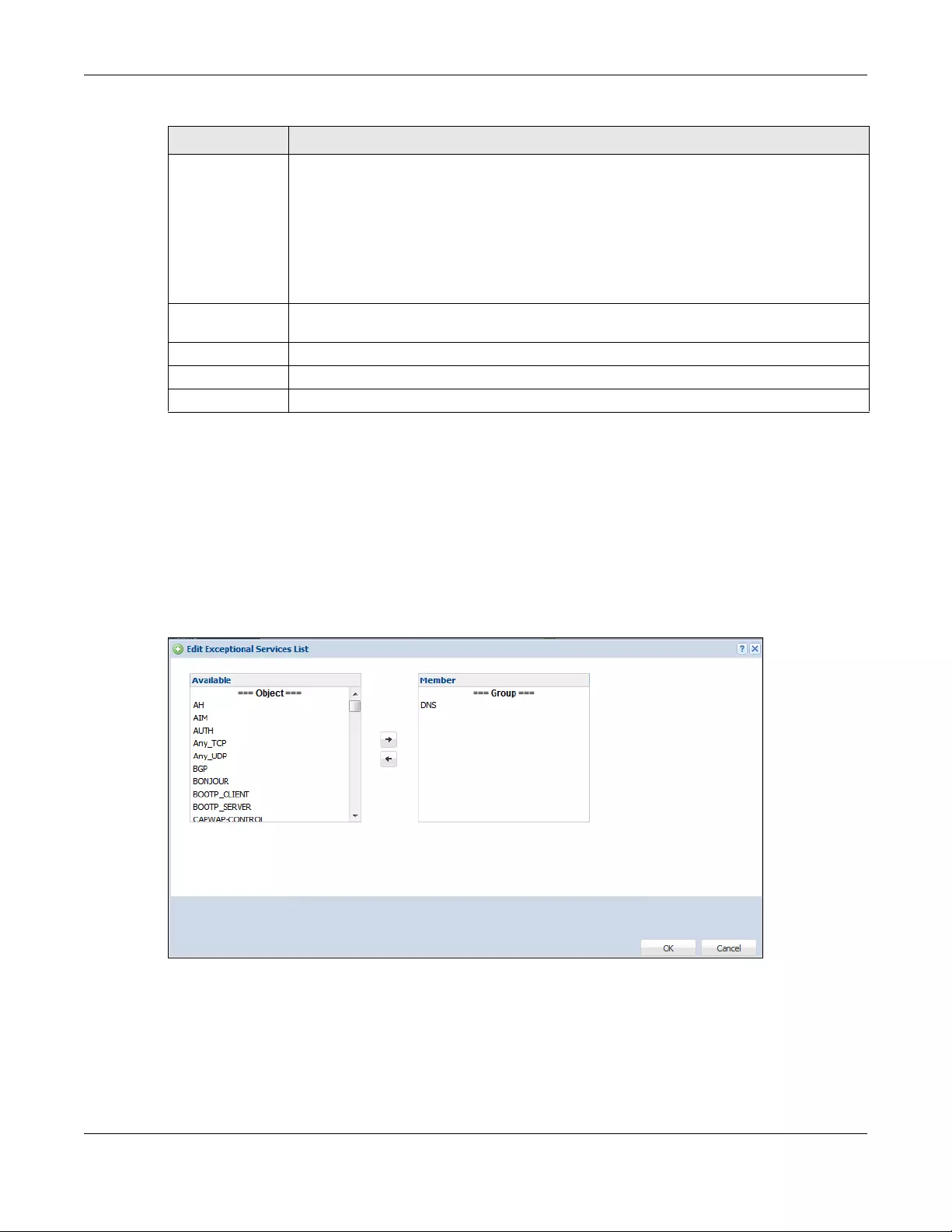
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
444
Creating Exceptional Services
This screen lists services that users can access without logging in. Click Add under Exceptional Services in
the previous screen to display this screen. You can change the list’s membership here. Available
services appear on the left. Select any services you want users to be able to access without logging in
and click the right arrow button -> to add them. The member services are on the right. Select any
service that you want to remove from the member list, and click the left arrow <- button to remove
them. Then click OK to apply the changes and return to the main Web Authentication screen.
Alternatively, click Cancel to discard the changes and return to the main Web Authentication screen.
Figure 321 Configuration > Web Authentication > General > Add Exceptional Service
Creating/Editing an Authentication Policy
Open the Configuration > Web Authentication > General screen, then click the Add icon or select an
entry and click the Edit icon in the Web Authentication Policy Summary section to open the Auth. Policy
Add/Edit screen. Use this screen to configure an authentication policy.
Authentication This field displays the authentication requirement for users when their traffic matches this policy.
unnecessary - Users do not need to be authenticated.
required - Users need to be authenticated. They must manually go to the login screen or user
agreement page. The Zyxel Device will not redirect them to the login screen.
force - Users need to be authenticated. The Zyxel Device automatically displays the login
screen or user agreement page whenever it routes HTTP traffic for users who have not logged
in yet.
Authentication
Type
This field displays the name of the authentication type profile used in this policy to define how
users authenticate their sessions. It shows n/a if Authentication is set to unnecessary.
Description If the entry has a description configured, it displays here. This is n/a for the default policy.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
Table 161 Configuration > Web Authentication > General (continued)
LABEL DESCRIPTION
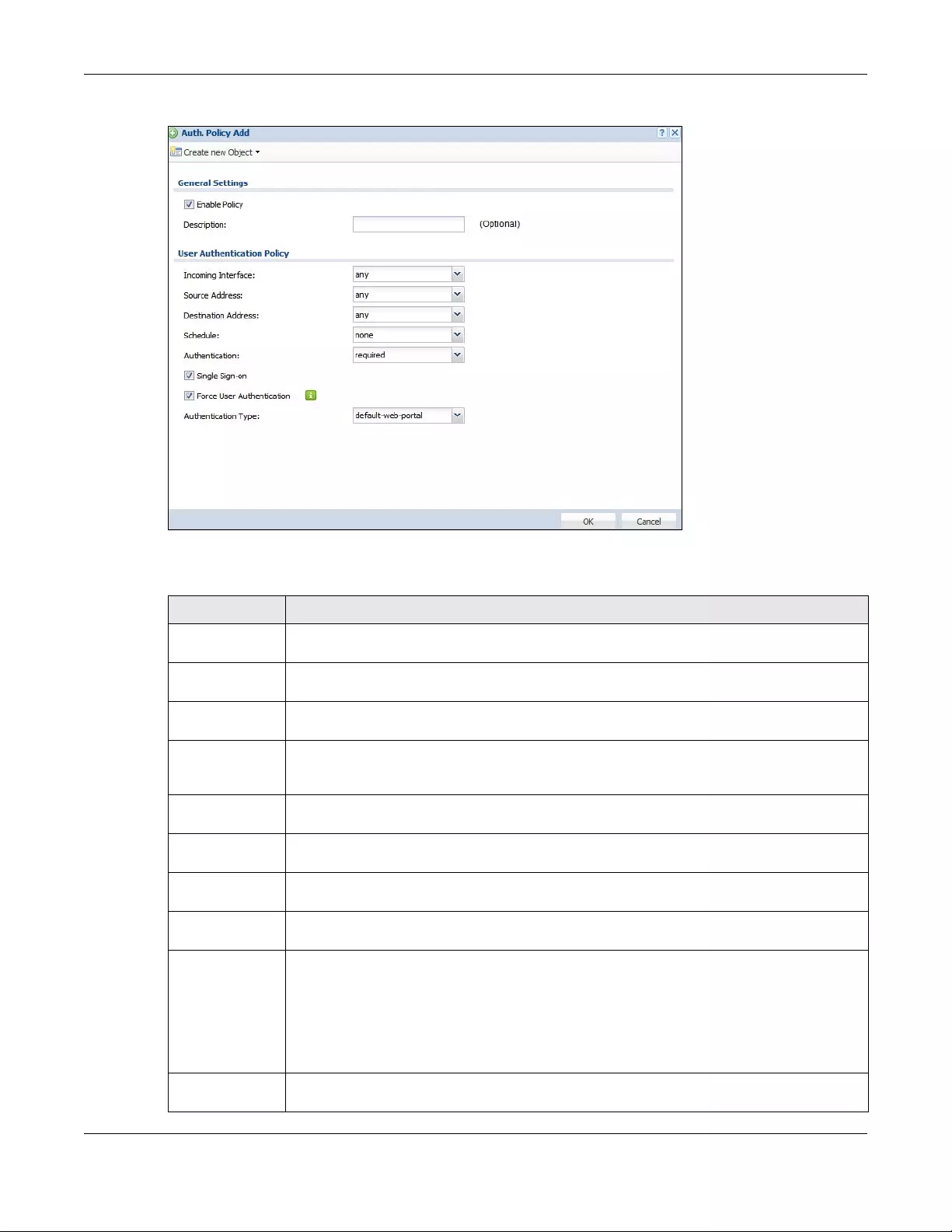
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
445
Figure 322 Configuration > Web Authentication > General > Add Authentication Policy
The following table gives an overview of the objects you can configure.
Table 162 Configuration > Web Authentication > General > Add Authentication Policy
LABEL DESCRIPTION
Create new
Object
Use to configure any new settings objects that you need to use in this screen. Select Address or
Schedule.
Enable Policy Select this check box to activate the authentication policy. This field is available for user-
configured policies.
Description Enter a descriptive name of up to 60 printable ASCII characters for the policy. Spaces are
allowed. This field is available for user-configured policies.
User
Authentication
Policy
Use this section of the screen to determine which traffic requires (or does not require) the
senders to be authenticated in order to be routed.
Incoming
Interface
Select the interface on which packets for this policy are received.
Source Address Select a source address or address group for whom this policy applies. Select any if the policy is
effective for every source. This is any and not configurable for the default policy.
Destination
Address
Select a destination address or address group for whom this policy applies. Select any if the
policy is effective for every destination. This is any and not configurable for the default policy.
Schedule Select a schedule that defines when the policy applies. Otherwise, select none and the rule is
always effective. This is none and not configurable for the default policy.
Authentication Select the authentication requirement for users when their traffic matches this policy.
unnecessary - Users do not need to be authenticated.
required - Users need to be authenticated. If Force User Authentication is selected, all HTTP
traffic from unauthenticated users is redirected to a default or user-defined login page.
Otherwise, they must manually go to the login screen. The Zyxel Device will not redirect them to
the login screen.
Single Sign-on This field is available for user-configured policies that require Single Sign-On (SSO). Select this to
have the Zyxel Device enable the SSO feature. You can set up this feature in the SSO screen.
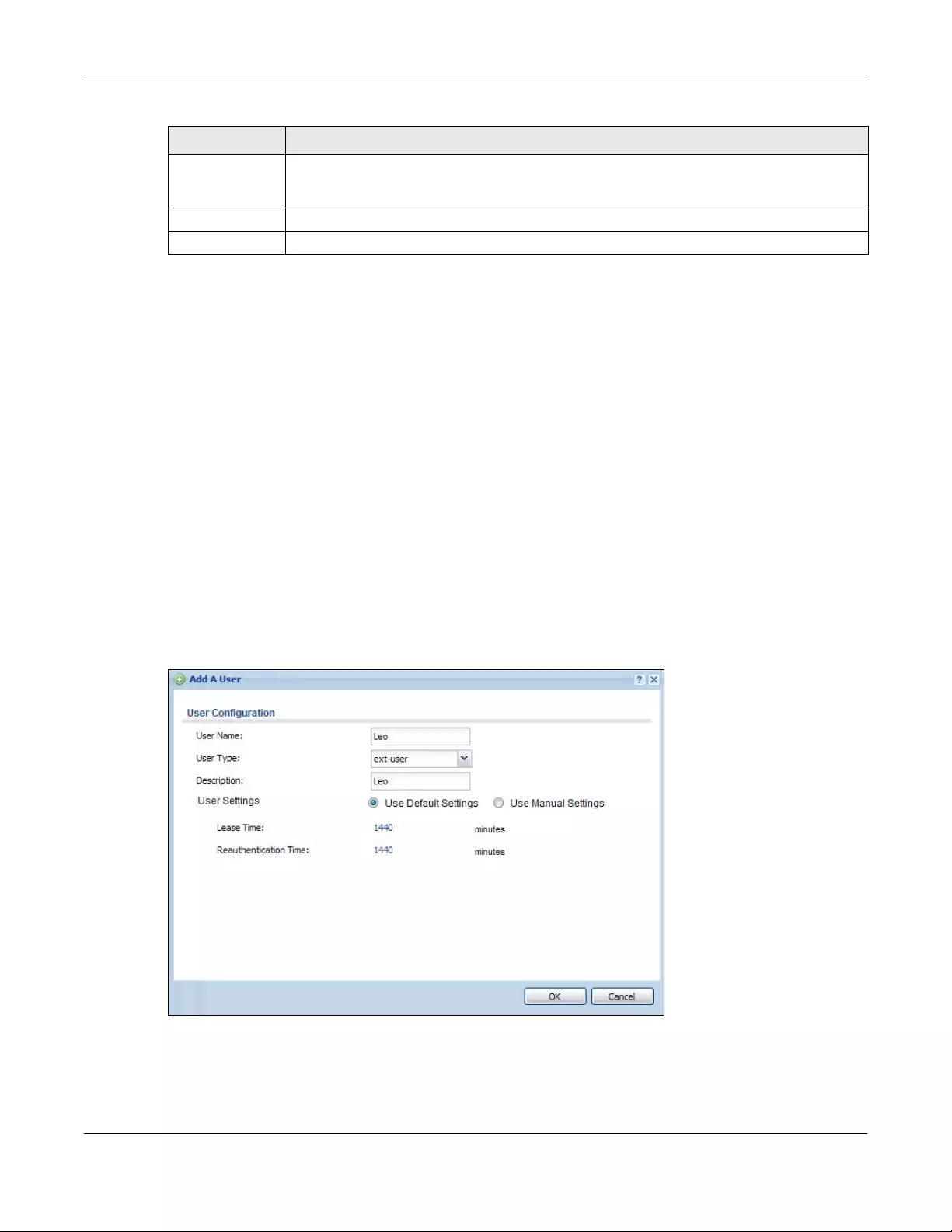
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
446
20.2.1 User-aware Access Control Example
You can configure many policies and security settings for specific users or groups of users. Users can be
authenticated locally by the Zyxel Device or by an external (RADIUS) authentication server.
In this example the users are authenticated by an external RADIUS server at 172.16.1.200. First, set up the
user accounts and user groups in the Zyxel Device. Then, set up user authentication using the RADIUS
server. Finally, set up the policies in the table above.
20.2.1.1 Set Up User Accounts
Set up user accounts in the RADIUS server. This example uses the Web Configurator. If you can export
user names from the RADIUS server to a text file, then you might configure a script to create the user
accounts instead.
1Click Configuration > Object > User/Group > User. Click the Add icon.
2Enter the same user name that is used in the RADIUS server, and set the User Type to ext-user because
this user account is authenticated by an external server. Click OK.
Figure 323 Configuration > Object > User/Group > User > Add
3Repeat this process to set up the remaining user accounts.
Force User
Authentication
This field is available for user-configured policies that require authentication. Select this to have
the Zyxel Device automatically display the login screen when users who have not logged in yet
try to send HTTP traffic.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 162 Configuration > Web Authentication > General > Add Authentication Policy (continued)
LABEL DESCRIPTION
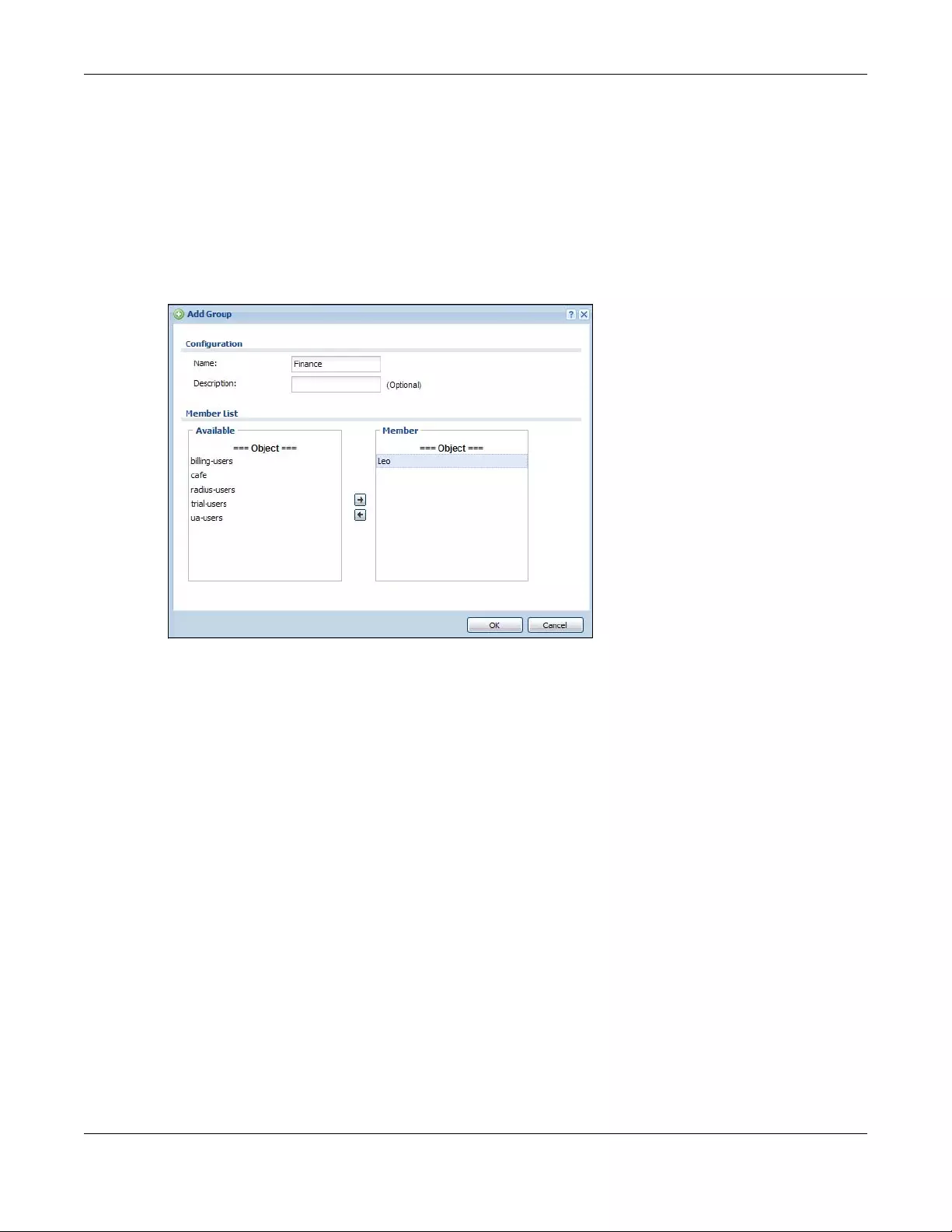
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
447
20.2.1.2 Set Up User Groups
Set up the user groups and assign the users to the user groups.
1Click Configuration > Object > User/Group > Group. Click the Add icon.
2Enter the name of the group. In this example, it is “Finance”. Then, select Object/Leo and click the right
arrow to move him to the Member list. This example only has one member in this group, so click OK. Of
course you could add more members later.
Figure 324 Configuration > Object > User/Group > Group > Add
3Repeat this process to set up the remaining user groups.
20.2.1.3 Set Up User Authentication Using the RADIUS Server
This step sets up user authentication using the RADIUS server. First, configure the settings for the RADIUS
server. Then, set up the authentication method, and configure the Zyxel Device to use the
authentication method. Finally, force users to log into the Zyxel Device before it routes traffic for them.
1Click Configuration > Object > AAA Server > R ADIUS. Double-click the radius entry. Configure the RADIUS
server’s address, authentication port (1812 if you were not told otherwise), and key. Click OK.
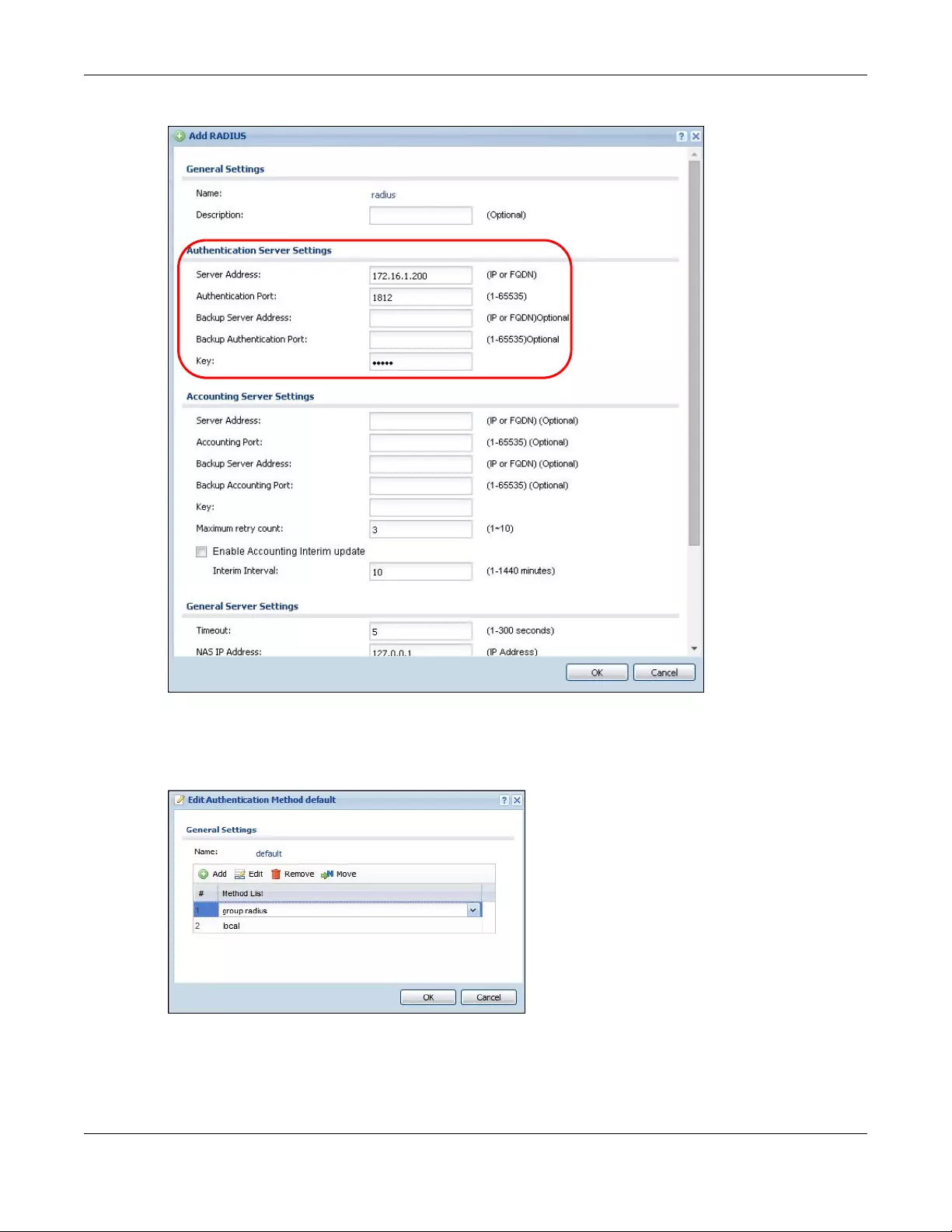
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
448
Figure 325 Configuration > Object > AAA Server > RADIUS > Add
2Click Configuration > Object > Auth. Method. Double-click the default entry. Click the Add icon. Select
group radius because the Zyxel Device should use the specified RADIUS server for authentication. Click
OK.
Figure 326 Configuration > Object > Auth. method > Edit
3Click Configuration > Web Authentication. In the Web Authentication > General screen, select Enable
Web Authentication to turn on the web authentication feature and click Apply.
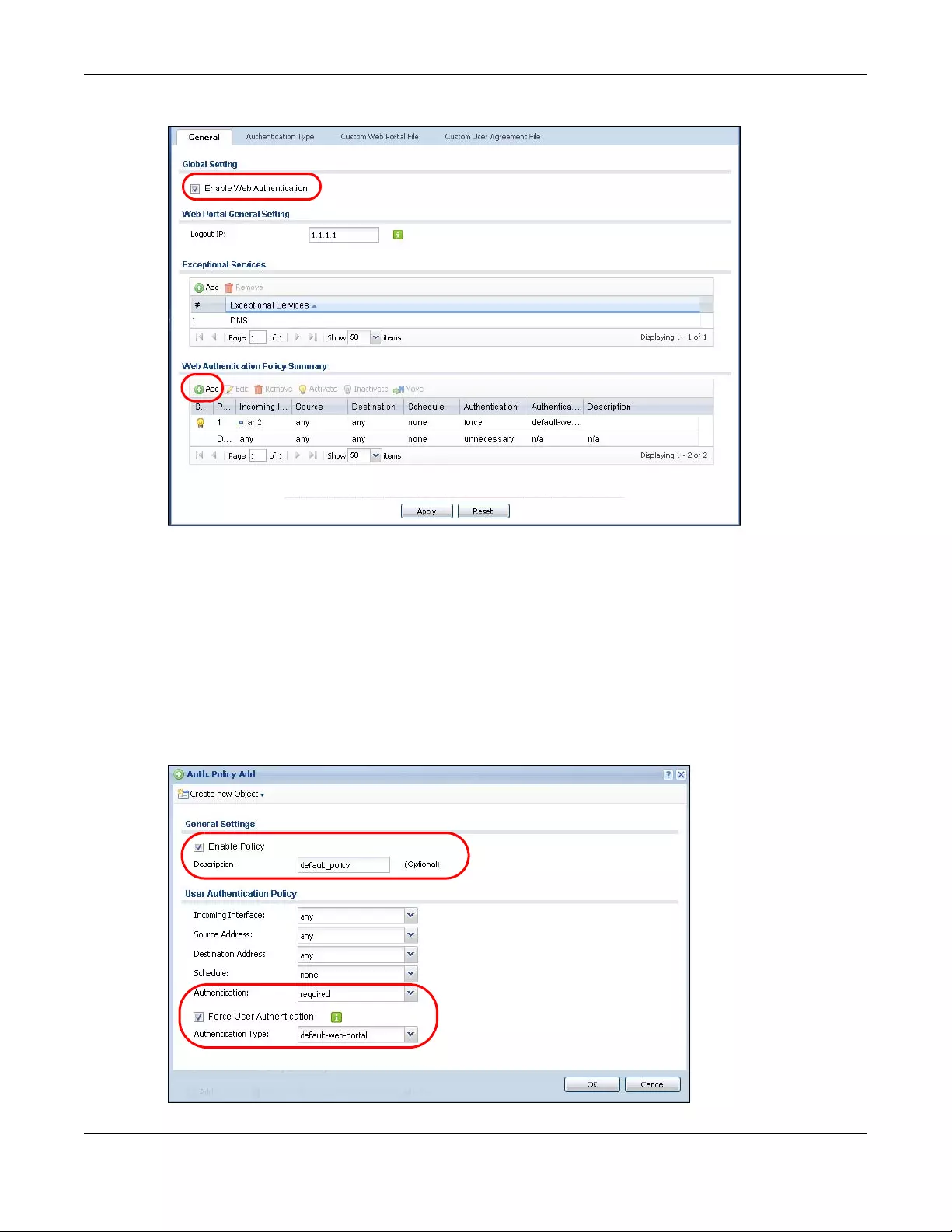
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
449
Figure 327 Configuration > Web Authentication
4In the Web Authentication Policy Summary section, click the Add icon to set up a default policy that has
priority over other policies and forces every user to log into the Zyxel Device before the Zyxel Device
routes traffic for them.
5Select Enable Policy. Enter a descriptive name, “default_policy” for example. Set the Authentication
field to required, and make sure Force User Authentication is selected. Select an authentication type
profile (“default-web-portal” in this example). Keep the rest of the default settings, and click OK.
Note: The users must log in at the Web Configurator login screen before they can use HTTP or
MSN.
Figure 328 Configuration > Web Authentication: General: Add
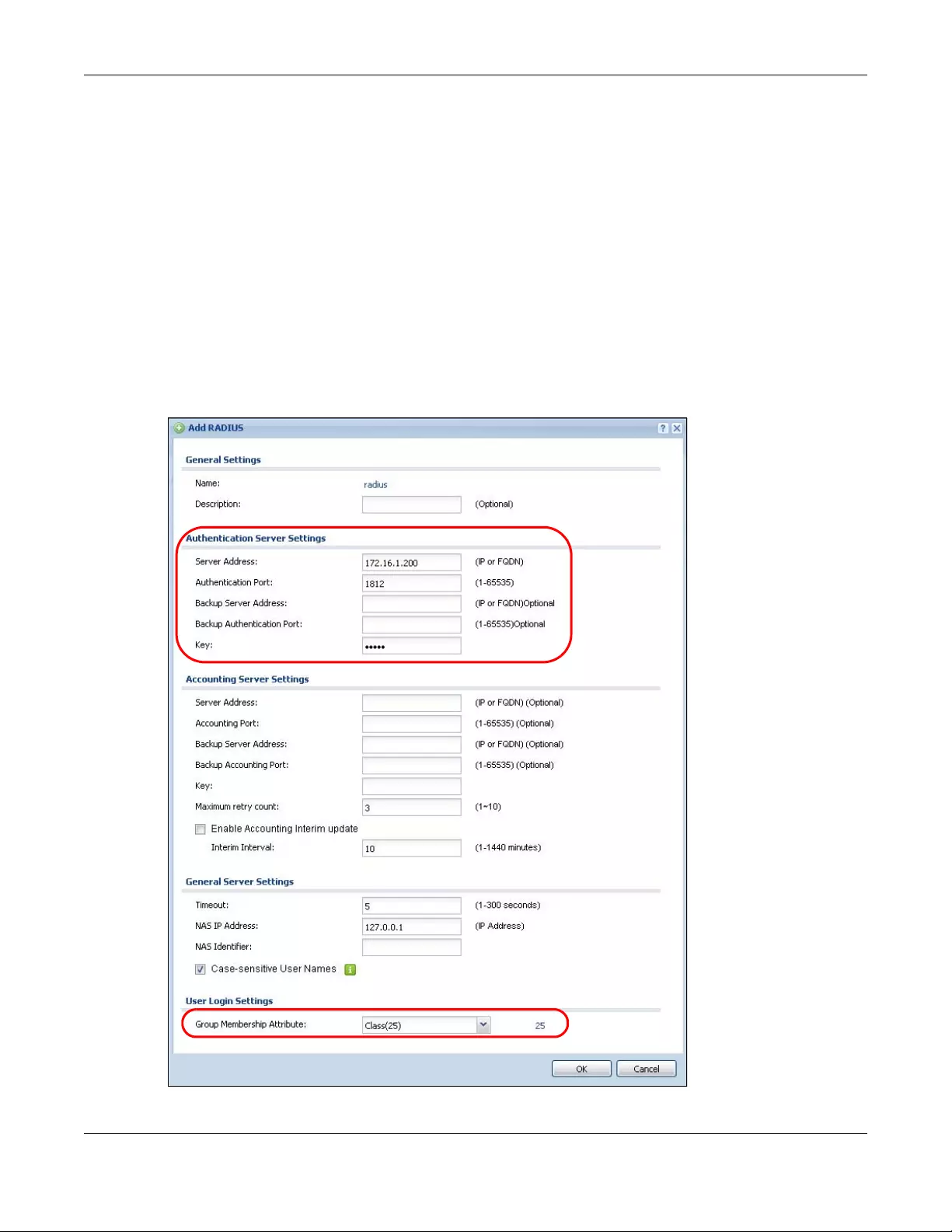
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
450
When the users try to browse the web (or use any HTTP application), the login screen appears. They
have to log in using the user name and password in the RADIUS server.
20.2.1.4 User Group Authentication Using the RADIUS Server
The previous example showed how to have a RADIUS server authenticate individual user accounts. If
the RADIUS server has different user groups distinguished by the value of a specific attribute, you can
make a couple of slight changes in the configuration to have the RADIUS server authenticate groups of
user accounts defined in the RADIUS server.
1Click Configuration > Object > AAA Server > RADIUS. Double-click the radius entry. Besides configuring
the RADIUS server’s address, authentication port, and key; set the Group Membership Attribute field to
the attribute that the Zyxel Device is to check to determine to which group a user belongs. This example
uses Class. This attribute’s value is called a group identifier; it determines to which group a user belongs.
In this example the values are Finance, Engineer, Sales, and Boss.
Figure 329 Configuration > Object > AAA Server > RADIUS > Add
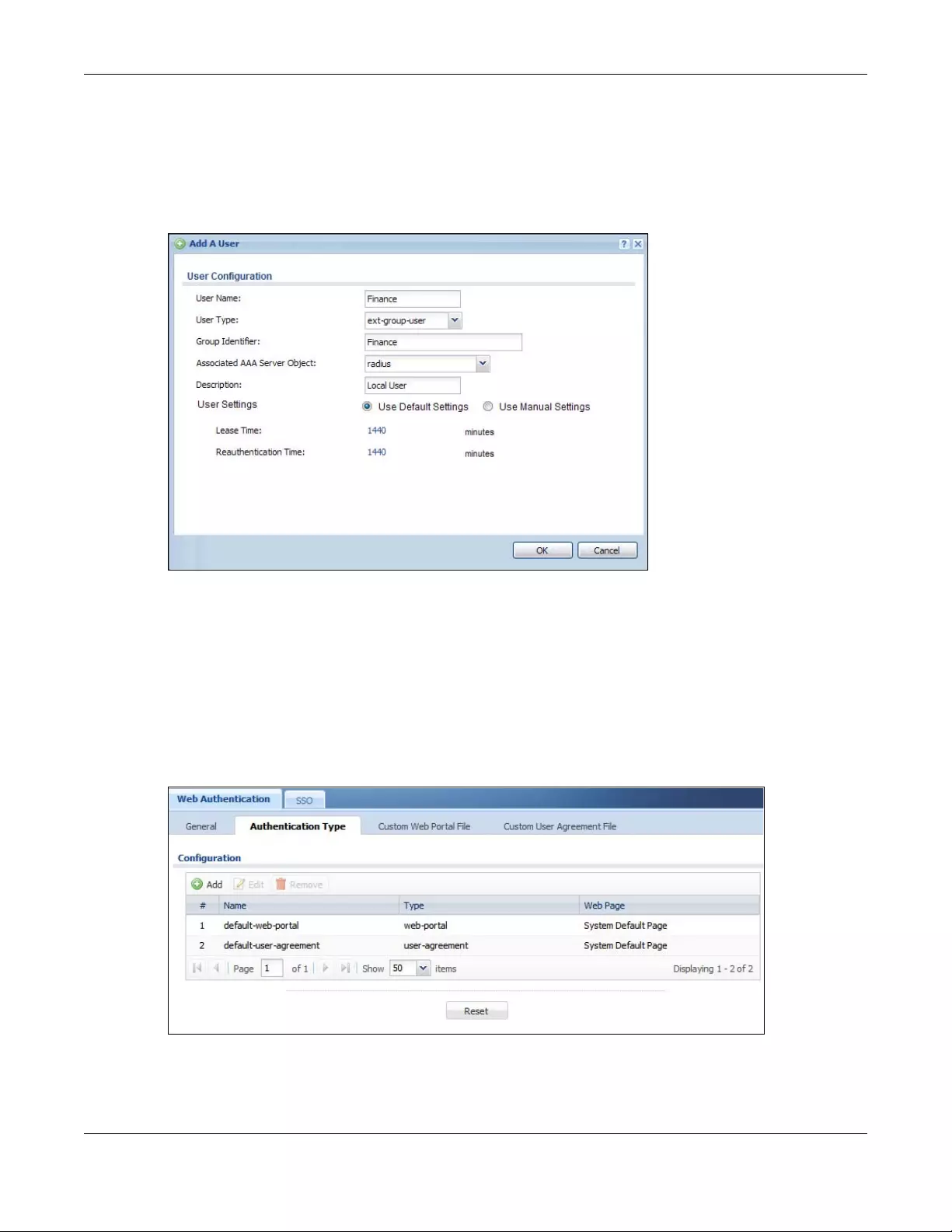
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
451
2Now you add ext-group-user objects to identify groups based on the group identifier values. Set up one
user account for each group of user accounts in the RADIUS server. Click Configuration > Object > User/
Group > User. Click the Add icon.
Enter a user name and set the User Type to ext-group-user. In the Group Identifier field, enter Finance,
Engineer, Sales, or Boss and set the Associated AAA Server Object to radius.
Figure 330 Configuration > Object > User/Group > User > Add
3Repeat this process to set up the remaining groups of user accounts.
20.2.2 Authentication Type Screen
Use this screen to view, create and manage the authentication type profiles on the Zyxel Device. An
authentication type profile decides which type of web authentication pages to be used for user
authentication. Go to Configuration > Web Authentication and then select the Authentication Type tab
to display the screen.
Figure 331 Configuration > Web Authentication > Authentication Type
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
452
The following table describes the labels in this screen.
Add/Edit an Authentication Type Profile
Click the Add icon or select an entry in the Web Authentication > Authentication Type screen and click
the Edit icon to display the screen. The screen differs depending on what you select in the Type field.
Table 163 Configuration > Web Authentication > Authentication Type
LABEL DESCRIPTION
Add Click this to create a new entry. Select an entry and click Add to create a new entry after the
selected entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
#This field is a sequential value, and it is not associated with a specific entry.
Name This field displays the name of the profile.
default-web-portal: the default login page built into the Zyxel Device.
Note: You can also customize the default login page built into the Zyxel Device in
the System > WWW > Login Page screen.
default-web-portal: the default user agreement page built into the Zyxel Device.
Type This field displays the type of the web authentication page used by this profile.
Web Page This field displays whether this profile uses the default web authentication page built into the
Zyxel Device (System Default Page) or custom web authentication pages from an external web
server (External Page).
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
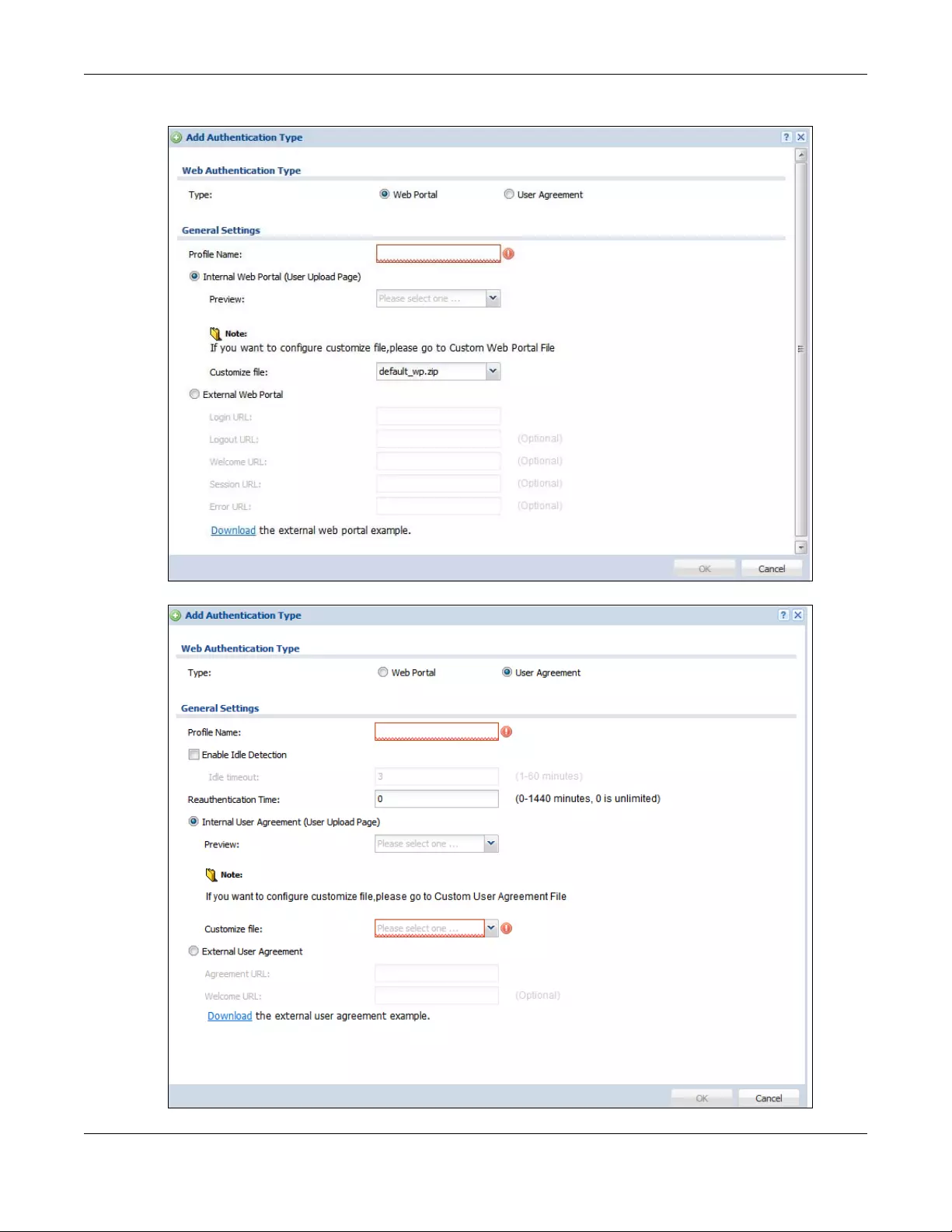
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
453
Figure 332 Configuration > Web Authentication > Authentication Type: Add/Edit (Web Portal)
Figure 333 Configuration > Web Authentication > Authentication Type: Add/Edit (User Agreement)
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
454
The following table describes the labels in this screen.
Table 164 Configuration > Web Authentication > Authentication Type: Add/Edit
LABEL DESCRIPTION
Type Select the type of the web authentication page through which users authenticate their
connections.
If you select User Agreement, by agreeing to the policy of user agreement, users can access
the Internet without a guest account.
Profile Name Enter a name for the profile.
You can use up to 31 alphanumeric characters (A-Z, a-z, 0-9) and underscores (_). Spaces are
not allowed. The first character must be a letter.
The following fields are available if you set Type to Web Portal.
Internal Web
Portal
Select this to use the web portal pages uploaded to the Zyxel Device.
The login page appears whenever the web portal intercepts network traffic, preventing
unauthorized users from gaining access to the network.
Preview Select to display the page you uploaded to the Zyxel Device in a new frame.
Note: You must select a custom file uploaded to the Zyxel Device before you can
preview the pages.
Customize file Select the file name of the web portal file in the Zyxel Device.
Note: You can upload zipped custom web portal files to the Zyxel Device using the
Configuration > Web Authentication > Web Portal Customize File screen.
External Web
Portal
Select this to use a custom login page from an external web portal instead of the one
uploaded to the Zyxel Device. You can configure the look and feel of the web portal page.
Login URL Specify the login page’s URL; for example, http://IIS server IP Address/login.html.
The Internet Information Server (IIS) is the web server on which the web portal files are installed.
Logout URL Specify the logout page’s URL; for example, http://IIS server IP Address/logout.html.
The Internet Information Server (IIS) is the web server on which the web portal files are installed.
Welcome URL Specify the welcome page’s URL; for example, http://IIS server IP Address/welcome.html.
Users will be redirected to the welcome page after authentication. This field is optional.
The Internet Information Server (IIS) is the web server on which the web portal files are installed.
Session URL Specify the session page’s URL; for example, http://IIS server IP Address/session.html.
The Internet Information Server (IIS) is the web server on which the web portal files are installed.
Error URL Specify the error page’s URL; for example, http://IIS server IP Address/error.html.
The Internet Information Server (IIS) is the web server on which the web portal files are installed.
Download Click this to download an example external web portal file for your reference.
The following fields are available if you set Type to User Agreement.
Enable Idle
Detection
This is applicable for access users.
Select this check box if you want the Zyxel Device to monitor how long each access user is
logged in and idle (in other words, there is no traffic for this access user). The Zyxel Device
automatically logs out the access user once the Idle timeout has been reached.
Idle timeout This is applicable for access users.
This field is effective when Enable Idle Detection is checked. Type the number of minutes each
access user can be logged in and idle before the Zyxel Device automatically logs out the
access user.
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
455
20.2.3 Custom Web Portal / User Agreement File Screen
Use this screen to upload the zipped custom web portal or user agreement files to the Zyxel Device. You
can also download the custom files to your computer.
Click Configuration > Web Authentication and then select the Custom Web Portal File or Custom User
Agreement File tab to display the screen.
Reauthentication
Time
Enter the number of minutes the user can be logged into the Zyxel Device in one session before
having to log in again.
Internal User
Agreement
Select this to use the user agreement pages in the Zyxel Device. The user agreement page
appears whenever the Zyxel Device intercepts network traffic, preventing unauthorized users
from gaining access to the network.
Preview Select to display the page you uploaded to the Zyxel Device in a new frame.
Note: You must select a custom file uploaded to the Zyxel Device before you can
preview the pages.
Customize file Select the file name of the user agreement file in the Zyxel Device.
Note: You can upload zipped custom user agreement files to the Zyxel Device using
the Configuration > Web Authentication > User Agreement Customize File
screen.
External User
Agreement
Select this to use custom user agreement pages from an external web server instead of the
default one built into the Zyxel Device. You can configure the look and feel of the user
agreement page.
Agreement
URL Specify the user agreement page’s URL; for example, http://IIS server IP Address/logout.html.
The Internet Information Server (IIS) is the web server on which the user agreement files are
installed.
Welcome URL Specify the welcome page’s URL; for example, http://IIS server IP Address/welcome.html.
The Internet Information Server (IIS) is the web server on which the user agreement files are
installed.
If you leave this field blank, the Zyxel Device will use the welcome page of internal user
agreement file.
Download Click this to download an example external user agreement file for your reference.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 164 Configuration > Web Authentication > Authentication Type: Add/Edit (continued)
LABEL DESCRIPTION
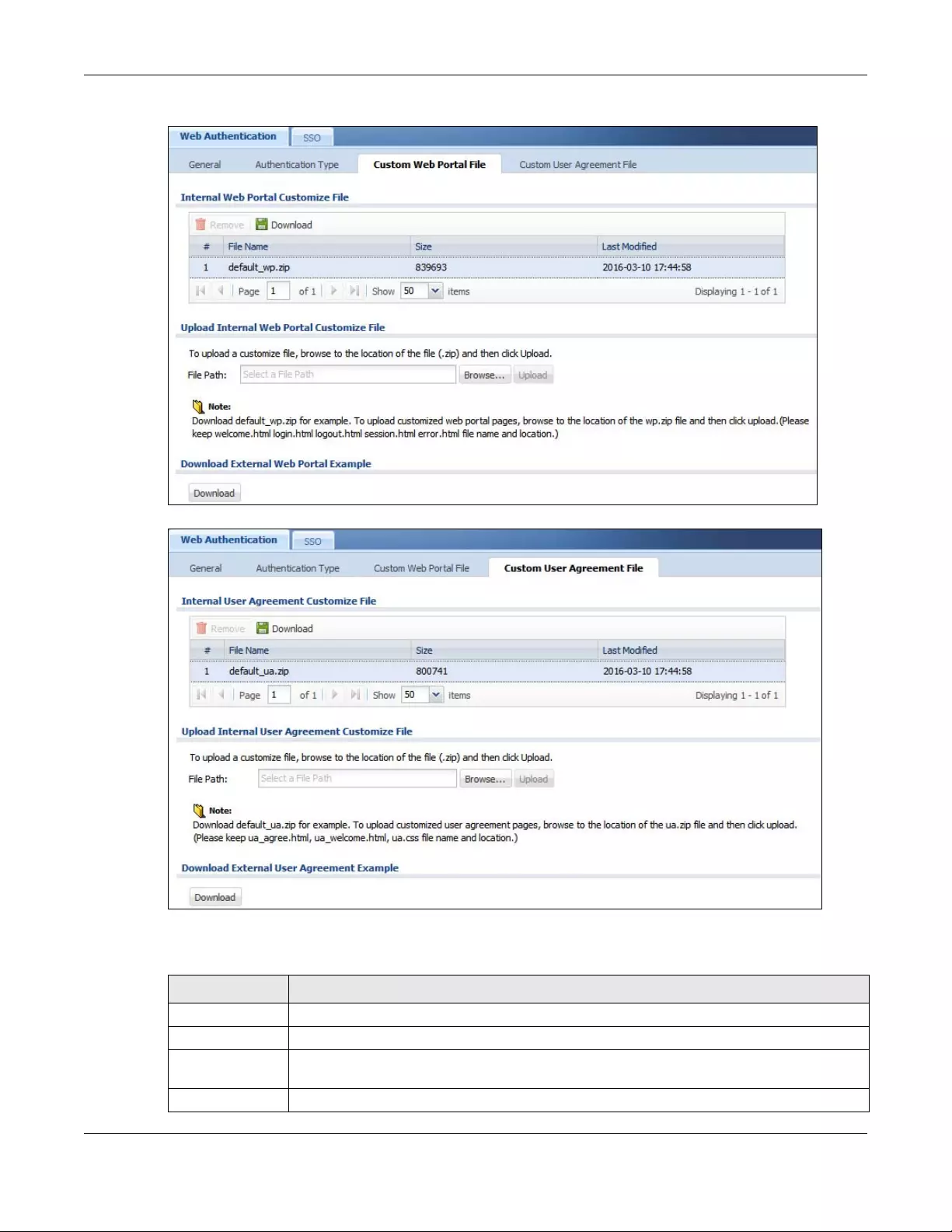
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
456
Figure 334 Configuration > Web Authentication > Custom Web Portal File
Figure 335 Configuration > Web Authentication > Custom User Agreement File
The following table describes the labels in this screen.
Table 165 Configuration > Web Authentication > Custom Web Portal / User Agreement File
LABEL DESCRIPTION
Remove Click a file’s row to select it and click Remove to delete it from the Zyxel Device.
Download Click a file’s row to select it and click Download to save the zipped file to your computer.
# This column displays the index number for each file entry. This field is a sequential value, and it is
not associated with a specific entry.
File Name This column displays the label that identifies a web portal or user agreement file.
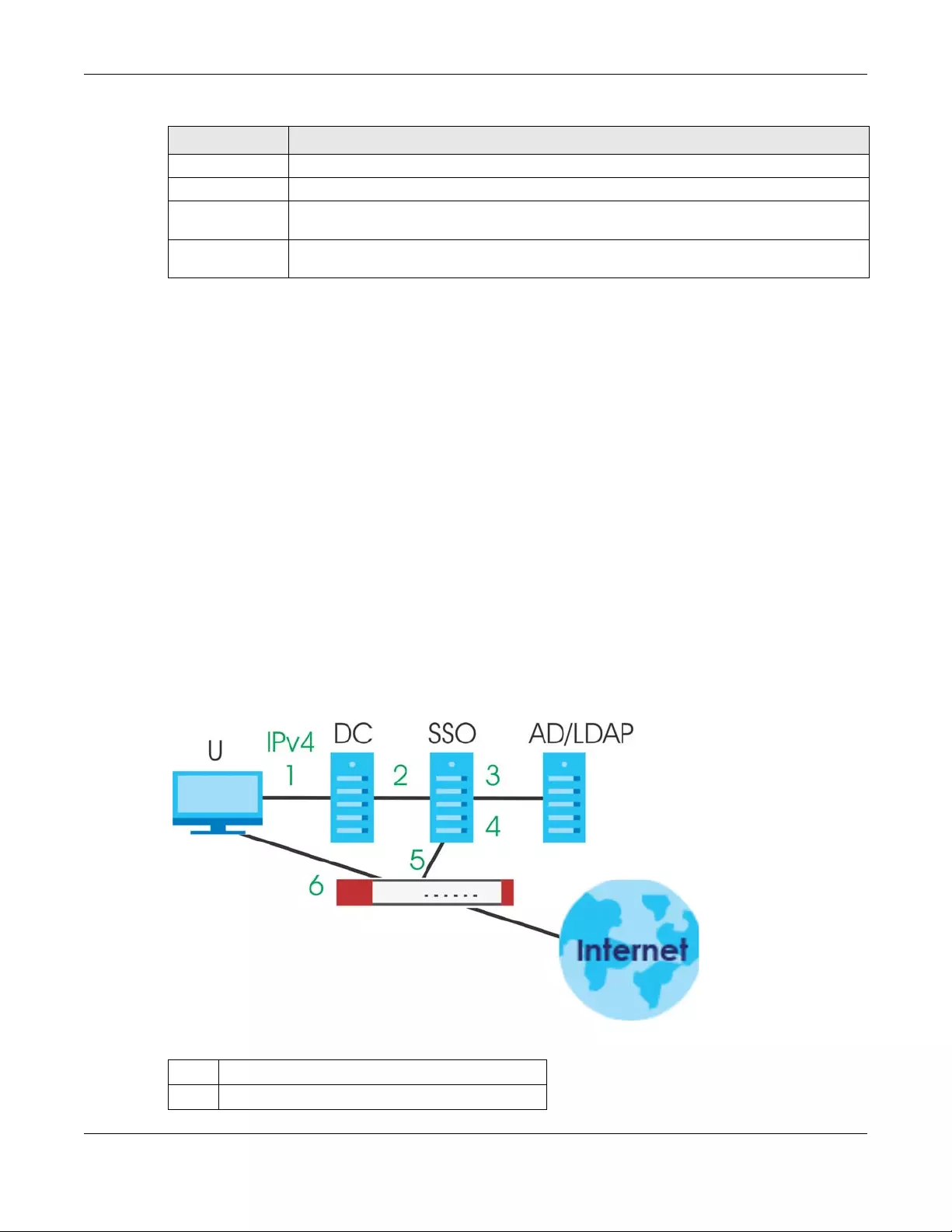
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
457
20.3 SSO Overview
The SSO (Single Sign-On) function integrates Domain Controller and Zyxel Device authentication
mechanisms, so that users just need to log in once (single login) to get access to permitted resources.
In the following figure, U user logs into a Domain Controller (DC) which passes the user’s login credentials
to the SSO agent. The SSO agent checks that these credentials are correct with the AD server, and if the
AD server confirms so, the SSO then notifies the Zyxel Device to allow access for the user to the permitted
resource (Internet access, for example).
Note: The Zyxel Device, the DC, the SSO agent and the AD server must all be in the same
domain and be able to communicate with each other.
SSO does not support IPv6, LDAP or RADIUS; you must use it in an IPv4 network
environment with Windows AD (Active Directory) authentication database.
You must enable Web Authentication in the Configuration > Web Authentication
screen.
Figure 336 SSO Overview
Size This column displays the size (in KB) of a file.
Last Modified This column displays the date and time that the individual files were last changed or saved.
Browse / Upload Click Browse... to find the zipped file you want to upload, then click the Upload button to put it
on the Zyxel Device.
Download Click this to download an example external web portal or user agreement file for your
reference.
Table 165 Configuration > Web Authentication > Custom Web Portal / User Agreement File
LABEL DESCRIPTION
U User
DC Domain Controller
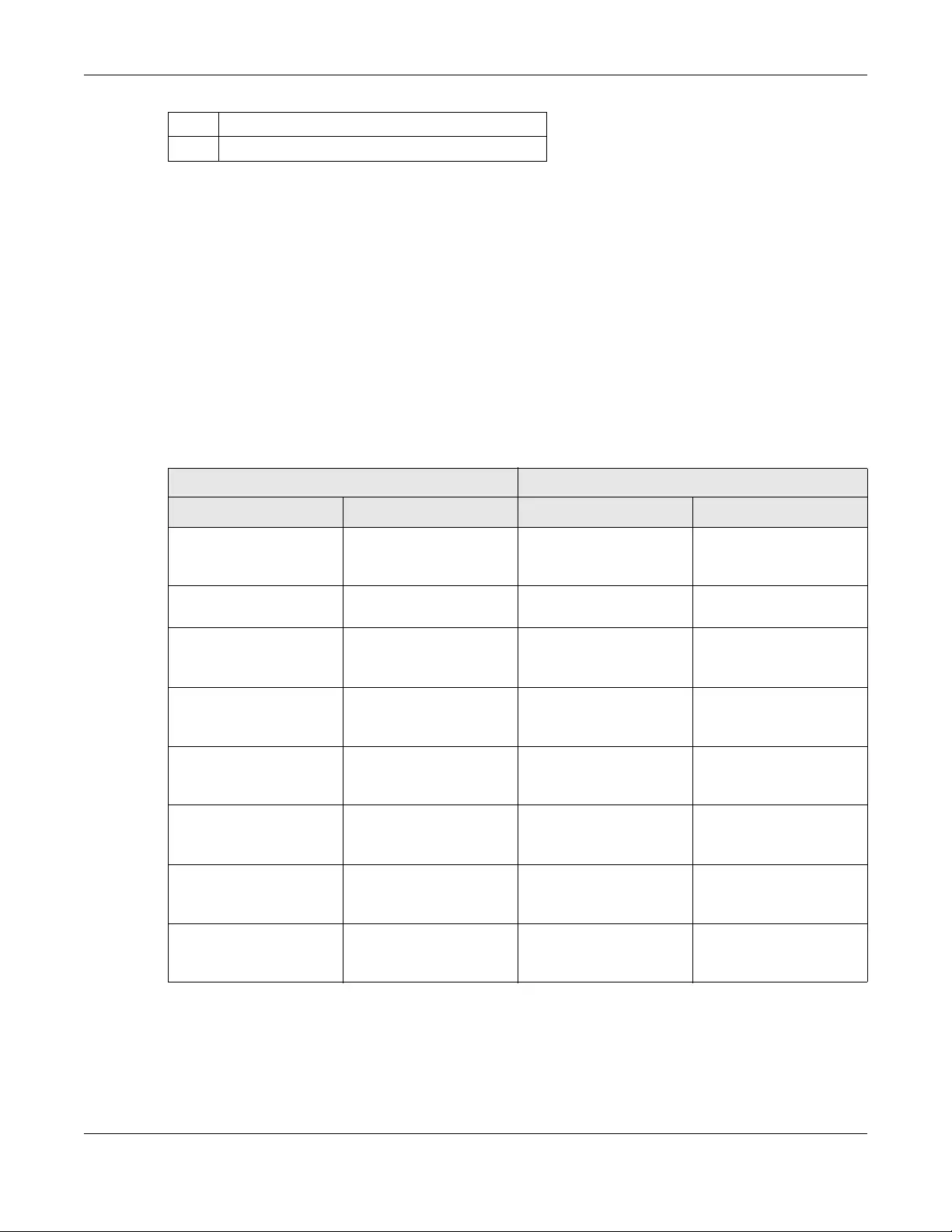
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
458
Install the SSO Agent on one of the following platforms:
• Windows 7 Professional (32-bit and 64-bit)
• Windows Server 2008 Enterprise (32-bit and 64-bit)
• Windows 2008 R2 (64-bit)
• Windows Server 2012 (64-bit)
20.4 SSO - Zyxel Device Configuration
This section shows what you have to do on the Zyxel Device in order to use SSO.
20.4.1 Configuration Overview
These are the screens you need to configure:
•Configure the Zyxel Device to Communicate with SSO on page 459
SSO Single Sign-On agent
AD Active Directory
Table 166 Zyxel Device - SSO Agent Field Mapping
ZYXEL DEVICE SSO
SCREEN FIELD SCREEN FIELD
Web Authentication >
SSO
Listen Port Agent Configuration
Page > Gateway
Setting
Gateway Port
Web Authentication >
SSO
Primary Agent Port Agent Configuration
Page
Agent Listening Port
Object > User/Group >
User > Add
Group Identifier Agent Configuration
Page > Configure
LDAP/AD Server
Group Membership
Object > AAA Server >
Active Directory > Add
Base DN Agent Configuration
Page > Configure
LDAP/AD Server
Base DN
Object > AAA Server >
Active Directory > Add
Bind DN Agent Configuration
Page > Configure
LDAP/AD Server
Bind DN
Object > User/Group >
User > Add
User Name Agent Configuration
Page > Configure
LDAP/AD Server
Login Name Attribute
Object > AAA Server >
Active Directory > Add
Server Address Agent Configuration
Page > Configure
LDAP/AD Server
Server Address
Network > Interface >
Ethernet > wan (IPv4)
IP address Agent Configuration
Page > Gateway
Setting
Gateway IP
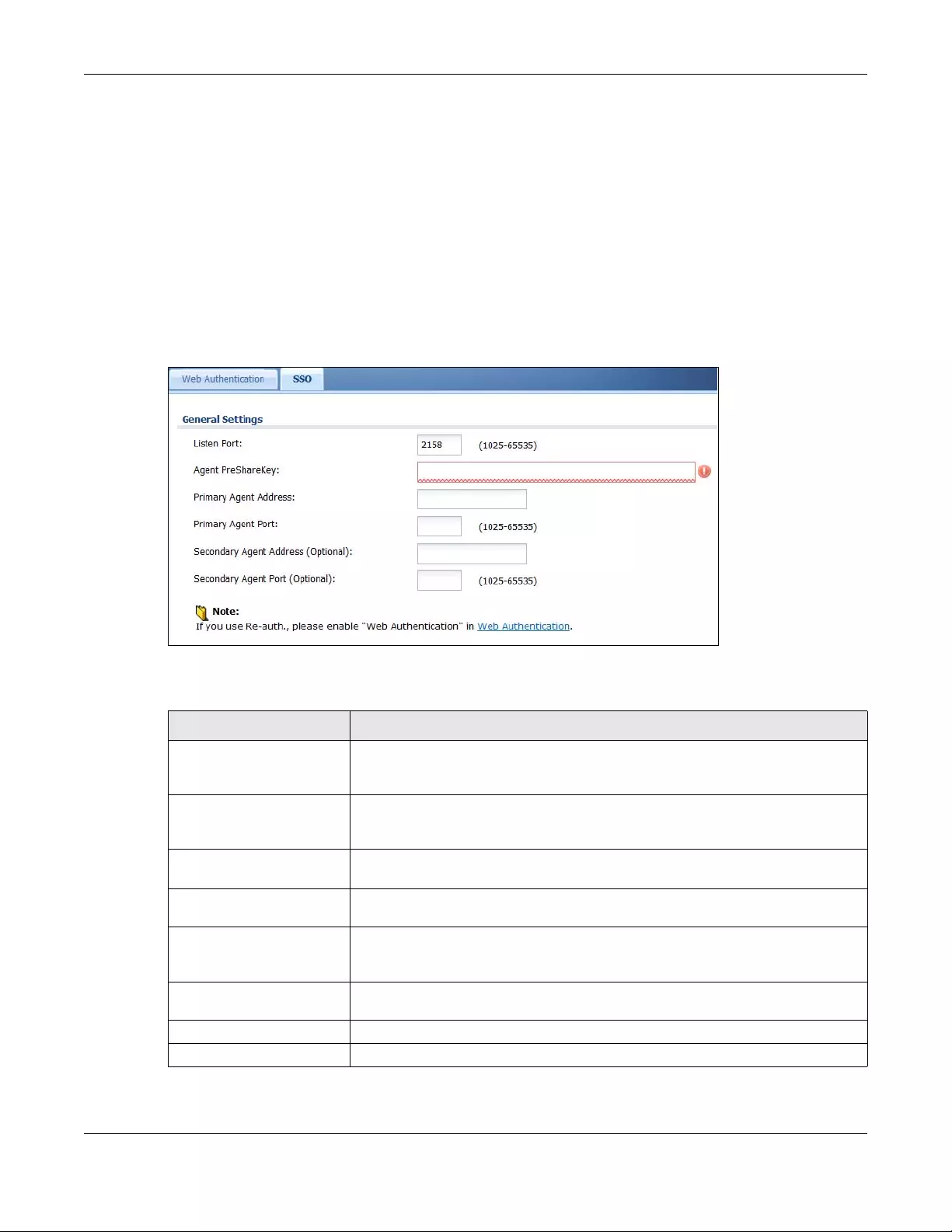
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
459
•Enable Web Authentication on page 460
•Create a Security Policy on page 461
•Configure User Information on page 461
•Configure an Authentication Method on page 462
•Configure Active Directory on page 463 or Configure Active Directory on page 463
20.4.2 Configure the Zyxel Device to Communicate with SSO
Use Configuration > Web Authentication > SSO to configure how the Zyxel Device communicates with
the Single Sign-On (SSO) agent.
Figure 337 Configuration > Web Authentication > SSO
The following table gives an overview of the objects you can configure.
Table 167 Configuration > Web Authentication > SSO
LABEL DESCRIPTION
Listen Port The default agent listening port is 2158. If you change it on the Zyxel Device, then
change it to the same number in the Gateway Port field on the SSO agent too. Type
a number ranging from 1025 to 65535.
Agent PreShareKey Type 8-32 printable ASCII characters or exactly 32 hex characters (0-9; a-f). The
Agent PreShareKey is used to encrypt communications between the Zyxel Device
and the SSO agent.
Primary Agent Address Type the IPv4 address of the SSO agent. The Zyxel Device and the SSO agent must
be in the same domain and be able to communicate with each other.
Primary Agent Port Type the same port number here as in the Agent Listening Port field on the SSO
agent. Type a number ranging from 1025 to 65535.
Secondary Agent Address
(Optional)
Type the IPv4 address of the backup SSO agent if there is one. The Zyxel Device and
the backup SSO agent must be in the same domain and be able to communicate
with each other.
Secondary Agent Port
(Optional)
Type the same port number here as in the Agent Listening Port field on the backup
SSO agent if there is one. Type a number ranging from 1025 to 65535.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings
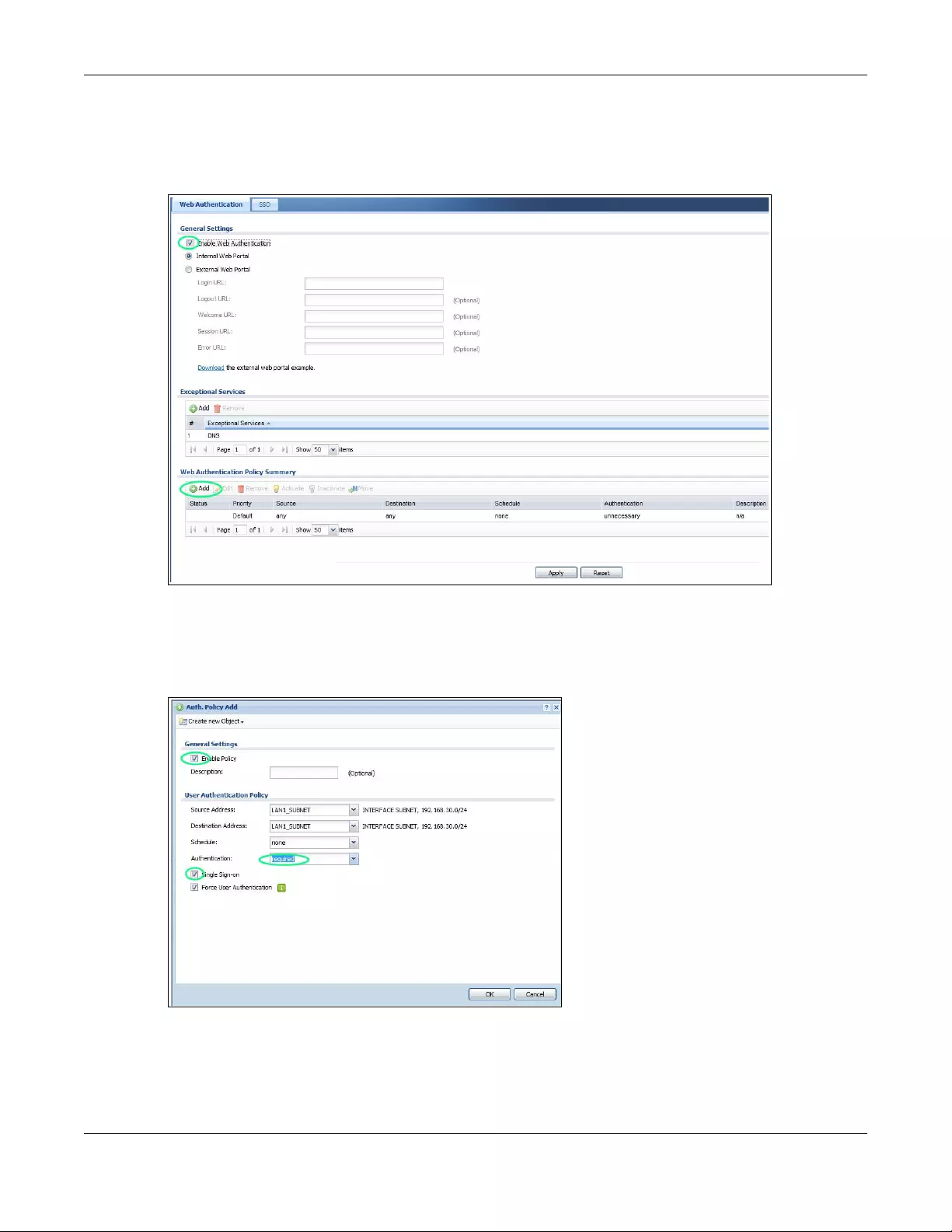
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
460
20.4.3 Enable Web Authentication
Enable Web Authentication and add a web authentication policy.
Make sure you select Enable Policy, Single Sign-On and choose required in Authentication.
Do NOT select any as the source address unless you want all incoming connections to be
authenticated!
See Table 161 on page 442 and Table 162 on page 445 for more information on configuring these
screens.
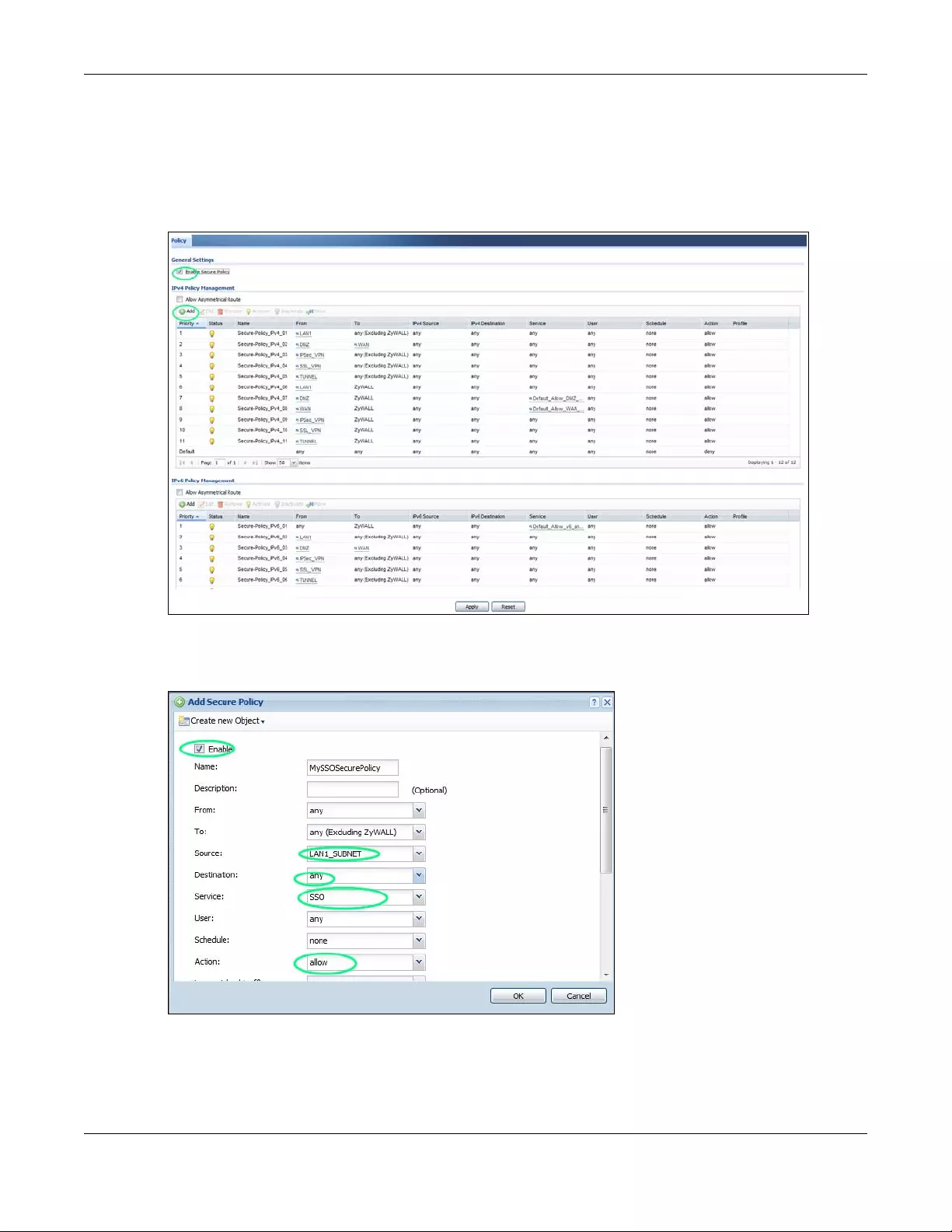
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
461
20.4.4 Create a Security Policy
Configure a Security Policy for SSO traffic source and destination direction in order to prevent the
security policy from blocking this traffic. Go to Configuration > Security Policy > Policy and add a new
policy if a default one does not cover the SSO web authentication traffic direction.
Configure the fields as shown in the following screen. Configure the source and destination addresses
according to the SSO web authentication traffic in your network.
20.4.5 Configure User Information
Configure a User account of the ext-group-user type.
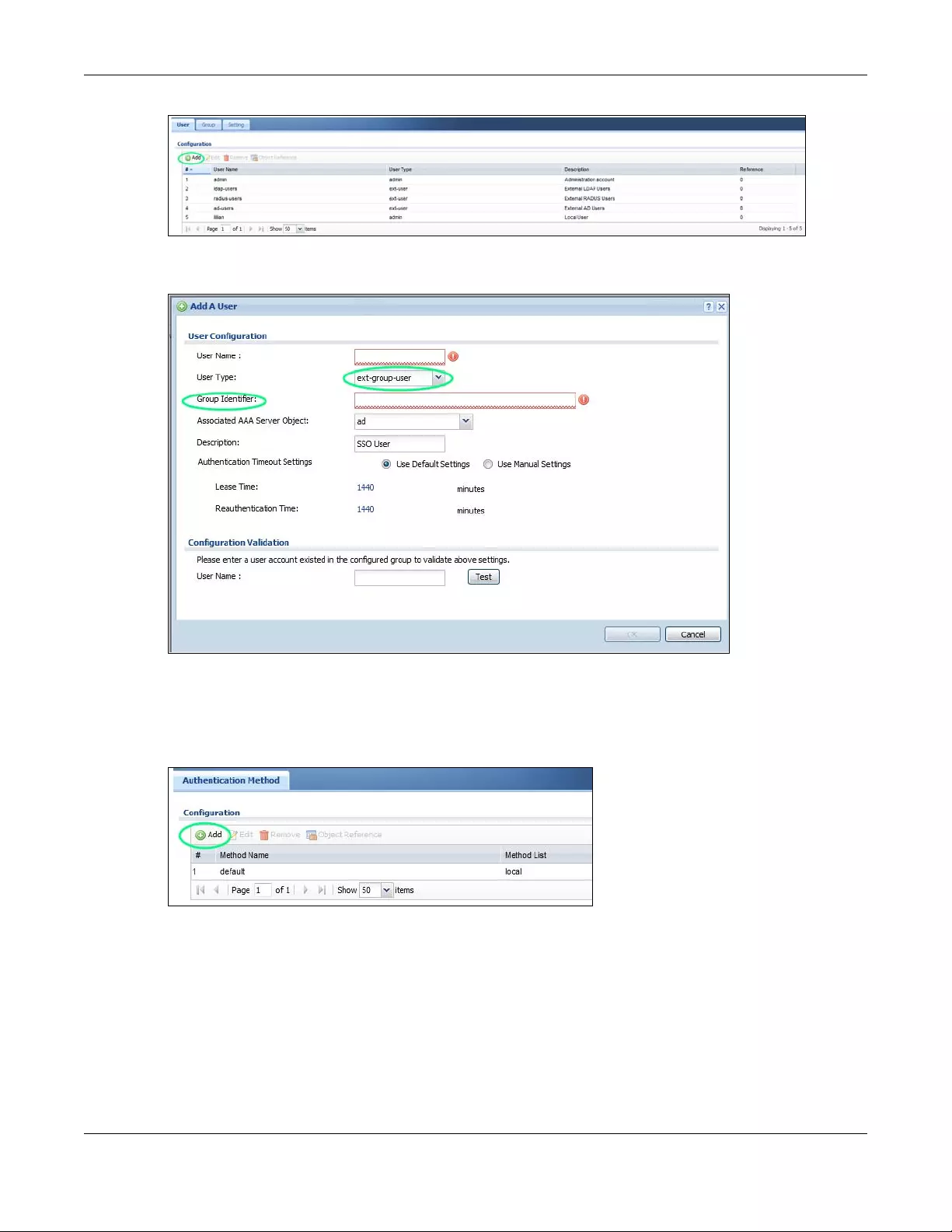
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
462
Configure Group Identifier to be the same as Group Membership on the SSO agent.
20.4.6 Configure an Authentication Method
Configure Active Directory (AD) for authentication with SSO.
Choose group ad as the authentication server for SSO.
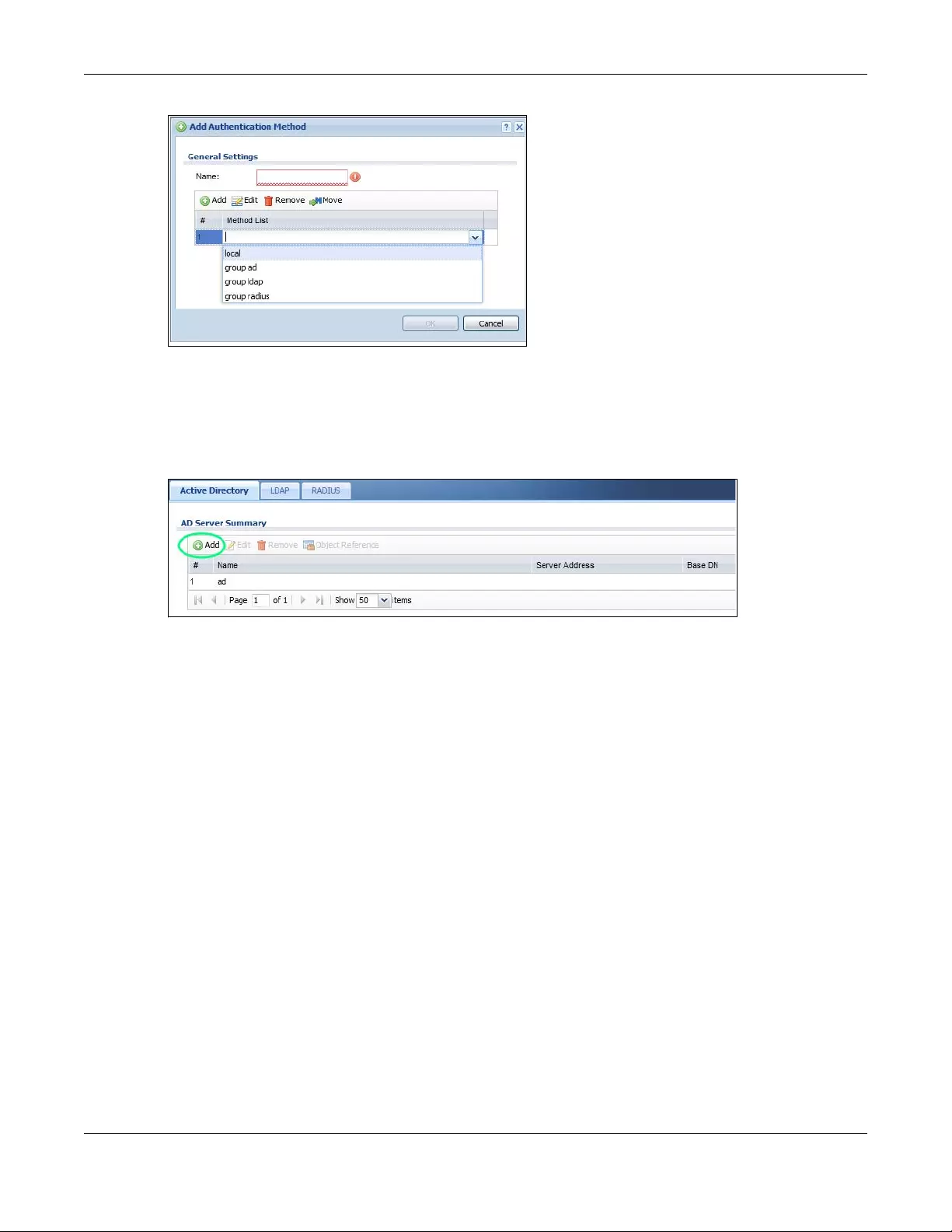
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
463
20.4.7 Configure Active Directory
You must configure an Active Directory (AD) server in AAA Setup to be the same as AD configured on
the SSO agent.
The default AD server port is 389. If you change this, make sure you make the same changes on the SSO.
Configure the Base DN exactly the same as on the Domain Controller and SSO. Bind DN is a user name
and password that allows the Zyxel Device to join the domain with administrative privileges. It is a
required field.
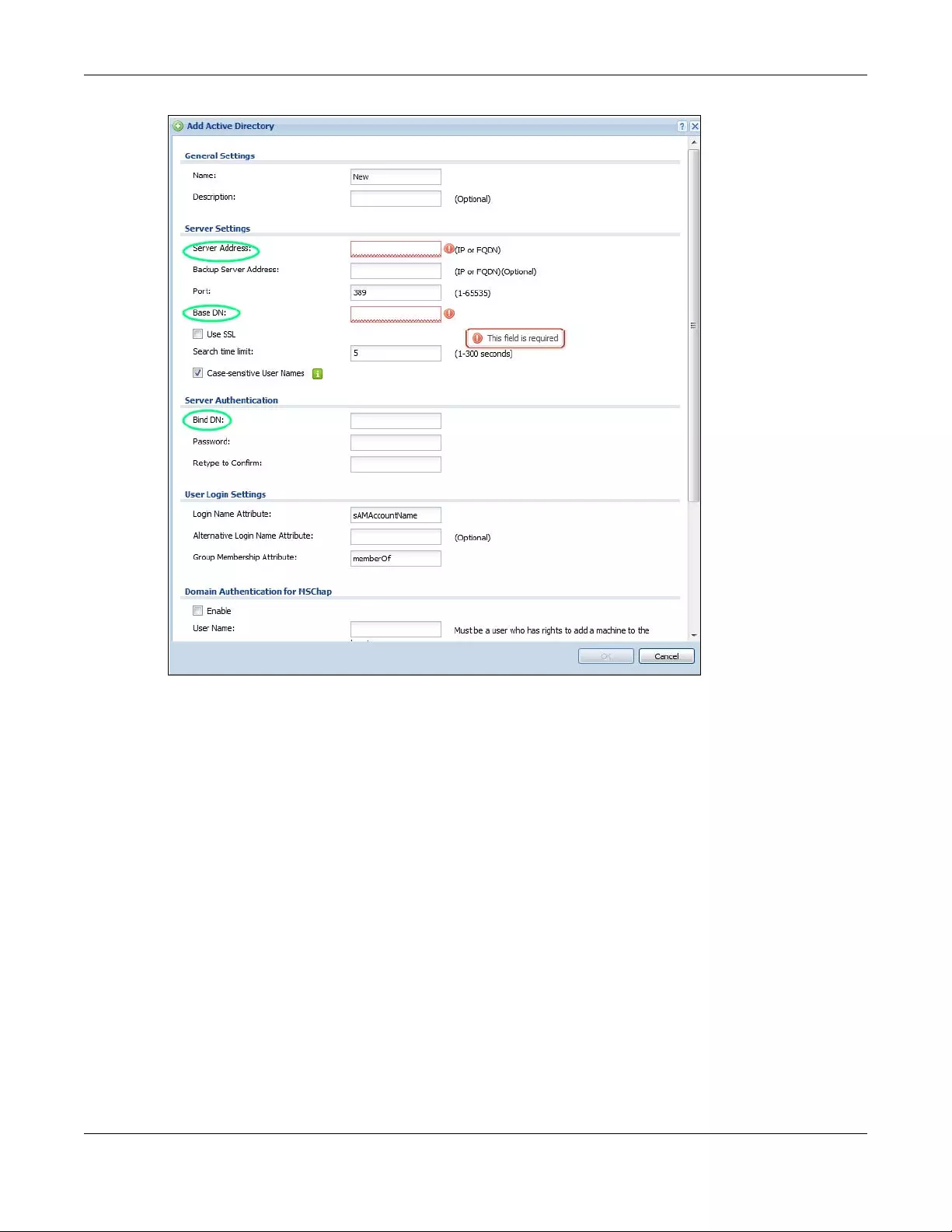
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
464
20.5 SSO Agent Configuration
This section shows what you have to do on the SSO agent in order to work with the Zyxel Device.
After you install the SSO agent, you will see an icon in the system tray (bottom right of the screen)
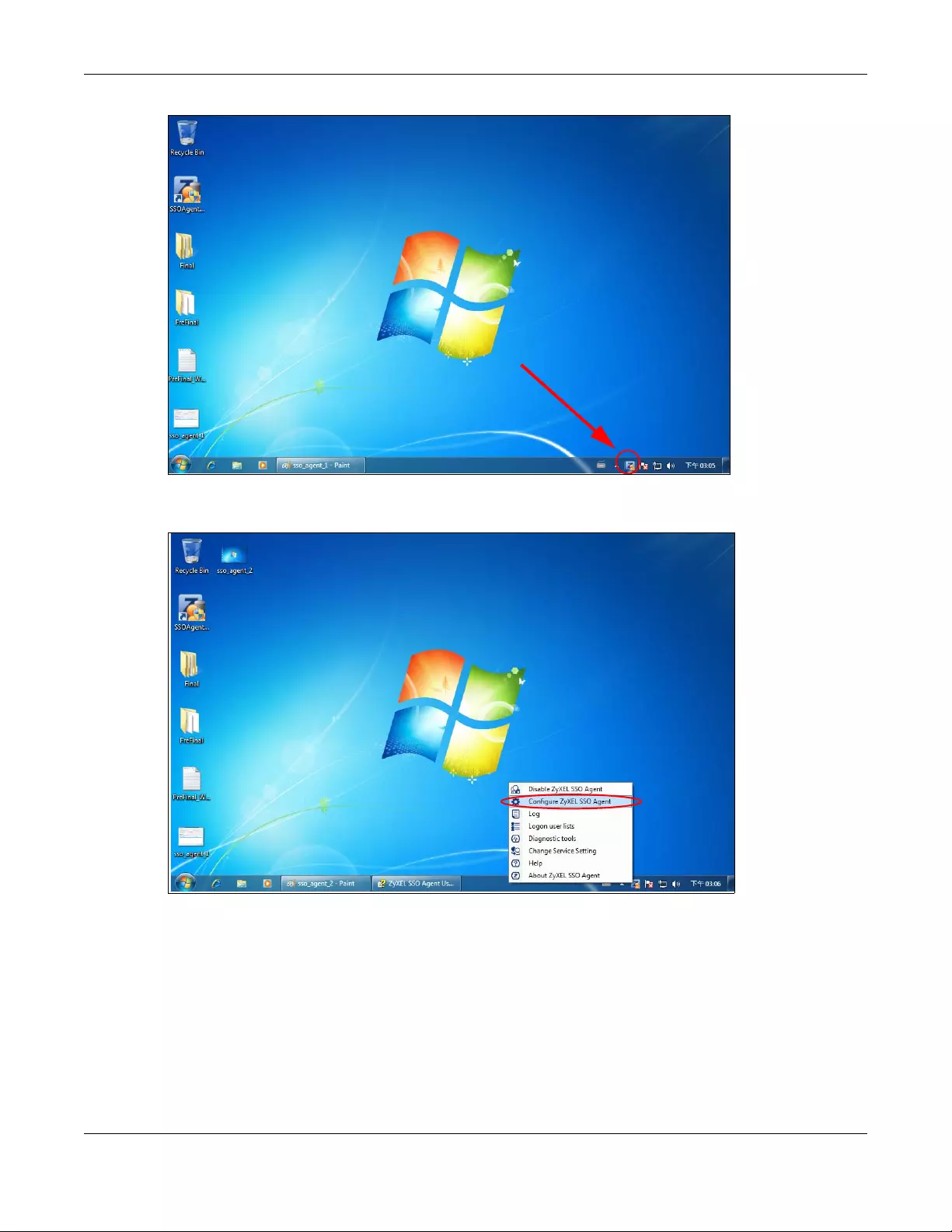
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
465
Right-click the SSO icon and select Configure Zyxel SSO Agent.
Configure the Agent Listening Port, AD server exactly as you have done on the Zyxel Device. Add the
Zyxel Device IP address as the Gateway. Make sure the Zyxel Device and SSO agent are able to
communicate with each other.
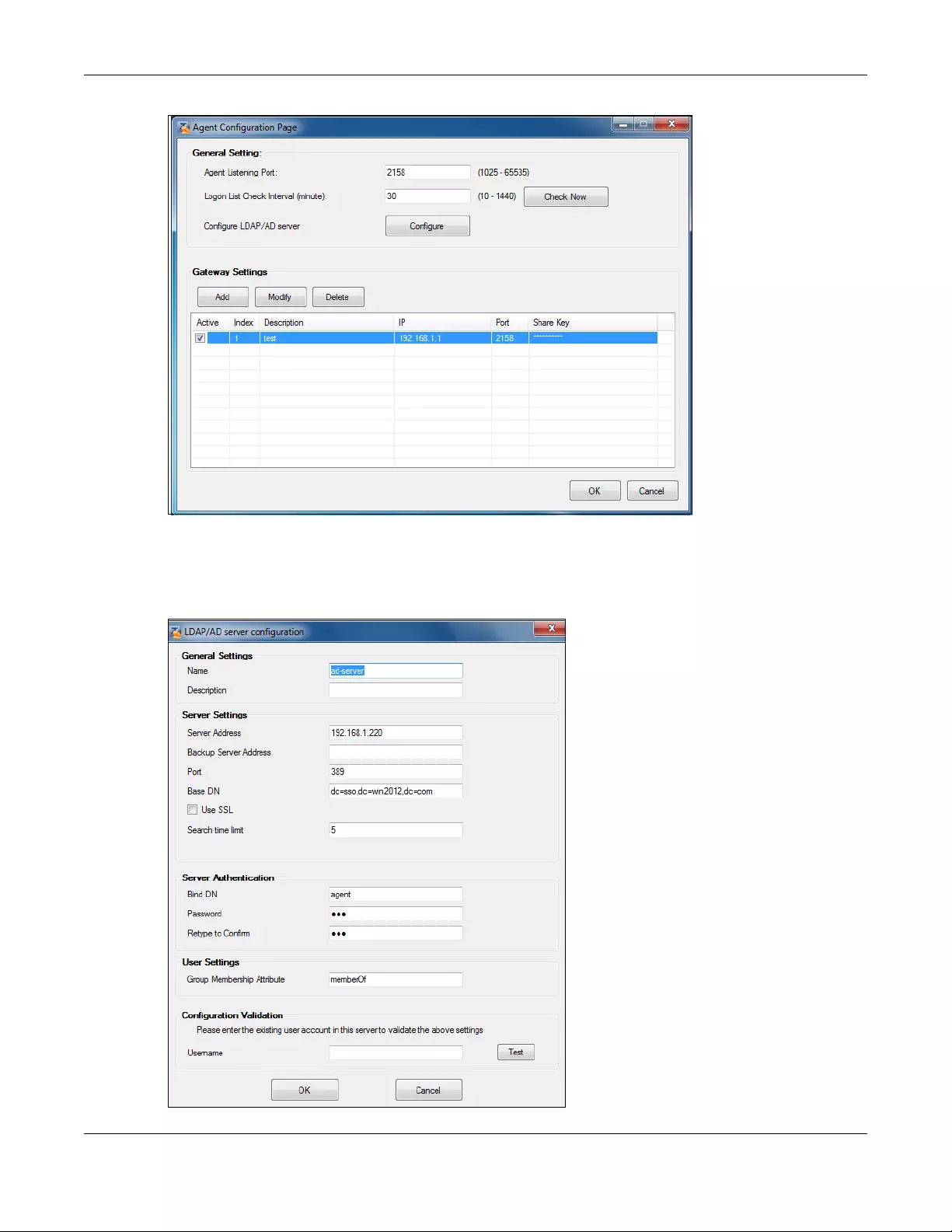
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
466
Configure the Server Address, Port, Base DN, Bind DN, Login Name Attribute and Group Membership for
the AD server settings exactly as you have done on the Zyxel Device. Group Membership is called Group
Identifier on the Zyxel Device.
LDAP/AD Server Configuration
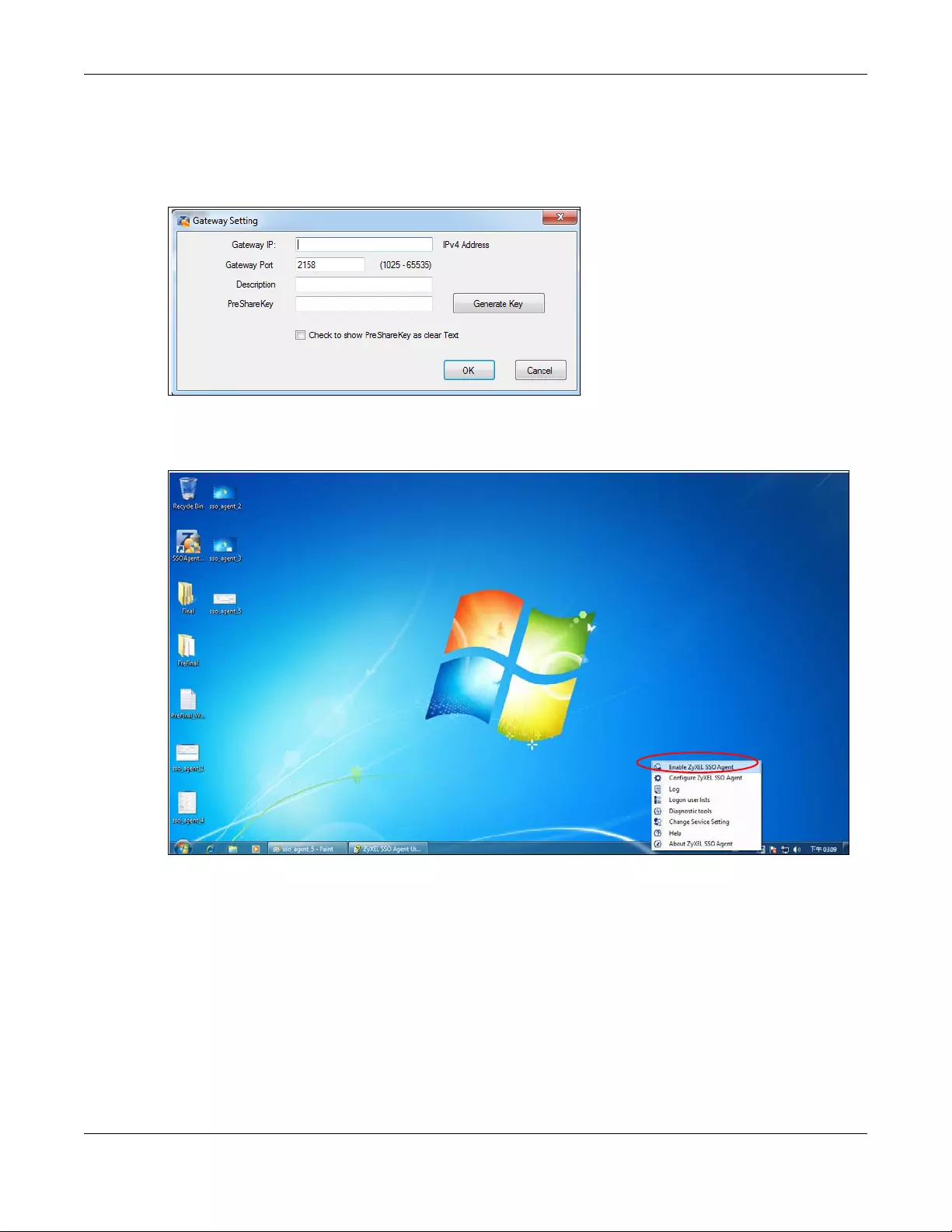
Chapter 20 Web Authentication
USG/ZyWALL User’s Guide
467
Configure the Gateway IP address, Gateway Port and PreShareKey exactly as you have done in the
Zyxel Device Configuration > Web Authen tication > SSO screen. If you want to use Generate Key to have
the SSO create a random password, select Check to show PreShareKey as clear Text so as to see the
password, then copy and paste it to the Zyxel Device.
After all SSO agent configurations are done, right-click the SSO icon in the system tray and select Enable
Zyxel SSO Agent.
USG/ZyWALL User’s Guide
468
CHAPTER 21
Hotspot
21.1 Overview
At the time of writing, the following models support Hotspot management:
• ZyWALL 310
• ZyWALL 1100
• USG310
• USG1100
• USG1900
• USG2200-VPN
21.2 Billing Overview
You can use the built-in billing function to setup billing profiles. A billing profile describes how to charge
users. This chapter also shows you how to select an accounting method, configure a discount price plan
or use an online payment service by credit card.
• Use the General screen (see Section 21.3 on page 469) to configure the general billing settings, such
as the accounting method, currency unit and the SSID profiles to which the settings are applied.
• Use the Billing Profile screen (see Section 21.4 on page 471) to configure the billing profiles for the
web-based account generator and each button on the connected statement printer.
• Use the Discount screen (see Section 21.5 on page 478) to enable and configure discount price plans.
• Use the Payment Service screen (see Section 21.6 on page 480) to enable online payment service
and configure the service pages.
21.2.1 What You Need to Know
Accumulation Accounting Method
The accumulation accounting method allows multiple re-logins until the allocated time period or until
the user account is expired. The Zyxel Device accounts the time that the user is logged in for Internet
access.
Time-to-finish Accounting Method
The time-to-finish accounting method is good for one-time logins. Once a user logs in, the Zyxel Device
stores the IP address of the user’s computer for the duration of the time allocated. Thus the user does not
have to enter the user name and password again for re-login within the allocated time. Once
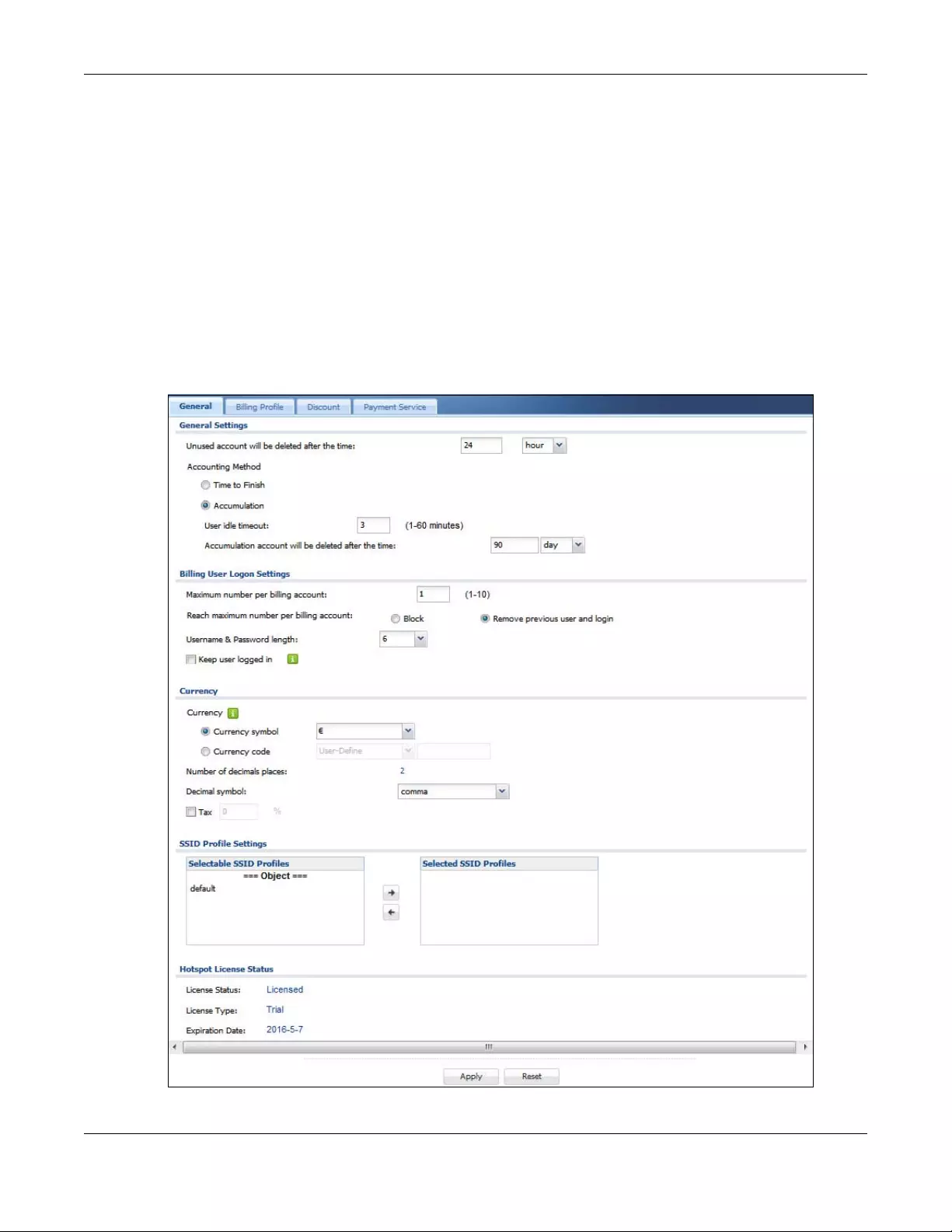
Chapter 21 Hotspot
USG/ZyWALL User’s Guide
469
activated, the user account is valid until the allocated time is reached even if the user disconnects
Internet access for a certain period within the allocated time. For example, Joe purchases a one-hour
time-to-finish account. He starts using the Internet for the first 20 minutes and then disconnects his
Internet access to go to a 20-minute meeting. After the meeting, he only has 20 minutes left on his
account.
21.3 The General Screen
Use this screen to configure the general billing settings, such as the accounting method, currency unit
and the SSID profiles to which the settings are applied. Click Configuration > Hotspot > Billing > General
to open the following screen.
Figure 338 Configuration > Hotspot > Billing > General
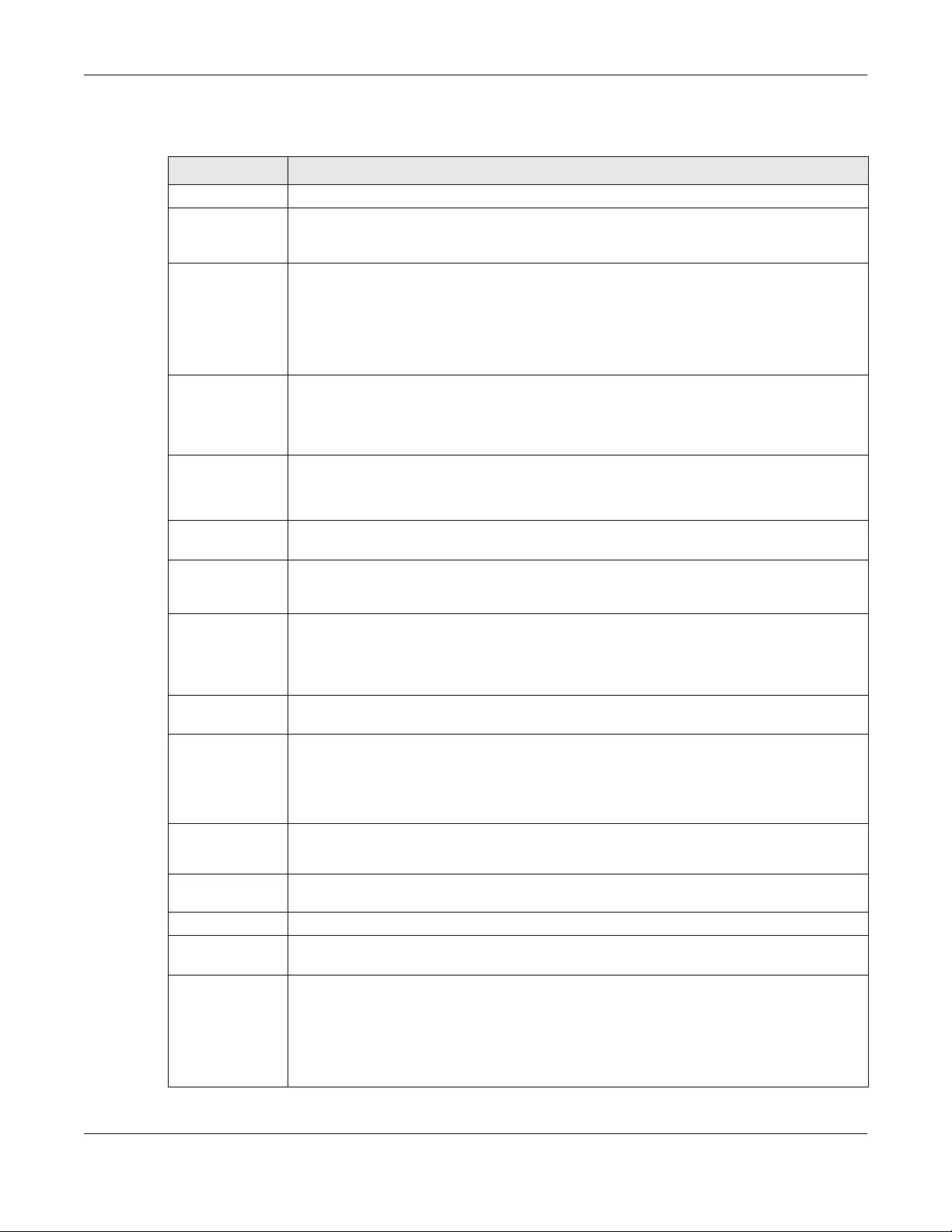
Chapter 21 Hotspot
USG/ZyWALL User’s Guide
470
The following table describes the labels in this screen.
Table 168 Configuration > Hotspot > Billing > General
LABEL DESCRIPTION
General Settings
Unused account
will be deleted
after the time:
Enter the number and select a time unit from the drop-down list box to specify how long to wait
before the Zyxel Device deletes an account that has not been used.
Accounting
Method
Select Time to Finish to allow each user a one-time login. Once the user logs in, the system starts
counting down the pre-defined usage even if the user stops the Internet access before the
time period is finished. If a user disconnects and reconnects before the allocated time expires,
the user does not have to enter the user name and password to access the Internet again.
Select Accumulation to allow each user multiple re-login until the time allocated is used up. The
Zyxel Device accounts the time that the user is logged in for Internet access.
User idle
timeout The Zyxel Device automatically disconnects a computer from the network after a period of
inactivity. The user may need to enter the username and password again before access to the
network is allowed.
If you select Accumulation, specify the idle timeout between 1 and 60 minutes.
Accumulatio
n account will
be deleted
after the time:
Enter the number and select a time unit from the drop-down list box to specify how long to wait
before the Zyxel Device deletes the account.
This is for use with accumulation accounting.
Billing User Logon
Settings
Maximum
number per
billing account
Enter the maximum number of the users that are allowed to log in with the same account.
Reach maximum
number per
billing account
Select Block to stop new users from logging in when the Maximum number per billing account
is reached.
Select Remove previous user and login to disassociate the first user that logged in and allow
new user to log in when the Maximum number per billing account is reached.
Username &
Password length
Select to specify how many characters the username and password of a newly-created
dynamic guest account will have after you click Apply.
Keep user logged
in
Select to let the users automatically log in without entering their user name and password if the
Zyxel Device restarts.
Note: This works only for free guest accounts or when the accounting method is Time
to Finish.
Currency Select the appropriate currency symbol or currency unit.
If you set Currency code to User-Define, enter a three-letter alphabetic code manually.
Number of
decimals places
This shows the number of decimal places to be used for billing.
Decimal symbol Select whether you would like to use a dot (.) or a comma (,) for the decimal point.
Tax Select this option to charge sales tax for the account. Enter the tax rate (a 6% sales tax is
entered as 6).
SSID Profile
Settings
The Selectable SSID Profiles list displays the name(s) of the SSID profile(s) to which you can
apply the general billing settings.
To apply settings to an SSID profile, you can double-click a single entry to move it or use the
[Shift] or [Ctrl] key to select multiple entries and click the right arrow button to add to the
Selected SSID Profiles list. To remove an SSID profile, select the name(s) in the Selected SSID
Profiles list and click the left arrow button.
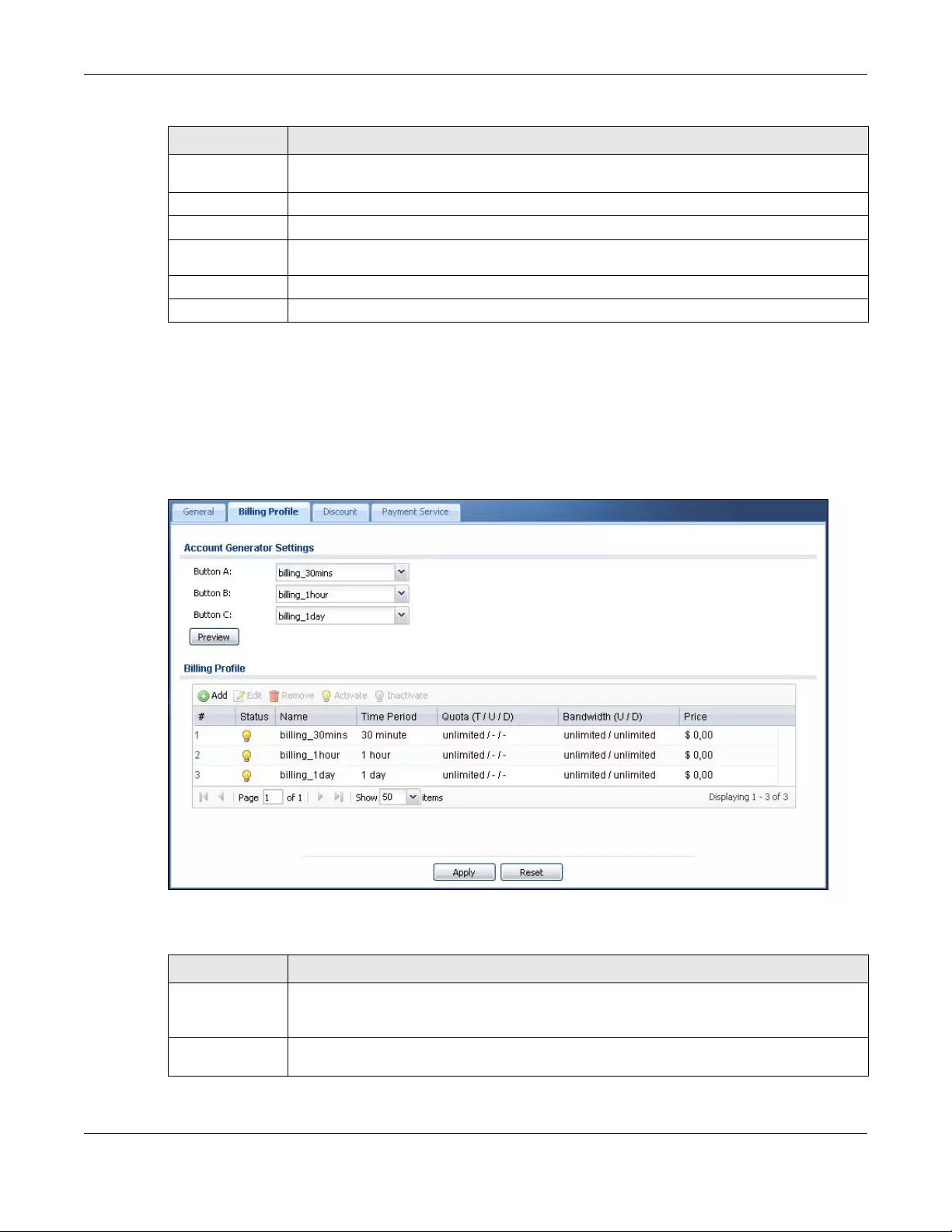
Chapter 21 Hotspot
USG/ZyWALL User’s Guide
471
21.4 The Billing Profile Screen
Use this screen to configure the billing profiles that defines the maximum Internet access time and
charge per time unit. Click Configuration > Hotspot > Billing > Billing Profile to open the following screen.
Figure 339 Configuration > Hotspot > Billing > Billing Profile
The following table describes the labels in this screen.
Hotspot License
Status
License Status This field displays whether the service is activated (Licensed) or not (Not Licensed).
License Type This shows whether you have a trial or standard license or none (Trial, Standard, None).
Expiration
Date This shows when your hotspot license will expire.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
Table 168 Configuration > Hotspot > Billing > General (continued)
LABEL DESCRIPTION
Table 169 Configuration > Hotspot > Billing > Billing Profile
LABEL DESCRIPTION
Account
Generator
Settings
Button A ~ C Select a billing profile for each button of the web-based account generator. The buttons
correspond to the buttons on a connected statement printer.
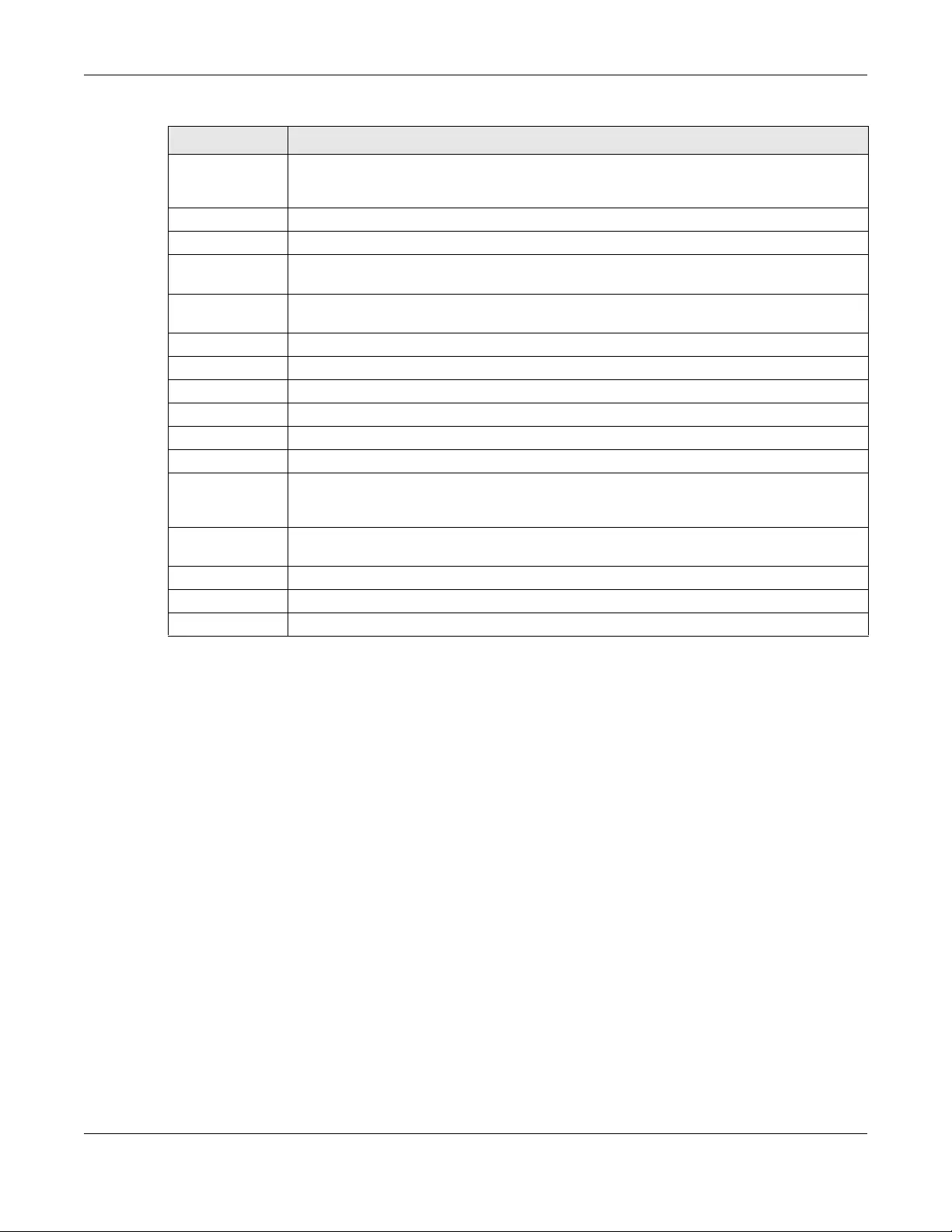
Chapter 21 Hotspot
USG/ZyWALL User’s Guide
472
21.4.1 The Account Generator Screen
The Account Generator screen allows you to automatically create dynamic guest accounts (see
Section 7.10 on page 202 and Dynamic-Guest Accounts for more information on dynamic guest
accounts).
Click Configuration > Hotspot > Billing > Billing Profile and then the Preview button to open this screen.
You can also open this screen by logging into the Web Configurator with the guest-manager account.
Preview Click this button to open the Account Generator screen, where you can generate a dynamic
guest account and print the account information using a statement printer connected to the
Zyxel Device (see Section 21.4.1 on page 472 for more information).
Billing Profile
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
#This field is a sequential value, and it is not associated with a specific entry.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
Name This field displays the descriptive profile name for this entry.
Time Period This field displays the duration of the billing period.
Quota (T/U/D) This field displays how much data in both directions (Total) or upstream data (Upload) and
downstream data (Download) can be transmitted through the WAN interface before the
account expires.
Bandwidth (U/D) This field displays the maximum upstream (Upload) and downstream (Download) bandwidth
allowed for the user account in kilobits per second.
Price This field displays each profile’s price per time unit.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
Table 169 Configuration > Hotspot > Billing > Billing Profile (continued)
LABEL DESCRIPTION
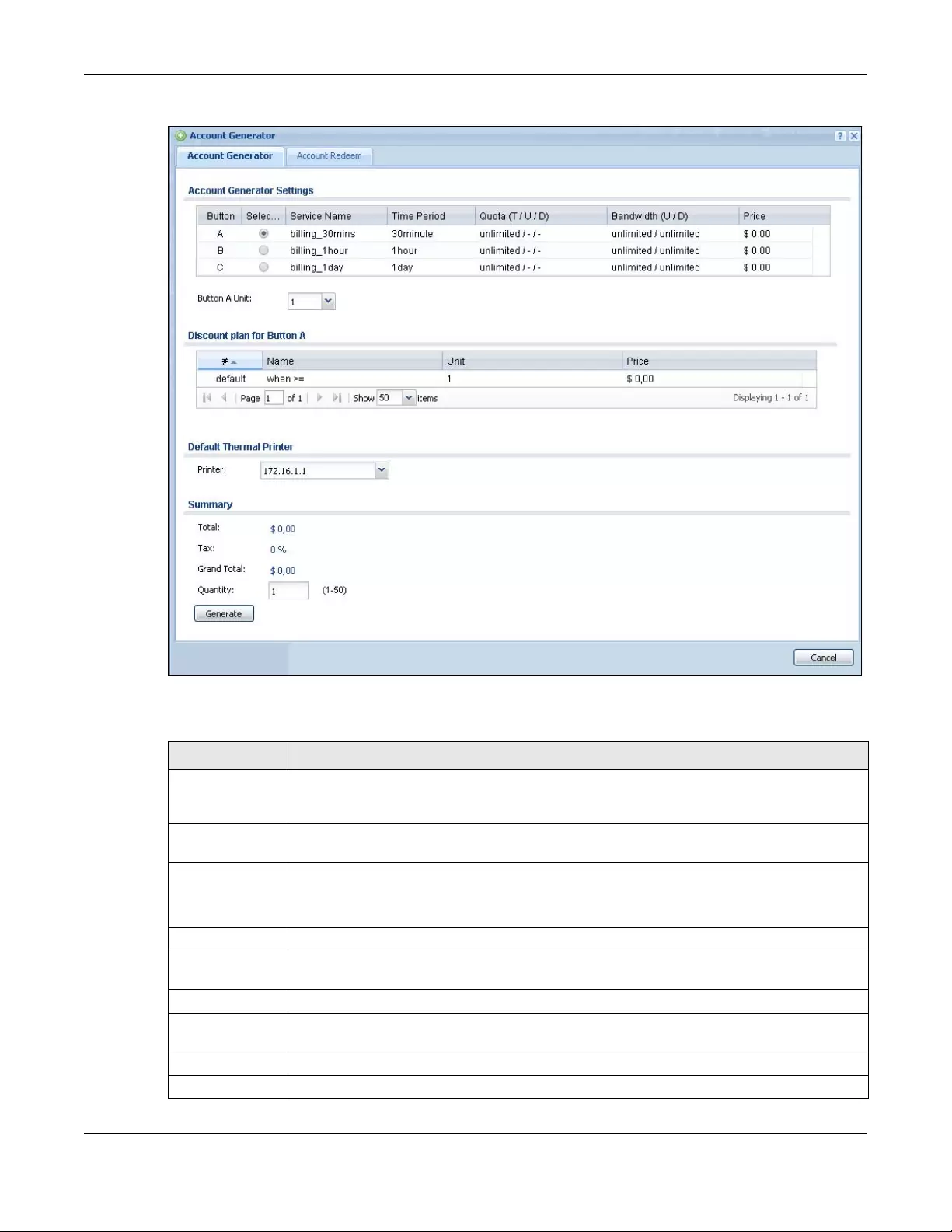
Chapter 21 Hotspot
USG/ZyWALL User’s Guide
473
Figure 340 Account Generator
The following table describes the labels in this screen.
Table 170 Account Generator
LABEL DESCRIPTION
Account
Generator
Settings
Select a button and specify how many units of billing period to be charged for new account in
the Button x Unit field.
Discount plan for
Button x
This section displays only when you enable the discount price plan in the Billing > Discount
screen.
#This is the number of each discount level.
The default (first) level cannot be edited or deleted. It is created automatically according to
the billing profile of the button you select.
Name This field displays the conditions of each discount level.
Unit This field displays the duration of the billing period that should be reached before the Zyxel
Device charges users at this level.
Price This field displays the price per time unit for each level.
Default Thermal
Printer
Select a statement printer that is attached to the Zyxel Device. It displays n/a if there is no
printer attached.
Summary
Total This shows the total price for the account before sales tax is added.
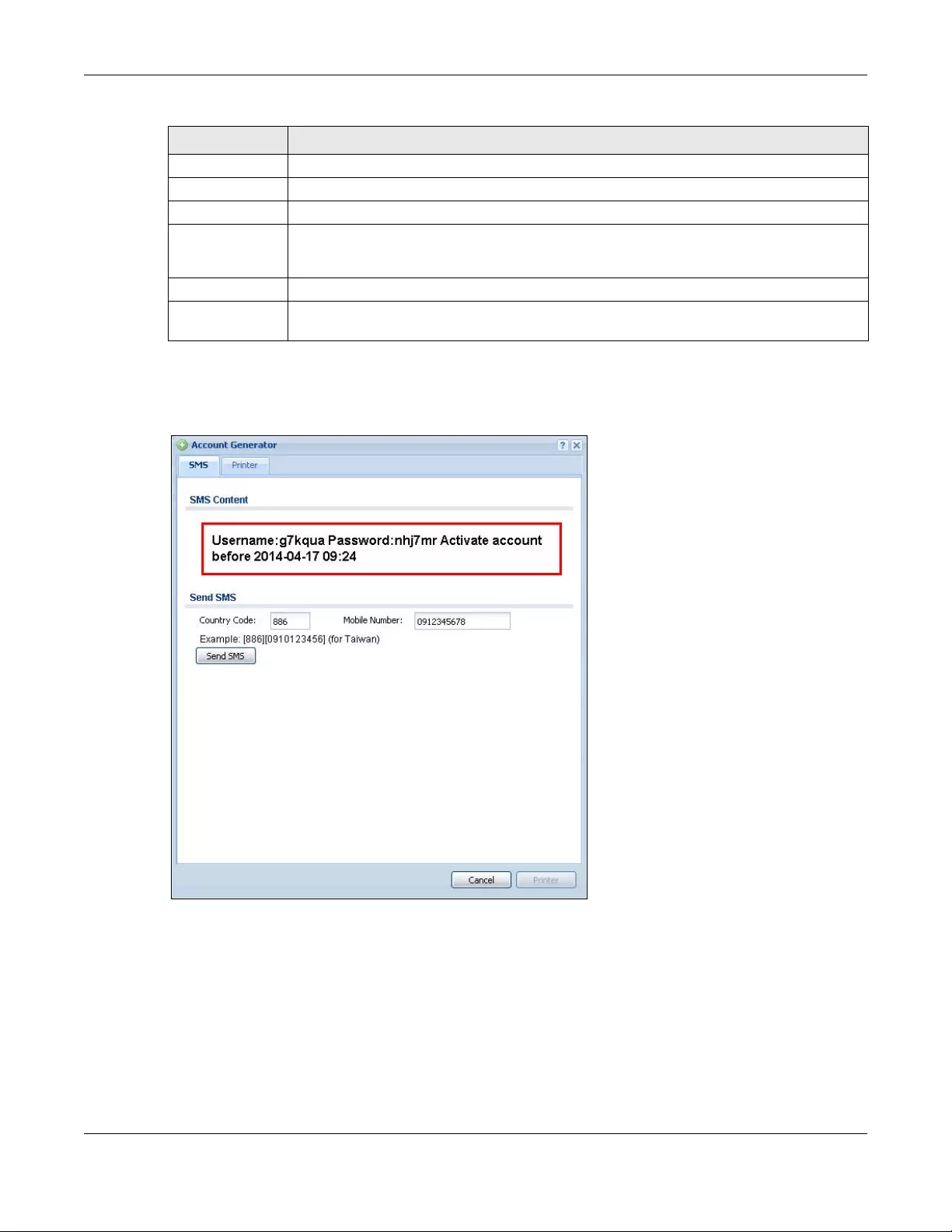
Chapter 21 Hotspot
USG/ZyWALL User’s Guide
474
The following figure shows an example SMS message with account information. The SMS screen displays
only when you enable SMS in the Configuration > Hotspot > SMS screen. You can enter the user’s mobile
phone number and click Send SMS to send the account information in an SMS text message to the
user’s mobile phone. Click Cancel to close this window when you are finished viewing it.
Tax This shows the tax rate.
Grand Total This shows the total price including tax.
Quantity Specify the number of account to be created.
Generate Click Generate to generate an account based on the billing settings you configure for the
selected button in the Billing Profile screen. A window displays showing the SMS message and/
or a printout preview of the account generated.
Cancel Click Cancel to exit this screen without saving.
Logout Click Logout to log out of the web configurator. This button is available only when you open this
screen by logging in with the guest-manager account.
Table 170 Account Generator (continued)
LABEL DESCRIPTION
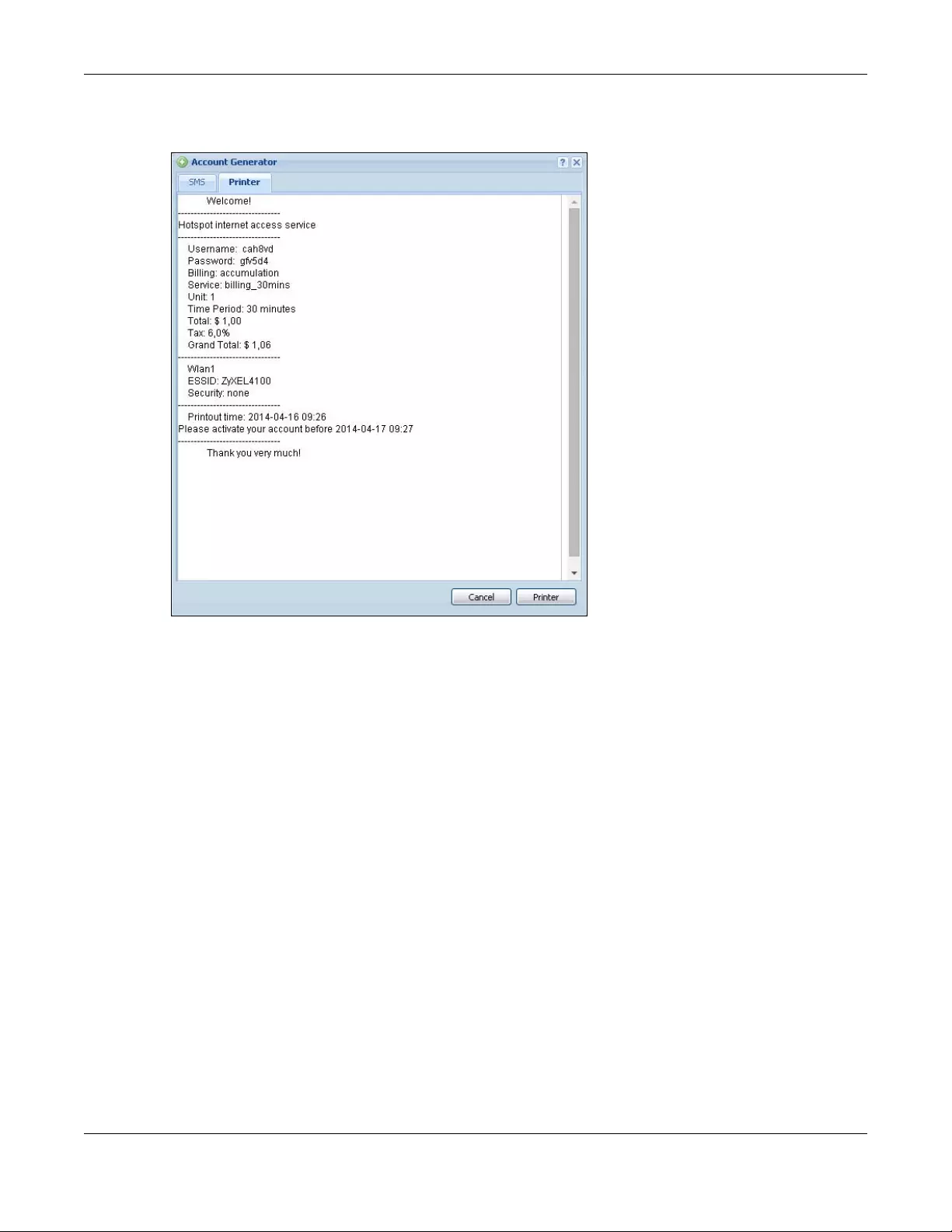
Chapter 21 Hotspot
USG/ZyWALL User’s Guide
475
The Printer screen shows a printout preview example. Click Printer to print this subscriber statement. Click
Cancel to close this window when you are finished viewing it.
21.4.2 The Account Redeem Screen
The Account Redeem screen allows you to send SMS messages for certain accounts. Click the Account
Redeem tab in the Account Generator screen to open this screen.
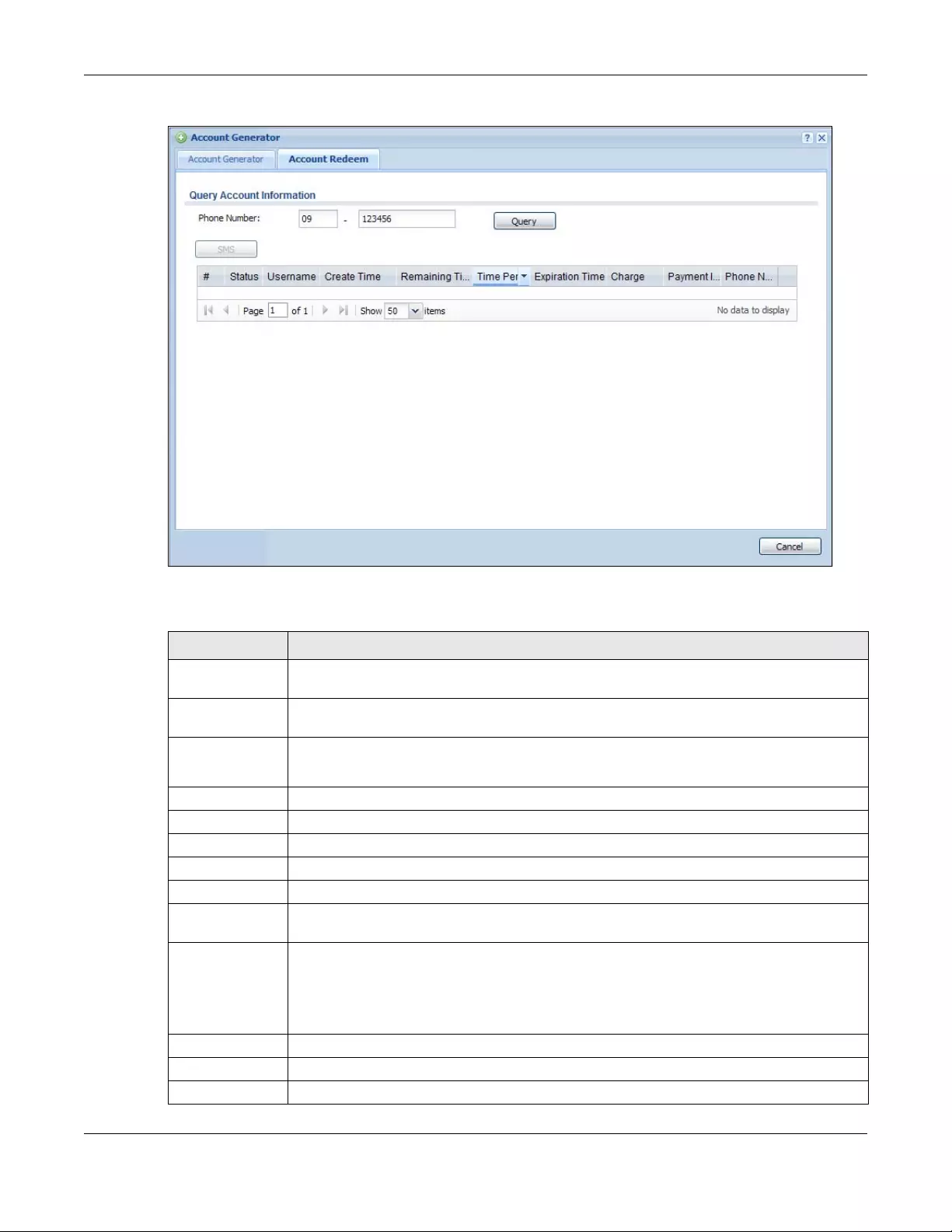
Chapter 21 Hotspot
USG/ZyWALL User’s Guide
476
Figure 341 Account Redeem
The following table describes the labels in this screen.
Table 171 Account Redeem
LABEL DESCRIPTION
Query Account
Information
Phone Number Enter the country code and mobile phone number and click Query to display only the
account(s) that has the specified phone number.
SMS Click this button to send text messages for the accounts in the list below.
You can use this button only when SMS is enabled and there is at least one account in the list.
# This is the index number of the dynamic guest account in the list.
Status This field displays whether an account expires or not.
Username This field displays the user name of the account.
Create Time This field displays when the account was created.
Remaining Time This field displays the amount of Internet access time remaining for each account.
Time Period This field displays the total account of time the account can use to access the Internet through
the Zyxel Device.
Expiration Time This field displays the date and time the account becomes invalid.
Note: Once the time allocated to a dynamic account is used up or a dynamic
account remains unused after the expiration time, the account is deleted from
the account list.
Charge This field displays the total cost of the account.
Payment Info This field displays the method of payment for each account.
Phone Num This field displays the mobile phone number for the account.
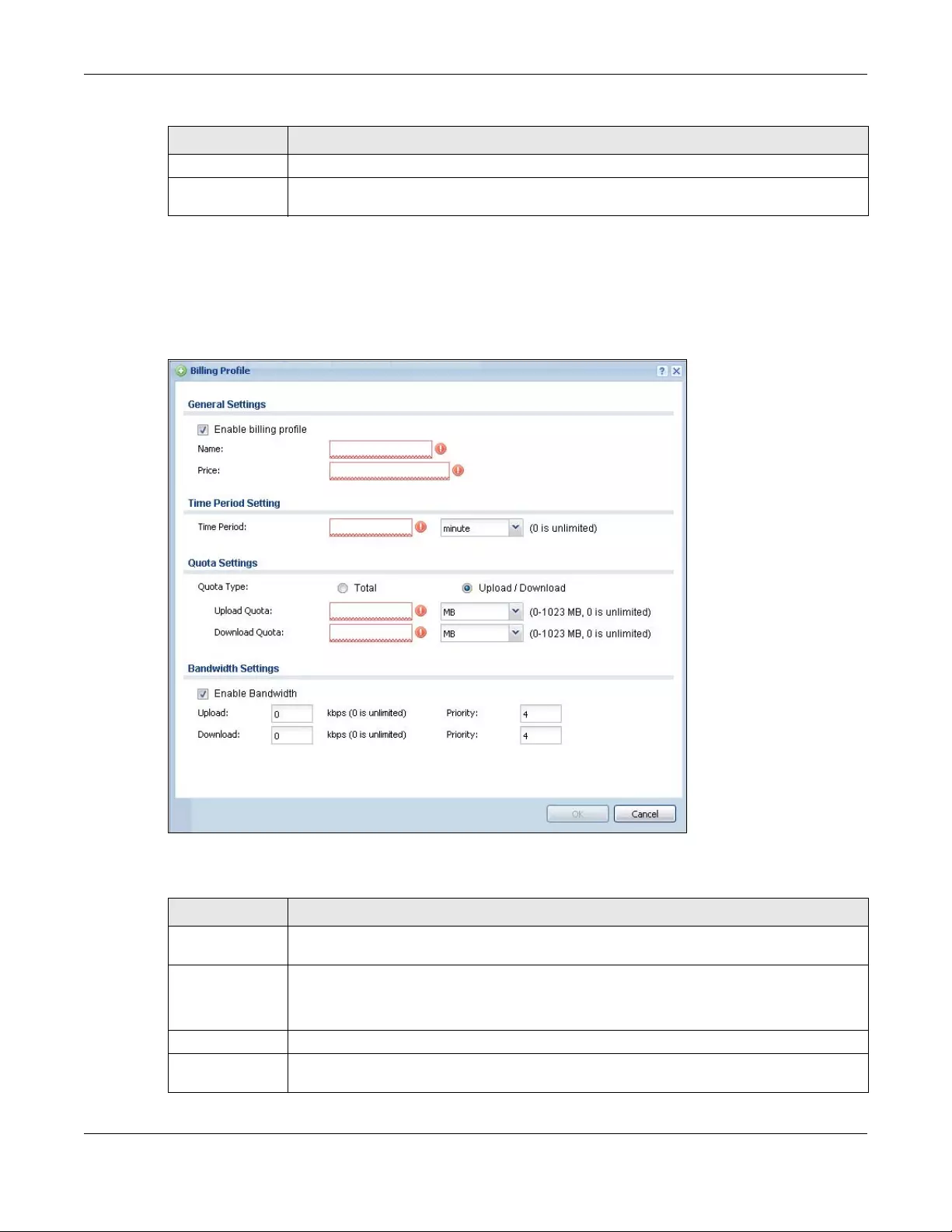
Chapter 21 Hotspot
USG/ZyWALL User’s Guide
477
21.4.3 The Billing Profile Add/Edit Screen
The Billing Profile Add/Edit screen allows you to create a new billing profile or edit an existing one. Click
Configuration > Hotspot > Billing > Billing Profile and then an Add or Edit icon to open this screen.
Figure 342 Configuration > Hotspot > Billing > Billing Profile > Add/Edit
The following table describes the labels in this screen.
Cancel Click Cancel to exit this screen without saving.
Logout Click Logout to log out of the web configurator. This button is available only when you open this
screen by logging in with the guest-manager account.
Table 171 Account Redeem (continued)
LABEL DESCRIPTION
Table 172 Configuration > Hotspot > Billing > Billing Profile > Add/Edit
LABEL DESCRIPTION
Enable billing
profile
Select this option to activate the profile.
Name Enter a name for the billing profile.
You can use up to 31 alphanumeric characters (A-Z, a-z, 0-9) and underscores (_). Spaces are
not allowed. The first character must be a letter.
Price Define each profile’s price, up to 999999.99, per time unit.
Time Period Set the duration of the billing period (minute, hour, or day). When this period expires, the user’s
access will be stopped.
Chapter 21 Hotspot
USG/ZyWALL User’s Guide
478
21.5 The Discount Screen
Use this screen to configure a custom discount pricing plan. This is useful for providing reduced rates for
purchases of longer periods of time. You can charge higher rates per unit at lower levels (fewer units
purchased) and lower rates per unit at higher levels (more units purchased). Click Configuration >
Hotspot > Billing > Discount to open the following screen.
Note: The discount price plan does not apply to users who purchase access time online with a
credit card.
Quota Type The quota settings section is NOT available when you set Accounting Method to Time to Finish
in the Billing > General screen.
Set a limit for the user accounts. This only applies to user’s traffic that is received or transmitted
through the WAN interface.
Note: When the limit is exceeded, the user is not allowed to access the Internet
through the Zyxel Device.
Select Total to set a limit on the total traffic in both directions.
Select Upload/Download to set a limit on the upstream traffic and downstream traffic
respectively.
Total Quota If you select Total, specify how much downstream and/or upstream data (in MB (Megabytes)
or GB (Gigabytes)) can be transmitted through the WAN interface before the account expires.
0 means there is no data limit for the user account.
Upload Quota If you select Upload/Download, specify how much upstream data (in MB (Megabytes) or GB
(Gigabytes)) can be transmitted through the WAN interface before the account expires.
0 means there is no data limit for the user account.
Download Quota If you select Upload/Download, specify how much downstream data (in MB (Megabytes) or GB
(Gigabytes)) can be transmitted through the WAN interface before the account expires.
0 means there is no data limit for the user account.
Enable
Bandwidth
Select this option to turn on bandwidth management for the user accounts.
Upload Specify the maximum outgoing bandwidth allowed for the user account in kilobits per second.
Upload refers to the traffic the Zyxel Device sends out from a user.
Download Specify the maximum incoming bandwidth allowed for the user account in kilobits per second.
Download refers to the traffic the Zyxel Device sends to a user.
Priority Enter a number between 1 and 7 to set the priority for the user’s traffic. The smaller the number,
the higher the priority.
Traffic with a higher priority is given bandwidth before traffic with a lower priority.
Note: The priority setting here has priority over the priority setting in a bandwidth
management rule.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
Table 172 Configuration > Hotspot > Billing > Billing Profile > Add/Edit (continued)
LABEL DESCRIPTION
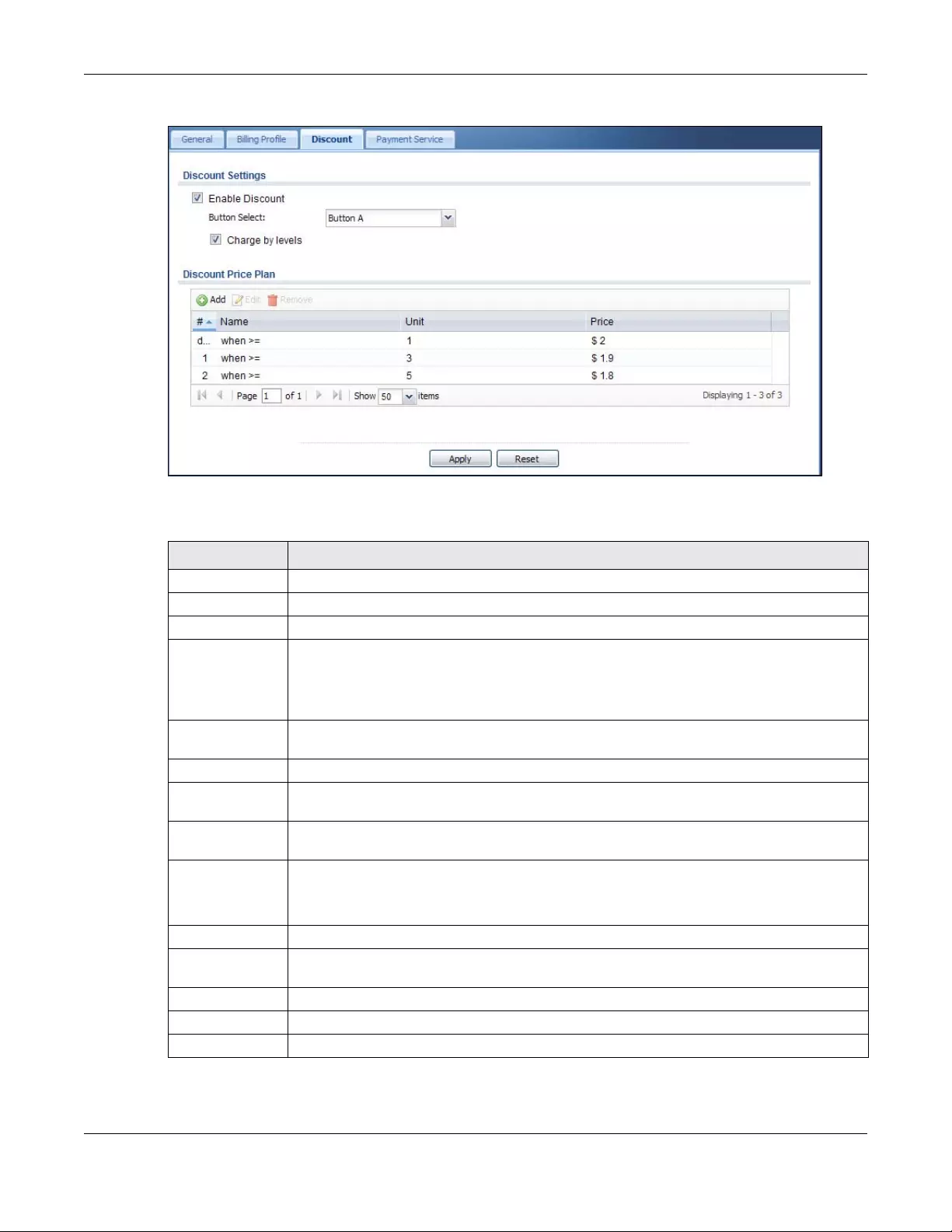
Chapter 21 Hotspot
USG/ZyWALL User’s Guide
479
Figure 343 Configuration > Hotspot > Billing > Discount
The following table describes the labels in this screen.
Table 173 Configuration > Hotspot > Billing > Discount
LABEL DESCRIPTION
Discount Settings
Enable Discount Select the check box to activate the discount price plan.
Button Select Select a button from the drop-down list box to assign the base charge.
Charge by levels Select this to charge the rate at each successive level from the first level (most expensive per
unit) to the highest level (least expensive per unit) that the total purchase reaches.
Otherwise, clear this to charge all of the user’s time units only at the highest level (least
expensive) that their total purchase reaches.
Discount Price
Plan
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
#This is the number of each discount level.
The default (first) level cannot be edited or deleted. It is created automatically according to
the billing profile of the button you select.
Name This field displays the conditions of each discount level.
Unit This field displays the duration of the billing period that should be reached before the Zyxel
Device charges users at this level.
Price This field displays the price per time unit for each level.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
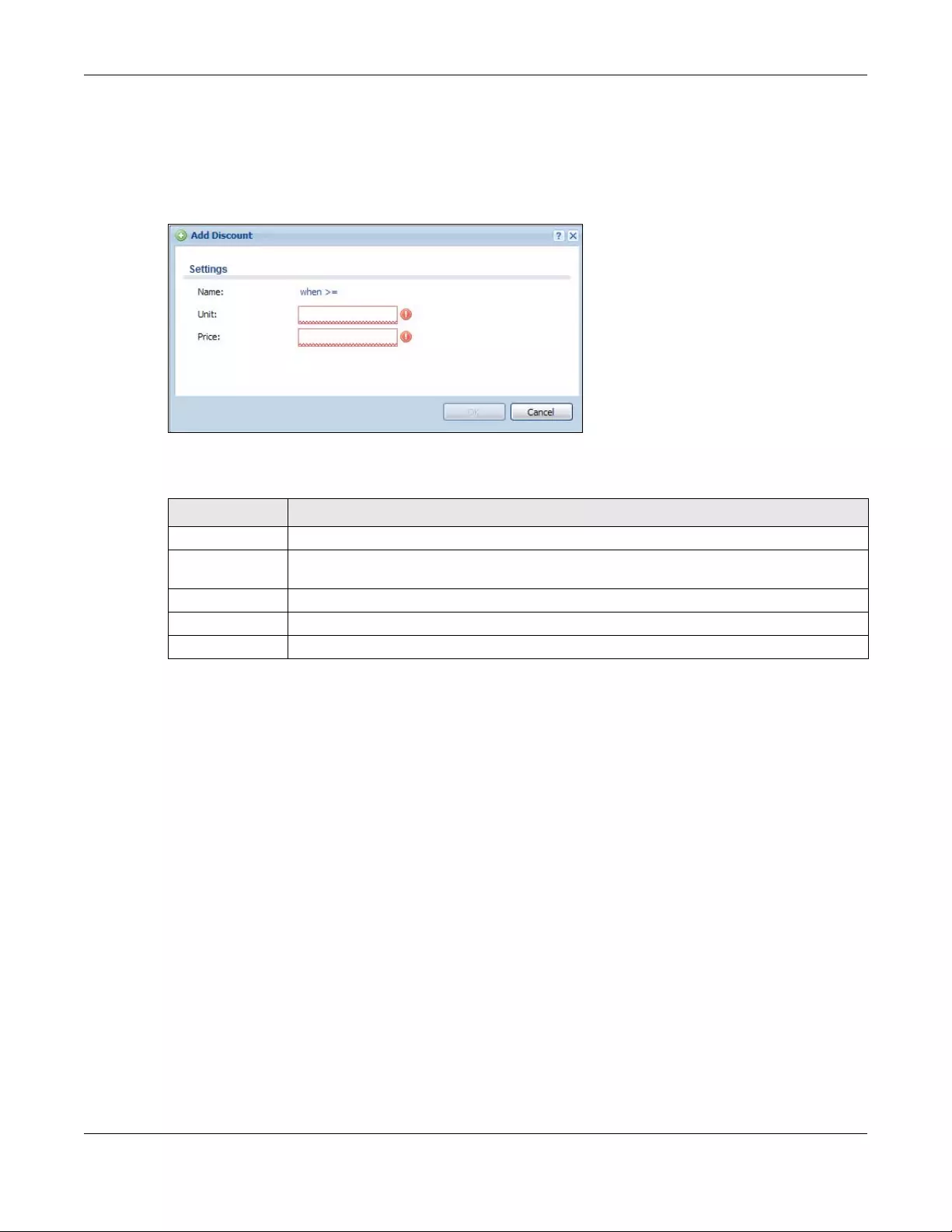
Chapter 21 Hotspot
USG/ZyWALL User’s Guide
480
21.5.1 The Discount Add/Edit Screen
The Discount Add/Edit screen allows you to create a new discount level or edit an existing one. Click
Configuration > Hotspot > Billing > Discount and then an Add or Edit icon to open this screen.
Figure 344 Configuration > Hotspot > Billing > Discount > Add/Edit
The following table describes the labels in this screen.
21.6 The Payment Service General Screen
Use this screen to use a credit card service to authorize, process, and manage credit card transactions
directly through the Internet. You must register with the supported credit card service before you can
configure the Zyxel Device to handle credit card transactions. Click Configuration > Hotspot > Billing >
Payment Service to open the following screen.
Table 174 Configuration > Hotspot > Billing > Discount > Add/Edit
LABEL DESCRIPTION
Name This field displays the conditions of each discount level.
Unit Set the duration of the billing period that should be reached before the Zyxel Device charges
users at this level.
Price Define this level’s charge per time unit.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
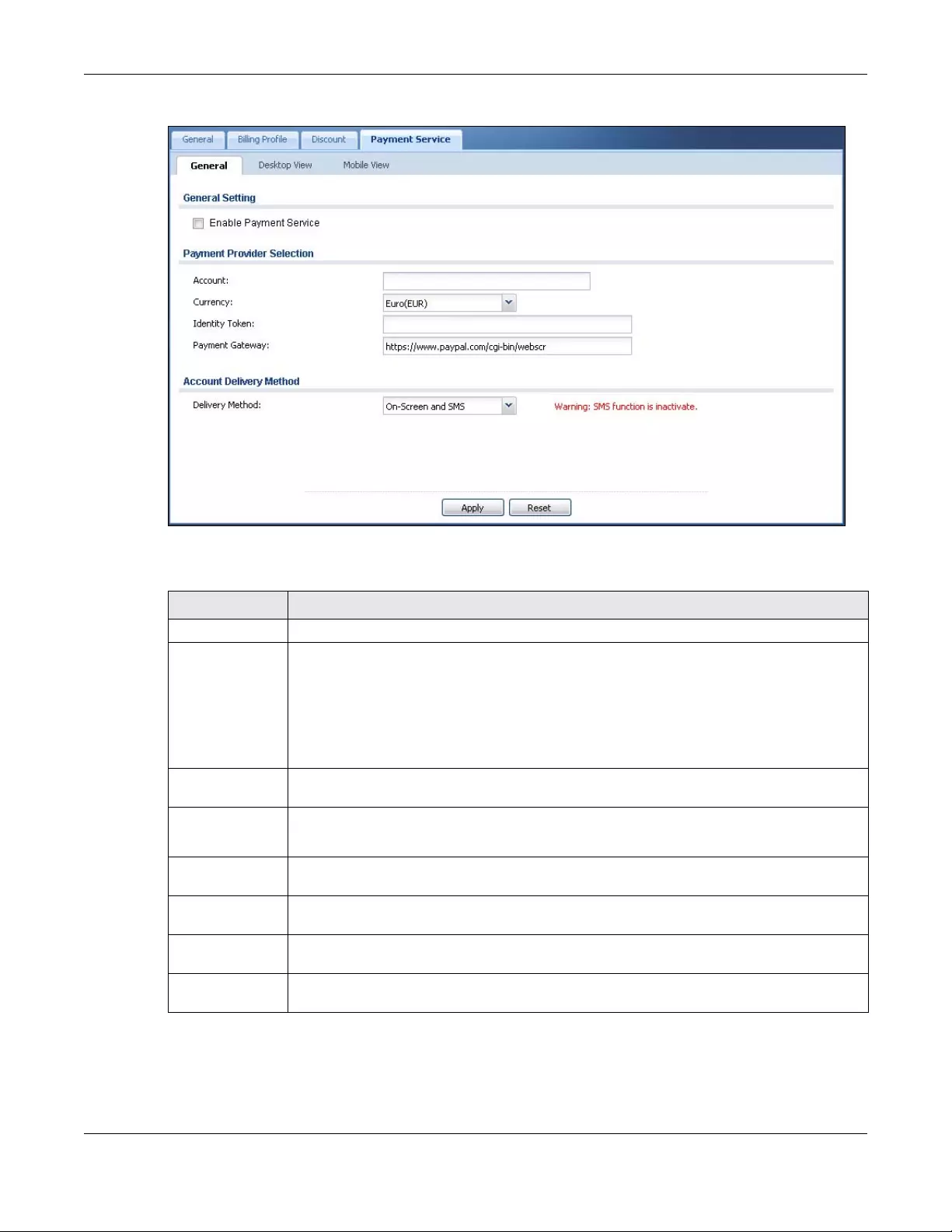
Chapter 21 Hotspot
USG/ZyWALL User’s Guide
481
Figure 345 Configuration > Hotspot > Billing > Payment Service > General
The following table describes the labels in this screen.
Table 175 Configuration > Hotspot > Billing > Payment Service > General
LABEL DESCRIPTION
General Setting
Enable Payment
Service
Select the check box to use PayPal to authorize credit card payments.
Note: After you set up web authentication policies and enable the online payment
service on the Zyxel Device, a link displays in the login screen when users try to
access the Internet. The link redirects users to a screen where they can make
online payments by credit card to purchase access time and get dynamic
guest account information.
Payment Provider
Selection
Account You should already have a PayPal account to receive credit card payments.
Enter your PayPal account name.
Currency Select the currency in which payments are made. The available options depend on currencies
that PayPal supports.
Identity Token Enter the ID token provided to you by PayPal after successfully applying for your PayPal
account.
Payment
Gateway
Enter the address of the PayPal gateway provided to you by PayPal after applying for your
PayPal account.
Account Delivery
Method
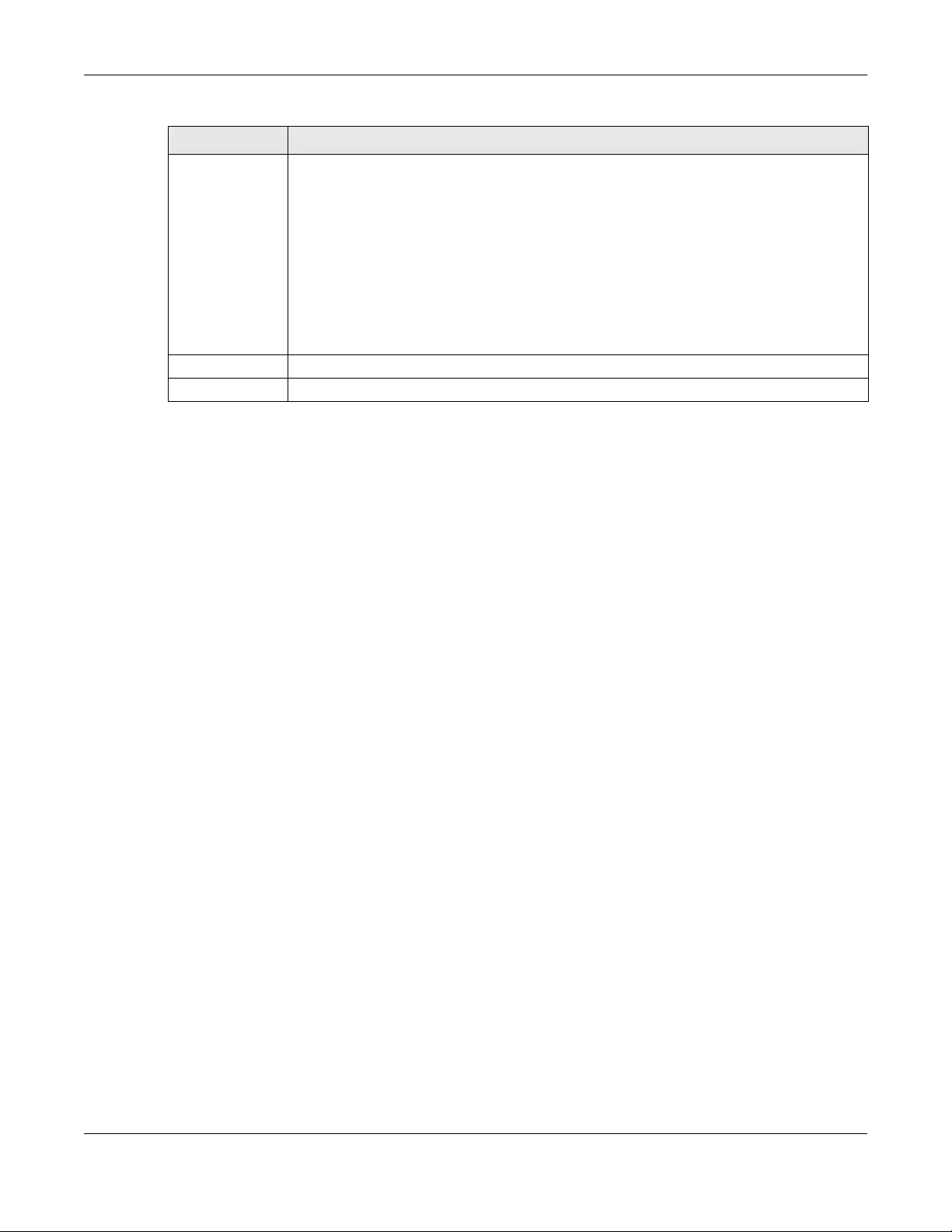
Chapter 21 Hotspot
USG/ZyWALL User’s Guide
482
21.6.1 The Payment Service Desktop View / Mobile View Screen
Use this screen to customize the online payment service pages that displays after an unauthorized user
clicks the link in the Web Configurator login screen to purchase access time. You can configure both
the desktop and mobile versions of the service pages. Users click a link in the pages to switch between
the two versions.
Click Configuration > Hotspot > Billing > Payment Service > Desktop View or Mobile View to open the
following screen.
Delivery Method Specify how the Zyxel Device provides dynamic guest account information after the user’s
online payment is done.
Select On-Screen to display the user account information in the web screen.
Select SMS to use Short Message Service (SMS) to send account information in a text message
to the user’s mobile device.
Select On-Screen and SMS to provide the account information both in the web screen and via
SMS text messages.
Note: You should have enabled SMS in the Configuration > SMS screen to send text
messages to the user’s mobile device.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
Table 175 Configuration > Hotspot > Billing > Payment Service > General (continued)
LABEL DESCRIPTION
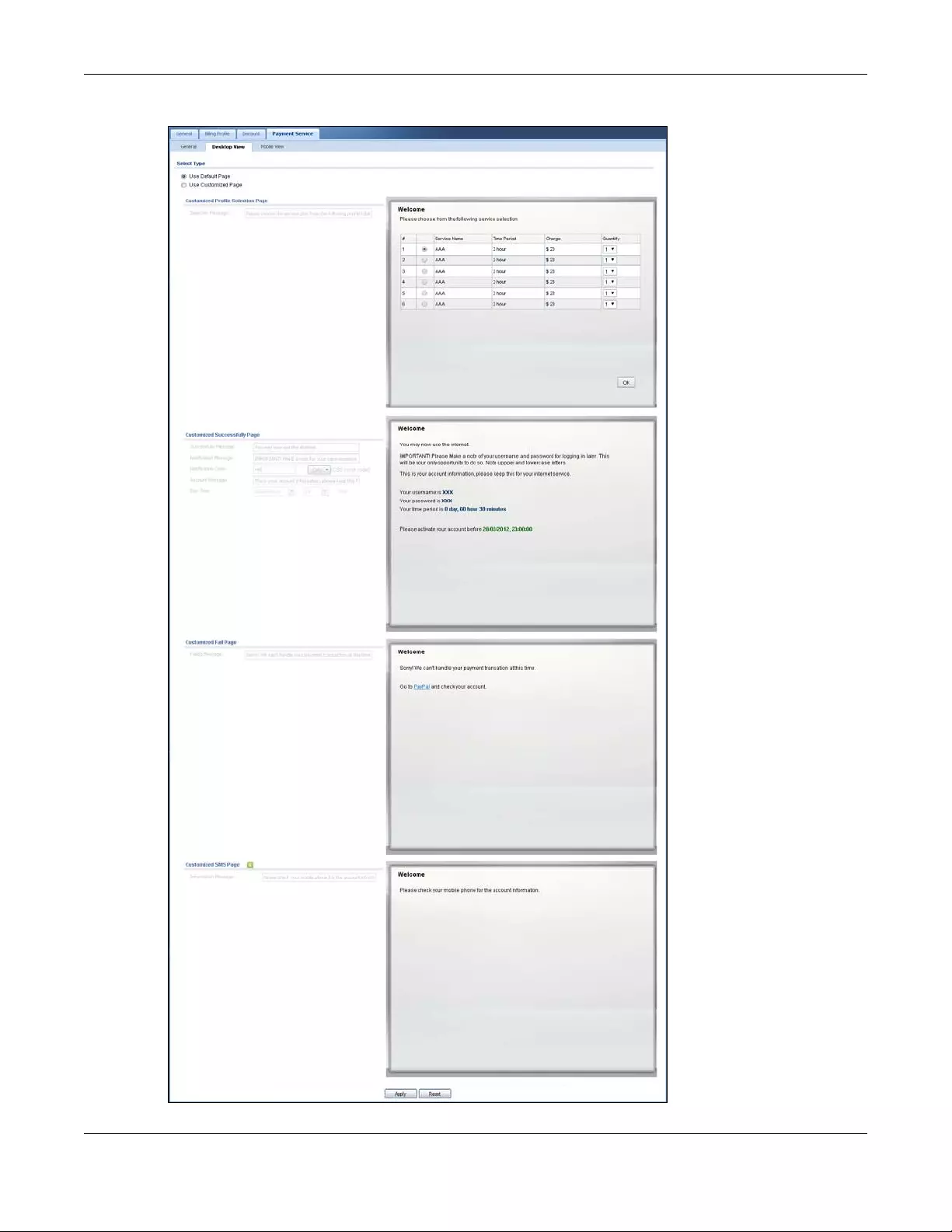
Chapter 21 Hotspot
USG/ZyWALL User’s Guide
483
Figure 346 Configuration > Hotspot > Billing > Payment Service > Desktop View
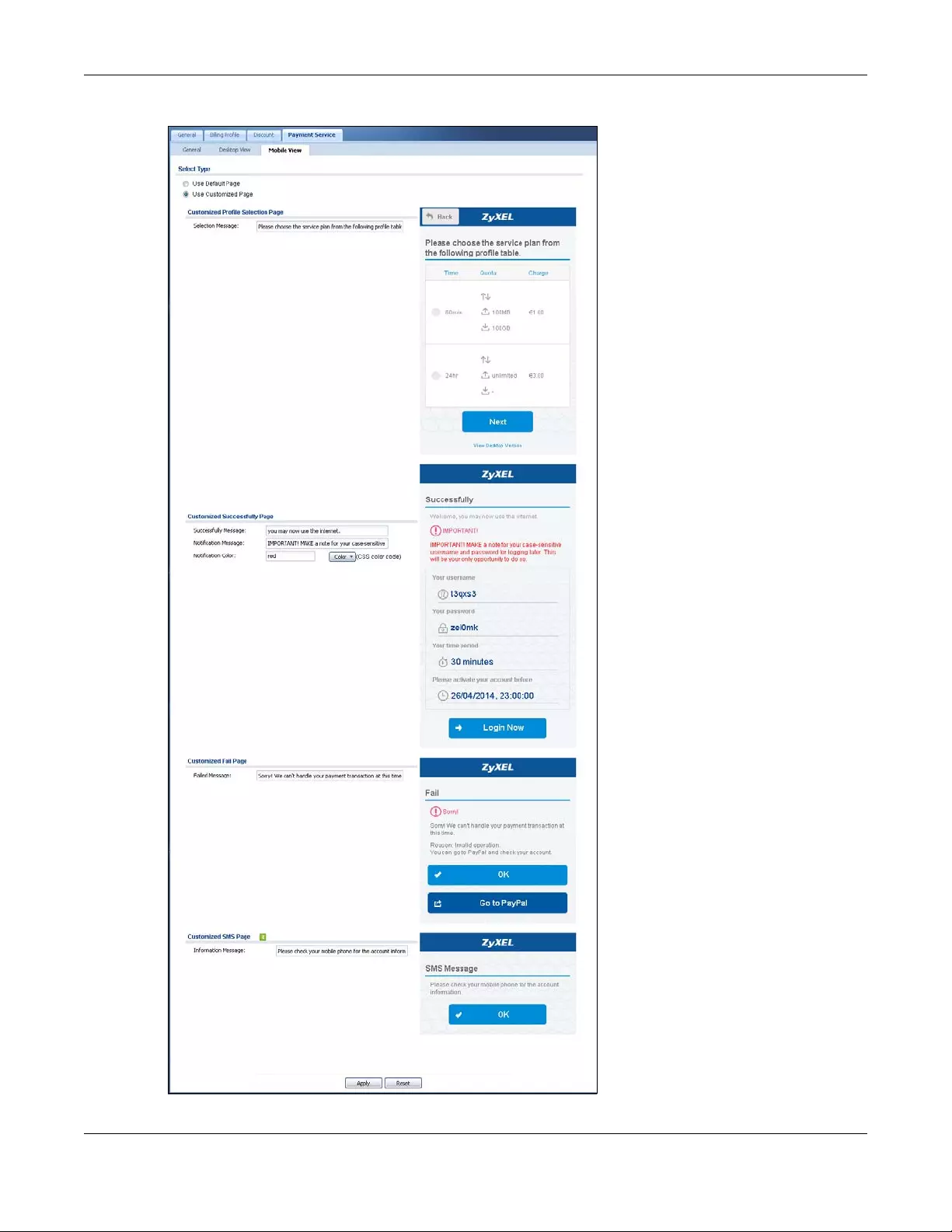
Chapter 21 Hotspot
USG/ZyWALL User’s Guide
484
Figure 347 Configuration > Hotspot > Billing > Payment Service > Mobile View
Chapter 21 Hotspot
USG/ZyWALL User’s Guide
485
The following table describes the labels in this screen.
Table 176 Configuration > Hotspot > Billing > Payment Service > Desktop View or Mobile View
LABEL DESCRIPTION
Select Type
Use Default Page Select this to use the default online payment service page built into the device. If you later
create a custom online payment service page, you can still return to the Zyxel Device’s default
page as it is saved indefinitely.
Use Customized
Page
Select this to use a custom online payment service page instead of the default one built into
the Zyxel Device. Once this option is selected, the custom page controls below become
active.
Customized
Profile Selection
Page
Selection
Message
Enter a note to display in the first welcome page that allows users to choose a billing period
they want. Use up to 256 printable ASCII characters. Spaces are allowed.
Customized
Successfully Page
Successfully
Message
Enter a note to display in the second page after the user’s online payment is made
successfully. Use up to 256 printable ASCII characters. Spaces are allowed.
Notification
Message
Enter the important information you want to display. Use up to 256 printable ASCII characters.
Spaces are allowed.
Notification Color Specify the font color of the important information. You can use the color palette chooser, or
enter a color value of your own.
Account
Message
Enter a note to display above the user account information. Use up to 256 printable ASCII
characters. Spaces are allowed.
Day Time Select the format in which you want to display the date and how long an account is allowed
to stay unused before it expires.
Customized Fail
Page
Failed Message Enter a note to display when the user’s online payment failed. Use up to 256 printable ASCII
characters. Spaces are allowed.
Customized SMS
Page
Information
Message
Enter a note to display when you set the Zyxel Device to send account information via SMS text
messages. Use up to 256 printable ASCII characters. Spaces are allowed.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.

USG/ZyWALL User’s Guide
486
CHAPTER 22
Printer Manager
22.1 Printer Manager Overview
You can create dynamic guest accounts and print guest account information by pressing the button on
an external statement printer, such as SP350E.
Make sure that the printer is connected to the appropriate power and the Zyxel Device, and that there
is printing paper in the printer. Refer to the printer’s documentation for details.
22.1.1 What You Can Do in this Chapter
• Use the Printer Manager > General screen (see Section 21.3 on page 469) to configure the printer list
and enable printer management.
• Use the Printer Manager > Printout Configuration screen (see Section 22.3 on page 492) to customize
the account printout.
22.2 The General Setting Screen
Use this screen to configure a printer list and allow the Zyxel Device to monitor the printer status. Click
Configuration > Hotspot > Printer Manager > General to open the following screen.
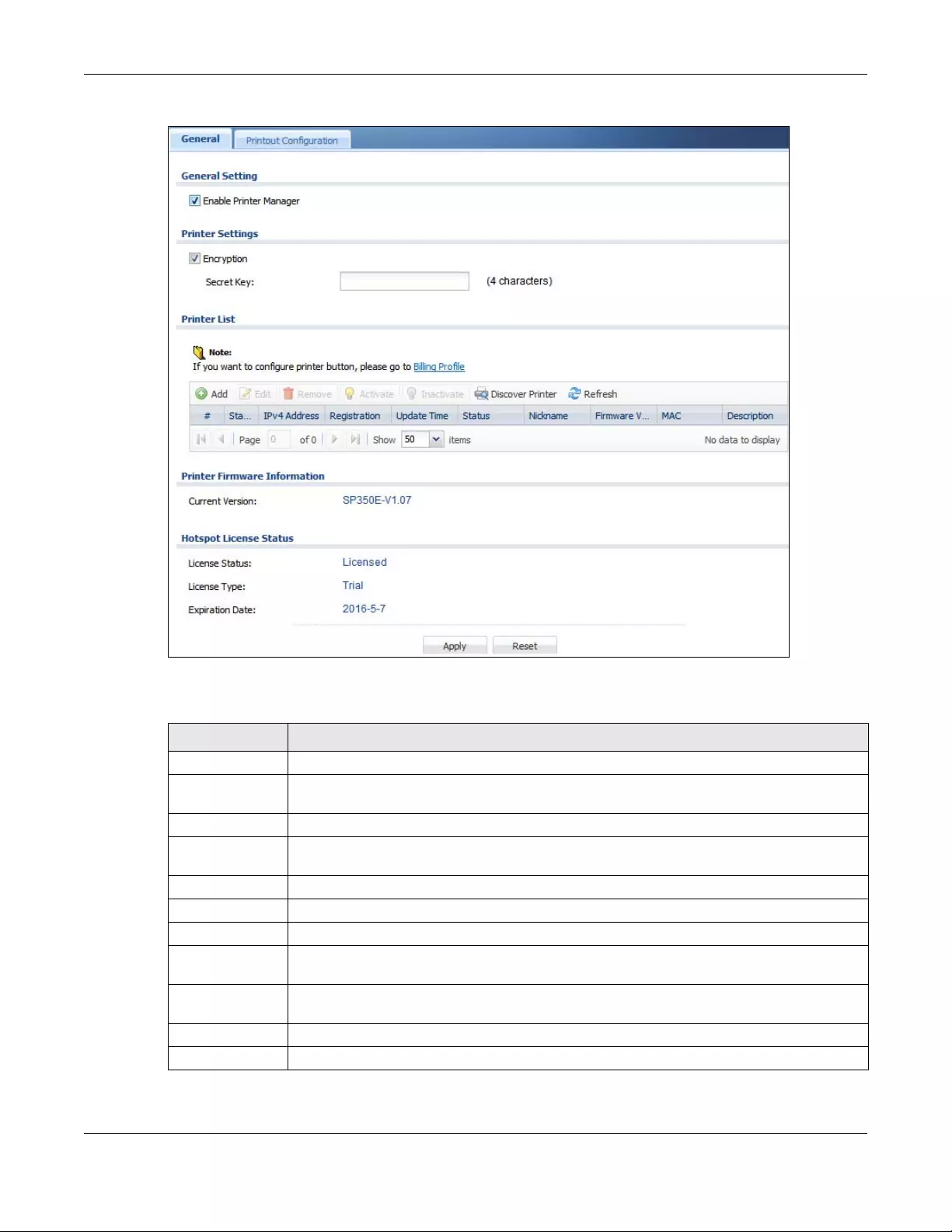
Chapter 22 Printer Manager
USG/ZyWALL User’s Guide
487
Figure 348 Configuration > Hotspot > Printer Manager > General
The following table describes the labels in this screen.
Table 177 Configuration > Hotspot > Printer Manager > General
LABEL DESCRIPTION
General Setting
Enable Printer
Manager
Select the check box to allow the Zyxel Device to manage and monitor the printer status.
Printer Settings
Encryption Select the check box to turn on data encryption. Data transmitted between the Zyxel Device
and the printer will be encrypted with a secret key
Secret Key Enter four alphanumeric characters (A-Z, a-z, 0-9) to specify a key for data encryption.
Printer List Use this section to add the printer(s) that can be managed by the Zyxel Device.
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Chapter 22 Printer Manager
USG/ZyWALL User’s Guide
488
Discover
Printer Click this to discover the printer(s) that is connected to the Zyxel Device and display the printer
information in a pop-up window. IPnP is enabled while discovering the printer and disabled
when the discovering process has finished.
Use Printer Manager > Ge neral > Add to manually configure a printer’s IP address and add
it to the managed printer list when the printer is not detected or connected to the Zyxel
Device.
Refresh Click this to update the printer list table.
# This field is a sequential value, and it is not associated with any entry.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
IPv4 Address This field displays the IP address of the printer.
Registration This field displays whether the printer is added to the managed printer list (Mgnt Printer) or not
(Un-Mgnt Printer).
Uptime This field displays the date and time the Zyxel Device last synchronized with the printer.
This shows n/a when the printer is not in the managed printer list or the printer status is sync fail
or sync progressing.
Status This field displays whether the Zyxel Device can connect to the printer and update the printer
information.
This shows n/a when the printer is not in the managed printer list.
Nickname This shows an optional friendly name for the printer that you configured.
Firmware Version This field displays the model number and firmware version of the printer.
This shows n/a when the printer is not in the managed printer list or the printer status is sync fail.
MAC This shows the hardware MAC address of the printer.
Description This field displays the descriptive name for the printer that you configured.
Printer Firmware
Information
Current Version This is the version of the printer firmware currently uploaded to the Zyxel Device. The Zyxel
Device automatically installs it in the connected printers to make sure the printers are
upgraded to the same version.
Hotspot License
Status
The hotspot license must be registered in order to be activated.
License Status This field displays whether the service is activated (Licensed) or not (Not Licensed).
License Type This shows whether you have a trial or standard license or none (Trial, Standard, None).
Expiration
Date This shows when your hotspot license will expire.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
Table 177 Configuration > Hotspot > Printer Manager > General (continued)
LABEL DESCRIPTION
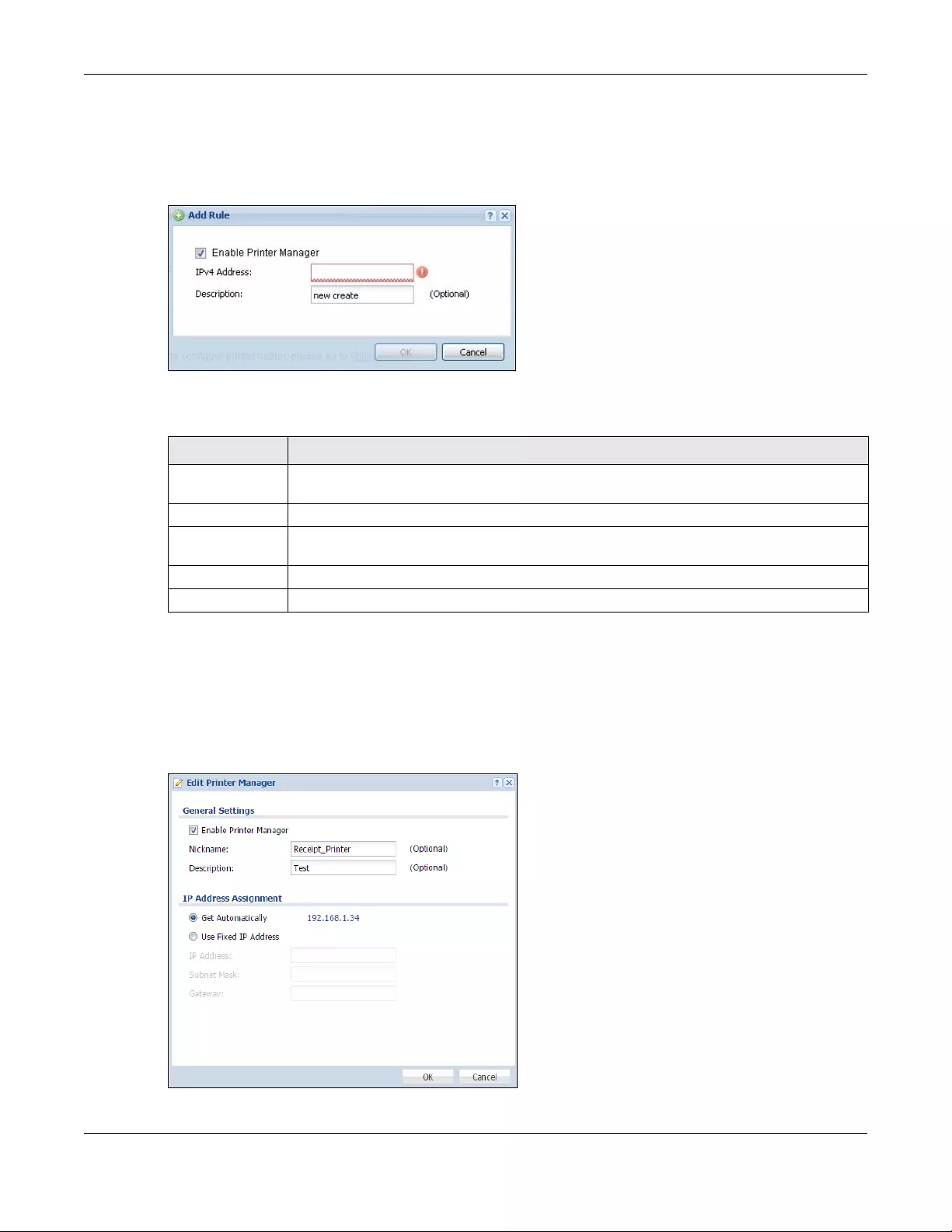
Chapter 22 Printer Manager
USG/ZyWALL User’s Guide
489
22.2.1 Add Printer Rule
Click the Add icon to open the following screen. Use this screen to add a new printer.
Figure 349 Configuration > Hotspot > Printer Manager > General: Add
The following table describes the labels in this screen.
22.2.2 Edit Printer Rule
Select an entry in the Printer Manager > General screen and click the Edit icon to open the following
screen. Use this screen to modify the printer’s settings. You can't click the Edit icon when the printer
status is sync fail or sync progressing.
Figure 350 Configuration > Hotspot > Printer Manager > General: Edit
Table 178 Configuration > Hotspot > Printer Manager > General: Add
LABEL DESCRIPTION
Enable Printer
Manager
Select this option to turn on this entry in order to allow the Zyxel Device to manage this printer.
IPv4 Address Enter an IPv4 address for the printer.
Description Enter a description of this printer. You can use alphanumeric and ()+,/:=?!*#@$_%-”
characters, and it can be up to 60 characters long.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
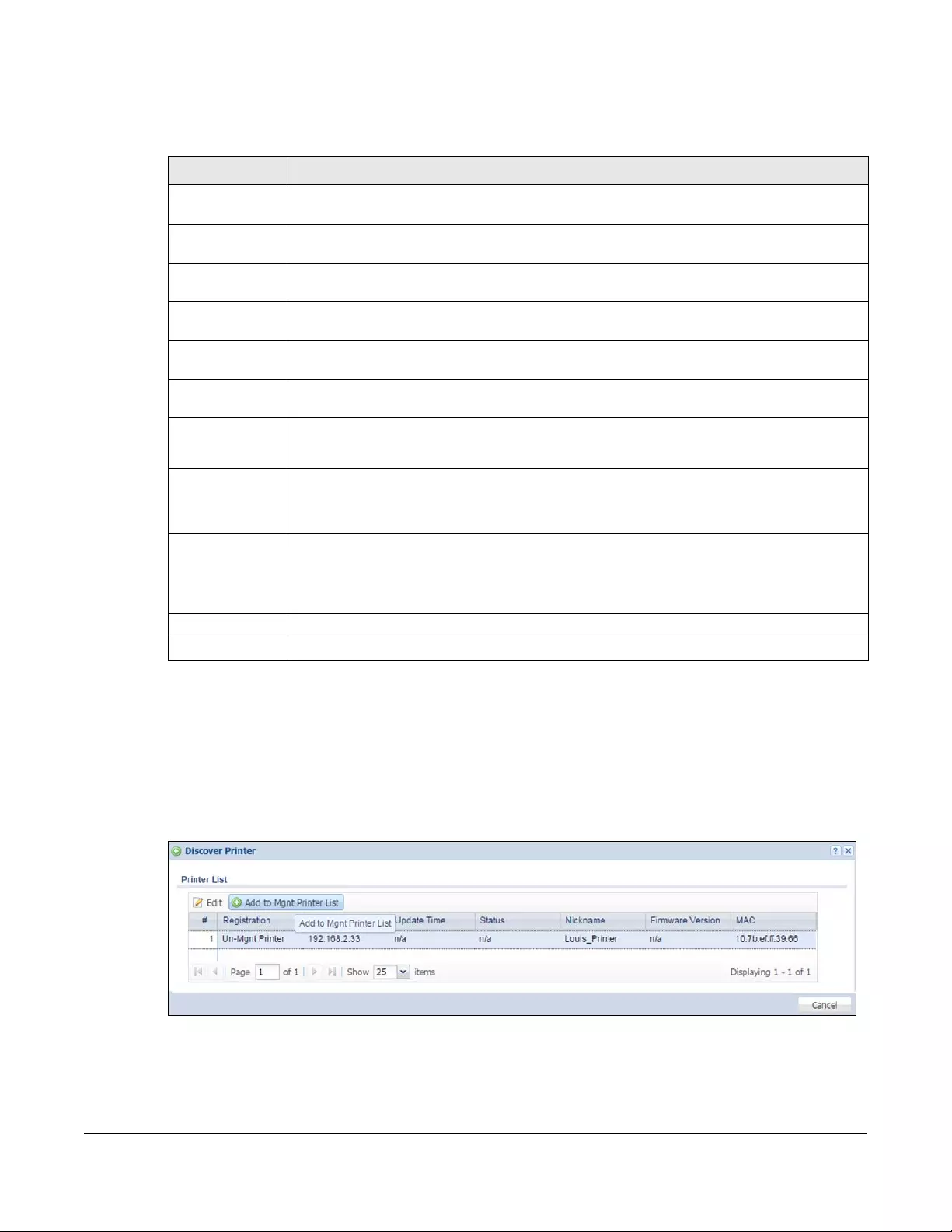
Chapter 22 Printer Manager
USG/ZyWALL User’s Guide
490
The following table describes the labels in this screen.
22.2.3 Discover Printer
Click the Discover Printer icon in the Printer Manager > Ge neral screen to open the following screen. Use
this screen to find connected printers or edit a connected printer’s settings. Use Printer Manager >
General > Add to manually configure a printer’s IP address and add it to the managed printer list when
the printer is not detected or connected to the Zyxel Device.
Figure 351 Configuration > Hotspot > Printer Manager > General: Discover Printer
Table 179 Configuration > Hotspot > Printer Manager > General: Edit
LABEL DESCRIPTION
Enable Printer
Manager
Select this option to turn on this entry in order to allow the Zyxel Device to manage this printer.
Nickname Type an optional friendly name for the printer. A nickname must begin with a letter and cannot
exceed 15 characters. Valid characters are [a-zA-Z0-9_-].
Description Enter a description of this printer. You can use alphanumeric and ()+,/:=?!*#@$_%-”
characters, and it can be up to 60 characters long.
IP Address
Assignment
Get
Automatically
Select this to make the printer a DHCP client and automatically get the IP address, subnet
mask, and gateway address from a DHCP server.
Use Fixed IP
Address
Select this if you want to specify the IP address, subnet mask, and gateway manually.
IP Address This field is enabled if you select Use Fixed IP Addres s.
Enter the IP address for the printer.
Subnet Mask This field is enabled if you select Use Fixed IP Address.
Enter the subnet mask of the printer in dot decimal notation. The subnet mask indicates what
part of the IP address is the same for all computers in the network.
Gateway This field is enabled if you select Use Fixed IP Address.
Enter the IP address of the gateway. The Zyxel Device sends packets to the gateway when it
does not know how to route the packet to its destination. The gateway should be on the same
network as the printer.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
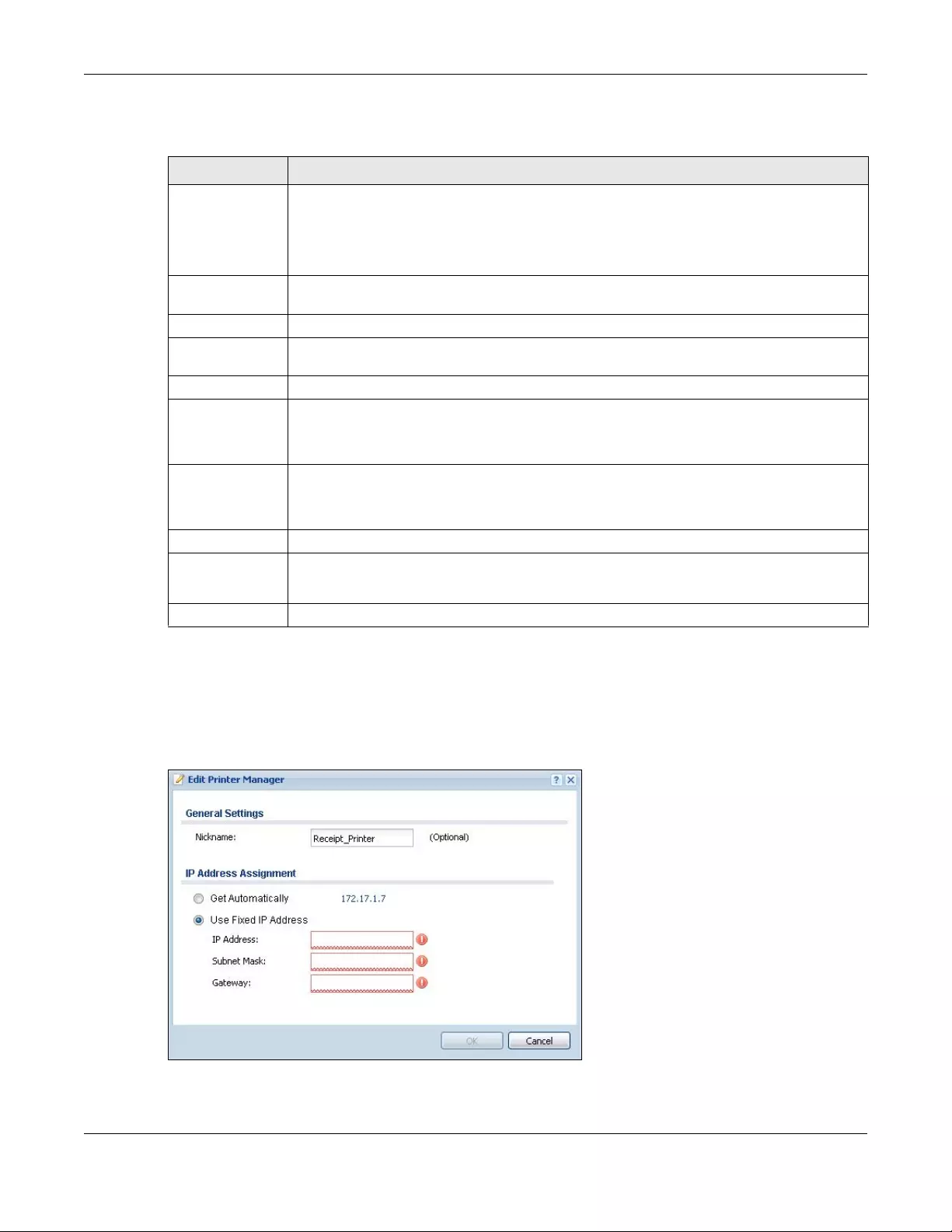
Chapter 22 Printer Manager
USG/ZyWALL User’s Guide
491
The following table describes the labels in this screen.
22.2.4 Edit Printer Manager (Discover Printer)
Select an entry in the Printer Manager > General > Discover Printer screen and click the Edit icon to open
the following screen. Use this screen to modify the printer’s nickname and IP address.
Figure 352 Configuration > Hotspot > Printer Manager > General > Discover Printer: Edit
Table 180 Configuration > Hotspot > Printer Manager > General > Discover Printer
LABEL DESCRIPTION
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Note: You cannot edit an entry’s settings when the printer status is sync fail or sync
progressing.
Add to Mgnt
Printer List
Click this to add the selected printer to the managed printer list.
# This is the index number of the printer in the list.
Registration This field displays whether the printer is added to the managed printer list (Mgnt Printer) or not
(Un-Mgnt Printer).
IPv4 Address This field displays the IP address of the printer.
Update Time This field displays the date and time the Zyxel Device last synchronized with the printer.
This shows n/a when the printer is not in the managed printer list or the printer status is sync fail
or sync progressing.
Status This field displays whether the Zyxel Device can connect to the printer and update the printer
information.
This shows n/a when the printer is not in the managed printer list.
Nickname This field displays the optional friendly name of the printer that you configured.
Firmware Version This field displays the model number and firmware version of the printer.
This shows n/a when the printer is not in the managed printer list or the printer status is sync fail.
MAC This field displays the MAC address of the printer.
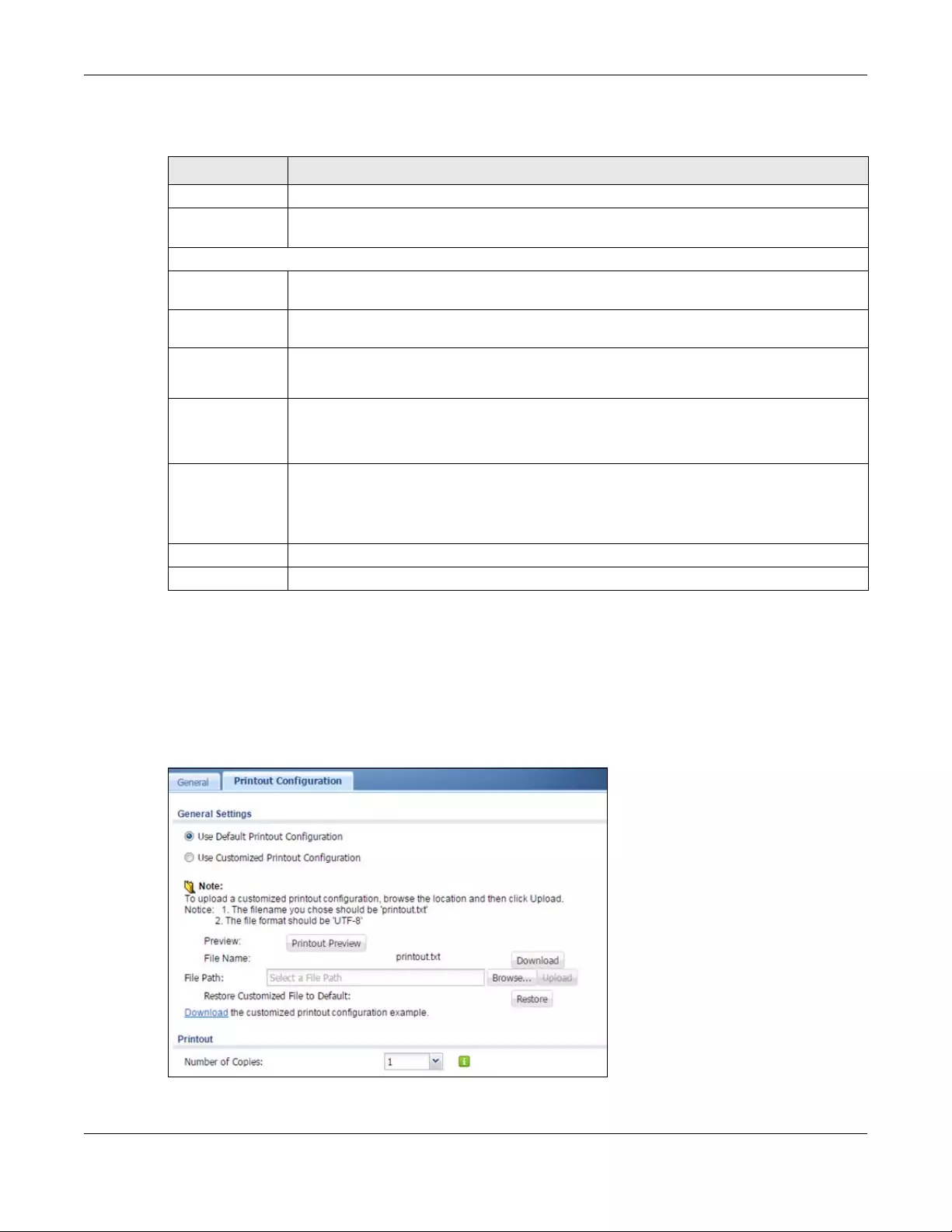
Chapter 22 Printer Manager
USG/ZyWALL User’s Guide
492
The following table describes the labels in this screen.
22.3 The Printout Configuration Screen
Use this screen to customize the account printout. Click Configuration > Hotspot > Printer Manager >
Printout Configuration to open the following screen.
Figure 353 Configuration > Hotspot > Printer Manager > Printout Configuration
Table 181 Configuration > Hotspot > Printer Manager > General > Discover Printer: Edit
LABEL DESCRIPTION
General Settings
Nickname Type an optional friendly name for the printer. A nickname must begin with a letter and cannot
exceed 15 characters. Valid characters are [a-zA-Z0-9_-].
IP Address Assignment
Get
Automatically
Select this to make the printer a DHCP client and automatically get the IP address, subnet
mask, and gateway address from a DHCP server.
Use Fixed IP
Address
Select this if you want to specify the IP address, subnet mask, and gateway manually.
IP Address This field is enabled if you select Use Fixed IP Addres s.
Enter the IP address for the printer.
Subnet Mask This field is enabled if you select Use Fixed IP Address.
Enter the subnet mask of the printer in dot decimal notation. The subnet mask indicates what
part of the IP address is the same for all computers in the network.
Gateway This field is enabled if you select Use Fixed IP Address.
Enter the IP address of the gateway. The Zyxel Device sends packets to the gateway when it
does not know how to route the packet to its destination. The gateway should be on the same
network as the printer.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
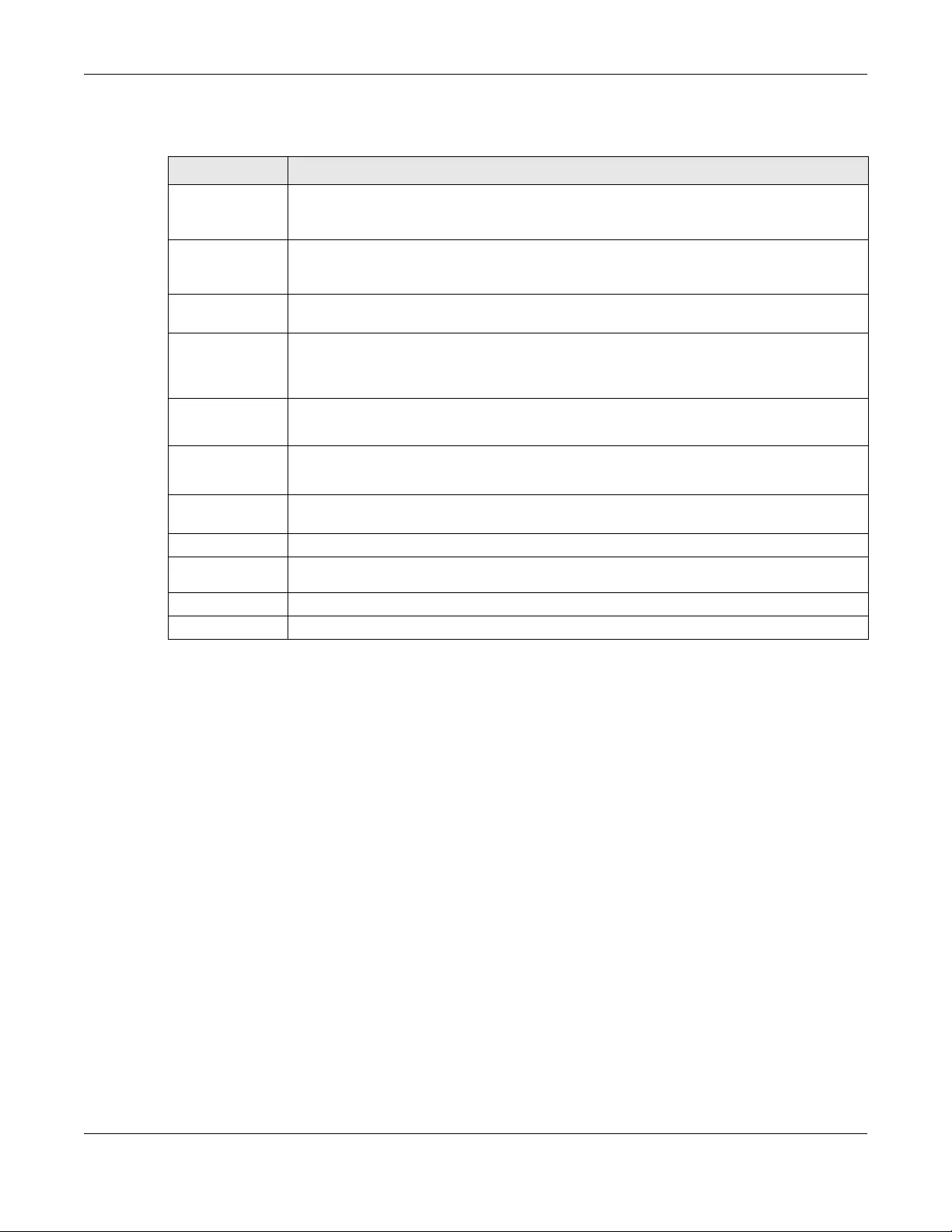
Chapter 22 Printer Manager
USG/ZyWALL User’s Guide
493
The following table describes the labels in this screen.
22.4 Printer Reports Overview
The SP350E allows you to print status reports about the guest accounts and general Zyxel Device system
information. Simply press a key combination on the SP350E to print a report instantly without accessing
the web configurator.
The following lists the reports that you can print using the SP300E.
• Daily account summary
• Monthly account summary
• Last month account summary
•System status
22.4.1 Key Combinations
The following table lists the key combination to print each report.
Table 182 Configuration > Hotspot > Printer Manager > Printout Configuration
LABEL DESCRIPTION
Use Default
Printout
Configuration
Select this to use the default account printout format built into the device. If you later create a
custom account printout format, you can still return to the Zyxel Device’s default format as it is
saved indefinitely.
Use Customized
Printout
Configuration
Select this to use a custom account printout format instead of the default one built into the
Zyxel Device. Once this option is selected, the custom format controls below become active.
Preview Click the button to display a preview of account printout format you uploaded to the Zyxel
Device.
File Name This shows the file name of account printout format file in the Zyxel Device.
Click Download to download the account printout format file from the Zyxel Device to your
computer.
File Path /
Browse /
Upload
Browse for the account printout format file or enter the file path in the available input box, then
click the Upload button to put it on the Zyxel Device.
Restore
Customized
File to Default
Click Restore to set the Zyxel Device back to use the default built-in account printout format.
Download Click this to download an example account printout format file from the Zyxel Device for your
reference.
Printout
Number of
Copies Select how many copies of subscriber statements you want to print (1 is the default).
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
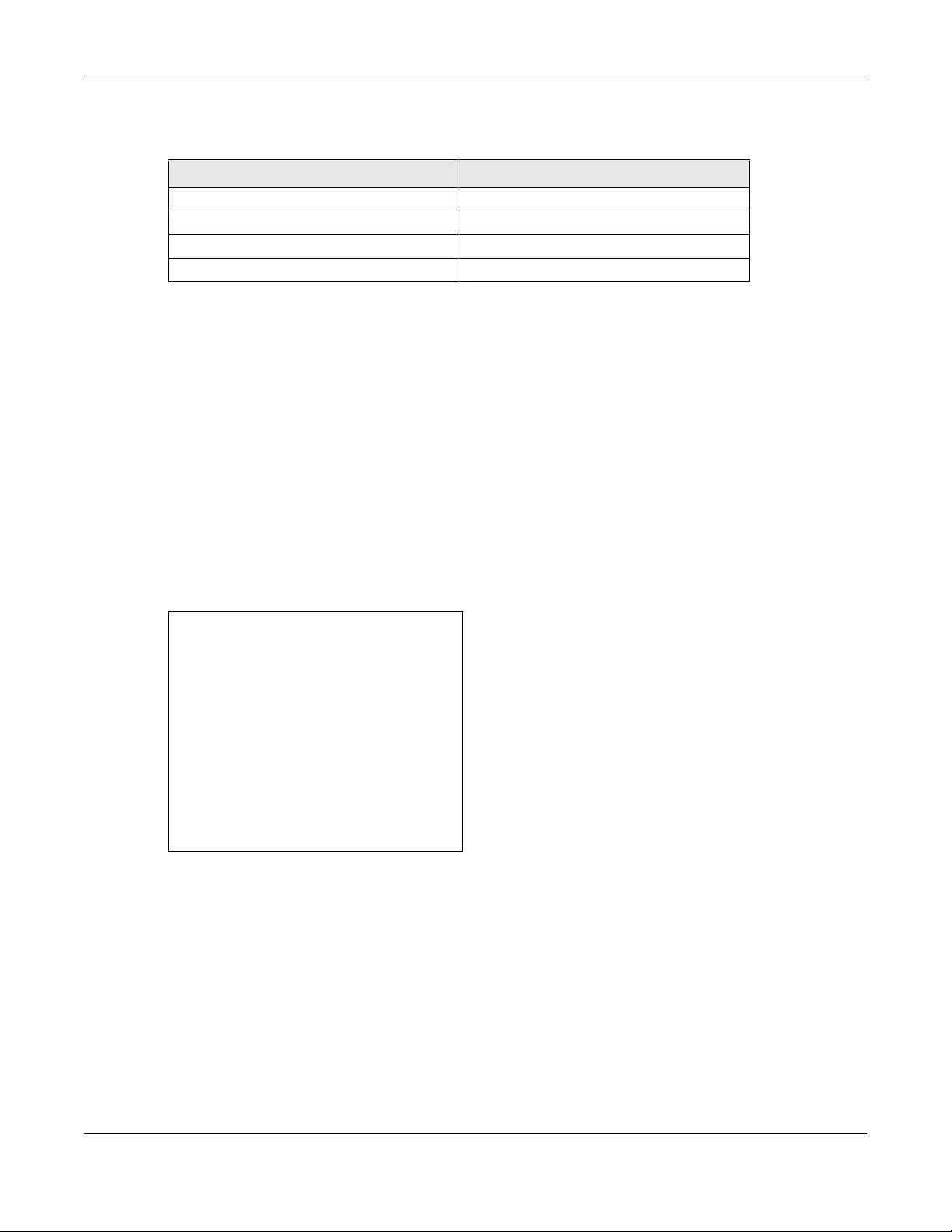
Chapter 22 Printer Manager
USG/ZyWALL User’s Guide
494
Note: You must press the key combination on the SP350E within five seconds to print.
The following sections describe each report printout in detail.
22.4.2 Daily Account Summary
The daily account report lists the accounts printed during the current day, the current day’s total
number of accounts and the total charge. It covers the accounts that have been printed during the
current day starting from midnight (not the past 24 hours). For example, if you press the daily account
key combination on 2013/05/10 at 20:00:00, the daily account report includes the accounts created on
2013/05/10 between 00:00:01 and 19:59:59.
Key combination: A B C A A
The following figure shows an example.
Figure 354 Daily Account Example
22.4.3 Monthly Account Summary
The monthly account report lists the accounts printed during the current month, the current month’s
total number of accounts and the total charge. It covers the accounts that have been printed during
the current month starting from midnight of the first day of the current month (not the past one month
period). For example, if you press the monthly account key combination on 2013/05/17 at 20:00:00, the
monthly account report includes the accounts created from 2013/05/01 at 00:00:01 to 2013/05/17 at
19:59:59.
Key combination: A B C B A
The following figure shows an example.
Table 183 Report Printing Key Combinations
REPORT TYPE KEY COMBINATION
Daily Account Summary A B C A A
Monthly Account Summary A B C B A
Last Month Account Summary A B C B B
System Status A B C C A
Daily Account
----------------------------
2013/05/10
Username Price
----------------------------
p2m6pf52 1.00
s4pcms28 2.00
----------------------------
TOTAL ACCOUNTS: 2
TOTAL PRICE: $ 3.00
----------------------------
2013/05/10 20:00:00
---End---
Chapter 22 Printer Manager
USG/ZyWALL User’s Guide
495
Figure 355 Monthly Account Example
22.4.4 Account Report Notes
The daily, monthly or last month account report holds up to 2000 entries. If there are more than 2000
accounts created in the same month or same day, the account report’s calculations only include the
latest 2000.
For example, if 2030 accounts (each priced at $1) have been created from 2013/05/01 00:00:00 to 2013/
05/31 19:59:59, the monthly account report includes the latest 2000 accounts, so the total would be
$2,000 instead of $2,030.
Use the Monitor > System Status > Dynamic Guest screen to see the accounts generated on another
day or month (up to 2000 entries total).
22.4.5 System Status
This report shows the current system information such as the host name and WAN IP address.
Key combination: A B C C A
The following figure shows an example.
Monthly Account
----------------------------
2013/05
Username Price
----------------------------
p2m6pf52 1.00
s4pcms28 2.00
7ufm7z22 2.00
qm5fxn95 6.00
----------------------------
TOTAL ACCOUNTS: 4
TOTAL PRICE: $ 11.00
----------------------------
2013/05/17 20:00:11
---End---
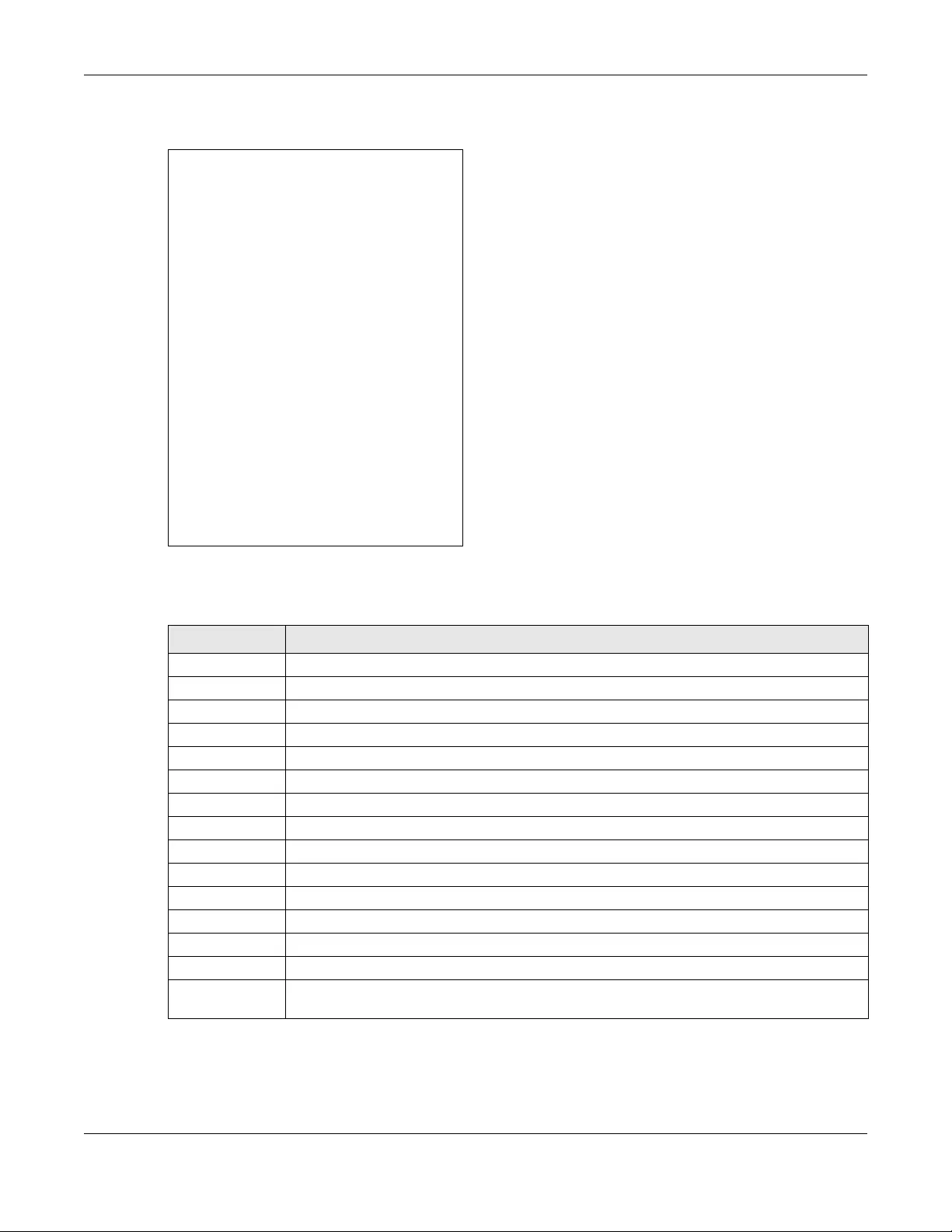
Chapter 22 Printer Manager
USG/ZyWALL User’s Guide
496
Figure 356 System Status Example
The following table describes the labels in this report.
System Status
--------------------------------------
Item Description
--------------------------------------
SYST 02:02:35
WAST Link up
WLST Activate
FWVR 2.50(AACG.0)
BTVR 1.22
WAMA 00-90-0E-00-4A-29
LAMA 00-90-0E-00-4A-30
WAIP 10.21.2.267
LAIP 172.16.0.1
WLIP 10.59.1.1
DHSP 10.59.1.33
DHEP 10.59.1.254
--------------------------------------
CPUS 5%
MEMS 40%
DKST 5%
--------------------------------------
2012/04/12 17:10:22
---End---
Table 184 System Status
LABEL DESCRIPTION
SYST This field displays the time since the system was last restarted.
WAST This field displays the WAN connection status.
WLST This field displays the status of the Zyxel Device’s wireless LAN.
FWVR This field displays the version of the firmware on the Zyxel Device.
BTVR This field displays the version of the bootrom.
WAMA This field displays the MAC address of the Zyxel Device on the WAN.
LAMA This field displays the MAC address of the Zyxel Device on the LAN.
WAIP This field displays the IP address of the WAN port on the Zyxel Device.
LAIP This field displays the IP address of the LAN port on the Zyxel Device.
WLIP This field displays the IP address of the wireless LAN interface on the Zyxel Device.
DHSP This field displays the first of the continuous addresses in the IP address pool.
DHEP This field displays the end of the continuous addresses in the IP address pool.
CPUS This field displays the Zyxel Device’s recent CPU usage.
MEMS This field displays the Zyxel Device’s recent memory usage.
DKST This field displays what percentage of the Zyxel Device’s on-board flash memory is currently
being used.
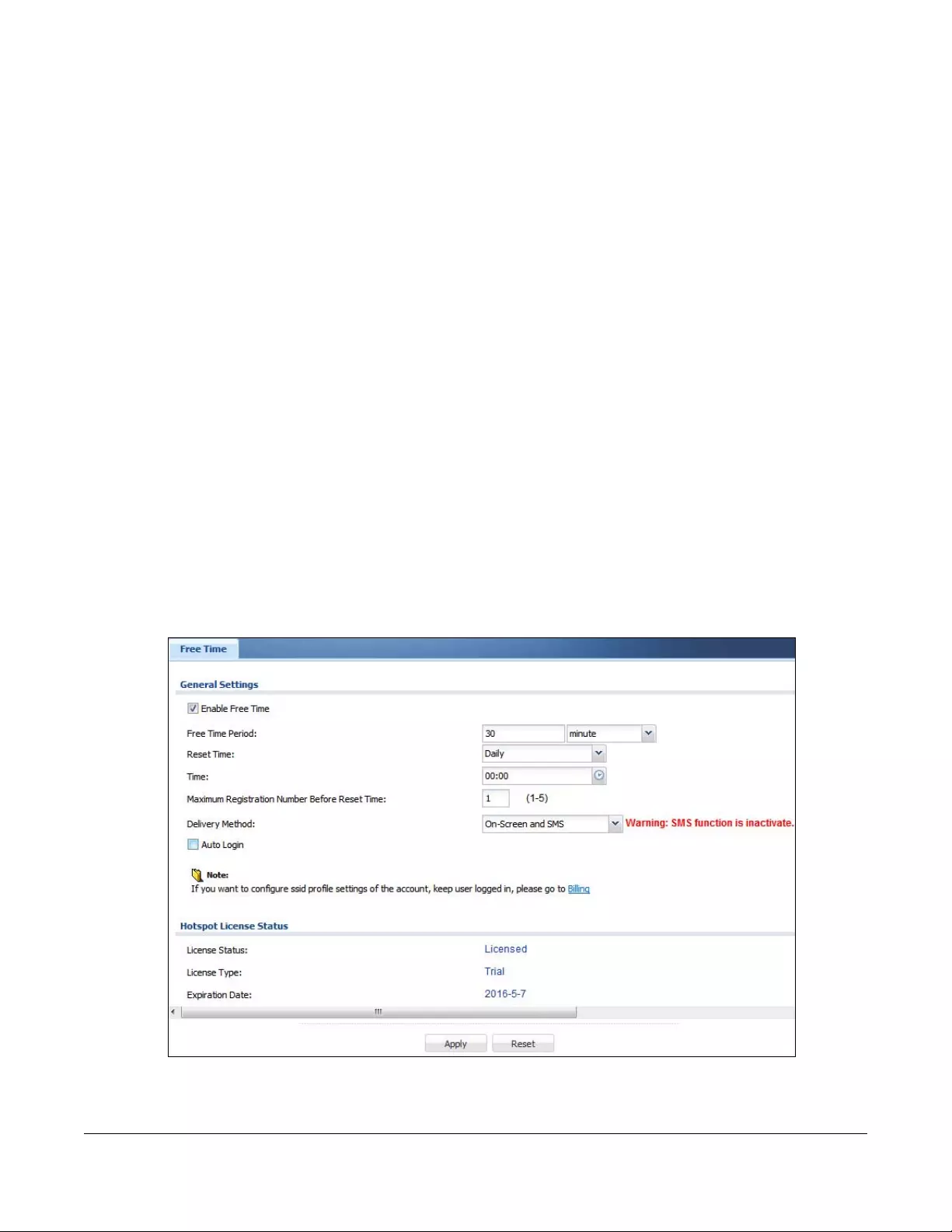
USG/ZyWALL User’s Guide
497
CHAPTER 23
Free Time
23.1 Free Time Overview
With Free Time, the Zyxel Device can create dynamic guest accounts that allow users to browse the
Internet free of charge for a specified period of time.
23.1.1 What You Can Do in this Chapter
Use the Free Time screen (see Section 23.2 on page 497) to turn on this feature to allow users to get a
free account for Internet surfing during the specified time period.
23.2 The Free Time Screen
Use this screen to enable and configure the free time settings. Click Configuration > Hotspot > Free Time
to open the following screen.
Figure 357 Configuration > Hotspot > Free Time
Chapter 23 Free Time
USG/ZyWALL User’s Guide
498
The following table describes the labels in this screen.
Table 185 Configuration > Hotspot > Free Time
LABEL DESCRIPTION
Enable Free Time Select the check box to turn on the free time feature.
Note: After you set up web authentication policies and enable the free time feature
on the Zyxel Device, a link displays in the login screen when users try to access
the Internet. The link redirects users to a screen where they can get a free
account.
Free Time Period Select the duration of time period for which the free time account is allowed to access the
Internet.
Reset Time Select Daily to have the Zyxel Device allow free account access every day at the specified
time.
Select Weekly to have the Zyxel Device allow free account access once a week on the day
you select.
Select Monthly to have the Zyxel Device allow free account access once a month on a set
date.
Time If you select Daily, select the time in 24-hour format at which the new free time account is
allowed to access the Internet.
Day If you select Weekly, select the day on which the new free time account is allowed to access
the Internet.
If you select Monthly, enter the date on which the new free time account is allowed to access
the Internet. If the date you selected is not available in a month, such as 30th or 31th, the Zyxel
Device allows the free account access on the last day of the month.
Maximum
Registration
Number Before
Reset Time
Enter the maximum number of the users that are allowed to log in for Internet access with a
free guest account before the time specified in the Reset Time field. This also sets how many
free guest accounts a user can get.
For example, if you set the Maximum Registration Number Before Reset Time to 1, the Reset
Time to Daily and the Reset Time to 13:00, even the first free guest account has expired at
11:30, the user cannot get a second account and/or access the Internet until 13:00.
Delivery Method Specify how the Zyxel Device provides dynamic guest account information.
Select On-Screen to display the user account information in the web screen.
Select SMS to use Short Message Service (SMS) to send account information in a text message
to the user’s mobile device.
Select On-Screen and SMS to provide the account information both in the web screen and via
SMS text messages.
Note: You should have enabled SMS in the Configuration > SMS screen to send text
messages to the user’s mobile device.
Auto Login Select this to allow users to log into their free account directly without having to enter their user
name and password.
Clearing this requires users to enter their user name and password, and click login to access
their free account.
Hotspot License
Status
License Status This field displays whether the service is activated (Licensed) or not (Not Licensed).
License Type This shows whether you have a trial or standard license or none (Trial, Standard, None).
Expiration
Date This shows when your hotspot license will expire.
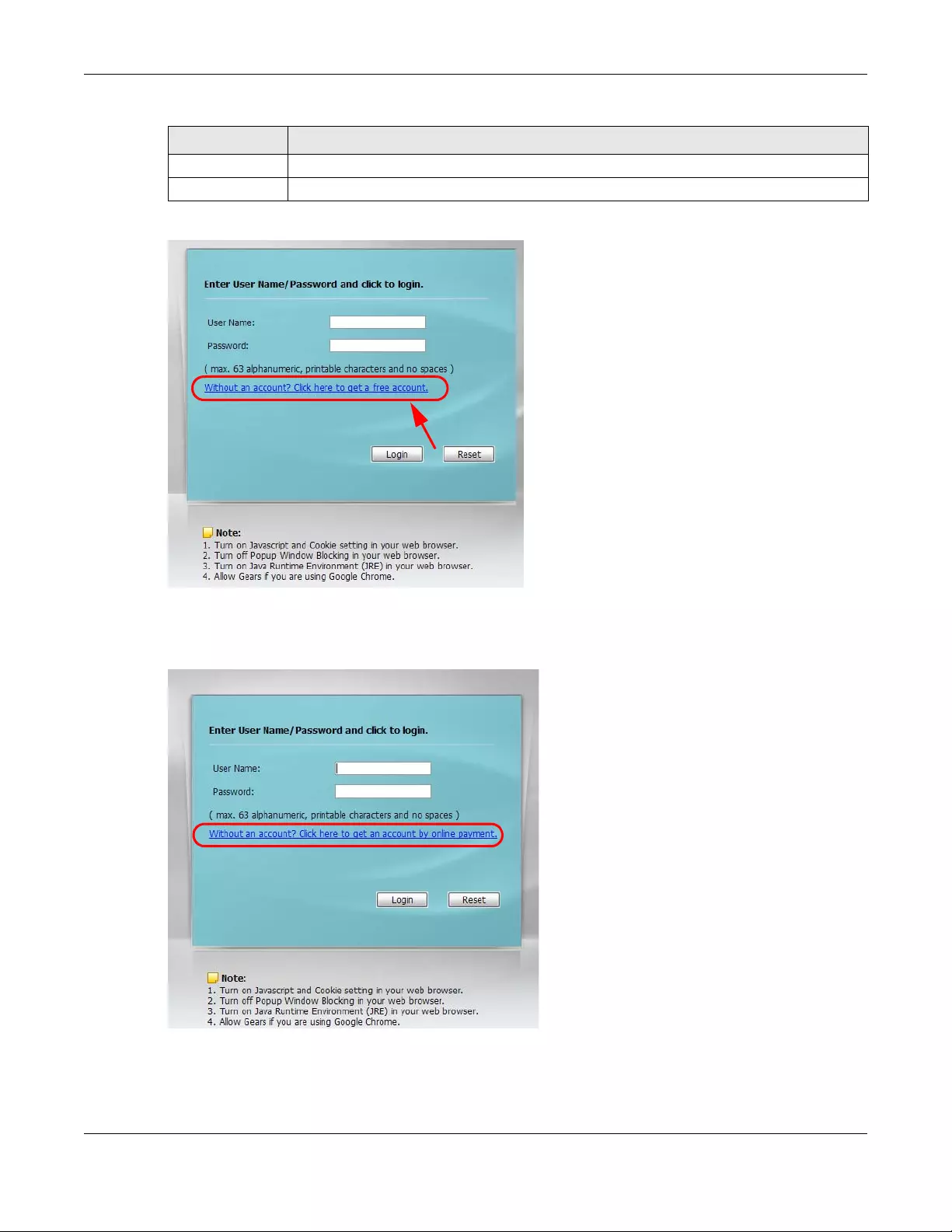
Chapter 23 Free Time
USG/ZyWALL User’s Guide
499
The following figure shows an example login screen with a link to create a free guest account.
If you enable both online payment service and free time feature on the Zyxel Device, the link description
in the login screen will be mainly for online payment service. You can still click the link to get a free
account.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
Table 185 Configuration > Hotspot > Free Time (continued)
LABEL DESCRIPTION
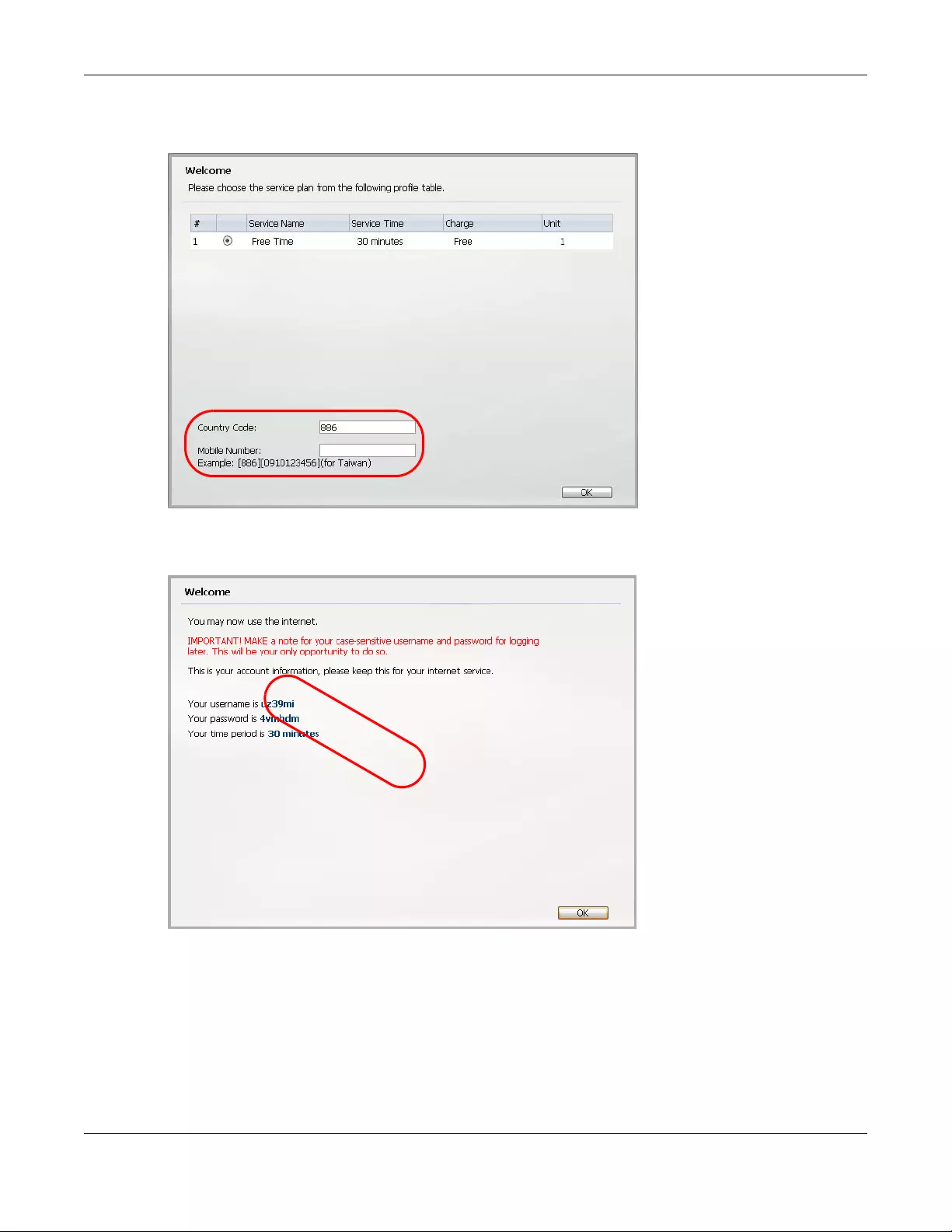
Chapter 23 Free Time
USG/ZyWALL User’s Guide
500
If SMS is enabled on the Zyxel Device, you have to enter your mobile phone number before clicking OK
to get a free guest account.
The guest account information then displays in the screen and/or is sent to the configured mobile phone
number.
EXAMPLE
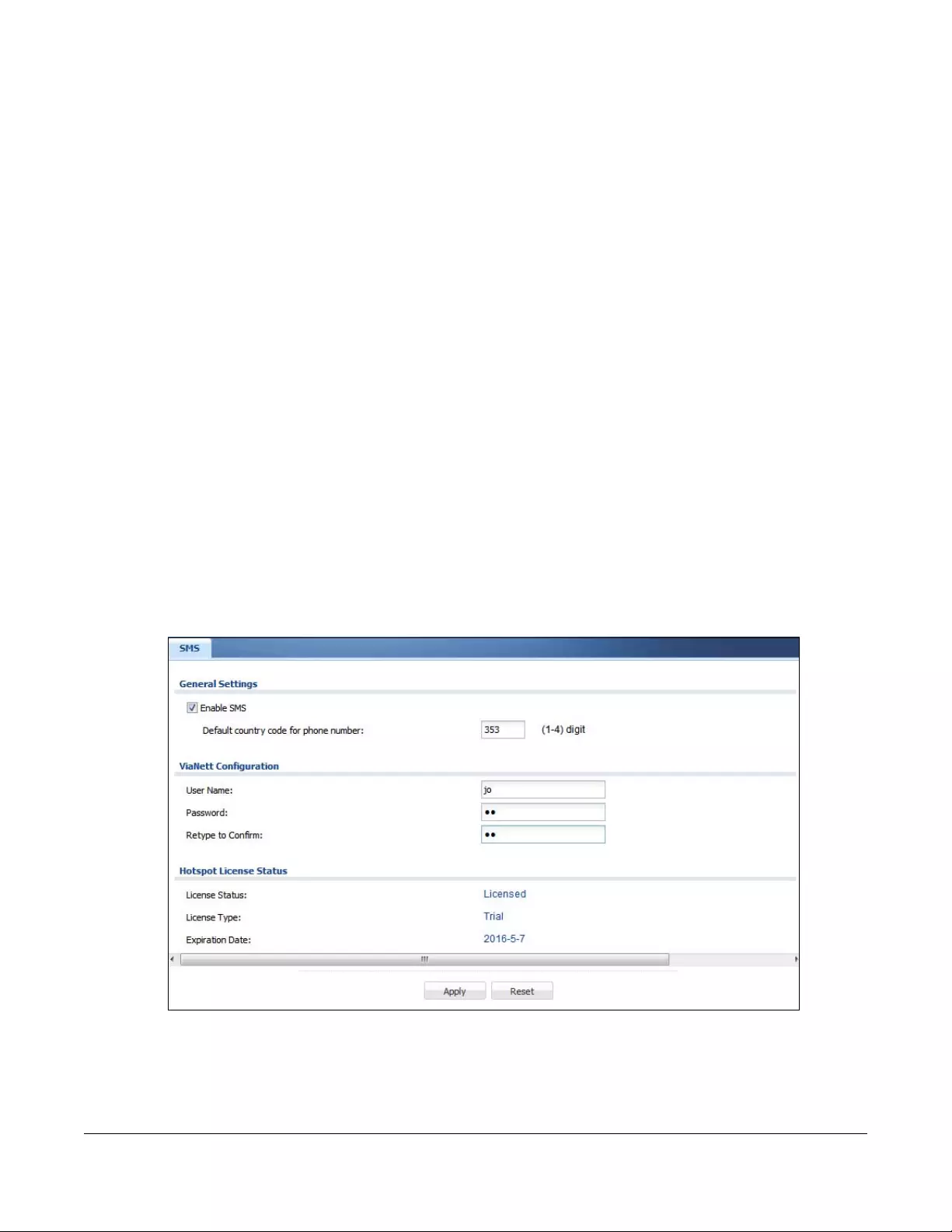
USG/ZyWALL User’s Guide
501
CHAPTER 24
SMS
24.1 SMS Overview
The Zyxel Device supports Short Message Service (SMS) to send short text messages to mobile phone
devices. At the time of writing, the Zyxel Device uses ViaNett as the SMS gateway to help forward SMS
messages. You must already have a ViaNett account in order to use the SMS service.
24.1.1 What You Can Do in this Chapter
Use the SMS screen (see Section 24.2 on page 501) to turn on the SMS service on the Zyxel Device.
24.2 The SMS Screen
Use this screen to enable SMS in order to send dynamic guest account information in text messages.
Click Configuration > Hotspot > SMS to open the following screen.
Figure 358 Configuration > Hotspot > SMS
Chapter 24 SMS
USG/ZyWALL User’s Guide
502
The following table describes the labels in this screen.
Table 186 Configuration > Hotspot > SMS
LABEL DESCRIPTION
General Settings
Enable SMS Select the check box to turn on the SMS service.
Default country
code for phone
number
Enter the default country code for the mobile phone number to which you want to send SMS
messages.
ViaNett
Configuration
User Name Enter the user name for your ViaNett account.
Password Type the Password associated with the user name.
Retype to
Confirm
Type your password again for confirmation.
Hotspot License
Status
License Status This field displays whether the service is activated (Licensed) or not (Not Licensed).
You must subscribe to the SMS service before you can use the service to send a text
message.
License Type This shows whether you have a trial or standard license or none (Trial, Standard, None).
Expiration
Date This shows when your hotspot license will expire.
Register Now Click the link to go to myZyxel.com where you can register your Zyxel Device and activate the
service.
This link is available only when the service is not activated yet.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
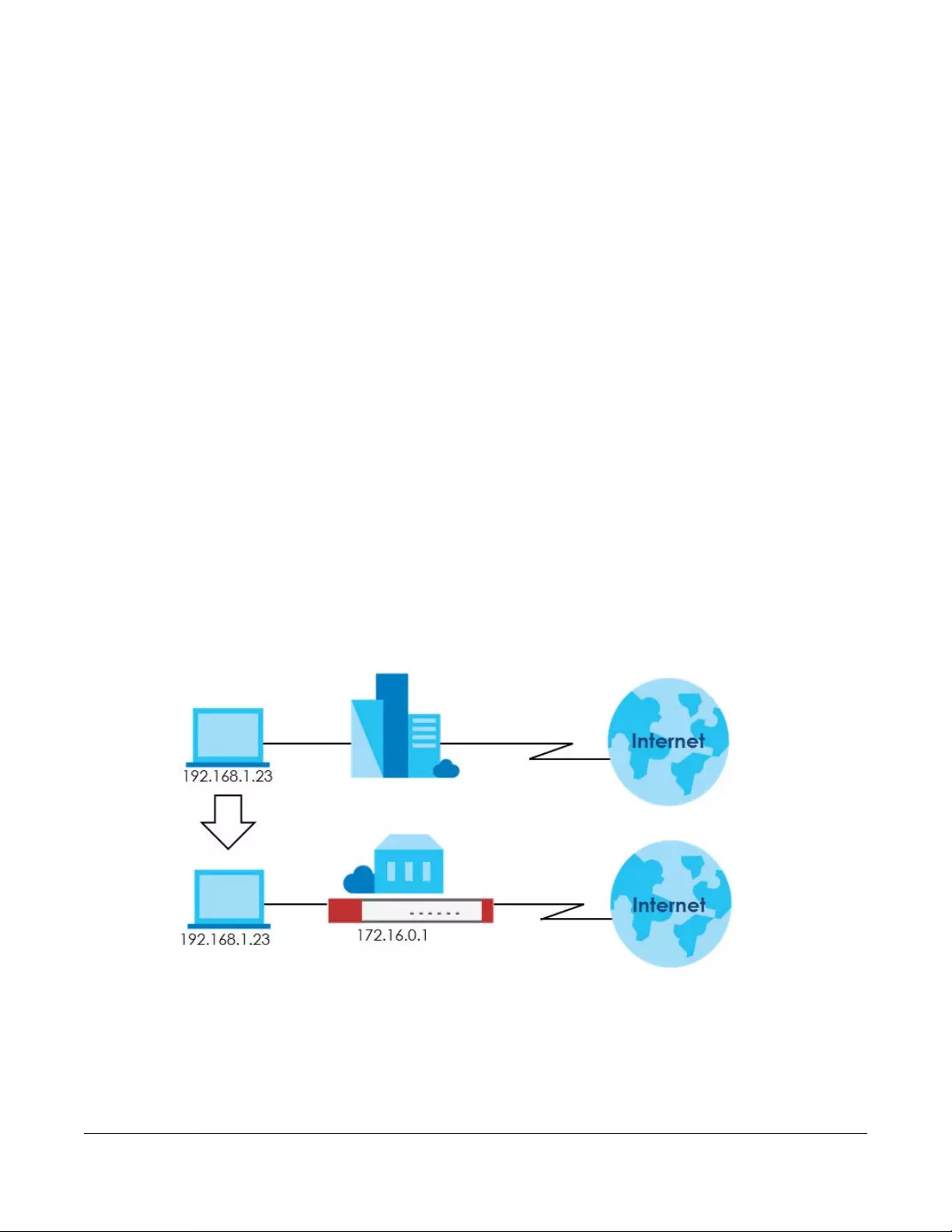
USG/ZyWALL User’s Guide
503
CHAPTER 25
IPnP
25.1 IPnP Overview
IP Plug and Play (IPnP) allows a computer to access the Internet without changing the network settings
(such as IP address and subnet mask) of the computer, even when the IP addresses of the computer
and the Zyxel Device are not in the same subnet.
When you disable the IPnP feature, only computers with dynamic IP addresses or static IP addresses in
the same subnet as the Zyxel Device’s LAN IP address can connect to the Zyxel Device or access the
Internet through the Zyxel Device.
The IPnP feature does not apply to a computer using either a dynamic IP address or a static IP address
that is in the same subnet as the Zyxel Device's IP address.
Note: You must enable NAT to use the IPnP feature.
The following figure depicts a scenario where a computer is set to use a static private IP address in the
corporate environment. In a residential house where a Zyxel Device is installed, you can still use the
computer to access the Internet without changing the network settings, even when the IP addresses of
the computer and the Zyxel Device are not in the same subnet.
Figure 359 IPnP Application
25.1.1 What You Can Do in this Chapter
Use the IP screen (Section 25.2 on page 504) to enable IPnP on the Zyxel Device and the internal
interface(s).
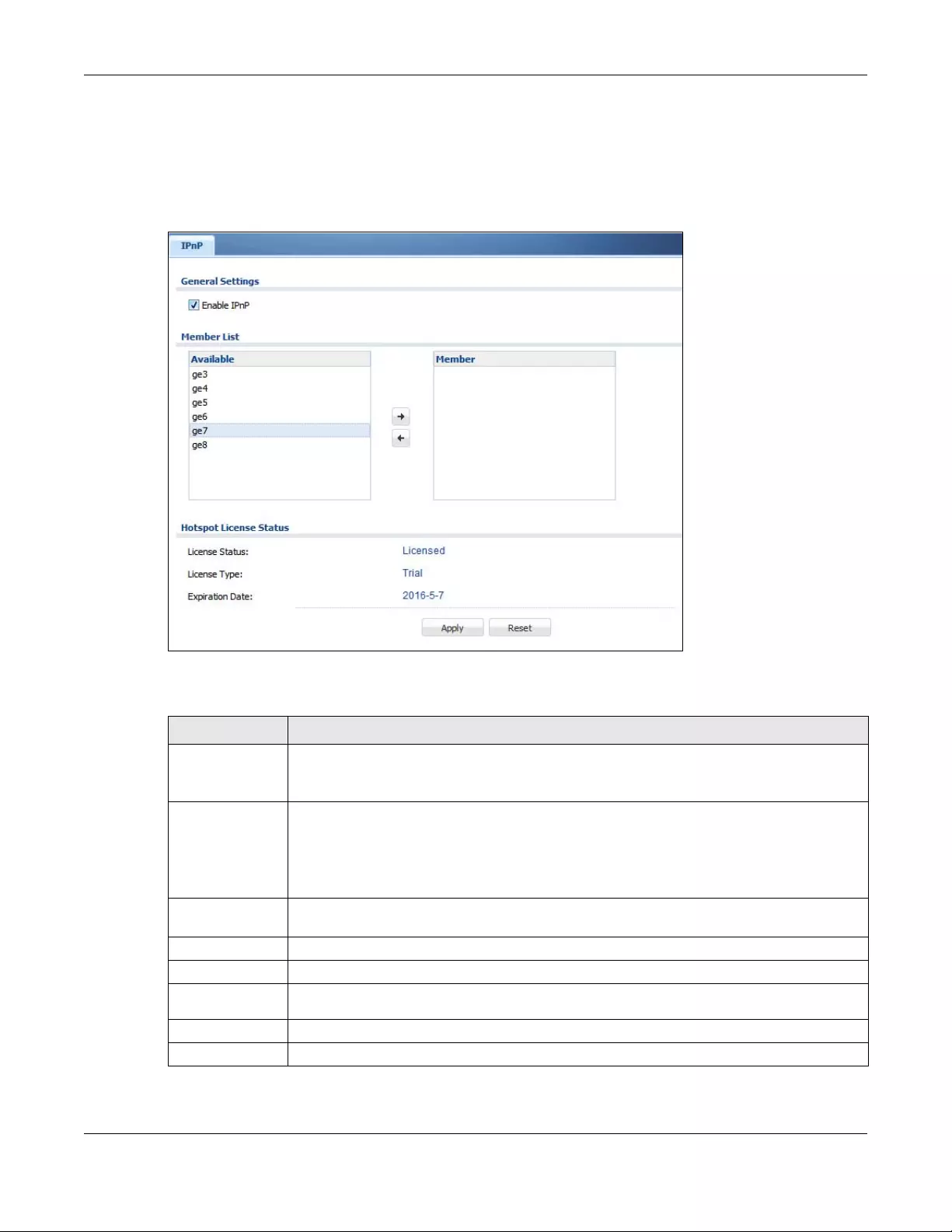
Chapter 25 IPnP
USG/ZyWALL User’s Guide
504
25.2 IPnP Screen
This screen allows you to enable IPnP on the Zyxel Device and specific internal interface(s). To access
this screen click Configuration > Hotspot > Network > IPnP.
Figure 360 Configuration > Hotspot > Network > IPnP
The following table describes the labels in this screen.
Table 187 Configuration > Hotspot > Network > IPnP
LABEL DESCRIPTION
Enable IPnP Select this option to turn on the IPnP feature on the Zyxel Device.
Note: You can enable this feature only when the security policy is enabled.
Member List The Available list displays the name(s) of the internal interface(s) on which you can enable
IPnP.
To enable IPnP on an interface, you can double-click a single entry to move it or use the [Shift]
or [Ctrl] key to select multiple entries and click the right arrow button to add to the Member list.
To remove an interface, select the name(s) in the Member list and click the left arrow button.
Hotspot License
Status
License Status This field displays whether the service is activated (Licensed) or not (Not Licensed).
License Type This shows whether you have a trial or standard license or none (Trial, Standard, None).
Expiration
Date This shows when your hotspot license will expire.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
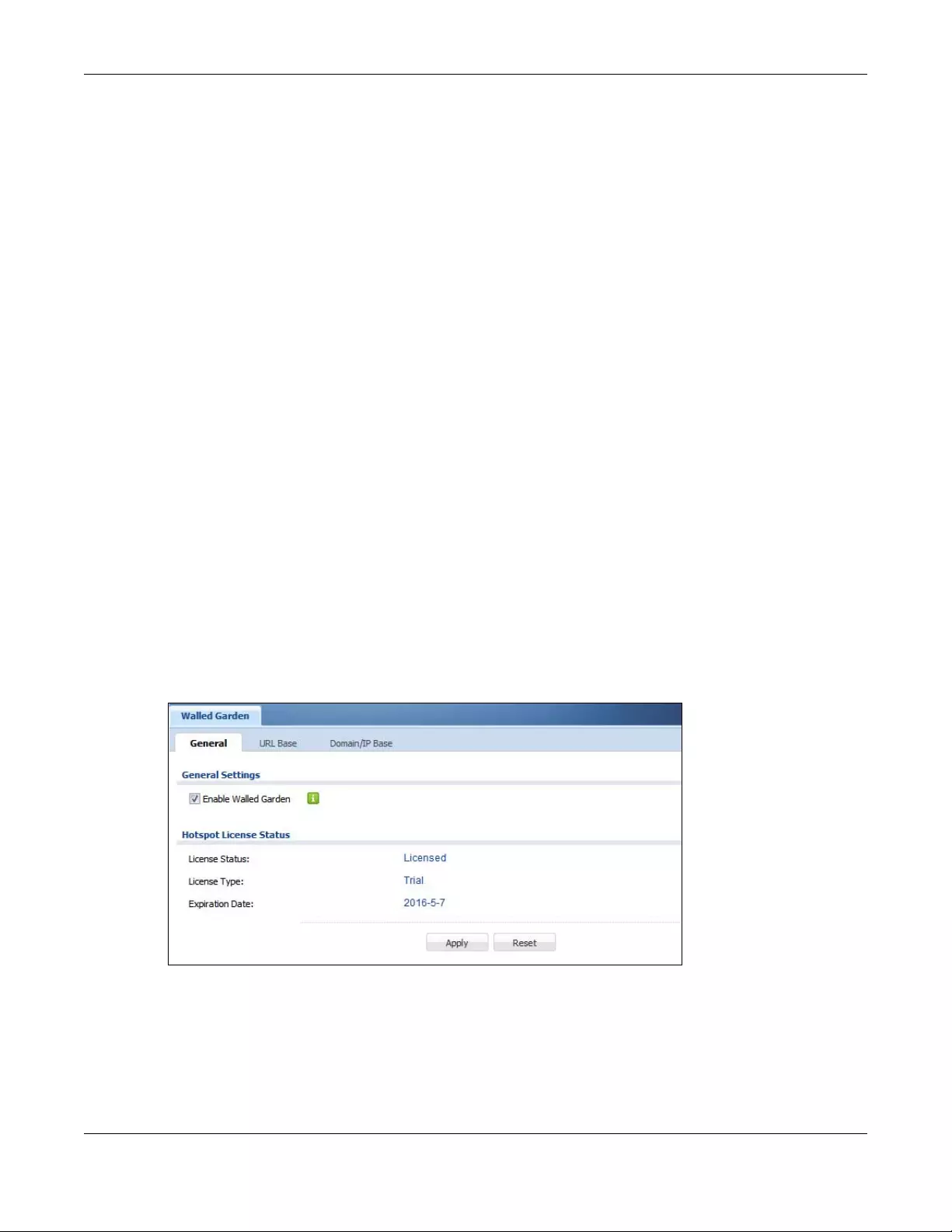
Chapter 26 Walled Garden
USG/ZyWALL User’s Guide
505
CHAPTER 26
Walled Garden
26.1 Walled Garden Overview
A user must log in before the Zyxel Device allows the user’s access to the Internet. However, with a
walled garden, you can define one or more web site addresses that all users can access without
logging in. These can be used for advertisements for example.
26.2 General Screen
Use this screen to turn on the walled garden feature.
Note: You must enable web authentication before you can access the Walled Garden
screens.
Note: You can configure up to 50 walled garden web site links.
Click Configuration > Hotspot > Walled Garden to display the screen.
Figure 361 Configuration > Hotspot > Walled Garden: General
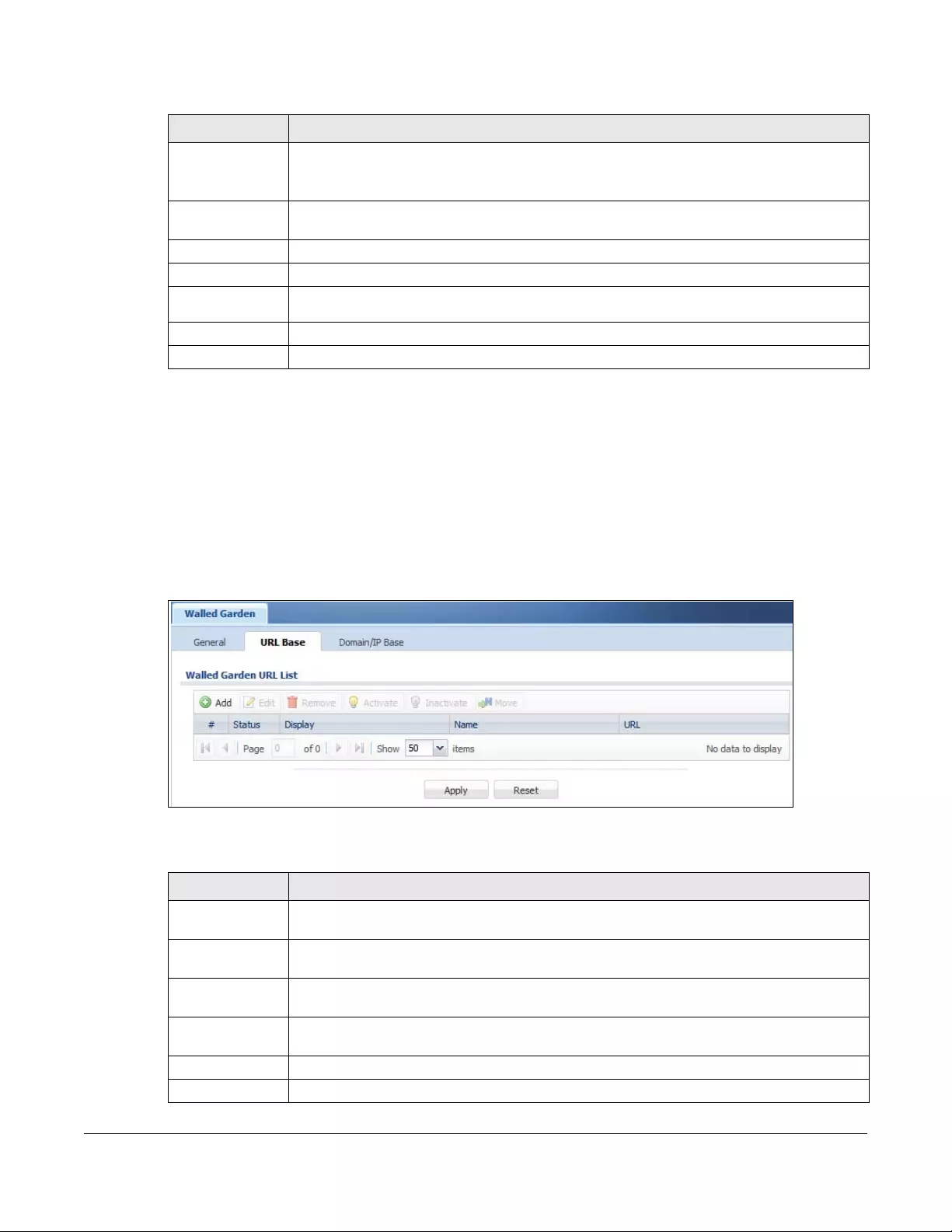
USG/ZyWALL User’s Guide
506
The following table describes the labels in this screen.
26.3 URL Base Screen
Use this screen to configure the walled garden web addresses (URLs that use the HTTP or HTTPS protocol)
for web sites that all users are allowed to access without logging in. The web site link(s) displays in the
user login screen by default.
Click Configuration > Hotspot > Walled Garden and then select the URL Base tab to display the screen.
Figure 362 Configuration > Hotspot > Walled Garden: URL Base
The following table describes the labels in this screen.
Table 188 Configuration > Hotspot > Walled Garden: General
LABEL DESCRIPTION
Enable Walled
Garden
Select this to turn on the walled garden feature.
Note: This feature works only with the web portal authentication type.
Hotspot License
Status
License Status This field displays whether the service is activated (Licensed) or not (Not Licensed).
License Type This shows whether you have a trial or standard license or none (Trial, Standard, None).
Expiration
Date This shows when your hotspot license will expire.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
Table 189 Configuration > Hotspot > Walled Garden: URL Based
LABEL DESCRIPTION
Walled Garden
URL List
Use this table to manage the list of walled garden web site links.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after the
selected entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
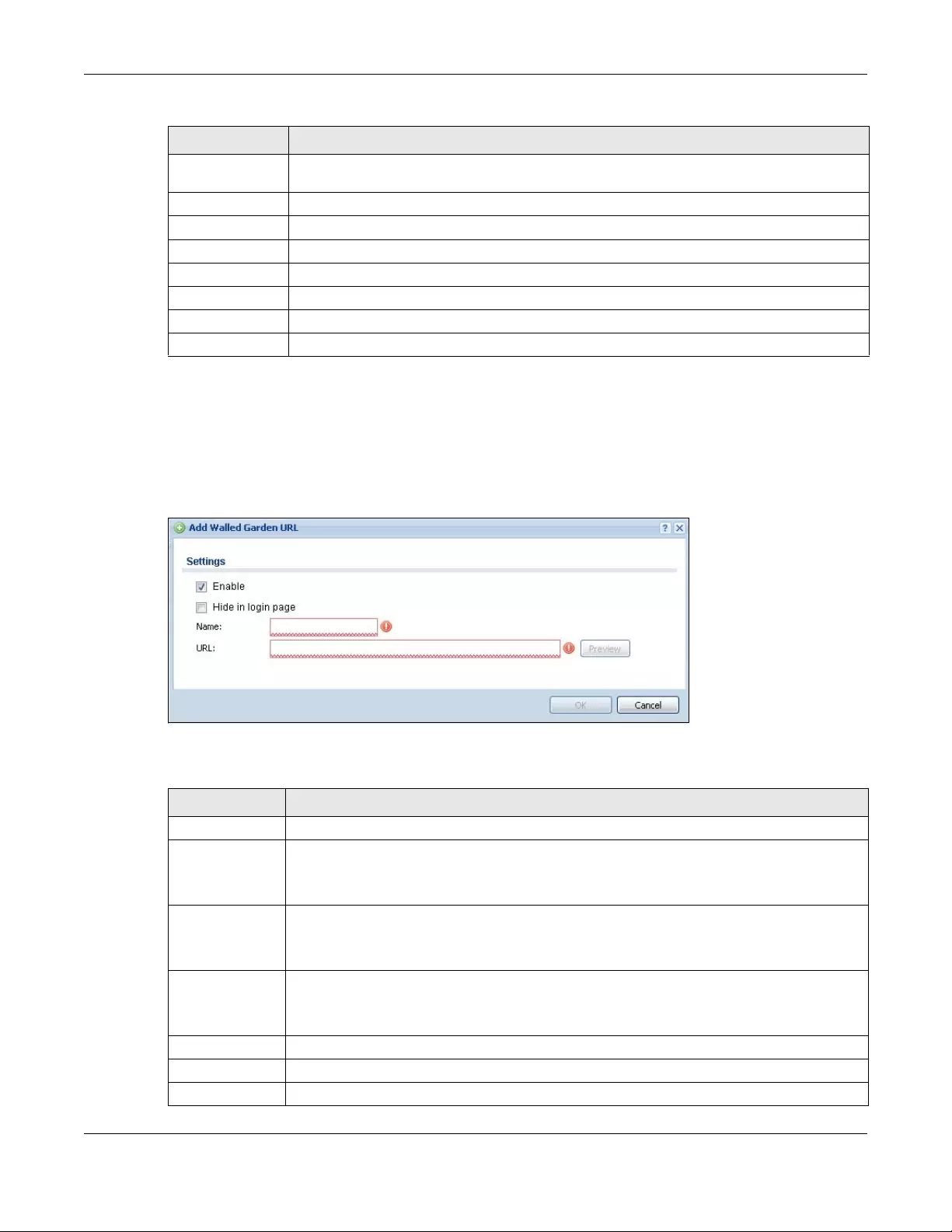
Chapter 26 Walled Garden
USG/ZyWALL User’s Guide
507
26.3.1 Adding/Editing a Walled Garden URL
Go to the Configuration > Web Authentication > Walled Garden > URL Base screen. Click Add or select
an entry and click the Edit to open the Add/Edit Walled Garden URL screen. Use this screen to configure
a walled garden web site URL entry.
Figure 363 Configuration > Hotspot > Walled Garden: URL Base: Add/Edit
The following table describes the labels in this screen.
Move To move an entry to a different number in the list, click the Move icon. In the field that appears,
specify the number to which you want to move the interface.
# This field is a sequential value, and it is not associated with any entry.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
Display This icon is lit when the web site link is set to display in the user login screen.
Name This field displays the descriptive name of the web site.
URL This field displays the URL of the web site.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
Table 189 Configuration > Hotspot > Walled Garden: URL Based (continued)
LABEL DESCRIPTION
Table 190 Configuration > Hotspot > Walled Garden: URL Base: Add/Edit
LABEL DESCRIPTION
Enable Select this to activate the entry.
Hide in login
page
Select this to not display the web site link in the user login screen.
This is helpful if a user’s access to a specific web site is required to stay connected but he or she
doesn’t need to visit that web site.
Name Enter a descriptive name for the walled garden link to be displayed in the login screen.
You can use up to 31 alphanumeric characters (A-Z, a-z, 0-9) and underscores (_). Spaces are
also allowed. The first character must be a letter.
URL Enter the URL of the web site.
Use “http://” or “https://” followed by up to 262 characters (0-9a-zA-Z;/?:@&=+$\.-_!~*'()%). For
example, http://www.example.com or http://172.16.1.35.
Preview Click this button to open the specified web site in a new frame.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
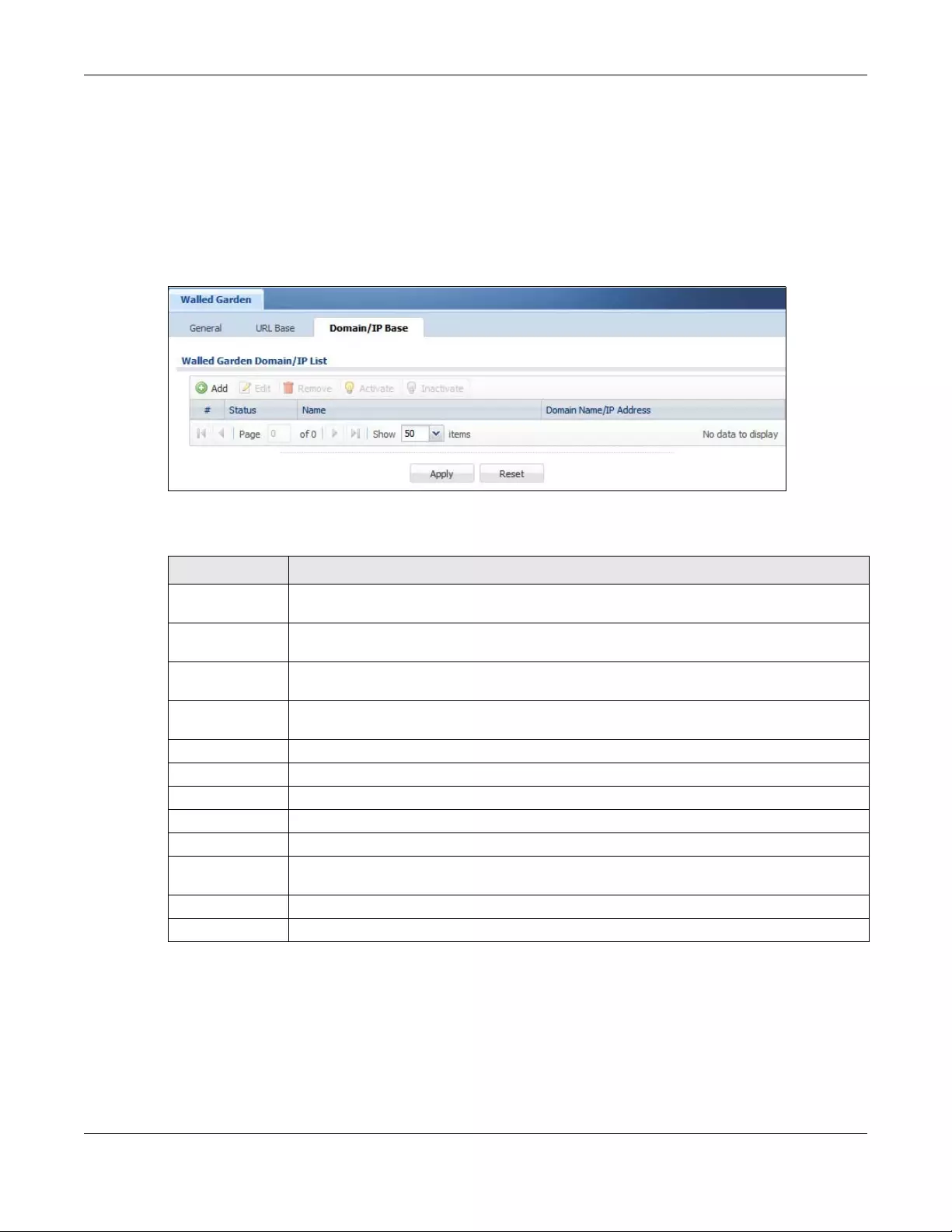
Chapter 26 Walled Garden
USG/ZyWALL User’s Guide
508
26.4 Domain/IP Base Screen
Use this screen to configure walled garden web site links, which use a (wildcard) domain name or an IP
address. These links will not display in the login page.
Click Configuration > Hotspot > Walled Garden and then select the Domain/IP Base tab to display the
screen.
Figure 364 Configuration > Hotspot > Walled Garden: Domain/IP Base
The following table describes the labels in this screen.
26.4.1 Adding/Editing a Walled Garden Domain or IP
Go to the Configuration > Hotspot > Walled Garden > Domain/IP Base screen. Click Add or select an
entry and click the Edit to open the Add/Edit Walled Garden Domain/IP screen. Use this screen to
configure the domain name or IP address entry for a walled garden web site.
Table 191 Configuration > Hotspot > Walled Garden: Domain/IP Based
LABEL DESCRIPTION
Walled Garden
Domain/IP List
Use this table to manage the list of walled garden web site links.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after the
selected entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
# This field is a sequential value, and it is not associated with any entry.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
Name This field displays the descriptive name of the web site.
Domain Name/IP
Address
This field displays the domain name or IP address and subnet mask of the web site.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
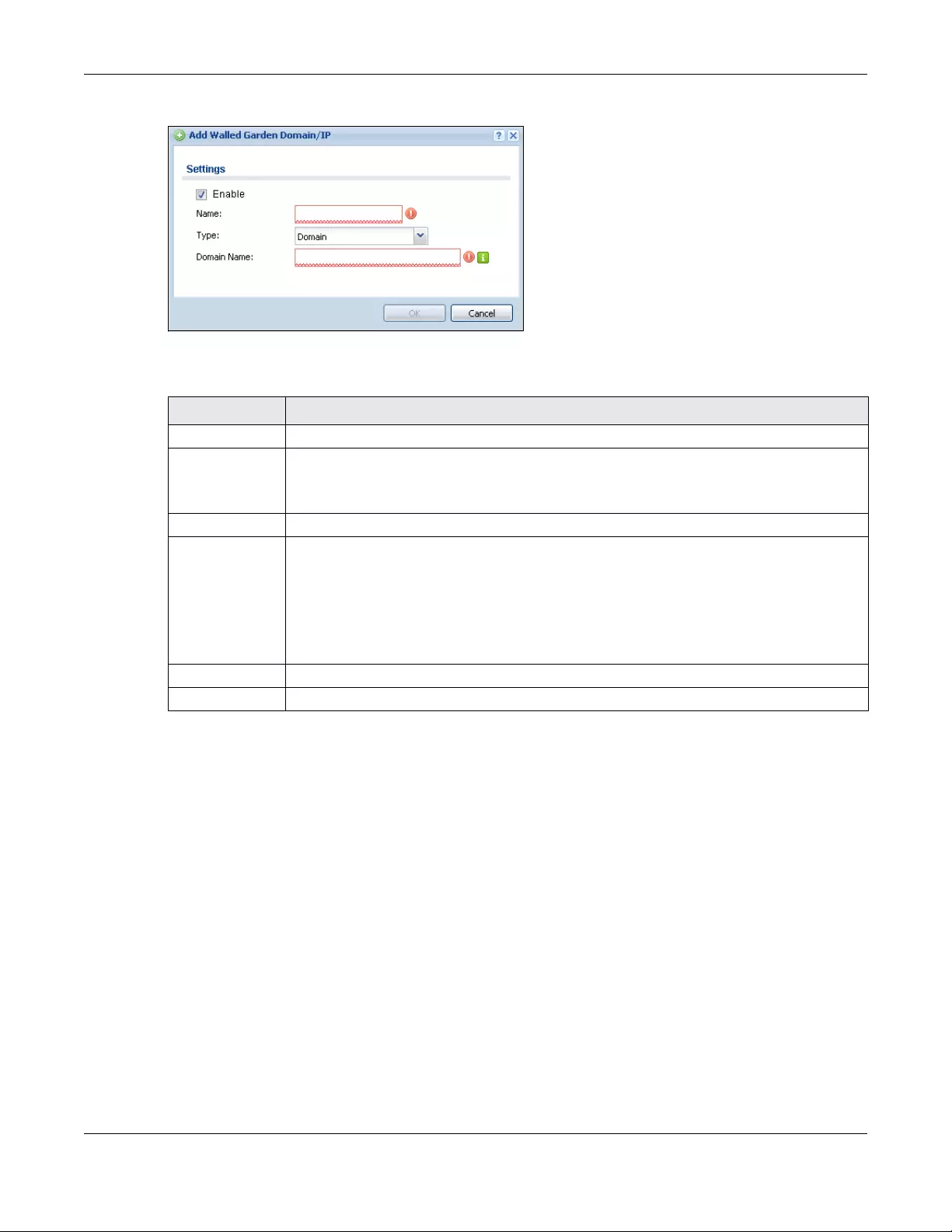
Chapter 26 Walled Garden
USG/ZyWALL User’s Guide
509
Figure 365 Configuration > Hotspot > Walled Garden: Domain/IP Base: Add/Edit
The following table describes the labels in this screen.
26.4.2 Walled Garden Login Example
The following figure shows the user login screen with two walled garden links. The links are named
WalledGardenLink1 through 2 for demonstration purposes.
Table 192 Configuration > Hotspot > Walled Garden: Domain/IP Base: Add/Edit
LABEL DESCRIPTION
Enable Select this to activate the entry.
Name Enter a descriptive name for the walled garden link.
You can use up to 31 alphanumeric characters (A-Z, a-z, 0-9) and underscores (_). Spaces are
also allowed. The first character must be a letter.
Type Select whether you want to create the link by entering a domain name or an IP address.
Domain Name /
IP Address
If you select Domain, type a Fully-Qualified Domain Name (FQDN) of a web site. An FQDN starts
with a host name and continues all the way up to the top-level domain name. For example,
www.zyxel.com.tw is a fully qualified domain name, where “www” is the host, “zyxel” is the
third-level domain, “com” is the second-level domain, and “tw” is the top level domain.
Underscores are not allowed. Use "*." as a prefix in the FQDN for a wildcard domain name (for
example, *.example.com).
If you select IP, enter the IP address and subnet mask of the web site.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
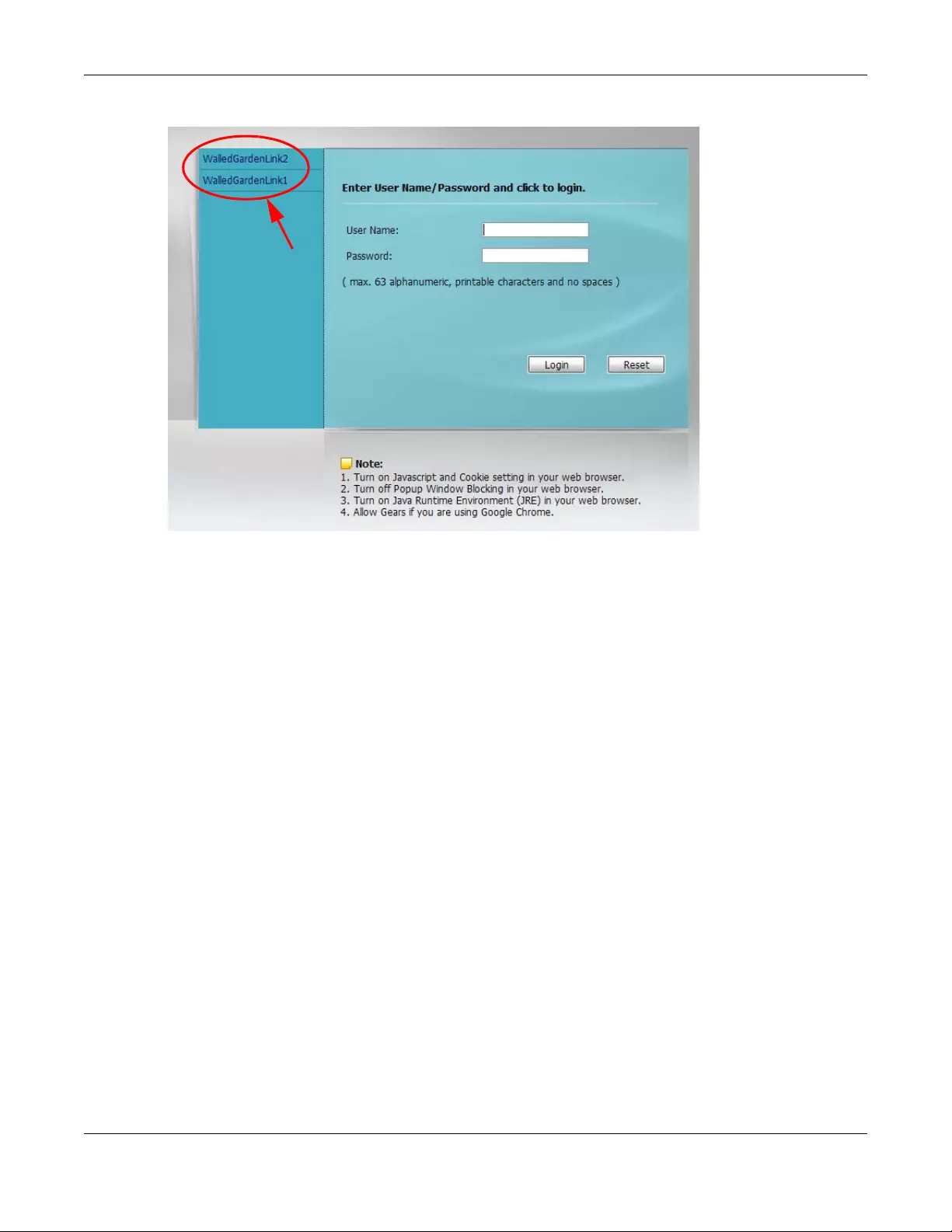
Chapter 26 Walled Garden
USG/ZyWALL User’s Guide
510
Figure 366 Walled Garden Login Example
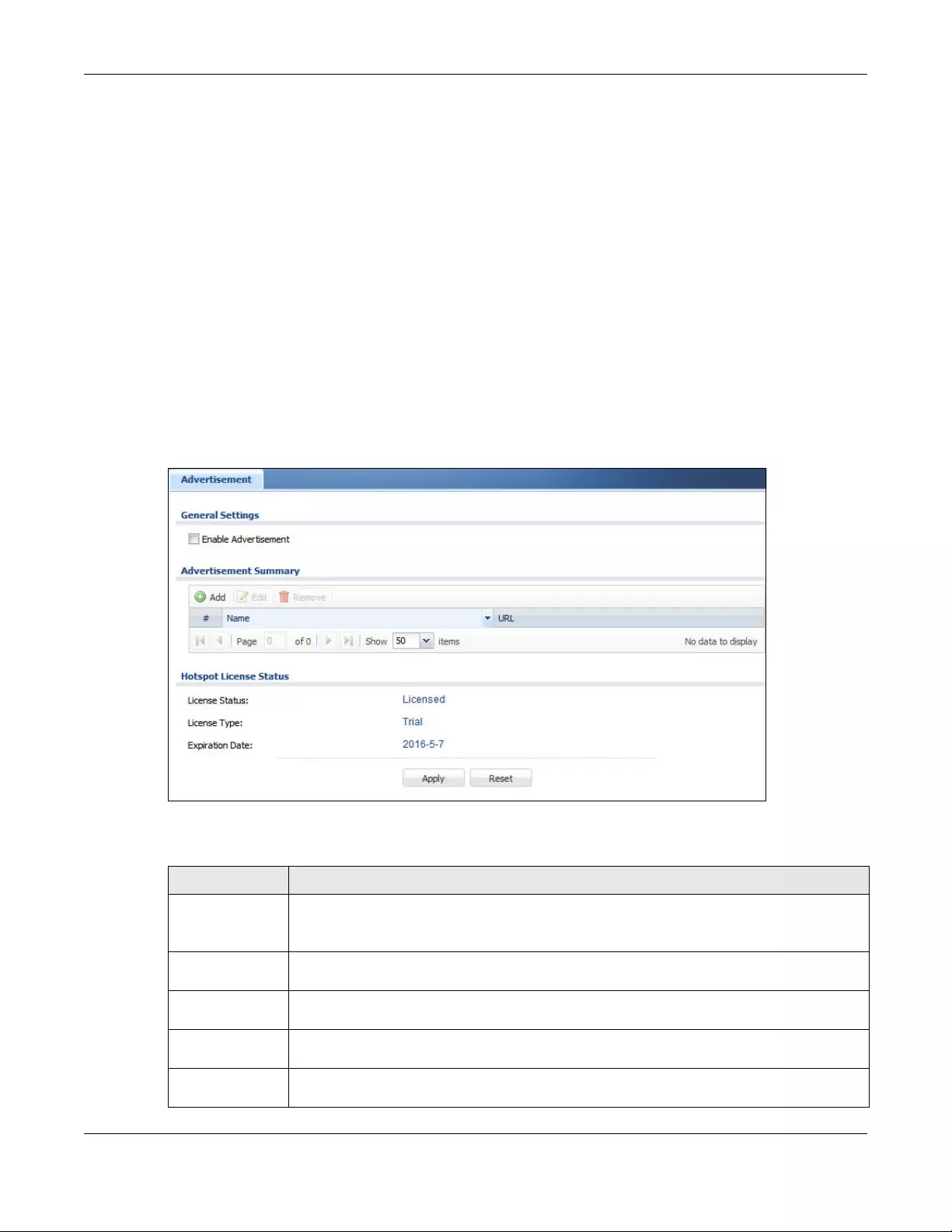
Chapter 27 Advertisement Screen
USG/ZyWALL User’s Guide
511
CHAPTER 27
Advertisement Screen
27.1 Advertisement Overview
Use this screen to set the Zyxel Device to display an advertisement web page as the first web page
whenever the user connects to the Internet.
Click Configuration > Hotspot > Advertisement to display the screen.
Figure 367 Configuration > Hotspot > Advertisement
The following table gives an overview of the objects you can configure.
Table 193 Configuration > Hotspot > Advertisement
LABEL DESCRIPTION
Enable
Advertisement
Select this to turn on the advertisement feature.
Note: This feature works only when you enable web authentication.
Advertisement
Summary
Use this table to manage the list of advertisement web pages.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after the
selected entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
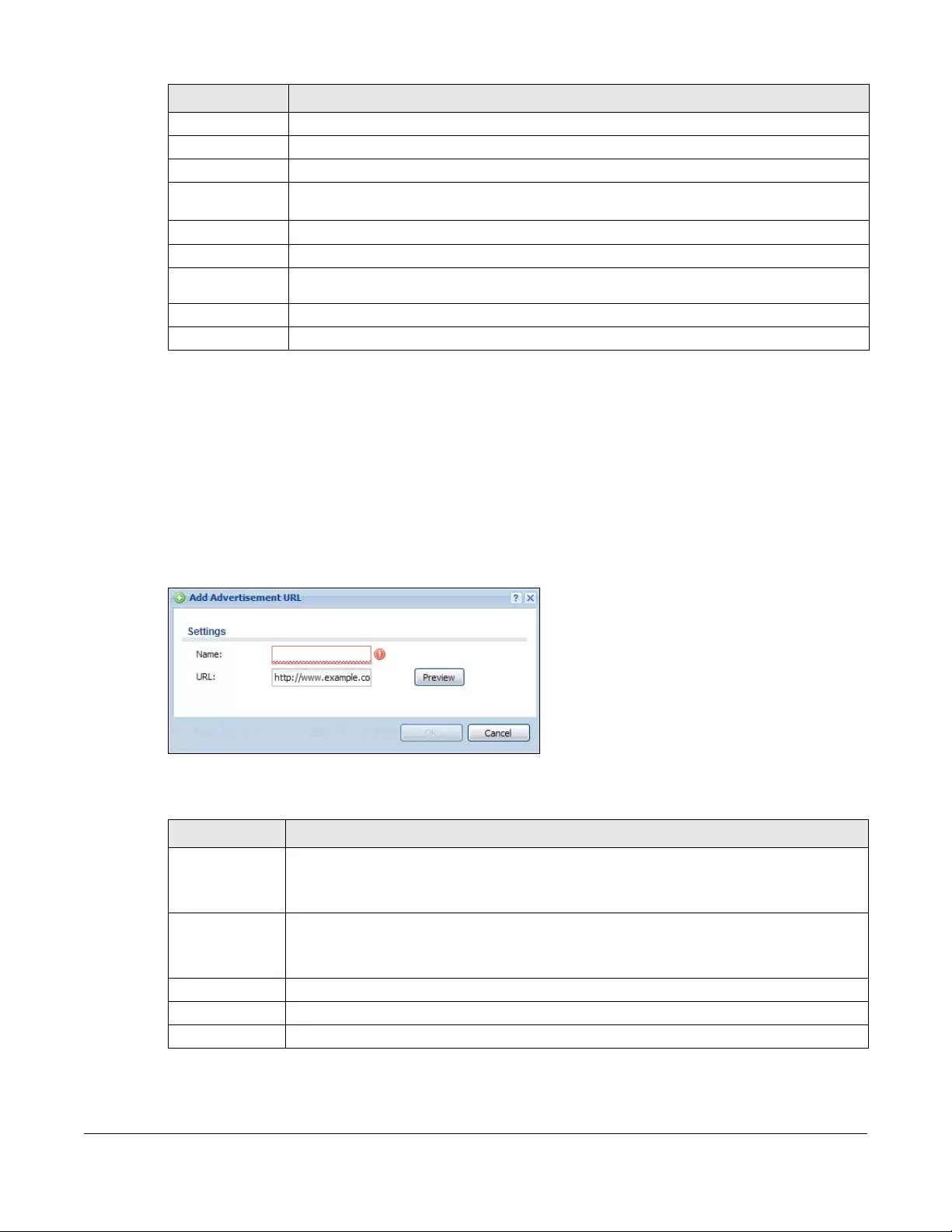
USG/ZyWALL User’s Guide
512
27.1.1 Adding/Editing an Advertisement URL
Click Configuration > Hotspot > Advertisement and then the Add (or Edit) icon in the Advertisement
Summary section to open the Add/Edit Advertisement URL screen. Use this screen to configure an
advertisement address entry.
Note: You can create up to 20 advertisement URL entries. The Zyxel Device randomly picks
one and open the specified web site in a new frame when an authenticated user is
attempts to access the Internet.
Figure 368 Configuration > Hotspot > Advertisement > Add/Edit
The following table gives an overview of the objects you can configure.
# This field is a sequential value, and it is not associated with any entry.
Name This field displays the descriptive name of web site.
URL This field displays the address of web site.
Hotspot License
Status
License Status This field displays whether the service is activated (Licensed) or not (Not Licensed).
License Type This shows whether you have a trial or standard license or none (Trial, Standard, None).
Expiration
Date This shows when your hotspot license will expire.
Apply Click this button to save your changes to the Zyxel Device.
Reset Click this button to return the screen to its last-saved settings.
Table 193 Configuration > Hotspot > Advertisement (continued)
LABEL DESCRIPTION
Table 194 Configuration > Hotspot > Advertisement > Add/Edit
LABEL DESCRIPTION
Name Enter a descriptive name for the advertisement web site.
You can use up to 31 alphanumeric characters (A-Z, a-z, 0-9) and underscores (_). Spaces are
not allowed. The first character must be a letter.
URL Enter the URL or IP address of the web site.
Use “http://” followed by up to 262 characters (0-9a-zA-Z;/?:@&=+$\.-_!~*'()%). For example,
http://www.example.com or http://172.16.1.35.
Preview Click this button to open the specified web site in a new frame.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
USG/ZyWALL User’s Guide
513
CHAPTER 28
Security Policy
28.1 Overview
A security policy is a template of security settings that can be applied to specific traffic at specific times.
The policy can be applied:
• to a specific direction of travel of packets (from / to)
• to a specific source and destination address objects
• to a specific type of traffic (services)
• to a specific user or group of users
• at a specific schedule
The policy can be configured:
• to allow or deny traffic that matches the criteria above
• send a log or alert for traffic that matches the criteria above
• to apply the actions configured in the UTM profiles (application patrol, content filter, IDP, anti-virus,
anti-spam) to traffic that matches the criteria above
Note: Security policies can be applied to both IPv4 and IPv6 traffic.
The security policies can also limit the number of user sessions.
The following example shows the Zyxel Device’s default security policies behavior for a specific direction
of travel of packets. WAN to LAN traffic and how stateful inspection works. A LAN user can initiate a
Telnet session from within the LAN zone and the Zyxel Device allows the response. However, the Zyxel
Device blocks incoming Telnet traffic initiated from the WAN zone and destined for the LAN zone.
Figure 369 Default Directional Security Policy Example
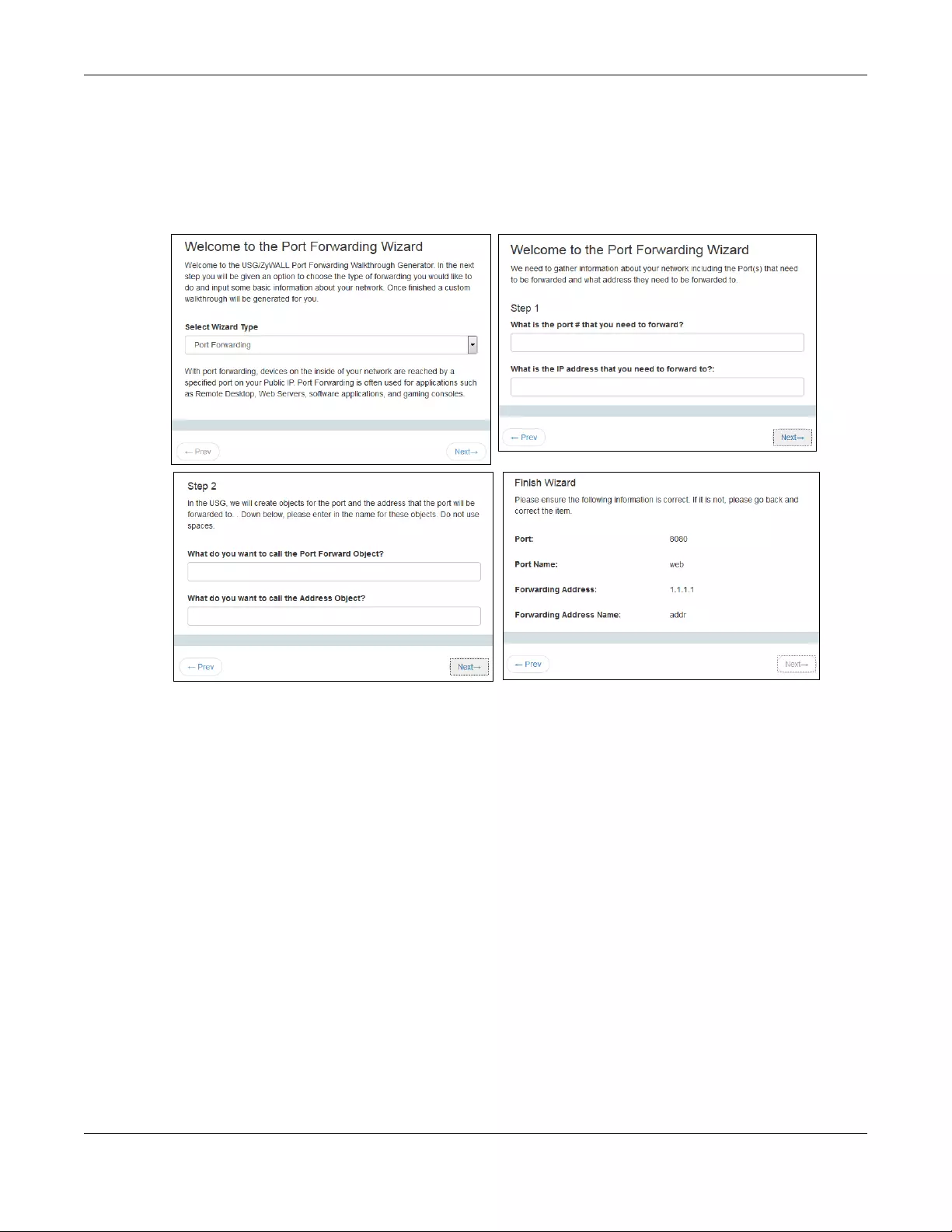
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
514
28.2 One Security
OneSecurity.com is a website with guidance on configuration walkthroughs, troubleshooting, and other
information. This is an example of a port forwarding configuration walkthrough.
Figure 370 Example of a Port Forwarding Configuration Walkthrough.
This is an example of L2TP over IPSec VPN Troubleshooting troubleshooting.
12
34
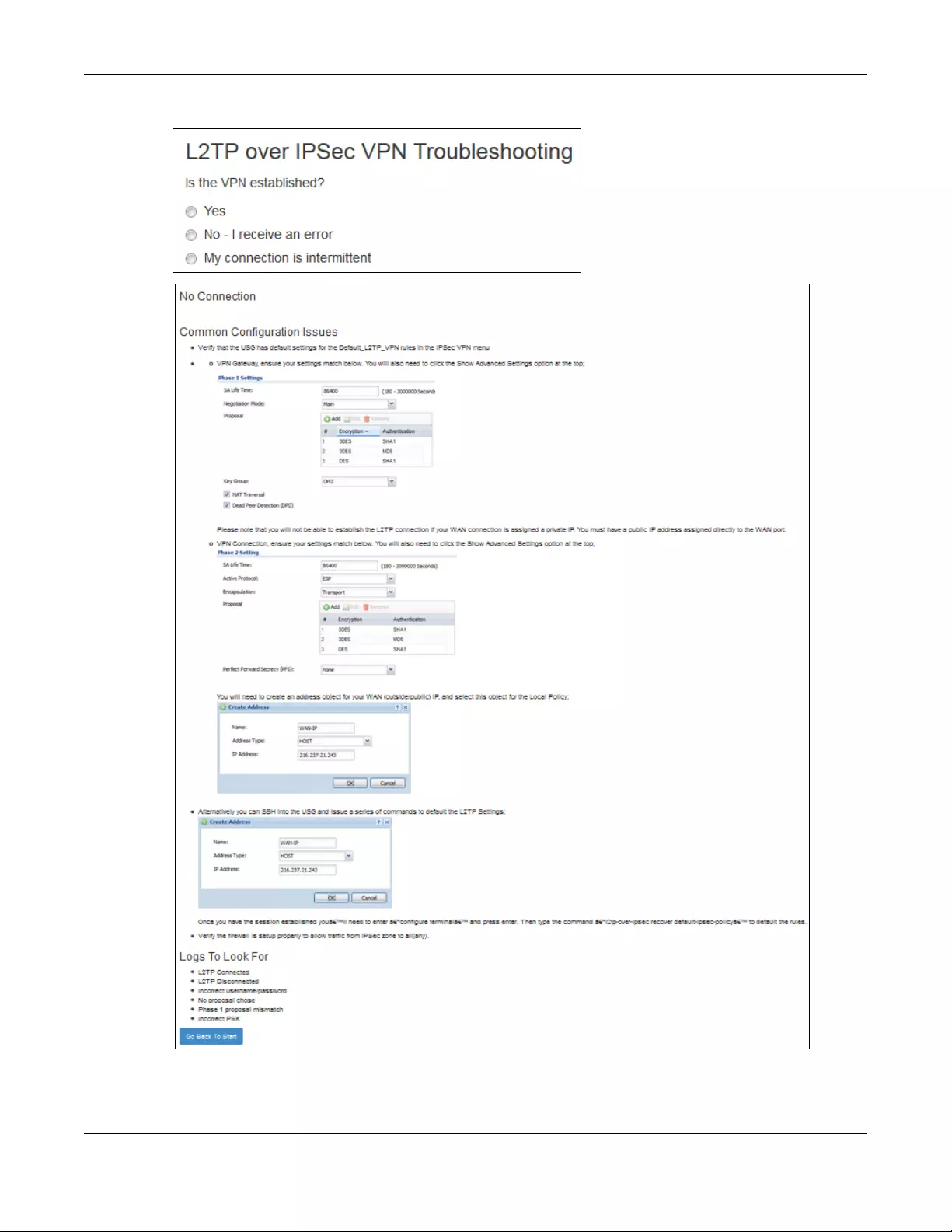
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
515
Figure 371 Example of L2TP over IPSec Troubleshooting - 1
1
2
23
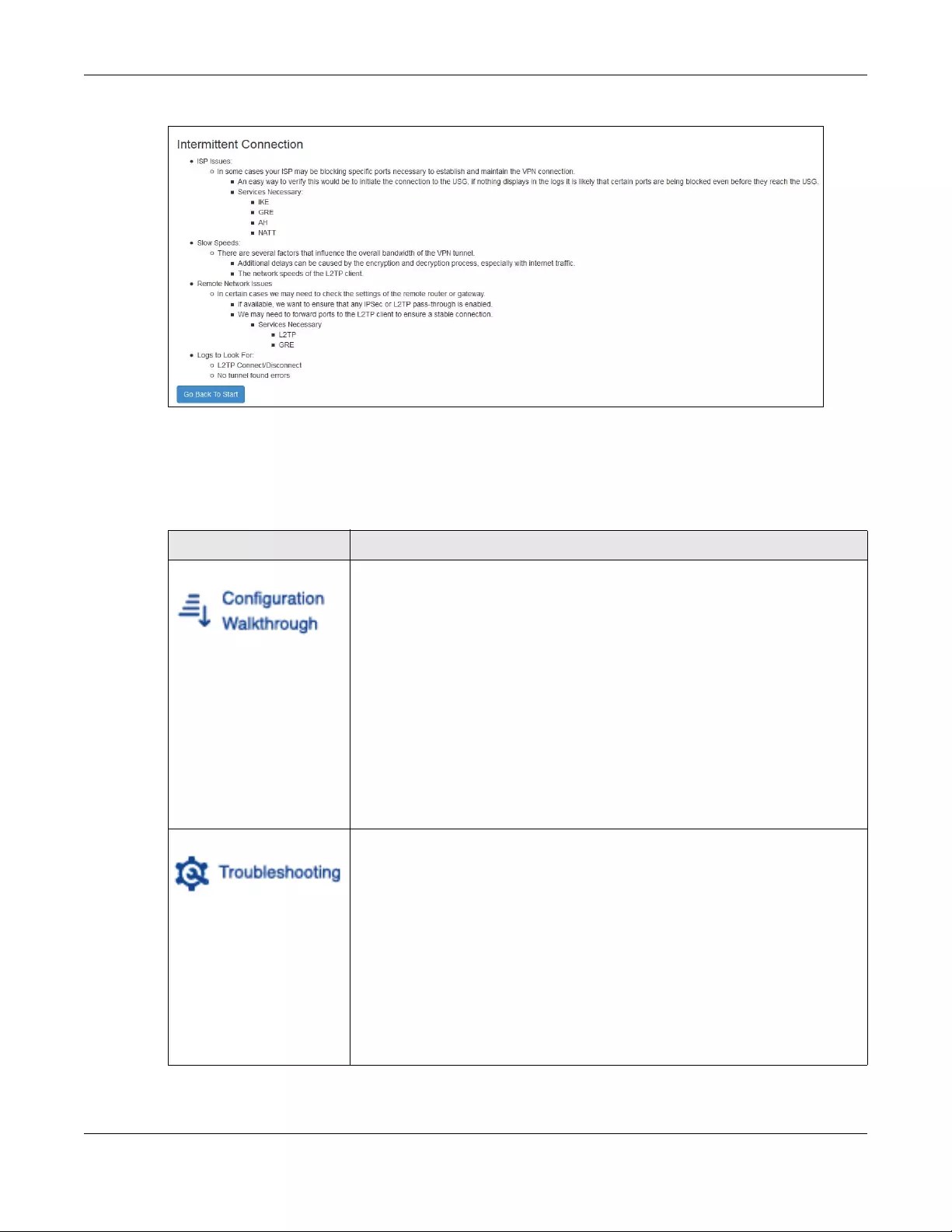
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
516
Figure 372 Example of L2TP over IPSec Troubleshooting - 2
In the Zyxel Device, you will see icons that link to OneSecurity walkthroughs, troubleshooting and so on in
certain screens.
For example, at the time of writing, these are the OneSecurity icons you can see.
Table 195 OneSecurity Icons
ONESECURITY ICON SCREEN
Click this icon to go to a series of screens that guide you how to configure the
feature. Note that the walkthroughs do not perform the actual configuring, but just
show you how to do it.
• Device HA > General
• Licensing > Registration
• Network > NAT
• Network > Routing > Policy Route
• UTM Profile > App Patrol
• UTM Profile > Content Filter
• UTM Profile > IDP
• UTM Profile > Anti-Virus
• UTM Profile > Anti-Spam
•VPN > IPSec VPN
•VPN > SSL VPN
•VPN > L2TP VPN
Click this icon to go to a series of screens that guide you how to fix problems with the
feature.
• Device HA > General
• Network > NAT
• Network > Routing > Policy Route
• UTM Profile > App Patrol
• UTM Profile > Content Filter
• UTM Profile > IDP
• UTM Profile > Anti-Virus
• UTM Profile > Anti-Spam
•VPN > IPSec VPN
•VPN > SSL VPN
•VPN > L2TP VPN
3
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
517
28.3 What You Can Do in this Chapter
• Use the Security Policy Control screens (Section 28.4 on page 519) to enable or disable policies,
asymmetrical routes, and manage and configure policies.
• Use the Anomaly Detection and Prevention (ADP) screens (Section 28.5 on page 525) to detect traffic
with protocol anomalies and take appropriate action.
• Use the Session Control screens (see Section 28.5 on page 525) to limit the number of concurrent NAT/
security policies traffic sessions a client can use.
Click this icon for more information on Application Patrol, which identifies traffic that
passes through the Zyxel Device, so you can decide what to do with specific types
of traffic. Traffic not recognized by application patrol is ignored.
• UTM Profile > Application Patrol
Click this icon for more information on Content Filter, which controls access to
specific web sites or web content.
• UTM Profile > Content Filter
Click this icon for more information on Intrusion Detection which can detect
malicious or suspicious packets used in network-based intrusions.
• UTM Profile > IDP
Click this icon for more information on Anti-Virus, which checks traffic flows through
your network for known virus and spyware signature patterns.
• UTM Profile > Anti-Virus
Click this icon for more information on Anti-Spam which can mark or discard spam
(unsolicited commercial or junk e-mail) and e-mail from certain servers suspect of
being used by spammers.
• UTM Profile > Anti-Spam
Click this icon for more information on IPSec and SSL VPN. Internet Protocol Security
(IPSec) VPN connects IPSec routers or remote users using IPSec client software. SSL
VPN allows users to use a web browser for secure remote user login without need of
a VPN router or VPN client software.
•VPN > IPSec VPN
•VPN > SSL VPN
Click this icon to download VPN client software.
•VPN > IPSec VPN
•VPN > SSL VPN
Click this icon for more information on the Wireless AP Controller which sets how the
Zyxel Device allows APs to connect to the wireless network.
• Wireless > AP Management > Mgnt. AP List
Table 195 OneSecurity Icons (continued)
ONESECURITY ICON SCREEN
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
518
28.3.1 What You Need to Know
Stateful Inspection
The Zyxel Device uses stateful inspection in its security policies. The Zyxel Device restricts access by
screening data packets against defined access rules. It also inspects sessions. For example, traffic from
one zone is not allowed unless it is initiated by a computer in another zone first.
Zones
A zone is a group of interfaces. Group the Zyxel Device’s interfaces into different zones based on your
needs. You can configure security policies for data passing between zones or even between interfaces.
Default Directional Security Policy Behavior
Security Policies can be grouped based on the direction of travel of packets to which they apply. Here
is the The Zyxel Device has default Security Policy behavior for traffic going through the Zyxel Device in
various directions.
To-Device Policies
Policies with Device as the To Zone apply to traffic going to the Zyxel Device itself. By default:
• The Security Policy allows only LAN, or WAN computers to access or manage the Zyxel Device.
• The Zyxel Device allows DHCP traffic from any interface to the Zyxel Device.
• The Zyxel Device drops most packets from the WAN zone to the Zyxel Device itself and generates a
log except for AH, ESP, GRE, HTTPS, IKE, NATT.
When you configure a Security Policy rule for packets destined for the Zyxel Device itself, make sure it
does not conflict with your service control rule. The Zyxel Device checks the security policy before the
service control rules for traffic destined for the Zyxel Device.
A From Any To Device direction policy applies to traffic from an interface which is not in a zone.
Table 196 Directional Security Policy Behavior
FROM ZONE TO ZONE BEHAVIOR
From any to Device DHCP traffic from any interface to the Zyxel Device is allowed.
From LAN1 to any (other than
the Zyxel Device)
Traffic from the LAN1 to any of the networks connected to the Zyxel Device is
allowed.
From LAN2 to any (other than
the Zyxel Device)
Traffic from the LAN2 to any of the networks connected to the Zyxel Device is
allowed.
From LAN1 to Device Traffic from the LAN1 to the Zyxel Device itself is allowed.
From LAN2 to Device Traffic from the LAN2 to the Zyxel Device itself is allowed.
From WAN to Device The default services listed in To-Device Policies on page 518 are allowed from the
WAN to the Zyxel Device itself. All other WAN to Zyxel Device traffic is dropped.
From any to any Traffic that does not match any Security policy is dropped. This includes traffic
from the WAN to any of the networks behind the Zyxel Device.
This also includes traffic to or from interfaces that are not assigned to a zone
(extra-zone traffic).

Chapter 28 Security Policy
USG/ZyWALL User’s Guide
519
Global Security Policies
Security Policies with from any and/or to any as the packet direction are called global Security Policies.
The global Security Policies are the only Security Policies that apply to an interface that is not included in
a zone. The from any policies apply to traffic coming from the interface and the to any policies apply to
traffic going to the interface.
Security Policy Rule Criteria
The Zyxel Device checks the schedule, user name (user’s login name on the Zyxel Device), source IP
address and object, destination IP address and object, IP protocol type of network traffic (service) and
UTM profile criteria against the Security Policies (in the order you list them). When the traffic matches a
policy, the Zyxel Device takes the action specified in the policy.
User Specific Security Policies
You can specify users or user groups in Security Policies. For example, to allow a specific user from any
computer to access a zone by logging in to the Zyxel Device, you can set up a policy based on the user
name only. If you also apply a schedule to the Security Policy, the user can only access the network at
the scheduled time. A user-aware Security Policy is activated whenever the user logs in to the Zyxel
Device and will be disabled after the user logs out of the Zyxel Device.
Session Limits
Accessing the Zyxel Device or network resources through the Zyxel Device requires a NAT session and
corresponding Security Policy session. Peer to peer applications, such as file sharing applications, may
use a large number of NAT sessions. A single client could use all of the available NAT sessions and
prevent others from connecting to or through the Zyxel Device. The Zyxel Device lets you limit the
number of concurrent NAT/Security Policy sessions a client can use.
28.4 The Security Policy Screen
Asymmetrical Routes
If an alternate gateway on the LAN has an IP address in the same subnet as the Zyxel Device’s LAN IP
address, return traffic may not go through the Zyxel Device. This is called an asymmetrical or “triangle”
route. This causes the Zyxel Device to reset the connection, as the connection has not been
acknowledged.
You can have the Zyxel Device permit the use of asymmetrical route topology on the network (not reset
the connection). However, allowing asymmetrical routes may let traffic from the WAN go directly to the
LAN without passing through the Zyxel Device. A better solution is to use virtual interfaces to put the Zyxel
Device and the backup gateway on separate subnets. Virtual interfaces allow you to partition your
network into logical sections over the same interface. See the chapter about interfaces for more
information.
By putting LAN 1 and the alternate gateway (A in the figure) in different subnets, all returning network
traffic must pass through the Zyxel Device to the LAN. The following steps and figure describe such a
scenario.
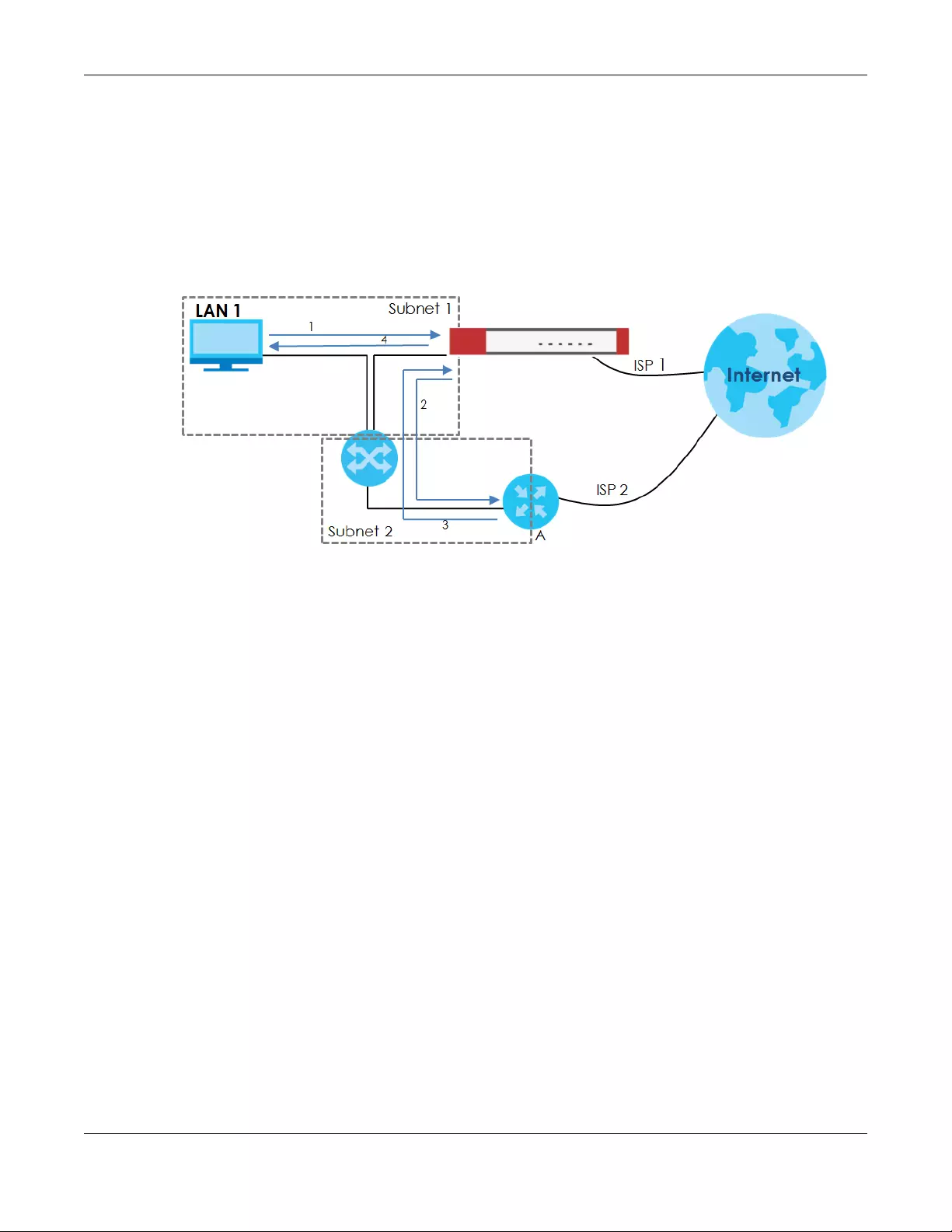
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
520
1A computer on the LAN1 initiates a connection by sending a SYN packet to a receiving server on the
WAN.
2The Zyxel Device reroutes the packet to gateway A, which is in Subnet 2.
3The reply from the WAN goes to the Zyxel Device.
4The Zyxel Device then sends it to the computer on the LAN1 in Subnet 1.
Figure 373 Using Virtual Interfaces to Avoid Asymmetrical Routes
28.4.1 Configuring the Security Policy Control Screen
Click Configuration > Security Policy > Policy Control to open the Security Policy screen. Use this screen
to enable or disable the Security Policy and asymmetrical routes, set a maximum number of sessions per
host, and display the configured Security Policies. Specify from which zone packets come and to which
zone packets travel to display only the policies specific to the selected direction. Note the following.
• Besides configuring the Security Policy, you also need to configure NAT rules to allow computers on
the WAN to access LAN devices.
• The Zyxel Device applies NAT (Destination NAT) settings before applying the Security Policies. So for
example, if you configure a NAT entry that sends WAN traffic to a LAN IP address, when you configure
a corresponding Security Policy to allow the traffic, you need to set the LAN IP address as the
destination.
• The ordering of your policies is very important as policies are applied in sequence.
The following screen shows the Security Policy summary screen.
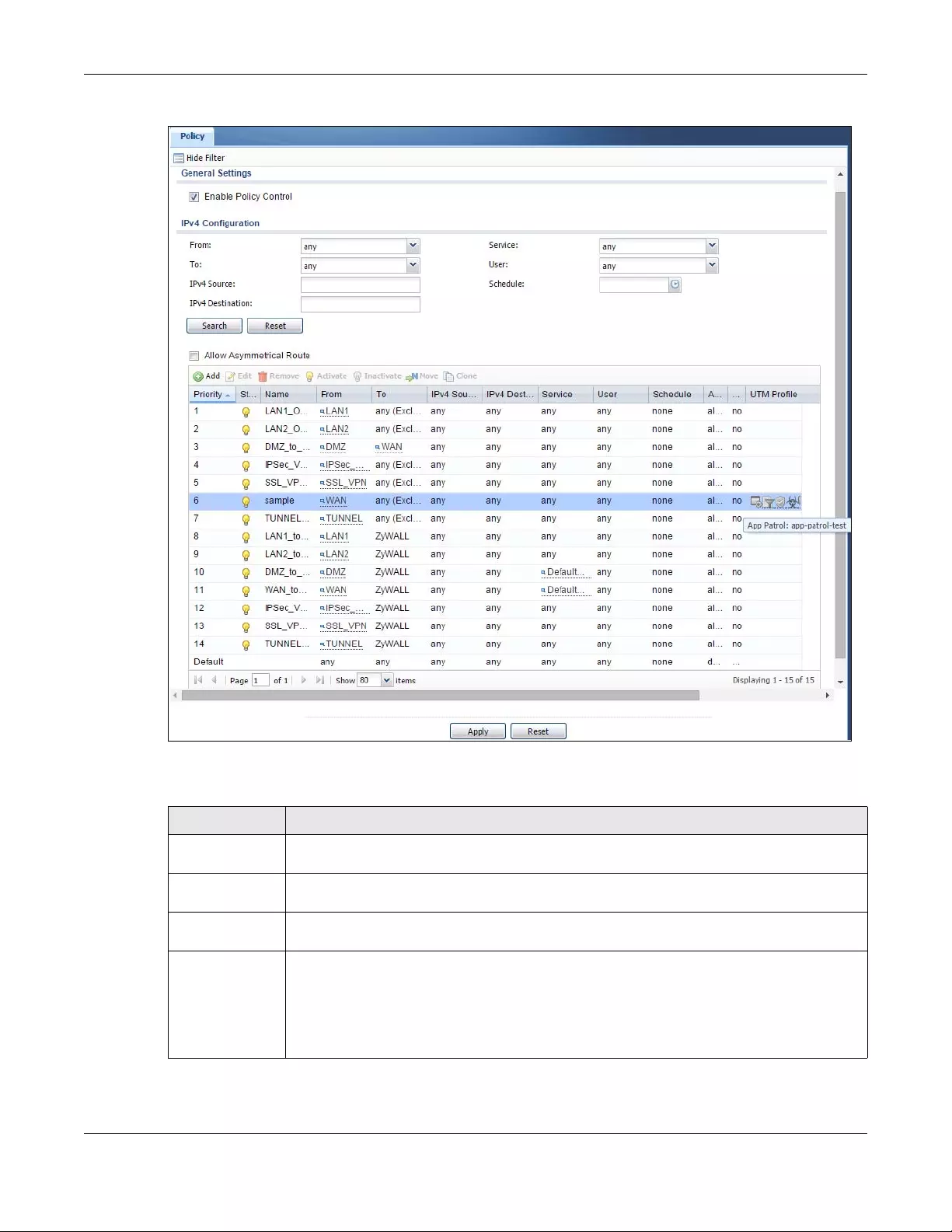
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
521
Figure 374 Configuration > Security Policy > Policy Control
The following table describes the labels in this screen.
Table 197 Configuration > Security Policy > Policy Control
LABEL DESCRIPTION
Show Filter/Hide
Filter
Click Show Filter to display IPv4 and IPv6 (if enabled) security policy search filters.
IPv4 / IPv6
Configuration
Use IPv4 / IPv6 search filters to find specific IPv4 and IPv6 (if enabled) security policies based on
direction, application, user, source, destination and/or schedule.
From / To Select a zone to view all security policies from a particular zone and/or to a particular zone.
any means all zones.
IPv4 / IPv6
Source Type an IPv4 or IPv6 IP address to view all security policies based on the IPv4 / IPv6 source
address object used.
• An IPv4 IP address is written as four integer blocks separated by periods. This is an example
IPv4 address: 172.16.6.7.
• An 128-bit IPv6 address is written as eight 16-bit hexadecimal blocks separated by colons
(:). This is an example IPv6 address: 2001:0db8:1a2b:0015:0000:0000:1a2f:0000.
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
522
IPv4 / IPv6
Destination Type an IPv4 or IPv6 IP address to view all security policies based on the IPv4 / IPv6 destination
address object used.
• An IPv4 IP address is written as four integer blocks separated by periods. This is an example
IPv4 address: 172.16.6.7.
• An 128-bit IPv6 address is written as eight 16-bit hexadecimal blocks separated by colons
(:). This is an example IPv6 address: 2001:0db8:1a2b:0015:0000:0000:1a2f:0000.
Service View all security policies based the service object used.
User View all security policies based on user or user group object used.
Schedule View all security policies based on the schedule object used.
General Settings Enable or disable the Security Policy feature on the Zyxel Device.
Enable Policy
Control
Select this to activate Security Policy on the Zyxel Device to perform access control.
IPv4/IPv6 Policy
Management
Use the following items to manage IPv4 and IPv6 policies.
Allow
Asymmetrical
Route
If an alternate gateway on the LAN has an IP address in the same subnet as the Zyxel Device’s
LAN IP address, return traffic may not go through the Zyxel Device. This is called an
asymmetrical or “triangle” route. This causes the Zyxel Device to reset the connection, as the
connection has not been acknowledged.
Select this check box to have the Zyxel Device permit the use of asymmetrical route topology
on the network (not reset the connection).
Note: Allowing asymmetrical routes may let traffic from the WAN go directly to the
LAN without passing through the Zyxel Device. A better solution is to use virtual
interfaces to put the Zyxel Device and the backup gateway on separate
subnets.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after the
selected entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Move To change a policy’s position in the numbered list, select the policy and click Move to display a
field to type a number for where you want to put that policy and press [ENTER] to move the
policy to the number that you typed.
The ordering of your policies is important as they are applied in order of their numbering.
Clone Use Clone to create a new entry by modifying an existing one.
• Select an existing entry.
•Click Clone, type a number where the new entry should go and then press [ENTER].
• A configuration copy of the selected entry pops up. You must at least change the name as
duplicate entry names are not allowed.
The following read-only fields summarize the policies you have created that apply to traffic traveling in the
selected packet direction.
Priority This is the position of your Security Policy in the global policy list (including all through-Zyxel
Device and to-Zyxel Device policies). The ordering of your policies is important as policies are
applied in sequence. Default displays for the default Security Policy behavior that the Zyxel
Device performs on traffic that does not match any other Security Policy.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
Table 197 Configuration > Security Policy > Policy Control (continued)
LABEL DESCRIPTION
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
523
28.4.2 The Security Policy Control Add/Edit Screen
In the Security Policy Control screen, click the Edit or Add icon to display the Security Policy Edit or Add
screen.
Name This is the name of the Security policy.
From / To This is the direction of travel of packets. Select from which zone the packets come and to
which zone they go.
Security Policies Rare grouped based on the direction of travel of packets to which they apply.
For example, from LAN to LAN means packets traveling from a computer or subnet on the LAN
to either another computer or subnet on the LAN.
From any displays all the Security Policies for traffic going to the selected To Zone.
To any displays all the Security Policies for traffic coming from the selected Fr om Zone.
From any to any displays all of the Security Policies.
To ZyWALL policies are for traffic that is destined for the Zyxel Device and control which
computers can manage the Zyxel Device.
IPv4 / IPv6 Source This displays the IPv4 / IPv6 source address object to which this Security Policy applies.
IPv4 / IPv6
Destination
This displays the IPv4 / IPv6 destination address object to which this Security Policy applies.
Service This displays the service object to which this Security Policy applies.
User This is the user name or user group name to which this Security Policy applies.
Schedule This field tells you the schedule object that the policy uses. none means the policy is active at all
times if enabled.
Action This field displays whether the Security Policy silently discards packets without notification
(deny), permits the passage of packets (allow) or drops packets with notification (reject)
UTM Profile This field shows you which UTM profiles (application patrol, content filter, IDP, anti-virus, anti-
spam) apply to this Security policy. Click an applied UTM profile icon to edit the profile directly.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 197 Configuration > Security Policy > Policy Control (continued)
LABEL DESCRIPTION
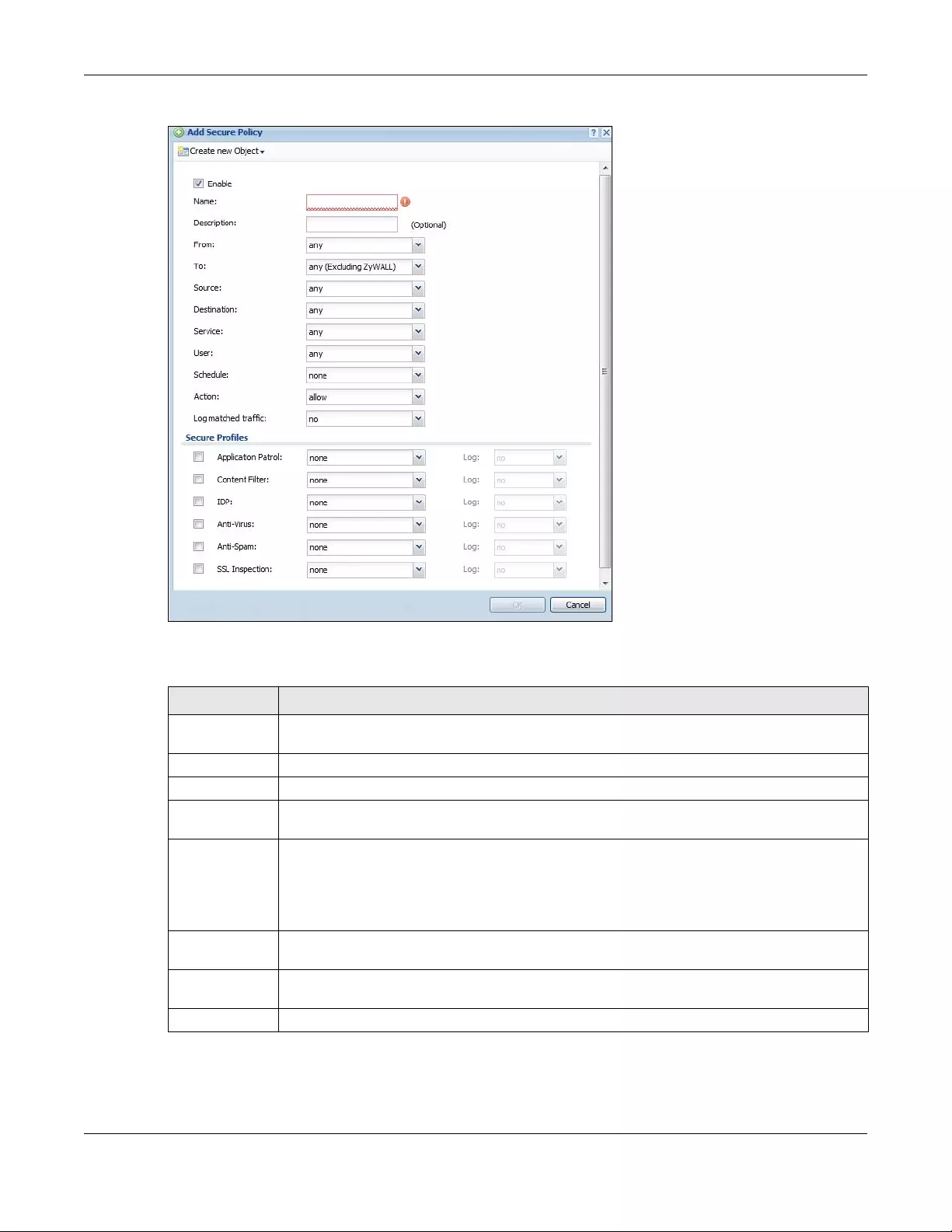
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
524
Figure 375 Configuration > Security Policy > Policy Control > Add
The following table describes the labels in this screen.
Table 198 Configuration > Security Policy > Policy Control > Add
LABEL DESCRIPTION
Create new
Object
Use to configure any new settings objects that you need to use in this screen.
Enable Select this check box to activate the Security policy.
Name Type a name to identify the policy
Description Enter a descriptive name of up to 60 printable ASCII characters for the Policy. Spaces are
allowed.
From
To
For through-Zyxel Device policies, select the direction of travel of packets to which the policy
applies.
any means all interfaces.
Device means packets destined for the Zyxel Device itself.
Source Select an IPv4 / IPv6 address or address group object to apply the policy to traffic coming from
it. Select any to apply the policy to all traffic coming from IPv4 / IPv6 addresses.
Destination Select an IPv4 / IPv6 address or address group to apply the policy to traffic going to it. Select any
to apply the policy to all traffic going to IPv4 / IPv6 addresses.
Service Select a service or service group from the drop-down list box.
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
525
28.5 Anomaly Detection and Prevention Overview
Anomaly Detection and Prevention (ADP) protects against anomalies based on violations of protocol
standards (RFCs – Requests for Comments) and abnormal flows such as port scans. This section
introduces ADP, anomaly profiles and applying an ADP profile to a traffic direction.
User This field is not available when you are configuring a to-Zyxel Device policy.
Select a user name or user group to which to apply the policy. The Security Policy is activated
only when the specified user logs into the system and the policy will be disabled when the user
logs out.
Otherwise, select any and there is no need for user logging.
Note: If you specified a source IP address (group) instead of any in the field below, the
user’s IP address should be within the IP address range.
Schedule Select a schedule that defines when the policy applies. Otherwise, select none and the policy is
always effective.
Action Use the drop-down list box to select what the Security Policy is to do with packets that match this
policy.
Select deny to silently discard the packets without sending a TCP reset packet or an ICMP
destination-unreachable message to the sender.
Select reject to discard the packets and send a TCP reset packet or an ICMP destination-
unreachable message to the sender.
Select allow to permit the passage of the packets.
Log matched
traffic
Select whether to have the Zyxel Device generate a log (log), log and alert (log alert) or not (no)
when the policy is matched to the criteria listed above..
UTM Profile Use this section to apply anti- x profiles (created in the Configuration > UTM Profile screens) to
traffic that matches the criteria above. You must have created a profile first; otherwise none
displays.
Use Log to generate a log (log), log and alert (log alert) or not (no) for all traffic that matches
criteria in the profile.
Application
Patrol Select an Application Patrol profile from the list box; none displays if no profiles have been
created in the Configuration > UTM Profile > App Patrol screen.
Content
Filter Select a Content Filter profile from the list box; none displays if no profiles have been created in
the Configuration > UTM Profile > Content Filter screen.
IDP Select an IDP profile from the list box; none displays if no profiles have been created in the
Configuration > UTM Profile > IDP screen.
Anti-Virus Select an Anti-Virus profile from the list box; none displays if no profiles have been created in the
Configuration > UTM Profile > Anti-Virus screen.
Anti-Spam Select an Anti-Spam profile from the list box; none displays if no profiles have been created in the
Configuration > UTM Profile > Anti-Spam screen.
SSL
Inspection Select an SSL Inspection profile from the list box; none displays if no profiles have been created in
the Configuration > UTM Profile > SSL Inspection screen.
OK Click OK to save your customized settings and exit this screen.
Cancel Click Cancel to exit this screen without saving.
Table 198 Configuration > Security Policy > Policy Control > Add (continued)
LABEL DESCRIPTION
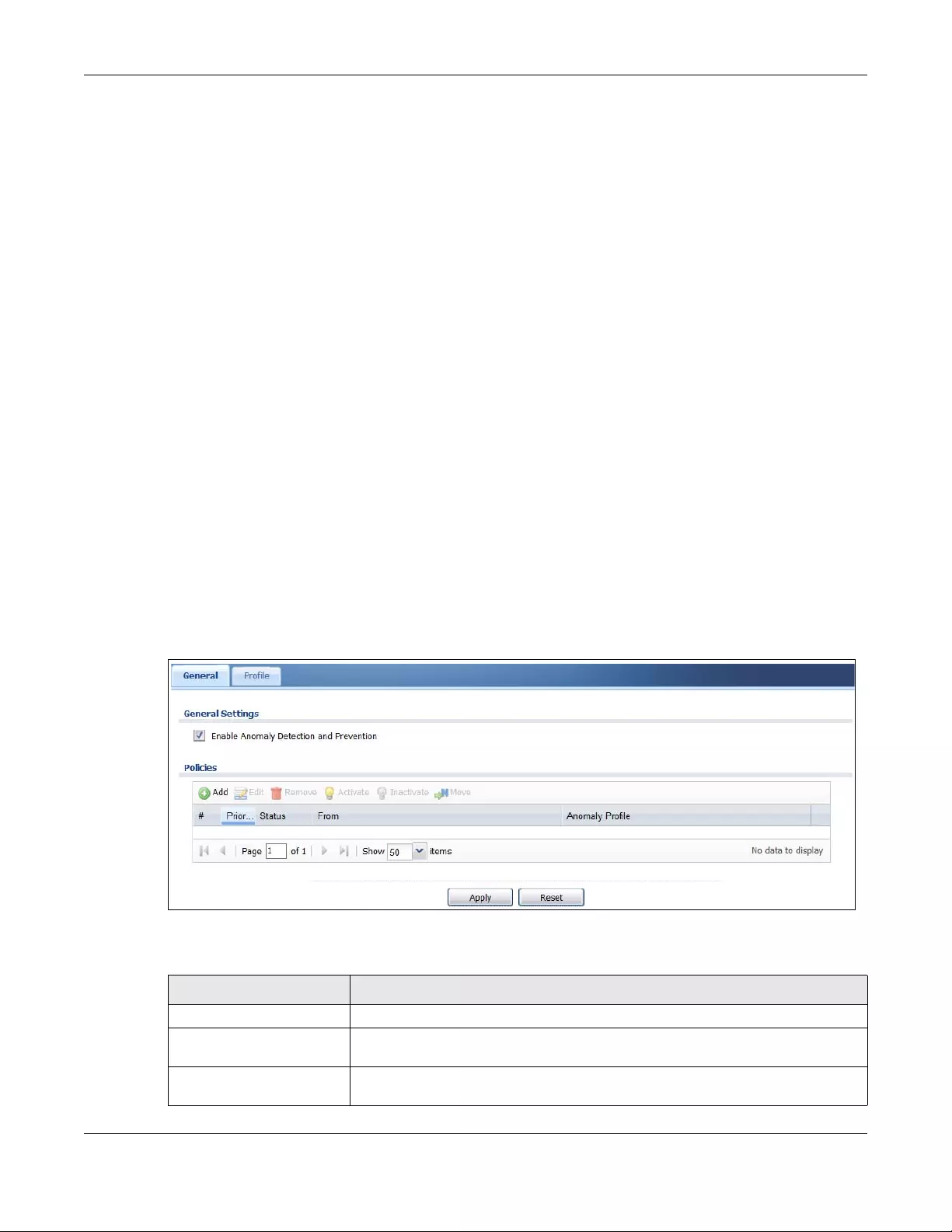
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
526
Traffic Anomalies
Traffic anomaly policies look for abnormal behavior or events such as port scanning, sweeping or
network flooding. They operate at OSI layer-2 and layer-3. Traffic anomaly policies may be updated
when you upload new firmware.
Protocol Anomalies
Protocol anomalies are packets that do not comply with the relevant RFC (Request For Comments).
Protocol anomaly detection includes:
•TCP Decoder
• UDP Decoder
•ICMP Decoder
Protocol anomaly policies may be updated when you upload new firmware.
Note: First, create an ADP profile in the In the Configuration > Security Policy > ADP > Profile
screen.
Then, apply the profile to traffic originating from a specific zone in the Configuration >
Security Policy > ADP > General screen.
28.5.1 The Anomaly Detection and Prevention General Screen
Click Configuration > Security Policy > ADP > General to display the next screen.
Figure 376 Configuration > Security Policy > ADP > General
The following table describes the labels in this screen.
Table 199 Configuration > Security Policy > ADP > General
LABEL DESCRIPTION
General Settings
Enable Anomaly Detection
and Prevention
Select this to enable traffic anomaly and protocol anomaly detection and
prevention.
Add Select an entry and click Add to append a new row beneath the one selected. ADP
policies are applied in order (Priority) shown in this screen
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
527
28.5.2 Creating New ADP Profiles
Create new ADP profiles in the Configuration > Security Policy > ADP > Profile screens.
When creating ADP profiles. you may find that certain policies are triggering too many false positives or
false negatives. A false positive is when valid traffic is flagged as an attack. A false negative is when
invalid traffic is wrongly allowed to pass through the Zyxel Device. As each network is different, false
positives and false negatives are common on initial ADP deployment.
To counter this, you could create a ‘monitor profile’ that creates logs, but all actions are disabled.
Observe the logs over time and try to eliminate the causes of the false alarms. When you’re satisfied that
they have been reduced to an acceptable level, you could then create an ‘in-line profile’ whereby you
configure appropriate actions to be taken when a packet matches a policy.
ADP profiles consist of traffic anomaly profiles and protocol anomaly profiles. To create a new profile,
select a base profile and then click OK to go to the profile details screen. Type a new profile name,
enable or disable individual policies and then edit the default log options and actions.
Click Configuration > Security Policy > ADP > Profile to view the following screen.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Move To change an entry’s position in the numbered list, select it and click Move to display
a field to type a number for where you want to put that entry and press [ENTER] to
move the entry to the number that you typed.
#This is the entry’s index number in the list.
Priority This is the rank in the list of anomaly profile policies. The list is applied in order of
priority.
Status The activate (light bulb) icon is lit when the entry is active and dimmed when the
entry is inactive.
From This is the direction of travel of packets to which an anomaly profile is bound. Traffic
direction is defined by the zone the traffic is coming from.
Use the From field to specify the zone from which the traffic is coming. Select ZyWALL
to specify traffic coming from the Zyxel Device itself.
From LAN means packets traveling from a computer on one LAN subnet to a
computer on another subnet via the Zyxel Device’s LAN1 zone interfaces. The Zyxel
Device does not check packets traveling from a LAN computer to another LAN
computer on the same subnet.
From WAN means packets that come in from the WAN zone and the Zyxel Device
routes back out through the WAN zone.
Note: Depending on your network topology and traffic load, applying
every packet direction to an anomaly profile may affect the Zyxel
Device’s performance.
Anomaly Profile An anomaly profile is a set of anomaly policies with configured activation, log and
action settings. This field shows which anomaly profile is bound to which traffic
direction. Select an ADP profile to apply to the entry’s traffic direction. Configure the
ADP profiles in the ADP profile screens.
Table 199 Configuration > Security Policy > ADP > General
LABEL DESCRIPTION
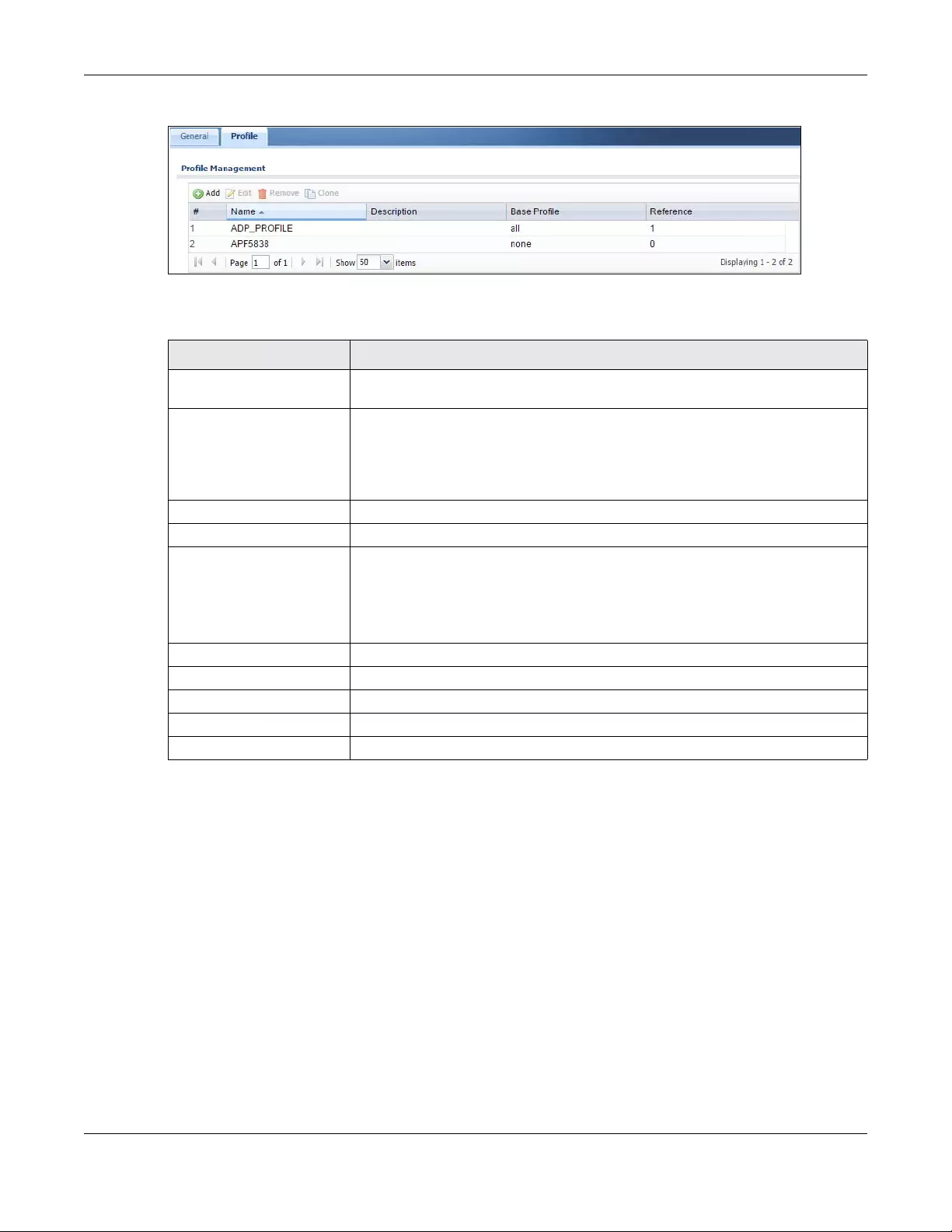
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
528
Figure 377 Configuration > Security Policy > ADP > Profile
The following table describes the labels in this screen.
28.5.3 Traffic Anomaly Profiles
Traffic anomaly detection looks for abnormal behavior such as scan or flooding attempts. In the
Configuration > Security Policy > ADP > Profile screen, click the Edit or Add icon and choose a base
profile. Traffic Anomaly is the first tab in the profile.
Table 200 Configuration > Security Policy > ADP > Profile
LABEL DESCRIPTION
Profile Management Create ADP profiles here and then apply them in the Configuration > Security Policy
> ADP > Profile screen.
Add Click Add and first choose a none or all Base Profile.
•none base profile sets all ADP entries to have Log set to no and Action set to
none by default.
•all base profile sets all ADP entries to have Log set to log and Action set to block
by default.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
Clone Use Clone to create a new entry by modifying an existing one.
• Select an existing entry.
•Click Clone.
• A configuration copy of the selected entry pops up. You must at least change
the name as duplicate entry names are not allowed.
#This is the entry’s index number in the list.
Name This is the name of the profile you created.
Description This is the description of the profile you created.
Base Profile This is the name of the base profile used to create this profile.
Reference This is the number of object references used to create this profile.
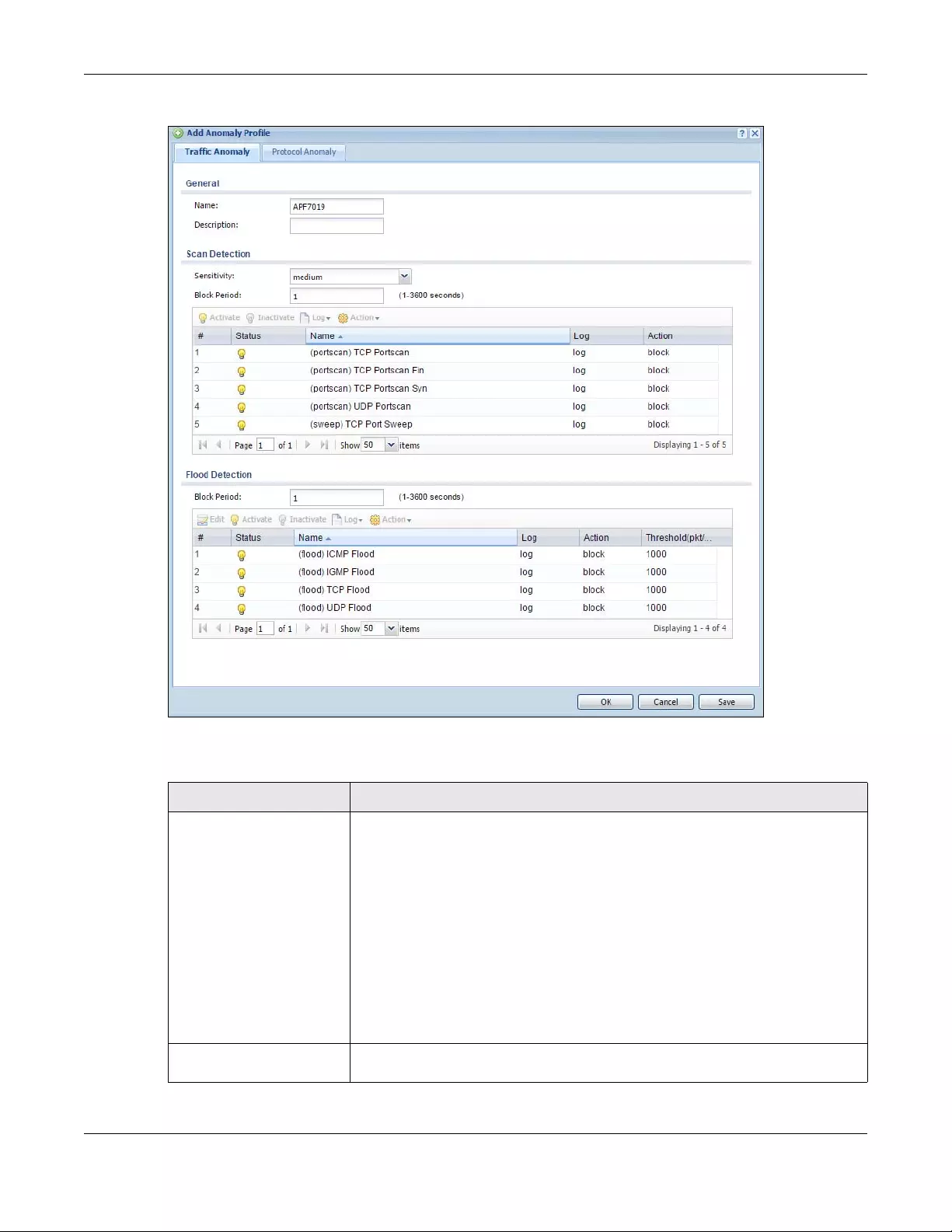
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
529
Figure 378 Configuration > Security Policy > ADP > Profile > Add-Traffic-Anomaly
The following table describes the labels in this screen.
Table 201 Configuration > Security Policy > ADP > Profile > Add-Traffic-Anomaly
LABELS DESCRIPTION
Name A name is automatically generated that you can edit. The name must be the same
in the Traffic Anomaly and Protocol Anomaly screens for the same ADP profile. You
may use 1-31 alphanumeric characters, underscores(_), or dashes (-), but the first
character cannot be a number. This value is case-sensitive. These are valid, unique
profile names:
•MyProfile
• mYProfile
• Mymy12_3-4
• These are invalid profile names:
•1mYProfile
•My Profile
• MyProfile?
• Whatalongprofilename123456789012
Description In addition to the name, type additional information to help you identify this ADP
profile.
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
530
Scan/Flood Detection Scan detection, such as port scanning, tries to find attacks where an attacker scans
device(s) to determine what types of network protocols or services a device
supports.
Flood detection tries to find attacks that saturate a network with useless data, use up
all available bandwidth, and so aim to make communications in the network
impossible.
Sensitivity (Scan detection only.) Select a sensitivity level so as to reduce false positives in your
network. If you choose low sensitivity, then scan thresholds and sample times are set
low, so you will have fewer logs and false positives; however some traffic anomaly
attacks may not be detected.
If you choose high sensitivity, then scan thresholds and sample times are set high, so
most traffic anomaly attacks will be detected; however you will have more logs and
false positives.
Block Period Specify for how many seconds the Zyxel Device blocks all packets from being sent
to the victim (destination) of a detected anomaly attack. Flood Detection applies
blocking to the destination IP address and Scan Detection applies blocking to the
source IP address.
Edit (Flood Detection
only) Select an entry and click this to be able to modify it.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Log To edit an item’s log option, select it and use the Log icon. Select whether to have
the Zyxel Device generate a log (log), log and alert (log alert) or neither (no) when
traffic matches this anomaly policy.
Action To edit what action the Zyxel Device takes when a packet matches a policy, select
the policy and use the Action icon.
none: The Zyxel Device takes no action when a packet matches the policy.
block: The Zyxel Device silently drops packets that matches the policy. Neither
sender nor receiver are notified.
#This is the entry’s index number in the list.
Status The activate (light bulb) icon is lit when the entry is active and dimmed when the
entry is inactive.
Name This is the name of the anomaly policy. Click the Name column heading to sort in
ascending or descending order according to the protocol anomaly policy name.
Log These are the log options. To edit this, select an item and use the Log icon.
Action This is the action the Zyxel Device should take when a packet matches a policy. To
edit this, select an item and use the Action icon.
Threshold (pkt/sec) (Flood detection only.) Select a suitable threshold level (the number of packets per
second that match the flood detection criteria) for your network. If you choose a
low threshold, most traffic anomaly attacks will be detected, but you may have
more logs and false positives.
If you choose a high threshold, some traffic anomaly attacks may not be detected,
but you will have fewer logs and false positives.
OK Click OK to save your settings to the Zyxel Device, complete the profile and return to
the profile summary page.
Cancel Click Cancel to return to the profile summary page without saving any changes.
Save Click Save to save the configuration to the Zyxel Device but remain in the same
page. You may then go to the another profile screen (tab) in order to complete the
profile. Click OK in the final profile screen to complete the profile.
Table 201 Configuration > Security Policy > ADP > Profile > Add-Traffic-Anomaly (continued)
LABELS DESCRIPTION

Chapter 28 Security Policy
USG/ZyWALL User’s Guide
531
28.5.4 Protocol Anomaly Profiles
Protocol anomalies are packets that do not comply with the relevant RFC (Request For Comments).
Protocol anomaly detection includes:
•TCP Decoder
• UDP Decoder
•ICMP Decoder
• IP Decoder
Teardrop
When an IP packet is larger than the Maximum Transmission Unit (MTU) configured in the Zyxel Device, it
is fragmented using the TCP or ICMP protocol.
A Teardrop attack falsifies the offset which defines the size of the fragment and the original packet. A
series of IP fragments with overlapping offset fields can cause some systems to crash, hang, or reboot
when fragment reassembling is attempted at the destination.
IP Spoofing
IP Spoofing is used to gain unauthorized access to network devices by modifying packet headers so
that it appears that the packets originate from a host within a trusted network.
• In an IP Spoof from the WAN, the source address appears to be in the same subnet as a Zyxel Device
LAN interface.
• In an IP Spoof from a LAN interface, the source address appears to be in a different subnet from that
Zyxel Device LAN interface.
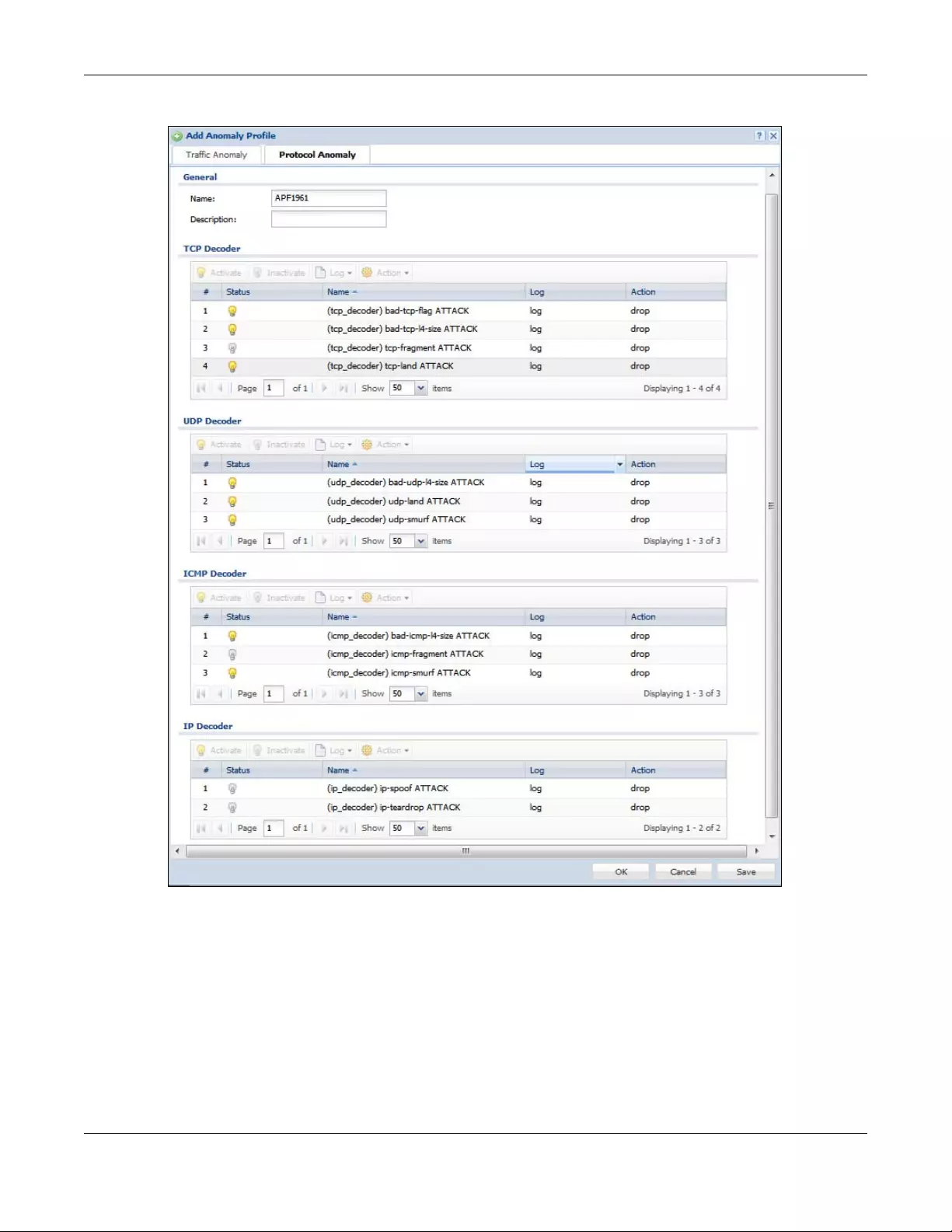
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
532
Figure 379 Configuration > Security Policy > ADP > Profile > Add-Protocol-Anomaly
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
533
The following table describes the labels in this screen.
Table 202 Configuration > Security Policy > ADP > Profile > Add-Protocol-Anomaly
LABEL DESCRIPTION
Name A name is automatically generated that you can edit. The name must be the same
in the Traffic Anomaly and Protocol Anomaly screens for the same ADP profile. You
may use 1-31 alphanumeric characters, underscores(_), or dashes (-), but the first
character cannot be a number. This value is case-sensitive. These are valid, unique
profile names:
•MyProfile
• mYProfile
• Mymy12_3-4
• These are invalid profile names:
•1mYProfile
•My Profile
• MyProfile?
• Whatalongprofilename123456789012
Description In addition to the name, type additional information to help you identify this ADP
profile.
TCP Decoder/UDP
Decoder/ICMP Decoder/IP
Decoder
Perform the following actions for each type of encoder.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Log To edit an item’s log option, select it and use the Log icon. Select whether to have
the Zyxel Device generate a log (log), log and alert (log alert) or neither (no) when
traffic matches this anomaly policy.
Action To edit what action the Zyxel Device takes when a packet matches a policy, select
the policy and use the Action icon.
original setting: Select this action to return each rule in a service group to its
previously saved configuration.
none: Select this action to have the Zyxel Device take no action when a packet
matches a policy.
drop: Select this action to have the Zyxel Device silently drop a packet that matches
a policy. Neither sender nor receiver are notified.
reject-sender: Select this action to have the Zyxel Device send a reset to the sender
when a packet matches the policy. If it is a TCP attack packet, the Zyxel Device will
send a packet with a ‘RST’ flag. If it is an ICMP or UDP attack packet, the Zyxel
Device will send an ICMP unreachable packet.
reject-receiver: Select this action to have the Zyxel Device send a reset to the
receiver when a packet matches the policy. If it is a TCP attack packet, the Zyxel
Device will send a packet with an a ‘RST’ flag. If it is an ICMP or UDP attack packet,
the Zyxel Device will do nothing.
reject-both: Select this action to have the Zyxel Device send a reset to both the
sender and receiver when a packet matches the policy. If it is a TCP attack packet,
the Zyxel Device will send a packet with a ‘RST’ flag to the receiver and sender. If it is
an ICMP or UDP attack packet, the Zyxel Device will send an ICMP unreachable
packet.
#This is the entry’s index number in the list.
Status The activate (light bulb) icon is lit when the entry is active and dimmed when the
entry is inactive.
Name This is the name of the anomaly policy. Click the Name column heading to sort in
ascending or descending order according to the protocol anomaly policy name.
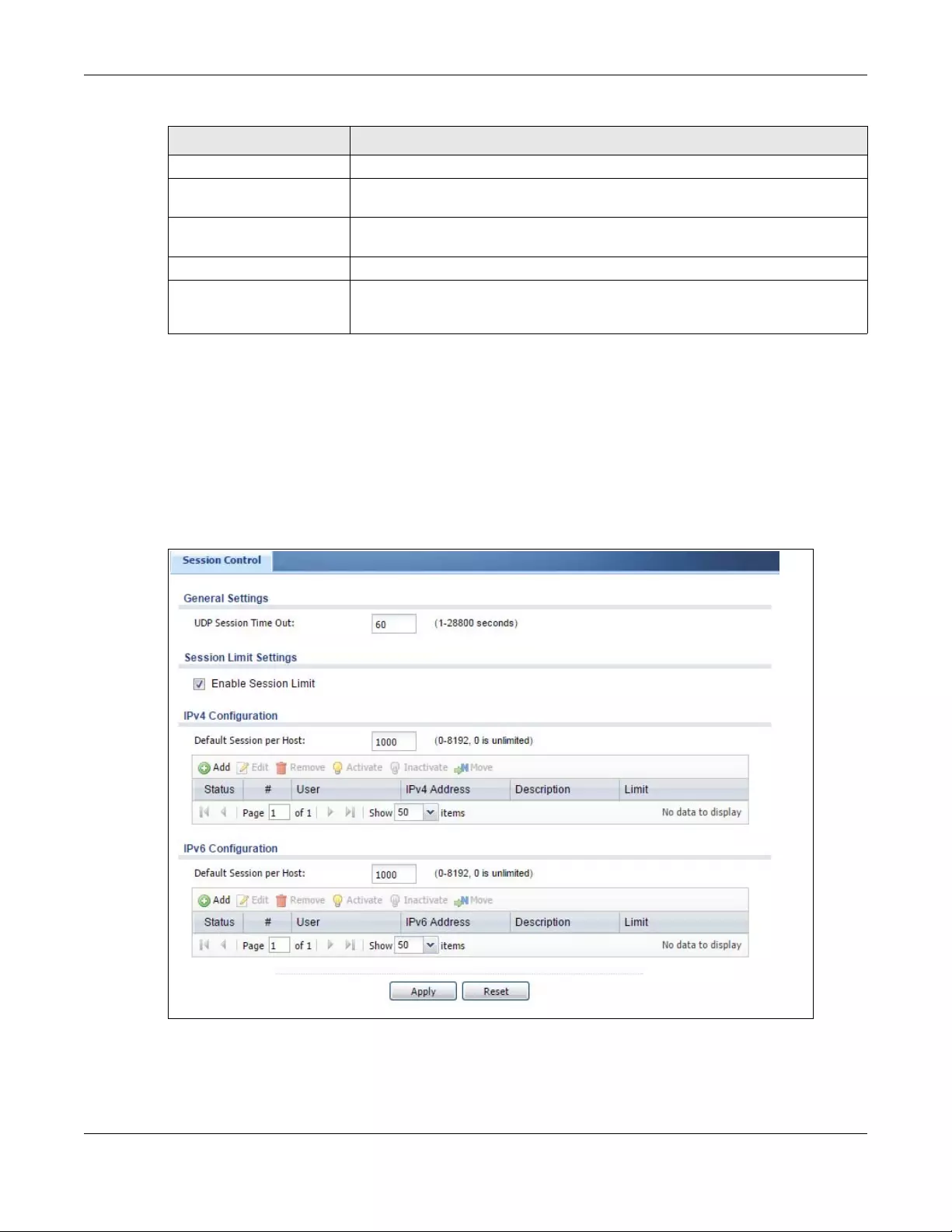
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
534
28.6 The Session Control Screen
Click Configuration > Security Policy > Session Control to display the Security Policy Session Control
screen. Use this screen to limit the number of concurrent NAT/Security Policy sessions a client can use.
You can apply a default limit for all users and individual limits for specific users, addresses, or both. The
individual limit takes priority if you apply both.
Figure 380 Configuration > Security Policy > Session Control
Log These are the log options. To edit this, select an item and use the Log icon.
Action This is the action the Zyxel Device should take when a packet matches a policy. To
edit this, select an item and use the Action icon.
OK Click OK to save your settings to the Zyxel Device, complete the profile and return to
the profile summary page.
Cancel Click Cancel to return to the profile summary page without saving any changes.
Save Click Save to save the configuration to the Zyxel Device but remain in the same
page. You may then go to the another profile screen (tab) in order to complete the
profile. Click OK in the final profile screen to complete the profile.
Table 202 Configuration > Security Policy > ADP > Profile > Add-Protocol-Anomaly
LABEL DESCRIPTION
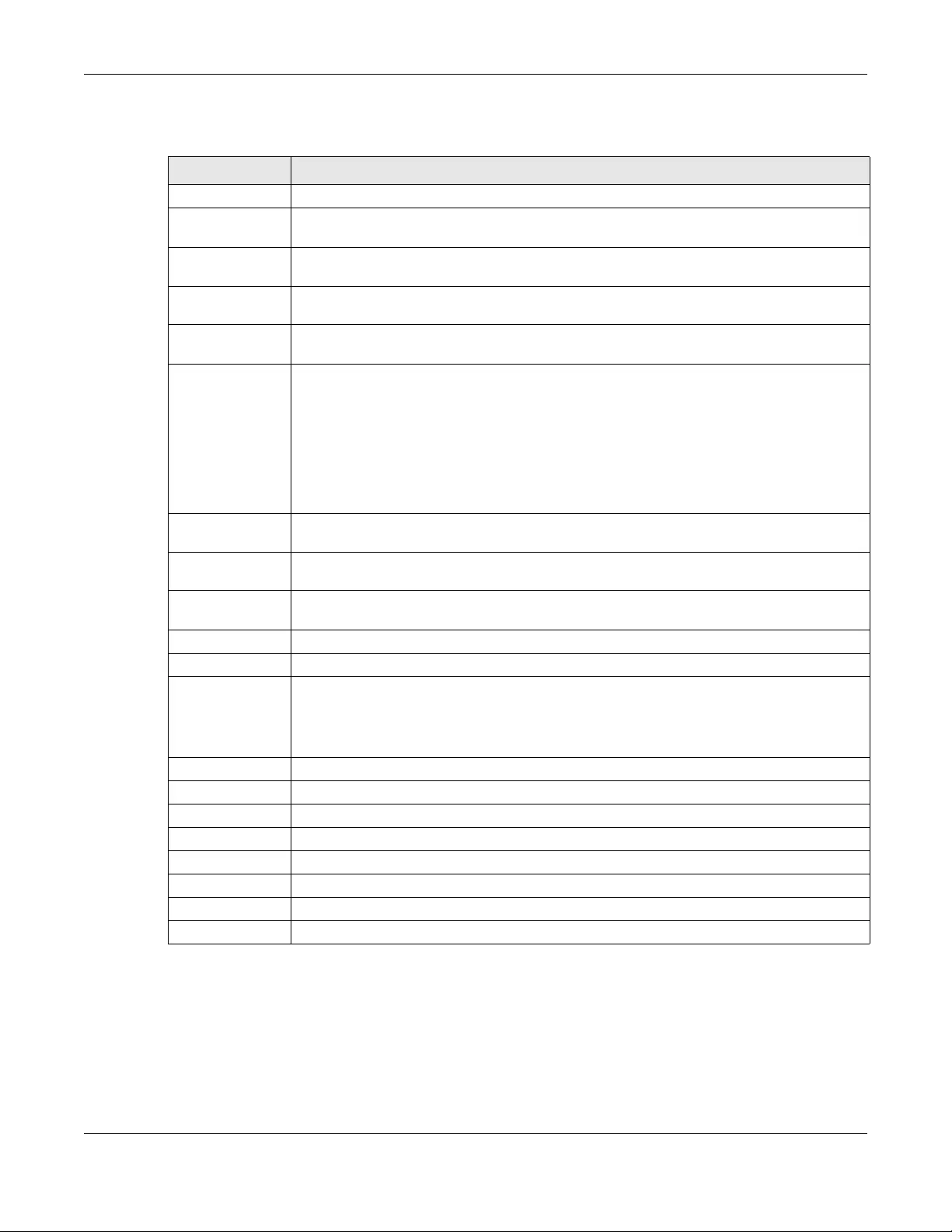
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
535
The following table describes the labels in this screen.
28.6.1 The Session Control Add/Edit Screen
Click Configuration > Security Policy > Ses sion Control and the Add or Edit icon to display the Add or Edit
screen. Use this screen to configure rules that define a session limit for specific users or addresses.
Table 203 Configuration > Security Policy > Session Control
LABEL DESCRIPTION
General Settings
UDP Session Time
Out
Set how many seconds the Zyxel Device will allow a UDP session to remain idle (without UDP
traffic) before closing it.
Session Limit
Settings
Enable Session
limit
Select this check box to control the number of concurrent sessions hosts can have.
IPv4 / IPv6 Rule
Summary
This table lists the rules for limiting the number of concurrent sessions hosts can have.
Default
Session per
Host
This field is configurable only when you enable session limit.
Use this field to set a common limit to the number of concurrent NAT/Security Policy sessions
each client computer can have.
If only a few clients use peer to peer applications, you can raise this number to improve their
performance. With heavy peer to peer application use, lower this number to ensure no single
client uses too many of the available NAT sessions.
Create rules below to apply other limits for specific users or addresses.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after the
selected entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Move To change a rule’s position in the numbered list, select the rule and click Move to display a field
to type a number for where you want to put that rule and press [ENTER] to move the rule to the
number that you typed.
The ordering of your rules is important as they are applied in order of their numbering.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
# This is the index number of a session limit rule. It is not associated with a specific rule.
User This is the user name or user group name to which this session limit rule applies.
IPv4 / IPv6 Address This is the IPv4 / IPv6 address object to which this session limit rule applies.
Description This is the information configured to help you identify the rule.
Limit This is how many concurrent sessions this user or address is allowed to have.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
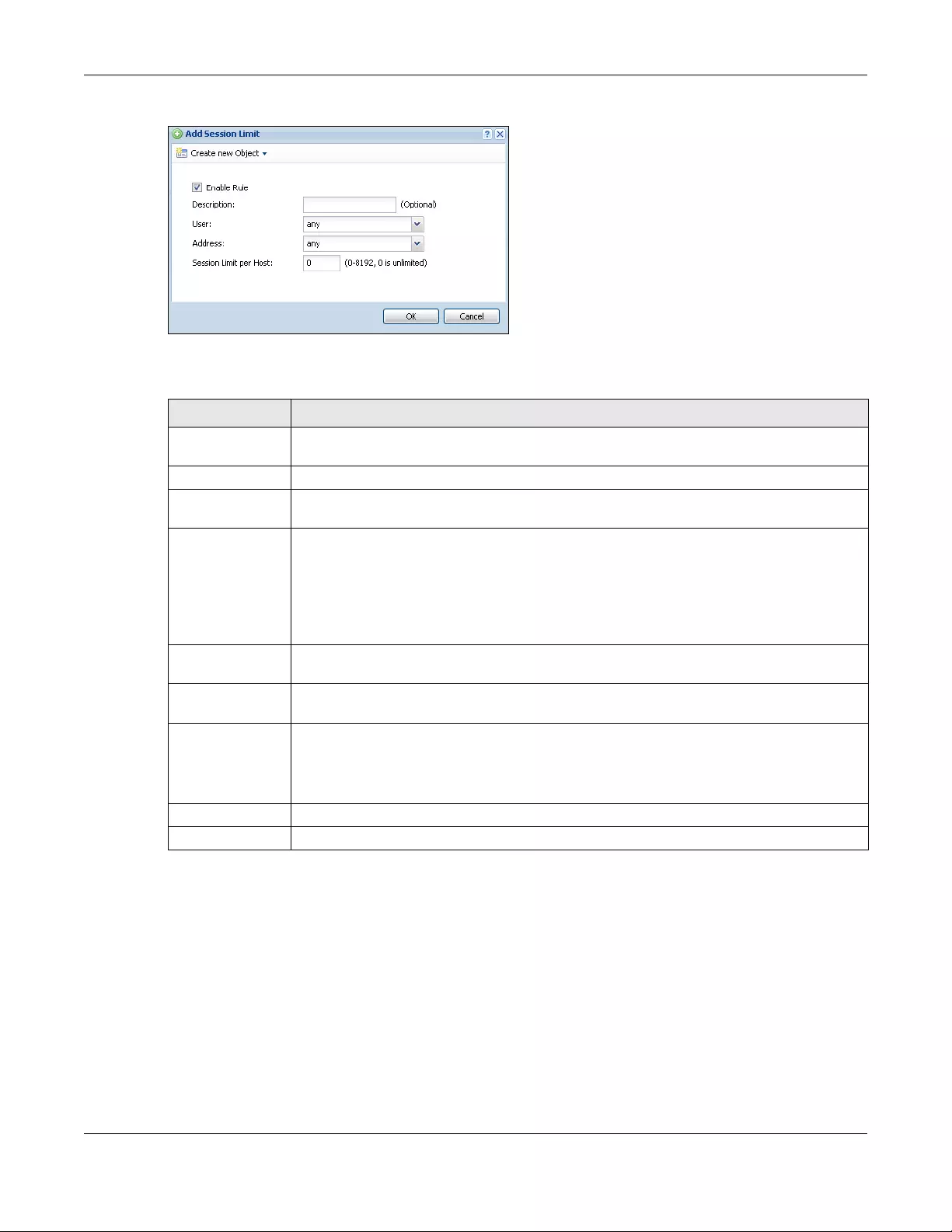
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
536
Figure 381 Configuration > Security Policy > Session Control > Edit
The following table describes the labels in this screen.
28.7 Security Policy Example Applications
Suppose you decide to block LAN users from using IRC (Internet Relay Chat) through the Internet. To do
this, you would configure a LAN to WAN Security Policy that blocks IRC traffic from any source IP address
from going to any destination address. You do not need to specify a schedule since you need the
Security Policy to always be in effect. The following figure shows the results of this policy.
Table 204 Configuration > Security Policy > Session Control > Add / Edit
LABEL DESCRIPTION
Create new
Object
Use to configure new settings for User or Address objects that you need to use in this
screen.Click on the down arrow to see the menu.
Enable Rule Select this check box to turn on this session limit rule.
Description Enter information to help you identify this rule. Use up to 60 printable ASCII characters. Spaces
are allowed.
User Select a user name or user group to which to apply the rule. The rule is activated only when the
specified user logs into the system and the rule will be disabled when the user logs out.
Otherwise, select any and there is no need for user logging.
Note: If you specified an IP address (or address group) instead of any in the field
below, the user’s IP address should be within the IP address range.
Address Select the IPv4 source address or address group to which this rule applies. Select any to apply
the rule to all IPv4 source addresses.
IPv6 Address Select the IPv6 source address or address group to which this rule applies. Select any to apply
the rule to all IPv6 source addresses.
Session Limit per
Host
Use this field to set a limit to the number of concurrent NAT/Security Policy sessions this rule’s
users or addresses can have.
For this rule’s users and addresses, this setting overrides the Default Session per Host setting in
the general Security Policy Session Control screen.
OK Click OK to save your customized settings and exit this screen.
Cancel Click Cancel to exit this screen without saving.
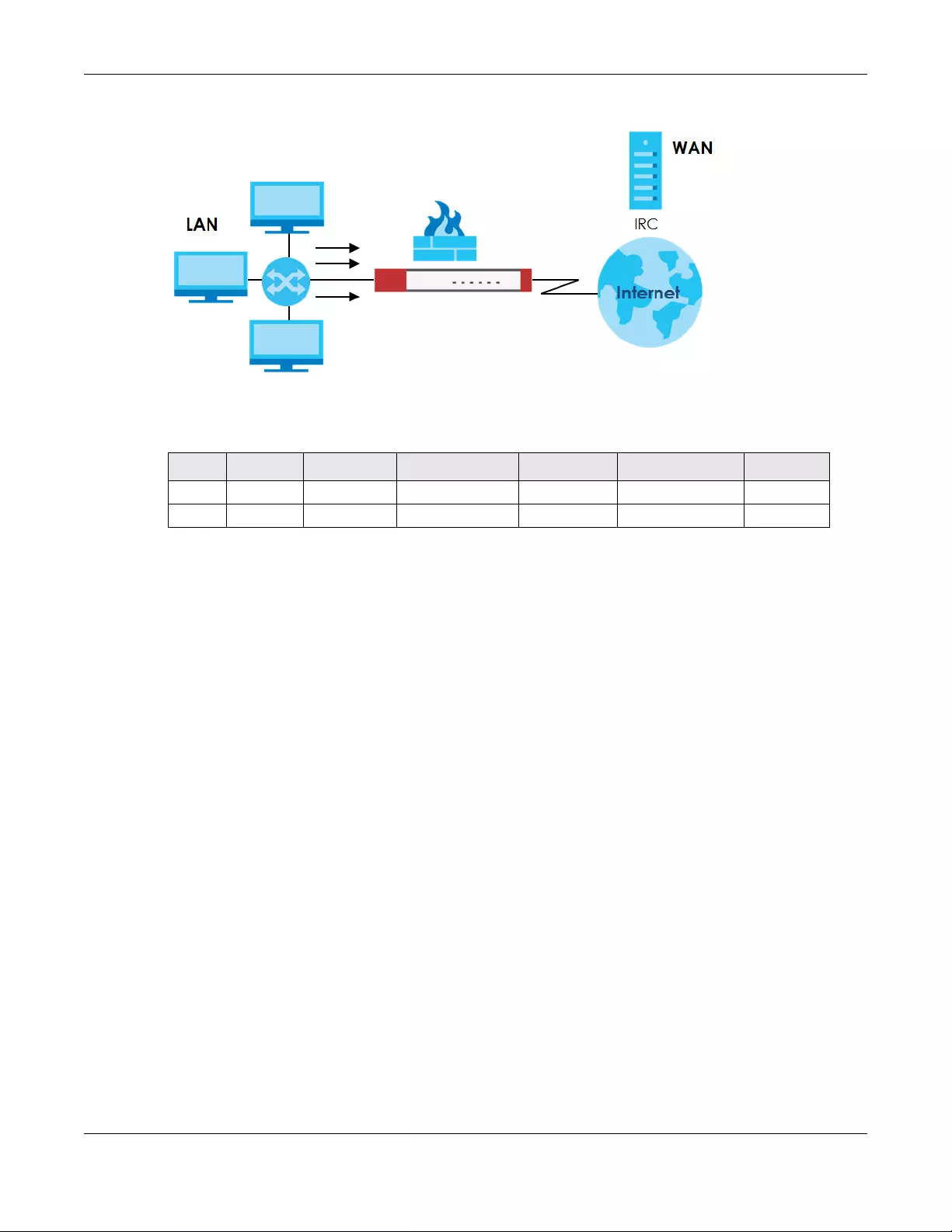
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
537
Figure 382 Blocking All LAN to WAN IRC Traffic Example
Your Security Policy would have the following settings.
• The first row blocks LAN access to the IRC service on the WAN.
• The second row is the Security Policy’s default policy that allows all LAN1 to WAN traffic.
The Zyxel Device applies the security policies in order. So for this example, when the Zyxel Device
receives traffic from the LAN, it checks it against the first policy. If the traffic matches (if it is IRC traffic)
the security policy takes the action in the policy (drop) and stops checking the subsequent security
policies. Any traffic that does not match the first security policy will match the second security policy
and the Zyxel Device forwards it.
Now suppose you need to let the CEO use IRC. You configure a LAN1 to WAN security policy that allows
IRC traffic from the IP address of the CEO’s computer. You can also configure a LAN to WAN policy that
allows IRC traffic from any computer through which the CEO logs into the Zyxel Device with his/her user
name. In order to make sure that the CEO’s computer always uses the same IP address, make sure it
either:
• Has a static IP address,
or
• You configure a static DHCP entry for it so the Zyxel Device always assigns it the same IP address.
Now you configure a LAN1 to WAN security policy that allows IRC traffic from the IP address of the CEO’s
computer (172.16.1.7 for example) to go to any destination address. You do not need to specify a
schedule since you want the security policy to always be in effect. The following figure shows the results
of your two custom policies.
Table 205 Blocking All LAN to WAN IRC Traffic Example
# USER SOURCE DESTINATION SCHEDULE UTM PROFILE ACTION
1 Any Any Any Any IRC Deny
2 Any Any Any Any Any Allow
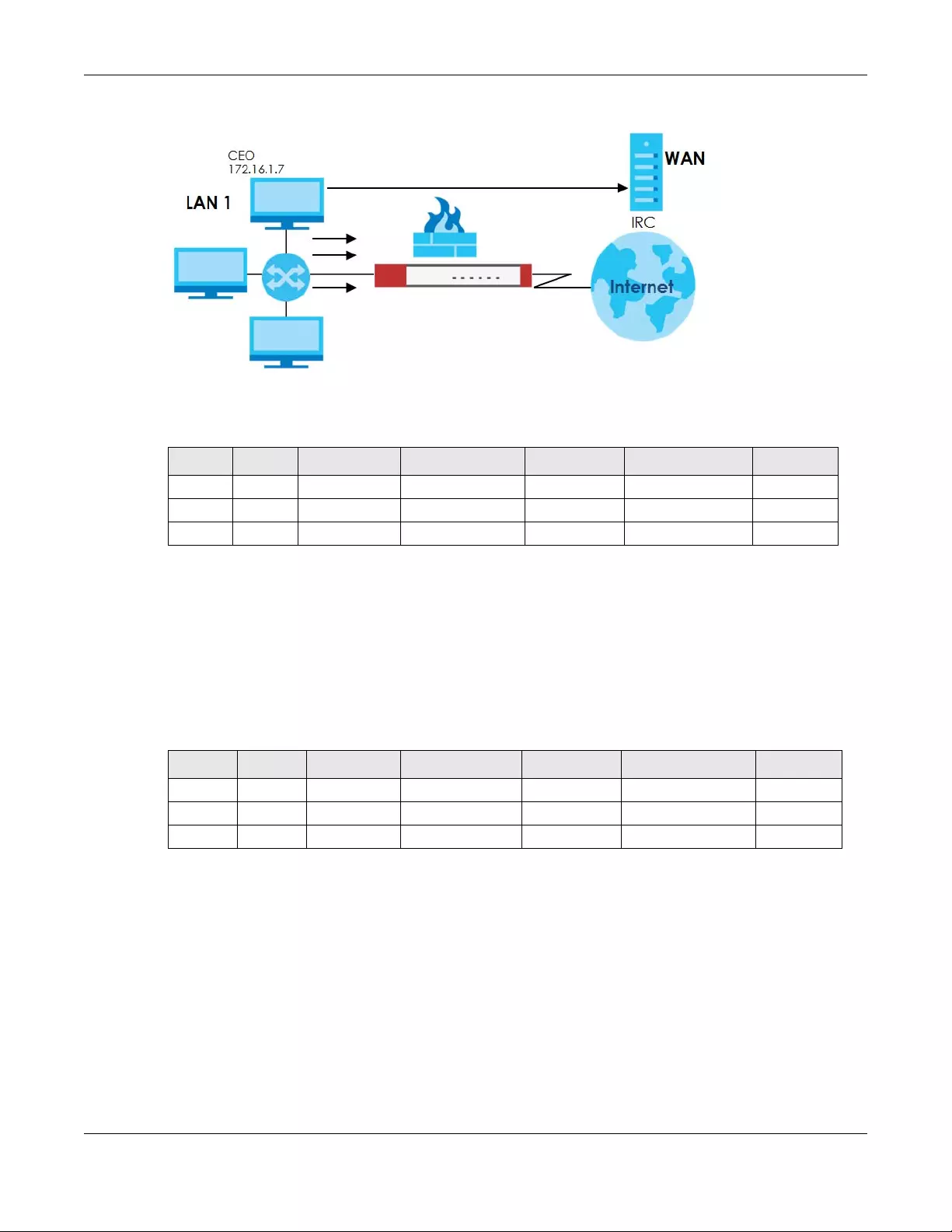
Chapter 28 Security Policy
USG/ZyWALL User’s Guide
538
Figure 383 Limited LAN to WAN IRC Traffic Example
Your security policy would have the following configuration.
• The first row allows the LAN1 computer at IP address 172.16.1.7 to access the IRC service on the WAN.
• The second row blocks LAN1 access to the IRC service on the WAN.
• The third row is the default policy of allowing all traffic from the LAN1 to go to the WAN.
Alternatively, you configure a LAN1 to WAN policy with the CEO’s user name (say CEO) to allow IRC
traffic from any source IP address to go to any destination address.
Your Security Policy would have the following settings.
• The first row allows any LAN1 computer to access the IRC service on the WAN by logging into the Zyxel
Device with the CEO’s user name.
• The second row blocks LAN1 access to the IRC service on the WAN.
• The third row is the default policy of allowing allows all traffic from the LAN1 to go to the WAN.
The policy for the CEO must come before the policy that blocks all LAN1 to WAN IRC traffic. If the policy
that blocks all LAN1 to WAN IRC traffic came first, the CEO’s IRC traffic would match that policy and the
Zyxel Device would drop it and not check any other security policies.
Table 206 Limited LAN1 to WAN IRC Traffic Example 1
# USER SOURCE DESTINATION SCHEDULE UTM PROFILE ACTION
1 Any 172.16.1.7 Any Any IRC Allow
2 Any Any Any Any IRC Deny
3 Any Any Any Any Any Allow
Table 207 Limited LAN1 to WAN IRC Traffic Example 2
# USER SOURCE DESTINATION SCHEDULE UTM PROFILE ACTION
1 CEO Any Any Any IRC Allow
2 Any Any Any Any IRC Deny
3 Any Any Any Any Any Allow

USG/ZyWALL User’s Guide
539
CHAPTER 29
Cloud CNM
29.1 Cloud CNM Overview
You need licenses to use Cloud CNM SecuManager and Cloud CNM SecuReporter. You need the
SecuManager license to get a CNM ID with which you can access the SecuManager server. It is
independent from the Zyxel Devices. The SecuReporter license must be activated on each Zyxel Device.
29.1.1 What You Can Do in this Chapter
• Use the Cloud CNM > SecuManager screen (Section 29.2 on page 539) to enable and configure
management of the Zyxel Device by a Central Network Management system.
• Use the Cloud CNM > SecuReporter screen (Section 29.3 on page 542) to enable SecuReporter
logging on your Zyxel Device, see license status, type, expiration date and access a link to the
SecuReporter web portal. The SecuReporter web portal collects and analyzes logs from your Zyxel
Device in order to identify anomalies, alert on potential internal / external threats, and report on
network usage.
29.2 Cloud CNM SecuManager
Cloud CNM SecuManager is a Virtual Machine-based (VM) management system that uses the TR-069
protocol to encapsulate commands to ZyWALL/USG devices for management and monitoring; these
devices must have firmware that supports the TR-069 protocol.
In the following figure, SP is the management service provider, while A and B are sites with devices being
managed by SP.
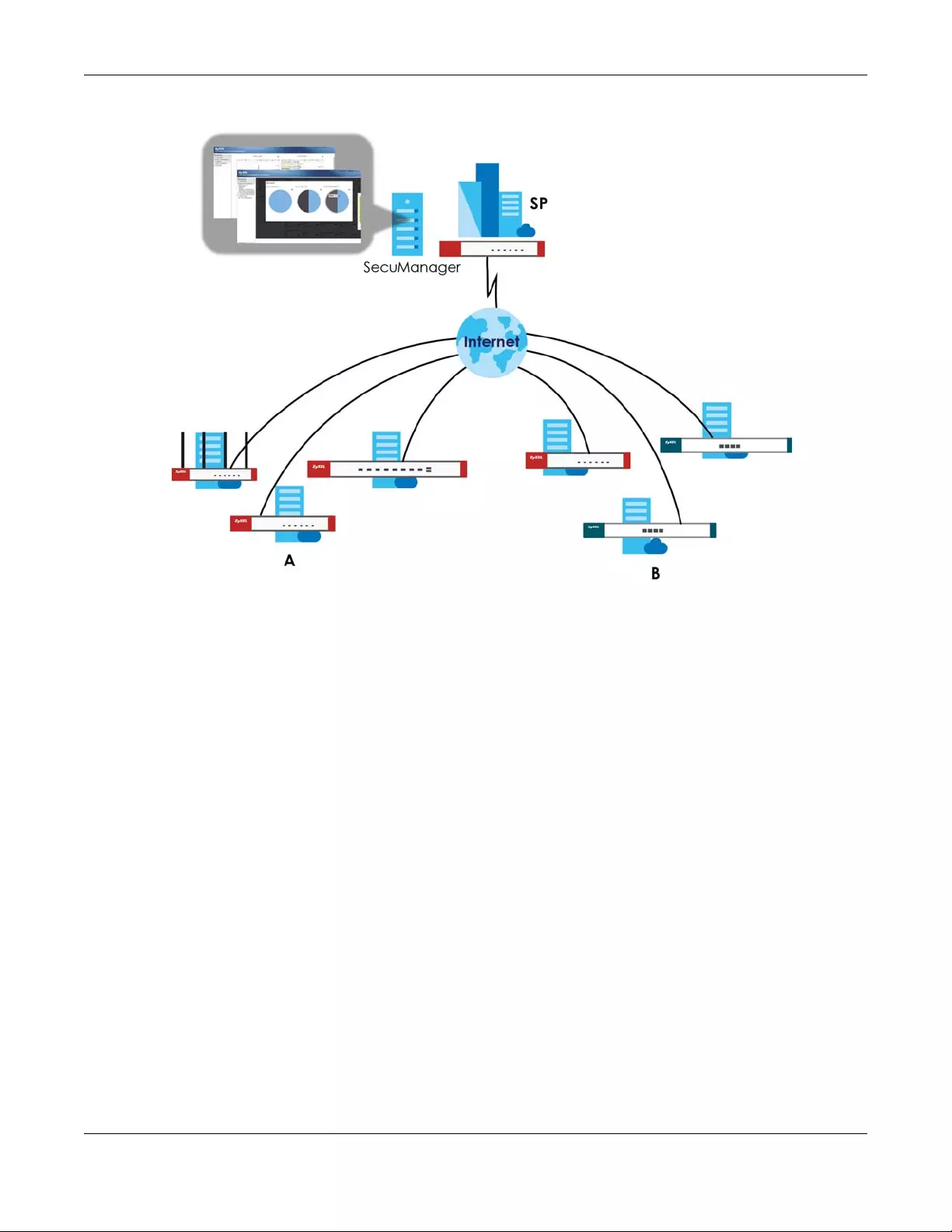
Chapter 29 Cloud CNM
USG/ZyWALL User’s Guide
540
Figure 384 Cloud CNM SecuManager Example Network Topology
Cloud CNM SecuManager features include:
• Batch import of managed devices at one time using one CSV file
• See an overview of all managed devices and system information in one place
• Monitor and manage devices
• Install firmware to multiple devices of the same model at one time
• Backup and restore device configuration
• View the location of managed devices on a map
• Receive notification for events and alarms, such as when a device goes down
• Graphically monitor individual devices and see related statistics
• Directly access a device for remote configuration
• Create four types of administrators with different privileges
• Perform Site-to-Site, Hub & Spoke, Fully-meshed and Remote Access VPN provisioning.
To allow Cloud CNM SecuManager management of your Zyxel Device:
• You must have a Cloud CNM SecuManager license with CNM ID number or a Cloud CNM
SecuManager server URL.
• The Zyxel Device must be able to communicate with the Cloud CNM SecuManager server.
You must configure Configuration > Cloud CNM > SecuManager to allow the Zyxel Device to find the
Cloud CNM SecuManager server.
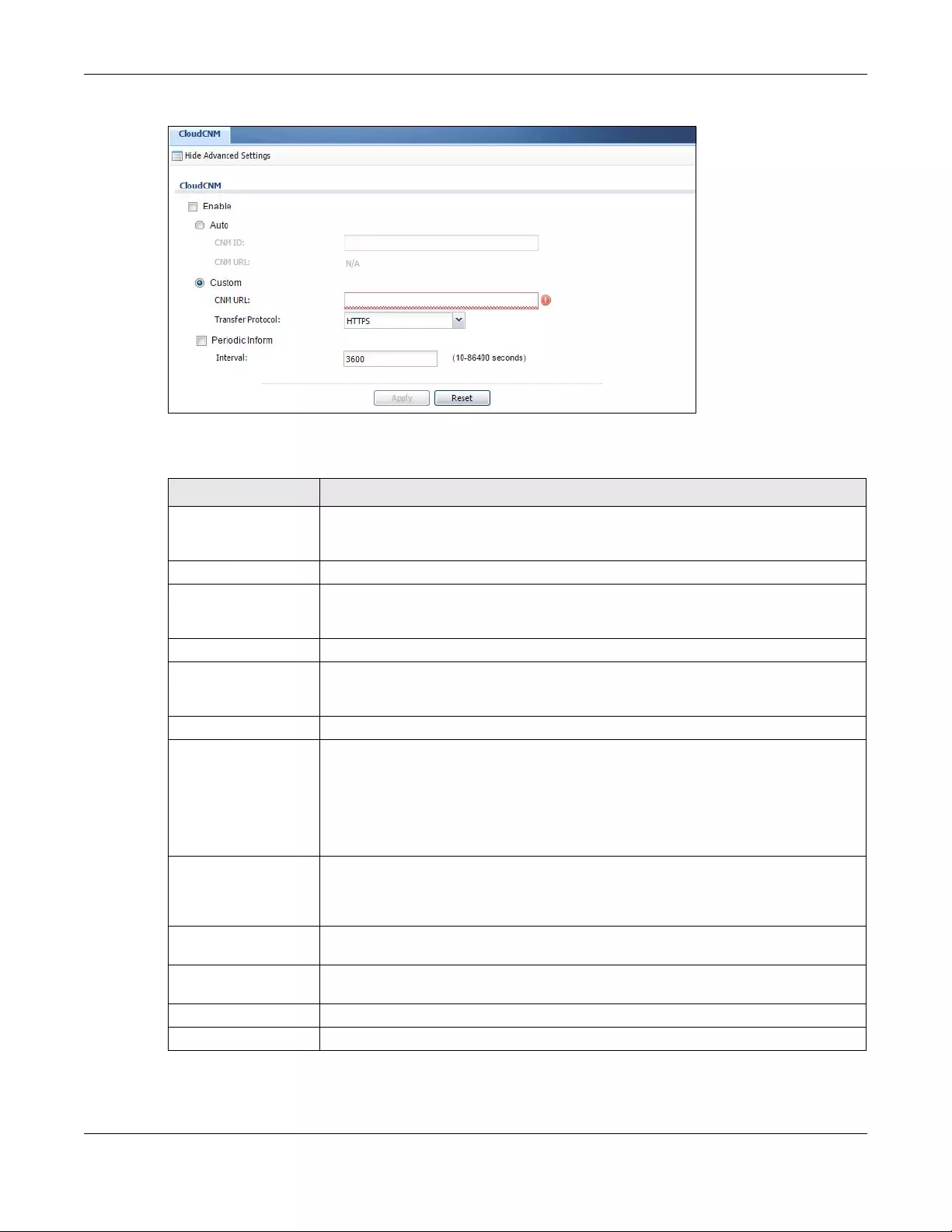
Chapter 29 Cloud CNM
USG/ZyWALL User’s Guide
541
Figure 385 Configuration > Cloud CNM > SecuManager
The following table describes the labels in this screen.
Note: See the Cloud CNM SecuManager User’s Guide for more information on Cloud CNM
SecuManager.
Table 208 Configuration > Cloud CNM > SecuManager
LABEL DESCRIPTION
Show Advanced
Settings / Hide
Advanced Settings
Click this button to display a greater or lesser number of configuration fields.
Enable Select this to allow management of the Zyxel Device by Cloud CNM SecuManager.
Auto Select this if your Cloud CNM SecuManager server can access MyZyxel.com to
automatically get the VM server URL from myZyxel.com. You also need CNM ID from the
Cloud CNM SecuManager license.
CNM ID Enter the CNM ID exactly as on the Cloud CNM SecuManager license.
CNM URL MyZyxel.com associates the CNM ID with the CNM URL which identifies the server on
which Cloud CNM SecuManager is installed. Therefore you don’t need to enter the CNM
URL when you select Auto.
Custom Select this if your Cloud CNM SecuManager server cannot access MyZyxel.com.
CNM URL Select this if your VM server or Zyxel Device are in a private network, or if the VM server is
behind a NAT router. You then need to manually enter the VM server URL into the Zyxel
Device. Enter the IPv4 IP address of the Cloud CNM SecuManager server followed by the
port number (default 7547 for HTTPS or 7549 for HTPP) followed by the CNM ID from the
license in CNM URL. For example, if you installed Cloud CNM SecuManager on a server
with IP address 1.1.1.1 and CNM ID V6ABQNTPYGD, then type 1.1.1.1:7547/
V6ABQNTPYG or 1.1.1.1:7549/V6ABQNTPYG as the CNM URL.
Transfer Protocol Choose the CNM URL protocol: HTTP or HTTPS. If you enter 1.1.1.1:7547 as the CNM URL,
you must choose HTTPS as the Transfer Protocol, and then the whole CNM URL is https://
1.1.1.1:7547. If you enter 1.1.1.1:7549 as the CNM URL, you must choose HTTP as the
Transfer Protocol, and then the whole CNM URL is http://1.1.1.1:7549.
Periodic Inform Enable this to have the Zyxel Device inform the Cloud CNM SecuManager server of its
presence at regular intervals.
Interval Type how often the Zyxel Device should inform Cloud CNM SecuManager server of its
presence.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
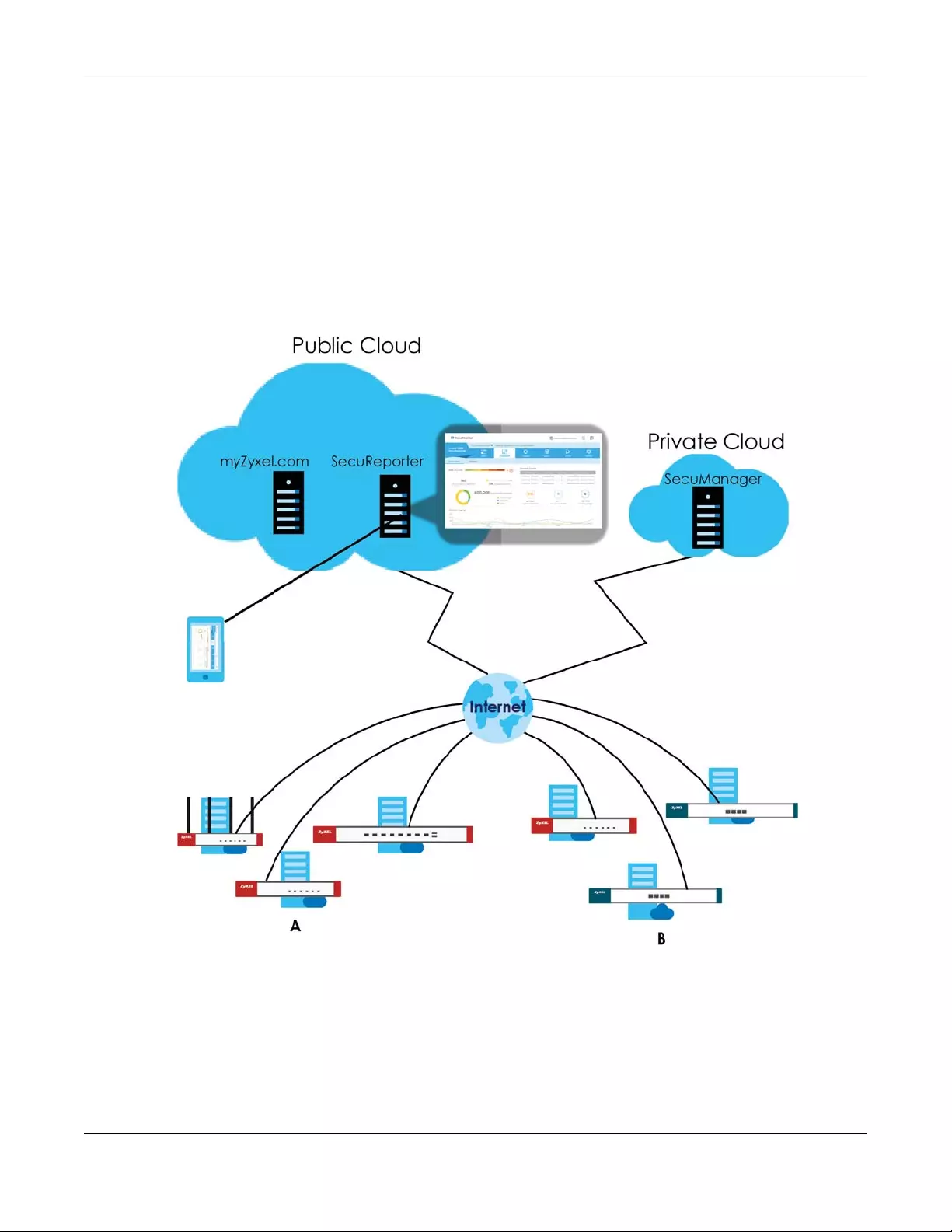
Chapter 29 Cloud CNM
USG/ZyWALL User’s Guide
542
29.3 Cloud CNM SecuReporter
Cloud CNM SecuReporter is a security analytics portal that collects and analyzes logs from
SecuReporter-licensed Zyxel Devices in order to identify anomalies, alert on potential internal / external
threats, and report on network usage. You need to buy a license for SecuReporter for your Zyxel Device
and register it at myZyxel.com. You must be a registered user at myZyXEL.com.
You can access the portal from a web browser and also get notifications sent to an app on your mobile
phone.
Figure 386 Cloud CNM SecuReporter Application Scenario
Your SecuReporter license displays in Configuration > Licensing > Registration > Service after you
purchase a license and register it at myZyxel.com. The Zyxel Device must be able to communicate with
the myZyxel.com server.
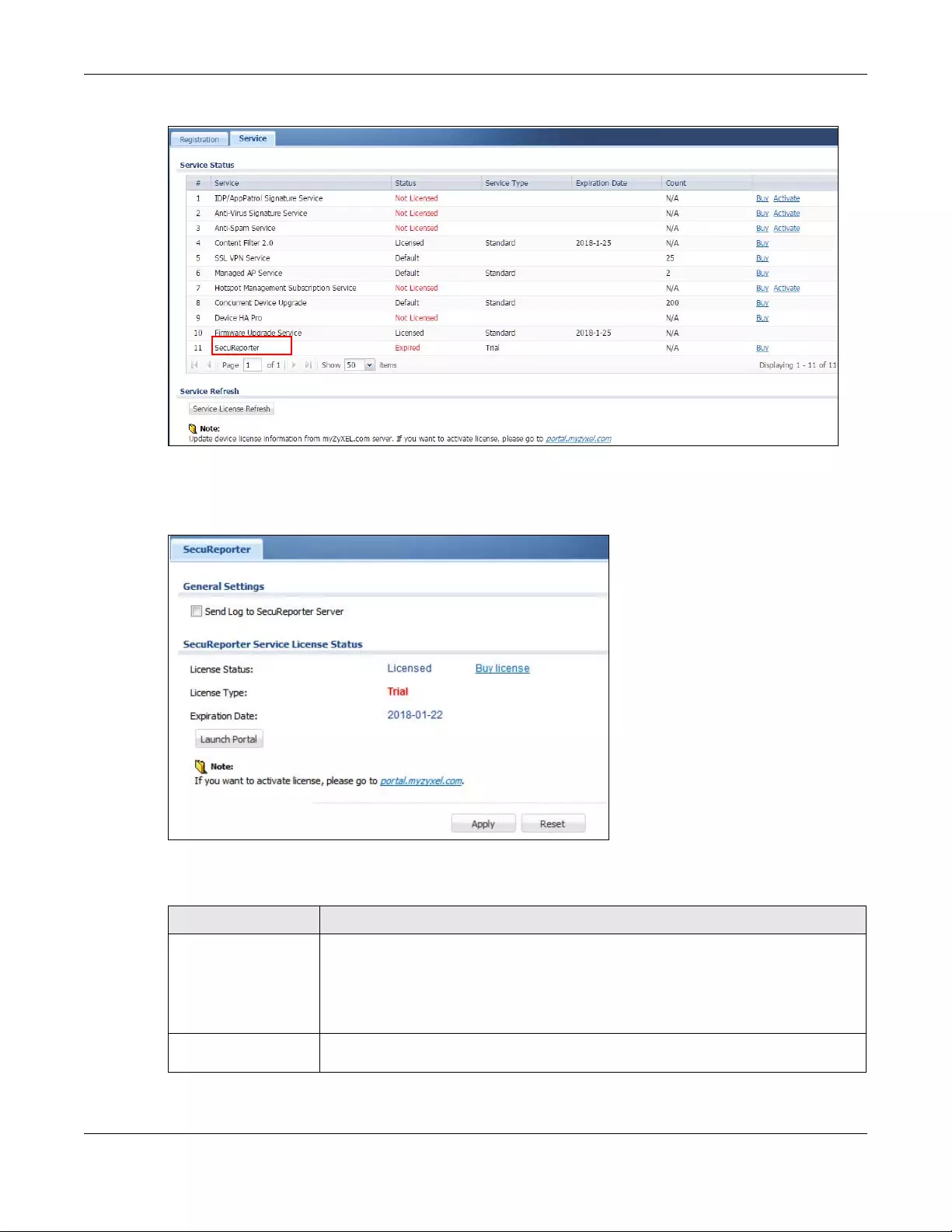
Chapter 29 Cloud CNM
USG/ZyWALL User’s Guide
543
Figure 387 Configuration > Licensing > Registration > Service
Click Configuration > Cloud CNM > SecuReporter to enable SecuReporter logging on your Zyxel Device,
see license status, type, expiration date and access a link to the SecuReporter web portal.
Figure 388 Configuration > Cloud CNM > SecuReporter
The following table describes the labels in this screen.
Table 209 Configuration > Cloud CNM > SecuReporter
LABEL DESCRIPTION
Send Log to
SecuReporter Server
This must be selected to have SecuReporter collect and analyze logs from this Zyxel
Device.
• It’s selected by default if you have activated a SecuReporter Standard license,
• You need to select this if you have a SecuReporter Trial license.
• This field is not available if you do not have a SecuReporter license.
License Status This field displays whether this service is activated (Licensed) at myZyxel.com or not (Not
Licensed) or expired (Expired).
Chapter 29 Cloud CNM
USG/ZyWALL User’s Guide
544
License Type This field displays whether you applied for a trial application (Trial) or registered this
service with your iCard’s PIN number (Standard). This field is blank when the service is not
activated.
Expiration Date This field displays the date your service expires.
Launch Portal Click this to go to the SecuReporter security analytics portal.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 209 Configuration > Cloud CNM > SecuReporter (continued)
LABEL DESCRIPTION

USG/ZyWALL User’s Guide
545
CHAPTER 30
IPSec VPN
30.1 Virtual Private Networks (VPN) Overview
A virtual private network (VPN) provides secure communications between sites without the expense of
leased site-to-site lines. A secure VPN is a combination of tunneling, encryption, authentication, access
control and auditing. It is used to transport traffic over the Internet or any insecure network that uses
TCP/IP for communication.
IPSec VPN
Internet Protocol Security (IPSec) VPN connects IPSec routers or remote users using IPSec client software.
This standards-based VPN offers flexible solutions for secure data communications across a public
network. IPSec is built around a number of standardized cryptographic techniques to provide
confidentiality, data integrity and authentication at the IP layer. The Zyxel Device can also combine
multiple IPSec VPN connections into one secure network. Here local Zyxel Device X uses an IPSec VPN
tunnel to remote (peer) Zyxel Device Y to connect the local (A) and remote (B) networks.
Figure 389 IPSec VPN Example
Internet Key Exchange (IKE): IKEv1 and IKEv2
The Zyxel Device supports IKEv1 and IKEv2 for IPv4 and IPv6 traffic. IKE (Internet Key Exchange) is a
protocol used in setting up security associations that allows two parties to send data securely.
IKE uses certificates or pre-shared keys for authentication and a Diffie–Hellman key exchange to set up
a shared session secret from which encryption keys are derived. A security policy for each peer must be
manually created.
IPSec VPN consists of two phases: Phase 1 and Phase 2. Phase 1's purpose is to establish a secure
authenticated communication channel by using the Diffie–Hellman key exchange algorithm to
generate a shared secret key to encrypt IKE communications. This negotiation results in one single bi-
directional ISAKMP Security Association (SA). The authentication can be performed using either pre-
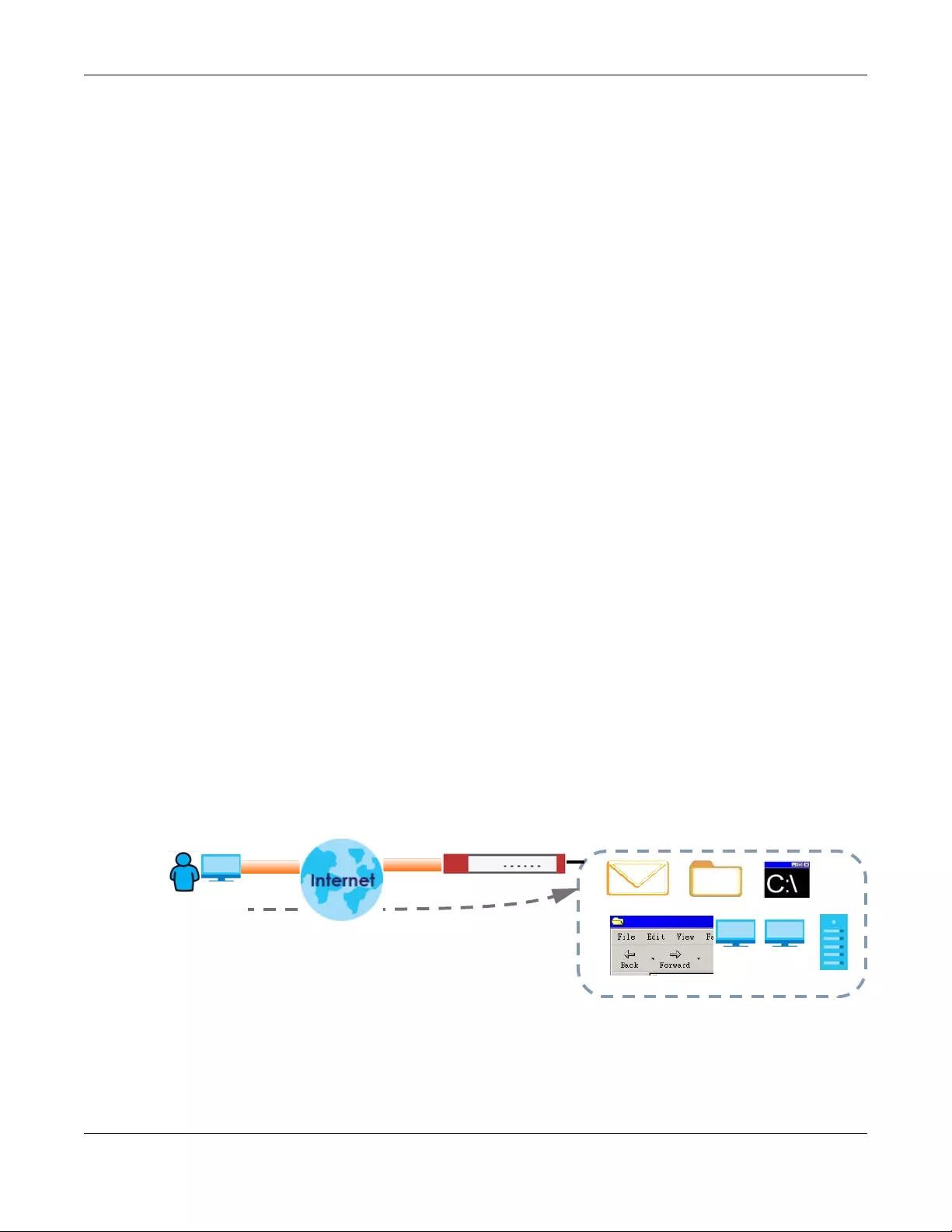
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
546
shared key (shared secret), signatures, or public key encryption. Phase 1 operates in either Main Mode
or Aggressive Mode. Main Mode protects the identity of the peers, but Aggressive Mode does not.
During Phase 2, the remote IPSec routers use the secure channel established in Phase 1 to negotiate
Security Associations for IPSec. The negotiation results in a minimum of two unidirectional security
associations (one inbound and one outbound). Phase 2 uses Quick Mode (only). Quick mode occurs
after IKE has established the secure tunnel in Phase 1. It negotiates a shared IPSec policy, derives shared
secret keys used for the IPSec security algorithms, and establishes IPSec SAs. Quick mode is also used to
renegotiate a new IPSec SA when the IPSec SA lifetime expires.
In the Zyxel Device, use the VPN Connection tab to set up Phase 2 and the VPN Gateway tab to set up
Phase 1.
Some differences between IKEv1 and IKEv2 include:
• IKEv2 uses less bandwidth than IKEv1. IKEv2 uses one exchange procedure with 4 messages. IKEv1 uses
two phases with Main Mode (9 messages) or Aggressive Mode (6 messages) in phase 1.
• IKEv2 supports Extended Authentication Protocol (EAP) authentication, and IKEv1 supports X-Auth.
EAP is important when connecting to existing enterprise authentication systems.
• IKEv2 always uses NAT traversal and Dead Peer Detection (DPD), but they can be disabled in IKEv1
using Zyxel Device firmware (the default is on).
• Configuration payload (includes the IP address pool in the VPN setup data) is supported in IKEv2 (off
by default), but not in IKEv1.
• Narrowed is supported in IKEv2, but not in IKEv1. Narrowed has the SA apply only to IP addresses in
common between the Zyxel Device and the remote IPSec router.
• The IKEv2 protocol supports connectivity checks which is used to detect whether the tunnel is still up
or not. If the check fails (the tunnel is down), IKEv2 can re-establish the connection automatically. The
Zyxel Device uses firmware to perform connectivity checks when using IKEv1.
SSL VPN
SSL VPN uses remote users’ web browsers to provide the easiest-to-use of the Zyxel Device’s VPN
solutions. A user just browses to the Zyxel Device’s web address and enters his user name and password
to securely connect to the Zyxel Device’s network. Remote users do not need to configure security
settings. Here a user uses his browser to securely connect to network resources in the same way as if he
were part of the internal network. See Chapter 31 on page 581 for more on SSL VPN.
Figure 390 SSL VPN
Web Mail File Share
Web-based Application
https://
Application Server
Non-Web
LAN (192.168.1.X)
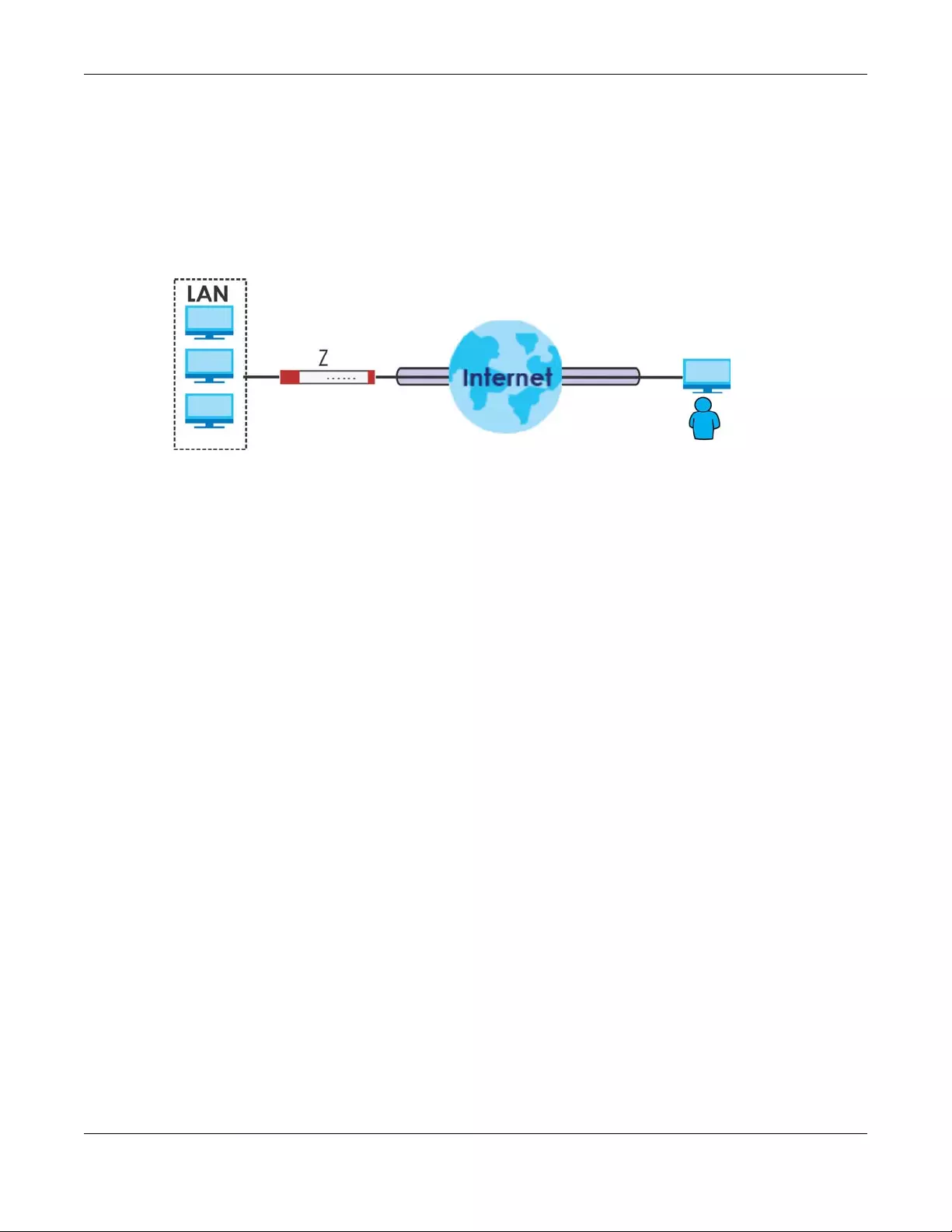
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
547
L2TP VPN
L2TP VPN uses the L2TP and IPSec client software included in remote users’ Android, iOS, or Windows
operating systems for secure connections to the network behind the Zyxel Device. The remote users do
not need their own IPSec gateways or third-party VPN client software. For example, configure sales
representatives’ laptops, tablets, or smartphones to securely connect to the Zyxel Device’s network. See
Chapter 34 on page 609 for more on L2TP over IPSec.
Figure 391 L2TP VPN
30.1.1 What You Can Do in this Chapter
• Use the VPN Connection screens (see Section 30.2 on page 550) to specify which IPSec VPN gateway
an IPSec VPN connection policy uses, which devices behind the IPSec routers can use the VPN tunnel,
and the IPSec SA settings (phase 2 settings). You can also activate or deactivate and connect or
disconnect each VPN connection (each IPSec SA).
• Use the VPN Gateway screens (see Section 30.2.1 on page 552) to manage the Zyxel Device’s VPN
gateways. A VPN gateway specifies the IPSec routers at either end of a VPN tunnel and the IKE SA
settings (phase 1 settings). You can also activate and deactivate each VPN gateway.
• Use the VPN Concentrator screens (see Section 30.4 on page 567) to combine several IPSec VPN
connections into a single secure network.
• Use the Configuration Provisioning screen (see Section 30.5 on page 569) to set who can retrieve VPN
rule settings from the Zyxel Device using the Zyxel Device IPSec VPN Client.
30.1.2 What You Need to Know
An IPSec VPN tunnel is usually established in two phases. Each phase establishes a security association
(SA), a contract indicating what security parameters the Zyxel Device and the remote IPSec router will
use. The first phase establishes an Internet Key Exchange (IKE) SA between the Zyxel Device and remote
IPSec router. The second phase uses the IKE SA to securely establish an IPSec SA through which the Zyxel
Device and remote IPSec router can send data between computers on the local network and remote
network. This is illustrated in the following figure.
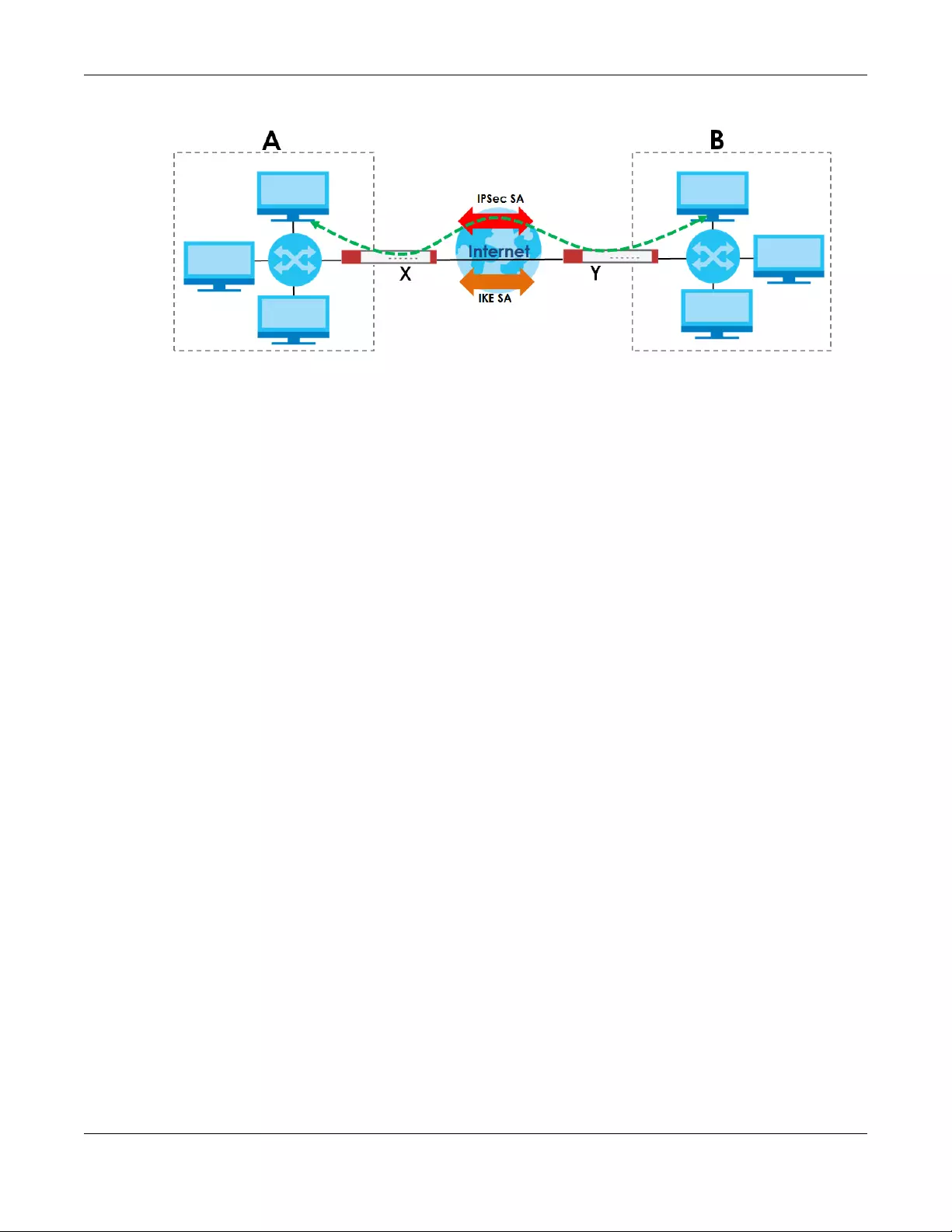
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
548
Figure 392 VPN: IKE SA and IPSec SA
In this example, a computer in network A is exchanging data with a computer in network B. Inside
networks A and B, the data is transmitted the same way data is normally transmitted in the networks.
Between routers X and Y, the data is protected by tunneling, encryption, authentication, and other
security features of the IPSec SA. The IPSec SA is secure because routers X and Y established the IKE SA
first.
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
549
Application Scenarios
The Zyxel Device’s application scenarios make it easier to configure your VPN connection settings.
Finding Out More
•See Section 30.6 on page 571 for IPSec VPN background information.
• See the help in the IPSec VPN quick setup wizard screens.
Table 210 IPSec VPN Application Scenarios
SITE-TO-SITE SITE-TO-SITE WITH
DYNAMIC PEER REMOTE ACCESS
(SERVER ROLE) REMOTE ACCESS
(CLIENT ROLE) VPN TUNNEL
INTERFACE
Choose this if the
remote IPSec router
has a static IP address
or a domain name.
This Zyxel Device can
initiate the VPN
tunnel.
The remote IPSec
router can also initiate
the VPN tunnel if this
Zyxel Device has a
static IP address or a
domain name.
Choose this if the
remote IPSec router has
a dynamic IP address.
You don’t specify the
remote IPSec router’s
address, but you specify
the remote policy (the
addresses of the devices
behind the remote
IPSec router).
This Zyxel Device must
have a static IP address
or a domain name.
Only the remote IPSec
router can initiate the
VPN tunnel.
Choose this to allow
incoming connections
from IPSec VPN clients.
The clients have
dynamic IP addresses
and are also known as
dial-in users.
You don’t specify the
addresses of the client
IPSec routers or the
remote policy.
This creates a dynamic
IPSec VPN rule that can
let multiple clients
connect.
Only the clients can
initiate the VPN tunnel.
Choose this to
connect to an
IPSec server.
This Zyxel Device is
the client (dial-in
user).
Client role Zyxel
Devices initiate
IPSec VPN
connections to a
server role Zyxel
Device.
This Zyxel Device
can have a
dynamic IP
address.
The IPSec server
doesn’t configure
this Zyxel Device’s
IP address or the
addresses of the
devices behind it.
Only this Zyxel
Device can initiate
the VPN tunnel.
Choose this to
set up a VPN
tunnel
interface to
bind with a
VPN
connection.
The Zyxel
Device can
use the
interface to do
load
balancing
using a specific
Trunk. The
remote IPSec
router should
have a static IP
address or a
domain name.

Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
550
30.1.3 Before You Begin
This section briefly explains the relationship between VPN tunnels and other features. It also gives some
basic suggestions for troubleshooting.
You should set up the following features before you set up the VPN tunnel.
• In any VPN connection, you have to select address objects to specify the local policy and remote
policy. You should set up the address objects first.
• In a VPN gateway, you can select an Ethernet interface, virtual Ethernet interface, VLAN interface, or
virtual VLAN interface to specify what address the Zyxel Device uses as its IP address when it
establishes the IKE SA. You should set up the interface first.
• In a VPN gateway, you can enable extended authentication. If the Zyxel Device is in server mode,
you should set up the authentication method (AAA server) first. The authentication method specifies
how the Zyxel Device authenticates the remote IPSec router.
• In a VPN gateway, the Zyxel Device and remote IPSec router can use certificates to authenticate
each other. Make sure the Zyxel Device and the remote IPSec router will trust each other’s
certificates.
30.2 The VPN Connection Screen
Click Configuration > VPN > IPSec VPN to open the VP N Connection screen. The VPN Connection screen
lists the VPN connection policies and their associated VPN gateway(s), and various settings. In addition,
it also lets you activate or deactivate and connect or disconnect each VPN connection (each IPSec
SA). Click a column’s heading cell to sort the table entries by that column’s criteria. Click the heading
cell again to reverse the sort order.
Click on the icons to go to the OneSecurity.com website where there is guidance on configuration
walkthroughs, troubleshooting and other information.
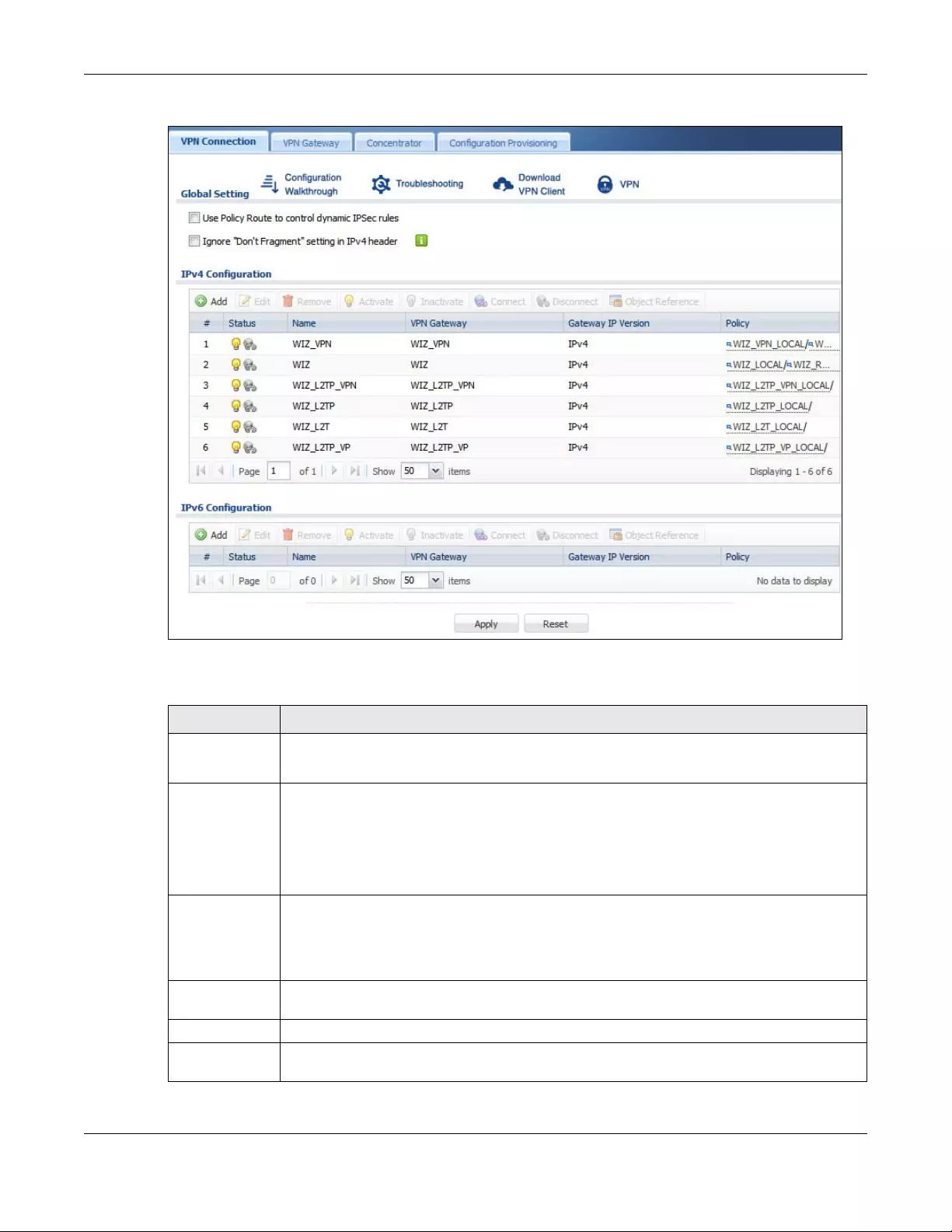
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
551
Figure 393 Configuration > VPN > IPSec VPN > VPN Connection
Each field is discussed in the following table.
Table 211 Configuration > VPN > IPSec VPN > VPN Connection
LABEL DESCRIPTION
Global Setting The following two fields are for all IPSec VPN policies.
Click on the VPN icon to go to the Zyxel VPN Client product page at the Zyxel website.
Use Policy
Route to
control
dynamic
IPSec rules
Select this to be able to use policy routes to manually specify the destination addresses of
dynamic IPSec rules. You must manually create these policy routes. The Zyxel Device
automatically obtains source and destination addresses for dynamic IPSec rules that do not
match any of the policy routes.
Clear this to have the Zyxel Device automatically obtain source and destination addresses for all
dynamic IPSec rules.
Ignore
“Don't
Fragment”
setting in
packet
header
Select this to fragment packets larger than the MTU (Maximum Transmission Unit) that have the
“Don't Fragment” bit in the IP header turned on. When you clear this the Zyxel Device drops
packets larger than the MTU that have the “Don't Fragment” bit in the header turned on.
IPv4 / IPv6
Configuration
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
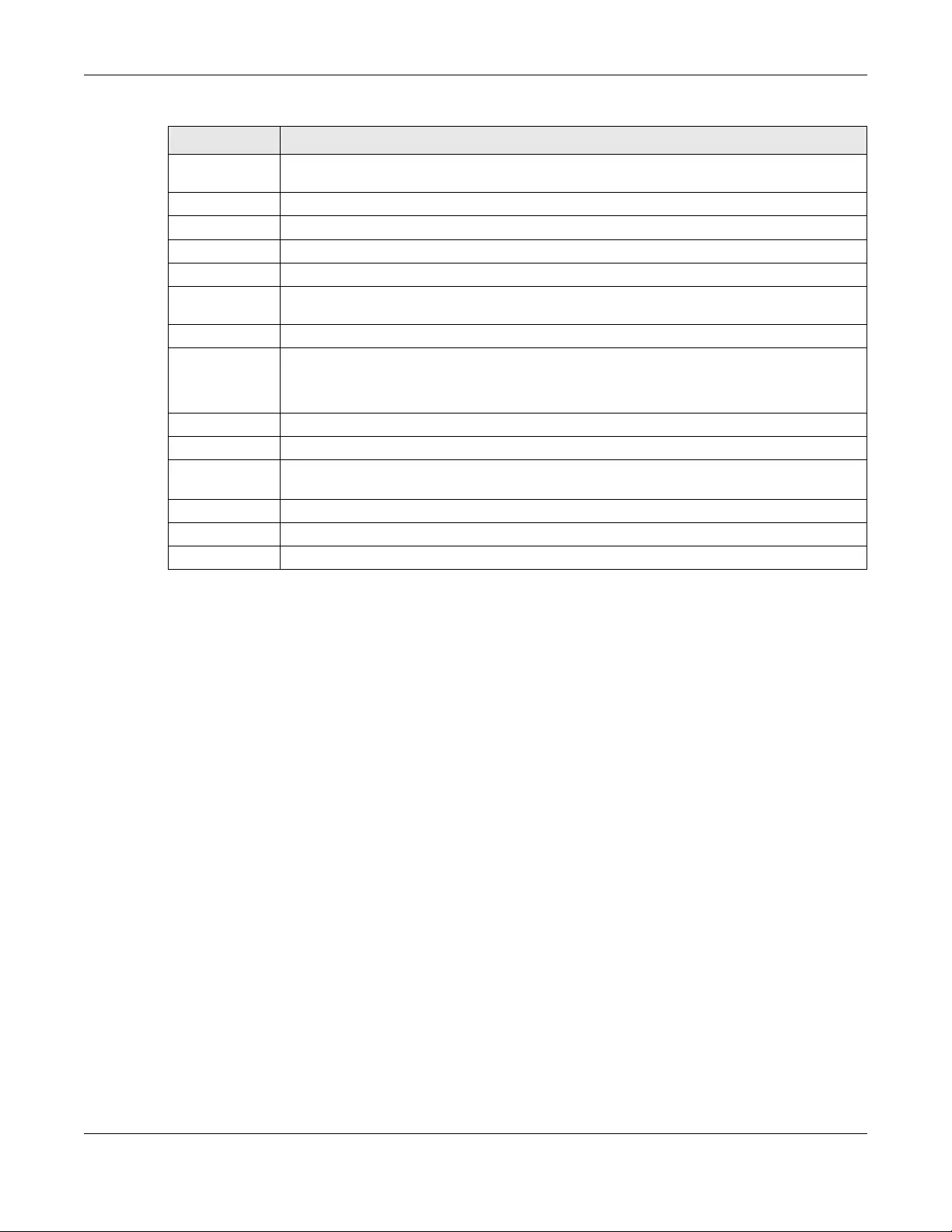
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
552
30.2.1 The VPN Connection Add/Edit Screen
The VPN Connection Add/Edit Gateway screen allows you to create a new VPN connection policy or
edit an existing one. To access this screen, go to the Configuration > VPN Connection screen (see
Section 30.2 on page 550), and click either the Add icon or an Edit icon.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove it
before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Connect To connect an IPSec SA, select it and click Connect.
Disconnect To disconnect an IPSec SA, select it and click Disconnect.
Object
Reference
Select an entry and click Object Reference to open a screen that shows which settings use the
entry. See Section 10.4.4 on page 294 for an example.
# This field is a sequential value, and it is not associated with a specific connection.
Status The activate (light bulb) icon is lit when the entry is active and dimmed when the entry is
inactive.
The connect icon is lit when the interface is connected and dimmed when it is disconnected.
Name This field displays the name of the IPSec SA.
VPN Gateway This field displays the VPN gateway in use for this VPN connection.
Gateway IP
Version
This field displays what IP version the associated VPN gateway(s) is using. An IPv4 gateway may
use an IKEv1 or IKEv2 SA. An IPv6 gateway may use IKEv2 only.
Policy This field displays the local policy and the remote policy, respectively.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 211 Configuration > VPN > IPSec VPN > VPN Connection (continued)
LABEL DESCRIPTION
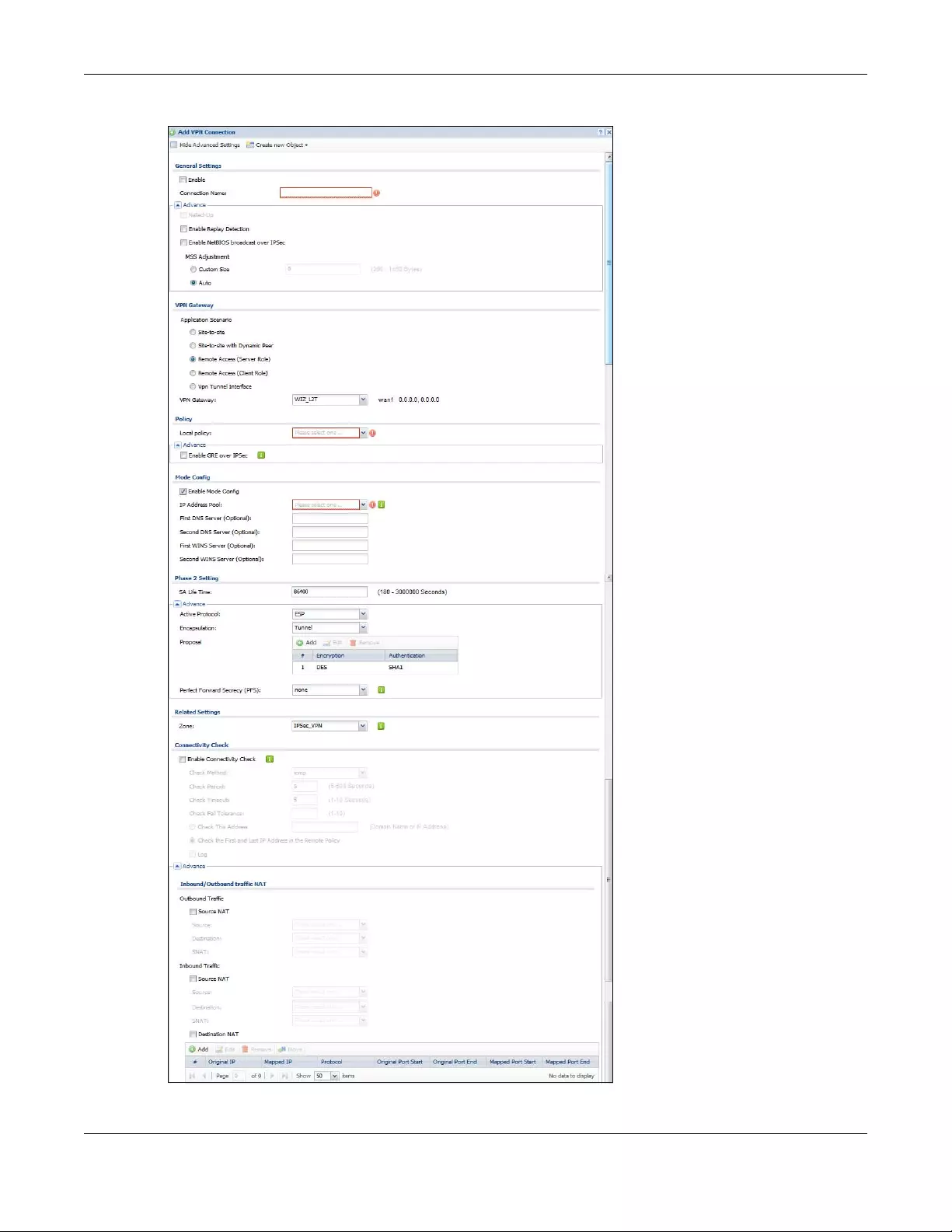
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
553
Figure 394 Configuration > VPN > IPSec VPN > VPN Connection > Add/Edit
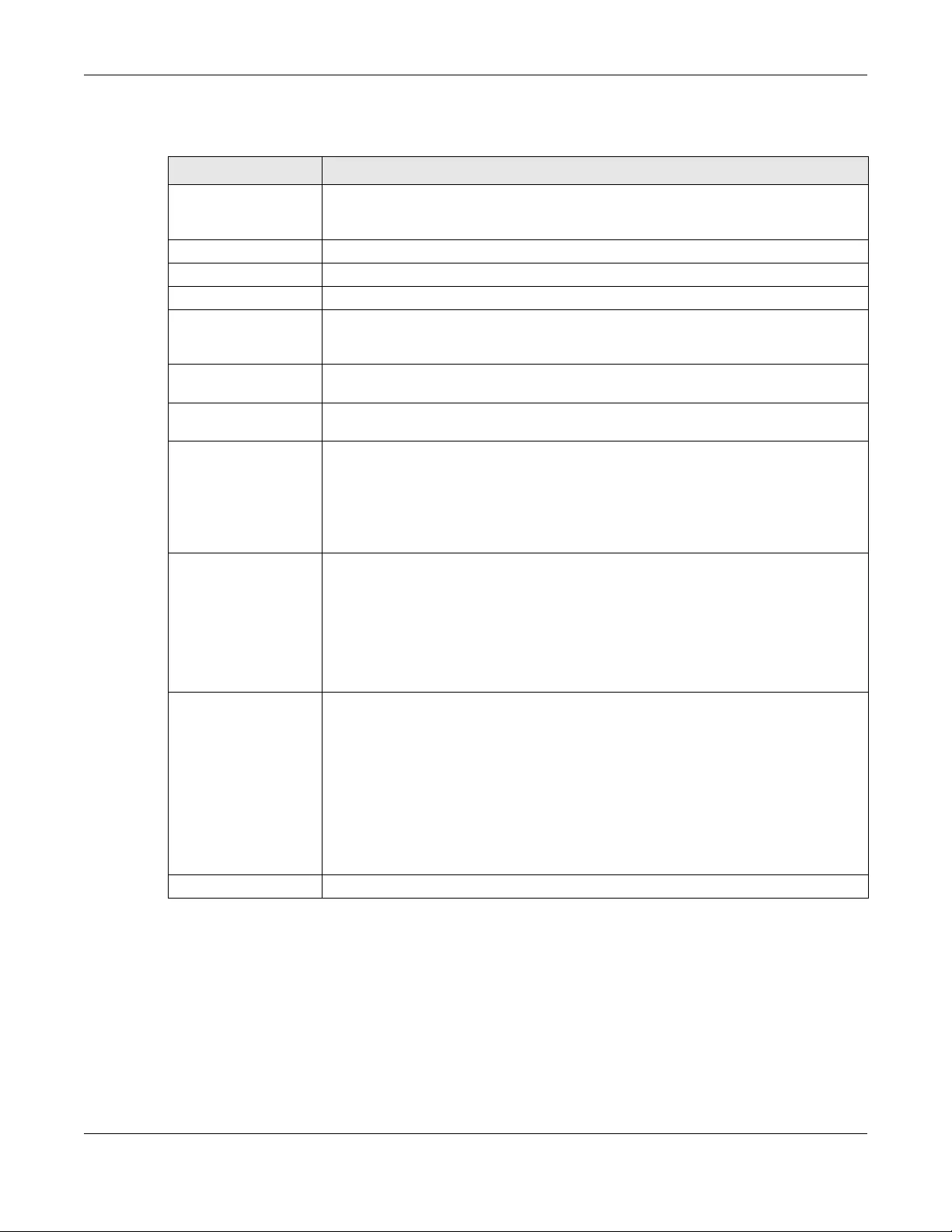
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
554
Each field is described in the following table.
Table 212 Configuration > VPN > IPSec VPN > VPN Connection > Add/Edit
LABEL DESCRIPTION
Show Advanced
Settings / Hide
Advanced Settings
Click this button to display a greater or lesser number of configuration fields.
Create new Object Use to configure any new settings objects that you need to use in this screen.
General Settings
Enable Select this check box to activate this VPN connection.
Connection Name Type the name used to identify this IPSec SA. You may use 1-31 alphanumeric characters,
underscores (_), or dashes (-), but the first character cannot be a number. This value is
case-sensitive.
Nailed-Up Select this if you want the Zyxel Device to automatically renegotiate the IPSec SA when
the SA life time expires.
Enable Replay
Detection Select this check box to detect and reject old or duplicate packets to protect against
Denial-of-Service attacks.
Enable NetBIOS
Broadcast over
IPSec
Select this check box if you the Zyxel Device to send NetBIOS (Network Basic Input/
Output System) packets through the IPSec SA.
NetBIOS packets are TCP or UDP packets that enable a computer to connect to and
communicate with a LAN. It may sometimes be necessary to allow NetBIOS packets to
pass through IPSec SAs in order to allow local computers to find computers on the remote
network and vice versa.
MSS Adjustment Select Custom Size to set a specific number of bytes for the Maximum Segment Size (MSS)
meaning the largest amount of data in a single TCP segment or IP datagram for this VPN
connection.
Some VPN clients may not be able to use a custom MSS size if it is set too small. In that
case those VPN clients will ignore the size set here and use the minimum size that they
can use.
Select Auto to have the Zyxel Device automatically set the MSS for this VPN connection.
Narrowed If the IP range on the Zyxel Device (local policy) and the local IP range on the remote
IPSec router overlap in an IKEv2 SA, then you may select Narrowed to have the SA only
apply to the IP addresses in common.
Here are some examples.
Zyxel Device (local policy) Remote IPSec router
IKEv2 SA-1 192.168.20.0/24 192.168.20.1 ~ 192.168.20.20
Narrowed 192.168.20.1 ~ 192.168.20.20
IKEv2 SA- 2 192.168.30.50 ~ 192.168.30.70 192.168.30.60 ~ 192.168.30.80
Narrowed 192.168.30.60 ~ 192.168.30.70
VPN Gateway
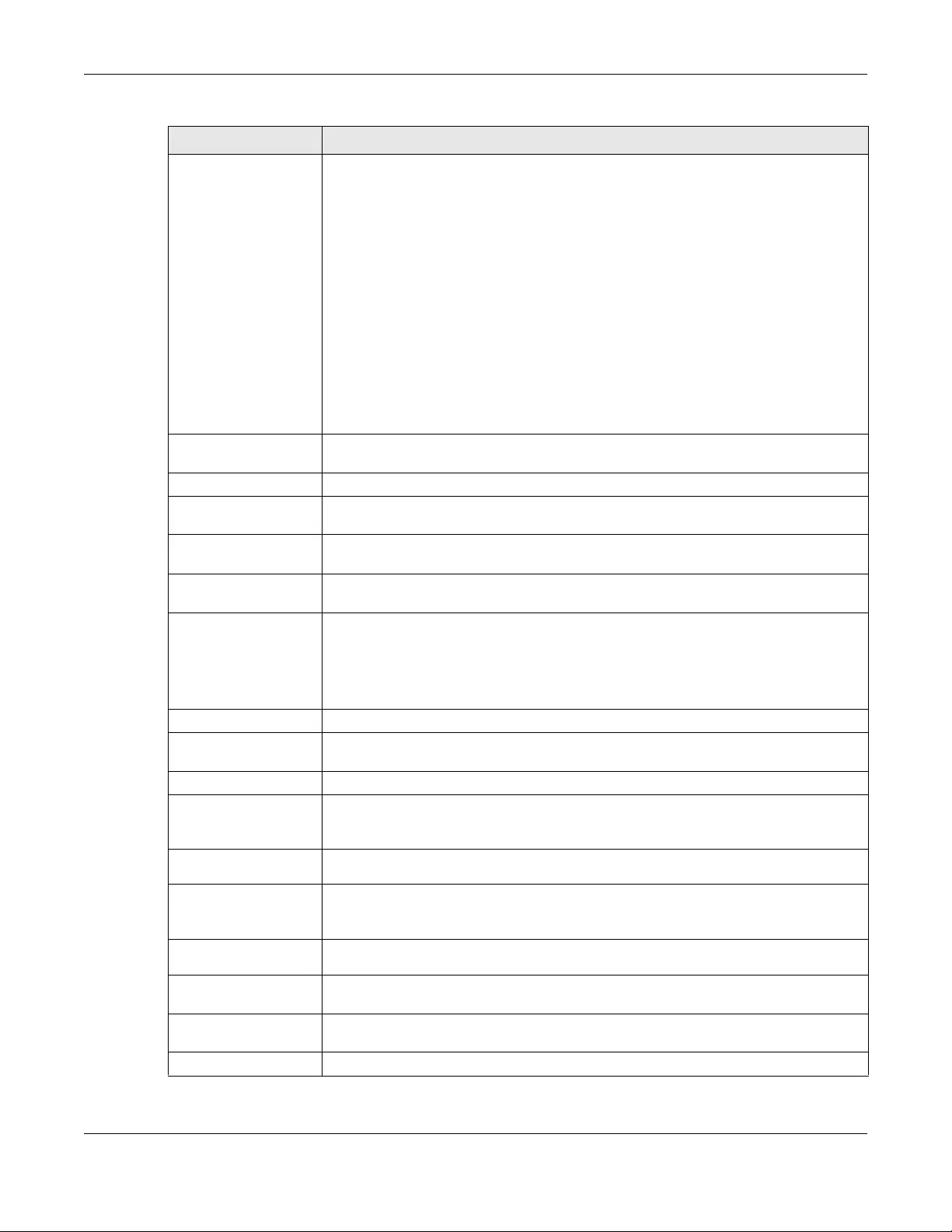
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
555
Application
Scenario Select the scenario that best describes your intended VPN connection.
Site-to-site - Choose this if the remote IPSec router has a static IP address or a domain
name. This Zyxel Device can initiate the VPN tunnel.
Site-to-site with Dynamic Peer - Choose this if the remote IPSec router has a dynamic IP
address. Only the remote IPSec router can initiate the VPN tunnel.
Remote Ac cess (Server Ro le) - Choose this to allow incoming connections from IPSec VPN
clients. The clients have dynamic IP addresses and are also known as dial-in users. Only
the clients can initiate the VPN tunnel.
Remote Access (Client Role) - Choose this to connect to an IPSec server. This Zyxel Device
is the client (dial-in user) and can initiate the VPN tunnel.
Vpn Tunnel Interface - Choose this to set up a VPN tunnel interface to bind with a VPN
connection. The Zyxel Device can use the interface to do load balancing using a specific
Trunk. The remote IPSec router should have a static IP address or a domain name. See
Configuration > Network > Interface > VTI.
VPN Gateway Select the VPN gateway this VPN connection is to use or select Create Object to add
another VPN gateway for this VPN connection to use.
Policy
Local Policy Select the address corresponding to the local network. Use Create new Object if you
need to configure a new one.
Remote Policy Select the address corresponding to the remote network. Use Create new Object if you
need to configure a new one.
Enable GRE over
IPSec Select this to allow traffic using the Generic Routing Encapsulation (GRE) tunneling
protocol through an IPSec tunnel.
Policy Enforcement Clear this to allow traffic with source and destination IP addresses that do not match the
local and remote policy to use the VPN tunnel. Leave this cleared for free access
between the local and remote networks.
Selecting this restricts who can use the VPN tunnel. The Zyxel Device drops traffic with
source and destination IP addresses that do not match the local and remote policy.
Mode Config This is visible when you select Remote Access (Server Rol e) and a VPN Gateway.
Enable Mode
Config Select this to have the IPSec VPN client receive an IP address, DNS and WINS information
from the Zyxel Device.
IP Address Pool Select an address object from the drop-down list box.
First DNS Server
(Optional) The Domain Name System (DNS) maps a domain name to an IP address and vice versa.
The Zyxel Device uses these (in the order you specify here) to resolve domain names for
VPN. Enter a DNS server's IP address.
Second DNS Server
(Optional) Enter a secondary DNS server's IP address that is checked if the first one is unavailable.
First WINS Server
(Optional) Type the IP address of the WINS (Windows Internet Naming Service) server that you want
to send to the DHCP clients. The WINS server keeps a mapping table of the computer
names on your network and the IP addresses that they are currently using.
Second WINS
Server (Optional) Enter a secondary WINS server's IP address that is checked if the first one is unavailable.
Configuration Payload This is only available when you have created an IKEv2 Gateway and are using Remote
Access (Server Role).
Enable Configuration
Payload
Select this to have at least have the IP address pool included in the VPN setup data.
IP Address Pool: Select an address object from the drop-down list box.
Table 212 Configuration > VPN > IPSec VPN > VPN Connection > Add/Edit (continued)
LABEL DESCRIPTION
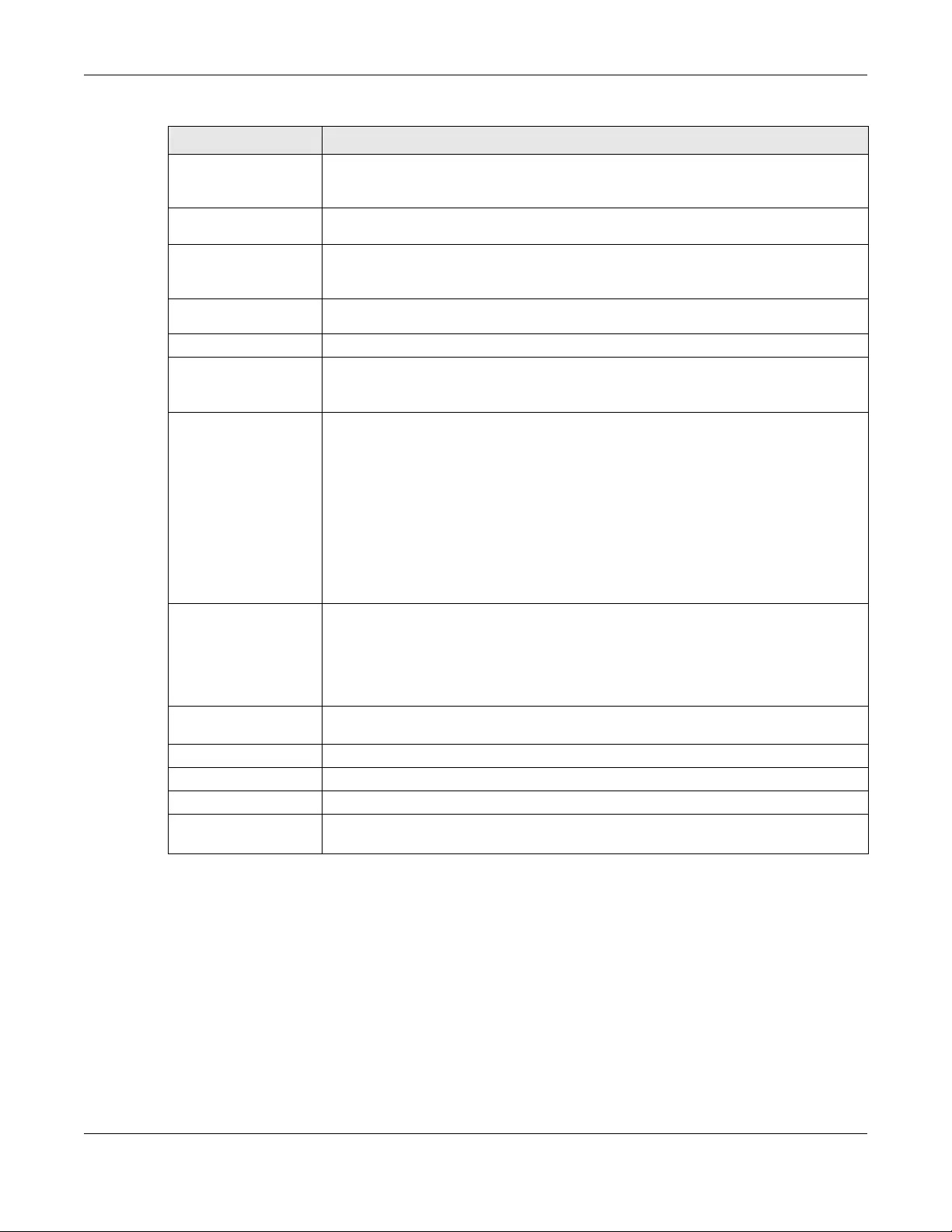
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
556
First DNS Server
(optional) The Domain Name System (DNS) maps a domain name to an IP address and vice versa.
The Zyxel Device uses these (in the order you specify here) to resolve domain names for
VPN. Enter a DNS server's IP address.
Second DNS Server
(Optional) Enter a secondary DNS server's IP address that is checked if the first one is unavailable.
First WINS Server
(Optional) Type the IP address of the WINS (Windows Internet Naming Service) server that you want
to send to the DHCP clients. The WINS server keeps a mapping table of the computer
names on your network and the IP addresses that they are currently using.
Second WINS
Server (Optional) Enter a secondary WINS server's IP address that is checked if the first one is unavailable.
Phase 2 Settings
SA Life Time Type the maximum number of seconds the IPSec SA can last. Shorter life times provide
better security. The Zyxel Device automatically negotiates a new IPSec SA before the
current one expires, if there are users who are accessing remote resources.
Active Protocol Select which protocol you want to use in the IPSec SA. Choices are:
AH (RFC 2402) - provides integrity, authentication, sequence integrity (replay resistance),
and non-repudiation but not encryption. If you select AH, you must select an
Authentication algorithm.
ESP (RFC 2406) - provides encryption and the same services offered by AH, but its
authentication is weaker. If you select ESP, you must select an Encryption algorithm and
Authentication algorithm.
Both AH and ESP increase processing requirements and latency (delay).
The Zyxel Device and remote IPSec router must use the same active protocol.
Encapsulation Select which type of encapsulation the IPSec SA uses. Choices are
Tunnel - this mode encrypts the IP header information and the data.
Transport - this mode only encrypts the data.
The Zyxel Device and remote IPSec router must use the same encapsulation.
Proposal Use this section to manage the encryption algorithm and authentication algorithm pairs
the Zyxel Device accepts from the remote IPSec router for negotiating the IPSec SA.
Add Click this to create a new entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
# This field is a sequential value, and it is not associated with a specific proposal. The
sequence of proposals should not affect performance significantly.
Table 212 Configuration > VPN > IPSec VPN > VPN Connection > Add/Edit (continued)
LABEL DESCRIPTION
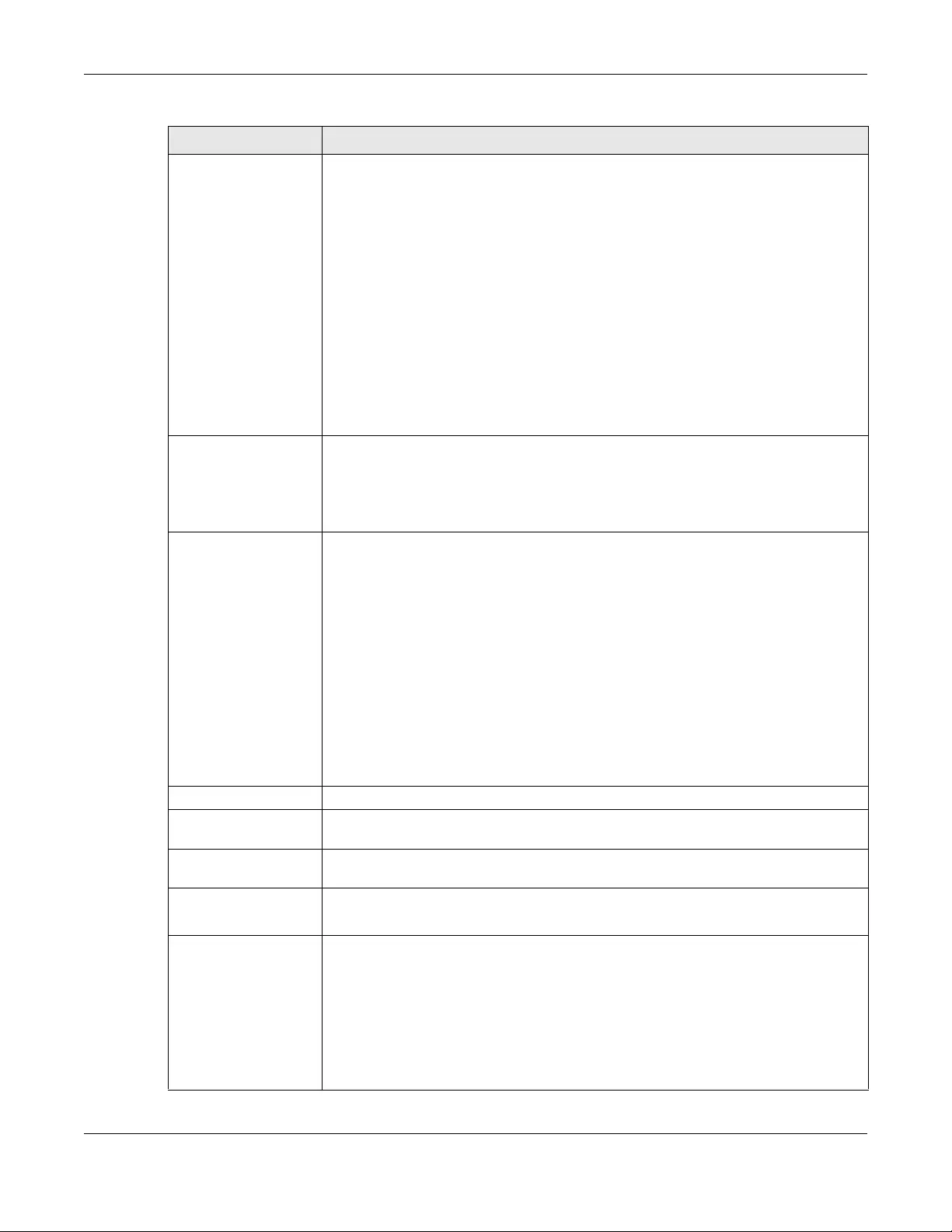
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
557
Encryption This field is applicable when the Active Protocol is ESP. Select which key size and
encryption algorithm to use in the IPSec SA. Choices are:
NULL - no encryption key or algorithm
DES - a 56-bit key with the DES encryption algorithm
3DES - a 168-bit key with the DES encryption algorithm
AES128 - a 128-bit key with the AES encryption algorithm
AES192 - a 192-bit key with the AES encryption algorithm
AES256 - a 256-bit key with the AES encryption algorithm
The Zyxel Device and the remote IPSec router must both have at least one proposal that
uses use the same encryption and the same key.
Longer keys are more secure, but require more processing power, resulting in increased
latency and decreased throughput.
Authentication Select which hash algorithm to use to authenticate packet data in the IPSec SA. Choices
are SHA1, SHA256, SHA512 and MD5. SHA is generally considered stronger than MD5, but
it is also slower.
The Zyxel Device and the remote IPSec router must both have a proposal that uses the
same authentication algorithm.
Perfect Forward
Secrecy (PFS) Select whether or not you want to enable Perfect Forward Secrecy (PFS) and, if you do,
which Diffie-Hellman key group to use for encryption. Choices are:
none - disable PFS
DH1 - enable PFS and use a 768-bit random number
DH2 - enable PFS and use a 1024-bit random number
DH5 - enable PFS and use a 1536-bit random number
DH14 - enable PFS and use a 2048 bit random number
PFS changes the root key that is used to generate encryption keys for each IPSec SA. The
longer the key, the more secure the encryption, but also the longer it takes to encrypt
and decrypt information. Both routers must use the same DH key group.
PFS is ignored in initial IKEv2 authentication but is used when re-authenticating.
Related Settings
Zone Select the security zone into which to add this VPN connection policy. Any security rules
or settings configured for the selected zone apply to this VPN connection policy.
Connectivity Check The Zyxel Device can regularly check the VPN connection to the gateway you specified
to make sure it is still available.
Enable
Connectivity
Check
Select this to turn on the VPN connection check.
Check Method Select how the Zyxel Device checks the connection. The peer must be configured to
respond to the method you select.
Select icmp to have the Zyxel Device regularly ping the address you specify to make sure
traffic can still go through the connection. You may need to configure the peer to
respond to pings.
Select tcp to have the Zyxel Device regularly perform a TCP handshake with the address
you specify to make sure traffic can still go through the connection. You may need to
configure the peer to accept the TCP connection.
Table 212 Configuration > VPN > IPSec VPN > VPN Connection > Add/Edit (continued)
LABEL DESCRIPTION
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
558
Check Port This field displays when you set the Check Method to tcp. Specify the port number to use
for a TCP connectivity check.
Check Period Enter the number of seconds between connection check attempts.
Check Timeout Enter the number of seconds to wait for a response before the attempt is a failure.
Check Fail
Tolerance Enter the number of consecutive failures allowed before the Zyxel Device disconnects
the VPN tunnel. The Zyxel Device resumes using the first peer gateway address when the
VPN connection passes the connectivity check.
Check this Address Select this to specify a domain name or IP address for the connectivity check. Enter that
domain name or IP address in the field next to it.
Check the First and
Last IP Address in
the Remote Policy
Select this to have the Zyxel Device check the connection to the first and last IP
addresses in the connection’s remote policy. Make sure one of these is the peer
gateway’s LAN IP address.
Log Select this to have the Zyxel Device generate a log every time it checks this VPN
connection.
Inbound/Outbound
traffic NAT
Outbound Traffic
Source NAT This translation hides the source address of computers in the local network. It may also be
necessary if you want the Zyxel Device to route packets from computers outside the local
network through the IPSec SA.
Source Select the address object that represents the original source address (or select Create
Object to configure a new one). This is the address object for the computer or network
outside the local network. The size of the original source address range (Source) must be
equal to the size of the translated source address range (SNAT).
Destination Select the address object that represents the original destination address (or select
Create Object to configure a new one). This is the address object for the remote network.
SNAT Select the address object that represents the translated source address (or select Create
Object to configure a new one). This is the address object for the local network. The size
of the original source address range (Source) must be equal to the size of the translated
source address range (SNAT).
Inbound Traffic
Source NAT This translation hides the source address of computers in the remote network.
Source Select the address object that represents the original source address (or select Create
Object to configure a new one). This is the address object for the remote network. The size
of the original source address range (Source) must be equal to the size of the translated
source address range (SNAT).
Destination Select the address object that represents the original destination address (or select
Create Object to configure a new one). This is the address object for the local network.
SNAT Select the address object that represents the translated source address (or select Create
Object to configure a new one). This is the address that hides the original source address.
The size of the original source address range (Source) must be equal to the size of the
translated source address range (SNAT).
Destination NAT This translation forwards packets (for example, mail) from the remote network to a
specific computer (for example, the mail server) in the local network.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after
the selected entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
Table 212 Configuration > VPN > IPSec VPN > VPN Connection > Add/Edit (continued)
LABEL DESCRIPTION
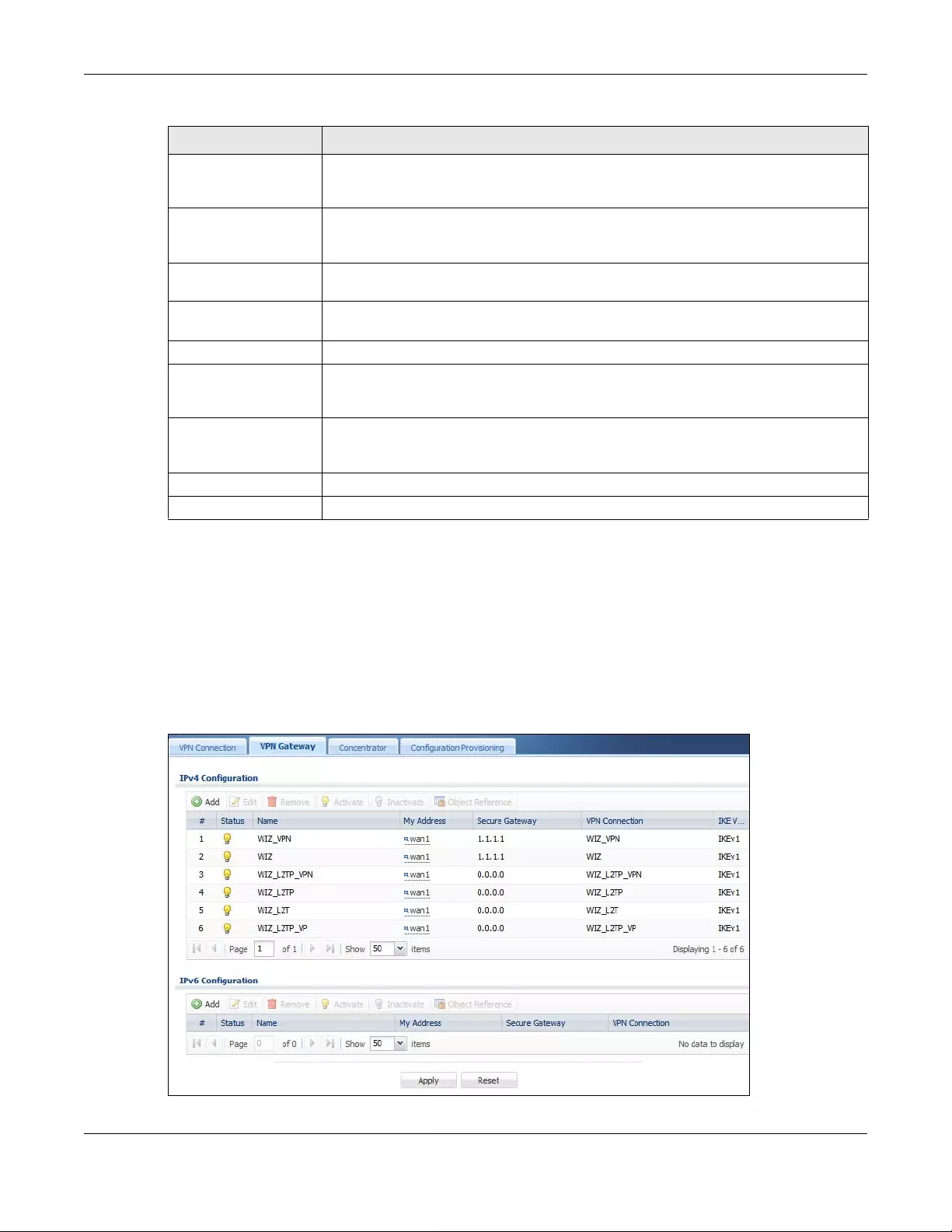
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
559
30.3 The VPN Gateway Screen
The VPN Gateway summary screen displays the IPSec VPN gateway policies in the Zyxel Device, as well
as the Zyxel Device’s address, remote IPSec router’s address, and associated VPN connections for each
one. In addition, it also lets you activate and deactivate each VPN gateway. To access this screen, click
Configuration > VPN > Network > IPSec VPN > VPN Gateway. The following screen appears.
Figure 395 Configuration > VPN > IPSec VPN > VPN Gateway
Move To change an entry’s position in the numbered list, select it and click Move to display a
field to type a number for where you want to put that entry and press [ENTER] to move
the entry to the number that you typed.
# This field is a sequential value, and it is not associated with a specific NAT record.
However, the order of records is the sequence in which conditions are checked and
executed.
Original IP Select the address object that represents the original destination address. This is the
address object for the remote network.
Mapped IP Select the address object that represents the desired destination address. For example,
this is the address object for the mail server.
Protocol Select the protocol required to use this translation. Choices are: TCP, UDP, or All.
Original Port Start /
Original Port End These fields are available if the protocol is TCP or UDP. Enter the original destination port or
range of original destination ports. The size of the original port range must be the same
size as the size of the mapped port range.
Mapped Port Start /
Mapped Port End These fields are available if the protocol is TCP or UDP. Enter the translated destination
port or range of translated destination ports. The size of the original port range must be
the same size as the size of the mapped port range.
OK Click OK to save the changes.
Cancel Click Cancel to discard all changes and return to the main VPN screen.
Table 212 Configuration > VPN > IPSec VPN > VPN Connection > Add/Edit (continued)
LABEL DESCRIPTION
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
560
Each field is discussed in the following table. See Section 30.3.1 on page 560 for more information.
30.3.1 The VPN Gateway Add/Edit Screen
The VPN Gateway Add/Edit screen allows you to create a new VPN gateway policy or edit an existing
one. To access this screen, go to the VPN Gateway summary screen (see Section 30.3 on page 559),
and click either the Add icon or an Edit icon.
Table 213 Configuration > VPN > IPSec VPN > VPN Gateway
LABEL DESCRIPTION
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Object References Select an entry and click Object References to open a screen that shows which settings use
the entry. See Section 10.4.4 on page 294 for an example.
# This field is a sequential value, and it is not associated with a specific VPN gateway.
Status The activate (light bulb) icon is lit when the entry is active and dimmed when the entry is
inactive.
Name This field displays the name of the VPN gateway
My address This field displays the interface or a domain name the Zyxel Device uses for the VPN gateway.
Secure Gateway This field displays the IP address(es) of the remote IPSec routers.
VPN Connection This field displays VPN connections that use this VPN gateway.
IKE Version This field displays whether the gateway is using IKEv1 or IKEv2. IKEv1 applies to IPv4 traffic only.
IKEv2 applies to both IPv4 and IPv6 traffic. IKE (Internet Key Exchange) is a protocol used in
setting up security associations that allows two parties to send data securely. See Section 30.1
on page 545 for more information on IKEv1 and IKEv2.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
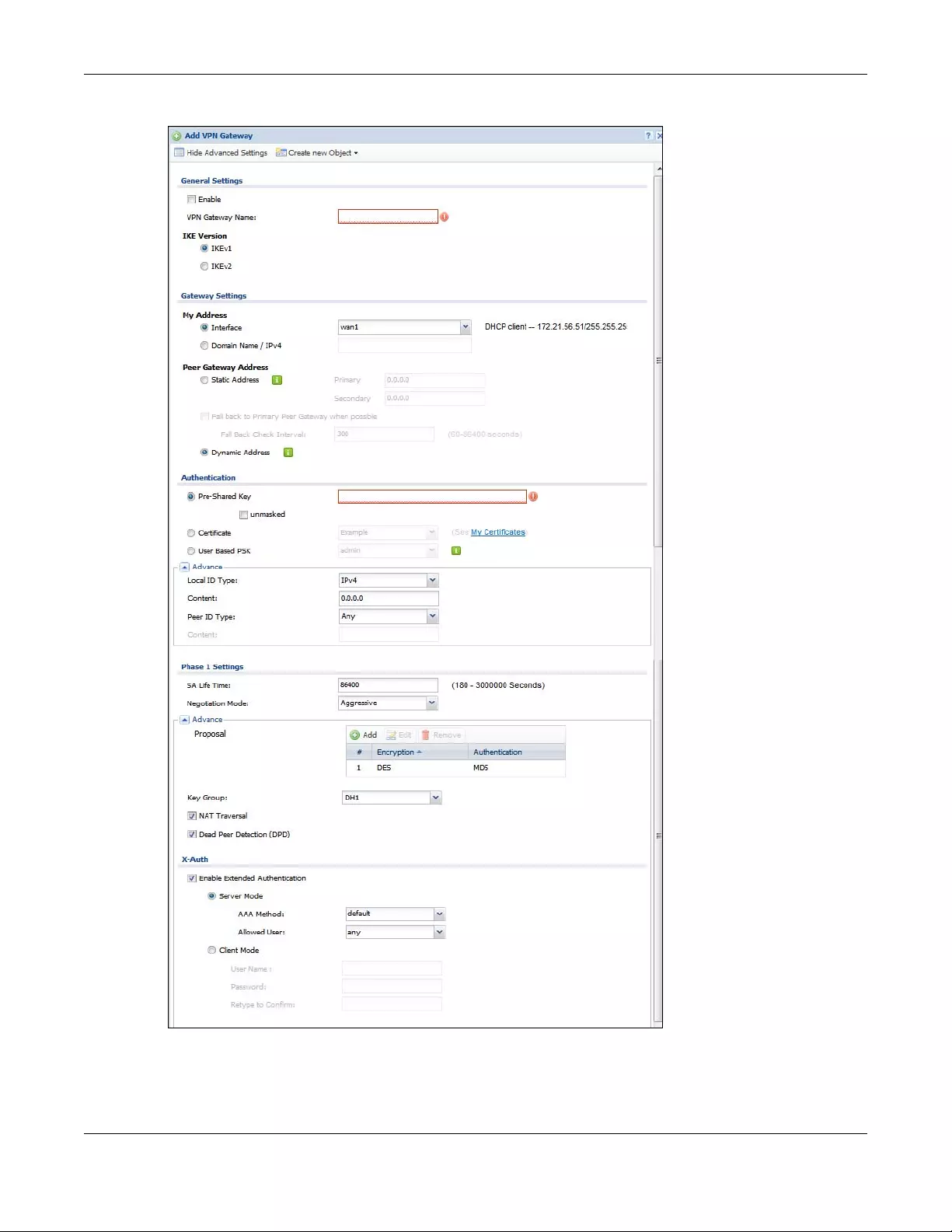
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
561
Figure 396 Configuration > VPN > IPSec VPN > VPN Gateway > Add/Edit
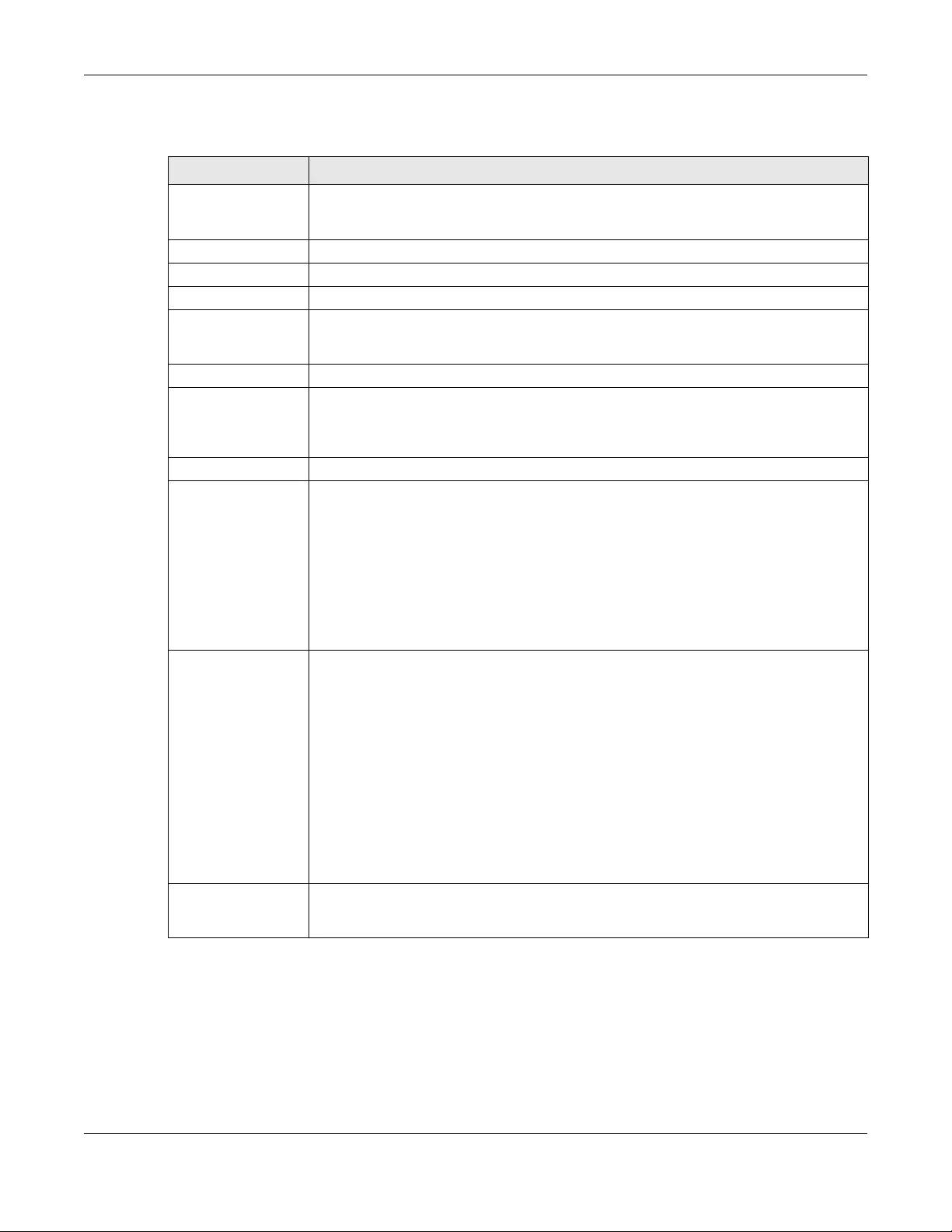
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
562
Each field is described in the following table.
Table 214 Configuration > VPN > IPSec VPN > VPN Gateway > Add/Edit
LABEL DESCRIPTION
Show Advanced
Settings / Hide
Advanced Settings
Click this button to display a greater or lesser number of configuration fields.
Create New Object Use to configure any new settings objects that you need to use in this screen.
General Settings
Enable Select this to activate the VPN Gateway policy.
VPN Gateway
Name Type the name used to identify this VPN gateway. You may use 1-31 alphanumeric
characters, underscores(_), or dashes (-), but the first character cannot be a number. This
value is case-sensitive.
IKE Version
IKEv1 / IKEv2 Select IKEv1 or IKEv2. IKEv1 applies to IPv4 traffic only. IKEv2 applies to both IPv4 and IPv6
traffic. IKE (Internet Key Exchange) is a protocol used in setting up security associations that
allows two parties to send data securely. See Section 30.1 on page 545 for more information
on IKEv1 and IKEv2.
Gateway Settings
My Address Select how the IP address of the Zyxel Device in the IKE SA is defined.
If you select Interface, select the Ethernet interface, VLAN interface, virtual Ethernet
interface, virtual VLAN interface or PPPoE/PPTP interface. The IP address of the Zyxel Device
in the IKE SA is the IP address of the interface.
If you select Domain Name / IP, enter the domain name or the IP address of the Zyxel
Device. The IP address of the Zyxel Device in the IKE SA is the specified IP address or the IP
address corresponding to the domain name. 0.0.0.0 is not generally recommended as it
has the Zyxel Device accept IPSec requests destined for any interface address on the Zyxel
Device.
Peer Gateway
Address Select how the IP address of the remote IPSec router in the IKE SA is defined.
Select Static Address to enter the domain name or the IP address of the remote IPSec
router. You can provide a second IP address or domain name for the Zyxel Device to try if it
cannot establish an IKE SA with the first one.
Fall back to Primary Peer Gateway when possible: When you select this, if the
connection to the primary address goes down and the Zyxel Device changes to using
the secondary connection, the Zyxel Device will reconnect to the primary address
when it becomes available again and stop using the secondary connection. Users will
lose their VPN connection briefly while the Zyxel Device changes back to the primary
connection. To use this, the peer device at the secondary address cannot be set to use
a nailed-up VPN connection. In the Fallback Check Interval field, set how often to
check if the primary address is available.
Select Dynamic Address if the remote IPSec router has a dynamic IP address (and does not
use DDNS).
Authentication Note: The Zyxel Device and remote IPSec router must use the same
authentication method to establish the IKE SA.
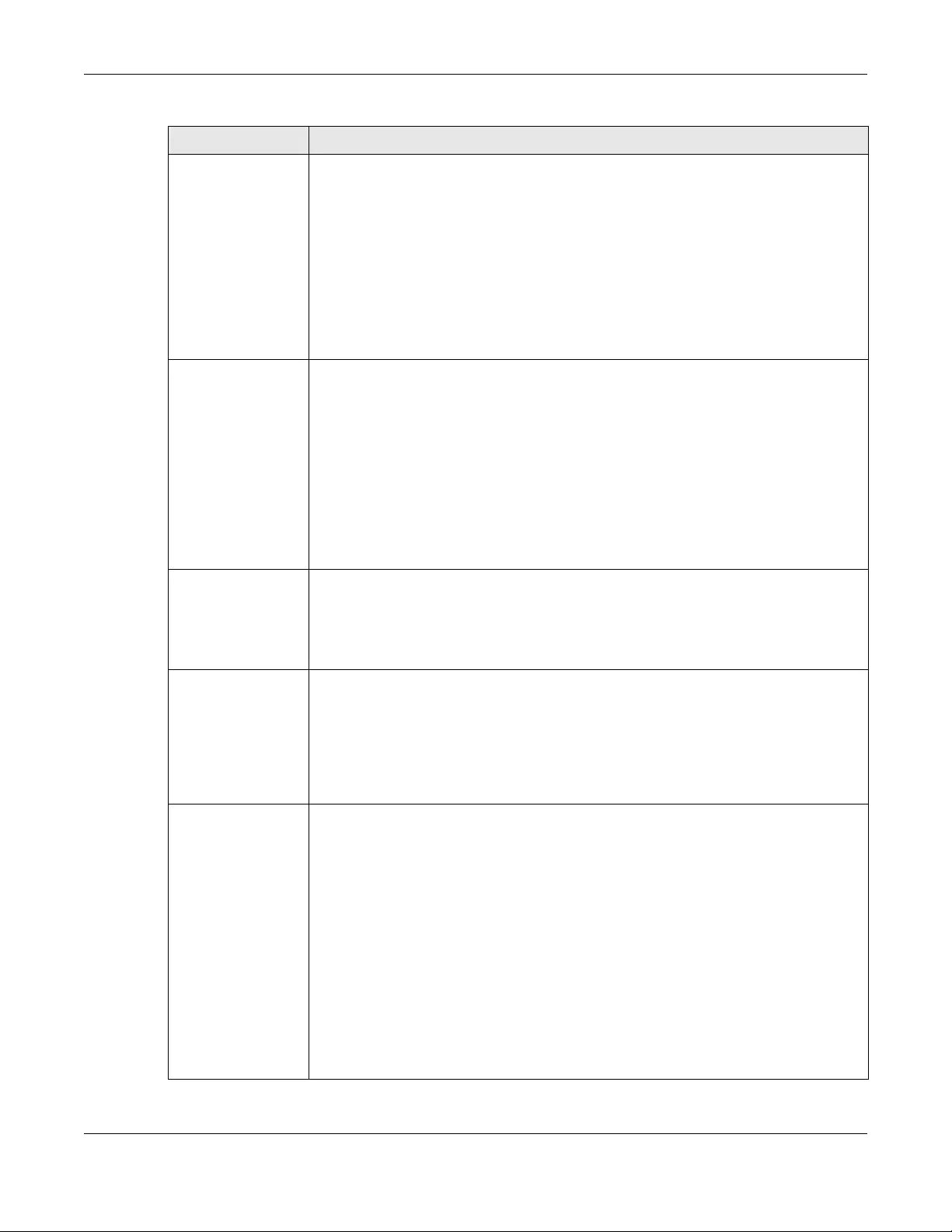
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
563
Pre-Shared Key Select this to have the Zyxel Device and remote IPSec router use a pre-shared key
(password) to identify each other when they negotiate the IKE SA. Type the pre-shared key
in the field to the right. The pre-shared key can be:
• alphanumeric characters or ,;.|`~!@#$%^&*()_+\{}':./<>=-"
• pairs of hexadecimal (0-9, A-F) characters, preceded by “0x”.
Type “0x” at the beginning of a hexadecimal key. For example, "0x0123456789ABCDEF" is in
hexadecimal format; “0123456789ABCDEF” is in ASCII format. If you use hexadecimal, you
must enter twice as many characters since you need to enter pairs.
The Zyxel Device and remote IPSec router must use the same pre-shared key.
Select unmasked to see the pre-shared key in readable plain text.
Certificate Select this to have the Zyxel Device and remote IPSec router use certificates to
authenticate each other when they negotiate the IKE SA. Then select the certificate the
Zyxel Device uses to identify itself to the remote IPSec router.
This certificate is one of the certificates in My Certificates. If this certificate is self-signed,
import it into the remote IPsec router. If this certificate is signed by a CA, the remote IPsec
router must trust that CA.
Note: The IPSec routers must trust each other’s certificates.
The Zyxel Device uses one of its Trusted Certificates to authenticate the remote IPSec
router’s certificate. The trusted certificate can be a self-signed certificate or that of a
trusted CA that signed the remote IPSec router’s certificate.
User-based PSK User-based PSK (IKEv1 only) generates and manages separate pre-shared keys for every
user. This enables multiple users, each with a unique key, to access the same VPN gateway
policy with one-to-one authentication and strong encryption. Access can be denied on a
per-user basis thus allowing VPN SA user-based policies. Click User-Based PSK then select a
user or group object who is allowed VPN SA access using this VPN gateway policy. This is for
IKEv1 only.
Local ID Type This field is read-only if the Zyxel Device and remote IPSec router use certificates to identify
each other. Select which type of identification is used to identify the Zyxel Device during
authentication. Choices are:
IPv4 or IPv6 - the Zyxel Device is identified by an IP address
DNS - the Zyxel Device is identified by a domain name
E-mail - the Zyxel Device is identified by the string specified in this field
Content This field is read-only if the Zyxel Device and remote IPSec router use certificates to identify
each other. Type the identity of the Zyxel Device during authentication. The identity
depends on the Local ID Type.
IP - type an IP address; if you type 0.0.0.0, the Zyxel Device uses the IP address specified in
the My Address field. This is not recommended in the following situations:
• There is a NAT router between the Zyxel Device and remote IPSec router.
• You want the remote IPSec router to be able to distinguish between IPSec SA requests
that come from IPSec routers with dynamic WAN IP addresses.
In these situations, use a different IP address, or use a different Local ID Type.
DNS - type the fully qualified domain name (FQDN). This value is only used for identification
and can be any string that matches the peer ID string.
E-mail - the Zyxel Device is identified by the string you specify here; you can use up to 63
ASCII characters including spaces, although trailing spaces are truncated. This value is only
used for identification and can be any string.
Table 214 Configuration > VPN > IPSec VPN > VPN Gateway > Add/Edit (continued)
LABEL DESCRIPTION
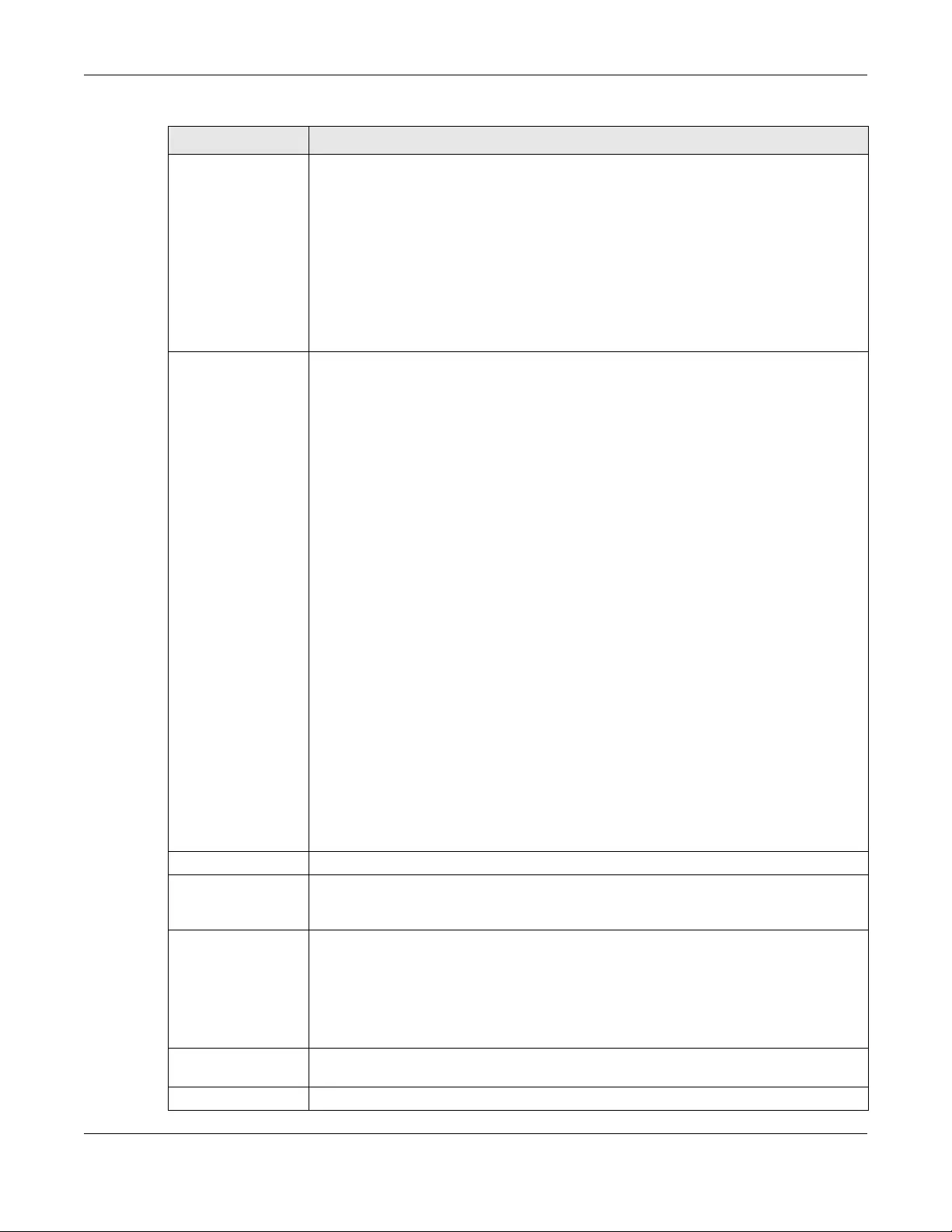
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
564
Peer ID Type Select which type of identification is used to identify the remote IPSec router during
authentication. Choices are:
IP - the remote IPSec router is identified by an IP address
DNS - the remote IPSec router is identified by a domain name
E-mail - the remote IPSec router is identified by the string specified in this field
Any - the Zyxel Device does not check the identity of the remote IPSec router
If the Zyxel Device and remote IPSec router use certificates, there is one more choice.
Subject Name - the remote IPSec router is identified by the subject name in the certificate
Content This field is disabled if the Peer ID Type is Any. Type the identity of the remote IPSec router
during authentication. The identity depends on the Peer ID Type.
If the Zyxel Device and remote IPSec router do not use certificates,
IP - type an IP address; see the note at the end of this description.
DNS - type the fully qualified domain name (FQDN). This value is only used for identification
and can be any string that matches the peer ID string.
E-mail - the remote IPSec router is identified by the string you specify here; you can use up
to 31 ASCII characters including spaces, although trailing spaces are truncated. This value is
only used for identification and can be any string.
If the Zyxel Device and remote IPSec router use certificates, type the following fields from
the certificate used by the remote IPSec router.
IP - subject alternative name field; see the note at the end of this description.
DNS - subject alternative name field
E-mail - subject alternative name field
Subject Name - subject name (maximum 255 ASCII characters, including spaces)
Note: If Peer ID Type is IP, please read the rest of this section.
If you type 0.0.0.0, the Zyxel Device uses the IP address specified in the Secure Gateway
Address field. This is not recommended in the following situations:
• There is a NAT router between the Zyxel Device and remote IPSec router.
• You want the remote IPSec router to be able to distinguish between IPSec SA requests
that come from IPSec routers with dynamic WAN IP addresses.
In these situations, use a different IP address, or use a different Peer ID Type.
Phase 1 Settings
SA Life Time
(Seconds) Type the maximum number of seconds the IKE SA can last. When this time has passed, the
Zyxel Device and remote IPSec router have to update the encryption and authentication
keys and re-negotiate the IKE SA. This does not affect any existing IPSec SAs, however.
Negotiation
Mode Select the negotiation mode to use to negotiate the IKE SA. Choices are
Main - this encrypts the Zyxel Device’s and remote IPSec router’s identities but takes more
time to establish the IKE SA
Aggressive - this is faster but does not encrypt the identities
The Zyxel Device and the remote IPSec router must use the same negotiation mode.
Proposal Use this section to manage the encryption algorithm and authentication algorithm pairs the
Zyxel Device accepts from the remote IPSec router for negotiating the IKE SA.
Add Click this to create a new entry.
Table 214 Configuration > VPN > IPSec VPN > VPN Gateway > Add/Edit (continued)
LABEL DESCRIPTION
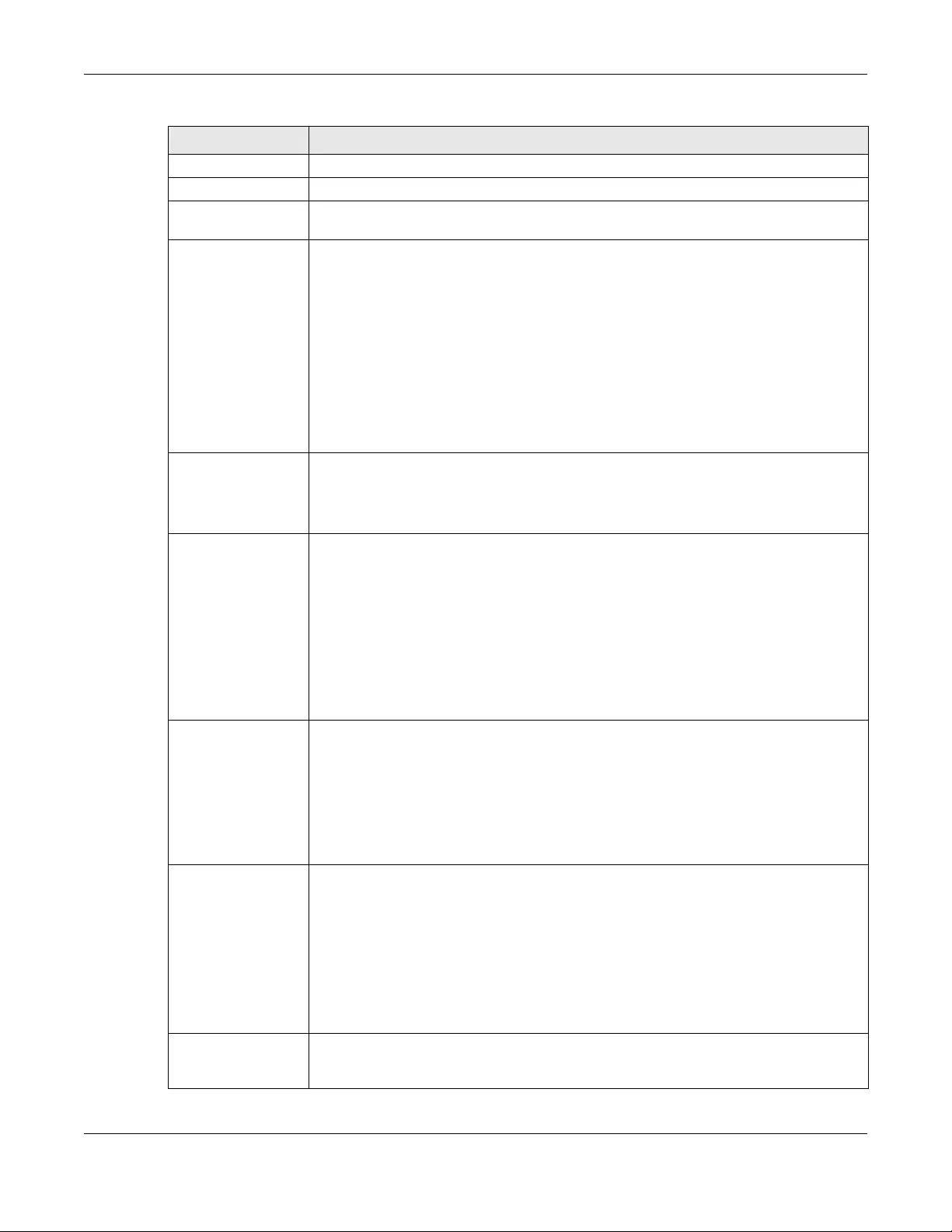
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
565
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
# This field is a sequential value, and it is not associated with a specific proposal. The
sequence of proposals should not affect performance significantly.
Encryption Select which key size and encryption algorithm to use in the IKE SA. Choices are:
DES - a 56-bit key with the DES encryption algorithm
3DES - a 168-bit key with the DES encryption algorithm
AES128 - a 128-bit key with the AES encryption algorithm
AES192 - a 192-bit key with the AES encryption algorithm
AES256 - a 256-bit key with the AES encryption algorithm
The Zyxel Device and the remote IPSec router must use the same key size and encryption
algorithm. Longer keys require more processing power, resulting in increased latency and
decreased throughput.
Authentication Select which hash algorithm to use to authenticate packet data in the IPSec SA. Choices
are SHA1, SHA256, SHA512 and MD5. SHA is generally considered stronger than MD5, but it is
also slower.
The remote IPSec router must use the same authentication algorithm.
Key Group Select which Diffie-Hellman key group (DHx) you want to use for encryption keys. Choices
are:
DH1 - use a 768-bit random number
DH2 - use a 1024-bit random number
DH5 - use a 1536-bit random number
DH14 - use a 2048 bit random number
The longer the key, the more secure the encryption, but also the longer it takes to encrypt
and decrypt information. Both routers must use the same DH key group.
NAT Traversal Select this if any of these conditions are satisfied.
• This IKE SA might be used to negotiate IPSec SAs that use ESP as the active protocol.
• There are one or more NAT routers between the Zyxel Device and remote IPSec router,
and these routers do not support IPSec pass-thru or a similar feature.
The remote IPSec router must also enable NAT traversal, and the NAT routers have to
forward packets with UDP port 500 and UDP 4500 headers unchanged.
This field applies for IKEv1 only. NAT Traversal is always performed when you use IKEv2.
Dead Peer
Detection (DPD) Select this check box if you want the Zyxel Device to make sure the remote IPSec router is
there before it transmits data through the IKE SA. The remote IPSec router must support DPD.
If there has been no traffic for at least 15 seconds, the Zyxel Device sends a message to the
remote IPSec router. If the remote IPSec router responds, the Zyxel Device transmits the
data. If the remote IPSec router does not respond, the Zyxel Device shuts down the IKE SA.
If the remote IPSec router does not support DPD, see if you can use the VPN connection
connectivity check (see Section 30.2.1 on page 552).
This field applies for IKEv1 only. Dead Peer Detection (DPD) is always performed when you
use IKEv2.
X Auth / Extended
Authentication
Protocol
This part of the screen displays X-Auth when using IKEv1 and Extended Authentication
Protocol when using IKEv2.
Table 214 Configuration > VPN > IPSec VPN > VPN Gateway > Add/Edit (continued)
LABEL DESCRIPTION
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
566
X-Auth This displays when using IKEv1. When different users use the same VPN tunnel to connect to
the Zyxel Device (telecommuters sharing a tunnel for example), use X-auth to enforce a
user name and password check. This way even though telecommuters all know the VPN
tunnel’s security settings, each still has to provide a unique user name and password.
Enable Extended
Authentication Select this if one of the routers (the Zyxel Device or the remote IPSec router) verifies a user
name and password from the other router using the local user database and/or an external
server.
Server Mode Select this if the Zyxel Device authenticates the user name and password from the remote
IPSec router. You also have to select the authentication method, which specifies how the
Zyxel Device authenticates this information.
AAA Method Select the authentication method, which specifies how the Zyxel Device authenticates this
information.
Allowed User Extended authentication now supports an allowed user. Select what users should be
authenticated.
Client Mode Select this radio button if the Zyxel Device provides a username and password to the
remote IPSec router for authentication. You also have to provide the User Name and the
Password.
User Name This field is required if the Zyxel Device is in Client Mode for extended authentication. Type
the user name the Zyxel Device sends to the remote IPSec router. The user name can be 1-
31 ASCII characters. It is case-sensitive, but spaces are not allowed.
Password This field is required if the Zyxel Device is in Client Mode for extended authentication. Type
the password the Zyxel Device sends to the remote IPSec router. The password can be 1-31
ASCII characters. It is case-sensitive, but spaces are not allowed.
Retype to
Confirm Type the exact same password again here to make sure an error was not made when
typing it originally.
Extended
Authentication
Protocol
This displays when using IKEv2. EAP uses a certificate for authentication.
Enable Extended
Authentication Select this if one of the routers (the Zyxel Device or the remote IPSec router) verifies a user
name and password from the other router using the local user database and/or an external
server or a certificate.
Server Mode Select this if the Zyxel Device authenticates the user name and password from the remote
IPSec router. You also have to select an AAA method, which specifies how the Zyxel Device
authenticates this information and who may be authenticated (Allowed User).
Client Mode Select this radio button if the Zyxel Device provides a username and password to the
remote IPSec router for authentication. You also have to provide the User Name and the
Password.
User Name This field is required if the Zyxel Device is in Client Mode for extended authentication. Type
the user name the Zyxel Device sends to the remote IPSec router. The user name can be 1-
31 ASCII characters. It is case-sensitive, but spaces are not allowed.
Password This field is required if the Zyxel Device is in Client Mode for extended authentication. Type
the password the Zyxel Device sends to the remote IPSec router. The password can be 1-31
ASCII characters. It is case-sensitive, but spaces are not allowed.
Retype to
Confirm Type the exact same password again here to make sure an error was not made when
typing it originally.
OK Click OK to save your settings and exit this screen.
Cancel Click Cancel to exit this screen without saving.
Table 214 Configuration > VPN > IPSec VPN > VPN Gateway > Add/Edit (continued)
LABEL DESCRIPTION
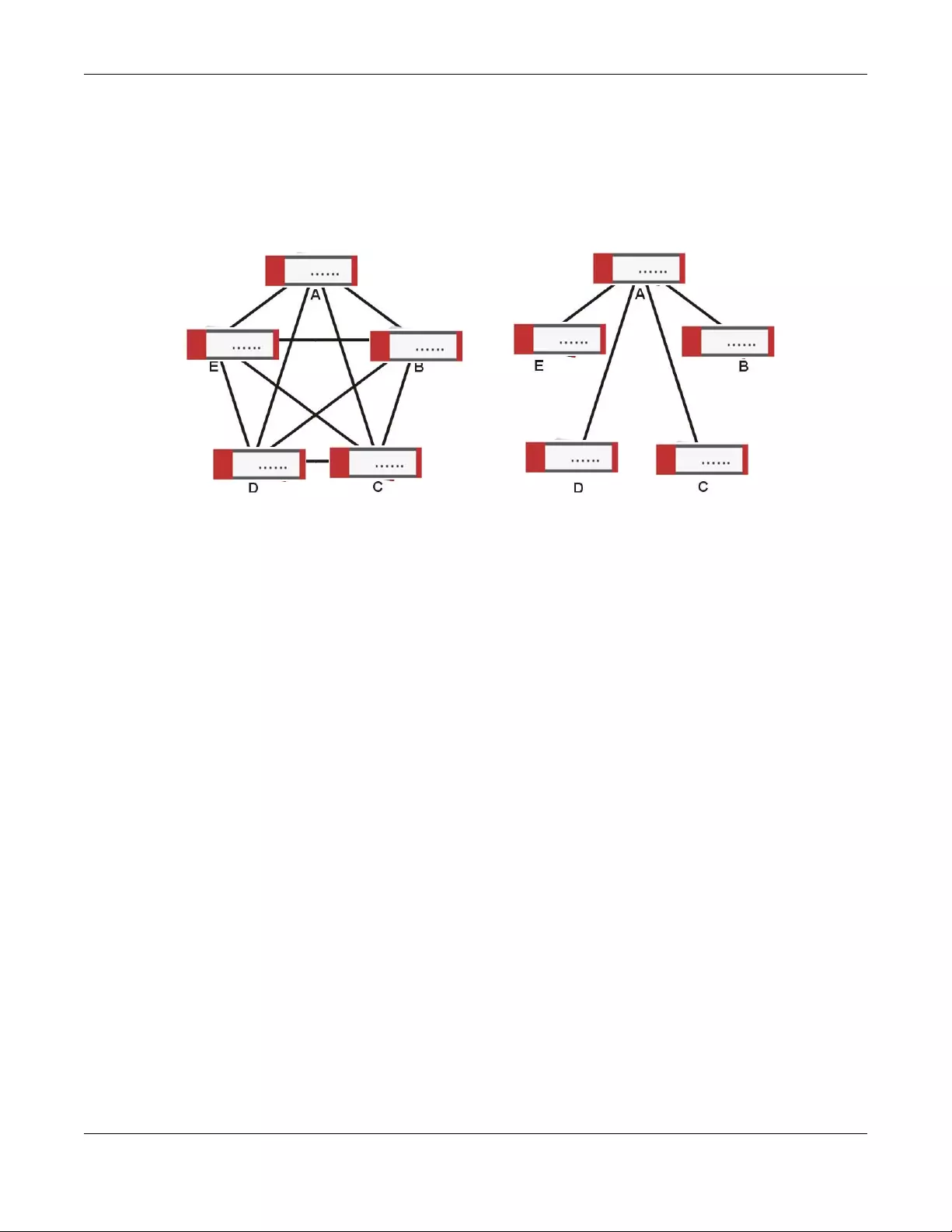
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
567
30.4 VPN Concentrator
A VPN concentrator combines several IPSec VPN connections into one secure network.
Figure 397 VPN Topologies (Fully Meshed and Hub and Spoke)
In a fully-meshed VPN topology (1 in the figure), there is a VPN connection between every pair of
routers. In a hub-and-spoke VPN topology (2 in the figure), there is a VPN connection between each
spoke router (B, C, D, and E) and the hub router (A), which uses the VPN concentrator. The VPN
concentrator routes VPN traffic between the spoke routers and itself.
A VPN concentrator reduces the number of VPN connections that you have to set up and maintain in
the network. You might also be able to consolidate the policy routes in each spoke router, depending
on the IP addresses and subnets of each spoke.
However a VPN concentrator is not for every situation. The hub router is a single failure point, so a VPN
concentrator is not as appropriate if the connection between spoke routers cannot be down
occasionally (maintenance, for example). There is also more burden on the hub router. It receives VPN
traffic from one spoke, decrypts it, inspects it to find out to which spoke to route it, encrypts it, and sends
it to the appropriate spoke. Therefore, a VPN concentrator is more suitable when there is a minimum
amount of traffic between spoke routers.
30.4.1 VPN Concentrator Requirements and Suggestions
Consider the following when using the VPN concentrator.
• The local IP addresses configured in the VPN rules should not overlap.
• The concentrator must have at least one separate VPN rule for each spoke. In the local policy,
specify the IP addresses of the networks with which the spoke is to be able to have a VPN tunnel. This
may require you to use more than one VPN rule for each spoke.
• To have all Internet access from the spoke routers go through the VPN tunnel, set the VPN rules in the
spoke routers to use 0.0.0.0 (any) as the remote IP address.
• Your security policies can still block VPN packets.
12
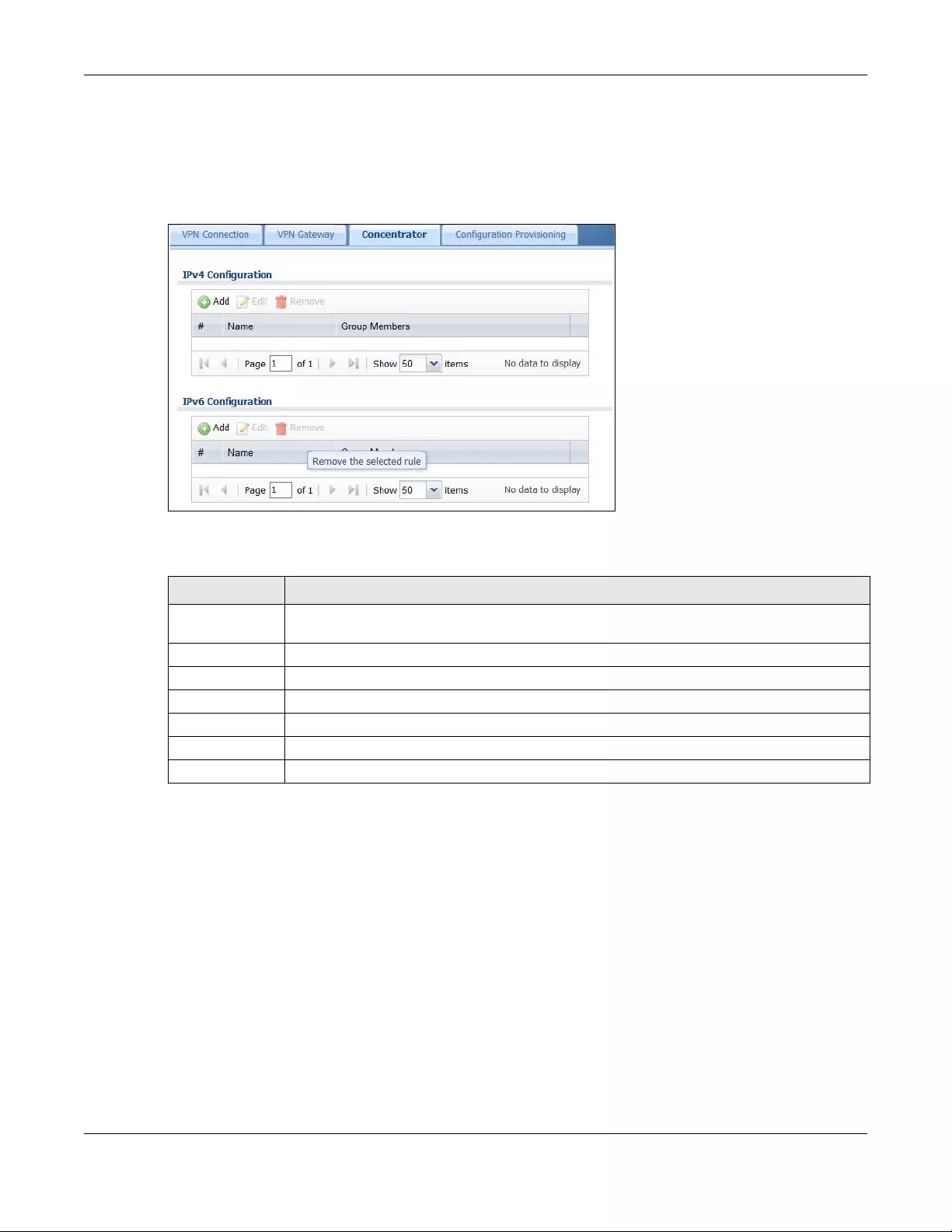
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
568
30.4.2 VPN Concentrator Screen
The VPN Concentrator summary screen displays the VPN concentrators in the Zyxel Device. To access
this screen, click Configuration > VPN > IPSec VPN > Concentrator.
Figure 398 Configuration > VPN > IPSec VPN > Concentrator
Each field is discussed in the following table. See Section 30.4.3 on page 568 for more information.
30.4.3 The VPN Concentrator Add/Edit Screen
Use the VPN Concentrator Add/Edit screen to create or edit a VPN concentrator. To access this screen,
go to the VPN Concentrator summary screen (see Section 30.4 on page 567), and click either the Add
icon or an Edit icon.
Table 215 Configuration > VPN > IPSec VPN > Concentrator
LABEL DESCRIPTION
IPv4/IPv6
Configuration
Choose to configure for IPv4 or IPv6 traffic.
Add Click this to create a new entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
# This field is a sequential value, and it is not associated with a specific concentrator.
Name This field displays the name of the VPN concentrator.
Group Members These are the VPN connection policies that are part of the VPN concentrator.
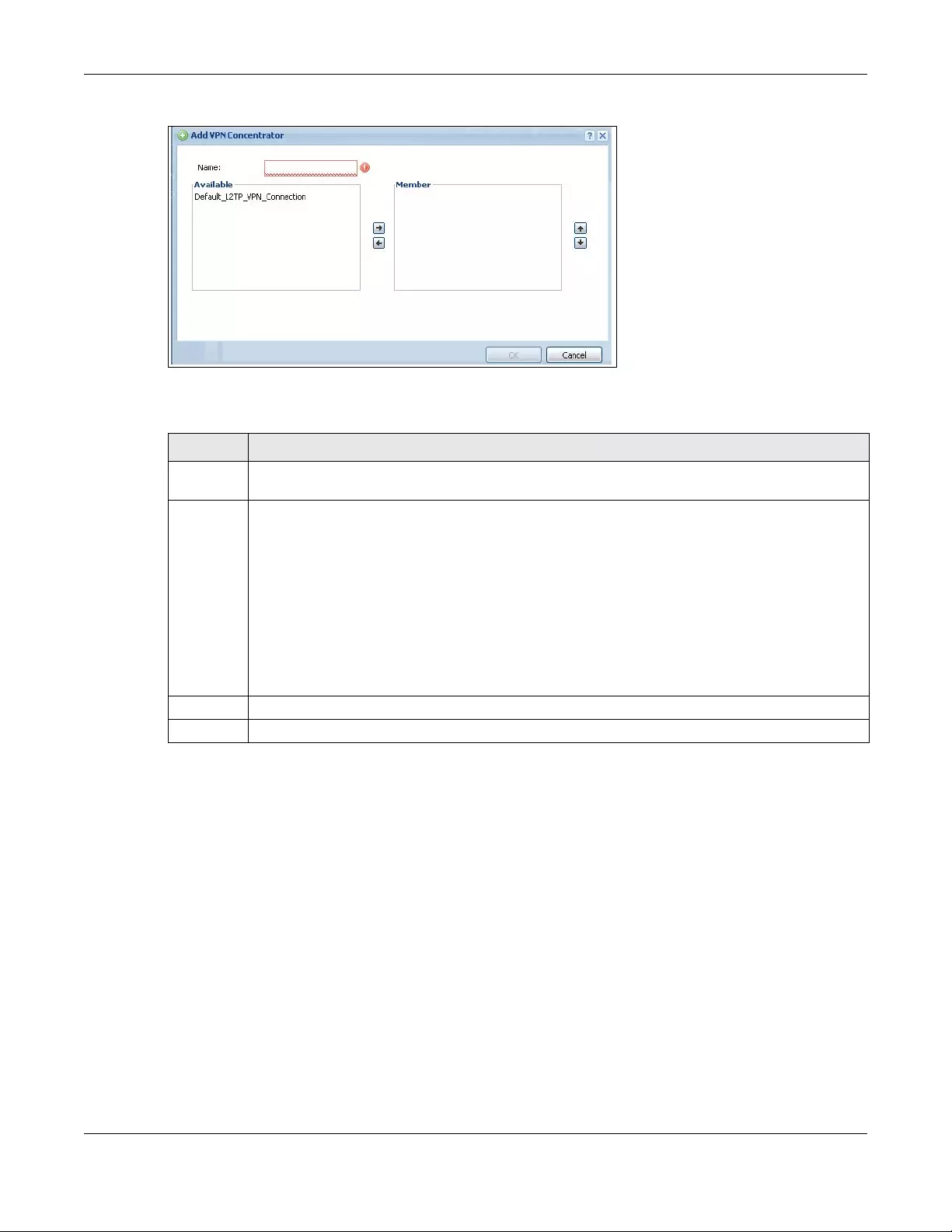
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
569
Figure 399 Configuration > VPN > IPSec VPN > Concentrator > Add/Edit
Each field is described in the following table.
30.5 Zyxel Device IPSec VPN Client Configuration
Provisioning
Use the Configuration > VPN > IPSec VPN > Configuration Provisioning screen to configure who can
retrieve VPN rule settings from the Zyxel Device using the Zyxel Device IPSec VPN Client. In the Zyxel
Device IPSec VPN Client, you just need to enter the IP address of the Zyxel Device to get all the VPN rule
settings automatically. You do not need to manually configure all rule settings in the Zyxel Device IPSec
VPN client.
VPN rules for the Zyxel Device IPSec VPN Client have certain restrictions. They must not contain the
following settings:
•AH active protocol
•NULL encryption
•SHA512 authentication
Table 216 VPN > IPSec VPN > Concentrator > Add/Edit
LABEL DESCRIPTION
Name Enter the name of the concentrator. You may use 1-31 alphanumeric characters, underscores(_), or
dashes (-), but the first character cannot be a number. This value is case-sensitive.
Member Select the concentrator’s IPSec VPN connection policies.
Note: You must disable policy enforcement in each member. See Section 30.2.1 on page
552.
IPSec VPN connection policies that do not belong to a VPN concentrator appear under Available.
Select any VPN connection policies that you want to add to the VPN concentrator and click the right
arrow button to add them.
The VPN concentrator’s member VPN connections appear under Member. Select any VPN
connections that you want to remove from the VPN concentrator, and click the left arrow button to
remove them.
OK Click OK to save your changes in the Zyxel Device.
Cancel Click Cancel to exit this screen without saving.
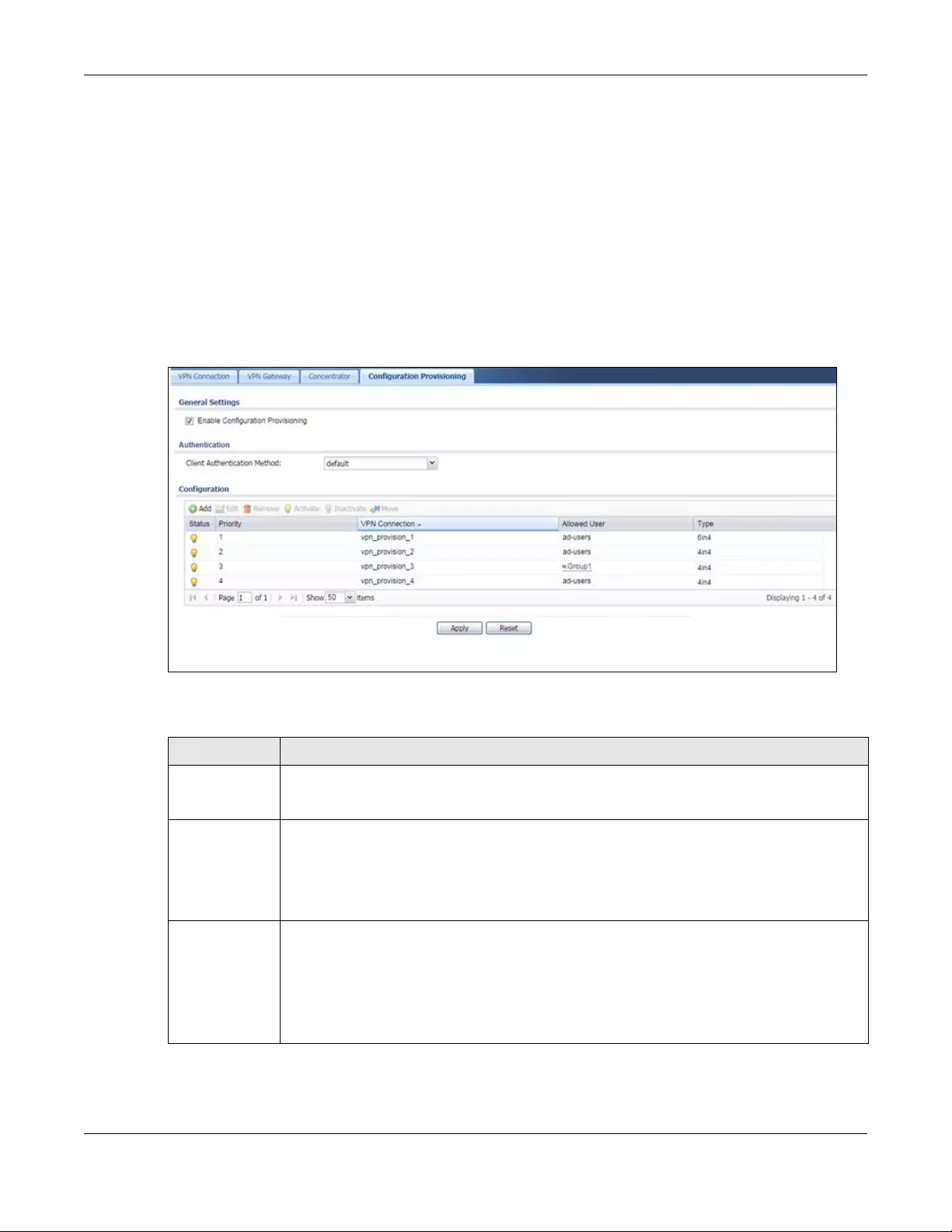
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
570
• A subnet or range remote policy
The following VPN Gateway rules configured on the Zyxel Device cannot be provisioned to the IPSec
VPN Client:
• IPv4 rules with IKEv2 version
• IPv4 rules with User-based PSK authentication
Note: You must enable IPv6 in System > IPv6 to activate IPv6 VPN tunneling rules.
In the Zyxel Device Quick Setup wizard, you can use the VPN Settings for Configuration Provisioning
wizard to create a VPN rule that will not violate these restrictions.
Figure 400 Configuration > VPN > IPSec VPN > Configuration Provisioning
Each field is discussed in the following table.
Table 217 Configuration > VPN > IPSec VPN > Configuration Provisioning
LABEL DESCRIPTION
Enable
Configuration
Provisioning
Select this for users to be able to retrieve VPN rule settings using the Zyxel Device IPSec VPN
client.
Client
Authentication
Method
Choose how users should be authenticated. They can be authenticated using the local
database on the Zyxel Device or an external authentication database such as LDAP, Active
Directory or RADIUS. default is a method you configured in Object > Auth Method. You may
configure multiple methods there. If you choose the local database on the Zyxel Device, then
configure users using the Object > User/Group screen. If you choose LDAP, Active Directory or
RADIUS authentication servers, then configure users on the respective server.
Configuration When you add or edit a configuration provisioning entry, you are allowed to set the VPN
Connection and Allowed User fields.
Duplicate entries are not allowed. You cannot select the same VPN Connection and Allowed
User pair in a new entry if the same pair exists in a previous entry.
You can bind different rules to the same user, but the Zyxel Device will only allow VPN rule setting
retrieval for the first match found.
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
571
30.6 IPSec VPN Background Information
Here is some more detailed IPSec VPN background information.
IKE SA Overview
The IKE SA provides a secure connection between the Zyxel Device and remote IPSec router.
It takes several steps to establish an IKE SA. The negotiation mode determines how many. There are two
negotiation modes--main mode and aggressive mode. Main mode provides better security, while
aggressive mode is faster.
Add Click Add to bind a configured VPN rule to a user or group. Only that user or group may then
retrieve the specified VPN rule settings.
If you click Add without selecting an entry in advance then the new entry appears as the first
entry. Entry order is important as the Zyxel Device searches entries in the order listed here to find
a match. After a match is found, the Zyxel Device stops searching. If you want to add an entry
as number three for example, then first select entry 2 and click Add. To reorder an entry, use
Move.
Edit Select an existing entry and click Edit to change its settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove it
before doing so.
Activate To turn on an entry, select it and click Activate. Make sure that Enable Configuration Provisioning
is also selected.
Inactivate To turn off an entry, select it and click Inactivate.
Move Use Move to reorder a selected entry. Select an entry, click Move, type the number where the
entry should be moved, press <ENTER>, then click Apply.
Status This icon shows if the entry is active (yellow) or not (gray). VPN rule settings can only be retrieved
when the entry is activated (and Enable Configuration Provisioning is also selected).
Priority Priority shows the order of the entry in the list. Entry order is important as the Zyxel Device
searches entries in the order listed here to find a match. After a match is found the Zyxel Device
stops searching.
VPN
Connection
This field shows all configured VPN rules that match the rule criteria for the Zyxel Device IPSec
VPN client. Select a rule to bind to the associated user or group.
Allowed User Select which user or group of users is allowed to retrieve the associated VPN rule settings using
the Zyxel Device IPSec VPN client. A user may belong to a number of groups. If entries are
configured for different groups, the Zyxel Device will allow VPN rule setting retrieval based on the
first match found.
Users of type admin or limited-admin are not allowed.
Type This field shows how traffic is tunneled from the Zyxel Device to the Zyxel VPN client:
•6in4 (tunnel IPv6 traffic from the Zyxel Device to the Zyxel client in an IPv4 network);
•4in6 (tunnel IPv4 traffic from the Zyxel Device to the Zyxel VPN client in an IPv6 network);
•4in4 (tunnel IPv4 traffic from the Zyxel Device to the Zyxel VPN client in an IPv4 network).
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 217 Configuration > VPN > IPSec VPN > Configuration Provisioning (continued)
LABEL DESCRIPTION
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
572
Note: Both routers must use the same negotiation mode.
These modes are discussed in more detail in Negotiation Mode on page 575. Main mode is used in
various examples in the rest of this section.
The Zyxel Device supports IKEv1 and IKEv2. See Section 30.1 on page 545 for more information.
IP Addresses of the Zyxel Device and Remote IPSec Router
To set up an IKE SA, you have to specify the IP addresses of the Zyxel Device and remote IPSec router.
You can usually enter a static IP address or a domain name for either or both IP addresses. Sometimes,
your Zyxel Device might offer another alternative, such as using the IP address of a port or interface, as
well.
You can also specify the IP address of the remote IPSec router as 0.0.0.0. This means that the remote
IPSec router can have any IP address. In this case, only the remote IPSec router can initiate an IKE SA
because the Zyxel Device does not know the IP address of the remote IPSec router. This is often used for
telecommuters.
IKE SA Proposal
The IKE SA proposal is used to identify the encryption algorithm, authentication algorithm, and Diffie-
Hellman (DH) key group that the Zyxel Device and remote IPSec router use in the IKE SA. In main mode,
this is done in steps 1 and 2, as illustrated next.
Figure 401 IKE SA: Main Negotiation Mode, Steps 1 - 2: IKE SA Proposal
The Zyxel Device sends one or more proposals to the remote IPSec router. (In some devices, you can
only set up one proposal.) Each proposal consists of an encryption algorithm, authentication algorithm,
and DH key group that the Zyxel Device wants to use in the IKE SA. The remote IPSec router selects an
acceptable proposal and sends the accepted proposal back to the Zyxel Device. If the remote IPSec
router rejects all of the proposals, the Zyxel Device and remote IPSec router cannot establish an IKE SA.
Note: Both routers must use the same encryption algorithm, authentication algorithm, and DH
key group.
In most Zyxel Devices, you can select one of the following encryption algorithms for each proposal. The
algorithms are listed in order from weakest to strongest.
• Data Encryption Standard (DES) is a widely used method of data encryption. It applies a 56-bit key to
each 64-bit block of data.
One or more proposals, each one consisting of:
- encryption algorithm
- authentication algorithm
- Diffie-Hellman key group
1
2
XY
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
573
• Triple DES (3DES) is a variant of DES. It iterates three times with three separate keys, effectively tripling
the strength of DES.
• Advanced Encryption Standard (AES) is a newer method of data encryption that also uses a secret
key. AES applies a 128-bit key to 128-bit blocks of data. It is faster than 3DES.
Some Zyxel Devices also offer stronger forms of AES that apply 192-bit or 256-bit keys to 128-bit blocks of
data.
In most Zyxel Devices, you can select one of the following authentication algorithms for each proposal.
The algorithms are listed in order from weakest to strongest.
• MD5 (Message Digest 5) produces a 128-bit digest to authenticate packet data.
• SHA1 (Secure Hash Algorithm) produces a 160-bit digest to authenticate packet data.
• SHA256 (Secure Hash Algorithm) produces a 256-bit digest to authenticate packet data.
• SHA512 (Secure Hash Algorithm) produces a 512-bit digest to authenticate packet data.
See Diffie-Hellman (DH) Key Exchange on page 573 for more information about DH key groups.
Diffie-Hellman (DH) Key Exchange
The Zyxel Device and the remote IPSec router use DH public-key cryptography to establish a shared
secret. The shared secret is then used to generate encryption keys for the IKE SA and IPSec SA. In main
mode, this is done in steps 3 and 4, as illustrated next.
Figure 402 IKE SA: Main Negotiation Mode, Steps 3 - 4: DH Key Exchange
DH public-key cryptography is based on DH key groups. Each key group is a fixed number of bits long.
The longer the key, the more secure the encryption, but also the longer it takes to encrypt and decrypt
information. For example, DH2 keys (1024 bits) are more secure than DH1 keys (768 bits), but DH2 keys
take longer to encrypt and decrypt.
Authentication
Before the Zyxel Device and remote IPSec router establish an IKE SA, they have to verify each other’s
identity. This process is based on pre-shared keys and router identities.
In main mode, the Zyxel Device and remote IPSec router authenticate each other in steps 5 and 6, as
illustrated below. The identities are also encrypted using the encryption algorithm and encryption key
the Zyxel Device and remote IPSec router selected in previous steps.
Diffie-Hellman key exchange
3
4
XY
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
574
Figure 403 IKE SA: Main Negotiation Mode, Steps 5 - 6: Authentication (continued)
You have to create (and distribute) a pre-shared key. The Zyxel Device and remote IPSec router use it in
the authentication process, though it is not actually transmitted or exchanged.
Note: The Zyxel Device and the remote IPSec router must use the same pre-shared key.
Router identity consists of ID type and content. The ID type can be domain name, IP address, or e-mail
address, and the content is a (properly-formatted) domain name, IP address, or e-mail address. The
content is only used for identification. Any domain name or e-mail address that you enter does not have
to actually exist. Similarly, any domain name or IP address that you enter does not have to correspond
to the Zyxel Device’s or remote IPSec router’s properties.
The Zyxel Device and the remote IPSec router have their own identities, so both of them must store two
sets of information, one for themselves and one for the other router. Local ID type and content refers to
the ID type and content that applies to the router itself, and peer ID type and content refers to the ID
type and content that applies to the other router.
Note: The Zyxel Device’s local and peer ID type and content must match the remote IPSec
router’s peer and local ID type and content, respectively.
For example, in Table 218 on page 574, the Zyxel Device and the remote IPSec router authenticate
each other successfully. In contrast, in Table 219 on page 575, the Zyxel Device and the remote IPSec
router cannot authenticate each other and, therefore, cannot establish an IKE SA.
Step 5:
pre-shared key
Zyxel Device identity, consisting of
- ID type
- content
Step 6:
pre-shared key
Remote IPSec router identity, consisting of
- ID type
- content
Table 218 VPN Example: Matching ID Type and Content
ZYXEL DEVICE REMOTE IPSEC ROUTER
Local ID type: E-mail Local ID type: IP
Local ID content: tom@yourcompany.com Local ID content: 1.1.1.2
Peer ID type: IP Peer ID type: E-mail
Peer ID content: 1.1.1.2 Peer ID content: tom@yourcompany.com
5
6
XY
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
575
It is also possible to configure the Zyxel Device to ignore the identity of the remote IPSec router. In this
case, you usually set the peer ID type to Any. This is less secure, so you should only use this if your Zyxel
Device provides another way to check the identity of the remote IPSec router (for example, extended
authentication) or if you are troubleshooting a VPN tunnel.
Additional Topics for IKE SA
This section provides more information about IKE SA.
Negotiation Mode
There are two negotiation modes--main mode and aggressive mode. Main mode provides better
security, while aggressive mode is faster.
Main mode takes six steps to establish an IKE SA.
Steps 1 - 2: The Zyxel Device sends its proposals to the remote IPSec router. The remote IPSec router
selects an acceptable proposal and sends it back to the Zyxel Device.
Steps 3 - 4: The Zyxel Device and the remote IPSec router exchange pre-shared keys for authentication
and participate in a Diffie-Hellman key exchange, based on the accepted DH key group, to establish a
shared secret.
Steps 5 - 6: Finally, the Zyxel Device and the remote IPSec router generate an encryption key (from the
shared secret), encrypt their identities, and exchange their encrypted identity information for
authentication.
In contrast, aggressive mode only takes three steps to establish an IKE SA. Aggressive mode does not
provide as much security because the identity of the Zyxel Device and the identity of the remote IPSec
router are not encrypted. It is usually used in remote-access situations, where the address of the initiator
is not known by the responder and both parties want to use pre-shared keys for authentication. For
example, the remote IPSec router may be a telecommuter who does not have a static IP address.
VPN, NAT, and NAT Traversal
In the following example, there is another router (A) between router X and router Y.
Table 219 VPN Example: Mismatching ID Type and Content
ZYXEL DEVICE REMOTE IPSEC ROUTER
Local ID type: E-mail Local ID type: IP
Local ID content: tom@yourcompany.com Local ID content: 1.1.1.2
Peer ID type: IP Peer ID type: E-mail
Peer ID content: 1.1.1.20 Peer ID content: tom@yourcompany.com
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
576
Figure 404 VPN/NAT Example
If router A does NAT, it might change the IP addresses, port numbers, or both. If router X and router Y try
to establish a VPN tunnel, the authentication fails because it depends on this information. The routers
cannot establish a VPN tunnel.
Most routers like router A now have an IPSec pass-thru feature. This feature helps router A recognize VPN
packets and route them appropriately. If router A has this feature, router X and router Y can establish a
VPN tunnel as long as the active protocol is ESP. (See Active Protocol on page 577 for more information
about active protocols.)
If router A does not have an IPSec pass-thru or if the active protocol is AH, you can solve this problem by
enabling NAT traversal. In NAT traversal, router X and router Y add an extra header to the IKE SA and
IPSec SA packets. If you configure router A to forward these packets unchanged, router X and router Y
can establish a VPN tunnel.
You have to do the following things to set up NAT traversal.
• Enable NAT traversal on the Zyxel Device and remote IPSec router.
• Configure the NAT router to forward packets with the extra header unchanged. (See the field
description for detailed information about the extra header.)
The extra header may be UDP port 500 or UDP port 4500, depending on the standard(s) the Zyxel Device
and remote IPSec router support.
X-Auth / Extended Authentication
X-Auth / Extended authentication is often used when multiple IPSec routers use the same VPN tunnel to
connect to a single IPSec router. For example, this might be used with telecommuters.
In extended authentication, one of the routers (the Zyxel Device or the remote IPSec router) provides a
user name and password to the other router, which uses a local user database and/or an external
server to verify the user name and password. If the user name or password is wrong, the routers do not
establish an IKE SA.
You can set up the Zyxel Device to provide a user name and password to the remote IPSec router, or
you can set up the Zyxel Device to check a user name and password that is provided by the remote
IPSec router.
If you use extended authentication, it takes four more steps to establish an IKE SA. These steps occur at
the end, regardless of the negotiation mode (steps 7-10 in main mode, steps 4-7 in aggressive mode).
A
XY
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
577
Certificates
It is possible for the Zyxel Device and remote IPSec router to authenticate each other with certificates. In
this case, you do not have to set up the pre-shared key, local identity, or remote identity because the
certificates provide this information instead.
• Instead of using the pre-shared key, the Zyxel Device and remote IPSec router check the signatures
on each other’s certificates. Unlike pre-shared keys, the signatures do not have to match.
• The local and peer ID type and content come from the certificates.
Note: You must set up the certificates for the Zyxel Device and remote IPSec router first.
IPSec SA Overview
Once the Zyxel Device and remote IPSec router have established the IKE SA, they can securely
negotiate an IPSec SA through which to send data between computers on the networks.
Note: The IPSec SA stays connected even if the underlying IKE SA is not available anymore.
This section introduces the key components of an IPSec SA.
Local Network and Remote Network
In an IPSec SA, the local network, the one(s) connected to the Zyxel Device, may be called the local
policy. Similarly, the remote network, the one(s) connected to the remote IPSec router, may be called
the remote policy.
Active Protocol
The active protocol controls the format of each packet. It also specifies how much of each packet is
protected by the encryption and authentication algorithms. IPSec VPN includes two active protocols,
AH (Authentication Header, RFC 2402) and ESP (Encapsulating Security Payload, RFC 2406).
Note: The Zyxel Device and remote IPSec router must use the same active protocol.
Usually, you should select ESP. AH does not support encryption, and ESP is more suitable with NAT.
Encapsulation
There are two ways to encapsulate packets. Usually, you should use tunnel mode because it is more
secure. Transport mode is only used when the IPSec SA is used for communication between the Zyxel
Device and remote IPSec router (for example, for remote management), not between computers on
the local and remote networks.
Note: The Zyxel Device and remote IPSec router must use the same encapsulation.
These modes are illustrated below.
Figure 405 VPN: Transport and Tunnel Mode Encapsulation
Original Packet IP Header TCP Header Data
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
578
In tunnel mode, the Zyxel Device uses the active protocol to encapsulate the entire IP packet. As a
result, there are two IP headers:
• Outside header: The outside IP header contains the IP address of the Zyxel Device or remote IPSec
router, whichever is the destination.
• Inside header: The inside IP header contains the IP address of the computer behind the Zyxel Device
or remote IPSec router. The header for the active protocol (AH or ESP) appears between the IP
headers.
In transport mode, the encapsulation depends on the active protocol. With AH, the Zyxel Device
includes part of the original IP header when it encapsulates the packet. With ESP, however, the Zyxel
Device does not include the IP header when it encapsulates the packet, so it is not possible to verify the
integrity of the source IP address.
IPSec SA Proposal and Perfect Forward Secrecy
An IPSec SA proposal is similar to an IKE SA proposal (see IKE SA Proposal on page 572), except that you
also have the choice whether or not the Zyxel Device and remote IPSec router perform a new DH key
exchange every time an IPSec SA is established. This is called Perfect Forward Secrecy (PFS).
If you enable PFS, the Zyxel Device and remote IPSec router perform a DH key exchange every time an
IPSec SA is established, changing the root key from which encryption keys are generated. As a result, if
one encryption key is compromised, other encryption keys remain secure.
If you do not enable PFS, the Zyxel Device and remote IPSec router use the same root key that was
generated when the IKE SA was established to generate encryption keys.
The DH key exchange is time-consuming and may be unnecessary for data that does not require such
security.
PFS is ignored in initial IKEv2 authentication but is used when re-authenticating.
Additional Topics for IPSec SA
This section provides more information about IPSec SA in your Zyxel Device.
Authentication and the Security Parameter Index (SPI)
For authentication, the Zyxel Device and remote IPSec router use the SPI, instead of pre-shared keys, ID
type and content. The SPI is an identification number.
Note: The Zyxel Device and remote IPSec router must use the same SPI.
Transport Mode Packet IP Header AH/ESP
Header
TCP Header Data
Tunnel Mode Packet IP Header AH/ESP
Header
IP Header TCP Header Data
Figure 405 VPN: Transport and Tunnel Mode Encapsulation
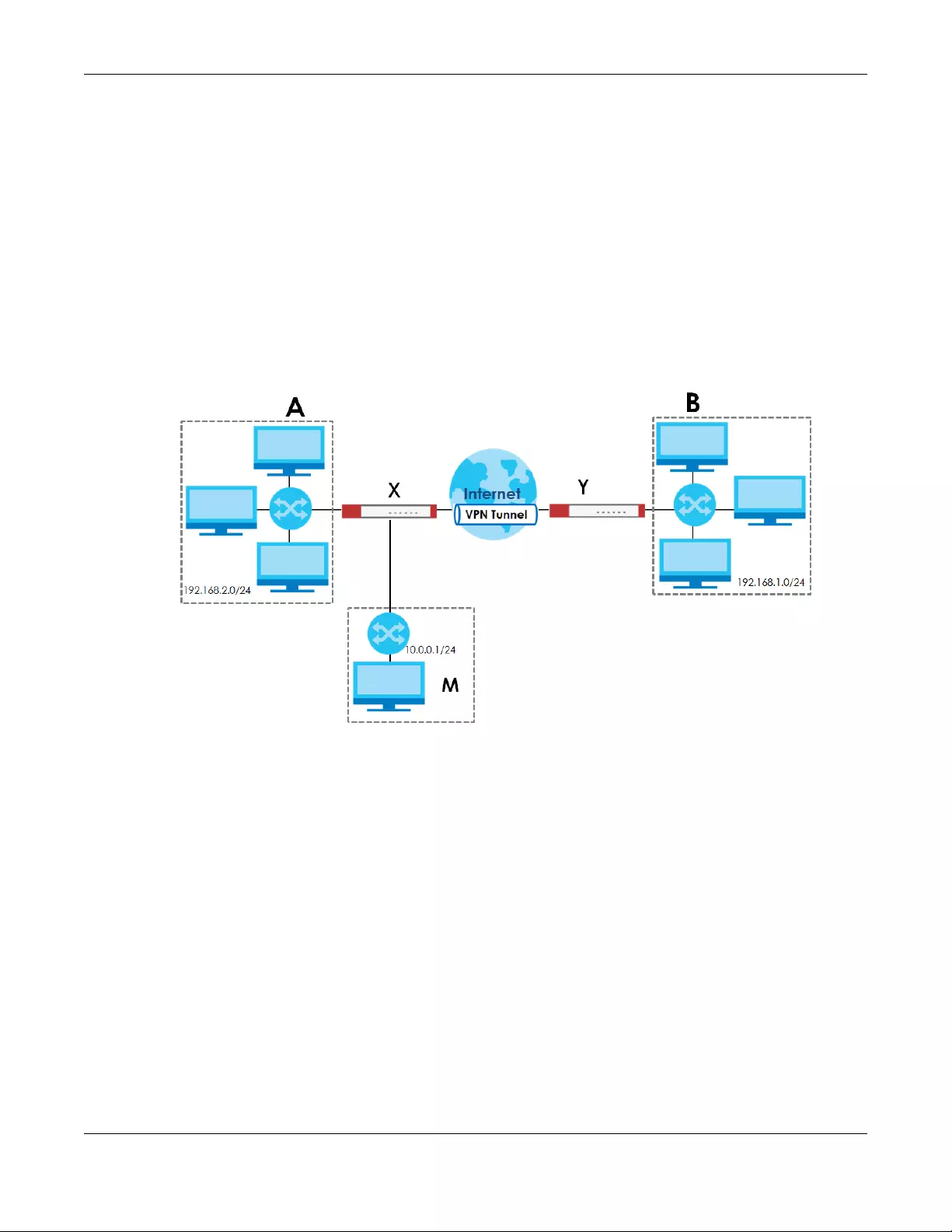
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
579
NAT for Inbound and Outbound Traffic
The Zyxel Device can translate the following types of network addresses in IPSec SA.
• Source address in outbound packets - this translation is necessary if you want the Zyxel Device to
route packets from computers outside the local network through the IPSec SA.
• Source address in inbound packets - this translation hides the source address of computers in the
remote network.
• Destination address in inbound packets - this translation is used if you want to forward packets (for
example, mail) from the remote network to a specific computer (like the mail server) in the local
network.
Each kind of translation is explained below. The following example is used to help explain each one.
Figure 406 VPN Example: NAT for Inbound and Outbound Traffic
Source Address in Outbound Packets (Outbound Traffic, Source NAT)
This translation lets the Zyxel Device route packets from computers that are not part of the specified
local network (local policy) through the IPSec SA. For example, in Figure 406 on page 579, you have to
configure this kind of translation if you want computer M to establish a connection with any computer in
the remote network (B). If you do not configure it, the remote IPSec router may not route messages for
computer M through the IPSec SA because computer M’s IP address is not part of its local policy.
To set up this NAT, you have to specify the following information:
• Source - the original source address; most likely, computer M’s network.
• Destination - the original destination address; the remote network (B).
• SNAT - the translated source address; the local network (A).
Source Address in Inbound Packets (Inbound Traffic, Source NAT)
You can set up this translation if you want to change the source address of computers in the remote
network. To set up this NAT, you have to specify the following information:
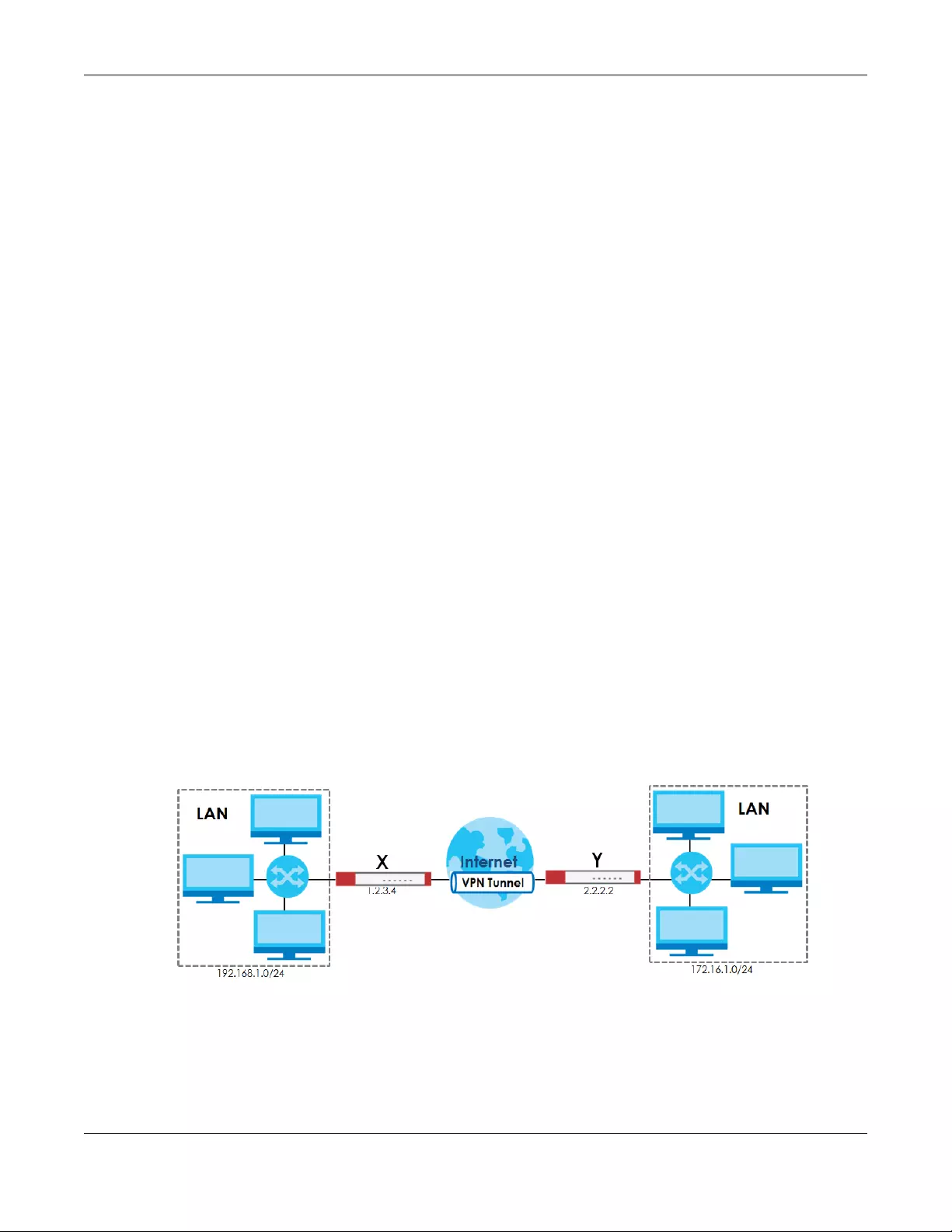
Chapter 30 IPSec VPN
USG/ZyWALL User’s Guide
580
• Source - the original source address; the remote network (B).
• Destination - the original destination address; the local network (A).
• SNAT - the translated source address; a different IP address (range of addresses) to hide the original
source address.
Destination Address in Inbound Packets (Inbound Traffic, Destination NAT)
You can set up this translation if you want the Zyxel Device to forward some packets from the remote
network to a specific computer in the local network. For example, in Figure 406 on page 579, you can
configure this kind of translation if you want to forward mail from the remote network to the mail server in
the local network (A).
You have to specify one or more rules when you set up this kind of NAT. The Zyxel Device checks these
rules similar to the way it checks rules for a security policy. The first part of these rules define the
conditions in which the rule apply.
• Original IP - the original destination address; the remote network (B).
• Protocol - the protocol [TCP, UDP, or both] used by the service requesting the connection.
• Original Port - the original destination port or range of destination ports; in Figure 406 on page 579, it
might be port 25 for SMTP.
The second part of these rules controls the translation when the condition is satisfied.
• Mapped IP - the translated destination address; in Figure 406 on page 579, the IP address of the mail
server in the local network (A).
• Mapped Port - the translated destination port or range of destination ports.
The original port range and the mapped port range must be the same size.
IPSec VPN Example Scenario
Here is an example site-to-site IPSec VPN scenario.
Figure 407 Site-to-site IPSec VPN Example

USG/ZyWALL User’s Guide
581
CHAPTER 31
SSL VPN
31.1 Overview
Use SSL VPN to allow users to use a web browser for secure remote user login. The remote users do not
need a VPN router or VPN client software.
31.1.1 What You Can Do in this Chapter
• Use the VPN > SSL VPN > Access Privilege screens (see Section 31.2 on page 582) to configure SSL
access policies.
• Use the Click VPN > SSL VPN > Global Setting screen (see Section 31.3 on page 586) to set the IP
address of the Zyxel Device (or a gateway device) on your network for full tunnel mode access, enter
access messages or upload a custom logo to be displayed on the remote user screen.
• Use the VPN > SSL VPN > SecuExtender screen (see Section 31.4 on page 588) to update and check
the current and latest version of the Security Extender.
31.1.2 What You Need to Know
Full Tunnel Mode
In full tunnel mode, a virtual connection is created for remote users with private IP addresses in the same
subnet as the local network. This allows them to access network resources in the same way as if they
were part of the internal network.
Figure 408 Network Access Mode: Full Tunnel Mode
SSL Access Policy
An SSL access policy allows the Zyxel Device to perform the following tasks:
• limit user access to specific applications or file sharing server on the network.
• allow user access to specific networks.
• assign private IP addresses and provide DNS/WINS server information to remote users to access
internal networks.
Web Mail File Share
Web-based Application
https://
Application Server
Non-Web
LAN (192.168.1.X)
192.168.1.100
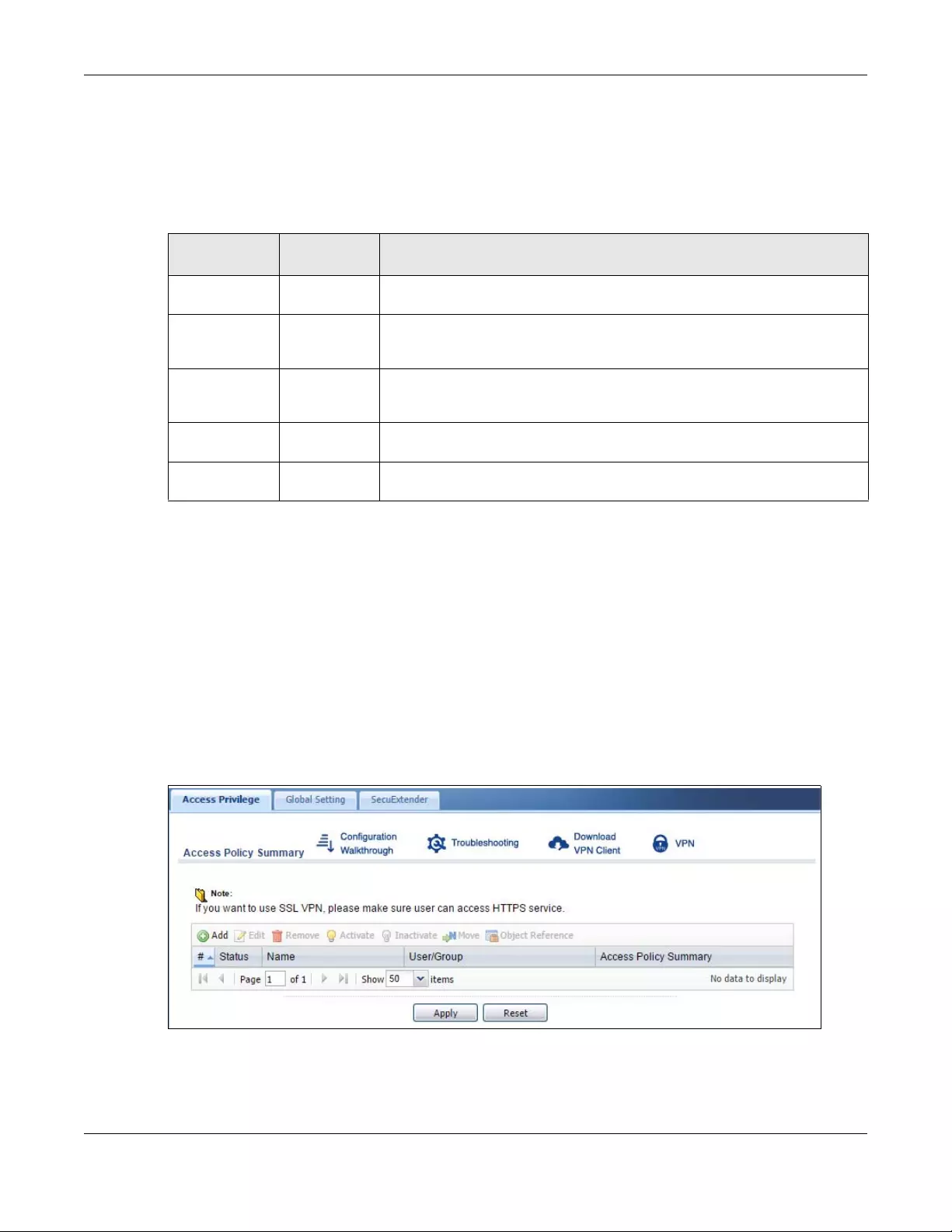
Chapter 31 SSL VPN
USG/ZyWALL User’s Guide
582
SSL Access Policy Objects
The SSL access policies reference the following objects. If you update this information, in response to
changes, the Zyxel Device automatically propagates the changes through the SSL policies that use the
object(s). When you delete an SSL policy, the objects are not removed.
You cannot delete an object that is referenced by an SSL access policy. To delete the object, you must
first unassociate the object from the SSL access policy.
31.2 The SSL Access Privilege Screen
Click VPN > SSL VPN to open the Access Privilege screen. This screen lists the configured SSL access
policies.
Click on the icons to go to the OneSecurity.com website where there is guidance on configuration
walkthroughs, troubleshooting and other information.
Figure 409 VPN > SSL VPN > Access Privilege
Table 220 Objects
OBJECT TYPE OBJECT
SCREEN DESCRIPTION
User Accounts User Account/
User Group
Configure a user account or user group to which you want to apply this SSL
access policy.
Application SSL
Application
Configure an SSL application object to specify the type of application and the
address of the local computer, server, or web site SSL users are to be able to
access.
IP Pool Address Configure an address object that defines a range of private IP addresses to
assign to user computers so they can access the internal network through a
VPN connection.
Server
Addresses
Address Configure address objects for the IP addresses of the DNS and WINS servers that
the Zyxel Device sends to the VPN connection users.
VPN Network Address Configure an address object to specify which network segment users are
allowed to access through a VPN connection.
Chapter 31 SSL VPN
USG/ZyWALL User’s Guide
583
The following table describes the labels in this screen.
31.2.1 The SSL Access Privilege Policy Add/Edit Screen
To create a new or edit an existing SSL access policy, click the Add or Edit icon in the Access Privilege
screen.
Table 221 VPN > SSL VPN > Access Privilege
LABEL DESCRIPTION
Access Policy
Summary
This screen shows a summary of SSL VPN policies created.
Click on the VPN icon to go to the Zyxel VPN Client product page at the Zyxel website.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after the
selected entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the entry’s
settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove it
before doing so.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Move To move an entry to a different number in the list, click the Move icon. In the field that appears,
specify the number to which you want to move the interface.
Object
References
Select an entry and click Object References to open a screen that shows which settings use the
entry. Click Refresh to update information on this screen.
# This field displays the index number of the entry.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
Name This field displays the descriptive name of the SSL access policy for identification purposes.
User/Group This field displays the user account or user group name(s) associated to an SSL access policy.
This field displays up to three names.
Access Policy
Summary
This field displays details about the SSL application object this policy uses including its name, type,
and address.
Apply Click Apply to save the settings.
Reset Click Reset to discard all changes.
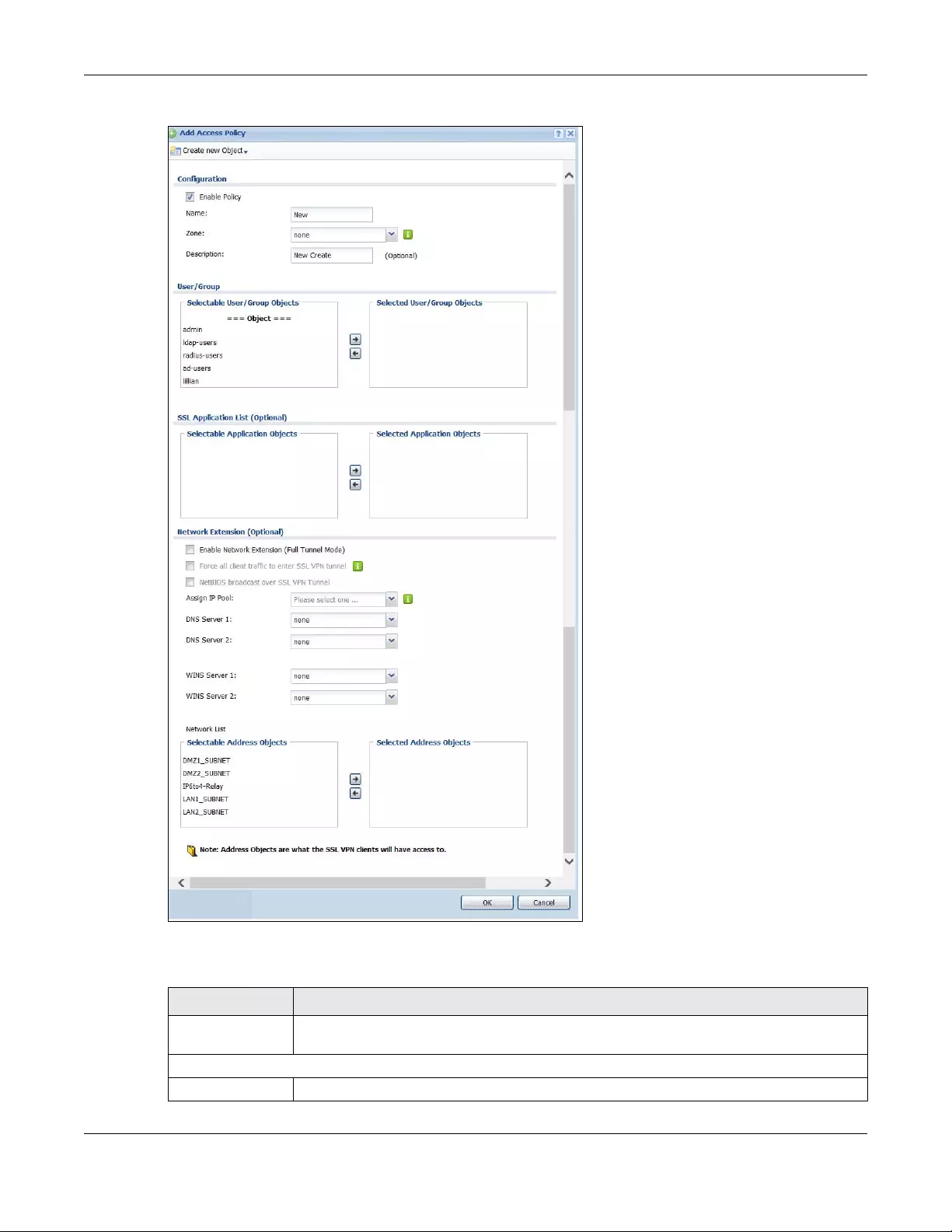
Chapter 31 SSL VPN
USG/ZyWALL User’s Guide
584
Figure 410 VPN > SSL VPN > Add/Edit
The following table describes the labels in this screen.
Table 222 VPN > SSL VPN > Access Privilege > Add/Edit
LABEL DESCRIPTION
Create new
Object
Use to configure any new settings objects that you need to use in this screen.
Configuration
Enable Policy Select this option to activate this SSL access policy.
Chapter 31 SSL VPN
USG/ZyWALL User’s Guide
585
Name Enter a descriptive name to identify this policy. You can enter up to 31 characters (“a-z”, A-Z”,
“0-9”) with no spaces allowed.
Zone Select the zone to which to add this SSL access policy. You use zones to apply security settings
such as security policy and remote management.
Description Enter additional information about this SSL access policy. You can enter up to 60 characters
("0-9", "a-z", "A-Z", "-" and "_").
User/Group The Selectable User/Group Objects list displays the name(s) of the user account and/or user
group(s) to which you have not applied an SSL access policy yet.
To associate a user or user group to this SSL access policy, select a user account or user group
and click the right arrow button to add to the Selected User/Group Objects list. You can
select more than one name.
To remove a user or user group, select the name(s) in the Selected User /Group Obje cts list and
click the left arrow button.
Note: Although you can select admin and limited-admin accounts in this screen,
they are reserved for device configuration only. You cannot use them to
access the SSL VPN portal.
SSL Application List
(Optional)
The Selectable Application Objects list displays the name(s) of the SSL application(s) you can
select for this SSL access policy.
To associate an SSL application to this SSL access policy, select a name and click the right
arrow button to add to the Selected Application Objects list. You can select more than one
application.
To remove an SSL application, select the name(s) in the Selected Application Objects list and
click the left arrow button.
Note: To allow access to shared files on a Windows 7 computer, within Windows 7
you must enable sharing on the folder and also go to the Network and
Sharing Center’s Advanced sharing settings and turn on the current network
profile’s file and printer sharing.
Network Extension (Optional)
Enable Network
Extension
Select this option to create a VPN tunnel between the authenticated users and the internal
network. This allows the users to access the resources on the network as if they were on the
same local network. This includes access to resources not supported by SSL application
objects. For example this lets users Telnet to the internal network even though the Zyxel Device
does not have SSL application objects for Telnet.
Clear this option to disable this feature. Users can only access the applications as defined by
the VPN tunnel’s selected SSL application settings and the remote user computers are not
made to be a part of the local network.
Force all client
traffic to SSL VPN
tunnel
Select this to send all traffic from the SSL VPN clients through the SSL VPN tunnel. This replaces
the default gateway of the SSL VPN clients with the SSL VPN gateway.
NetBIOS
broadcast over
SSL VPN Tunnel
Select this to search for a remote computer and access its applications as if it was in a Local
Area Network. The user can find a computer not only by its IP address but also by computer
name.
Assign IP Pool Define a separate pool of IP addresses to assign to the SSL users. Select it here.
The SSL VPN IP pool should not overlap with IP addresses on the Zyxel Device's local networks
(LAN and DMZ for example), the SSL user's network, or the networks you specify in the SSL VPN
Network List.
DNS/WINS Server
1..2
Select the name of the DNS or WINS server whose information the Zyxel Device sends to the
remote users. This allows them to access devices on the local network using domain names
instead of IP addresses.
Table 222 VPN > SSL VPN > Access Privilege > Add/Edit (continued)
LABEL DESCRIPTION
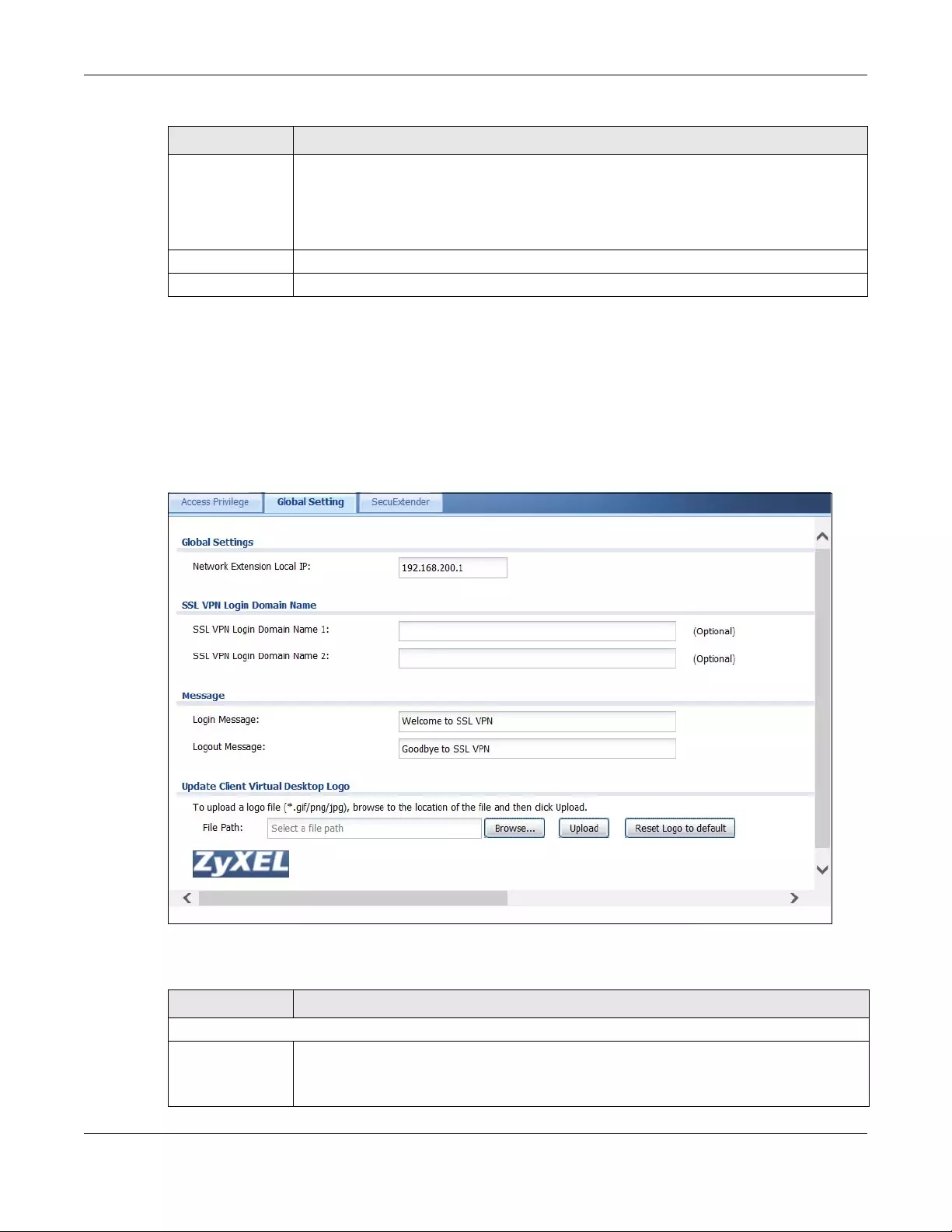
Chapter 31 SSL VPN
USG/ZyWALL User’s Guide
586
31.3 The SSL Global Setting Screen
Click VPN > SSL VPN and click the Global Setting tab to display the following screen. Use this screen to
set the IP address of the Zyxel Device (or a gateway device) on your network for full tunnel mode
access, enter access messages or upload a custom logo to be displayed on the remote user screen.
Figure 411 VPN > SSL VPN > Global Setting
The following table describes the labels in this screen.
Network List To allow user access to local network(s), select a network name in the Selectable Address
Objects list and click the right arrow button to add to the Selecte d Address Objects list. You
can select more than one network.
To block access to a network, select the network name in the Selected Address Objects list
and click the left arrow button.
OK Click OK to save the changes and return to the main Access Privilege screen.
Cancel Click Cancel to discard all changes and return to the main Access Privilege screen.
Table 222 VPN > SSL VPN > Access Privilege > Add/Edit (continued)
LABEL DESCRIPTION
Table 223 VPN > SSL VPN > Global Setting
LABEL DESCRIPTION
Global Setting
Network Extension
Local IP
Specify the IP address of the Zyxel Device (or a gateway device) for full tunnel mode SSL VPN
access.
Leave this field to the default settings unless it conflicts with another interface.
Chapter 31 SSL VPN
USG/ZyWALL User’s Guide
587
31.3.1 How to Upload a Custom Logo
Follow the steps below to upload a custom logo to display on the remote user SSL VPN screens.
1Click VPN > SSL VPN and click the Global Setting tab to display the configuration screen.
2Click Browse to locate the logo graphic. Make sure the file is in GIF, JPG, or PNG format.
3Click Apply to start the file transfer process.
4Log in as a user to verify that the new logo displays properly.
The following shows an example logo on the remote user screen.
SSL VPN Login Domain Name
SSL VPN Login
Domain Name 1/2
Specify a full domain name for users to use for SSL VPN login. The domain name must be
registered to one of the Zyxel Device’s IP addresses or be one of the Zyxel Device’s DDNS
entries. You can specify up to two domain names so you could use one domain name for
each of two WAN ports. For example, www.zyxel.com is a fully qualified domain name where
“www” is the host.
The Zyxel Device displays the normal login screen without the button for logging into the Web
Configurator.
Message
Login Message Specify a message to display on the screen when a user logs in and an SSL VPN connection is
established successfully. You can enter up to 60 characters (0-9, a-z, A-Z, '()+,/:=?;!*#@$_%-")
with spaces allowed.
Logout Message Specify a message to display on the screen when a user logs out and the SSL VPN connection
is terminated successfully. You can enter up to 60 characters (0-9, a-z, A-Z, '()+,/:=?;!*#@$_%-")
with spaces allowed.
Update Client
Virtual Desktop
Logo
You can upload a graphic logo to be displayed on the web browser on the remote user
computer. The Zyxel company logo is the default logo.
Specify the location and file name of the logo graphic or click Browse to locate it.
Note: The logo graphic must be GIF, JPG, or PNG format. The graphic should use a
resolution of 103 x 29 pixels to avoid distortion when displayed. The Zyxel
Device automatically resizes a graphic of a different resolution to 103 x 29
pixels. The file size must be 100 kilobytes or less. Transparent background is
recommended.
Browse Click Browse to locate the graphic file on your computer.
Upload Click Upload to transfer the specified graphic file from your computer to the Zyxel Device.
Reset Logo to
Default
Click Reset Logo to Default to display the Zyxel company logo on the remote user’s web
browser.
Apply Click Apply to save the changes and/or start the logo file upload process.
Reset Click Reset to return the screen to its last-saved settings.
Table 223 VPN > SSL VPN > Global Setting (continued)
LABEL DESCRIPTION
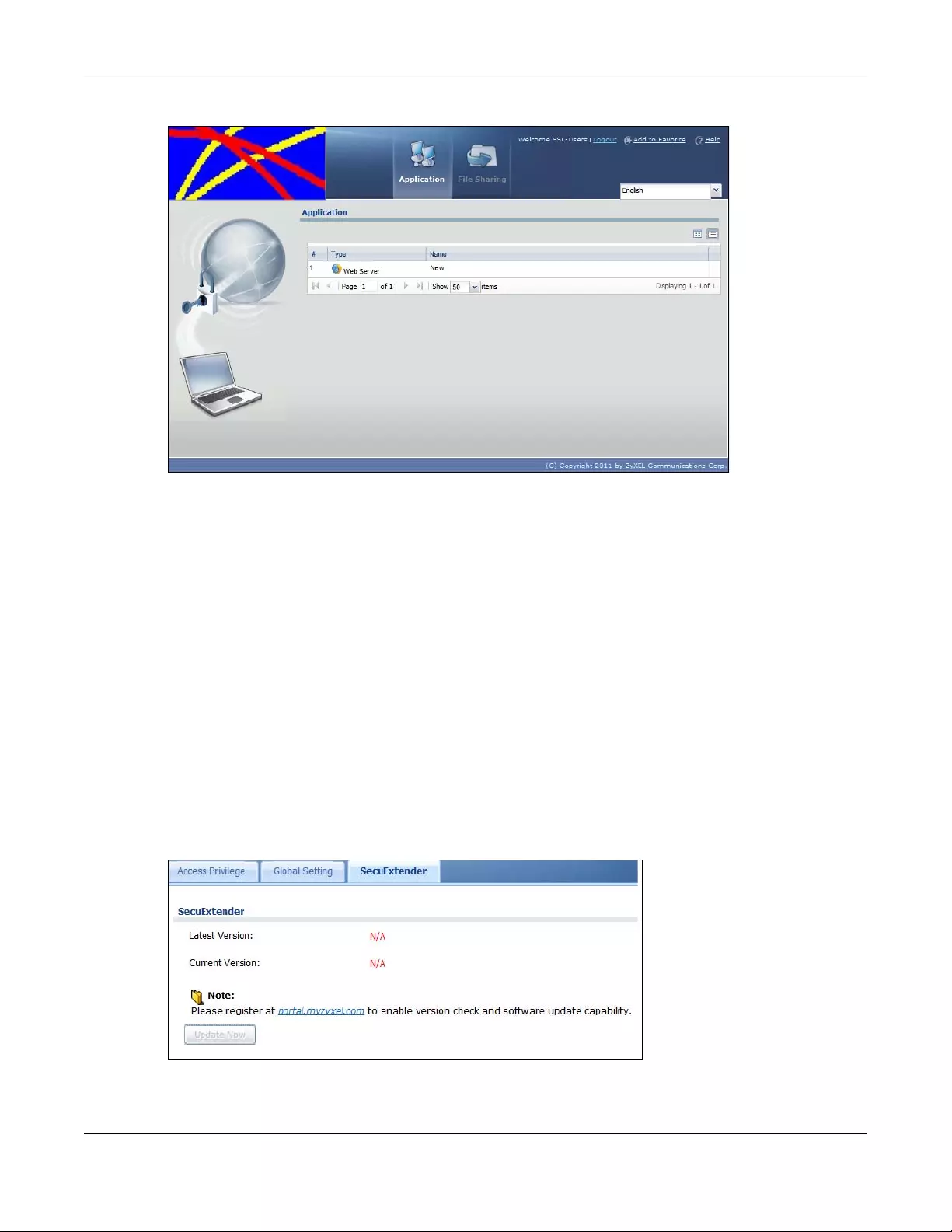
Chapter 31 SSL VPN
USG/ZyWALL User’s Guide
588
Figure 412 Example Logo Graphic Display
31.4 Zyxel Device SecuExtender
The Zyxel Device automatically loads the Zyxel Device SecuExtender client program to your computer
after a successful login to an SSL VPN tunnel with network extension support enabled. The Zyxel Device
SecuExtender lets you:
• Access servers, remote desktops and manage files as if you were on the local network.
• Use applications like e-mail, file transfer, and remote desktop programs directly without using a
browser. For example, you can use Outlook for e-mail instead of the Zyxel Device’s web-based e-mail.
• Use applications, even proprietary applications, for which the Zyxel Device does not offer SSL
application objects.
The applications must be installed on your computer. For example, to use the VNC remote desktop
program, you must have the VNC client installed on your computer. Please refer to the SecuExtender
chapter for details.
Figure 413 Configuration > VPN > SSL VPN > SecuExtender.
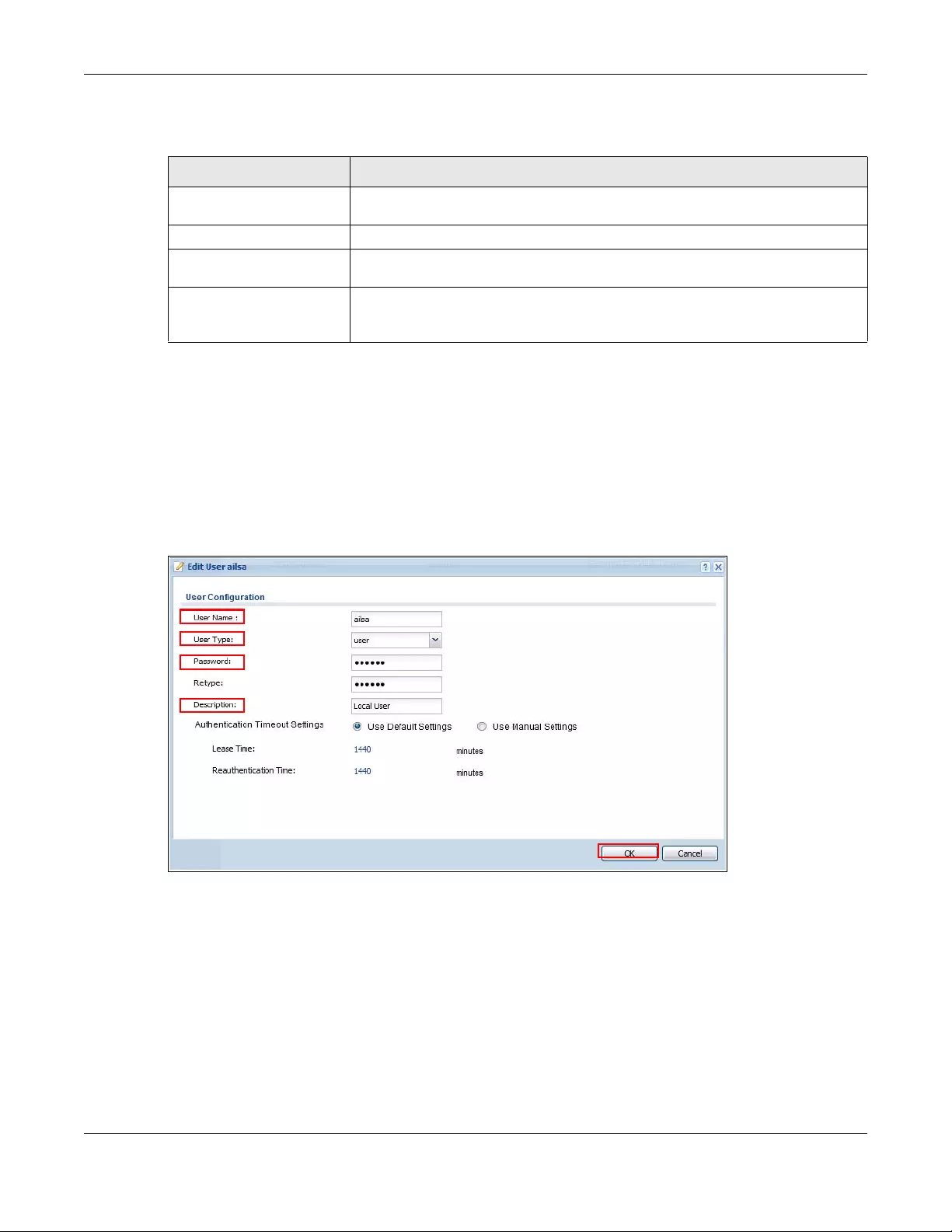
Chapter 31 SSL VPN
USG/ZyWALL User’s Guide
589
The following table describes the labels in this screen.
31.4.1 Example: Configure Zyxel Device for SecuExtender
Make these configurations on the Zyxel Device to allow the remote user to access resources behind the
Zyxel Device using SecuExtender. These steps can be performed in any order.
1Create a user that can log into the Zyxel Device. Using the Zyxel Device web configurator, go to
Configuration > Object > User > Add and substitute your information for the information shown in the
following example.
Figure 414 Create a User
2Next create an SSL VPN Access Privilege policy substituting your information for the information shown in
the following example. Using the Zyxel Device web configurator, go to Configuration > VPN > SSL VPN >
Access Privilege > Add.
Table 224 Configuration > VPN > SSL VPN > SecuExtender
LABEL DESCRIPTION
Latest Version This displays the latest version of the Zyxel Device Security SecuExtender that is
available.
Current Version This displays the current version of SecuExtender that is installed in the Zyxel Device.
Note: You need to register first at portal.myzyxel.com to download the latest version of
SecuExtender.
Update Now The Zyxel Device periodically checks if there’s a later version of SecuExtender at the
portal. The Update Now button is enabled when there is.Click Update Now to get the
latest version of SecuExtender.
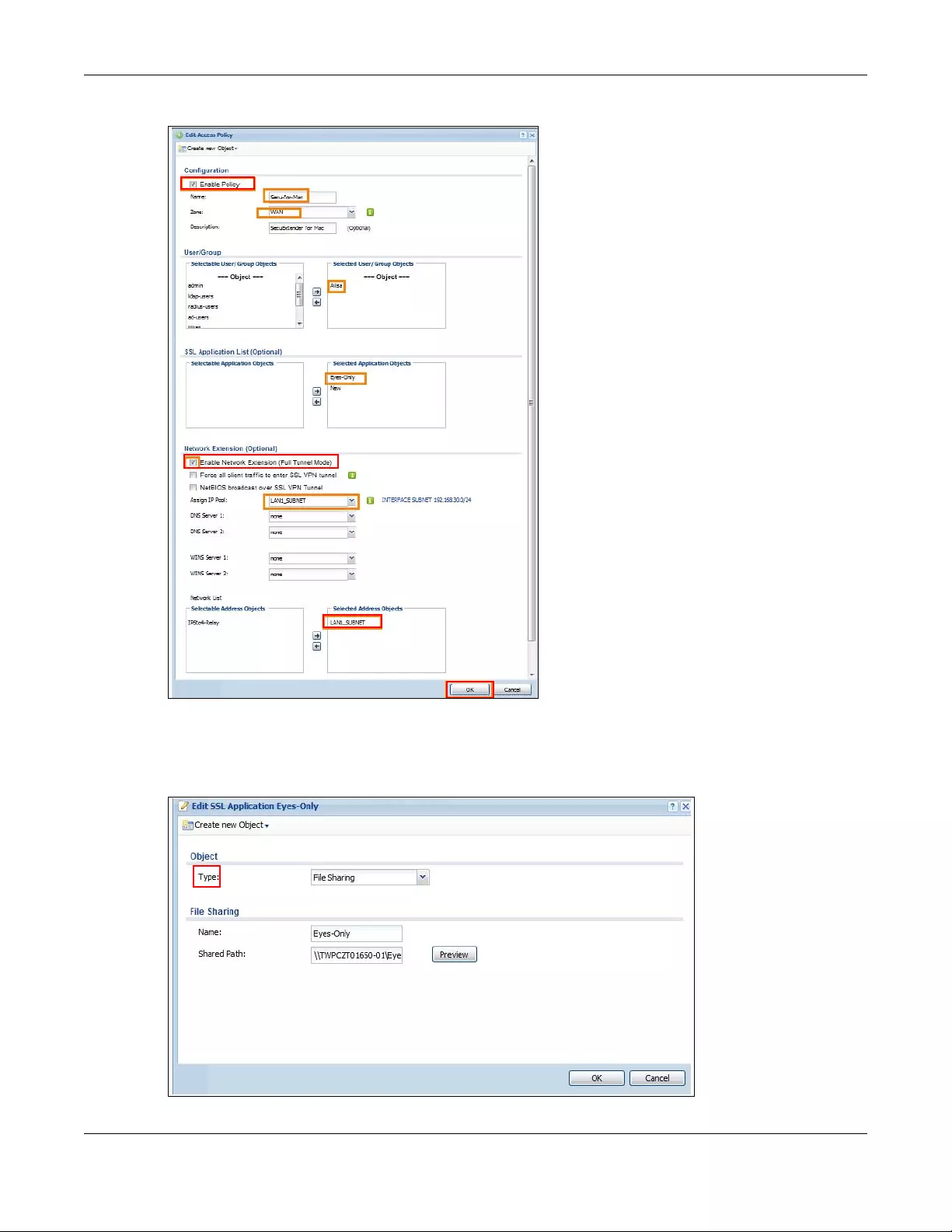
Chapter 31 SSL VPN
USG/ZyWALL User’s Guide
590
Figure 415 Create an SSL VPN Access Privilege Policy
3Then create File Sharing and Web Application SSL Application objects. Using the Zyxel Device web
configurator, go to Configuration > Object > SSL Application > Add and select the Type accordingly.
Substitute your information for the information shown in the following example.
Figure 416 Create a File Sharing SSL Application Object
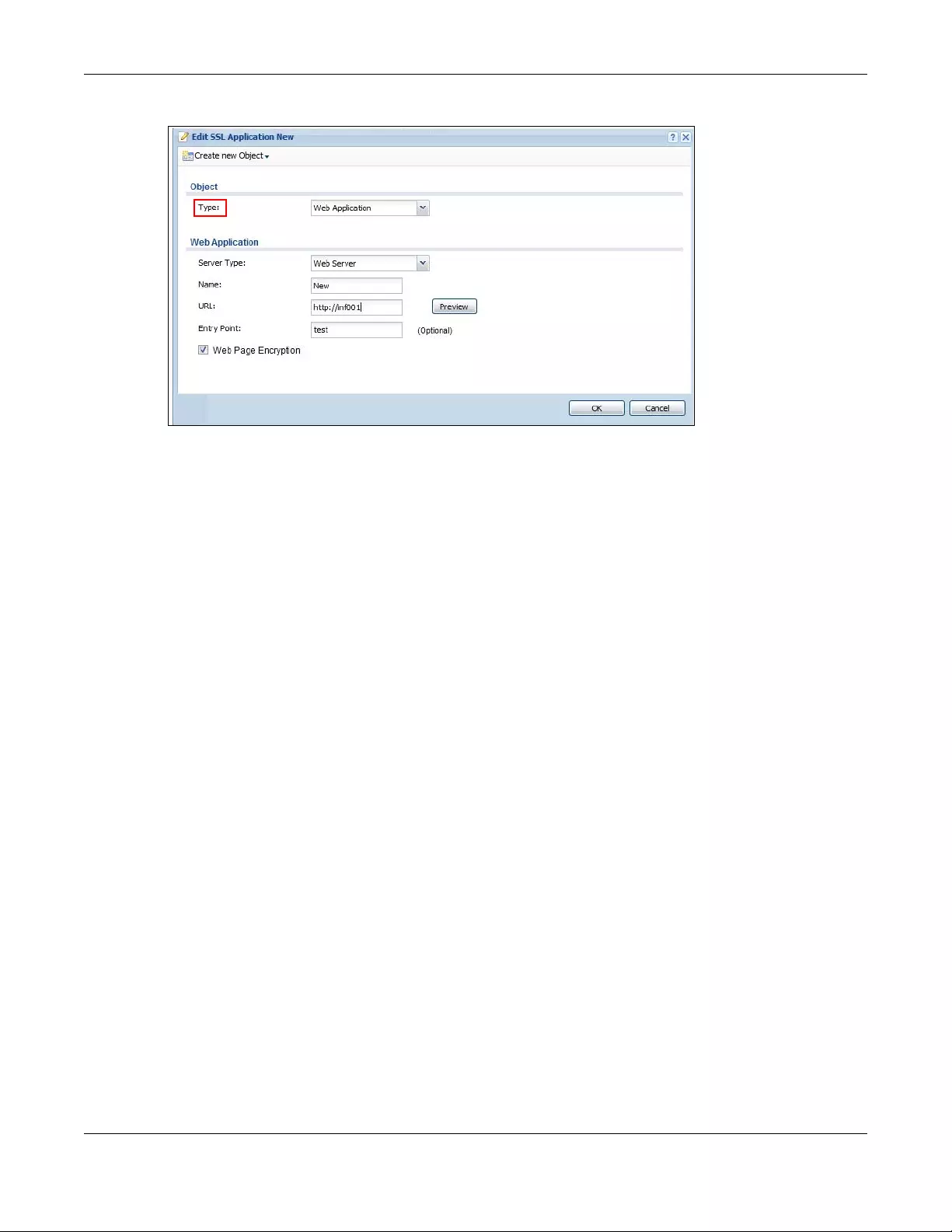
Chapter 31 SSL VPN
USG/ZyWALL User’s Guide
591
Create a Web Application SSL Application Object
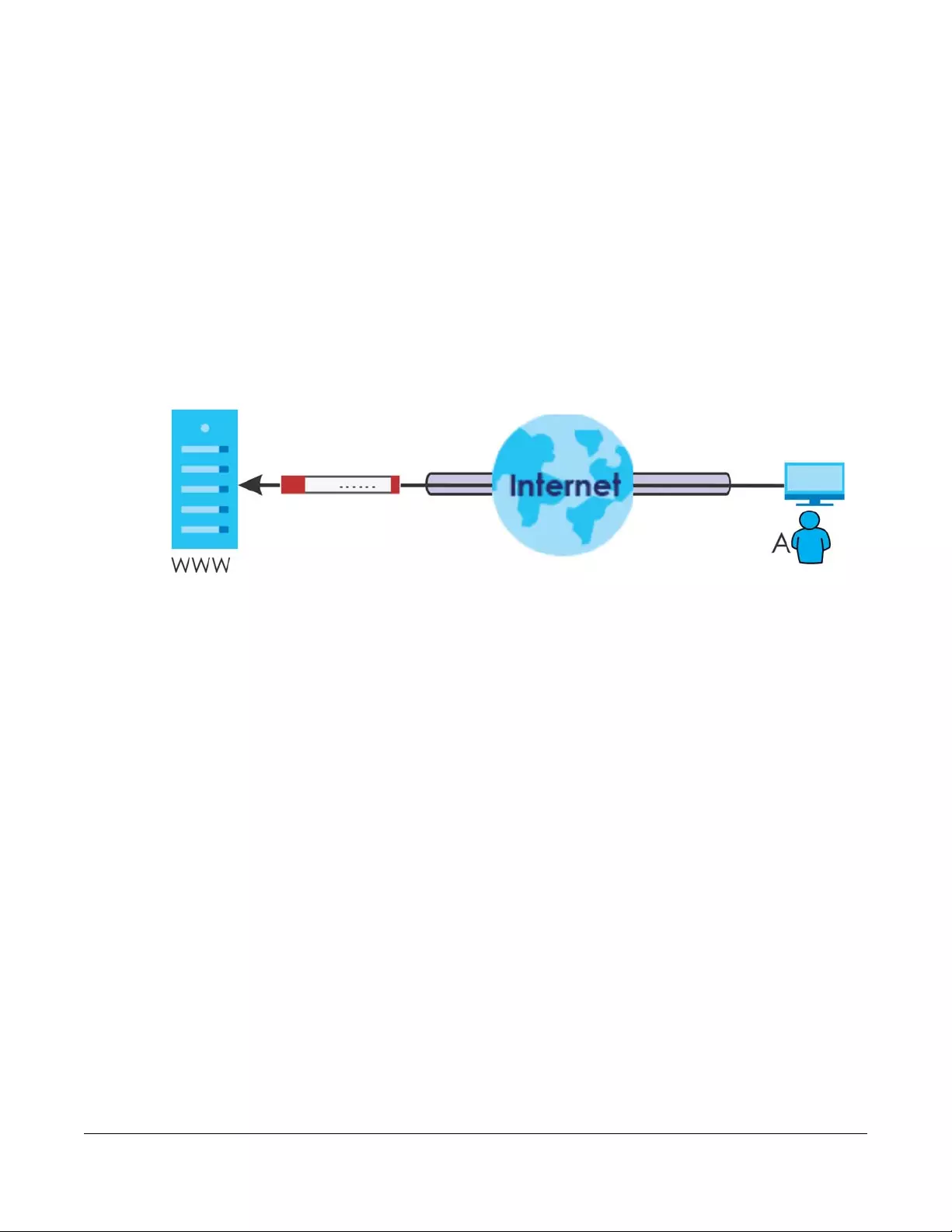
USG/ZyWALL User’s Guide
592
CHAPTER 32
SSL User Screens
32.1 Overview
This chapter introduces the remote user SSL VPN screens. The following figure shows a network example
where a remote user (A) logs into the Zyxel Device from the Internet to access the web server (WWW) on
the local network.
Figure 417 SSL User Network Example
32.1.1 What You Need to Know
The Zyxel Device can use SSL VPN to provide secure connections to network resources such as
applications, files, intranet sites or e-mail through a web-based interface and using Microsoft Outlook
Web Access (OWA).
Network Resource Access Methods
As a remote user, you can access resources on the local network using one of the following methods.
• Using a supported web browser
Once you have successfully logged in through the Zyxel Device, you can access intranet sites, web-
based applications, or web-based e-mails using one of the supported web browsers.
• Using the Zyxel Device SecuExtender client
Once you have successfully logged into the Zyxel Device, if the SSL VPN access policy has network
extension enabled the Zyxel Device automatically loads the Zyxel Device SecuExtender client
program to your computer. With the Zyxel Device SecuExtender, you can access network resources,
remote desktops and manage files as if you were on the local network. See Chapter 33 on page 605
for more on the Zyxel Device SecuExtender.
System Requirements
Here are the browser and computer system requirements for remote user access.
• Windows 7 (32 or 64-bit), Vista (32 or 64-bit), 2003 (32-bit), XP (32-bit), or 2000 (32-bit)

Chapter 32 SSL User Screens
USG/ZyWALL User’s Guide
593
• Internet Explorer 7 and above or Firefox 1.5 and above
• Using RDP requires Internet Explorer
• Sun’s Runtime Environment (JRE) version 1.6 or later installed and enabled.
Required Information
A remote user needs the following information from the network administrator to log in and access
network resources.
• the domain name or IP address of the Zyxel Device
• the login account user name and password
• if also required, the user name and/or password to access the network resource
Certificates
The remote user’s computer establishes an HTTPS connection to the Zyxel Device to access the login
screen. If instructed by your network administrator, you must install or import a certificate (provided by
the Zyxel Device or your network administrator).
Finding Out More
See Chapter 31 on page 581 for how to configure SSL VPN on the Zyxel Device.
32.2 Remote SSL User Login
This section shows you how to access and log into the network through the Zyxel Device. Example
screens for Internet Explorer are shown.
1Open a web browser and enter the web site address or IP address of the Zyxel Device. For example,
“http://sslvpn.mycompany.com”.
Figure 418 Enter the Address in a Web Browser
2Click OK or Yes if a security screen displays.
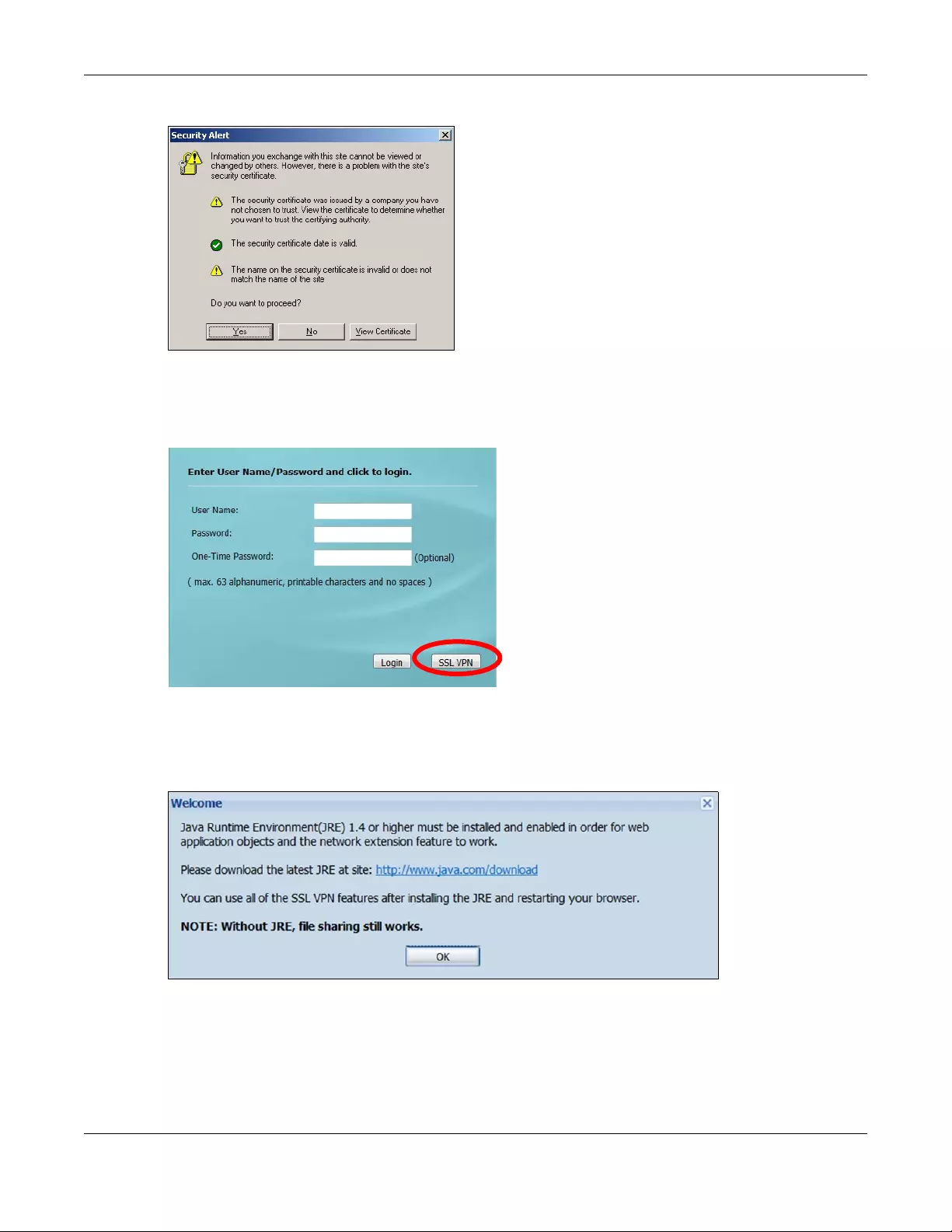
Chapter 32 SSL User Screens
USG/ZyWALL User’s Guide
594
Figure 419 Login Security Screen
3A login screen displays. Enter the user name and password of your login account. If a token password is
also required, enter it in the One-Time Password field. Click SSL VPN to log in and establish an SSL VPN
connection to the network to access network resources.
Figure 420 Login Screen
4Your computer starts establishing a secure connection to the Zyxel Device after a successful login. This
may take up to two minutes. If you get a message about needing Java, download and install it and
restart your browser and re-login. If a certificate warning screen displays, click OK, Yes or Continue.
Figure 421 Java Needed Message
5The Zyxel Device tries to install the SecuExtender client. As shown next, you may have to click some pop-
ups to get your browser to allow the installation.
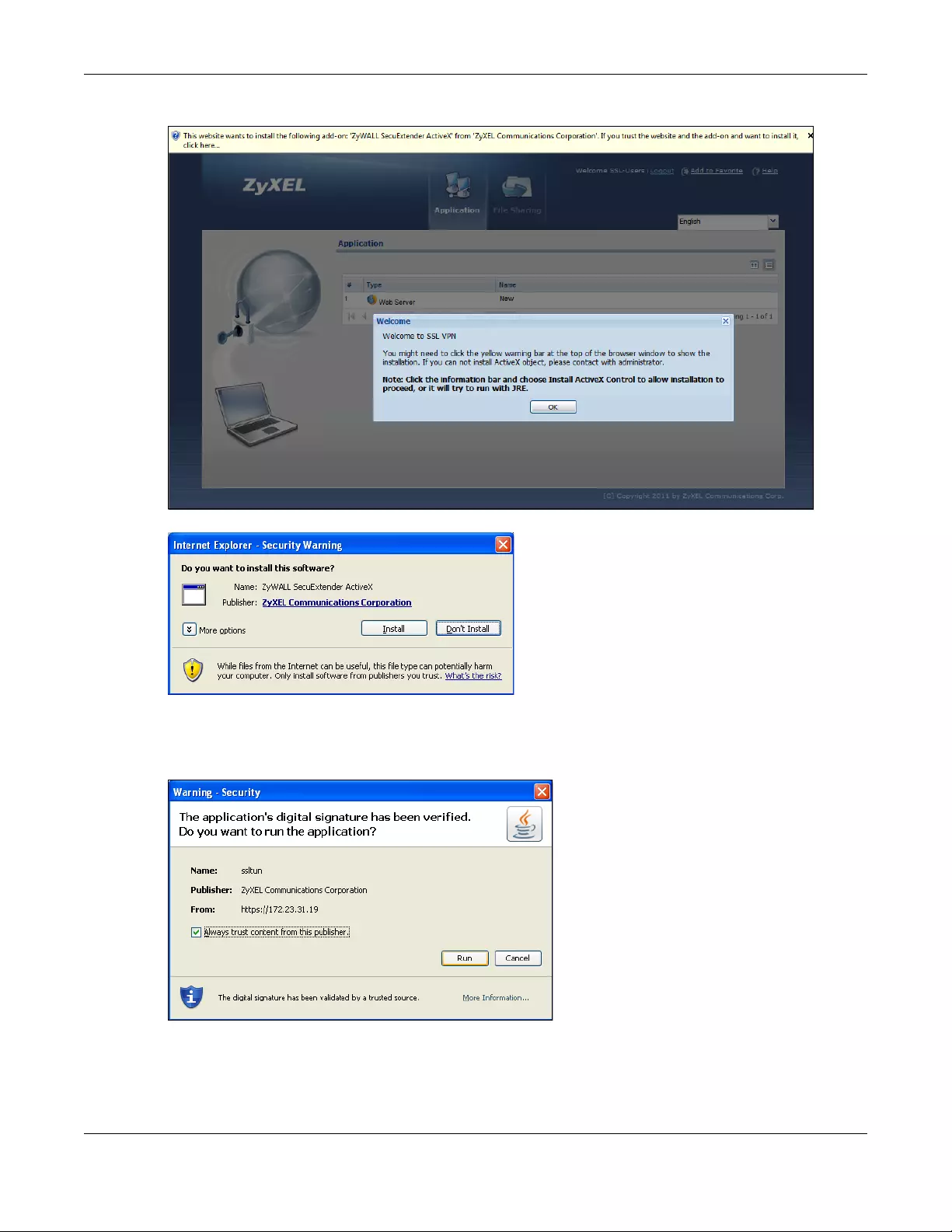
Chapter 32 SSL User Screens
USG/ZyWALL User’s Guide
595
Figure 422 Active X Object Installation Blocked by Browser
Figure 423 SecuExtender Blocked by Internet Explorer
6The Zyxel Device tries to run the “ssltun” application. You may need to click something to get your
browser to allow this. In Internet Explorer, click Run.
Figure 424 SecuExtender Progress
7Click Next to use the setup wizard to install the SecuExtender client on your computer.
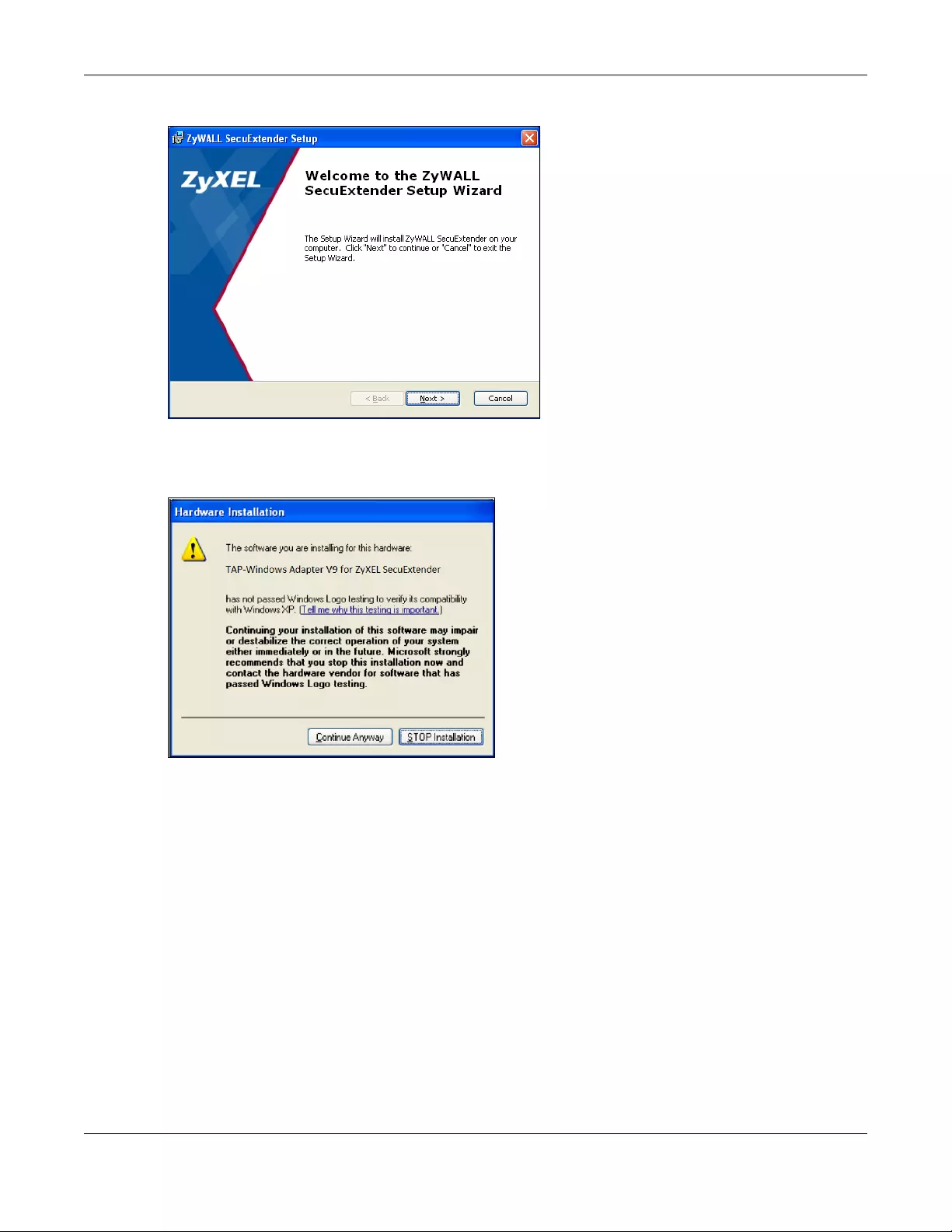
Chapter 32 SSL User Screens
USG/ZyWALL User’s Guide
596
Figure 425 SecuExtender Progress
8If a screen like the following displays, click Continue Anyway to finish installing the SecuExtender client
on your computer.
Figure 426 Installation Warning
9The Application screen displays showing the list of resources available to you. See Figure 427 on page
597 for a screen example.
Note: Available resource links vary depending on the configuration your network
administrator made.
32.3 The SSL VPN User Screens
This section describes the main elements in the remote user screens.
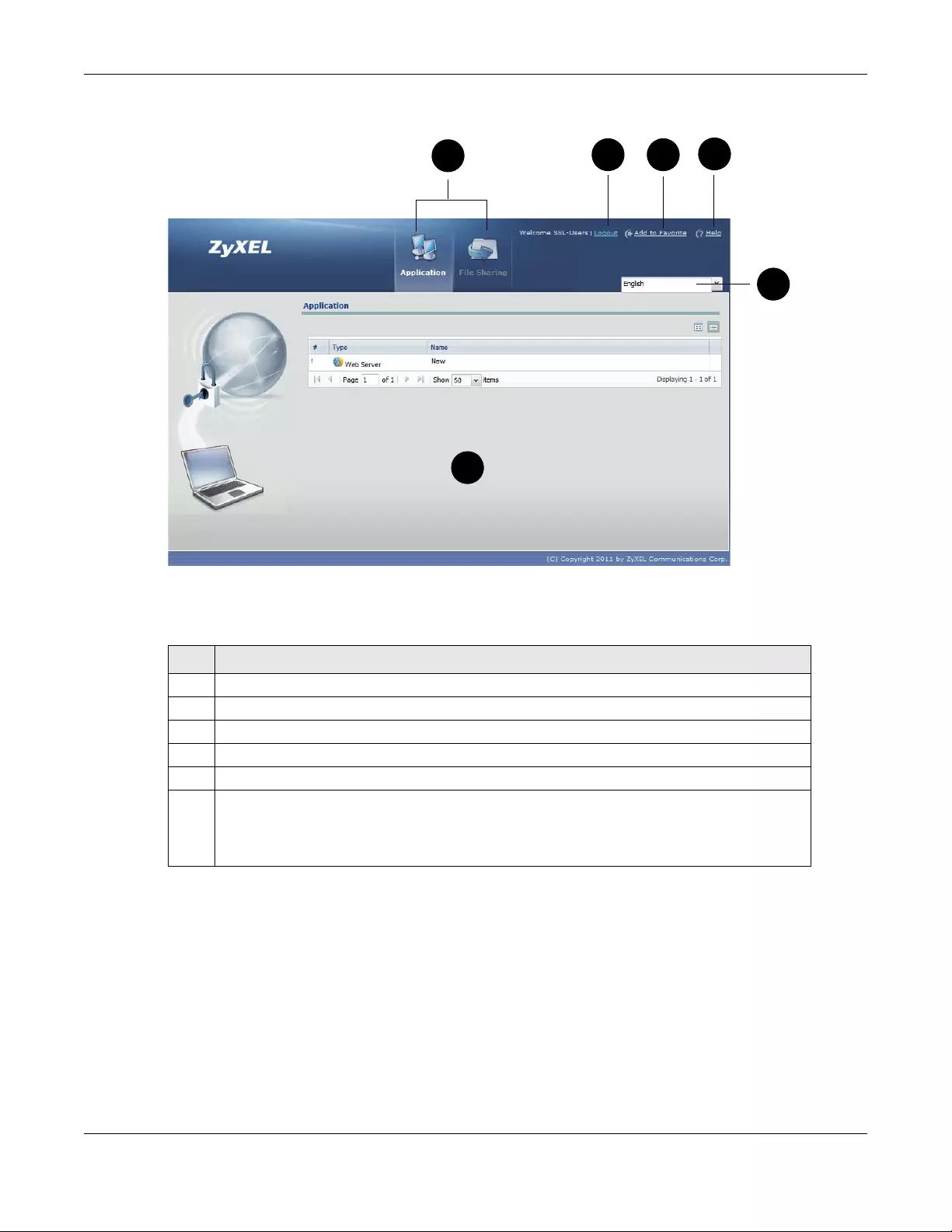
Chapter 32 SSL User Screens
USG/ZyWALL User’s Guide
597
Figure 427 Remote User Screen
The following table describes the various parts of a remote user screen.
32.4 Bookmarking the Zyxel Device
You can create a bookmark of the Zyxel Device by clicking the Add to Favorite icon. This allows you to
access the Zyxel Device using the bookmark without having to enter the address every time.
1In any remote user screen, click the Add to Favorite icon.
2A screen displays. Accept the default name in the Name field or enter a descriptive name to identify this
link.
Table 225 Remote User Screen Overview
# DESCRIPTION
1 Click on a menu tab to go to the Application or File Sharing screen.
2 Click this icon to log out and terminate the secure connection.
3 Click this icon to create a bookmark to the SSL VPN user screen in your web browser.
4 Click this icon to display the on-line help window.
5 Select your preferred language for the interface.
6 This part of the screen displays a list of the resources available to you.
In the Application screen, click on a link to access or display the access method.
In the File Sharing screen, click on a link to open a file or directory.
234
5
1
6
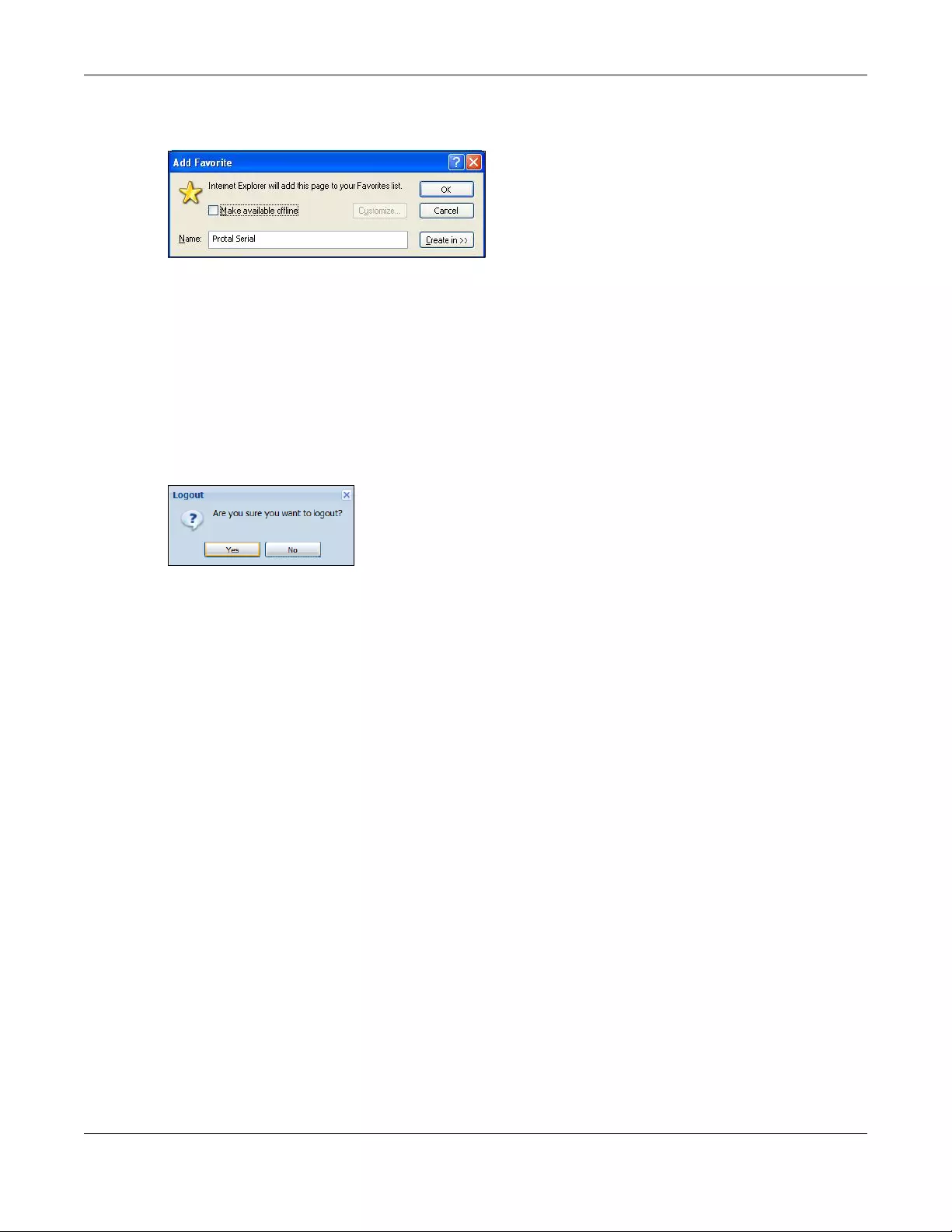
Chapter 32 SSL User Screens
USG/ZyWALL User’s Guide
598
3Click OK to create a bookmark in your web browser.
Figure 428 Add Favorite
32.5 Logging Out of the SSL VPN User Screens
To properly terminate a connection, click on the Logout icon in any remote user screen.
1Click the Logout icon in any remote user screen.
2A prompt window displays. Click OK to continue.
Figure 429 Logout: Prompt
32.6 SSL User Application Screen
Use the Application tab’s screen to access web-based applications (such as web sites and e-mail) on
the network through the SSL VPN connection. Which applications you can access depends on the Zyxel
Device’s configuration.
The Name field displays the descriptive name for an application. The Type field displays whether the
application is a web site (Web Server) or web-based e-mail using Microsoft Outlook Web Access (OWA).
To access a web-based application, simply click a link in the Application screen to display the web
screen in a separate browser window.
Chapter 32 SSL User Screens
USG/ZyWALL User’s Guide
599
Figure 430 Application
32.7 SSL User File Sharing
The File Sharing screen lets you access files on a file server through the SSL VPN connection. Use it to
display and access shared files/folders on a file server.
You can also perform the following actions:
• Access a folder.
• Open a file (if your web browser cannot open the file, you are prompted to download it).
• Save a file to your computer.
• Create a new folder.
• Rename a file or folder.
• Delete a file or folder.
• Upload a file.
Note: Available actions you can perform in the File Sharing screen vary depending on the
rights granted to you on the file server.
32.7.1 The Main File Sharing Screen
The first File Sharing screen displays the name(s) of the shared folder(s) available. The following figure
shows an example with one file share.
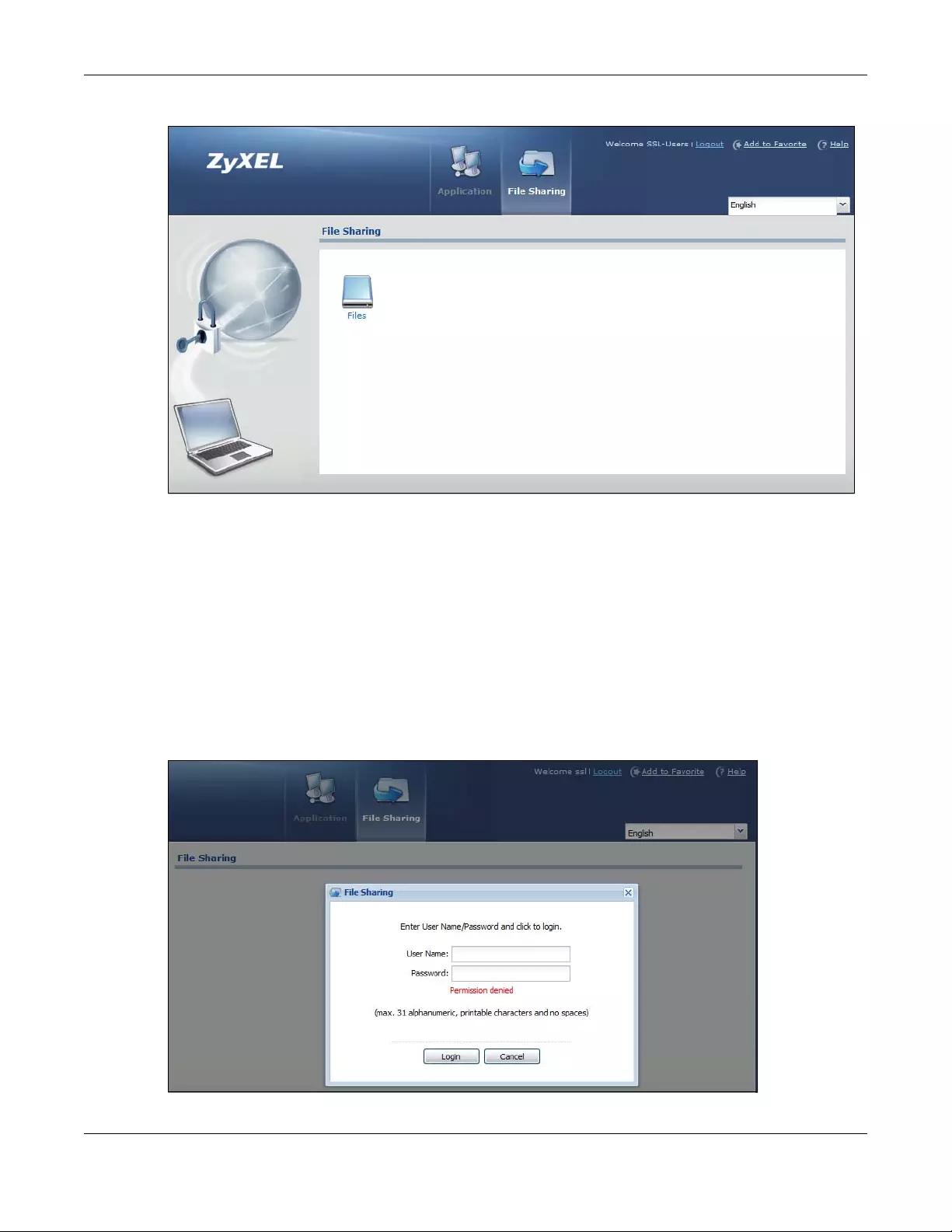
Chapter 32 SSL User Screens
USG/ZyWALL User’s Guide
600
Figure 431 File Sharing
32.7.2 Opening a File or Folder
You can open a file if the file extension is recognized by the web browser and the associated
application is installed on your computer.
1Log in as a remote user and click the File Sharing tab.
2Click on a file share icon.
3If an access user name and password are required, a screen displays as shown in the following figure.
Enter the account information and click Login to continue.
Figure 432 File Sharing: Enter Access User Name and Password
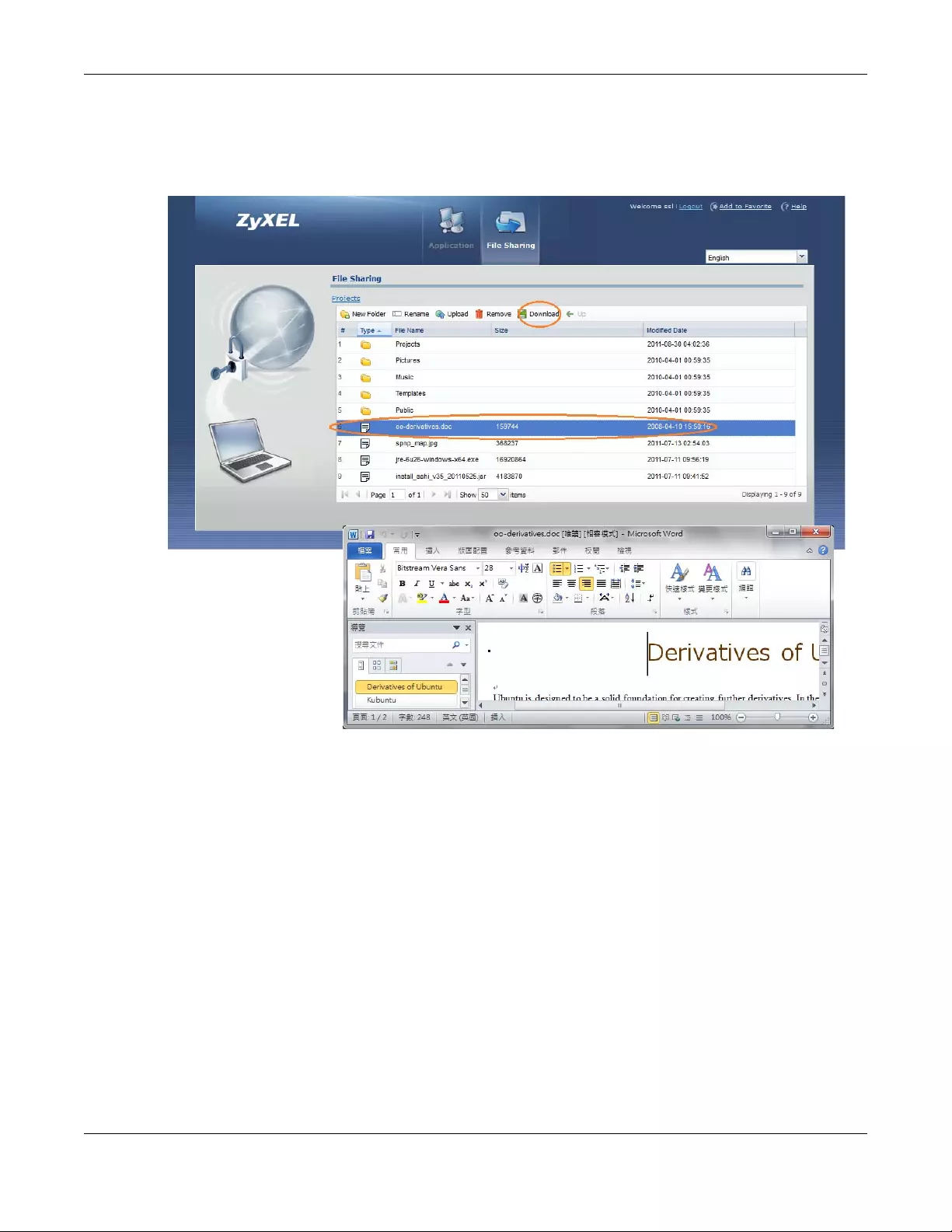
Chapter 32 SSL User Screens
USG/ZyWALL User’s Guide
601
4A list of files/folders displays. Double click a file to open it in a separate browser window or select a file
and click Download to save it to your computer. You can also click a folder to access it.
For this example, click on a .doc file to open the Word document.
Figure 433 File Sharing: Open a Word File
32.7.3 Downloading a File
You are prompted to download a file which cannot be opened using a web browser.
Follow the on-screen instructions to download and save the file to your computer. Then launch the
associated application to open the file.
32.7.4 Saving a File
After you have opened a file in a web browser, you can save a copy of the file by clicking File > Save As
and following the on-screen instructions.
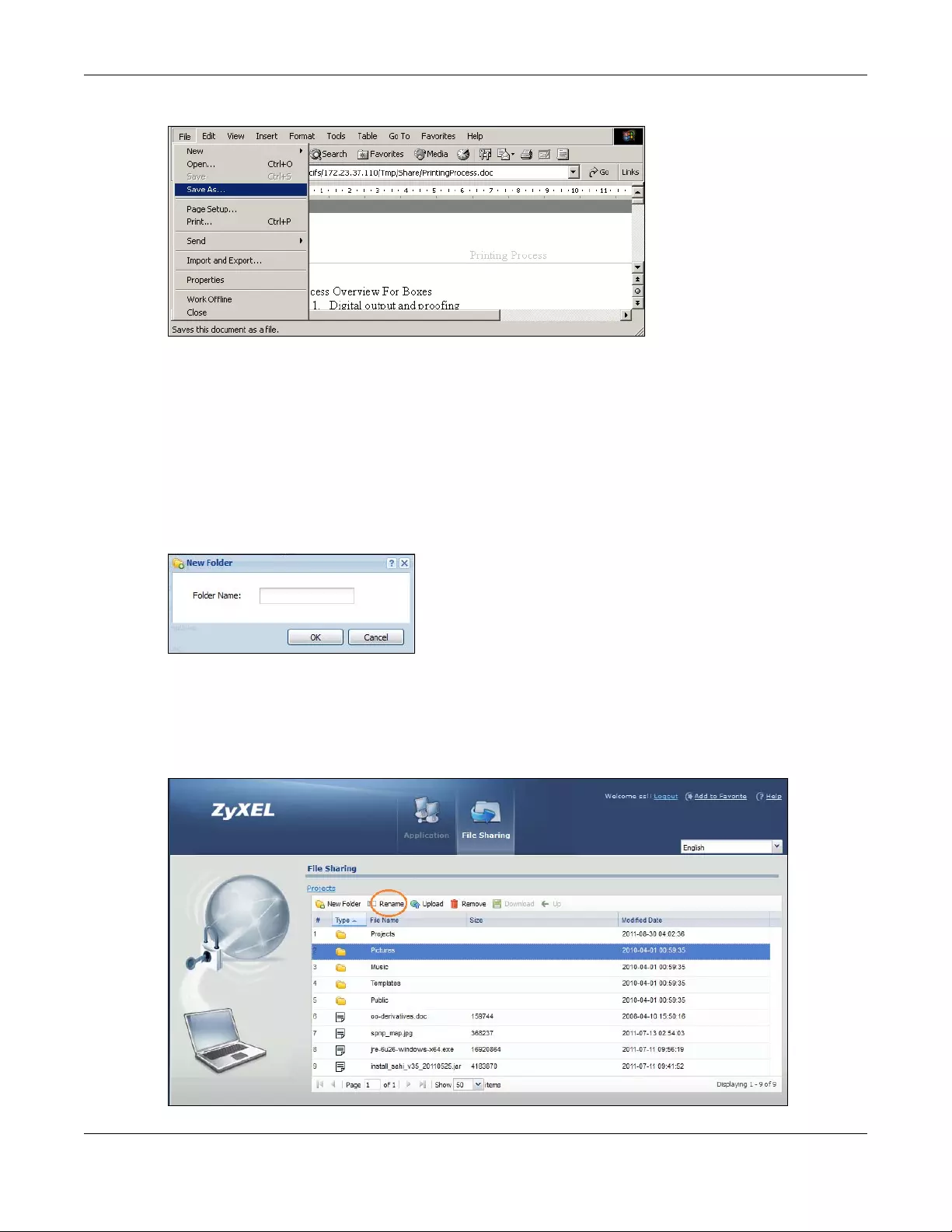
Chapter 32 SSL User Screens
USG/ZyWALL User’s Guide
602
Figure 434 File Sharing: Save a Word File
32.7.5 Creating a New Folder
To create a new folder in the file share location, click the New Folder icon.
Specify a descriptive name for the folder. You can enter up to 356 characters. Then click Add.
Note: Make sure the length of the folder name does not exceed the maximum allowed on
the file server.
Figure 435 File Sharing: Create a New Folder
32.7.6 Renaming a File or Folder
To rename a file or folder, select a file or folder and click the Rename icon.
Figure 436 File Sharing: Rename
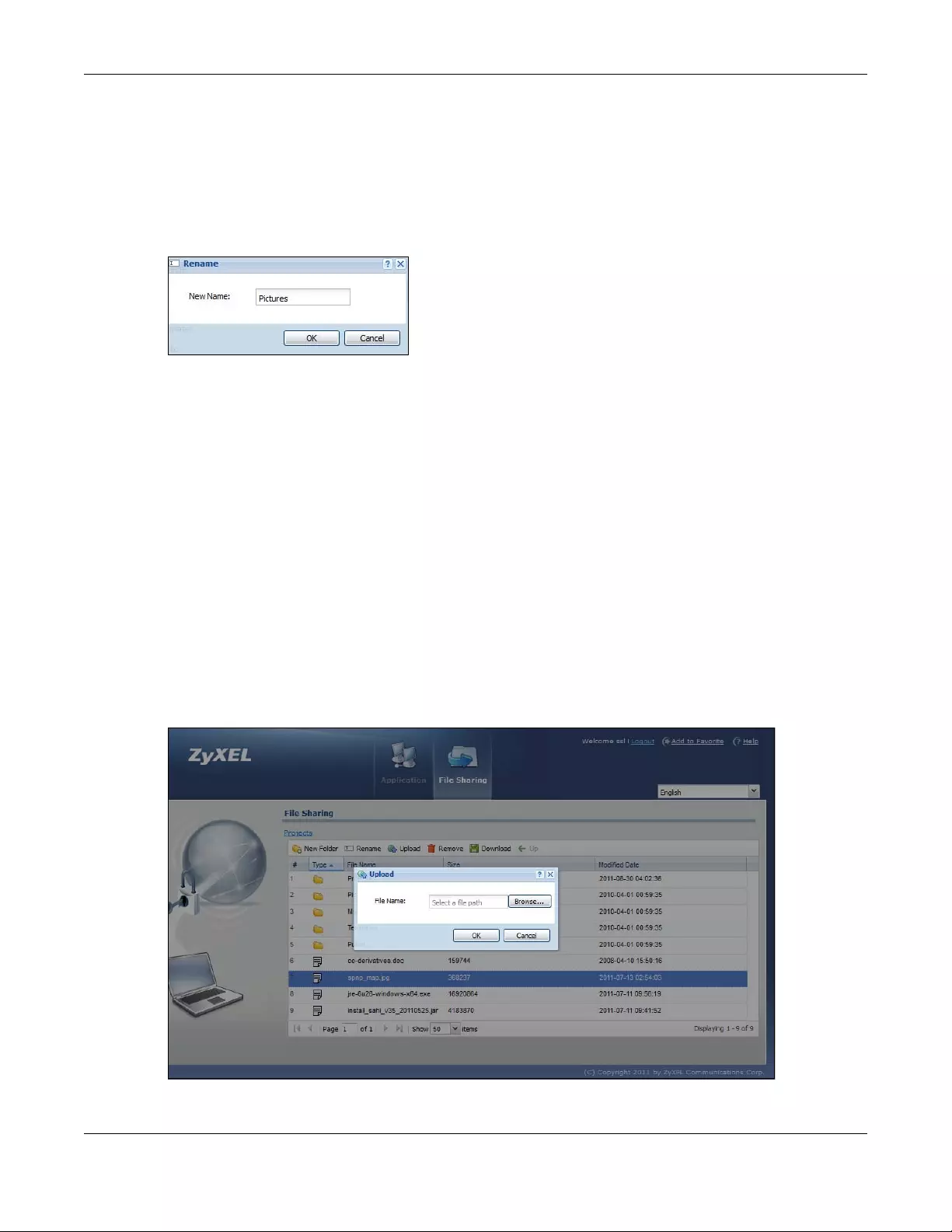
Chapter 32 SSL User Screens
USG/ZyWALL User’s Guide
603
A popup window displays. Specify the new name and/or file extension in the field provided. You can
enter up to 356 characters. Then click Apply.
Note: Make sure the length of the name does not exceed the maximum allowed on the file
server.
You may not be able to open a file if you change the file extension.
Figure 437 File Sharing: Rename
32.7.7 Deleting a File or Folder
Click the Delete icon next to a file or folder to remove it.
32.7.8 Uploading a File
Follow the steps below to upload a file to the file server.
1Log into the remote user screen and click the File Sharing tab.
2Click Upload and specify the location and/or name of the file you want to upload. Or click Browse to
locate it.
3Click OK to send the file to the file server.
4After the file is uploaded successfully, you should see the name of the file and a message in the screen.
Figure 438 File Sharing: File Upload

Chapter 32 SSL User Screens
USG/ZyWALL User’s Guide
604
Note: Uploading a file with the same name and file extension replaces the existing file on the
file server. No warning message is displayed.
USG/ZyWALL User’s Guide
605
CHAPTER 33
Zyxel Device SecuExtender
(Windows)
The Zyxel Device automatically loads the Zyxel Device SecuExtender for Windows client program to your
computer after a successful login to an SSL VPN tunnel with network extension support enabled.
Note: For information on using the Zyxel Device SecuExtender for Mac client program, please
see its User’s Guide at the download library on the Zyxel website.
The Zyxel Device SecuExtender (Windows) lets you:
• Access servers, remote desktops and manage files as if you were on the local network.
• Use applications like e-mail, file transfer, and remote desktop programs directly without using a
browser. For example, you can use Outlook for e-mail instead of the Zyxel Device’s web-based e-mail.
• Use applications, even proprietary applications, for which the Zyxel Device does not offer SSL
application objects.
The applications must be installed on your computer. For example, to use the VNC remote desktop
program, you must have the VNC client installed on your computer.
33.1 The Zyxel Device SecuExtender Icon
The Zyxel Device SecuExtender icon color indicates the SSL VPN tunnel’s connection status.
Figure 439 Zyxel Device SecuExtender Icon
• Green: the SSL VPN tunnel is connected. You can connect to the SSL application and network
resources. You can also use another application to access resources behind the Zyxel Device.
• Gray: the SSL VPN tunnel’s connection is suspended. This means the SSL VPN tunnel is connected, but
the Zyxel Device SecuExtender will not send any traffic through it until you right-click the icon and
resume the connection.
• Red: the SSL VPN tunnel is not connected. You cannot connect to the SSL application and network
resources.
33.2 Status
Right-click the Zyxel Device SecuExtender icon in the system tray and select Status to open the Status
screen. Use this screen to view the Zyxel Device SecuExtender’s connection status and activity statistics.
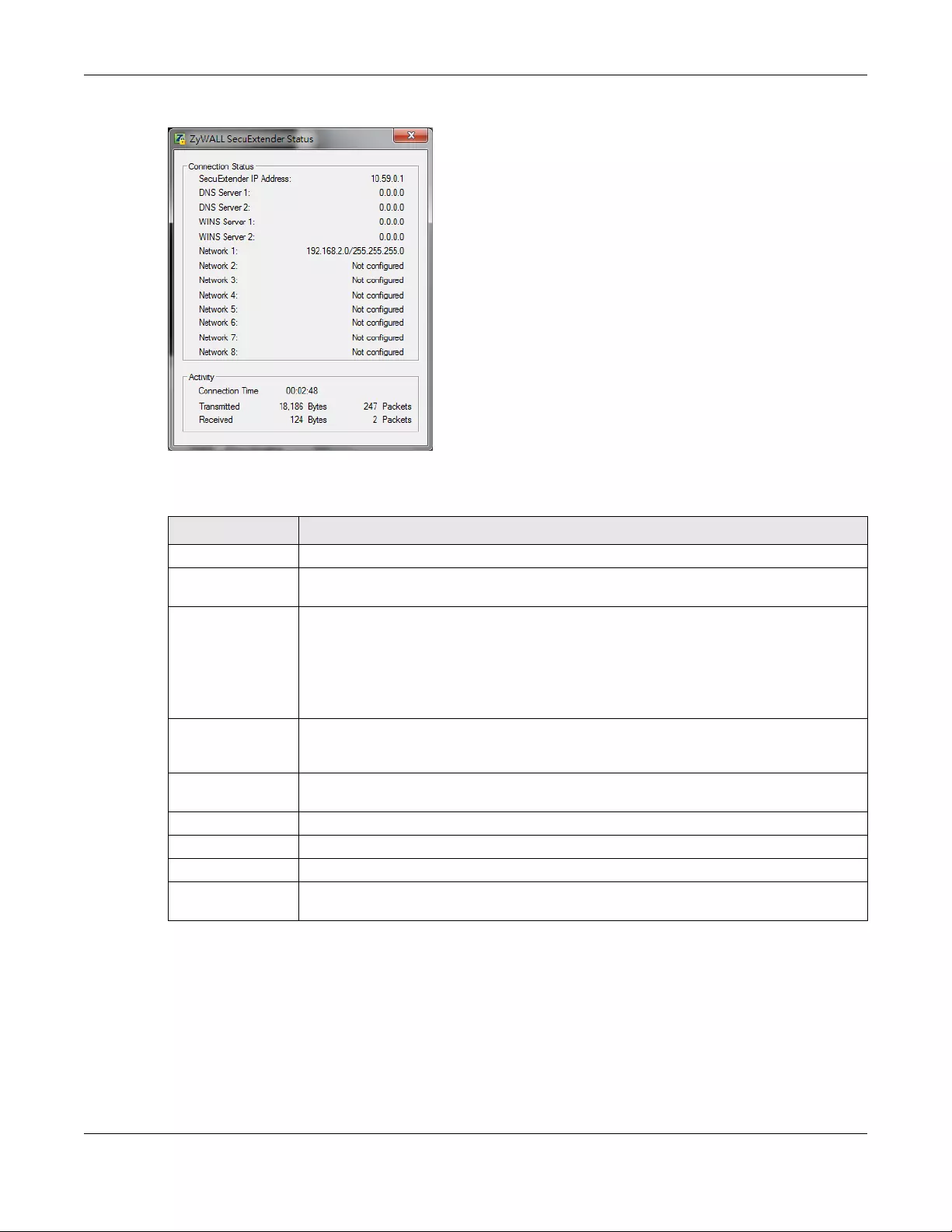
Chapter 33 Zyxel Device SecuExtender (Windows)
USG/ZyWALL User’s Guide
606
Figure 440 Zyxel Device SecuExtender Status
The following table describes the labels in this screen.
33.3 View Log
If you have problems with the Zyxel Device SecuExtender, customer support may request you to provide
information from the log. Right-click the Zyxel Device SecuExtender icon in the system tray and select
Log to open a notepad file of the Zyxel Device SecuExtender’s log.
Table 226 Zyxel Device SecuExtender Status
LABEL DESCRIPTION
Connection Status
SecuExtender IP
Address
This is the IP address the Zyxel Device assigned to this remote user computer for an SSL VPN
connection.
DNS Server 1/2 These are the IP addresses of the DNS server and backup DNS server for the SSL VPN
connection.
DNS (Domain Name System) maps a domain name to its corresponding IP address and vice
versa. The DNS server is extremely important because without it, you must know the IP address
of a computer before you can access it. Your computer uses the DNS server specified here to
resolve domain names for resources you access through the SSL VPN connection.
WINS Server 1/2 These are the IP addresses of the WINS (Windows Internet Naming Service) and backup WINS
servers for the SSL VPN connection. The WINS server keeps a mapping table of the computer
names on your network and the IP addresses that they are currently using.
Network 1~8 These are the networks (including netmask) that you can access through the SSL VPN
connection.
Activity
Connected Time This is how long the computer has been connected to the SSL VPN tunnel.
Transmitted This is how many bytes and packets the computer has sent through the SSL VPN connection.
Received This is how many bytes and packets the computer has received through the SSL VPN
connection.
Chapter 33 Zyxel Device SecuExtender (Windows)
USG/ZyWALL User’s Guide
607
Figure 441 Zyxel Device SecuExtender Log Example
33.4 Suspend and Resume the Connection
When the Zyxel Device SecuExtender icon in the system tray is green, you can right-click the icon and
select Suspend Connection to keep the SSL VPN tunnel connected but not send any traffic through it
until you right-click the icon and resume the connection.
33.5 Stop the Connection
Right-click the icon and select Stop Connection to disconnect the SSL VPN tunnel.
33.6 Uninstalling the Zyxel Device SecuExtender
Do the following if you need to remove the Zyxel Device SecuExtender.
1Click start > All Programs > Zyxel > Zyxel Device SecuExtender > Uninstall ZyWALL SecuExtender.
2In the confirmation screen, click Yes.
##################################################################################
##############
[ 2009/03/12 13:35:50 ][SecuExtender Agent][DETAIL] Build Datetime: Feb 24 2009/
10:25:07
[ 2009/03/12 13:35:50 ][SecuExtender Agent][DEBUG] rasphone.pbk: C:\Documents and
Settings\11746\rasphone.pbk
[ 2009/03/12 13:35:50 ][SecuExtender Agent][DEBUG] SecuExtender.log:
C:\Documents and Settings\11746\SecuExtender.log
[ 2009/03/12 13:35:50 ][SecuExtender Agent][DETAIL] Check Parameters
[ 2009/03/12 13:35:50 ][SecuExtender Agent][DETAIL] Connect to 172.23.31.19:443/
10444
[ 2009/03/12 13:35:50 ][SecuExtender Agent][DETAIL] Parameter is OK
[ 2009/03/12 13:35:50 ][SecuExtender Agent][DETAIL] Checking System status...
[ 2009/03/12 13:35:50 ][SecuExtender Agent][DETAIL] Checking service (first) ...
[ 2009/03/12 13:35:50 ][SecuExtender Agent][DETAIL] SecuExtender Helper is running
[ 2009/03/12 13:35:50 ][SecuExtender Agent][DETAIL] System is OK
[ 2009/03/12 13:35:50 ][SecuExtender Agent][DEBUG] Connect to 2887196435/443
[ 2009/03/12 13:35:50 ][SecuExtender Agent][DETAIL] Handshake LoopCounter: 0
[ 2009/03/12 13:35:50 ][SecuExtender Agent][DETAIL] 611 bytes of handshake data
received
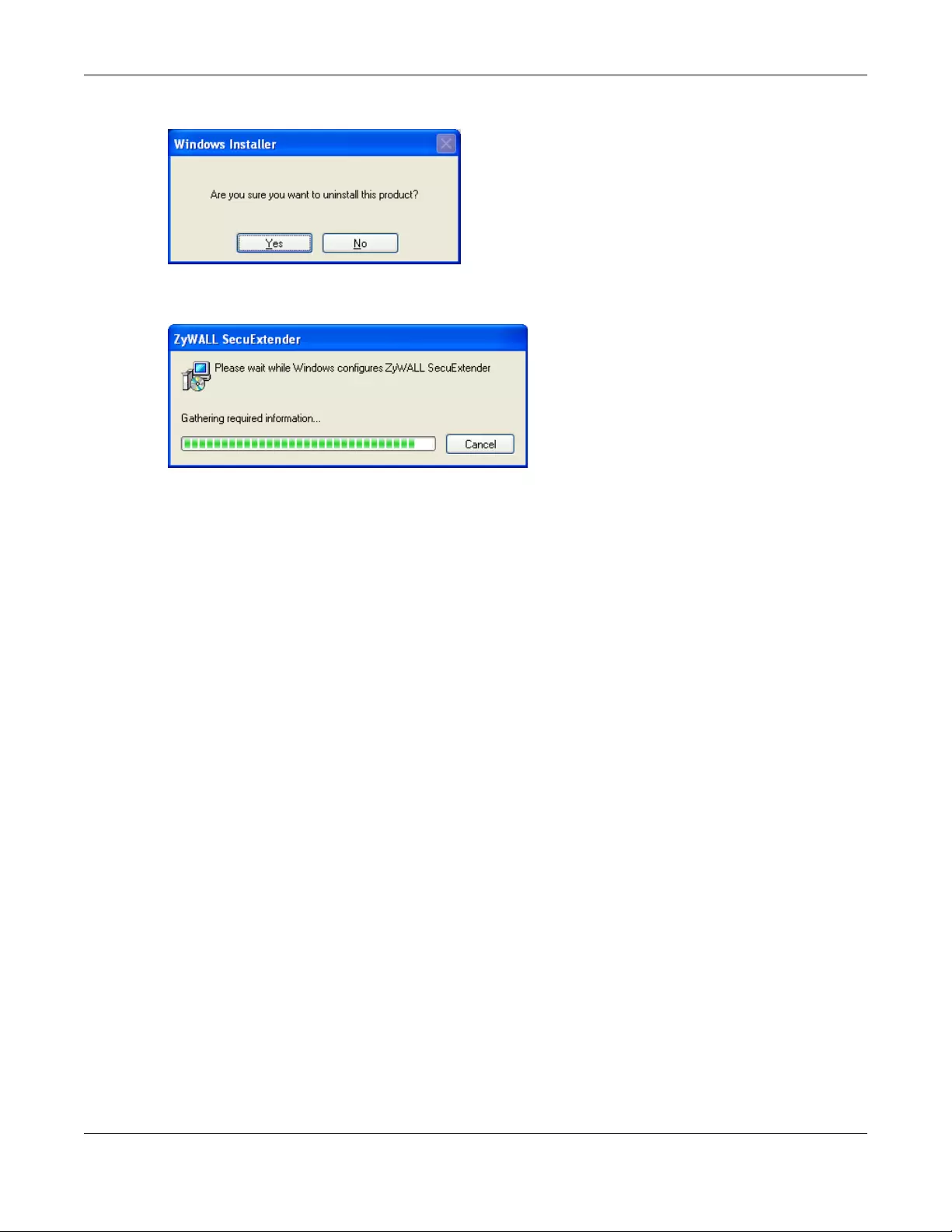
Chapter 33 Zyxel Device SecuExtender (Windows)
USG/ZyWALL User’s Guide
608
Figure 442 Uninstalling the Zyxel Device SecuExtender Confirmation
3Windows uninstalls the Zyxel Device SecuExtender.
Figure 443 Zyxel Device SecuExtender Uninstallation
USG/ZyWALL User’s Guide
609
CHAPTER 34
L2TP VPN
34.1 Overview
L2TP VPN uses the L2TP and IPSec client software included in remote users’ Android, iOS, Windows or
Mac OS X operating systems for secure connections to the network behind the Zyxel Device. The remote
users do not need their own IPSec gateways or third-party VPN client software.
Figure 444 L2TP VPN Overview
34.1.1 What You Can Do in this Chapter
• Use the L2TP VPN screen (see Section 34.2 on page 610) to configure the Zyxel Device’s L2TP VPN
settings.
• Use the VPN Setup Wizard screen in Quick Setup (Chapter 5 on page 138) to configure the Zyxel
Device’s L2TP VPN settings.
34.1.2 What You Need to Know
The Layer 2 Tunneling Protocol (L2TP) works at layer 2 (the data link layer) to tunnel network traffic
between two peers over another network (like the Internet). In L2TP VPN, an IPSec VPN tunnel is
established first and then an L2TP tunnel is built inside it. See Chapter 30 on page 545 for information on
IPSec VPN.
IPSec Configuration Required for L2TP VPN
You must configure an IPSec VPN connection prior to proper L2TP VPN usage (see Chapter 34 on page
609 for details). The IPSec VPN connection must:
• Be enabled.
• Use transport mode.
• Use Pre-Shared Key authentication.

Chapter 34 L2TP VPN
USG/ZyWALL User’s Guide
610
• Use a VPN gateway with the Secure Gateway set to 0.0.0.0 if you need to allow L2TP VPN clients to
connect from more than one IP address.
Using the Quick Setup VPN Setup Wizard
The VPN Setup Wizard is an easy and convenient way to configure the L2TP VPN settings. Click
Configuration > Quick Setup > VPN Setup > VPN Settings for L2TP VPN Settings to get started.
Policy Route
The Policy Route for return traffic (from LAN to L2TP clients) is automatically created when Zyxel Device
adds a new L2TP connection, allowing users access the resources on a network without additional
configuration. However, if some of the traffic from the L2TP clients needs to go to the Internet, you will
need to create a policy route to send that traffic from the L2TP tunnels out through a WAN trunk. This task
can be easily performed by clicking the Allow L2TP traffic through WAN checkbox at Quick Setu p > VPN
Setup > Allow L2TP traffic through WAN.
Figure 445 Policy Route for L2TP VPN
34.2 L2TP VPN Screen
Click Configuration > VPN > L2T P VPN to open the following screen. Use this screen to configure the Zyxel
Device’s L2TP VPN settings.
Note: Disconnect any existing L2TP VPN sessions before modifying L2TP VPN settings. The
remote users must make any needed matching configuration changes and re-establish
the sessions using the new settings.
Click on the icons to go to the OneSecurity.com website where there is guidance on configuration
walkthroughs, troubleshooting, and other information.
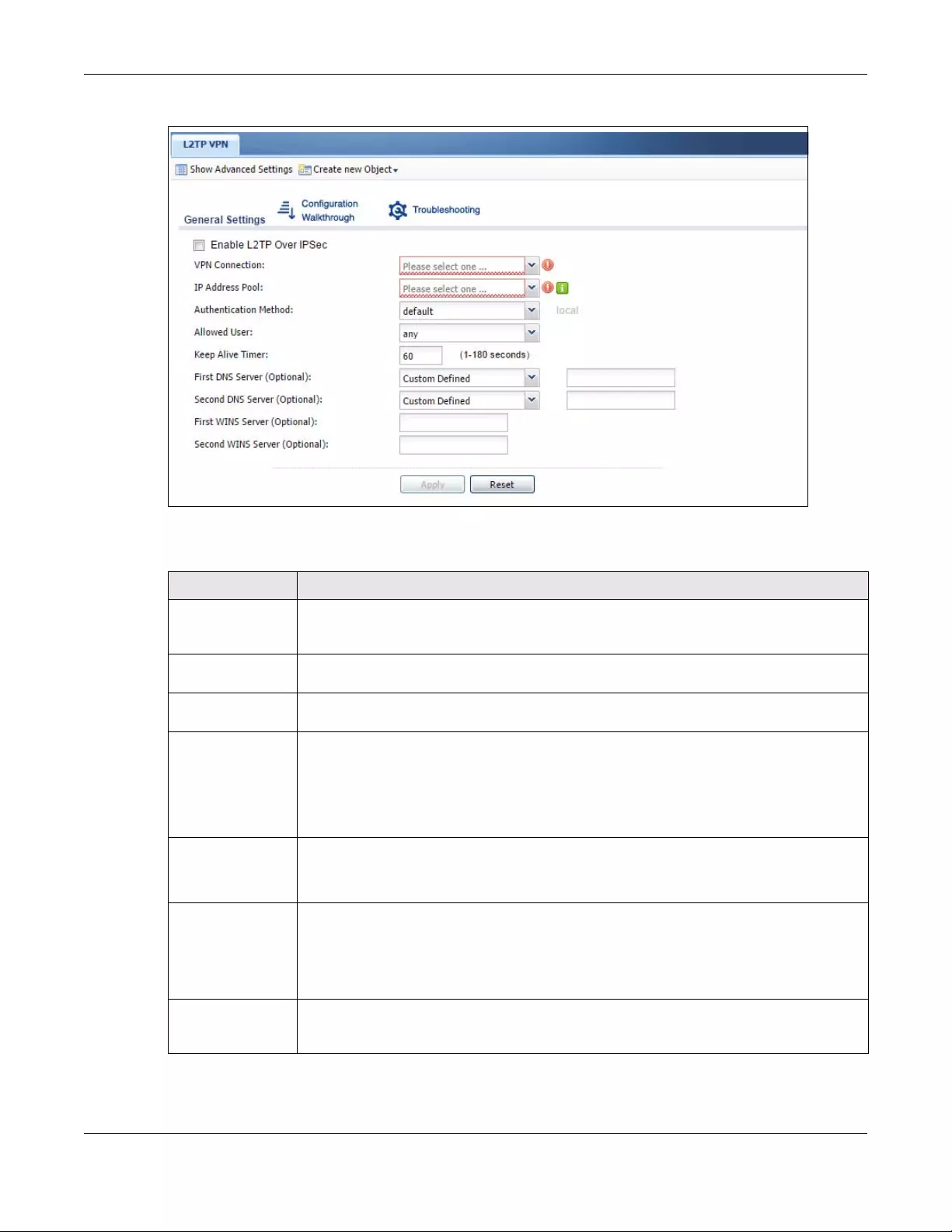
Chapter 34 L2TP VPN
USG/ZyWALL User’s Guide
611
Figure 446 Configuration > VPN > L2TP VPN
The following table describes the fields in this screen.
Table 227 Configuration > VPN > L2TP VPN
LABEL DESCRIPTION
Show Advanced
Settings / Hide
Advanced Settings
Click this button to display a greater or lesser number of configuration fields.
Create new
Object
Use to configure any new settings objects that you need to use in this screen.
Enable L2TP Over
IPSec
Use this field to turn the Zyxel Device’s L2TP VPN function on or off.
VPN Connection Select the IPSec VPN connection the Zyxel Device uses for L2TP VPN. All of the configured VPN
connections display here, but the one you use must meet the requirements listed in IPSec
Configuration Required for L2TP VPN on page 609.
Note: Modifying this VPN connection (or the VPN gateway that it uses) disconnects
any existing L2TP VPN sessions.
IP Address Pool Select the pool of IP addresses that the Zyxel Device uses to assign to the L2TP VPN clients. Use
Create new Object if you need to configure a new pool of IP addresses.
This should not conflict with any WAN, LAN, DMZ or WLAN subnet even if they are not in use.
Authentication
Method
Select how the Zyxel Device authenticates a remote user before allowing access to the L2TP
VPN tunnel.
The authentication method has the Zyxel Device check a user’s user name and password
against the Zyxel Device’s local database, a remote LDAP, RADIUS, a Active Directory server,
or more than one of these.
Authentication
Server Certificate
Select the certificate to use to identify the Zyxel Device for L2TP VPN connections. You must
have certificates already configured in the My Certificates screen. The certificate is used with
the EAP, PEAP, and MSCHAPv2 authentication protocols.
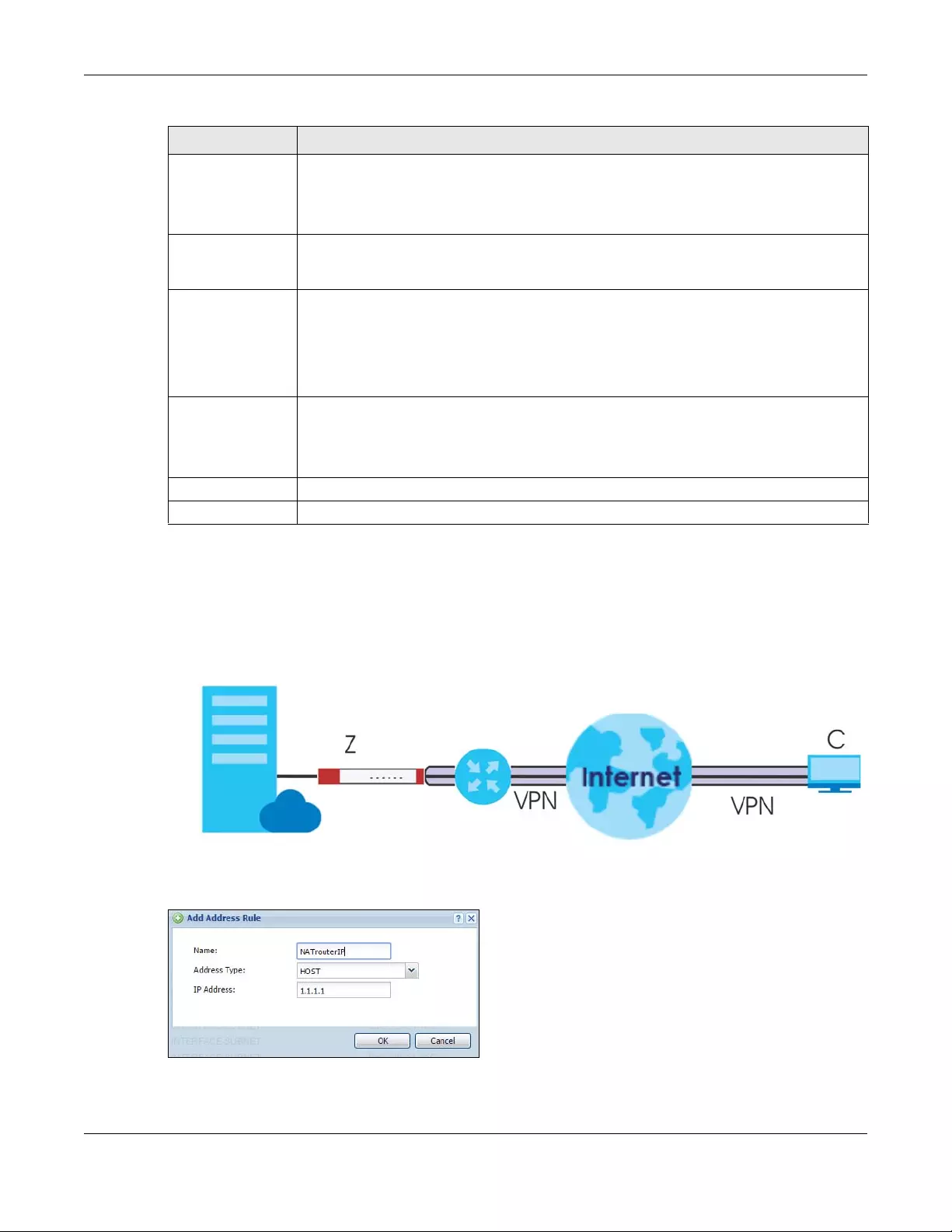
Chapter 34 L2TP VPN
USG/ZyWALL User’s Guide
612
34.2.1 Example: L2TP and Zyxel Device Behind a NAT Router
If the Zyxel Device (Z) is behind a NAT router (N), then do the following for remote clients (C) to access
the network behind the Zyxel Device (Z) using L2TP over IPv4.
Figure 447 L2TP and Zyxel Device Behind a NAT Router
1Create an address object in Configuration > Object > Address for the WAN IP address of the NAT router.
2Go to Configuration > VPN > IPSec VPN > VPN Connection and click Add for IPv4 Configuration to create
a new VPN connection.
Allowed User The remote user must log into the Zyxel Device to use the L2TP VPN tunnel.
Select a user or user group that can use the L2TP VPN tunnel. Use Cr eate new Object if you
need to configure a new user account. Otherwise, select any to allow any user with a valid
account and password on the Zyxel Device to log in.
Keep Alive Timer The Zyxel Device sends a Hello message after waiting this long without receiving any traffic
from the remote user. The Zyxel Device disconnects the VPN tunnel if the remote user does
not respond.
First DNS Server,
Second DNS Server
Specify the IP addresses of DNS servers to assign to the remote users. You can specify these IP
addresses two ways.
Custom Defined - enter a static IP address.
From ISP - use the IP address of a DNS server that another interface received from its DHCP
server.
First WINS Server,
Second WINS
Server
The WINS (Windows Internet Naming Service) server keeps a mapping table of the computer
names on your network and the IP addresses that they are currently using.
Type the IP addresses of up to two WINS servers to assign to the remote users. You can specify
these IP addresses two ways.
Apply Click Apply to save your changes in the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 227 Configuration > VPN > L2TP VPN (continued)
LABEL DESCRIPTION
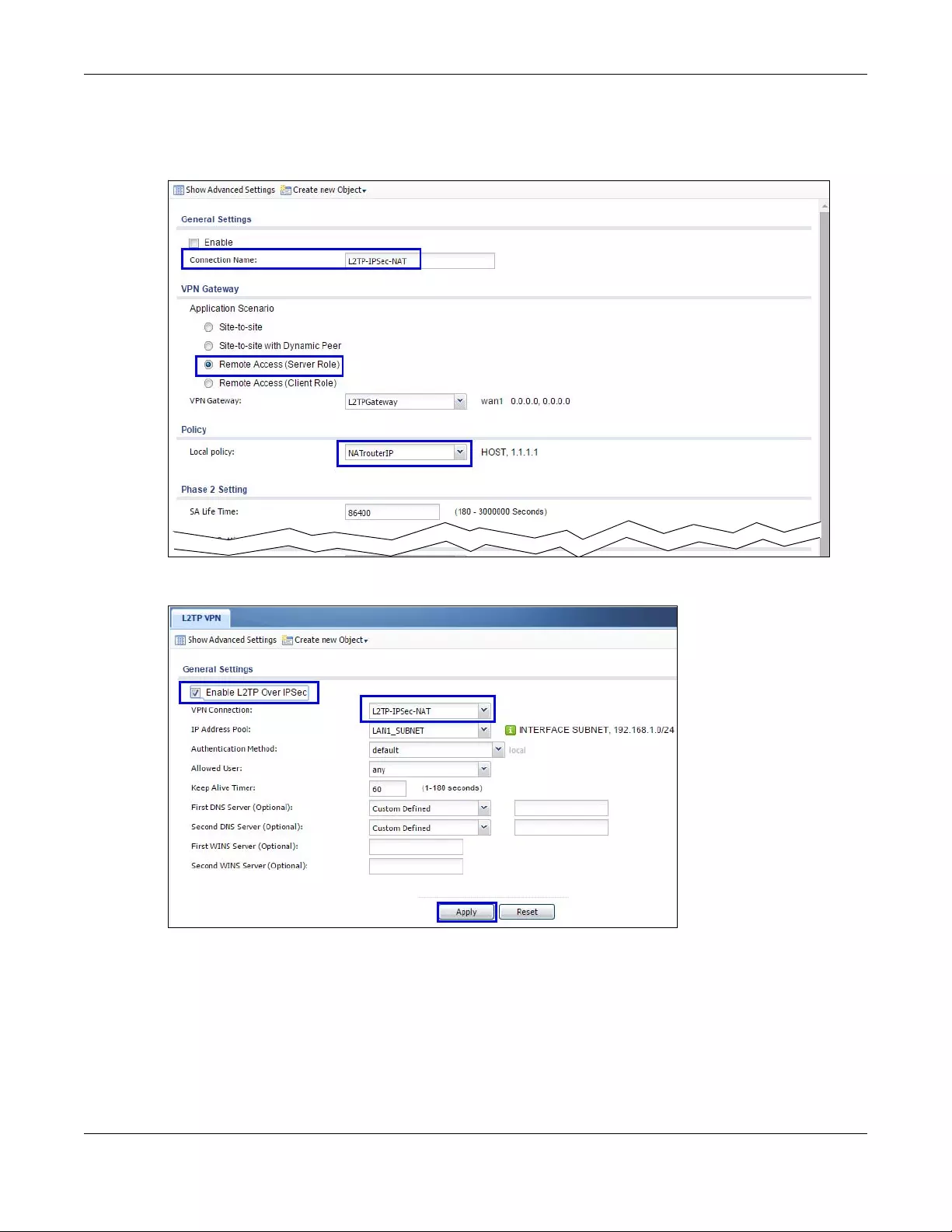
Chapter 34 L2TP VPN
USG/ZyWALL User’s Guide
613
3Select Remote Access (Server Role) as the VPN scenario for the remote client.
4Select the NAT router WAN IP address object as the Local Policy.
5Go to Configuration > VPN > L2TP VPN and select the VPN Connection just configured.

USG/ZyWALL User’s Guide
614
CHAPTER 35
BWM (Bandwidth
Management)
35.1 Overview
Bandwidth management provides a convenient way to manage the use of various services on the
network. It manages general protocols (for example, HTTP and FTP) and applies traffic prioritization to
enhance the performance of delay-sensitive applications like voice and video.
35.1.1 What You Can Do in this Chapter
Use the BWM screens (see Section 35.2 on page 618) to control bandwidth for services passing through
the Zyxel Device, and to identify the conditions that define the bandwidth control.
35.1.2 What You Need to Know
When you allow a service, you can restrict the bandwidth it uses. It controls TCP and UDP traffic. Use
policy routes to manage other types of traffic (like ICMP).
Note: Bandwidth management in policy routes has priority over TCP and UDP traffic policies.
If you want to use a service, make sure both the security policy allow the service’s packets to go through
the Zyxel Device.
Note: The Zyxel Device checks security policies before it checks bandwidth management
rules for traffic going through the Zyxel Device.
Bandwidth management examines every TCP and UDP connection passing through the Zyxel Device.
Then, you can specify, by port, whether or not the Zyxel Device continues to route the connection.
BWM Type
The Zyxel Device supports three types of bandwidth management: Shared, Per user and Per-Source-IP.
The Shared BWM type is selected by default in a bandwidth management rule. All matched traffic
shares the bandwidth configured in the rule.
If the BWM type is set to Per user in a rule, each user that matches the rule can use up to the configured
bandwidth by his/her own.
Select the Per-Source-IP type when you want to set the maximum bandwidth for traffic from an
individual source IP address.
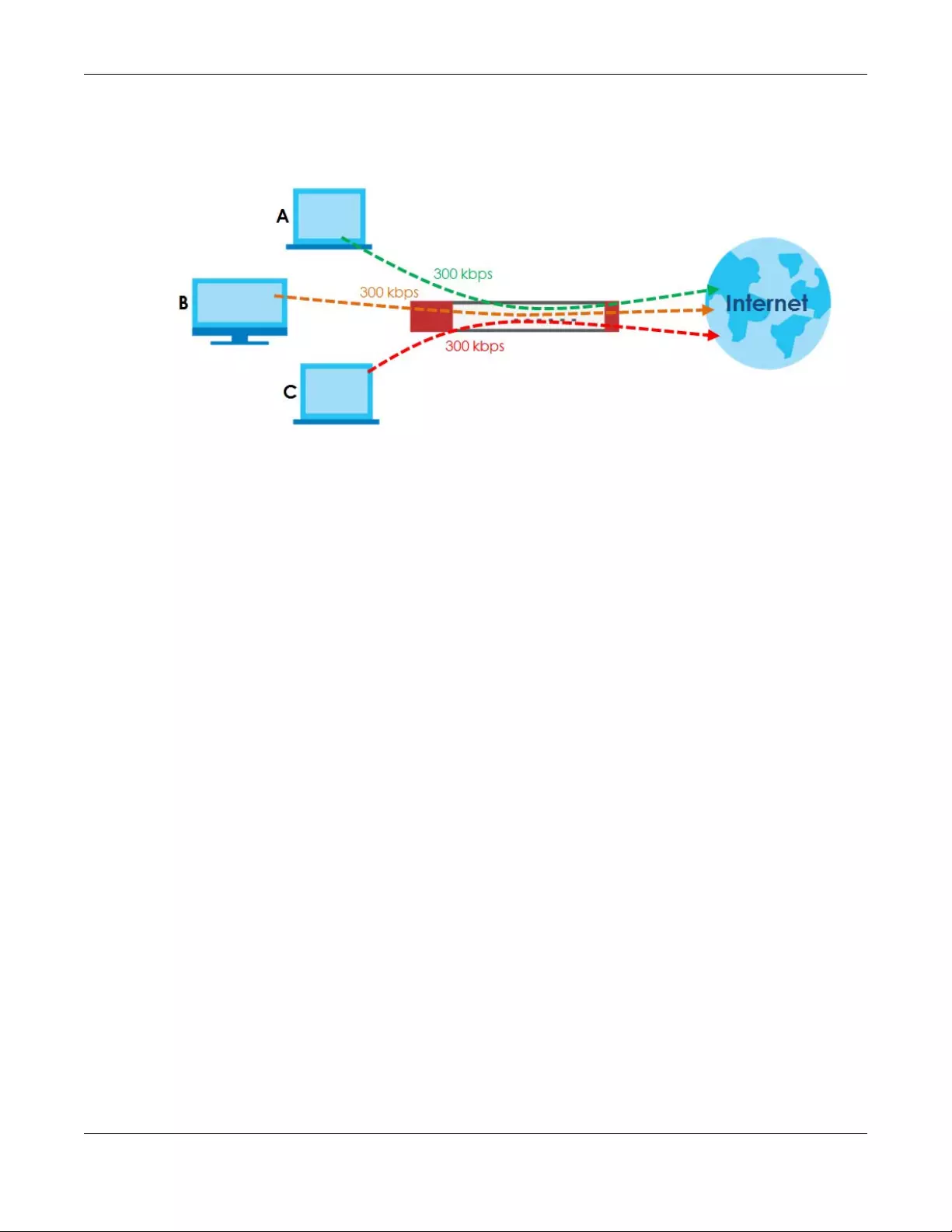
Chapter 35 BWM (Bandwidth Management)
USG/ZyWALL User’s Guide
615
In the following example, you configure a Per user bandwidth management rule for radius-users to limit
outgoing traffic to 300 kbs. Then all radius-users (A, B and C) can send 300 kbps of traffic.
Figure 448 Bandwidth Management Per User Type
DiffServ and DSCP Marking
QoS is used to prioritize source-to-destination traffic flows. All packets in the same flow are given the
same priority. CoS (class of service) is a way of managing traffic in a network by grouping similar types of
traffic together and treating each type as a class. You can use CoS to give different priorities to different
packet types.
DiffServ (Differentiated Services) is a class of service (CoS) model that marks packets so that they
receive specific per-hop treatment at DiffServ-compliant network devices along the route based on the
application types and traffic flow. Packets are marked with DiffServ Code Points (DSCPs) indicating the
level of service desired. This allows the intermediary DiffServ-compliant network devices to handle the
packets differently depending on the code points without the need to negotiate paths or remember
state information for every flow. In addition, applications do not have to request a particular service or
give advanced notice of where the traffic is going.
Connection and Packet Directions
Bandwidth management looks at the connection direction, that is, from which interface the connection
was initiated and to which interface the connection is going.
A connection has outbound and inbound packet flows. The Zyxel Device controls the bandwidth of
traffic of each flow as it is going out through an interface or VPN tunnel.
• The outbound traffic flows from the connection initiator to the connection responder.
• The inbound traffic flows from the connection responder to the connection initiator.
For example, a LAN1 to WAN connection is initiated from LAN1 and goes to the WAN.
• Outbound traffic goes from a LAN1 device to a WAN device. Bandwidth management is applied
before sending the packets out a WAN interface on the Zyxel Device.
• Inbound traffic comes back from the WAN device to the LAN1 device. Bandwidth management is
applied before sending the traffic out a LAN1 interface.
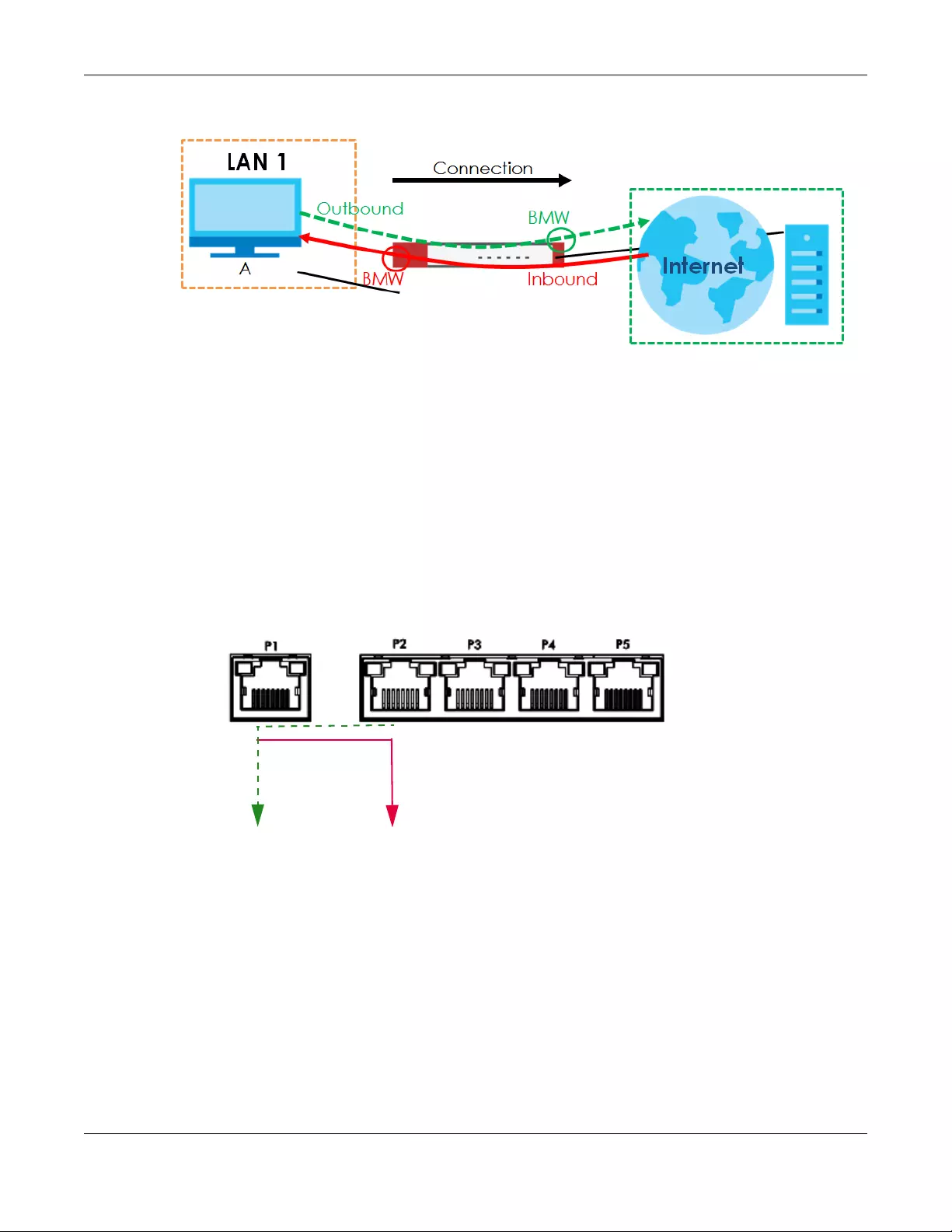
Chapter 35 BWM (Bandwidth Management)
USG/ZyWALL User’s Guide
616
Figure 449 LAN1 to WAN Connection and Packet Directions
Outbound and Inbound Bandwidth Limits
You can limit an application’s outbound or inbound bandwidth. This limit keeps the traffic from using up
too much of the out-going interface’s bandwidth. This way you can make sure there is bandwidth for
other applications. When you apply a bandwidth limit to outbound or inbound traffic, each member of
the out-going zone can send up to the limit. Take a LAN1 to WAN policy for example.
• Outbound traffic is limited to 200 kbps. The connection initiator is on the LAN1 so outbound means the
traffic traveling from the LAN1 to the WAN. Each of the WAN zone’s two interfaces can send the limit
of 200 kbps of traffic.
• Inbound traffic is limited to 500 kbs. The connection initiator is on the LAN1 so inbound means the
traffic traveling from the WAN to the LAN1.
Figure 450 LAN1 to WAN, Outbound 200 kbps, Inbound 500 kbps
Bandwidth Management Priority
• The Zyxel Device gives bandwidth to higher-priority traffic first, until it reaches its configured
bandwidth rate.
• Then lower-priority traffic gets bandwidth.
• The Zyxel Device uses a fairness-based (round-robin) scheduler to divide bandwidth among traffic
flows with the same priority.
• The Zyxel Device automatically treats traffic with bandwidth management disabled as priority 7 (the
lowest priority).
Inbound
Outbound
500 kbps
200 kbps
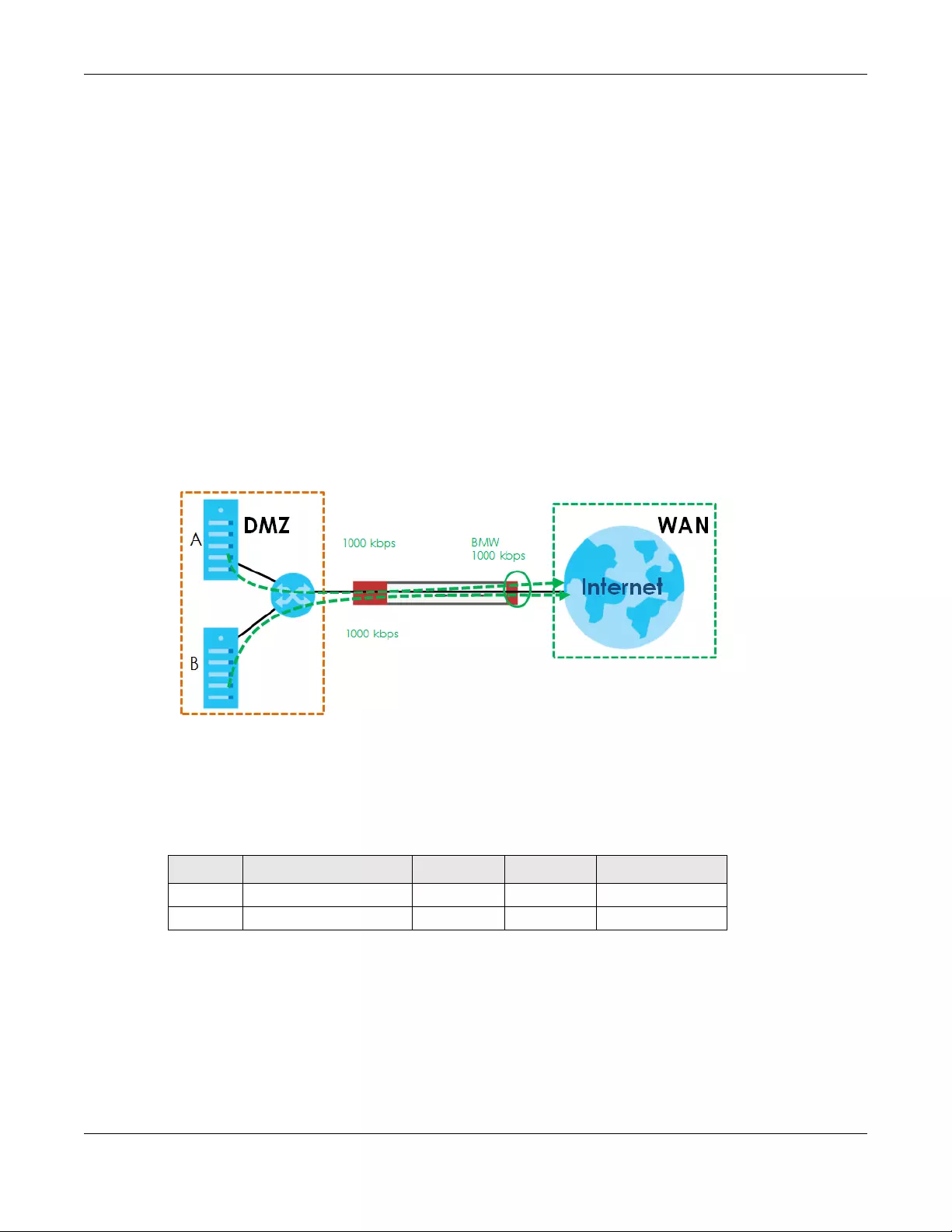
Chapter 35 BWM (Bandwidth Management)
USG/ZyWALL User’s Guide
617
Maximize Bandwidth Usage
Maximize bandwidth usage allows applications with maximize bandwidth usage enabled to “borrow”
any unused bandwidth on the out-going interface.
After each application gets its configured bandwidth rate, the Zyxel Device uses the fairness- based
scheduler to divide any unused bandwidth on the out-going interface amongst applications that need
more bandwidth and have maximize bandwidth usage enabled.
Unused bandwidth is divided equally. Higher priority traffic does not get a larger portion of the unused
bandwidth.
Bandwidth Management Behavior
The following sections show how bandwidth management behaves with various settings. For example,
you configure DMZ to WAN policies for FTP servers A and B. Each server tries to send 1000 kbps, but the
WAN is set to a maximum outgoing speed of 1000 kbps. You configure policy A for server A’s traffic and
policy B for server B’s traffic.
Figure 451 Bandwidth Management Behavior
Configured Rate Effect
In the following table the configured rates total less than the available bandwidth and maximize
bandwidth usage is disabled, both servers get their configured rate.
Table 228 Configured Rate Effect
POLICY CONFIGURED RATE MAX. B. U. PRIORITY ACTUAL RATE
A 300 kbps No 1 300 kbps
B 200 kbps No 1 200 kbps
Chapter 35 BWM (Bandwidth Management)
USG/ZyWALL User’s Guide
618
Priority Effect
Here the configured rates total more than the available bandwidth. Because server A has higher priority,
it gets up to it’s configured rate (800 kbps), leaving only 200 kbps for server B.
Maximize Bandwidth Usage Effect
With maximize bandwidth usage enabled, after each server gets its configured rate, the rest of the
available bandwidth is divided equally between the two. So server A gets its configured rate of 300 kbps
and server B gets its configured rate of 200 kbps. Then the Zyxel Device divides the remaining bandwidth
(1000 - 500 = 500) equally between the two (500 / 2 = 250 kbps for each). The priority has no effect on
how much of the unused bandwidth each server gets.
So server A gets its configured rate of 300 kbps plus 250 kbps for a total of 550 kbps. Server B gets its
configured rate of 200 kbps plus 250 kbps for a total of 450 kbps.
Priority and Over Allotment of Bandwidth Effect
Server A has a configured rate that equals the total amount of available bandwidth and a higher
priority. You should regard extreme over allotment of traffic with different priorities (as shown here) as a
configuration error. Even though the Zyxel Device still attempts to let all traffic get through and not be
lost, regardless of its priority, server B gets almost no bandwidth with this configuration.
35.2 The Bandwidth Management Screen
The Bandwidth management screens control the bandwidth allocation for TCP and UDP traffic. You can
use source interface, destination interface, destination port, schedule, user, source, destination
information, DSCP code and service type as criteria to create a sequence of specific conditions, similar
to the sequence of rules used by firewalls, to specify how the Zyxel Device handles the DSCP value and
allocate bandwidth for the matching packets.
Click Configuration > BWM to open the following screen. This screen allows you to enable/disable
bandwidth management and add, edit, and remove user-defined bandwidth management policies.
Table 229 Priority Effect
POLICY CONFIGURED RATE MAX. B. U. PRIORITY ACTUAL RATE
A 800 kbps Yes 1 800 kbps
B 1000 kbps Yes 2 200 kbps
Table 230 Maximize Bandwidth Usage Effect
POLICY CONFIGURED RATE MAX. B. U. PRIORITY ACTUAL RATE
A 300 kbps Yes 1 550 kbps
B 200 kbps Yes 2 450 kbps
Table 231 Priority and Over Allotment of Bandwidth Effect
POLICY CONFIGURED RATE MAX. B. U. PRIORITY ACTUAL RATE
A 1000 kbps Yes 1 999 kbps
B 1000 kbps Yes 2 1 kbps
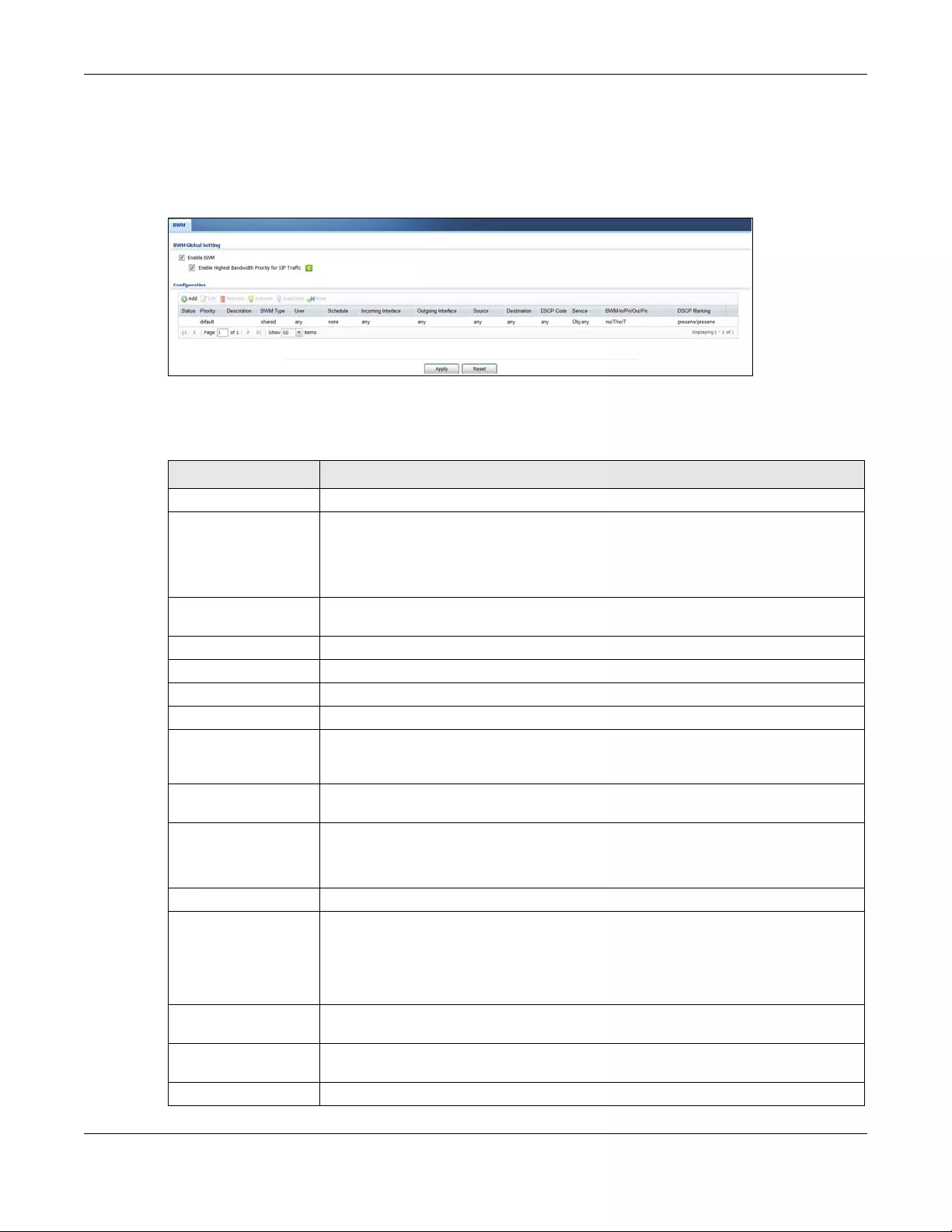
Chapter 35 BWM (Bandwidth Management)
USG/ZyWALL User’s Guide
619
The default bandwidth management policy is the one with the priority of “default”. It is the last policy
the Zyxel Device checks if traffic does not match any other bandwidth management policies you have
configured. You cannot remove, activate, deactivate or move the default bandwidth management
policy.
Figure 452 Configuration > Bandwidth Management
The following table describes the labels in this screen. See Section 35.2.1 on page 621 for more
information as well.
Table 232 Configuration > Bandwidth Management
LABEL DESCRIPTION
Enable BWM Select this check box to activate management bandwidth.
Enable Highest
Bandwidth Priority
for SIP Traffic
Select this to maximize the throughput of SIP traffic to improve SIP-based VoIP call sound
quality. This has the Zyxel Device immediately send SIP traffic upon identifying it. When
this option is enabled the Zyxel Device ignores any other application patrol rules for SIP
traffic (so there is no bandwidth control for SIP traffic) and does not record SIP traffic
bandwidth usage statistics.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after
the selected entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Move To change an entry’s position in the numbered list, select it and click Move to display a
field to type a number for where you want to put that entry and press [ENTER] to move
the entry to the number that you typed.
Status The activate (light bulb) icon is lit when the entry is active and dimmed when the entry is
inactive. The status icon is not available for the default bandwidth management policy.
Priority This field displays a sequential value for each bandwidth management policy and it is
not associated with a specific setting.
This field displays default for the default bandwidth management policy.
Description This field displays additional information about this policy.
BWM Type This field displays the below types of BWM:
•Shared, when the policy is set for all matched traffic
•Per User, when the policy is set for an individual user or a user group
•Per-Source-IP, when the policy is set for a source IP
User This is the type of user account to which the policy applies. If any displays, the policy
applies to all user accounts.
Schedule This is the schedule that defines when the policy applies. none means the policy always
applies.
Incoming Interface This is the source interface of the traffic to which this policy applies.
Chapter 35 BWM (Bandwidth Management)
USG/ZyWALL User’s Guide
620
Outgoing Interface This is the destination interface of the traffic to which this policy applies.
Source This is the source address or address group for whom this policy applies. If any displays,
the policy is effective for every source.
Destination This is the destination address or address group for whom this policy applies. If any
displays, the policy is effective for every destination.
DSCP Code These are the DSCP code point values of incoming and outgoing packets to which this
policy applies. The lower the number the higher the priority with the exception of 0 which
is usually given only best-effort treatment.
any means all DSCP value or no DSCP marker.
default means traffic with a DSCP value of 0. This is usually best effort traffic
The “af” options stand for Assured Forwarding. The number following the “af” identifies
one of four classes and one of three drop preferences.
Service Type App and the service name displays if you selected App lication Object for the service
type. An Application Object is a pre-defined service.
Obj and the service name displays if you selected Service Object for the service type. A
Service Object is a customized pre-defined service or another service. Mouse over the
service object name to view the corresponding IP protocol number.
BWM In/Pri/Out/Pri This field shows the amount of bandwidth the traffic can use.
In - This is how much inbound bandwidth, in kilobits per second, this policy allows the
matching traffic to use. Inbound refers to the traffic the Zyxel Device sends to a
connection’s initiator. If no displays here, this policy does not apply bandwidth
management for the inbound traffic.
Out - This is how much outgoing bandwidth, in kilobits per second, this policy allows the
matching traffic to use. Outbound refers to the traffic the Zyxel Device sends out from a
connection’s initiator. If no displays here, this policy does not apply bandwidth
management for the outbound traffic.
Pri - This is the priority for the incoming (the first Pri value) or outgoing (the second Pri
value) traffic that matches this policy. The smaller the number, the higher the priority.
Traffic with a higher priority is given bandwidth before traffic with a lower priority. The
Zyxel Device ignores this number if the incoming and outgoing limits are both set to 0. In
this case the traffic is automatically treated as being set to the lowest priority (7)
regardless of this field’s configuration.
DSCP Marking This is how the Zyxel Device handles the DSCP value of the incoming and outgoing
packets that match this policy.
In - Inbound, the traffic the Zyxel Device sends to a connection’s initiator.
Out - Outbound, the traffic the Zyxel Device sends out from a connection’s initiator.
If this field displays a DSCP value, the Zyxel Device applies that DSCP value to the route’s
outgoing packets.
preserve means the Zyxel Device does not modify the DSCP value of the route’s
outgoing packets.
default means the Zyxel Device sets the DSCP value of the route’s outgoing packets to 0.
The “af” choices stand for Assured Forwarding. The number following the “af” identifies
one of four classes and one of three drop preferences.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 232 Configuration > Bandwidth Management
LABEL DESCRIPTION
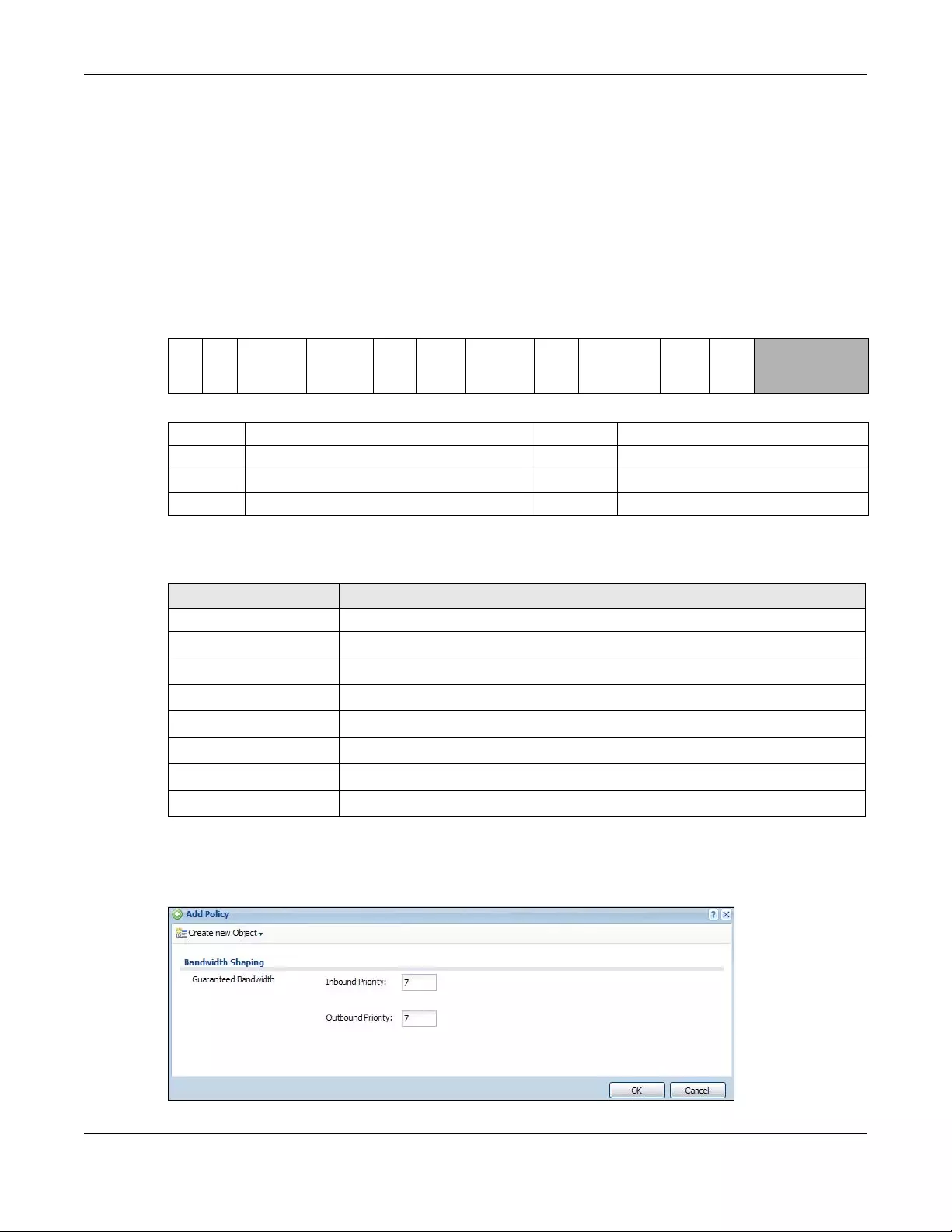
Chapter 35 BWM (Bandwidth Management)
USG/ZyWALL User’s Guide
621
35.2.1 The Bandwidth Management Add/Edit Screen
The Configuration > Bandwidth Management Add/Edit screen allows you to create a new condition or
edit an existing one.
802.1P Marking
Use 802.1P to prioritize outgoing traffic from a VLAN interface. The Priority Code is a 3-bit field within a
802.1Q VLAN tag that’s used to prioritize associated outgoing VLAN traffic. "0" is the lowest priority level
and "7" is the highest.
The following table is a guide to types of traffic for the priority code.
To access this screen, go to the Configuration > Bandwidth Management screen (see Section 35.2 on
page 618), and click either the Add icon or an Edit icon.
Figure 453 Configuration > Bandwidth Management > Edit (For the Default Policy)
Table 233 Single Tagged 802.1Q Frame Format
DA SA TPID Priority VID Len/Etype Data FCS IEEE 802.1Q
customer
tagged frame
Table 234 802.1Q Frame
DA Destination Address Priority 802.1p Priority
SA Source Address Len/Etype Length and type of Ethernet frame
TPID Tag Protocol IDentifier Data Frame data
VID VLAN ID FCS Frame Check Sequence
Table 235 Priority Code and Types of Traffic
PRIORITY TRAFFIC TYPES
0 (lowest) Background
1Best Effort
2 Excellent Effort
3 Critical Applications
4 Video, less than 100 ms latency and jitter
5 Voice, less than 10 ms latency and jitter
6 Internetwork Control
7 (highest) Network Control
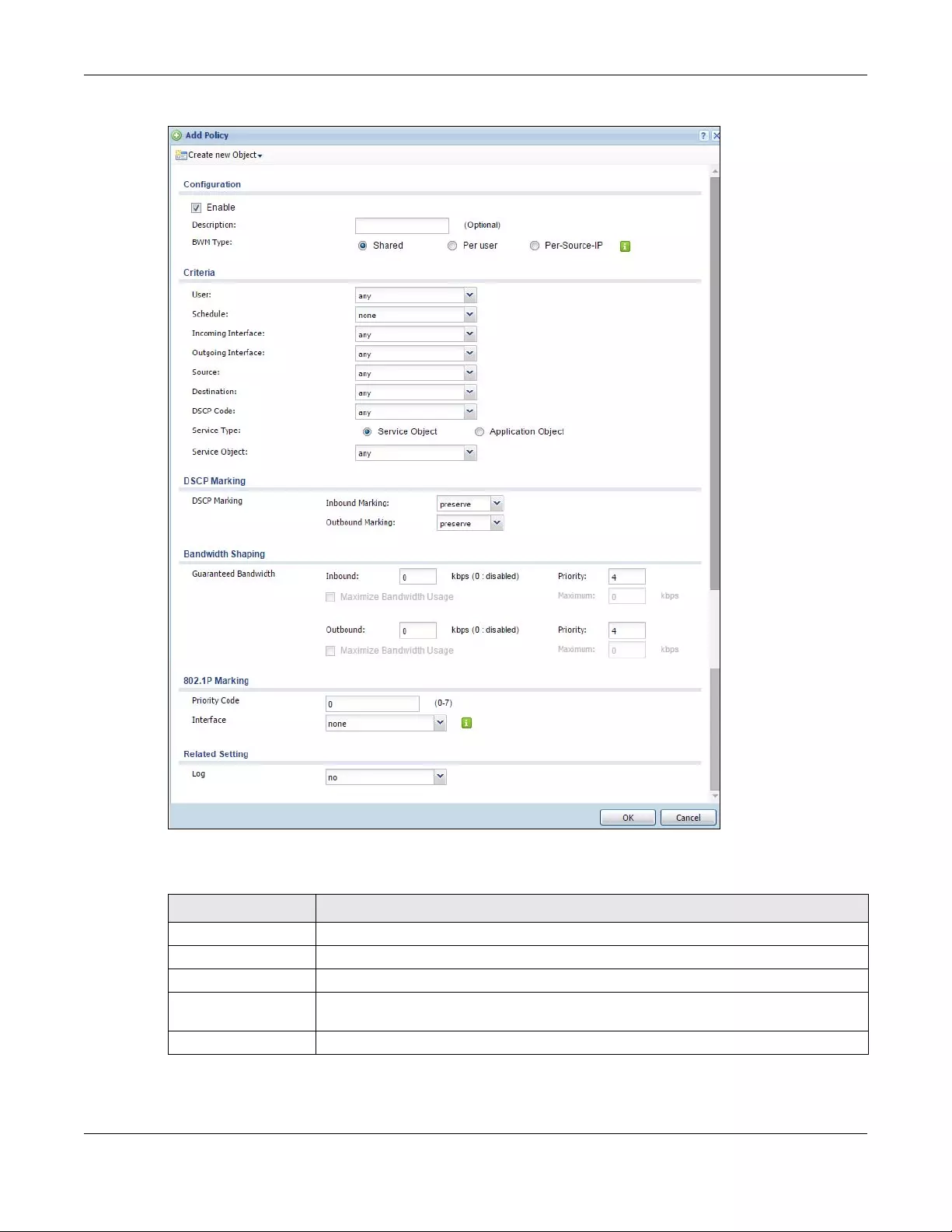
Chapter 35 BWM (Bandwidth Management)
USG/ZyWALL User’s Guide
622
Figure 454 Configuration > Bandwidth Management > Add/Edit
The following table describes the labels in this screen.
Table 236 Configuration > Bandwidth Management > Add/Edit
LABEL DESCRIPTION
Create new Object Use to configure any new settings objects that you need to use in this screen.
Configuration
Enable Select this check box to turn on this policy.
Description Enter a description of this policy. It is not used elsewhere. You can use alphanumeric and
()+/:=?!*#@$_%- characters, and it can be up to 60 characters long.
Criteria Use this section to configure the conditions of traffic to which this policy applies.
Chapter 35 BWM (Bandwidth Management)
USG/ZyWALL User’s Guide
623
BWM Type This field displays the below types of BWM rule:
• Shared, when the policy is set for all users
• Per User, when the policy is set for an individual user or a user group
• Per Source IP, when the policy is set for a source IP
User Select a user name or user group to which to apply the policy. Use Create new Object if
you need to configure a new user account. Select any to apply the policy for every user.
Schedule Select a schedule that defines when the policy applies or select Create Object to
configure a new one. Otherwise, select none to make the policy always effective.
Incoming Interface Select the source interface of the traffic to which this policy applies.
Outgoing Interface Select the destination interface of the traffic to which this policy applies.
Source Select a source address or address group for whom this policy applies. Use Create new
Object if you need to configure a new one. Select any if the policy is effective for every
source.
Destination Select a destination address or address group for whom this policy applies. Use Create
new Object if you need to configure a new one. Select any if the policy is effective for
every destination.
DSCP Code Select a DSCP code point value of incoming packets to which this policy
route applies or select User Defined to specify another DSCP code point. The lower the
number the higher the priority with the exception of 0 which is usually given only best-effort
treatment.
any means all DSCP value or no DSCP marker.
default means traffic with a DSCP value of 0. This is usually best effort traffic
The “af” choices stand for Assured Forwarding. The number following the “af” identifies
one of four classes and one of three drop preferences.
User-Defined DSCP
Code Use this field to specify a custom DSCP code point.
Service Type Select Service Object or Application Object if you want a specific service (defined in a
service object) or application patrol service to which the policy applies.
Service Object This field is available if you selected Service Object as the service type.
Select a service or service group to identify the type of traffic to which this policy applies.
any means all services.
Application Object This field is available if you selected Application Obje ct as the service type.
Select an application patrol service to identify the specific traffic to which this policy
applies.
DSCP Marking Set how the Zyxel Device handles the DSCP value of the incoming and outgoing packets
that match this policy. Inbound refers to the traffic the Zyxel Device sends to a
connection’s initiator. Outbound refers to the traffic the Zyxel Device sends out from a
connection’s initiator.
Select one of the pre-defined DSCP values to apply or select User Defined to specify
another DSCP value. The “af” choices stand for Assured Forwarding. The number following
the “af” identifies one of four classes and one of three drop preferences.
Select preserve to have the Zyxel Device keep the packets’ original DSCP value.
Select default to have the Zyxel Device set the DSCP value of the packets to 0.
Bandwidth Shaping Configure these fields to set the amount of bandwidth the matching traffic can use.
Table 236 Configuration > Bandwidth Management > Add/Edit
LABEL DESCRIPTION
Chapter 35 BWM (Bandwidth Management)
USG/ZyWALL User’s Guide
624
Inbound kbps Type how much inbound bandwidth, in kilobits per second, this policy allows the traffic to
use. Inbound refers to the traffic the Zyxel Device sends to a connection’s initiator.
If you enter 0 here, this policy does not apply bandwidth management for the matching
traffic that the Zyxel Device sends to the initiator. Traffic with bandwidth management
disabled (inbound and outbound are both set to 0) is automatically treated as the lowest
priority (7).
If the sum of the bandwidths for routes using the same next hop is higher than the actual
transmission speed, lower priority traffic may not be sent if higher priority traffic uses all of
the actual bandwidth.
Outbound kbps Type how much outbound bandwidth, in kilobits per second, this policy allows the traffic to
use. Outbound refers to the traffic the Zyxel Device sends out from a connection’s initiator.
If you enter 0 here, this policy does not apply bandwidth management for the matching
traffic that the Zyxel Device sends out from the initiator. Traffic with bandwidth
management disabled (inbound and outbound are both set to 0) is automatically treated
as the lowest priority (7).
If the sum of the bandwidths for routes using the same next hop is higher than the actual
transmission speed, lower priority traffic may not be sent if higher priority traffic uses all of
the actual bandwidth.
Priority This field displays when the inbound or outbound bandwidth management is not set to 0.
Enter a number between 1 and 7 to set the priority for traffic that matches this policy. The
smaller the number, the higher the priority.
Traffic with a higher priority is given bandwidth before traffic with a lower priority.
The Zyxel Device uses a fairness-based (round-robin) scheduler to divide bandwidth
between traffic flows with the same priority.
The number in this field is ignored if the incoming and outgoing limits are both set to 0. In
this case the traffic is automatically treated as being set to the lowest priority (7) regardless
of this field’s configuration.
Maximize
Bandwidth Usage This field displays when the inbound or outbound bandwidth management is not set to 0
and the BWM Type is set to Shared. Enable maximize bandwidth usage to let the traffic
matching this policy “borrow” all unused bandwidth on the out-going interface.
After each application or type of traffic gets its configured bandwidth rate, the Zyxel
Device uses the fairness-based scheduler to divide any unused bandwidth on the out-
going interface among applications and traffic types that need more bandwidth and
have maximize bandwidth usage enabled.
Maximum If you did not enable Maximize Bandwidth Usage, then type the maximum unused
bandwidth that traffic matching this policy is allowed to “borrow” on the out-going
interface (in Kbps), here.
802.1P Marking Use 802.1P to prioritize outgoing traffic from a VLAN interface.
Priority Code This is a 3-bit field within a 802.1Q VLAN tag that’s used to prioritize associated outgoing
VLAN traffic. "0" is the lowest priority level and "7" is the highest. See Table 235 on page 621.
The setting configured here overwrites existing priority settings.
Interface Choose a VLAN interface to which to apply the priority level for matching frames.
Related Setting
Log Select whether to have the Zyxel Device generate a log (log), log and alert (log alert) or
neither (no) when any traffic matches this policy.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
Table 236 Configuration > Bandwidth Management > Add/Edit
LABEL DESCRIPTION
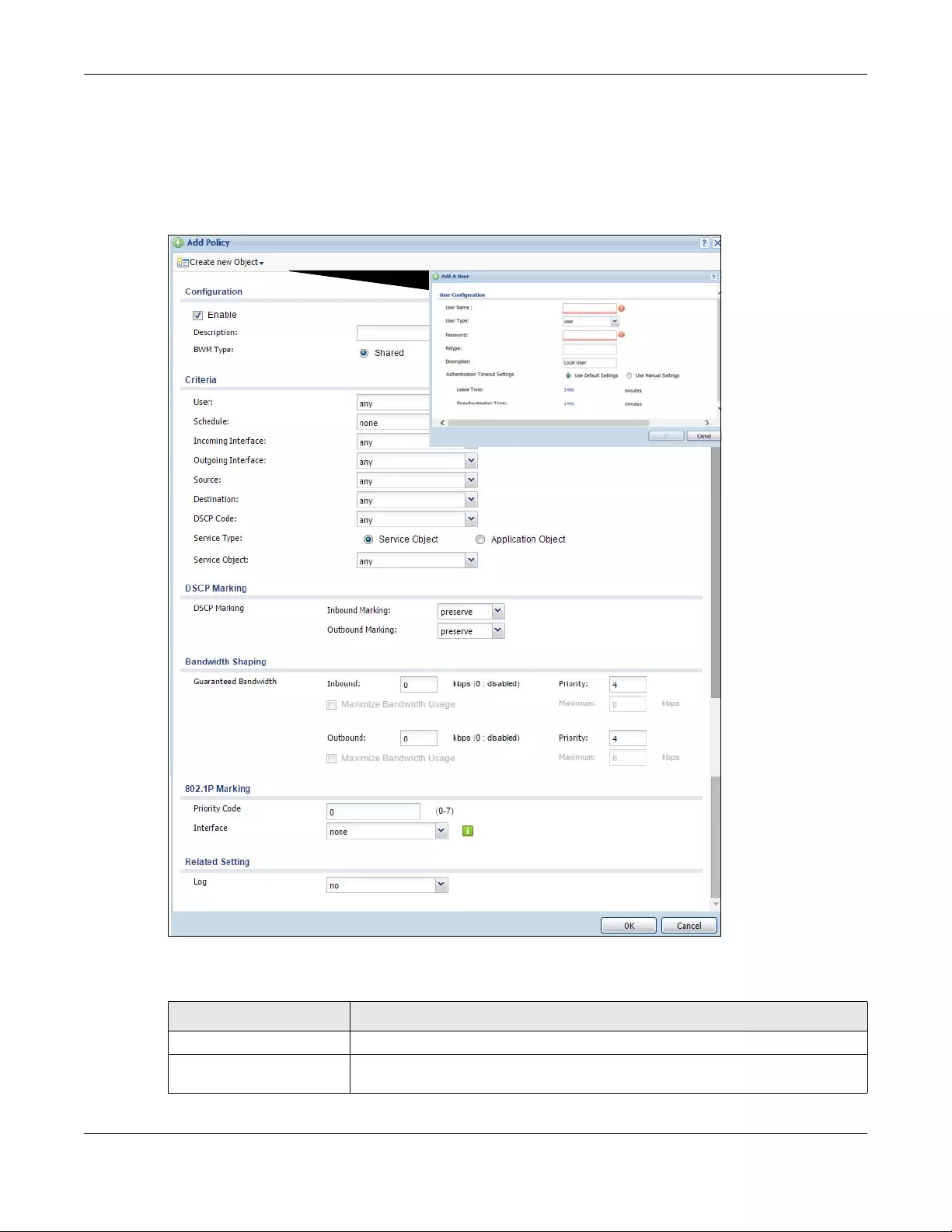
Chapter 35 BWM (Bandwidth Management)
USG/ZyWALL User’s Guide
625
35.2.1.1 Adding Objects for the BWM Policy
Objects are parameters to which the Policy rules are built upon. There are three kinds of objects you can
add/edit for the BWM policy, they are User, Schedule and Address objects. Click Configuration > BWM >
Add > Create New Object > Add User to see the following screen.
Figure 455 Configuration >BWM > Create New Object > Add User
The following table describes the fields in the above screen.
Table 237 Configuration > BWM > Create New Object > Add User
LABEL DESCRIPTION
User Name Type a user or user group object name of the rule.
User Type Select a user type from the drop down menu. The user types are Admin, Limited
admin, User, Guest, Ext-user, Ext-group-user.
Chapter 35 BWM (Bandwidth Management)
USG/ZyWALL User’s Guide
626
Password Type a password for the user object. The password can consist of alphanumeric
characters, the underscore, and some punctuation marks (+-/*= :; .! @$&%#~ ‘ \ () ),
and it can be up to eight characters long.
Retype Retype the password to confirm.
Description Enter a description for this user object. It is not used elsewhere. You can use
alphanumeric and ()+/:=?!*#@$_%- characters, and it can be up to 60
characters long.
Authentication Timeout
Settings
Choose either Use Default setting option, which shows the default Lease Time of
1,440 minutes and Reauthentication Time of 1,440 minutes or you can enter them
manually by choosing Use Manual Settings option.
Lease Time This shows the Lease Time setting for the user, by default it is 1,440 minutes.
Reauthentication Time This shows the Reauthentication Time for the user, by default it is 1,440 minutes.
OK Click OK to save the setting.
Cancel Click Cancel to abandon this screen.
Table 237 Configuration > BWM > Create New Object > Add User
LABEL DESCRIPTION
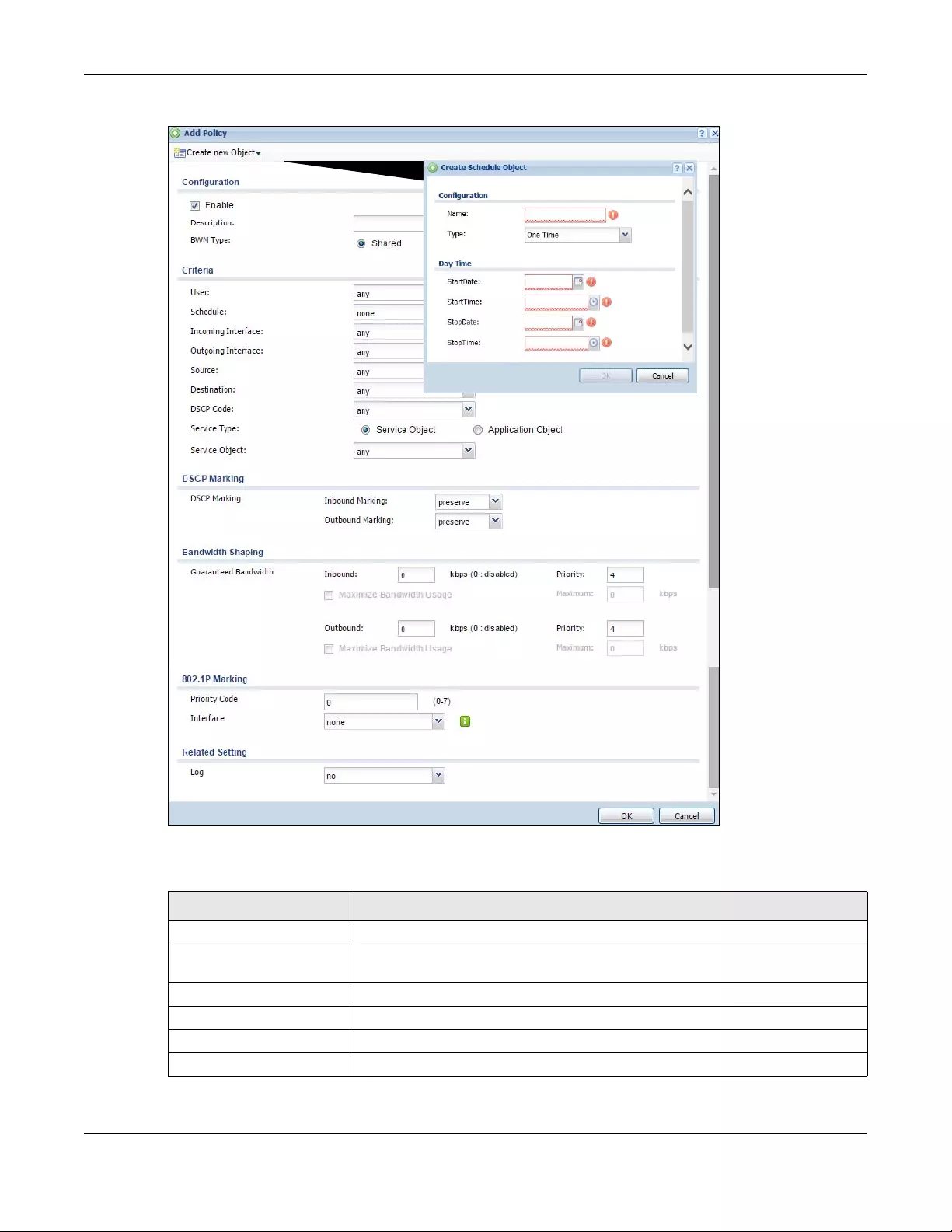
Chapter 35 BWM (Bandwidth Management)
USG/ZyWALL User’s Guide
627
Figure 456 Configuration > BWM > Create New Object > Add Schedule
The following table describes the fields in the above screen.
Table 238 Configuration > BWM > Create New Object > Add Schedule
LABEL DESCRIPTION
Name Enter a name for the schedule object of the rule.
Type Select an option from the drop down menu for the schedule object. It will show One
Time or Recurring.
Start Date Click the icon menu on the right to choose a Start Date for the schedule object.
Start Time Click the icon menu on the right to choose a Start Time for the schedule object.
Stop Date Click the icon menu on the right to choose a Stop Date for schedule object.
Stop Time Click the icon menu on the right to choose a Stop Time for the schedule object.
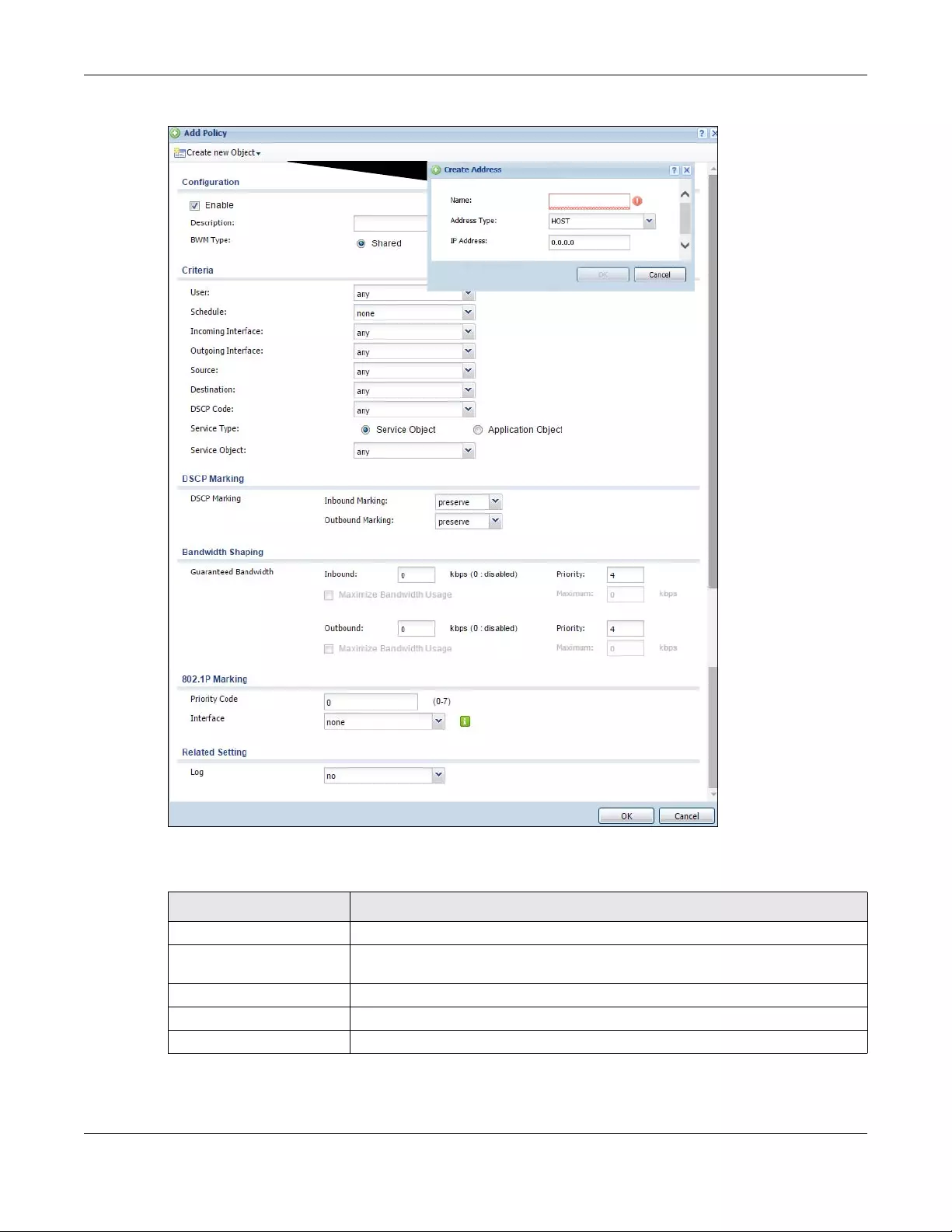
Chapter 35 BWM (Bandwidth Management)
USG/ZyWALL User’s Guide
628
Figure 457 Configuration > BWM > Create New Object > Add Address
The following table describes the fields in the above screen.
Table 239 Configuration > BWM > Create New Object > Add Address
LABEL DESCRIPTION
Name Enter a name for the Address object of the rule.
Address Type Select an Address Type from the drop down menu on the right. The Address Types
are Host, Range, Subnet, Interface IP, Interface Subnet, and Interface Gateway.
IP Address Enter an IP address for the Address object.
OK Click OK to save the setting.
Cancel Click Cancel to abandon the setting.
USG/ZyWALL User’s Guide
629
CHAPTER 36
Application Patrol
36.1 Overview
Application patrol provides a convenient way to manage the use of various applications on the
network. It manages general protocols (for example, HTTP and FTP) and instant messenger (IM), peer-to-
peer (P2P), Voice over IP (VoIP), and streaming (RSTP) applications. You can even control the use of a
particular application’s individual features (like text messaging, voice, video conferencing, and file
transfers). You can also configure bandwidth management with application patrol in the Configuration
> BWM screen for traffic prioritization to enhance the performance of delay-sensitive applications like
voice and video.
36.1.1 What You Can Do in this Chapter
• Use the Profile summary screen (see Section 36.2 on page 630) to view license registration and
signature information.
• Use the Profile Add/Edit screens (see Section 36.2 on page 630) to set actions for application
categories and for specific applications within the category.
36.1.2 What You Need to Know
If you want to use a service, make sure both the Security Policy and application patrol allow the
service’s packets to go through the Zyxel Device.
Note: The Zyxel Device checks secure policies before it checks application patrol rules for
traffic going through the Zyxel Device.
Application patrol examines every TCP and UDP connection passing through the Zyxel Device and
identifies what application is using the connection. Then, you can specify whether or not the Zyxel
Device continues to route the connection. Traffic not recognized by the application patrol signatures is
ignored.
Application Profiles & Policies
An application patrol profile is a group of categories of application patrol signatures. For each profile,
you can specify the default action the Zyxel Device takes once a packet matches a signature (forward,
drop, or reject a service’s connections and/or create a log alert).
Use policies to link profiles to traffic flows based on criteria such as source zone, destination zone, source
address, destination address, schedule, user.
Classification of Applications
There are two ways the Zyxel Device can identify the application. The first is called auto. The Zyxel
Device looks at the IP payload (OSI level-7 inspection) and attempts to match it with known patterns for

Chapter 36 Application Patrol
USG/ZyWALL User’s Guide
630
specific applications. Usually, this occurs at the beginning of a connection, when the payload is more
consistent across connections, and the Zyxel Device examines several packets to make sure the match
is correct. Before confirmation, packets are forwarded by App Patrol with no action taken. The number
of packets inspected before confirmation varies by signature.
Note: The Zyxel Device allows the first eight packets to go through the security policy,
regardless of the application patrol policy for the application. The Zyxel Device
examines these first eight packets to identify the application.
The second approach is called service ports. The Zyxel Device uses only OSI level-4 information, such as
ports, to identify what application is using the connection. This approach is available in case the Zyxel
Device identifies a lot of “false positives” for a particular application.
Custom Ports for SIP and the SIP ALG
Configuring application patrol to use custom port numbers for SIP traffic also configures the SIP ALG to
use the same port numbers for SIP traffic. Likewise, configuring the SIP ALG to use custom port numbers
for SIP traffic also configures application patrol to use the same port numbers for SIP traffic.
Finding Out More
• You must configure services in Objects > Application.
•See Configuration > BWM chapter for detailed information on bandwidth management.
36.2 Application Patrol Profile
Use the application patrol Profile screens to customize action and log settings for a group of application
patrol signatures. You then link a profile to a policy.Use this screen to create an application patrol
profile, and view signature information. It also lists the registration status and details about the signature
set the Zyxel Device is using.
Note: You must register for the IDP/AppPatrol signature service (at least the trial) before you
can use it.
A profile is an application object(s) or application group(s) that has customized action and log settings.
Click Configuration > UTM Profile > App Patrol > Profile to open the following screen.
Click on the icons to go to the OneSecurity.com website where there is guidance on configuration
walkthroughs, troubleshooting and other information.
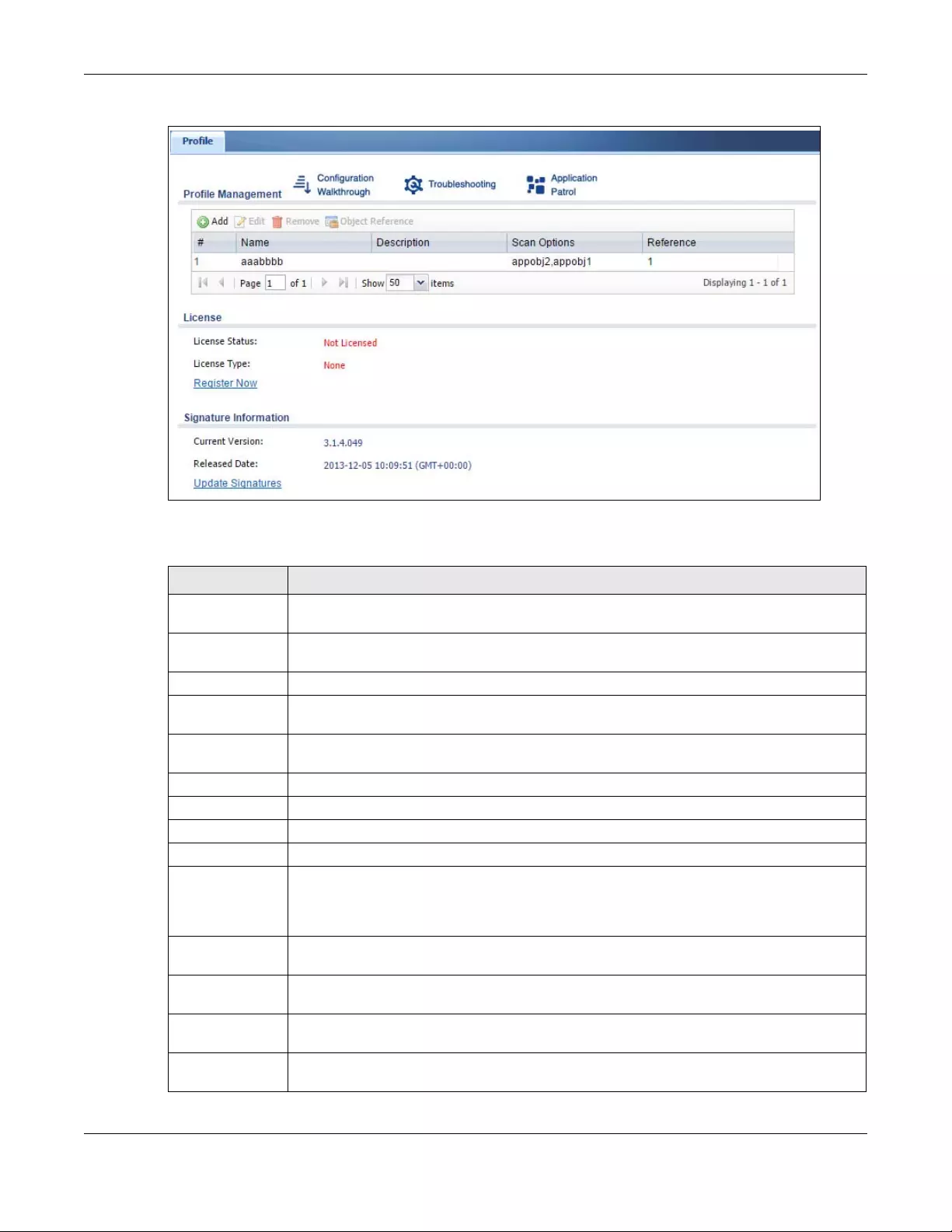
Chapter 36 Application Patrol
USG/ZyWALL User’s Guide
631
Figure 458 Configuration > UTM Profile > App Patrol > Profile
The following table describes the labels in this screen.
Table 240 Configuration > UTM Profile > App Patrol > Profile
LABEL DESCRIPTION
Add Click this to create a new entry. Select an entry and click Add to create a new entry after the
selected entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove Select an entry and click Remove to delete the selected entry.
Object
Reference
Select an entry and click Object References to open a screen that shows which settings use
the entry. Click Refresh to update information on this screen.
# This field is a sequential value showing the number of the profile. The profile order is not
important.
Name This displays the name of the profile created.
Description This displays the description of the App Patrol Profile.
Scan Option This field displays the scan options from the App Patrol profile.
Reference This displays the number of times an object reference is used in a profile.
License You need to create an account at myZyxel.com, register your Zyxel Device and then subscribe
for App Patrol in order to be able to download new packet inspection signatures from
myZyxel.com. There’s an initial free trial period for App Patrol after which you must pay to
subscribe to the service. See the Registration chapter for details.
License Status Licensed, Not Licensed or Expired indicates whether you have subscribed for App Patrol
services or not or your registration has expired.
License Type This field shows Trial, Standard or None depending on whether you subscribed to the App
Patrol trial, bought an iCard for App Patrol service or neither.
Signature
Information
The following fields display information on the current signature set that the Zyxel Device is
using.
Current Version This field displays the App Patrol signature set version number. This number gets larger as the set
is enhanced.
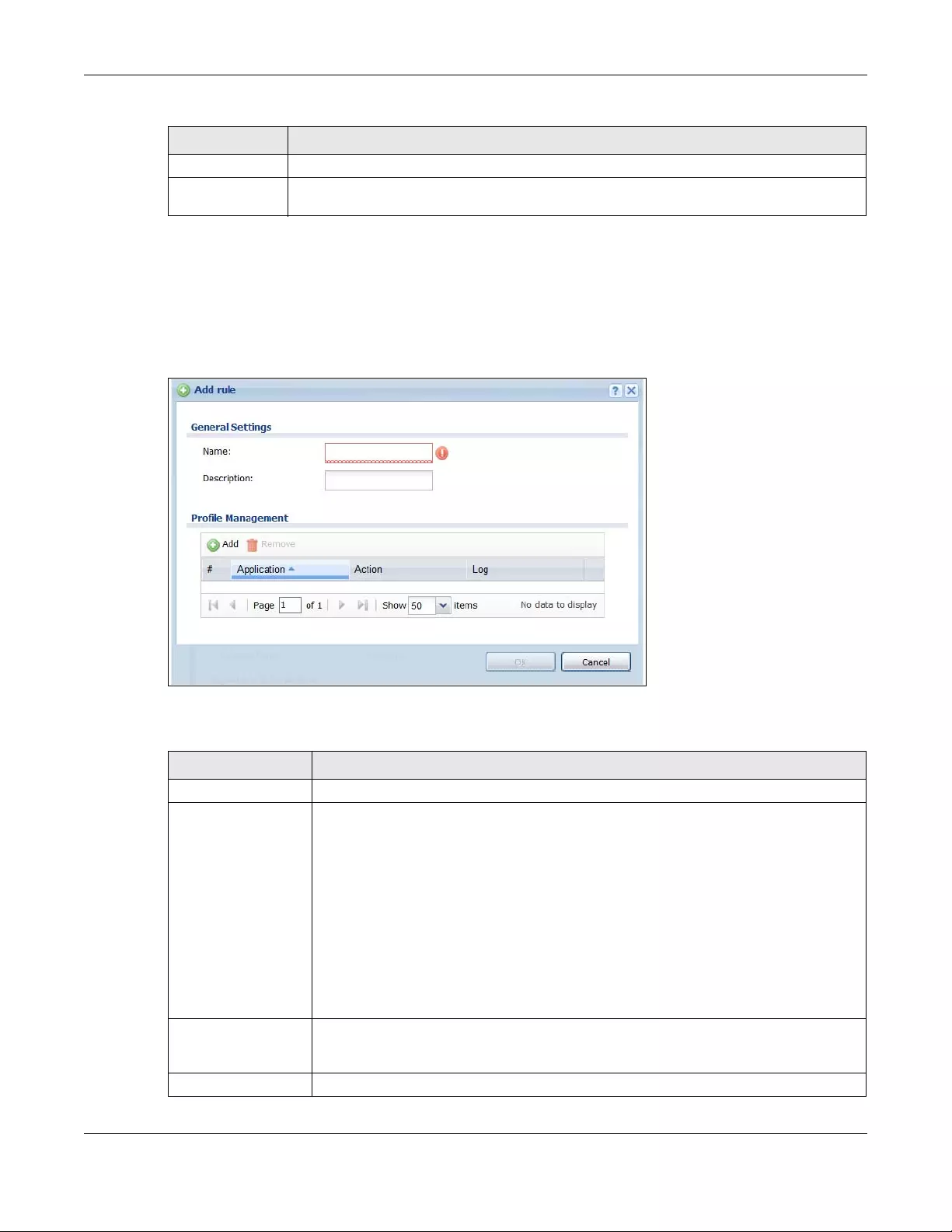
Chapter 36 Application Patrol
USG/ZyWALL User’s Guide
632
36.2.1 The Application Patrol Profile Add/Edit Screen
Use this screen to configure profile settings. Click Configuration > UTM Profile > App Patrol > Profile, then
click Add to create a new profile rule or click an existing profile and click Edit (or double-click it) to open
the following screen.
Figure 459 Configuration > UTM Profile > App Patrol > Profile > Add/Edit
The following table describes the labels in this screen.
Released Date This field displays the date and time the set was released.
Update
Signatures
Click this link to go to the screen you can use to download signatures from the update server.
Table 240 Configuration > UTM Profile > App Patrol > Profile
LABEL DESCRIPTION
Table 241 Configuration > UTM Profile > App Patrol > Profile > Add/Edit
LABEL DESCRIPTION
General Settings
Name Type the name of the profile. You may use 1-31 alphanumeric characters, underscores(_),
or dashes (-), but the first character cannot be a number. This value is case-sensitive. These
are valid, unique profile names:
•MyProfile
•mYProfile
•Mymy12_3-4
These are invalid profile names:
• 1mYProfile
• My Profile
• MyProfile?
• Whatalongprofilename123456789012
Description Type a description for the profile rule to help identify the purpose of rule. You may use 1-31
alphanumeric characters, underscores (_), or dashes (-), but the first character cannot be
a number. This value is case-sensitive. This field is optional.
Profile Management
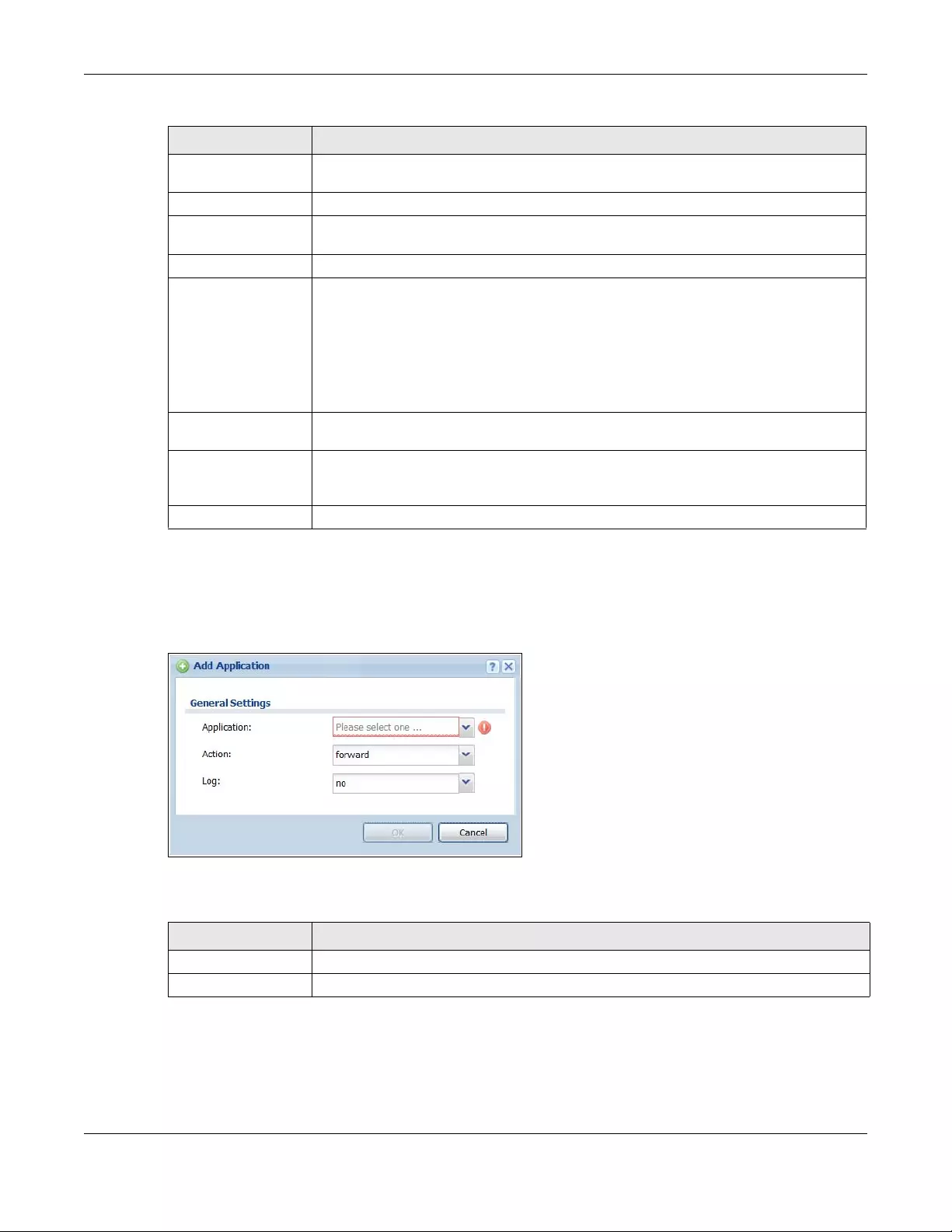
Chapter 36 Application Patrol
USG/ZyWALL User’s Guide
633
36.2.2 The Application Patrol Profile Rule Add Application Screen
Click Add or Edit under Profile Management in the previous screen to display the following screen.
Figure 460 Configuration > UTM Profile > App Patrol > Profile > Profile Management > Add/Edit
The following table describes the labels in this screen.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after
the selected entry.
Remove Select an entry and click Remove to delete the selected entry.
# This field is a sequential value showing the number of the profile. The profile order is not
important.
Application This field displays the application name of the policy.
Action Select the default action for all signatures in this category.
forward - the Zyxel Device routes packets that matches these signatures.
drop - the Zyxel Device silently drops packets that matches these signatures without
notification.
reject - the Zyxel Device drops packets that matches these signatures and sends
notification.
Log Select whether to have the Zyxel Device generate a log (log), log and alert (log alert) or
neither (no) by default when traffic matches a signature in this category.
OK A profile consists of separate category editing screens. If you want to configure just one
category for a profile, click OK to save your settings to the Zyxel Device, complete the
profile and return to the profile summary page.
Cancel Click Cancel to return to the profile summary page without saving any changes.
Table 241 Configuration > UTM Profile > App Patrol > Profile > Add/Edit (continued)
LABEL DESCRIPTION
Table 242 Configuration > UTM Profile > App Patrol > Profile > Profile Management > Add/Edit
LABEL DESCRIPTION
General Settings
Application Select an application to apply the policy.
Chapter 36 Application Patrol
USG/ZyWALL User’s Guide
634
Action Select the default action for all signatures in this category.
forward - the Zyxel Device routes packets that matches these signatures.
drop - the Zyxel Device silently drops packets that matches these signatures without
notification.
reject - the Zyxel Device drops packets that matches these signatures and sends
notification.
Log Select whether to have the Zyxel Device generate a log (log), log and alert (log alert) or
neither (no) by default when traffic matches a signature in this category.
OK Click OK to save your settings to the Zyxel Device.
Cancel Click Cancel to return to the profile summary page without saving any changes.
Table 242 Configuration > UTM Profile > App Patrol > Profile > Profile Management > Add/Edit
LABEL DESCRIPTION

USG/ZyWALL User’s Guide
635
CHAPTER 37
Content Filtering
37.1 Overview
Use the content filtering feature to control access to specific web sites or web content.
37.1.1 What You Can Do in this Chapter
• Use the Filter Profile screens (Section Figure 462 on page 640) to set up content filtering profiles.
• Use the Trusted Web Sites screens (Section 37.4 on page 650) to create a common list of good
(allowed) web site addresses.
• Use the Forbidden Web Sites screens (Section 37.5 on page 651) to create a common list of bad
(blocked) web site addresses.
37.1.2 What You Need to Know
Content Filtering
Content filtering allows you to block certain web features, such as cookies, and/or block access to
specific web sites. It can also block access to specific categories of web site content. You can create
different content filter policies for different addresses, schedules, users or groups and content filter
profiles. For example, you can configure one policy that blocks John Doe’s access to arts and
entertainment web pages during the workday and another policy that lets him access them after work.
Content Filtering Policies
A content filtering policy allows you to do the following.
• Use schedule objects to define when to apply a content filter profile.
• Use address and/or user/group objects to define to whose web access to apply the content filter
profile.
• Apply a content filter profile that you have custom-tailored.
Content Filtering Profiles
A content filtering profile conveniently stores your custom settings for the following features.
• Category-based Blocking
The Zyxel Device can block access to particular categories of web site content, such as pornography
or racial intolerance.
Chapter 37 Content Filtering
USG/ZyWALL User’s Guide
636
• Restrict Web Features
The Zyxel Device can disable web proxies and block web features such as ActiveX controls, Java
applets and cookies.
• Customize Web Site Access
You can specify URLs to which the Zyxel Device blocks access. You can alternatively block access to
all URLs except ones that you specify. You can also have the Zyxel Device block access to URLs that
contain particular keywords.
Content Filtering Configuration Guidelines
When the Zyxel Device receives an HTTP request, the content filter searches for a policy that matches
the source address and time (schedule). The content filter checks the policies in order (based on the
policy numbers). When a matching policy is found, the content filter allows or blocks the request
depending on the settings of the filtering profile specified by the policy. Some requests may not match
any policy. The Zyxel Device allows the request if the default policy is not set to block. The Zyxel Device
blocks the request if the default policy is set to block.
External Web Filtering Service
When you register for and enable the external web filtering service, your Zyxel Device accesses an
external database that has millions of web sites categorized based on content. You can have the Zyxel
Device block, block and/or log access to web sites based on these categories.
HTTPS Domain Filter
HTTPS Domain Filter works with the Content Filter category feature to identify HTTPS traffic and take
appropriate action. SSL Inspection identifies HTTPS traffic for all UTM traffic and has higher priority than
HTTPS Domain Filter. HTTPS Domain Filter only identifies keywords in the domain name of an URL and
matches it to a category. For example, if the keyword is 'picture' and the URL is http://
www.google.com/picture/index.htm, then HTTPS Domain Filter cannot identify 'picture' because that
keyword in not in the domain name 'www.google.com'. However, SSL Inspection can identify 'picture' in
the URL http://www.google.com/picture/index.htm.
Keyword Blocking URL Checking
The Zyxel Device checks the URL’s domain name (or IP address) and file path separately when
performing keyword blocking.
The URL’s domain name or IP address is the characters that come before the first slash in the URL. For
example, with the URL www.zyxel.com.tw/news/pressroom.php, the domain name is
www.zyxel.com.tw.
The file path is the characters that come after the first slash in the URL. For example, with the URL
www.zyxel.com.tw/news/pressroom.php, the file path is news/pressroom.php.
Since the Zyxel Device checks the URL’s domain name (or IP address) and file path separately, it will not
find items that go across the two. For example, with the URL www.zyxel.com.tw/news/pressroom.php,
the Zyxel Device would find “tw” in the domain name (www.zyxel.com.tw). It would also find “news” in
the file path (news/pressroom.php) but it would not find “tw/news”.
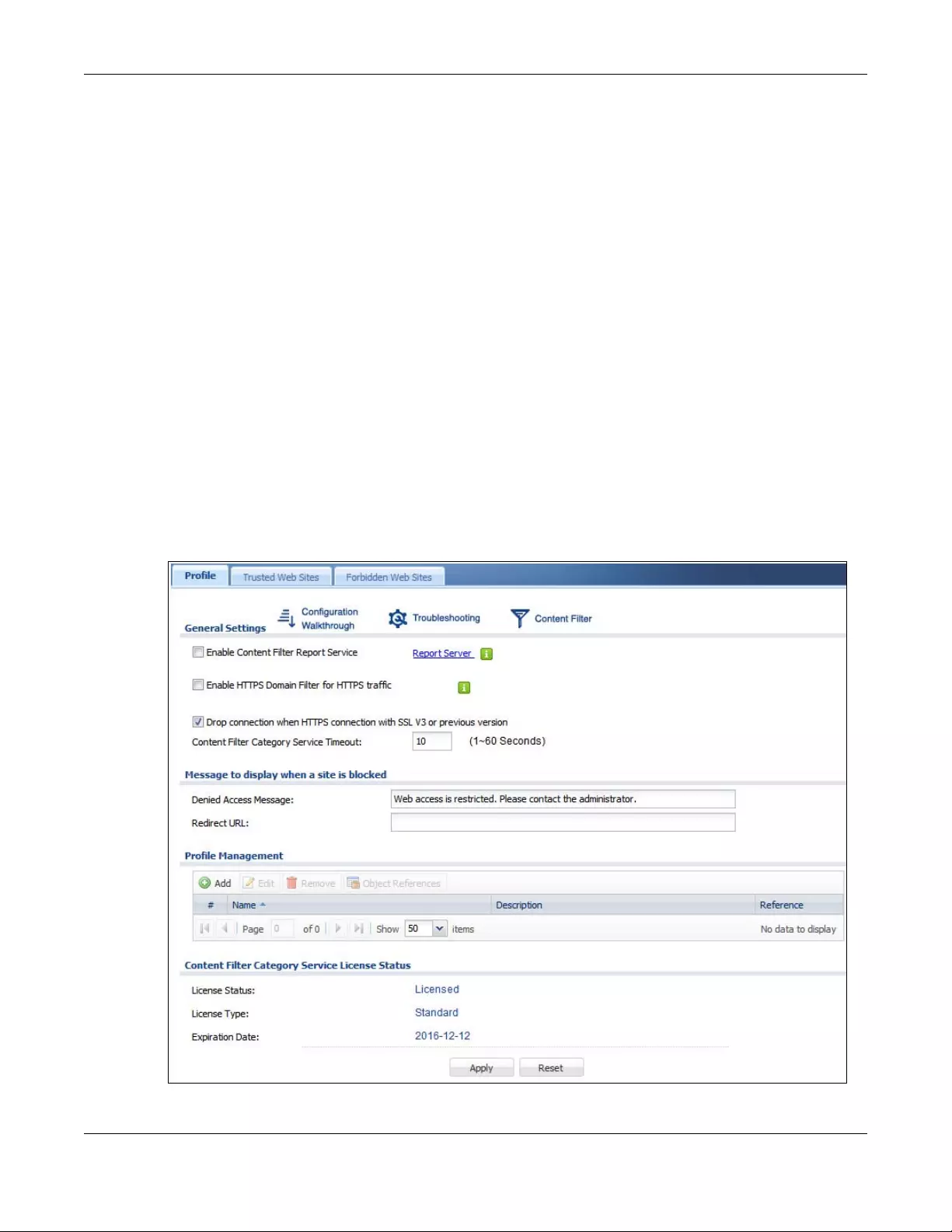
Chapter 37 Content Filtering
USG/ZyWALL User’s Guide
637
Finding Out More
•See Section 37.6 on page 652 for content filtering background/technical information.
37.1.3 Before You Begin
• You must configure an address object, a schedule object and a filtering profile before you can set up
a content security policy.
• You must have Content Filtering license in order to use the function.subscribe to use the external
database content filtering (see the Licensing > Registration screens).
37.2 Content Filter Profile Screen
Click Configuration > UTM Profile> Con tent Filter > Profile to open the Content Filter Profile screen. Use this
screen to enable content filtering, view and order your list of content filter policies, create a denial of
access message or specify a redirect URL and check your external web filtering service registration
status.
Click on the icons to go to the OneSecurity.com website where there is guidance on configuration
walkthroughs, troubleshooting and other information.
Figure 461 Configuration > UTM Profile > Content Filter > Profile
Chapter 37 Content Filtering
USG/ZyWALL User’s Guide
638
The following table describes the labels in this screen.
Table 243 Configuration > UTM Profile > Content Filter > Profile
LABEL DESCRIPTION
General Settings
Enable Content Filter
Report Service
Select this check box to have the Zyxel Device collect category-based content
filtering statistics.
Report Server Click this link to choose where your Zyxel Device is registered: myZyxel.com or
myZyxel.com 2.0. Choose myZyxel.com 2.0 for a model in this series.
Enable HTTPS Domain Filter
for HTTPS traffic
Select this check box to have the Zyxel Device block HTTPS web pages using the
CommTouch category service.
In an HTTPS connection, the Zyxel Device can extract the Server Name Indication
(SNI) from a client request, check if it matches a category in the CommTouch content
filter and then take appropriate action. The keyword match is for the domain name
only.
Drop connection when
HTTPS connection with SSL
V3 or previous version
Select this check box to have the Zyxel Device block HTTPS web pages using SSL V3 or
a previous version.
Content Filter Category
Service Timeout
Specify the allowable time period in seconds for accessing the external web filtering
service’s server.
Denied Access Message Enter a message to be displayed when content filter blocks access to a web page.
Use up to 127 characters (0-9a-zA-Z;/?:@&=+$\.-_!~*'()%,”). For example, “Access to
this web page is not allowed. Please contact the network administrator”.
It is also possible to leave this field blank if you have a URL specified in the Redirect URL
field. In this case if the content filter blocks access to a web page, the Zyxel Device
just opens the web page you specified without showing a denied access message.
Redirect URL Enter the URL of the web page to which you want to send users when their web
access is blocked by content filter. The web page you specify here opens in a new
frame below the denied access message.
Use “http://” or “https://” followed by up to 262 characters (0-9a-zA-Z;/?:@&=+$\.-
_!~*'()%). For example, http://192.168.1.17/blocked access.
Profile Management
Add Click Add to create a new content filter rule.
Edit Click Edit to make changes to a content filter rule.
Remove Click Remove the delete a content filter rule.
Object Reference Select an entry and click Object References to open a screen that shows which
settings use the entry. Click Refresh to update information on this screen.
# This column lists the index numbers of the content filter profile.
Name This column lists the names of the content filter profile rule.
Description This column lists the description of the content filter profile rule.
Reference This displays the number of times an Object Reference is used in a rule.
License Status This read-only field displays the status of your content-filtering database service
registration.
Not Licensed displays if you have not successfully registered and activated the
service.
Expired displays if your subscription to the service has expired.
Licensed displays if you have successfully registered the Zyxel Device and activated
the service.
You can view content filter reports after you register the Zyxel Device and activate
the subscription service in the Registration screen.
Chapter 37 Content Filtering
USG/ZyWALL User’s Guide
639
37.3 Content Filter Profile Add or Edit Screen
Click Configuration > UTM > Content Filter > Profile > Add or Edit to open the Add Filter Profile screen.
Configure Category Service and Custom Service tabs.
37.3.1 Content Filter Add Profile Category Service
License Type This read-only field displays what kind of service registration you have for the content-
filtering database.
None displays if you have not successfully registered and activated the service.
Standard displays if you have successfully registered the Zyxel Device and activated
the service.
Trial displays if you have successfully registered the Zyxel Device and activated the
trial service subscription.
Expiration Date This field displays the date your service license expires.
Register Now This link appears if you have not registered for the service or the service has expired.
Click this link to go to the screen where you can register for the service.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 243 Configuration > UTM Profile > Content Filter > Profile (continued)
LABEL DESCRIPTION
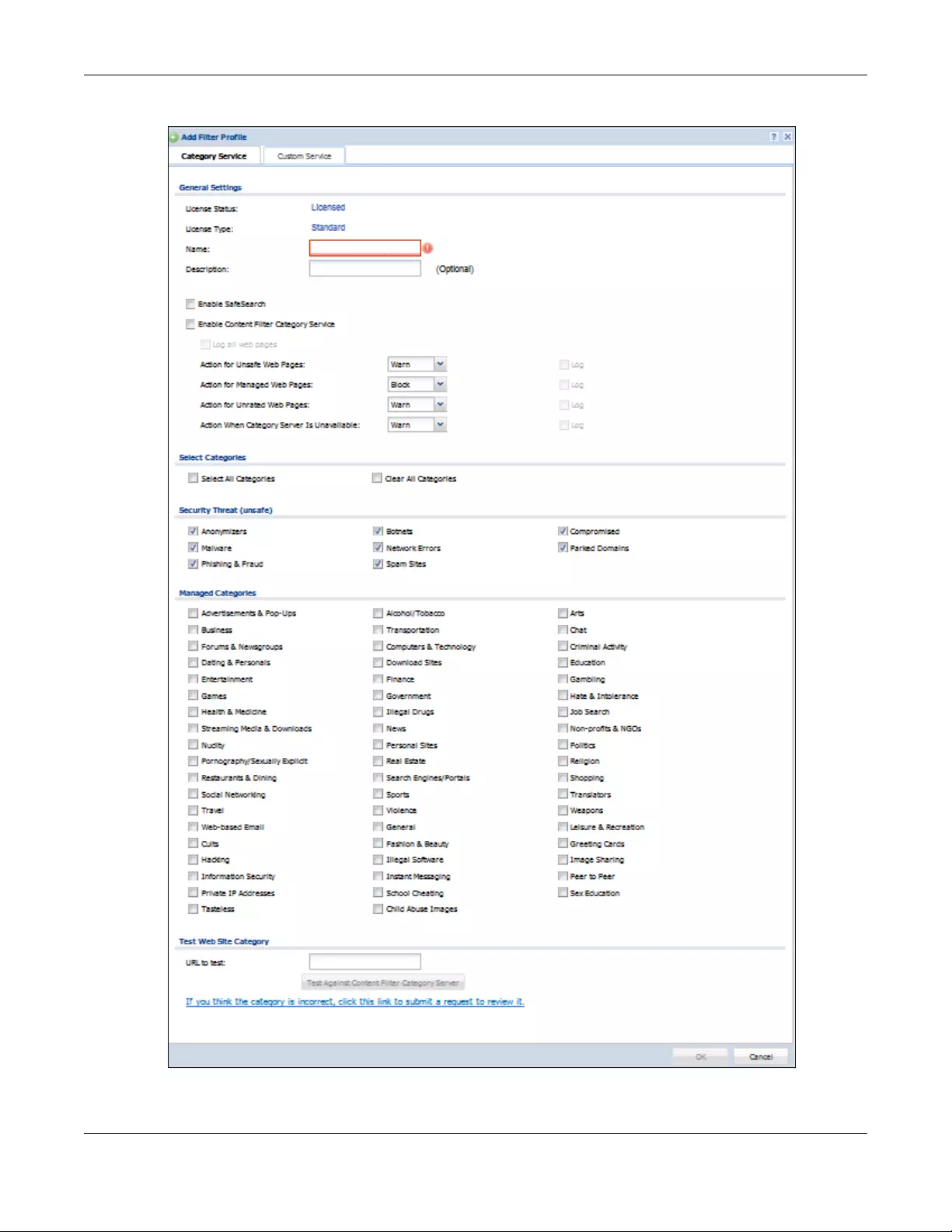
Chapter 37 Content Filtering
USG/ZyWALL User’s Guide
640
Figure 462 Content Filter > Profile > Add Filter Profile > Category Service
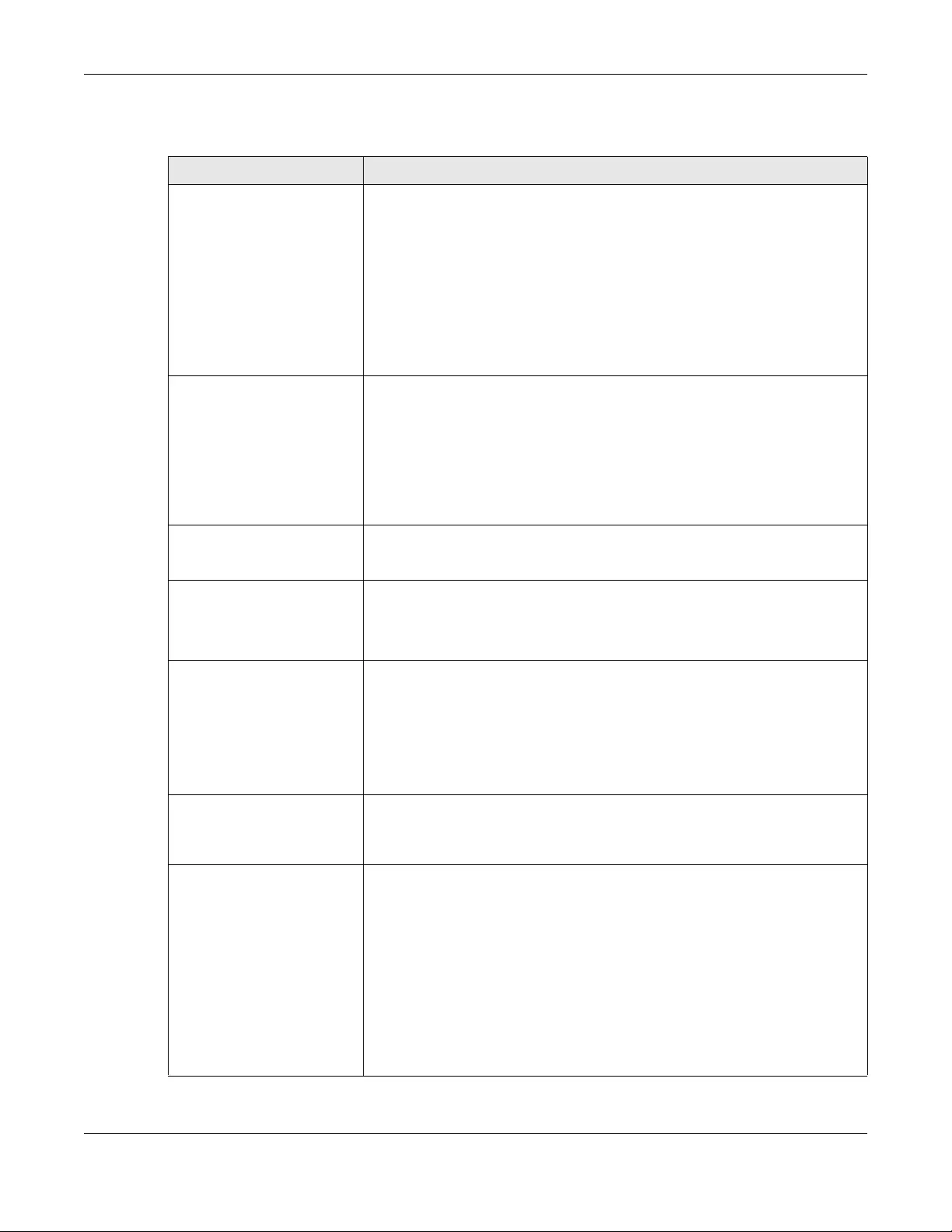
Chapter 37 Content Filtering
USG/ZyWALL User’s Guide
641
The following table describes the labels in this screen.
Table 244 Configuration > UTM Profile> Content Filter > Profile > Add > Category Service
LABEL DESCRIPTION
License Status This read-only field displays the status of your content-filtering database service
registration.
Not Licensed displays if you have not successfully registered and activated the
service.
Expired displays if your subscription to the service has expired.
Licensed displays if you have successfully registered the Zyxel Device and
activated the service.
You can view content filter reports after you register the Zyxel Device and activate
the subscription service in the Registration screen.
License Type This read-only field displays what kind of service registration you have for the
content-filtering database.
None displays if you have not successfully registered and activated the service.
Standard displays if you have successfully registered the Zyxel Device and
activated the standard content filtering service.
Trial displays if you have successfully registered the Zyxel Device and activated
the trial service subscription.
Name Enter a descriptive name for this content filtering profile name. You may use 1-31
alphanumeric characters, underscores(_), or dashes (-), but the first character
cannot be a number. This value is case-sensitive.
Description Enter a description for the content filtering profile rule to help identify the purpose
of rule. You may use 1-31 alphanumeric characters, underscores(_), or dashes (-),
but the first character cannot be a number. This value is case-sensitive.
This field is optional.
Enable SafeSearch SafeSearch is a search engine that can automatically filter sexually explicit videos
and images from the search result without overloading the Zyxel Device. It does
this by adding a parameter in the search URL:
https://www.google.com.tw/?gws_rd=ssl#q=porn&safe=active.
Supported search engines at the time of writing are:
Yahoo, Google, MSN Live Bing, Yandex
Enable Content Filter
Category Service
Enable external database content filtering to have the Zyxel Device check an
external database to find to which category a requested web page belongs. The
Zyxel Device then blocks or forwards access to the web page depending on the
configuration of the rest of this page.
Action for Unsafe Web
Pages Select Pass to allow users to access web pages that match the unsafe categories
that you select below.
Select Block to prevent users from accessing web pages that match the unsafe
categories that you select below. When external database content filtering
blocks access to a web page, it displays the denied access message that you
configured in the Content Filter General screen along with the category of the
blocked web page.
Select Warn to display a warning message before allowing users to access web
pages that match the unsafe categories that you select below.
Select Log to record attempts to access web pages that match the unsafe
categories that you select below.
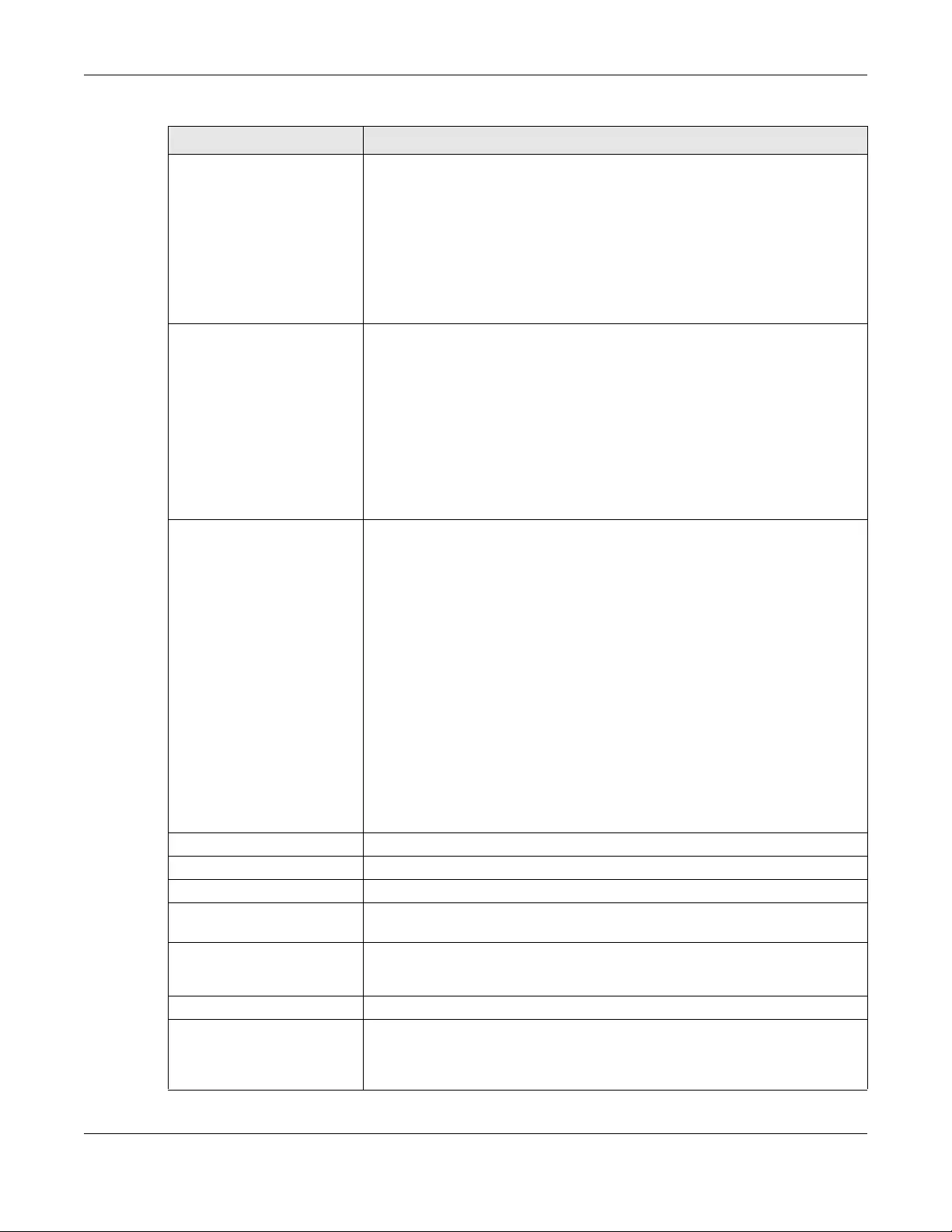
Chapter 37 Content Filtering
USG/ZyWALL User’s Guide
642
Action for Managed Web
Pages Select Pass to allow users to access web pages that match the other categories
that you select below.
Select Block to prevent users from accessing web pages that match the other
categories that you select below. When external database content filtering
blocks access to a web page, it displays the denied access message that you
configured in the Content Filter General screen along with the category of the
blocked web page.
Select Log to record attempts to access web pages that match the other
categories that you select below.
Action for Unrated Web
Pages Select Pass to allow users to access web pages that the external web filtering
service has not categorized.
Select Block to prevent users from accessing web pages that the external web
filtering service has not categorized. When the external database content filtering
blocks access to a web page, it displays the denied access message that you
configured in the Content Filter General screen along with the category of the
blocked web page.
Select Warn to display a warning message before allowing users to access web
pages that the external web filtering service has not categorized.
Select Log to record attempts to access web pages that are not categorized.
Action When Category
Server Is Unavailable Select Pass to allow users to access any requested web page if the external
content filtering database is unavailable.
Select Block to block access to any requested web page if the external content
filtering database is unavailable.
Select Warn to display a warning message before allowing users to access any
requested web page if the external content filtering database is unavailable.
The following are possible causes for the external content filtering server not being
available:
• There is no response from the external content filtering server within the time
period specified in the Content Filter Server Unavailable Timeout field.
• The Zyxel Device is not able to resolve the domain name of the external
content filtering database.
• There is an error response from the external content filtering database. This can
be caused by an expired content filtering registration (External content
filtering’s license key is invalid”).
Select Log to record attempts to access web pages that occur when the external
content filtering database is unavailable.
Select Categories
Select All Categories Select this check box to restrict access to all site categories listed below.
Clear All Categories Select this check box to clear the selected categories below.
Security Threat (unsafe) Thees are the categories of web pages that are known to pose a threat to users or
their computers.
Anonymizers Sites and proxies that act as an intermediary for surfing to other Web sites in an
anonymous fashion, whether to circumvent Web filtering or for other reasons. For
example, blog.go2.tw, anonymizer.com, www.qu365.com.
Botnets Sites that use bots (zombies) including command-and-control sites.
Compromised Sites that have been compromised by someone other than the site owner in order
to install malicious programs without the user's knowledge. Includes sites that may
be vulnerable to a particular high-risk attack. For example, www.wokoo.net,
movie.sx.zj.cn.
Table 244 Configuration > UTM Profile> Content Filter > Profile > Add > Category Service (continued)
LABEL DESCRIPTION
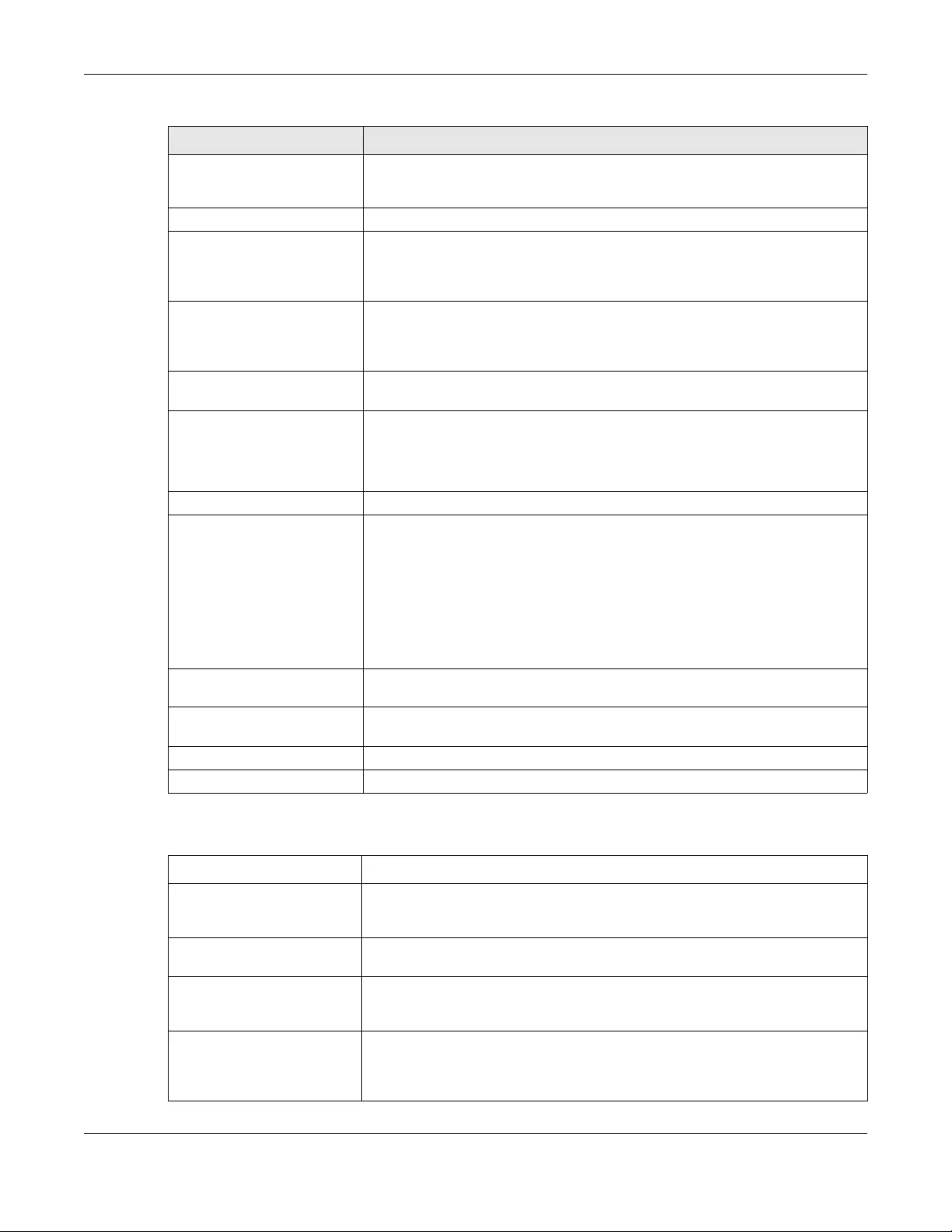
Chapter 37 Content Filtering
USG/ZyWALL User’s Guide
643
The following table describes the managed categories.
Malware Sites that install unwanted software on a user's computer with the intent to enable
third-party monitoring or make system changes without the user's consent. For
example, www.tqlkg.com, aladel.net.
Network Errors Sites that do not resolve to any IP address.
Parked Domains Sites that are inactive, typically reserved for later use. They most often do not
contain their own content, may simply say "under construction," "purchase this
domain," or display advertisements. For example, www.moemoon.com, artlin.net,
img.sedoparking.com.
Phishing & Fraud Sites that are used for deceptive or fraudulent purposes (e.g. phishing), such as
stealing financial or other user account information. These sites are most often
designed to appear as legitimate sites in order to mislead users into entering their
credentials. For example, optimizedby.rmxads.com, 218.1.71.226/.../e3b.
Spam Sites Sites that have been promoted through spam techniques. For example,
img.tongji.linezing.com, banner.chinesegamer.net.
Managed Categories These are categories of web pages based on their content. Select categories in
this section to control access to specific types of Internet content.
You must have the Category Service content filtering license to filter these
categories. See the next table for category details.
Test Web Site Category
URL to test You can check which category a web page belongs to. Enter a web site URL in
the text box.
When the content filter is active, you should see the web page’s category. The
query fails if the content filter is not active.
Content Filtering can query a category by full URL string (for example, http://
www.google.com/picture/index.htm), but HTTPS Domain Filter can only query a
category by domain name ('www.google.com'), so the category may be
different in the query result. URL to test displays both results in the test.
If you think the category is
incorrect
Click this link to see the category recorded in the Zyxel Device’s content filtering
database for the web page you specified (if the database has an entry for it).
Test Against Content Filter
Category Server
Click this button to see the category recorded in the external content filter server’s
database for the web page you specified.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
Table 245 Managed Category Descriptions
CATEGORY DESCRIPTION
Advertisements & Pop-Ups Sites that provide advertising graphics or other ad content files such as banners
and pop-ups. For example, pagead2.googlesyndication.com,
ad.yieldmanager.com.
Alcohol & Tobacco Sites that promote or sell alcohol- or tobacco-related products or services. For
example, www.drinks.com.tw, www.p9.com.tw, beer.ttl.com.tw.
Arts Sites with artistic content or relating to artistic institutions such as theaters,
museums, galleries, dance companies, photography, and digital graphic
resources. For example, www.npm.gov.tw, www.nmh.gov.tw.
Business Sites that provide business related information such as corporate Web sites.
Information, services, or products that help businesses of all sizes to do their day-to-
day commercial activities. For example, www.kinkos.com,
www.proctorgamble.com, www.bbb.org.
Table 244 Configuration > UTM Profile> Content Filter > Profile > Add > Category Service (continued)
LABEL DESCRIPTION
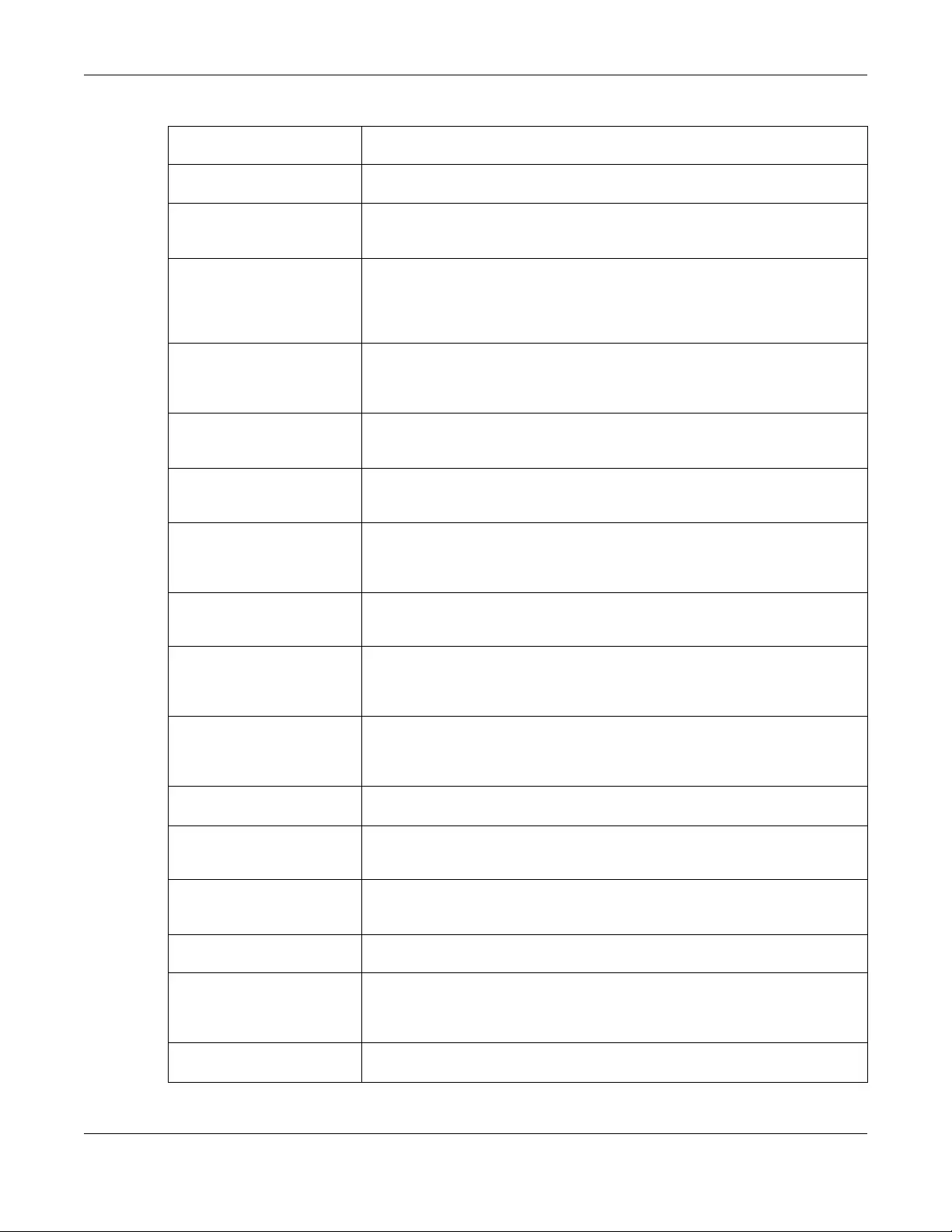
Chapter 37 Content Filtering
USG/ZyWALL User’s Guide
644
Chat Sites that enable web-based exchange of real time messages through chat
services or chat rooms. For example, me.sohu.com, blufiles.storage.live.com.
Child Abuse Images Sites that portray or discuss children in sexual or other abusive acts. For example,
a.uuzhijia.info.
Computers & Technology Sites that contain information about computers, software, hardware, IT, peripheral
and computer services, such as product reviews, discussions, and IT news. For
example, www.informationsecurity.com.tw, blog.ithome.com.tw.
Criminal Activity Sites that offer advice on how to commit illegal or criminal activities, or to avoid
detection. These can include how to commit murder, build bombs, pick locks, etc.
Also includes sites with information about illegal manipulation of electronic
devices, hacking, fraud and illegal distribution of software. For example,
www.hackbase.com, jia.hackbase.com, ad.adver.com.tw.
Cults Sites relating to non-traditional religious practice typically known as "cults," that is,
considered to be false, unorthodox, extremist, or coercive, with members often
living under the direction of a charismatic leader. For example,
www.churchofsatan.com, www.ccya.org.tw.
Dating & Personals Sites that promote networking for interpersonal relationships such as dating and
marriage. Includes sites for match-making, online dating, spousal introduction. For
example, www.i-part.com.tw, www.imatchi.com.
Download Sites Sites that contain downloadable software, whether shareware, freeware, or for a
charge. Includes peer-to-peer sites. For example, www.hotdl.com,
toget.pchome.com.tw, www.azroo.com.
Education Sites sponsored by educational institutions and schools of all types including
distance education. Includes general educational and reference materials such
as dictionaries, encyclopedias, online courses, teaching aids and discussion
guides. For example, www.tfam.museum, www.lksf.org, www.1980.org.tw.
Entertainment Sites related to television, movies, music and video (including video on demand),
such as program guides, celebrity sites, and entertainment news. For example,
www.ctitv.com.tw, www.hboasia.com, www.startv.com.tw.
Fashion & Beauty Sites concerning fashion, jewelry, glamour, beauty, modeling, cosmetics or related
products or services. Includes product reviews, comparisons, and general
consumer information. For example, women.sohu.com,
baodian.women.sohu.com.
Finance Sites related to banking, finance, payment or investment, including banks,
brokerages, online stock trading, stock quotes, fund management, insurance
companies, credit unions, credit card companies, and so on. For example,
www.concords.com.tw, www.polaris.com.tw, www.bochk.com.
Forums & Newsgroups Sites for sharing information in the form of newsgroups, forums, bulletin boards. For
example, ck101.com, my.xuite.net, ptt.cc.
Gambling Sites that offer or are related to online gambling, lottery, casinos and betting
agencies involving chance. For example, www.taiwanlottery.com.tw, www.i-
win.com.tw, www.hkjc.com.
Games Sites relating to computer or other games, information about game producers, or
how to obtain cheat codes. Game-related publication sites. For example,
www.gamer.com.tw, www.wowtaiwan.com.tw, tw.lineage.gamania.com.
General Sites that do not clearly fall into other categories, for example, blank Web pages.
For example, bs.serving-sys.com, simg.sinajs.cn, i0.itc.cn.
Government Sites run by governmental organizations, departments, or agencies, including
police departments, fire departments, customs bureaus, emergency services, civil
defense, counter-terrorism organizations, military and hospitals. For example,
www.ey.gov.tw, www.whitehouse.gov, www.npa.gov.tw.
Greeting cards Sites that allow people to send and receive greeting cards and postcards. For
example, www.e-card.com.tw, card.ivy.net.tw.
Table 245 Managed Category Descriptions (continued)
Chapter 37 Content Filtering
USG/ZyWALL User’s Guide
645
Hacking Sites that promote or give advice about how to gain unauthorized access to
proprietary computer systems, for the purpose of stealing information,
perpetrating fraud, creating viruses, or committing other illegal activity related to
theft of digital information. For example, www.hackbase.com,
www.chinahacker.com.
Hate & Intolerance Sites that promote a supremacist political agenda, encouraging oppression of
people or groups of people based on their race, religion, gender, age, disability,
sexual orientation or nationality. For example, www.racist-jokes.com, aryan-
nations.org, whitepower.com.
Health & Medicine Sites containing information pertaining to health, healthcare services, fitness and
well-being, including information about medical equipment, hospitals, drugstores,
nursing, medicine, procedures, prescription medications, etc. For example,
www.lksf.org, www.ohayo.com.tw.
Illegal Drug Sites with information on the purchase, manufacture, and use of illegal or
recreational drugs and their paraphernalia, and misuse of prescription drugs and
other compounds For example, www.cannabis.net, www.amphetamines.com.
Illegal Software Sites that illegally distribute software or copyrighted materials such as movies or
music, software cracks, illicit serial numbers, illegal license key generators. For
example, www.zhaokey.com.cn, www.tiansha.net.
Image Sharing Sites that host digital photographs and images, online photo albums and digital
photo exchanges. For example, photo.pchome.com.tw, photo.xuite.net,
photobucket.com.
Information Security Sites that provide legitimate information about data protection, including newly
discovered vulnerabilities and how to block them. For example,
www.informationsecurity.com.tw, www.itis.tw.
Instant Messaging Sites that enable logging in to instant messaging services such as ICQ, AOL Instant
Messenger, IRC, MSN, Jabber, Yahoo Messenger, and the like. For example,
www.meebo.com, www.aim.com, www. ebuddy.com.
Job Search Sites containing job listings, career information, assistance with job searches (such
as resume writing, interviewing tips, etc.), employment agencies or head hunters.
For example, www.104.com.tw, www.1111.com.tw, www.yes123.com.tw.
Leisure & Recreation Sites relating to recreational activities and hobbies including zoos, public
recreation centers, pools, amusement parks, and hobbies such as gardening,
literature, arts & crafts, home improvement, home d?cor, family, etc. For example,
tpbg.tfri.gov.tw, tw.fashion.yahoo.com, www.relaxtimes.com.tw.
News Sites covering news and current events such as newspapers, newswire services,
personalized news services, broadcasting sites, and magazines. For example,
www.tvbs.com.tw?Awww.ebc.net.tw?Awww.iset.com.tw.
Non-profits & NGOs Sites devoted to clubs, communities, unions, and non-profit organizations. Many of
these groups exist for educational or charitable purposes. For example,
www.tzuchi.org.tw, web.redcross.org.tw, www.lksf.org.
Nudity Sites that contain full or partial nudity that are not necessarily overtly sexual in
intent. Includes sites that advertise or sell lingerie, intimate apparel, or swim wear.
For example, www.easyshop.com.tw, www.faster-swim.com.tw,
image.baidu.com.
Peer-to-Peer Sites that enable direct exchange of files between users without dependence on
a central server. For example, www.eyny.com.
Personal Sites Sites about or hosted by personal individuals, including those hosted on
commercial sites. For example, blog.yam.com, www.wretch.cc, blog.xuite.net.
Politics Sites that promote political parties or political advocacy, or provide information
about political parties, interest groups, elections, legislation or lobbying. Also
includes sites that offer legal information and advice. For example,
www.kmt.org.tw, www.dpp.org.tw, cpc.people.com.cn.
Table 245 Managed Category Descriptions (continued)
Chapter 37 Content Filtering
USG/ZyWALL User’s Guide
646
Pornography/Sexually Explicit Sites that contain explicit sexual content. Includes adult products such as sex toys,
CD-ROMs, and videos, adult services such as videoconferencing, escort services,
and strip clubs, erotic stories and textual descriptions of sexual acts. For example,
www.dvd888.com, www.18center.com, blog.sina.com.tw.
Private IP Addresses Sites that are private IP addresses as defined in RFC 1918, that is, hosts that do not
require access to hosts in other enterprises (or require just limited access) and
whose IP address may be ambiguous between enterprises but are well defined
within a certain enterprise. For example, 172.21.20.123, 192.168.35.62.
Real Estate Sites relating to commercial or residential real estate services, including renting,
purchasing, selling or financing homes, offices, etc. For example,
www.sinyi.com.tw, www.yungching.com.tw, house.focus.cn.
Religion Sites that deal with faith, human spirituality or religious beliefs, including sites of
churches, synagogues, mosques and other houses of worship. For example,
www.fgs.org.tw, www.twtaoism.net, www.fhl.net.
Restaurants & Dining Sites that list, review, promote or advertise food, dining or catering services.
Includes sites for recipes, cooking instruction and tips, food products, and wine
advisors. For example, www.jogoya.com.tw, www.dintaifung.com.tw,
www2.pizzahut.com.tw.
School Cheating Sites that promote unethical practices such as cheating or plagiarism by providing
test answers, written essays, research papers, or term papers. For example,
www.zydk788.com, www.huafengksw.com.
Search Engines & Portals Sites enabling the searching of the Web, newsgroups, images, directories, and
other online content. Includes portal and directory sites such as white/yellow
pages. For example, tw.yahoo.com, www.pchome.com.tw, www.google.com.tw.
Sex Education Sites relating to sex education, including subjects such as respect for partner,
abortion, gay and lesbian lifestyle, contraceptives, sexually transmitted diseases,
and pregnancy. For example, apps.rockyou.com, www.howmama.com.tw,
www.mombaby.com.tw.
Shopping Sites for online shopping, catalogs, online ordering, auctions, classified ads.
Excludes shopping for products and services exclusively covered by another
category such as health & medicine. For example, shopping.pchome.com.tw,
buy.yahoo.com.tw, www.tkec.com.tw.
Social Networking Sites that enable social networking for online communities of various topics, for
friendship, dating, or professional reasons. For example, www.facebook.com,
www.flickr.com, www.groups.google.com.
Sports Sites relating to sports teams, fan clubs, scores and sports news. Relates to all
sports, whether professional or recreational. For example, www.yankees.com,
www.nba.com, mlb.mlb.com.
Streaming Media &
Downloads
Sites that deliver streaming content, such as Internet radio, Internet TV or MP3 and
live or archived media download sites. Includes fan sites, or official sites run by
musicians, bands, or record labels. For example, www.youtube.com,
pfp.sina.com.cn, my.xunlei.com.
Tasteless Sites with offensive or tasteless content such as bathroom humor or profanity. For
example, comedycentral.com, dilbert.com.
Translators Sites that translate Web pages or phrases from one language to another. These
sites may be used to attempt to bypass a filtering system. For example,
translate.google.com.tw, www.smartlinkcorp.com, translation.paralink.com.
Transportation Sites that provide information about motor vehicles such as cars, motorcycles,
boats, trucks, RVs and the like. Includes manufacturer sites, dealerships, review
sites, pricing,, online purchase sites, enthusiasts clubs, etc. For example,
www.toyota.com.tw, www.ford.com.tw, www.sym.com.tw.
Travel Sites that provide travel and tourism information or online booking of travel
services such as airlines, accommodations, car rentals. Includes regional or city
information sites. For example, www.startravel.com.tw, taipei.grand.hyatt.com.tw,
www.car-plus.com.tw.
Table 245 Managed Category Descriptions (continued)
Chapter 37 Content Filtering
USG/ZyWALL User’s Guide
647
37.3.2 Content Filter Add Filter Profile Custom Service
Click Configuration > UTM Profile > Content Filter > Filter Profile > Add or Edit > Custom Service to open
the Custom Service screen. You can create a list of good (allowed) web site addresses and a list of bad
(blocked) web site addresses. You can also block web sites based on whether the web site’s address
contains a keyword. Use this screen to add or remove specific sites or keywords from the filter list.
Unknown Unknown For example, www.669.com.tw, www.appleballoon.com.tw,
www.uimco.com.tw.
Violence Sites that contain images or text depicting or advocating physical assault against
humans, animals, or institutions. Sites of a particularly gruesome nature such as
shocking depictions of blood or wounds, or cruel animal treatment. For example,
crimescene.com, deathnet.com, michiganmilitia.com.
Weapons Sites that depict, sell, review or describe guns and weapons, including for sport. For
example, www.ak-47.net, warfare.ru.
Web-based Email Sites that enable users to send and receive email through a web-accessible email
account. For example, mail.163.com, mail.google.com, mail.yahoo.com.tw.
Table 245 Managed Category Descriptions (continued)
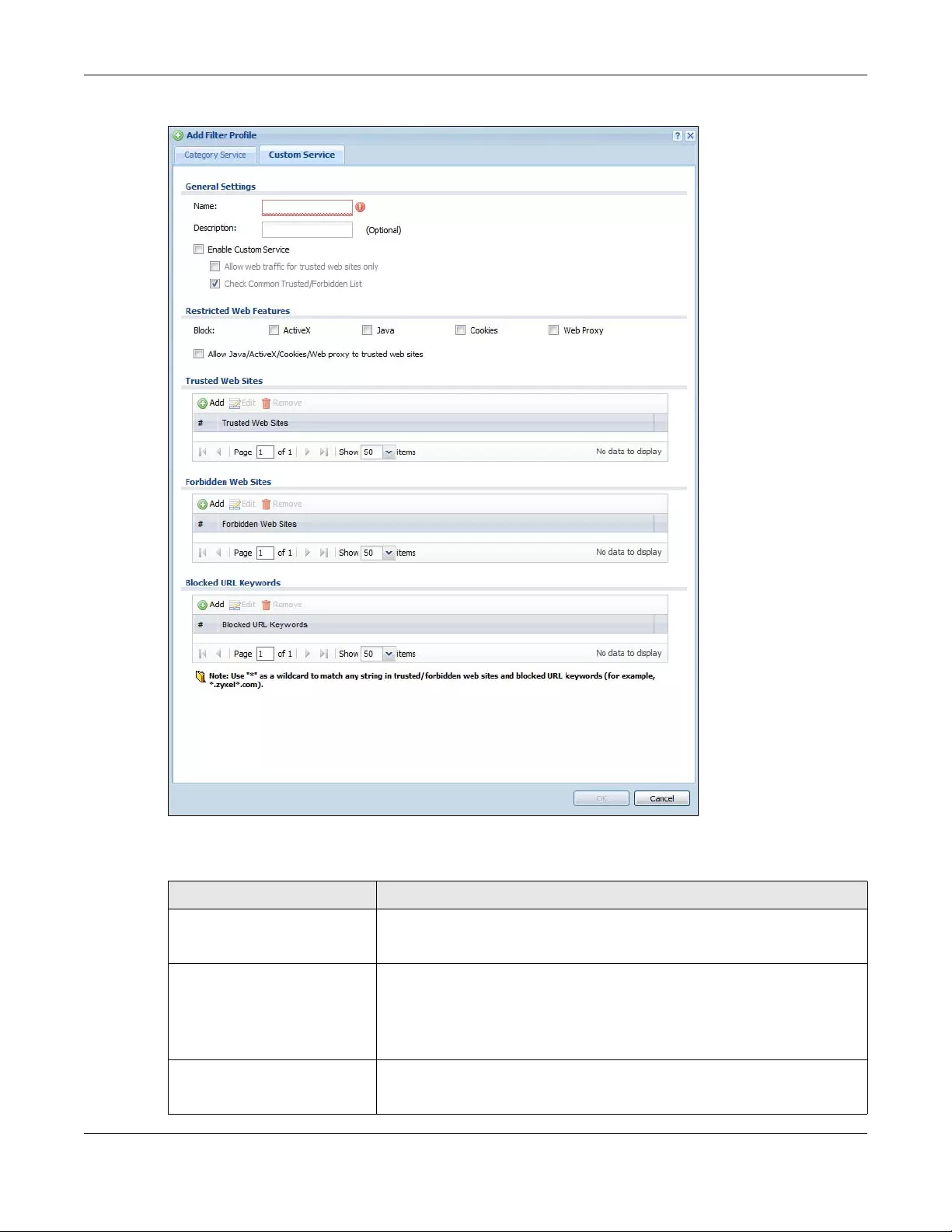
Chapter 37 Content Filtering
USG/ZyWALL User’s Guide
648
Figure 463 Configuration > UTM Profile > Content Filter > Filter Profile > Custom Service
The following table describes the labels in this screen.
Table 246 Configuration > UTM Profile > Content Filter > Profile > Custom Service
LABEL DESCRIPTION
Name Enter a descriptive name for this content filtering profile name. You may use 1-31
alphanumeric characters, underscores(_), or dashes (-), but the first character
cannot be a number. This value is case-sensitive.
Description Enter a description for the content filtering profile rule to help identify the
purpose of rule. You may use 1-31 alphanumeric characters, underscores(_), or
dashes (-), but the first character cannot be a number. This value is case-
sensitive.
This field is optional.
Enable Custom Service Select this check box to allow trusted web sites and block forbidden web sites.
Content filter list customization may be enabled and disabled without re-
entering these site names.
Chapter 37 Content Filtering
USG/ZyWALL User’s Guide
649
Allow Web traffic for trusted web
sites only
When this box is selected, the Zyxel Device blocks Web access to sites that are
not on the Trusted Web Sites list. If they are chosen carefully, this is the most
effective way to block objectionable material.
Check Common Trusted/
Forbidden List
Select this check box to check the common trusted and forbidden web sites
lists. See Section 37.4 on page 650 and Section 37.5 on page 651 for information
on configuring these lists.
Restricted Web Features Select the check box(es) to restrict a feature. Select the check box(es) to
restrict a feature.
• When you download a page containing ActiveX or Java, that part of the
web page will be blocked with an X.
• When you download a page coming from a Web Proxy, the whole web
page will be blocked.
• When you download a page containing cookies, the cookies will be
removed, but the page will not be blocked.
Block
ActiveX
ActiveX is a tool for building dynamic and active web pages and distributed
object applications. When you visit an ActiveX web site, ActiveX controls are
downloaded to your browser, where they remain in case you visit the site again.
Java Java is a programming language and development environment for building
downloadable Web components or Internet and intranet business applications
of all kinds.
Cookies Cookies are files stored on a computer’s hard drive. Some web servers use them
to track usage and provide service based on ID.
Web Proxy A server that acts as an intermediary between a user and the Internet to
provide security, administrative control, and caching service. When a proxy
server is located on the WAN it is possible for LAN users to circumvent content
filtering by pointing to this proxy server.
Allow Java/ActiveX/Cookies/
Web proxy to trusted web sites
When this box is selected, the Zyxel Device will permit Java, ActiveX and
Cookies from sites on the Trusted Web Sites list to the LAN. In certain cases, it
may be desirable to allow Java, ActiveX or Cookies from sites that are known
and trusted.
Trusted Web Sites These are sites that you want to allow access to, regardless of their content
rating, can be allowed by adding them to this list.
Add Click this to create a new entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
# This displays the index number of the trusted web sites.
Trusted Web Site This column displays the trusted web sites already added.
Enter host names such as www.good-site.com into this text field. Do not enter
the complete URL of the site – that is, do not include “http://”. All subdomains
are allowed. For example, entering “*zyxel.com” also allows “www.zyxel.com”,
“partner.zyxel.com”, “press.zyxel.com”, and so on. You can also enter just a top
level domain. For example, enter “*.com” to allow all .com domains.
Use up to 127 characters (0-9a-z-). The casing does not matter. “*” can be used
as a wildcard to match any string. The entry must contain at least one “.” or it
will be invalid.
Forbidden Web Site List Sites that you want to block access to, regardless of their content rating, can be
allowed by adding them to this list.
Add Click this to create a new entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
Table 246 Configuration > UTM Profile > Content Filter > Profile > Custom Service (continued)
LABEL DESCRIPTION
Chapter 37 Content Filtering
USG/ZyWALL User’s Guide
650
37.4 Content Filter Trusted Web Sites Screen
Click Configuration > UTM Profile > Content Filter > Trusted Web Sites to open the Trusted Web Sites
screen. You can create a common list of good (allowed) web site addresses. When you configure Filter
Profiles, you can select the option to check the Common Trusted Web Sites list. Use this screen to add or
remove specific sites from the filter list.
# This displays the index number of the forbidden web sites.
Forbidden Web Sites This list displays the forbidden web sites already added.
Enter host names such as www.bad-site.com into this text field. Do not enter the
complete URL of the site – that is, do not include “http://”. All subdomains are
also blocked. For example, entering “*bad-site.com” also blocks “www.bad-
site.com”, “partner.bad-site.com”, “press.bad-site.com”, and do on. You can
also enter just a top level domain. For example, enter “*.com” to block all .com
domains.
Use up to 127 characters (0-9a-z-). The casing does not matter. “*” can be used
as a wildcard to match any string. The entry must contain at least one “.” or it
will be invalid.
Blocked URL Keywords This section allows you to block Web sites with URLs that contain certain
keywords in the domain name or IP address.
Add Click this to create a new entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
# This displays the index number of the blocked URL keywords.
Blocked URL Keywords This list displays the keywords already added.
Enter a keyword or a numerical IP address to block. You can also enter a
numerical IP address.
Use up to 127 case-insensitive characters (0-9a-zA-Z;/?:@&=+$\.-_!~*()%). “*”
can be used as a wildcard to match any string. Use “|*” to indicate a single
wildcard character.
For example enter *Bad_Site* to block access to any web page that includes
the exact phrase Bad_Site. This does not block access to web pages that only
include part of the phrase (such as Bad for example).
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
Table 246 Configuration > UTM Profile > Content Filter > Profile > Custom Service (continued)
LABEL DESCRIPTION
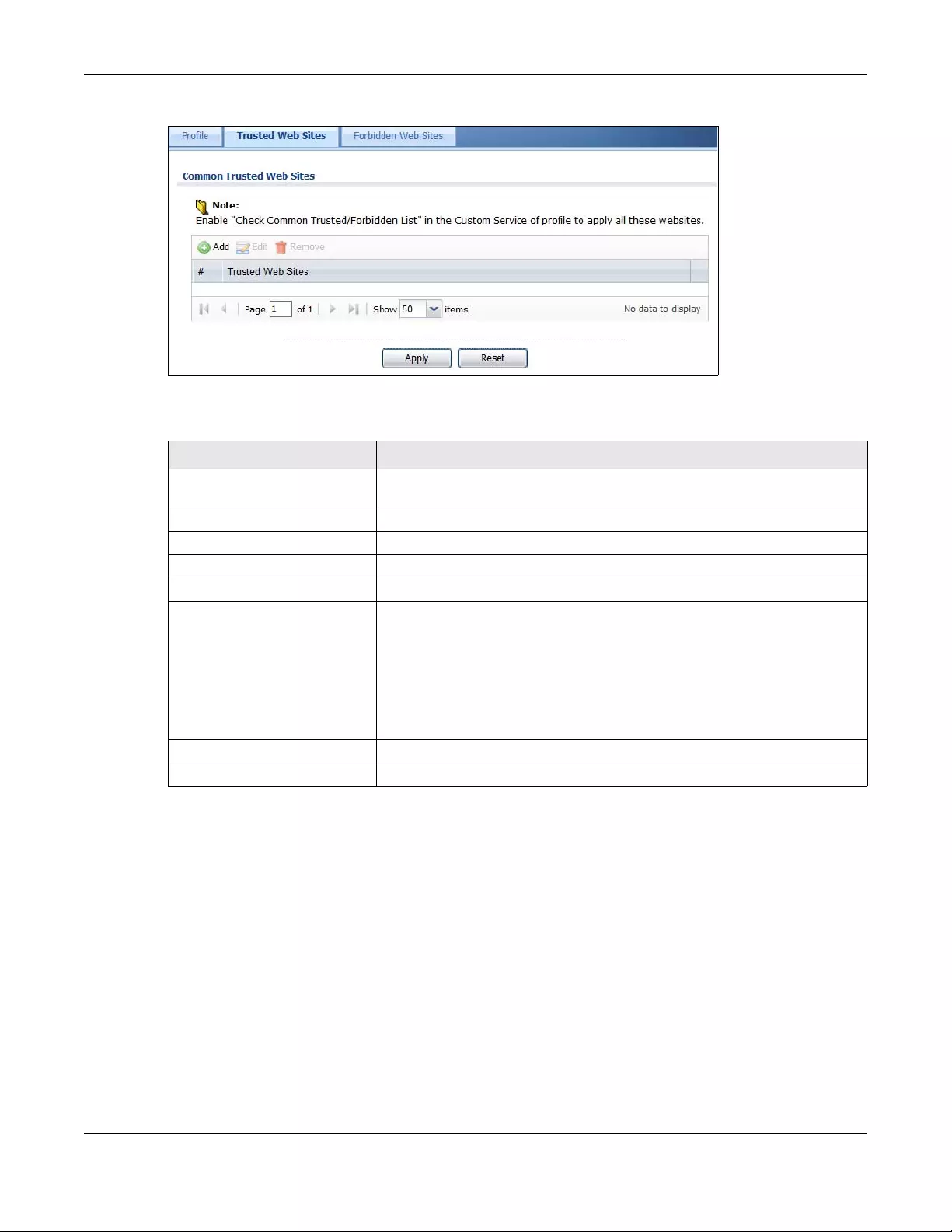
Chapter 37 Content Filtering
USG/ZyWALL User’s Guide
651
Figure 464 Configuration > UTM Profile > Content Filter > Trusted Web Sites
The following table describes the labels in this screen.
37.5 Content Filter Forbidden Web Sites Screen
Click Configuration > UTM Profile > Content Filter > Forbidden Web Sites to open the Forbidden Web Sites
screen. You can create a common list of bad (blocked) web site addresses. When you configure Filter
Profiles, you can select the option to check the Common Forbidden Web Sites list. Use this screen to add
or remove specific sites from the filter list.
Table 247 Configuration > UTM Profile > Content Filter > Trusted Web Sites
LABEL DESCRIPTION
Common Trusted Web Sites These are sites that you want to allow access to, regardless of their content
rating, can be allowed by adding them to this list.
Add Click this to create a new entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
# This displays the index number of the trusted web sites.
Trusted Web Site This column displays the trusted web sites already added.
Enter host names such as www.good-site.com into this text field. Do not enter
the complete URL of the site – that is, do not include “http://”. All subdomains
are allowed. For example, entering “zyxel.com” also allows “www.zyxel.com”,
“partner.zyxel.com”, “press.zyxel.com”, and so on. You can also enter just a top
level domain. For example, enter .com to allow all .com domains.
Use up to 127 characters (0-9a-z-). The casing does not matter.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
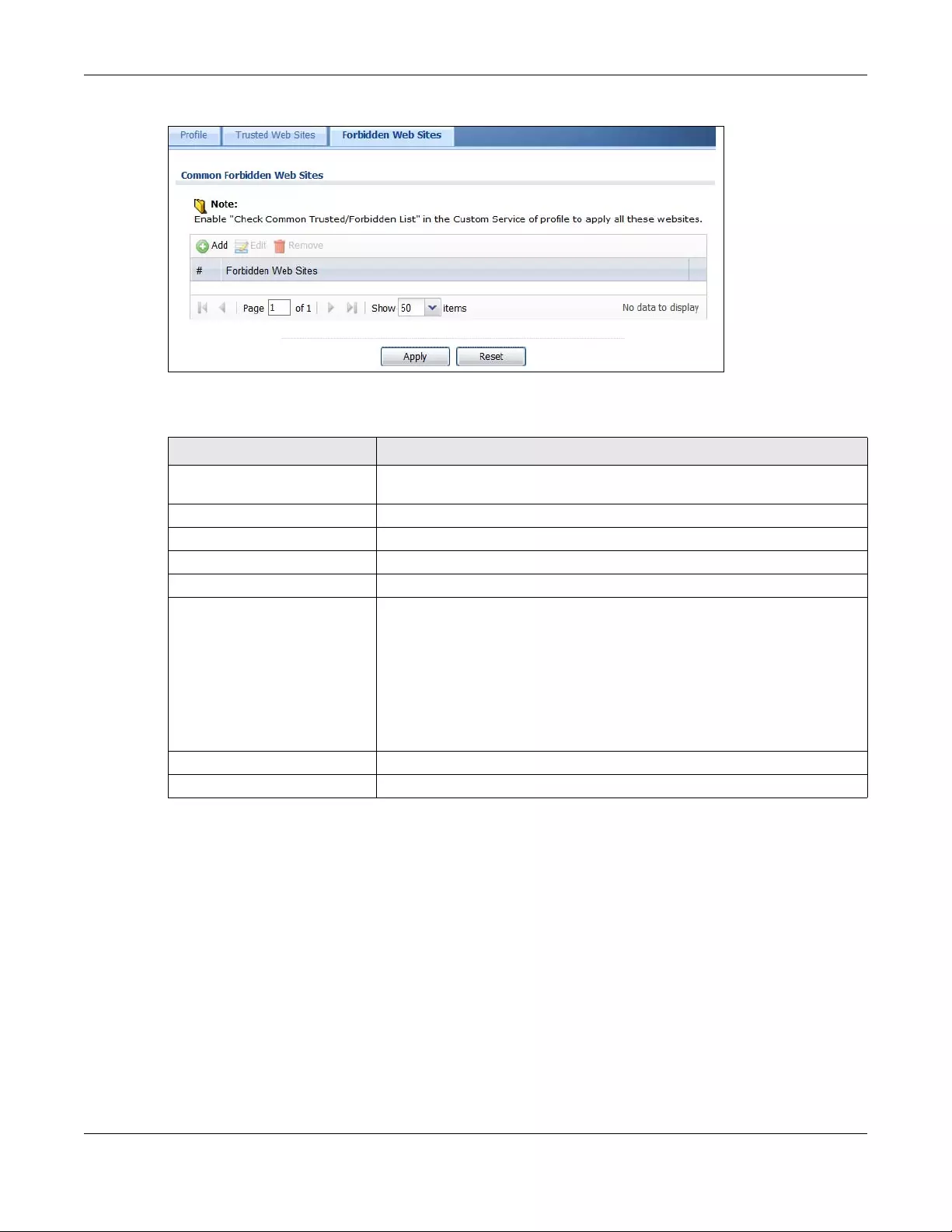
Chapter 37 Content Filtering
USG/ZyWALL User’s Guide
652
Figure 465 Configuration > UTM Profile > Content Filter > Forbidden Web Sites
The following table describes the labels in this screen.
37.6 Content Filter Technical Reference
This section provides content filtering background information.
External Content Filter Server Lookup Procedure
The content filter lookup process is described below.
Table 248 Configuration > UTM Profile > Content Filter > Forbidden Web Sites
LABEL DESCRIPTION
Forbidden Web Site List Sites that you want to block access to, regardless of their content rating, can be
allowed by adding them to this list.
Add Click this to create a new entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
# This displays the index number of the forbidden web sites.
Forbidden Web Sites This list displays the forbidden web sites already added.
Enter host names such as www.bad-site.com into this text field. Do not enter the
complete URL of the site – that is, do not include “http://”. All subdomains are
also blocked. For example, entering “bad-site.com” also blocks “www.bad-
site.com”, “partner.bad-site.com”, “press.bad-site.com”, and do on. You can
also enter just a top level domain. For example, enter .com to block all .com
domains.
Use up to 127 characters (0-9a-z-). The casing does not matter.
Apply Click Apply to save your changes back to the Zyxel Device.
Cancel Click Reset to return the screen to its last-saved settings.
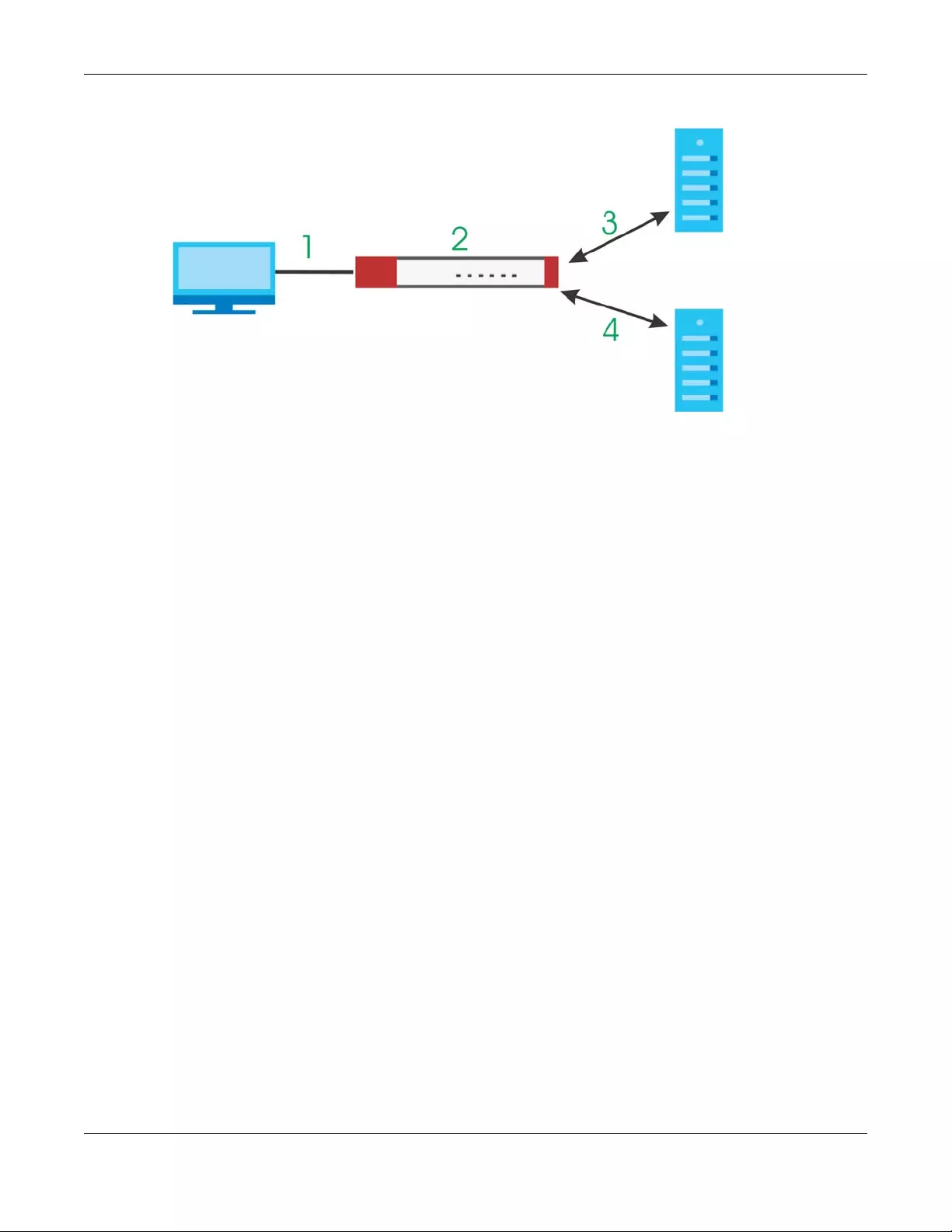
Chapter 37 Content Filtering
USG/ZyWALL User’s Guide
653
Figure 466 Content Filter Lookup Procedure
1A computer behind the Zyxel Device tries to access a web site.
2The Zyxel Device looks up the web site in its cache. If an attempt to access the web site was made in the
past, a record of that web site’s category will be in the Zyxel Device’s cache. The Zyxel Device blocks,
blocks and logs or just logs the request based on your configuration.
3Use the Content Filter Cache screen to configure how long a web site address remains in the cache as
well as view those web site addresses. All of the web site address records are also cleared from the local
cache when the Zyxel Device restarts.
4If the Zyxel Device has no record of the web site, it queries the external content filter database and
simultaneously sends the request to the web server.
5The external content filter server sends the category information back to the Zyxel Device, which then
blocks and/or logs access to the web site based on the settings in the content filter profile. The web
site’s address and category are then stored in the Zyxel Device’s content filter cache.

USG/ZyWALL User’s Guide
654
CHAPTER 38
IDP
38.1 Overview
This chapter introduces packet inspection IDP (Intrusion, Detection and Prevention), IDP profiles, binding
an IDP profile to a traffic flow, custom signatures and updating signatures. An IDP system can detect
malicious or suspicious packets and respond instantaneously. IDP on the Zyxel Device protects against
network-based intrusions.
38.1.1 What You Can Do in this Chapter
• Use the UTM Profile > IDP > Profile screen (Section 38.2 on page 655) to view registration and signature
information. Click the Add or Edit icon in this screen to bind an IDP profile to a traffic direction.
• Use the UTM Profile > IDP > Profile > Add screen (Section 38.2.2 on page 657) to add a new profile, edit
an existing profile or delete an existing profile.
• Use the UTM Profile > IDP > Custom Signature screens (Section 38.3 on page 666) to create a new
custom signature, edit an existing signature, delete existing signatures or save signatures to your
computer.
38.1.2 What You Need To Know
Packet Inspection Signatures
A signature identifies a malicious or suspicious packet and specifies an action to be taken. You can
change the action in the profile screens. Packet inspection signatures examine OSI (Open System
Interconnection) layer-4 to layer-7 packet contents for malicious data. Generally, packet inspection
signatures are created for known attacks while anomaly detection looks for abnormal behavior.
Applying Your IDP Configuration
Changes to the Zyxel Device’s IDP settings affect new sessions (not the sessions that already existed
before you applied the changed settings).
38.1.3 Before You Begin
• Register for a trial IDP subscription in the Registration screen. This gives you access to free signature
updates. This is important as new signatures are created as new attacks evolve. When the trial
subscription expires, purchase and enter a license key using the same screens to continue the
subscription.
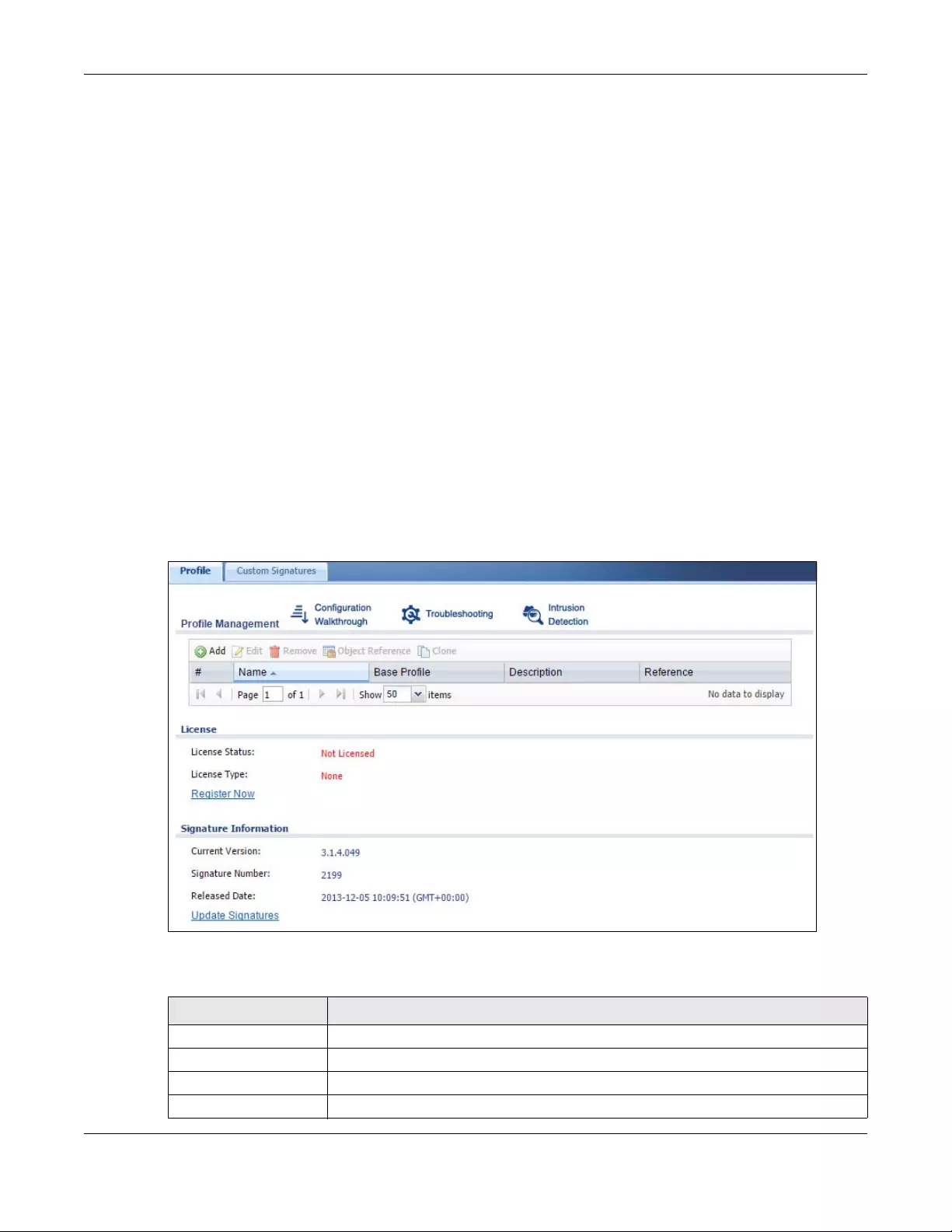
Chapter 38 IDP
USG/ZyWALL User’s Guide
655
38.2 The IDP Profile Screen
An IDP profile is a set of packet inspection signatures.
Packet inspection signatures examine packet content for malicious data. Packet inspection applies to
OSI (Open System Interconnection) layer-4 to layer-7 contents. You need to subscribe for IDP service in
order to be able to download new signatures.
In general, packet inspection signatures are created for known attacks while anomaly detection looks
for abnormal behavior.
Click Configuration > UTM Profile > IDP > Profile to open this screen. Use this screen to view registration
and signature information.
Note: You must register in order to use packet inspection signatures. See the Registration
screens.
If you try to enable IDP when the IDP service has not yet been registered, a warning screen displays and
IDP is not enabled.
Click on the icons to go to the OneSecurity.com website where there is guidance on configuration
walkthroughs, troubleshooting and other information.
Figure 467 Configuration > UTM Profile > IDP > Profile
The following table describes the fields in this screen.
Table 249 Configuration > UTM Profile > IDP > Profile
LABEL DESCRIPTION
Profile Management
Add Click Add to create a new profile. Select from the options in the box.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
Chapter 38 IDP
USG/ZyWALL User’s Guide
656
38.2.1 Base Profiles
The Zyxel Device comes with several base profiles. You use base profiles to create new profiles. In the
Configuration > UTM > IDP > Profile screen, click Add to display the following screen.
Figure 468 Base Profiles
Object Reference Select an entry and click Object References to open a screen that shows which settings
use the entry. Click Refresh to update information on this screen.
Clone Use Clone to create a new entry by modifying an existing one.
• Select an existing entry.
• Click Clone.
• A configuration copy of the selected entry pops up. You must at least change the
name as duplicate entry names are not allowed.
#This is the entry’s index number in the list.
Name This displays the name of the IDP Profile.
Base Profile This displays the base profile used to create the IDP profile.
Description This displays the description of the IDP Profile.
Reference This displays the number of times an object reference is used in a profile.
License You need to create an account at myZyxel.com, register your Zyxel Device and then
subscribe for IDP in order to be able to download new packet inspection signatures from
myZyxel.com. There’s an initial free trial period for IDP after which you must pay to
subscribe to the service. See the Registration chapter for details.
License Status Licensed, Not Licensed or Expired indicates whether you have subscribed for IDP
services or not or your registration has expired.
License Type This field shows Trial, Standard or None depending on whether you subscribed to the IDP
trial, bought an iCard for IDP service or neither.
Signature Information The following fields display information on the current signature set that the Zyxel Device
is using.
Current Version This field displays the IDP signature set version number. This number gets larger as the set
is enhanced.
Signature Number This field displays the number of IDP signatures in this set. This number usually gets larger
as the set is enhanced. Older signatures and rules may be removed if they are no longer
applicable or have been supplanted by newer ones.
Released Date This field displays the date and time the set was released.
Update Signatures Click this link to go to the screen you can use to download signatures from the update
server.
Table 249 Configuration > UTM Profile > IDP > Profile (continued)
LABEL DESCRIPTION
Chapter 38 IDP
USG/ZyWALL User’s Guide
657
The following table describes this screen.
38.2.2 Adding / Editing Profiles
You may want to create a new profile if not all signatures in a base profile are applicable to your
network. In this case you should disable non-applicable signatures so as to improve Zyxel Device IDP
processing efficiency.
You may also find that certain signatures are triggering too many false positives or false negatives. A
false positive is when valid traffic is flagged as an attack. A false negative is when invalid traffic is
wrongly allowed to pass through the Zyxel Device. As each network is different, false positives and false
negatives are common on initial IDP deployment.
You could create a new ‘monitor profile’ that creates logs but all actions are disabled. Observe the logs
over time and try to eliminate the causes of the false alarms. When you’re satisfied that they have been
reduced to an acceptable level, you could then create an ‘inline profile’ whereby you configure
appropriate actions to be taken when a packet matches a signature.
Packet inspection signatures examine the contents of a packet for malicious data. It operates at layer-
4 to layer-7. An IDP profile is a group of IDP signatures that have the same log and action settings. In
‘group view’ you can configure the same log and action settings for all IDP signatures by severity level in
the Add Profile screen. You may also configure signature exceptions in the same view.
Table 250 Base Profiles
BASE PROFILE DESCRIPTION
none All signatures are disabled. No logs are generated nor actions are taken.
all All signatures are enabled. Signatures with a high or severe severity level (greater than
three) generate log alerts and cause packets that trigger them to be dropped. Signatures
with a very low, low or medium severity level (less than or equal to three) generate logs (not
log alerts) and no action is taken on packets that trigger them.
wan Signatures for all services are enabled. Signatures with a medium, high or severe severity
level (greater than two) generate logs (not log alerts) and no action is taken on packets
that trigger them. Signatures with a very low or low severity level (less than or equal to two)
are disabled.
lan This profile is most suitable for common LAN network services. Signatures for common
services such as DNS, FTP, HTTP, ICMP, IM, IMAP, MISC, NETBIOS, P2P, POP3, RPC, RSERVICE,
SMTP, SNMP, SQL, TELNET, TFTP, MySQL are enabled. Signatures with a high or severe severity
level (greater than three) generate logs (not log alerts) and cause packets that trigger them
to be dropped. Signatures with a low or medium severity level (two or three) generate logs
(not log alerts) and no action is taken on packets that trigger them. Signatures with a very
low severity level (one) are disabled.
dmz This profile is most suitable for networks containing your servers. Signatures for common
services such as DNS, FTP, HTTP, ICMP, IMAP, MISC, NETBIOS, POP3, RPC, RSERVICE, SMTP,
SNMP, SQL, TELNET, Oracle, MySQL are enabled. Signatures with a high or severe severity
level (greater than three) generate log alerts and cause packets that trigger them to be
dropped. Signatures with a low or medium severity level (two or three) generate logs (not
log alerts) and no action is taken on packets that trigger them. Signatures with a very low
severity level (one) are disabled.
OK Click OK to save your changes.
Cancel Click Cancel to exit this screen without saving your changes.
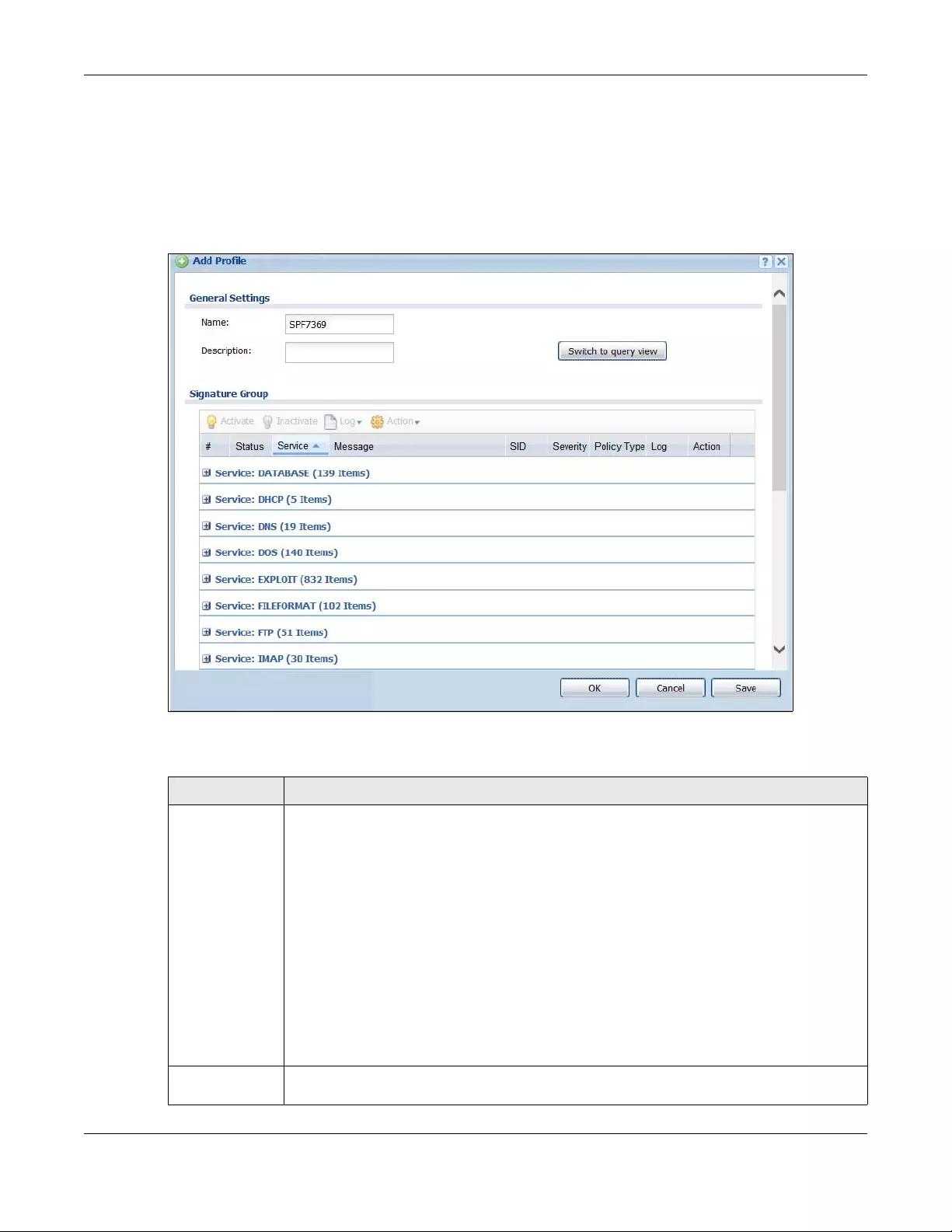
Chapter 38 IDP
USG/ZyWALL User’s Guide
658
38.2.3 Profile > Group View Screen
Select Configuration > UTM Profile > IDP > Profile and then click Add to create a new profile or select an
existing profile, then click a grouDosn the base profile box (or double-click the existing profile) to modify
it. Group view is displayed first by default.
Figure 469 Configuration > UTM Profile > IDP > Profile > Add > Edit: Group View
The following table describes the fields in this screen.
Table 251 Configuration > UTM Profile> IDP > Profile > Add > Group View
LABEL DESCRIPTION
Name This is the name of the profile. You may use 1-31 alphanumeric characters, underscores(_), or
dashes (-), but the first character cannot be a number. This value is case-sensitive. These are
valid, unique profile names:
• MyProfile
• mYProfile
• Mymy12_3-4
These are invalid profile names:
• 1mYProfile
• My Profile
• MyProfile?
• Whatalongprofilename123456789012
Description Enter additional information about this IDP rule. You can enter up to 60 characters ("0-9", "a-z",
"A-Z", "-" and "_").
Chapter 38 IDP
USG/ZyWALL User’s Guide
659
Switch to query
view
Click this button to go to a screen where you can search for signatures by criteria such as
name, ID, severity, attack type, vulnerable attack platforms, service category, log options or
actions.
Severity Level Select a severity level and these use the icons to enable/disable and configure logs and
actions for all signatures of that level.
Signature
Group
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Log To edit an item’s log option, select it and use the Log icon. These are the log options:
no: Select this option on an individual signature or a complete service group to have the Zyxel
Device create no log when a packet matches a signature(s).
log: Select this option on an individual signature or a complete service group to have the Zyxel
Device create a log when a packet matches a signature(s).
log alert: An alert is an e-mailed log for more serious events that may need more immediate
attention. They also appear in red in the Monitor > Log screen. Select this option to have the
Zyxel Device send an alert when a packet matches a signature(s).
Action To edit what action the Zyxel Device takes when a packet matches a signature, select the
signature and use the Action icon.
none: Select this action on an individual signature or a complete service group to have the
Zyxel Device take no action when a packet matches the signature(s).
drop: Select this action on an individual signature or a complete service group to have the
Zyxel Device silently drop a packet that matches the signature(s). Neither sender nor receiver
are notified.
reject-sender: Select this action on an individual signature or a complete service group to have
the Zyxel Device send a reset to the sender when a packet matches the signature. If it is a TCP
attack packet, the Zyxel Device will send a packet with a ‘RST’ flag. If it is an ICMP or UDP
attack packet, the Zyxel Device will send an ICMP unreachable packet.
reject-receiver: Select this action on an individual signature or a complete service group to
have the Zyxel Device send a reset to the receiver when a packet matches the signature. If it is
a TCP attack packet, the Zyxel Device will send a packet with an a ‘RST’ flag. If it is an ICMP or
UDP attack packet, the Zyxel Device will do nothing.
reject-both: Select this action on an individual signature or a complete service group to have
the Zyxel Device send a reset to both the sender and receiver when a packet matches the
signature. If it is a TCP attack packet, the Zyxel Device will send a packet with a ‘RST’ flag to the
receiver and sender. If it is an ICMP or UDP attack packet, the Zyxel Device will send an ICMP
unreachable packet.
#This is the entry’s index number in the list.
Status The activate (light bulb) icon is lit when the entry is active and dimmed when the entry is
inactive.
Message This displays the message of the violation of IDP Profile rule.
SID This displays the Signature ID number. The SID is a numerical field in the 9000000 to 9999999
range.
Table 251 Configuration > UTM Profile> IDP > Profile > Add > Group View (continued)
LABEL DESCRIPTION
Chapter 38 IDP
USG/ZyWALL User’s Guide
660
Severity These are the severities as defined in the Zyxel Device. The number in brackets is the number
you use if using commands.
Severe (5): These denote attacks that try to run arbitrary code or gain system privileges.
High (4): These denote known serious vulnerabilities or attacks that are probably not false
alarms.
Medium (3): These denote medium threats, access control attacks or attacks that could be
false alarms.
Low (2): These denote mild threats or attacks that could be false alarms.
Very Low (1): These denote possible attacks caused by traffic such as Ping, trace route, ICMP
queries etc.
Policy Type This displays the application of the IDP profile.
Log These are the log options. To edit this, select an item and use the Log icon.
Action This is the action the Zyxel Device should take when a packet matches a signature here. To edit
this, select an item and use the Action icon.
Excepted
Signatures
Use the icons to enable/disable and configure logs and actions for individual signatures that
are different to the general settings configured for the severity level to which the signatures
belong. Signatures configured in Query View will appear in Group View.
Add Click this to configure settings to a signature that are different to the severity level to which it
belongs.
Remove Select an existing signature exception and then click this to delete the exception.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Log To edit an item’s log option, select it and use the Log icon. These are the log options:
no: Select this option on an individual signature or a complete service group to have the Zyxel
Device create no log when a packet matches a signature(s).
log: Select this option on an individual signature or a complete service group to have the Zyxel
Device create a log when a packet matches a signature(s).
log alert: An alert is an e-mailed log for more serious events that may need more immediate
attention. Select this option to have the Zyxel Device send an alert when a packet matches a
signature(s).
Table 251 Configuration > UTM Profile> IDP > Profile > Add > Group View (continued)
LABEL DESCRIPTION
Chapter 38 IDP
USG/ZyWALL User’s Guide
661
38.2.4 Add Profile > Query View
In the group view screen, click Switch to query view to search for signatures by criteria such as Name, ID,
Severity, Policy Type, Platform, Service, Platforms, or actions.
Action To edit what action the Zyxel Device takes when a packet matches a signature, select the
signature and use the Action icon.
none: Select this action on an individual signature or a complete service group to have the
Zyxel Device take no action when a packet matches the signature(s).
drop: Select this action on an individual signature or a complete service group to have the
Zyxel Device silently drop a packet that matches the signature(s). Neither sender nor receiver
are notified.
reject-sender: Select this action on an individual signature or a complete service group to have
the Zyxel Device send a reset to the sender when a packet matches the signature. If it is a TCP
attack packet, the Zyxel Device will send a packet with a ‘RST’ flag. If it is an ICMP or UDP
attack packet, the Zyxel Device will send an ICMP unreachable packet.
reject-receiver: Select this action on an individual signature or a complete service group to
have the Zyxel Device send a reset to the receiver when a packet matches the signature. If it is
a TCP attack packet, the Zyxel Device will send a packet with an a ‘RST’ flag. If it is an ICMP or
UDP attack packet, the Zyxel Device will do nothing.
reject-both: Select this action on an individual signature or a complete service group to have
the Zyxel Device send a reset to both the sender and receiver when a packet matches the
signature. If it is a TCP attack packet, the Zyxel Device will send a packet with a ‘RST’ flag to the
receiver and sender. If it is an ICMP or UDP attack packet, the Zyxel Device will send an ICMP
unreachable packet.
#This is the entry’s index number in the list.
Status The activate (light bulb) icon is lit when the entry is active and dimmed when the entry is
inactive.
SID Type the exact signature ID (identification) number that uniquely identifies a Zyxel Device IDP
signature.
Log These are the log options. To edit this, select an item and use the Log icon.
Action This is the action the Zyxel Device should take when a packet matches a signature here. To edit
this, select an item and use the Action icon.
OK A profile consists of three separate screens. If you want to configure just one screen for an IDP
profile, click OK to save your settings to the Zyxel Device, complete the profile and return to the
profile summary page.
Cancel Click Cancel to return to the profile summary page without saving any changes.
Save If you want to configure more than one screen for an IDP profile, click Save to save the
configuration to the Zyxel Device, but remain in the same page. You may then go to another
profile screen (tab) in order to complete the profile. Click OK in the final profile screen to
complete the profile.
Table 251 Configuration > UTM Profile> IDP > Profile > Add > Group View (continued)
LABEL DESCRIPTION
Chapter 38 IDP
USG/ZyWALL User’s Guide
662
Policy Types
This table describes Policy Types as categorized in the Zyxel Device.
Table 252 Policy Types
POLICY TYPE DESCRIPTION
Access Control Access control refers to procedures and controls that limit or detect access. Access
control attacks try to bypass validation checks in order to access network resources such
as servers, directories, and files.
Any Any attack includes all other kinds of attacks that are not specified in the policy such as
password, spoof, hijack, phishing, and close-in.
Backdoor/Trojan Horse A backdoor (also called a trapdoor) is hidden software or a hardware mechanism that
can be triggered to gain access to a program, online service or an entire computer
system. A Trojan horse is a harmful program that is hidden inside apparently harmless
programs or data.
Although a virus, a worm and a Trojan are different types of attacks, they can be
blended into one attack. For example, W32/Blaster and W32/Sasser are blended attacks
that feature a combination of a worm and a Trojan.
BotNet A Botnet is a number of Internet computers that have been set up to forward
transmissions including spam or viruses to other computers on the Internet though their
owners are unaware of it. It is also a collection of Internet-connected programs
communicating with other similar programs in order to perform tasks and participate in
distributed Denial-Of-Service attacks.
Buffer Overflow A buffer overflow occurs when a program or process tries to store more data in a buffer
(temporary data storage area) than it was intended to hold. The excess information can
overflow into adjacent buffers, corrupting or overwriting the valid data held in them.
Intruders could run codes in the overflow buffer region to obtain control of the system,
install a backdoor or use the victim to launch attacks on other devices.
DoS/DDoS The goal of Denial of Service (DoS) attacks is not to steal information, but to disable a
device or network on the Internet.
A Distributed Denial of Service (DDoS) attack is one in which multiple compromised
systems attack a single target, thereby causing denial of service for users of the targeted
system.
Instant Messenger IM (Instant Messenger) refers to chat applications. Chat is real-time, text-based
communication between two or more users via networks-connected computers. After
you enter a chat (or chat room), any room member can type a message that will
appear on the monitors of all the other participants.
Mail A Mail or E-mail bombing attack involves sending several thousand identical messages to
an electronic mailbox in order to overflow it, making it unusable.
Misc Miscellaneous attacks takes advantage of vulnerable computer networks and web
servers by forcing cache servers or web browsers into disclosing user-specific information
that might be sensitive and confidential. The most common type of Misc. attacks are
HTTP Response Smuggling, HTTP Response Splitting and JSON Hijacking.
P2P Peer-to-peer (P2P) is where computing devices link directly to each other and can
directly initiate communication with each other; they do not need an intermediary. A
device can be both the client and the server. In the Zyxel Device, P2P refers to peer-to-
peer applications such as e-Mule, e-Donkey, BitTorrent, iMesh, etc.
Chapter 38 IDP
USG/ZyWALL User’s Guide
663
IDP Service Groups
An IDP service group is a set of related packet inspection signatures.
The n/a service group is for signatures that are not for a specific service.
Scan A scan describes the action of searching a network for an exposed service. An attack
may then occur once a vulnerability has been found. Scans occur on several network
levels.
A network scan occurs at layer-3. For example, an attacker looks for network devices
such as a router or server running in an IP network.
A scan on a protocol is commonly referred to as a layer-4 scan. For example, once an
attacker has found a live end system, he looks for open ports.
A scan on a service is commonly referred to a layer-7 scan. For example, once an
attacker has found an open port, say port 80 on a server, he determines that it is a HTTP
service run by some web server application. He then uses a web vulnerability scanner (for
example, Nikto) to look for documented vulnerabilities.
SPAM Spam is unsolicited “junk” e-mail sent to large numbers of people to promote products or
services.
Stream Media A Stream Media attack occurs when a malicious network node downloads an
overwhelming amount of media stream data that could potentially exhaust the entire
system. This method allows users to send small requests messages that result in the
streaming of large media objects, providing an opportunity for malicious users to exhaust
resources in the system with little effort expended on their part.
Tunnel A Tunneling attack involves sending IPv6 traffic over IPv4, slipping viruses, worms and
spyware through the network using secret tunnels. This method infiltrates standard
security measures through IPv6 tunnels, passing through IPv4 undetected. An external
signal then triggers the malware to spring to life and wreak havoc from inside the
network.
Virus/Worm A computer virus is a small program designed to corrupt and/or alter the operation of
other legitimate programs. A worm is a program that is designed to copy itself from one
computer to another on a network. A worm’s uncontrolled replication consumes system
resources, thus slowing or stopping other tasks.
Web Attack Web attacks refer to attacks on web servers such as IIS (Internet Information Services).
Table 253 IDP Service Groups
WEB_PHP WEB_MISC WEB_IIS WEB_FRONTPAGE
WEB_CGI WEB_ATTACKS TFTP TELNET
SQL SNMP SMTP RSERVICES
RPC POP3 POP2 P2P
ORACLE NNTP NETBIOS MYSQL
MISC_EXPLOIT MISC_DDOS MISC_BACKDOOR MISC
IMAP IM ICMP FTP
FINGER DNS n/a
Table 252 Policy Types (continued)
POLICY TYPE DESCRIPTION
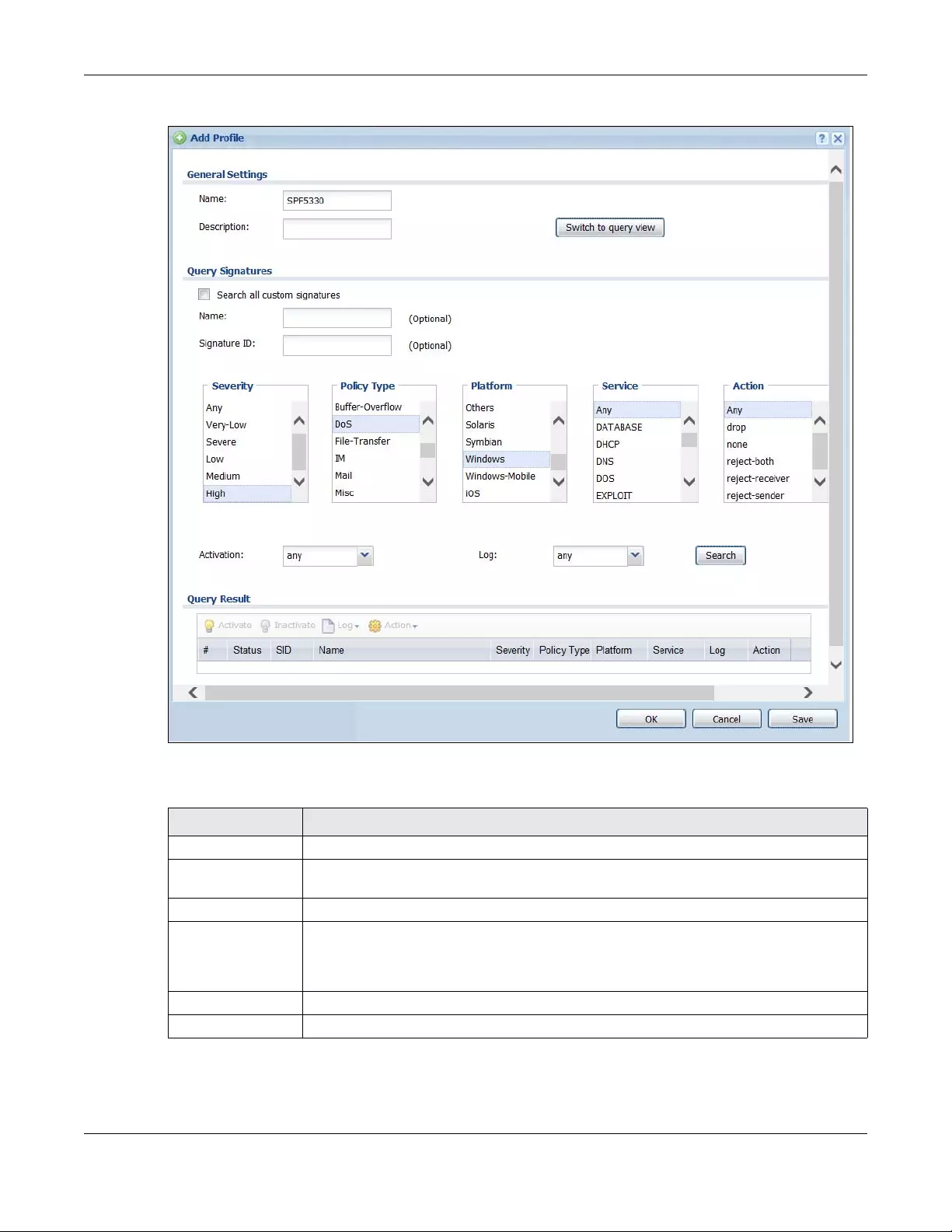
Chapter 38 IDP
USG/ZyWALL User’s Guide
664
Figure 470 Configuration > UTM Profile> IDP > Profile: Query View
The following table describes the fields specific to this screen’s query view.
Table 254 Configuration > UTM Profile > IDP > Profile: Query View
LABEL DESCRIPTION
Name This is the name of the profile that you created in the IDP > Profiles > Group View screen.
Switch to query
view
Click this button to go to the IDP profile group view screen where IDP signatures are grouped
by service and you can configure activation, logs and/or actions.
Query Signatures Select the criteria on which to perform the search.
Search all
custom
signatures
Select this check box to include signatures you created or imported in the Custom
Signatures screen in the search. You can search for specific signatures by name or ID. If the
name and ID fields are left blank, then all signatures are searched according to the criteria
you select.
Name Type the name or part of the name of the signature(s) you want to find.
Signature ID Type the ID or part of the ID of the signature(s) you want to find.
Chapter 38 IDP
USG/ZyWALL User’s Guide
665
38.2.5 Query Example
This example shows a search with these criteria:
•Severity: high
• Policy Type: DoS
• Platform: Windows
•Service: Any
•Actions: Any
Severity Search for signatures by severity level(s). Hold down the [Ctrl] key if you want to make
multiple selections.
These are the severities as defined in the Zyxel Device. The number in brackets is the number
you use if using commands.
Severe (5): These denote attacks that try to run arbitrary code or gain system privileges.
High (4): These denote known serious vulnerabilities or attacks that are probably not false
alarms.
Medium (3): These denote medium threats, access control attacks or attacks that could be
false alarms.
Low (2): These denote mild threats or attacks that could be false alarms.
Very-Low (1): These denote possible attacks caused by traffic such as Ping, trace route,
ICMP queries etc.
Attack Type Search for signatures by attack type(s) (see Table 252 on page 662). Attack types are known
as policy types in the group view screen. Hold down the [Ctrl] key if you want to make
multiple selections.
Platform Search for signatures created to prevent intrusions targeting specific operating system(s).
Hold down the [Ctrl] key if you want to make multiple selections.
Service Search for signatures by IDP service group(s). See Table 252 on page 662 for group details.
Hold down the [Ctrl] key if you want to make multiple selections.
Action Search for signatures by the response the Zyxel Device takes when a packet matches a
signature. See Table 251 on page 658 for action details. Hold down the [Ctrl] key if you want
to make multiple selections.
Activation Search for activated and/or inactivated signatures here.
Log Search for signatures by log option here. See Table 251 on page 658 for option details.
Search Click this button to begin the search. The results display at the bottom of the screen. Results
may be spread over several pages depending on how broad the search criteria selected
were. The tighter the criteria selected, the fewer the signatures returned.
Query Result The results are displayed in a table showing the SID, Name, Severity, Attack Type, Platform,
Service, Activation, Log, and Action criteria as selected in the search. Click the SID column
header to sort search results by signature ID.
OK Click OK to save your settings to the Zyxel Device, complete the profile and return to the
profile summary page.
Cancel Click Cancel to return to the profile summary page without saving any changes.
Save Click Save to save the configuration to the Zyxel Device, but remain in the same page. You
may then go to the another profile screen (tab) in order to complete the profile. Click OK in
the final profile screen to complete the profile.
Table 254 Configuration > UTM Profile > IDP > Profile: Query View (continued)
LABEL DESCRIPTION
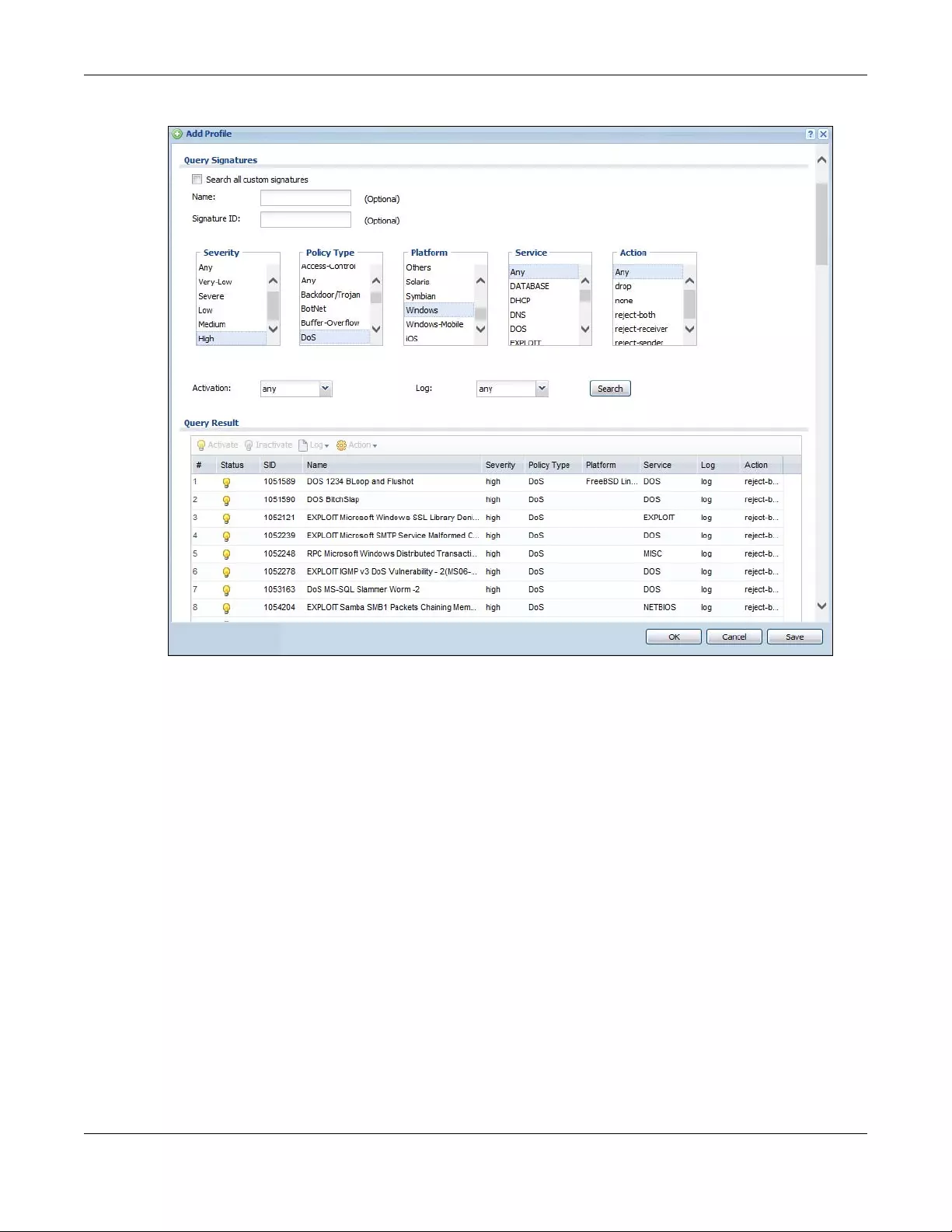
Chapter 38 IDP
USG/ZyWALL User’s Guide
666
Figure 471 Query Example Search
38.3 IDP Custom Signatures
Create custom signatures for new attacks or attacks peculiar to your network. Custom signatures can
also be saved to/from your computer so as to share with others.
You need some knowledge of packet headers and attack types to create your own custom signatures.
IP Packet Header
These are the fields in an Internet Protocol (IP) version 4 packet header.
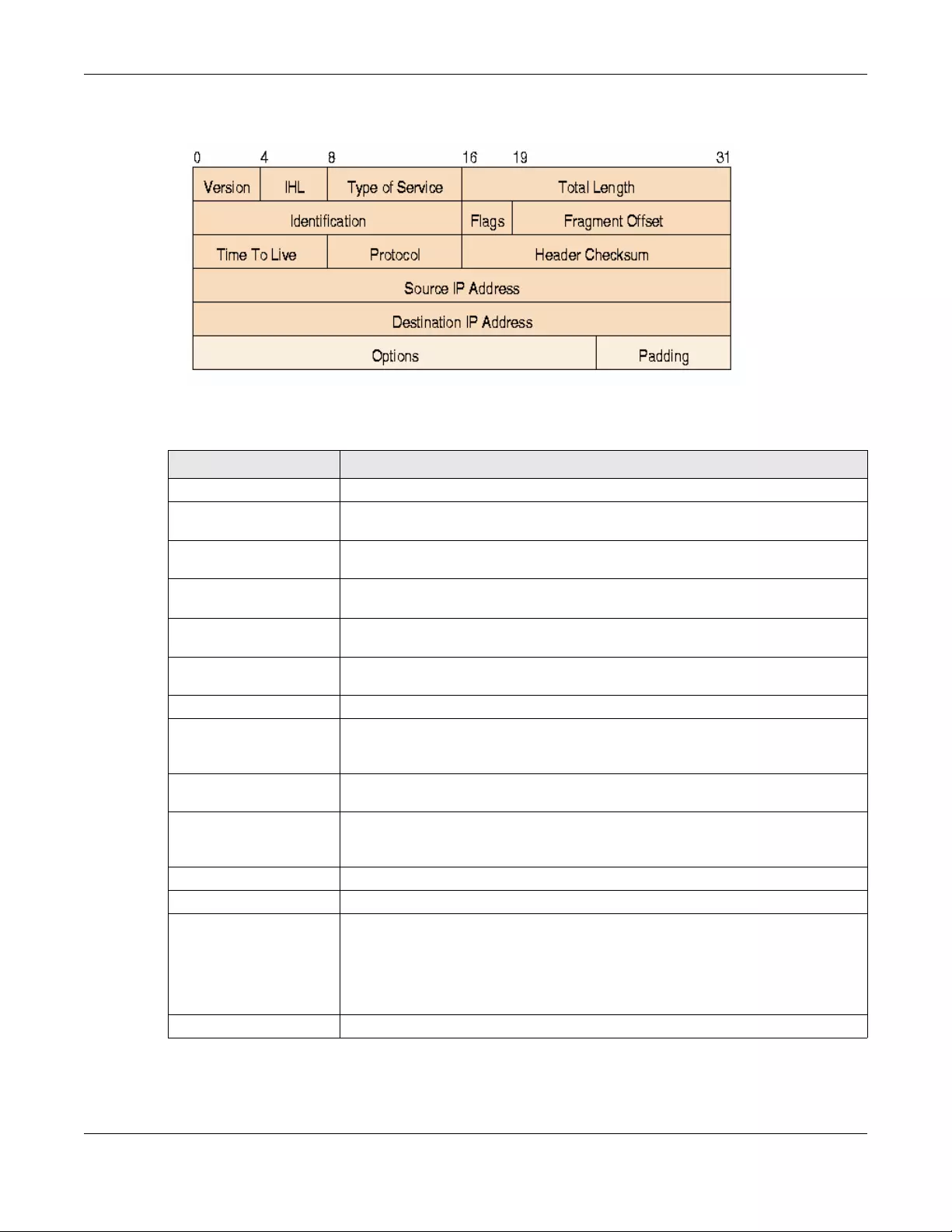
Chapter 38 IDP
USG/ZyWALL User’s Guide
667
Figure 472 IP v4 Packet Headers
The header fields are discussed in the following table.
Select Configuration > UTM Profile > IDP > Custom Signatures. The first screen shows a summary of all
custom signatures created. Click the SID or Name heading to sort. Click the Add icon to create a new
Table 255 IP v4 Packet Headers
HEADER DESCRIPTION
Version The value 4 indicates IP version 4.
IHL IP Header Length is the number of 32 bit words forming the total length of the header
(usually five).
Type of Service The Type of Service, (also known as Differentiated Services Code Point (DSCP)) is
usually set to 0, but may indicate particular quality of service needs from the network.
Total Length This is the size of the datagram in bytes. It is the combined length of the header and
the data.
Identification This is a 16-bit number, which together with the source address, uniquely identifies this
packet. It is used during reassembly of fragmented datagrams.
Flags Flags are used to control whether routers are allowed to fragment a packet and to
indicate the parts of a packet to the receiver.
Fragment Offset This is a byte count from the start of the original sent packet.
Time To Live This is a counter that decrements every time it passes through a router. When it
reaches zero, the datagram is discarded. It is used to prevent accidental routing
loops.
Protocol The protocol indicates the type of transport packet being carried, for example, 1 =
ICMP; 2= IGMP; 6 = TCP; 17= UDP.
Header Checksum This is used to detect processing errors introduced into the packet inside a router or
bridge where the packet is not protected by a link layer cyclic redundancy check.
Packets with an invalid checksum are discarded by all nodes in an IP network.
Source IP Address This is the IP address of the original sender of the packet.
Destination IP Address This is the IP address of the final destination of the packet.
Options IP options is a variable-length list of IP options for a datagram that define IP Security
Option, IP Stream Identifier, (security and handling restrictions for the military), Record
Route (have each router record its IP address), Loose Source Routing (specifies a list of
IP addresses that must be traversed by the datagram), Strict Source Routing (specifies
a list of IP addresses that must ONLY be traversed by the datagram), Timestamp (have
each router record its IP address and time), End of IP List and No IP Options.
Padding Padding is used as a filler to ensure that the IP packet is a multiple of 32 bits.
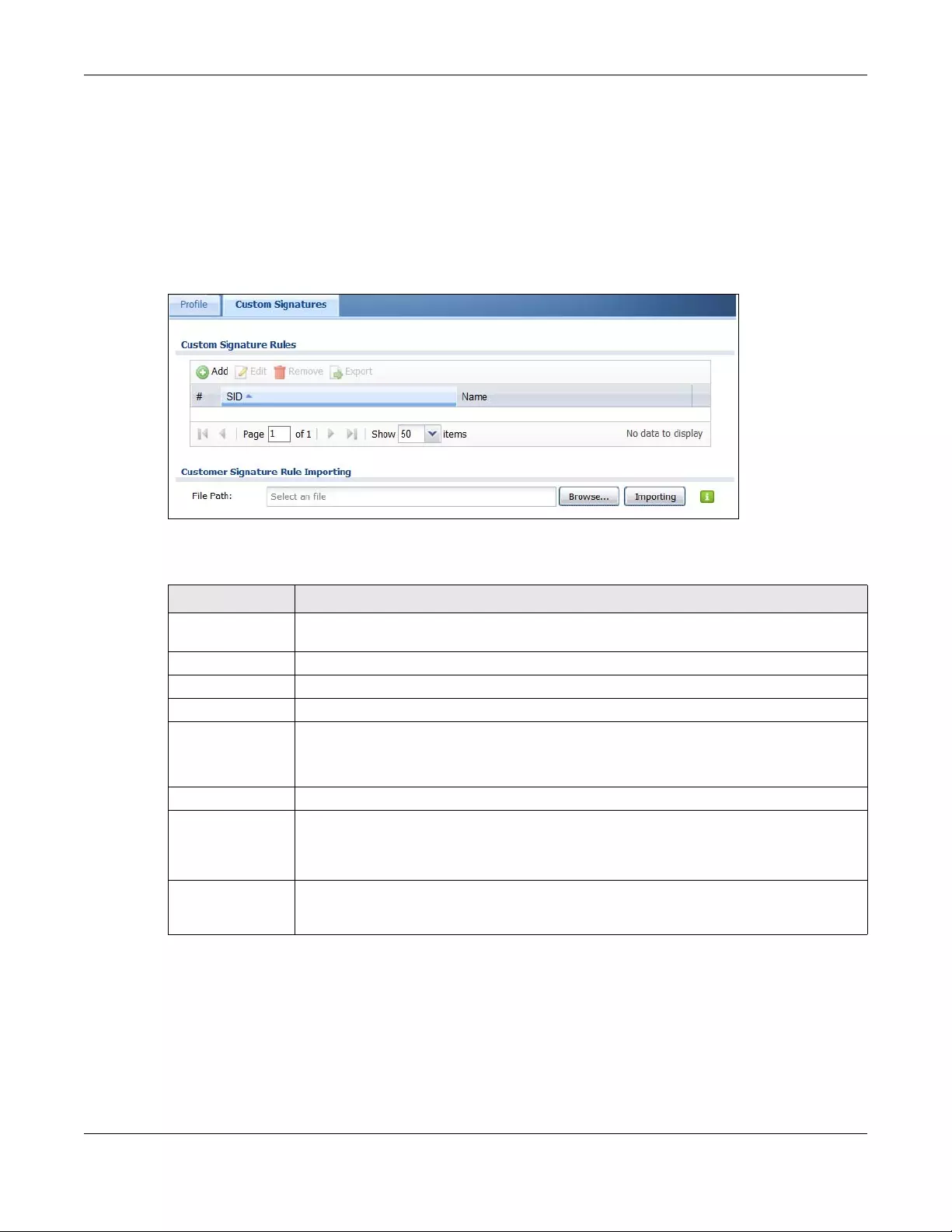
Chapter 38 IDP
USG/ZyWALL User’s Guide
668
signature or click the Edit icon to edit an existing signature. You can also delete custom signatures here
or save them to your computer.
Note: The Zyxel Device checks all signatures and continues searching even after a match is
found. If two or more rules have conflicting actions for the same packet, then the Zyxel
Device applies the more restrictive action (reject-both, reject-receiver or reject-sender,
drop, none in this order). If a packet matches a rule for reject-receiver and it also
matches a rule for reject-sender, then the Zyxel Device will reject-both.
Figure 473 Configuration > UTM Profile > IDP > Custom Signatures
The following table describes the fields in this screen.
Table 256 Configuration > UTM Profile> IDP > Custom Signatures
LABEL DESCRIPTION
Custom Signature
Rules
Use this part of the screen to create, edit, delete or export (save to your computer) custom
signatures.
Add Click this to create a new entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
Export To save an entry or entries as a file on your computer, select them and click Export. Click Save
in the file download dialog box and then select a location and name for the file.
Custom signatures must end with the ‘rules’ file name extension, for example, MySig.rules.
#This is the entry’s index number in the list.
SID SID is the signature ID that uniquely identifies a signature. Click the SID header to sort
signatures in ascending or descending order. It is automatically created when you click the
Add icon to create a new signature. You can edit the ID, but it cannot already exist and it
must be in the 9000000 to 9999999 range.
Name This is the name of your custom signature. Duplicate names can exist, but it is advisable to use
unique signature names that give some hint as to intent of the signature and the type of
attack it is supposed to prevent.
Chapter 38 IDP
USG/ZyWALL User’s Guide
669
38.3.1 Add / Edit Custom Signatures
Click the Add icon to create a new signature or click the Edit icon to edit an existing signature in the
screen as shown in Figure 473 on page 668.
A packet must match all items you configure in this screen before it matches the signature. The more
specific your signature (including packet contents), then the fewer false positives the signature will
trigger.
Try to write signatures that target a vulnerability, for example a certain type of traffic on certain
operating systems, instead of a specific exploit.
Customer
Signature Rule
Importing
Use this part of the screen to import custom signatures (previously saved to your computer) to
the Zyxel Device.
Note: The name of the complete custom signature file on the Zyxel Device is
‘custom.rules’. If you import a file named ‘custom.rules’, then all custom
signatures on the Zyxel Device are overwritten with the new file. If this is not
your intention, make sure that the files you import are not named
‘custom.rules’.
File Path Type the file path and name of the custom signature file you want to import in the text box (or
click Browse to find it on your computer) and then click Importing to transfer the file to the
Zyxel Device.
New signatures then display in the Zyxel Device IDP > Custom Signatures screen.
Table 256 Configuration > UTM Profile> IDP > Custom Signatures (continued)
LABEL DESCRIPTION
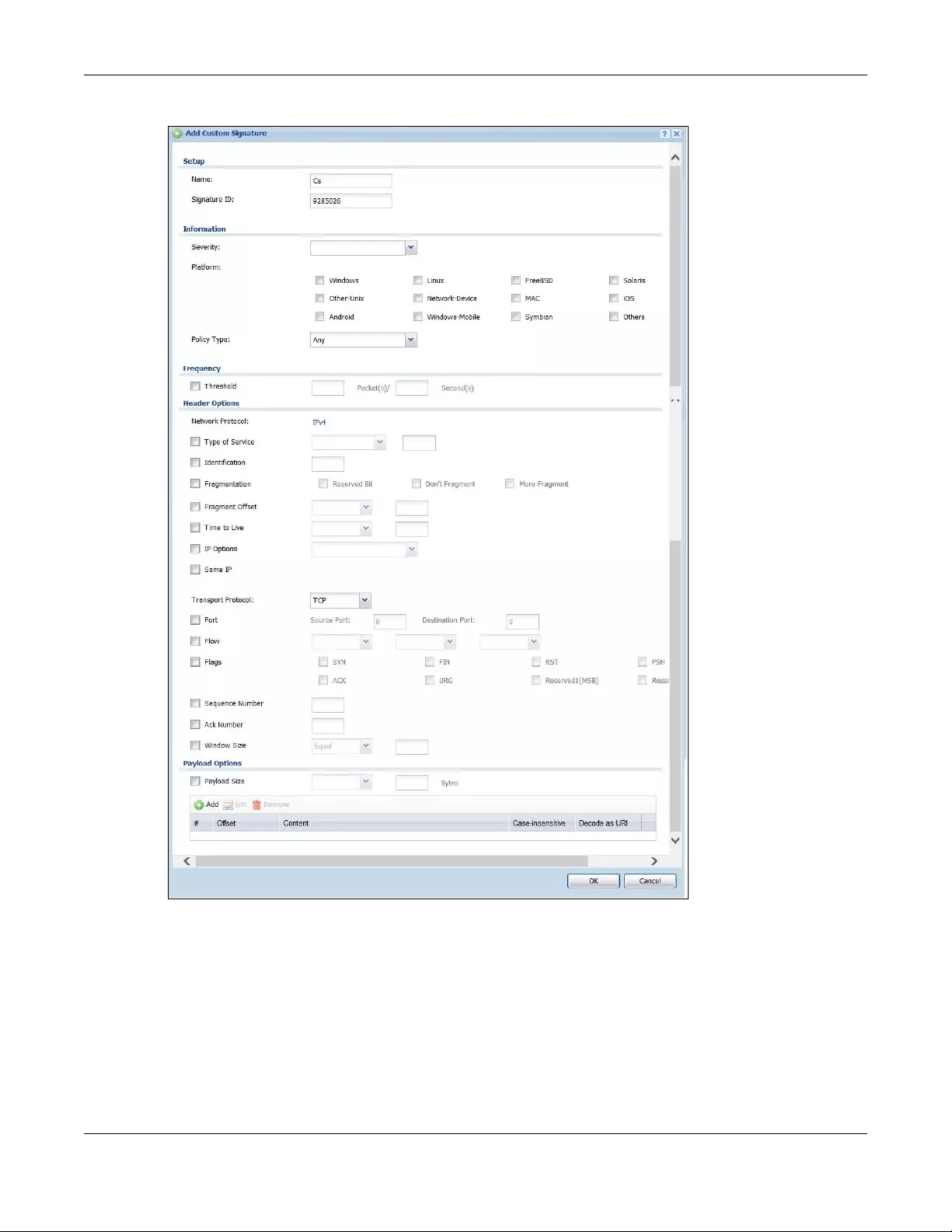
Chapter 38 IDP
USG/ZyWALL User’s Guide
670
Figure 474 Configuration > UTM Profile > IDP > Custom Signatures > Add/Edit
Chapter 38 IDP
USG/ZyWALL User’s Guide
671
The following table describes the fields in this screen.
Table 257 Configuration > UTM Profile > IDP > Custom Signatures > Add/Edit
LABEL DESCRIPTION
Name Type the name of your custom signature. You may use 1-31 alphanumeric characters,
underscores(_), or dashes (-), but the first character cannot be a number. This value is
case-sensitive.
Duplicate names can exist but it is advisable to use unique signature names that give
some hint as to intent of the signature and the type of attack it is supposed to prevent.
Refer to (but do not copy) the packet inspection signature names for hints on creating a
naming convention.
Signature ID A signature ID is automatically created when you click the Add icon to create a new
signature. You can edit the ID to create a new one (in the 9000000 to 9999999 range),
but you cannot use one that already exists. You may want to do that if you want to order
custom signatures by SID.
Information Use the following fields to set general information about the signature as denoted below.
Severity The severity level denotes how serious the intrusion is. Categorize the seriousness of the
intrusion here. See Table 251 on page 658 as a reference.
Platform Some intrusions target specific operating systems only. Select the operating systems that
the intrusion targets, that is, the operating systems you want to protect from this intrusion.
SGI refers to Silicon Graphics Incorporated, who manufactures multi-user Unix
workstations that run the IRIX operating system (SGI's version of UNIX). A router is an
example of a network device.
Service Select the IDP service group that the intrusion exploits or targets. See Table 253 on page
663 for a list of IDP service groups. The custom signature then appears in that group in the
IDP > Profile > Group View screen.
Policy Type Categorize the attack type here. See Table 252 on page 662 as a reference.
Frequency Recurring packets of the same type may indicate an attack. Use the following field to
indicate how many packets per how many seconds constitute an intrusion
Threshold Select Threshold and then type how many packets (that meet the criteria in this
signature) per how many seconds constitute an intrusion.
Header Options
Network Protocol Configure signatures for IP version 4.
Type Of Service Type of service in an IP header is used to specify levels of speed and/or reliability. Some
intrusions use an invalid Type Of Service number. Select the check box, then select Equal
or Not-Equal and then type in a number.
Identification The identification field in a datagram uniquely identifies the datagram. If a datagram is
fragmented, it contains a value that identifies the datagram to which the fragment
belongs. Some intrusions use an invalid Identification number. Select the check box and
then type in the invalid number that the intrusion uses.
Fragmentation A fragmentation flag identifies whether the IP datagram should be fragmented, not
fragmented or is a reserved bit. Some intrusions can be identified by this flag. Select the
check box and then select the flag that the intrusion uses.
Fragment Offset When an IP datagram is fragmented, it is reassembled at the final destination. The
fragmentation offset identifies where the fragment belongs in a set of fragments. Some
intrusions use an invalid Fragment Offset number. Select the check box, select Equal,
Smaller or Greater and then type in a number
Time to Live Time to Live is a counter that decrements every time it passes through a router. When it
reaches zero, the datagram is discarded. Usually it’s used to set an upper limit on the
number of routers a datagram can pass through. Some intrusions can be identified by
the number in this field. Select the check box, select Equal, Smaller or Greater and then
type in a number.
Chapter 38 IDP
USG/ZyWALL User’s Guide
672
IP Options IP options is a variable-length list of IP options for a datagram that define IP Security
Option, IP Stream Identifier, (security and handling restrictions for the military), Record
Route (have each router record its IP address), Loose Source Routing (specifies a list of IP
addresses that must be traversed by the datagram), Strict Sourc e Routi ng (specifies a list
of IP addresses that must ONLY be traversed by the datagram), Timestamp (have each
router record its IP address and time), End of IP List and No IP Options. IP Options can help
identify some intrusions. Select the check box, then select an item from the list box that
the intrusion uses
Same IP Select the check box for the signature to check for packets that have the same source
and destination IP addresses.
Transport Protocol The following fields vary depending on whether you choose TCP, UDP or ICMP.
Transport Protocol: TCP
Port Select the check box and then enter the source and destination TCP port numbers that
will trigger this signature.
Flow If selected, the signature only applies to certain directions of the traffic flow and only to
clients or servers. Select Flow and then select the identifying options.
Established: The signature only checks for established TCP connections
Stateless: The signature is triggered regardless of the state of the stream processor (this is
useful for packets that are designed to cause devices to crash)
To Client: The signature only checks for server responses from A to B.
To Server: The signature only checks for client requests from B to A.
From Client: The signature only checks for client requests from B to A.
From Servers: The signature only checks for server responses from A to B.
No Stream: The signature does not check rebuilt stream packets.
Only Stream: The signature only checks rebuilt stream packets.
Flags Select what TCP flag bits the signature should check.
Sequence Number Use this field to check for a specific TCP sequence number.
Ack Number Use this field to check for a specific TCP acknowledgment number.
Window Size Use this field to check for a specific TCP window size.
Transport Protocol: UDP
Port Select the check box and then enter the source and destination UDP port numbers that
will trigger this signature.
Transport Protocol:
ICMP
Type Use this field to check for a specific ICMP type value.
Code Use this field to check for a specific ICMP code value.
ID Use this field to check for a specific ICMP ID value. This is useful for covert channel
programs that use static ICMP fields when they communicate.
Sequence Number Use this field to check for a specific ICMP sequence number. This is useful for covert
channel programs that use static ICMP fields when they communicate.
Payload Options The longer a payload option is, the more exact the match, the faster the signature
processing. Therefore, if possible, it is recommended to have at least one payload option
in your signature.
Table 257 Configuration > UTM Profile > IDP > Custom Signatures > Add/Edit (continued)
LABEL DESCRIPTION
Chapter 38 IDP
USG/ZyWALL User’s Guide
673
38.3.2 Custom Signature Example
Before creating a custom signature, you must first clearly understand the vulnerability.
Payload Size This field may be used to check for abnormally sized packets or for detecting buffer
overflows.
Select the check box, then select Equal, Smaller or Greater and then type the payload
size.
Stream rebuilt packets are not checked regardless of the size of the payload.
Add Click this to create a new entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
#This is the entry’s index number in the list.
Offset This field specifies where to start searching for a pattern within a packet. For example, an
offset of 5 would start looking for the specified pattern after the first five bytes of the
payload.
Content Type the content that the signature should search for in the packet payload.
Hexadecimal code entered between pipes is converted to ASCII. For example, you
could represent the ampersand as either & or |26| (26 is the hexadecimal code for the
ampersand).
Case-insensitive Select Yes if content casing does NOT matter.
Decode as URI A Uniform Resource Identifier (URI) is a string of characters for identifying an abstract or
physical resource (RFC 2396). A resource can be anything that has identity, for example,
an electronic document, an image, a service (“today's weather report for Taiwan”), a
collection of other resources. An identifier is an object that can act as a reference to
something that has identity. Example URIs are:
ftp://ftp.is.co.za/rfc/rfc1808.txt; ftp scheme for File Transfer Protocol services
http://www.math.uio.no/faq/compression-faq/part1.html; http scheme for Hypertext
Transfer Protocol services
mailto:mduerst@ifi.unizh.ch; mailto scheme for electronic mail addresses
telnet://melvyl.ucop.edu/; telnet scheme for interactive services via the TELNET Protocol
Select Yes for the signature to search for normalized URI fields. This means that if you are
writing signatures that includes normalized content, such as %2 for directory traversals,
these signatures will not be triggered because the content is normalized out of the URI
buffer.
For example, the URI:
/scripts/..%c0%af../winnt/system32/cmd.exe?/c+ver
will get normalized into:
/winnt/system32/cmd.exe?/c+ver
OK Click this button to save your changes to the Zyxel Device and return to the summary
screen.
Cancel Click this button to return to the summary screen without saving any changes.
Table 257 Configuration > UTM Profile > IDP > Custom Signatures > Add/Edit (continued)
LABEL DESCRIPTION
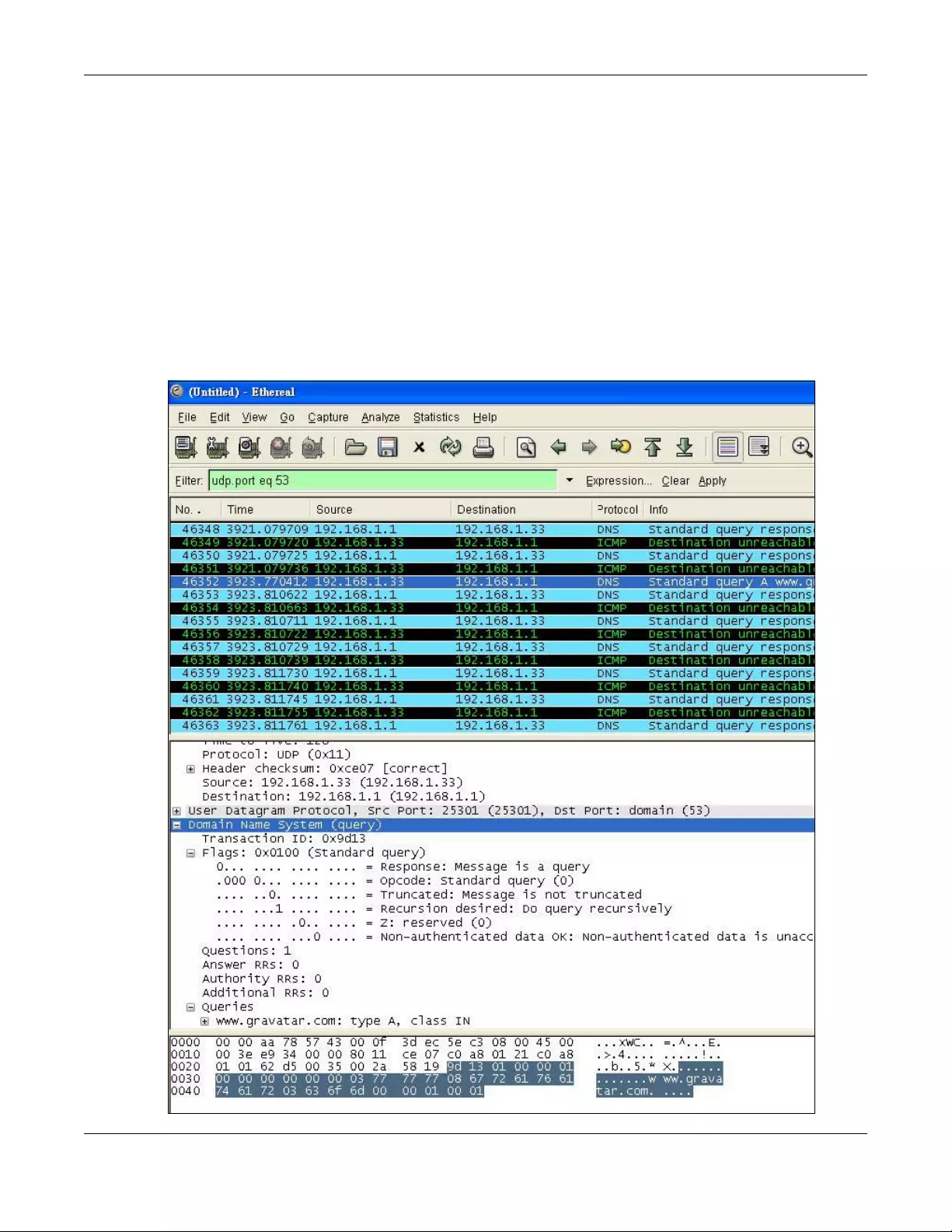
Chapter 38 IDP
USG/ZyWALL User’s Guide
674
38.3.2.1 Understand the Vulnerability
Check the Zyxel Device logs when the attack occurs. Use web sites such as Google or Security Focus to
get as much information about the attack as you can. The more specific your signature, the less chance
it will cause false positives.
As an example, say you want to check if your router is being overloaded with DNS queries so you create
a signature to detect DNS query traffic.
38.3.2.2 Analyze Packets
Use the packet capture screen and a packet analyzer (also known as a network or protocol analyzer)
such as Wireshark or Ethereal to investigate some more.
Figure 475 DNS Query Packet Details
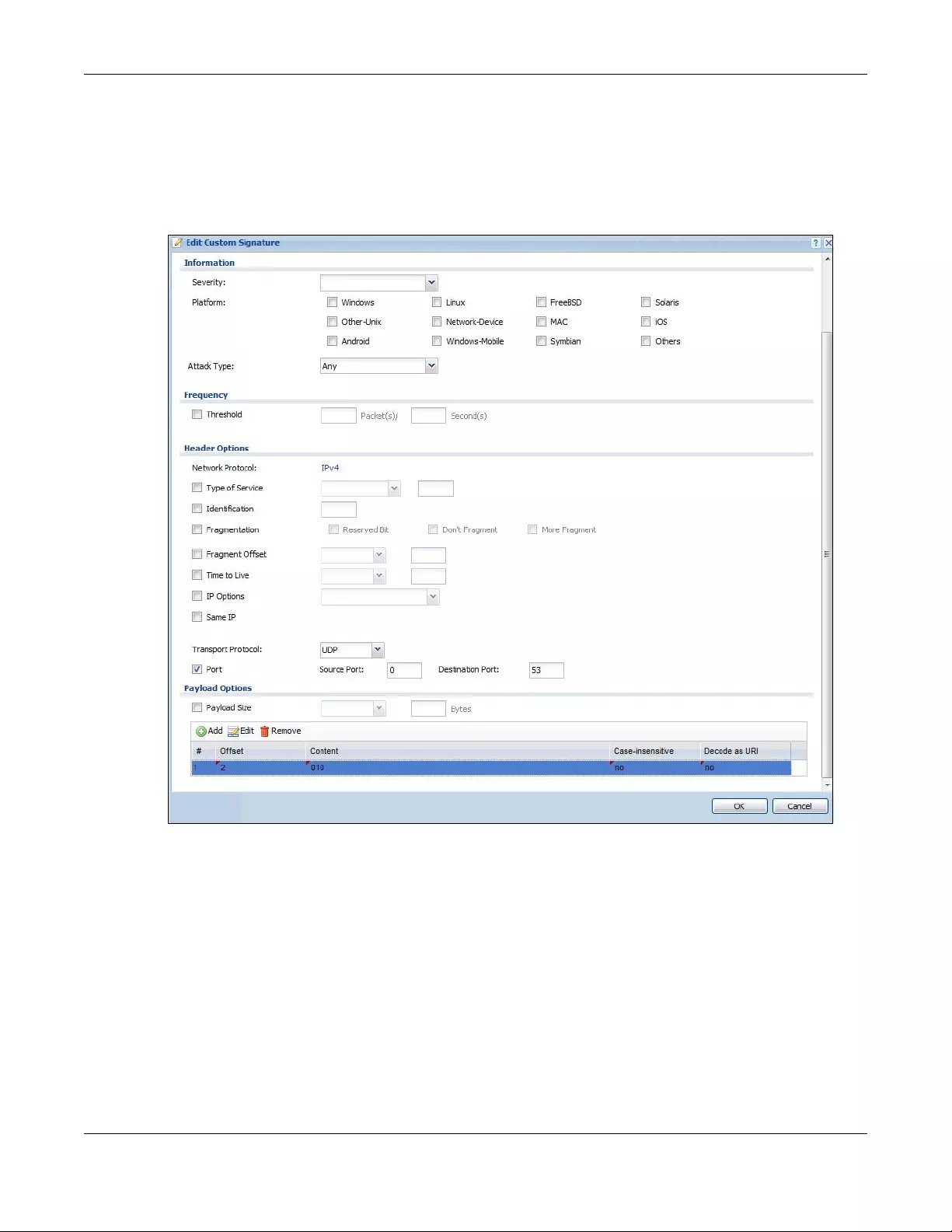
Chapter 38 IDP
USG/ZyWALL User’s Guide
675
From the details about DNS query you see that the protocol is UDP and the port is 53. The type of DNS
packet is standard query and the Flag is 0x0100 with an offset of 2. Therefore enter |010| as the first
pattern.
The final custom signature should look like as shown in the following figure.
Figure 476 Example Custom Signature
38.3.3 Applying Custom Signatures
After you create your custom signature, it becomes available in an IDP profile (Configuration > UTM
Profile > IDP > Profile > Edit) screen. Custom signatures have an SID from 9000000 to 9999999.
Search for, then activate the signature, configure what action to take when a packet matches it and if
it should generate a log or alert in a profile. Then bind the profile to a zone.
38.3.4 Verifying Custom Signatures
Configure the signature to create a log when traffic matches the signature. (You may also want to
configure an alert if it is for a serious attack and needs immediate attention.) After you apply the
signature to a zone, you can see if it works by checking the logs (Monitor > Log).
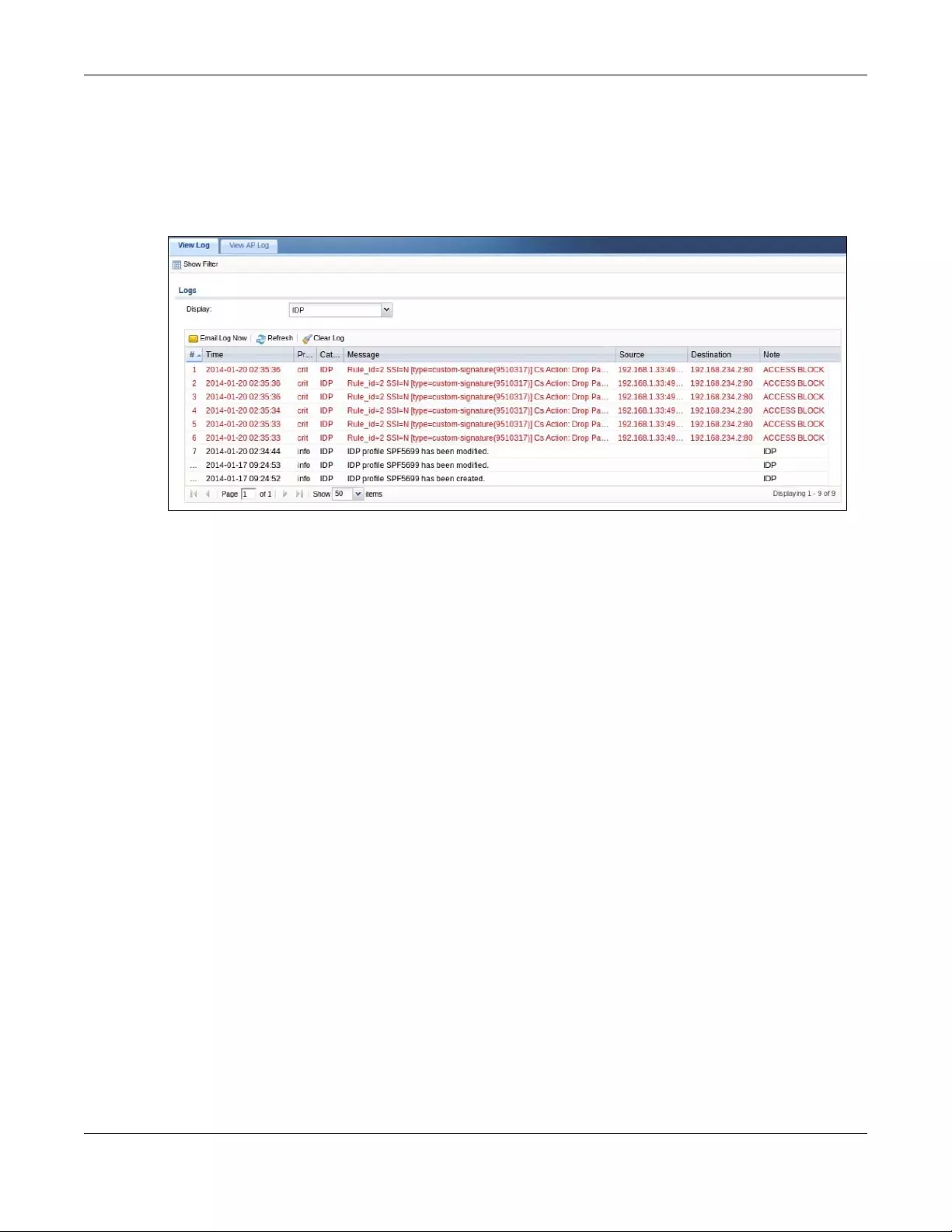
Chapter 38 IDP
USG/ZyWALL User’s Guide
676
The Priority column shows warn for signatures that are configured to generate a log only. It shows critical
for signatures that are configured to generate a log and alert. All IDP signatures come under the IDP
category. The Note column displays ACCESS FORWARD when no action is configured for the signature. It
displays ACCESS DENIED if you configure the signature action to drop the packet. The destination port is
the service port (53 for DNS in this case) that the attack tries to exploit.
Figure 477 Custom Signature Log
38.4 IDP Technical Reference
This section contains some background information on IDP.
Host Intrusions
The goal of host-based intrusions is to infiltrate files on an individual computer or server in with the goal of
accessing confidential information or destroying information on a computer.
You must install a host IDP directly on the system being protected. It works closely with the operating
system, monitoring and intercepting system calls to the kernel or APIs in order to prevent attacks as well
as log them.
Disadvantages of host IDPs are that you have to install them on each device (that you want to protect)
in your network and due to the necessarily tight integration with the host operating system, future
operating system upgrades could cause problems.
Network Intrusions
Network-based intrusions have the goal of bringing down a network or networks by attacking
computer(s), switch(es), router(s) or modem(s). If a LAN switch is compromised for example, then the
whole LAN is compromised. Host-based intrusions may be used to cause network-based intrusions when
the goal of the host virus is to propagate attacks on the network, or attack computer/server operating
system vulnerabilities with the goal of bringing down the computer/server. Typical “network-based
intrusions” are SQL slammer, Blaster, Nimda MyDoom etc.
Chapter 38 IDP
USG/ZyWALL User’s Guide
677
Snort Signatures
You may want to refer to open source Snort signatures when creating custom Zyxel Device ones. Most
Snort rules are written in a single line. Snort rules are divided into two logical sections, the rule header
and the rule options as shown in the following example:
alert tcp any any -> 192.168.1.0/24 111 (content:”|00 01 a5|”; msg:”mountd access”;)
The text up to the first parenthesis is the rule header and the section enclosed in parenthesis contains the
rule options. The words before the colons in the rule options section are the option keywords.
The rule header contains the rule's:
•Action
•Protocol
• Source and destination IP addresses and netmasks
• Source and destination ports information.
The rule option section contains alert messages and information on which parts of the packet should be
inspected to determine if the rule action should be taken.
These are some equivalent Snort terms in the Zyxel Device.
Table 258 Zyxel Device - Snort Equivalent Terms
ZYXEL DEVICE TERM SNORT EQUIVALENT TERM
Type Of Service tos
Identification id
Fragmentation fragbits
Fragmentation Offset fragoffset
Time to Live ttl
IP Options ipopts
Same IP sameip
Transport Protocol
Transport Protocol: TCP
Port (In Snort rule header)
Flow flow
Flags flags
Sequence Number seq
Ack Number ack
Window Size window
Transport Protocol: UDP (In Snort rule header)
Port (In Snort rule header)
Transport Protocol: ICMP
Type itype
Code icode
ID icmp_id
Sequence Number icmp_seq
Chapter 38 IDP
USG/ZyWALL User’s Guide
678
Note: Not all Snort functionality is supported in the Zyxel Device.
Payload Options (Snort rule options)
Payload Size dsize
Offset (relative to start of payload) offset
Relative to end of last match distance
Content content
Case-insensitive nocase
Decode as URI uricontent
Table 258 Zyxel Device - Snort Equivalent Terms (continued)
ZYXEL DEVICE TERM SNORT EQUIVALENT TERM

USG/ZyWALL User’s Guide
679
CHAPTER 39
Anti-Virus
39.1 Overview
Use the Zyxel Device’s anti-virus feature to protect your connected network from virus/spyware
infection. The Zyxel Device checks traffic going in the direction(s) you specify for signature matches. In
the following figure the Zyxel Device is set to check traffic coming from the WAN zone (which includes
two interfaces) to the LAN zone.
Figure 478 Zyxel Device Anti-Virus Example
39.1.1 What You Can Do in this Chapter
• Use the Profile screens (Section 39.2 on page 681) to turn anti-virus on or off, set up anti-virus policies
and custom service port rules. You can also check the anti-virus engine type and the anti-virus license
and signature status.
• Use the Black/White List screen (Section 39.3 on page 685) to set up anti-virus black (blocked) and
white (allowed) lists of virus file patterns.
• Use the Signature screen (Section 39.4 on page 687) to search for particular signatures and get more
information about them.

Chapter 39 Anti-Virus
USG/ZyWALL User’s Guide
680
39.1.2 What You Need to Know
Anti-Virus Engines
Subscribe to signature files for Kaspersky’s anti-virus engine. After the trial expires, you need to purchase
an iCard for the anti-virus engine you want to use and register it in the Registration > Service screen. You
must use the Kaspersky anti-virus iCard for the Kaspersky anti-virus engine.
Virus and Worm
A computer virus is a small program designed to corrupt and/or alter the operation of other legitimate
programs. A worm is a self-replicating virus that resides in active memory and duplicates itself. The effect
of a virus attack varies from doing so little damage that you are unaware your computer is infected to
wiping out the entire contents of a hard drive to rendering your computer inoperable.
Zyxel Device Anti-Virus Scanner
The Zyxel Device has a built-in signature database. Setting up the Zyxel Device between your local
network and the Internet allows the Zyxel Device to scan files transmitting through the enabled
interfaces into your network. As a network-based anti-virus scanner, the Zyxel Device helps stop threats
at the network edge before they reach the local host computers.
You can set the Zyxel Device to examine files received through the following protocols:
• FTP (File Transfer Protocol)
• HTTP (Hyper Text Transfer Protocol)
• SMTP (Simple Mail Transfer Protocol)
• POP3 (Post Office Protocol version 3)
• IMAP4 (Internet Message Access Protocol version 4)
How the Zyxel Device Anti-Virus Scanner Works
The following describes the virus scanning process on the Zyxel Device.
1The Zyxel Device first identifies SMTP, POP3, IMAP4, HTTP and FTP packets through standard ports.
2If the packets are not session connection setup packets (such as SYN, ACK and FIN), the Zyxel Device
records the sequence of the packets.
3The scanning engine checks the contents of the packets for virus.
4If a virus pattern is matched, the Zyxel Device removes the infected portion of the file along with the rest
of the file. The uninfected portion of the file before a virus pattern was matched still goes through.
Note: If a virus pattern is matched, the Zyxel Device removes the infected portion of the file along with
the rest of the file. The uninfected portion of the file before a virus pattern was matched still goes
through. Since the Zyxel Device erases the infected portion of the file before sending it,
you may not be able to open the file.

Chapter 39 Anti-Virus
USG/ZyWALL User’s Guide
681
Notes About the Zyxel Device Anti-Virus
The following lists important notes about the anti-virus scanner:
1The Zyxel Device anti-virus scanner can detect polymorphic viruses.
2When a virus is detected, an alert message is displayed in Microsoft Windows computers.
3Changes to the Zyxel Device’s anti-virus settings affect new sessions (not the sessions that already
existed before you applied the changed settings).
4The Zyxel Device does not scan the following file/traffic types:
• Simultaneous downloads of a file using multiple connections. For example, when you use FlashGet
to download sections of a file simultaneously.
• Encrypted traffic. This could be password-protected files or VPN traffic where the Zyxel Device is not
the endpoint (pass-through VPN traffic).
• Traffic through custom (non-standard) ports. The only exception is FTP traffic. The Zyxel Device scans
whatever port number is specified for FTP in the ALG screen.
• ZIP file(s) within a ZIP file.
• Traffic a server or client compressed or encoded using a method the Zyxel Device does not
support.
Finding Out More
•See Section 39.5 on page 688 for anti-virus background information.
39.2 Anti-Virus Profile Screen
Click Configuration > UTM Profile > Anti-Virus to display the configuration screen as shown next.
Click on the icons to go to the OneSecurity.com website where there is guidance on configuration
walkthroughs, troubleshooting and other information.
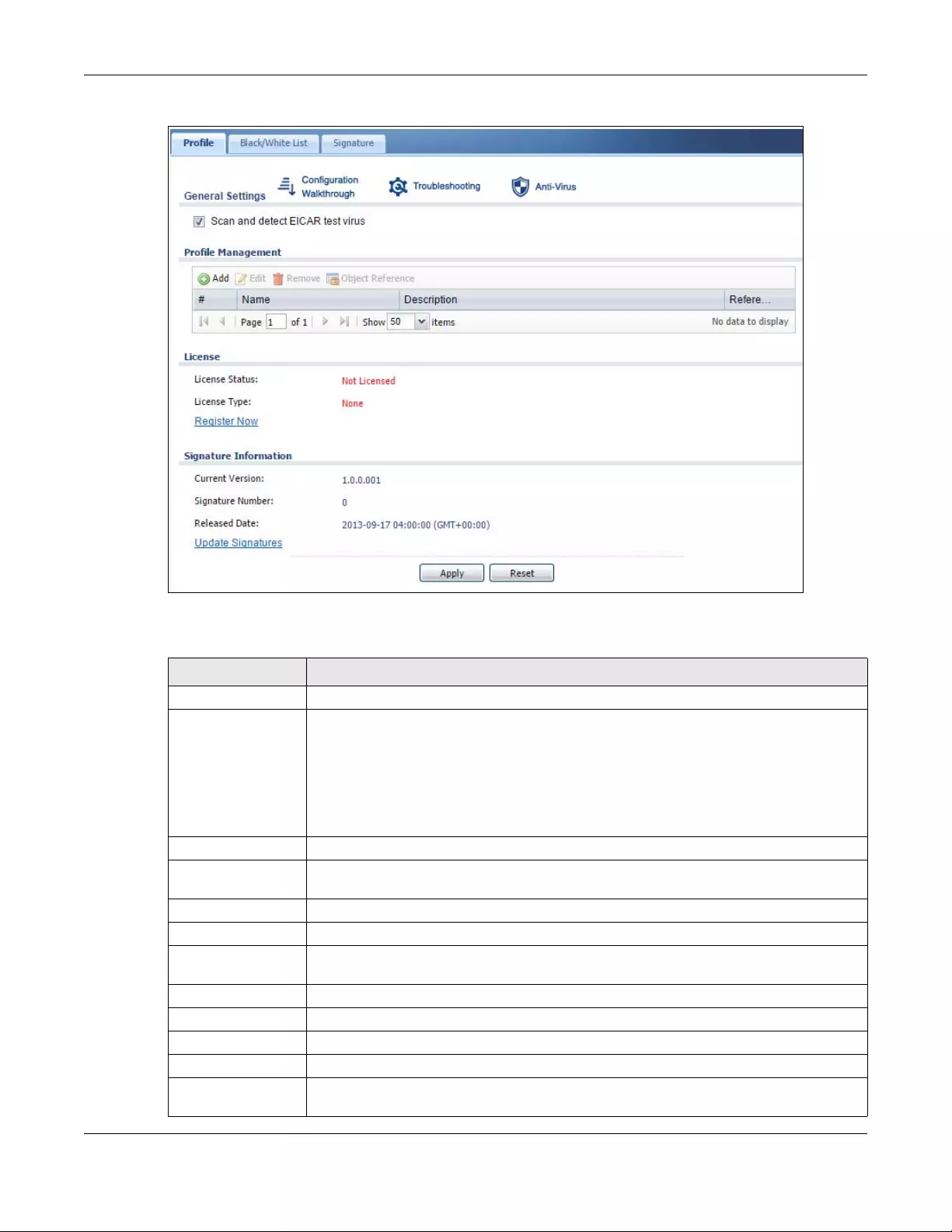
Chapter 39 Anti-Virus
USG/ZyWALL User’s Guide
682
Figure 479 Configuration > UTM Profile > Anti-Virus > Profile
The following table describes the labels in this screen.
Table 259 Configuration > UTM Profile > Anti-Virus > Profile
LABEL DESCRIPTION
General Setting
Scan and detect
EICAR test virus
Select this option to have the Zyxel Device check for the EICAR test file and treat it in the
same way as a real virus file. The EICAR test file is a standardized test file for signature based
anti-virus scanners. When the virus scanner detects the EICAR file, it responds in the same
way as if it found a real virus. Besides straightforward detection, the EICAR file can also be
compressed to test whether the anti-virus software can detect it in a compressed file. The
test string consists of the following human-readable ASCII characters.
X5O!P%@AP[4\PZX54(P^)7CC)7}$EICAR-STANDARD-ANTIVIRUS-TEST-FILE!$H+H*
Profile Management
Add Click this to create a new entry. Select an entry and click Add to create a new entry after
the selected entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
Object Reference Select an entry and click Object References to open a screen that shows which settings use
the entry. Click Refresh to update information in this screen.
# This displays the index number of the rule.
Name This displays the name for the anti-virus rule.
Description This displays the description of the anti-virus rule.
Reference This displays the number of times an Object Reference is used in a rule.
License The following fields display information about the current state of your subscription for virus
signatures.
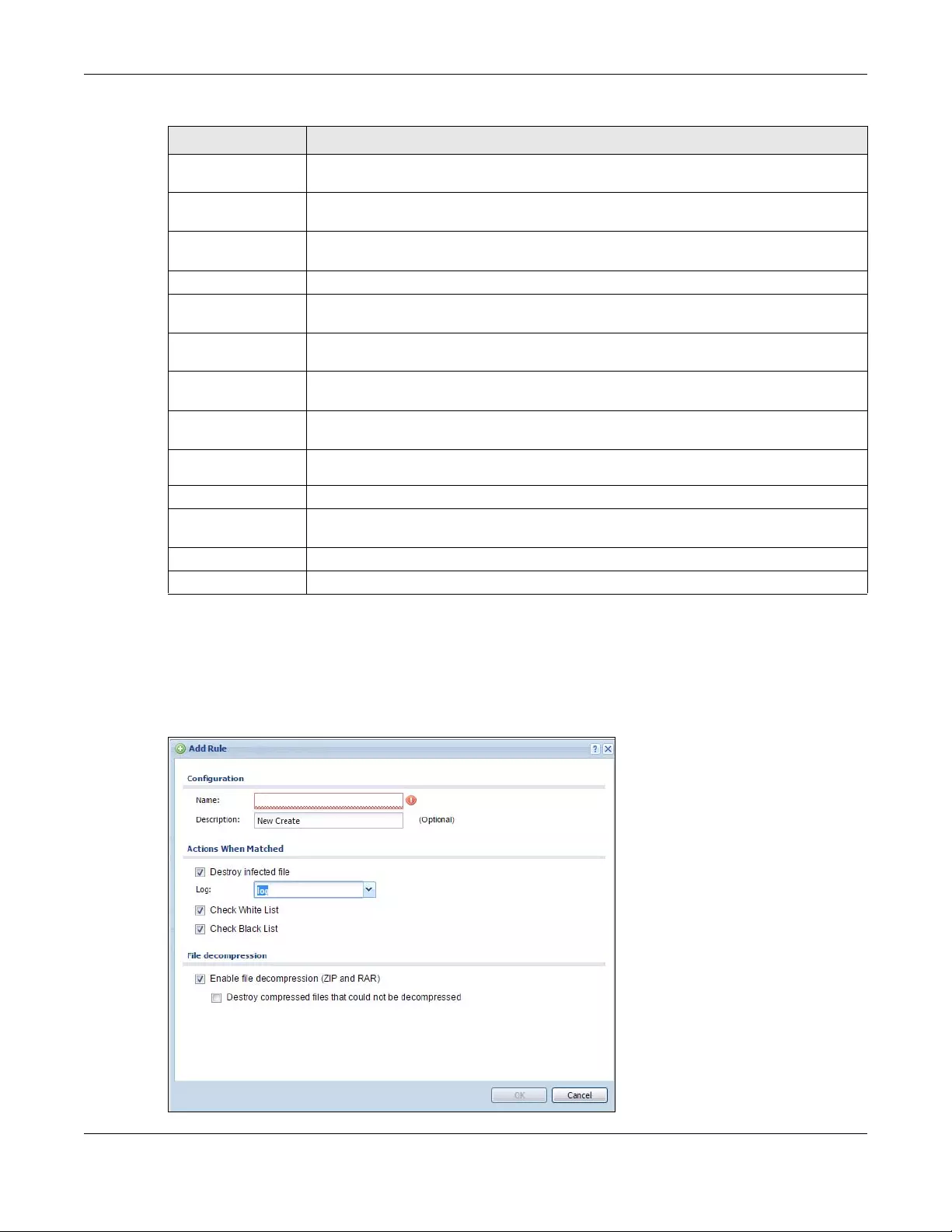
Chapter 39 Anti-Virus
USG/ZyWALL User’s Guide
683
39.2.1 Anti-Virus Profile Add or Edit
Click the Add or Edit icon in the Configuration > UTM Profile > Anti-Virus > Profile screen to display the
configuration screen as shown next.
Figure 480 Configuration > UTM Profile > Anti-Virus > Profile: Profile Management > Add
License Status This field displays whether a service is activated (Licensed) or not (Not Licensed) or expired
(Expired).
License Type This field displays whether you applied for a trial application (Trial) or registered a service
with your iCard’s PIN number (Standard). None displays when the service is not activated.
Denied Access
Message
Write a message that will display when a web site is blocked.
Redirect URL Type the URL of the web site to go to when a web site is blocked.
License Status This field displays whether a service is activated (Licensed) or not (Not Licensed) or expired
(Expired).
License Type This field displays whether you applied for a trial application (Trial) or registered a service
with your iCard’s PIN number (Standard). None displays when the service is not activated.
Signature
Information
The following fields display information on the current signature set that the Zyxel Device is
using.
Current Version This field displays the anti-virus signature set version number. This number gets larger as the
set is enhanced.
Signature
Number This field displays the number of anti-virus signatures in this set.
Released Date This field displays the date and time the set was released.
Update
Signatures Click this link to go to the screen you can use to download signatures from the update
server.
Apply Click Apply to save your changes.
Reset Click Reset to return the screen to its last-saved settings.
Table 259 Configuration > UTM Profile > Anti-Virus > Profile (continued)
LABEL DESCRIPTION
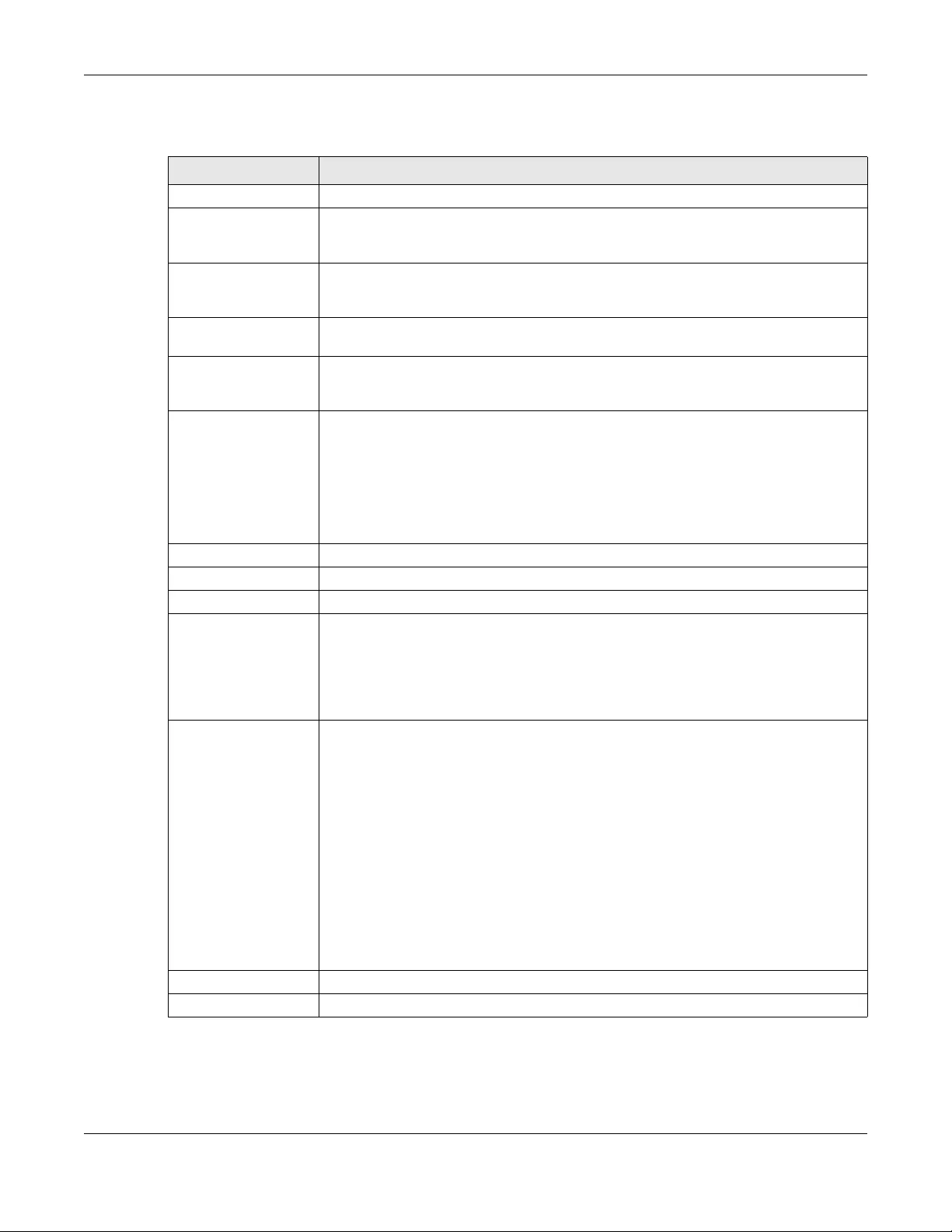
Chapter 39 Anti-Virus
USG/ZyWALL User’s Guide
684
The following table describes the labels in this screen.
Table 260 Configuration > UTM > Anti-Virus > Profile: Profile Management > Add
LABEL DESCRIPTION
Configuration
Name Enter a descriptive name for this anti-virus rule. You may use 1-31 alphanumeric
characters, underscores(_), or dashes (-), but the first character cannot be a number. This
value is case-sensitive.Enter the name of the anti-virus policy.
Description Enter a descriptive name for this anti-virus rule. You may use 1-31 alphanumeric
characters, underscores(_), or dashes (-), but the first character cannot be a number. This
value is case-sensitive.
Actions When
Matched
Destroy infected file When you select this check box, if a virus pattern is matched, the Zyxel Device overwrites
the infected portion of the file (and the rest of the file) with zeros. The uninfected portion
of the file before a virus pattern was matched goes through unmodified.
Log These are the log options:
no: Do not create a log when a packet matches a signature(s).
log: Create a log on the Zyxel Device when a packet matches a signature(s).
log alert: An alert is an e-mailed log for more serious events that may need more
immediate attention. Select this option to have the Zyxel Device send an alert when a
packet matches a signature(s).
Check White List Select this check box to check files against the white list.
Check Black List Select this check box to check files against the black list.
File decompression
Enable file
decompression (ZIP
and RAR)
Select this check box to have the Zyxel Device scan a ZIP file (the file does not have to
have a “zip” or “rar” file extension). The Zyxel Device first decompresses the ZIP file and
then scans the contents for viruses.
Note: The Zyxel Device decompresses a ZIP file once. The Zyxel Device does
NOT decompress any ZIP file(s) within a ZIP file.
Destroy
compressed files
that could not be
decompressed
Note: When you select this option, the Zyxel Device deletes ZIP files that use
password encryption.
Select this check box to have the Zyxel Device delete any ZIP files that it is not able to
unzip. The Zyxel Device cannot unzip password protected ZIP files or a ZIP file within
another ZIP file. There are also limits to the number of ZIP files that the Zyxel Device can
concurrently unzip.
Note: The Zyxel Device’s firmware package cannot go through the Zyxel
Device with this option enabled. The Zyxel Device classifies the firmware
package as not being able to be decompressed and deletes it.
You can upload the firmware package to the Zyxel Device with the option enabled, so
you only need to clear this option while you download the firmware package.
OK Click OK to save your changes.
Cancel Click Cancel to exit this screen without saving your changes.
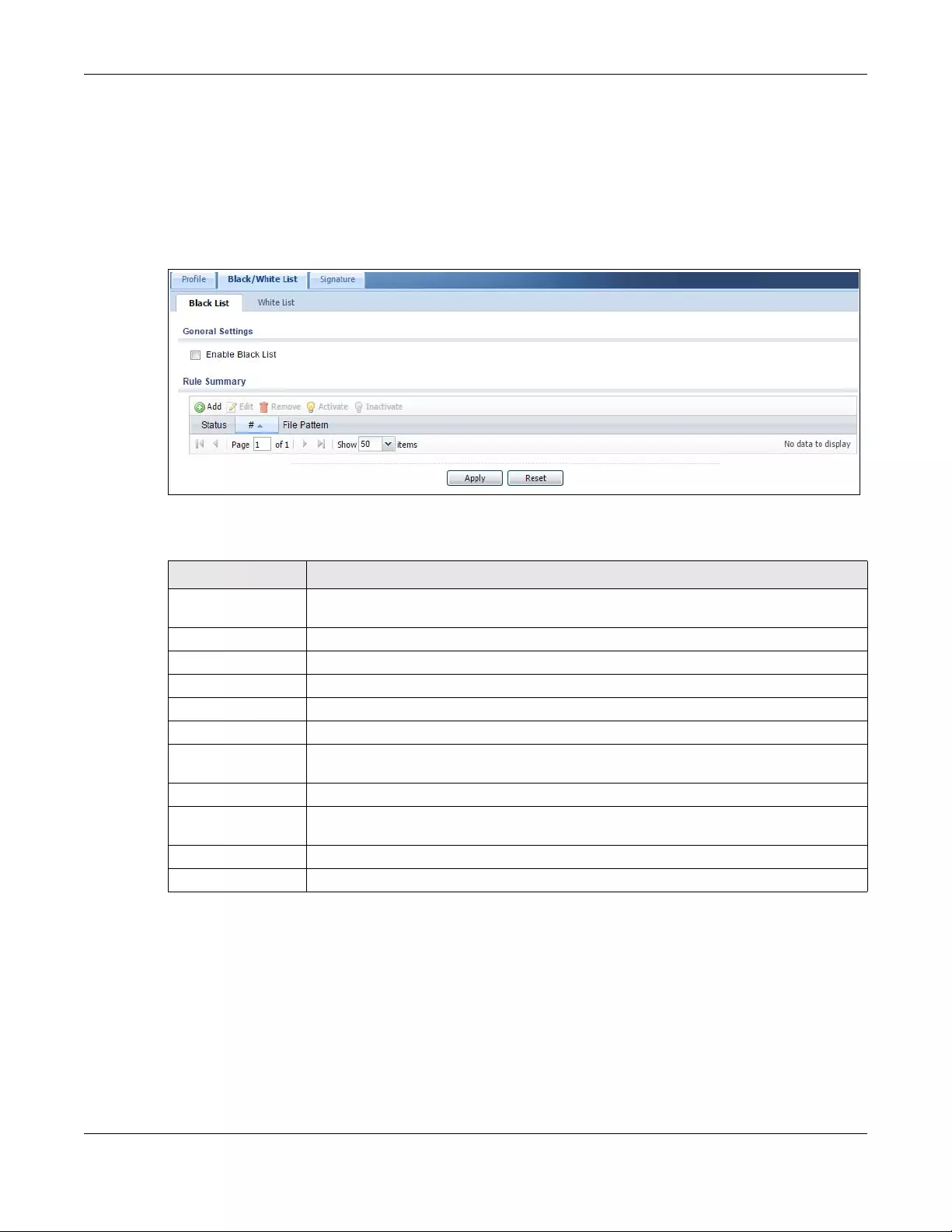
Chapter 39 Anti-Virus
USG/ZyWALL User’s Guide
685
39.3 Anti-Virus Black List
Click Configuration > UTM Profile > Anti-Virus > Black/White List to display the screen shown next. Use the
Black List screen to set up the Anti-Virus black (blocked) list of virus file patterns. Click a column’s
heading cell to sort the table entries by that column’s criteria. Click the heading cell again to reverse
the sort order.
Figure 481 Configuration > UTM Profile > Anti-Virus > Black/White List > Black List
The following table describes the labels in this screen.
39.3.1 Anti-Virus Black List or White List Add/Edit
From the Configuration > UTM Profile > Anti-Virus > Black/White List > Black List (or White List) screen, click
the Add icon or an Edit icon to display the following screen.
• For a black list entry, enter a file pattern that should cause the Zyxel Device to log and delete a file.
• For a white list entry, enter a file pattern that should cause the Zyxel Device to allow a file.
Table 261 Configuration > UTM Profile > Anti-Virus > Black/White List > Black List
LABEL DESCRIPTION
Enable Black List Select this check box to log and delete files with names that match the black list patterns.
Use the black list to log and delete files with names that match the black list patterns.
Add Click this to create a new entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Status The activate (light bulb) icon is lit when the entry is active and dimmed when the entry is
inactive.
#This is the entry’s index number in the list.
File Pattern This is the file name pattern. If a file’s name that matches this pattern, the Zyxel Device logs
and deletes the file.
Apply Click Apply to save your changes.
Reset Click Reset to return the screen to its last-saved settings.
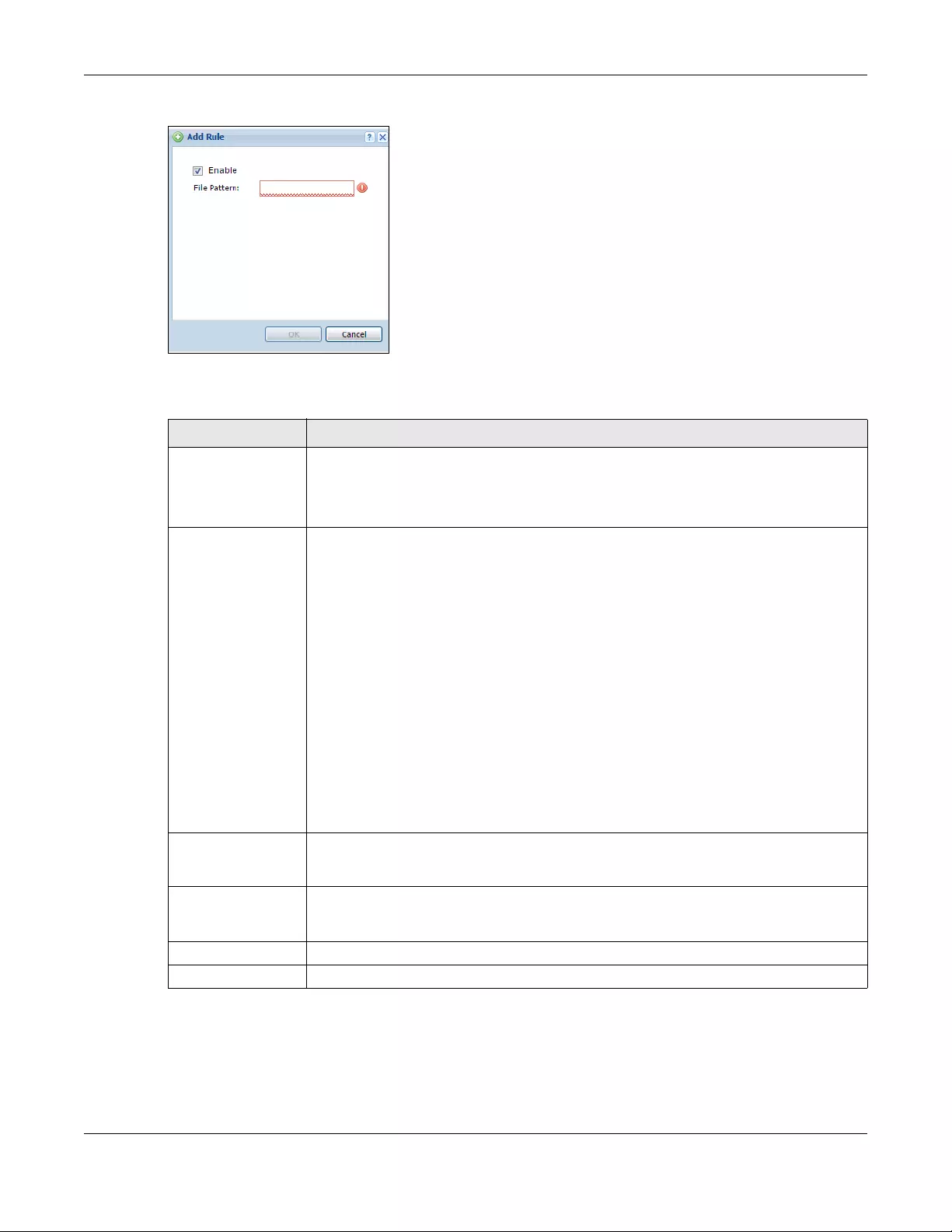
Chapter 39 Anti-Virus
USG/ZyWALL User’s Guide
686
Figure 482 Configuration > UTM Profile > Anti-Virus > Black/White List > Black List (or White List) > Add
The following table describes the labels in this screen.
39.3.2 Anti-Virus White List
Click Configuration > UTM Profile > Anti-Virus > Black/White List > White List to display the screen shown
next. Use the Black/White List screen to set up Anti-Virus black (blocked) and white (allowed) lists of virus
Table 262 Configuration > UTM Profile > Anti-Virus > Black/White List > Black List (or White List) > Add
LABEL DESCRIPTION
Enable If this is a black list entry, select this option to have the Zyxel Device apply this entry when
using the black list.
If this is a white list entry, select this option to have the Zyxel Device apply this entry when
using the white list.
File Pattern For a black list entry, specify a pattern to identify the names of files that the Zyxel Device
should log and delete.
For a white list entry, specify a pattern to identify the names of files that the Zyxel Device
should not scan for viruses.
• Use up to 80 characters. Alphanumeric characters, underscores (_), dashes (-), question
marks (?) and asterisks (*) are allowed.
• A question mark (?) lets a single character in the file name vary. For example, use
“a?.zip” (without the quotation marks) to specify aa.zip, ab.zip and so on.
• Wildcards (*) let multiple files match the pattern. For example, use “*a.zip” (without the
quotation marks) to specify any file that ends with “a.zip”. A file named “testa.zip would
match. There could be any number (of any type) of characters in front of the “a.zip” at
the end and the file name would still match. A file named “test.zipa” for example would
not match.
• A * in the middle of a pattern has the Zyxel Device check the beginning and end of the
file name and ignore the middle. For example, with “abc*.zip”, any file starting with
“abc” and ending in “.zip” matches, no matter how many characters are in between.
• The whole file name has to match if you do not use a question mark or asterisk.
• If you do not use a wildcard, the Zyxel Device checks up to the first 80 characters of a
file name.
Source Select a source address or address group for whom this policy applies. You can configure a
new one in the Object > Address > Add screen. Select any if the policy is effective for every
source.
Destination Select a destination address or address group for whom this policy applies. You can
configure a new one in the Object > Addres s > Ad d screen. Select any if the policy is
effective for every destination.
OK Click OK to save your changes.
Cancel Click Cancel to exit this screen without saving your changes.
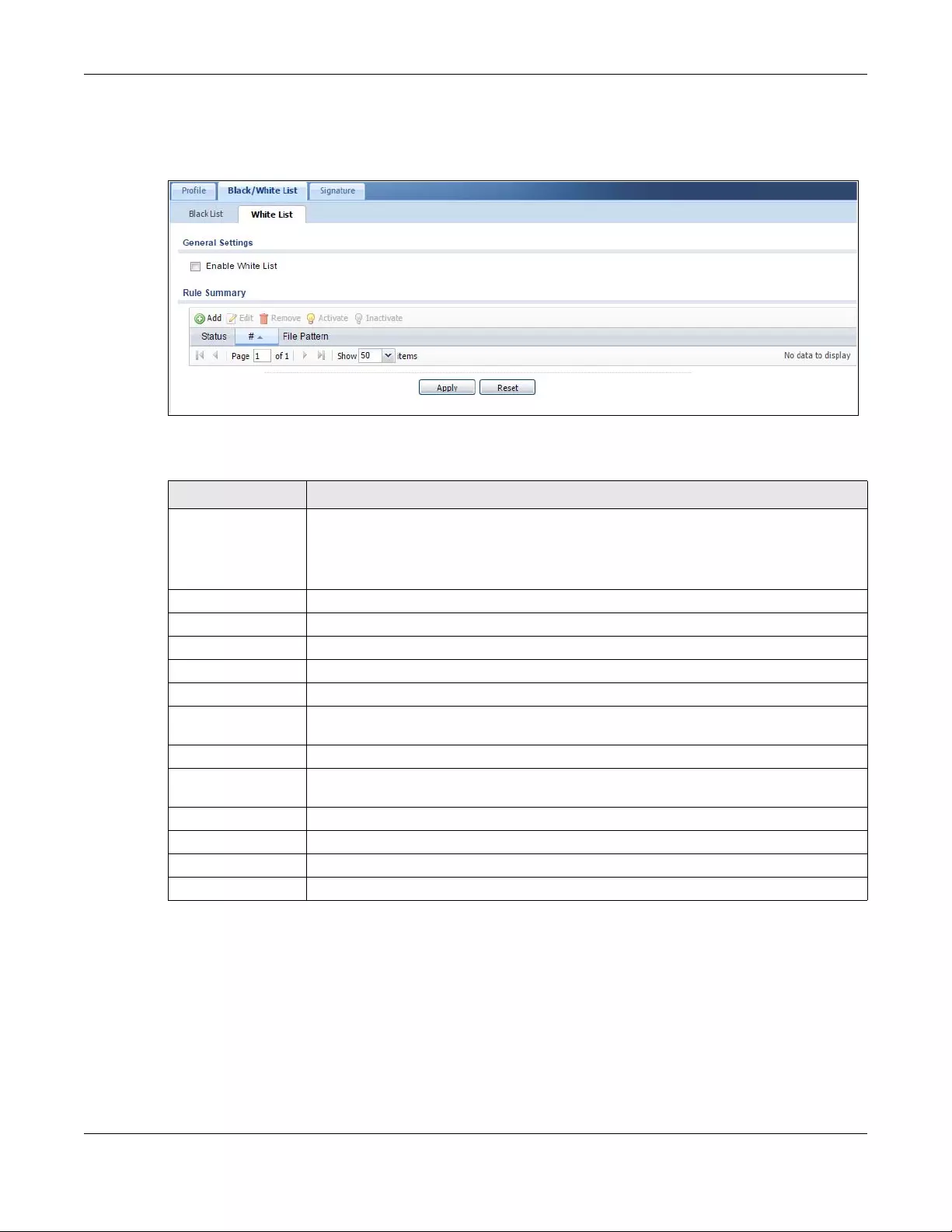
Chapter 39 Anti-Virus
USG/ZyWALL User’s Guide
687
file patterns. Click a column’s heading cell to sort the table entries by that column’s criteria. Click the
heading cell again to reverse the sort order.
Figure 483 Configuration > UTM Profile > Anti-Virus > Black/White List > White List
The following table describes the labels in this screen.
39.4 AV Signature Searching
Click Configuration > UTM Profile > Anti-Virus > Signature to display this screen. Use this screen to locate
signatures and display details about them.
If Internet Explorer opens a warning screen about a script making Internet Explorer run slowly and the
computer maybe becoming unresponsive, just click No to continue. Click a column’s heading cell to
sort the table entries by that column’s criteria. Click the heading cell again to reverse the sort order.
Table 263 Configuration > UTM Profile > Anti-Virus > Black/White List > White List
LABEL DESCRIPTION
Enable White List Select this check box to have the Zyxel Device not perform the anti-virus check on files with
names that match the white list patterns.
Use the white list to have the Zyxel Device not perform the anti-virus check on files with
names that match the white list patterns.
Add Click this to create a new entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Status The activate (light bulb) icon is lit when the entry is active and dimmed when the entry is
inactive.
#This is the entry’s index number in the list.
File Pattern This is the file name pattern. If a file’s name matches this pattern, the Zyxel Device does not
check the file for viruses.
Source This is the source address or address group for whom this policy applies.
Destination This is the destination address or address group for whom this policy applies.
Apply Click Apply to save your changes.
Reset Click Reset to return the screen to its last-saved settings.
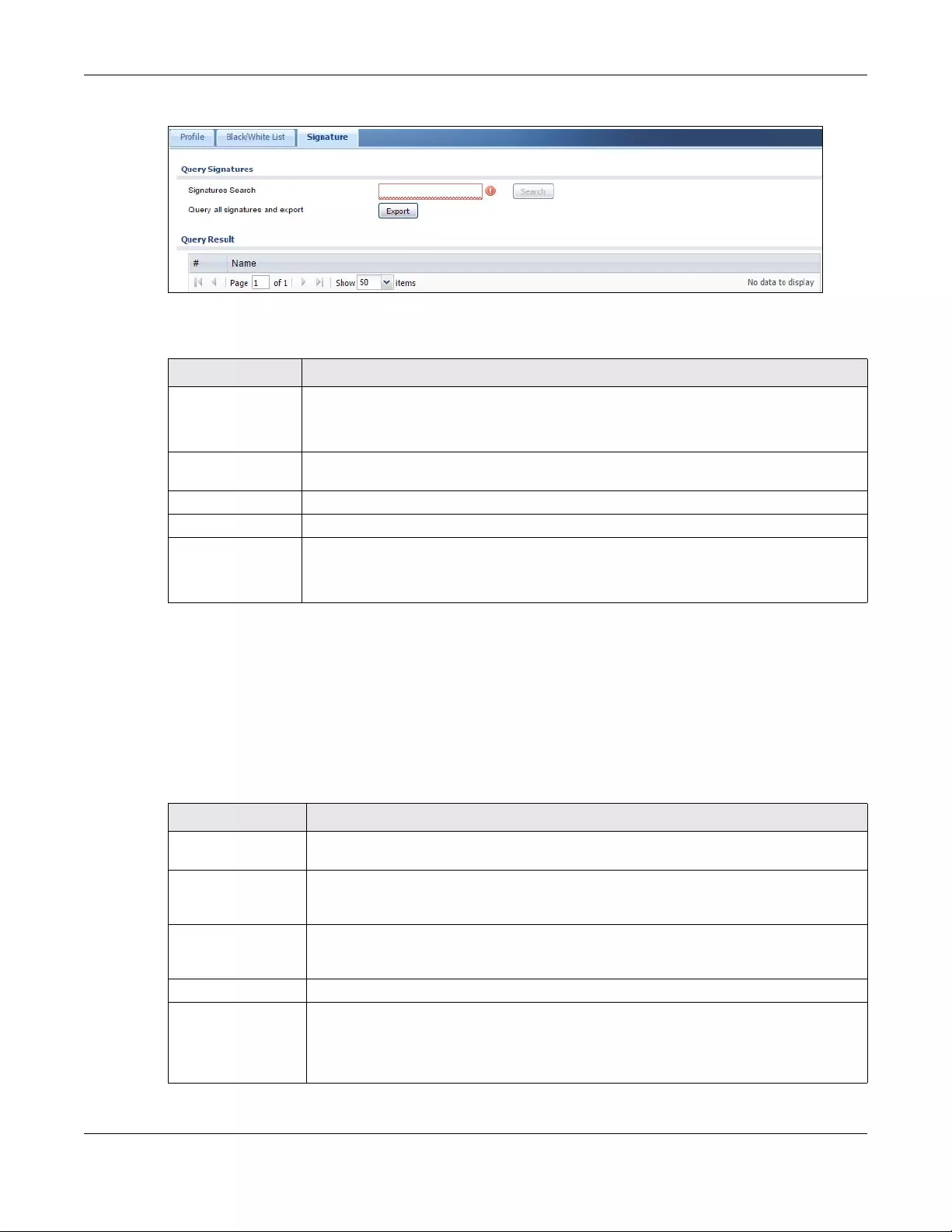
Chapter 39 Anti-Virus
USG/ZyWALL User’s Guide
688
Figure 484 Configuration > UTM Profile > Anti-Virus > Signature
The following table describes the labels in this screen.
39.5 Anti-Virus Technical Reference
Types of Computer Viruses
The following table describes some of the common computer viruses.
Table 264 Configuration > UTM > Anti-Virus > Signature
LABEL DESCRIPTION
Signatures Search Enter the name, part of the name or keyword of the signature(s) you want to find. This search
is not case-sensitive and accepts numerical strings.
Query all signatures
and export
Click Export to have the Zyxel Device save all of the anti-virus signatures to your computer in
a .txt file.
Query Result
# This is the entry’s index number in the list.
Name This is the name of the anti-virus signature. Click the Name column heading to sort your
search results in ascending or descending order according to the signature name.
Click a signature’s name to see details about the virus.
Table 265 Common Computer Virus Types
TYPE DESCRIPTION
File Infector This is a small program that embeds itself in a legitimate program. A file infector is able to
copy and attach itself to other programs that are executed on an infected computer.
Boot Sector Virus This type of virus infects the area of a hard drive that a computer reads and executes
during startup. The virus causes computer crashes and to some extend renders the infected
computer inoperable.
Macro Virus Macro viruses or Macros are small programs that are created to perform repetitive actions.
Macros run automatically when a file to which they are attached is opened. Macros
spread more rapidly than other types of viruses as data files are often shared on a network.
E-mail Virus E-mail viruses are malicious programs that spread through e-mail.
Polymorphic Virus A polymorphic virus (also known as a mutation virus) tries to evade detection by changing
a portion of its code structure after each execution or self replication. This makes it harder
for an anti-virus scanner to detect or intercept it.
A polymorphic virus can also belong to any of the virus types discussed above.

Chapter 39 Anti-Virus
USG/ZyWALL User’s Guide
689
Computer Virus Infection and Prevention
The following describes a simple life cycle of a computer virus.
1A computer gets a copy of a virus from a source such as the Internet, e-mail, file sharing or any
removable storage media. The virus is harmless until the execution of an infected program.
2The virus spreads to other files and programs on the computer.
3The infected files are unintentionally sent to another computer thus starting the spread of the virus.
4Once the virus is spread through the network, the number of infected networked computers can grow
exponentially.
Types of Anti-Virus Scanner
The section describes two types of anti-virus scanner: host-based and network-based.
A host-based anti-virus (HAV) scanner is often software installed on computers and/or servers in the
network. It inspects files for virus patterns as they are moved in and out of the hard drive. However, host-
based anti-virus scanners cannot eliminate all viruses for a number of reasons:
• HAV scanners are slow in stopping virus threats through real-time traffic (such as from the Internet).
• HAV scanners may reduce computing performance as they also share the resources (such as CPU
time) on the computer for file inspection.
• You have to update the virus signatures and/or perform virus scans on all computers in the network
regularly.
A network-based anti-virus (NAV) scanner is often deployed as a dedicated security device (such as
your Zyxel Device) on the network edge. NAV scanners inspect real-time data traffic (such as E-mail
messages or web) that tends to bypass HAV scanners. The following lists some of the benefits of NAV
scanners.
• NAV scanners stops virus threats at the network edge before they enter or exit a network.
• NAV scanners reduce computing loading on computers as the read-time data traffic inspection is
done on a dedicated security device.

USG/ZyWALL User’s Guide
690
CHAPTER 40
Anti-Spam
40.1 Overview
The anti-spam feature can mark or discard spam (unsolicited commercial or junk e-mail). Use the white
list to identify legitimate e-mail. Use the black list to identify spam e-mail. The Zyxel Device can also
check e-mail against a DNS black list (DNSBL) of IP addresses of servers that are suspected of being used
by spammers.
40.1.1 What You Can Do in this Chapter
• Use the General Profile screens (Section 40.3 on page 692) to turn anti-spam on or off and manage
anti-spam policies.
• Use the Mail Scan screen (Section 40.4 on page 695) to enable and configure the mail scan functions.
• Use the Black/White List screens (Section 40.5 on page 697) to set up a black list to identify spam and
a white list to identify legitimate e-mail.
• Use the DNSBL screens (Section 40.7 on page 702) to have the Zyxel Device check e-mail against DNS
Black Lists.
40.1.2 What You Need to Know
White List
Configure white list entries to identify legitimate e-mail. The white list entries have the Zyxel Device
classify any e-mail that is from a specified sender or uses a specified header field and header value as
being legitimate (see E-mail Headers on page 691 for more on mail headers). The anti-spam feature
checks an e-mail against the white list entries before doing any other anti-spam checking. If the e-mail
matches a white list entry, the Zyxel Device classifies the e-mail as legitimate and does not perform any
more anti-spam checking on that individual e-mail. A properly configured white list helps keep
important e-mail from being incorrectly classified as spam. The white list can also increases the Zyxel
Device’s anti-spam speed and efficiency by not having the Zyxel Device perform the full anti-spam
checking process on legitimate e-mail.
Black List
Configure black list entries to identify spam. The black list entries have the Zyxel Device classify any e-
mail that is from or forwarded by a specified IP address or uses a specified header field and header
value as being spam. If an e-mail does not match any of the white list entries, the Zyxel Device checks it
against the black list entries. The Zyxel Device classifies an e-mail that matches a black list entry as spam
and immediately takes the configured action for dealing with spam. If an e-mail matches a blacklist
entry, the Zyxel Device does not perform any more anti-spam checking on that individual e-mail. A
properly configured black list helps catch spam e-mail and increases the Zyxel Device’s anti-spam
speed and efficiency.

Chapter 40 Anti-Spam
USG/ZyWALL User’s Guide
691
SMTP and POP3
Simple Mail Transfer Protocol (SMTP) is the Internet’s message transport standard. It controls the sending
of e-mail messages between servers. E-mail clients (also called e-mail applications) then use mail server
protocols such as POP (Post Office Protocol) or IMAP (Internet Message Access Protocol) to retrieve e-
mail. E-mail clients also generally use SMTP to send messages to a mail server. The older POP2 requires
SMTP for sending messages while the newer POP3 can be used with or without it. This is why many e-mail
applications require you to specify both the SMTP server and the POP or IMAP server (even though they
may actually be the same server).
The Zyxel Device’s anti-spam feature checks SMTP (TCP port 25) and POP3 (TCP port 110) e-mails by
default. You can also specify custom SMTP and POP3 ports for the Zyxel Device to check.
E-mail Headers
Every email has a header and a body. The header is structured into fields and includes the addresses of
the recipient and sender, the subject, and other information about the e-mail and its journey. The body
is the actual message text and any attachments. You can have the Zyxel Device check for specific
header fields with specific values.
E-mail programs usually only show you the To:, From:, Subject:, and Date: header fields but there are
others such as Received: and Content-Type:. To see all of an e-mail’s header, you can select an e-mail
in your e-mail program and look at its properties or details. For example, in Microsoft’s Outlook Express,
select a mail and click File > Pro perties > Details. This displays the e-mail’s header. Click Message Source
to see the source for the entire mail including both the header and the body.
E-mail Header Buffer Size
The Zyxel Device has a 5 K buffer for an individual e-mail header. If an e-mail’s header is longer than 5 K,
the Zyxel Device only checks up to the first 5 K.
DNSBL
A DNS Black List (DNSBL) is a server that hosts a list of IP addresses known or suspected of having sent or
forwarded spam. A DNSBL is also known as a DNS spam blocking list. The Zyxel Device can check the
routing addresses of e-mail against DNSBLs and classify an e-mail as spam if it was sent or forwarded by
a computer with an IP address in the DNSBL.
Finding Out More
See Section 40.8 on page 704 for more background information on anti-spam.
40.2 Before You Begin
• Before using the Anti-Spam features (IP Reputation, Mail Content Analysis and Virus Outbreak
Detection) you must activate your Anti-Spam Service license.
• Configure your zones before you configure anti-spam.
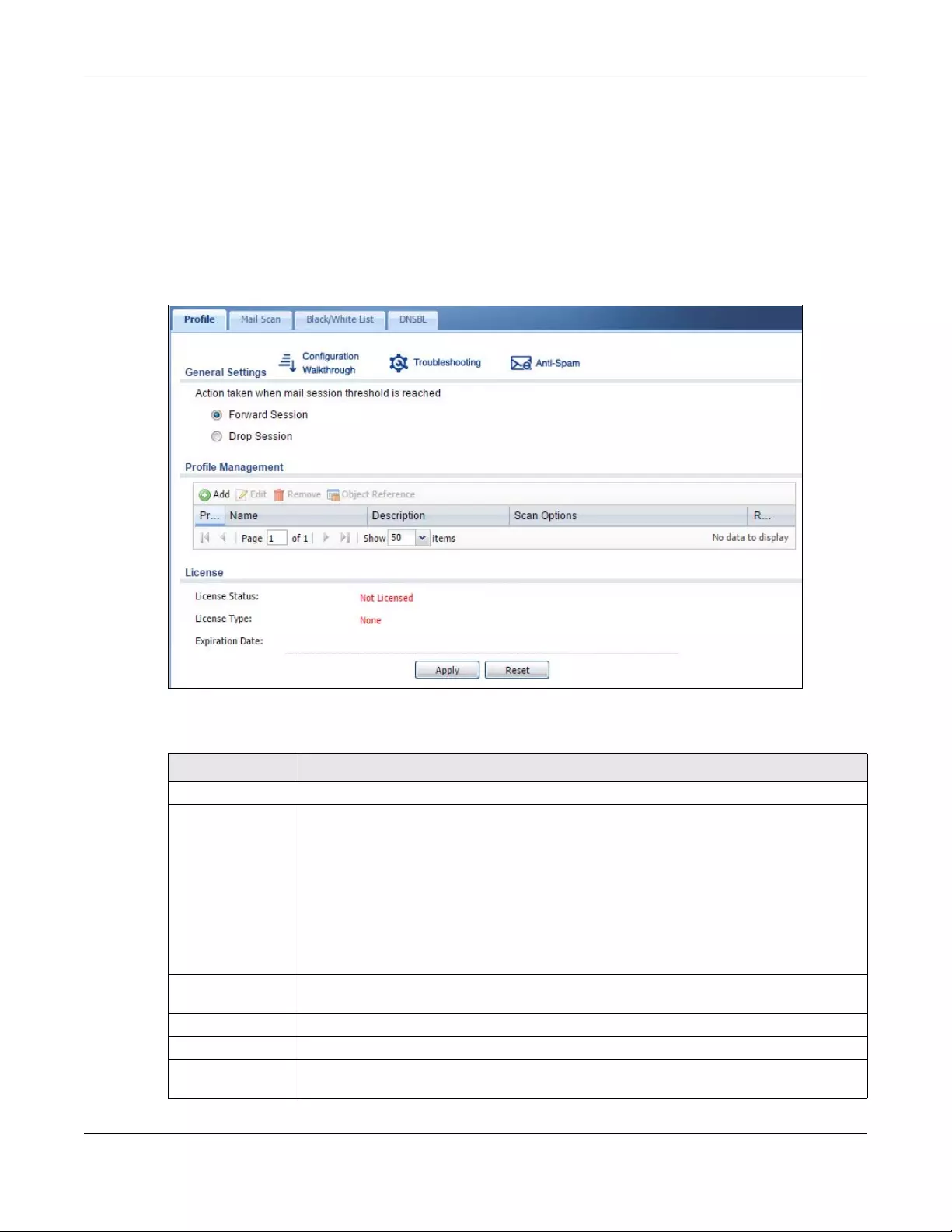
Chapter 40 Anti-Spam
USG/ZyWALL User’s Guide
692
40.3 The Anti-Spam Profile Screen
Click Configuration > UTM Profile > Anti-Spam to open the Anti-Spam Profile screen. Use this screen to
turn the anti-spam feature on or off and manage anti-spam policies. You can also select the action the
Zyxel Device takes when the mail sessions threshold is reached.
Click on the icons to go to the OneSecurity.com website where there is guidance on configuration
walkthroughs, troubleshooting and other information.
Figure 485 Configuration > UTM Profile > Anti-Spam > Profile
The following table describes the labels in this screen.
Table 266 Configuration > UTM Profile > Anti-Spam > Profile
LABEL DESCRIPTION
General Settings
Action taken when
mail sessions
threshold is
reached
An e-mail session is when an e-mail client and e-mail server (or two e-mail servers) connect
through the Zyxel Device. Select how to handle concurrent e-mail sessions that exceed the
maximum number of concurrent e-mail sessions that the anti-spam feature can handle. See
the chapter of product specifications for the threshold.
Select Forward Session to have the Zyxel Device allow the excess e-mail sessions without any
spam filtering.
Select Drop Session to have the Zyxel Device drop mail connections to stop the excess e-mail
sessions. The e-mail client or server will have to re-attempt to send or receive e-mail later
when the number of e-mail sessions is under the threshold.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after the
selected entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
Object
Reference Select an entry and click Object References to open a screen that shows which settings use
the entry. Click Refresh to update information in this screen.
Chapter 40 Anti-Spam
USG/ZyWALL User’s Guide
693
40.3.1 The Anti-Spam Profile Add or Edit Screen
Click the Add or Edit icon in the Configuration > UTM Profile > Anti-Spam > Profile screen to display the
configuration screen as shown next. Use this screen to configure an anti-spam policy that controls what
traffic direction of e-mail to check, which e-mail protocols to scan, the scanning options, and the action
to take on spam traffic.
Priority This is the index number of the anti-spam rule. Antis-spam rules are applied in turn.
Name The name identifies the anti-spam rule.
Description This is some optional extra information on the rule.
Scan Options This shows which types (protocols) of traffic to scan for spam.
Reference This shows how many objects are referenced in the rule.
License
License Status This read-only field displays the status of your anti-spam scanning service registration.
Not Licensed displays if you have not successfully registered and activated the service.
Expired displays if your subscription to the service has expired.
Licensed displays if you have successfully registered the Zyxel Device and activated the
service.
License Type This read-only field displays what kind of service registration you have for the anti-spam
scanning.
None displays if you have not successfully registered and activated the service.
Standard displays if you have successfully registered the Zyxel Device and activated the
service with your iCard’s PIN number.
Trial displays if you have successfully registered the Zyxel Device and activated the trial
service subscription.
Expiration Date This field displays the date your service license expires.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 266 Configuration > UTM Profile > Anti-Spam > Profile
LABEL DESCRIPTION
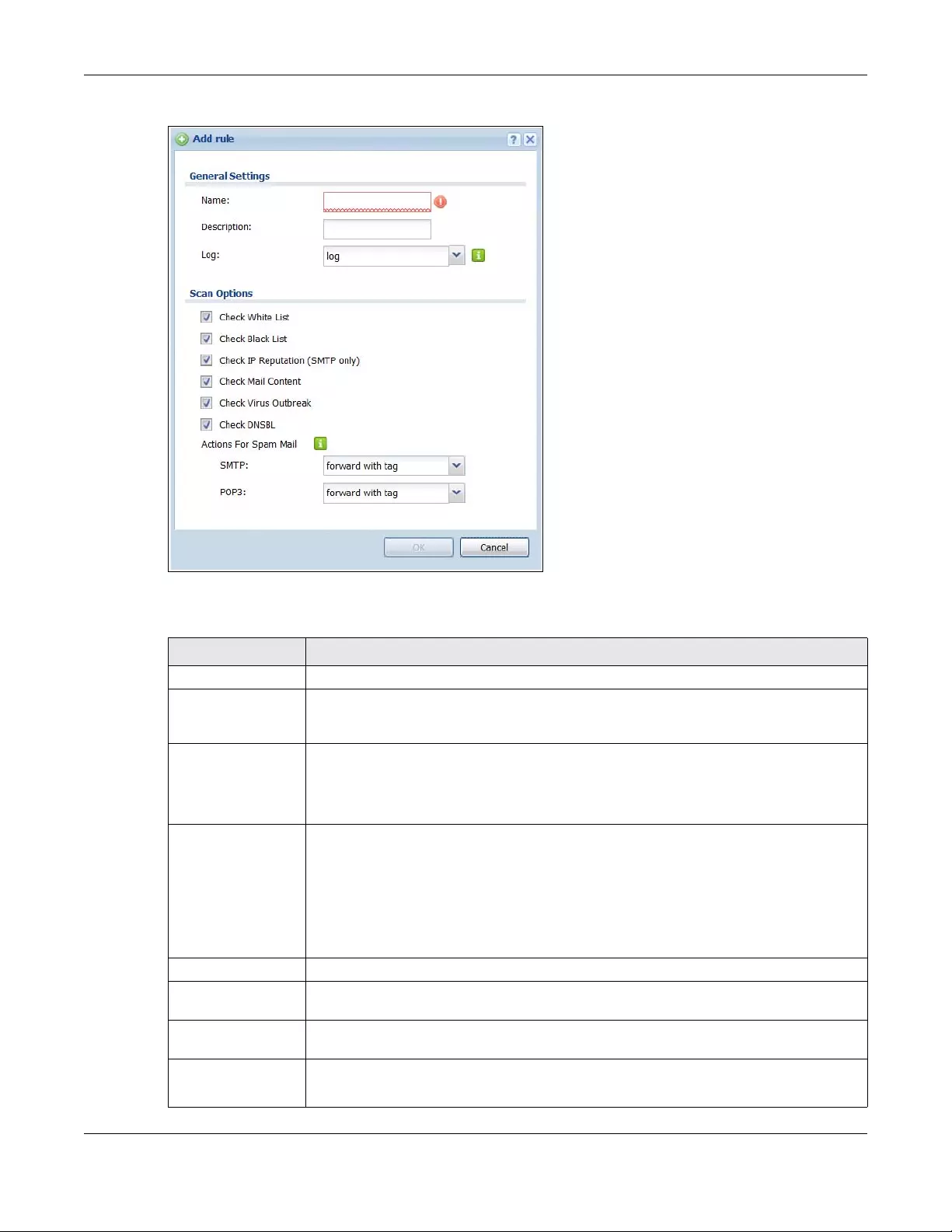
Chapter 40 Anti-Spam
USG/ZyWALL User’s Guide
694
Figure 486 Configuration > UTM Profile > Anti-Spam > Profile > Add
The following table describes the labels in this screen.
Table 267 Configuration > UTM Profile > Anti-Spam > Profile > Add
LABEL DESCRIPTION
General Settings
Name Enter a descriptive name for this anti-spam rule. You may use 1-31 alphanumeric
characters, underscores(_), or dashes (-), but the first character cannot be a number. This
value is case-sensitive.
Description Enter a description for the anti-spam rule to help identify the purpose of rule. You may use 1-
31 alphanumeric characters, underscores(_), or dashes (-), but the first character cannot
be a number. This value is case-sensitive.
This field is optional.
Log Select how the Zyxel Device is to log the event when the DNSBL times out or an e-mail
matches the white list, black list, or DNSBL.
no: Do not create a log.
log: Create a log on the Zyxel Device.
log alert: An alert is an e-mailed log for more serious events that may need more immediate
attention. Select this option to have the Zyxel Device send an alert.
Scan Options
Check White List Select this check box to check e-mail against the white list. The Zyxel Device classifies e-mail
that matches a white list entry as legitimate (not spam).
Check Black List Select this check box to check e-mail against the black list. The Zyxel Device classifies e-mail
that matches a black list entry as spam.
Check IP
Reputation
(SMTP Only)
Select this to use IP reputation to identify Spam or Unwanted Bulk Email by the sender’s IP
address.
Chapter 40 Anti-Spam
USG/ZyWALL User’s Guide
695
40.4 The Mail Scan Screen
Click Configuration > UTM Profile > Anti-Spam > Mail Scan to open the Mail Scan screen. Use this screen
to enable and configure the Mail Scan functions. You must first enable the Mail Scan functions on this
screen before selecting them in the Configuration > UTM Profile > Anti-Spam > Profile > Add/Edit screen.
Check Mail
Content Select this to identify Spam Email by content, such as malicious content.
Check Virus
Outbreak Select this to scan emails for attached viruses.
Check DNSBL Select this check box to check e-mail against the Zyxel Device’s configured DNSBL
domains. The Zyxel Device classifies e-mail that matches a DNS black list as spam.
Actions for Spam
Mail
Use this section to set how the Zyxel Device is to handle spam mail.
SMTP Select how the Zyxel Device is to handle spam SMTP mail.
Select drop to discard spam SMTP mail.
Select forward to allow spam SMTP mail to go through.
Select forward with tag to add a spam tag to an SMTP spam mail’s mail subject and send it
on to the destination.
POP3 Select how the Zyxel Device is to handle spam POP3 mail.
Select forward to allow spam POP3 mail to go through.
Select forward with tag to add a spam tag to an POP3 spam mail’s mail subject and send it
on to the destination.
OK Click OK to save your changes.
Cancel Click Cancel to exit this screen without saving your changes.
Table 267 Configuration > UTM Profile > Anti-Spam > Profile > Add (continued)
LABEL DESCRIPTION
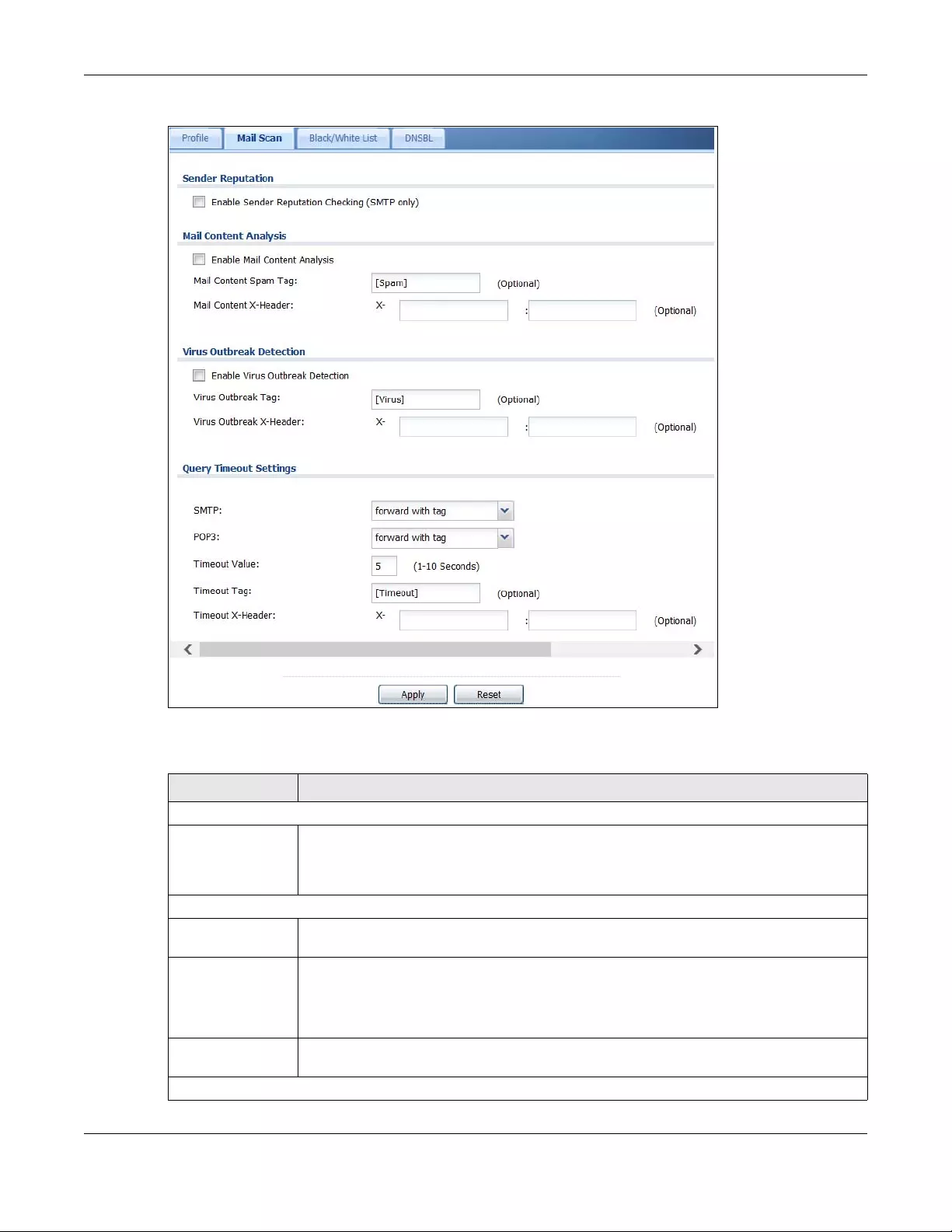
Chapter 40 Anti-Spam
USG/ZyWALL User’s Guide
696
Figure 487 Configuration > UTM Profile > Anti-Spam > Mail Scan
The following table describes the labels in this screen.
Table 268 Configuration > UTM Profile > Anti-Spam > Mail Scan
LABEL DESCRIPTION
Sender Reputation
Enable Sender
Reputation
Checking (SMTP
only)
Select this to have the Zyxel Device scan for spam e-mail by IP Reputation. Spam or
Unwanted Bulk Email is determined by the sender’s IP address.
Mail Content Analysis
Enable Mail
Content Analysis
Select this to identify Spam Email by content, such as malicious content.
Mail Content Spam
Tag
Enter a message or label (up to 15 ASCII characters) to add to the beginning of the mail
subject of e-mails that are determined to spam based on the mail content analysis.
This tag is only added if the anti-spam policy is configured to forward spam mail with a spam
tag.
Mail Content X-
Header
Specify the name and value for the X-Header to be added when an email is determined to
be spam by mail content.
Virus Outbreak Detection
Chapter 40 Anti-Spam
USG/ZyWALL User’s Guide
697
40.5 The Anti-Spam Black List Screen
Click Configuration > UTM Profile > Anti-Spam > Black /White List to display the Anti-Spam Black List
screen.
Configure the black list to identify spam e-mail. You can create black list entries based on the sender’s
or relay server’s IP address or e-mail address. You can also create entries that check for particular e-mail
header fields with specific values or specific subject text. Click a column’s heading cell to sort the table
entries by that column’s criteria. Click the heading cell again to reverse the sort order.
Enable Virus
Outbreak
Detection
This scans emails for attached viruses.
Virus Outbreak Tag Enter a message or label (up to 15 ASCII characters) to add to the beginning of the mail
subject of e-mails that are determined have an attached viruses.
This tag is only added if the anti-spam policy is configured to forward spam mail with a spam
tag.
Virus Outbreak X-
Header
Specify the name and value for the X-Header to be added when an email is determined to
have an attached virus.
Query Timeout Settings
SMTP Select how the Zyxel Device is to handle SMTP mail query timeout.
Select drop to discard SMTP mail.
Select forward to allow SMTP mail to go through.
Select forward with tag to add a tag to an SMTP query timeout mail’s mail subject and send it
on to the destination.
POP3 Select how the Zyxel Device is to handle POP3 mail query timeout.
Select forward to allow POP3 mail to go through.
Select forward with tag to add a tag to an POP3 query timeout mail’s mail subject and send it
on to the destination.
Timeout Value Set how long the Zyxel Device waits for a reply from the mail scan server. If there is no reply
before this time period expires, the Zyxel Device takes the action defined in the relevant
Actions when Query Time out field.
Timeout Tag Enter a message or label (up to 15 ASCII characters) to add to the mail subject of e-mails that
the Zyxel Device forwards if queries to the mail scan servers time out.
Timeout X-Header Specify the name and value for the X-Header to be added when queries to the mail scan
servers time out.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 268 Configuration > UTM Profile > Anti-Spam > Mail Scan
LABEL DESCRIPTION
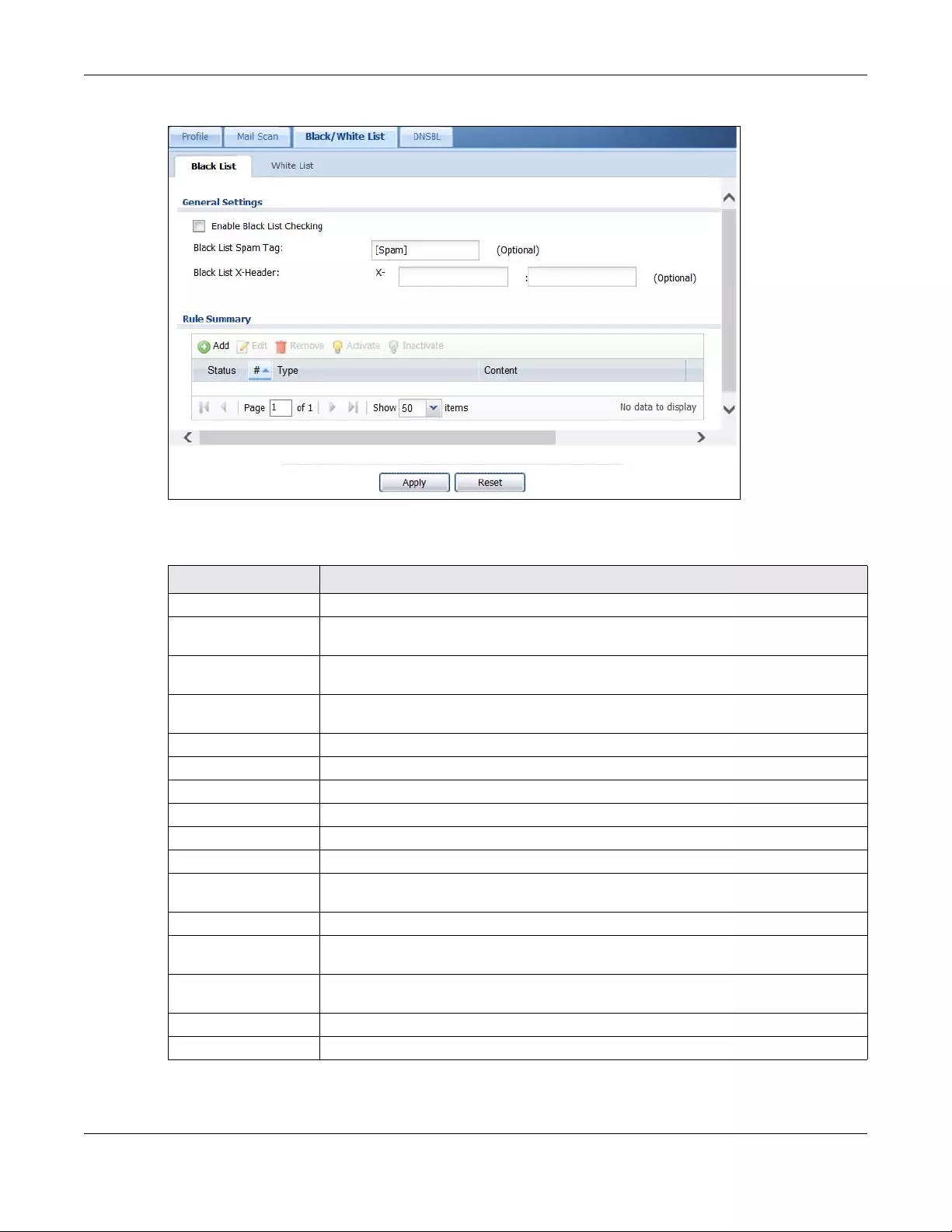
Chapter 40 Anti-Spam
USG/ZyWALL User’s Guide
698
Figure 488 Configuration > UTM Profile > Anti-Spam > Black/White List > Black List
The following table describes the labels in this screen.
Table 269 Configuration > UTM Profile > Anti-Spam > Black/White List > Black List
LABEL DESCRIPTION
General Settings
Enable Black List
Checking
Select this check box to have the Zyxel Device treat e-mail that matches (an active)
black list entry as spam.
Black List Spam Tag Enter a message or label (up to 15 ASCII characters) to add to the mail subject of e-mails
that match the Zyxel Device’s spam black list.
Black List X-Header Specify the name and value for the X-Header to be added to e-mails that match the
Zyxel Device’s spam black list.
Rule Summary
Add Click this to create a new entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Status The activate (light bulb) icon is lit when the entry is active and dimmed when the entry is
inactive.
#This is the entry’s index number in the list.
Type This field displays whether the entry is based on the e-mail’s subject, source or relay IP
address, source e-mail address, or header.
Content This field displays the subject content, source or relay IP address, source e-mail address, or
header value for which the entry checks.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
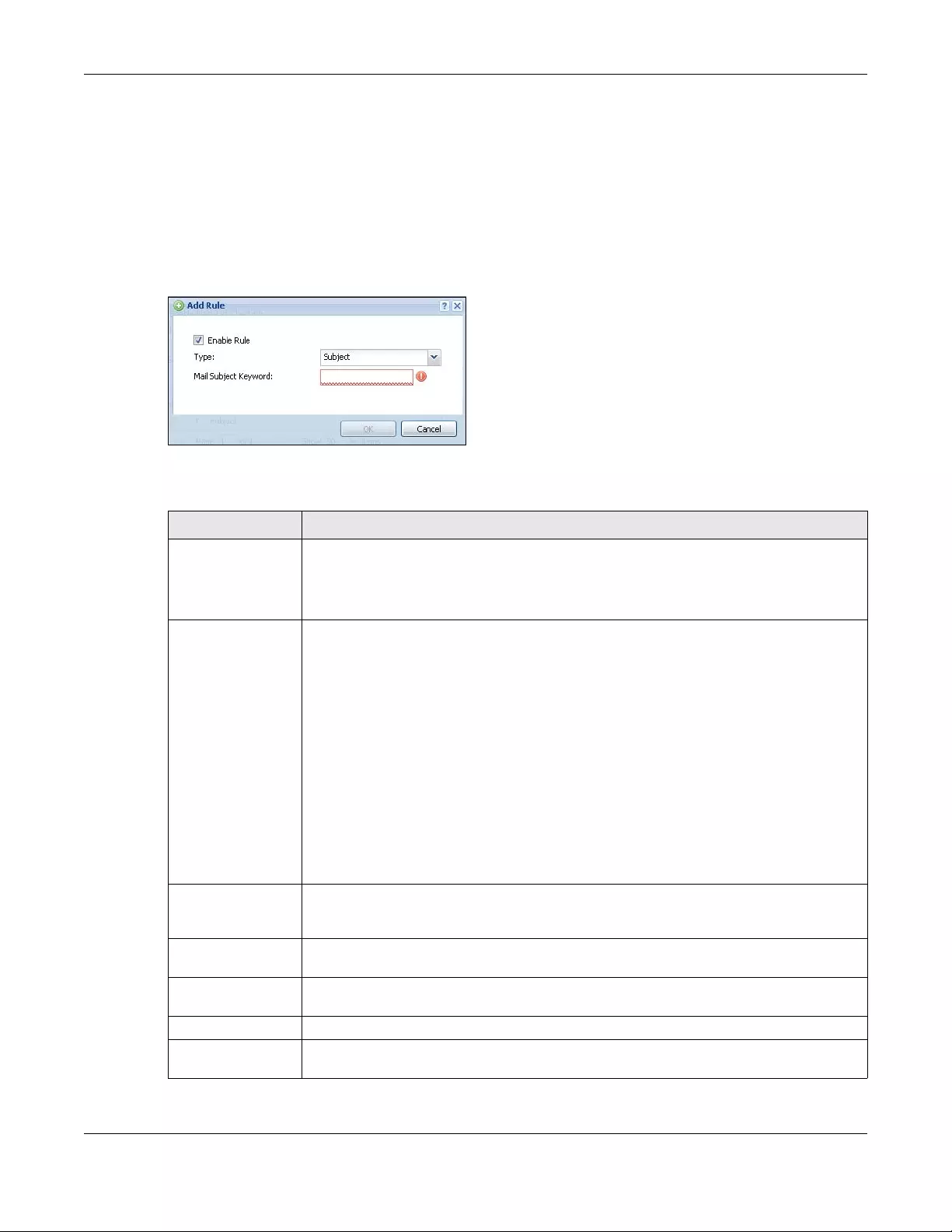
Chapter 40 Anti-Spam
USG/ZyWALL User’s Guide
699
40.5.1 The Anti-Spam Black or White List Add/Edit Screen
In the anti-spam Black List or White List screen, click the Add icon or an Edit icon to display the following
screen.
Use this screen to configure an anti-spam black list entry to identify spam e-mail. You can create entries
based on specific subject text, or the sender’s or relay’s IP address or e-mail address. You can also
create entries that check for particular header fields and values.
Figure 489 Configuration > UTM Profile > Anti-Spam > Black/White List > Black List (or White List) > Add
The following table describes the labels in this screen.
Table 270 Configuration > UTM Profile > Anti-Spam > Black/White List > Black/White List > Add
LABEL DESCRIPTION
Enable Rule Select this to have the Zyxel Device use this entry as part of the black or white list.
To actually use the entry, you must also turn on the use of the list in the corresponding list
screen, enable the anti-spam feature in the anti-spam general screen, and configure an
anti-spam policy to use the list.
Type Use this field to base the entry on the e-mail’s subject, source or relay IP address, source e-
mail address, or header.
Select Subject to have the Zyxel Device check e-mail for specific content in the subject line.
Select IP Address to have the Zyxel Device check e-mail for a specific source or relay IP
address.
Select IPv6 Address to have the Zyxel Device check e-mail for a specific source or relay IPv6
address.
Select E-Mail Address to have the Zyxel Device check e-mail for a specific source e-mail
address or domain name.
Select Mail Header to have the Zyxel Device check e-mail for specific header fields and
values. Configure black list header entries to check for e-mail from bulk mail programs or
with content commonly used in spam. Configure white list header entries to allow certain
header values that identify the e-mail as being from a trusted source.
Mail Subject
Keyword
This field displays when you select the Subject type. Enter up to 63 ASCII characters of text to
check for in e-mail headers. Spaces are not allowed, although you could substitute a
question mark (?). See Section 40.5.2 on page 700 for more details.
Sender or Mail Relay
IP Address
This field displays when you select the IP Address type. Enter an IP address in dotted decimal
notation.
Sender or Mail Relay
IPv6 Address
This field displays when you select the IPv6 Address type. Enter an IPv6 address with prefix.
Netmask This field displays when you select the IP type. Enter the subnet mask here, if applicable.
Sender E-Mail
Address
This field displays when you select the E-Mail type. Enter a keyword (up to 63 ASCII
characters). See Section 40.5.2 on page 700 for more details.
Chapter 40 Anti-Spam
USG/ZyWALL User’s Guide
700
40.5.2 Regular Expressions in Black or White List Entries
The following applies for a black or white list entry based on an e-mail subject, e-mail address, or e-mail
header value.
• Use a question mark (?) to let a single character vary. For example, use “a?c” (without the quotation
marks) to specify abc, acc and so on.
• You can also use a wildcard (*). For example, if you configure *def.com, any e-mail address that ends
in def.com matches. So “mail.def.com” matches.
• The wildcard can be anywhere in the text string and you can use more than one wildcard. You
cannot use two wildcards side by side, there must be other characters between them.
• The Zyxel Device checks the first header with the name you specified in the entry. So if the e-mail has
more than one “Received” header, the Zyxel Device checks the first one.
40.6 The Anti-Spam White List Screen
Click Configuration > UTM Profile > Anti-Spam > Black/White List and then the White List tab to display the
Anti-Spam White List screen.
Configure the white list to identify legitimate e-mail. You can create white list entries based on the
sender’s or relay’s IP address or e-mail address. You can also create entries that check for particular
header fields and values or specific subject text.
Mail Header Field
Name
This field displays when you select the Mail Header type.
Type the name part of an e-mail header (the part that comes before the colon). Use up to
63 ASCII characters.
For example, if you want the entry to check the “Received:” header for a specific mail
server’s domain, enter “Received” here.
Field Value
Keyword
This field displays when you select the Mail Header type.
Type the value part of an e-mail header (the part that comes after the colon). Use up to 63
ASCII characters.
For example, if you want the entry to check the “Received:” header for a specific mail
server’s domain, enter the mail server’s domain here.
See Section 40.5.2 on page 700 for more details.
OK Click OK to save your changes.
Cancel Click Cancel to exit this screen without saving your changes.
Table 270 Configuration > UTM Profile > Anti-Spam > Black/White List > Black/White List > Add
LABEL DESCRIPTION
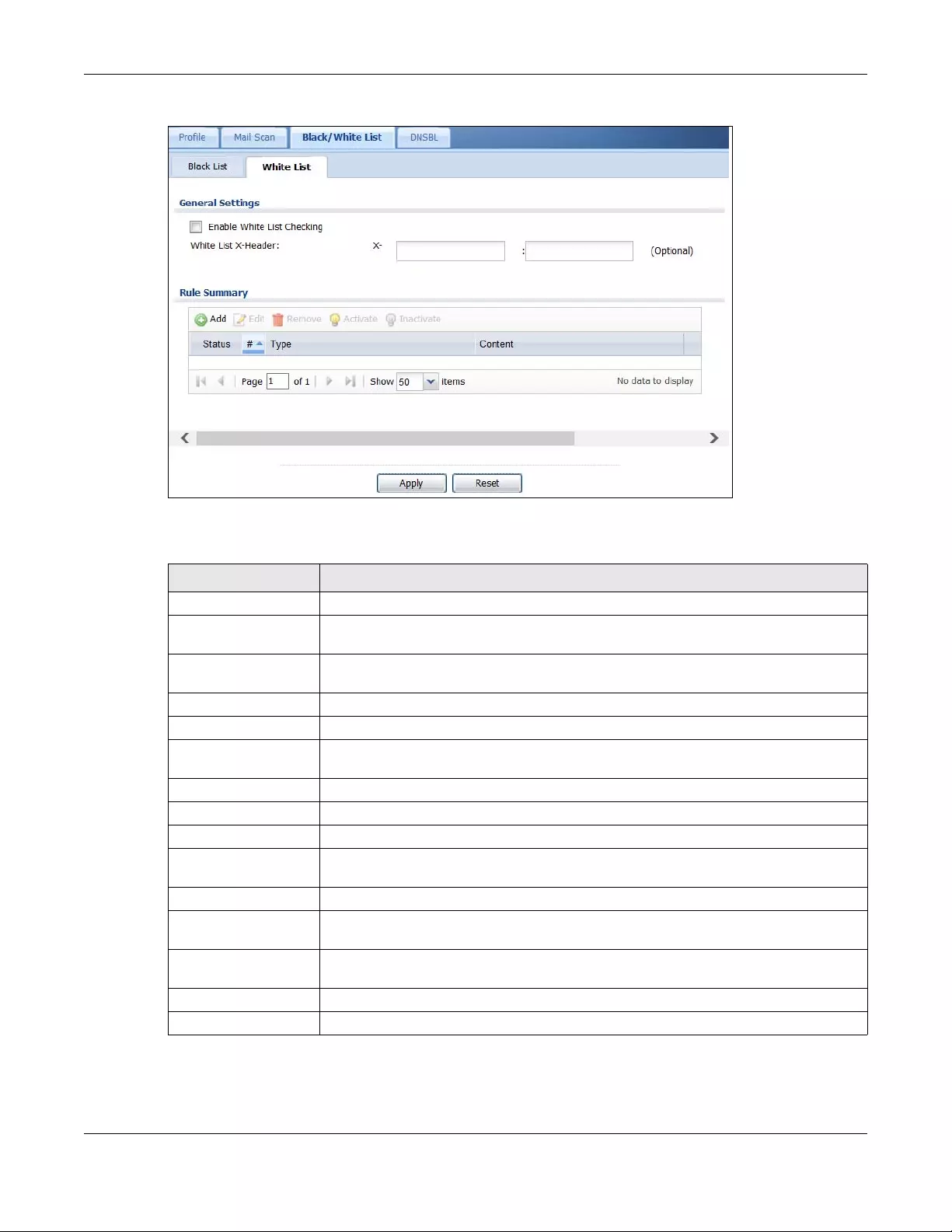
Chapter 40 Anti-Spam
USG/ZyWALL User’s Guide
701
Figure 490 Configuration > UTM Profile > Anti-Spam > Black/White List > White List
The following table describes the labels in this screen.
Table 271 Configuration > UTM Profile > Anti-Spam > Black/White List > White List
LABEL DESCRIPTION
General Settings
Enable White List
Checking
Select this check box to have the Zyxel Device forward e-mail that matches (an active)
white list entry without doing any more anti-spam checking on that individual e-mail.
White List X-Header Specify the name and value for the X-Header to be added to e-mails that match the
Zyxel Device’s spam white list.
Rule Summary
Add Click this to create a new entry. See Section 40.5.1 on page 699 for details.
Edit Select an entry and click this to be able to modify it. See Section 40.5.1 on page 699 for
details.
Remove Select an entry and click this to delete it.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Status The activate (light bulb) icon is lit when the entry is active and dimmed when the entry is
inactive.
#This is the entry’s index number in the list.
Type This field displays whether the entry is based on the e-mail’s subject, source or relay IP
address, source e-mail address, or a header.
Content This field displays the subject content, source or relay IP address, source e-mail address, or
header value for which the entry checks.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
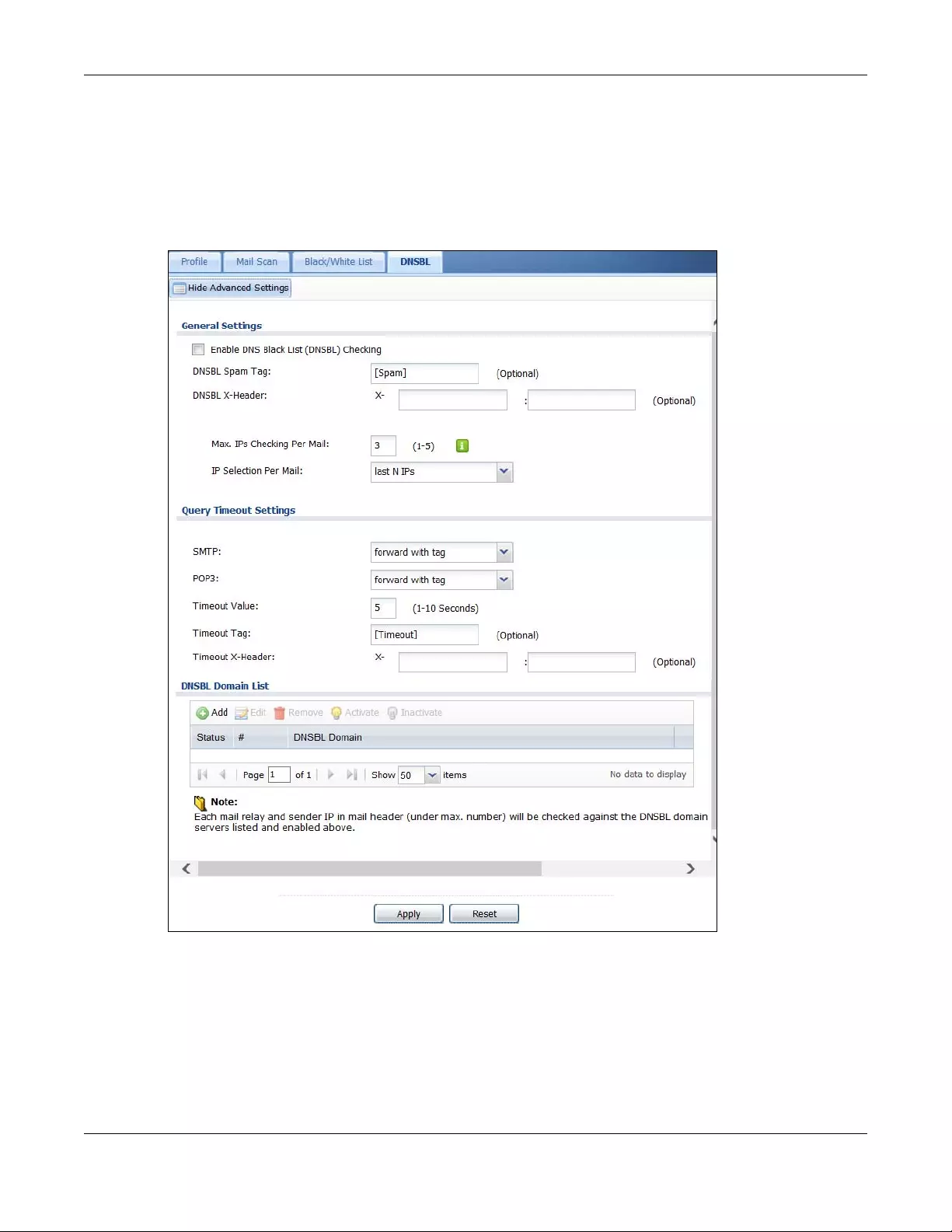
Chapter 40 Anti-Spam
USG/ZyWALL User’s Guide
702
40.7 The DNSBL Screen
Click Configuration > UTM Profile > Anti-Spam > DNSBL to display the anti-spam DNSBL screen. Use this
screen to configure the Zyxel Device to check the sender and relay IP addresses in e-mail headers
against DNS (Domain Name Service)-based spam Black Lists (DNSBLs).
Figure 491 Configuration > UTM Profile > Anti-Spam > DNSBL
Chapter 40 Anti-Spam
USG/ZyWALL User’s Guide
703
The following table describes the labels in this screen.
Table 272 Configuration > UTM Profile > Anti-Spam > DNSBL
LABEL DESCRIPTION
Show Advanced
Settings / Hide
Advanced Settings
Click this button to display a greater or lesser number of configuration fields.
Enable DNS Black List
(DNSBL) Checking
Select this to have the Zyxel Device check the sender and relay IP addresses in e-mail
headers against the DNSBL servers maintained by the DNSBL domains listed in the Zyxel
Device.
DNSBL Spam Tag Enter a message or label (up to 15 ASCII characters) to add to the beginning of the mail
subject of e-mails that have a sender or relay IP address in the header that matches a
black list maintained by one of the DNSBL domains listed in the Zyxel Device.
This tag is only added if the anti-spam policy is configured to forward spam mail with a
spam tag.
DSBNL X-Header Specify the name and value for the X-Header to be added to e-mails that have a sender
or relay IP address in the header that matches a black list maintained by one of the
DNSBL domains listed in the Zyxel Device.
Max. IPs Checking Per
Mail
Set the maximum number of sender and relay server IP addresses in the mail header to
check against the DNSBL domain servers.
IP Selection Per Mail Select first N IPs to have the Zyxel Device start checking from the first IP address in the mail
header. This is the IP of the sender or the first server that forwarded the mail.
Select last N IPs to have the Zyxel Device start checking from the last IP address in the
mail header. This is the IP of the last server that forwarded the mail.
Query Timeout Setting
SMTP Select how the Zyxel Device is to handle SMTP mail (mail going to an e-mail server) if the
queries to the DNSBL domains time out.
Select drop to discard SMTP mail.
Select forward to allow SMTP mail to go through.
Select forward with tag to add a DNSBL timeout tag to the mail subject of an SMTP mail
and send it.
POP3 Select how the Zyxel Device is to handle POP3 mail (mail coming to an e-mail client) if the
queries to the DNSBL domains time out.
Select forward to allow POP3 mail to go through.
Select forward with tag to add a DNSBL timeout tag to the mail subject of an POP3 mail
and send it.
Timeout Value Set how long the Zyxel Device waits for a reply from the DNSBL domains listed below. If
there is no reply before this time period expires, the Zyxel Device takes the action defined
in the relevant Actions when Query Timeout field.
Timeout Tag Enter a message or label (up to 15 ASCII characters) to add to the mail subject of e-mails
that the Zyxel Device forwards if queries to the DNSBL domains time out.
Timeout X-Header Specify the name and value for the X-Header to be added to e-mails that the Zyxel
Device forwards if queries to the DNSBL domains time out.
DNSBL Domain List
Add Click this to create a new entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Chapter 40 Anti-Spam
USG/ZyWALL User’s Guide
704
40.8 Anti-Spam Technical Reference
Here is more detailed anti-spam information.
DNSBL
• The Zyxel Device checks only public sender and relay IP addresses, it does not check private IP
addresses.
• The Zyxel Device sends a separate query (DNS lookup) for each sender or relay IP address in the e-
mail’s header to each of the Zyxel Device’s DNSBL domains at the same time.
• The DNSBL servers send replies as to whether or not each IP address matches an entry in their list. Each
IP address has a separate reply.
• As long as the replies are indicating the IP addresses do not match entries on the DNSBL lists, the Zyxel
Device waits until it receives at least one reply for each IP address.
• If the Zyxel Device receives a DNSBL reply that one of the IP addresses is in the DNSBL list, the Zyxel
Device immediately classifies the e-mail as spam and takes the anti-spam policy’s configured action
for spam. The Zyxel Device does not wait for any more DNSBL replies.
• If the Zyxel Device receives at least one non-spam reply for each of an e-mail’s routing IP addresses,
the Zyxel Device immediately classifies the e-mail as legitimate and forwards it.
• Any further DNSBL replies that come after the Zyxel Device classifies an e-mail as spam or legitimate
have no effect.
• The Zyxel Device records DNSBL responses for IP addresses in a cache for up to 72 hours. The Zyxel
Device checks an e-mail’s sender and relay IP addresses against the cache first and only sends DNSBL
queries for IP addresses that are not in the cache.
Here is an example of an e-mail classified as spam based on DNSBL replies.
Status The activate (light bulb) icon is lit when the entry is active and dimmed when the entry is
inactive.
#This is the entry’s index number in the list.
DNSBL Domain This is the name of a domain that maintains DNSBL servers. Enter the domain that is
maintaining a DNSBL.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 272 Configuration > UTM Profile > Anti-Spam > DNSBL (continued)
LABEL DESCRIPTION
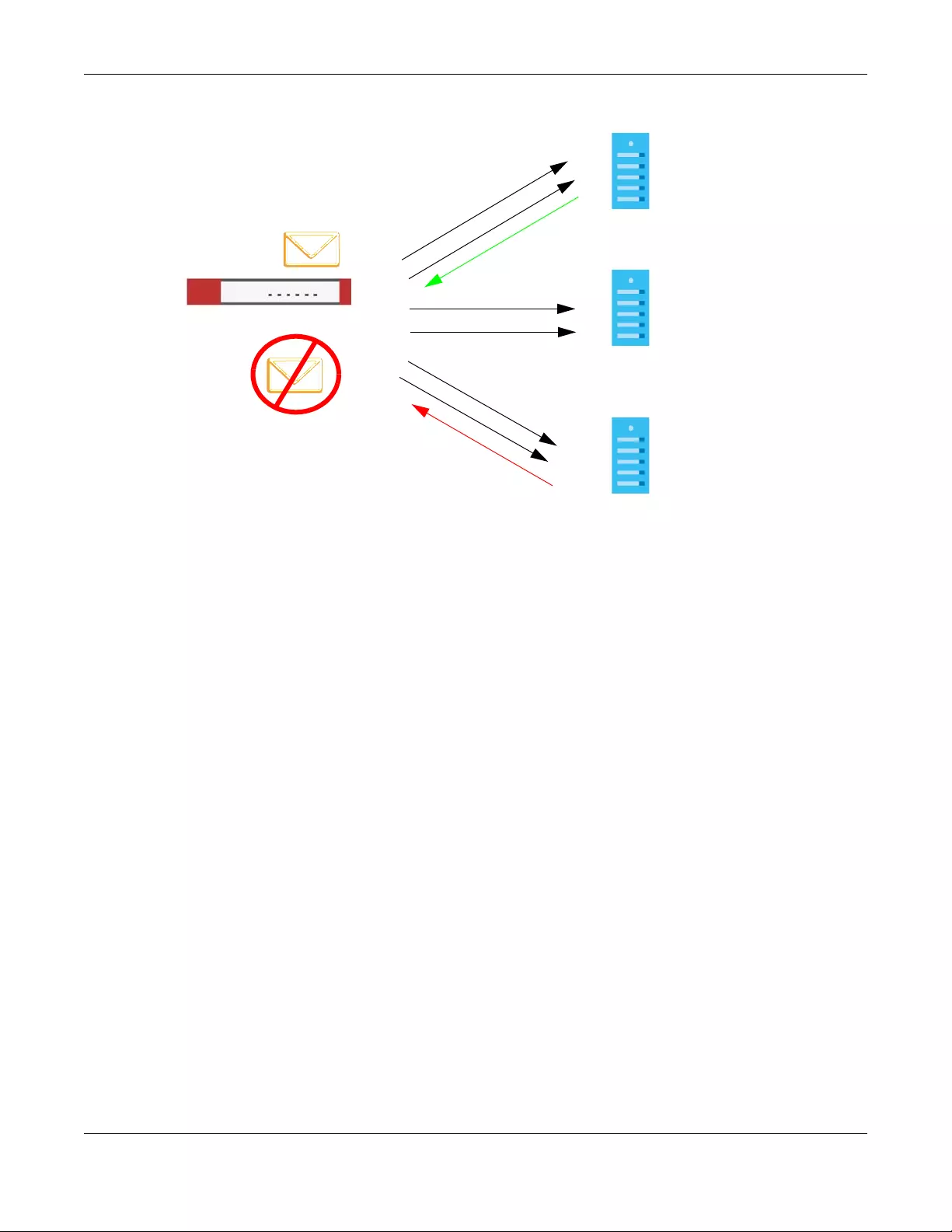
Chapter 40 Anti-Spam
USG/ZyWALL User’s Guide
705
Figure 492 DNSBL Spam Detection Example
1The Zyxel Device receives an e-mail that was sent from IP address a.a.a.a and relayed by an e-mail
server at IP address b.b.b.b. The Zyxel Device sends a separate query to each of its DNSBL domains for IP
address a.a.a.a. The Zyxel Device sends another separate query to each of its DNSBL domains for IP
address b.b.b.b.
2DNSBL A replies that IP address a.a.a.a does not match any entries in its list (not spam).
3DNSBL C replies that IP address b.b.b.b matches an entry in its list.
4The Zyxel Device immediately classifies the e-mail as spam and takes the action for spam that you
defined in the anti-spam policy. In this example it was an SMTP mail and the defined action was to drop
the mail. The Zyxel Device does not wait for any more DNSBL replies.
Here is an example of an e-mail classified as legitimate based on DNSBL replies.
DNSBL A
DNSBL B
DNSBL C
IPs: a.a.a.a
b.b.b.b
1
2
a.a.a.a Not spam
3
4
a.a.a.a?
b.b.b.b?
a.a.a.a?
b.b.b.b?
a.a.a.a?
b.b.b.b?
b.b.b.b Spam
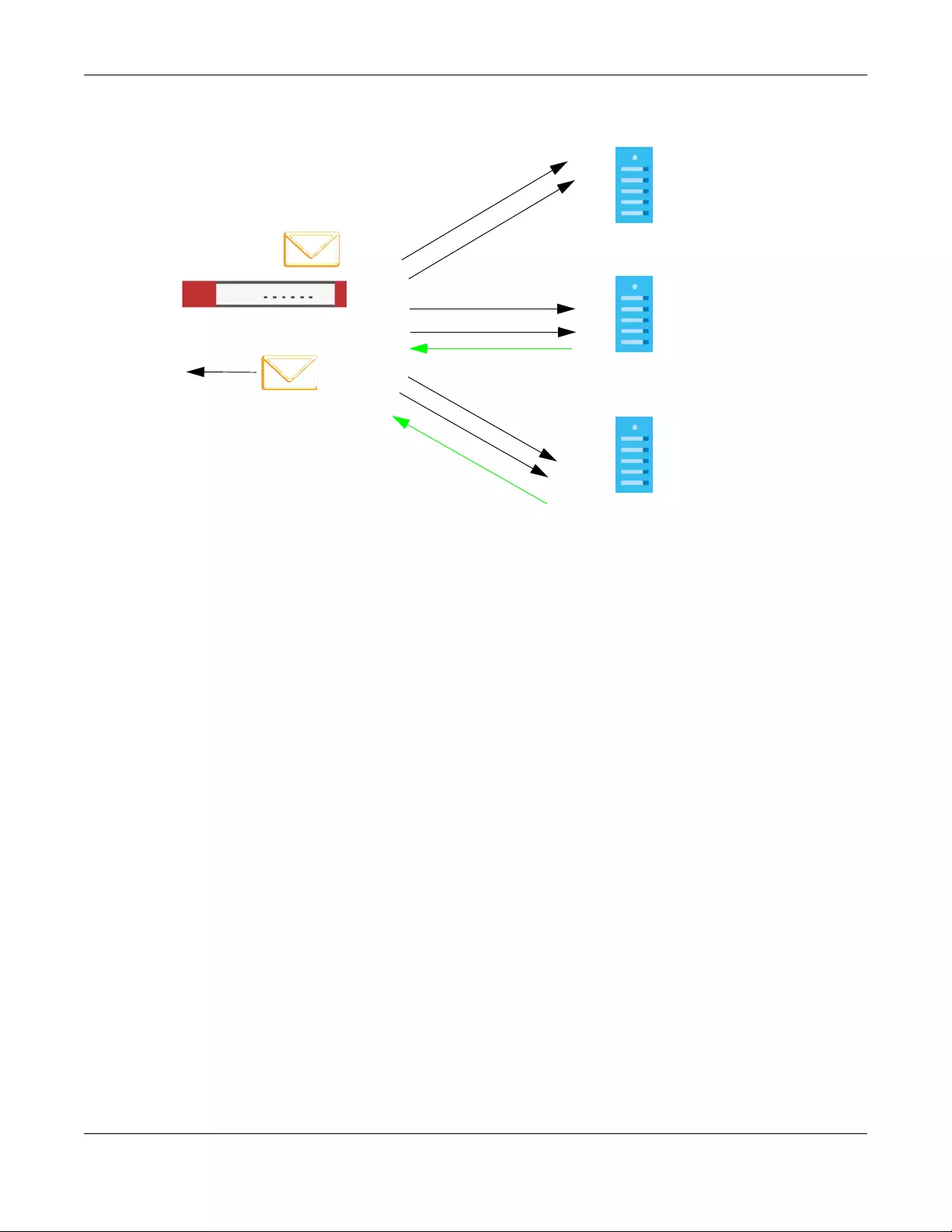
Chapter 40 Anti-Spam
USG/ZyWALL User’s Guide
706
Figure 493 DNSBL Legitimate E-mail Detection Example
1The Zyxel Device receives an e-mail that was sent from IP address c.c.c.c and relayed by an e-mail
server at IP address d.d.d.d. The Zyxel Device sends a separate query to each of its DNSBL domains for IP
address c.c.c.c. The Zyxel Device sends another separate query to each of its DNSBL domains for IP
address d.d.d.d.
2DNSBL B replies that IP address d.d.d.d does not match any entries in its list (not spam).
3DNSBL C replies that IP address c.c.c.c does not match any entries in its list (not spam).
4Now that the Zyxel Device has received at least one non-spam reply for each of the e-mail’s routing IP
addresses, the Zyxel Device immediately classifies the e-mail as legitimate and forwards it. The Zyxel
Device does not wait for any more DNSBL replies.
If the Zyxel Device receives conflicting DNSBL replies for an e-mail routing IP address, the Zyxel Device
classifies the e-mail as spam. Here is an example.
DNSBL A
DNSBL B
DNSBL C
IPs: c.c.c.c
d.d.d.d
1
c.c.c.c Not spam
2
4
c.c.c.c?
d.d.d.d?
c.c.c.c?
d.d.d.d?
c.c.c.c?
d.d.d.d?
d.d.d.d Not spam
3
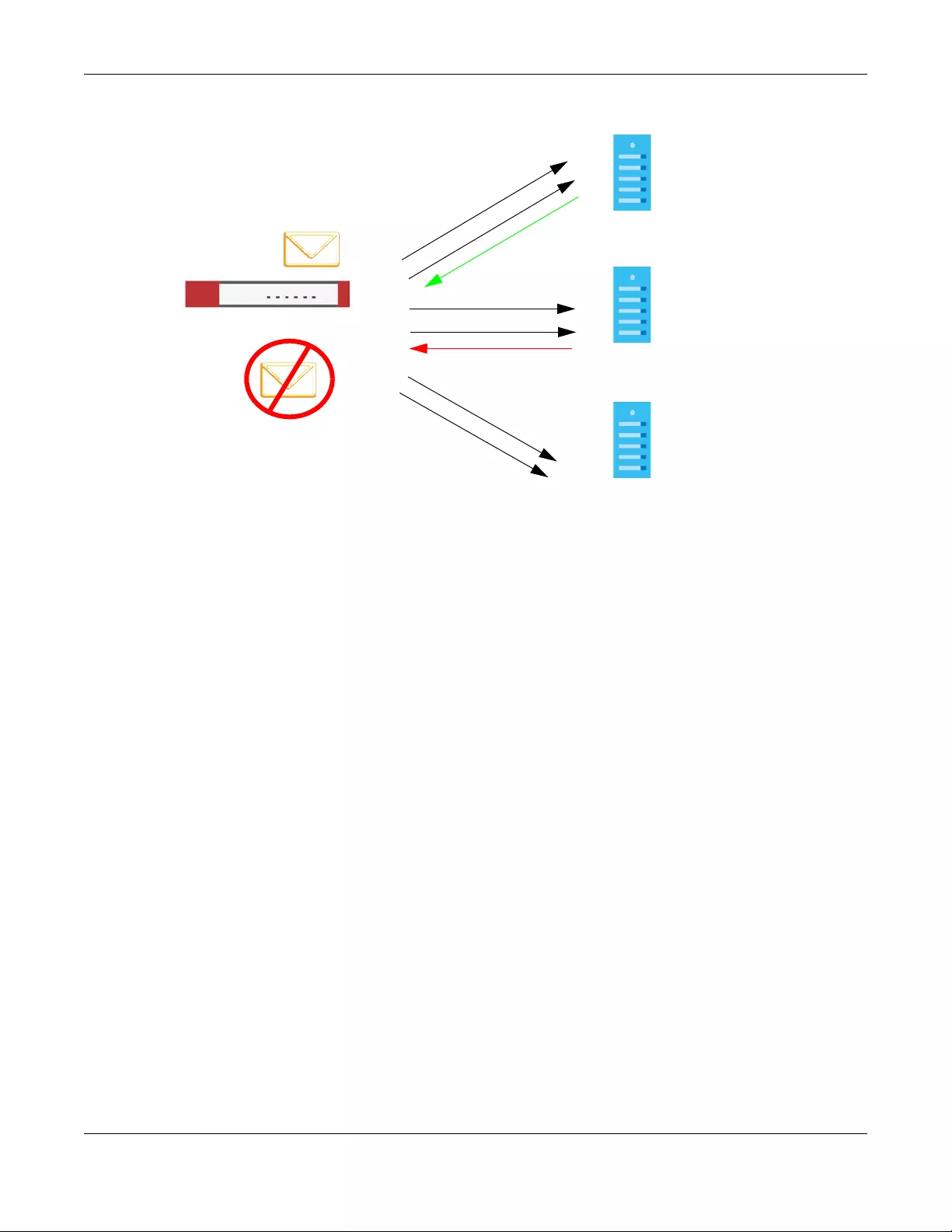
Chapter 40 Anti-Spam
USG/ZyWALL User’s Guide
707
Figure 494 Conflicting DNSBL Replies Example
1The Zyxel Device receives an e-mail that was sent from IP address a.b.c.d and relayed by an e-mail
server at IP address w.x.y.z. The Zyxel Device sends a separate query to each of its DNSBL domains for IP
address a.b.c.d. The Zyxel Device sends another separate query to each of its DNSBL domains for IP
address w.x.y.z.
2DNSBL A replies that IP address a.b.c.d does not match any entries in its list (not spam).
3While waiting for a DNSBL reply about IP address w.x.y.z, the Zyxel Device receives a reply from DNSBL B
saying IP address a.b.c.d is in its list.
4The Zyxel Device immediately classifies the e-mail as spam and takes the action for spam that you
defined in the anti-spam policy. In this example it was an SMTP mail and the defined action was to drop
the mail. The Zyxel Device does not wait for any more DNSBL replies.
DNSBL A
DNSBL B
DNSBL C
IPs: a.b.c.d
w.x.y.z
1
2
a.b.c.d Not spam
3
4
a.b.c.d?
w.x.y.z?
a.b.c.d?
w.x.y.z?
a.b.c.d?
w.x.y.z?
a.b.c.d Spam!
USG/ZyWALL User’s Guide
708
CHAPTER 41
SSL Inspection
41.1 SSL Inspection Overview
Secure Socket Layer (SSL) traffic, such as https://www.google.com/HTTPS, FTPs, POP3s, SMTPs, etc. is
encrypted, and cannot be inspected using Unified Threat Management (UTM) profiles such as App
Patrol, Content Filter, Intrusion, Detection and Prevention (IDP), or Anti-Virus. The Zyxel Device uses SSL
Inspection to decrypt SSL traffic, sends it to the UTM engines for inspection, then encrypts traffic that
passes inspection and forwards it to the destination server, such as Google.
An example process is shown in the following figure. User U sends a HTTPS request (SSL) to destination
server D, via the Zyxel Device, Z. The traffic matches an SSL Inspection profile in a security policy, so the
Zyxel Device decrypts the traffic using SSL Inspection. The decrypted traffic is then inspected by the UTM
profiles in the same security profile that matched the SSL Inspection profile. If all is OK, then the Zyxel
Device re-encrypts the traffic using SSL Inspection and forwards it to the destination server D. SSL traffic
could be in the opposite direction for other examples.
Figure 495 SSL Inspection Overview
Note: Anti-Spam cannot be applied to traffic decrypted by SSL Inspection.
41.1.1 What You Can Do in this Chapter
• Use the UTM Profile > SSL Inspection > Profile screen (Section 41.2 on page 709) to view SSL Inspection
profiles. Click the Add or Edit icon in this screen to configure the CA certificate, action and log in an
SSL Inspection profile.
• Use the UTM Profile > SSL Inspection > Exclude List screens (Section 41.3 on page 713) to create a
whitelist of destination servers to which traffic is passed through uninspected.
• Use the UTM Profile > SSL Inspection > Certificate Update screen (Section 41.4 on page 714) to update
the latest certificates of servers using SSL connections to the Zyxel Device network.
HTTPS SSL
Inspection
Decrypt
UTM
AP
CF
IDP
AV
SSL
Inspection
Encrypt

Chapter 41 SSL Inspection
USG/ZyWALL User’s Guide
709
41.1.2 What You Need To Know
• Supported Cipher Suite
• RC4 (Rivest Cipher 4)
• DES (Data Encryption Standard)
•3DES
• AES (Advanced Encryption Standard)
• SSLv3/TLS1.0 (Transport Layer Security) Support
• SSLv3/TLS1.0 is currently supported with option to pass or block SSLv2 traffic
• Traffic using TLS1.1 (Transport Layer Security) or TLS1.2 is downgraded to TLS1.0 for SSL Inspection
• No Compression Support Now
• No Client Authentication Request Support Now
•Finding Out More
•See Configuration > Object > Certificate > My Certificates for information on creating certificates
on the Zyxel Device.
•See Monitor > UTM Statistics > SSL In spection to get usage data and easily add a destination server
to the whitelist of exclusion servers.
•See Configuration > Security Policy > Policy Control > Policy to bind an SSL Inspection profile to a
traffic flow(s).
41.1.3 Before You Begin
• If you don’t want to use the default Zyxel Device certificate, then create a new certificate in Object >
Certificate > My Certificates.
• Decide what destination servers to which traffic is sent directly without inspection. This may be a
matter of privacy and legality regarding inspecting an individual’s encrypted session, such as
financial websites. This may vary by locale.
41.2 The SSL Inspection Profile Screen
An SSL Inspection profile is a template with pre-configured certificate, action and log.
Click Configuration > UTM Profile > SSL Inspection > Profile to open this screen.
Figure 496 Configuration > UTM Profile > SSL Inspection > Profile
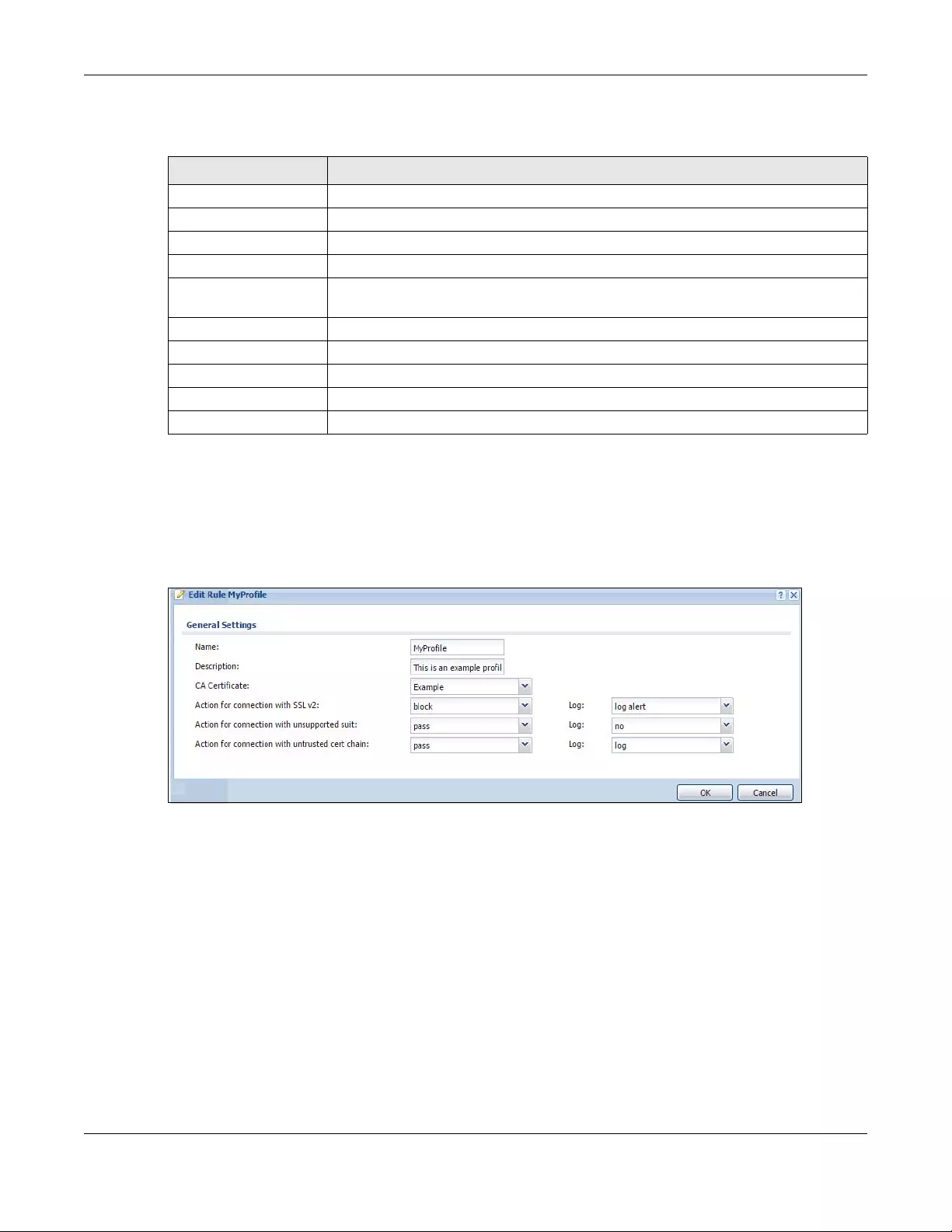
Chapter 41 SSL Inspection
USG/ZyWALL User’s Guide
710
The following table describes the fields in this screen.
41.2.1 Add / Edit SSL Inspection Profiles
Click Configuration > UTM Profile > SSL Inspection > Profile > Add to create a new profile or select an
existing profile and click Edit to change its settings.
Figure 497 Configuration > UTM Profile > SSL Inspection > Profile > Add / Edit
Table 273 Configuration > UTM Profile > SSL Inspection > Profile
LABEL DESCRIPTION
Profile Management
Add Click Add to create a new profile.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
Object Reference Select an entry and click Object References to open a screen that shows which settings
use the entry. Click Refresh to update information on this screen.
#This is the entry’s index number in the list.
Name This displays the name of the profile.
Description This displays the description of the profile.
CA Certificate This displays the CA certificate being used in this profile.
Reference This displays the number of times an object reference is used in a profile.
Chapter 41 SSL Inspection
USG/ZyWALL User’s Guide
711
The following table describes the fields in this screen.
Table 274 Configuration > UTM Profile > SSL Inspection > Profile > Add / Edit
LABEL DESCRIPTION
Name This is the name of the profile. You may use 1-31 alphanumeric characters, underscores(_), or
dashes (-), but the first character cannot be a number. This value is case-sensitive. These are
valid, unique profile names:
• MyProfile
• mYProfile
• Mymy12_3-4
These are invalid profile names:
• 1mYProfile
• My Profile
• MyProfile?
• Whatalongprofilename123456789012
Description Enter additional information about this SSL Inspection entry. You can enter up to 60 characters
("0-9", "a-z", "A-Z", "-" and "_").
CA Certificate This contains the default certificate and the certificates created in Object > Certificate > My
Certificates. Choose the certificate for this profile.
Severity Level Select a severity level and these use the icons to enable/disable and configure logs and
actions for all signatures of that level.
Action for
connection with
SSL v2
SSL Inspection supports SSLv3 and TLS1.0. Select to pass or block SSLv2 traffic that matches
traffic bound to this policy here.
Log These are the log options for SSLv2 traffic that matches traffic bound to this policy:
•no: Select this option to have the Zyxel Device create no log for SSLv2 traffic that matches
traffic bound to this policy.
•log: Select this option to have the Zyxel Device create a log for SSLv2 traffic that matches
traffic bound to this policy.
•log alert: An alert is an e-mailed log for more serious events that may need more immediate
attention. They also appear in red in the Monitor > Log screen. Select this option to have the
Zyxel Device send an alert for SSLv2 traffic that matches traffic bound to this policy.
Action for
Connection with
unsupported suit
SSL Inspection supports these cipher suites:
•RC4
•DES
•3DES
•AES
Select to pass or block unsupported traffic (such as other cipher suites, compressed traffic,
client authentication requests, and so on) that matches traffic bound to this policy here.
Log These are the log options for unsupported traffic that matches traffic bound to this policy:
•no: Select this option to have the Zyxel Device create no log for unsupported traffic that
matches traffic bound to this policy.
•log: Select this option to have the Zyxel Device create a log for unsupported traffic that
matches traffic bound to this policy
•log alert: An alert is an e-mailed log for more serious events that may need more immediate
attention. They also appear in red in the Monitor > Log screen. Select this option to have the
Zyxel Device send an alert for unsupported traffic that matches traffic bound to this policy.
Excepted
Signatures
Use the icons to enable/disable and configure logs and actions for individual signatures that
are different to the general settings configured for the severity level to which the signatures
belong. Signatures configured in Query View will appear in Group View.
Add Click this to configure settings to a signature that are different to the severity level to which it
belongs.
Chapter 41 SSL Inspection
USG/ZyWALL User’s Guide
712
Remove Select an existing signature exception and then click this to delete the exception.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Log To edit an item’s log option, select it and use the Log icon. These are the log options:
no: Select this option on an individual signature or a complete service group to have the Zyxel
Device create no log when a packet matches a signature(s).
log: Select this option on an individual signature or a complete service group to have the Zyxel
Device create a log when a packet matches a signature(s).
log alert: An alert is an e-mailed log for more serious events that may need more immediate
attention. Select this option to have the Zyxel Device send an alert when a packet matches a
signature(s).
Action To edit what action the Zyxel Device takes when a packet matches a signature, select the
signature and use the Action icon.
none: Select this action on an individual signature or a complete service group to have the
Zyxel Device take no action when a packet matches the signature(s).
drop: Select this action on an individual signature or a complete service group to have the
Zyxel Device silently drop a packet that matches the signature(s). Neither sender nor receiver
are notified.
reject-sender: Select this action on an individual signature or a complete service group to have
the Zyxel Device send a reset to the sender when a packet matches the signature. If it is a TCP
attack packet, the Zyxel Device will send a packet with a ‘RST’ flag. If it is an ICMP or UDP
attack packet, the Zyxel Device will send an ICMP unreachable packet.
reject-receiver: Select this action on an individual signature or a complete service group to
have the Zyxel Device send a reset to the receiver when a packet matches the signature. If it is
a TCP attack packet, the Zyxel Device will send a packet with an a ‘RST’ flag. If it is an ICMP or
UDP attack packet, the Zyxel Device will do nothing.
reject-both: Select this action on an individual signature or a complete service group to have
the Zyxel Device send a reset to both the sender and receiver when a packet matches the
signature. If it is a TCP attack packet, the Zyxel Device will send a packet with a ‘RST’ flag to the
receiver and sender. If it is an ICMP or UDP attack packet, the Zyxel Device will send an ICMP
unreachable packet.
#This is the entry’s index number in the list.
Status The activate (light bulb) icon is lit when the entry is active and dimmed when the entry is
inactive.
SID Type the exact signature ID (identification) number that uniquely identifies a Zyxel Device IDP
signature.
Log These are the log options. To edit this, select an item and use the Log icon.
Action This is the action the Zyxel Device should take when a packet matches a signature here. To edit
this, select an item and use the Action icon.
OK Click OK to save your settings to the Zyxel Device, and return to the profile summary page.
Cancel Click Cancel to return to the profile summary page without saving any changes.
Table 274 Configuration > UTM Profile > SSL Inspection > Profile > Add / Edit (continued)
LABEL DESCRIPTION
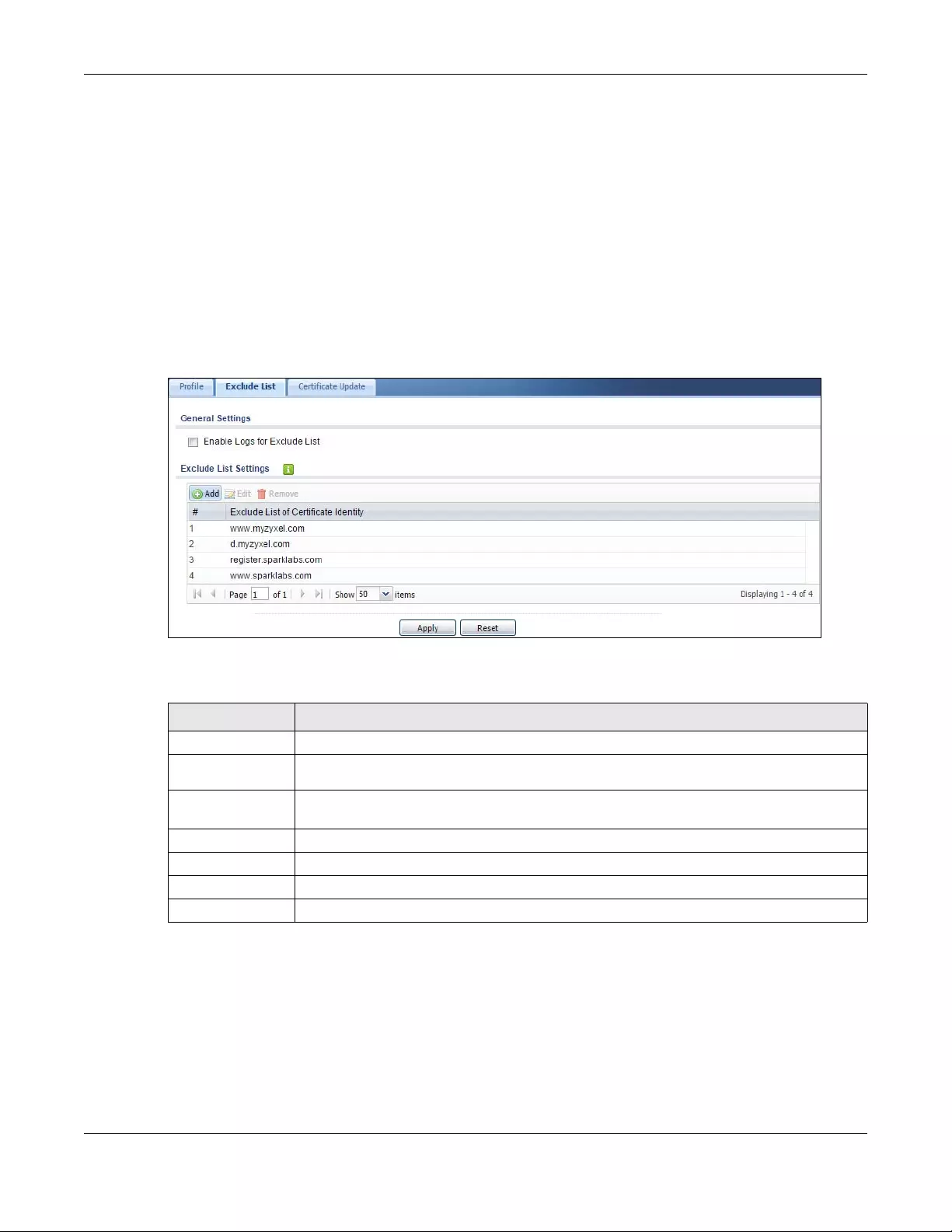
Chapter 41 SSL Inspection
USG/ZyWALL User’s Guide
713
41.3 Exclude List Screen
There may be privacy and legality issues regarding inspecting a user's encrypted session. The legal issues
may vary by locale, so it's important to check with your legal department to make sure that it’s OK to
intercept SSL traffic from your Zyxel Device users.
To ensure individual privacy and meet legal requirements, you can configure an exclusion list to exclude
matching sessions to destination servers. This traffic is not intercepted and is passed through
uninspected.
Click Configuration > UTM Profile > SSL Inspection > Exclude List to display the following screen. Use Add
to put a new item in the list or Edit to change an existing one or Remove to delete an existing entry.
Figure 498 Configuration > UTM Profile > SSL Inspection > Exclude List (> Add/Edit)
The following table describes the fields in this screen.
Table 275 Configuration > UTM Profile > SSL Inspection > Exclude List
LABEL DESCRIPTION
General Settings
Enable Logs for
Exclude List Click this to create a log for traffic that bypasses SSL Inspection.
Exclude List
Settings
Use this part of the screen to create, edit, or delete items in the SSL Inspection exclusion list.
Add Click this to create a new entry.
Edit Select an entry and click this to be able to modify it.
Remove Select an entry and click this to delete it.
#This is the entry’s index number in the list.
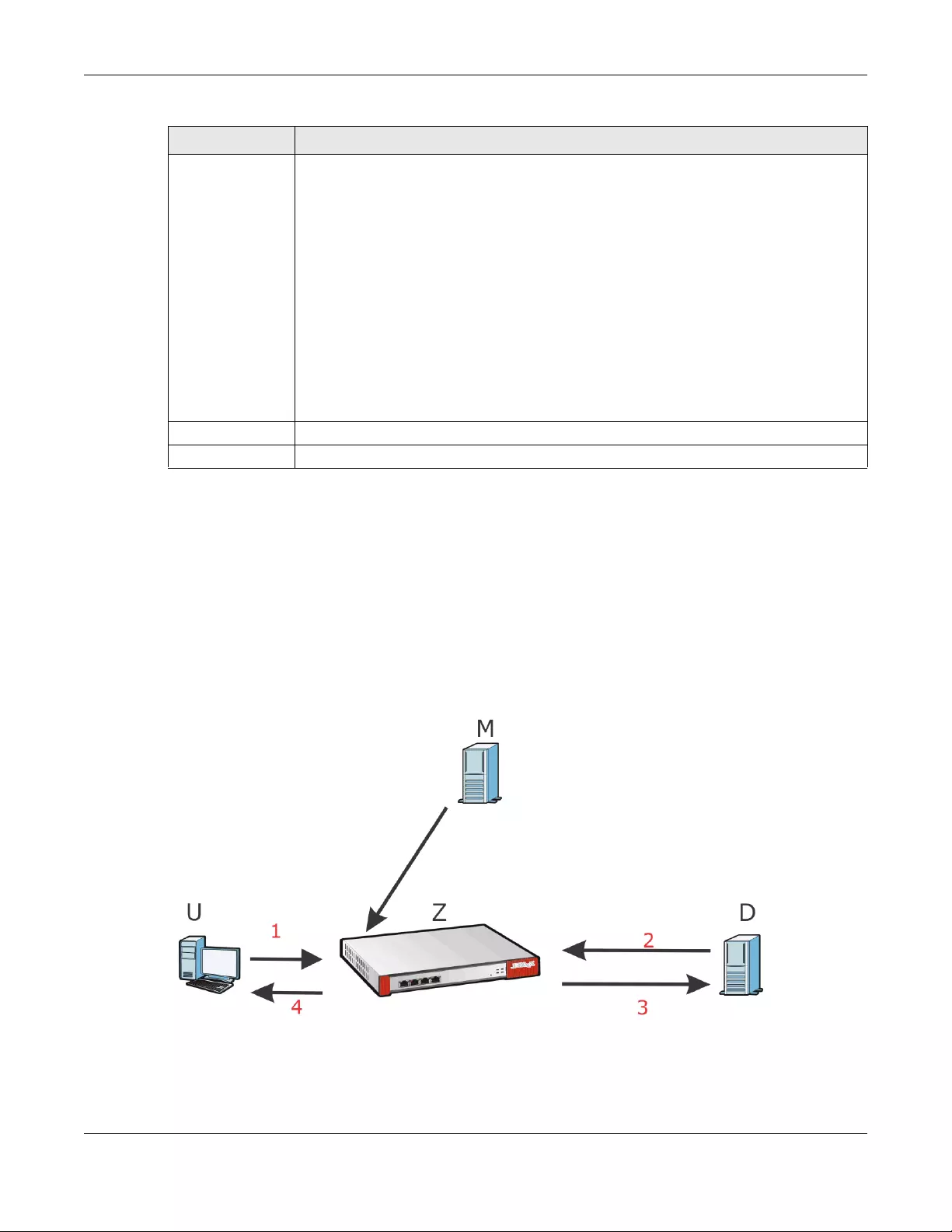
Chapter 41 SSL Inspection
USG/ZyWALL User’s Guide
714
41.4 Certificate Update Screen
Use this screen to update the latest certificates of servers using SSL connections to the Zyxel Device
network. User U sends an SSL request to destination server D (1), via the Zyxel Device, Z. D replies (2); Z
intercepts the response from D and checks if the certificate has been previously signed. Z then replies to
D (3) and also to U (4). D’s latest certificate is stored at myZyxel.com (M) along with other server
certificates and can be downloaded to the Zyxel Device.
Figure 499 SSL Inspection Certificate Update Overview
Click Configuration > UTM Profile > SSL Inspection > Certificate Update to display the following screen.
Exclude List of
Certificate
Identity
SSL traffic to a server to be excluded from SSL Inspection is identified by its certificate. Identify
the certificate in one of the following ways:
• The Common Name (CN) of the certificate. The common name of the certificate can be
created in the Object > Certificate > My Certificates screen.
• Type an IPv4 or IPv6 address. For example, type 192.168.1.35, or 2001:7300:3500::1
• Type an IPv4/IPv6 in CIDR notation. For example, type 192.168.1.1/24, or 2001:7300:3500::1/
64
• Type an IPv4/IPv6 address range. For example, type 192.168.1.1-192.168.1.35, or
2001:7300:3500::1-2001:7300:3500::35
• Type an email address. For example, type abc@zyxel.com.tw
• Type a DNS name or a common name (wildcard char: '*', escape char: '\'). Use up to 127
case-insensitive characters (0-9a-zA-Z`~!@#$%^&*()-_=+[]{}\|;:',.<>/?). ‘*’ can be used as
a wildcard to match any string. Use ‘\*’ to indicate a single wildcard character.
Alternatively, to automatically add an entry for existing SSL traffic to a destination server, go to
Monitor > UTM Statistics > SSL Inspection > Certificate Cache List, select an item and then click
Add to Exclude List. The item will then appear here.
Apply Click Apply to save your settings to the Zyxel Device.
Reset Click Reset to return to the profile summary page without saving any changes.
Table 275 Configuration > UTM Profile > SSL Inspection > Exclude List (continued)
LABEL DESCRIPTION
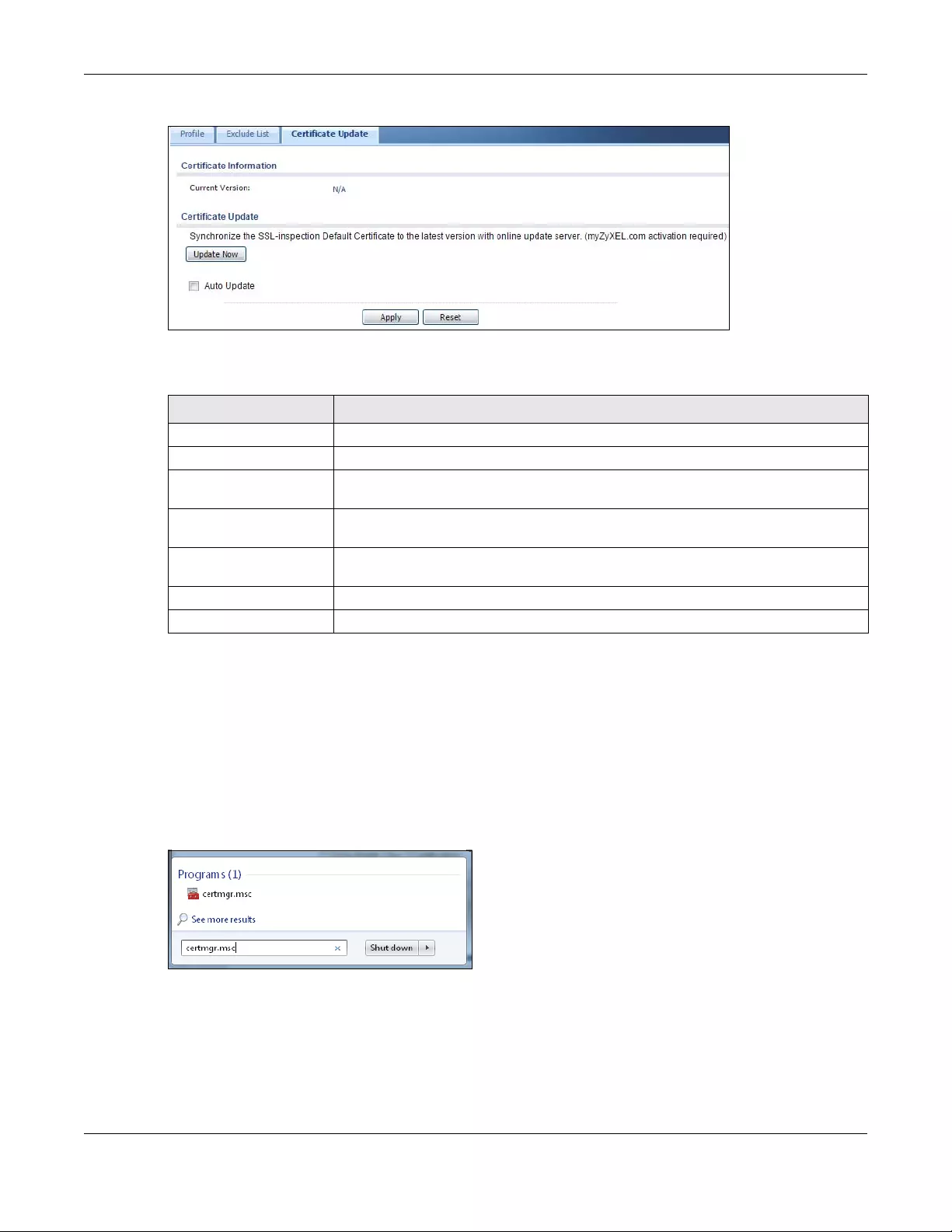
Chapter 41 SSL Inspection
USG/ZyWALL User’s Guide
715
Figure 500 Configuration > UTM Profile > SSL Inspection > Certificate Update
The following table describes the fields in this screen.
41.5 Install a CA Certificate in a Browser
Certificates used in SSL Inspection profiles should be installed in user web browsers. Do the following
steps to install a certificate in a computer with a Windows operating system (PC). First, save the
certificate to your computer.
1Run the certificate manager using certmgr.msc.
2Go to Trusted Root Certification Authorities > Certificates.
Table 276 Configuration > UTM Profile > SSL Inspection > Certificate Update
LABEL DESCRIPTION
Certificate Information
Current Version This displays the current certificate set version.
Certificate Update You should have Internet access and have activated SSL Inspection on the Zyxel
Device at myZyxel.com.
Update Now Click this button to download the latest certificate set from the myZyxel.com and
update it on the Zyxel Device.
Auto Update Select this to automatically have the Zyxel Device update the certificate set when a
new one becomes available on myZyxel.com.
Apply Click Apply to save your settings to the Zyxel Device.
Reset Click Reset to return to the profile summary page without saving any changes.
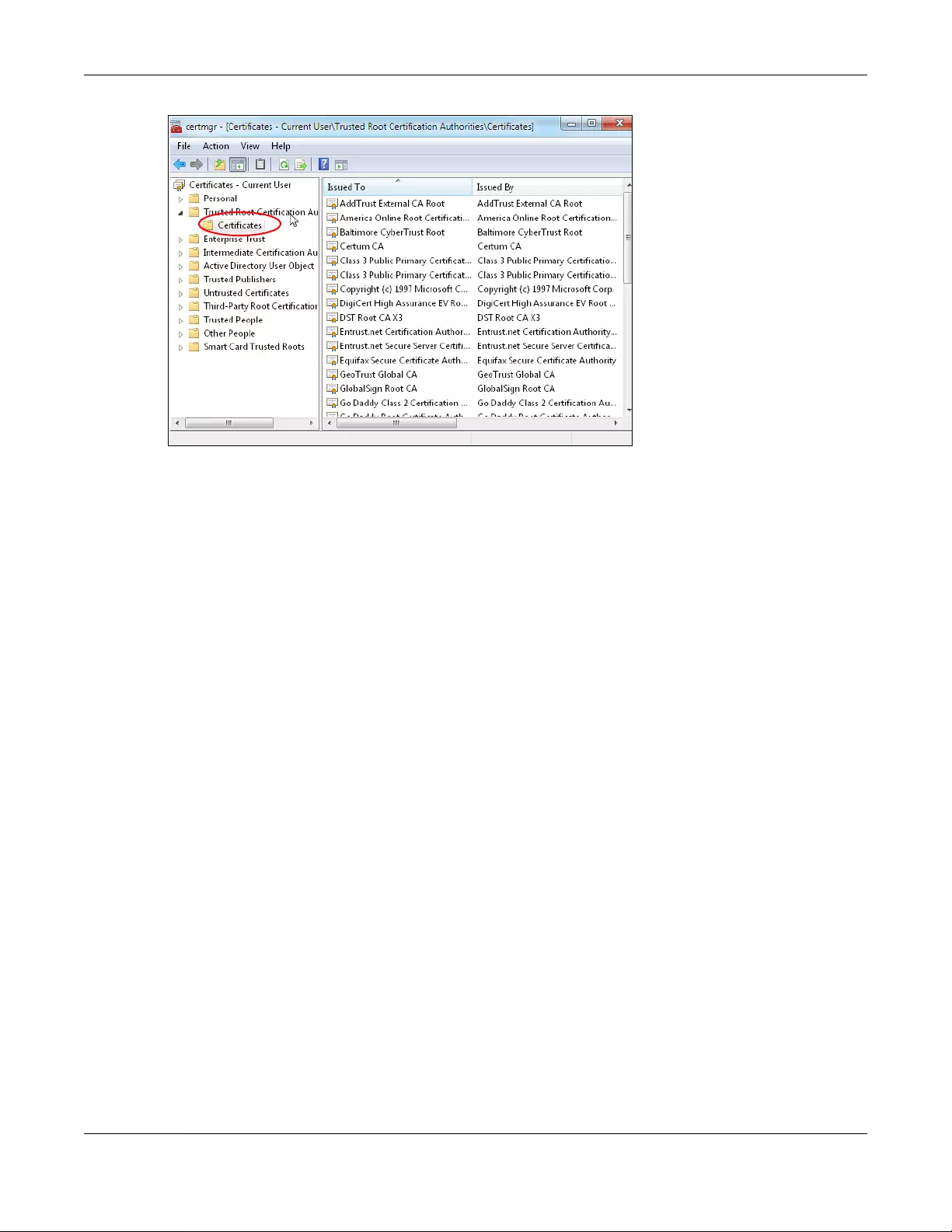
Chapter 41 SSL Inspection
USG/ZyWALL User’s Guide
716
3From the main menu, select Action > All Tasks > Import and run the Certificate Import Wizard to install
the certificate on the PC.
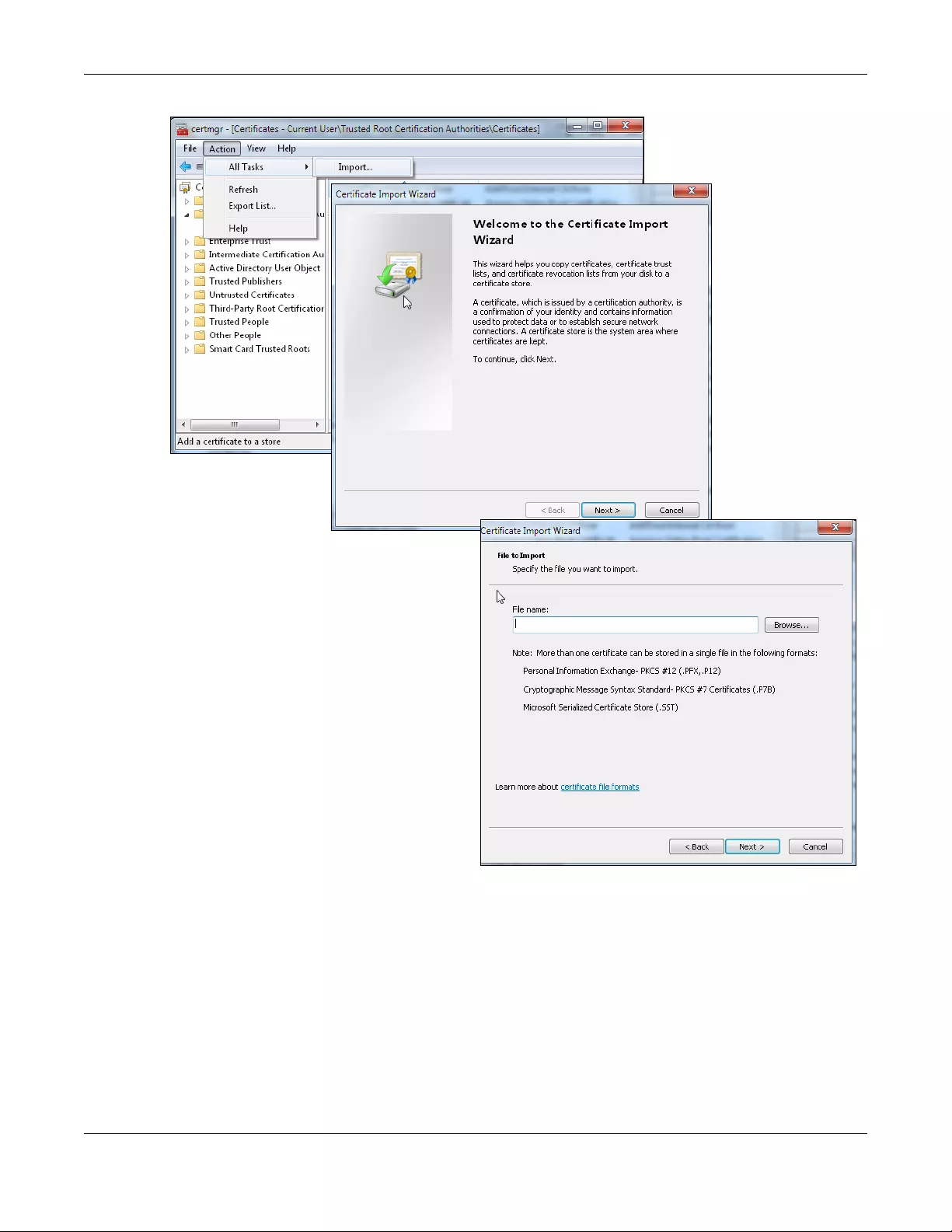
Chapter 41 SSL Inspection
USG/ZyWALL User’s Guide
717
41.5.0.1 Firefox Browser
If you’re using a Firefox browser, in addition to the above you need to do the following to import a
certificate into the browser.
Click Tools > Options > Advanced > Encryption > View Certificates, click Import and enter the filename
of the certificate you want to import. See the browser's help for further information.
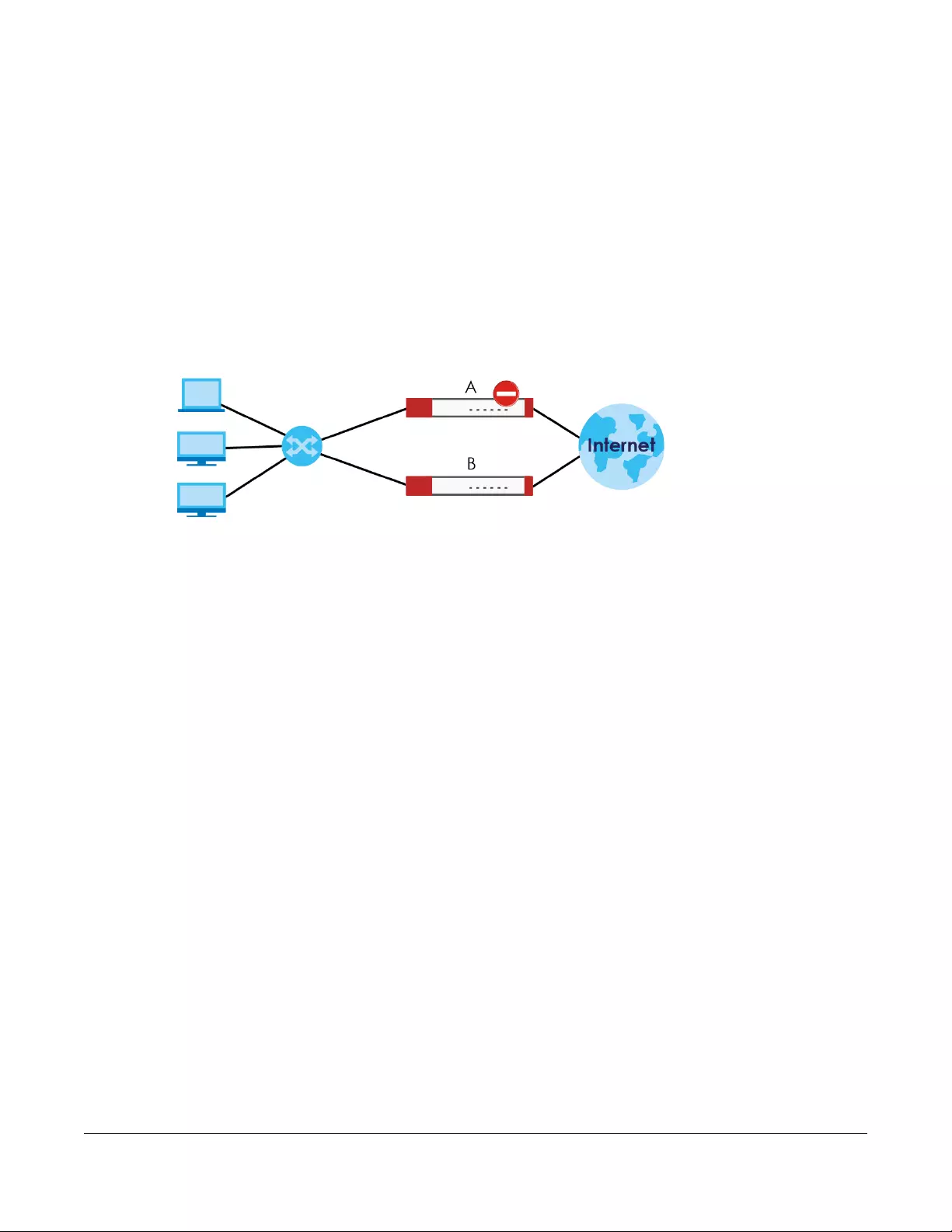
USG/ZyWALL User’s Guide
718
CHAPTER 42
Device HA
42.1 Overview
Device HA lets a backup Zyxel Device (B) automatically take over if the master Zyxel Device (A) fails.
Figure 501 Device HA Backup Taking Over for the Master
The following models support Device HA (High Availability):
• ZyWALL 110
• ZyWALL 310
•ZyWALL 1100
• USG110
• USG210
• USG310
• USG1100
• USG1900
• USG2200-VPN
42.1.1 What You Can Do in These Screens
• Use the General screen (Section 42.2 on page 719) to configure Device HA global settings, and see
the status of each interface monitored by Device HA.
• Use the Device HA Pro screen (Section 42.3 on page 721) to configure Device HA Pro global,
monitored interfaces and synchronization settings.
• Use the Active-Passive Mode screens (Section 42.4 on page 724) to use active-passive mode Device
HA. You can configure general active-passive mode Device HA settings, view and manage the list of
monitored interfaces, and synchronize backup Zyxel Devices.

Chapter 42 Device HA
USG/ZyWALL User’s Guide
719
42.2 Device HA General
Active-Passive Mode
• Active-passive mode lets a backup Zyxel Device take over if the master Zyxel Device fails.
• The Zyxel Devices must be set to use the same Device HA mode (active-passive).
Management Access
You can configure a separate management IP address for each interface. You can use it to access the
Zyxel Device for management whether the Zyxel Device is the master or a backup. The management IP
address should be in the same subnet as the interface IP address.
Synchronization
Use synchronization to have a backup Zyxel Device copy the master Zyxel Device’s configuration,
signatures (anti-virus, IDP/application patrol, and system protect), and certificates.
Note: Only Zyxel Devices of the same model and firmware version can synchronize.
Otherwise you must manually configure the master Zyxel Device’s settings on the backup (by editing
copies of the configuration files in a text editor for example).
Finding Out More
•See Section 42.6 on page 730 for Device HA background/technical information.
42.2.1 Before You Begin
• Configure a static IP address for each interface that you will have Device HA monitor.
Note: Subscribe to services on the backup Zyxel Device before synchronizing it with the
master Zyxel Device.
Synchronization includes updates for services to which the master and backup Zyxel Devices are both
subscribed. For example, a backup subscribed to IDP/AppPatrol, but not anti-virus, gets IDP/AppPatrol
updates from the master, but not anti-virus updates. It is highly recommended to subscribe the master
and backup Zyxel Devices to the same services.
The C onfiguration > Device HA General screen lets you enable or disable Device HA, and displays which
Device HA mode the Zyxel Device is set to use along with a summary of the monitored interfaces.
Click on the icons to go to the OneSecurity.com website where there is guidance on configuration
walkthroughs, troubleshooting, and other information.
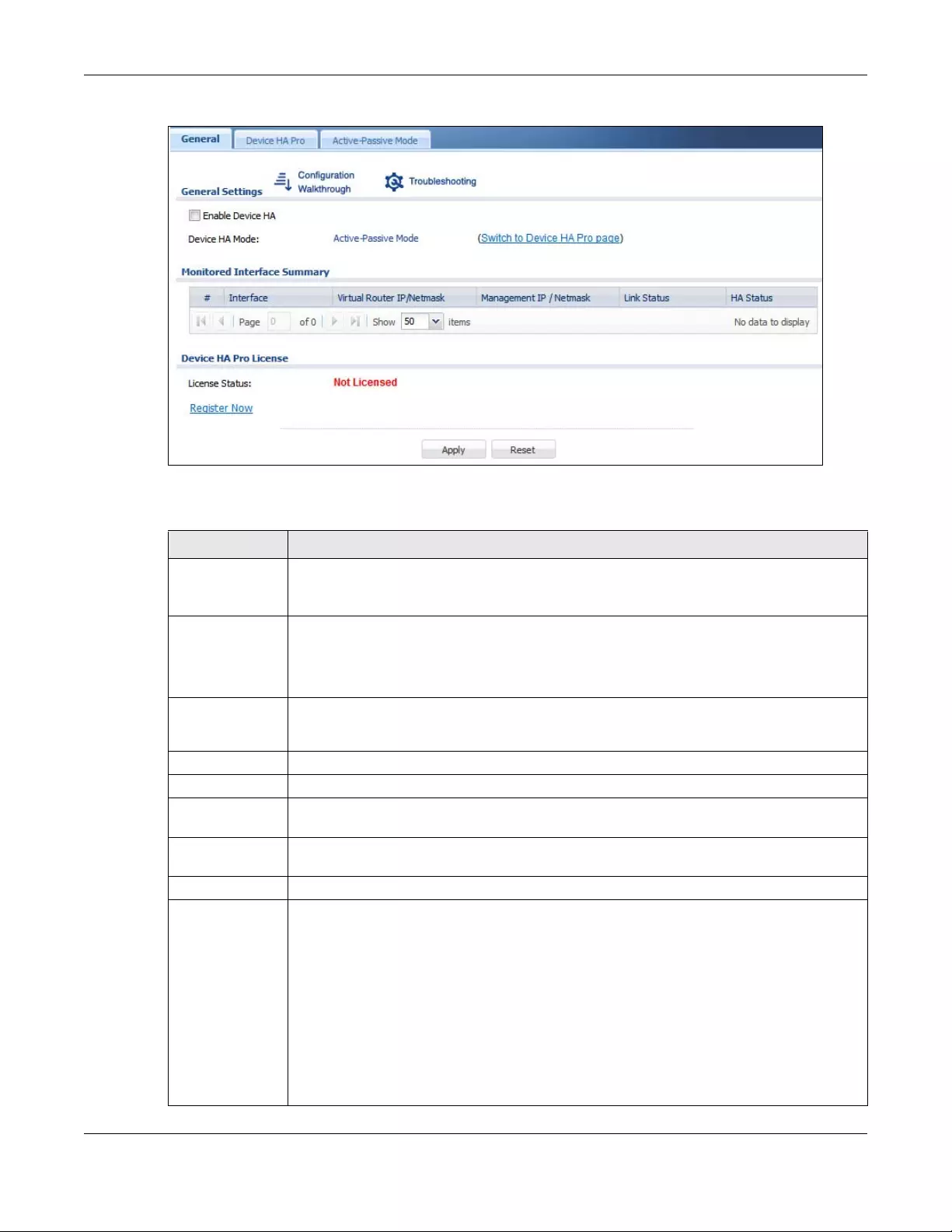
Chapter 42 Device HA
USG/ZyWALL User’s Guide
720
Figure 502 Configuration > Device HA > General
The following table describes the labels in this screen.
Table 277 Configuration > Device HA > General
LABEL DESCRIPTION
Enable Device
HA
Turn the Zyxel Device’s Device HA feature on or off.
Note: It is not recommended to use STP (Spanning Tree Protocol) with Device HA.
Device HA Mode This displays whether the Zyxel Device is currently set to use active-passive mode Device HA.
Active-passive mode is recommended for general device failover deployments.
Click the link to go to the screen where you can configure the Zyxel Device to use the Device
HA pro mode that it is not currently using.
Monitored
Interface
Summary
This table shows the status of the interfaces that you selected for monitoring in the other Device
HA screens.
#This is the entry’s index number in the list.
Interface These are the names of the interfaces that are monitored by Device HA.
Virtual Router IP /
Netmask
This is the interface’s IP address and subnet mask. Whichever Zyxel Device is the master uses this
virtual router IP address and subnet mask.
Management IP /
Netmask
This field displays the interface’s management IP address and subnet mask. You can use this IP
address and subnet mask to access the Zyxel Device whether it is in master or backup mode.
Link Status This tells whether the monitored interface’s connection is down or up.
HA Status The text before the slash shows whether the device is configured as the master or the backup
role.
This text after the slash displays the monitored interface’s status in the virtual router.
Active - This interface is up and using the virtual IP address and subnet mask.
Stand-By - This interface is a backup interface in the virtual router. It is not using the virtual IP
address and subnet mask.
Fault - This interface is not functioning in the virtual router right now. In active-passive mode if
one of the master Zyxel Device’s interfaces loses its connection, the master Zyxel Device forces
all of its interfaces to the fault state so the backup Zyxel Device can take over all of the master
Zyxel Device’s functions.
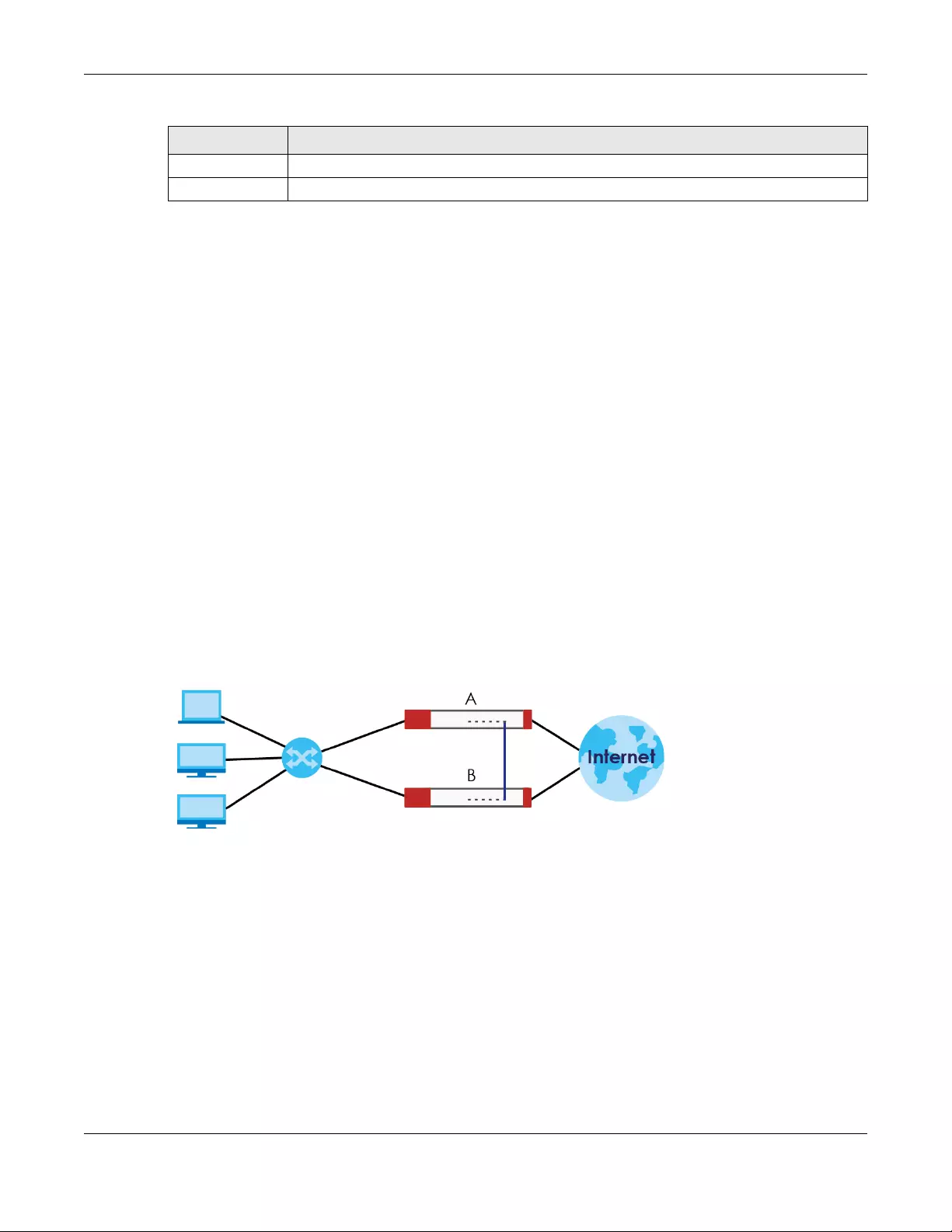
Chapter 42 Device HA
USG/ZyWALL User’s Guide
721
42.3 Device HA Pro
You need a license to use Device HA Pro. Device HA Pro is easier to deploy than Device HA, is more
reliable (no risk of overloading), and faster (Device HA causes a connection break of 10~30 seconds
while Device HA Pro just has 1~2 seconds). In addition to configuration file backup in Device HA, device
time, TCP sessions (IPv4/IPv6), IPSec VPN sessions, login/logout information and license status can also be
backed up using Device HA Pro.
Active and Passive Devices
Device HA Pro uses a dedicated heartbeat link between an active device (‘master’) and a passive
device (‘backup’) for status syncing and backup to the passive device. On the passive device, all ports
are disabled except for the port with the heartbeat link.
In the following example, Zyxel Device A is the active device that is connected to passive device Zyxel
Device B via a dedicated link that is used for heartbeat control, configuration synchronization and
troubleshooting. All links on Zyxel Device B are down except for the dedicated heartbeat link.
Note: The dedicated heartbeat link port must be the highest-numbered port on each Zyxel
Device for Device HA Pro to work.
Figure 503 Device HA Pro
Failover from the active Zyxel Device to the passive Zyxel Device is activated when:
• A monitored interface is down
• A monitored service (daemon) is down
• The heartbeat link exceeds the failure tolerance.
After failover, the initial active Zyxel Device becomes the passive Zyxel Device after it recovers.
42.3.1 Deploying Device HA Pro
1Register either the active or passive Zyxel Device with a Device HA Pro license at MyZyxel.com. Check
that it’s properly licensed in Licensing > Registration > Service in the active Zyxel Device.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 277 Configuration > Device HA > General (continued)
LABEL DESCRIPTION
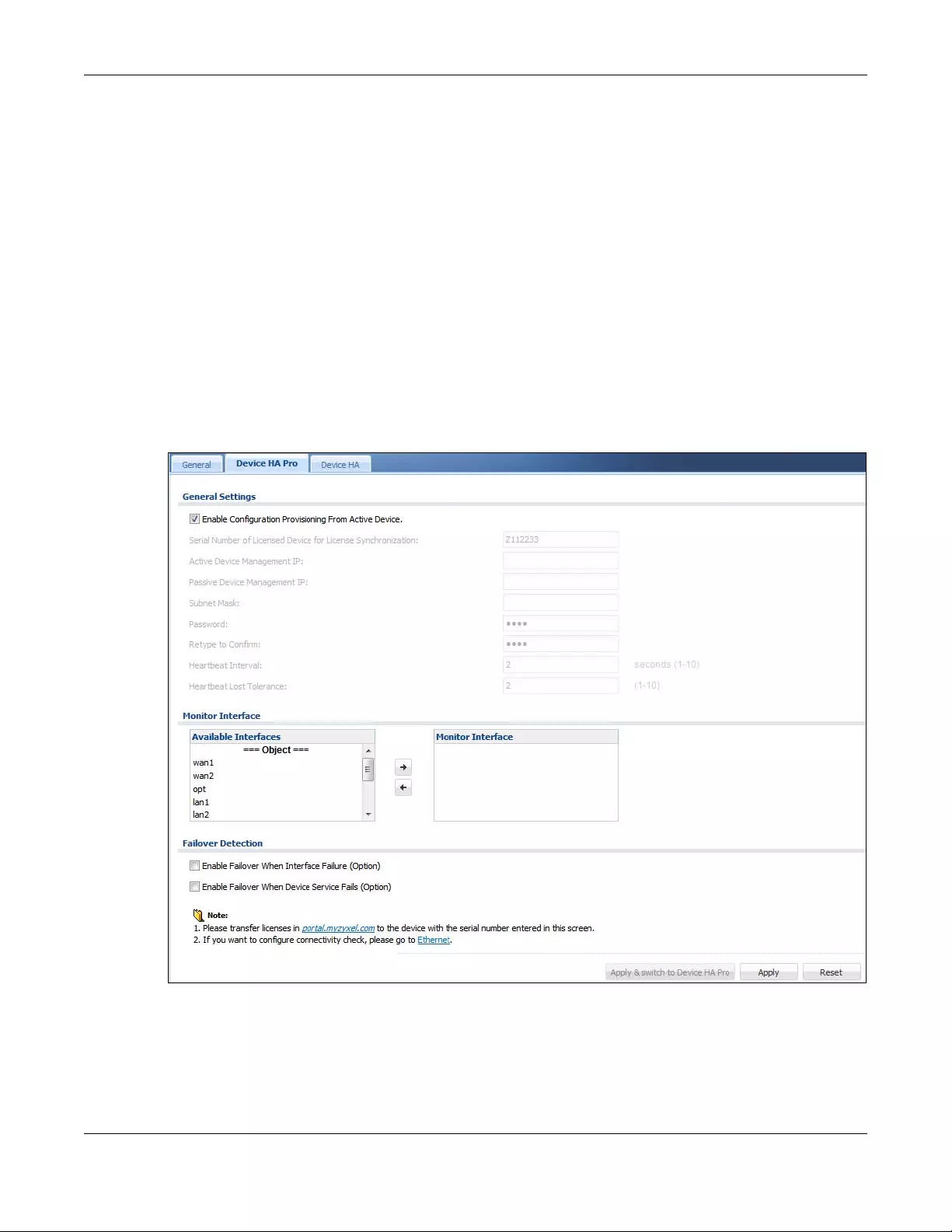
Chapter 42 Device HA
USG/ZyWALL User’s Guide
722
2Make sure the passive Zyxel Device is offline, then enable Device HA in Device HA > General in the
passive Zyxel Device.
3Must make sure the FTP port in System > FTP (default 21) is the same on both Zyxel Devices. FTP is used for
transferring files in the event of failover from active to passive Zyxel Device.
4Connect the passive Zyxel Device to the active Zyxel Device using the highest-numbered ports on both
Zyxel Devices.
Note: If both Zyxel Devices are turned on at the same time with Device HA enabled, then
they may send the heartbeat at the same time. In this case, the Zyxel Device with the
bigger MAC address becomes the passive Zyxel Device.
42.3.2 Configuring Device HA Pro
Go to Configuration > Device HA > Device HA Pro and configure the following screen.
Figure 504 Configuration > Device HA > Device HA Prol
Chapter 42 Device HA
USG/ZyWALL User’s Guide
723
The following table describes the labels in this screen.
Table 278 Configuration > Device HA > Device HA Pro
LABEL DESCRIPTION
Enable Configuration
Provisioning From Active
Device.
Select this to have a passive Zyxel Device copy the active Zyxel Device’s
configuration, signatures (anti-virus, IDP/application patrol, and system protect),
and certificates.
Note: Only Zyxel Devices of the same model and firmware version can
synchronize.
Serial Number of Licensed
Device for License
Synchronization
Type the serial number of the Zyxel Device (active or passive) with the Device HA Pro
subscribed license.
Active Device
Management IP
Type the IPv4 address of the highest-numbered port on the active Zyxel Device (the
heartbeat dedicated link port).
Passive Device
Management IP
Type the IPv4 address of the highest-numbered port on the passive Zyxel Device (the
heartbeat dedicated link port).
Note: The active and passive Zyxel Device Management IP addresses must
be in the same subnet.
Subnet Mask Type the subnet mask for the management IP addresses.
Password Type a synchronization password of between 1 and 32 single-byte printable
characters. You will be prompted for the password before synchronization takes
place.
Retype to Confirm Type the exact same synchronization password as typed above.
Heartbeat Interval Type the number of seconds (1-10) allowed for absence of a heartbeat signal
before a failure of the active Zyxel Device is recorded.
Heartbeat Lost Tolerance Type the number of heartbeat failures allowed before failover is activated on the
passive Zyxel Device.
Monitor Interface Select an interface in Available Interfaces and click the right-arrow button to move
it to Monitor Interface to become a Device HA pro monitored interface. To remove
a Device HA pro monitored interface, select it in Monitor Interface and click the left-
arrow button to move it to Available Interfaces.
Failover Detection
Enable Failover When
Interface Failure (Option) Select this to have the passive Zyxel Device take over when a monitored interface
fails.
Enable Failover When
Device Service Fails
(Option)
Select this to have the passive Zyxel Device take over when a monitored service
daemon on the active Zyxel Device fails.
Apply & switch to Device
HA Pro
Click Apply to save your changes back to the Zyxel Device and change the Zyxel
Device to begin using Device HA Pro from Device HA (general) if it isn’t already. You
need a Device HA Pro license registered at MyZyxel.com to do this.
Apply Click Apply to save your Device HA Pro configurations back to the Zyxel Device but
keep the Zyxel Device using Device HA (general).
Reset Click Reset to return the screen to its last-saved settings.
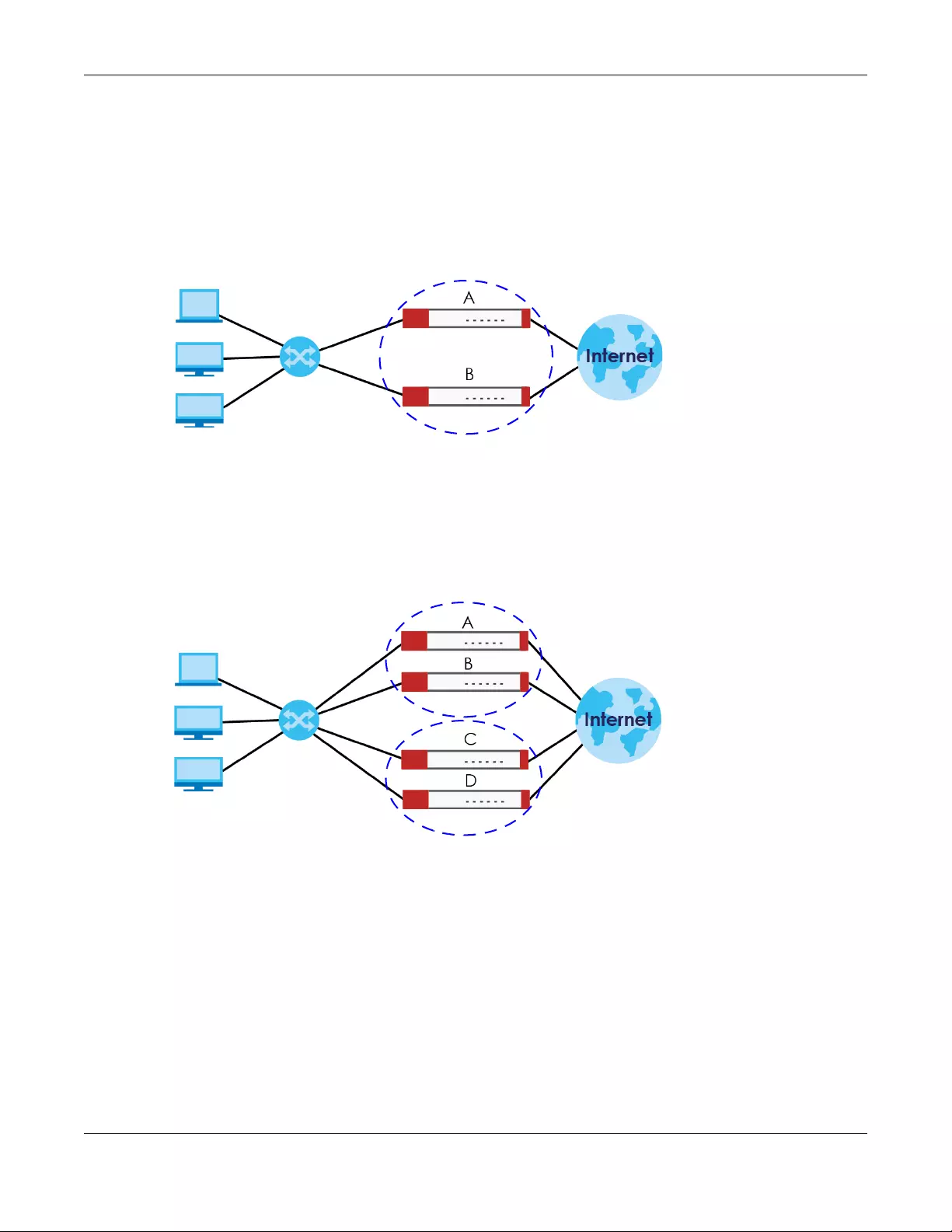
Chapter 42 Device HA
USG/ZyWALL User’s Guide
724
42.4 The Active-Passive Mode Screen
Virtual Router
The master and backup Zyxel Device form a single ‘virtual router’. In the following example, master Zyxel
Device A and backup Zyxel Device B form a virtual router.
Figure 505 Virtual Router
Cluster ID
You can have multiple Zyxel Device virtual routers on your network. Use a different cluster ID to identify
each virtual router. In the following example, Zyxel Devices A and B form a virtual router that uses cluster
ID 1. Zyxel Devices C and D form a virtual router that uses cluster ID 2.
Figure 506 Cluster IDs for Multiple Virtual Routers
Monitored Interfaces in Active-Passive Mode Device HA
You can select which interfaces Device HA monitors. If a monitored interface on the Zyxel Device loses
its connection, Device HA has the backup Zyxel Device take over.
Enable monitoring for the same interfaces on the master and backup Zyxel Devices. Each monitored
interface must have a static IP address and be connected to the same subnet as the corresponding
interface on the backup or master Zyxel Device.
Virtual Router and Management IP Addresses
• If a backup takes over for the master, it uses the master’s IP addresses. These IP addresses are known
as the virtual router IP addresses.
1
2
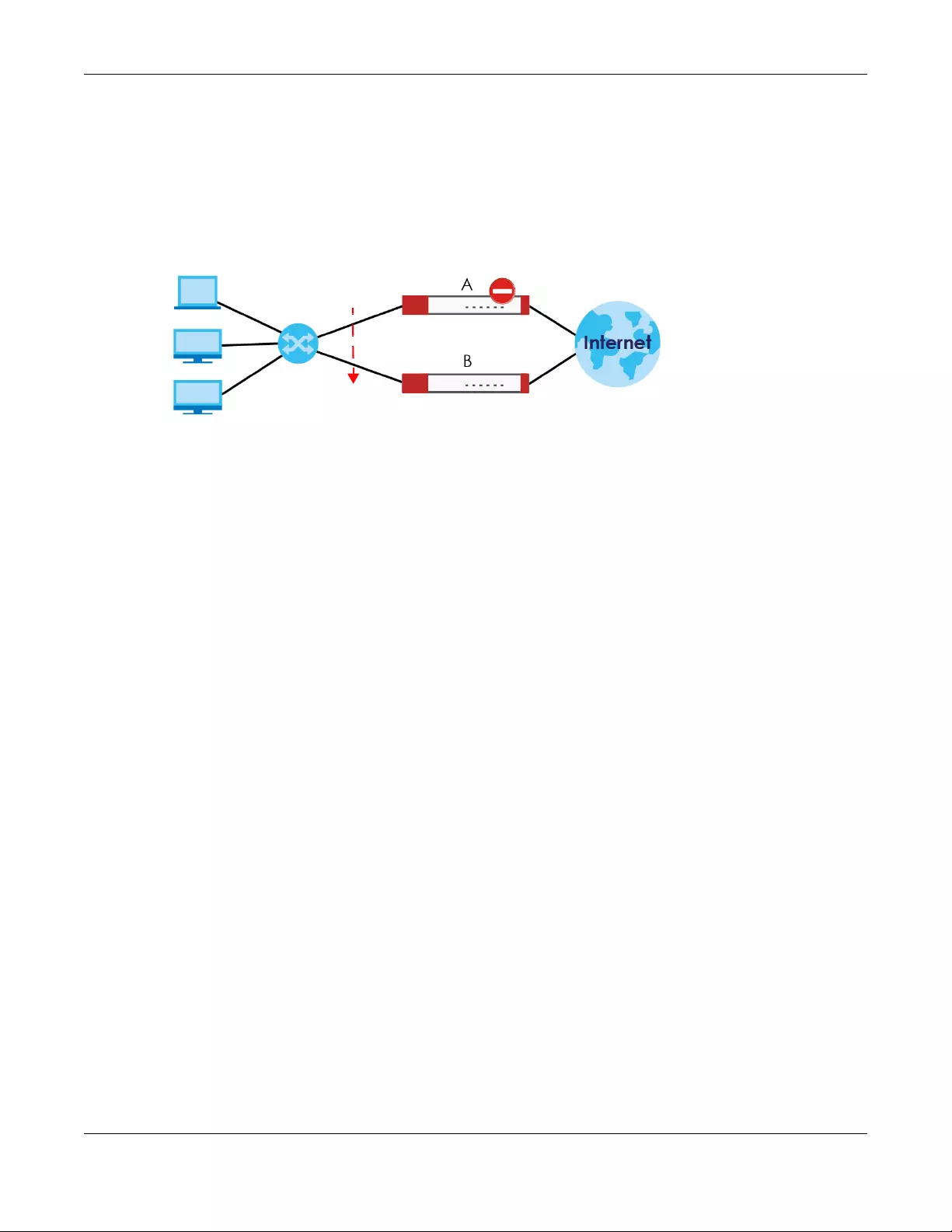
Chapter 42 Device HA
USG/ZyWALL User’s Guide
725
• Each interface can also have a management IP address. You can connect to this IP address to
manage the Zyxel Device regardless of whether it is the master or the backup.
For example, Zyxel Device B takes over A’s 192.168.1.1 LAN interface IP address. This is a virtual router IP
address. Zyxel Device A keeps it’s LAN management IP address of 192.168.1.5 and Zyxel Device B has its
own LAN management IP address of 192.168.1.6. These do not change when Zyxel Device B becomes
the master.
Figure 507 Management IP Addresses
42.4.1 Configuring Active-Passive Mode Device HA
The Device HA Active-Passive Mode screen lets you configure general active-passive mode Device HA
settings, view and manage the list of monitored interfaces, and synchronize backup Zyxel Devices. To
access this screen, click Configuration > Device HA > Active-Passive Mode.
192.168.1.1
192.168.1.1
192.168.1.5
192.168.1.6
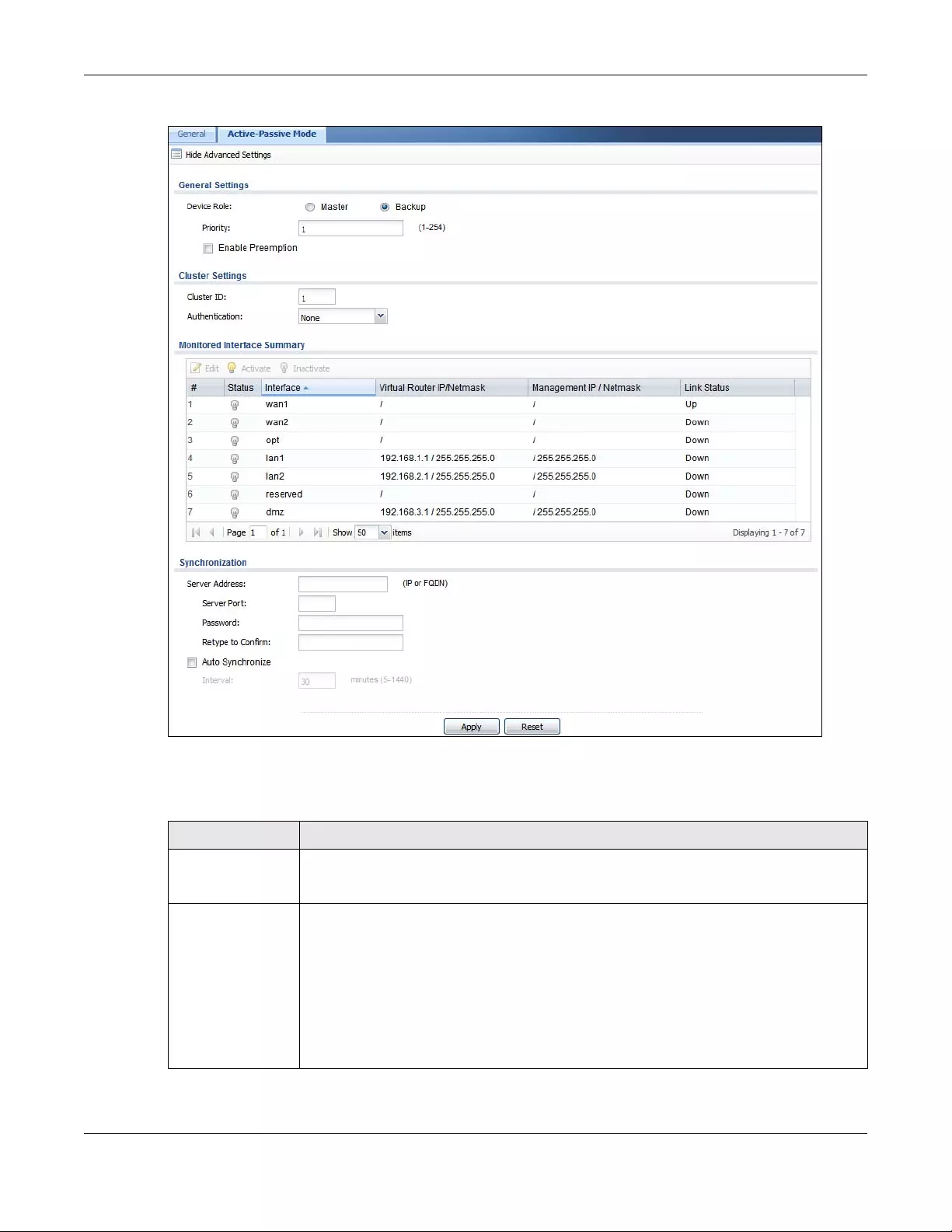
Chapter 42 Device HA
USG/ZyWALL User’s Guide
726
Figure 508 Configuration > Device HA > Active Passive Mode
The following table describes the labels in this screen. See Section 42.5 on page 728 for more information
as well.
Table 279 Configuration > Device HA > Active-Passive Mode
LABEL DESCRIPTION
Show Advanced
Settings / Hide
Advanced Settings
Click this button to display a greater or lesser number of configuration fields.
Device Role Select the Device HA role that the Zyxel Device plays in the virtual router. Choices are:
Master - This Zyxel Device is the master Zyxel Device in the virtual router. This Zyxel Device uses
the virtual IP address for each monitored interface.
Note: Do not set this field to Master for two or more Zyxel Devices in the same
virtual router (same cluster ID).
Backup - This Zyxel Device is a backup Zyxel Device in the virtual router. This Zyxel Device
does not use any of the virtual IP addresses.
Chapter 42 Device HA
USG/ZyWALL User’s Guide
727
Priority This field is available for a backup Zyxel Device. Type the priority of the backup Zyxel Device.
The backup Zyxel Device with the highest value takes over the role of the master Zyxel
Device if the master Zyxel Device becomes unavailable. The priority must be between 1 and
254. (The master interface has priority 255.)
Enable Preemption This field is available for a backup Zyxel Device. Select this if this Zyxel Device should become
the master Zyxel Device if a lower-priority Zyxel Device is the master when this one is enabled.
(If the role is master, the Zyxel Device preempts by default.)
Cluster Settings
Cluster ID Type the cluster ID number. A virtual router consists of a master Zyxel Device and all of its
backup Zyxel Devices. If you have multiple Zyxel Device virtual routers on your network, use a
different cluster ID for each virtual router.
Authentication Select the authentication method the virtual router uses. Every interface in a virtual router
must use the same authentication method and password. Choices are:
None - this virtual router does not use any authentication method.
Text - this virtual router uses a plain text password for authentication. Type the password in the
field next to the radio button. The password can consist of alphanumeric characters, the
underscore, and some punctuation marks (+-/*= :; .! @$&%#~ ‘ \ () ), and it can be up to
eight characters long.
IP AH (MD5) - this virtual router uses an encrypted MD5 password for authentication. Type the
password in the field next to the radio button. The password can consist of alphanumeric
characters, the underscore, and some punctuation marks (+-/*= :; .! @$&%#~ ‘ \ () ), and it
can be up to eight characters long.
Monitored
Interface Summary
This table shows the status of the Device HA settings and status of the Zyxel Device’s
interfaces.
Edit Select an entry and click this to be able to modify it.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
#This is the entry’s index number in the list.
Status The activate (light bulb) icon is lit when the entry is active and dimmed when the entry is
inactive.
Interface This field identifies the interface. At the time of writing, Ethernet and bridge interfaces can be
included in the active-passive mode virtual router. The member interfaces of any bridge
interfaces do not display separately.
Virtual Router IP /
Netmask
This is the master Zyxel Device’s (static) IP address and subnet mask for this interface. If a
backup takes over for the master, it uses this IP address. These fields are blank if the interface
is a DHCP client or has no IP settings.
Management IP /
Netmask
This field displays the interface’s management IP address and subnet mask. You can use this
IP address and subnet mask to access the Zyxel Device whether it is in master or backup
mode.
Link Status This tells whether the monitored interface’s connection is down or up.
Synchronization Use synchronization to have a backup Zyxel Device copy the master Zyxel Device’s
configuration, certificates, AV signatures, IDP and application patrol signatures, and system
protect signatures.
Every interface’s management IP address must be in the same subnet as the interface’s IP
address (the virtual router IP address).
Table 279 Configuration > Device HA > Active-Passive Mode (continued)
LABEL DESCRIPTION
Chapter 42 Device HA
USG/ZyWALL User’s Guide
728
42.5 Active-Passive Mode Edit Monitored Interface
The Device HA Active-Passive Mode Monitored Interface Edit screen lets you enable or disable
monitoring of an interface and set the interface’s management IP address and subnet mask. To access
this screen, click Configuration > Device HA > Active-Passive Mode > Edit.
If you configure Device HA settings for an Ethernet interface and later add the Ethernet interface to a
bridge, the Zyxel Device retains the interface’s Device HA settings and uses them again if you later
remove the interface from the bridge. If the bridge is later deleted or the interface is removed from it,
Device HA will recover the interface’s setting.
A bridge interface’s Device HA settings are not retained if you delete the bridge interface.
Server Address If this Zyxel Device is set to backup role, enter the IP address or Fully-Qualified Domain Name
(FQDN) of the Zyxel Device from which to get updated configuration. Usually, you should
enter the IP address or FQDN of a virtual router on a secure network.
If this Zyxel Device is set to master role, this field displays the Zyxel Device’s IP addresses and/
or Fully-Qualified Domain Names (FQDN) through which Zyxel Devices in backup role can get
updated configuration from this Zyxel Device.
Sync. Now This displays if the Zyxel Device is set to use active-passive mode Device HA, the Zyxel Device
is in the backup role and Device HA is enabled. Click this to copy the specified Zyxel Device’s
configuration.
Server Port If this Zyxel Device is set to the backup role, enter the port number to use for Secure FTP when
synchronizing with the specified master Zyxel Device.
If this Zyxel Device is set to master role, this field displays the Zyxel Device’s Secure FTP port
number. Click the Configure link if you need to change the FTP port number.
Every Zyxel Device in the virtual router must use the same port number. If the master Zyxel
Device changes, you have to manually change this port number in the backups.
Password Enter the password used for verification during synchronization. Every Zyxel Device in the
virtual router must use the same password.
If you leave this field blank in the master Zyxel Device, no backup Zyxel Devices can
synchronize from it.
If you leave this field blank in a backup Zyxel Device, it cannot synchronize from the master
Zyxel Device.
Retype to Confirm Type the password again here to confirm it.
Auto Synchronize Select this to get the updated configuration automatically from the specified Zyxel Device
according to the specified Interval. The first synchronization begins after the specified
Interval; the Zyxel Device does not synchronize immediately.
Interval When you select Auto Synchronize, set how often the Zyxel Device synchronizes with the
master.
Next Sync Time This appears the next time and date (in hh:mm yyyy-mm-dd format) the Zyxel Device will
synchronize with the master.
Apply This appears when the Zyxel Device is currently using active-passive mode Device HA. Click
Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 279 Configuration > Device HA > Active-Passive Mode (continued)
LABEL DESCRIPTION
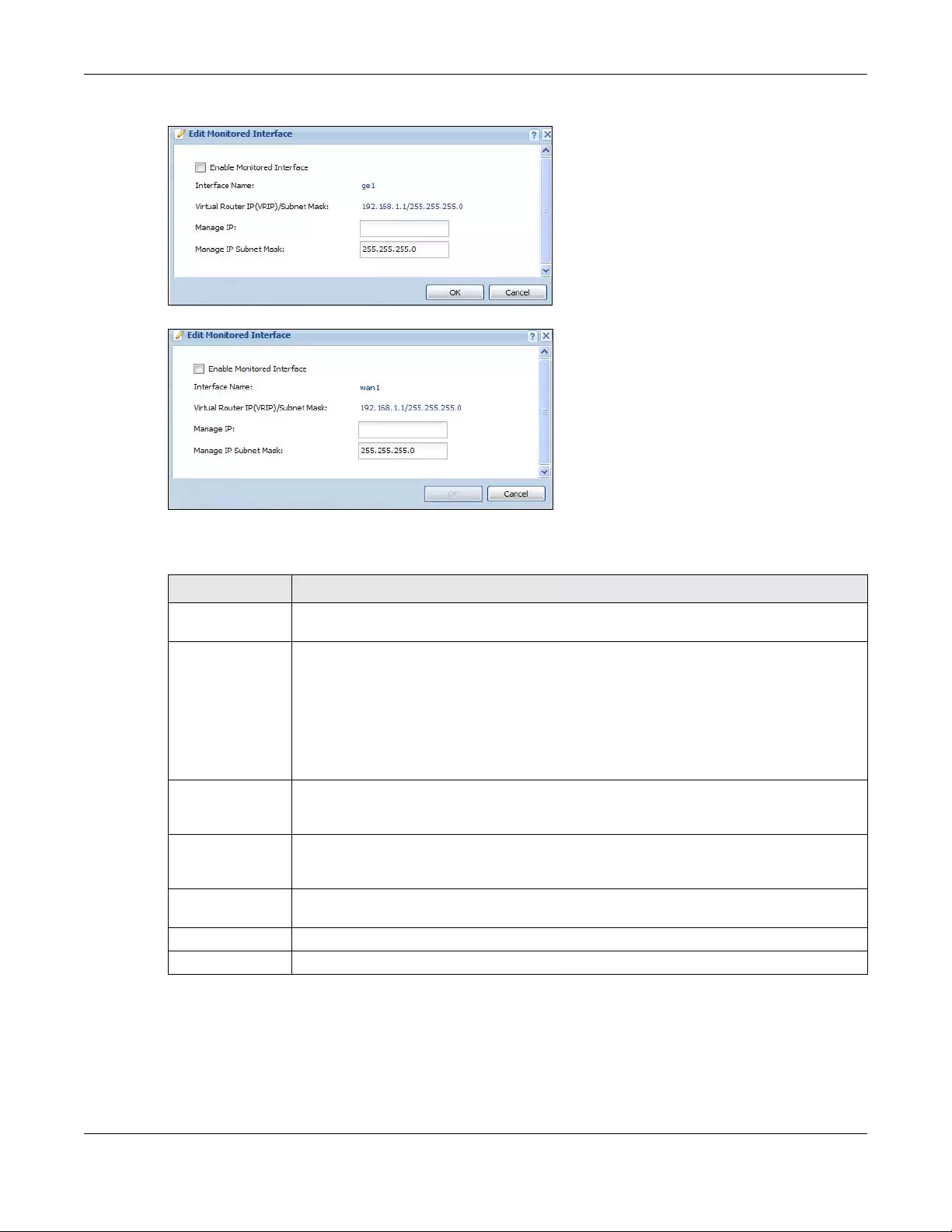
Chapter 42 Device HA
USG/ZyWALL User’s Guide
729
Figure 509 Configuration > Device HA > Active-Passive Mode > Edit
Figure 510 Configuration > Device HA > Active-Passive Mode > Edit
The following table describes the labels in this screen.
Table 280 Configuration > Device HA > Active-Passive Mode > Edit
LABEL DESCRIPTION
Enable Monitored
Interface
Select this to have Device HA monitor the status of this interface’s connection.
Interface Name This identifies the interface.
Note: Do not connect the bridge interfaces on two Zyxel Devices without Device HA
activated on both. Doing so could cause a broadcast storm.
Either activate Device HA before connecting the bridge interfaces or disable the bridge
interfaces, connect the bridge interfaces, activate Device HA, and finally reactivate the
bridge interfaces.
Virtual Router IP
(VRIP) / Subnet
Mask
This is the interface’s (static) IP address and subnet mask in the virtual router. Whichever Zyxel
Device is currently serving as the master uses this virtual router IP address and subnet mask.
These fields are blank if the interface is a DHCP client or has no IP settings.
Manage IP Enter the interface’s IP address for management access. You can use this IP address to access
the Zyxel Device whether it is the master or a backup. This management IP address should be
in the same subnet as the interface IP address.
Manage IP Subnet
Mask
Enter the subnet mask of the interface’s management IP address.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
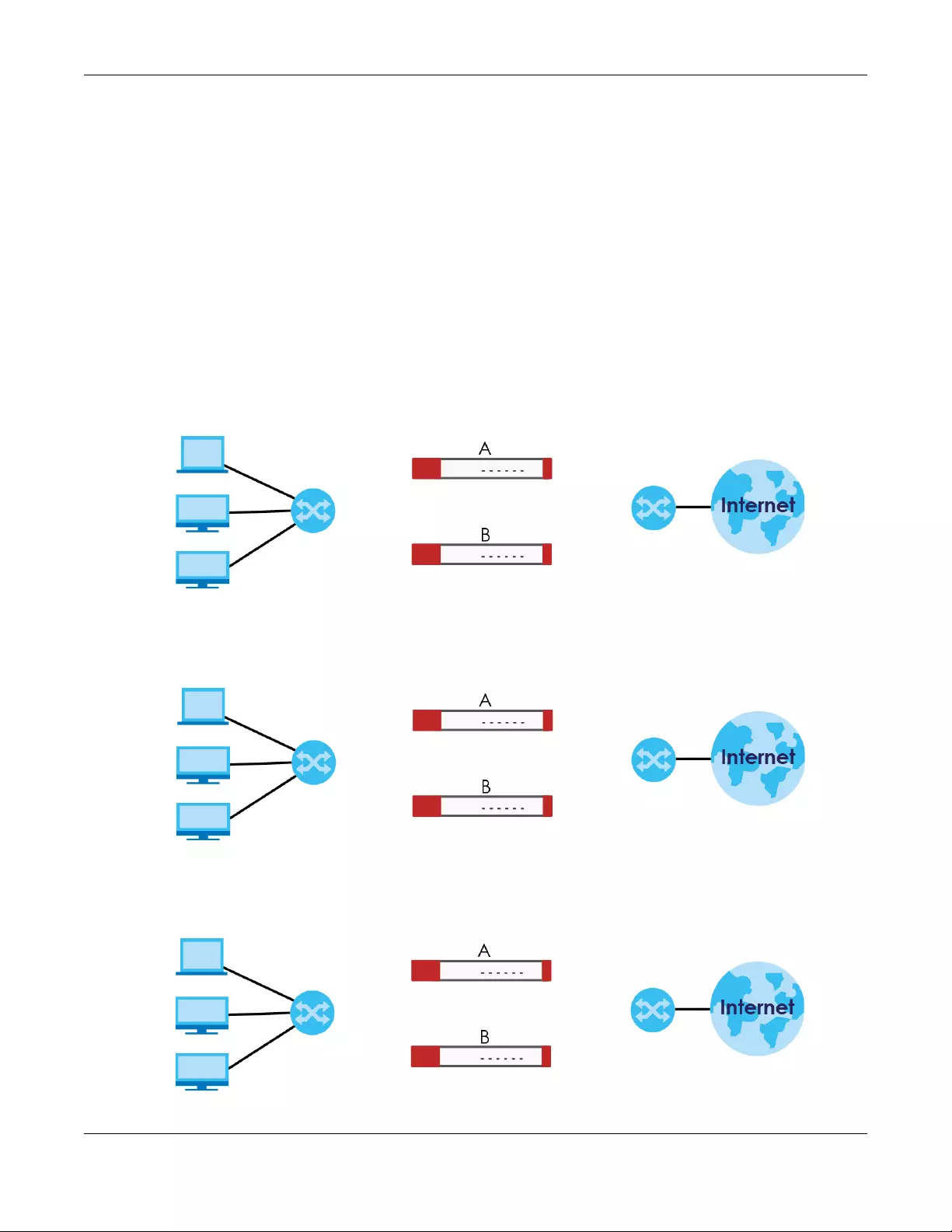
Chapter 42 Device HA
USG/ZyWALL User’s Guide
730
42.6 Device HA Technical Reference
Active-Passive Mode Device HA with Bridge Interfaces
Here are two ways to avoid a broadcast storm when you connect the bridge interfaces on two Zyxel
Devices.
First Option for Connecting the Bridge Interfaces on Two Zyxel Devices
The first way is to activate Device HA before connecting the bridge interfaces as shown in the following
example.
1Make sure the bridge interfaces of the master Zyxel Device (A) and the backup Zyxel Device (B) are not
connected.
2Configure the bridge interface on the master Zyxel Device, set the bridge interface as a monitored
interface, and activate Device HA.
3Configure the bridge interface on the backup Zyxel Device, set the bridge interface as a monitored
interface, and activate Device HA.
Br0 {ge4, ge5}
Br0 {ge4, ge5}
Br0 {ge4, ge5}
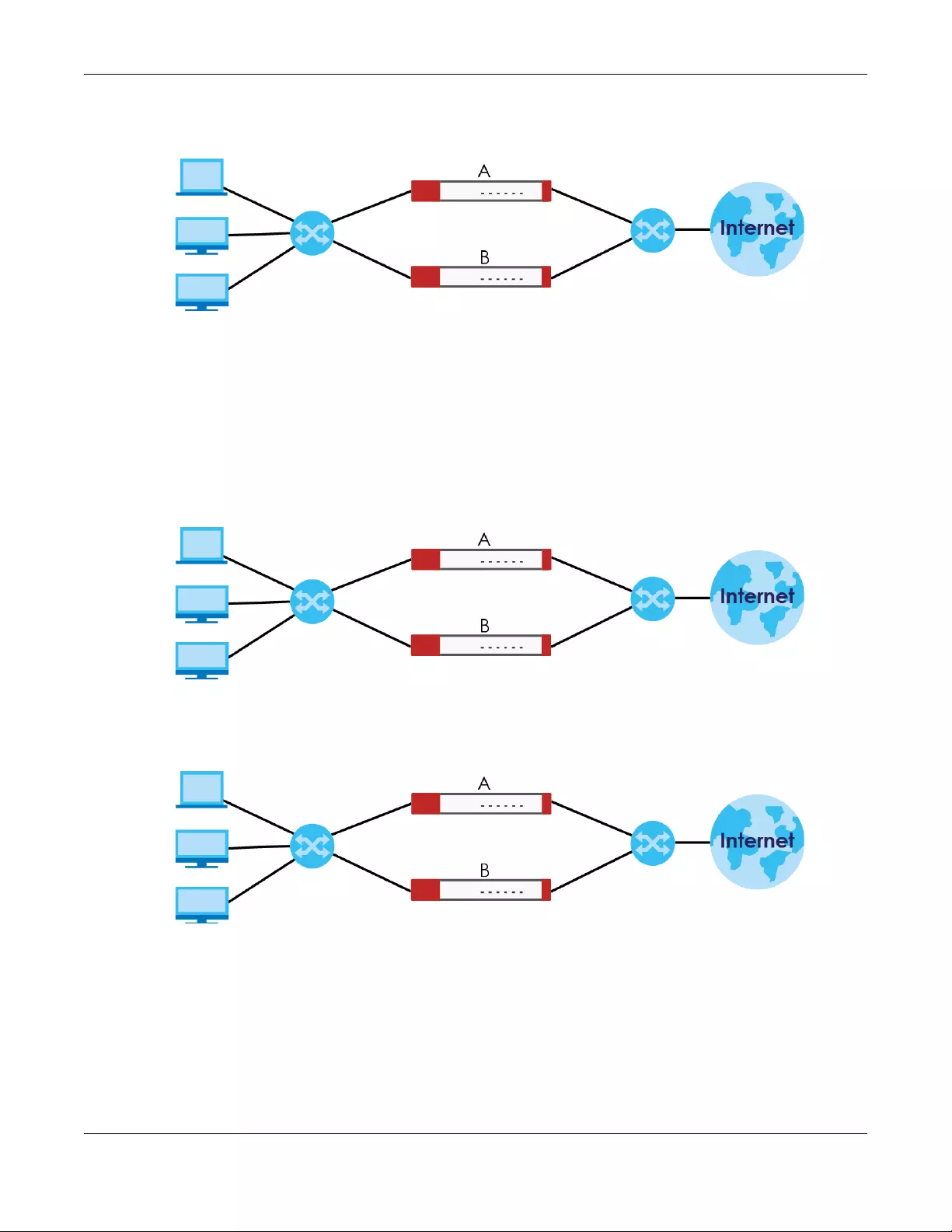
Chapter 42 Device HA
USG/ZyWALL User’s Guide
731
4Connect the Zyxel Devices.
Second Option for Connecting the Bridge Interfaces on Two Zyxel Devices
Another option is to disable the bridge interfaces, connect the bridge interfaces, activate Device HA,
and finally reactivate the bridge interfaces as shown in the following example.
1In this case the Zyxel Devices are already connected, but the bridge faces have not been configured
yet. Configure a disabled bridge interface on the master Zyxel Device but disable it. Then set the bridge
interface as a monitored interface, and activate Device HA.
2Configure a corresponding disabled bridge interface on the backup Zyxel Device. Then set the bridge
interface as a monitored interface, and activate Device HA.
3Enable the bridge interface on the master Zyxel Device and then on the backup Zyxel Device.
Br0 {ge4, ge5}
Br0 {ge4, ge5}
Br0 {ge4, ge5}
Br0 {ge4, ge5}
Disabled
Br0 {ge4, ge5}
Br0 {ge4, ge5}
Disabled
Disabled
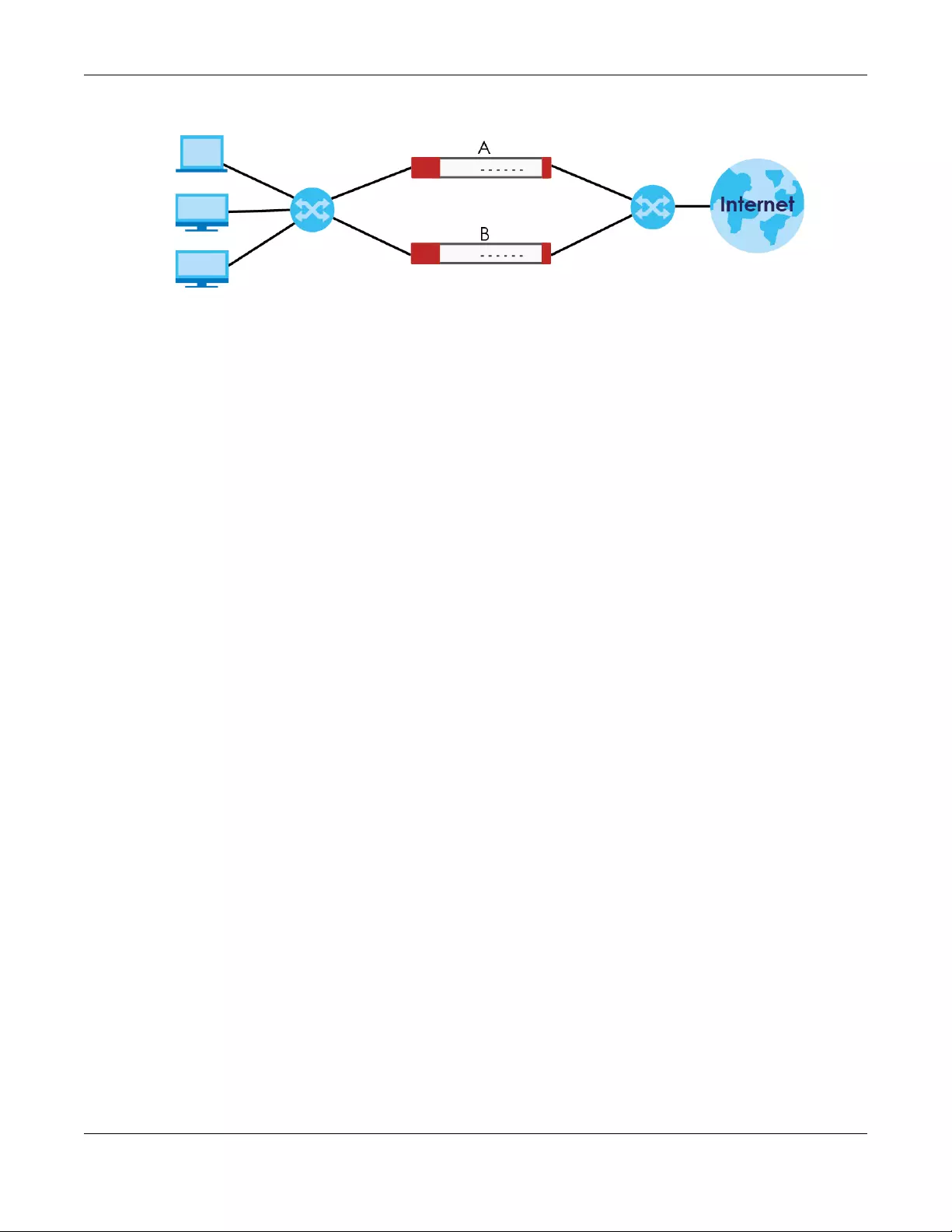
Chapter 42 Device HA
USG/ZyWALL User’s Guide
732
Synchronization
During synchronization, the master Zyxel Device sends the following information to the backup Zyxel
Device.
• Startup configuration file (startup-config.conf)
•AV signatures
• IDP and application patrol signatures
• System protect signatures
• Certificates (My Certificates, and Trusted Certificates)
Synchronization does not change the Device HA settings in the backup Zyxel Device.
Synchronization affects the entire device configuration. You can only configure one set of settings for
synchronization, regardless of how many VRRP groups you might configure. The Zyxel Device uses
Secure FTP (on a port number you can change) to synchronize, but it is still recommended that the
backup Zyxel Device synchronize with a master Zyxel Device on a secure network.
The backup Zyxel Device gets the configuration from the master Zyxel Device. The backup Zyxel Device
cannot become the master or be managed while it applies the new configuration. This usually takes
two or three minutes or longer depending on the configuration complexity.
The following restrictions apply with active-passive mode.
• The master Zyxel Device must have no inactive monitored interfaces.
• The backup Zyxel Device cannot be the master. This refers to the actual role at the time of
synchronization, not the role setting in the configuration screen.
The backup applies the entire configuration if it is different from the backup’s current configuration.
Br0 {ge4, ge5}
Br0 {ge4, ge5}
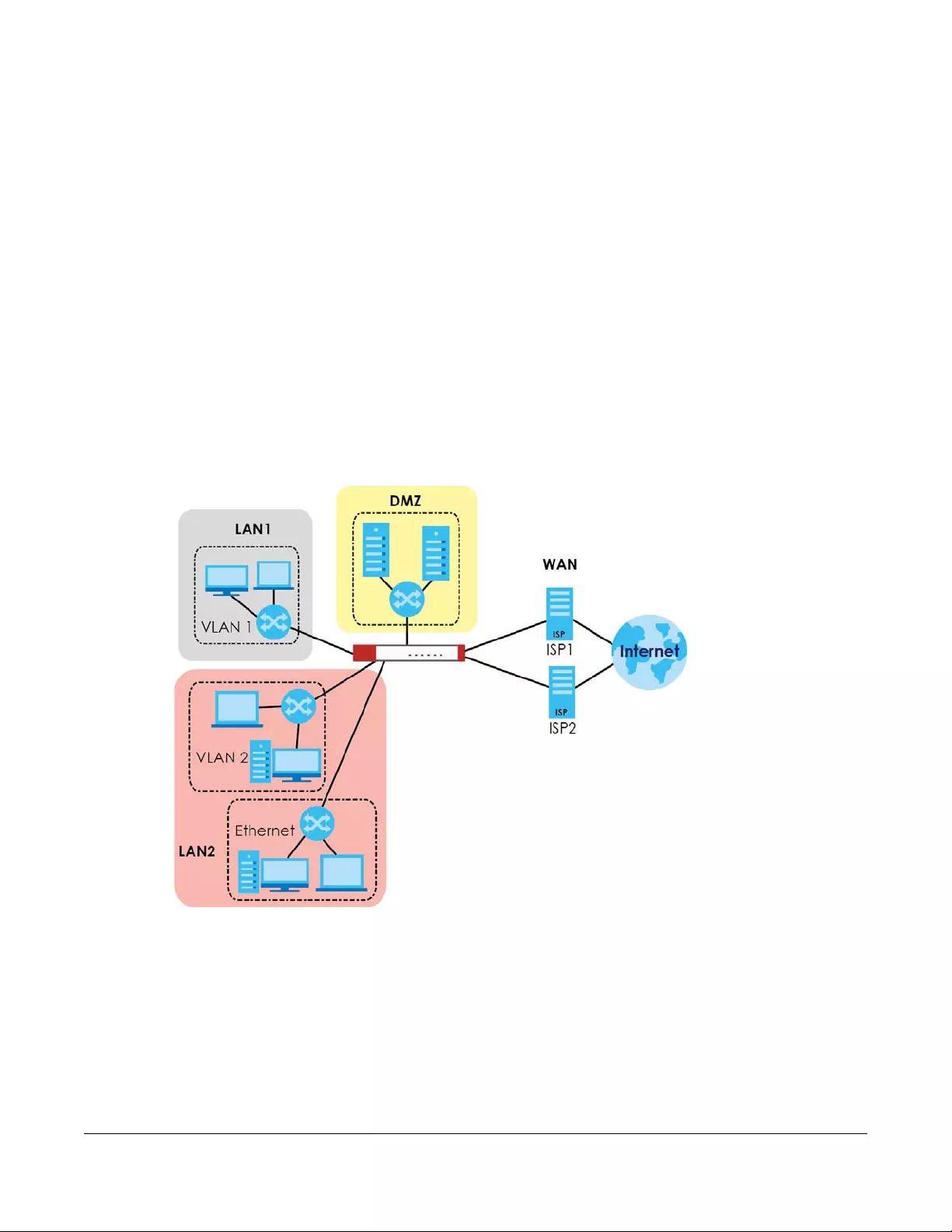
USG/ZyWALL User’s Guide
733
CHAPTER 43
Object
43.1 Zones Overview
Set up zones to configure network security and network policies in the Zyxel Device. A zone is a group of
interfaces and/or VPN tunnels. The Zyxel Device uses zones instead of interfaces in many security and
policy settings, such as Secure Policies rules, UTM Profile, and remote management.
Zones cannot overlap. Each Ethernet interface, VLAN interface, bridge interface, PPPoE/PPTP interface
and VPN tunnel can be assigned to at most one zone. Virtual interfaces are automatically assigned to
the same zone as the interface on which they run.
Figure 511 Example: Zones
Use the Zone screens (see Section 43.8.2 on page 788) to manage the Zyxel Device’s zones.
43.1.1 What You Need to Know
Zones effectively divide traffic into three types--intra-zone traffic, inter-zone traffic, and extra-zone
traffic.
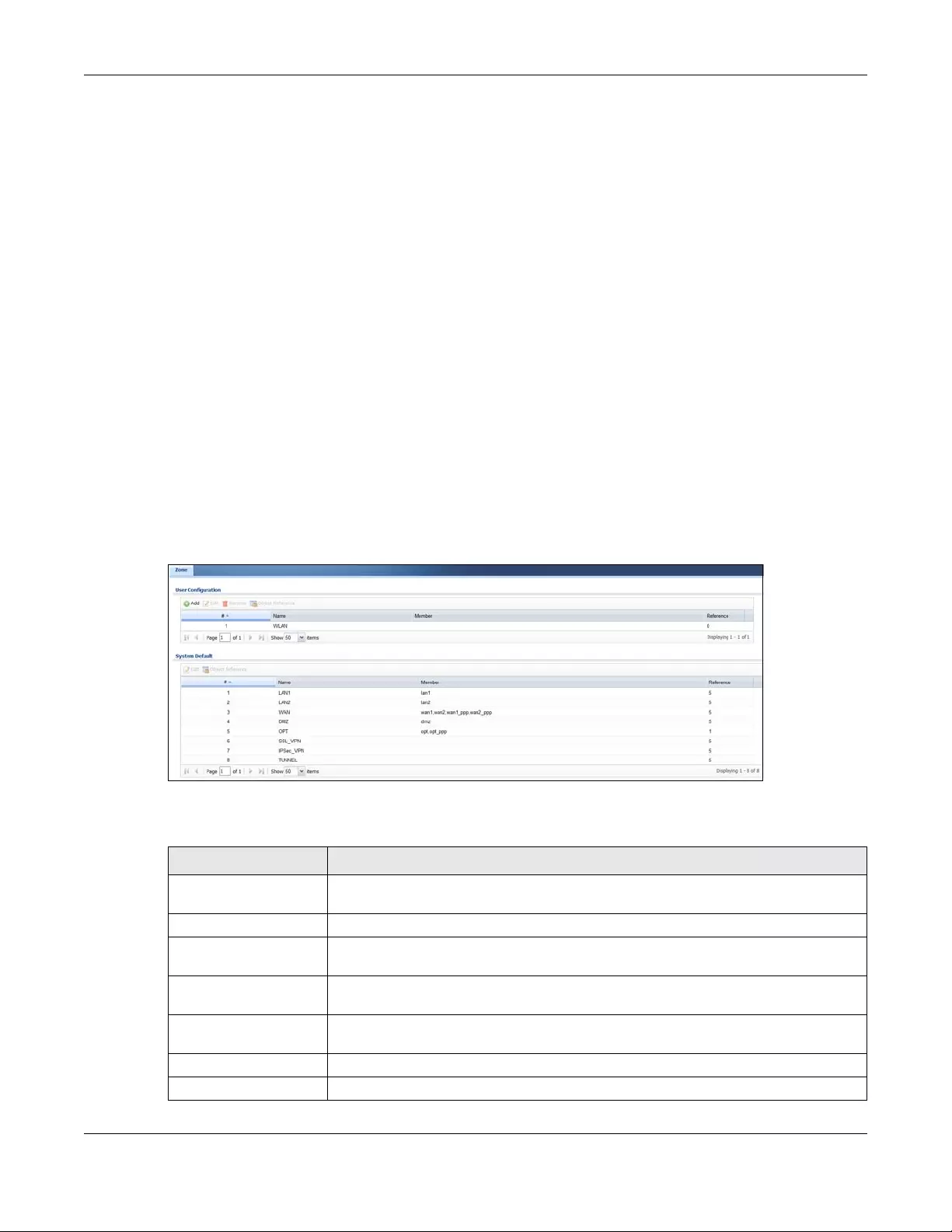
Chapter 43 Object
USG/ZyWALL User’s Guide
734
Intra-zone Traffic
• Intra-zone traffic is traffic between interfaces or VPN tunnels in the same zone. For example, in Figure
511 on page 733, traffic between VLAN 2 and the Ethernet is intra-zone traffic.
Inter-zone Traffic
Inter-zone traffic is traffic between interfaces or VPN tunnels in different zones. For example, in Figure 511
on page 733, traffic between VLAN 1 and the Internet is inter-zone traffic. This is the normal case when
zone-based security and policy settings apply.
Extra-zone Traffic
• Extra-zone traffic is traffic to or from any interface or VPN tunnel that is not assigned to a zone. For
example, in Figure 511 on page 733, traffic to or from computer C is extra-zone traffic.
• Some zone-based security and policy settings may apply to extra-zone traffic, especially if you can
set the zone attribute in them to Any or All. See the specific feature for more information.
43.1.2 The Zone Screen
The Zone screen provides a summary of all zones. In addition, this screen allows you to add, edit, and
remove zones. To access this screen, click Configuration > Object > Zone.
Figure 512 Configuration > Object > Zone
The following table describes the labels in this screen.
Table 281 Configuration > Object > Zone
LABEL DESCRIPTION
User Configuration /
System Default
The Zyxel Device comes with pre-configured System Default zones that you cannot
delete. You can create your own User Configuration zones
Add Click this to create a new, user-configured zone.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify
the entry’s settings.
Remove To remove a user-configured trunk, select it and click Remove. The Zyxel Device
confirms you want to remove it before doing so.
Object References Select an entry and click Object References to open a screen that shows which settings
use the entry. Click Refresh to update information in this screen.
# This field is a sequential value, and it is not associated with any interface.
Name This field displays the name of the zone.
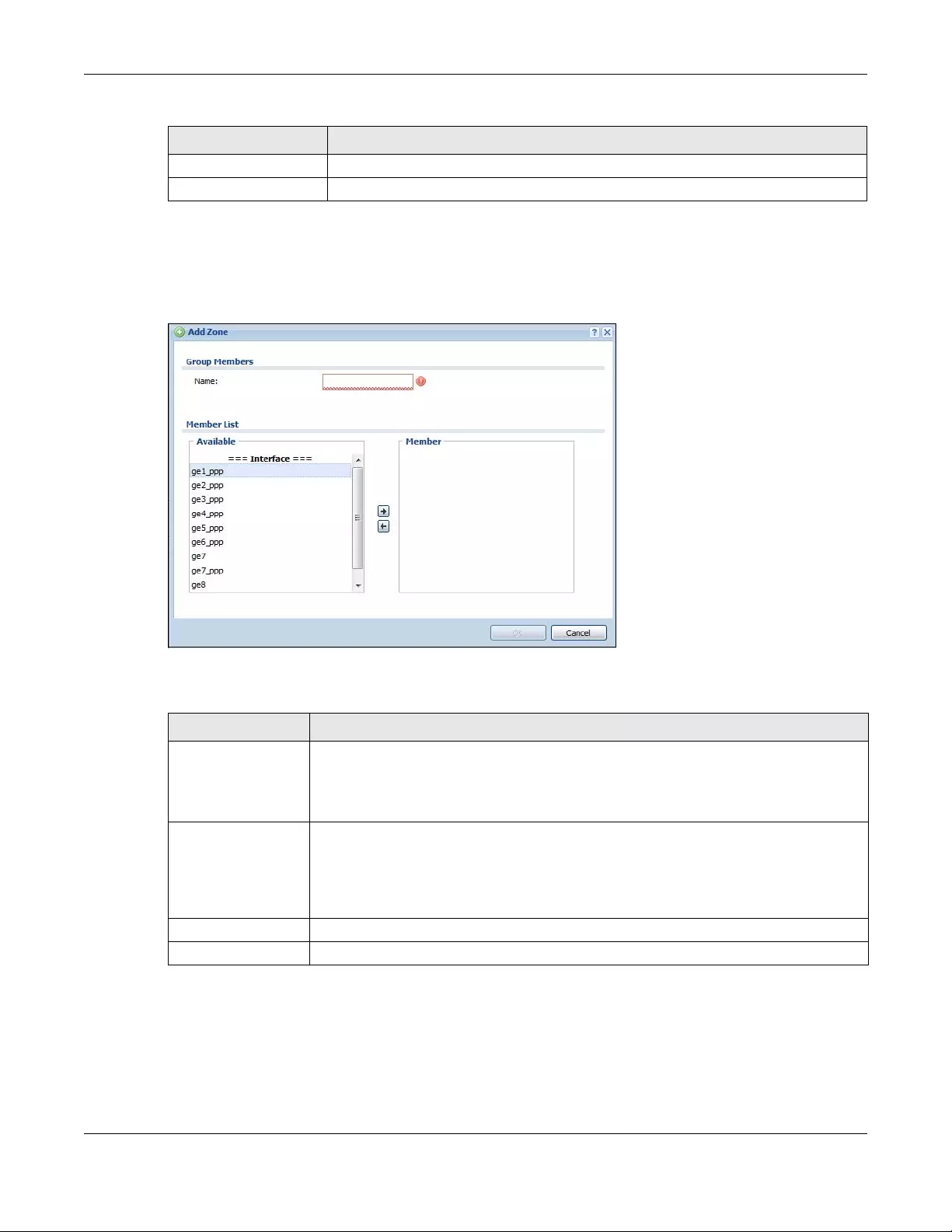
Chapter 43 Object
USG/ZyWALL User’s Guide
735
43.1.2.1 Zone Edit
The Zone Edit screen allows you to add or edit a zone. To access this screen, go to the Zone screen (see
Section 43.8.2 on page 788), and click the Add icon or an Edit icon.
Figure 513 Configuration > Object > Zone > Add
The following table describes the labels in this screen.
Member This field displays the names of the interfaces that belong to each zone.
Reference This field displays the number of times an Object Reference is used in a policy.
Table 281 Configuration > Object > Zone (continued)
LABEL DESCRIPTION
Table 282 Configuration > Object > Zone > Add/Edit
LABEL DESCRIPTION
Name For a system default zone, the name is read only.
For a user-configured zone, type the name used to refer to the zone. You may use 1-31
alphanumeric characters, underscores (_), or dashes (-), but the first character cannot be
a number. This value is case-sensitive.
Member List Available lists the interfaces and VPN tunnels that do not belong to any zone. Select the
interfaces and VPN tunnels that you want to add to the zone you are editing, and click the
right arrow button to add them.
Member lists the interfaces and VPN tunnels that belong to the zone. Select any interfaces
that you want to remove from the zone, and click the left arrow button to remove them.
OK Click OK to save your customized settings and exit this screen.
Cancel Click Cancel to exit this screen without saving.
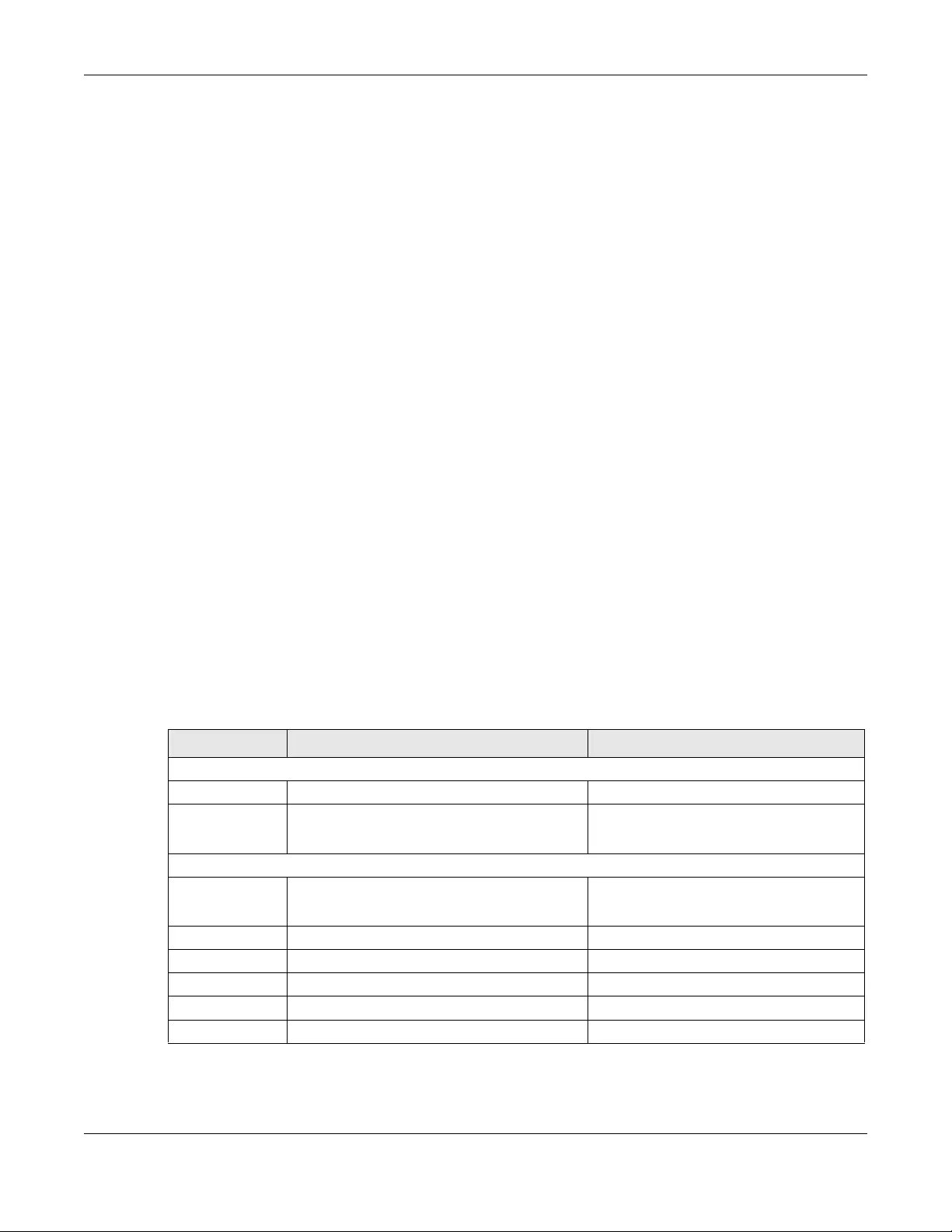
Chapter 43 Object
USG/ZyWALL User’s Guide
736
43.2 User/Group Overview
This section describes how to set up user accounts, user groups, and user settings for the Zyxel Device.
You can also set up rules that control when users have to log in to the Zyxel Device before the Zyxel
Device routes traffic for them.
• The User screen (see Section 43.14.1 on page 827) provides a summary of all user accounts.
• The Group screen (see Section 43.2.3 on page 741) provides a summary of all user groups. In addition,
this screen allows you to add, edit, and remove user groups. User groups may consist of access users
and other user groups. You cannot put admin users in user groups.
•The Setting screen (see Section 43.2.4 on page 743) controls default settings, login settings, lockout
settings, and other user settings for the Zyxel Device. You can also use this screen to specify when
users must log in to the Zyxel Device before it routes traffic for them.
•The MAC Address screen (see Section 43.2.5 on page 747) allows you to configure the MAC
addresses or OUI (Organizationally Unique Identifier) of wireless clients for MAC authentication using
the local user database. The OUI is the first three octets in a MAC address and uniquely identifies the
manufacturer of a network device.
43.2.1 What You Need To Know
User Account
A user account defines the privileges of a user logged into the Zyxel Device. User accounts are used in
security policies and application patrol, in addition to controlling access to configuration and services in
the Zyxel Device.
User Types
These are the types of user accounts the Zyxel Device uses.
Note: The default admin account is always authenticated locally, regardless of the
authentication method setting. (See Chapter 43 on page 801 for more information
about authentication methods.)
Table 283 Types of User Accounts
TYPE ABILITIES LOGIN METHOD(S)
Admin Users
admin Change Zyxel Device configuration (web, CLI) WWW, TELNET, SSH, FTP, Console
limited-admin Look at Zyxel Device configuration (web, CLI)
Perform basic diagnostics (CLI)
WWW, TELNET, SSH, Console
Access Users
user Access network services
Browse user-mode commands (CLI)
WWW, TELNET, SSH
guest Access network services WWW
ext-user External user account WWW
ext-group-user External group user account WWW
guest-manager Create dynamic guest accounts WWW
dynamic-guest Access network services Hotspot Portal

Chapter 43 Object
USG/ZyWALL User’s Guide
737
Ext-User Accounts
Set up an ext-user account if the user is authenticated by an external server and you want to set up
specific policies for this user in the Zyxel Device. If you do not want to set up policies for this user, you do
not have to set up an ext-user account.
All ext-user users should be authenticated by an external server, such as AD, LDAP or RADIUS. If the Zyxel
Device tries to use the local database to authenticate an ext-user, the authentication attempt always
fails. (This is related to AAA servers and authentication methods, which are discussed in those chapters in
this guide.)
Note: If the Zyxel Device tries to authenticate an ext-user using the local database, the
attempt always fails.
Once an ext-user user has been authenticated, the Zyxel Device tries to get the user type (see Table 283
on page 736) from the external server. If the external server does not have the information, the Zyxel
Device sets the user type for this session to User.
For the rest of the user attributes, such as reauthentication time, the Zyxel Device checks the following
places, in order.
1User account in the remote server.
2User account (Ext-User) in the Zyxel Device.
3Default user account for AD users (ad-users), LDAP users (ldap-users) or RADIUS users (radius-users) in
the Zyxel Device.
See Setting up User Attributes in an External Server on page 749 for a list of attributes and how to set up
the attributes in an external server.
Ext-Group-User Accounts
Ext-Group-User accounts work are similar to ext-user accounts but allow you to group users by the value
of the group membership attribute configured for the AD or LDAP server. See Section 43.9.5.1 on page
797 for more on the group membership attribute.
Dynamic-Guest Accounts
Dynamic guest accounts are guest accounts, but are created dynamically and stored in the Zyxel
Device’s local user database. A dynamic guest account has a dynamically-created user name and
password. A dynamic guest account user can access the Zyxel Device’s services only within a given
period of time and will become invalid after the expiration date/time.
There are three types of dynamic guest accounts depending on how they are created or
authenticated: billing-users, ua-users and trial-users.
billing-users are guest account created with the guest manager account or an external printer and
paid by cash or created and paid via the on-line payment service. ua-users are users that log in from
the user agreement page. trial-users are free guest accounts that are created with the Free Time
function.
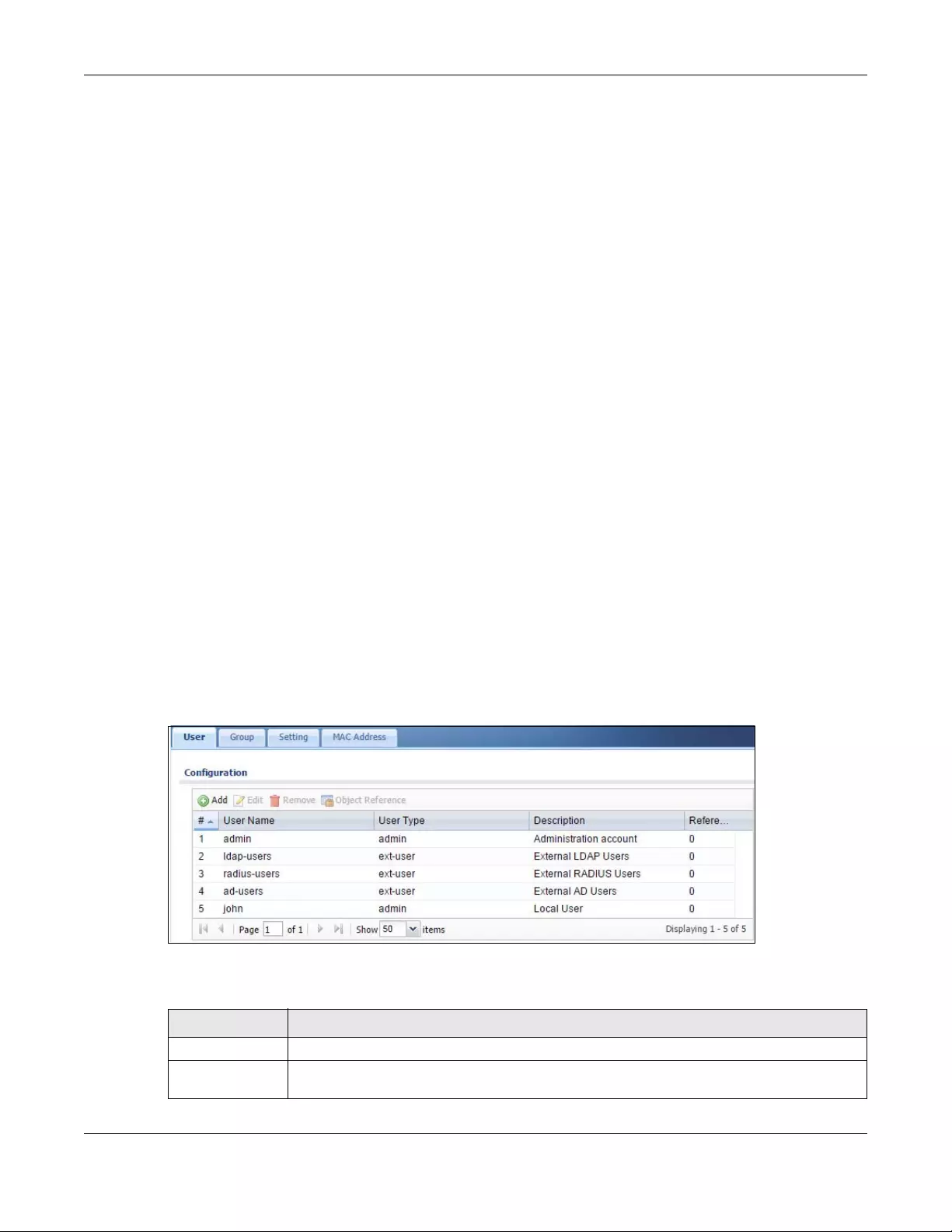
Chapter 43 Object
USG/ZyWALL User’s Guide
738
User Groups
User groups may consist of user accounts or other user groups. Use user groups when you want to create
the same rule for several user accounts, instead of creating separate rules for each one.
Note: You cannot put access users and admin users in the same user group.
Note: You cannot put the default admin account into any user group.
The sequence of members in a user group is not important.
User Awareness
By default, users do not have to log into the Zyxel Device to use the network services it provides. The
Zyxel Device automatically routes packets for everyone. If you want to restrict network services that
certain users can use via the Zyxel Device, you can require them to log in to the Zyxel Device first. The
Zyxel Device is then ‘aware’ of the user who is logged in and you can create ‘user-aware policies’ that
define what services they can use. See Section 43.2.6 on page 748 for a user-aware login example.
Finding Out More
•See Section 43.2.6 on page 748 for some information on users who use an external authentication
server in order to log in.
• The Zyxel Device supports TTLS using PAP so you can use the Zyxel Device’s local user database to
authenticate users with WPA or WPA2 instead of needing an external RADIUS server.
43.2.2 User/Group User Summary Screen
The User screen provides a summary of all user accounts. To access this screen, login to the Web
Configurator, and click Configuration > Object > User/Group.
Figure 514 Configuration > Object > User/Group > User
The following table describes the labels in this screen.
Table 284 Configuration > Object > User/Group > User
LABEL DESCRIPTION
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Chapter 43 Object
USG/ZyWALL User’s Guide
739
43.2.2.1 User Add/Edit Screen
The User Add/Edit screen allows you to create a new user account or edit an existing one.
43.2.2.2 Rules for User Names
Enter a user name from 1 to 31 characters.
The user name can only contain the following characters:
• Alphanumeric A-z 0-9 (there is no unicode support)
• _ [underscores]
• - [dashes]
The first character must be alphabetical (A-Z a-z), an underscore (_), or a dash (-). Other limitations on
user names are:
• User names are case-sensitive. If you enter a user 'bob' but use 'BOB' when connecting via CIFS or FTP,
it will use the account settings used for 'BOB' not ‘bob’.
• User names have to be different than user group names.
• Here are the reserved user names:
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Object
References
Select an entry and click Object References to open a screen that shows which settings use
the entry.
# This field is a sequential value, and it is not associated with a specific user.
User Name This field displays the user name of each user.
User Type This field displays the types of user accounts the Zyxel Device uses:
•admin - this user can look at and change the configuration of the Zyxel Device
•limited-admin - this user can look at the configuration of the Zyxel Device but not to
change it
•dynamic-guest - this user has access to the Zyxel Device’s services but cannot look at the
configuration.
•user - this user has access to the Zyxel Device’s services and can also browse user-mode
commands (CLI).
•guest - this user has access to the Zyxel Device’s services but cannot look at the
configuration
•ext-user - this user account is maintained in a remote server, such as RADIUS or LDAP. See
Ext-User Accounts on page 737 for more information about this type.
•ext-group-user - this user account is maintained in a remote server, such as RADIUS or
LDAP. See Ext-Group-User Accounts on page 737 for more information about this type.
•guest-manager - this user can log in via the web configurator login screen and create
dynamic guest accounts using the Account Generator screen that pops up. See Section
21.4.1 on page 472 for detailed information about the Account Generator screen.
Description This field displays the description for each user.
Reference This displays the number of times an object reference is used in a profile.
Table 284 Configuration > Object > User/Group > User (continued)
LABEL DESCRIPTION
•adm •admin •any •bin •daemon
•debug •devicehaecived•ftp •games •halt
•ldap-users •lp •mail •news •nobody
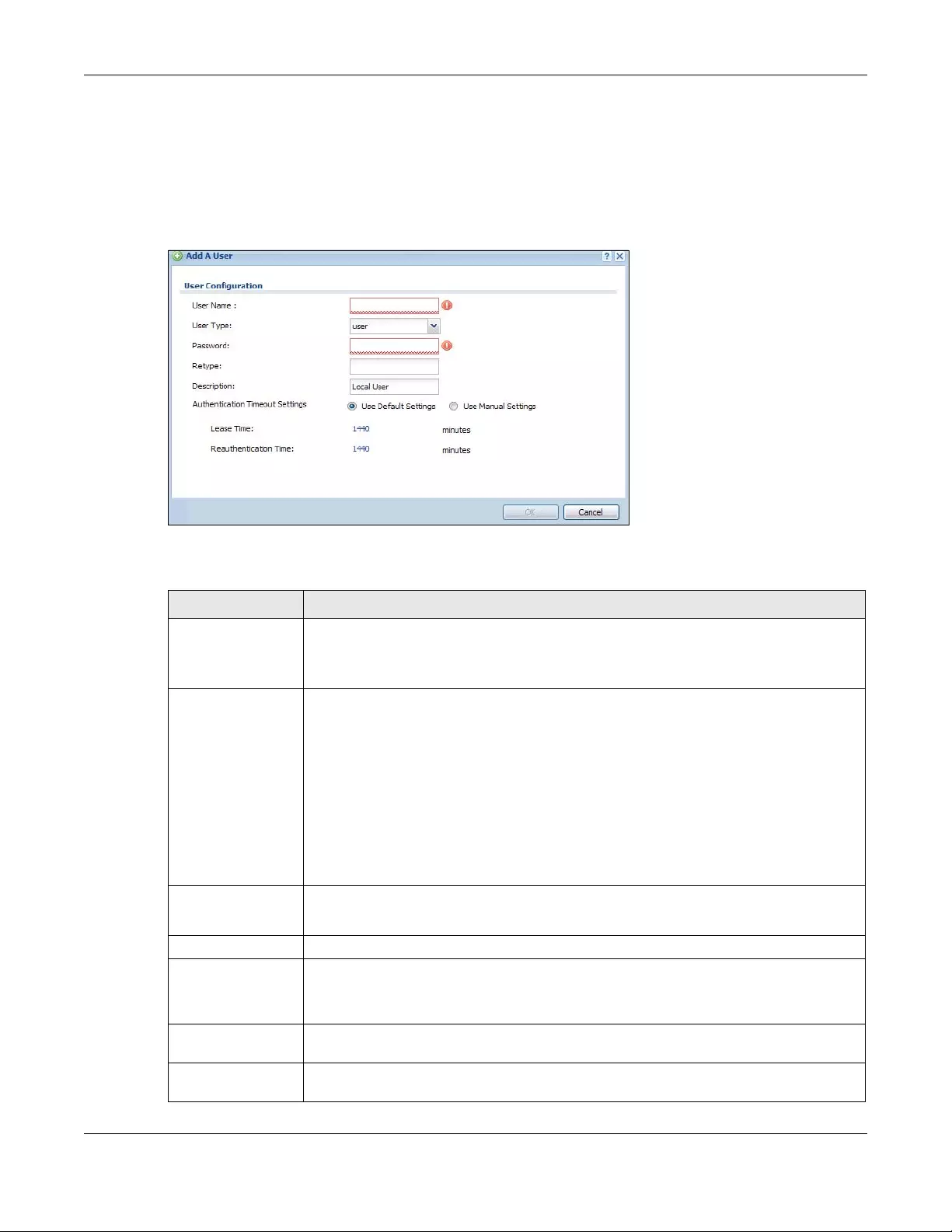
Chapter 43 Object
USG/ZyWALL User’s Guide
740
To access this screen, go to the User screen (see Section 43.14.1 on page 827), and click either the Add
icon or an Edit icon.
Figure 515 Configuration > Object > User/Group > User > Add
The following table describes the labels in this screen.
• operator • radius-users • root • shutdown • sshd
• sync • uucp • zyxel
Table 285 Configuration > Object > User/Group > User > Add
LABEL DESCRIPTION
User Name Type the user name for this user account. You may use 1-31 alphanumeric characters,
underscores(_), or dashes (-), but the first character cannot be a number. This value is case-
sensitive. User names have to be different than user group names, and some words are
reserved. See Section 43.2.2.2 on page 739.
User Type This field displays the types of user accounts the Zyxel Device uses:
•admin - this user can look at and change the configuration of the Zyxel Device
•limited-admin - this user can look at the configuration of the Zyxel Device but not to
change it
•user - this user has access to the Zyxel Device’s services and can also browse user-mode
commands (CLI).
•guest - this user has access to the Zyxel Device’s services but cannot look at the
configuration.
•ext-user - this user account is maintained in a remote server, such as RADIUS or LDAP.
See Ext-User Accounts on page 737 for more information about this type.
•ext-group-user - this user account is maintained in a remote server, such as RADIUS or
LDAP. See Ext-Group-User Accounts on page 737 for more information about this type.
Password This field is not available if you select the ext-user or ext-group-user type.
Enter the password of this user account. It can consist of 4 - 31 alphanumeric characters.
Retype This field is not available if you select the ext-user or ext-group-user type.
Group Identifier This field is available for a ext-group-user type user account.
Specify the value of the AD or LDAP server’s Group Membership Attribute that identifies the
group to which this user belongs.
Associated AAA
Server Object
This field is available for a ext-group-user type user account. Select the AAA server to use to
authenticate this account’s users.
Description Enter the description of each user, if any. You can use up to 60 printable ASCII characters.
Default descriptions are provided.
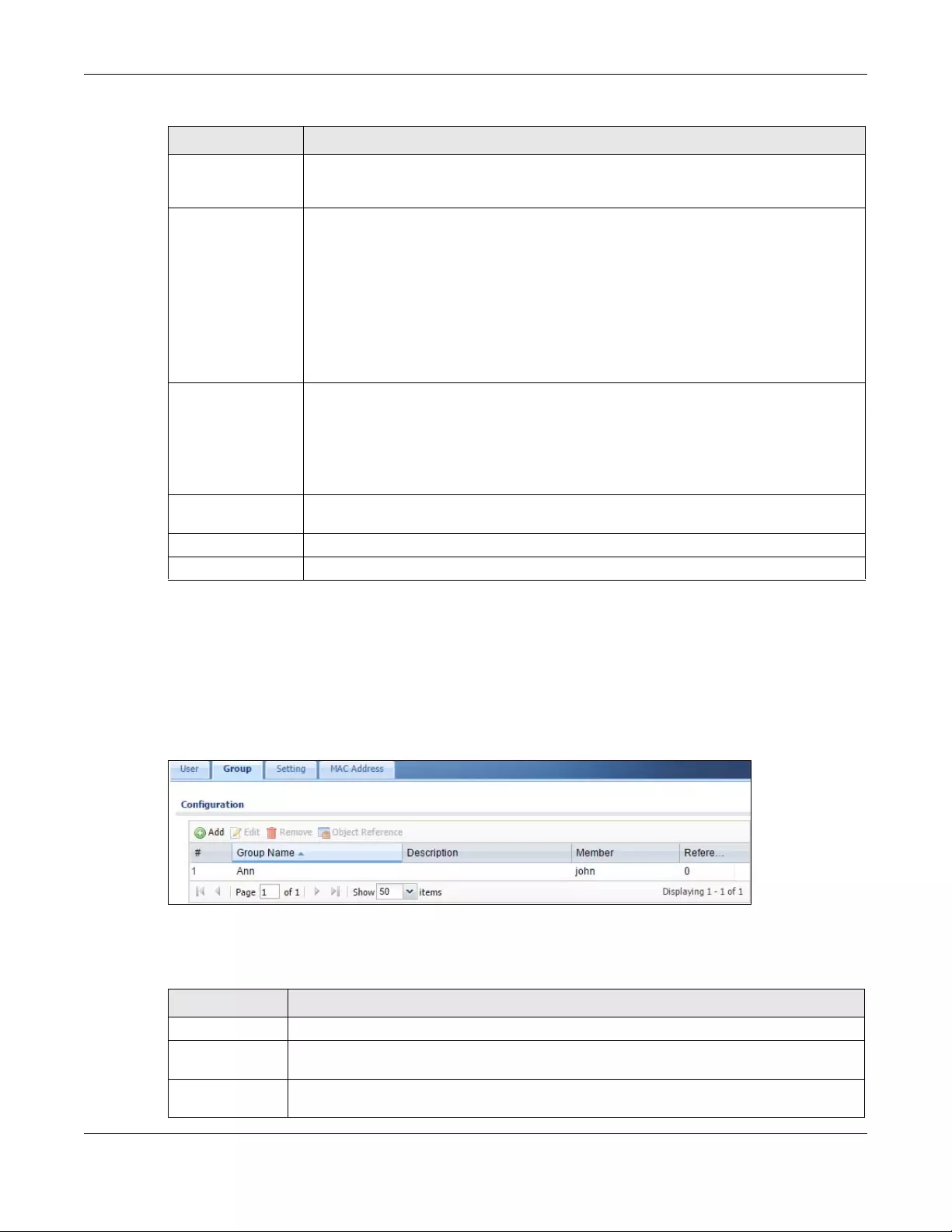
Chapter 43 Object
USG/ZyWALL User’s Guide
741
43.2.3 User/Group Group Summary Screen
User groups consist of access users and other user groups. You cannot put admin users in user groups.
The Group screen provides a summary of all user groups. In addition, this screen allows you to add, edit,
and remove user groups. To access this screen, login to the Web Configurator, and click Configuration >
Object > User/Group > Group.
Figure 516 Configuration > Object > User/Group > Group
The following table describes the labels in this screen. See Section 43.2.3.1 on page 742 for more
information as well.
Authentication
Timeout Settings
If you want the system to use default settings, select Use Default Settings. If you want to set
authentication timeout to a value other than the default settings, select Use Manual Settings
then fill your preferred values in the fields that follow.
Lease Time If you select Use Default Settings in the Authentication Timeout Settings field, the default
lease time is shown.
If you select Use Manual Settings, you need to enter the number of minutes this user has to
renew the current session before the user is logged out. You can specify 1 to 1440 minutes.
You can enter 0 to make the number of minutes unlimited. Admin users renew the session
every time the main screen refreshes in the Web Configurator. Access users can renew the
session by clicking the Renew button on their screen. If you allow access users to renew time
automatically (see Section 43.2.4 on page 743), the users can select this check box on their
screen as well. In this case, the session is automatically renewed before the lease time
expires.
Reauthentication
Time
If you select Use Default Settings in the Authentication Timeout Settings field, the default
lease time is shown.
If you select Use Manual Settings, you need to type the number of minutes this user can be
logged into the Zyxel Device in one session before the user has to log in again. You can
specify 1 to 1440 minutes. You can enter 0 to make the number of minutes unlimited. Unlike
Lease Time, the user has no opportunity to renew the session without logging out.
Configuration
Validation
Use a user account from the group specified above to test if the configuration is correct.
Enter the account’s user name in the User Name field and click Test.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
Table 285 Configuration > Object > User/Group > User > Add (continued)
LABEL DESCRIPTION
Table 286 Configuration > Object > User/Group > Group
LABEL DESCRIPTION
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so. Removing a group does not remove the user accounts in the group.
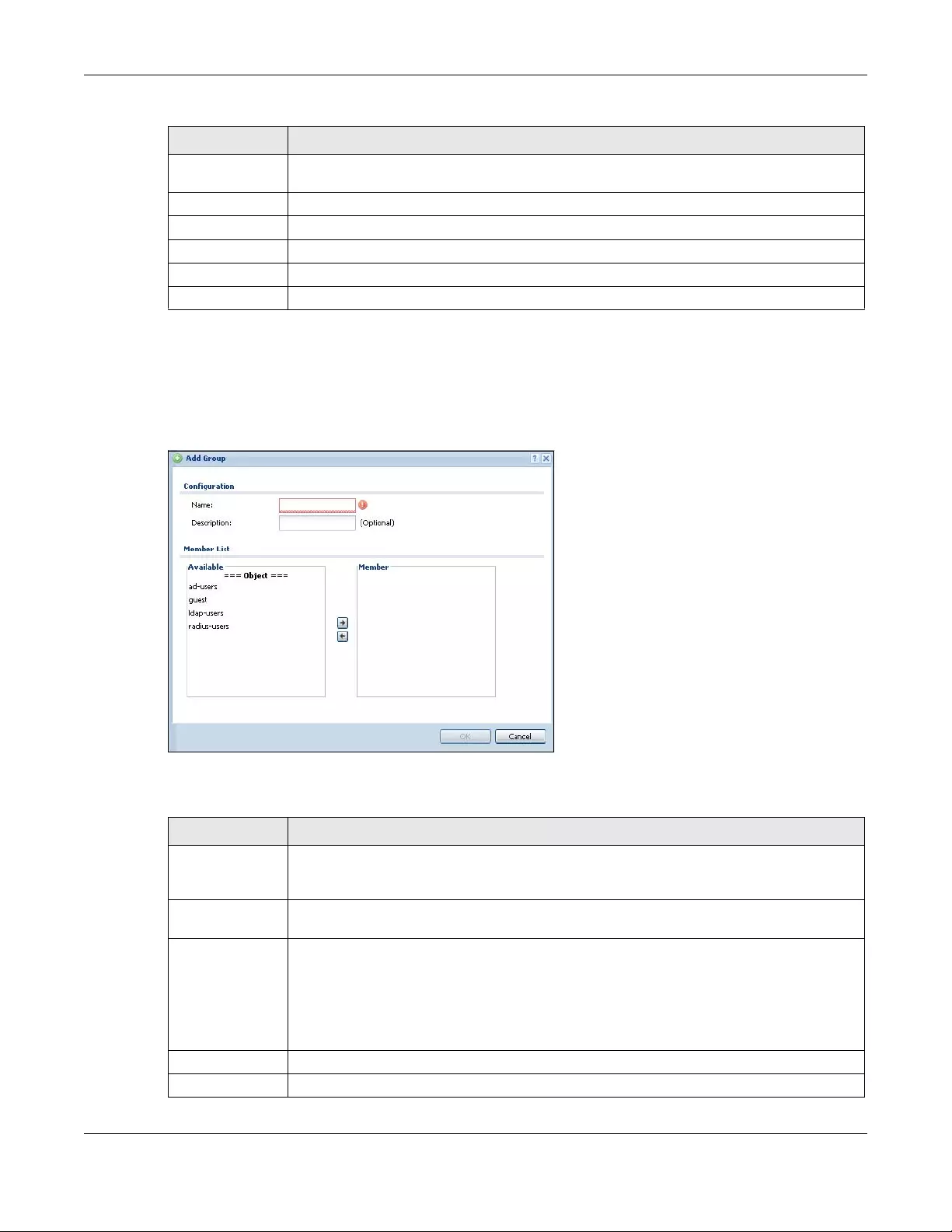
Chapter 43 Object
USG/ZyWALL User’s Guide
742
43.2.3.1 Group Add/Edit Screen
The Group Add/Edit screen allows you to create a new user group or edit an existing one. To access this
screen, go to the Group screen (see Section 43.2.3 on page 741), and click either the Add icon or an
Edit icon.
Figure 517 Configuration > Object > User/Group > Group > Add
The following table describes the labels in this screen.
Object
References
Select an entry and click Object References to open a screen that shows which settings use
the entry.
# This field is a sequential value, and it is not associated with a specific user group.
Group Name This field displays the name of each user group.
Description This field displays the description for each user group.
Member This field lists the members in the user group. Each member is separated by a comma.
Reference This displays the number of times an object reference is used in a profile.
Table 286 Configuration > Object > User/Group > Group (continued)
LABEL DESCRIPTION
Table 287 Configuration > Object > User/Group > Group > Add
LABEL DESCRIPTION
Name Type the name for this user group. You may use 1-31 alphanumeric characters,
underscores(_), or dashes (-), but the first character cannot be a number. This value is case-
sensitive. User group names have to be different than user names.
Description Enter the description of the user group, if any. You can use up to 60 characters, punctuation
marks, and spaces.
Member List The Member list displays the names of the users and user groups that have been added to the
user group. The order of members is not important. Select users and groups from the Available
list that you want to be members of this group and move them to the Member list. You can
double-click a single entry to move it or use the [Shift] or [Ctrl] key to select multiple entries and
use the arrow button to move them.
Move any members you do not want included to the Available list.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
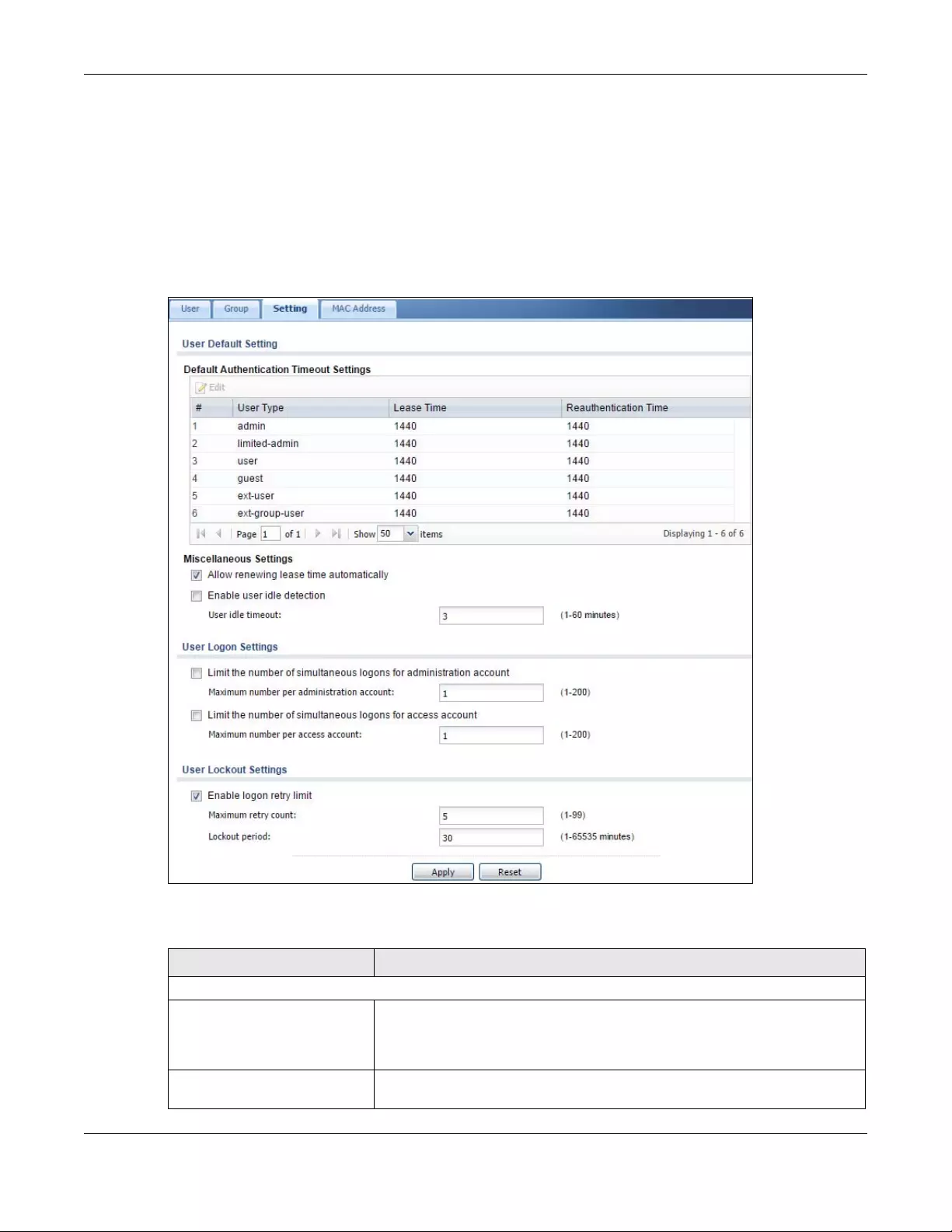
Chapter 43 Object
USG/ZyWALL User’s Guide
743
43.2.4 User/Group Setting Screen
The Setting screen controls default settings, login settings, lockout settings, and other user settings for the
Zyxel Device. You can also use this screen to specify when users must log in to the Zyxel Device before it
routes traffic for them.
To access this screen, login to the Web Configurator, and click Configuration > Object > User/Group >
Setting.
Figure 518 Configuration > Object > User/Group > Setting
The following table describes the labels in this screen.
Table 288 Configuration > Object > User/Group > Setting
LABEL DESCRIPTION
User Authentication Timeout Settings
Default Authentication Timeout
Settings
These authentication timeout settings are used by default when you create a
new user account. They also control the settings for any existing user accounts
that are set to use the default settings. You can still manually configure any user
account’s authentication timeout settings.
Edit Double-click an entry or select it and click Edit to open a screen where you can
modify the entry’s settings.
Chapter 43 Object
USG/ZyWALL User’s Guide
744
# This field is a sequential value, and it is not associated with a specific entry.
User Type These are the kinds of user account the Zyxel Device supports.
•admin - this user can look at and change the configuration of the Zyxel
Device
•limited-admin - this user can look at the configuration of the Zyxel Device
but not to change it
•user - this user has access to the Zyxel Device’s services but cannot look at
the configuration
•guest - this user has access to the Zyxel Device’s services but cannot look
at the configuration
•ext-user - this user account is maintained in a remote server, such as RADIUS
or LDAP. See Ext-User Accounts on page 737 for more information about this
type.
•ext-group-user - this user account is maintained in a remote server, such as
RADIUS or LDAP. See Ext-Group-User Accounts on page 737 for more
information about this type.
Lease Time This is the default lease time in minutes for each type of user account. It defines
the number of minutes the user has to renew the current session before the user
is logged out.
Admin users renew the session every time the main screen refreshes in the Web
Configurator. Access users can renew the session by clicking the Renew button
on their screen. If you allow access users to renew time automatically (see
Section 43.2.4 on page 743), the users can select this check box on their screen
as well. In this case, the session is automatically renewed before the lease time
expires.
Reauthentication Time This is the default reauthentication time in minutes for each type of user
account. It defines the number of minutes the user can be logged into the Zyxel
Device in one session before having to log in again. Unlike Lease Time, the user
has no opportunity to renew the session without logging out.
Miscellaneous Settings
Allow renewing lease time
automatically Select this check box if access users can renew lease time automatically, as well
as manually, simply by selecting the Updating lease time automatically check
box on their screen.
Enable user idle detection This is applicable for access users.
Select this check box if you want the Zyxel Device to monitor how long each
access user is logged in and idle (in other words, there is no traffic for this access
user). The Zyxel Device automatically logs out the access user once the User idle
timeout has been reached.
User idle timeout This is applicable for access users.
This field is effective when Enable user idle detection is checked. Type the
number of minutes each access user can be logged in and idle before the Zyxel
Device automatically logs out the access user.
User Logon Settings
Limit the number of
simultaneous logons for
administration account
Select this check box if you want to set a limit on the number of simultaneous
logins by admin users. If you do not select this, admin users can login as many
times as they want at the same time using the same or different IP addresses.
Maximum number per
administration account This field is effective when Limit ... for administration account is checked. Type
the maximum number of simultaneous logins by each admin user.
Limit the number of
simultaneous logons for
access account
Select this check box if you want to set a limit on the number of simultaneous
logins by non-admin users. If you do not select this, access users can login as
many times as they want as long as they use different IP addresses.
Maximum number per
access account This field is effective when Limit ... for access account is checked. Type the
maximum number of simultaneous logins by each access user.
Table 288 Configuration > Object > User/Group > Setting (continued)
LABEL DESCRIPTION
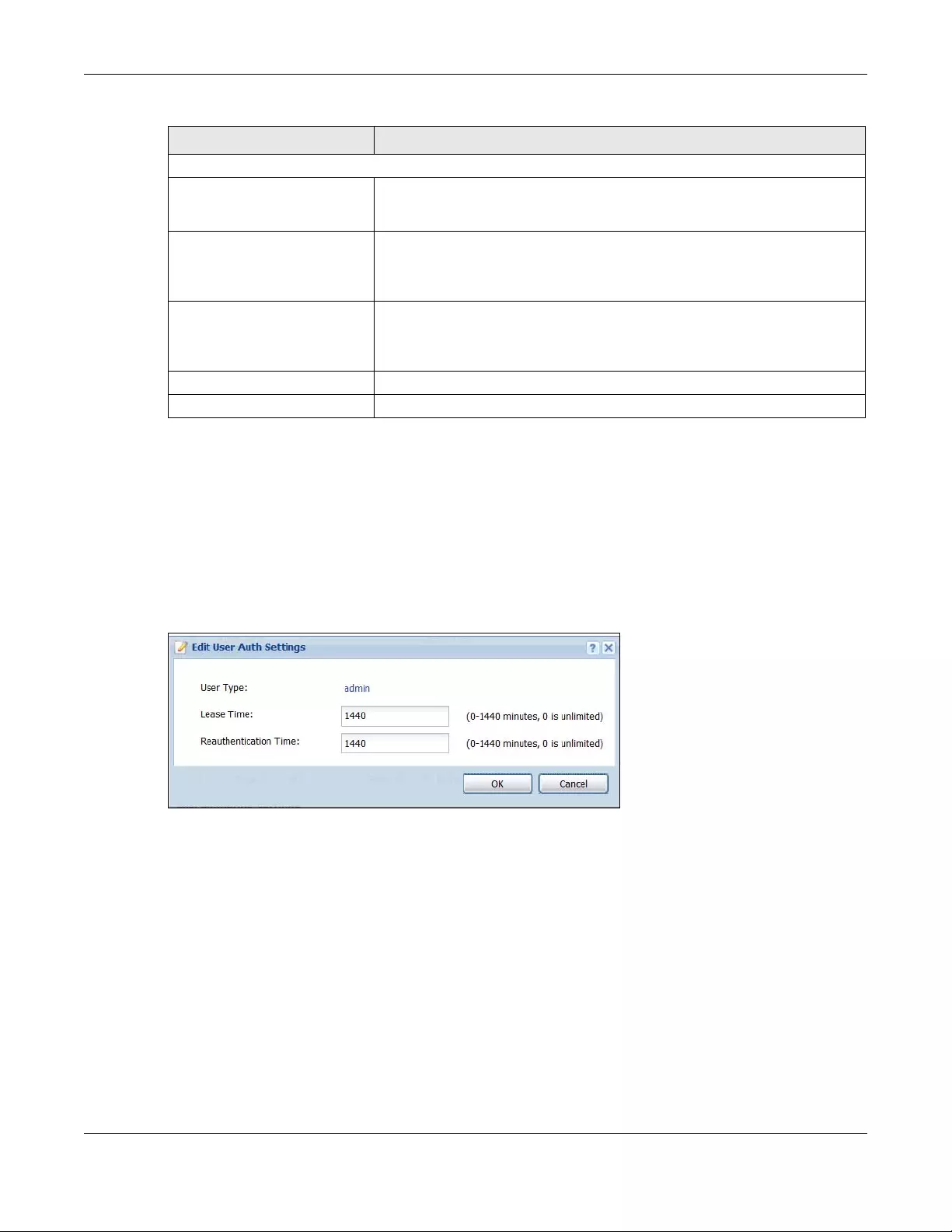
Chapter 43 Object
USG/ZyWALL User’s Guide
745
43.2.4.1 Default User Authentication Timeout Settings Edit Screens
The Default Authentication Timeout Settings Edit screen allows you to set the default authentication
timeout settings for the selected type of user account. These default authentication timeout settings
also control the settings for any existing user accounts that are set to use the default settings. You can
still manually configure any user account’s authentication timeout settings.
To access this screen, go to the Configuration > Object > User/Group > Setting screen (see Section 43.2.4
on page 743), and click one of the Default Authentication Timeout Settings section’s Edit icons.
Figure 519 Configuration > Object > User/Group > Setting > Edit
User Lockout Settings
Enable logon retry limit Select this check box to set a limit on the number of times each user can login
unsuccessfully (for example, wrong password) before the IP address is locked
out for a specified amount of time.
Maximum retry count This field is effective when Enable logon retry limit is checked. Type the
maximum number of times each user can login unsuccessfully before the IP
address is locked out for the specified lockout period. The number must be
between 1 and 99.
Lockout period This field is effective when Enable logon retry limit is checked. Type the number
of minutes the user must wait to try to login again, if logon retry limit is enabled
and the maximum retry count is reached. This number must be between 1 and
65,535 (about 45.5 days).
Apply Click Apply to save the changes.
Reset Click Reset to return the screen to its last-saved settings.
Table 288 Configuration > Object > User/Group > Setting (continued)
LABEL DESCRIPTION
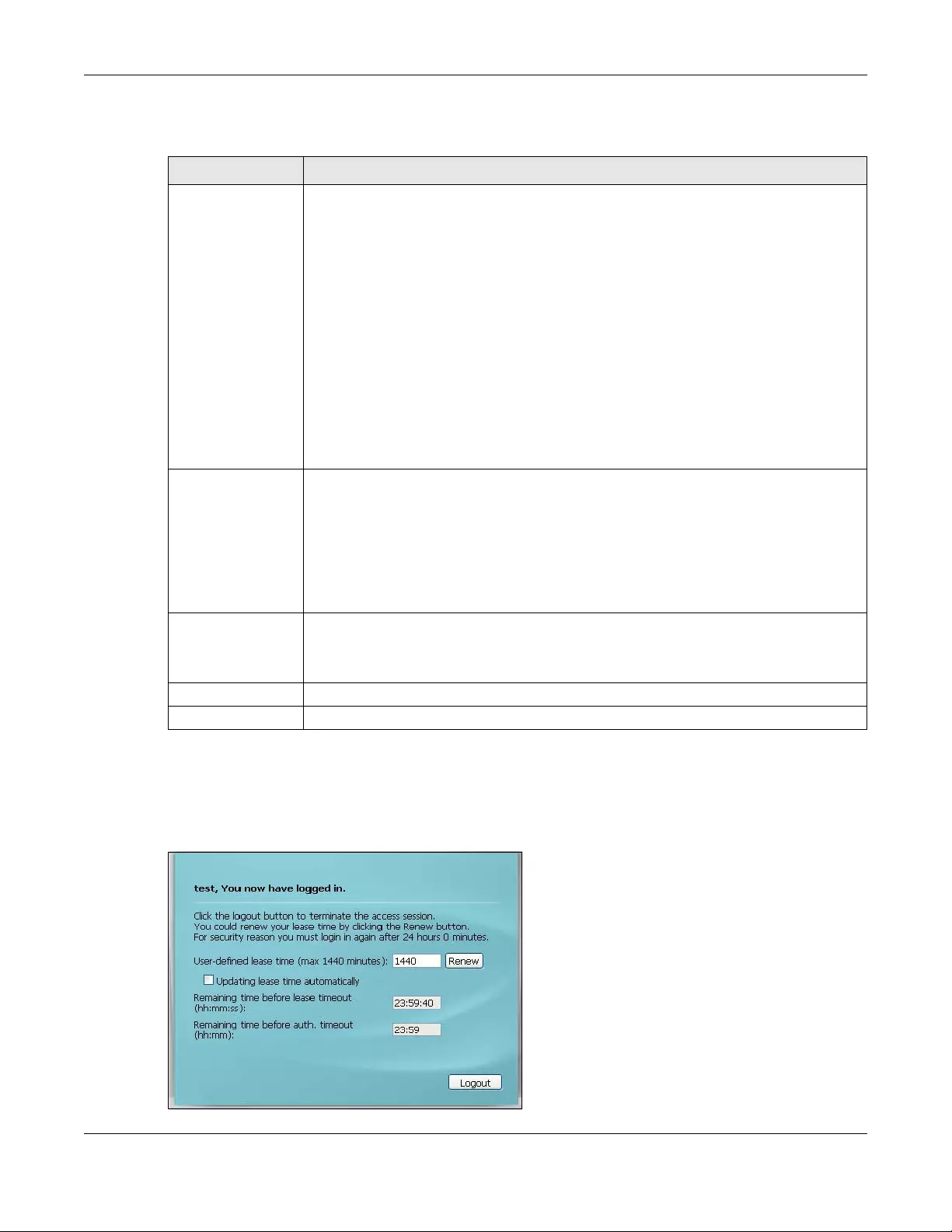
Chapter 43 Object
USG/ZyWALL User’s Guide
746
The following table describes the labels in this screen.
43.2.4.2 User Aware Login Example
Access users cannot use the Web Configurator to browse the configuration of the Zyxel Device. Instead,
after access users log into the Zyxel Device, the following screen appears.
Figure 520 Web Configurator for Non-Admin Users
Table 289 Configuration > Object > User/Group > Setting > Edit
LABEL DESCRIPTION
User Type This read-only field identifies the type of user account for which you are configuring the
default settings.
•admin - this user can look at and change the configuration of the Zyxel Device
•limited-admin - this user can look at the configuration of the Zyxel Device but not to
change it.
•dynamic-guest - this user has access to the Zyxel Device’s services but cannot look at
the configuration.
•user - this user has access to the Zyxel Device’s services but cannot look at the
configuration.
•guest - this user has access to the Zyxel Device’s services but cannot look at the
configuration.
•ext-user - this user account is maintained in a remote server, such as RADIUS or LDAP.
See Ext-User Accounts on page 737 for more information about this type.
•ext-group-user - this user account is maintained in a remote server, such as RADIUS or
LDAP. See Ext-Group-User Accounts on page 737 for more information about this type.
•guest-manager - this user can log in via the web configurator login screen and create
dynamic guest accounts using the Account Generator screen that pops up. See Section
21.4.1 on page 472 for detailed information about the Account Generator screen.
Lease Time Enter the number of minutes this type of user account has to renew the current session
before the user is logged out. You can specify 1 to 1440 minutes. You can enter 0 to make
the number of minutes unlimited.
Admin users renew the session every time the main screen refreshes in the Web
Configurator. Access users can renew the session by clicking the Renew button on their
screen. If you allow access users to renew time automatically (see Section 43.2.4 on page
743), the users can select this check box on their screen as well. In this case, the session is
automatically renewed before the lease time expires.
Reauthentication
Time
Type the number of minutes this type of user account can be logged into the Zyxel Device in
one session before the user has to log in again. You can specify 1 to 1440 minutes. You can
enter 0 to make the number of minutes unlimited. Unlike Lease Time, the user has no
opportunity to renew the session without logging out.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
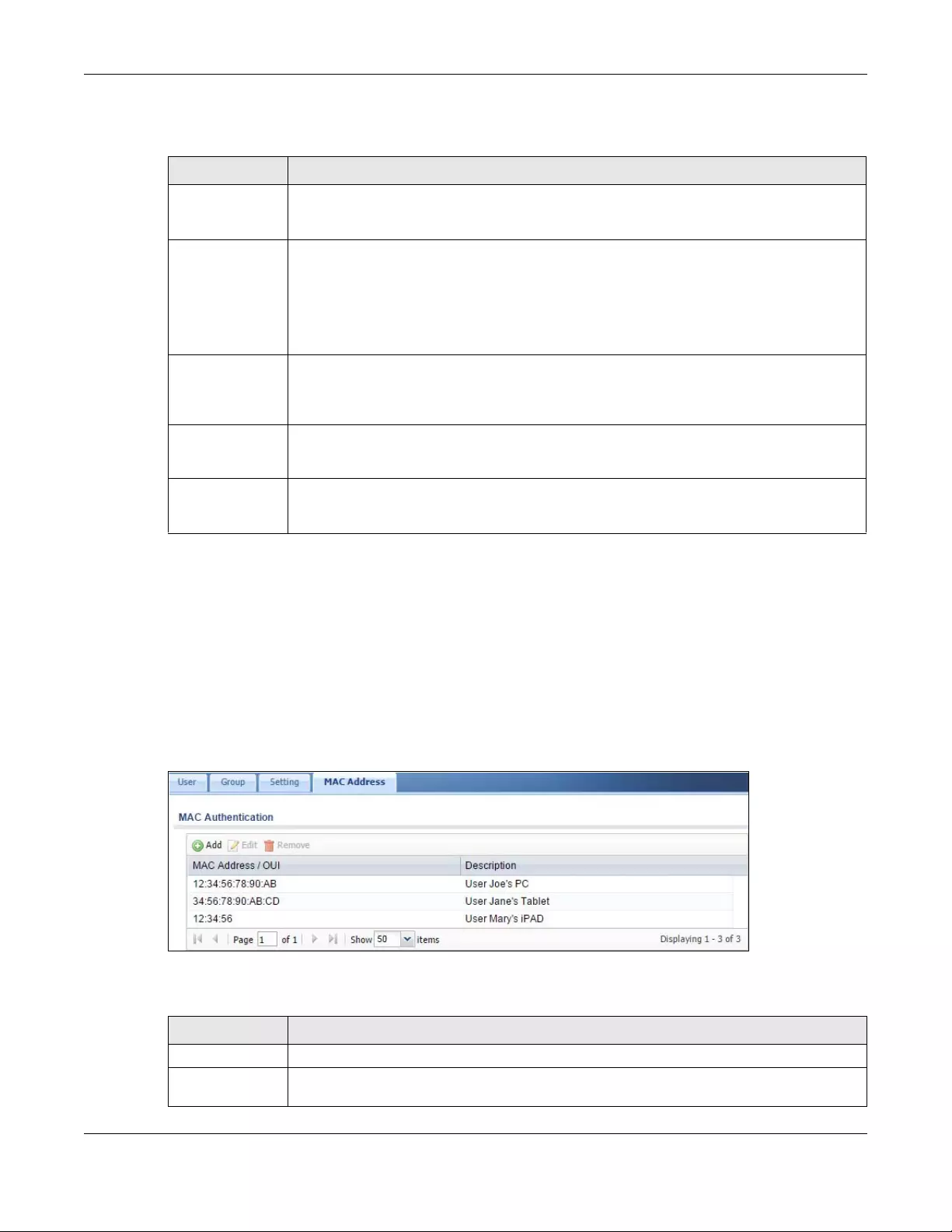
Chapter 43 Object
USG/ZyWALL User’s Guide
747
The following table describes the labels in this screen.
43.2.5 User/Group MAC Address Summary Screen
This screen shows the MAC addresses of wireless clients, which can be authenticated by their MAC
addresses using the local user database. Click Configuration > Object > User/Group > MAC Address to
open this screen.
Note: You need to configure an SSID security profile’s MAC authentication settings to have
the AP use the Zyxel Device’s local database to authenticate wireless clients by their
MAC addresses.
Figure 521 Configuration > Object > User/Group > MAC Address
The following table describes the labels in this screen.
Table 290 Web Configurator for Non-Admin Users
LABEL DESCRIPTION
User-defined
lease time (max
... minutes)
Access users can specify a lease time shorter than or equal to the one that you specified. The
default value is the lease time that you specified.
Renew Access users can click this button to reset the lease time, the amount of time remaining before
the Zyxel Device automatically logs them out. The Zyxel Device sets this amount of time
according to the
•User-defined lease time field in this screen
•Lease time field in the User Add/Edit screen (see Section 43.2.5.1 on page 748)
•Lease time field in the Setting screen (see Section 43.2.4 on page 743)
Updating lease
time
automatically
This box appears if you checked the Allow renewing lease time automatically box in the
Setting screen. (See Section 43.2.4 on page 743.) Access users can select this check box to
reset the lease time automatically 30 seconds before it expires. Otherwise, access users have
to click the Renew button to reset the lease time.
Remaining time
before lease
timeout
This field displays the amount of lease time that remains, though the user might be able to reset
it.
Remaining time
before auth.
timeout
This field displays the amount of time that remains before the Zyxel Device automatically logs
the access user out, regardless of the lease time.
Table 291 Configuration > Object > User/Group > MAC Address
LABEL DESCRIPTION
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
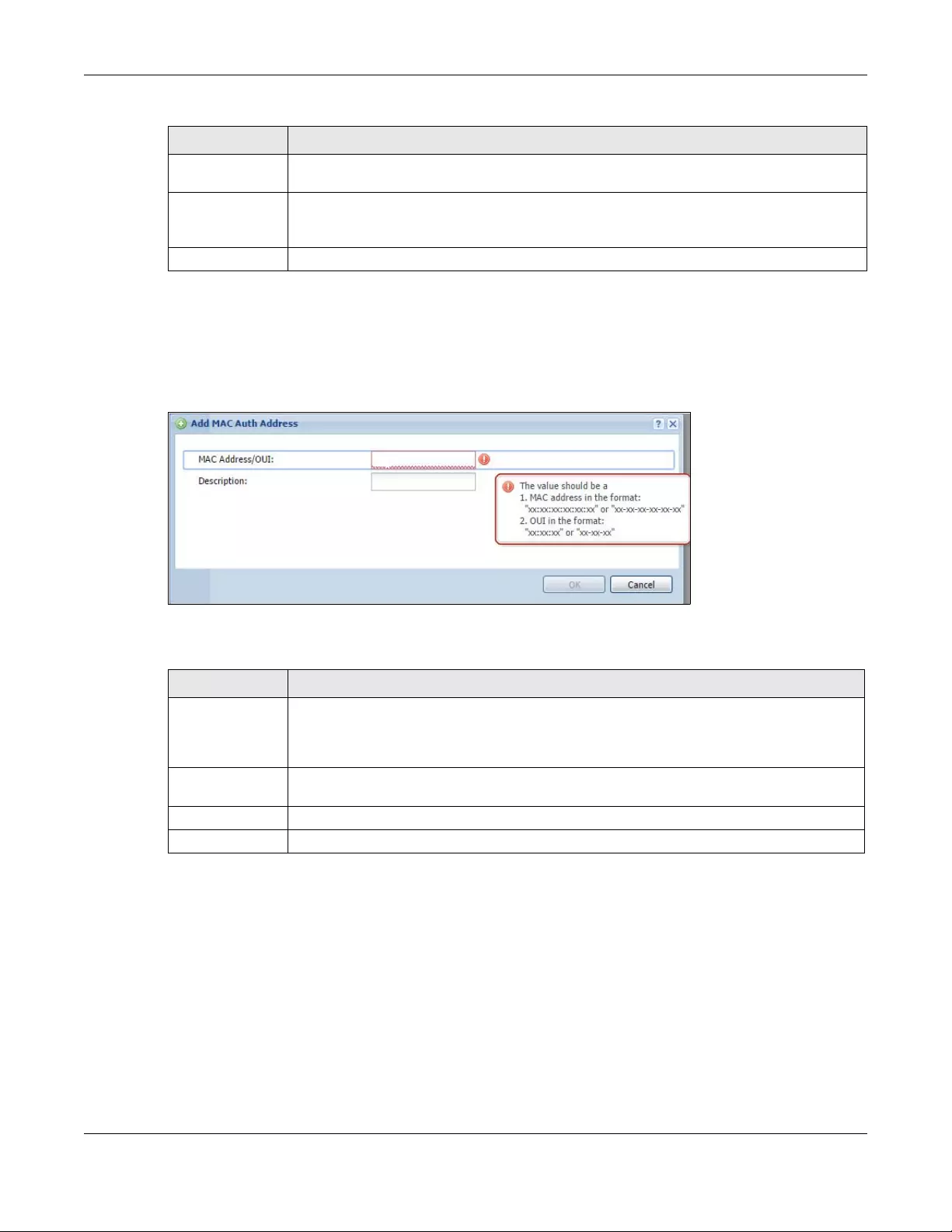
Chapter 43 Object
USG/ZyWALL User’s Guide
748
43.2.5.1 MAC Address Add/Edit Screen
This screen allows you to create a new allowed device or edit an existing one. To access this screen, go
to the MAC Address screen (see Section 43.2.5 on page 747), and click either the Add icon or an Edit
icon.
Figure 522 Configuration > Object > User/Group > MAC Address > Add
The following table describes the labels in this screen.
43.2.6 User /Group Technical Reference
This section provides some information on users who use an external authentication server in order to log
in.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
MAC Address/
OUI
This field displays the MAC address or OUI (Organizationally Unique Identifier of computer
hardware manufacturers) of wireless clients using MAC authentication with the Zyxel Device
local user database.
Description This field displays a description of the device identified by the MAC address or OUI.
Table 291 Configuration > Object > User/Group > MAC Address (continued)
LABEL DESCRIPTION
Table 292 Configuration > Object > User/Group > MAC Address > Add
LABEL DESCRIPTION
MAC Address/
OUI
Type the MAC address (six hexadecimal number pairs separated by colons or hyphens) or OUI
(three hexadecimal number pairs separated by colons or hyphens) to identify specific wireless
clients for MAC authentication using the Zyxel Device local user database. The OUI is the first
three octets in a MAC address and uniquely identifies the manufacturer of a network device.
Description Enter an optional description of the wireless device(s) identified by the MAC or OUI. You can
use up to 60 characters, punctuation marks, and spaces.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
Chapter 43 Object
USG/ZyWALL User’s Guide
749
Setting up User Attributes in an External Server
To set up user attributes, such as reauthentication time, in LDAP or RADIUS servers, use the following
keywords in the user configuration file.
The following examples show you how you might set up user attributes in LDAP and RADIUS servers.
Creating a Large Number of Ext-User Accounts
If you plan to create a large number of Ext-User accounts, you might use CLI commands, instead of the
Web Configurator, to create the accounts. Extract the user names from the LDAP or RADIUS server, and
create a shell script that creates the user accounts.
43.3 AP Profile Overview
This section shows you how to configure preset profiles for the Access Points (APs) connected to your
Zyxel Device’s wireless network.
• The Radio screen (Section 43.3.1 on page 750) creates radio configurations that can be used by the
APs.
• The SSID screen (Section 43.3.2 on page 756) configures three different types of profiles for your
networked APs.
43.3.0.1 What You Need To Know
The following terms and concepts may help as you read this section.
Wireless Profiles
At the heart of all wireless AP configurations on the Zyxel Device are profiles. A profile represents a group
of saved settings that you can use across any number of connected APs. You can set up the following
wireless profile types:
Table 293 LDAP/RADIUS: Keywords for User Attributes
KEYWORD CORRESPONDING ATTRIBUTE IN WEB CONFIGURATOR
type User Type. Possible Values: admin, limited-admin, dynamic-guest, user, guest.
leaseTime Lease Time. Possible Values: 1-1440 (minutes).
reauthTime Reauthentication Time. Possible Values: 1-1440 (minutes).
Figure 523 LDAP Example: Keywords for User Attributes
type: admin
leaseTime: 99
reauthTime: 199
Figure 524 RADIUS Example: Keywords for User Attributes
type=user;leaseTime=222;reauthTime=222

Chapter 43 Object
USG/ZyWALL User’s Guide
750
•Radio - This profile type defines the properties of an AP’s radio transmitter. You can have a maximum
of 32 radio profiles on the Zyxel Device.
•SSID - This profile type defines the properties of a single wireless network signal broadcast by an AP.
Each radio on a single AP can broadcast up to 8 SSIDs. You can have a maximum of 32 SSID profiles
on the Zyxel Device.
•Security - This profile type defines the security settings used by a single SSID. It controls the encryption
method required for a wireless client to associate itself with the SSID. You can have a maximum of 32
security profiles on the Zyxel Device.
•MAC Filtering - This profile provides an additional layer of security for an SSID, allowing you to block
access or allow access to that SSID based on wireless client MAC addresses. If a client’s MAC address
is on the list, then it is either allowed or denied, depending on how you set up the MAC Filter profile.
You can have a maximum of 32 MAC filtering profiles on the Zyxel Device.
SSID
The SSID (Service Set IDentifier) is the name that identifies the Service Set with which a wireless station is
associated. Wireless stations associating to the access point (AP) must have the same SSID. In other
words, it is the name of the wireless network that clients use to connect to it.
WEP
WEP (Wired Equivalent Privacy) encryption scrambles all data packets transmitted between the AP and
the wireless stations associated with it in order to keep network communications private. Both the
wireless stations and the access points must use the same WEP key for data encryption and decryption.
WPA and WPA2
Wi-Fi Protected Access (WPA) is a subset of the IEEE 802.11i standard. WPA2 (IEEE 802.11i) is a wireless
security standard that defines stronger encryption, authentication and key management than WPA.
Key differences between WPA(2) and WEP are improved data encryption and user authentication.
IEEE 802.1x
The IEEE 802.1x standard outlines enhanced security methods for both the authentication of wireless
stations and encryption key management. Authentication is done using an external RADIUS server.
43.3.1 Radio Screen
This screen allows you to create radio profiles for the APs on your network. A radio profile is a list of
settings that a supported managed AP (NWA5121-N for example) can use to configure either one of its
two radio transmitters. To access this screen click Configuration > Object > AP Profile.
Note: You can have a maximum of 32 radio profiles on the Zyxel Device.
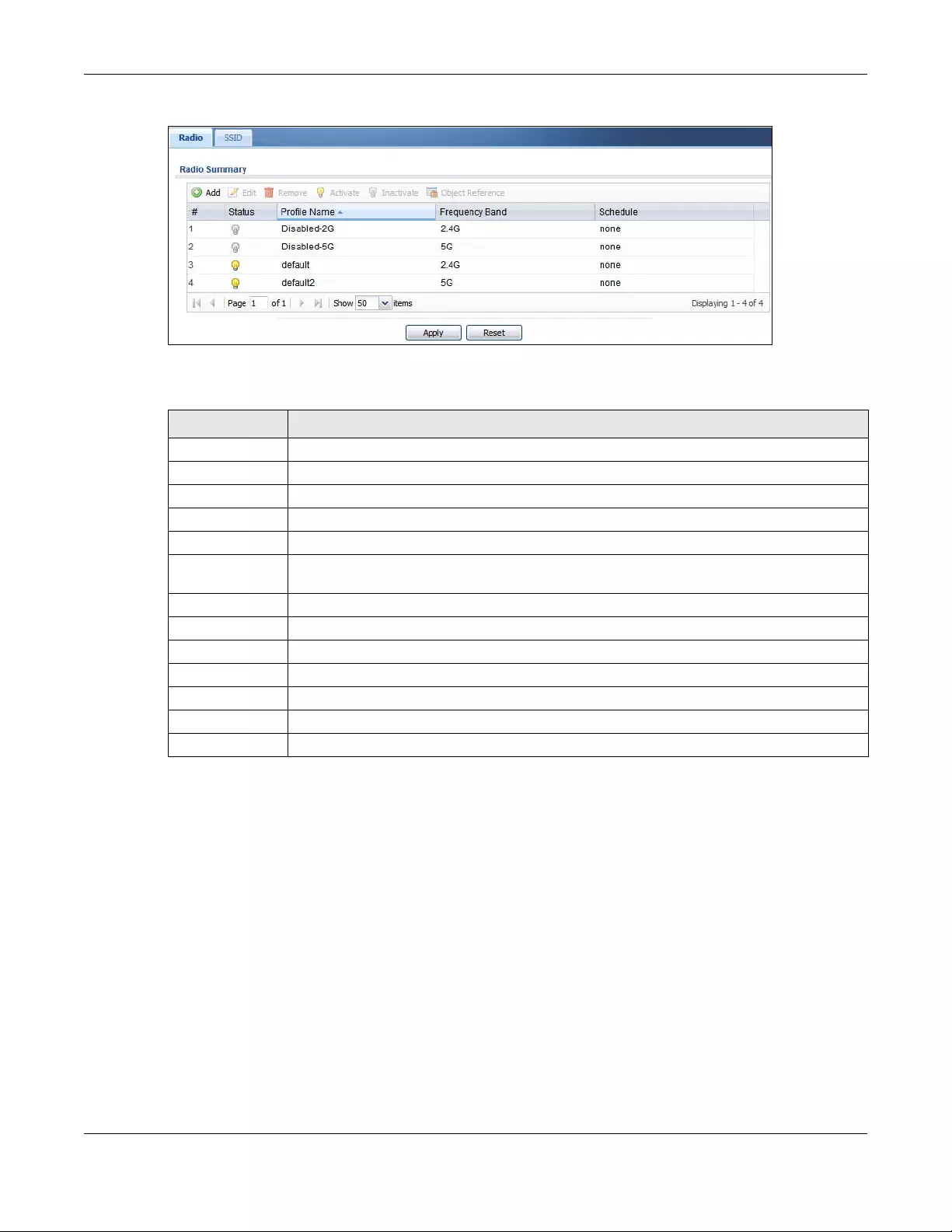
Chapter 43 Object
USG/ZyWALL User’s Guide
751
Figure 525 Configuration > Object > AP Profile > Radio
The following table describes the labels in this screen.
Table 294 Configuration > Object > AP Profile > Radio
LABEL DESCRIPTION
Add Click this to add a new radio profile.
Edit Click this to edit the selected radio profile.
Remove Click this to remove the selected radio profile.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Object
Reference
Click this to view which other objects are linked to the selected radio profile.
# This field is a sequential value, and it is not associated with a specific profile.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
Profile Name This field indicates the name assigned to the radio profile.
Frequency Band This field indicates the frequency band which this radio profile is configured to use.
Schedule This field displays the schedule object which defines when this radio profile can be used.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
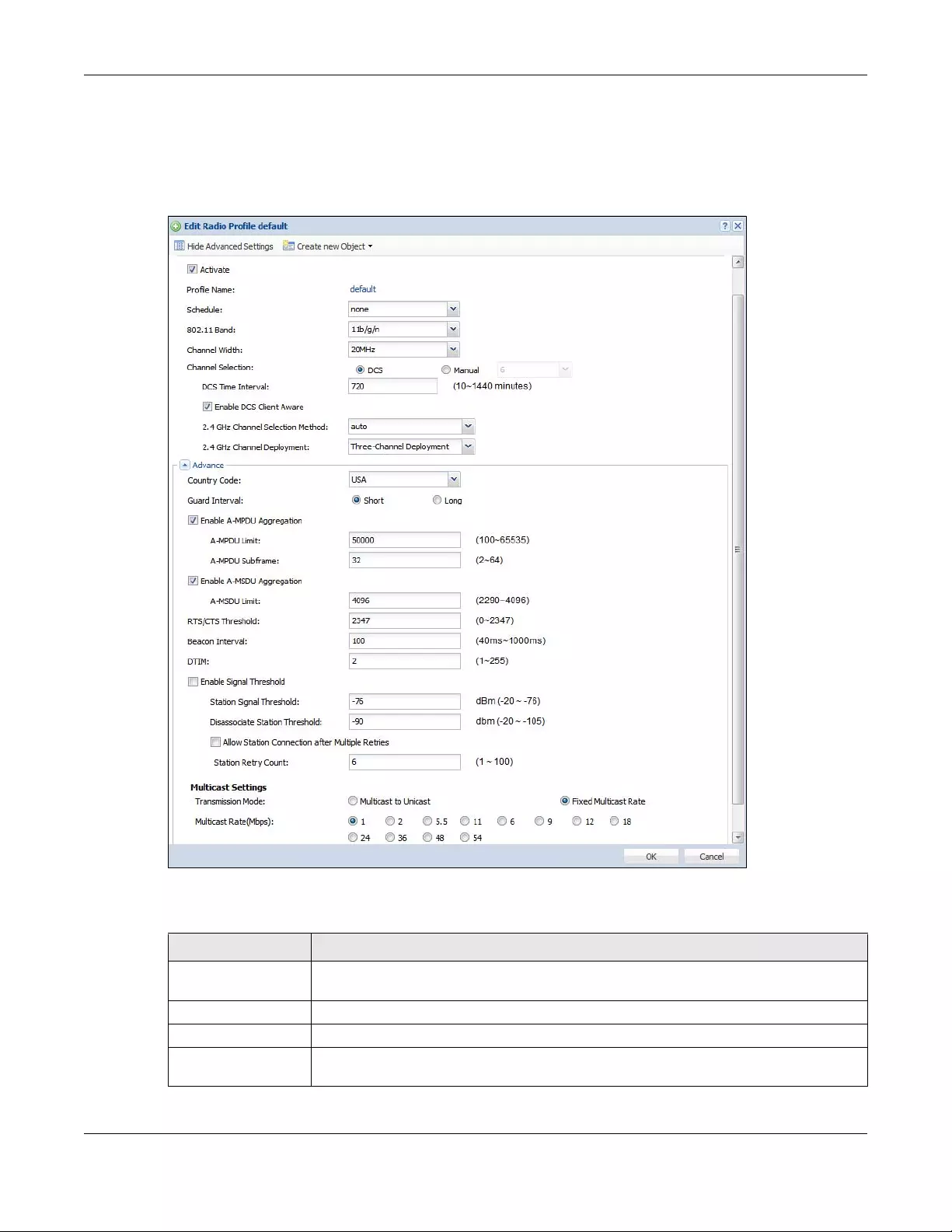
Chapter 43 Object
USG/ZyWALL User’s Guide
752
43.3.1.1 Add/Edit Radio Profile
This screen allows you to create a new radio profile or edit an existing one. To access this screen, click
the Add button or select a radio profile from the list and click the Edit button.
Figure 526 Configuration > Object > AP Profile > Add/Edit Radio Profile
The following table describes the labels in this screen.
Table 295 Configuration > Object > AP Profile > Add/Edit Radio Profile
LABEL DESCRIPTION
Hide / Show
Advanced Settings
Click this to hide or show the Advanced Settings in this window.
General Settings
Activate Select this option to make this profile active.
Profile Name Enter up to 31 alphanumeric characters to be used as this profile’s name. Spaces and
underscores are allowed.
Chapter 43 Object
USG/ZyWALL User’s Guide
753
802.11 Band Select how to let wireless clients connect to the AP.
•11b/g: allows either IEEE 802.11b or IEEE 802.11g compliant WLAN devices to associate
with the AP. The AP adjusts the transmission rate automatically according to the
wireless standard supported by the wireless devices.
•11b/g/n: allows IEEE802.11b, IEEE802.11g and IEEE802.11n compliant WLAN devices to
associate with the AP. The transmission rate of your AP might be reduced.
•11a: allows only IEEE 802.11a compliant WLAN devices to associate with the AP.
•11a/n: allows both IEEE802.11n and IEEE802.11a compliant WLAN devices to associate
with the AP. The transmission rate of your AP might be reduced.
•11ac: allows only IEEE802.11ac compliant WLAN devices to associate with the AP.
Channel Width Select the wireless channel bandwidth you want the AP to use.
A standard 20 MHz channel offers transfer speeds of up to 144Mbps (2.4GHz) or 217Mbps
(5GHZ) whereas a 40MHz channel uses two standard channels and offers speeds of up to
300Mbps (2.4GHz) or 450Mbps (5GHZ). An IEEE 802.11ac-specific 80MHz channel offers
speeds of up to 1.3Gbps.
40 MHz (channel bonding or dual channel) bonds two adjacent radio channels to increase
throughput. A 80 MHz channel consists of two adjacent 40 MHz channels. The wireless
clients must also support 40 MHz or 80 MHz. It is often better to use the 20 MHz setting in a
location where the environment hinders the wireless signal.
Because not all devices support 40 MHz and/or 80 MHz channels, select 20/40MHz or 20/
40/80MHz to allow the AP to adjust the channel bandwidth automatically.
Select 20MHz if you want to lessen radio interference with other wireless devices in your
neighborhood or the wireless clients do not support channel bonding.
Channel
Selection Select the wireless channel which this radio profile should use.
It is recommended that you choose the channel least in use by other APs in the region
where this profile will be implemented. This will reduce the amount of interference between
wireless clients and the AP to which this profile is assigned.
Select DCS to have the AP automatically select the radio channel upon which it
broadcasts by scanning the area around it and determining what channels are currently
being used by other devices.
Note: If you change the country code later, Channel Selection is set to Manual
automatically.
Select Manual and specify the channels the AP uses.
DCS Time Interval This field is available when you set Channel Selection to DCS.
Enter a number of minutes. This regulates how often the AP surveys the other APs within its
broadcast radius. If the channel on which it is currently broadcasting suddenly comes into
use by another AP, the AP will then dynamically select the next available clean channel or
a channel with lower interference.
Enable DCS
Client Aware This field is available when you set Channel Selection to DCS.
Select this to have the AP wait until all connected clients have disconnected before
switching channels.
If you disable this then the AP switches channels immediately regardless of any client
connections. In this instance, clients that are connected to the AP when it switches
channels are dropped.
2.4 GHz Channel
Selection Method This field is available when you set Channel Selection to DCS.
Select auto to have the AP search for available channels automatically in the 2.4 GHz
band. The available channels vary depending on what you select in the 2.4 GHz Channel
Deployment field.
Select manual and specify the channels the AP uses in the 2.4 GHz band.
Table 295 Configuration > Object > AP Profile > Add/Edit Radio Profile (continued)
LABEL DESCRIPTION
Chapter 43 Object
USG/ZyWALL User’s Guide
754
Channel ID This field is available only when you set Channel Selection to DCS and set 2.4 GHz Channel
Selection Method to manual.
Select the check boxes of the channels that you want the AP to use.
2.4 GHz Channel
Deployment This field is available only when you set Channel Selection to DCS and set 2.4 GHz Channel
Selection Method to auto.
Select Three-Channel Deployment to limit channel switching to channels 1,6, and 11, the
three channels that are sufficiently attenuated to have almost no impact on one another.
In other words, this allows you to minimize channel interference by limiting channel-
hopping to these three “safe” channels.
Select Four-Channel Deployment to limit channel switching to four channels. Depending
on the country domain, if the only allowable channels are 1-11 then the Zyxel Device uses
channels 1, 4, 7, 11 in this configuration; otherwise, the Zyxel Device uses channels 1, 5, 9, 13
in this configuration. Four channel deployment expands your pool of possible channels
while keeping the channel interference to a minimum.
Enable 5 GHz DFS
Aware This field is available only when you select 11a, 11a/n or 11ac in the 802.11 Band field.
Select this if your APs are operating in an area known to have RADAR devices. This allows
the device to downgrade its frequency to below 5 GHz in the event a RADAR signal is
detected, thus preventing it from interfering with that signal.
Enabling this forces the AP to select a non-DFS channel.
5 GHz Channel
Selection Method This shows auto and allows the AP to search for available channels automatically in the 5
GHz band.
Advanced Settings
Country Code Select the country code of APs that are connected to the Zyxel Device to be the same as
where the Zyxel Device is located/installed.
The available channels vary depending on the country you selected. Be sure to select the
correct/same country for both radios on an AP and all connected APs, in order to prevent
roaming failure and interference to other systems.
Guard Interval This field is available only when the channel width is 20/40MHz or 20/40/80MHz.
Set the guard interval for this radio profile to either Short or Long.
The guard interval is the gap introduced between data transmission from users in order to
reduce interference. Reducing the interval increases data transfer rates but also increases
interference. Increasing the interval reduces data transfer rates but also reduces
interference.
Enable A-MPDU
Aggregation Select this to enable A-MPDU aggregation.
Message Protocol Data Unit (MPDU) aggregation collects Ethernet frames along with their
802.11n headers and wraps them in a 802.11n MAC header. This method is useful for
increasing bandwidth throughput in environments that are prone to high error rates.
A-MPDU Limit Enter the maximum frame size to be aggregated.
A-MPDU
Subframe Enter the maximum number of frames to be aggregated each time.
Enable A-MSDU
Aggregation Select this to enable A-MSDU aggregation.
Mac Service Data Unit (MSDU) aggregation collects Ethernet frames without any of their
802.11n headers and wraps the header-less payload in a single 802.11n MAC header. This
method is useful for increasing bandwidth throughput. It is also more efficient than A-MPDU
except in environments that are prone to high error rates.
A-MSDU Limit Enter the maximum frame size to be aggregated.
Table 295 Configuration > Object > AP Profile > Add/Edit Radio Profile (continued)
LABEL DESCRIPTION
Chapter 43 Object
USG/ZyWALL User’s Guide
755
RTS/CTS Threshold Use RTS/CTS to reduce data collisions on the wireless network if you have wireless clients
that are associated with the same AP but out of range of one another. When enabled, a
wireless client sends an RTS (Request To Send) and then waits for a CTS (Clear To Send)
before it transmits. This stops wireless clients from transmitting packets at the same time
(and causing data collisions).
A wireless client sends an RTS for all packets larger than the number (of bytes) that you
enter here. Set the RTS/CTS equal to or higher than the fragmentation threshold to turn RTS/
CTS off.
Beacon Interval When a wirelessly networked device sends a beacon, it includes with it a beacon interval.
This specifies the time period before the device sends the beacon again. The interval tells
receiving devices on the network how long they can wait in low-power mode before
waking up to handle the beacon. A high value helps save current consumption of the
access point.
DTIM Delivery Traffic Indication Message (DTIM) is the time period after which broadcast and
multicast packets are transmitted to mobile clients in the Active Power Management
mode. A high DTIM value can cause clients to lose connectivity with the network. This value
can be set from 1 to 255.
Enable Signal
Threshold Select the check box to use the signal threshold to ensure wireless clients receive good
throughput. This allows only wireless clients with a strong signal to connect to the AP.
Clear the check box to not require wireless clients to have a minimum signal strength to
connect to the AP.
Station Signal
Threshold Set a minimum client signal strength. A wireless client is allowed to connect to the AP only
when its signal strength is stronger than the specified threshold.
-20 dBm is the strongest signal you can require and -76 is the weakest.
Disassociate
Station Threshold Set a minimum kick-off signal strength. When a wireless client’s signal strength is lower than
the specified threshold, the Zyxel Device disconnects the wireless client from the AP.
-20 dBm is the strongest signal you can require and -90 is the weakest.
Allow Station
Connection after
Multiple Retries
Select this option to allow a wireless client to try to associate with the AP again after it is
disconnected due to weak signal strength.
Station Retry
Count Set the maximum number of times a wireless client can attempt to re-connect to the AP
Multicast Settings Use this section to set a transmission mode and maximum rate for multicast traffic.
Transmission
Mode Set how the AP handles multicast traffic.
Select Multicast to Unicast to broadcast wireless multicast traffic to all of the wireless clients
as unicast traffic. Unicast traffic dynamically changes the data rate based on the
application’s bandwidth requirements. The retransmit mechanism of unicast traffic
provides more reliable transmission of the multicast traffic, although it also produces
duplicate packets.
Select Fixed Multicast Rate to send wireless multicast traffic at a single data rate. You must
know the multicast application’s bandwidth requirements and set it in the following field.
Multicast Rate
(Mbps) If you set the multicast transmission mode to fixed multicast rate, set the data rate for
multicast traffic here. For example, to deploy 4 Mbps video, select a fixed multicast rate
higher than 4 Mbps.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
Table 295 Configuration > Object > AP Profile > Add/Edit Radio Profile (continued)
LABEL DESCRIPTION
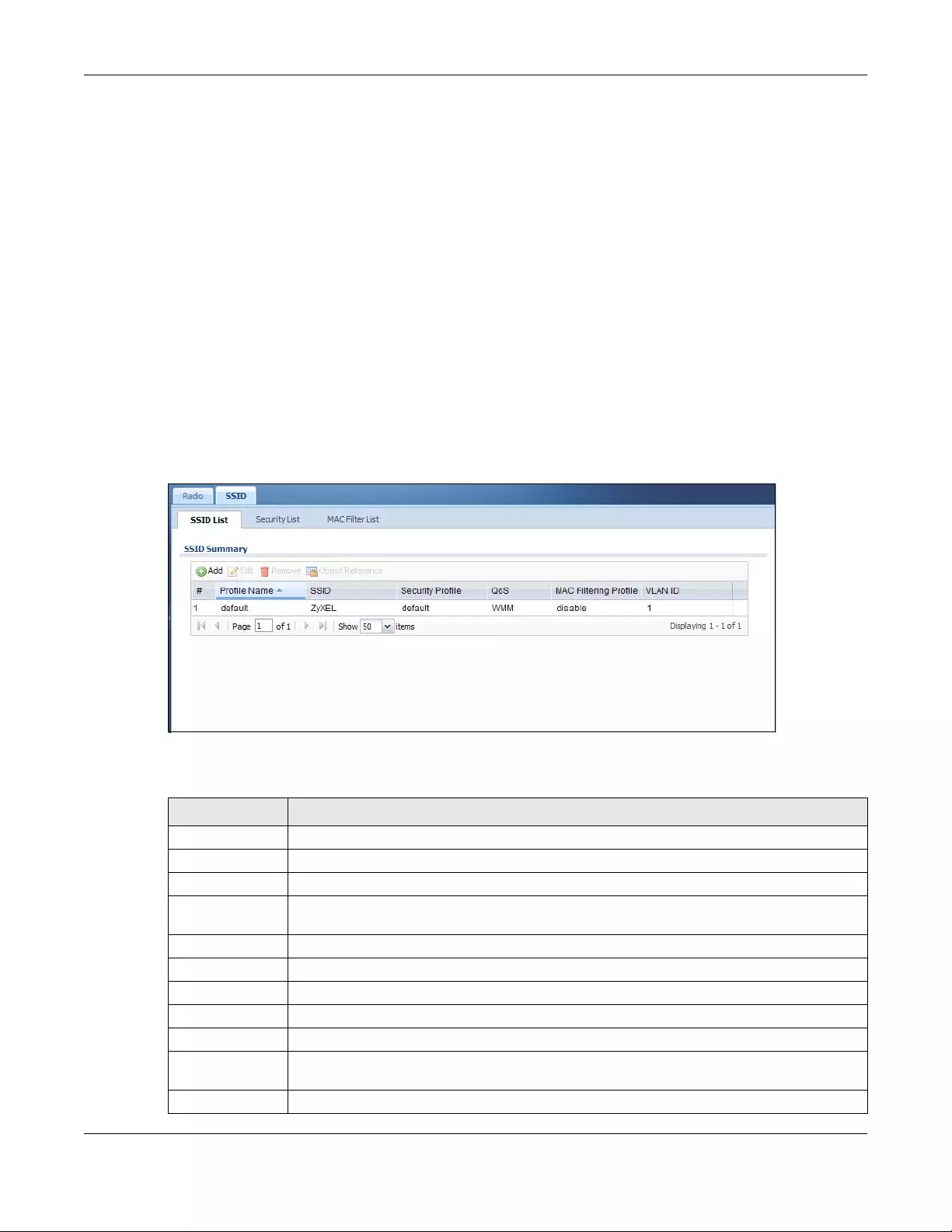
Chapter 43 Object
USG/ZyWALL User’s Guide
756
43.3.2 SSID Screen
The SSID screens allow you to configure three different types of profiles for your networked APs: an SSID
list, which can assign specific SSID configurations to your APs; a security list, which can assign specific
encryption methods to the APs when allowing wireless clients to connect to them; and a MAC filter list,
which can limit connections to an AP based on wireless clients MAC addresses.
43.3.2.1 SSID List
This screen allows you to create and manage SSID configurations that can be used by the APs. An SSID,
or Service Set IDentifier, is basically the name of the wireless network to which a wireless client can
connect. The SSID appears as readable text to any device capable of scanning for wireless frequencies
(such as the WiFi adapter in a laptop), and is displayed as the wireless network name when a person
makes a connection to it.
To access this screen click Configuration > Object > AP Profile > SSID.
Note: You can have a maximum of 32 SSID profiles on the Zyxel Device.
Figure 527 Configuration > Object > AP Profile > SSID List
The following table describes the labels in this screen.
Table 296 Configuration > Object > AP Profile > SSID List
LABEL DESCRIPTION
Add Click this to add a new SSID profile.
Edit Click this to edit the selected SSID profile.
Remove Click this to remove the selected SSID profile.
Object
Reference
Click this to view which other objects are linked to the selected SSID profile (for example, radio
profile).
# This field is a sequential value, and it is not associated with a specific profile.
Profile Name This field indicates the name assigned to the SSID profile.
SSID This field indicates the SSID name as it appears to wireless clients.
Security Profile This field indicates which (if any) security profile is associated with the SSID profile.
QoS This field indicates the QoS type associated with the SSID profile.
MAC Filtering
Profile
This field indicates which (if any) MAC Filter Profile is associated with the SSID profile.
VLAN ID This field indicates the VLAN ID associated with the SSID profile.
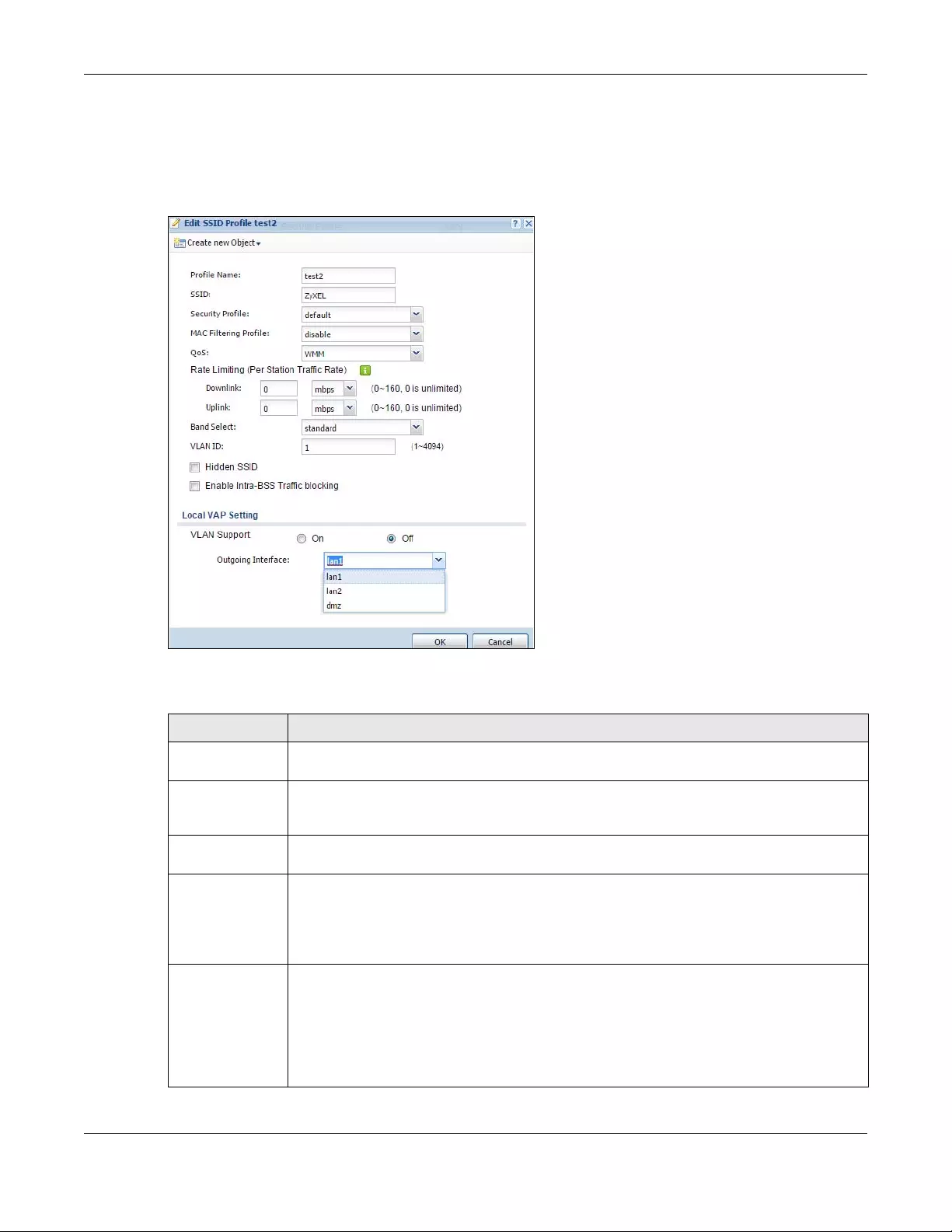
Chapter 43 Object
USG/ZyWALL User’s Guide
757
43.3.2.2 Add/Edit SSID Profile
This screen allows you to create a new SSID profile or edit an existing one. To access this screen, click the
Add button or select an SSID profile from the list and click the Edit button.
Figure 528 Configuration > Object > AP Profile > SSID > Add/Edit SSID Profile
The following table describes the labels in this screen.
Table 297 Configuration > Object > AP Profile > SSID > Add/Edit SSID Profile
LABEL DESCRIPTION
Create new
Object
Select an object type from the list to create a new one associated with this SSID profile.
Profile Name Enter up to 31 alphanumeric characters for the profile name. This name is only visible in the
Web Configurator and is only for management purposes. Spaces and underscores are
allowed.
SSID Enter the SSID name for this profile. This is the name visible on the network to wireless clients.
Enter up to 32 characters, spaces and underscores are allowed.
Security Profile Select a security profile from this list to associate with this SSID. If none exist, you can use the
Create new Object menu to create one.
Note: It is highly recommended that you create security profiles for all of your SSIDs to
enhance your network security.
MAC Filtering
Profile
Select a MAC filtering profile from the list to associate with this SSID. If none exist, you can use
the Create new Object menu to create one.
MAC filtering allows you to limit the wireless clients connecting to your network through a
particular SSID by wireless client MAC addresses. Any clients that have MAC addresses not in
the MAC filtering profile of allowed addresses are denied connections.
The disable setting means no MAC filtering is used.
Chapter 43 Object
USG/ZyWALL User’s Guide
758
QoS Select a Quality of Service (QoS) access category to associate with this SSID. Access categories
minimize the delay of data packets across a wireless network. Certain categories, such as
video or voice, are given a higher priority due to the time sensitive nature of their data packets.
QoS access categories are as follows:
disable: Turns off QoS for this SSID. All data packets are treated equally and not tagged with
access categories.
WMM: Enables automatic tagging of data packets. The Zyxel Device assigns access categories
to the SSID by examining data as it passes through it and making a best guess effort. If
something looks like video traffic, for instance, it is tagged as such.
WMM_VOICE: All wireless traffic to the SSID is tagged as voice data. This is recommended if an
SSID is used for activities like placing and receiving VoIP phone calls.
WMM_VIDEO: All wireless traffic to the SSID is tagged as video data. This is recommended for
activities like video conferencing.
WMM_BEST_EFFORT: All wireless traffic to the SSID is tagged as “best effort,” meaning the data
travels the best route it can without displacing higher priority traffic. This is good for activities
that do not require the best bandwidth throughput, such as surfing the Internet.
WMM_BACKGROUND: All wireless traffic to the SSID is tagged as low priority or “background
traffic”, meaning all other access categories take precedence over this one. If traffic from an
SSID does not have strict throughput requirements, then this access category is recommended.
For example, an SSID that only has network printers connected to it.
Rate Limiting (Per
Station Traffic
Rate)
Define the maximum incoming and outgoing transmission data rate per wireless station
Downlink: Define the maximum incoming transmission data rate (either in Mbps or Kbps) on a per-station
basis.
Uplink: Define the maximum outgoing transmission data rate (either in Mbps or Kbps) on a per-station
basis.
Band Select: To improve network performance and avoid interference in the 2.4 GHz frequency band, you
can enable this feature to use the 5 GHz band first. You should set 2.4GHz and 5 GHz radio
profiles to use the same SSID and security settings.
Select standard to have the AP try to connect the wireless clients to the same SSID using the 5
GHZ band. Connections to an SSID using the 2.4GHz band are still allowed.
Otherwise, select disable to turn off this feature.
VLAN ID Enter the VLAN ID that will be used to tag all traffic originating from this SSID if the VLAN is
different from the native VLAN.
Hidden SSID Select this if you want to “hide” your SSID from wireless clients. This tells any wireless clients in the
vicinity of the AP using this SSID profile not to display its SSID name as a potential connection.
Not all wireless clients respect this flag and display it anyway.
When an SSID is “hidden” and a wireless client cannot see it, the only way you can connect to
the SSID is by manually entering the SSID name in your wireless connection setup screen(s)
(these vary by client, client connectivity software, and operating system).
Enable Intra-BSS
Traffic Blocking
Select this option to prevent crossover traffic from within the same SSID.
Local VAP Setting This part of the screen only applies to Zyxel Device models that have built-in wireless
functionality (AP) - see Table 1 on page 24.
Table 297 Configuration > Object > AP Profile > SSID > Add/Edit SSID Profile (continued)
LABEL DESCRIPTION
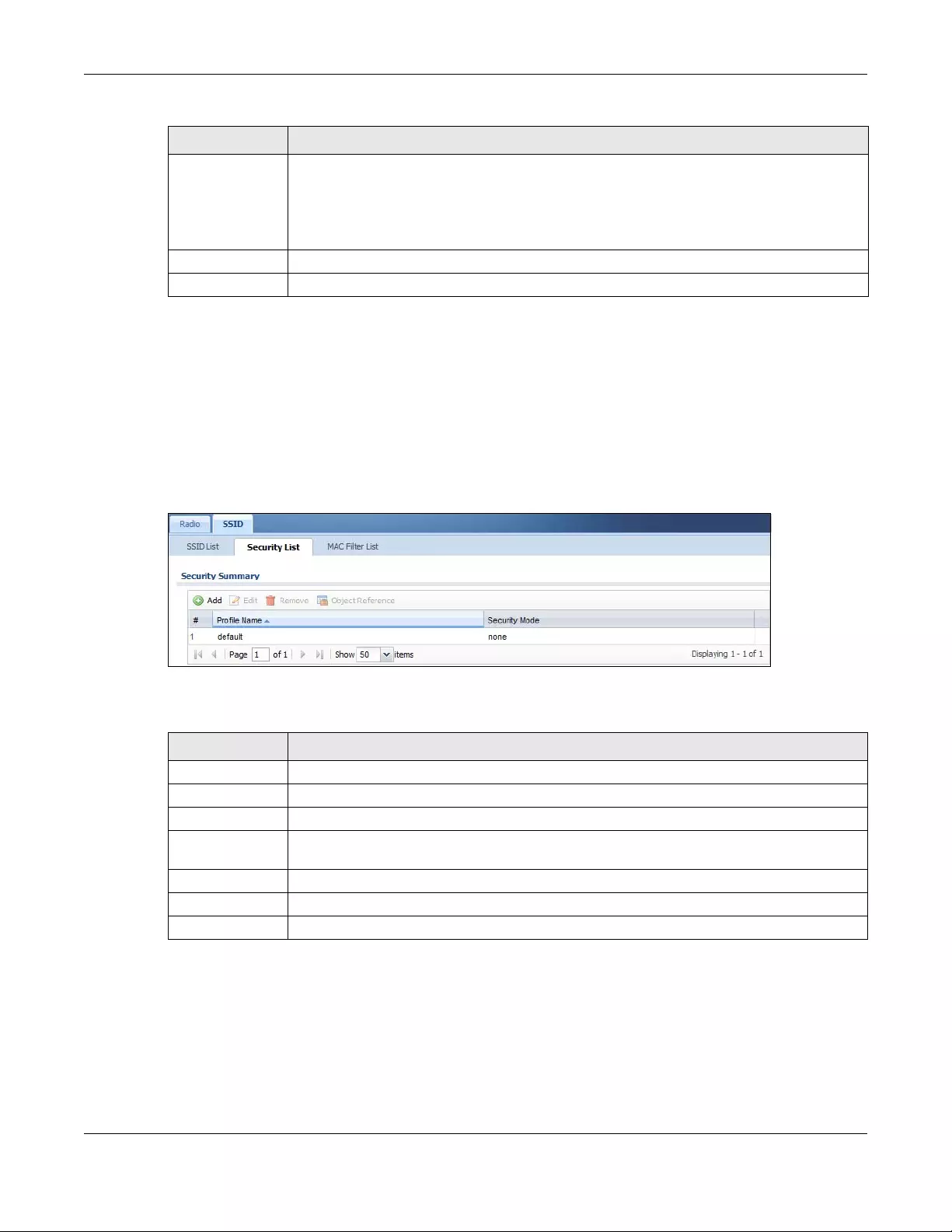
Chapter 43 Object
USG/ZyWALL User’s Guide
759
43.3.2.3 Security List
This screen allows you to manage wireless security configurations that can be used by your SSIDs.
Wireless security is implemented strictly between the AP broadcasting the SSID and the stations that are
connected to it.
To access this screen click Configuration > Object > AP Profile > SSID > Security List.
Note: You can have a maximum of 32 security profiles on the Zyxel Device.
Figure 529 Configuration > Object > AP Profile > SSID > Security List
The following table describes the labels in this screen.
VLAN Support Select On to have the Zyxel Device assign the VLAN ID listed in the top part of the screen to the
built-in AP.
Select Off to have the Zyxel Device ignore the VLAN ID listed in the top part of the screen.
Select an Outgoing Interface to have the Zyxel Device assign an IP address in the same subnet
as the selected interface to the built-in AP.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
Table 297 Configuration > Object > AP Profile > SSID > Add/Edit SSID Profile (continued)
LABEL DESCRIPTION
Table 298 Configuration > Object > AP Profile > SSID > Security List
LABEL DESCRIPTION
Add Click this to add a new security profile.
Edit Click this to edit the selected security profile.
Remove Click this to remove the selected security profile.
Object
Reference
Click this to view which other objects are linked to the selected security profile (for example,
SSID profile).
# This field is a sequential value, and it is not associated with a specific profile.
Profile Name This field indicates the name assigned to the security profile.
Security Mode This field indicates this profile’s security mode (if any).
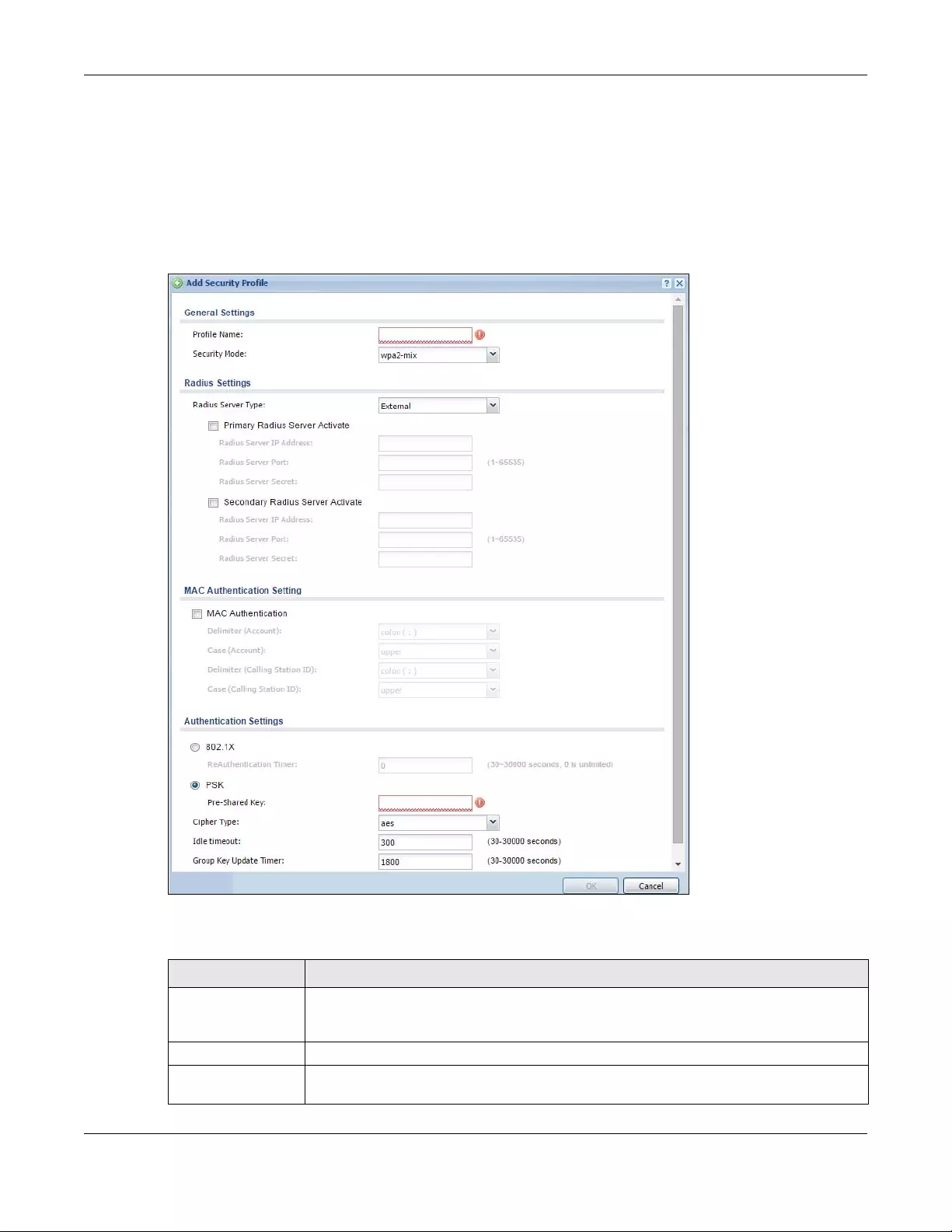
Chapter 43 Object
USG/ZyWALL User’s Guide
760
43.3.2.4 Add/Edit Security Profile
This screen allows you to create a new security profile or edit an existing one. To access this screen, click
the Add button or select a security profile from the list and click the Edit button.
Note: This screen’s options change based on the Security Mode selected. Only the default
screen is displayed here.
Figure 530 Configuration > Object > AP Profile > SSID > Security Profile > Add/Edit Security Profile
The following table describes the labels in this screen.
Table 299 Configuration > Object > AP Profile > SSID > Security Profile > Add/Edit Security Profile
LABEL DESCRIPTION
Profile Name Enter up to 31 alphanumeric characters for the profile name. This name is only visible in the
Web Configurator and is only for management purposes. Spaces and underscores are
allowed.
Security Mode Select a security mode from the list: wep, wpa, wpa2, or wpa2-mix.
Radius Server Type Select Internal to use the Zyxel Device’s internal authentication database, or External to use
an external RADIUS server for authentication.
Chapter 43 Object
USG/ZyWALL User’s Guide
761
Primary / Secondary
Radius Server
Activate
Select this to have the Zyxel Device use the specified RADIUS server.
Radius Server IP
Address
Enter the IP address of the RADIUS server to be used for authentication.
Radius Server Port Enter the port number of the RADIUS server to be used for authentication.
Radius Server Secret Enter the shared secret password of the RADIUS server to be used for authentication.
MAC Authentication Select this to use an external server or the Zyxel Device’s local database to authenticate
wireless clients by their MAC addresses. Users cannot get an IP address if the MAC
authentication fails.
An external server can use the wireless client’s account (username/password) or Calling
Station ID for MAC authentication. Configure the ones the external server uses.
Delimiter
(Account) Select the separator the external server uses for the two-character pairs within account
MAC addresses.
Case (Account) Select the case (upper or lower) the external server requires for letters in the account MAC
addresses.
Delimiter (Calling
Station ID) RADIUS servers can require the MAC address in the Calling Station ID RADIUS attribute.
Select the separator the external server uses for the pairs in calling station MAC addresses.
Case (Calling
Station ID) Select the case (upper or lower) the external server requires for letters in the calling station
MAC addresses.
802.1X Select this to enable 802.1x secure authentication.
Auth. Method This field is available only when you set the RADIUS server type to Internal.
Select an authentication method if you have created any in the Configuration > Object >
Auth. Method screen.
Reauthenticatio
n Timer Enter the interval (in seconds) between authentication requests. Enter a 0 for unlimited
requests.
The following fields are available if you set Security Mode to wep.
Idle Timeout Enter the idle interval (in seconds) that a client can be idle before authentication is
discontinued.
Authentication Type Select a WEP authentication method. Choices are Open or Share key.
Key Length Select the bit-length of the encryption key to be used in WEP connections.
If you select WEP-64:
• Enter 10 hexadecimal digits in the range of “A-F”, “a-f” and “0-9” (for example,
0x11AA22BB33) for each Key used.
or
• Enter 5 ASCII characters (case sensitive) ranging from “a-z”, “A-Z” and “0-9” (for
example, MyKey) for each Key used.
If you select WEP-128:
• Enter 26 hexadecimal digits in the range of “A-F”, “a-f” and “0-9” (for example,
0x00112233445566778899AABBCC) for each Key used.
or
• Enter 13 ASCII characters (case sensitive) ranging from “a-z”, “A-Z” and “0-9” (for
example, MyKey12345678) for each Key used.
Key 1~4 Based on your Key Length selection, enter the appropriate length hexadecimal or ASCII key.
The following fields are available if you set Security Mode to wpa, wpa2 or wpa2-mix.
PSK Select this option to use a Pre-Shared Key with WPA encryption.
Table 299 Configuration > Object > AP Profile > SSID > Security Profile > Add/Edit Security Profile
LABEL DESCRIPTION
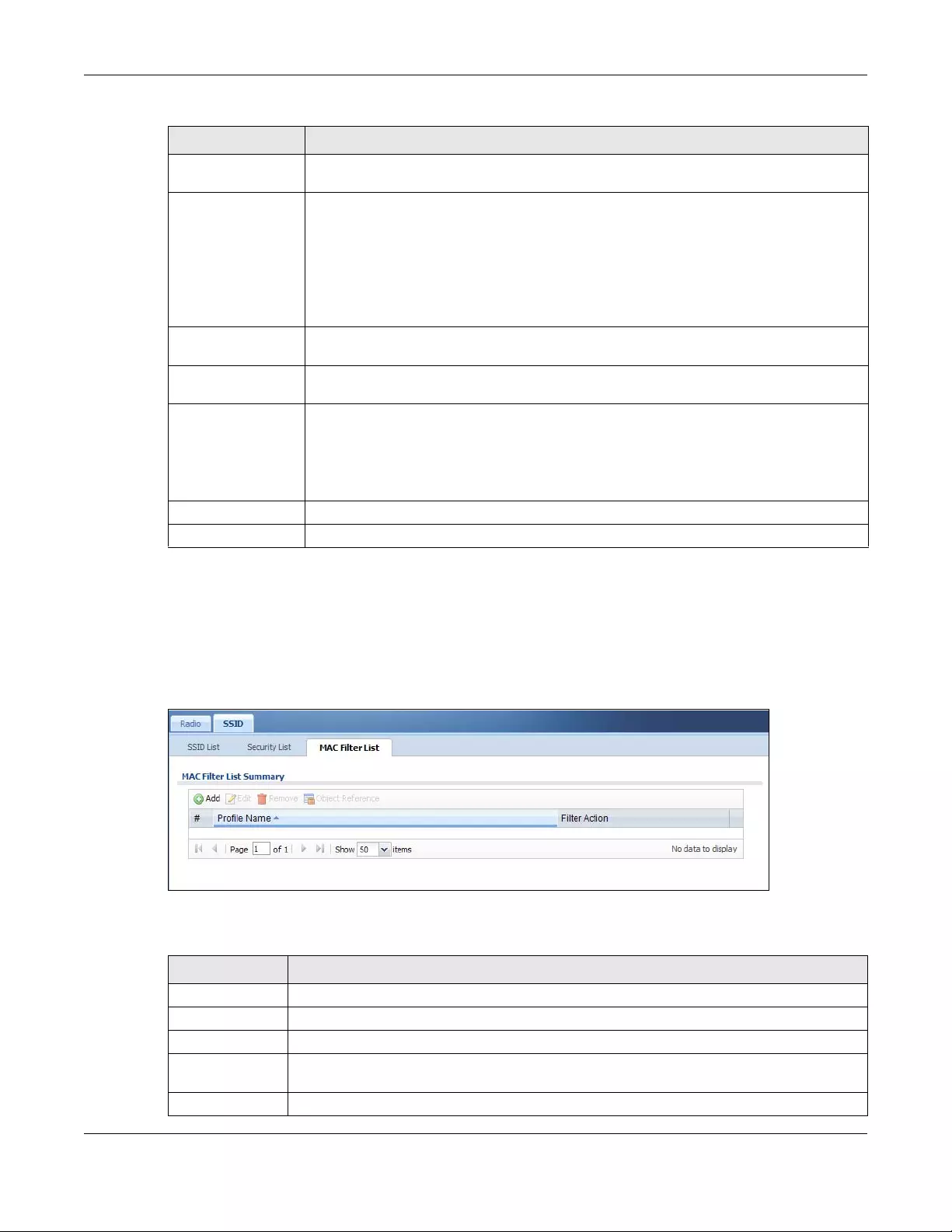
Chapter 43 Object
USG/ZyWALL User’s Guide
762
43.3.2.5 MAC Filter List
This screen allows you to create and manage security configurations that can be used by your SSIDs. To
access this screen click Configuration > Object > AP Profile > SSID > MAC Filter List.
Note: You can have a maximum of 32 MAC filtering profiles on the Zyxel Device.
Figure 531 Configuration > Object > AP Profile > SSID > MAC Filter List
The following table describes the labels in this screen.
Pre-Shared Key Enter a pre-shared key of between 8 and 63 case-sensitive ASCII characters (including
spaces and symbols) or 64 hexadecimal characters.
Cipher Type Select an encryption cipher type from the list.
•auto - This automatically chooses the best available cipher based on the cipher in use
by the wireless client that is attempting to make a connection.
•tkip - This is the Temporal Key Integrity Protocol encryption method added later to the
WEP encryption protocol to further secure. Not all wireless clients may support this.
•aes - This is the Advanced Encryption Standard encryption method. It is a more recent
development over TKIP and considerably more robust. Not all wireless clients may
support this.
Idle Timeout Enter the idle interval (in seconds) that a client can be idle before authentication is
discontinued.
Group Key Update
Timer
Enter the interval (in seconds) at which the AP updates the group WPA encryption key.
Pre-Authentication This field is available only when you set Security Mode to wpa2 or wpa2-mix and enable
802.1x authentication.
Enable or Disable pre-authentication to allow the AP to send authentication information to
other APs on the network, allowing connected wireless clients to switch APs without having
to re-authenticate their network connection.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
Table 299 Configuration > Object > AP Profile > SSID > Security Profile > Add/Edit Security Profile
LABEL DESCRIPTION
Table 300 Configuration > Object > AP Profile > SSID > MAC Filter List
LABEL DESCRIPTION
Add Click this to add a new MAC filtering profile.
Edit Click this to edit the selected MAC filtering profile.
Remove Click this to remove the selected MAC filtering profile.
Object
Reference
Click this to view which other objects are linked to the selected MAC filtering profile (for
example, SSID profile).
# This field is a sequential value, and it is not associated with a specific profile.
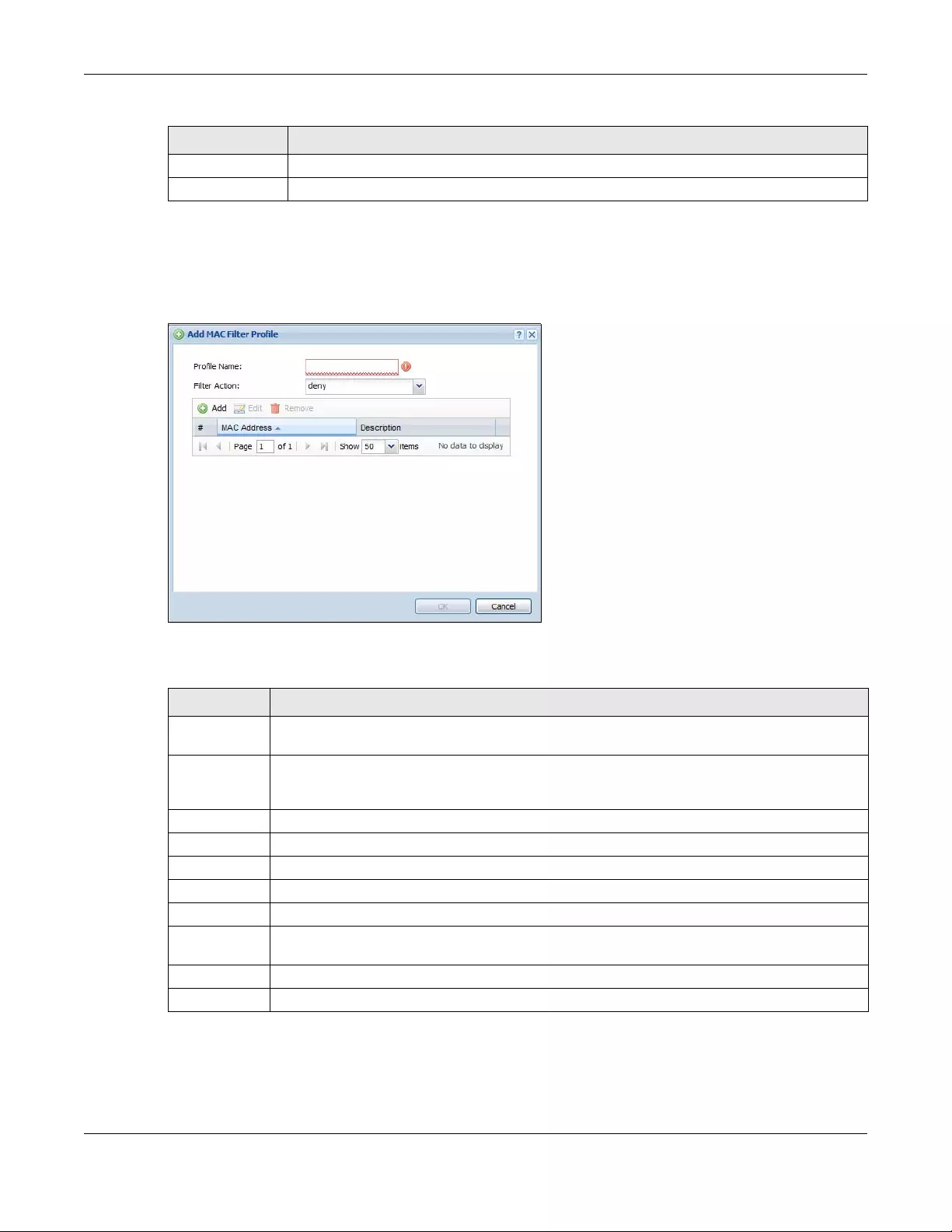
Chapter 43 Object
USG/ZyWALL User’s Guide
763
43.3.2.6 Add/Edit MAC Filter Profile
This screen allows you to create a new MAC filtering profile or edit an existing one. To access this screen,
click the Add button or select a MAC filter profile from the list and click the Edit button.
Figure 532 SSID > MAC Filter List > Add/Edit MAC Filter Profile
The following table describes the labels in this screen.
Profile Name This field indicates the name assigned to the MAC filtering profile.
Filter Action This field indicates this profile’s filter action (if any).
Table 300 Configuration > Object > AP Profile > SSID > MAC Filter List (continued)
LABEL DESCRIPTION
Table 301 SSID > MAC Filter List > Add/Edit MAC Filter Profile
LABEL DESCRIPTION
Profile Name Enter up to 31 alphanumeric characters for the profile name. This name is only visible in the Web
Configurator and is only for management purposes. Spaces and underscores are allowed.
Filter Action Select allow to permit the wireless client with the MAC addresses in this profile to connect to the
network through the associated SSID; select deny to block the wireless clients with the specified
MAC addresses.
Add Click this to add a MAC address to the profile’s list.
Edit Click this to edit the selected MAC address in the profile’s list.
Remove Click this to remove the selected MAC address from the profile’s list.
# This field is a sequential value, and it is not associated with a specific profile.
MAC Address This field specifies a MAC address associated with this profile.
Description This field displays a description for the MAC address associated with this profile. You can click the
description to make it editable. Enter up to 60 characters, spaces and underscores allowed.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
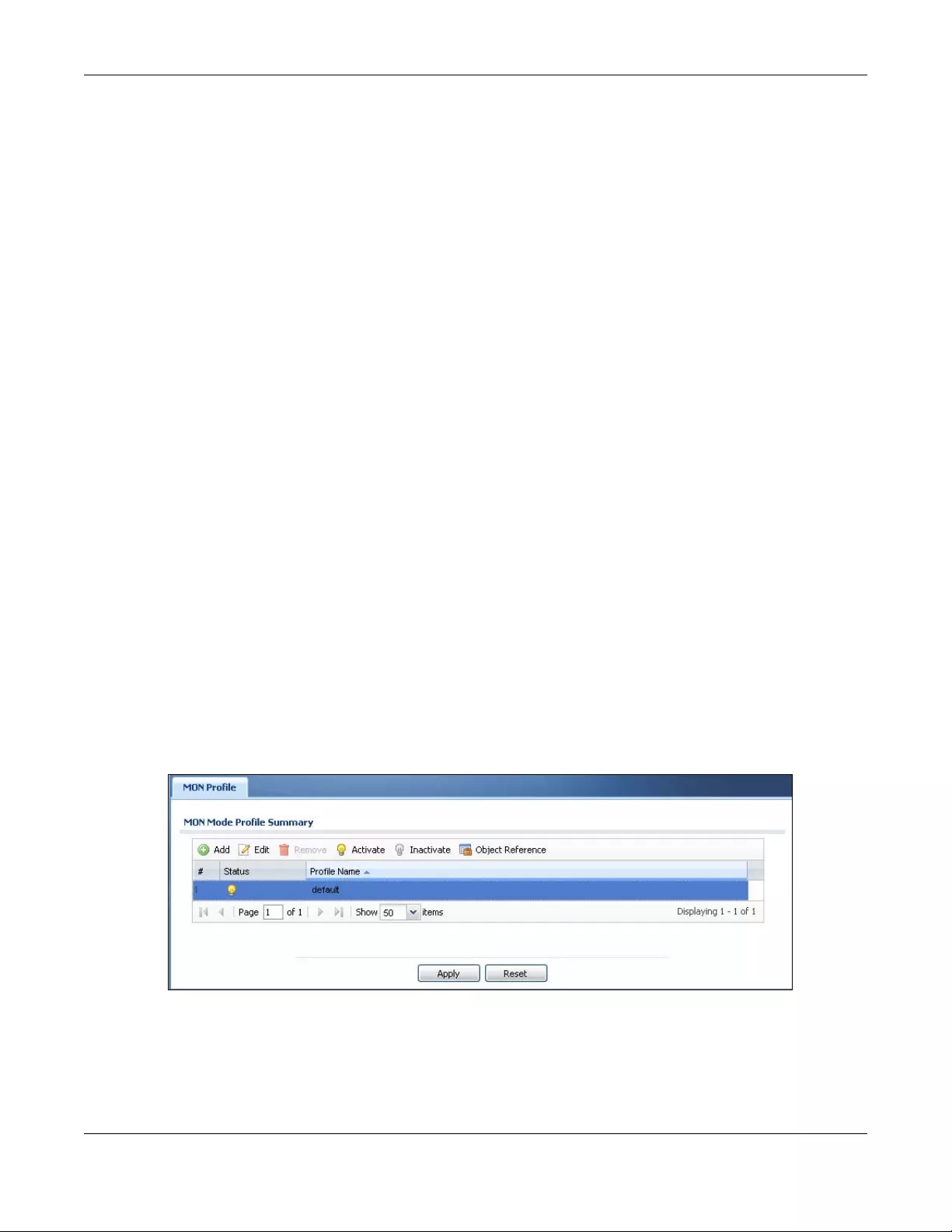
Chapter 43 Object
USG/ZyWALL User’s Guide
764
43.4 MON Profile
43.4.1 Overview
This screen allows you to set up monitor mode configurations that allow your connected APs to scan for
other wireless devices in the vicinity. Once detected, you can use the MON Mode screen (Section 9.4 on
page 261) to classify them as either rogue or friendly and then manage them accordingly.
The MON Profile screen (Section 43.4.2 on page 764) creates preset monitor mode configurations that
can be used by the APs.
43.4.1.1 What You Need To Know
The following terms and concepts may help as you read this chapter.
Active Scan
An active scan is performed when an 802.11-compatible wireless monitoring device is explicitly
triggered to scan a specified channel or number of channels for other wireless devices broadcasting on
the 802.11 frequencies by sending probe request frames.
Passive Scan
A passive scan is performed when an 802.11-compatible monitoring device is set to periodically listen to
a specified channel or number of channels for other wireless devices broadcasting on the 802.11
frequencies.
43.4.2 MON Profile
This screen allows you to create monitor mode configurations that can be used by the APs. To access
this screen, login to the Web Configurator, and click Configuration > Object > MON Profile.
Figure 533 Configuration > Object > MON Profile
Chapter 43 Object
USG/ZyWALL User’s Guide
765
The following table describes the labels in this screen.
43.4.2.1 Add/Edit MON Profile
This screen allows you to create a new monitor mode profile or edit an existing one. To access this
screen, click the Add button or select and existing monitor mode profile and click the Edit button.
Table 302 Configuration > Object > MON Profile
LABEL DESCRIPTION
Add Click this to add a new monitor mode profile.
Edit Click this to edit the selected monitor mode profile.
Remove Click this to remove the selected monitor mode profile.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
Object
Reference
Click this to view which other objects are linked to the selected monitor mode profile (for
example, an AP management profile).
# This field is a sequential value, and it is not associated with a specific user.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
Profile Name This field indicates the name assigned to the monitor profile.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
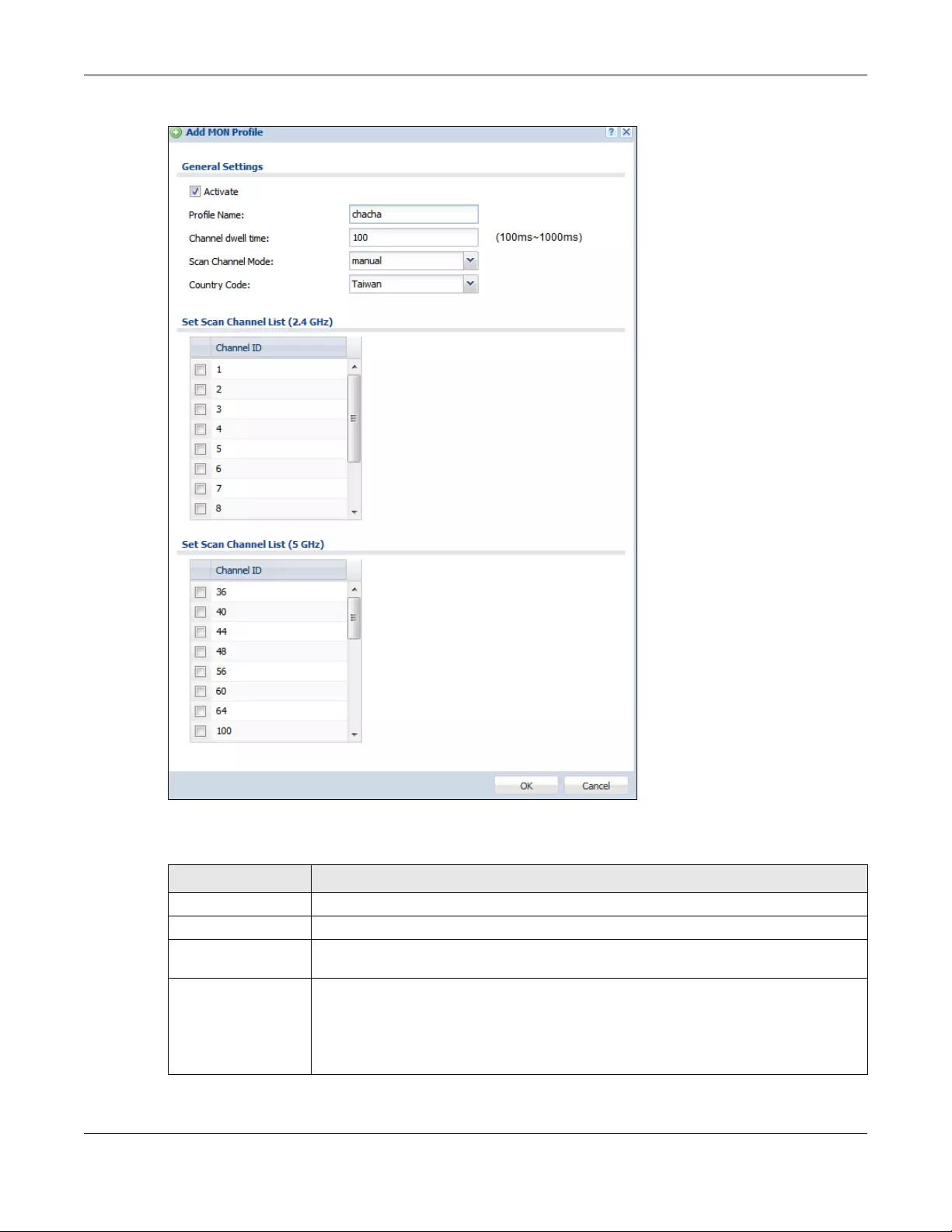
Chapter 43 Object
USG/ZyWALL User’s Guide
766
Figure 534 Configuration > Object > MON Profile > Add/Edit MON Profile
The following table describes the labels in this screen.
Table 303 Configuration > Object > MON Profile > Add/Edit MON Profile
LABEL DESCRIPTION
Activate Select this to activate this monitor mode profile.
Profile Name This field indicates the name assigned to the monitor mode profile.
Channel dwell time Enter the interval (in milliseconds) before the AP switches to another channel for
monitoring.
Scan Channel Mode Select auto to have the AP switch to the next sequential channel once the Channel dwell
time expires.
Select manual to set specific channels through which to cycle sequentially when the
Channel dwell time expires. Selecting this options makes the Scan Channel List options
available.
Chapter 43 Object
USG/ZyWALL User’s Guide
767
43.4.3 Technical Reference
The following section contains additional technical information about the features described in this
chapter.
Rogue APs
Rogue APs are wireless access points operating in a network’s coverage area that are not under the
control of the network’s administrators, and can open up holes in a network’s security. Attackers can
take advantage of a rogue AP’s weaker (or non-existent) security to gain access to the network, or set
up their own rogue APs in order to capture information from wireless clients. If a scan reveals a rogue AP,
you can use commercially-available software to physically locate it.
Country Code Select the country code of APs that are connected to the Zyxel Device to be the same as
where the Zyxel Device is located/installed.
The available channels vary depending on the country you selected. Be sure to select the
correct/same country for both radios on an AP and all connected APs, in order to prevent
roaming failure and interference to other systems.
After changing the country code, the AP channel setting will be reset if your manually
selected channel(s) are not valid in the new country code setting.
Set Scan Channel List
(2.4 GHz)
Move a channel from the Available channels column to the Channels selected column to
have the APs using this profile scan that channel when Scan Channel Mode is set to
manual.
These channels are limited to the 2 GHz range (802.11 b/g/n).
Set Scan Channel List
(5 GHz)
Move a channel from the Available channels column to the Channels selected column to
have the APs using this profile scan that channel when Scan Channel Mode is set to
manual.
These channels are limited to the 5 GHz range (802.11 a/n).
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
Table 303 Configuration > Object > MON Profile > Add/Edit MON Profile (continued)
LABEL DESCRIPTION
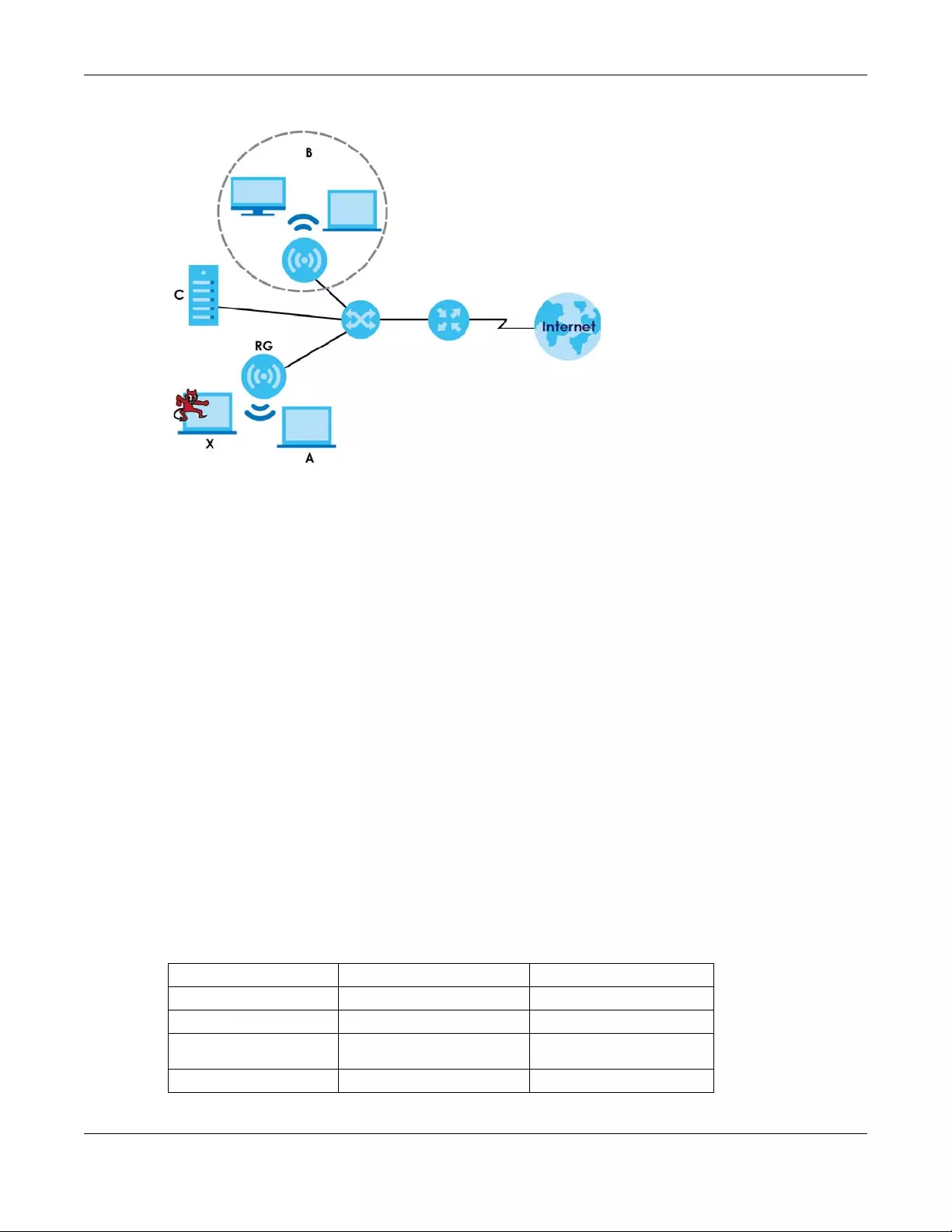
Chapter 43 Object
USG/ZyWALL User’s Guide
768
Figure 535 Rogue AP Example
In the example above, a corporate network’s security is compromised by a rogue AP (RG) set up by an
employee at his workstation in order to allow him to connect his notebook computer wirelessly (A). The
company’s legitimate wireless network (the dashed ellipse B) is well-secured, but the rogue AP uses
inferior security that is easily broken by an attacker (X) running readily available encryption-cracking
software. In this example, the attacker now has access to the company network, including sensitive
data stored on the file server (C).
Friendly APs
If you have more than one AP in your wireless network, you should also configure a list of “friendly” APs.
Friendly APs are other wireless access points that are detected in your network, as well as any others that
you know are not a threat (those from recognized networks, for example). It is recommended that you
export (save) your list of friendly APs often, especially if you have a network with a large number of
access points.
43.5 Application
Go to Configuration > Licensing > Signature Update > IDP/AppPatrol to check that you have the latest
IDP and App Patrol signatures. These signatures are available to create application objects in
Configuration > Object > Application > Application. Categories of applications include (at the time of
writing):
Table 304 Categories of Applications
• Instant Messaging • P2P • File Transfer
• Streaming Media • Mail and Collaboration • Voice over IP
• Database • Games • Network Management
• Remote Access
Terminals • Bypass Proxies and
Tunnels •Web
•Security Update •Web IM •TCP/UDP traffic
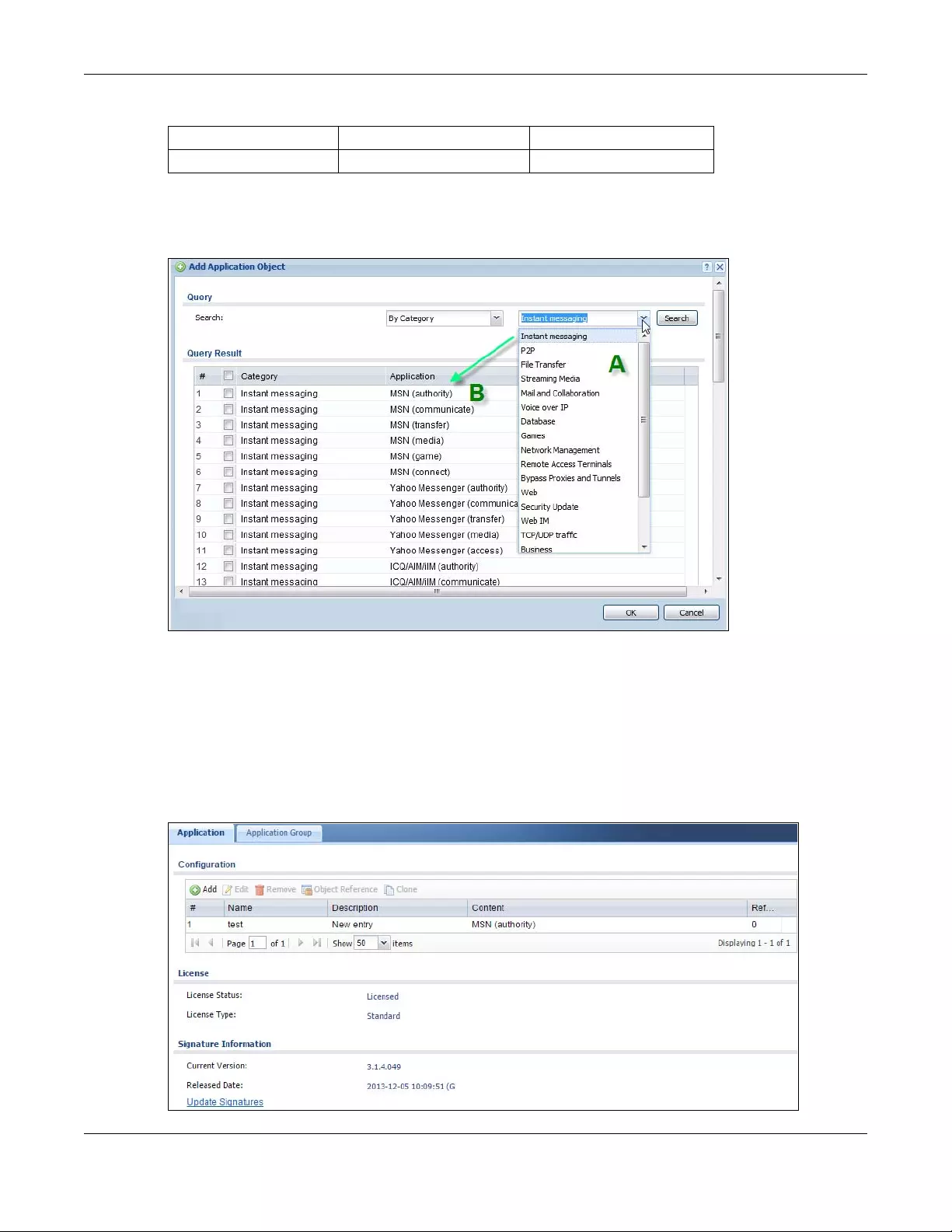
Chapter 43 Object
USG/ZyWALL User’s Guide
769
The following table shows the types of categories currently supported (A) and the associated signatures
for each category (B).
Figure 536 Application Categories and Associated Signatures
• Use the Application screen (Section on page 769) to create application objects that can be used in
App Patrol profiles.
• Use the Application Group screen (Section 43.5.2 on page 773) to group application objects as an
individual object that can be used in App Patrol profiles.
The Application screen allows you to create application objects consisting of service signatures as well
as view license and signature information. To access this screen click Configuration > Object >
Application > Application.
Figure 537 Configuration > Object > Application > Application
• Business • Network Protocols • Mobile
• Private Protocol • Social Network •
Table 304 Categories of Applications
Chapter 43 Object
USG/ZyWALL User’s Guide
770
The following table describes the labels in this screen.
43.5.1 Add Application Rule
Click Add in Configuration > Object > Application > Applicatio n to create a new application rule. In the
first screen you type a name to identify this application object and write an optional brief description of
it.
Table 305 Configuration > Object > Application > Application
LABEL DESCRIPTION
Configuration
Add Click this to add a new application object.
Edit Click this to edit the selected application object.
Remove Click this to remove the selected application object.
Object
Reference Click this to view which other objects are linked to the selected application object.
Clone Use Clone to create a new entry by modifying an existing one.
• Select an existing entry.
•Click Clone.
• A configuration copy of the selected entry pops up. You must at least change the name as
duplicate entry names are not allowed.
# This field is a sequential value associated with an application object.
Name This field indicates the name assigned to the application object.
Description This field shows some extra information on the application object.
Content This field shows the application signature(s) in this application object.
Reference This displays the number of times an object reference is used in a profile.
License You need to buy a license or use a trial license in order to use IDP/AppPatrol signatures. These
fields show license-related information.
License Status This field shows whether you have activated an IDP/AppPatrol signatures license
License Type This field shows the type of IDP/AppPatrol signatures license you have activated
Signature
Information
An activated license allows you to download signatures to the Zyxel Device from myZyxel.com.
These fields show details on the signatures downloaded.
Current
Version The version number increments when signatures are updated at myZyxel.com. This field shows
the current version downloaded to the Zyxel Device.
Released
Date This field shows the date (YYYY-MM-DD) and time the current signature version was released.
Update
Signatures If your signature set is not the most recent, click this to go to Configuration > Licensing >
Signature Update > IDP / AppPatrol to update your signatures.
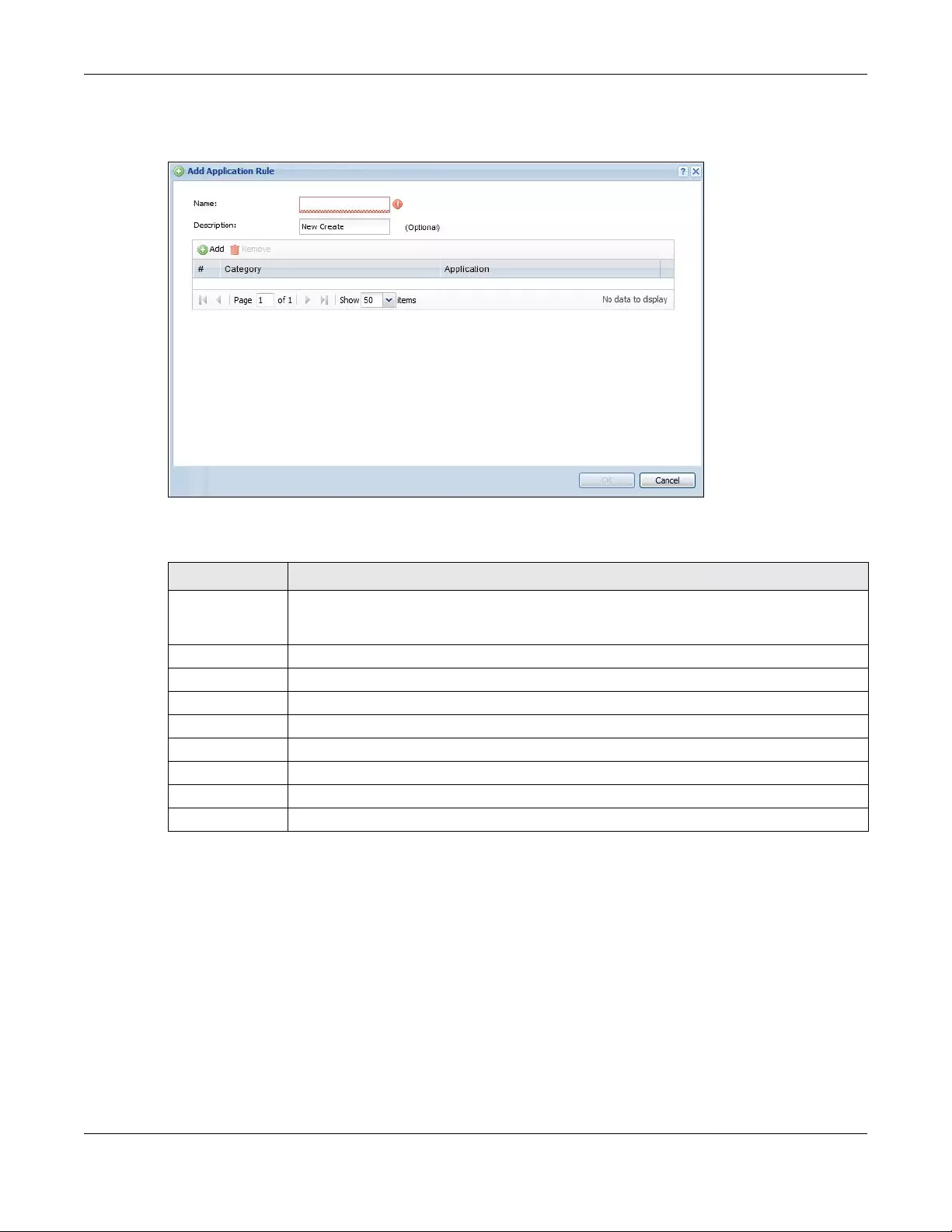
Chapter 43 Object
USG/ZyWALL User’s Guide
771
You then click Add again to choose the signatures that should go into this object.
Figure 538 Configuration > Object > Application > Application > Add Application Rule
The following table describes the labels in this screen.
Table 306 Configuration > Object > Application > Application > Add Application Rule
LABEL DESCRIPTION
Name Type a name to identify this application rule. You may use 1-31 alphanumeric characters,
underscores(_), or dashes (-), but the first character cannot be a number. This value is case-
sensitive.
Description You may type some extra information on the application object here.
Add Click this to create a new application rule.
Remove Click this to remove the selected application rule.
# This field is a sequential value associated with this application rule.
Category This field shows the category to which the signature belongs in this application rule.
Application This displays the name of the application signature used in this application rule.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
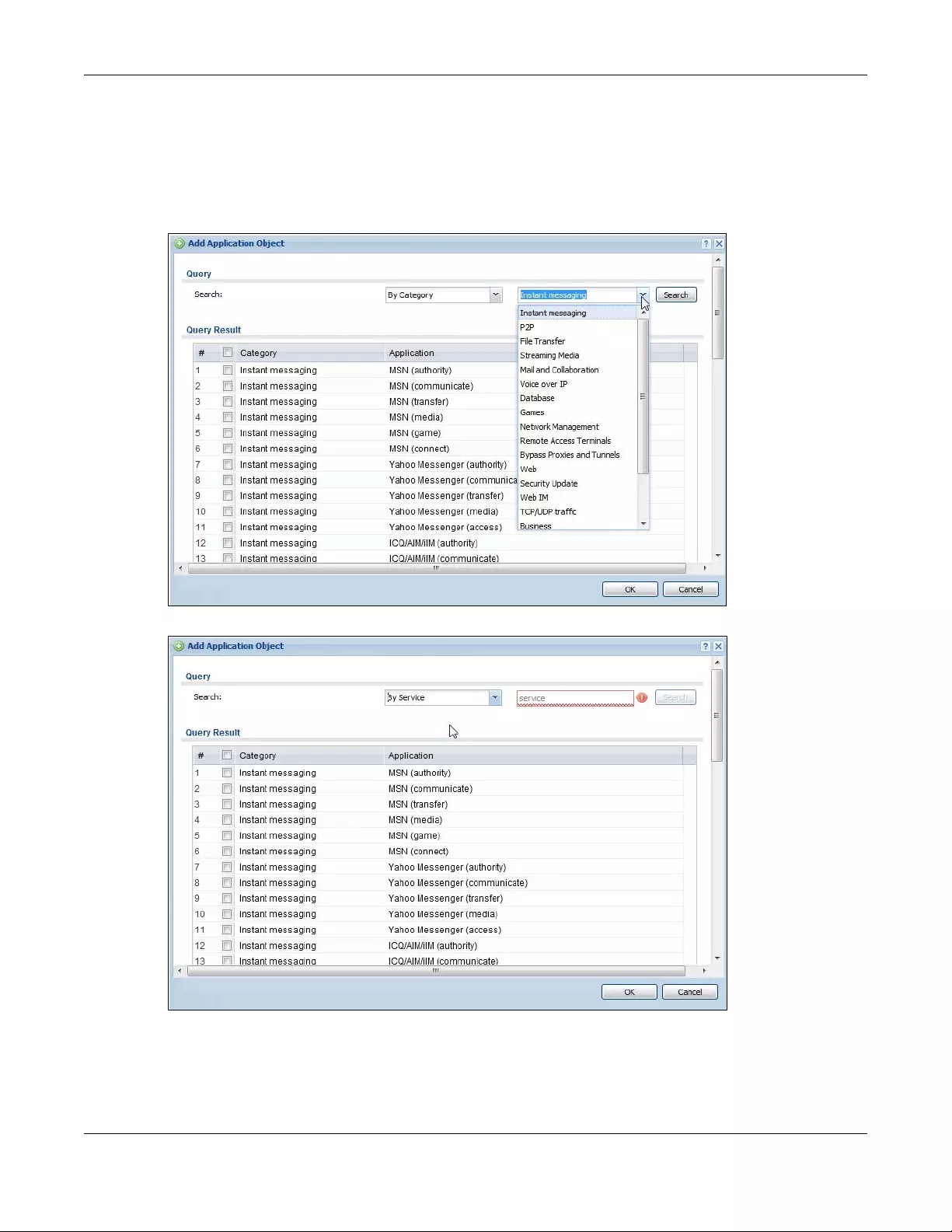
Chapter 43 Object
USG/ZyWALL User’s Guide
772
43.5.1.1 Add Application Object by Category or Service
Click Add in Configuration > Object > Application > Application > Add Application Rule to choose the
signatures that should go into this object.
Figure 539 Configuration > Object > Application > Application > Add Application Rule > Add By
Category
Figure 540 Configuration > Object > Application > Application > Add Application Rule > Add By Service
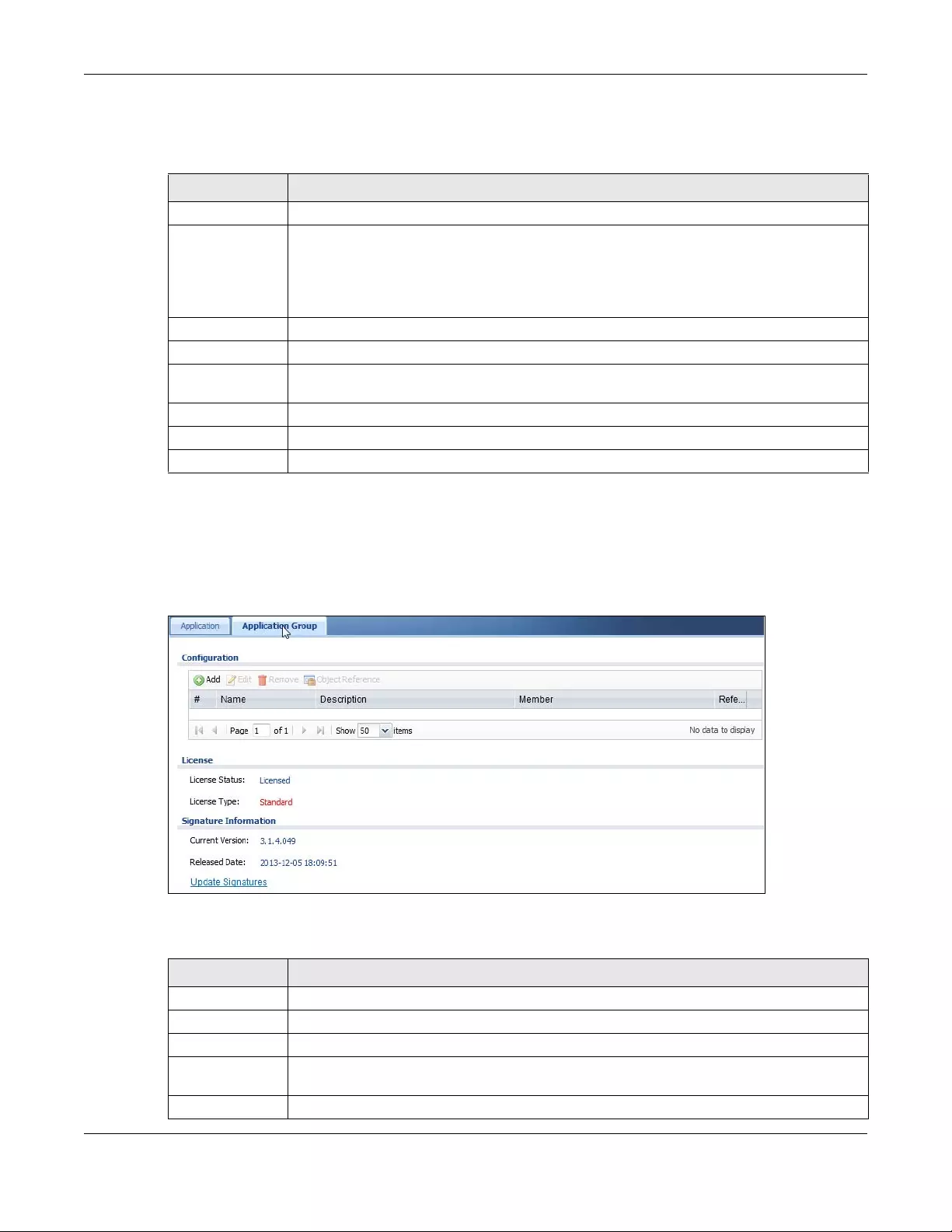
Chapter 43 Object
USG/ZyWALL User’s Guide
773
The following table describes the labels in this screen.
43.5.2 Application Group Screen
This screen allows you to group individual application objects to be treated as a single application
object. To access this screen click Configuration > Object > Application > Application Group.
Figure 541 Configuration > Object > Application > Application Group
The following table describes the labels in this screen.
Table 307 Configuration > Object > Application > Application > Add Application Rule > Add
Application Object
LABEL DESCRIPTION
Query
Search Choose signatures in one of the following ways:
• Select By Category then select a category in the adjacent drop-down list box to display all
signatures of that category
• Select By Service, type a keyword and click Search to display all signatures containing that
keyword.
Query Result The results of the search are displayed here.
# This field is a sequential value associated with this signature
Category This field shows the category to which the signature belongs. Select the checkbox to add this
signature to the application object.
Application This displays the name of the application signature.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
Table 308 Configuration > Object > Application > Application Group
LABEL DESCRIPTION
Add Click this to add a new application group.
Edit Click this to edit the selected application group.
Remove Click this to remove the selected application group.
Object
Reference
Click this to view which other objects are linked to the selected application group.
# This field is a sequential value associated with an application group.
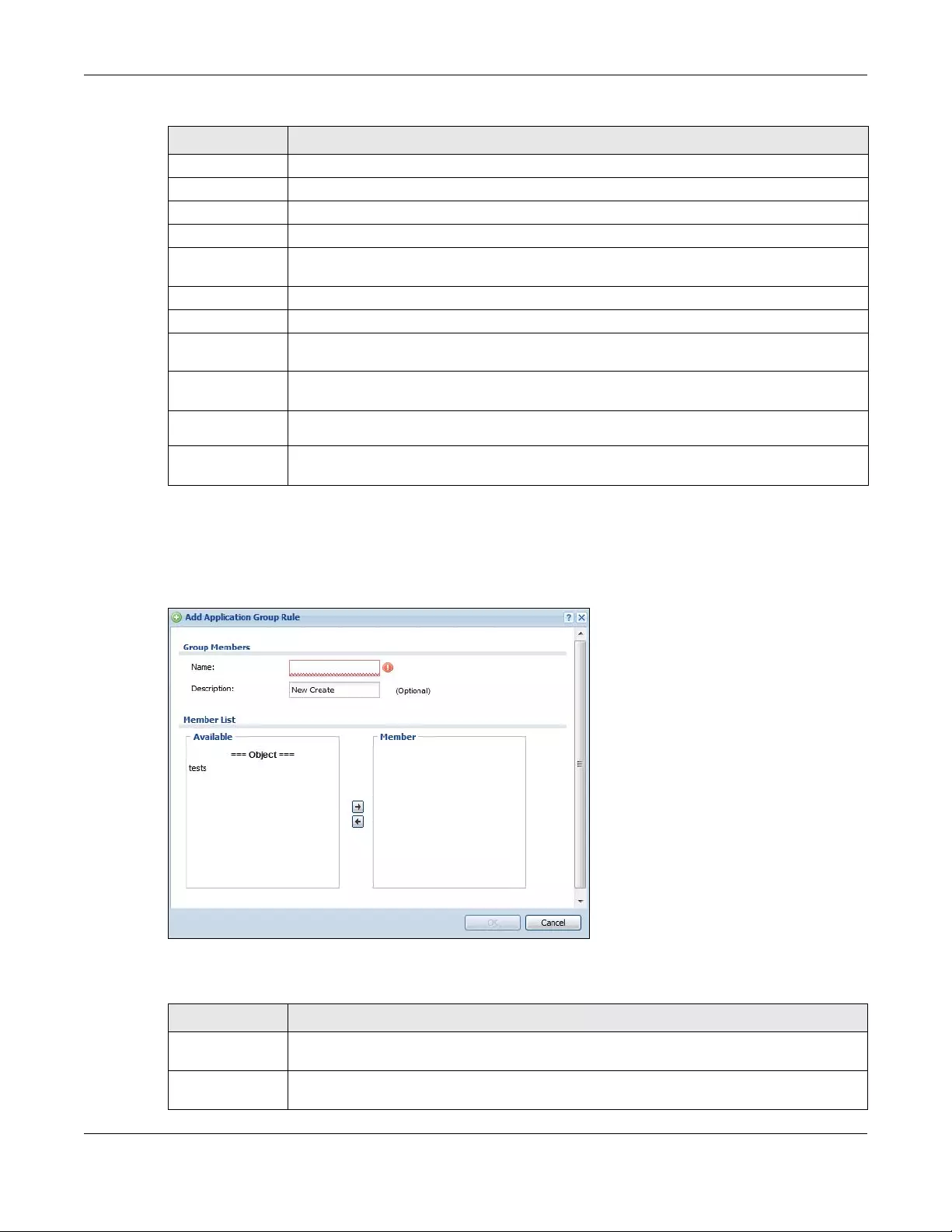
Chapter 43 Object
USG/ZyWALL User’s Guide
774
43.5.2.1 Add Application Group Rule
Click Add in Configuration > Object > Application > Application Group to select already created
application rules and combine them as a single new rule.
Figure 542 Configuration > Object > Application > Application > Add Application Group Rule
The following table describes the labels in this screen.
Name This field indicates the name assigned to the application group.
Description You may type some extra information on the application group here.
Member This field shows the application objects in this application group.
Reference This displays the number of times an object reference is used in a profile.
License You need to buy a license or use a trial license in order to use IDP/AppPatrol signatures. These
fields show license-related information.
License Status This field shows whether you have activated an IDP/AppPatrol signatures license
License Type This field shows the type of IDP/AppPatrol signatures license you have activated
Signature
Information
An activated license allows you to download signatures to the Zyxel Device from myZyxel.com.
These fields show details on the signatures downloaded.
Current
Version The version number increments when signatures are updated at myZyxel.com. This field shows
the current version downloaded to the Zyxel Device.
Released
Date This field shows the date (YYYY-MM-DD) and time the current signature version was released.
Update
Signatures If your signature set is not the most recent, click this to go to Configuration > Licensing >
Signature Update > IDP / AppPatrol to update your signatures.
Table 308 Configuration > Object > Application > Application Group (continued)
LABEL DESCRIPTION
Table 309 Configuration > Object > Application > Application > Add Application Group Rule
LABEL DESCRIPTION
Name Enter a name for the group. You may use 1-31 alphanumeric characters, underscores(_), or
dashes (-), but the first character cannot be a number. This value is case-sensitive.
Description This field displays the description of each group, if any. You can use up to 60 characters,
punctuation marks, and spaces.
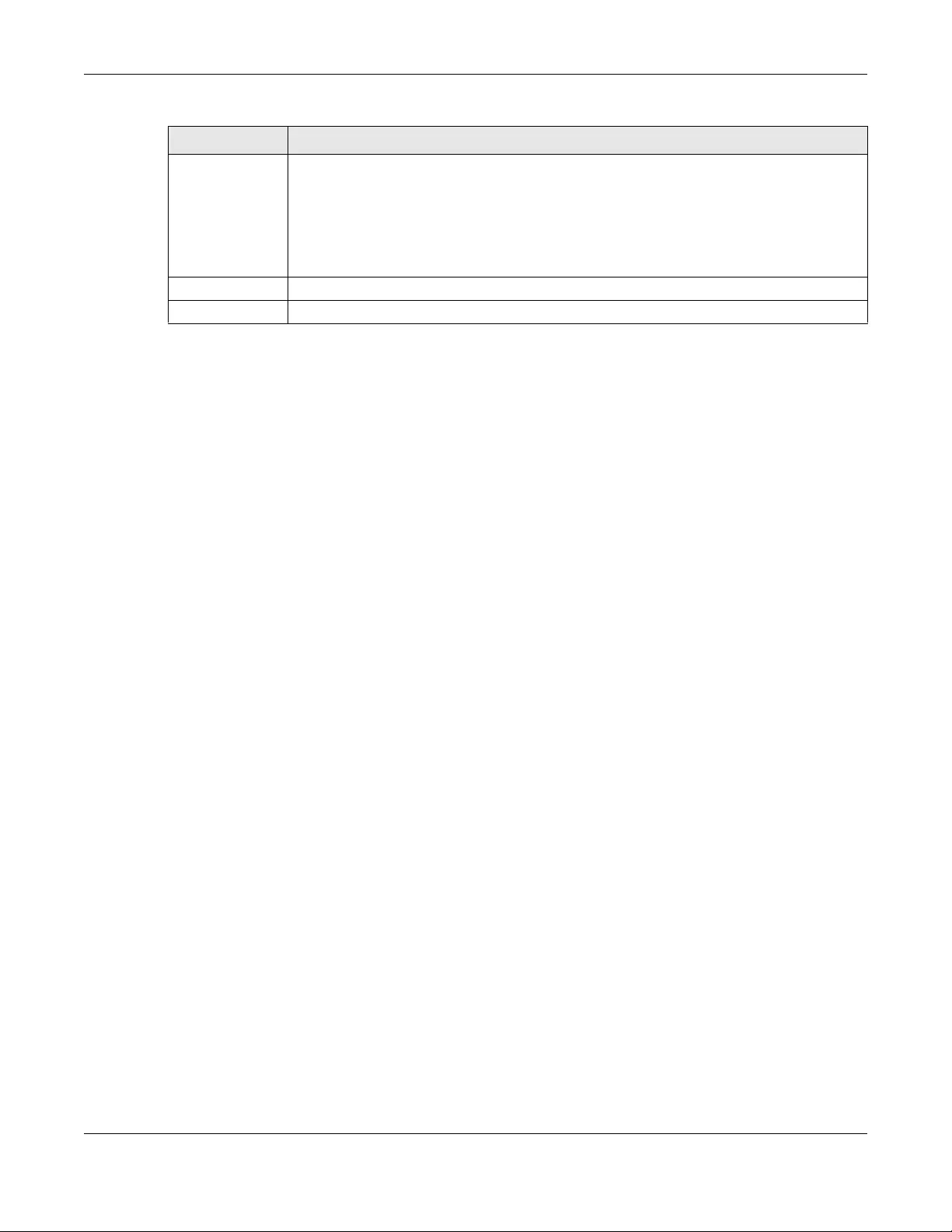
Chapter 43 Object
USG/ZyWALL User’s Guide
775
43.6 Address/Geo IP Overview
Address objects can represent a single IP address or a range of IP addresses. Address groups are
composed of address objects and other address groups.
• The Address screen (Section 43.6.2 on page 775) provides a summary of all addresses in the Zyxel
Device. Use the Address Add/Edit screen to create a new address or edit an existing one.
• Use the Address Group summary screen (Section 43.6.3 on page 779) and the Address Group Add/
Edit screen, to maintain address groups in the Zyxel Device.
• Use the Geo IP screen (Section 43.6.4 on page 781) to update the database of country-to-IP address
mappings and to manually configure country-to-IP address mappings.
43.6.1 What You Need To Know
Address objects and address groups are used in dynamic routes, security policies, application patrol,
content filtering, and VPN connection policies. For example, addresses are used to specify where
content restrictions apply in content filtering. Please see the respective sections for more information
about how address objects and address groups are used in each one.
Address groups are composed of address objects and address groups. The sequence of members in the
address group is not important.
43.6.2 Address Summary Screen
The address screens are used to create, maintain, and remove addresses. There are the types of
address objects:
•HOST - a host address is defined by an IP Address
•RANGE - a range address is defined by a Starting IP Address and an Ending IP Address
•SUBNET - a network address is defined by a Network IP address and Netmask subnet mask
•GEOGRAPHY - an address object is defined by the IP addresses of a country.
The Address screen provides a summary of all addresses in the Zyxel Device. To access this screen, click
Configuration > Object > Address > Address. Click a column’s heading cell to sort the table entries by
that column’s criteria. Click the heading cell again to reverse the sort order.
Member List The Member list displays the names of the application and application group objects that
have been added to the application group. The order of members is not important.
Select items from the Available list that you want to be members and move them to the
Member list. You can double-click a single entry to move it or use the [Shift] or [Ctrl] key to
select multiple entries and use the arrow button to move them.
Move any members you do not want included to the Available list.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
Table 309 Configuration > Object > Application > Application > Add Application Group Rule
LABEL DESCRIPTION
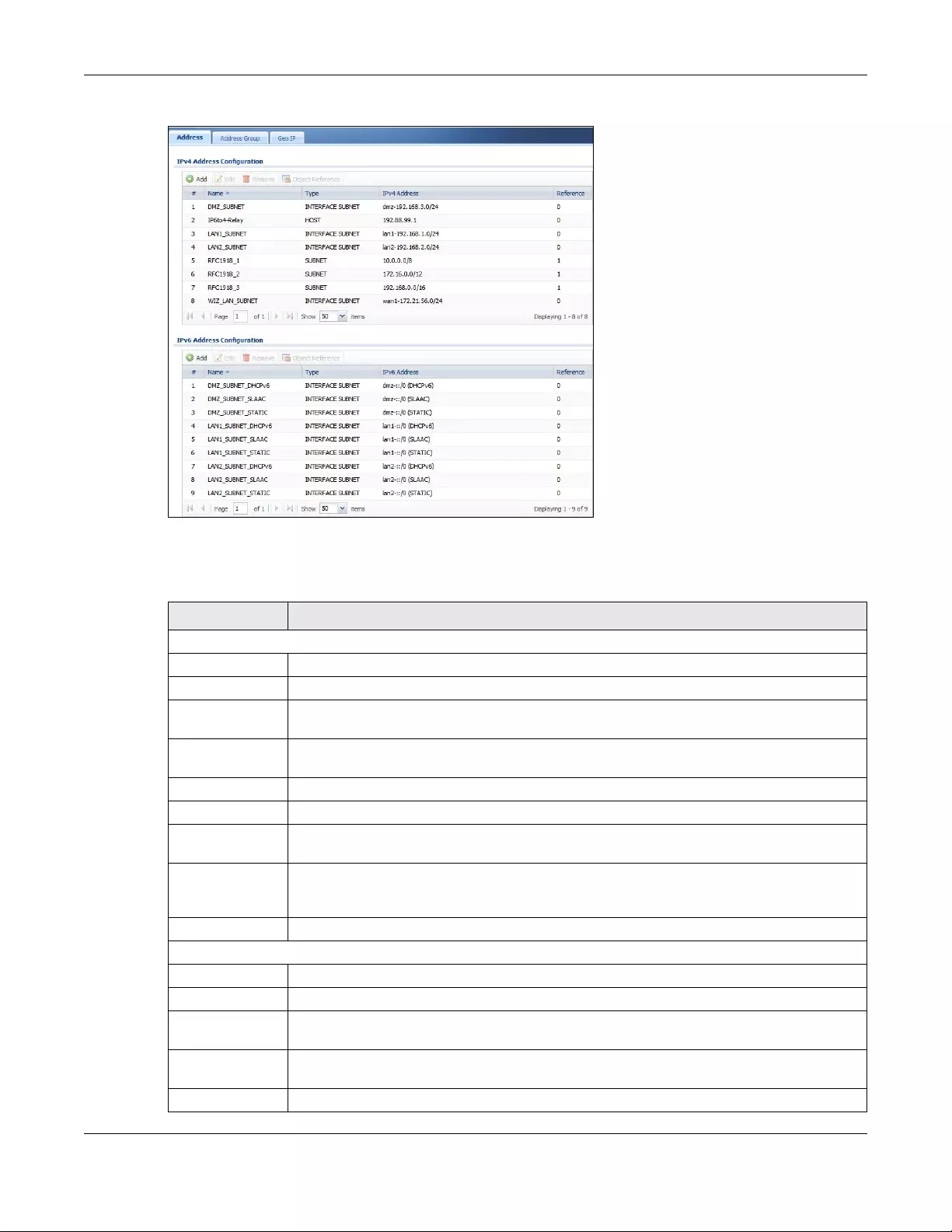
Chapter 43 Object
USG/ZyWALL User’s Guide
776
Figure 543 Configuration > Object > Address/Geo IP > Address
The following table describes the labels in this screen. See Section 43.6.2.1 on page 777 for more
information as well.
Table 310 Configuration > Object > Address/Geo IP > Address
LABEL DESCRIPTION
IPv4 Address Configuration
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Object
References
Select an entry and click Object References to open a screen that shows which settings use
the entry.
# This field is a sequential value, and it is not associated with a specific address.
Name This field displays the configured name of each address object.
Type This field displays the type of each address object. “INTERFACE” means the object uses the
settings of one of the Zyxel Device’s interfaces.
IPv4 Address This field displays the IPv4 addresses represented by each address object. If the object’s
settings are based on one of the Zyxel Device’s interfaces, the name of the interface displays
first followed by the object’s current address settings.
Reference This displays the number of times an object reference is used in a profile.
IPv6 Address Configuration
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Object
References
Select an entry and click Object References to open a screen that shows which settings use
the entry.
# This field is a sequential value, and it is not associated with a specific address.
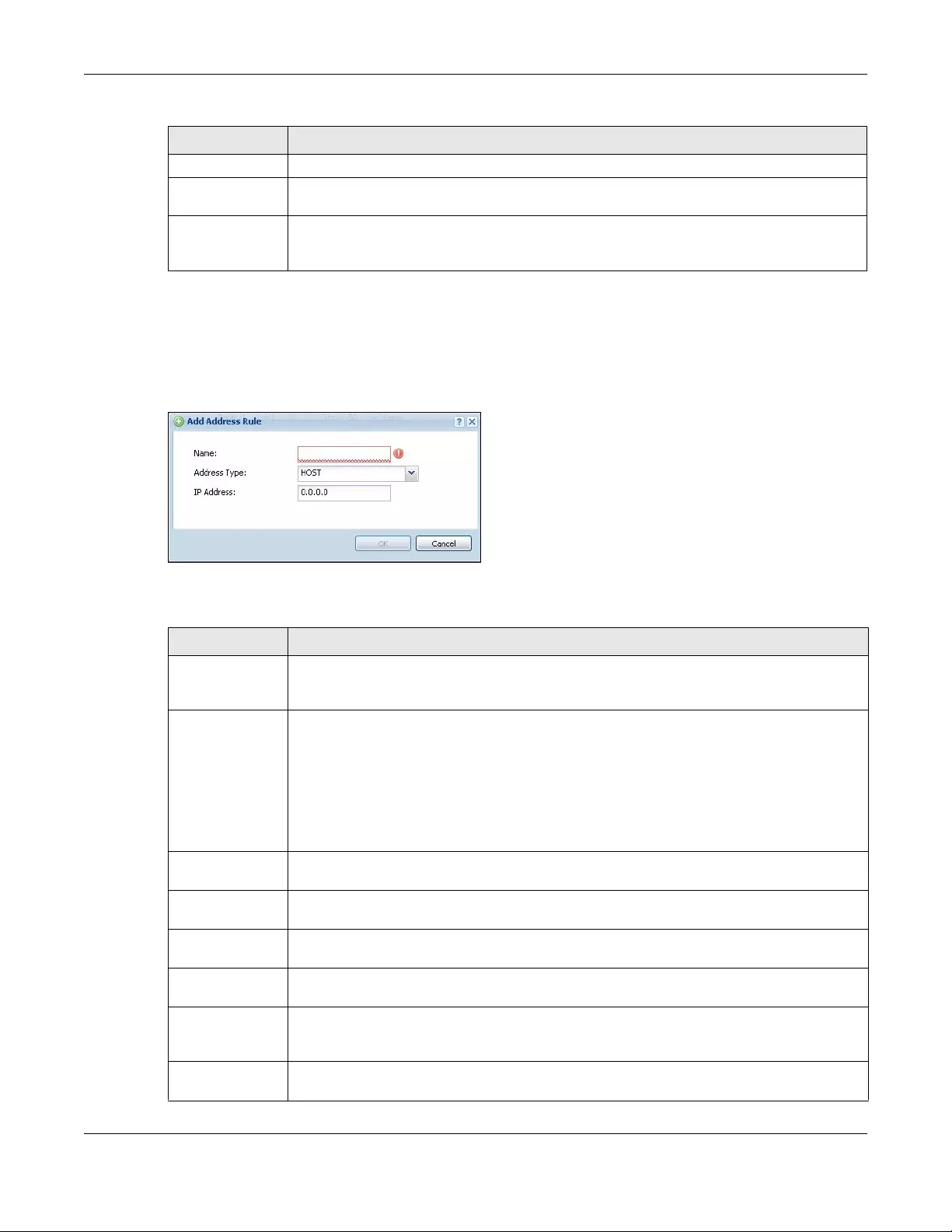
Chapter 43 Object
USG/ZyWALL User’s Guide
777
43.6.2.1 IPv4 Address Add/Edit Screen
The Configuration > IPv4 Add ress Add/Edit screen allows you to create a new address or edit an existing
one. To access this screen, go to the Address screen (see Section 43.6.2 on page 775), and click either
the Add icon or an Edit icon in the IPv4 Address Configuration section.
Figure 544 IPv4 Address Configuration > Add/Edit
The following table describes the labels in this screen.
Name This field displays the configured name of each address object.
Type This field displays the type of each address object. “INTERFACE” means the object uses the
settings of one of the Zyxel Device’s interfaces.
IPv6 Address This field displays the IPv6 addresses represented by each address object. If the object’s
settings are based on one of the Zyxel Device’s interfaces, the name of the interface displays
first followed by the object’s current address settings.
Table 310 Configuration > Object > Address/Geo IP > Address (continued)
LABEL DESCRIPTION
Table 311 IPv4 Address Configuration > Add/Edit
LABEL DESCRIPTION
Name Type the name used to refer to the address. You may use 1-31 alphanumeric characters,
underscores(_), or dashes (-), but the first character cannot be a number. This value is case-
sensitive.
Address Type Select the type of address you want to create. Choices are: HOST, RANGE, SUBNET, INTERFACE
IP, INTERFACE SUBNET, INTERFACE GATEWAY and GEOGRAPHY.
Note: The Zyxel Device automatically updates address objects that are based on an
interface’s IP address, subnet, or gateway if the interface’s IP address settings
change. For example, if you change 1’s IP address, the Zyxel Device
automatically updates the corresponding interface-based, LAN subnet
address object.
IP Address This field is only available if the Address Type is HOST. This field cannot be blank. Enter the IP
address that this address object represents.
Starting IP
Address
This field is only available if the Address Type is RANGE. This field cannot be blank. Enter the
beginning of the range of IP addresses that this address object represents.
Ending IP Address This field is only available if the Address Type is RANGE. This field cannot be blank. Enter the end
of the range of IP address that this address object represents.
Network This field is only available if the Address Type is SUBNET, in which case this field cannot be blank.
Enter the IP address of the network that this address object represents.
Netmask This field is only available if the Address Type is SUBNET, in which case this field cannot be blank.
Enter the subnet mask of the network that this address object represents. Use dotted decimal
format.
Interface If you selected INTERFACE IP , INTERFACE SUBNET, or INTERFACE GATEWAY as the Address Type,
use this field to select the interface of the network that this address object represents.
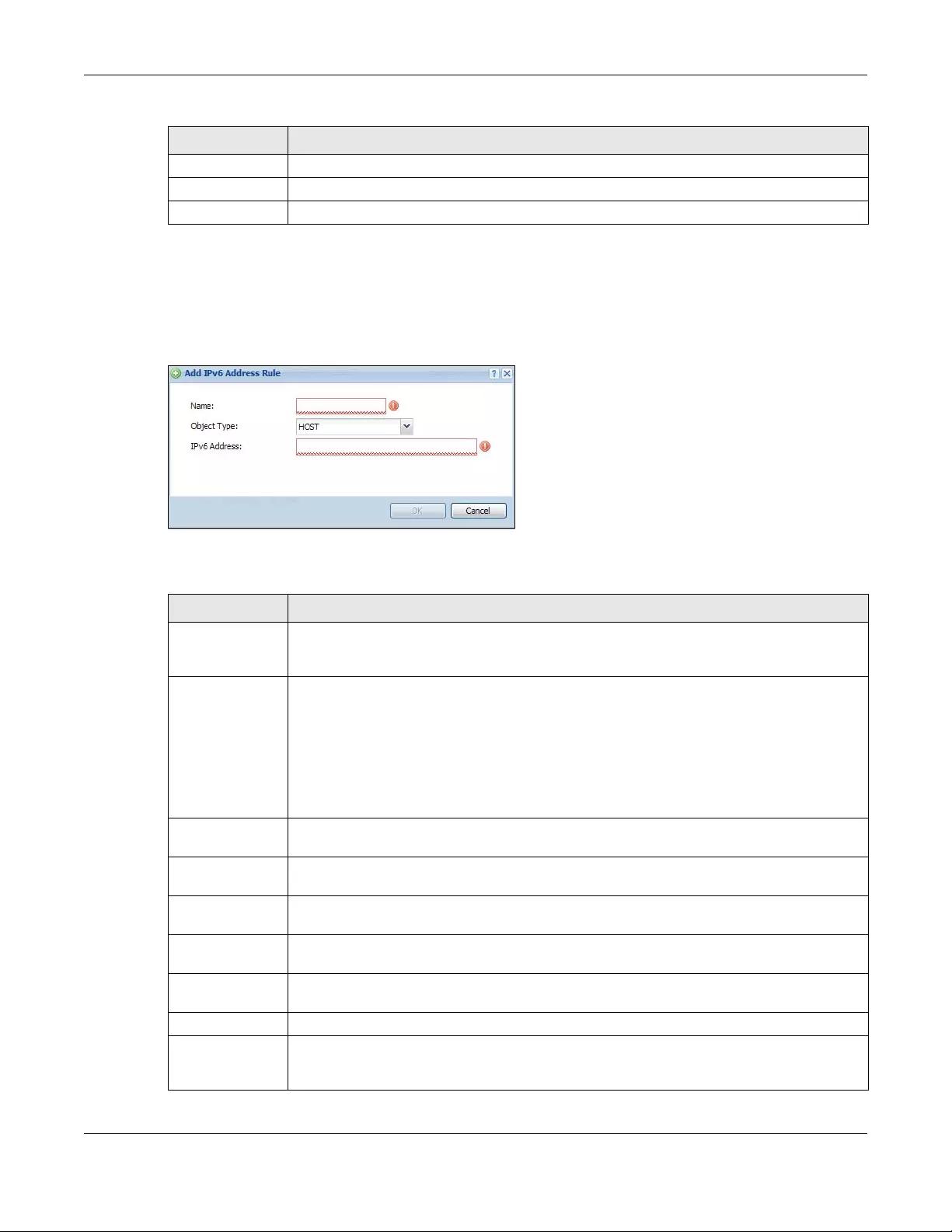
Chapter 43 Object
USG/ZyWALL User’s Guide
778
43.6.2.2 IPv6 Address Add/Edit Screen
The Configuration > IPv6 Add ress Add/Edit screen allows you to create a new address or edit an existing
one. To access this screen, go to the Address screen (see Section 43.6.2 on page 775), and click either
the Add icon or an Edit icon in the IPv6 Address Configuration section.
Figure 545 IPv6 Address Configuration > Add/Edit
The following table describes the labels in this screen.
Country If you selected Geography as the Address Type, use this field to select a country.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
Table 311 IPv4 Address Configuration > Add/Edit (continued)
LABEL DESCRIPTION
Table 312 IPv6 Address Configuration > Add/Edit
LABEL DESCRIPTION
Name Type the name used to refer to the address. You may use 1-31 alphanumeric characters,
underscores(_), or dashes (-), but the first character cannot be a number. This value is case-
sensitive.
Object Type Select the type of address you want to create. Choices are: HOST, RANGE, SUBNET, INTERFACE
IP, INTERFACE SUBNET, and INTER FACE GATE WAY and GEOGRAPHY.
Note: The Zyxel Device automatically updates address objects that are based on an
interface’s IP address, subnet, or gateway if the interface’s IP address settings
change. For example, if you change 1’s IP address, the Zyxel Device
automatically updates the corresponding interface-based, LAN subnet
address object.
IPv6 Address This field is only available if the Address Type is HOST. This field cannot be blank. Enter the IP
address that this address object represents.
IPv6 Starting
Address
This field is only available if the Address Type is RANGE. This field cannot be blank. Enter the
beginning of the range of IP addresses that this address object represents.
IPv6 Ending
Address
This field is only available if the Address Type is RANGE. This field cannot be blank. Enter the end
of the range of IP address that this address object represents.
IPv6 Address
Prefix
This field is only available if the Addr ess Type is SUBNET. This field cannot be blank. Enter the IPv6
address prefix that the Zyxel Device uses for the LAN IPv6 address.
Interface If you selected INTERFACE IP , INTERFACE SUBNET, or INTERFACE GATEWAY as the Address Type,
use this field to select the interface of the network that this address object represents.
Country If you selected Geography as the Address Type, use this field to select a country.
IPv6 Address Type Select whether the IPv6 address is a link-local IP address (LINK LOCAL), static IP address
(STATIC), an IPv6 StateLess Address Auto Configuration IP address (SLAAC), or is obtained from
a DHCPv6 server (DHCPv6).
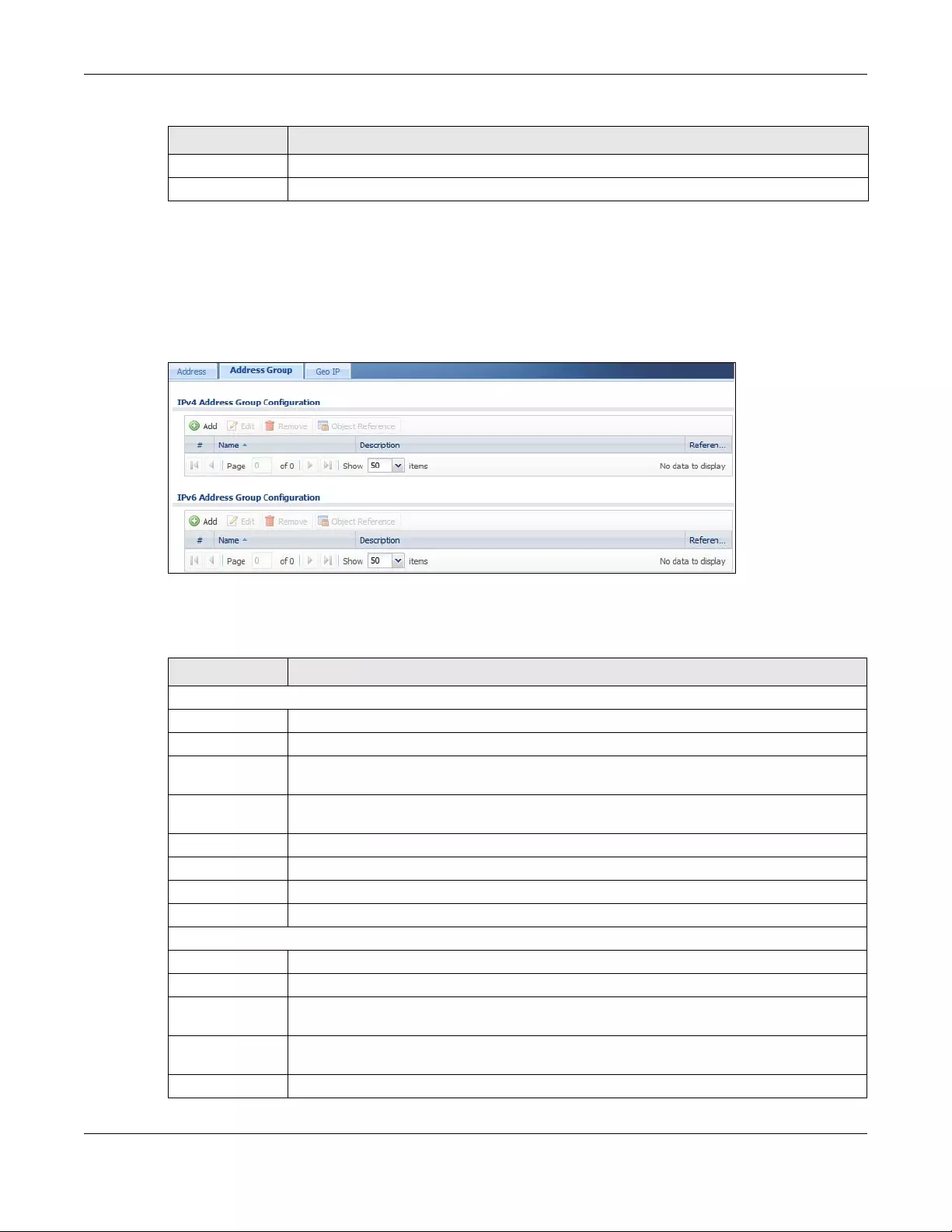
Chapter 43 Object
USG/ZyWALL User’s Guide
779
43.6.3 Address Group Summary Screen
The Address Group screen provides a summary of all address groups. To access this screen, click
Configuration > Object > Address/Geo IP > Address Group. Click a column’s heading cell to sort the
table entries by that column’s criteria. Click the heading cell again to reverse the sort order.
Figure 546 Configuration > Object > Address/Geo IP > Address Group
The following table describes the labels in this screen. See Section 43.6.3.1 on page 780 for more
information as well.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
Table 312 IPv6 Address Configuration > Add/Edit (continued)
LABEL DESCRIPTION
Table 313 Configuration > Object > Address/Geo IP > Address Group
LABEL DESCRIPTION
IPv4 Address Group Configuration
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Object
References
Select an entry and click Object References to open a screen that shows which settings use
the entry.
# This field is a sequential value, and it is not associated with a specific address group.
Name This field displays the name of each address group.
Description This field displays the description of each address group, if any.
Reference This displays the number of times an object reference is used in a profile.
IPv6 Address Group Configuration
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Object
References
Select an entry and click Object References to open a screen that shows which settings use
the entry.
# This field is a sequential value, and it is not associated with a specific address group.
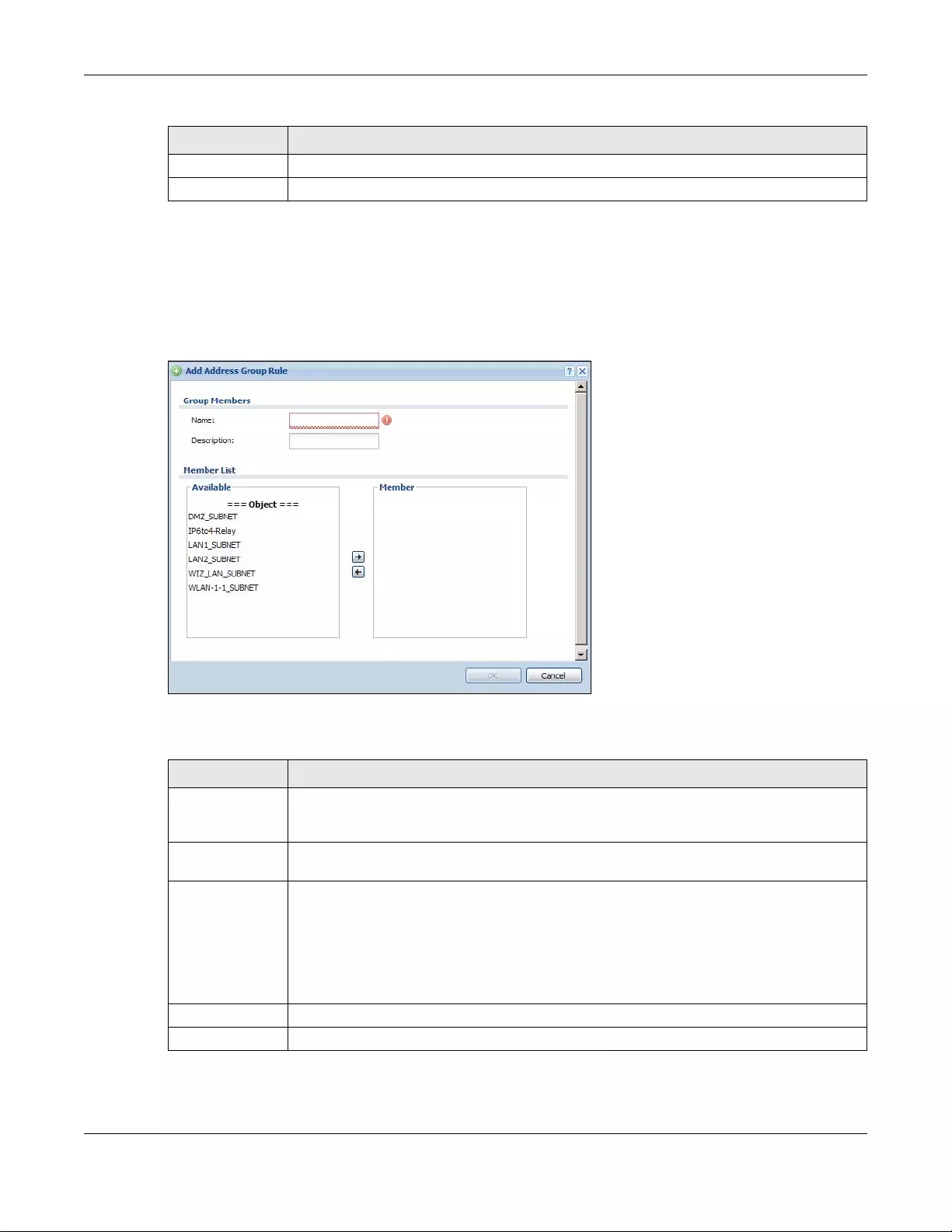
Chapter 43 Object
USG/ZyWALL User’s Guide
780
43.6.3.1 Address Group Add/Edit Screen
The Address Group Add/Edit screen allows you to create a new address group or edit an existing one. To
access this screen, go to the Address Group screen (see Section 43.6.3 on page 779), and click either
the Add icon or an Edit icon in the IPv4 Address Group Configuration or IPv6 Address Group
Configuration section.
Figure 547 IPv4/IPv6 Address Group Configuration > Add
The following table describes the labels in this screen.
Name This field displays the name of each address group.
Description This field displays the description of each address group, if any.
Table 313 Configuration > Object > Address/Geo IP > Address Group (continued)
LABEL DESCRIPTION
Table 314 IPv4/IPv6 Address Group Configuration > Add
LABEL DESCRIPTION
Name Enter a name for the address group. You may use 1-31 alphanumeric characters,
underscores(_), or dashes (-), but the first character cannot be a number. This value is case-
sensitive.
Description This field displays the description of each address group, if any. You can use up to 60
characters, punctuation marks, and spaces.
Member List The Member list displays the names of the address and address group objects that have been
added to the address group. The order of members is not important.
Select items from the Available list that you want to be members and move them to the
Member list. You can double-click a single entry to move it or use the [Shift] or [Ctrl] key to
select multiple entries and use the arrow button to move them.
Move any members you do not want included to the Available list.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
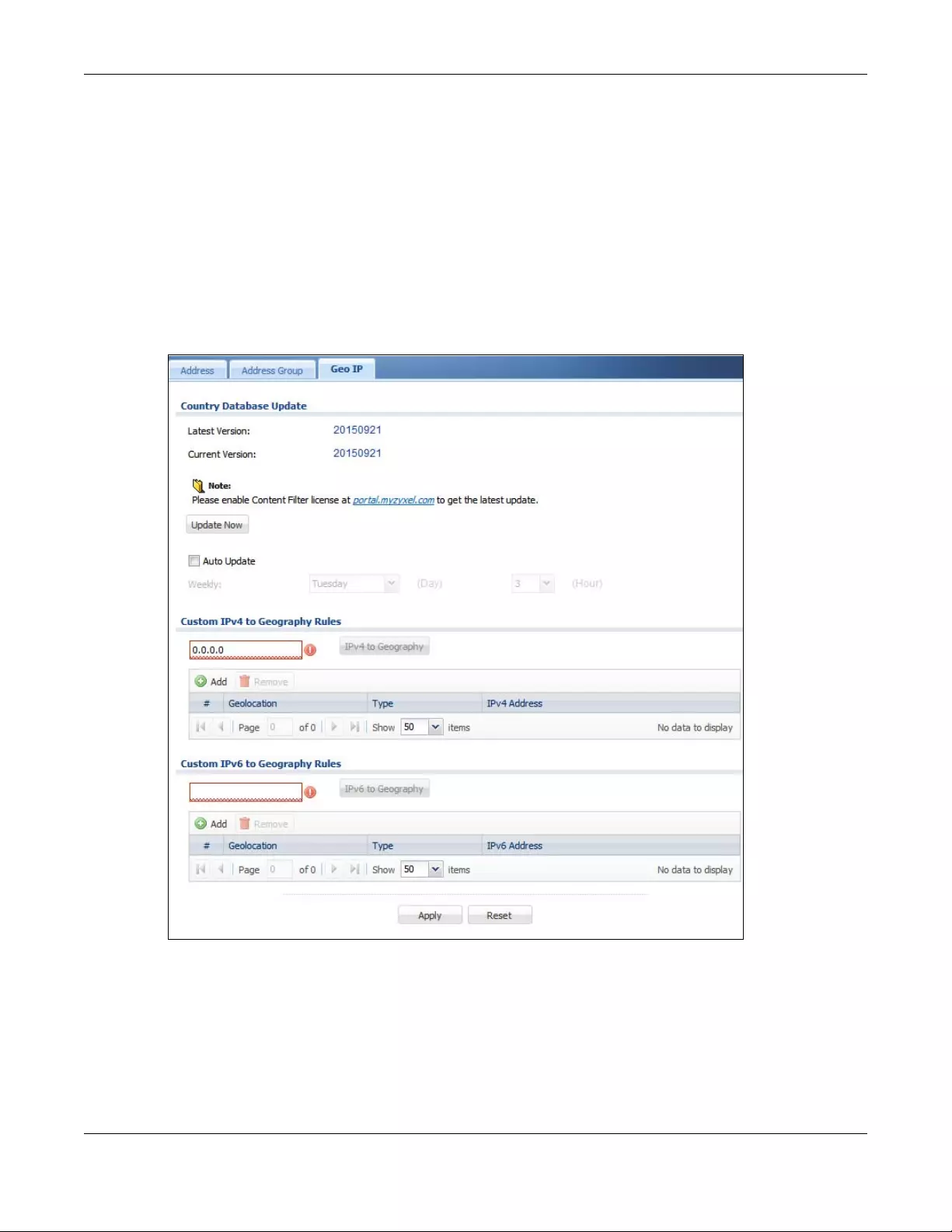
Chapter 43 Object
USG/ZyWALL User’s Guide
781
43.6.4 Geo IP Summary Screen
Use this screen to update the database of country-to-IP address mappings and manually configure
custom country-to-IP address mappings in geographic address objects. You can then use geographic
address objects in security policies to forward or deny traffic to whole countries or regions.
Note: You need to have a registered Content Filter 2.0 Service license to use the country-to-
IP-address database.
Click a column’s heading cell to sort the table entries by that column’s criteria. Click the heading cell
again to reverse the sort order.
Figure 548 Configuration > Object > Address/Geo IP > Geo IP
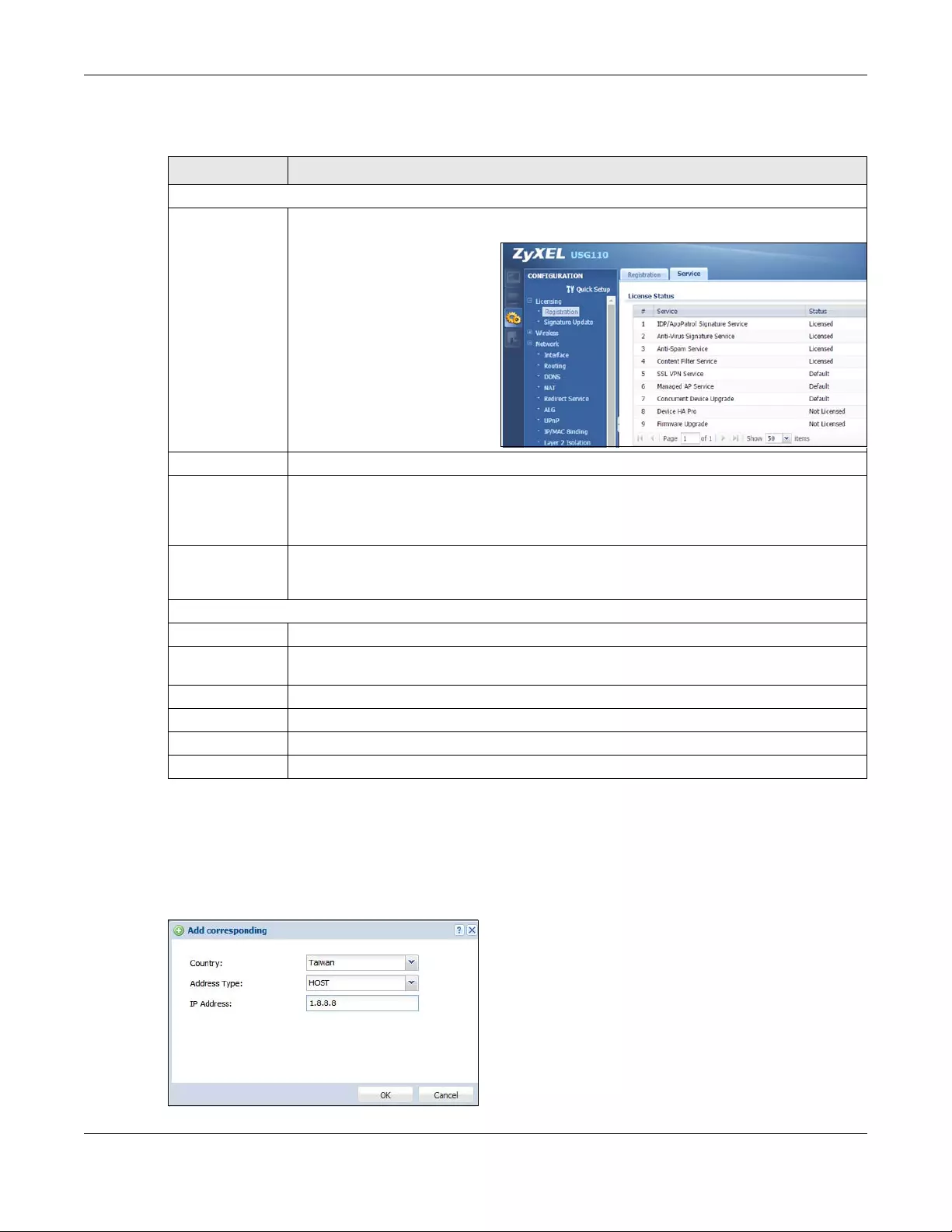
Chapter 43 Object
USG/ZyWALL User’s Guide
782
The following table describes the labels in this screen.
43.6.4.1 Add Custom IPv4/IPv6 Address to Geography Screen
This screen allows you to create a new geography-to-IP-address mapping. To access this screen, go to
the Geo IP screen (see Section 43.6.4 on page 781), and click the Add icon in the Custom IPv4 to
Geography Rules or Custom IPv6 to Geography Rules section.
Figure 549 Geo IP > Add
Table 315 Configuration > Object > Address/Geo IP > Geo IP
LABEL DESCRIPTION
Country Database Update
Latest Version This is the latest country-to-IP address database version on myZyxel.com. You need to have a
registered Content Filter 2.0 Service license.
Current Version This is the country-to-IP-address database version currently on the Zyxel Device.
Update Now Click this to check for the latest country-to-IP-address database version on myZyxel.com. The
latest version is downloaded to the Zyxel Device and replaces the current version if it is newer.
There are logs to show the update status. You need to have a registered Content Filter 2.0
Service license.
Auto Update If you want the Zyxel Device to check weekly for the latest country-to-IP-address database
version on myZyxel.com, select the checkbox, choose a day and time each week and then
click Apply. The default day and time displayed is the Zyxel Device current day and time.
Custom IPv4/IPv6 to Geography Rules
Add Click this to create a new entry.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
# This field is a sequential value, and it is not associated with a specific entry.
Geolocation This field displays the name of the country or region that is associated with this IP address.
Type This field displays whether this address object is HOST, RANGE or SUBNET.
IPv4 Address This field displays the IPv4 addresses represented by the type of address object.
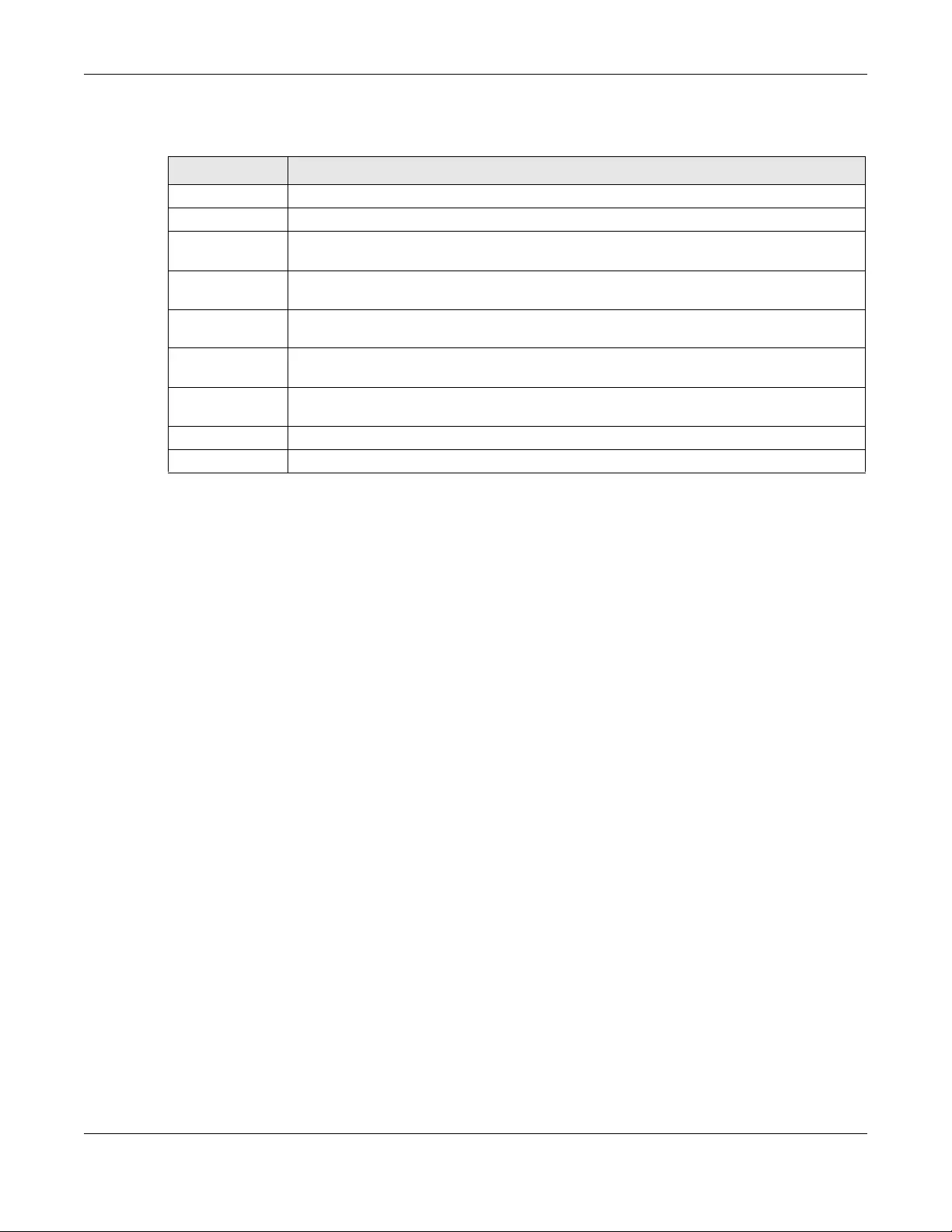
Chapter 43 Object
USG/ZyWALL User’s Guide
783
The following table describes the labels in this screen.
43.7 Service Overview
Use service objects to define TCP applications, UDP applications, and ICMP messages. You can also
create service groups to refer to multiple service objects in other features.
• Use the Service screens (Section 43.7.2 on page 784) to view and configure the Zyxel Device’s list of
services and their definitions.
• Use the Service Group screens (Section 43.7.2 on page 784) to view and configure the Zyxel Device’s
list of service groups.
43.7.1 What You Need to Know
IP Protocols
IP protocols are based on the eight-bit protocol field in the IP header. This field represents the next-level
protocol that is sent in this packet. This section discusses three of the most common IP protocols.
Computers use Transmission Control Protocol (TCP, IP protocol 6) and User Datagram Protocol (UDP, IP
protocol 17) to exchange data with each other. TCP guarantees reliable delivery but is slower and more
complex. Some uses are FTP, HTTP, SMTP, and TELNET. UDP is simpler and faster but is less reliable. Some
uses are DHCP, DNS, RIP, and SNMP.
TCP creates connections between computers to exchange data. Once the connection is established,
the computers exchange data. If data arrives out of sequence or is missing, TCP puts it in sequence or
waits for the data to be re-transmitted. Then, the connection is terminated.
In contrast, computers use UDP to send short messages to each other. There is no guarantee that the
messages arrive in sequence or that the messages arrive at all.
Table 316 Geo IP > Add
LABEL DESCRIPTION
Country Select the country or region that maps to this IP address.
Address Type Select the type of address you want to create. Choices are: HOST, RANGE, SUBNET.
IP Address This field is only available if the Address Type is HOST. This field cannot be blank. Enter the IP
address that this address object represents.
IP Starting
Address
This field is only available if the Address Type is RANGE. This field cannot be blank. Enter the
beginning of the range of IP addresses that this address object represents.
IP Ending Address This field is only available if the Address Type is RANGE. This field cannot be blank. Enter the end
of the range of IP address that this address object represents.
Network /
Netmask
These fields are only available if the IPv4 Address Type is SUBNET. They cannot be blank. Enter
the network IP and subnet mask that defines the IPv4 subnet.
IPv6 Address
Prefix
This field is only available if the IPv6 Address Type is SUBNET. This field cannot be blank. Enter the
IPv6 address prefix that the Zyxel Device uses for the LAN IPv6 address.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
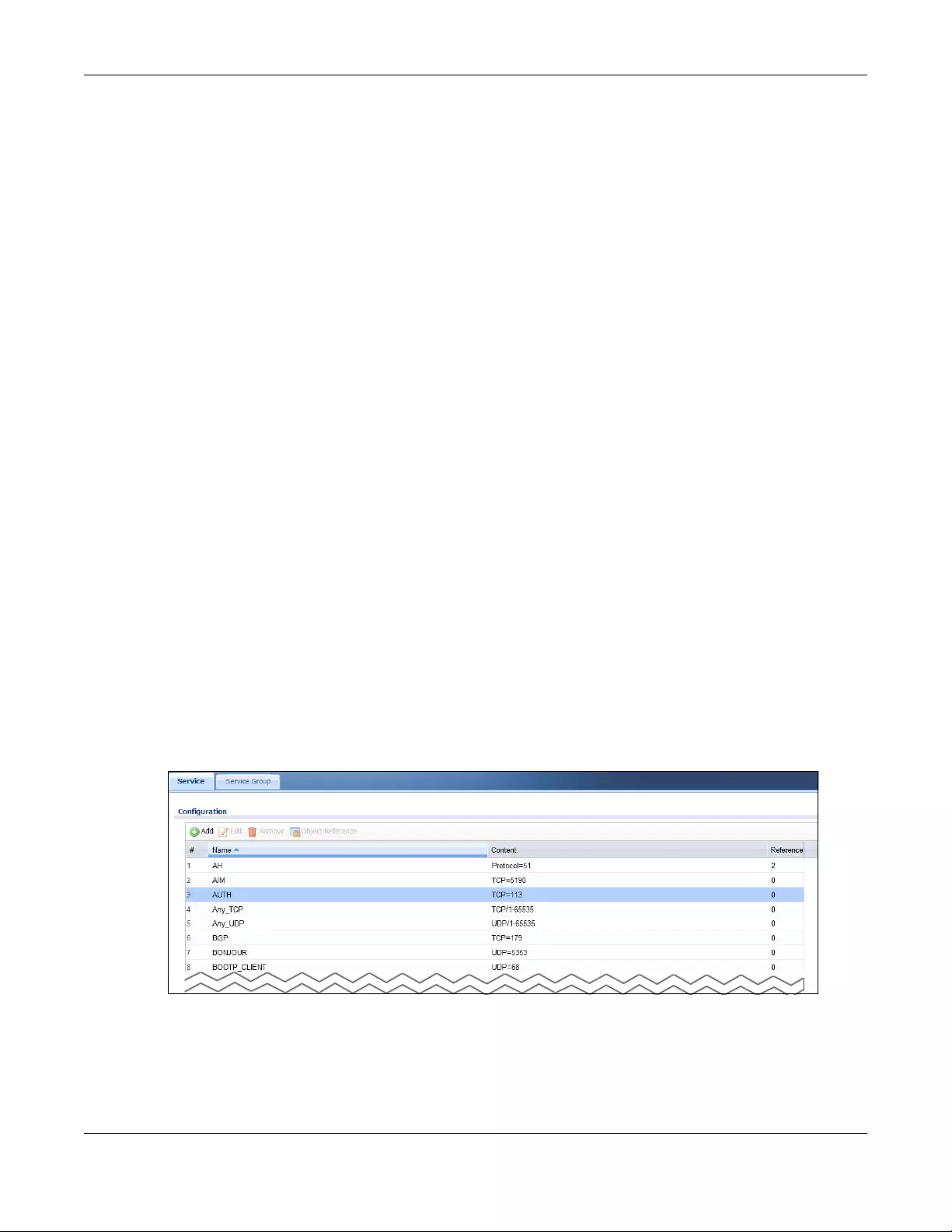
Chapter 43 Object
USG/ZyWALL User’s Guide
784
Both TCP and UDP use ports to identify the source and destination. Each port is a 16-bit number. Some
port numbers have been standardized and are used by low-level system processes; many others have
no particular meaning.
Unlike TCP and UDP, Internet Control Message Protocol (ICMP, IP protocol 1) is mainly used to send error
messages or to investigate problems. For example, ICMP is used to send the response if a computer
cannot be reached. Another use is ping. ICMP does not guarantee delivery, but networks often treat
ICMP messages differently, sometimes looking at the message itself to decide where to send it.
Service Objects and Service Groups
Use service objects to define IP protocols.
• TCP applications
• UDP applications
• ICMP messages
• user-defined services (for other types of IP protocols)
These objects are used in policy routes, security policies, and IDP profiles.
Use service groups when you want to create the same rule for several services, instead of creating
separate rules for each service. Service groups may consist of services and other service groups. The
sequence of members in the service group is not important.
43.7.2 The Service Summary Screen
The Service summary screen provides a summary of all services and their definitions. In addition, this
screen allows you to add, edit, and remove services.
To access this screen, log in to the Web Configurator, and click Configuration > Object > Service >
Service. Click a column’s heading cell to sort the table entries by that column’s criteria. Click the
heading cell again to reverse the sort order.
Figure 550 Configuration > Object > Service > Service
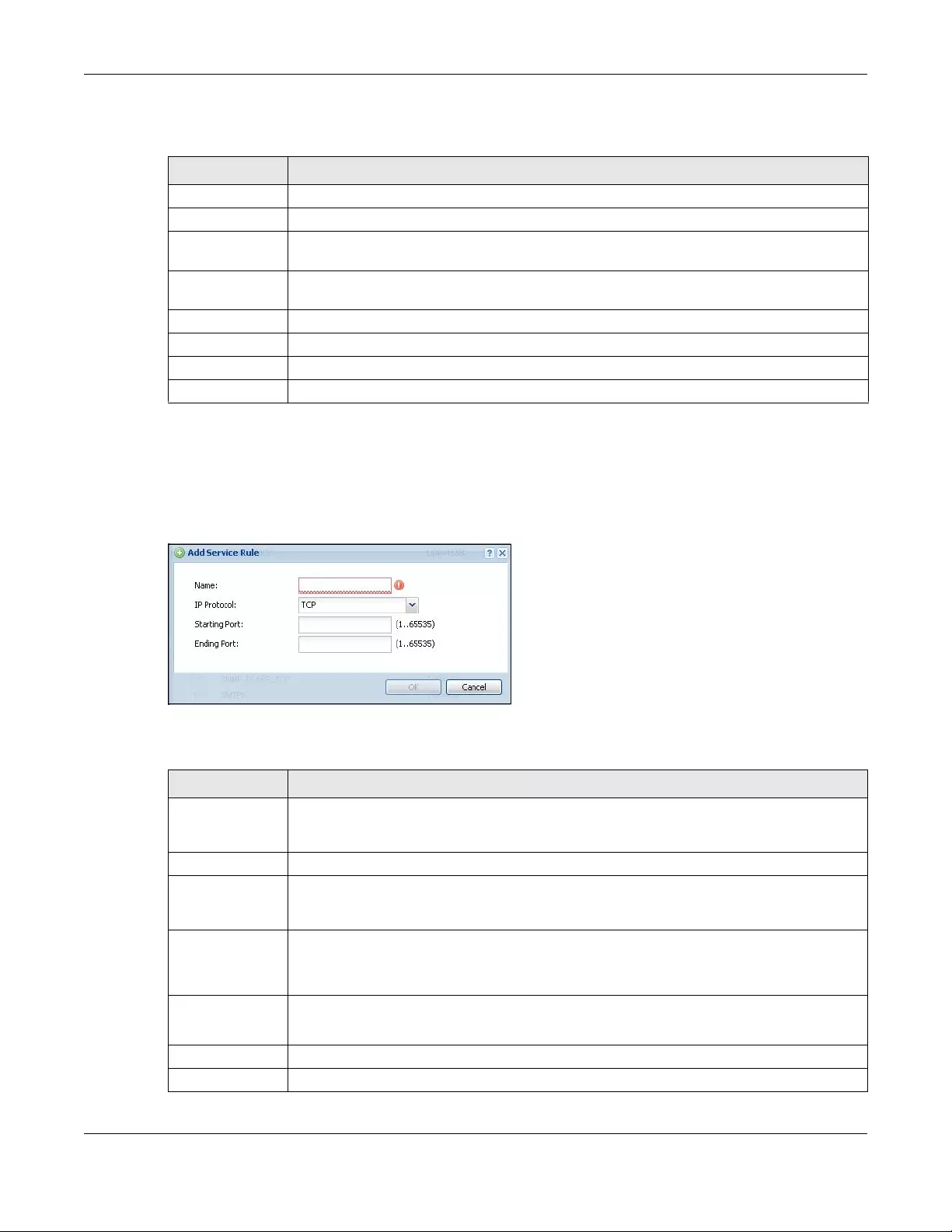
Chapter 43 Object
USG/ZyWALL User’s Guide
785
The following table describes the labels in this screen.
43.7.2.1 The Service Add/Edit Screen
The Service Add/Edit screen allows you to create a new service or edit an existing one. To access this
screen, go to the Service screen (see Section 43.7.2 on page 784), and click either the Add icon or an
Edit icon.
Figure 551 Configuration > Object > Service > Service > Edit
The following table describes the labels in this screen.
Table 317 Configuration > Object > Service > Service
LABEL DESCRIPTION
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Object
References
Select an entry and click Object References to open a screen that shows which settings use the
entry.
# This field is a sequential value, and it is not associated with a specific service.
Name This field displays the name of each service.
Content This field displays a description of each service.
Reference This displays the number of times an object reference is used in a profile.
Table 318 Configuration > Object > Service > Service > Edit
LABEL DESCRIPTION
Name Type the name used to refer to the service. You may use 1-31 alphanumeric characters,
underscores(_), or dashes (-), but the first character cannot be a number. This value is case-
sensitive.
IP Protocol Select the protocol the service uses. Choices are: TCP, UDP, ICMP, ICMPv6, and User Defined.
Starting Port
Ending Port
This field appears if the IP Protocol is TCP or UDP. Specify the port number(s) used by this service.
If you fill in one of these fields, the service uses that port. If you fill in both fields, the service uses
the range of ports.
ICMP Type This field appears if the IP Protocol is ICMP or ICMPv6.
Select the ICMP message used by this service. This field displays the message text, not the
message number.
IP Protocol
Number
This field appears if the IP Proto col is User Defined.
Enter the number of the next-level protocol (IP protocol). Allowed values are 1 - 255.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
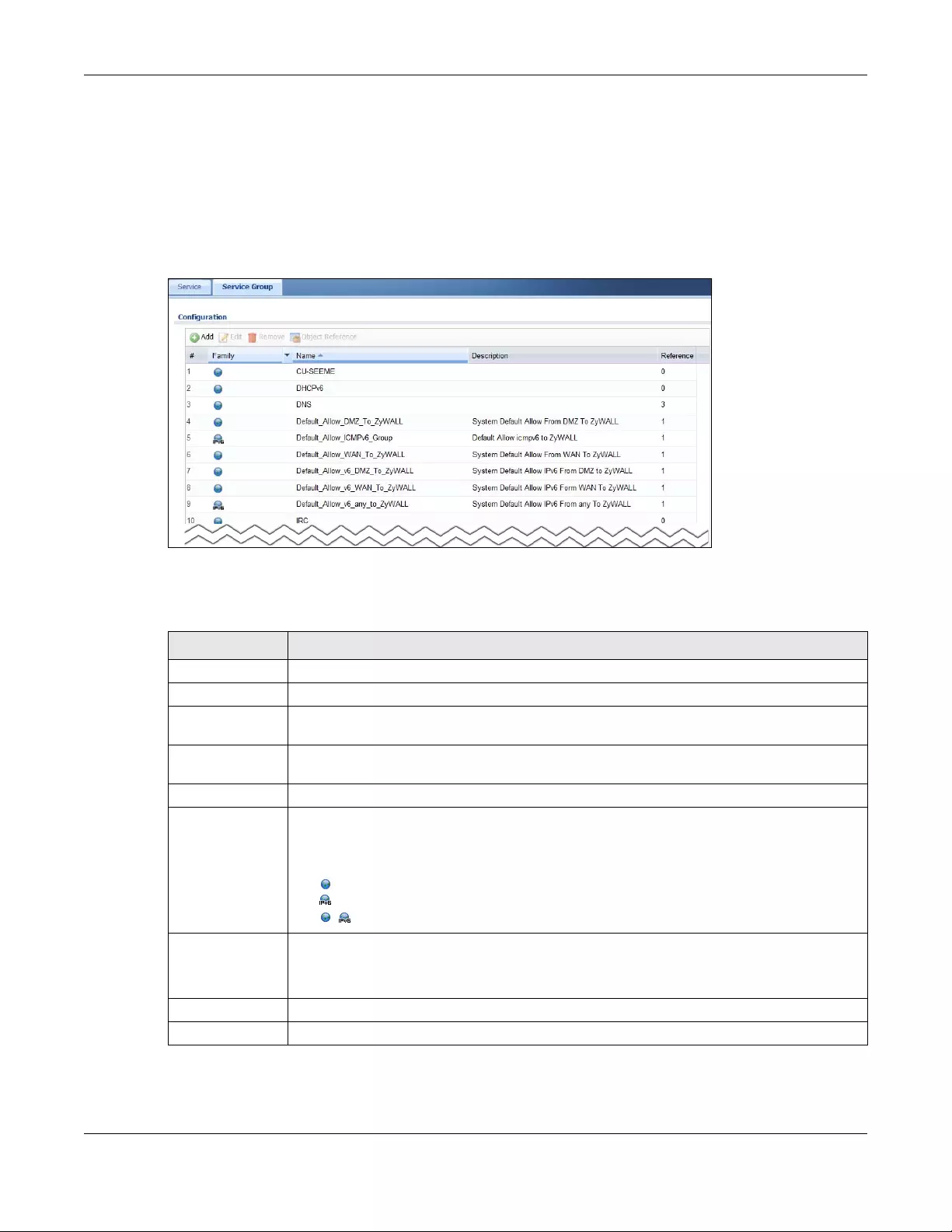
Chapter 43 Object
USG/ZyWALL User’s Guide
786
43.7.3 The Service Group Summary Screen
The Service Group summary screen provides a summary of all service groups. In addition, this screen
allows you to add, edit, and remove service groups.
To access this screen, log in to the Web Configurator, and click Configuration > Object > Service >
Service Group.
Figure 552 Configuration > Object > Service > Service Group
The following table describes the labels in this screen. See Section 43.7.3.1 on page 787 for more
information as well.
Table 319 Configuration > Object > Service > Service Group
LABEL DESCRIPTION
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Object
References
Select an entry and click Object References to open a screen that shows which settings use the
entry.
# This field is a sequential value, and it is not associated with a specific service group.
Family This field displays the Server Group supported type, which is according to your configurations in
the Service Group Add/Edit screen.
There are 3 types of families:
• : Supports IPv4 only
• : Supports IPv6 only
• : Supports both IPv4 and IPv6
Name This field displays the name of each service group.
By default, the Zyxel Device uses services starting with “Default_Allow_” in the security policies
to allow certain services to connect to the Zyxel Device.
Description This field displays the description of each service group, if any.
Reference This displays the number of times an object reference is used in a profile.
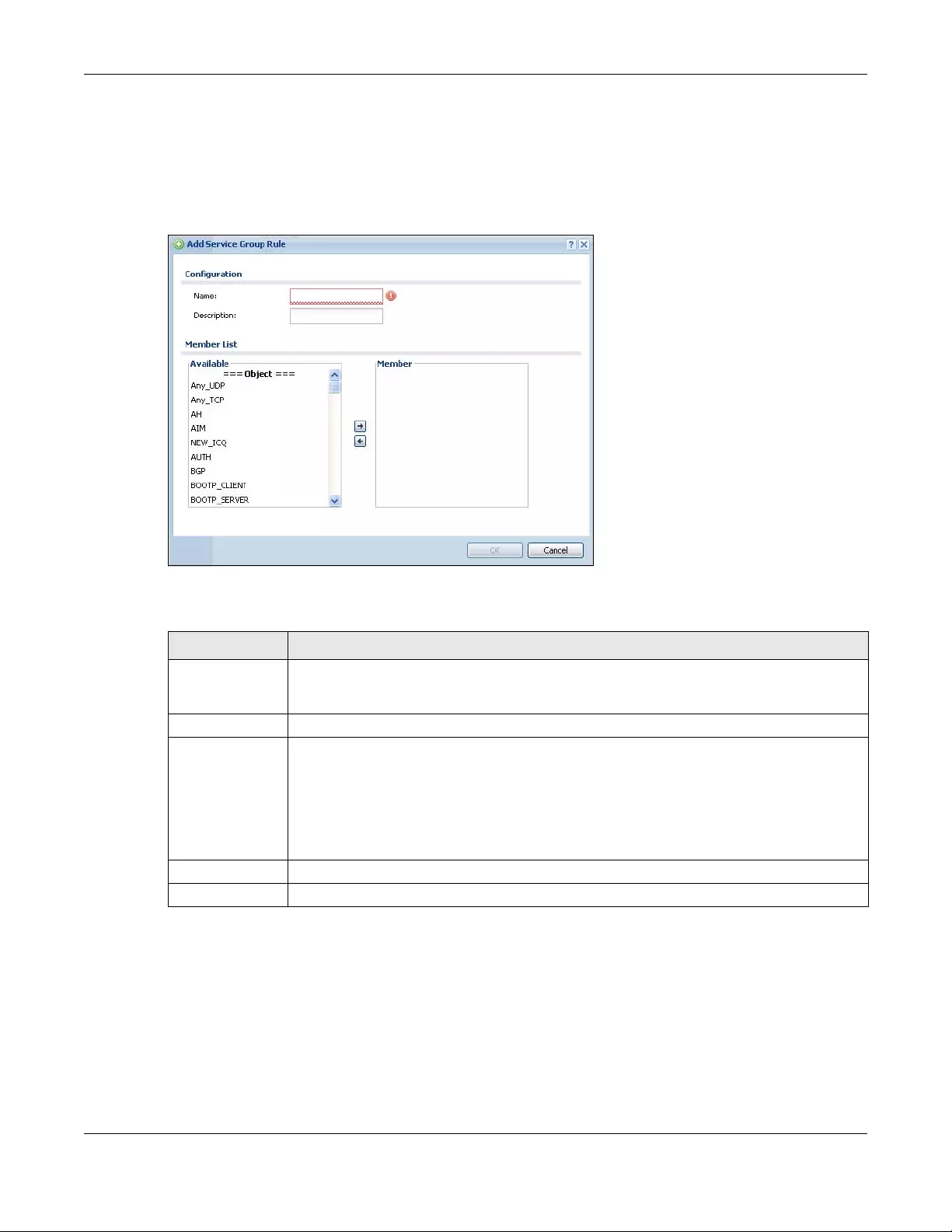
Chapter 43 Object
USG/ZyWALL User’s Guide
787
43.7.3.1 The Service Group Add/Edit Screen
The Service Group Add/Edit screen allows you to create a new service group or edit an existing one. To
access this screen, go to the Service Group screen (see Section 43.7.3 on page 786), and click either the
Add icon or an Edit icon.
Figure 553 Configuration > Object > Service > Service Group > Edit
The following table describes the labels in this screen.
43.8 Schedule Overview
Use schedules to set up one-time and recurring schedules for policy routes, security policies, application
patrol, and content filtering. The Zyxel Device supports one-time and recurring schedules. One-time
schedules are effective only once, while recurring schedules usually repeat. Both types of schedules are
based on the current date and time in the Zyxel Device.
Table 320 Configuration > Object > Service > Service Group > Edit
LABEL DESCRIPTION
Name Enter the name of the service group. You may use 1-31 alphanumeric characters,
underscores(_), or dashes (-), but the first character cannot be a number. This value is case-
sensitive.
Description Enter a description of the service group, if any. You can use up to 60 printable ASCII characters.
Member List The Member list displays the names of the service and service group objects that have been
added to the service group. The order of members is not important.
Select items from the Available list that you want to be members and move them to the
Member list. You can double-click a single entry to move it or use the [Shift] or [Ctrl] key to
select multiple entries and use the arrow button to move them.
Move any members you do not want included to the Available list.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
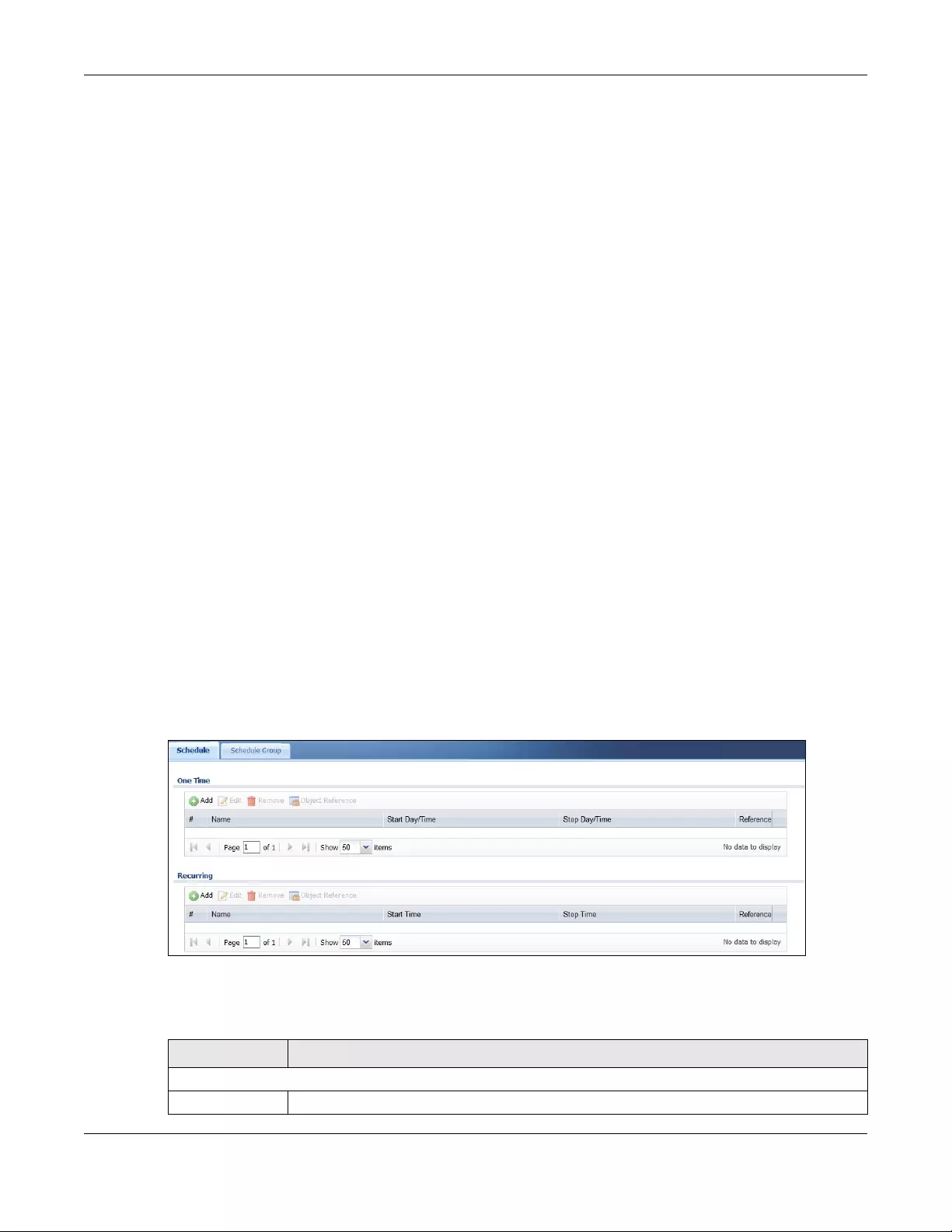
Chapter 43 Object
USG/ZyWALL User’s Guide
788
Note: Schedules are based on the Zyxel Device’s current date and time.
• Use the Schedule summary screen (Section 43.8.2 on page 788) to see a list of all schedules in the
Zyxel Device.
• Use the One-Time Schedule Add/Edit screen (Section 43.8.2.1 on page 789) to create or edit a one-
time schedule.
• Use the Recurring Schedule Add/Edit screen (Section 43.8.2.2 on page 790) to create or edit a
recurring schedule.
• Use the Schedule Group screen (Section 43.8.3 on page 791) to merge individual schedule objects as
one object.
43.8.1 What You Need to Know
One-time Schedules
One-time schedules begin on a specific start date and time and end on a specific stop date and time.
One-time schedules are useful for long holidays and vacation periods.
Recurring Schedules
Recurring schedules begin at a specific start time and end at a specific stop time on selected days of
the week (Sunday, Monday, Tuesday, Wednesday, Thursday, Friday, and Saturday). Recurring schedules
always begin and end in the same day. Recurring schedules are useful for defining the workday and off-
work hours.
43.8.2 The Schedule Screen
The Schedule screen provides a summary of all schedules in the Zyxel Device. To access this screen, click
Configuration > Object > Schedule.
Figure 554 Configuration > Object > Schedule
The following table describes the labels in this screen. See Section 43.8.2.1 on page 789 and Section
43.8.2.2 on page 790 for more information as well.
Table 321 Configuration > Object > Schedule
LABEL DESCRIPTION
One Time
Add Click this to create a new entry.
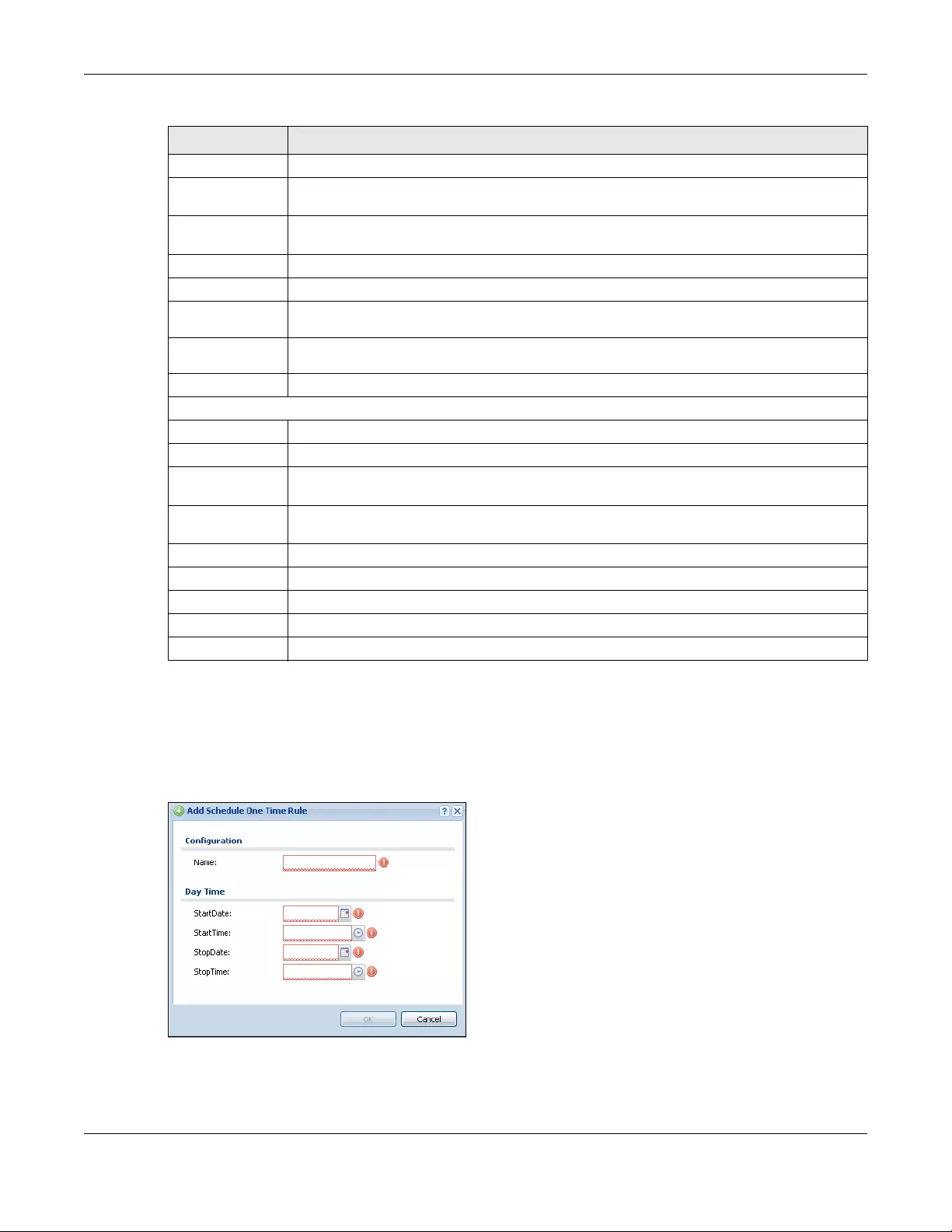
Chapter 43 Object
USG/ZyWALL User’s Guide
789
43.8.2.1 The One-Time Schedule Add/Edit Screen
The One-Time Schedule Add/Edit screen allows you to define a one-time schedule or edit an existing
one. To access this screen, go to the Schedule screen (see Section 43.8.2 on page 788), and click either
the Add icon or an Edit icon in the One Time section.
Figure 555 Configuration > Object > Schedule > Edit (One Time)
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Object
References Select an entry and click Object References to open a screen that shows which settings use
the entry.
# This field is a sequential value, and it is not associated with a specific schedule.
Name This field displays the name of the schedule, which is used to refer to the schedule.
Start Day /
Time This field displays the date and time at which the schedule begins.
Stop Day /
Time This field displays the date and time at which the schedule ends.
Reference This displays the number of times an object reference is used in a profile.
Recurring
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Object
References Select an entry and click Object References to open a screen that shows which settings use
the entry.
# This field is a sequential value, and it is not associated with a specific schedule.
Name This field displays the name of the schedule, which is used to refer to the schedule.
Start Time This field displays the time at which the schedule begins.
Stop Time This field displays the time at which the schedule ends.
Reference This displays the number of times an object reference is used in a profile.
Table 321 Configuration > Object > Schedule (continued)
LABEL DESCRIPTION
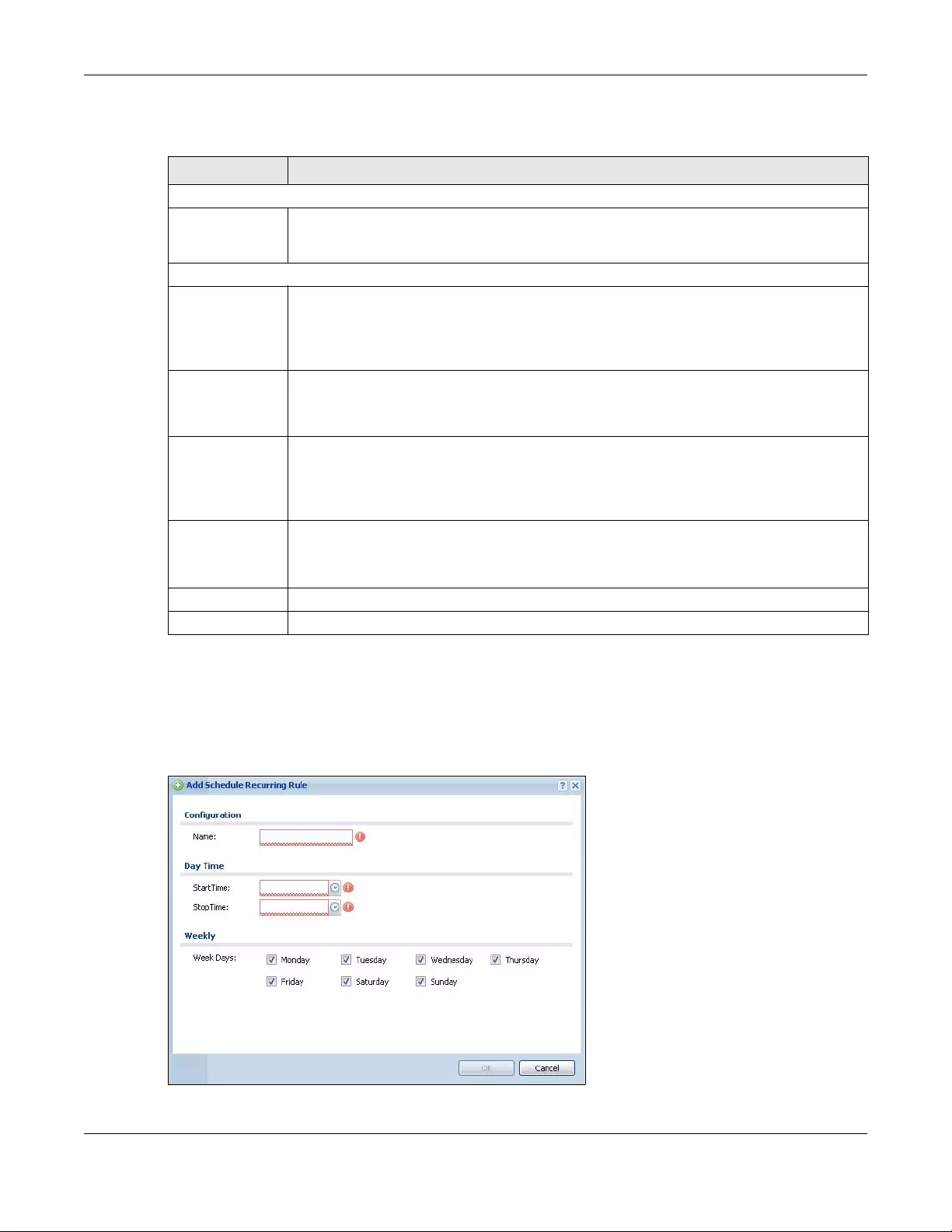
Chapter 43 Object
USG/ZyWALL User’s Guide
790
The following table describes the labels in this screen.
43.8.2.2 The Recurring Schedule Add/Edit Screen
The Recurring Schedule Add/Edit screen allows you to define a recurring schedule or edit an existing
one. To access this screen, go to the Schedule screen (see Section 43.8.2 on page 788), and click either
the Add icon or an Edit icon in the Recurring section.
Figure 556 Configuration > Object > Schedule > Edit (Recurring)
Table 322 Configuration > Object > Schedule > Edit (One Time)
LABEL DESCRIPTION
Configuration
Name Type the name used to refer to the one-time schedule. You may use 1-31 alphanumeric
characters, underscores(_), or dashes (-), but the first character cannot be a number. This
value is case-sensitive.
Date Time
StartDate Specify the year, month, and day when the schedule begins.
•Year - 1900 - 2999
•Month - 1 - 12
•Day - 1 - 31 (it is not possible to specify illegal dates, such as February 31.)
StartTime Specify the hour and minute when the schedule begins.
•Hour - 0 - 23
•Minute - 0 - 59
StopDate Specify the year, month, and day when the schedule ends.
•Year - 1900 - 2999
•Month - 1 - 12
•Day - 1 - 31 (it is not possible to specify illegal dates, such as February 31.)
StopTime Specify the hour and minute when the schedule ends.
•Hour - 0 - 23
•Minute - 0 - 59
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
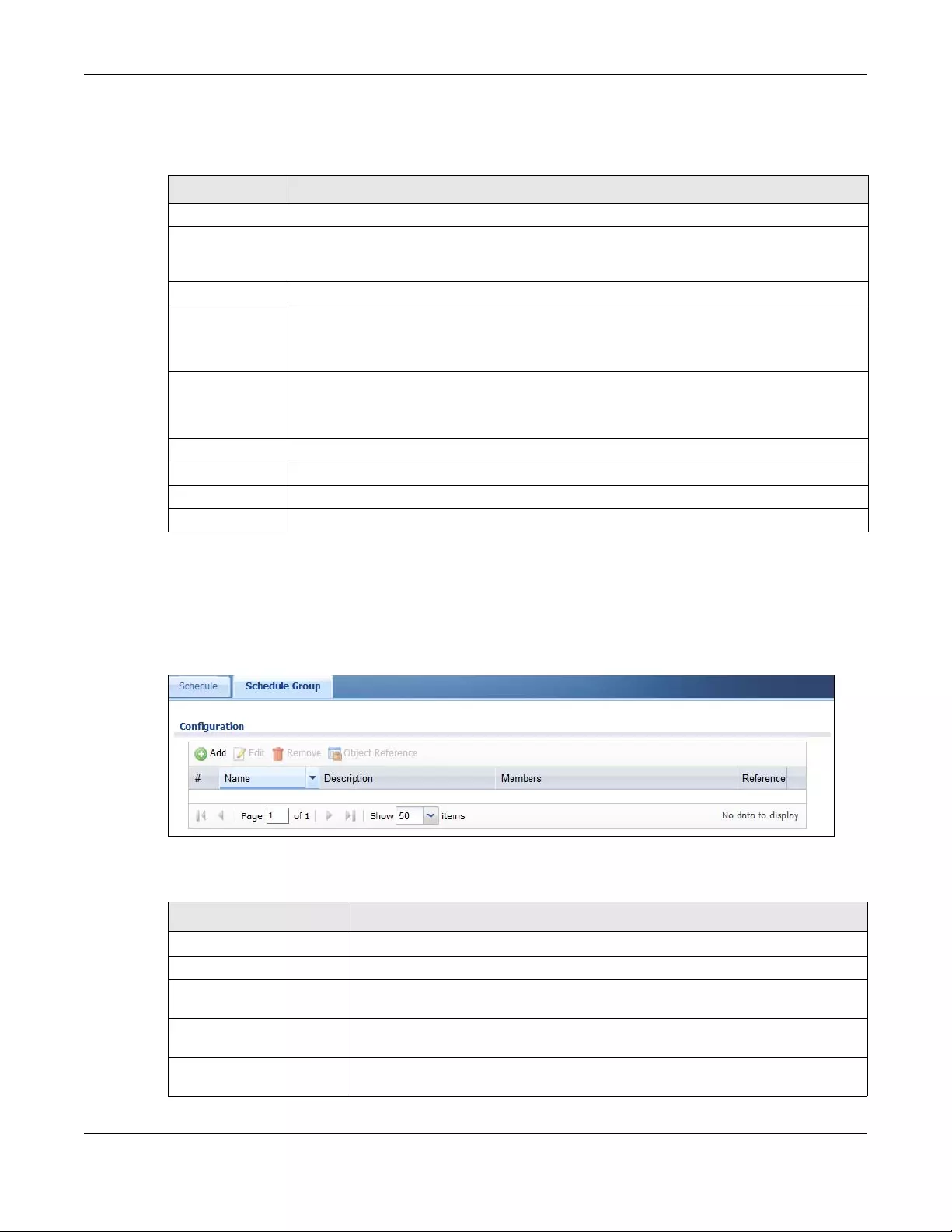
Chapter 43 Object
USG/ZyWALL User’s Guide
791
The Year, Month, and Day columns are not used in recurring schedules and are disabled in this screen.
The following table describes the remaining labels in this screen.
43.8.3 The Schedule Group Screen
The Schedule Group screen provides a summary of all groups of schedules in the Zyxel Device. To
access this screen, click Configuration > Object > Schedule >Group.
Figure 557 Configuration > Object > Schedule > Schedule Group
The following table describes the fields in the above screen.
Table 323 Configuration > Object > Schedule > Edit (Recurring)
LABEL DESCRIPTION
Configuration
Name Type the name used to refer to the recurring schedule. You may use 1-31 alphanumeric
characters, underscores(_), or dashes (-), but the first character cannot be a number. This
value is case-sensitive.
Date Time
StartTime Specify the hour and minute when the schedule begins each day.
•Hour - 0 - 23
•Minute - 0 - 59
StopTime Specify the hour and minute when the schedule ends each day.
•Hour - 0 - 23
•Minute - 0 - 59
Weekly
Week Days Select each day of the week the recurring schedule is effective.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
Table 324 Configuration > Object > Schedule > Schedule Group
LABEL DESCRIPTION
Configuration
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s
settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want
to remove it before doing so.
Object Reference Select an entry and click Object References to open a screen that shows which
settings use the entry.
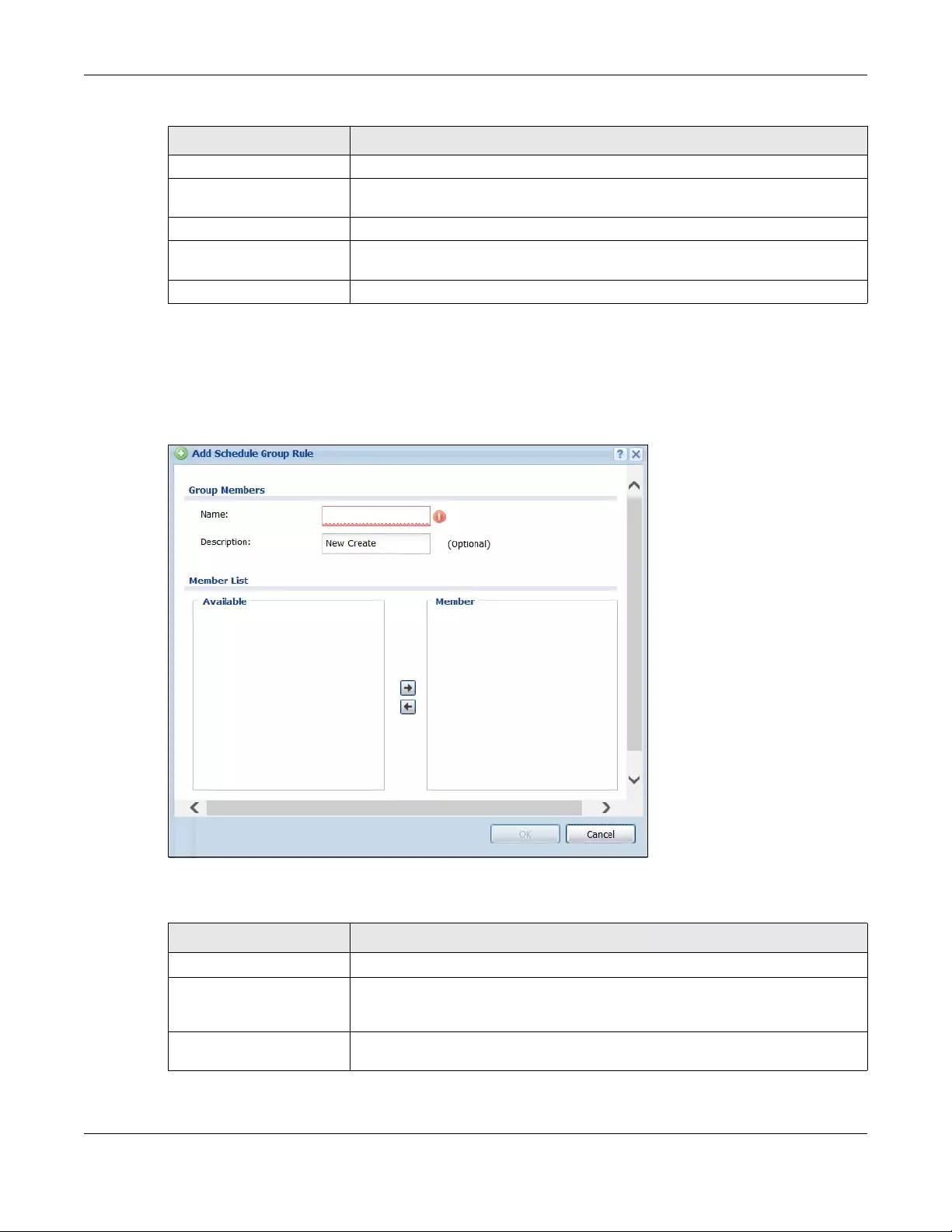
Chapter 43 Object
USG/ZyWALL User’s Guide
792
43.8.3.1 The Schedule Group Add/Edit Screen
The Schedule Group Add/Edit screen allows you to define a schedule group or edit an existing one. To
access this screen, go to the Schedule screen (see), and click either the Add icon or an Edit icon in the
Schedule Group section.
Figure 558 Configuration > Schedule > Schedule Group > Add
The following table describes the fields in the above screen.
# This field is a sequential value, and it is not associated with a specific schedule.
Name This field displays the name of the schedule group, which is used to refer to the
schedule.
Description This field displays the description of the schedule group.
Members This field lists the members in the schedule group. Each member is separated by a
comma.
Reference This displays the number of times an object reference is used in a profile.
Table 324 Configuration > Object > Schedule > Schedule Group
LABEL DESCRIPTION
Table 325 Configuration > Schedule > Schedule Group > Add
LABEL DESCRIPTION
Group Members
Name Type the name used to refer to the recurring schedule. You may use 1-31
alphanumeric characters, underscores(_), or dashes (-), but the first character
cannot be a number. This value is case-sensitive.
Description Enter a description of the service group, if any. You can use up to 60 printable ASCII
characters.
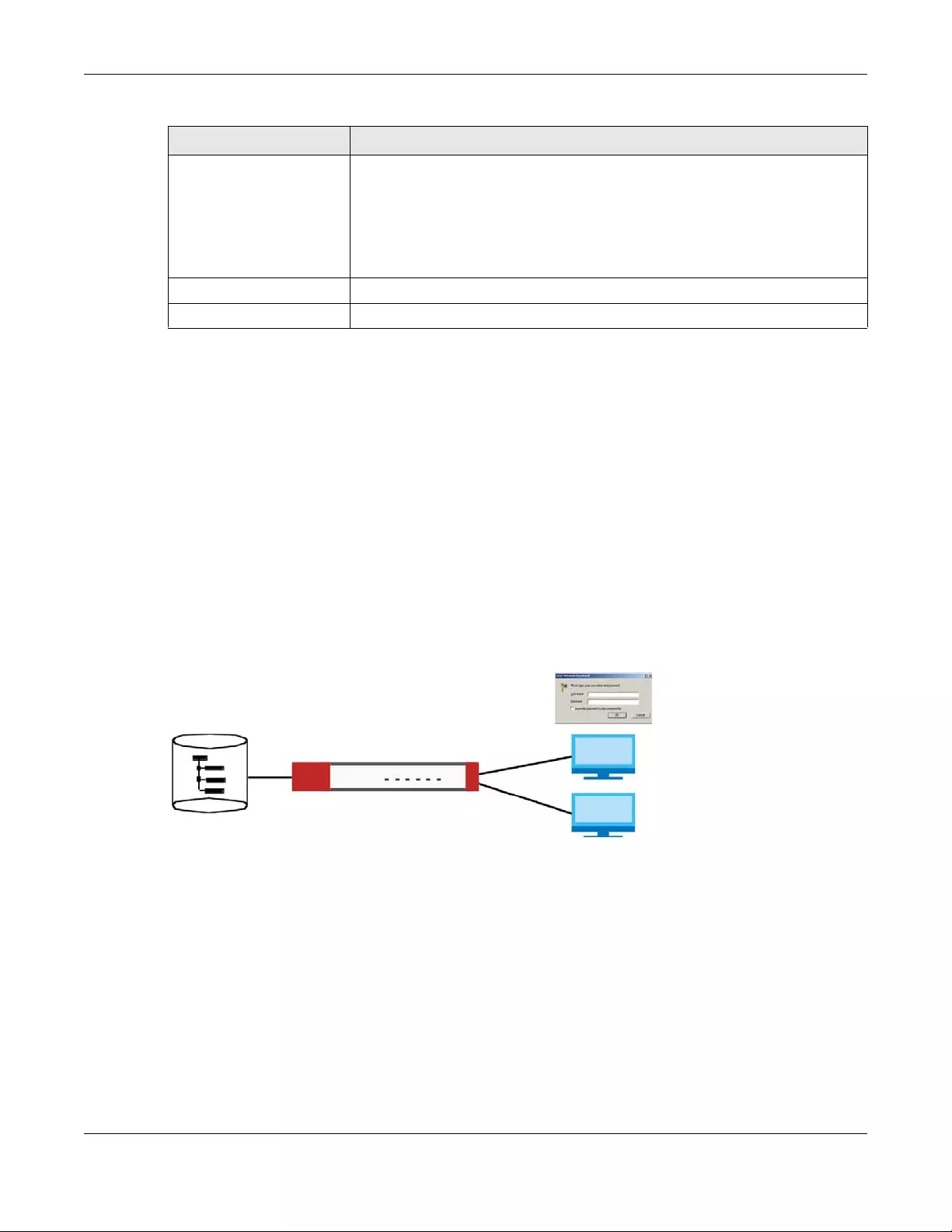
Chapter 43 Object
USG/ZyWALL User’s Guide
793
43.9 AAA Server Overview
You can use a AAA (Authentication, Authorization, Accounting) server to provide access control to your
network. The AAA server can be a Active Directory, LDAP, or RADIUS server. Use the AAA Server screens
to create and manage objects that contain settings for using AAA servers. You use AAA server objects in
configuring ext-group-user user objects and authentication method objects (see Chapter 43 on page
801).
43.9.1 Directory Service (AD/LDAP)
LDAP/AD allows a client (the Zyxel Device) to connect to a server to retrieve information from a
directory. A network example is shown next.
Figure 559 Example: Directory Service Client and Server
The following describes the user authentication procedure via an LDAP/AD server.
1A user logs in with a user name and password pair.
2The Zyxel Device tries to bind (or log in) to the LDAP/AD server.
3When the binding process is successful, the Zyxel Device checks the user information in the directory
against the user name and password pair.
4If it matches, the user is allowed access. Otherwise, access is blocked.
Member List The Member list displays the names of the service and service group objects that
have been added to the service group. The order of members is not important.
Select items from the Available list that you want to be members and move them to
the Member list. You can double-click a single entry to move it or use the [Shift] or
[Ctrl] key to select multiple entries and use the arrow button to move them.
Move any members you do not want included to the Available list.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
Table 325 Configuration > Schedule > Schedule Group > Add
LABEL DESCRIPTION

Chapter 43 Object
USG/ZyWALL User’s Guide
794
43.9.2 RADIUS Server
RADIUS (Remote Authentication Dial-In User Service) authentication is a popular protocol used to
authenticate users by means of an external server instead of (or in addition to) an internal device user
database that is limited to the memory capacity of the device. In essence, RADIUS authentication
allows you to validate a large number of users from a central location.
Figure 560 RADIUS Server Network Example
43.9.3 ASAS
ASAS (Authenex Strong Authentication System) is a RADIUS server that works with the One-Time Password
(OTP) feature. Purchase a Zyxel Device OTP package in order to use this feature. The package contains
server software and physical OTP tokens (PIN generators). Do the following to use OTP. See the
documentation included on the ASAS’ CD for details.
1Install the ASAS server software on a computer.
2Create user accounts on the Zyxel Device and in the ASAS server.
3Import each token’s database file (located on the included CD) into the server.
4Assign users to OTP tokens (on the ASAS server).
5Configure the ASAS as a RADIUS server in the Zyxel Device’s Configuration > Object > AAA Server
screens.
6Give the OTP tokens to (local or remote) users.
• Use the Configuration > Object > AAA Server > Active Directory (or LDAP) screens (Section 43.9.5 on
page 796) to configure Active Directory or LDAP server objects.
• Use the Configuration > Object > AAA Server > RADIUS screen (Section 43.9.2 on page 794) to
configure the default external RADIUS server to use for user authentication.
43.9.4 What You Need To Know
AAA Servers Supported by the Zyxel Device
The following lists the types of authentication server the Zyxel Device supports.
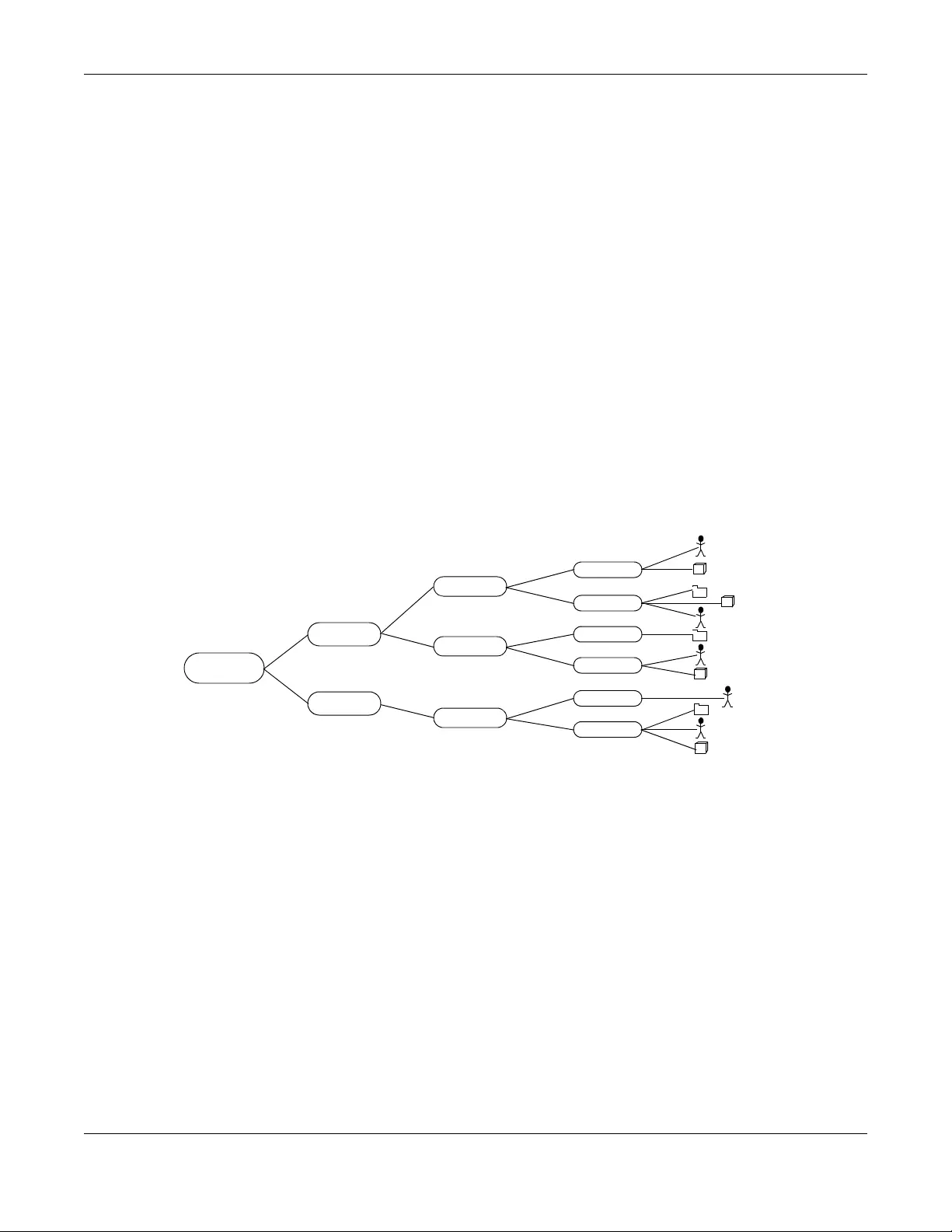
Chapter 43 Object
USG/ZyWALL User’s Guide
795
•Local user database
The Zyxel Device uses the built-in local user database to authenticate administrative users logging into
the Zyxel Device’s Web Configurator or network access users logging into the network through the
Zyxel Device. You can also use the local user database to authenticate VPN users.
• Directory Service (LDAP/AD)
LDAP (Lightweight Directory Access Protocol)/AD (Active Directory) is a directory service that is both
a directory and a protocol for controlling access to a network. The directory consists of a database
specialized for fast information retrieval and filtering activities. You create and store user profile and
login information on the external server.
•RADIUS
RADIUS (Remote Authentication Dial-In User Service) authentication is a popular protocol used to
authenticate users by means of an external or built-in RADIUS server. RADIUS authentication allows
you to validate a large number of users from a central location.
Directory Structure
The directory entries are arranged in a hierarchical order much like a tree structure. Normally, the
directory structure reflects the geographical or organizational boundaries. The following figure shows a
basic directory structure branching from countries to organizations to organizational units to individuals.
Figure 561 Basic Directory Structure
Distinguished Name (DN)
A DN uniquely identifies an entry in a directory. A DN consists of attribute-value pairs separated by
commas. The leftmost attribute is the Relative Distinguished Name (RDN). This provides a unique name
for entries that have the same “parent DN” (“cn=domain1.com, ou=Sales, o=MyCompany” in the
following examples).
cn=domain1.com, ou = Sales, o=MyCompany, c=US
cn=domain1.com, ou = Sales, o=MyCompany, c=JP
Root
US
Japan
Sprint
UPS
NEC
Sales
RD3
QA
CSO
Sales
RD
Countries (c) Organizations (o) Organization Units (ou) Unique
Common Name
(cn)
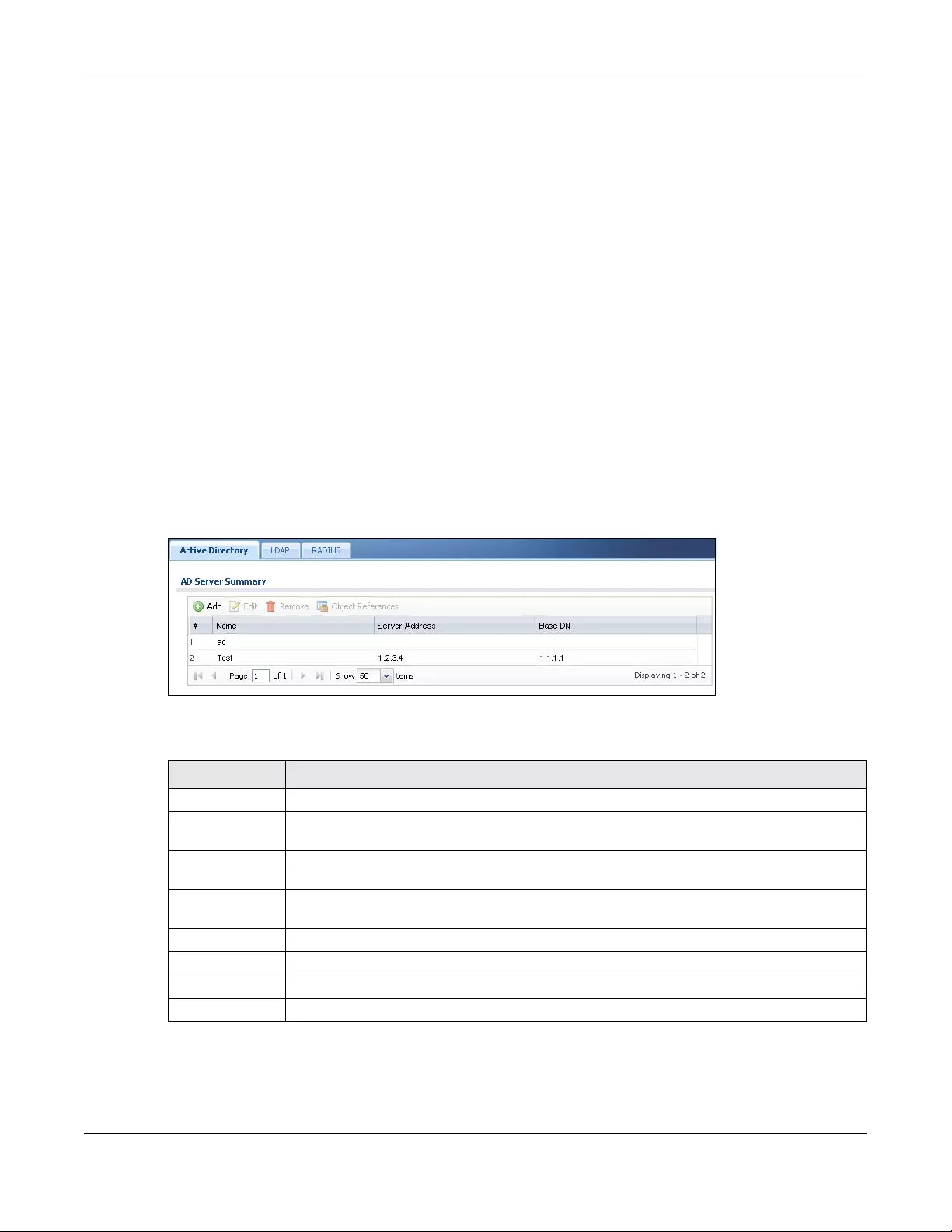
Chapter 43 Object
USG/ZyWALL User’s Guide
796
Base DN
A base DN specifies a directory. A base DN usually contains information such as the name of an
organization, a domain name and/or country. For example, o=MyCompany, c=UK where o means
organization and c means country.
Bind DN
A bind DN is used to authenticate with an LDAP/AD server. For example a bind DN of cn=zywallAdmin
allows the Zyxel Device to log into the LDAP/AD server using the user name of zywallAdmin. The bind
DN is used in conjunction with a bind password. When a bind DN is not specified, the Zyxel Device will try
to log in as an anonymous user. If the bind password is incorrect, the login will fail.
43.9.5 Active Directory or LDAP Server Summary
Use the Active Directory or LDAP screen to manage the list of AD or LDAP servers the Zyxel Device can
use in authenticating users.
Click Configuration > Object > AAA Server > Active Directory (or LDAP) to display the Active Directory (or
LDAP) screen.
Figure 562 Configuration > Object > AAA Server > Active Directory (or LDAP)
The following table describes the labels in this screen.
Table 326 Configuration > Object > AAA Server > Active Directory (or LDAP)
LABEL DESCRIPTION
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Object
References
Select an entry and click Object References to open a screen that shows which settings use the
entry.
# This field is a sequential value, and it is not associated with a specific AD or LDAP server.
Name This field displays the name of the Active Directory.
Server Address This is the address of the AD or LDAP server.
Base DN This specifies a directory. For example, o=Zyxel, c=US.
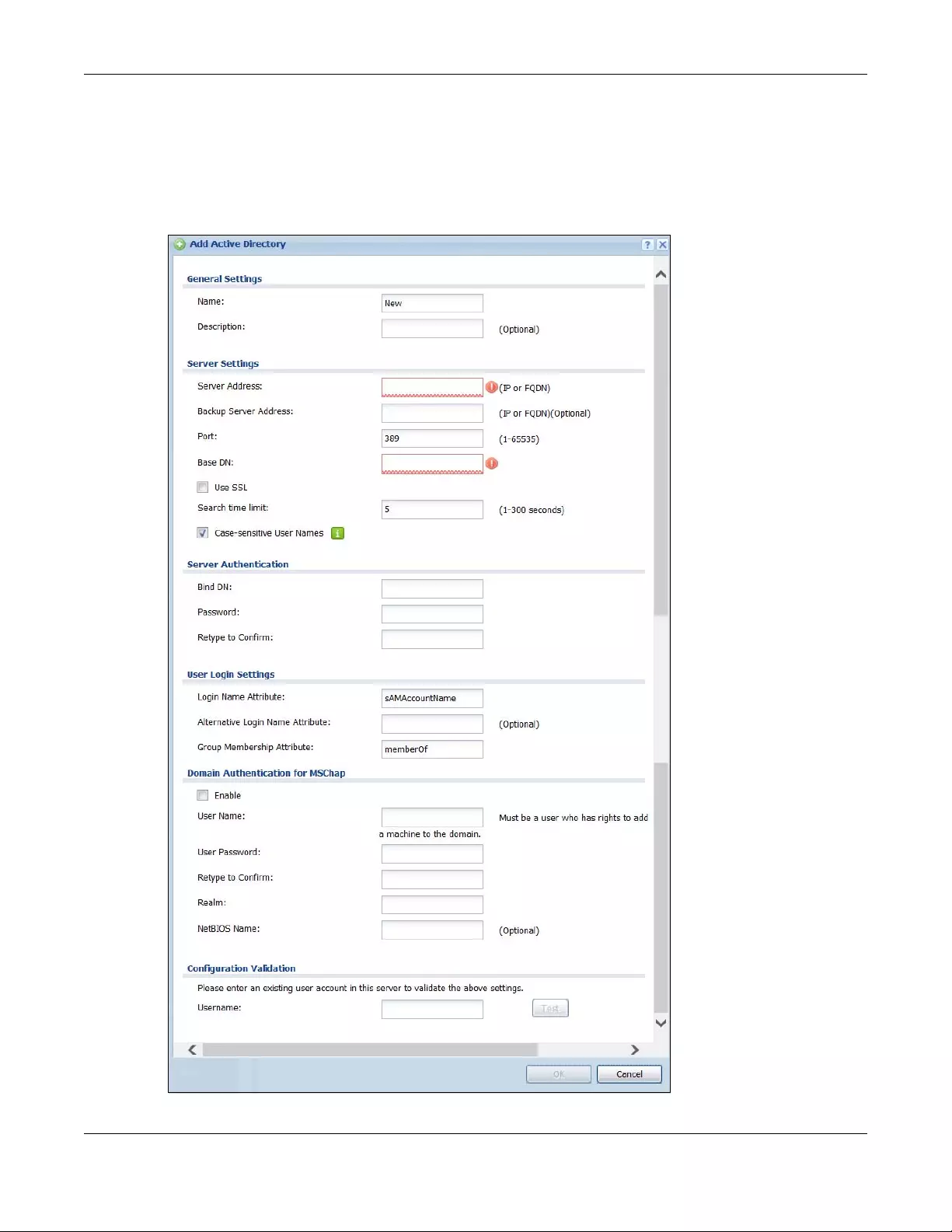
Chapter 43 Object
USG/ZyWALL User’s Guide
797
43.9.5.1 Adding an Active Directory or LDAP Server
Click Object > AAA Server > Active Directory (or LDAP) to display the Active Directory (or LDAP) screen.
Click the Add icon or an Edit icon to display the following screen. Use this screen to create a new AD or
LDAP entry or edit an existing one.
Figure 563 Configuration > Object > AAA Server > Active Directory (or LDAP) > Add
Chapter 43 Object
USG/ZyWALL User’s Guide
798
The following table describes the labels in this screen.
Table 327 Configuration > Object > AAA Server > Active Directory (or LDAP) > Add
LABEL DESCRIPTION
Name Enter a descriptive name (up to 63 alphanumerical characters) for identification purposes.
Description Enter the description of each server, if any. You can use up to 60 printable ASCII characters.
Server Address Enter the address of the AD or LDAP server.
Backup Server
Address
If the AD or LDAP server has a backup server, enter its address here.
Port Specify the port number on the AD or LDAP server to which the Zyxel Device sends
authentication requests. Enter a number between 1 and 65535.
This port number should be the same on all AD or LDAP server(s) in this group.
Base DN Specify the directory (up to 127 alphanumerical characters). For example, o=Zyxel,
c=US.
This is only for LDAP.
Use SSL Select Use SSL to establish a secure connection to the AD or LDAP server(s).
Search time limit Specify the timeout period (between 1 and 300 seconds) before the Zyxel Device
disconnects from the AD or LDAP server. In this case, user authentication fails.
Search timeout occurs when either the user information is not in the AD or LDAP server(s) or
the AD or LDAP server(s) is down.
Case-sensitive User
Names
Select this if the server checks the case of the usernames.
Bind DN Specify the bind DN for logging into the AD or LDAP server. Enter up to 127 alphanumerical
characters.
For example, cn=zywallAdmin specifies zywallAdmin as the user name.
Password If required, enter the password (up to 15 alphanumerical characters) for the Zyxel Device to
bind (or log in) to the AD or LDAP server.
Retype to Confirm Retype your new password for confirmation.
Login Name
Attribute
Enter the type of identifier the users are to use to log in. For example “name” or “e-mail
address”.
Alternative Login
Name Attribute
If there is a second type of identifier that the users can use to log in, enter it here. For example
“name” or “e-mail address”.
Group
Membership
Attribute
An AD or LDAP server defines attributes for its accounts. Enter the name of the attribute that
the Zyxel Device is to check to determine to which group a user belongs. The value for this
attribute is called a group identifier; it determines to which group a user belongs. You can
add ext-group-user user objects to identify groups based on these group identifier values.
For example you could have an attribute named “memberOf” with values like “sales”, “RD”,
and “management”. Then you could also create a ext-group-user user object for each
group. One with “sales” as the group identifier, another for “RD” and a third for
“management”.
Domain
Authentication for
MSChap
Select the Enable checkbox to enable domain authentication for MSChap.
This is only for Active Directory.
User Name Enter the user name for the user who has rights to add a machine to the domain.
This is only for Active Directory.
User Password Enter the password for the associated user name.
This is only for Active Directory.
Retype to Confirm Retype your new password for confirmation.
This is only for Active Directory.
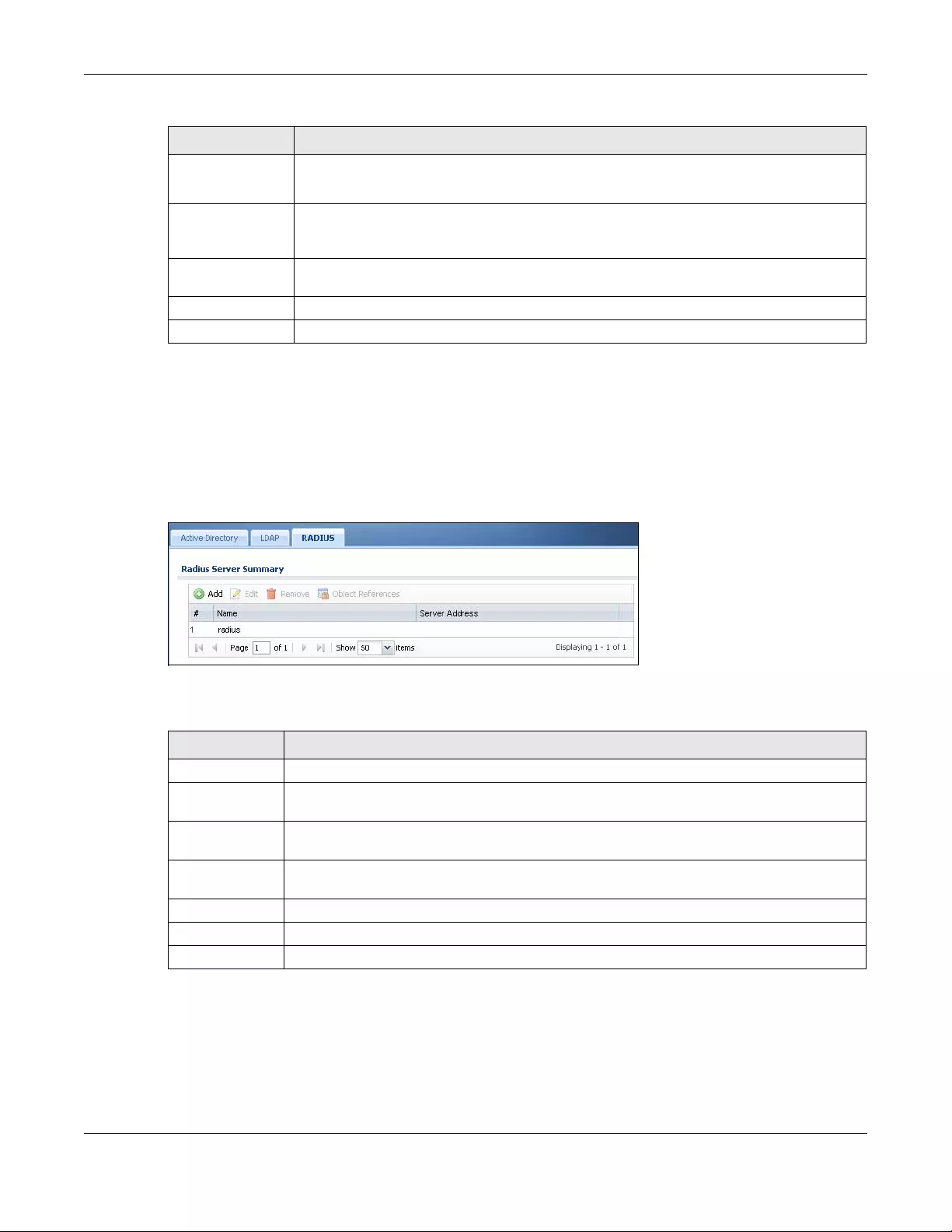
Chapter 43 Object
USG/ZyWALL User’s Guide
799
43.9.6 RADIUS Server Summary
Use the RADIUS screen to manage the list of RADIUS servers the Zyxel Device can use in authenticating
users.
Click Configuration > Object > AAA Server > RADIUS to display the RADIUS screen.
Figure 564 Configuration > Object > AAA Server > RADIUS
The following table describes the labels in this screen.
43.9.6.1 Adding a RADIUS Server
Click Configuration > Object > AAA Server > RADIUS to display the RADIUS screen. Click the Add icon or
an Edit icon to display the following screen. Use this screen to create a new AD or LDAP entry or edit an
existing one.
Realm Enter the realm FQDN.
This is only for Active Directory.
NetBIOS Name Type the NetBIOS name. This field is optional. NetBIOS packets are TCP or UDP packets that
enable a computer to connect to and communicate with a LAN which allows local
computers to find computers on the remote network and vice versa.
Configuration
Validation
Use a user account from the server specified above to test if the configuration is correct. Enter
the account’s user name in the Username field and click Test.
OK Click OK to save the changes.
Cancel Click Cancel to discard the changes.
Table 327 Configuration > Object > AAA Server > Active Directory (or LDAP) > Add (continued)
LABEL DESCRIPTION
Table 328 Configuration > Object > AAA Server > RADIUS
LABEL DESCRIPTION
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Object
References
Select an entry and click Object References to open a screen that shows which settings use the
entry.
# This field displays the index number.
Name This is the name of the RADIUS server entry.
Server Address This is the address of the AD or LDAP server.
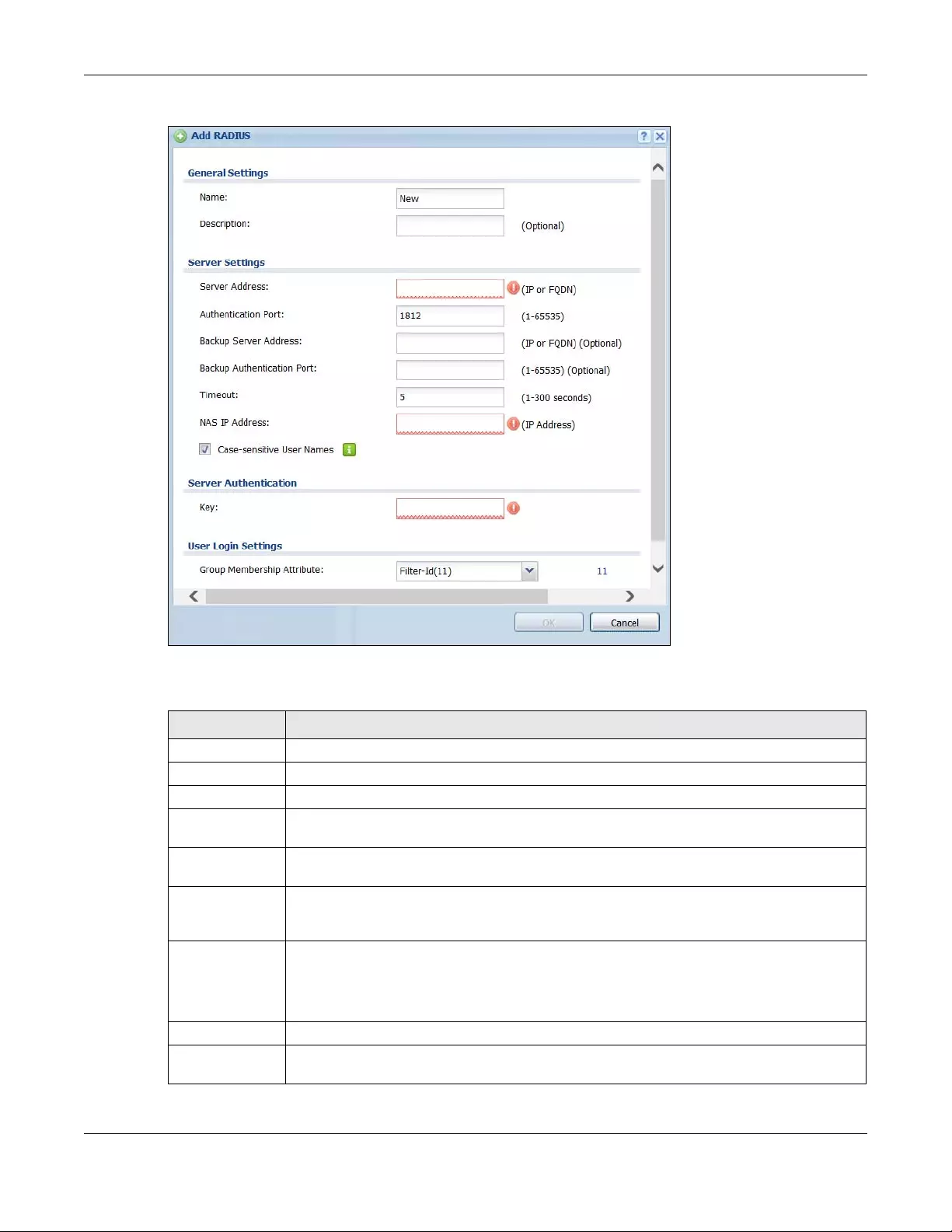
Chapter 43 Object
USG/ZyWALL User’s Guide
800
Figure 565 Configuration > Object > AAA Server > RADIUS > Add
The following table describes the labels in this screen.
Table 329 Configuration > Object > AAA Server > RADIUS > Add
LABEL DESCRIPTION
Name Enter a descriptive name (up to 63 alphanumerical characters) for identification purposes.
Description Enter the description of each server, if any. You can use up to 60 printable ASCII characters.
Server Address Enter the address of the RADIUS server.
Authentication
Port
Specify the port number on the RADIUS server to which the Zyxel Device sends authentication
requests. Enter a number between 1 and 65535.
Backup Server
Address
If the RADIUS server has a backup server, enter its address here.
Backup
Authentication
Port
Specify the port number on the RADIUS server to which the Zyxel Device sends authentication
requests. Enter a number between 1 and 65535.
Timeout Specify the timeout period (between 1 and 300 seconds) before the Zyxel Device disconnects
from the RADIUS server. In this case, user authentication fails.
Search timeout occurs when either the user information is not in the RADIUS server or the
RADIUS server is down.
NAS IP Address Type the IP address of the NAS (Network Access Server).
Case-sensitive
User Names
Select this if you want configure your username as case-sensitive.
Chapter 43 Object
USG/ZyWALL User’s Guide
801
43.10 Auth. Method Overview
Authentication method objects set how the Zyxel Device authenticates wireless, HTTP/HTTPS clients, and
peer IPSec routers (extended authentication) clients. Configure authentication method objects to have
the Zyxel Device use the local user database, and/or the authentication servers and authentication
server groups specified by AAA server objects. By default, user accounts created and stored on the
Zyxel Device are authenticated locally.
• Use the Configuration > Object > Auth. Method screens (Section 43.10.3 on page 802) to create and
manage authentication method objects.
43.10.1 Before You Begin
Configure AAA server objects before you configure authentication method objects.
43.10.2 Example: Selecting a VPN Authentication Method
After you set up an authentication method object in the Auth. Method screens, you can use it in the VPN
Gateway screen to authenticate VPN users for establishing a VPN connection. Refer to the chapter on
VPN for more information.
Follow the steps below to specify the authentication method for a VPN connection.
1Access the Configuration > VPN > IPSec VPN > VPN Gateway > Edit screen.
2Click Show Advance Setting and select Enable Extended Authentication.
3Select Server Mode and select an authentication method object from the drop-down list box.
4Click OK to save the settings.
Key Enter a password (up to 15 alphanumeric characters) as the key to be shared between the
external authentication server and the Zyxel Device.
The key is not sent over the network. This key must be the same on the external authentication
server and the Zyxel Device.
Group
Membership
Attribute
A RADIUS server defines attributes for its accounts. Select the name and number of the
attribute that the Zyxel Device is to check to determine to which group a user belongs. If it does
not display, select user-defined and specify the attribute’s number.
This attribute’s value is called a group identifier; it determines to which group a user belongs.
You can add ext-group-user user objects to identify groups based on these group identifier
values.
For example you could have an attribute named “memberOf” with values like “sales”, “RD”,
and “management”. Then you could also create a ext-group-user user object for each group.
One with “sales” as the group identifier, another for “RD” and a third for “management”.
OK Click OK to save the changes.
Cancel Click Cancel to discard the changes.
Table 329 Configuration > Object > AAA Server > RADIUS > Add (continued)
LABEL DESCRIPTION
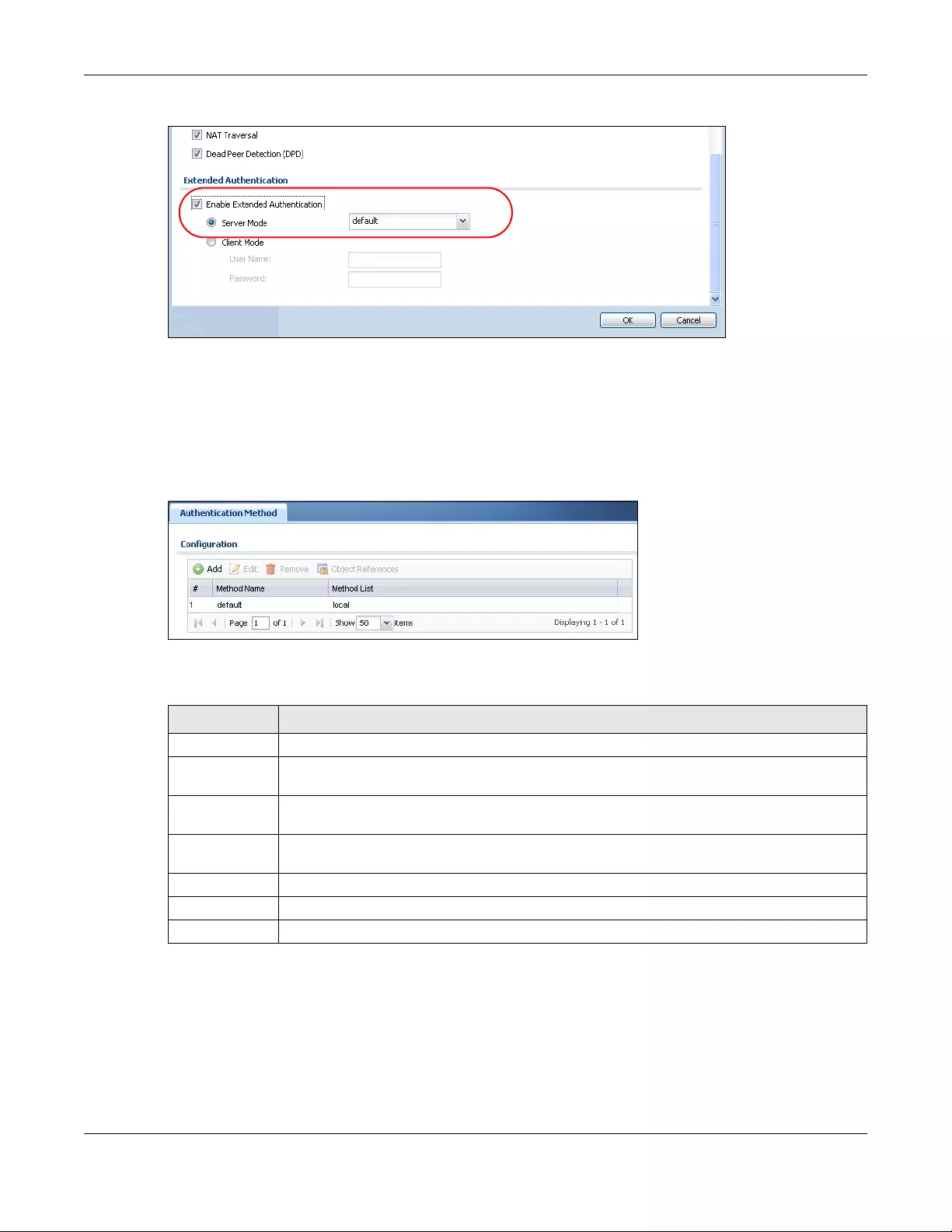
Chapter 43 Object
USG/ZyWALL User’s Guide
802
Figure 566 Example: Using Authentication Method in VPN
43.10.3 Authentication Method Objects
Click Configuration > Object > Auth. Method to display the screen as shown.
Note: You can create up to 16 authentication method objects.
Figure 567 Configuration > Object > Auth. Method
The following table describes the labels in this screen.
43.10.3.1 Creating an Authentication Method Object
Follow the steps below to create an authentication method object.
1Click Configuration > Object > Auth. Method.
2Click Add.
Table 330 Configuration > Object > Auth. Method
LABEL DESCRIPTION
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove it
before doing so.
Object
References
Select an entry and click Object References to open a screen that shows which settings use the
entry.
# This field displays the index number.
Method Name This field displays a descriptive name for identification purposes.
Method List This field displays the authentication method(s) for this entry.
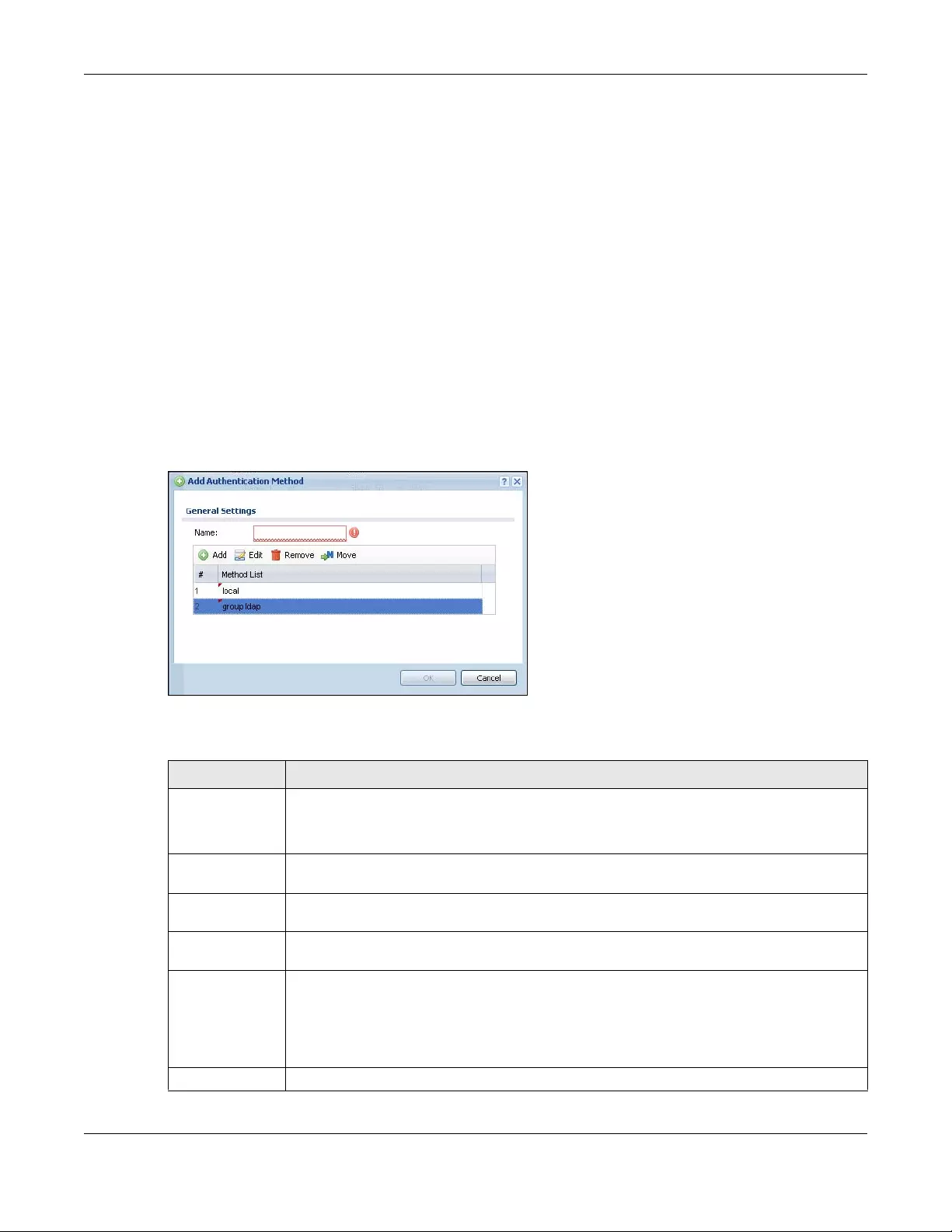
Chapter 43 Object
USG/ZyWALL User’s Guide
803
3Specify a descriptive name for identification purposes in the Name field. You may use 1-31
alphanumeric characters, underscores(_), or dashes (-), but the first character cannot be a number. This
value is case-sensitive. For example, “My_Device”.
4Click Add to insert an authentication method in the table.
5Select a server object from the Method List drop-down list box.
6You can add up to four server objects to the table. The ordering of the Method List column is important.
The Zyxel Device authenticates the users using the databases (in the local user database or the external
authentication server) in the order they appear in this screen.
If two accounts with the same username exist on two authentication servers you specify, the Zyxel
Device does not continue the search on the second authentication server when you enter the
username and password that doesn’t match the one on the first authentication server.
Note: You can NOT select two server objects of the same type.
7Click OK to save the settings or click Cancel to discard all changes and return to the previous screen.
Figure 568 Configuration > Object > Auth. Method > Add
The following table describes the labels in this screen.
Table 331 Configuration > Object > Auth. Method > Add
LABEL DESCRIPTION
Name Specify a descriptive name for identification purposes.
You may use 1-31 alphanumeric characters, underscores(_), or dashes (-), but the first
character cannot be a number. This value is case-sensitive. For example, “My_Device”.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after the
selected entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Move To change a method’s position in the numbered list, select the method and click Move to
display a field to type a number for where you want to put it and press [ENTER] to move the rule
to the number that you typed.
The ordering of your methods is important as Zyxel Device authenticates the users using the
authentication methods in the order they appear in this screen.
# This field displays the index number.
Chapter 43 Object
USG/ZyWALL User’s Guide
804
43.11 Certificate Overview
The Zyxel Device can use certificates (also called digital IDs) to authenticate users. Certificates are
based on public-private key pairs. A certificate contains the certificate owner’s identity and public key.
Certificates provide a way to exchange public keys for use in authentication.
• Use the My Certificates screens (see Section 43.11.3 on page 807 to Section 43.11.3.3 on page 813) to
generate and export self-signed certificates or certification requests and import the CA-signed
certificates.
• Use the Trusted Certificates screens (see Section 43.11.4 on page 814 to Section 43.11.4.2 on page
818) to save CA certificates and trusted remote host certificates to the Zyxel Device. The Zyxel Device
trusts any valid certificate that you have imported as a trusted certificate. It also trusts any valid
certificate signed by any of the certificates that you have imported as a trusted certificate.
43.11.1 What You Need to Know
When using public-key cryptology for authentication, each host has two keys. One key is public and can
be made openly available. The other key is private and must be kept secure.
These keys work like a handwritten signature (in fact, certificates are often referred to as “digital
signatures”). Only you can write your signature exactly as it should look. When people know what your
signature looks like, they can verify whether something was signed by you, or by someone else. In the
same way, your private key “writes” your digital signature and your public key allows people to verify
whether data was signed by you, or by someone else. This process works as follows.
1Tim wants to send a message to Jenny. He needs her to be sure that it comes from him, and that the
message content has not been altered by anyone else along the way. Tim generates a public key pair
(one public key and one private key).
2Tim keeps the private key and makes the public key openly available. This means that anyone who
receives a message seeming to come from Tim can read it and verify whether it is really from him or not.
3Tim uses his private key to sign the message and sends it to Jenny.
Method List Select a server object from the drop-down list box. You can create a server object in the AAA
Server screen.
The Zyxel Device authenticates the users using the databases (in the local user database or the
external authentication server) in the order they appear in this screen.
If two accounts with the same username exist on two authentication servers you specify, the
Zyxel Device does not continue the search on the second authentication server when you
enter the username and password that doesn’t match the one on the first authentication
server.
OK Click OK to save the changes.
Cancel Click Cancel to discard the changes.
Table 331 Configuration > Object > Auth. Method > Add (continued)
LABEL DESCRIPTION

Chapter 43 Object
USG/ZyWALL User’s Guide
805
4Jenny receives the message and uses Tim’s public key to verify it. Jenny knows that the message is from
Tim, and that although other people may have been able to read the message, no-one can have
altered it (because they cannot re-sign the message with Tim’s private key).
5Additionally, Jenny uses her own private key to sign a message and Tim uses Jenny’s public key to verify
the message.
The Zyxel Device uses certificates based on public-key cryptology to authenticate users attempting to
establish a connection, not to encrypt the data that you send after establishing a connection. The
method used to secure the data that you send through an established connection depends on the
type of connection. For example, a VPN tunnel might use the triple DES encryption algorithm.
The certification authority uses its private key to sign certificates. Anyone can then use the certification
authority’s public key to verify the certificates.
A certification path is the hierarchy of certification authority certificates that validate a certificate. The
Zyxel Device does not trust a certificate if any certificate on its path has expired or been revoked.
Certification authorities maintain directory servers with databases of valid and revoked certificates. A
directory of certificates that have been revoked before the scheduled expiration is called a CRL
(Certificate Revocation List). The Zyxel Device can check a peer’s certificate against a directory server’s
list of revoked certificates. The framework of servers, software, procedures and policies that handles keys
is called PKI (public-key infrastructure).
Advantages of Certificates
Certificates offer the following benefits.
• The Zyxel Device only has to store the certificates of the certification authorities that you decide to
trust, no matter how many devices you need to authenticate.
• Key distribution is simple and very secure since you can freely distribute public keys and you never
need to transmit private keys.
Self-signed Certificates
You can have the Zyxel Device act as a certification authority and sign its own certificates.
Factory Default Certificate
The Zyxel Device generates its own unique self-signed certificate when you first turn it on. This certificate
is referred to in the GUI as the factory default certificate.
Certificate File Formats
Any certificate that you want to import has to be in one of these file formats:
• Binary X.509: This is an ITU-T recommendation that defines the formats for X.509 certificates.
• PEM (Base-64) encoded X.509: This Privacy Enhanced Mail format uses lowercase letters, uppercase
letters and numerals to convert a binary X.509 certificate into a printable form.

Chapter 43 Object
USG/ZyWALL User’s Guide
806
• Binary PKCS#7: This is a standard that defines the general syntax for data (including digital signatures)
that may be encrypted. A PKCS #7 file is used to transfer a public key certificate. The private key is not
included. The Zyxel Device currently allows the importation of a PKS#7 file that contains a single
certificate.
• PEM (Base-64) encoded PKCS#7: This Privacy Enhanced Mail (PEM) format uses lowercase letters,
uppercase letters and numerals to convert a binary PKCS#7 certificate into a printable form.
• Binary PKCS#12: This is a format for transferring public key and private key certificates. The private key
in a PKCS #12 file is within a password-encrypted envelope. The file’s password is not connected to
your certificate’s public or private passwords. Exporting a PKCS #12 file creates this and you must
provide it to decrypt the contents when you import the file into the Zyxel Device.
Note: Be careful not to convert a binary file to text during the transfer process. It is easy for this
to occur since many programs use text files by default.
43.11.2 Verifying a Certificate
Before you import a trusted certificate into the Zyxel Device, you should verify that you have the correct
certificate. You can do this using the certificate’s fingerprint. A certificate’s fingerprint is a message
digest calculated using the MD5 or SHA1 algorithm. The following procedure describes how to check a
certificate’s fingerprint to verify that you have the actual certificate.
1Browse to where you have the certificate saved on your computer.
2Make sure that the certificate has a “.cer” or “.crt” file name extension.
Figure 569 Remote Host Certificates
3Double-click the certificate’s icon to open the Certificate window. Click the Details tab and scroll down
to the Thumbprint Algorithm and Thumbprint fields.
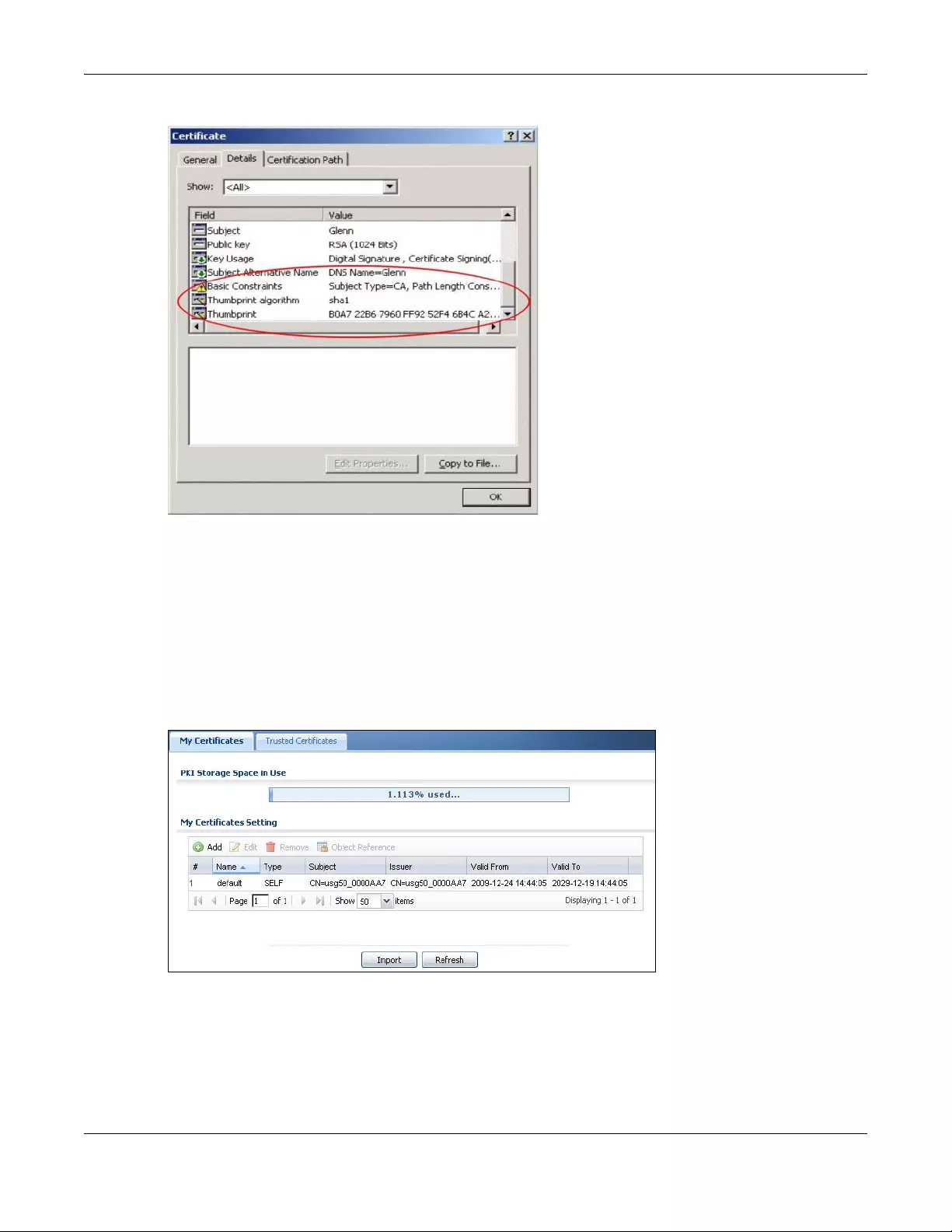
Chapter 43 Object
USG/ZyWALL User’s Guide
807
Figure 570 Certificate Details
4Use a secure method to verify that the certificate owner has the same information in the Thumbprint
Algorithm and Thumbprint fields. The secure method may very based on your situation. Possible
examples would be over the telephone or through an HTTPS connection.
43.11.3 The My Certificates Screen
Click Configuration > Object > Certifica te > My Certificates to open the My Certificates screen. This is the
Zyxel Device’s summary list of certificates and certification requests.
Figure 571 Configuration > Object > Certificate > My Certificates
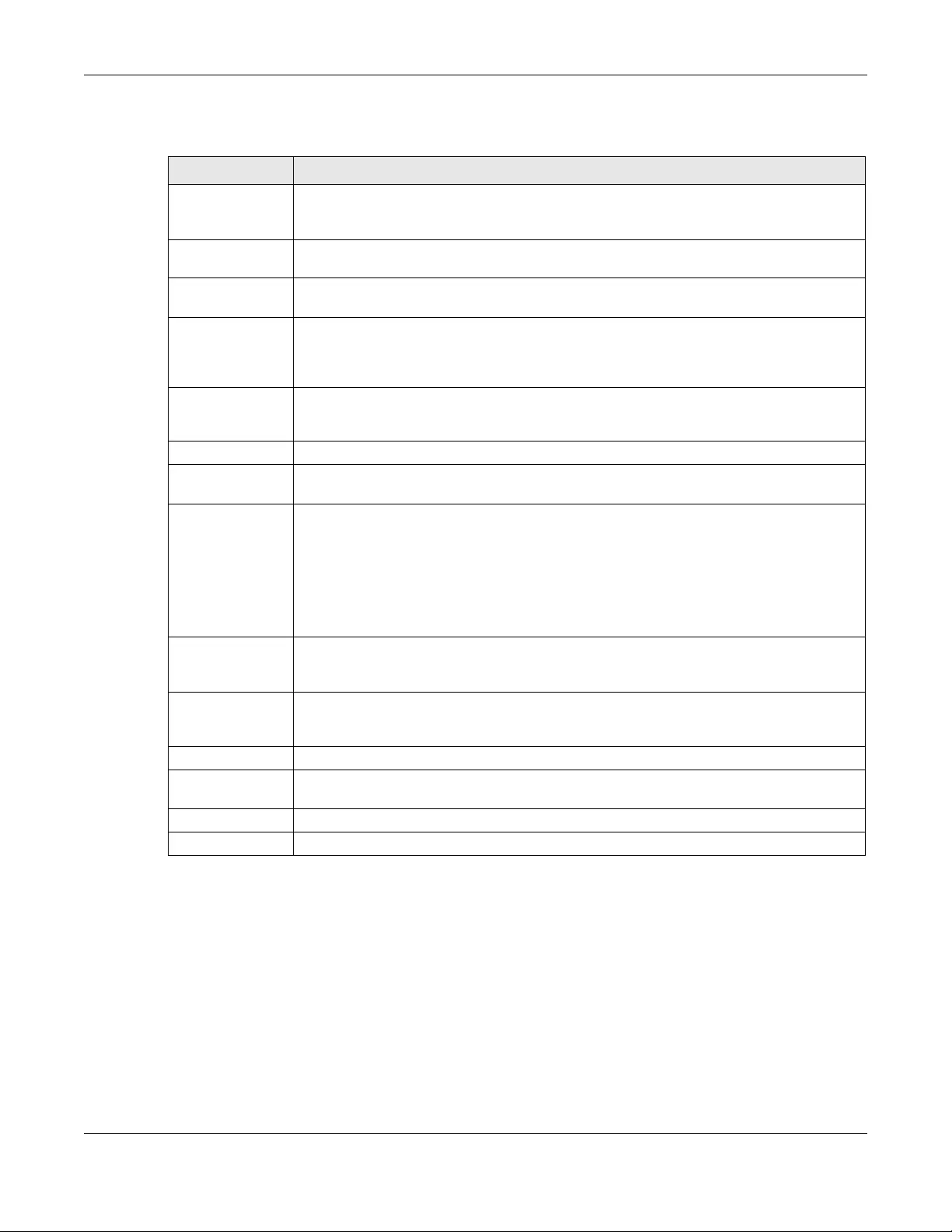
Chapter 43 Object
USG/ZyWALL User’s Guide
808
The following table describes the labels in this screen.
43.11.3.1 The My Certificates Add Screen
Click Configuration > Object > Certificate > My Certificates and then the Add icon to open the My
Certificates Add screen. Use this screen to have the Zyxel Device create a self-signed certificate, enroll a
certificate with a certification authority or generate a certification request.
Table 332 Configuration > Object > Certificate > My Certificates
LABEL DESCRIPTION
PKI Storage Space
in Use
This bar displays the percentage of the Zyxel Device’s PKI storage space that is currently in
use. When the storage space is almost full, you should consider deleting expired or
unnecessary certificates before adding more certificates.
Add Click this to go to the screen where you can have the Zyxel Device generate a certificate or
a certification request.
Edit Double-click an entry or select it and click Edit to open a screen with an in-depth list of
information about the certificate.
Remove The Zyxel Device keeps all of your certificates unless you specifically delete them. Uploading
a new firmware or default configuration file does not delete your certificates. To remove an
entry, select it and click Remove. The Zyxel Device confirms you want to remove it before
doing so. Subsequent certificates move up by one when you take this action.
Object References You cannot delete certificates that any of the Zyxel Device’s features are configured to use.
Select an entry and click Object References to open a screen that shows which settings use
the entry.
# This field displays the certificate index number. The certificates are listed in alphabetical order.
Name This field displays the name used to identify this certificate. It is recommended that you give
each certificate a unique name.
Type This field displays what kind of certificate this is.
REQ represents a certification request and is not yet a valid certificate. Send a certification
request to a certification authority, which then issues a certificate. Use the My Certificate
Import screen to import the certificate and replace the request.
SELF represents a self-signed certificate.
CERT represents a certificate issued by a certification authority.
Subject This field displays identifying information about the certificate’s owner, such as CN (Common
Name), OU (Organizational Unit or department), O (Organization or company) and C
(Country). It is recommended that each certificate have unique subject information.
Issuer This field displays identifying information about the certificate’s issuing certification authority,
such as a common name, organizational unit or department, organization or company and
country. With self-signed certificates, this is the same information as in the Subject field.
Valid From This field displays the date that the certificate becomes applicable.
Valid To This field displays the date that the certificate expires. The text displays in red and includes an
Expired! message if the certificate has expired.
Import Click Import to open a screen where you can save a certificate to the Zyxel Device.
Refresh Click Refresh to display the current validity status of the certificates.
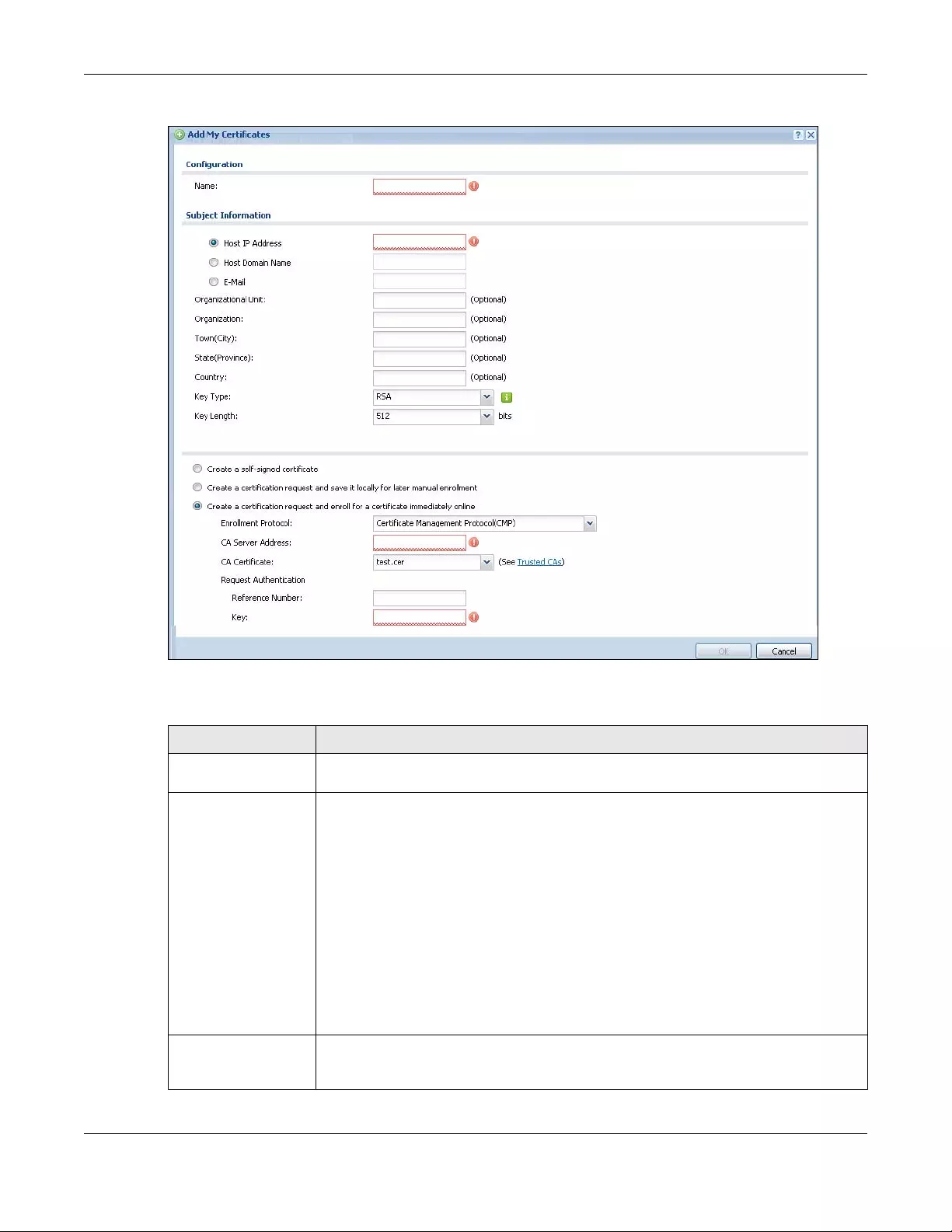
Chapter 43 Object
USG/ZyWALL User’s Guide
809
Figure 572 Configuration > Object > Certificate > My Certificates > Add
The following table describes the labels in this screen.
Table 333 Configuration > Object > Certificate > My Certificates > Add
LABEL DESCRIPTION
Name Type a name to identify this certificate. You can use up to 31 alphanumeric and
;‘~!@#$%^&()_+[]{}’,.=- characters.
Subject Information Use these fields to record information that identifies the owner of the certificate. You do
not have to fill in every field, although you must specify a Host IP Address, Host IPv6
Address, Host Domain Name, or E-Mail. The certification authority may add fields (such as
a serial number) to the subject information when it issues a certificate. It is recommended
that each certificate have unique subject information.
Select a radio button to identify the certificate’s owner by IP address, domain name or e-
mail address. Type the IP address (in dotted decimal notation), domain name or e-mail
address in the field provided. The domain name or e-mail address is for identification
purposes only and can be any string.
A domain name can be up to 255 characters. You can use alphanumeric characters, the
hyphen and periods.
An e-mail address can be up to 63 characters. You can use alphanumeric characters, the
hyphen, the @ symbol, periods and the underscore.
Organizational Unit Identify the organizational unit or department to which the certificate owner belongs. You
can use up to 31 characters. You can use alphanumeric characters, the hyphen and the
underscore.
Chapter 43 Object
USG/ZyWALL User’s Guide
810
If you configured the My Certificate Create screen to have the Zyxel Device enroll a certificate and the
certificate enrollment is not successful, you see a screen with a Return button that takes you back to the
My Certificate Create screen. Click Return and check your information in the My Certificate Create
screen. Make sure that the certification authority information is correct and that your Internet
connection is working properly if you want the Zyxel Device to enroll a certificate online.
Organization Identify the company or group to which the certificate owner belongs. You can use up to
31 characters. You can use alphanumeric characters, the hyphen and the underscore.
Town (City) Identify the town or city where the certificate owner is located. You can use up to 31
characters. You can use alphanumeric characters, the hyphen and the underscore.
State, (Province) Identify the state or province where the certificate owner is located. You can use up to 31
characters. You can use alphanumeric characters, the hyphen and the underscore.
Country Identify the nation where the certificate owner is located. You can use up to 31
characters. You can use alphanumeric characters, the hyphen and the underscore.
Key Type Select RSA to use the Rivest, Shamir and Adleman public-key algorithm.
Select DSA to use the Digital Signature Algorithm public-key algorithm.
Key Length Select a number from the drop-down list box to determine how many bits the key should
use (512 to 2048). The longer the key, the more secure it is. A longer key also uses more PKI
storage space.
Extended Key Usage
Server Authentication Select this to have Zyxel Device generate and store a request for server authentication
certificate.
Client Authentication Select this to have Zyxel Device generate and store a request for client authentication
certificate.
IKE Intermediate Select this to have Zyxel Device generate and store a request for IKE Intermediate
authentication certificate.
Create a self-signed
certificate
Select this to have the Zyxel Device generate the certificate and act as the Certification
Authority (CA) itself. This way you do not need to apply to a certification authority for
certificates.
Create a certification
request and save it
locally for later
manual enrollment
Select this to have the Zyxel Device generate and store a request for a certificate. Use the
My Certificate Details screen to view the certification request and copy it to send to the
certification authority.
Copy the certification request from the My Certificate Details screen (see Section 43.11.3.2
on page 811) and then send it to the certification authority.
Create a certification
request and enroll for
a certificate
immediately online
Select this to have the Zyxel Device generate a request for a certificate and apply to a
certification authority for a certificate.
You must have the certification authority’s certificate already imported in the Trusted
Certificates screen.
When you select this option, you must select the certification authority’s enrollment
protocol and the certification authority’s certificate from the drop-down list boxes and
enter the certification authority’s server address. You also need to fill in the Reference
Number and Key if the certification authority requires them.
OK Click OK to begin certificate or certification request generation.
Cancel Click Cancel to quit and return to the My Certificates screen.
Table 333 Configuration > Object > Certificate > My Certificates > Add (continued)
LABEL DESCRIPTION
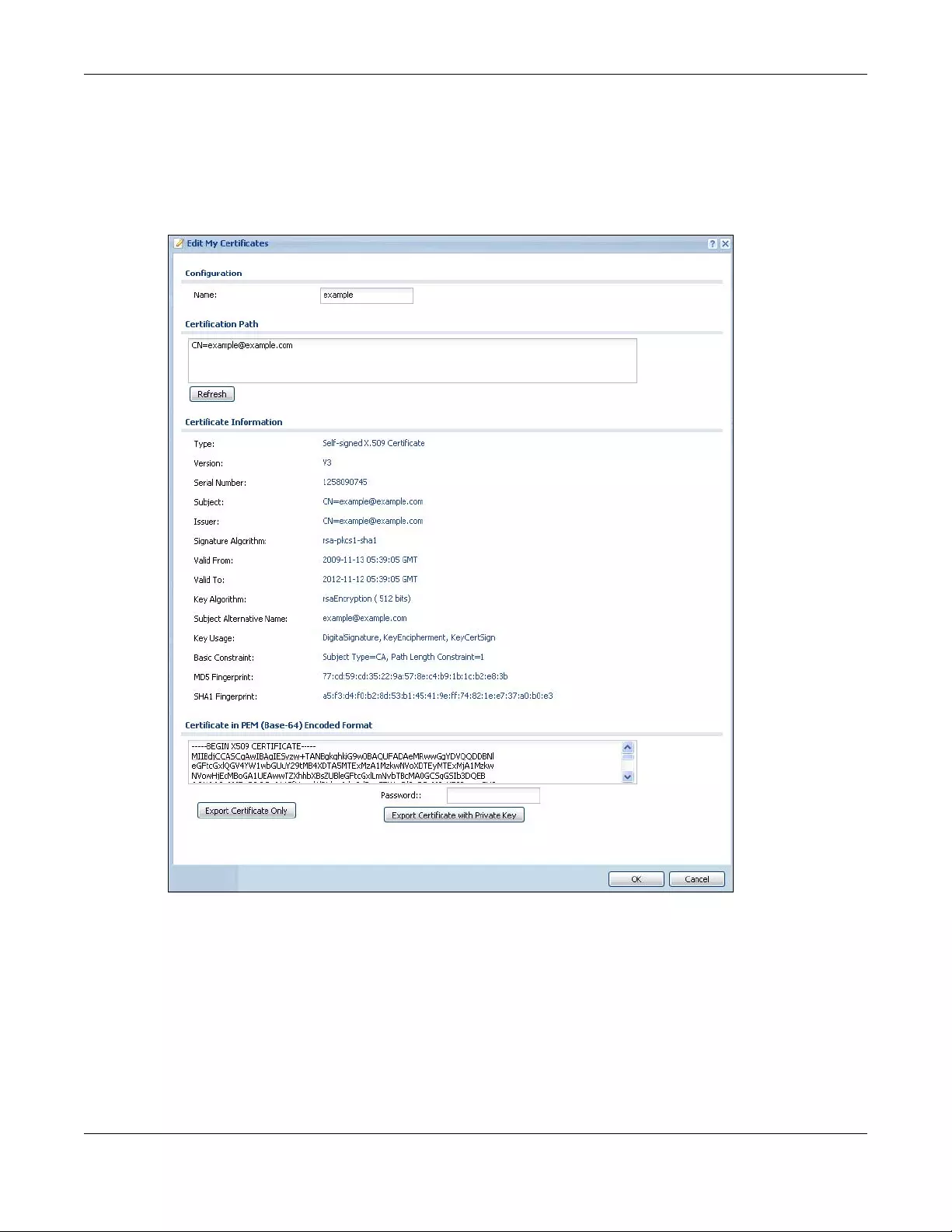
Chapter 43 Object
USG/ZyWALL User’s Guide
811
43.11.3.2 The My Certificates Edit Screen
Click Configuration > Object > Certificate > My Certificates and then the Edit icon to open the My
Certificate Edit screen. You can use this screen to view in-depth certificate information and change the
certificate’s name.
Figure 573 Configuration > Object > Certificate > My Certificates > Edit
Chapter 43 Object
USG/ZyWALL User’s Guide
812
The following table describes the labels in this screen.
Table 334 Configuration > Object > Certificate > My Certificates > Edit
LABEL DESCRIPTION
Name This field displays the identifying name of this certificate. You can use up to 31 alphanumeric
and ;‘~!@#$%^&()_+[]{}’,.=- characters.
Certification Path This field displays for a certificate, not a certification request.
Click the Refresh button to have this read-only text box display the hierarchy of certification
authorities that validate the certificate (and the certificate itself).
If the issuing certification authority is one that you have imported as a trusted certification
authority, it may be the only certification authority in the list (along with the certificate itself).
If the certificate is a self-signed certificate, the certificate itself is the only one in the list. The
Zyxel Device does not trust the certificate and displays “Not trusted” in this field if any
certificate on the path has expired or been revoked.
Refresh Click Refresh to display the certification path.
Certificate
Information
These read-only fields display detailed information about the certificate.
Type This field displays general information about the certificate. CA-signed means that a
Certification Authority signed the certificate. Self-signed means that the certificate’s owner
signed the certificate (not a certification authority). “X.509” means that this certificate was
created and signed according to the ITU-T X.509 recommendation that defines the formats
for public-key certificates.
Version This field displays the X.509 version number.
Serial Number This field displays the certificate’s identification number given by the certification authority
or generated by the Zyxel Device.
Subject This field displays information that identifies the owner of the certificate, such as Common
Name (CN), Organizational Unit (OU), Organization (O), State (ST), and Country (C).
Issuer This field displays identifying information about the certificate’s issuing certification
authority, such as Common Name, Organizational Unit, Organization and Country.
With self-signed certificates, this is the same as the Subject Name field.
“none” displays for a certification request.
Signature Algorithm This field displays the type of algorithm that was used to sign the certificate. The Zyxel
Device uses rsa-pkcs1-sha1 (RSA public-private key encryption algorithm and the SHA1
hash algorithm). Some certification authorities may use rsa-pkcs1-md5 (RSA public-private
key encryption algorithm and the MD5 hash algorithm).
Valid From This field displays the date that the certificate becomes applicable. “none” displays for a
certification request.
Valid To This field displays the date that the certificate expires. The text displays in red and includes
an Expired! message if the certificate has expired. “none” displays for a certification
request.
Key Algorithm This field displays the type of algorithm that was used to generate the certificate’s key pair
(the Zyxel Device uses RSA encryption) and the length of the key set in bits (1024 bits for
example).
Subject Alternative
Name
This field displays the certificate owner‘s IP address (IP), domain name (DNS) or e-mail
address (EMAIL).
Key Usage This field displays for what functions the certificate’s key can be used. For example,
“DigitalSignature” means that the key can be used to sign certificates and
“KeyEncipherment” means that the key can be used to encrypt text.
Basic Constraint This field displays general information about the certificate. For example, Subject Type=CA
means that this is a certification authority’s certificate and “Path Length Constraint=1”
means that there can only be one certification authority in the certificate’s path. This field
does not display for a certification request.
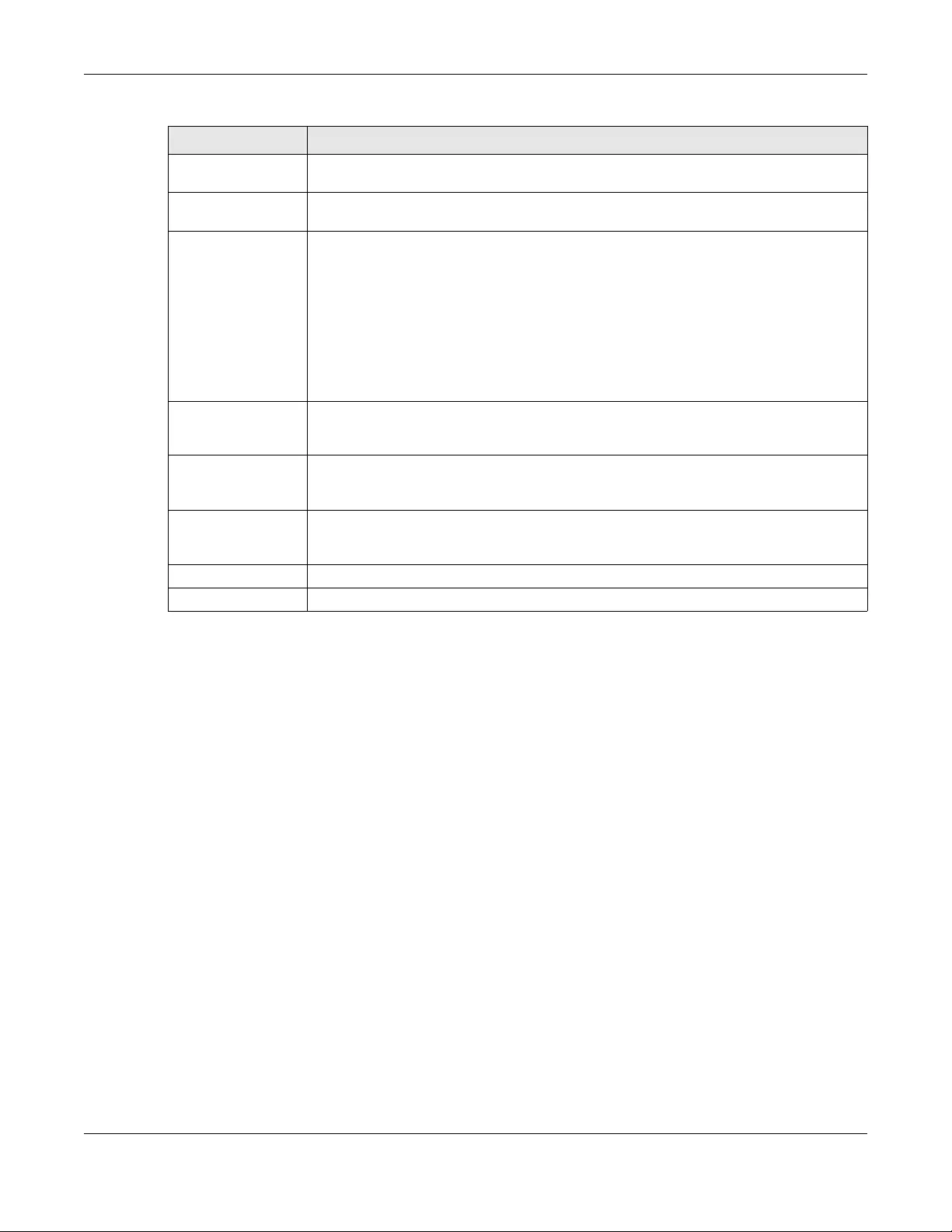
Chapter 43 Object
USG/ZyWALL User’s Guide
813
43.11.3.3 The My Certificates Import Screen
Click Configuration > Object > Certificate > My Certificates > Import to open the My Certificate Import
screen. Follow the instructions in this screen to save an existing certificate to the Zyxel Device.
Note: You can import a certificate that matches a corresponding certification request that
was generated by the Zyxel Device. You can also import a certificate in PKCS#12
format, including the certificate’s public and private keys.
The certificate you import replaces the corresponding request in the My Certificates screen.
You must remove any spaces from the certificate’s filename before you can import it.
MD5 Fingerprint This is the certificate’s message digest that the Zyxel Device calculated using the MD5
algorithm.
SHA1 Fingerprint This is the certificate’s message digest that the Zyxel Device calculated using the SHA1
algorithm.
Certificate in PEM
(Base-64) Encoded
Format
This read-only text box displays the certificate or certification request in Privacy Enhanced
Mail (PEM) format. PEM uses lowercase letters, uppercase letters and numerals to convert a
binary certificate into a printable form.
You can copy and paste a certification request into a certification authority’s web page,
an e-mail that you send to the certification authority or a text editor and save the file on a
management computer for later manual enrollment.
You can copy and paste a certificate into an e-mail to send to friends or colleagues or you
can copy and paste a certificate into a text editor and save the file on a management
computer for later distribution (via floppy disk for example).
Export Certificate
Only
Use this button to save a copy of the certificate without its private key. Click this button and
then Save in the File Download screen. The Save As screen opens, browse to the location
that you want to use and click Save.
Password If you want to export the certificate with its private key, create a password and type it here.
Make sure you keep this password in a safe place. You will need to use it if you import the
certificate to another device.
Export Certificate
with Private Key
Use this button to save a copy of the certificate with its private key. Type the certificate’s
password and click this button. Click Save in the File Download screen. The Save As screen
opens, browse to the location that you want to use and click Save.
OK Click OK to save your changes back to the Zyxel Device. You can only change the name.
Cancel Click Cancel to quit and return to the My Certificates screen.
Table 334 Configuration > Object > Certificate > My Certificates > Edit (continued)
LABEL DESCRIPTION
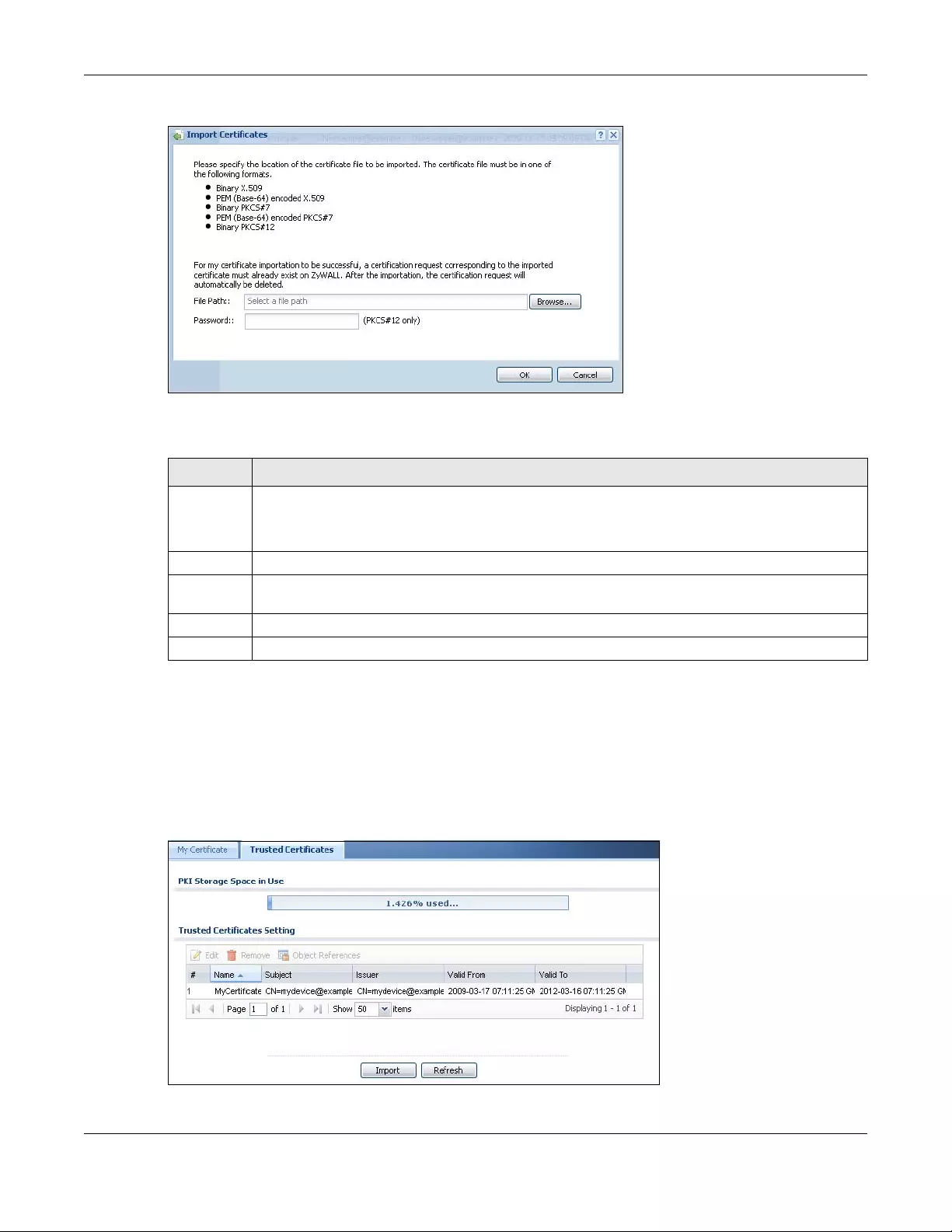
Chapter 43 Object
USG/ZyWALL User’s Guide
814
Figure 574 Configuration > Object > Certificate > My Certificates > Import
The following table describes the labels in this screen.
43.11.4 The Trusted Certificates Screen
Click Configuration > Object > Certificate > Trusted Certificates to open the Trusted Certificates screen.
This screen displays a summary list of certificates that you have set the Zyxel Device to accept as trusted.
The Zyxel Device also accepts any valid certificate signed by a certificate on this list as being
trustworthy; thus you do not need to import any certificate that is signed by one of these certificates.
Figure 575 Configuration > Object > Certificate > Trusted Certificates
Table 335 Configuration > Object > Certificate > My Certificates > Import
LABEL DESCRIPTION
File Path Type in the location of the file you want to upload in this field or click Browse to find it.
You cannot import a certificate with the same name as a certificate that is already in the Zyxel
Device.
Browse Click Browse to find the certificate file you want to upload.
Password This field only applies when you import a binary PKCS#12 format file. Type the file’s password that was
created when the PKCS #12 file was exported.
OK Click OK to save the certificate on the Zyxel Device.
Cancel Click Cancel to quit and return to the My Certificates screen.
Chapter 43 Object
USG/ZyWALL User’s Guide
815
The following table describes the labels in this screen.
43.11.4.1 The Trusted Certificates Edit Screen
Click Configuration > Object > Certificate > Trusted Certificates and then a certificate’s Edit icon to open
the Trusted Certificates Edit screen. Use this screen to view in-depth information about the certificate,
change the certificate’s name and set whether or not you want the Zyxel Device to check a
certification authority’s list of revoked certificates before trusting a certificate issued by the certification
authority.
Table 336 Configuration > Object > Certificate > Trusted Certificates
LABEL DESCRIPTION
PKI Storage Space
in Use
This bar displays the percentage of the Zyxel Device’s PKI storage space that is currently in
use. When the storage space is almost full, you should consider deleting expired or
unnecessary certificates before adding more certificates.
Edit Double-click an entry or select it and click Edit to open a screen with an in-depth list of
information about the certificate.
Remove The Zyxel Device keeps all of your certificates unless you specifically delete them. Uploading a
new firmware or default configuration file does not delete your certificates. To remove an
entry, select it and click Remove. The Zyxel Device confirms you want to remove it before
doing so. Subsequent certificates move up by one when you take this action.
Object
References
You cannot delete certificates that any of the Zyxel Device’s features are configured to use.
Select an entry and click Object References to open a screen that shows which settings use
the entry.
# This field displays the certificate index number. The certificates are listed in alphabetical order.
Name This field displays the name used to identify this certificate.
Subject This field displays identifying information about the certificate’s owner, such as CN (Common
Name), OU (Organizational Unit or department), O (Organization or company) and C
(Country). It is recommended that each certificate have unique subject information.
Issuer This field displays identifying information about the certificate’s issuing certification authority,
such as a common name, organizational unit or department, organization or company and
country. With self-signed certificates, this is the same information as in the Subject field.
Valid From This field displays the date that the certificate becomes applicable.
Valid To This field displays the date that the certificate expires. The text displays in red and includes an
Expired! message if the certificate has expired.
Import Click Import to open a screen where you can save the certificate of a certification authority
that you trust, from your computer to the Zyxel Device.
Refresh Click this button to display the current validity status of the certificates.
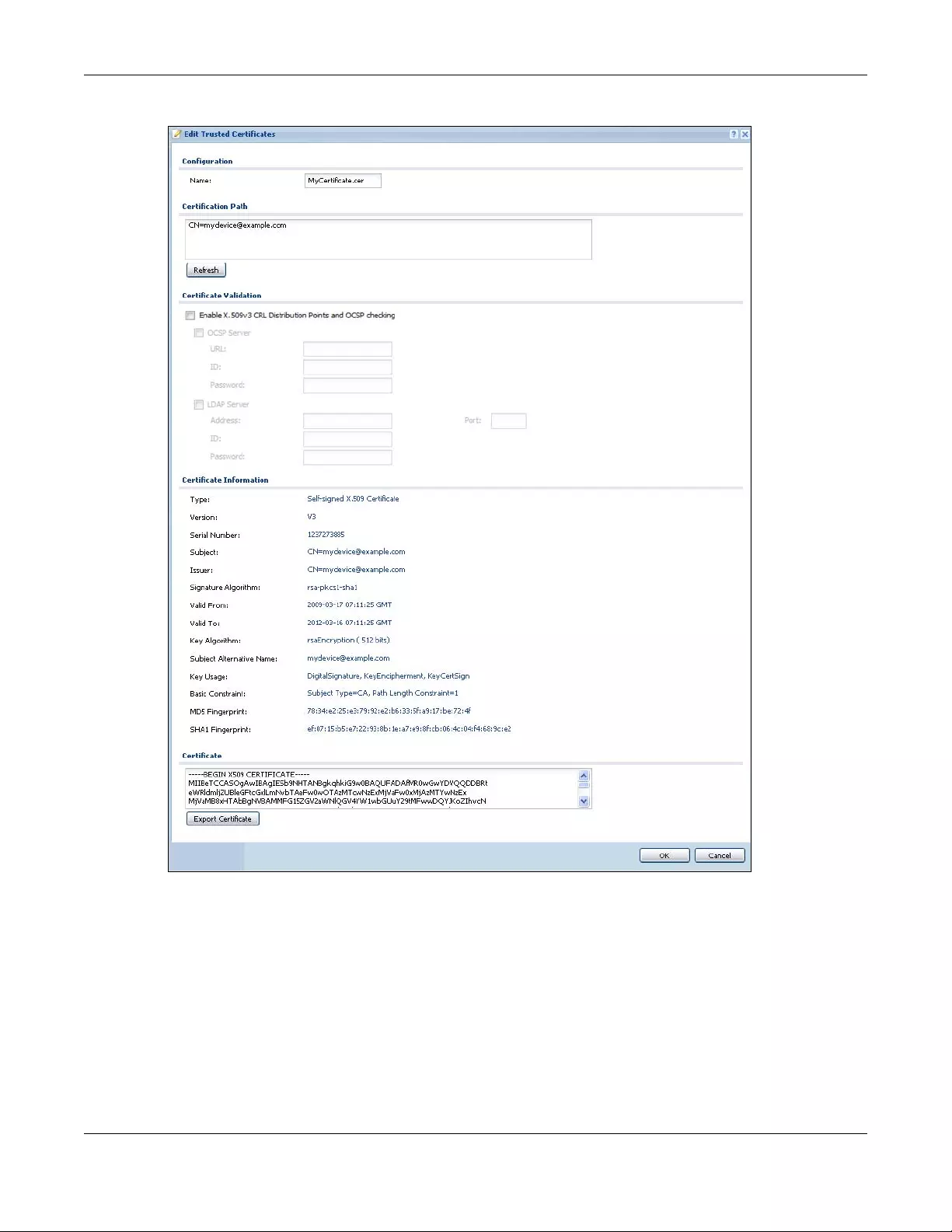
Chapter 43 Object
USG/ZyWALL User’s Guide
816
Figure 576 Configuration > Object > Certificate > Trusted Certificates > Edit
Chapter 43 Object
USG/ZyWALL User’s Guide
817
The following table describes the labels in this screen.
Table 337 Configuration > Object > Certificate > Trusted Certificates > Edit
LABEL DESCRIPTION
Name This field displays the identifying name of this certificate. You can change the name. You
can use up to 31 alphanumeric and ;‘~!@#$%^&()_+[]{}’,.=- characters.
Certification Path Click the Refresh button to have this read-only text box display the end entity’s certificate
and a list of certification authority certificates that shows the hierarchy of certification
authorities that validate the end entity’s certificate. If the issuing certification authority is
one that you have imported as a trusted certificate, it may be the only certification
authority in the list (along with the end entity’s own certificate). The Zyxel Device does not
trust the end entity’s certificate and displays “Not trusted” in this field if any certificate on
the path has expired or been revoked.
Refresh Click Refresh to display the certification path.
Enable X.509v3 CRL
Distribution Points
and OCSP checking
Select this check box to turn on/off certificate revocation. When it is turned on, the Zyxel
Device validates a certificate by getting Certificate Revocation List (CRL) through HTTP or
LDAP (can be configured after selecting the LDAP Server check box) and online responder
(can be configured after selecting the OCSP Server check box).
OCSP Server Select this check box if the directory server uses OCSP (Online Certificate Status Protocol).
URL Type the protocol, IP address and path name of the OCSP server.
ID The Zyxel Device may need to authenticate itself in order to assess the OCSP server. Type
the login name (up to 31 ASCII characters) from the entity maintaining the server (usually a
certification authority).
Password Type the password (up to 31 ASCII characters) from the entity maintaining the OCSP server
(usually a certification authority).
LDAP Server Select this check box if the directory server uses LDAP (Lightweight Directory Access
Protocol). LDAP is a protocol over TCP that specifies how clients access directories of
certificates and lists of revoked certificates.
Address Type the IP address (in dotted decimal notation) of the directory server.
Port Use this field to specify the LDAP server port number. You must use the same server port
number that the directory server uses. 389 is the default server port number for LDAP.
ID The Zyxel Device may need to authenticate itself in order to assess the CRL directory server.
Type the login name (up to 31 ASCII characters) from the entity maintaining the server
(usually a certification authority).
Password Type the password (up to 31 ASCII characters) from the entity maintaining the CRL directory
server (usually a certification authority).
Certificate
Information
These read-only fields display detailed information about the certificate.
Type This field displays general information about the certificate. CA-signed means that a
Certification Authority signed the certificate. Self-signed means that the certificate’s owner
signed the certificate (not a certification authority). X.509 means that this certificate was
created and signed according to the ITU-T X.509 recommendation that defines the formats
for public-key certificates.
Version This field displays the X.509 version number.
Serial Number This field displays the certificate’s identification number given by the certification authority.
Subject This field displays information that identifies the owner of the certificate, such as Common
Name (CN), Organizational Unit (OU), Organization (O) and Country (C).
Issuer This field displays identifying information about the certificate’s issuing certification
authority, such as Common Name, Organizational Unit, Organization and Country.
With self-signed certificates, this is the same information as in the Subject Name field.
Chapter 43 Object
USG/ZyWALL User’s Guide
818
43.11.4.2 The Trusted Certificates Import Screen
Click Co nfiguration > Object > Certificate > Trusted Certificates > Import to open the Trus ted Ce rtificates
Import screen. Follow the instructions in this screen to save a trusted certificate to the Zyxel Device.
Note: You must remove any spaces from the certificate’s filename before you can import the
certificate.
Signature Algorithm This field displays the type of algorithm that was used to sign the certificate. Some
certification authorities use rsa-pkcs1-sha1 (RSA public-private key encryption algorithm
and the SHA1 hash algorithm). Other certification authorities may use rsa-pkcs1-md5 (RSA
public-private key encryption algorithm and the MD5 hash algorithm).
Valid From This field displays the date that the certificate becomes applicable. The text displays in red
and includes a Not Yet Valid! message if the certificate has not yet become applicable.
Valid To This field displays the date that the certificate expires. The text displays in red and includes
an Expiring! or Expired! message if the certificate is about to expire or has already expired.
Key Algorithm This field displays the type of algorithm that was used to generate the certificate’s key pair
(the Zyxel Device uses RSA encryption) and the length of the key set in bits (1024 bits for
example).
Subject Alternative
Name
This field displays the certificate’s owner‘s IP address (IP), domain name (DNS) or e-mail
address (EMAIL).
Key Usage This field displays for what functions the certificate’s key can be used. For example,
“DigitalSignature” means that the key can be used to sign certificates and
“KeyEncipherment” means that the key can be used to encrypt text.
Basic Constraint This field displays general information about the certificate. For example, Subject Type=CA
means that this is a certification authority’s certificate and “Path Length Constraint=1”
means that there can only be one certification authority in the certificate’s path.
MD5 Fingerprint This is the certificate’s message digest that the Zyxel Device calculated using the MD5
algorithm. You can use this value to verify with the certification authority (over the phone for
example) that this is actually their certificate.
SHA1 Fingerprint This is the certificate’s message digest that the Zyxel Device calculated using the SHA1
algorithm. You can use this value to verify with the certification authority (over the phone for
example) that this is actually their certificate.
Certificate This read-only text box displays the certificate or certification request in Privacy Enhanced
Mail (PEM) format. PEM uses lowercase letters, uppercase letters and numerals to convert a
binary certificate into a printable form.
You can copy and paste the certificate into an e-mail to send to friends or colleagues or
you can copy and paste the certificate into a text editor and save the file on a
management computer for later distribution (via floppy disk for example).
Export Certificate Click this button and then Save in the File Download screen. The Save As screen opens,
browse to the location that you want to use and click Save.
OK Click OK to save your changes back to the Zyxel Device. You can only change the name.
Cancel Click Cancel to quit and return to the Trusted Certificates screen.
Table 337 Configuration > Object > Certificate > Trusted Certificates > Edit (continued)
LABEL DESCRIPTION
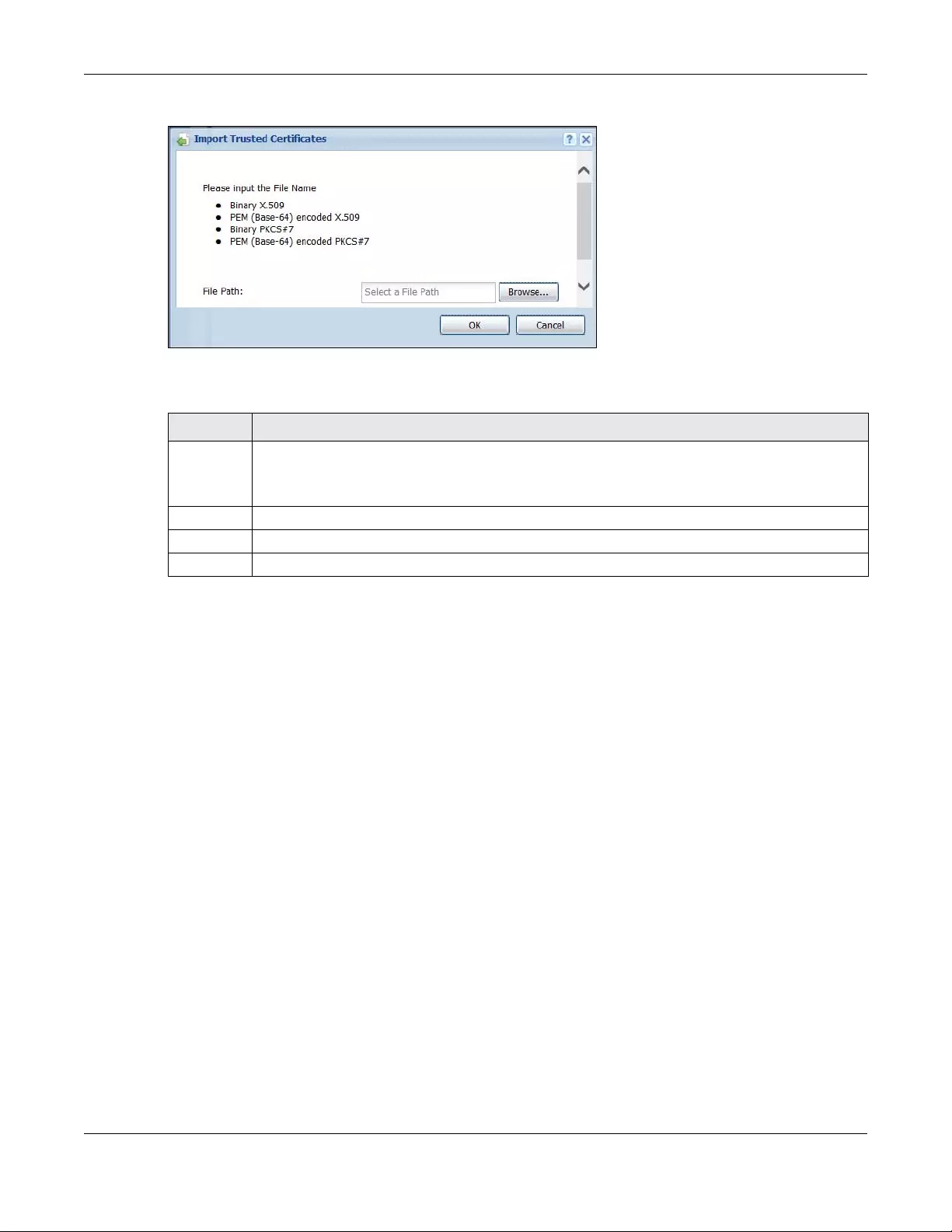
Chapter 43 Object
USG/ZyWALL User’s Guide
819
Figure 577 Configuration > Object > Certificate > Trusted Certificates > Import
The following table describes the labels in this screen.
43.11.5 Certificates Technical Reference
OCSP
OCSP (Online Certificate Status Protocol) allows an application or device to check whether a certificate
is valid. With OCSP the Zyxel Device checks the status of individual certificates instead of downloading a
Certificate Revocation List (CRL). OCSP has two main advantages over a CRL. The first is real-time status
information. The second is a reduction in network traffic since the Zyxel Device only gets information on
the certificates that it needs to verify, not a huge list. When the Zyxel Device requests certificate status
information, the OCSP server returns a “expired”, “current” or “unknown” response.
43.12 ISP Account Overview
Use ISP accounts to manage Internet Service Provider (ISP) account information for PPPoE/PPTP/L2TP
interfaces. An ISP account is a profile of settings for Internet access using PPPoE, PPTP or L2TP.
Use the Object > ISP Account screens (Section 43.12.1 on page 819) to create and manage ISP
accounts in the Zyxel Device.
43.12.1 ISP Account Summary
This screen provides a summary of ISP accounts in the Zyxel Device. To access this screen, click
Configuration > Object > ISP Account.
Table 338 Configuration > Object > Certificate > Trusted Certificates > Import
LABEL DESCRIPTION
File Path Type in the location of the file you want to upload in this field or click Browse to find it.
You cannot import a certificate with the same name as a certificate that is already in the Zyxel
Device.
Browse Click Browse to find the certificate file you want to upload.
OK Click OK to save the certificate on the Zyxel Device.
Cancel Click Cancel to quit and return to the previous screen.
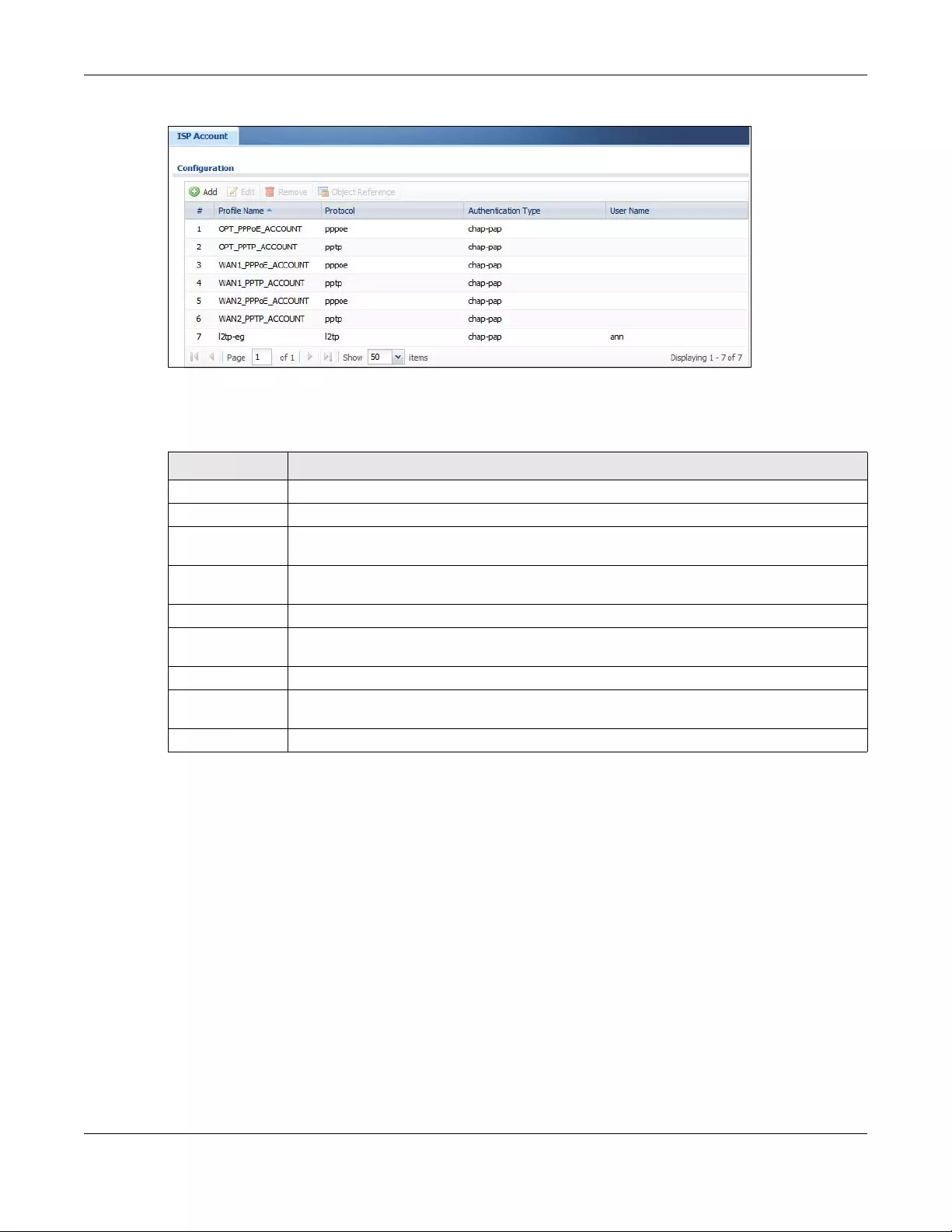
Chapter 43 Object
USG/ZyWALL User’s Guide
820
Figure 578 Configuration > Object > ISP Account
The following table describes the labels in this screen. See the ISP Account Add/Edit section below for
more information as well.
43.12.1.1 ISP Account Add/Edit
The ISP Account Add/Edit screen lets you add information about new accounts and edit information
about existing accounts. To open this window, open the ISP Account screen. (See Section 43.12.1 on
page 819.) Then, click on an Add icon or Edit icon to open the ISP Account Edit screen below.
Table 339 Configuration > Object > ISP Account
LABEL DESCRIPTION
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Object
References
Select an entry and click Object References to open a screen that shows which settings use
the entry.
# This field is a sequential value, and it is not associated with a specific entry.
Profile Name This field displays the profile name of the ISP account. This name is used to identify the ISP
account.
Protocol This field displays the protocol used by the ISP account.
Authentication
Type
This field displays the authentication type used by the ISP account.
User Name This field displays the user name of the ISP account.
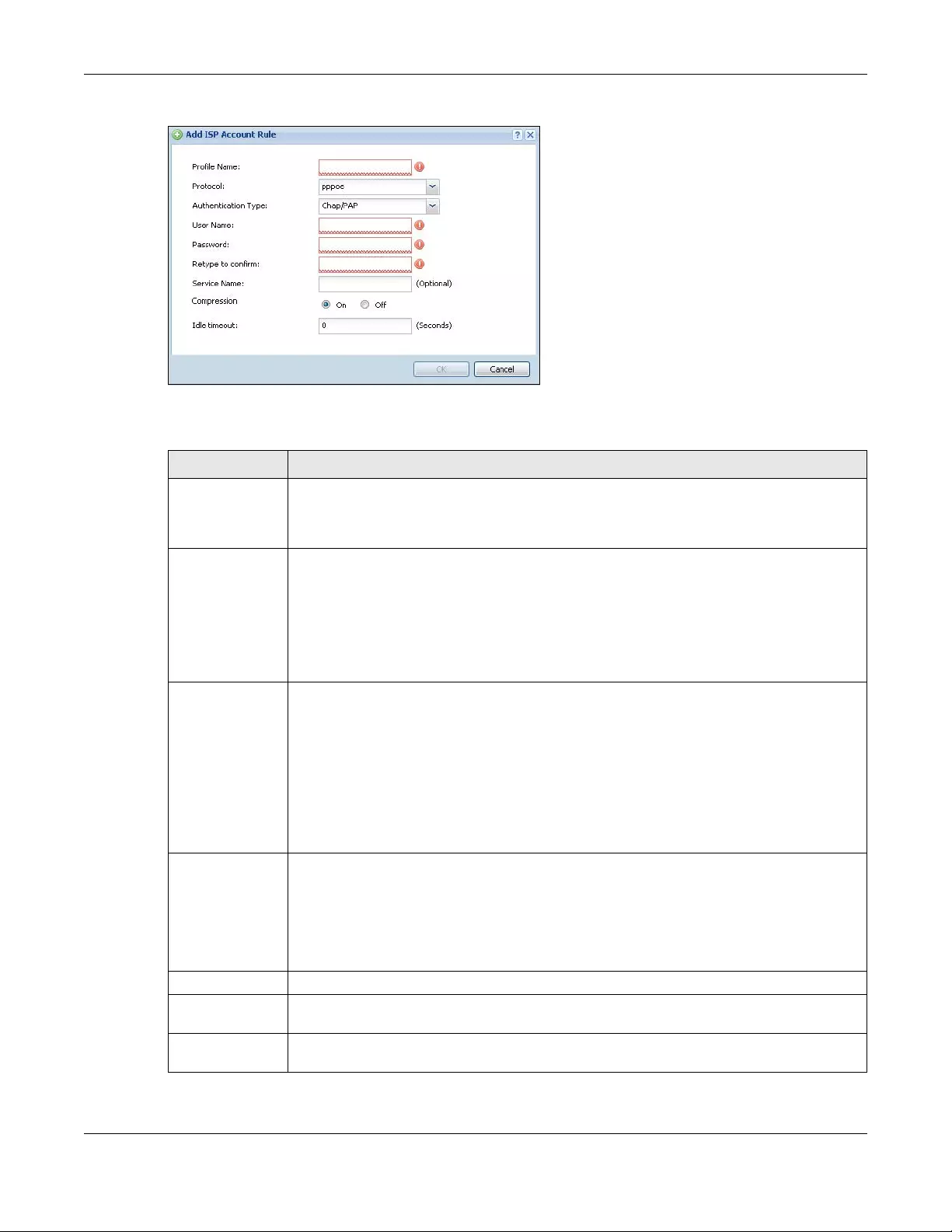
Chapter 43 Object
USG/ZyWALL User’s Guide
821
Figure 579 Configuration > Object > ISP Account > Edit
The following table describes the labels in this screen.
Table 340 Configuration > Object > ISP Account > Edit
LABEL DESCRIPTION
Profile Name This field is read-only if you are editing an existing account. Type in the profile name of the ISP
account. The profile name is used to refer to the ISP account. You may use 1-31 alphanumeric
characters, underscores(_), or dashes (-), but the first character cannot be a number. This
value is case-sensitive.
Protocol This field is read-only if you are editing an existing account. Select the protocol used by the ISP
account. Your ISP will provide you with a related username, password and IP (server)
information. Options are:
pppoe - This ISP account uses the PPPoE protocol.
pptp - This ISP account uses the PPTP protocol.
l2tp - This ISP account uses the L2TP protocol.
Authentication
Type
Use the drop-down list box to select an authentication protocol for outgoing calls. Options are:
CHAP/PAP - Your Zyxel Device accepts either CHAP or PAP when requested by this remote
node.
Chap - Your Zyxel Device accepts CHAP only.
PAP - Your Zyxel Device accepts PAP only.
MSCHAP - Your Zyxel Device accepts MSCHAP only.
MSCHAP-V2 - Your Zyxel Device accepts MSCHAP-V2 only.
Encryption
Method
This field is available if this ISP account uses the PPTP protocol. Use the drop-down list box to
select the type of Microsoft Point-to-Point Encryption (MPPE). Options are:
nomppe - This ISP account does not use MPPE.
mppe-40 - This ISP account uses 40-bit MPPE.
mppe-128 - This ISP account uses 128-bit MMPE.
User Name Type the user name given to you by your ISP.
Password Type the password associated with the user name above. The password can only consist of
alphanumeric characters (A-Z, a-z, 0-9). This field can be blank.
Retype to
Confirm
Type your password again to make sure that you have entered is correctly.
Chapter 43 Object
USG/ZyWALL User’s Guide
822
43.13 SSL Application Overview
You use SSL application objects in SSL VPN. Configure an SSL application object to specify the type of
application and the address of the local computer, server, or web site SSL users are to be able to
access. You can apply one or more SSL application objects in the VPN > SSL VPN screen for a user
account/user group.
• Use the SSL Application screen (Section 43.13.2 on page 824) to view the Zyxel Device’s configured
SSL application objects.
• Use the SSL Application Edit screen to create or edit web-based application objects to allow remote
users to access an application via standard web browsers (Section 43.13.2.1 on page 825).
• You can also use the SSL Application Edit screen to specify the name of a folder on a Linux or
Windows file server which remote users can access using a standard web browser (Section 43.13.2.1
on page 825).
43.13.1 What You Need to Know
Application Types
You can configure the following SSL application on the Zyxel Device.
•Web-based
A web-based application allows remote users to access an intranet site using standard web browsers.
Server IP If this ISP account uses the PPPoE protocol, this field is not displayed.
If this ISP account uses the PPTP protocol, type the IP address of the PPTP server.
Connection ID This field is available if this ISP account uses the PPTP protocol. Type your identification name for
the PPTP server. This field can be blank.
Service Name If this ISP account uses the PPPoE protocol, type the PPPoE service name to access. PPPoE uses
the specified service name to identify and reach the PPPoE server. This field can be blank.
If this ISP account uses the PPTP protocol, this field is not displayed.
Compression Select On button to turn on stac compression, and select Off to turn off stac compression. Stac
compression is a data compression technique capable of compressing data by a factor of
about four.
Idle Timeout This value specifies the number of seconds that must elapse without outbound traffic before
the Zyxel Device automatically disconnects from the PPPoE/PPTP server. This value must be an
integer between 0 and 360. If this value is zero, this timeout is disabled.
OK Click OK to save your changes back to the Zyxel Device. If there are no errors, the program
returns to the ISP Account screen. If there are errors, a message box explains the error, and the
program stays in the ISP Account Edit screen.
Cancel Click Cancel to return to the ISP Account screen without creating the profile (if it is new) or
saving any changes to the profile (if it already exists).
Table 340 Configuration > Object > ISP Account > Edit (continued)
LABEL DESCRIPTION

Chapter 43 Object
USG/ZyWALL User’s Guide
823
Remote User Screen Links
Available SSL application names are displayed as links in remote user screens. Depending on the
application type, remote users can simply click the links or follow the steps in the pop-up dialog box to
access.
Remote Desktop Connections
Use SSL VPN to allow remote users to manage LAN computers. Depending on the functions supported
by the remote desktop software, they can install or remove software, run programs, change settings,
and open, copy, create, and delete files. This is useful for troubleshooting, support, administration, and
remote access to files and programs.
The LAN computer to be managed must have VNC (Virtual Network Computing) or RDP (Remote
Desktop Protocol) server software installed. The remote user’s computer does not use VNC or RDP client
software. The Zyxel Device works with the following remote desktop connection software:
RDP
• Windows Remote Desktop (supported in Internet Explorer)
VNC
•RealVNC
•TightVNC
•UltraVNC
For example, user A uses an SSL VPN connection to log into the Zyxel Device. Then he manages LAN
computer B which has RealVNC server software installed.
Figure 580 SSL-protected Remote Management
Weblinks
You can configure weblink SSL applications to allow remote users to access web sites.
43.13.1.1 Example: Specifying a Web Site for Access
This example shows you how to create a web-based application for an internal web site. The address of
the web site is http://info with web page encryption.
1Click Configuration > Object > SSL Application in the navigation panel.
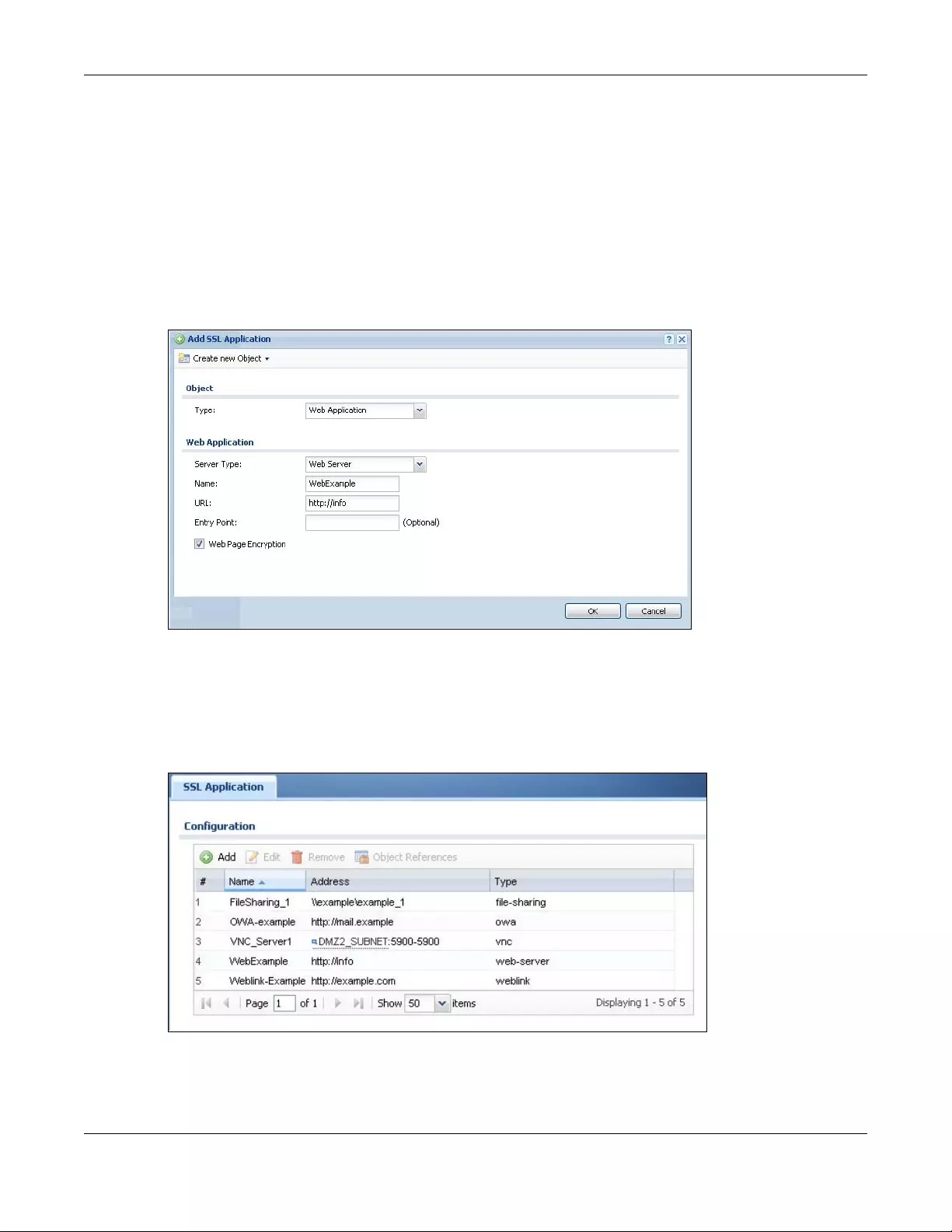
Chapter 43 Object
USG/ZyWALL User’s Guide
824
2Click the Add button and select Web Application in the Type field.
In the Server Type field, select Web Server.
Enter a descriptive name in the Display Name field. For example, “CompanyIntranet”.
In the URL Address field, enter “http://my-info”.
Select Web Page Encryption to prevent users from saving the web content.
Click OK to save the settings.
The configuration screen should look similar to the following figure.
Figure 581 Example: SSL Application: Specifying a Web Site for Access
43.13.2 The SSL Application Screen
The main SSL Application screen displays a list of the configured SSL application objects. Click
Configuration > Object > SSL Application in the navigation panel.
Figure 582 Configuration > Object > SSL Application
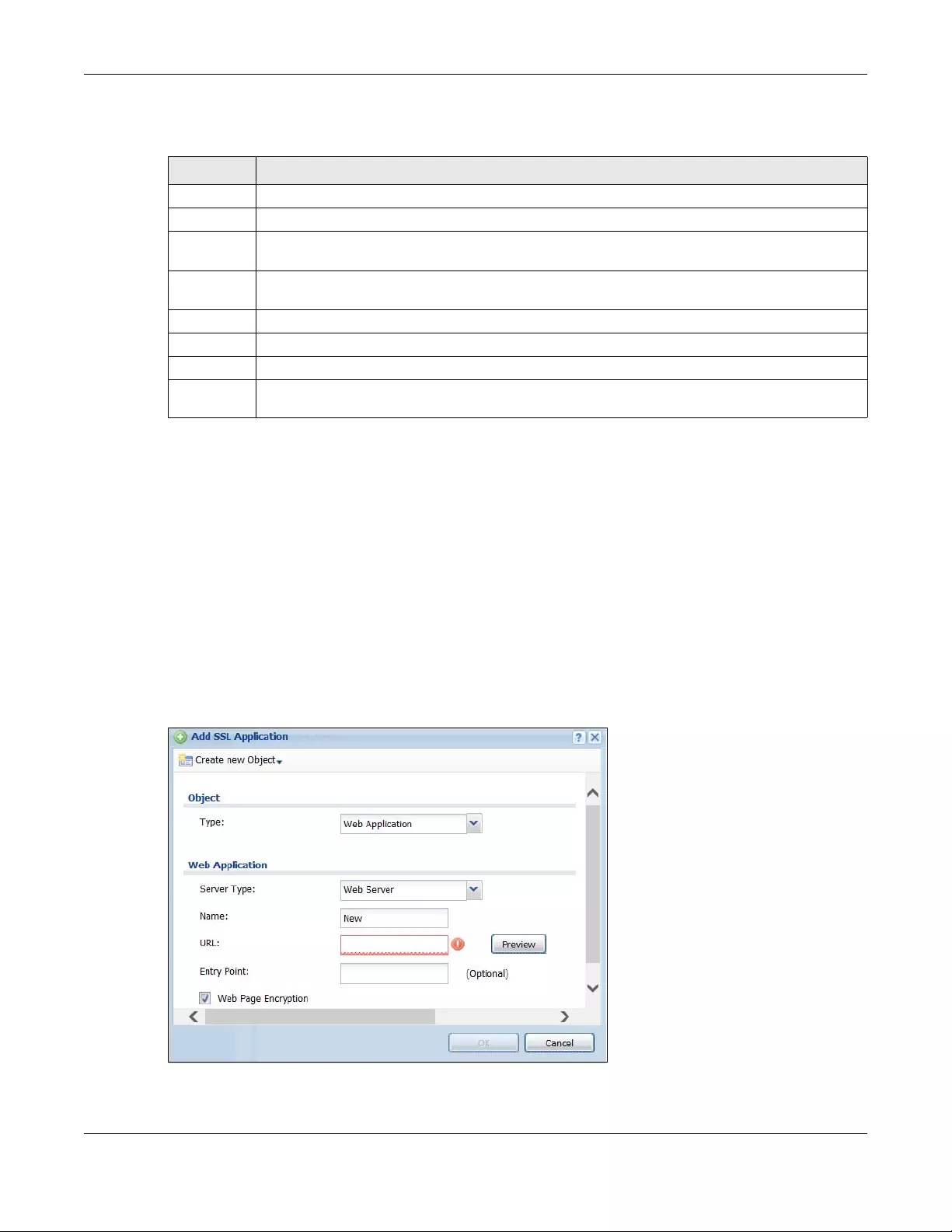
Chapter 43 Object
USG/ZyWALL User’s Guide
825
The following table describes the labels in this screen.
43.13.2.1 Creating/Editing an SSL Application Object
You can create a web-based application that allows remote users to access an application via
standard web browsers. You can also create a file sharing application that specify the name of a folder
on a file server (Linux or Windows) which remote users can access. Remote users can access files using a
standard web browser and files are displayed as links on the screen.
To configure an SSL application, click the Add or Edit button in the SSL Application screen and select
Web Application or File Sharing in the Type field. The screen differs depending on what object type you
choose.
Note: If you are creating a file sharing SSL application, you must also configure the shared
folder on the file server for remote access. Refer to the document that comes with your
file server.
Figure 583 Configuration > Object > SSL Application > Add/Edit: Web Application
Table 341 Configuration > Object > SSL Application
LABEL DESCRIPTION
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove it
before doing so.
Object
References
Select an entry and click Object References to open a screen that shows which settings use the
entry.
# This field displays the index number.
Name This field displays the name of the object.
Address This field displays the IP address/URL of the application server or the location of a file share.
Type This field shows whether the object is a file-sharing, web-server, Outlook Web Access, Virtual Network
Computing, or Remote Desktop Protocol SSL application.
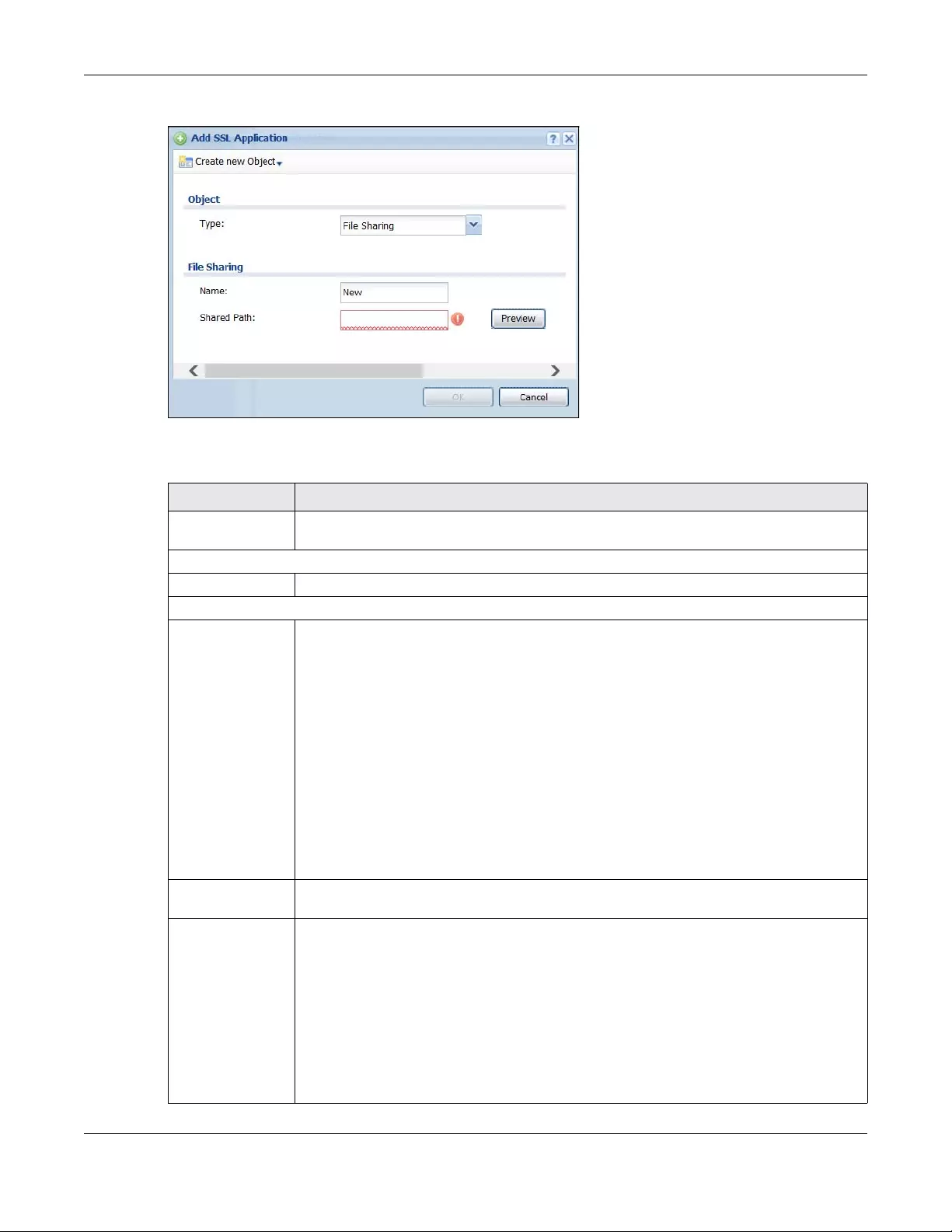
Chapter 43 Object
USG/ZyWALL User’s Guide
826
Figure 584 Configuration > Object > SSL Application > Add/Edit: File Sharing
The following table describes the labels in this screen.
Table 342 Configuration > Object > SSL Application > Add/Edit: Web Application/File Sharing
LABEL DESCRIPTION
Create new
Object
Use this to configure any new settings objects that you need to use in this screen.
Object
Type Select Web Application or File Sharing from the drop-down list box.
Web Application
Server Type This field only appears when you choose Web Application as the object type.
Specify the type of service for this SSL application.
Select Web Server to allow access to the specified web site hosted on the local network.
Select OWA (Outlook Web Access) to allow users to access e-mails, contacts, calenders via
Microsoft Outlook-like interface using supported web browsers. The Zyxel Device supports one
OWA object.
Select VNC to allow users to manage LAN computers that have Virtual Network Computing
remote desktop server software installed.
Select RDP to allow users to manage LAN computers that have Remote Desktop Protocol
remote desktop server software installed.
Select Weblink to create a link to a web site that you expect the SSL VPN users to commonly
use.
Name Enter a descriptive name to identify this object. You can enter up to 31 characters (“0-9”, “a-
z”, “A-Z”, “-” and “_”). Spaces are not allowed.
URL This field only appears when you choose Web Application as the object type.
This field displays if the Server Type is set to Web Server, OWA, or Weblink.
Enter the Fully-Qualified Domain Name (FQDN) or IP address of the application server.
Note: You must enter the “http://” or “https://” prefix.
Remote users are restricted to access only files in this directory. For example, if you enter
“\remote\” in this field, remote users can only access files in the “remote” directory.
If a link contains a file that is not within this domain, then remote users cannot access it.
Chapter 43 Object
USG/ZyWALL User’s Guide
827
43.14 DHCPv6 Overview
This section describes how to configure DHCPv6 request type and lease type objects.
• The Request screen (see Section 43.14.1 on page 827) allows you to configure DHCPv6 request type
objects.
• The Lease screen (see Section 43.2.3 on page 741) allows you to configure DHCPv6 lease type
objects.
43.14.1 The DHCPv6 Request Screen
The Request screen allows you to add, edit, and remove DHCPv6 request type objects. To access this
screen, login to the Web Configurator, and click Configuration > Object > DHCPv6 > Request.
Preview This field only appears when you choose Web Application or File Sharing as the object type.
This field displays if the Server Type is set to Web Server, OWA or Weblink.
Note: If your Internet Explorer or other browser screen doesn’t show a preview, it may be due
to your web browser security settings. You need to add the Zyxel Device’s IP address in
the trusted sites of your web browser. For example, in Internet Explorer, click Tools >
Internet Options > Security > Trusted Sites > Sites and type the Zyxel Device’s IP
address, then click Add. For other web browsers, please check the browser help.
Click Preview to access the URL you specified in a new web browser screen.
Entry Point This field only appears when you choose Web Application as the object type.
This field displays if the Server Type is set to Web Server or OWA.
This field is optional. You only need to configure this field if you need to specify the name of
the directory or file on the local server as the home page or home directory on the user
screen.
Web Page
Encryption
This field only appears when you choose Web Application as the object type.
Select this option to prevent users from saving the web content.
Shared Path This field only appears when you choose File Sharing as the object type.
Specify the IP address, domain name or NetBIOS name (computer name) of the file server
and the name of the share to which you want to allow user access. Enter the path in one of
the following formats.
“\\<IP address>\<share name>”
“\\<domain name>\<share name>”
“\\<computer name>\<share name>”
For example, if you enter “\\my-server\Tmp”, this allows remote users to access all files and/
or folders in the “\Tmp” share on the “my-server” computer.
OK Click OK to save the changes and return to the main SSL Application Configuration screen.
Cancel Click Cancel to discard the changes and return to the main SSL Application Configuration
screen.
Table 342 Configuration > Object > SSL Application > Add/Edit: Web Application/File Sharing
LABEL DESCRIPTION
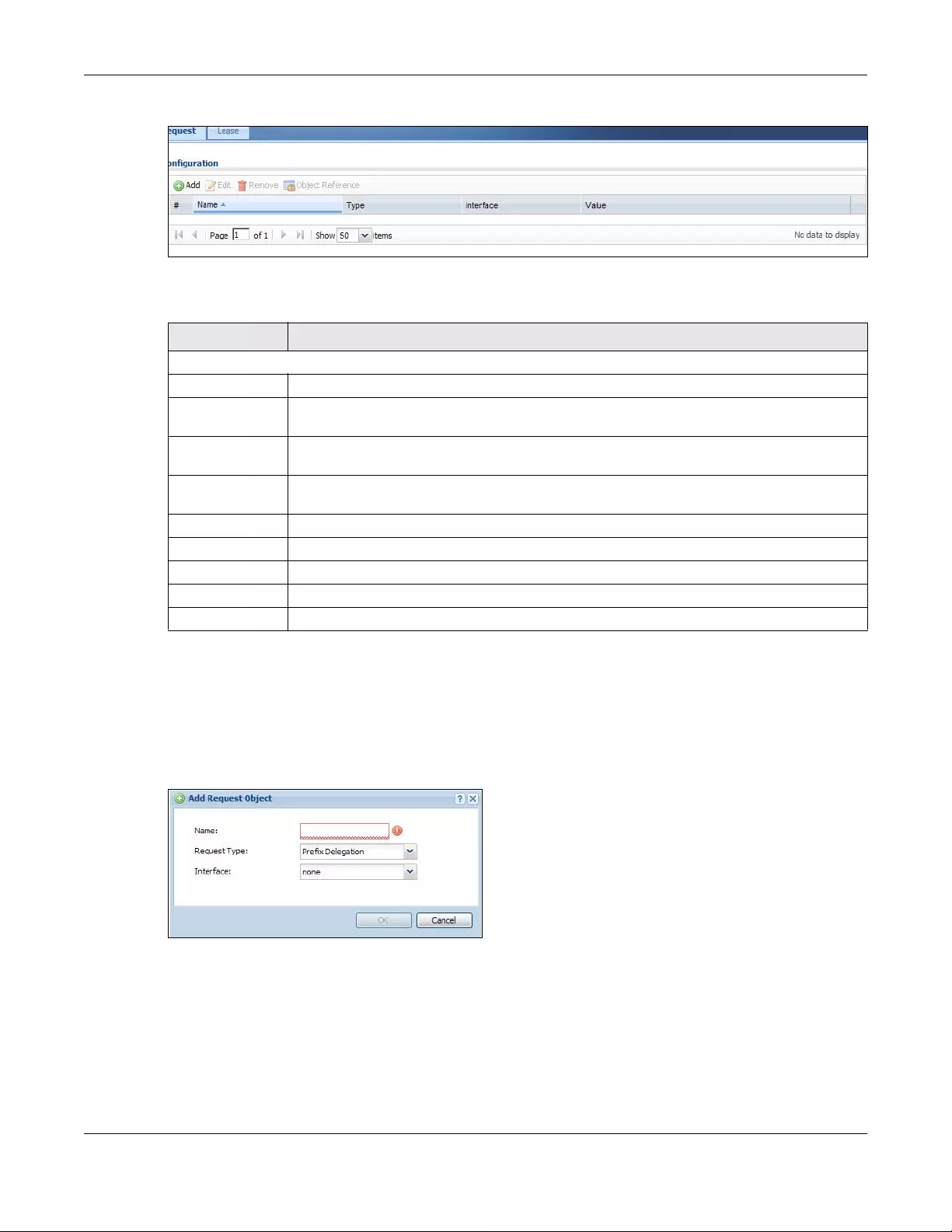
Chapter 43 Object
USG/ZyWALL User’s Guide
828
Figure 585 Configuration > Object > DHCPv6 > Request
The following table describes the labels in this screen.
43.14.1.1 DHCPv6 Request Add/Edit Screen
The Request Add/Edit screen allows you to create a new request object or edit an existing one.
To access this screen, go to the Request screen (see Section 43.14.1 on page 827), and click either the
Add icon or an Edit icon.
Figure 586 Configuration > DHCPv6 > Request > Add
Table 343 Configuration > Object > DHCPv6 > Request
LABEL DESCRIPTION
Configuration
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Object
References
Select an entry and click Object References to open a screen that shows which settings use
the entry.
# This field is a sequential value, and it is not associated with a specific object.
Name This field displays the name of each request object.
Type This field displays the request type of each request object.
Interface This field displays the interface used for each request object.
Value This field displays the value for each request object.
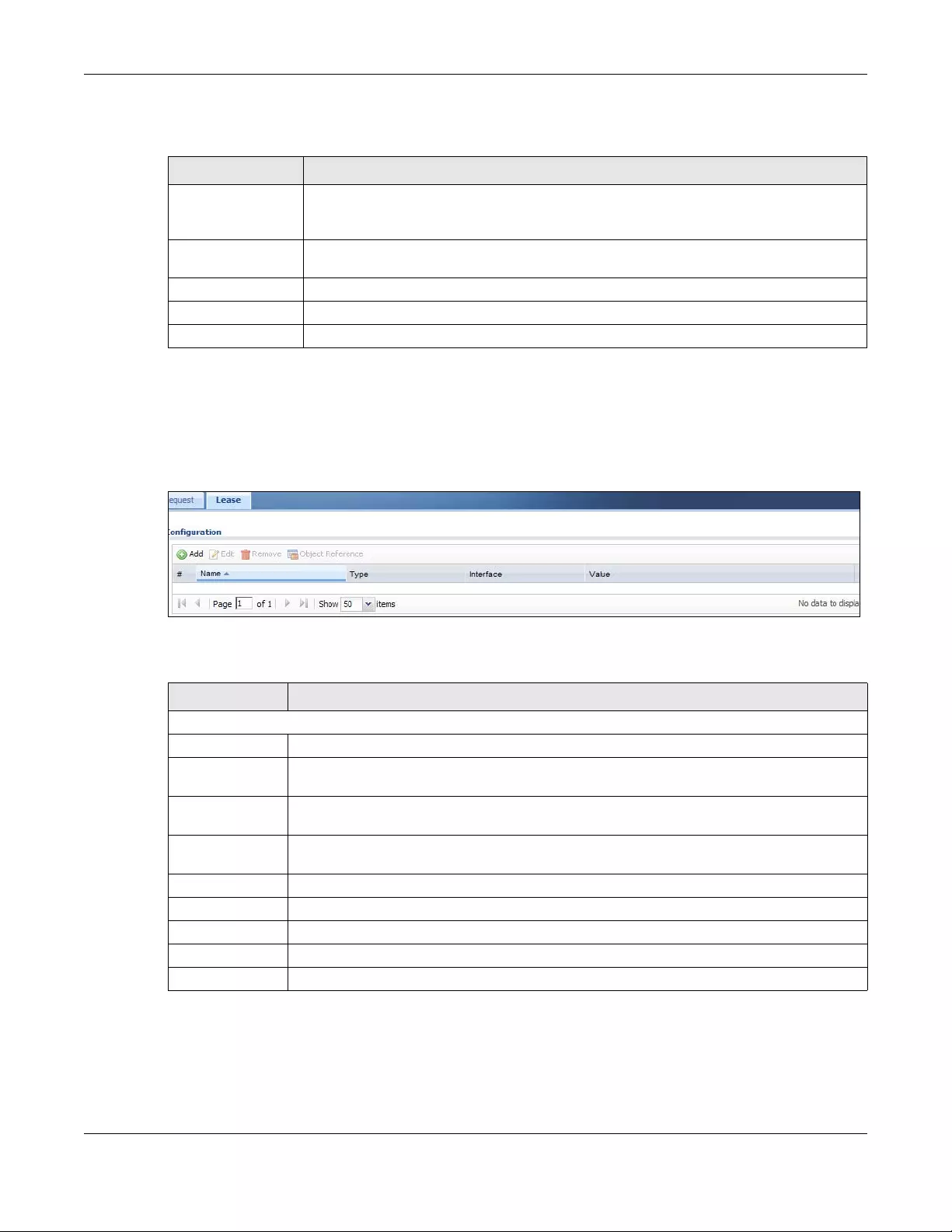
Chapter 43 Object
USG/ZyWALL User’s Guide
829
The following table describes the labels in this screen.
43.14.2 The DHCPv6 Lease Screen
The Lease screen allows you to add, edit, and remove DHCPv6 lease type objects. To access this screen,
login to the Web Configurator, and click Configuration > Object > DHCPv6 > Lease.
Figure 587 Configuration > Object > DHCPv6 > Lease
The following table describes the labels in this screen.
43.14.2.1 DHCPv6 Lease Add/Edit Screen
The Lease Add/Edit screen allows you to create a new lease object or edit an existing one.
To access this screen, go to the Lease screen (see Section 43.14.2 on page 829), and click either the
Add icon or an Edit icon.
Table 344 Configuration > DHCPv6 > Request > Add
LABEL DESCRIPTION
Name Type the name for this request object. You may use 1-31 alphanumeric characters,
underscores(_), or dashes (-), but the first character cannot be a number. This value is case-
sensitive.
Request Type Select the request type for this request object. You can choose from Prefix Delegation, DNS
Server, NTP Server, or SIP Server.
Interface Select the interface for this request object.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.
Table 345 Configuration > Object > DHCPv6 > Lease
LABEL DESCRIPTION
Configuration
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to open a screen where you can modify the
entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so.
Object
References
Select an entry and click Object References to open a screen that shows which settings use
the entry.
# This field is a sequential value, and it is not associated with a specific object.
Name This field displays the name of each lease object.
Type This field displays the request type of each lease object.
Interface This field displays the interface used for each lease object.
Value This field displays the value for each lease object.
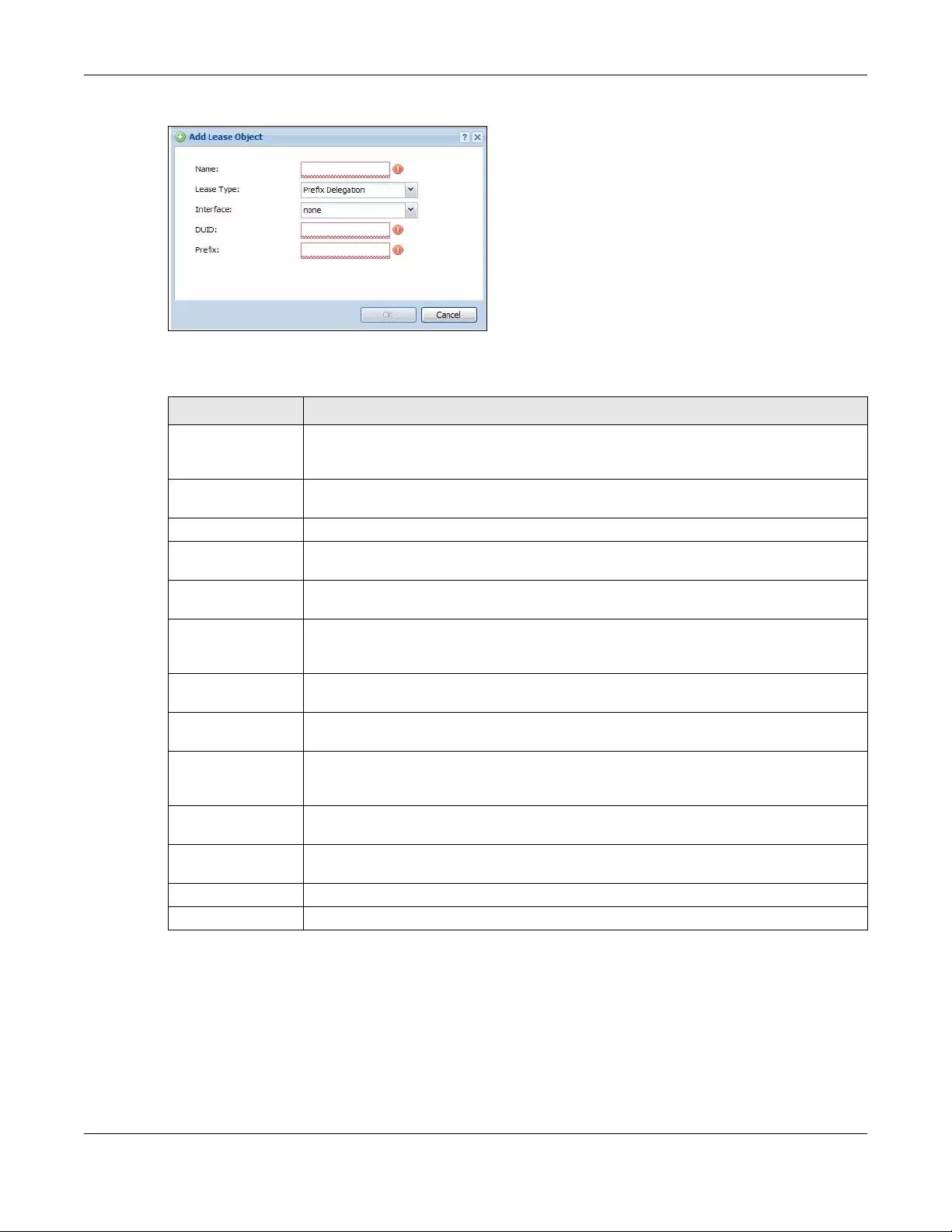
Chapter 43 Object
USG/ZyWALL User’s Guide
830
Figure 588 Configuration > DHCPv6 > Lease > Add
The following table describes the labels in this screen.
Table 346 Configuration > DHCPv6 > Lease > Add/Edit
LABEL DESCRIPTION
Name Type the name for this lease object. You may use 1-31 alphanumeric characters,
underscores(_), or dashes (-), but the first character cannot be a number. This value is case-
sensitive.
Lease Type Select the lease type for this lease object. You can choose from Prefix Delegation, DNS
Server, Address, Address Pool, NTP Server, or SIP Server.
Interface Select the interface for this lease object.
DUID If you select Prefix Delegation or Address in the Lease Type field, enter the DUID of the
interface.
Prefix If you select Prefix Delegation or Address in the Lease Type field, enter the IPv6 prefix of the
interface.
DNS Server If you select DNS Server in the Lease Type field, select a request object or User Defined in the
DNS Server field and enter the IP address of the DNS server in the User Defined Address field
below.
Starting IP Address If you select Address Pool in the Lease Type field, enter the first of the contiguous addresses
in the IP address pool.
End IP Address If you select Address Pool in the Lease Type field, enter the last of the contiguous addresses
in the IP address pool.
NTP Server If you select NTP Server in the Lease Type field, select a request object or User Defined in the
NTP Server field and enter the IP address of the NTP server in the User Defined Address field
below.
SIP Server If you select SIP Server in the Lease Type field, select a request object or User Defined in the
SIP field and enter the IP address of the SIP server in the User Defined Address field below.
User Defined
Address
If you select DNS Server, NTP Server, or SIP Server as your lease type, you must enter the IP
address of the server your selected.
OK Click OK to save your changes back to the Zyxel Device.
Cancel Click Cancel to exit this screen without saving your changes.

USG/ZyWALL User’s Guide
831
CHAPTER 44
System
44.1 Overview
Use the system screens to configure general Zyxel Device settings.
44.1.1 What You Can Do in this Chapter
• Use the System > Host Name screen (see Section 44.2 on page 832) to configure a unique name for
the Zyxel Device in your network.
• Use the System > USB Storage screen (see Section 44.3 on page 832) to configure the settings for the
connected USB devices.
• Use the System > Date/Time screen (see Section 44.4 on page 833) to configure the date and time for
the Zyxel Device.
• Use the System > Console Speed screen (see Section 44.5 on page 837) to configure the console port
speed when you connect to the Zyxel Device via the console port using a terminal emulation
program.
• Use the System > DNS screen (see Section 44.6 on page 838) to configure the DNS (Domain Name
System) server used for mapping a domain name to its corresponding IP address and vice versa.
• Use the System > WWW screens (see Section 44.7 on page 847) to configure settings for HTTP or HTTPS
access to the Zyxel Device and how the login and access user screens look.
• Use the System > SSH screen (see Section 44.8 on page 865) to configure SSH (Secure SHell) used to
securely access the Zyxel Device’s command line interface. You can specify which zones allow SSH
access and from which IP address the access can come.
• Use the System > TELNET screen (see Section 44.9 on page 870) to configure Telnet to access the Zyxel
Device’s command line interface. Specify which zones allow Telnet access and from which IP address
the access can come.
• Use the System > FTP screen (see Section 44.10 on page 871) to specify from which zones FTP can be
used to access the Zyxel Device. You can also specify from which IP addresses the access can come.
You can upload and download the Zyxel Device’s firmware and configuration files using FTP.
• Your Zyxel Device can act as an SNMP agent, which allows a manager station to manage and
monitor the Zyxel Device through the network. Use the System > SNMP screen (see Section 44.11 on
page 872) to configure SNMP settings, including from which zones SNMP can be used to access the
Zyxel Device. You can also specify from which IP addresses the access can come.
• Use the Auth. Server screen (Section 44.12 on page 877) to configure the Zyxel Device to operate as a
RADIUS server.
• Use the System > Language screen (see Section 44.13 on page 879) to set a language for the Zyxel
Device’s Web Configurator screens.
• Use the System > IPv6 screen (see Section 44.14 on page 880) to enable or disable IPv6 support on the
Zyxel Device.
• Use the System > ZON screen (see Section 44.15 on page 880) to enable or disable the Zyxel One
Network (ZON) utility that uses Zyxel Discovery Protocol (ZDP) for discovering and configuring ZDP-
aware Zyxel devices in the same network as the computer on which ZON is installed.
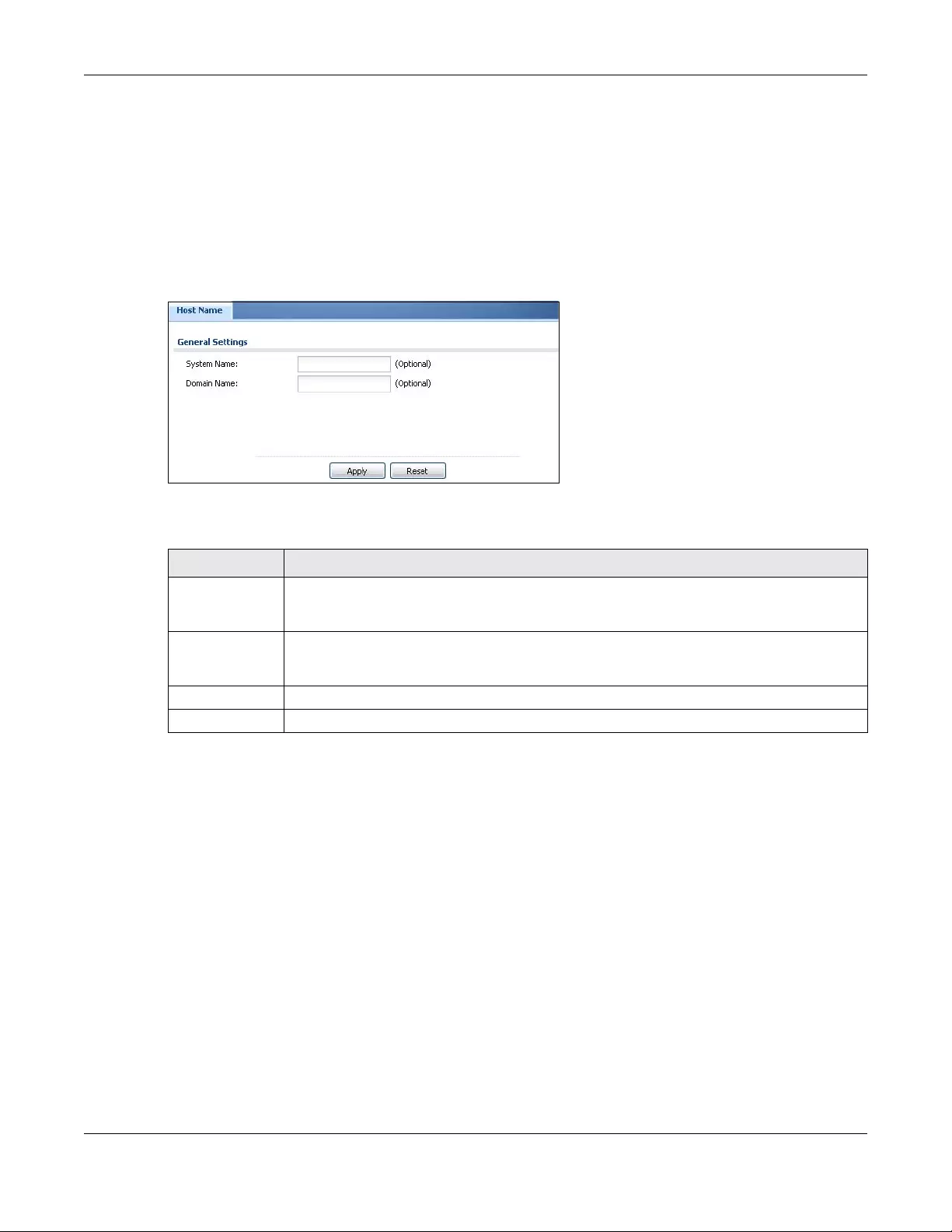
Chapter 44 System
USG/ZyWALL User’s Guide
832
Note: See each section for related background information and term definitions.
44.2 Host Name
A host name is the unique name by which a device is known on a network. Click Configuration > System
> Host Name to open the Host Name screen.
Figure 589 Configuration > System > Host Name
The following table describes the labels in this screen.
44.3 USB Storage
The Zyxel Device can use a connected USB device to store system logs and diagnostic information.
Note: The USB device must allow writing (it cannot be read-only) and use the FAT16, FAT32,
EXT2, or EXT3 file system.
For Zyxel Devices that have more than one USB port, these configurations only apply to
the first USB storage device that is attached to the Zyxel Device.
Use this screen to turn on this feature, set a disk full warning limit.
Click Configuration > System > USB Storage to open the screen as shown next.
Table 347 Configuration > System > Host Name
LABEL DESCRIPTION
System Name Enter a descriptive name to identify your Zyxel Device device. This name can be up to 64
alphanumeric characters long. Spaces are not allowed, but dashes (-) underscores (_) and
periods (.) are accepted.
Domain Name Enter the domain name (if you know it) here. This name is propagated to DHCP clients
connected to interfaces with the DHCP server enabled. This name can be up to 254
alphanumeric characters long. Spaces are not allowed, but dashes “-” are accepted.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
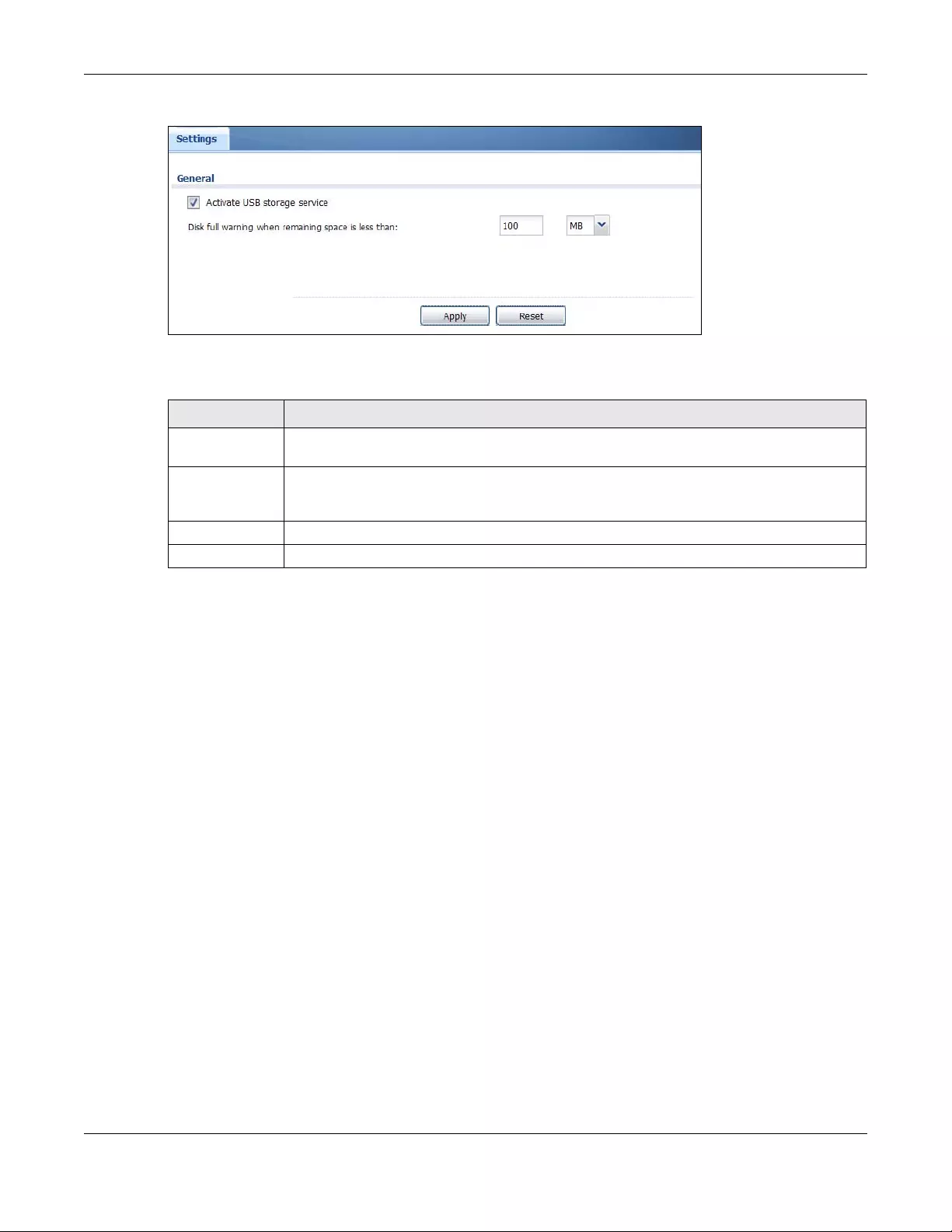
Chapter 44 System
USG/ZyWALL User’s Guide
833
Figure 590 Configuration > System > USB Storage
The following table describes the labels in this screen.
44.4 Date and Time
For effective scheduling and logging, the Zyxel Device system time must be accurate. The Zyxel
Device’s Real Time Chip (RTC) keeps track of the time and date. There is also a software mechanism to
set the time manually or get the current time and date from an external server.
To change your Zyxel Device’s time based on your local time zone and date, click Configuration >
System > Date/Time. The screen displays as shown. You can manually set the Zyxel Device’s time and
date or have the Zyxel Device get the date and time from a time server.
Table 348 Configuration > System > USB Storage
LABEL DESCRIPTION
Activate USB
storage service
Select this if you want to use the connected USB device(s).
Disk full warning
when remaining
space is less than
Set a number and select a unit (MB or %) to have the Zyxel Device send a warning message
when the remaining USB storage space is less than the value you set here.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
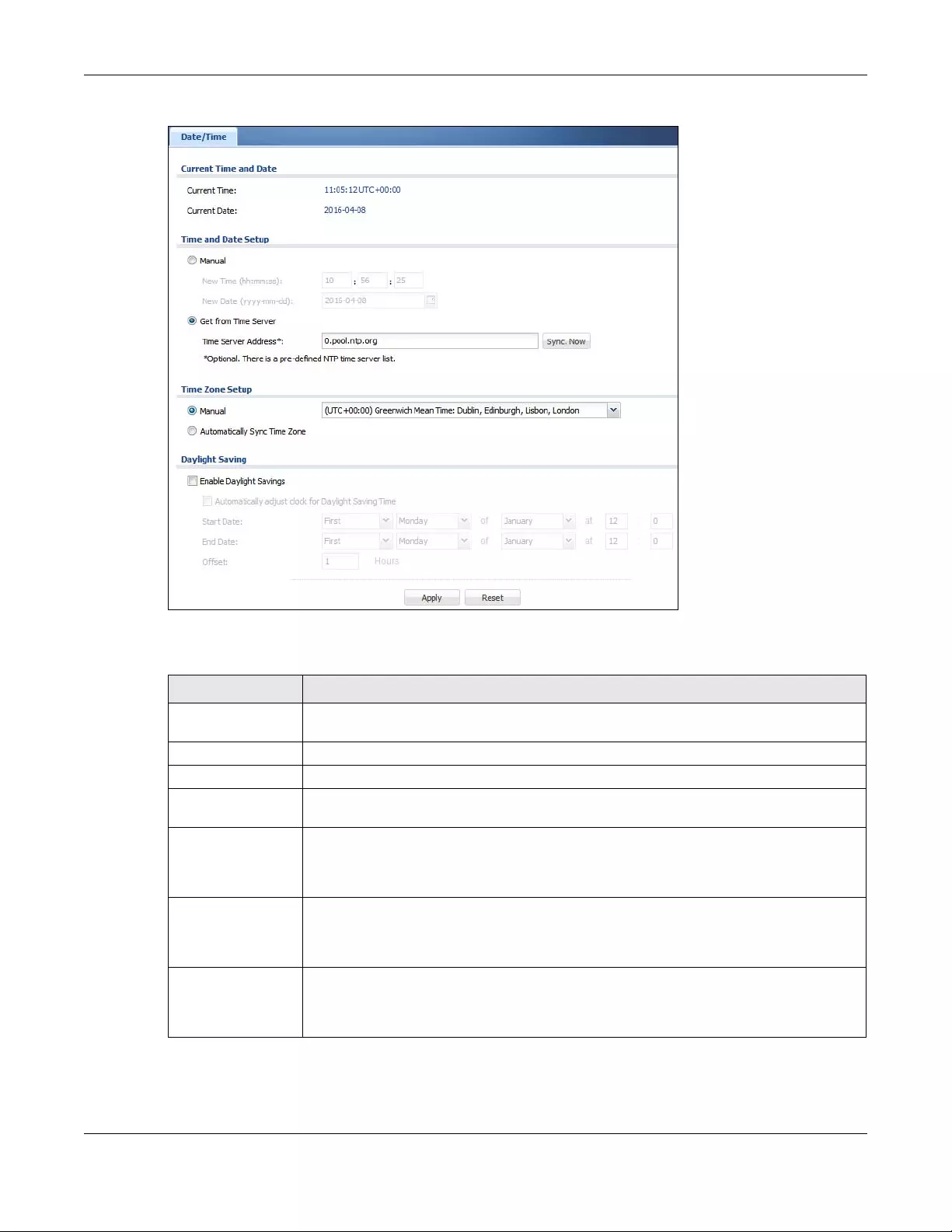
Chapter 44 System
USG/ZyWALL User’s Guide
834
Figure 591 Configuration > System > Date and Time
The following table describes the labels in this screen.
Table 349 Configuration > System > Date and Time
LABEL DESCRIPTION
Current Time and
Date
Current Time This field displays the present time of your Zyxel Device.
Current Date This field displays the present date of your Zyxel Device.
Time and Date
Setup
Manual Select this radio button to enter the time and date manually. If you configure a new time
and date, time zone and daylight saving at the same time, the time zone and daylight
saving will affect the new time and date you entered. When you enter the time settings
manually, the Zyxel Device uses the new setting once you click Apply.
New Time (hh-mm-
ss)
This field displays the last updated time from the time server or the last time configured
manually.
When you set Time and Date Setup to Manual, enter the new time in this field and then click
Apply.
New Date (yyyy-
mm-dd)
This field displays the last updated date from the time server or the last date configured
manually.
When you set Time and Date Setup to Manual, enter the new date in this field and then click
Apply.
Chapter 44 System
USG/ZyWALL User’s Guide
835
Get from Time
Server
Select this radio button to have the Zyxel Device get the time and date from the time server
you specify below. The Zyxel Device requests time and date settings from the time server
under the following circumstances.
• When the Zyxel Device starts up.
• When you click Apply or Synchronize Now in this screen.
• 24-hour intervals after starting up.
Time Server Address Enter the IP address or URL of your time server. Check with your ISP/network administrator if
you are unsure of this information.
Sync. Now Click this button to have the Zyxel Device get the time and date from a time server (see the
Time Server Address field). This also saves your changes (except the daylight saving
settings).
Time Zone Setup
Time Zone Choose the time zone of your location. This will set the time difference between your time
zone and Greenwich Mean Time (GMT).
Automatically Sync
Time Zone
Select this for the Zyxel Device to automatically get its time zone.
Daylight Saving
Enable Daylight
Savings
Daylight savings is a period from late spring to early fall when many countries set their clocks
ahead of normal local time by one hour to give more daytime light in the evening.
Select this option if you use Daylight Saving Time.
Automatically
adjust clock for
Daylight Saving
Time
Select this for the Zyxel Device to automatically adjust the time if daylight savings is
implemented in its time zone.
Start Date Configure the day and time when Daylight Saving Time starts if you selected Enable Daylight
Saving. The at field uses the 24 hour format. Here are a couple of examples:
Daylight Saving Time starts in most parts of the United States on the second Sunday of
March. Each time zone in the United States starts using Daylight Saving Time at 2 A.M. local
time. So in the United States you would select Second, Sunday, March and type 2 in the at
field.
Daylight Saving Time starts in the European Union on the last Sunday of March. All of the time
zones in the European Union start using Daylight Saving Time at the same moment (1 A.M.
GMT or UTC). So in the European Union you would select Last, Sunday, March. The time you
type in the at field depends on your time zone. In Germany for instance, you would type 2
because Germany's time zone is one hour ahead of GMT or UTC (GMT+1).
End Date Configure the day and time when Daylight Saving Time ends if you selected Enable Daylight
Saving. The at field uses the 24 hour format. Here are a couple of examples:
Daylight Saving Time ends in the United States on the first Sunday of November. Each time
zone in the United States stops using Daylight Saving Time at 2 A.M. local time. So in the
United States you would select First, Sunday, November and type 2 in the at field.
Daylight Saving Time ends in the European Union on the last Sunday of October. All of the
time zones in the European Union stop using Daylight Saving Time at the same moment (1
A.M. GMT or UTC). So in the European Union you would select Last, Sunday, October. The
time you type in the at field depends on your time zone. In Germany for instance, you would
type 2 because Germany's time zone is one hour ahead of GMT or UTC (GMT+1).
Offset Specify how much the clock changes when daylight saving begins and ends.
Enter a number from 1 to 5.5 (by 0.5 increments).
For example, if you set this field to 3.5, a log occurred at 6 P.M. in local official time will
appear as if it had occurred at 10:30 P.M.
Table 349 Configuration > System > Date and Time (continued)
LABEL DESCRIPTION
Chapter 44 System
USG/ZyWALL User’s Guide
836
44.4.1 Pre-defined NTP Time Servers List
When you turn on the Zyxel Device for the first time, the date and time start at 2003-01-01 00:00:00. The
Zyxel Device then attempts to synchronize with one of the following pre-defined list of Network Time
Protocol (NTP) time servers.
The Zyxel Device continues to use the following pre-defined list of NTP time servers if you do not specify a
time server or it cannot synchronize with the time server you specified.
When the Zyxel Device uses the pre-defined list of NTP time servers, it randomly selects one server and
tries to synchronize with it. If the synchronization fails, then the Zyxel Device goes through the rest of the
list in order from the first one tried until either it is successful or all the pre-defined NTP time servers have
been tried.
44.4.2 Time Server Synchronization
Click the Synchronize Now button to get the time and date from the time server you specified in the
Time Server Address field.
When the Please Wait... screen appears, you may have to wait up to one minute.
Figure 592 Synchronization in Process
The Current Time and Current Date fields will display the appropriate settings if the synchronization is
successful.
If the synchronization was not successful, a log displays in the View Log screen. Try re-configuring the
Date/Time screen.
To manually set the Zyxel Device date and time.
1Click System > Date/Time.
2Select Manual under Time and Date Setup.
3Enter the Zyxel Device’s time in the New Time field.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 349 Configuration > System > Date and Time (continued)
LABEL DESCRIPTION
Table 350 Default Time Servers
0.pool.ntp.org
1.pool.ntp.org
2.pool.ntp.org
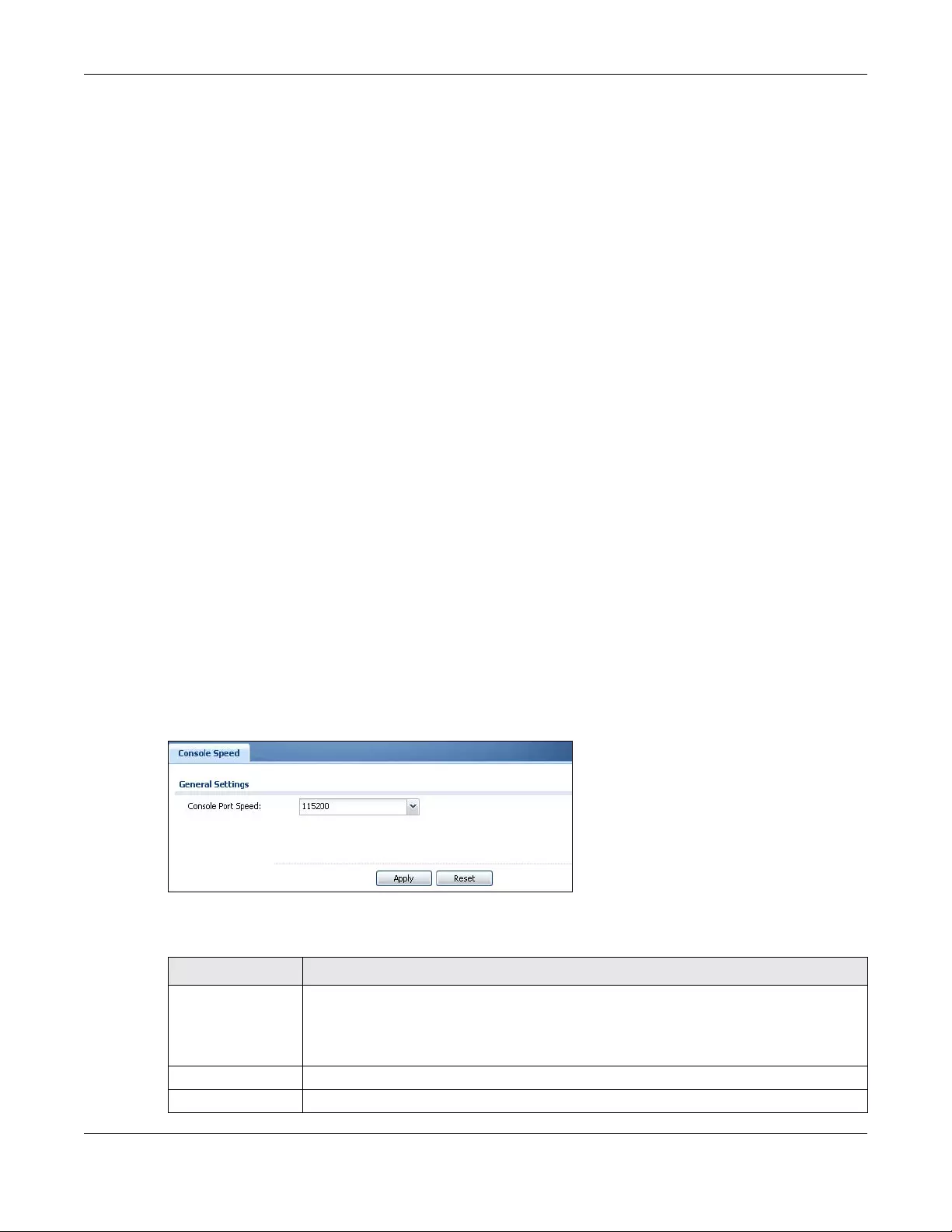
Chapter 44 System
USG/ZyWALL User’s Guide
837
4Enter the Zyxel Device’s date in the New Date field.
5Under Time Zone Setup, select your Time Zone from the list.
6As an option you can select the Enable Daylight Saving check box to adjust the Zyxel Device clock for
daylight savings.
7Click Apply.
To get the Zyxel Device date and time from a time server
1Click System > Date/Time.
2Select Get from Time Server under Time and Date Setup.
3Under Time Zone Setup, select your Time Zone from the list.
4As an option you can select the Enable Daylight Saving check box to adjust the Zyxel Device clock for
daylight savings.
5Under Time and Date Setup, enter a Time Server Address (Table 350 on page 836).
6Click Apply.
44.5 Console Port Speed
This section shows you how to set the console port speed when you connect to the Zyxel Device via the
console port using a terminal emulation program.
Click Configuration > System > Console Speed to open the Console Speed screen.
Figure 593 Configuration > System > Console Speed
The following table describes the labels in this screen.
Table 351 Configuration > System > Console Speed
LABEL DESCRIPTION
Console Port Speed Use the drop-down list box to change the speed of the console port. Your Zyxel Device
supports 9600, 19200, 38400, 57600, and 115200 bps (default) for the console port.
The Console Port Speed applies to a console port connection using terminal emulation
software and NOT the Console in the Zyxel Device Web Configurator Status screen.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Chapter 44 System
USG/ZyWALL User’s Guide
838
44.6 DNS Overview
DNS (Domain Name System) is for mapping a domain name to its corresponding IP address and vice
versa. The DNS server is extremely important because without it, you must know the IP address of a
machine before you can access it.
44.6.1 DNS Server Address Assignment
The Zyxel Device can get the DNS server addresses in the following ways.
• The ISP tells you the DNS server addresses, usually in the form of an information sheet, when you sign
up. If your ISP gives you DNS server addresses, manually enter them in the DNS server fields.
• If your ISP dynamically assigns the DNS server IP addresses (along with the Zyxel Device’s WAN IP
address), set the DNS server fields to get the DNS server address from the ISP.
• You can manually enter the IP addresses of other DNS servers.
44.6.2 Configuring the DNS Screen
Click Configuration > System > DNS to change your Zyxel Device’s DNS settings. Use the DNS screen to
configure the Zyxel Device to use a DNS server to resolve domain names for Zyxel Device system
features like VPN, DDNS and the time server. You can also configure the Zyxel Device to accept or
discard DNS queries. Use the Network > Interface screens to configure the DNS server information that
the Zyxel Device sends to the specified DHCP client devices.
A name query begins at a client computer and is passed to a resolver, a DNS client service, for
resolution. The Zyxel Device can be a DNS client service. The Zyxel Device can resolve a DNS query
locally using cached Resource Records (RR) obtained from a previous query (and kept for a period of
time). If the Zyxel Device does not have the requested information, it can forward the request to DNS
servers. This is known as recursion.
The Zyxel Device can ask a DNS server to use recursion to resolve its DNS client requests. If recursion on
the Zyxel Device or a DNS server is disabled, they cannot forward DNS requests for resolution.
A Domain Name Server (DNS) amplification attack is a kind of Distributed Denial of Service (DDoS)
attack that uses publicly accessible open DNS servers to flood a victim with DNS response traffic. An
open DNS server is a DNS server which is willing to resolve recursive DNS queries from anyone on the
Internet.
In a DNS amplification attack, an attacker sends a DNS name lookup request to an open DNS server
with the source address spoofed as the victim’s address. When the DNS server sends the DNS record
response, it is sent to the victim. Attackers can request as much information as possible to maximize the
amplification effect.
Configure the Security Option Control section in the Configuration > System > DNS screen (click Show
Advanced Settings to display it) if you suspect the Zyxel Device is being used (either by hackers or by a
corrupted open DNS server) in a DNS amplification attack.
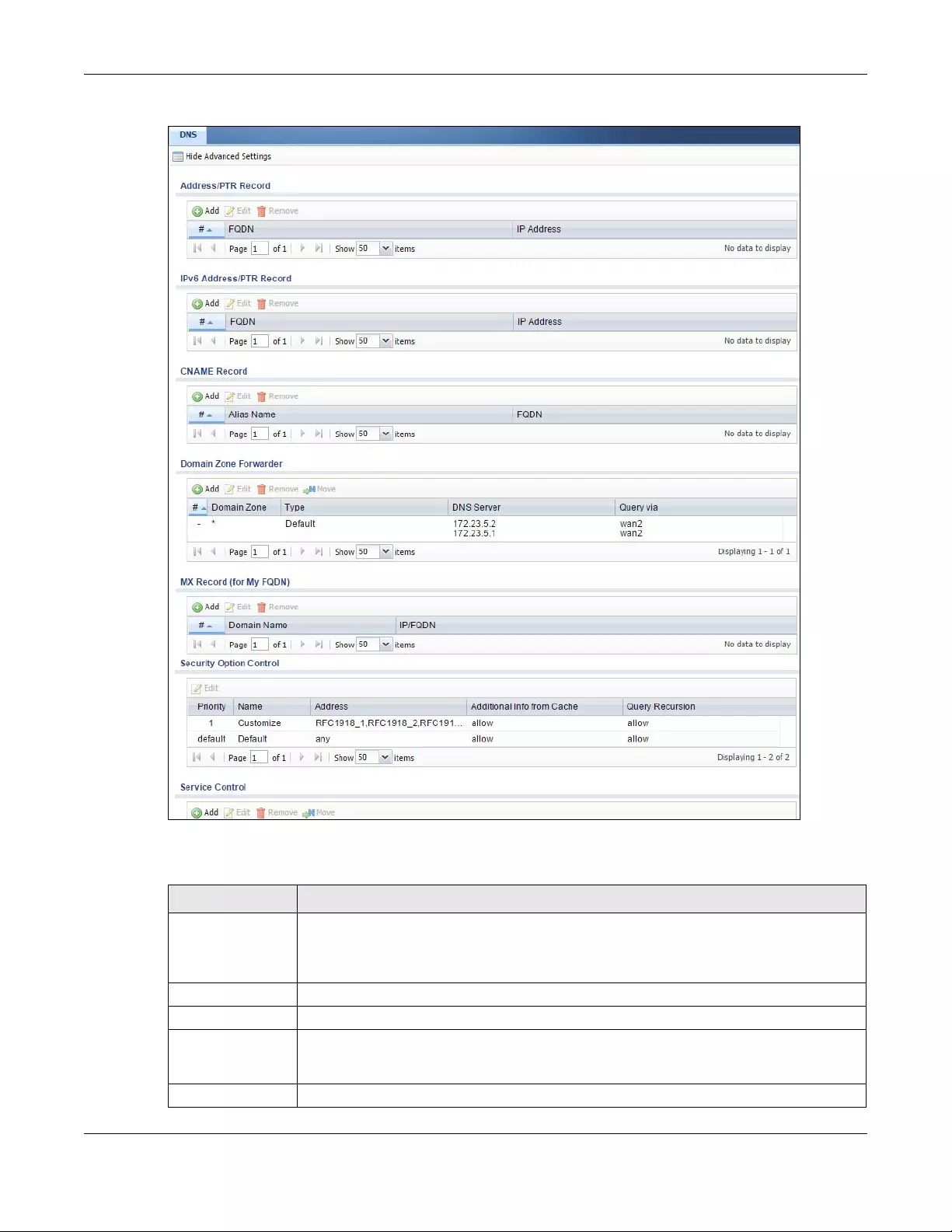
Chapter 44 System
USG/ZyWALL User’s Guide
839
Figure 594 Configuration > System > DNS
The following table describes the labels in this screen.
Table 352 Configuration > System > DNS
LABEL DESCRIPTION
Address/PTR
Record
This record specifies the mapping of a Fully-Qualified Domain Name (FQDN) to an IP address.
An FQDN consists of a host and domain name. For example, www.zyxel.com.tw is a fully
qualified domain name, where “www” is the host, “zyxel” is the third-level domain, “com” is
the second-level domain, and “tw” is the top level domain.
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so. Note that subsequent entries move up by one when you take this
action.
#This is the index number of the address/PTR record.
Chapter 44 System
USG/ZyWALL User’s Guide
840
FQDN This is a host’s fully qualified domain name.
IP Address This is the IP address of a host.
CNAME Record This record specifies an alias for a FQDN. Use this record to bind all subdomains with the same
IP address as the FQDN without having to update each one individually, which increases
chance for errors. See CNAME Record (Section 44.6.6 on page 842) for more details.
Add Click this to create a new entry.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so. Note that subsequent entries move up by one when you take this
action.
#This is the index number of the domain zone forwarder record. The ordering of your rules is
important as rules are applied in sequence.
A hyphen (-) displays for the default domain zone forwarder record. The default record is not
configurable. The Zyxel Device uses this default record if the domain zone that needs to be
resolved does not match any of the other domain zone forwarder records.
Alias Name Enter an Alias name. Use “*.” as prefix for a wildcard domain name. For example,
*.example.com.
FQDN Enter the Fully Qualified Domain Name (FQDN).
Domain Zone
Forwarder
This specifies a DNS server’s IP address. The Zyxel Device can query the DNS server to resolve
domain zones for features like VPN, DDNS and the time server.
When the Zyxel Device needs to resolve a domain zone, it checks it against the domain zone
forwarder entries in the order that they appear in this list.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after the
selected entry.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so. Note that subsequent entries move up by one when you take this
action.
Move To change an entry’s position in the numbered list, select the method and click Move to
display a field to type a number for where you want to put it and press [ENTER] to move the
rule to the number that you typed.
#This is the index number of the domain zone forwarder record. The ordering of your rules is
important as rules are applied in sequence.
A hyphen (-) displays for the default domain zone forwarder record. The default record is not
configurable. The Zyxel Device uses this default record if the domain zone that needs to be
resolved does not match any of the other domain zone forwarder records.
Domain Zone A domain zone is a fully qualified domain name without the host. For example, zyxel.com.tw
is the domain zone for the www.zyxel.com.tw fully qualified domain name.
A “*” means all domain zones.
Type This displays whether the DNS server IP address is assigned by the ISP dynamically through a
specified interface or configured manually (User-Defined).
DNS Server This is the IP address of a DNS server. This field displays N/A if you have the Zyxel Device get a
DNS server IP address from the ISP dynamically but the specified interface is not active.
Query Via This is the interface through which the Zyxel Device sends DNS queries to the entry’s DNS
server. If the Zyxel Device connects through a VPN tunnel, tunnel displays.
MX Record (for My
FQDN)
A MX (Mail eXchange) record identifies a mail server that handles the mail for a particular
domain.
Add Click this to create a new entry.
Table 352 Configuration > System > DNS (continued)
LABEL DESCRIPTION
Chapter 44 System
USG/ZyWALL User’s Guide
841
44.6.3 (IPv6) Address Record
An address record contains the mapping of a Fully-Qualified Domain Name (FQDN) to an IP address. An
FQDN consists of a host and domain name. For example, www.zyxel.com is a fully qualified domain
name, where “www” is the host, “zyxel” is the second-level domain, and “com” is the top level domain.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so. Note that subsequent entries move up by one when you take this
action.
#This is the index number of the MX record.
Domain Name This is the domain name where the mail is destined for.
IP/FQDN This is the IP address or Fully-Qualified Domain Name (FQDN) of a mail server that handles the
mail for the domain specified in the field above.
Security Option
Control
Click Show Advanced Settings to display this part of the screen. There are two control
policies: Default and Customize.
Edit Click either control policy and then click this button to change allow or deny actions for
Query Recursion and Additional Info from Cache.
Priority The Customize control policy is checked first and if an address object match is not found, the
Default control policy is checked.
Name You may change the name of the Customize control policy.
Address These are the object addresses used in the control policy. RFC1918 refers to private IP address
ranges. It can be modified in Object > Address.
Additional Info
from Cache This displays if the Zyxel Device is allowed or denied to cache Resource Records (RR)
obtained from previous DNS queries.
Query
Recursion This displays if the Zyxel Device is allowed or denied to forward DNS client requests to DNS
servers for resolution.
Service Control This specifies from which computers and zones you can send DNS queries to the Zyxel Device.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after the
selected entry.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so. Note that subsequent entries move up by one when you take this
action.
Move To change an entry’s position in the numbered list, select the method and click Move to
display a field to type a number for where you want to put it and press [ENTER] to move the
rule to the number that you typed.
#This the index number of the service control rule. The ordering of your rules is important as
rules are applied in sequence.
The entry with a hyphen (-) instead of a number is the Zyxel Device’s (non-configurable)
default policy. The Zyxel Device applies this to traffic that does not match any other
configured rule. It is not an editable rule. To apply other behavior, configure a rule that traffic
will match so the Zyxel Device will not have to use the default policy.
Zone This is the zone on the Zyxel Device the user is allowed or denied to access.
Address This is the object name of the IP address(es) with which the computer is allowed or denied to
send DNS queries.
Action This displays whether the Zyxel Device accepts DNS queries from the computer with the IP
address specified above through the specified zone (Accept) or discards them (Deny).
Table 352 Configuration > System > DNS (continued)
LABEL DESCRIPTION
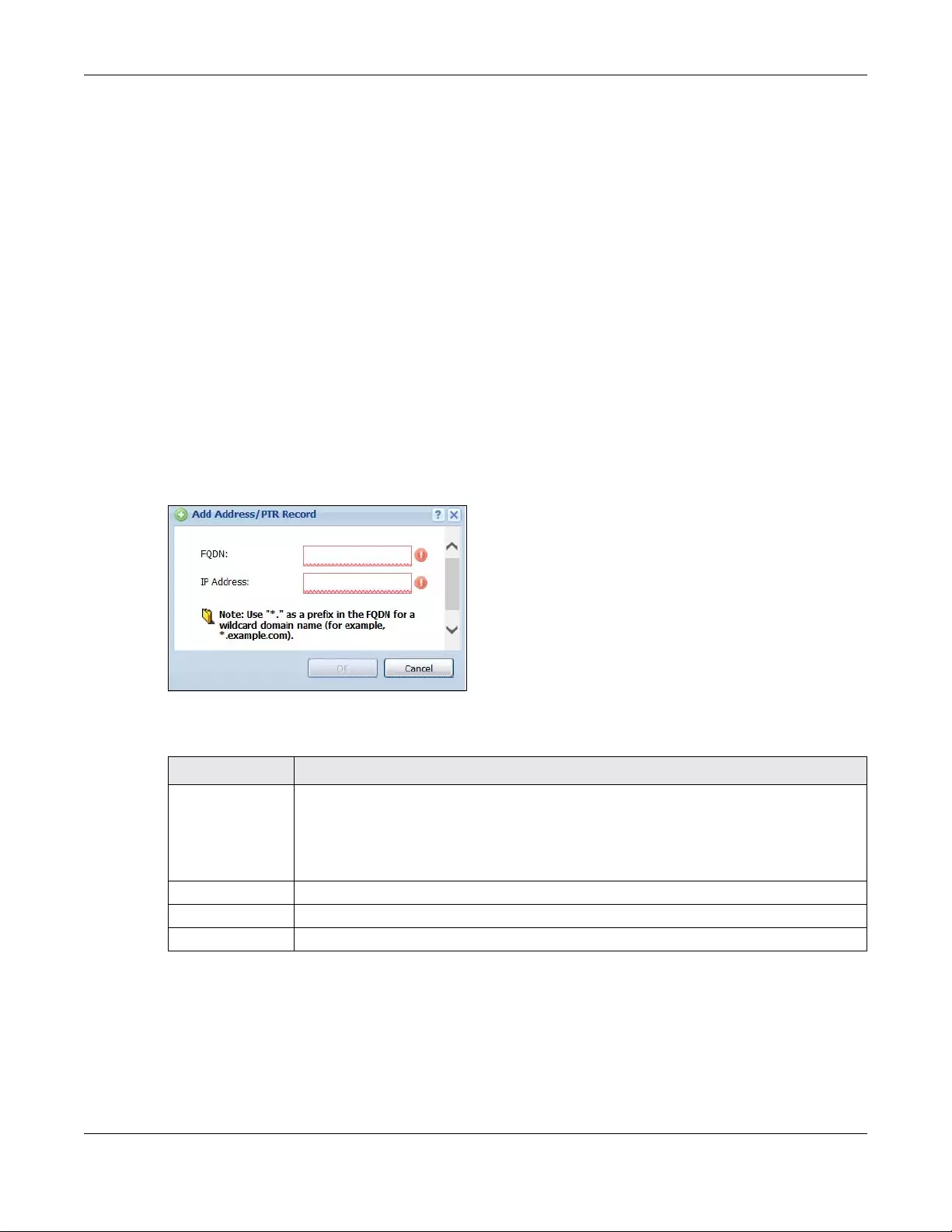
Chapter 44 System
USG/ZyWALL User’s Guide
842
mail.myZyxel.com.tw is also a FQDN, where “mail” is the host, “myZyxel” is the third-level domain, “com”
is the second-level domain, and “tw” is the top level domain.
The Zyxel Device allows you to configure address records about the Zyxel Device itself or another
device. This way you can keep a record of DNS names and addresses that people on your network may
use frequently. If the Zyxel Device receives a DNS query for an FQDN for which the Zyxel Device has an
address record, the Zyxel Device can send the IP address in a DNS response without having to query a
DNS name server.
44.6.4 PTR Record
A PTR (pointer) record is also called a reverse record or a reverse lookup record. It is a mapping of an IP
address to a domain name.
44.6.5 Adding an (IPv6) Address/PTR Record
Click the Add icon in the Address/PTR Record or IPv6 Address/PTR Record table to add an IPv4 or IPv6
address/PTR record.
Figure 595 Configuration > System > DNS > Address/PTR Record Edit
The following table describes the labels in this screen.
44.6.6 CNAME Record
A Canonical Name Record or CNAME record is a type of resource record in the Domain Name System
(DNS) that specifies that the domain name is an alias of another, canonical domain name. This allows
users to set up a record for a domain name which translates to an IP address, in other words, the domain
name is an alias of another. This record also binds all the subdomains to the same IP address without
Table 353 Configuration > System > DNS > (IPv6) Address/PTR Record Edit
LABEL DESCRIPTION
FQDN Type a Fully-Qualified Domain Name (FQDN) of a server. An FQDN starts with a host name and
continues all the way up to the top-level domain name. For example, www.zyxel.com.tw is a
fully qualified domain name, where “www” is the host, “zyxel” is the third-level domain, “com”
is the second-level domain, and “tw” is the top level domain. Underscores are not allowed.
Use "*." as a prefix in the FQDN for a wildcard domain name (for example, *.example.com).
IP Address Enter the IP address of the host in dotted decimal notation.
OK Click OK to save your customized settings and exit this screen.
Cancel Click Cancel to exit this screen without saving
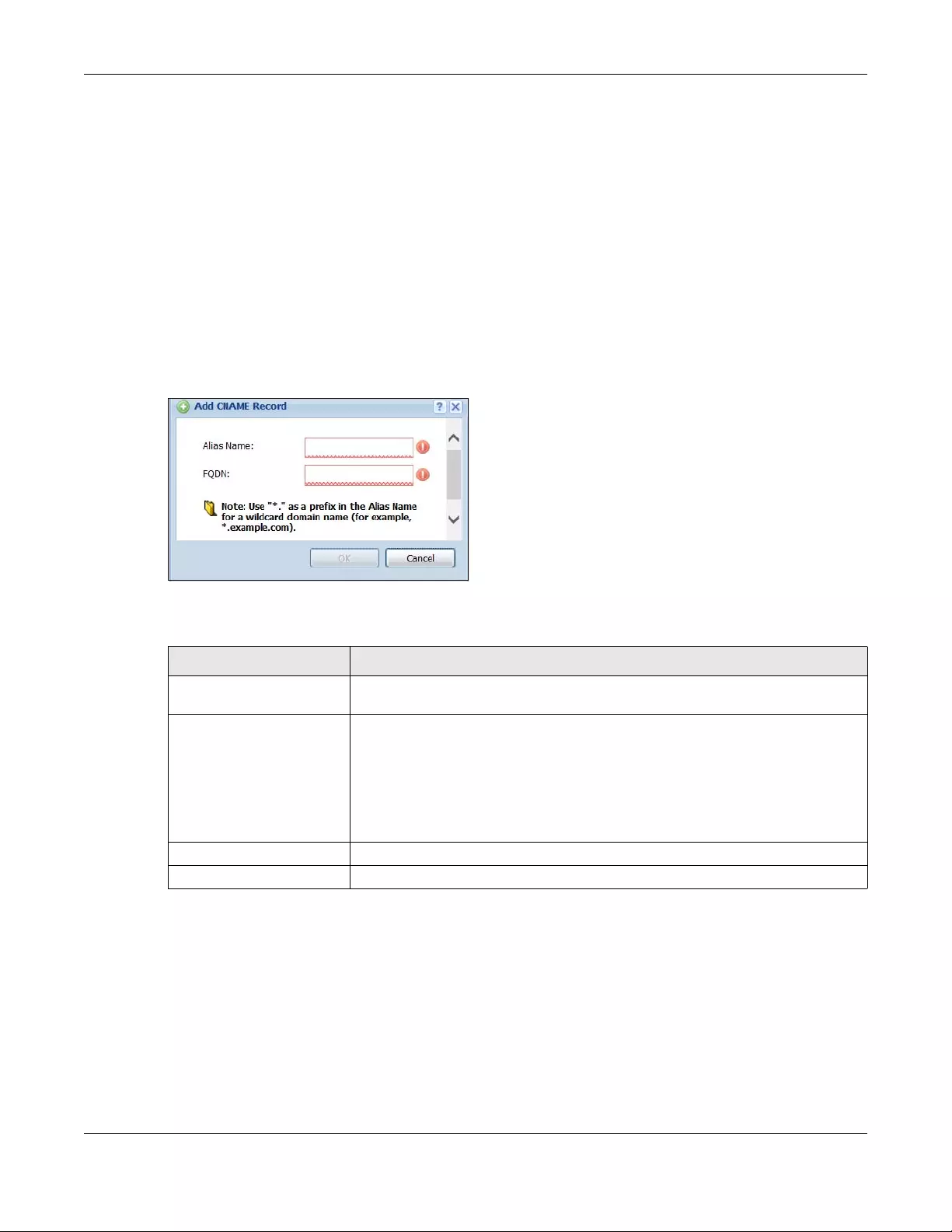
Chapter 44 System
USG/ZyWALL User’s Guide
843
having to create a record for each, so when the IP address is changed, all subdomain’s IP address is
updated as well, with one edit to the record.
For example, the domain name zyxel.com is hooked up to a record named A which translates it to
11.22.33.44. You also have several subdomains, like mail.zyxel.com, ftp.zyxel.com and you want this
subdomain to point to your main domain zyxel.com. Edit the IP Address in record A and all subdomains
will follow automatically. This eliminates chances for errors and increases efficiency in DNS
management.
44.6.7 Adding a CNAME Record
Click the Add icon in the CNAME Record table to add a record. Use “*.” as a prefix for a wildcard
domain name. For example *.zyxel.com.
Figure 596 Configuration > System > DNS > CNAME Record > Add
The following table describes the labels in this screen.
44.6.8 Domain Zone Forwarder
A domain zone forwarder contains a DNS server’s IP address. The Zyxel Device can query the DNS server
to resolve domain zones for features like VPN, DDNS and the time server. A domain zone is a fully
qualified domain name without the host. For example, zyxel.com.tw is the domain zone for the
www.zyxel.com.tw fully qualified domain name.
Table 354 Configuration > System > DNS > CNAME Record > Add
LABEL DESCRIPTION
Alias name Enter an Alias Name. Use "*." as a prefix in the Alias name for a wildcard domain
name (for example, *.example.com).
FQDN Type a Fully-Qualified Domain Name (FQDN) of a server. An FQDN starts with a host
name and continues all the way up to the top-level domain name. For example,
www.zyxel.com.tw is a fully qualified domain name, where “www” is the host, “zyxel”
is the third-level domain, “com” is the second-level domain, and “tw” is the top level
domain. Underscores are not allowed.
Use "*." as a prefix in the FQDN for a wildcard domain name (for example,
*.example.com).
OK Click OK to save your customized settings and exit this screen.
Cancel Click Cancel to exit this screen without saving.
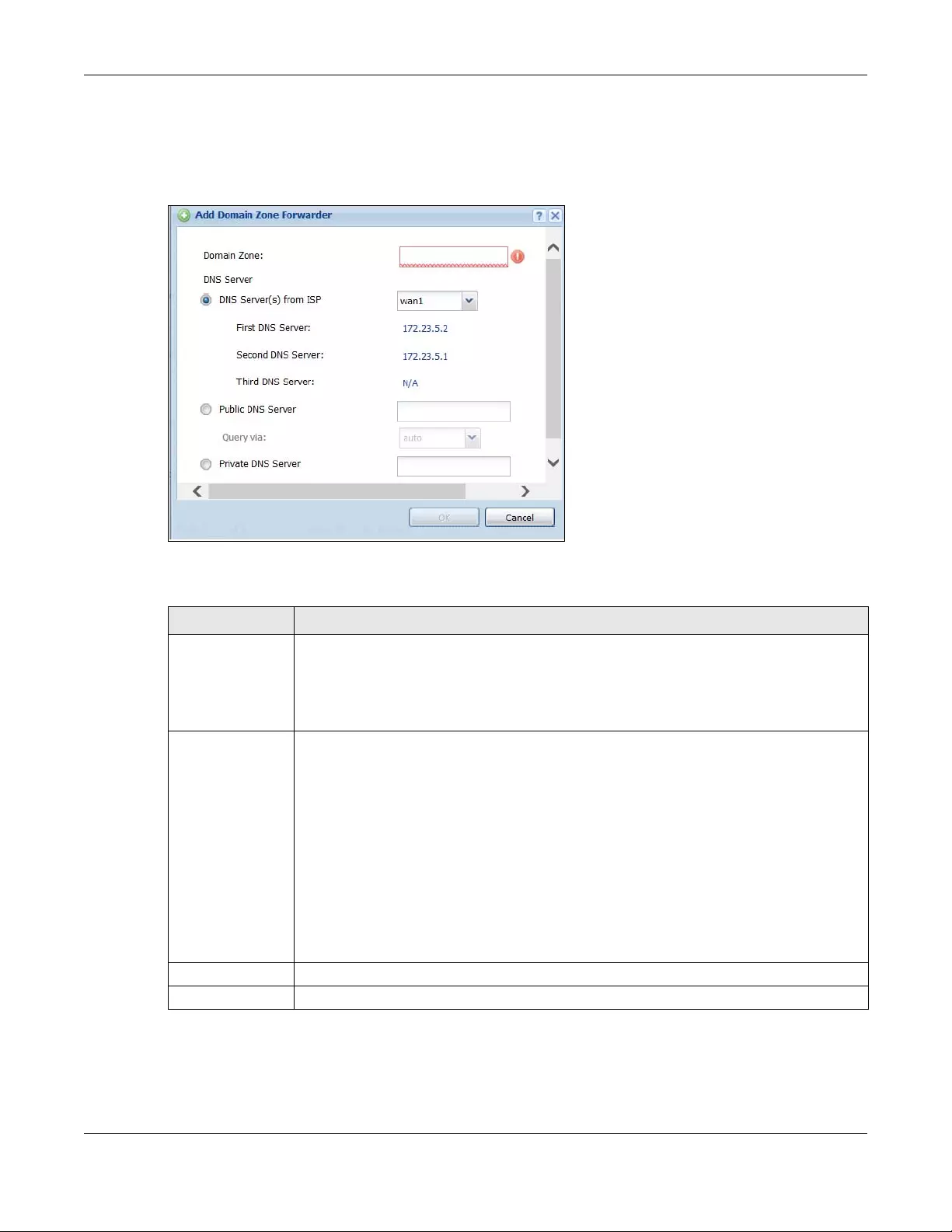
Chapter 44 System
USG/ZyWALL User’s Guide
844
44.6.9 Adding a Domain Zone Forwarder
Click the Add icon in the Domain Zone Forwarder table to add a domain zone forwarder record.
Figure 597 Configuration > System > DNS > Domain Zone Forwarder Add
The following table describes the labels in this screen.
44.6.10 MX Record
A MX (Mail eXchange) record indicates which host is responsible for the mail for a particular domain,
that is, controls where mail is sent for that domain. If you do not configure proper MX records for your
Table 355 Configuration > System > DNS > Domain Zone Forwarder Add
LABEL DESCRIPTION
Domain Zone A domain zone is a fully qualified domain name without the host. For example, zyxel.com.tw is
the domain zone for the www.zyxel.com.tw fully qualified domain name. For example,
whenever the Zyxel Device receives needs to resolve a zyxel.com.tw domain name, it can
send a query to the recorded name server IP address.
Enter * if all domain zones are served by the specified DNS server(s).
DNS Server Select DNS Server(s) from ISP if your ISP dynamically assigns DNS server information. You also
need to select an interface through which the ISP provides the DNS server IP address(es). The
interface should be activated and set to be a DHCP client. The fields below display the (read-
only) DNS server IP address(es) that the ISP assigns. N/A displays for any DNS server IP address
fields for which the ISP does not assign an IP address.
Select Public DNS Server if you have the IP address of a DNS server. Enter the DNS server's IP
address in the field to the right. The Zyxel Device must be able to connect to the DNS server
without using a VPN tunnel. The DNS server could be on the Internet or one of the Zyxel
Device’s local networks. You cannot use 0.0.0.0. Use the Query via field to select the interface
through which the Zyxel Device sends DNS queries to a DNS server.
Select Private DNS Server if you have the IP address of a DNS server to which the Zyxel Device
connects through a VPN tunnel. Enter the DNS server's IP address in the field to the right. You
cannot use 0.0.0.0.
OK Click OK to save your customized settings and exit this screen.
Cancel Click Cancel to exit this screen without saving
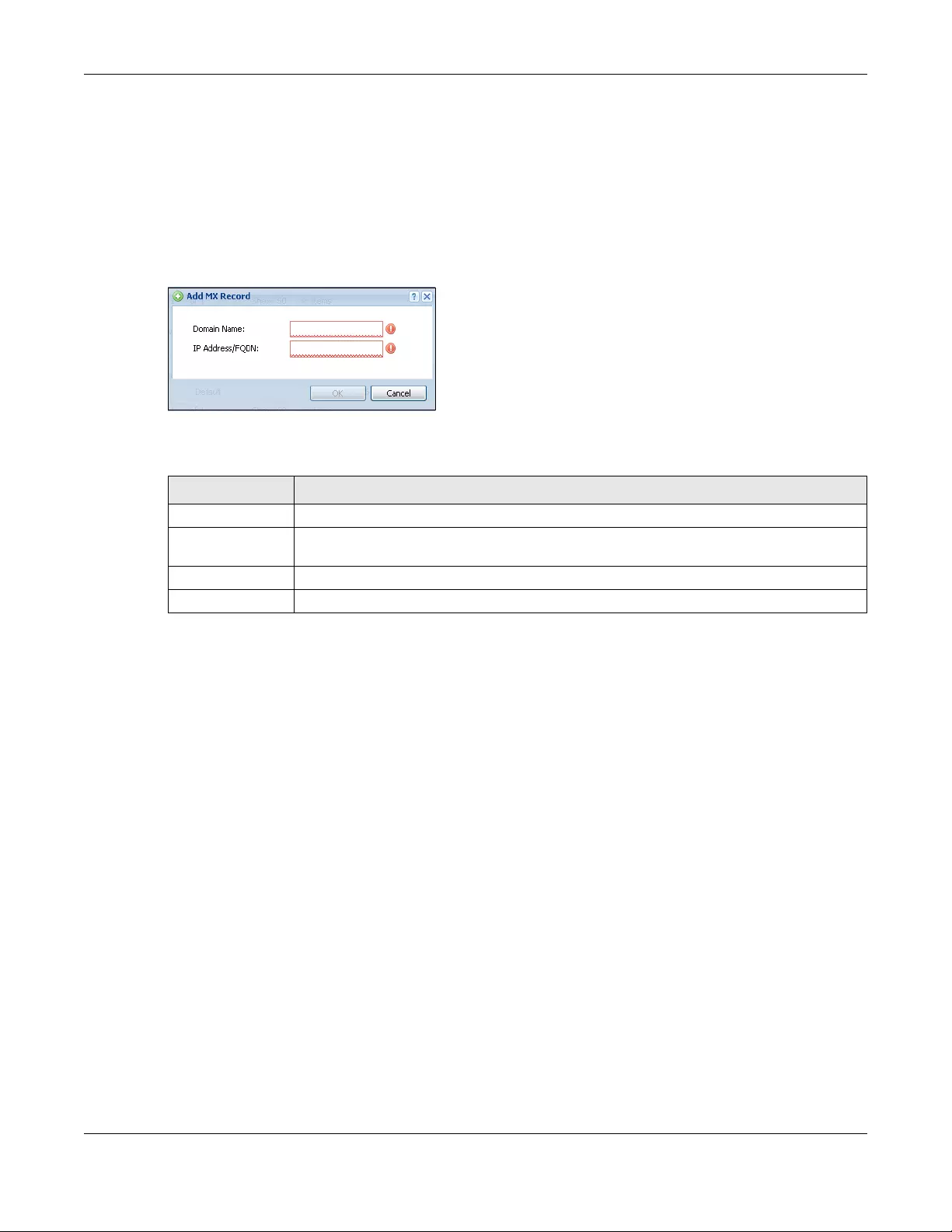
Chapter 44 System
USG/ZyWALL User’s Guide
845
domain or other domain, external e-mail from other mail servers will not be able to be delivered to your
mail server and vice versa. Each host or domain can have only one MX record, that is, one domain is
mapping to one host.
44.6.11 Adding a MX Record
Click the Add icon in the MX Record table to add a MX record.
Figure 598 Configuration > System > DNS > MX Record Add
The following table describes the labels in this screen.
44.6.12 Security Option Control
Configure the Security Option Control section in the Configuration > System > DNS screen (click Show
Advanced Settings to display it) if you suspect the Zyxel Device is being used by hackers in a DNS
amplification attack.
One possible strategy would be to deny Query Recursion and Additional Info from Cach e in the default
policy and allow Query Recursion and Additional Info from Cache only from trusted DNS servers
identified by address objects and added as members in the customized policy.
44.6.13 Editing a Security Option Control
Click a control policy and then click Edit to change allow or deny actions for Query Recursion and
Additional Info from Cache.
Table 356 Configuration > System > DNS > MX Record Add
LABEL DESCRIPTION
Domain Name Enter the domain name where the mail is destined for.
IP Address/FQDN Enter the IP address or Fully-Qualified Domain Name (FQDN) of a mail server that handles the
mail for the domain specified in the field above.
OK Click OK to save your customized settings and exit this screen.
Cancel Click Cancel to exit this screen without saving
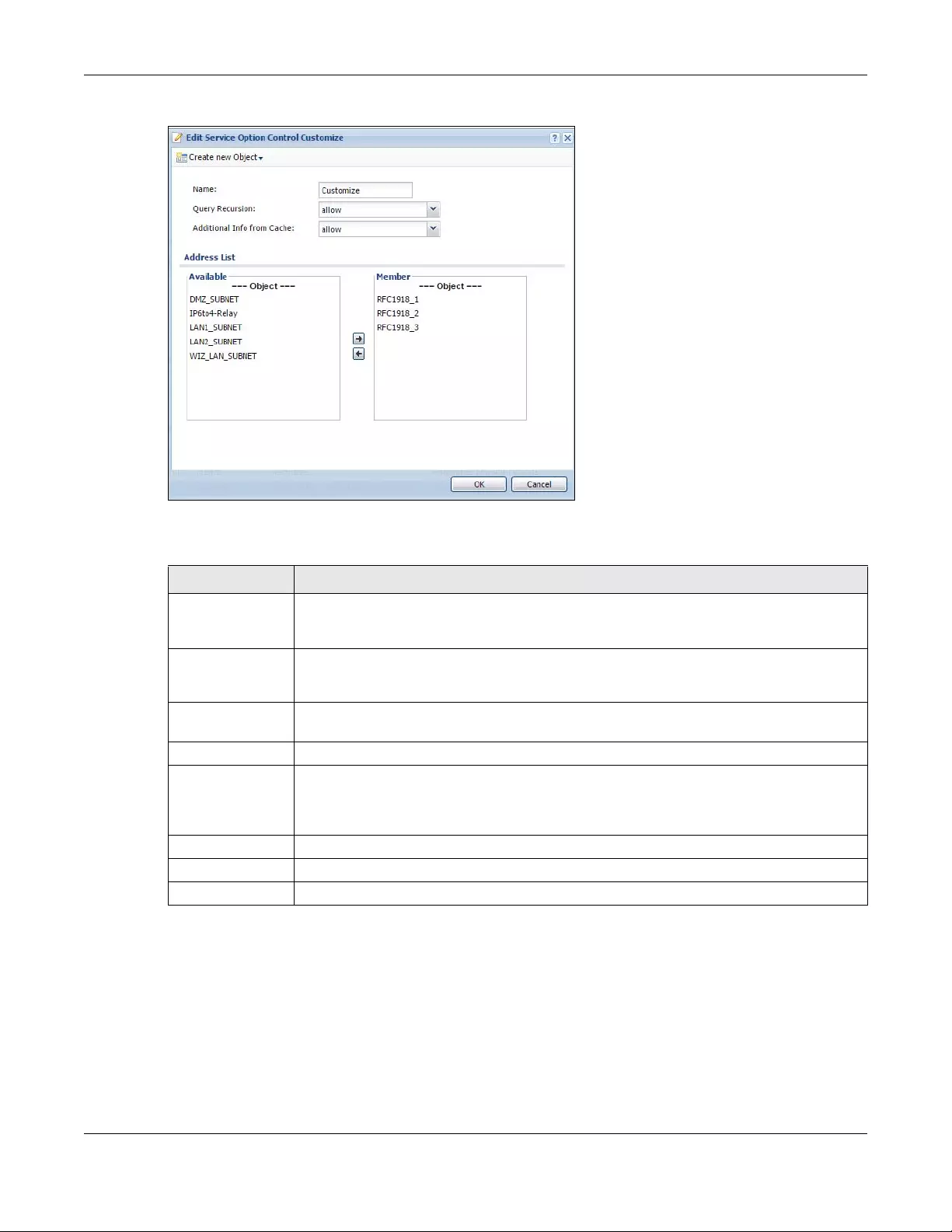
Chapter 44 System
USG/ZyWALL User’s Guide
846
Figure 599 Configuration > System > DNS > Security Option Control Edit (Customize)
The following table describes the labels in this screen.
44.6.14 Adding a DNS Service Control Rule
Click the Add icon in the Service Control table to add a service control rule.
Table 357 Configuration > System > DNS > Security Option Control Edit (Customize)
LABEL DESCRIPTION
Name You may change the name for the customized security option control policy. The customized
security option control policy is checked first and if an address object match is not found, the
Default control policy is checked
Query Recursion Choose if the ZyWALL/USG is allowed or denied to forward DNS client requests to DNS servers
for resolution. This can apply to specific open DNS servers using the address objects in a
customized rule.
Additional Info
from Cache
Choose if the ZyWALL/USG is allowed or denied to cache Resource Records (RR) obtained
from previous DNS queries.
Address List Specifying address objects is not available in the default policy as all addresses are included.
Available This box displays address objects created in Object > Address. Select one (or more), and click
the > arrow to have it (them) join the Member list of address objects that will apply to this rule.
For example, you could specify an open DNS server suspect of sending compromised
resource records by adding an address object for that server to the member list.
Member This box displays address objects that will apply to this rule.
OK Click OK to save your customized settings and exit this screen.
Cancel Click Cancel to exit this screen without saving
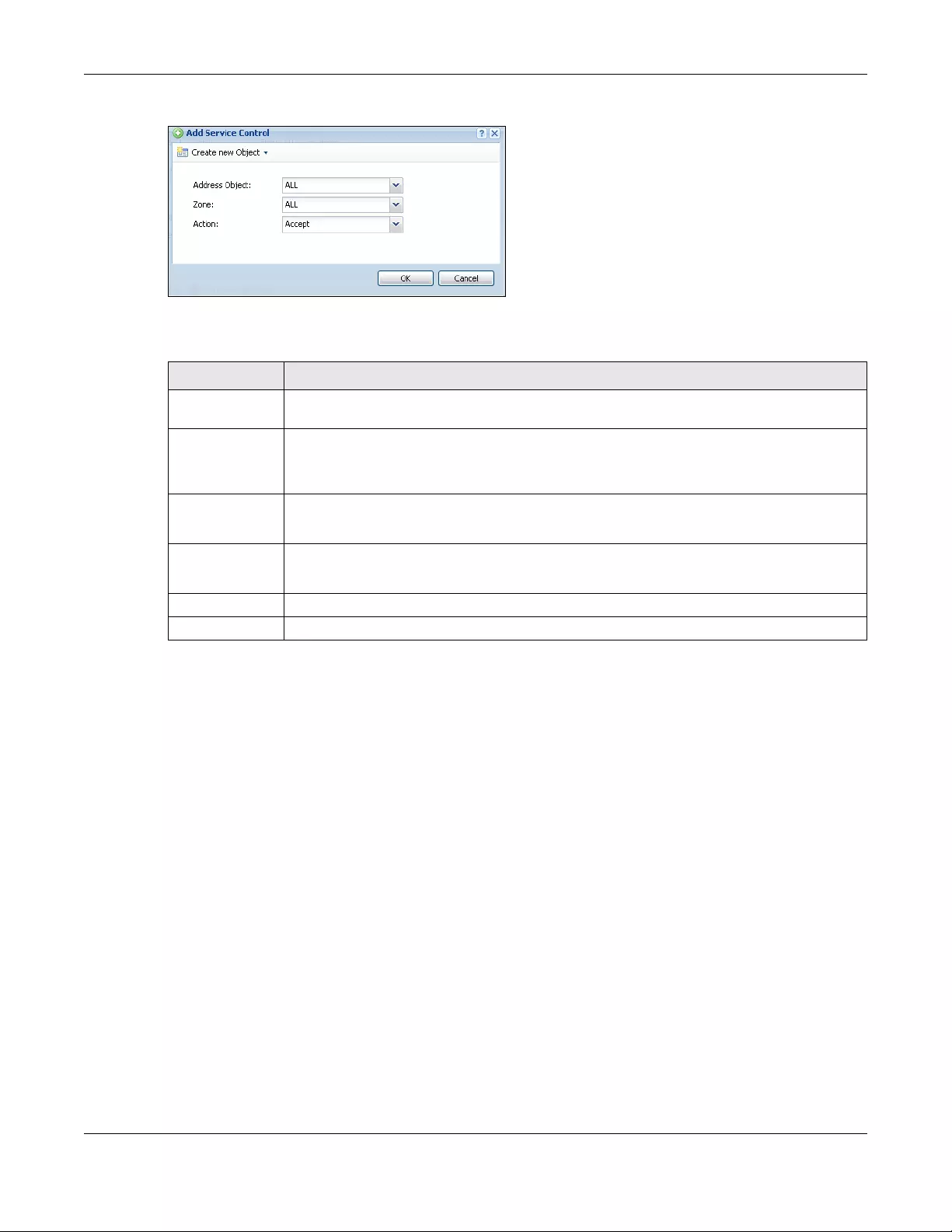
Chapter 44 System
USG/ZyWALL User’s Guide
847
Figure 600 Configuration > System > DNS > Service Control Rule Add
The following table describes the labels in this screen.
44.7 WWW Overview
The following figure shows secure and insecure management of the Zyxel Device coming in from the
WAN. HTTPS and SSH access are secure. HTTP and Telnet access are not secure.
Note: To allow the Zyxel Device to be accessed from a specified computer using a service,
make sure you do not have a service control rule or to-Zyxel Device security policy rule
to block that traffic.
To stop a service from accessing the Zyxel Device, clear Enable in the corresponding service screen.
44.7.1 Service Access Limitations
A service cannot be used to access the Zyxel Device when:
1You have disabled that service in the corresponding screen.
2The allowed IP address (address object) in the Service Control table does not match the client IP
address (the Zyxel Device disallows the session).
Table 358 Configuration > System > DNS > Service Control Rule Add
LABEL DESCRIPTION
Create new
Object
Use this to configure any new settings objects that you need to use in this screen.
Address Object Select ALL to allow or deny any computer to send DNS queries to the Zyxel Device.
Select a predefined address object to just allow or deny the computer with the IP address that
you specified to send DNS queries to the Zyxel Device.
Zone Select ALL to allow or prevent DNS queries through any zones.
Select a predefined zone on which a DNS query to the Zyxel Device is allowed or denied.
Action Select Accept to have the Zyxel Device allow the DNS queries from the specified computer.
Select Deny to have the Zyxel Device reject the DNS queries from the specified computer.
OK Click OK to save your customized settings and exit this screen.
Cancel Click Cancel to exit this screen without saving

Chapter 44 System
USG/ZyWALL User’s Guide
848
3The IP address (address object) in the Service Control table is not in the allowed zone or the action is set
to Deny.
4There is a security policy rule that blocks it.
44.7.2 System Timeout
There is a lease timeout for administrators. The Zyxel Device automatically logs you out if the
management session remains idle for longer than this timeout period. The management session does
not time out when a statistics screen is polling.
Each user is also forced to log in the Zyxel Device for authentication again when the reauthentication
time expires.
You can change the timeout settings in the User/Group screens.
44.7.3 HTTPS
You can set the Zyxel Device to use HTTP or HTTPS (HTTPS adds security) for Web Configurator sessions.
Specify which zones allow Web Configurator access and from which IP address the access can come.
HTTPS (HyperText Transfer Protocol over Secure Socket Layer, or HTTP over SSL) is a web protocol that
encrypts and decrypts web pages. Secure Socket Layer (SSL) is an application-level protocol that
enables secure transactions of data by ensuring confidentiality (an unauthorized party cannot read the
transferred data), authentication (one party can identify the other party) and data integrity (you know if
data has been changed).
It relies upon certificates, public keys, and private keys.
HTTPS on the Zyxel Device is used so that you can securely access the Zyxel Device using the Web
Configurator. The SSL protocol specifies that the HTTPS server (the Zyxel Device) must always
authenticate itself to the HTTPS client (the computer which requests the HTTPS connection with the Zyxel
Device), whereas the HTTPS client only should authenticate itself when the HTTPS server requires it to do
so (select Authenticate Client Certificates in the WWW screen). Authenticate Client Certificates is
optional and if selected means the HTTPS client must send the Zyxel Device a certificate. You must apply
for a certificate for the browser from a CA that is a trusted CA on the Zyxel Device.
Please refer to the following figure.
1HTTPS connection requests from an SSL-aware web browser go to port 443 (by default) on the Zyxel
Device’s web server.
2HTTP connection requests from a web browser go to port 80 (by default) on the Zyxel Device’s web
server.
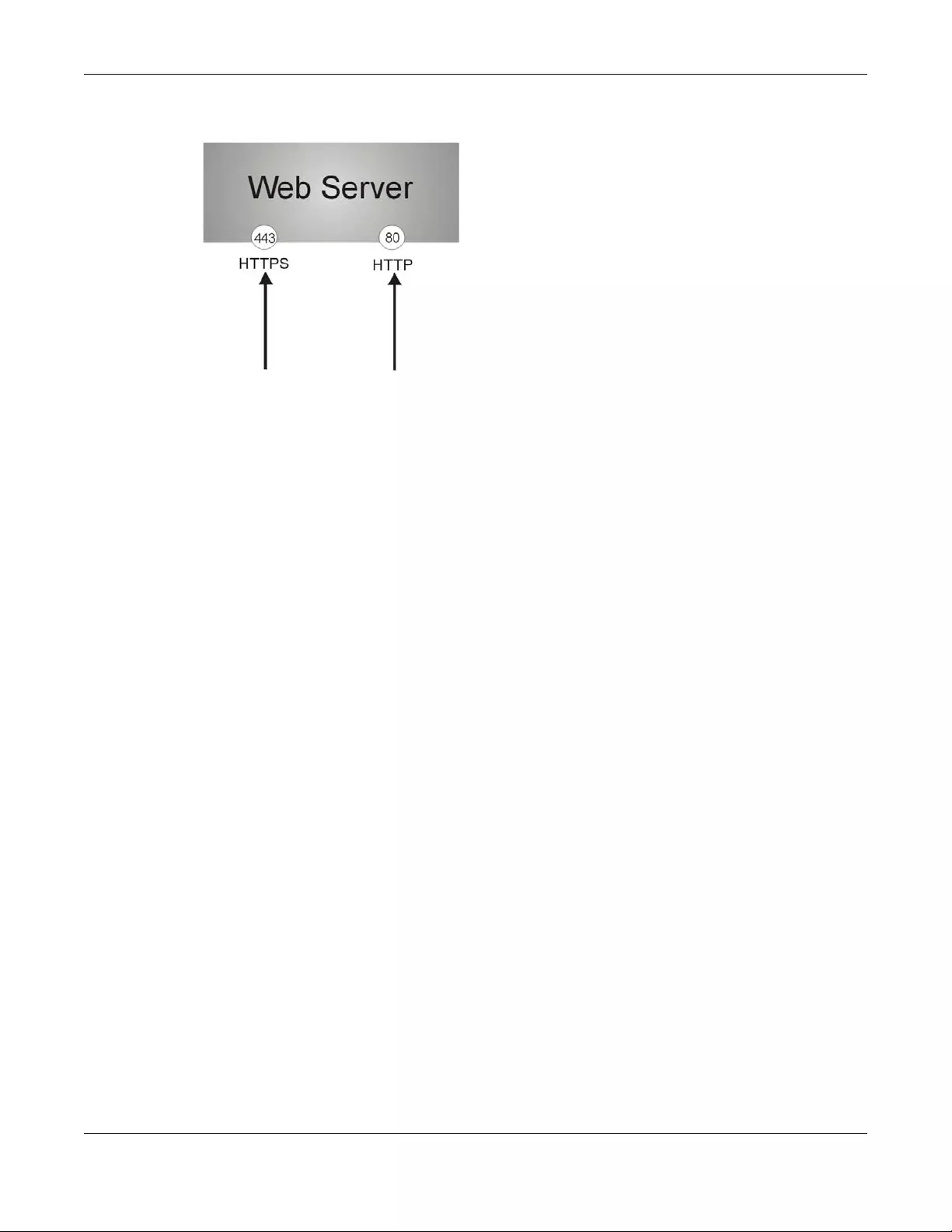
Chapter 44 System
USG/ZyWALL User’s Guide
849
Figure 601 HTTP/HTTPS Implementation
Note: If you disable HTTP in the WWW screen, then the Zyxel Device blocks all HTTP connection
attempts.
44.7.4 Configuring WWW Service Control
Click Configuration > System > WWW to open the WWW screen. Use this screen to specify from which
zones you can access the Zyxel Device using HTTP or HTTPS. You can also specify which IP addresses the
access can come from.
Note: Admin Service Control deals with management access (to the Web Configurator).
User Service Control deals with user access to the Zyxel Device (logging into SSL VPN for
example).
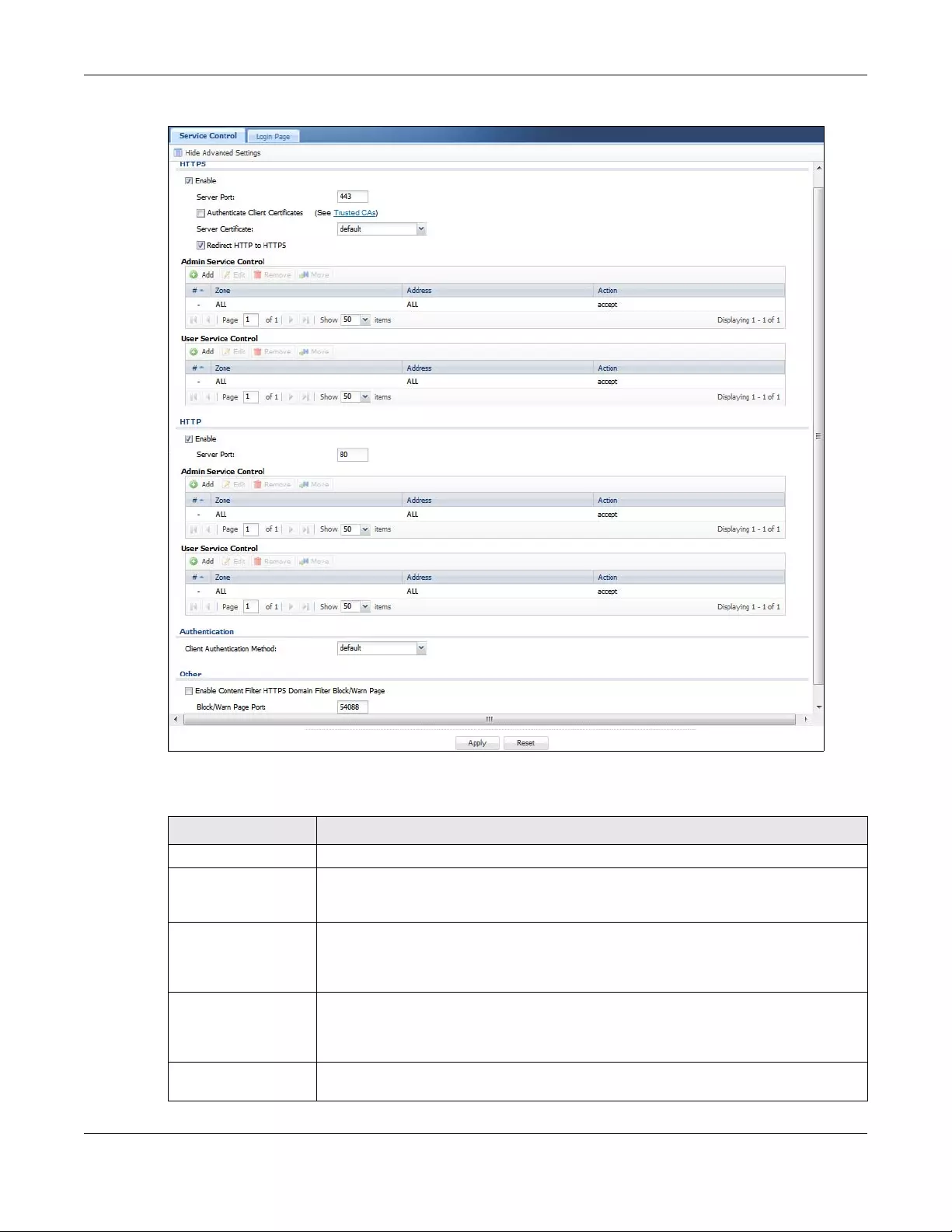
Chapter 44 System
USG/ZyWALL User’s Guide
850
Figure 602 Configuration > System > WWW > Service Control
The following table describes the labels in this screen.
Table 359 Configuration > System > WWW > Service Control
LABEL DESCRIPTION
HTTPS
Enable Select the check box to allow or disallow the computer with the IP address that matches
the IP address(es) in the Service Control table to access the Zyxel Device Web
Configurator using secure HTTPs connections.
Server Port The HTTPS server listens on port 443 by default. If you change the HTTPS server port to a
different number on the Zyxel Device, for example 8443, then you must notify people who
need to access the Zyxel Device Web Configurator to use “https://Zyxel Device IP
Address:8443” as the URL.
Authenticate Client
Certificates
Select Authenticate Client Certificates (optional) to require the SSL client to authenticate
itself to the Zyxel Device by sending the Zyxel Device a certificate. To do that the SSL client
must have a CA-signed certificate from a CA that has been imported as a trusted CA on
the Zyxel Device (see Section 44.7.7.5 on page 860 on importing certificates for details).
Server Certificate Select a certificate the HTTPS server (the Zyxel Device) uses to authenticate itself to the
HTTPS client. You must have certificates already configured in the My Certificates screen.
Chapter 44 System
USG/ZyWALL User’s Guide
851
Redirect HTTP to HTTPS To allow only secure Web Configurator access, select this to redirect all HTTP connection
requests to the HTTPS server.
Admin/User Service
Control
Admin Service Control specifies from which zones an administrator can use HTTPS to
manage the Zyxel Device (using the Web Configurator). You can also specify the IP
addresses from which the administrators can manage the Zyxel Device.
User Service Control specifies from which zones a user can use HTTPS to log into the Zyxel
Device (to log into SSL VPN for example). You can also specify the IP addresses from which
the users can access the Zyxel Device.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after
the selected entry.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so. Note that subsequent entries move up by one when you take
this action.
Move To change an entry’s position in the numbered list, select the method and click Move to
display a field to type a number for where you want to put it and press [ENTER] to move
the rule to the number that you typed.
#This is the index number of the service control rule.
The entry with a hyphen (-) instead of a number is the Zyxel Device’s (non-configurable)
default policy. The Zyxel Device applies this to traffic that does not match any other
configured rule. It is not an editable rule. To apply other behavior, configure a rule that
traffic will match so the Zyxel Device will not have to use the default policy.
Zone This is the zone on the Zyxel Device the user is allowed or denied to access.
Address This is the object name of the IP address(es) with which the computer is allowed or denied
to access.
Action This displays whether the computer with the IP address specified above can access the
Zyxel Device zone(s) configured in the Zone field (Accept) or not (Deny).
HTTP
Enable Select the check box to allow or disallow the computer with the IP address that matches
the IP address(es) in the Service Control table to access the Zyxel Device Web
Configurator using HTTP connections.
Server Port You may change the server port number for a service if needed, however you must use
the same port number in order to use that service to access the Zyxel Device.
Admin/User Service
Control
Admin Service Control specifies from which zones an administrator can use HTTP to
manage the Zyxel Device (using the Web Configurator). You can also specify the IP
addresses from which the administrators can manage the Zyxel Device.
User Service Control specifies from which zones a user can use HTTP to log into the Zyxel
Device (to log into SSL VPN for example). You can also specify the IP addresses from which
the users can access the Zyxel Device.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after
the selected entry.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to
remove it before doing so. Note that subsequent entries move up by one when you take
this action.
Move To change an entry’s position in the numbered list, select the method and click Move to
display a field to type a number for where you want to put it and press [ENTER] to move
the rule to the number that you typed.
Table 359 Configuration > System > WWW > Service Control (continued)
LABEL DESCRIPTION
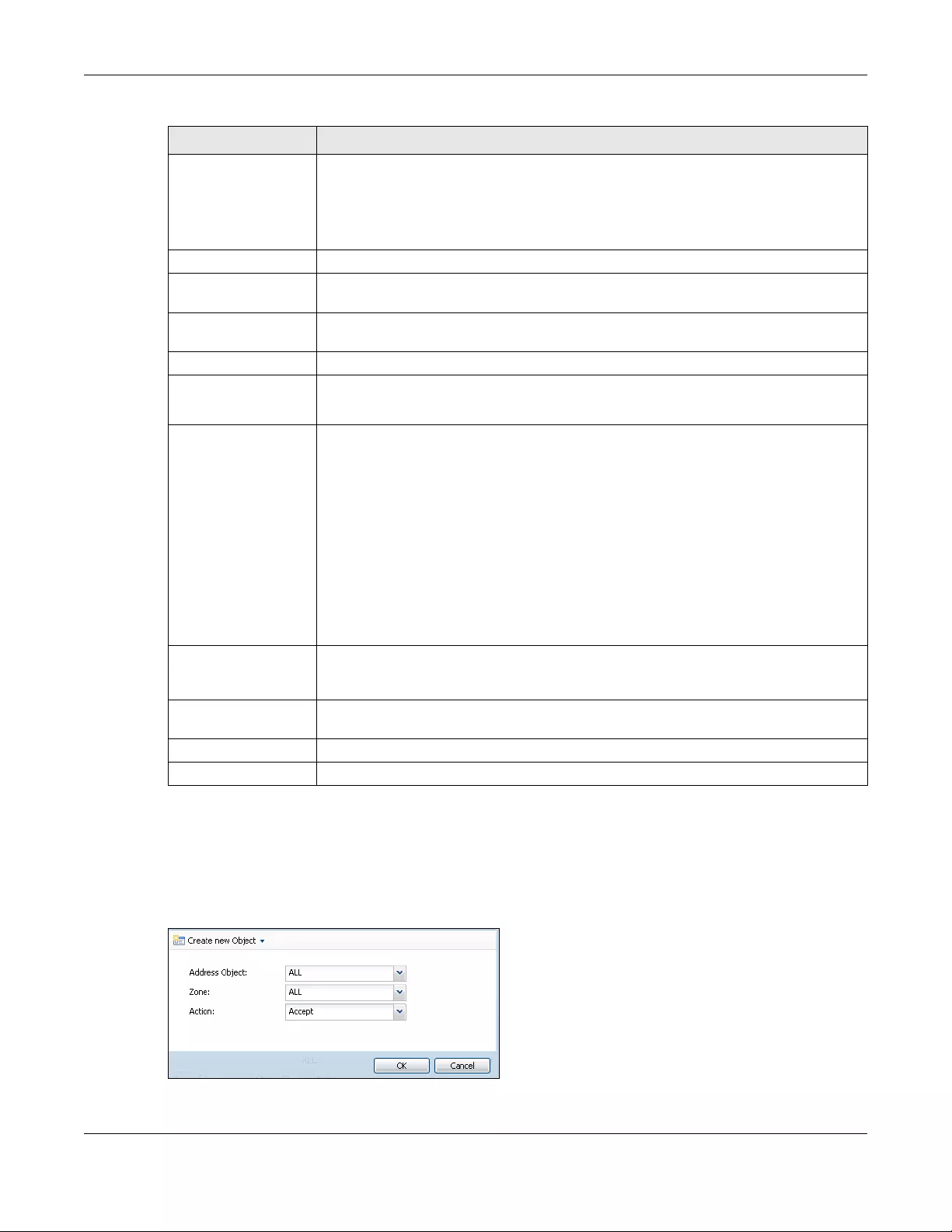
Chapter 44 System
USG/ZyWALL User’s Guide
852
44.7.5 Service Control Rules
Click Add or Edit in the Service Control table in a WWW, SSH, Telnet, FTP or SNMP screen to add a service
control rule.
Figure 603 Configuration > System > Service Control Rule > Edit
#This is the index number of the service control rule.
The entry with a hyphen (-) instead of a number is the Zyxel Device’s (non-configurable)
default policy. The Zyxel Device applies this to traffic that does not match any other
configured rule. It is not an editable rule. To apply other behavior, configure a rule that
traffic will match so the Zyxel Device will not have to use the default policy.
Zone This is the zone on the Zyxel Device the user is allowed or denied to access.
Address This is the object name of the IP address(es) with which the computer is allowed or denied
to access.
Action This displays whether the computer with the IP address specified above can access the
Zyxel Device zone(s) configured in the Zone field (Accept) or not (Deny).
Authentication
Client Authentication
Method
Select a method the HTTPS or HTTP server uses to authenticate a client.
You must have configured the authentication methods in the Auth. method screen.
Other When HTTPS Domain Filter blocks a page, the connection is redirected to a local web
server to display the blocking message. HSTS (HTTP Strict Transport Security) may be
activated in some browsers as the browser cached certificate is different to the one
displayed by the local server. In this case, you cannot see a blocking warning message.
Accessing a web page may require multiple connections to different sites to get all the
information in the web page. When there is a connection to a HTTPS website that belongs
to a blocked category, it is filtered, but you don't receive a warning page with the option
to continue. For example, you want to block www.google.com and issue a Warn action.
When you connect to www.google.com another connection to pic.google.com is
created to get the pictures on the Google page. www.google.com can display a
warning page in your browser (and you can click ‘Continue’ to forward the connection)
but the connection to pic.google.com cannot display a ‘Continue’ dialog, so parts of the
Google page will appear blank and will not display the related picture content.
Enable Content Filter
HTTPS Domain Filter
Block/Warn Page
Use this field to have the Zyxel Device display a warning page instead of a blank page
when an HTPPS connection is redirected.
Block/Warn Page Port Use the default port number as displayed for the warning page. If you change it, the new
port number should be unique.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 359 Configuration > System > WWW > Service Control (continued)
LABEL DESCRIPTION
Chapter 44 System
USG/ZyWALL User’s Guide
853
The following table describes the labels in this screen.
44.7.6 Customizing the WWW Login Page
Click Configuration > System > WWW > Login Page to open the Login Page screen. Use this screen to
customize the Web Configurator login screen. You can also customize the page that displays after an
access user logs into the Web Configurator to access network services like the Internet.
Table 360 Configuration > System > Service Control Rule > Edit
LABEL DESCRIPTION
Create new
Object
Use this to configure any new settings objects that you need to use in this screen.
Address Object Select ALL to allow or deny any computer to communicate with the Zyxel Device using this
service.
Select a predefined address object to just allow or deny the computer with the IP address that
you specified to access the Zyxel Device using this service.
Zone Select ALL to allow or prevent any Zyxel Device zones from being accessed using this service.
Select a predefined Zyxel Device zone on which a incoming service is allowed or denied.
Action Select Accept to allow the user to access the Zyxel Device from the specified computers.
Select Deny to block the user’s access to the Zyxel Device from the specified computers.
OK Click OK to save your customized settings and exit this screen.
Cancel Click Cancel to exit this screen without saving
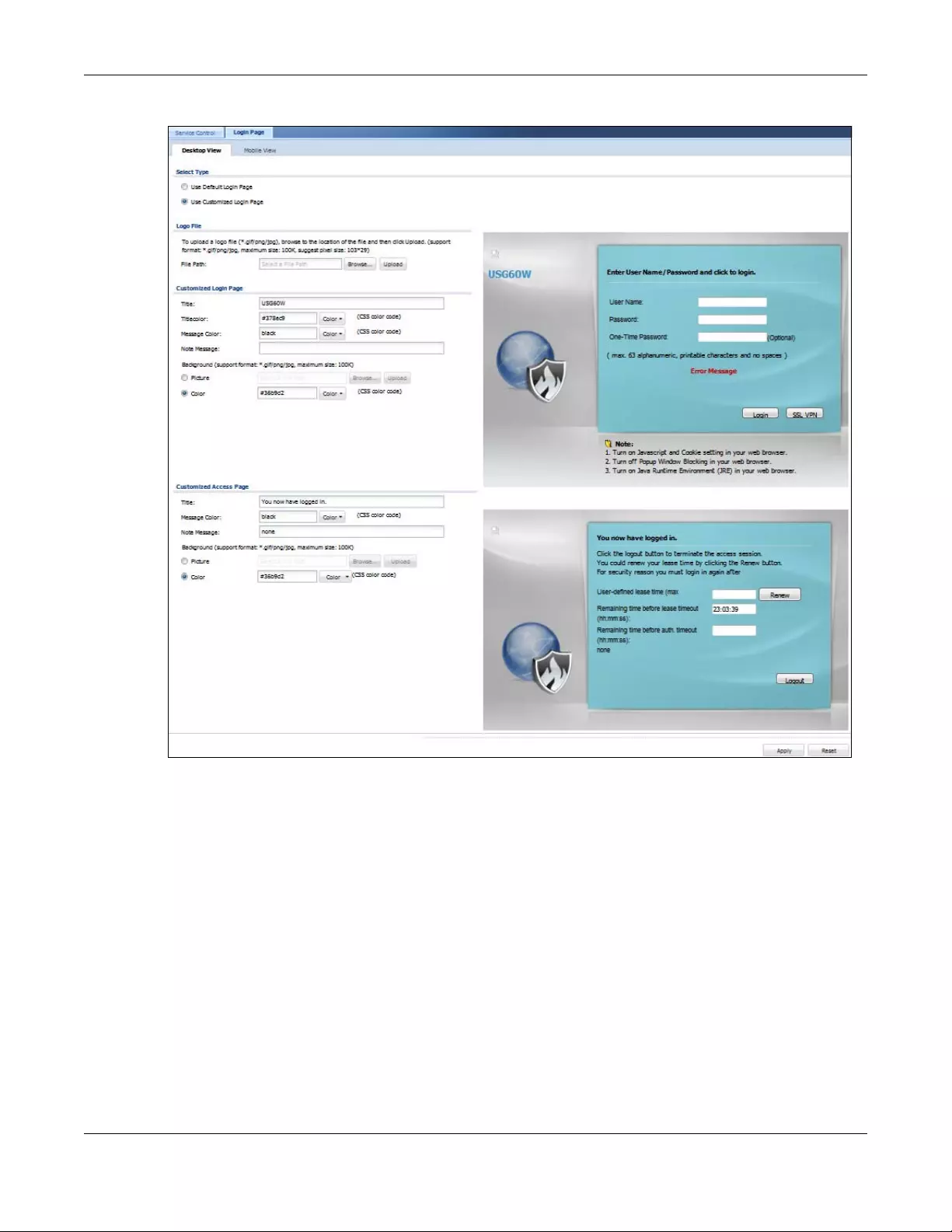
Chapter 44 System
USG/ZyWALL User’s Guide
854
Figure 604 Configuration > System > WWW > Login Page (Desktop View)
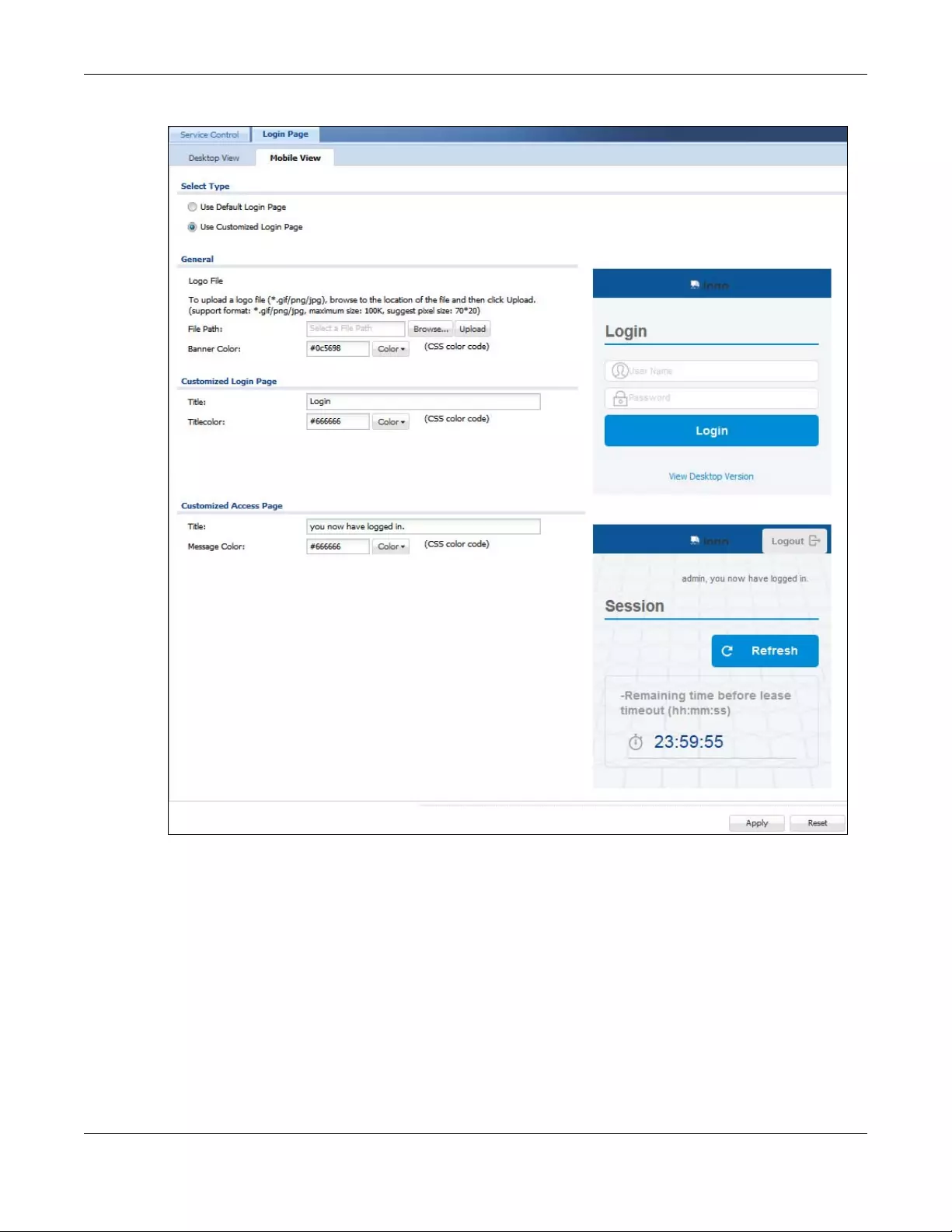
Chapter 44 System
USG/ZyWALL User’s Guide
855
Figure 605 Configuration > System > WWW > Login Page (Mobile View)
The following figures identify the parts you can customize in the login and access pages.
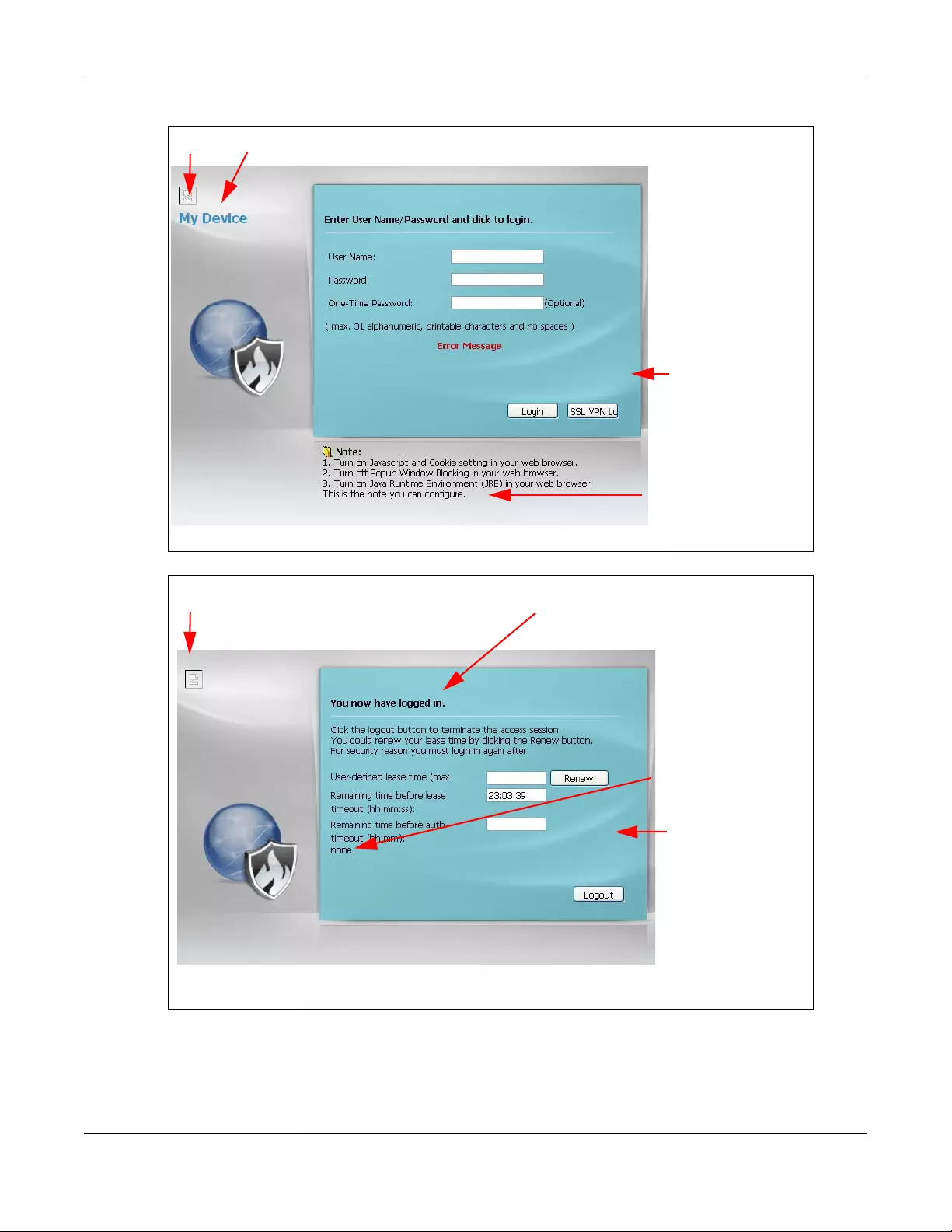
Chapter 44 System
USG/ZyWALL User’s Guide
856
Figure 606 Login Page Customization
Figure 607 Access Page Customization
You can specify colors in one of the following ways:
• Click Color to display a screen of web-safe colors from which to choose.
• Enter the name of the desired color.
Logo Title
Message
Note Message
Background
(last line of text)
(color of all text)
Logo Title
Message
Note Message
Window
(last line of text)
(color of all text)
Background
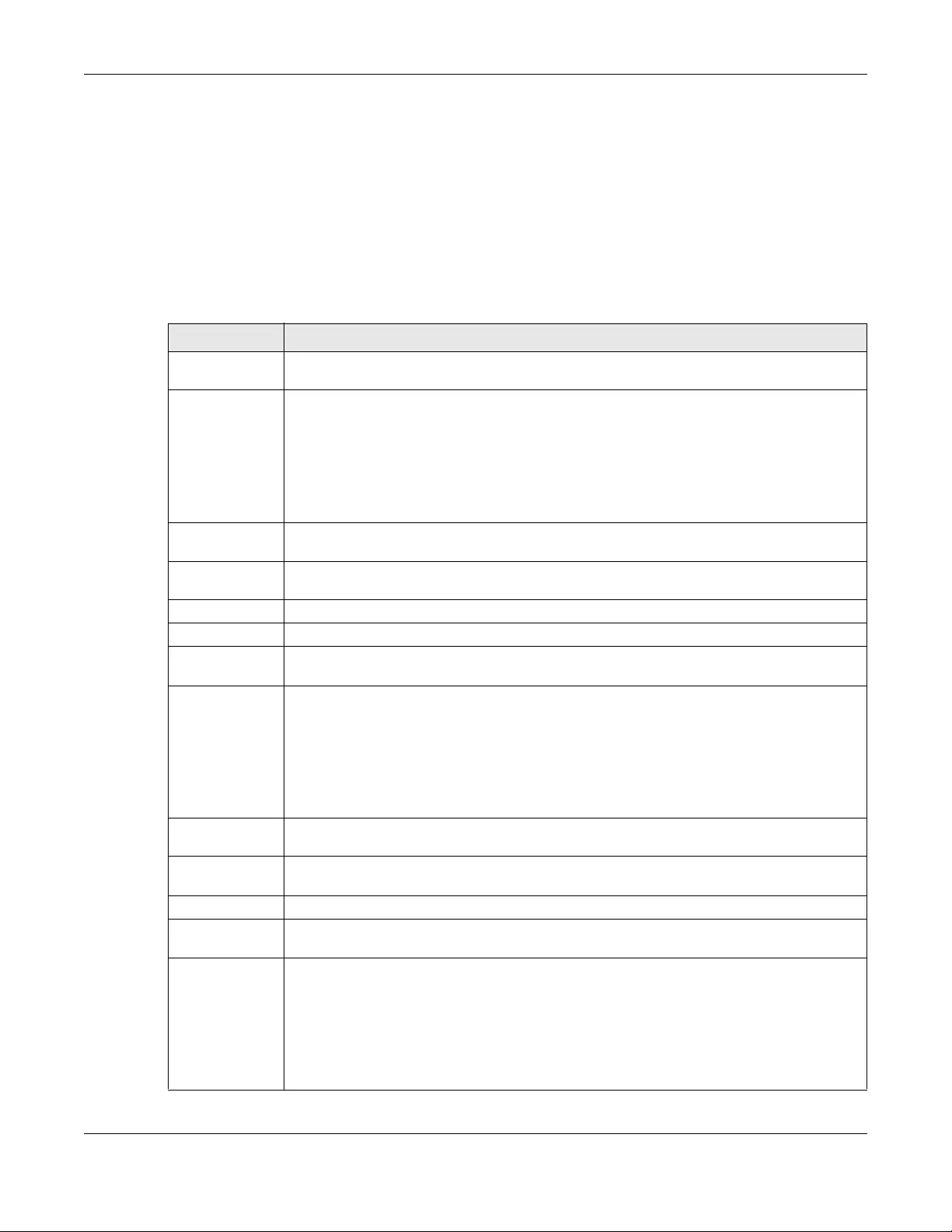
Chapter 44 System
USG/ZyWALL User’s Guide
857
• Enter a pound sign (#) followed by the six-digit hexadecimal number that represents the desired
color. For example, use “#000000” for black.
• Enter “rgb” followed by red, green, and blue values in parenthesis and separate by commas. For
example, use “rgb(0,0,0)” for black.
Your desired color should display in the preview screen on the right after you click in another field, click
Apply, or press [ENTER]. If your desired color does not display, your browser may not support it. Try
selecting another color.
The following table describes the labels in the screen.
Table 361 Configuration > System > WWW > Login Page
LABEL DESCRIPTION
Select Type Select whether the Web Configurator uses the default login screen or one that you customize in
the rest of this screen.
Logo File You can upload a graphic logo to be displayed on the upper left corner of the Web
Configurator login screen and access page.
Specify the location and file name of the logo graphic or click Browse to locate it.
Note: Use a GIF, JPG, or PNG of 100 kilobytes or less.
Click Upload to transfer the specified graphic file from your computer to the Zyxel Device.
Customized
Login Page
Use this section to set how the Web Configurator login screen looks.
Title Enter the title for the top of the screen. Use up to 64 printable ASCII characters. Spaces are
allowed.
Title Color Specify the color of the screen’s title text.
Message Color Specify the color of the screen’s text.
Note Message Enter a note to display at the bottom of the screen. Use up to 64 printable ASCII characters.
Spaces are allowed.
Background Set how the screen background looks.
To use a graphic, select Picture and upload a graphic. Specify the location and file name of
the logo graphic or click Browse to locate it. The picture’s size cannot be over 438 x 337 pixels.
Note: Use a GIF, JPG, or PNG of 100 kilobytes or less.
To use a color, select Color and specify the color.
Customized
Access Page
Use this section to customize the page that displays after an access user logs into the Web
Configurator to access network services like the Internet.
Title Enter the title for the top of the screen. Use up to 64 printable ASCII characters. Spaces are
allowed.
Message Color Specify the color of the screen’s text.
Note Message Enter a note to display below the title. Use up to 64 printable ASCII characters. Spaces are
allowed.
Background Set how the window’s background looks.
To use a graphic, select Picture and upload a graphic. Specify the location and file name of
the logo graphic or click Browse to locate it. The picture’s size cannot be over 438 x 337 pixels.
Note: Use a GIF, JPG, or PNG of 100 kilobytes or less.
To use a color, select Color and specify the color.
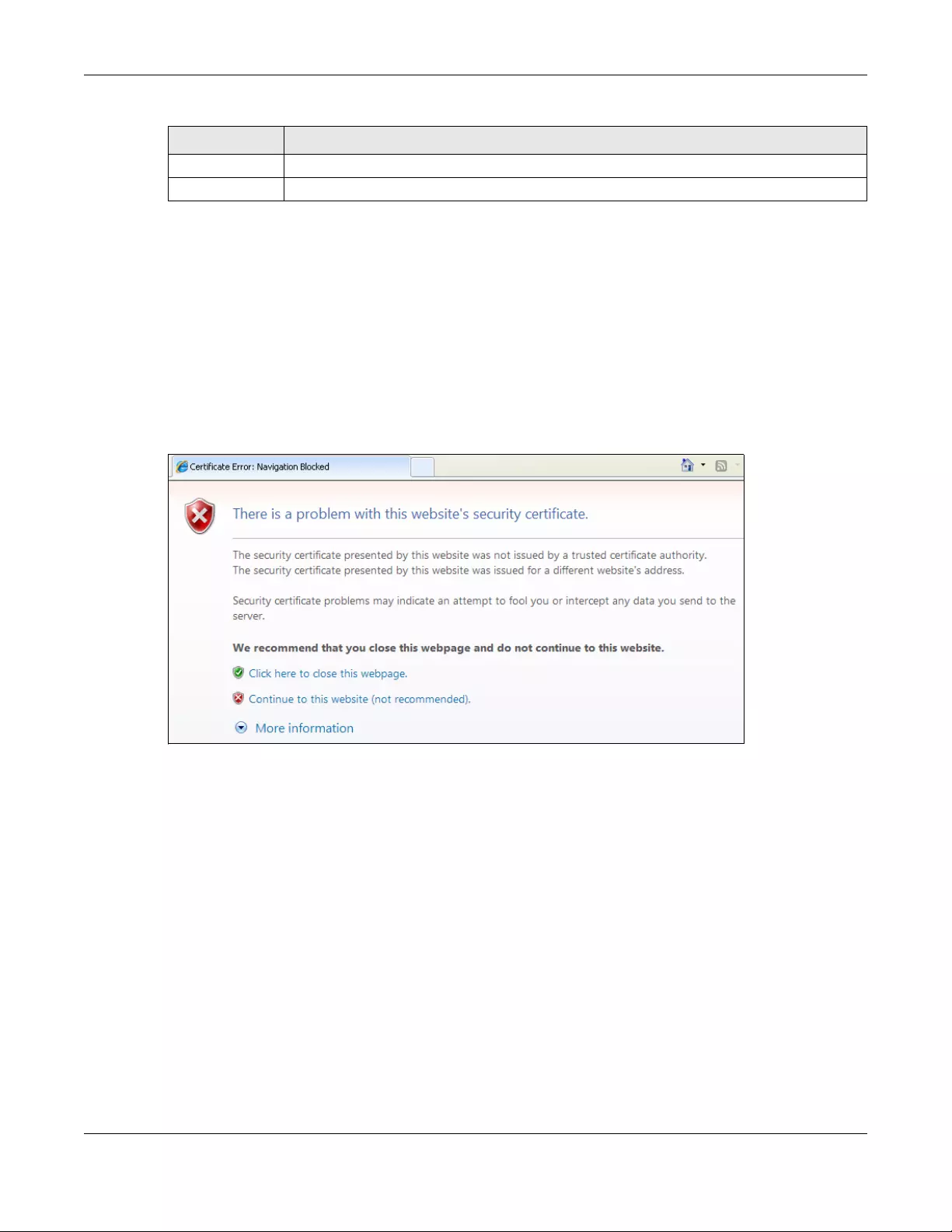
Chapter 44 System
USG/ZyWALL User’s Guide
858
44.7.7 HTTPS Example
If you haven’t changed the default HTTPS port on the Zyxel Device, then in your browser enter “https://
Zyxel Device IP Address/” as the web site address where “Zyxel Device IP Address” is the IP address or
domain name of the Zyxel Device you wish to access.
44.7.7.1 Internet Explorer Warning Messages
When you attempt to access the Zyxel Device HTTPS server, you will see the error message shown in the
following screen.
Figure 608 Security Alert Dialog Box (Internet Explorer)
Select Continue to this website to proceed to the Web Configurator login screen. Otherwise, select Click
here to close this web page to block the access.
44.7.7.2 Mozilla Firefox Warning Messages
When you attempt to access the Zyxel Device HTTPS server, a The Connection is Untrusted screen
appears as shown in the following screen. Click Technical Details if you want to verify more information
about the certificate from the Zyxel Device.
Select I Understand the Risks and then click Add Exception to add the Zyxel Device to the security
exception list. Click Confirm Security Exception.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 361 Configuration > System > WWW > Login Page (continued)
LABEL DESCRIPTION
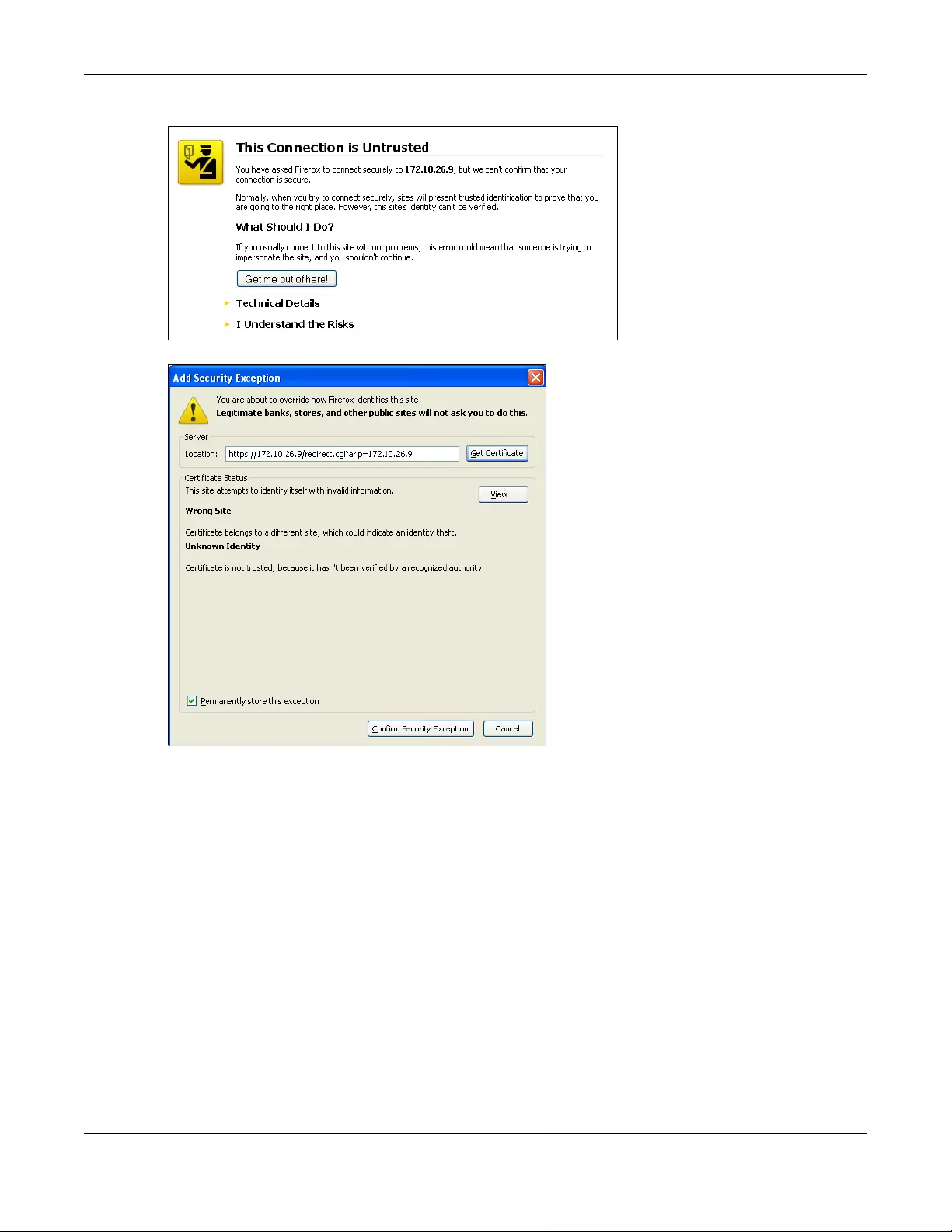
Chapter 44 System
USG/ZyWALL User’s Guide
859
Figure 609 Security Certificate 1 (Firefox)
Figure 610 Security Certificate 2 (Firefox)
44.7.7.3 Avoiding Browser Warning Messages
Here are the main reasons your browser displays warnings about the Zyxel Device’s HTTPS server
certificate and what you can do to avoid seeing the warnings:
• The issuing certificate authority of the Zyxel Device’s HTTPS server certificate is not one of the browser’s
trusted certificate authorities. The issuing certificate authority of the Zyxel Device's factory default
certificate is the Zyxel Device itself since the certificate is a self-signed certificate.
• For the browser to trust a self-signed certificate, import the self-signed certificate into your operating
system as a trusted certificate.
• To have the browser trust the certificates issued by a certificate authority, import the certificate
authority’s certificate into your operating system as a trusted certificate.
44.7.7.4 Login Screen
After you accept the certificate, the Zyxel Device login screen appears. The lock displayed in the
bottom of the browser status bar denotes a secure connection.
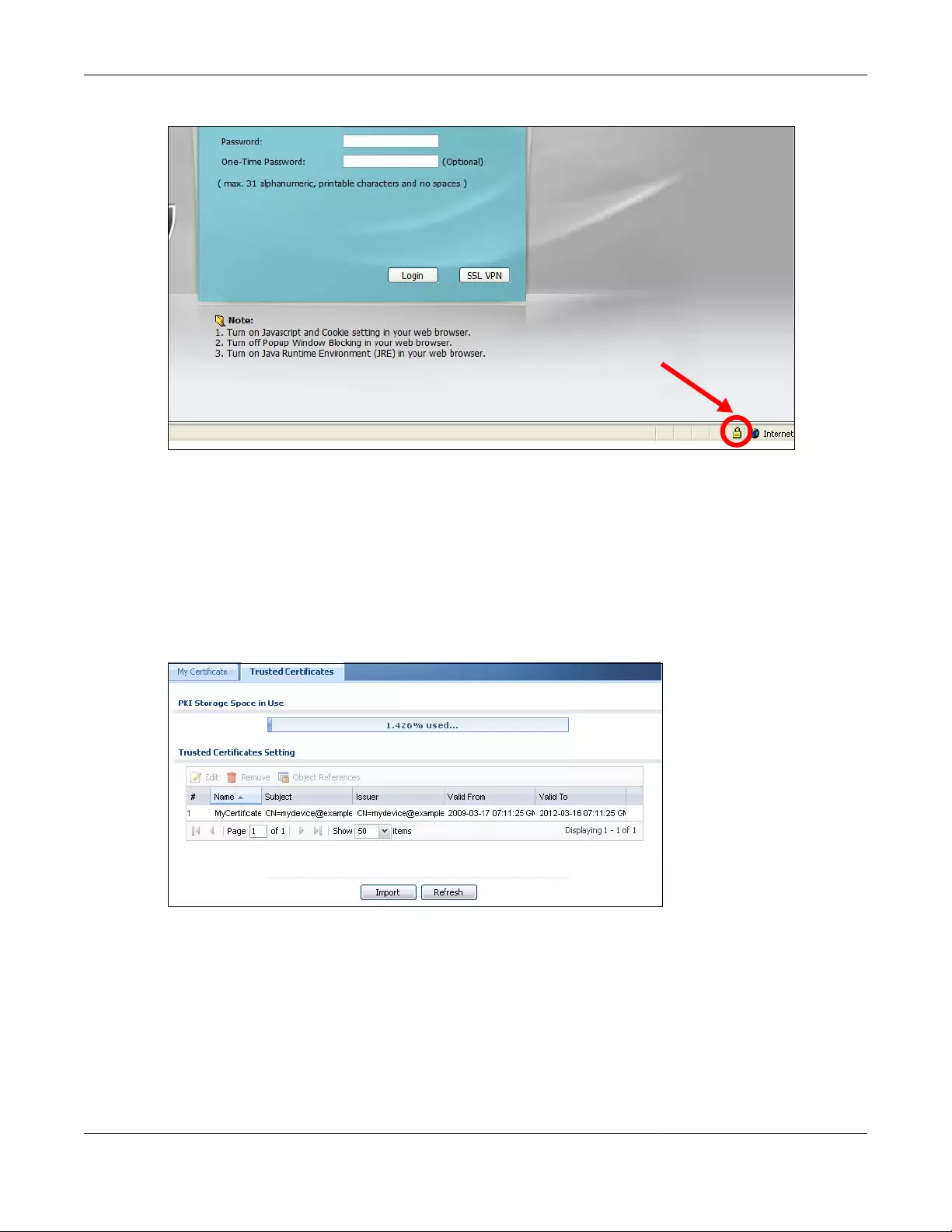
Chapter 44 System
USG/ZyWALL User’s Guide
860
Figure 611 Login Screen (Internet Explorer)
44.7.7.5 Enrolling and Importing SSL Client Certificates
The SSL client needs a certificate if Authenticate Client Certificates is selected on the Zyxel Device.
You must have imported at least one trusted CA to the Zyxel Device in order for the Authenticate Client
Certificates to be active (see the Certificates chapter for details).
Apply for a certificate from a Certification Authority (CA) that is trusted by the Zyxel Device (see the
Zyxel Device’s Trusted CA Web Configurator screen).
Figure 612 Zyxel Device Trusted CA Screen
The CA sends you a package containing the CA’s trusted certificate(s), your personal certificate(s) and
a password to install the personal certificate(s).
44.7.7.5.1 Installing the CA’s Certificate
1Double click the CA’s trusted certificate to produce a screen similar to the one shown next.
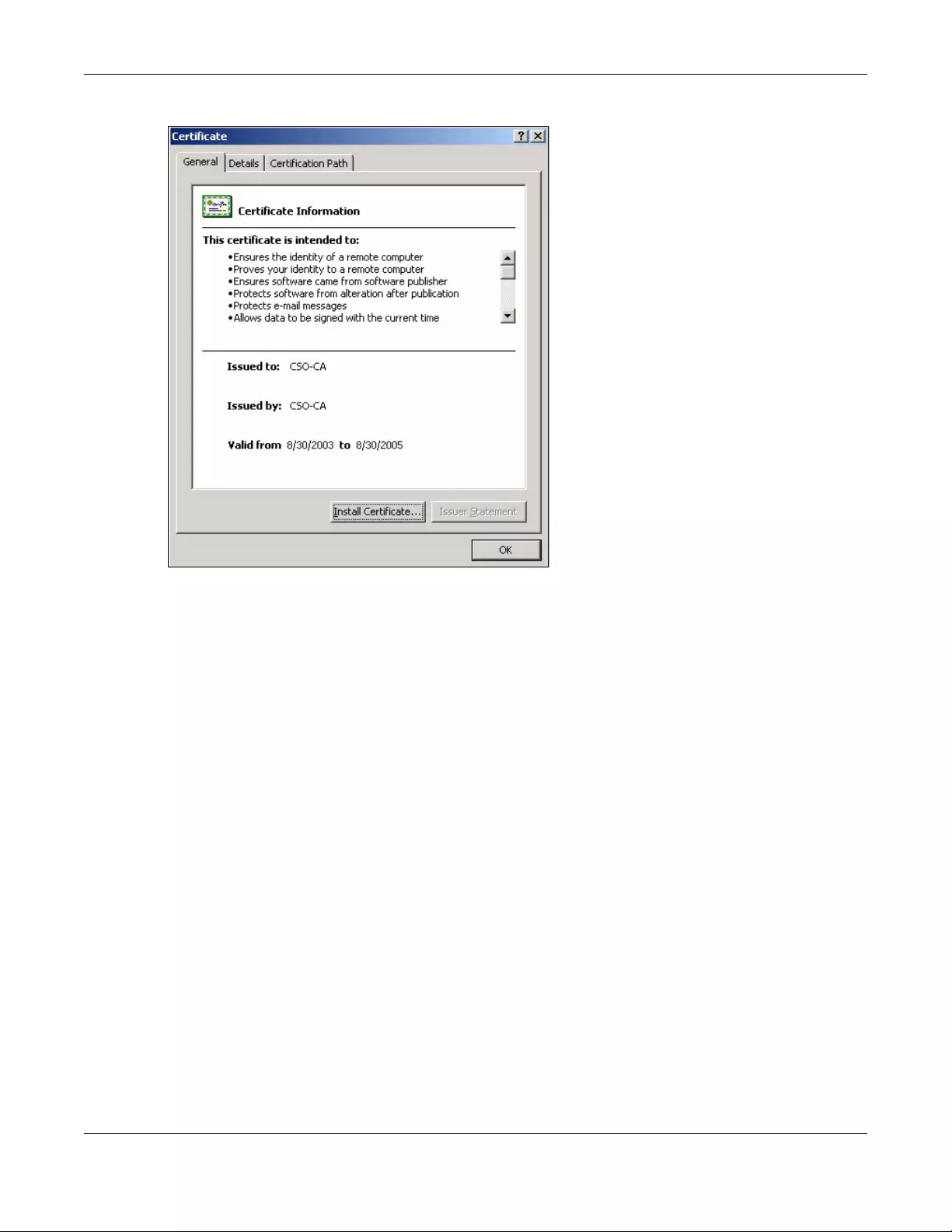
Chapter 44 System
USG/ZyWALL User’s Guide
861
Figure 613 CA Certificate Example
2Click Install Certificate and follow the wizard as shown earlier in this appendix.
44.7.7.5.2 Installing Your Personal Certificate(s)
You need a password in advance. The CA may issue the password or you may have to specify it during
the enrollment. Double-click the personal certificate given to you by the CA to produce a screen similar
to the one shown next
1Click Next to begin the wizard.
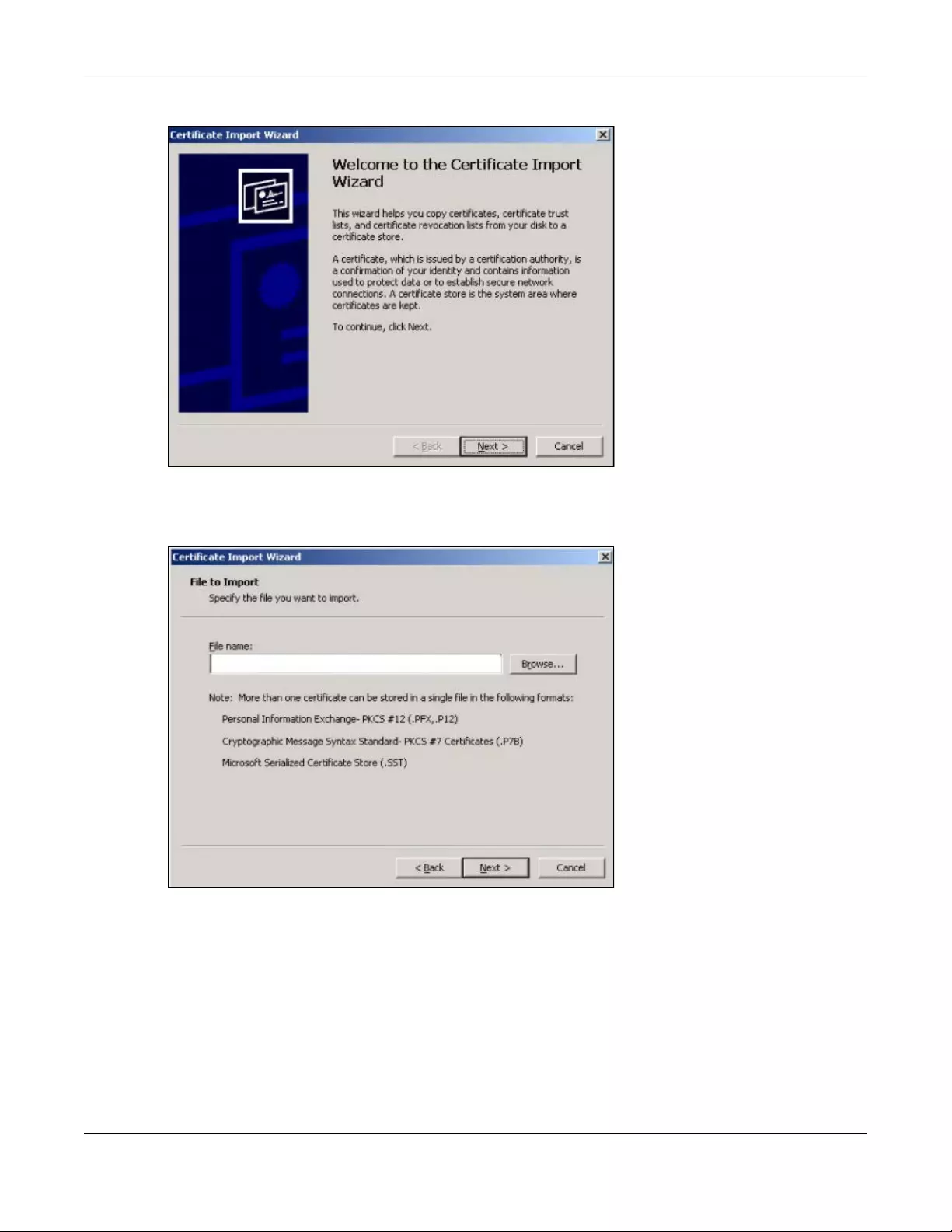
Chapter 44 System
USG/ZyWALL User’s Guide
862
Figure 614 Personal Certificate Import Wizard 1
2The file name and path of the certificate you double-clicked should automatically appear in the File
name text box. Click Browse if you wish to import a different certificate.
Figure 615 Personal Certificate Import Wizard 2
3Enter the password given to you by the CA.
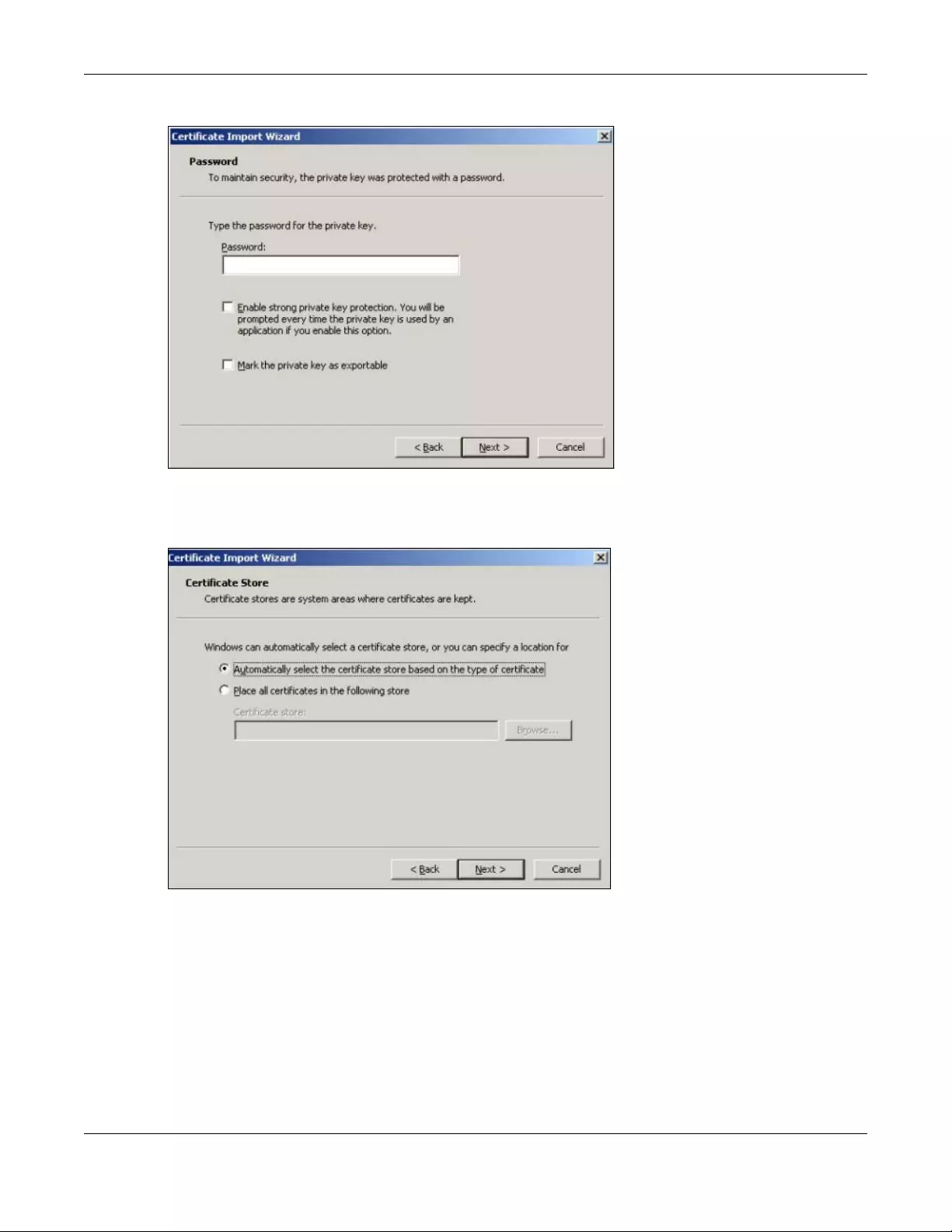
Chapter 44 System
USG/ZyWALL User’s Guide
863
Figure 616 Personal Certificate Import Wizard 3
4Have the wizard determine where the certificate should be saved on your computer or select Place all
certificates in the following store and choose a different location.
Figure 617 Personal Certificate Import Wizard 4
5Click Finish to complete the wizard and begin the import process.
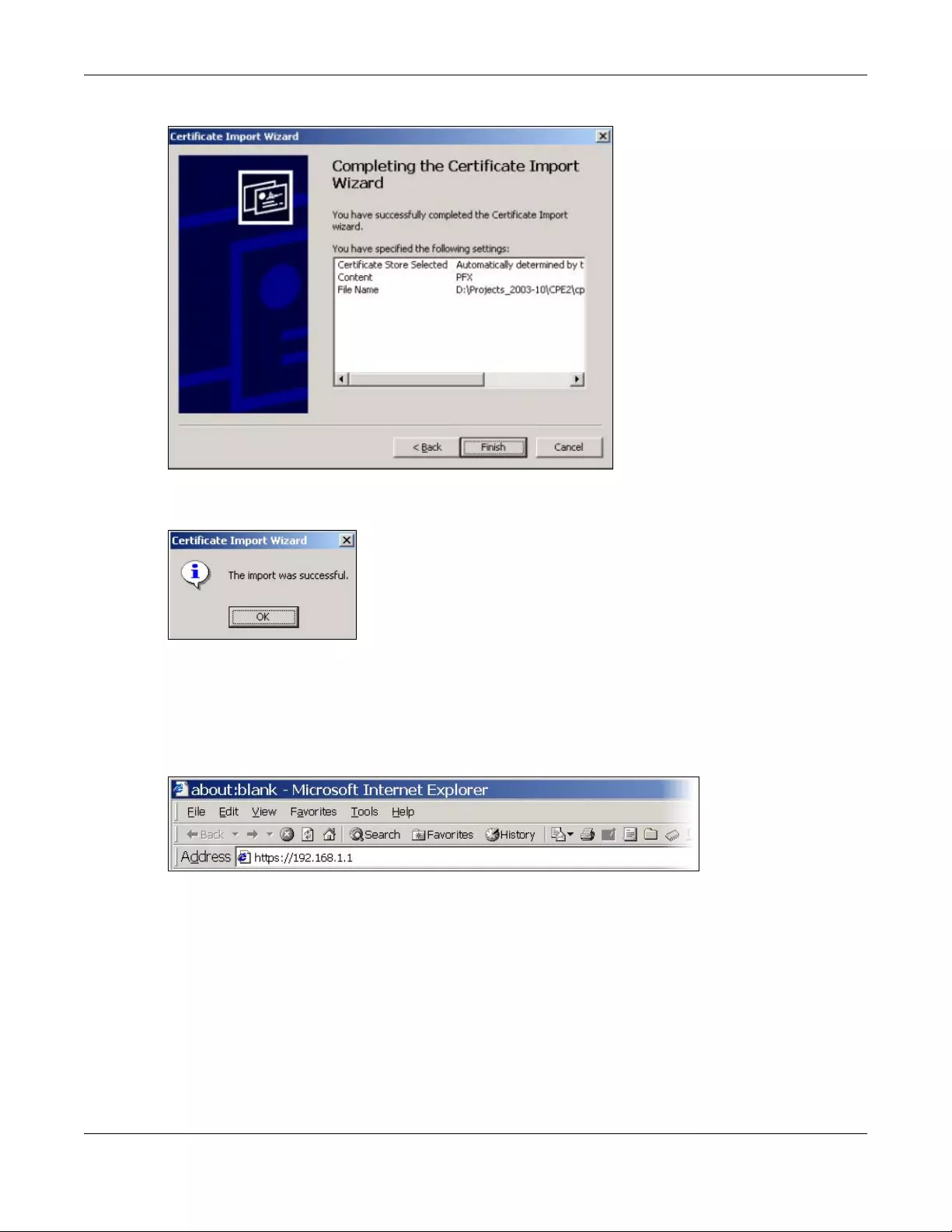
Chapter 44 System
USG/ZyWALL User’s Guide
864
Figure 618 Personal Certificate Import Wizard 5
6You should see the following screen when the certificate is correctly installed on your computer.
Figure 619 Personal Certificate Import Wizard 6
44.7.7.6 Using a Certificate When Accessing the Zyxel Device Example
Use the following procedure to access the Zyxel Device via HTTPS.
1Enter ‘https://Zyxel Device IP Address/ in your browser’s web address field.
Figure 620 Access the Zyxel Device Via HTTPS
2When Authenticate Client Certificates is selected on the Zyxel Device, the following screen asks you to
select a personal certificate to send to the Zyxel Device. This screen displays even if you only have a
single certificate as in the example.
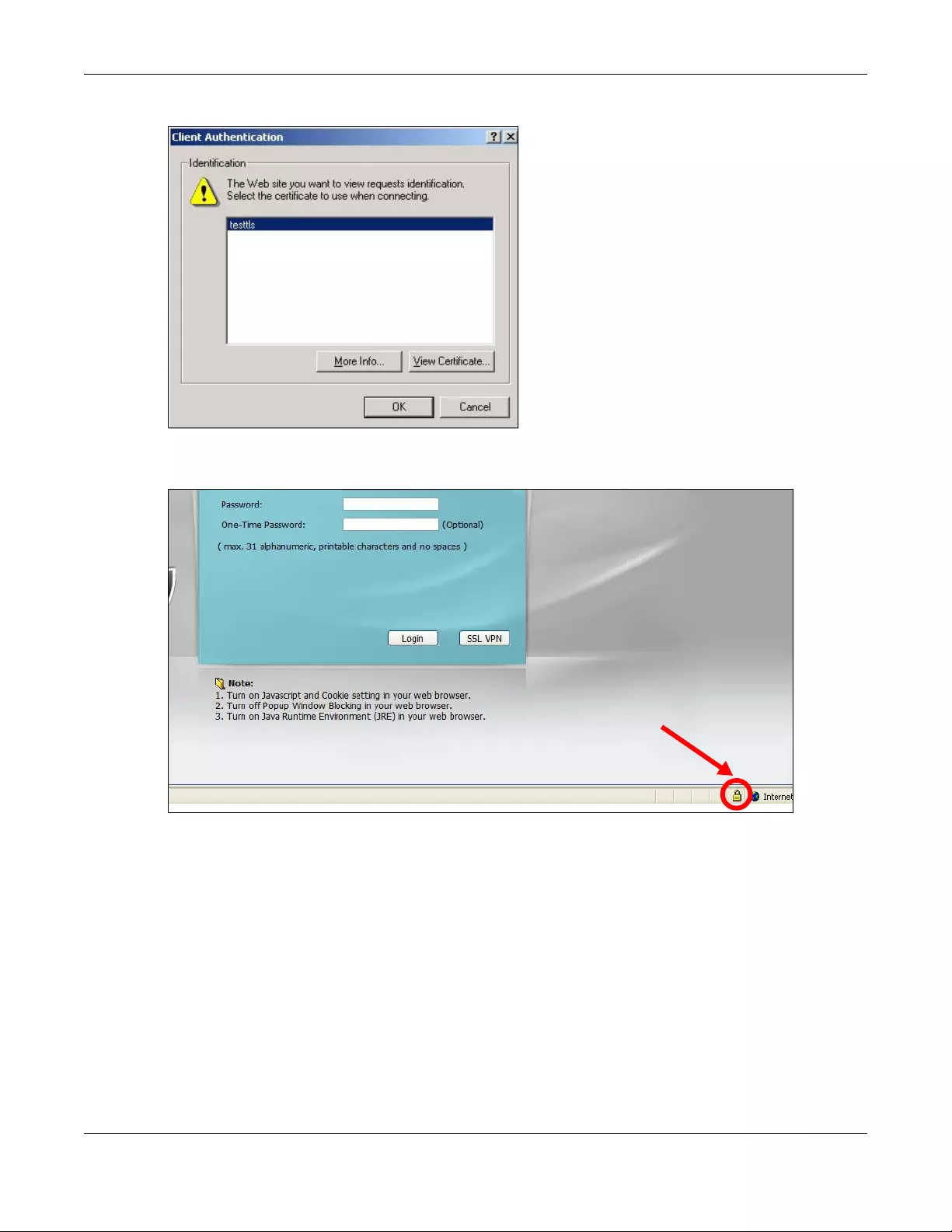
Chapter 44 System
USG/ZyWALL User’s Guide
865
Figure 621 SSL Client Authentication
3You next see the Web Configurator login screen.
Figure 622 Secure Web Configurator Login Screen
44.8 SSH
You can use SSH (Secure SHell) to securely access the Zyxel Device’s command line interface. Specify
which zones allow SSH access and from which IP address the access can come.
SSH is a secure communication protocol that combines authentication and data encryption to provide
secure encrypted communication between two hosts over an unsecured network. In the following
figure, computer A on the Internet uses SSH to securely connect to the WAN port of the Zyxel Device for
a management session.
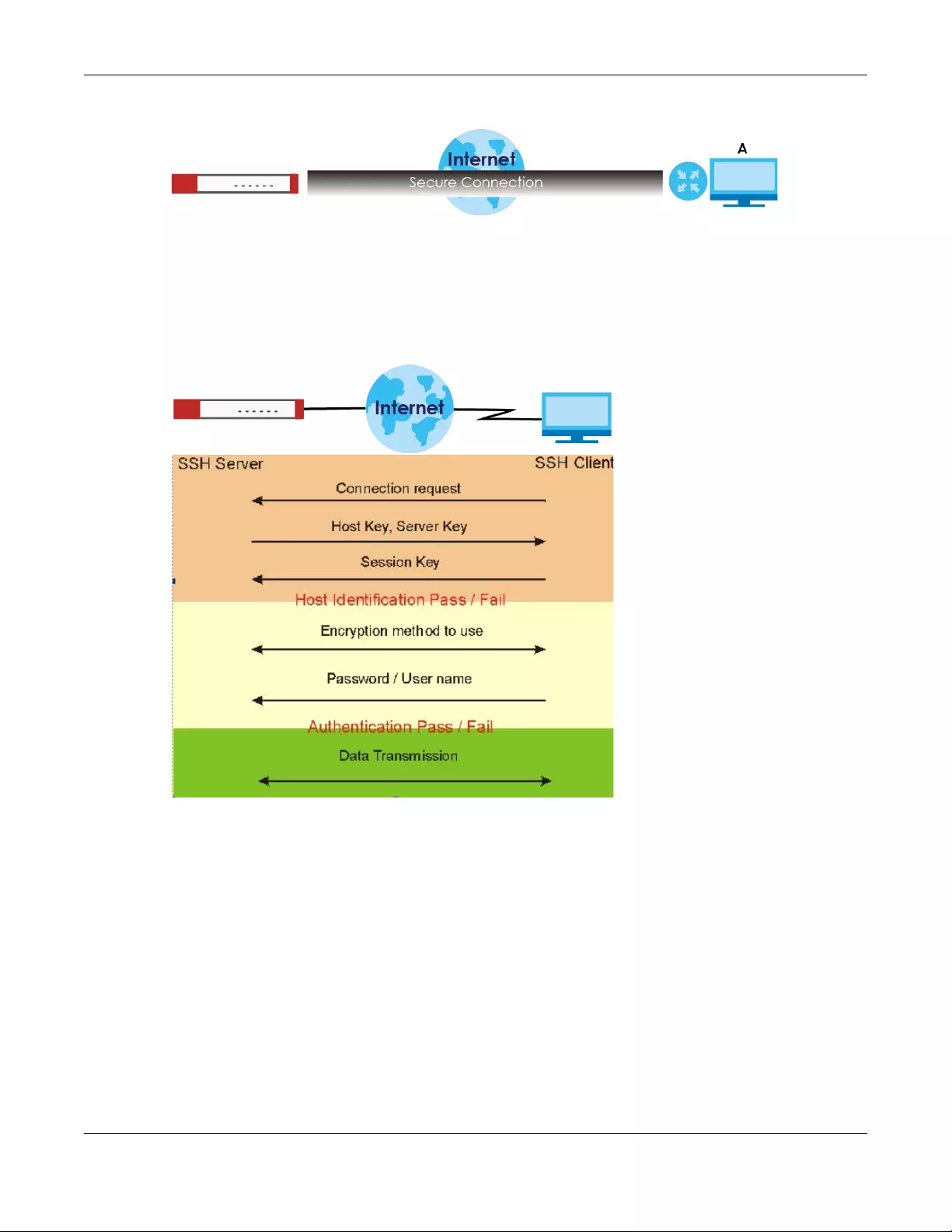
Chapter 44 System
USG/ZyWALL User’s Guide
866
Figure 623 SSH Communication Over the WAN Example
44.8.1 How SSH Works
The following figure is an example of how a secure connection is established between two remote hosts
using SSH v1.
Figure 624 How SSH v1 Works Example
1Host Identification
The SSH client sends a connection request to the SSH server. The server identifies itself with a host key. The
client encrypts a randomly generated session key with the host key and server key and sends the result
back to the server.
The client automatically saves any new server public keys. In subsequent connections, the server public
key is checked against the saved version on the client computer.
2Encryption Method
Once the identification is verified, both the client and server must agree on the type of encryption
method to use.
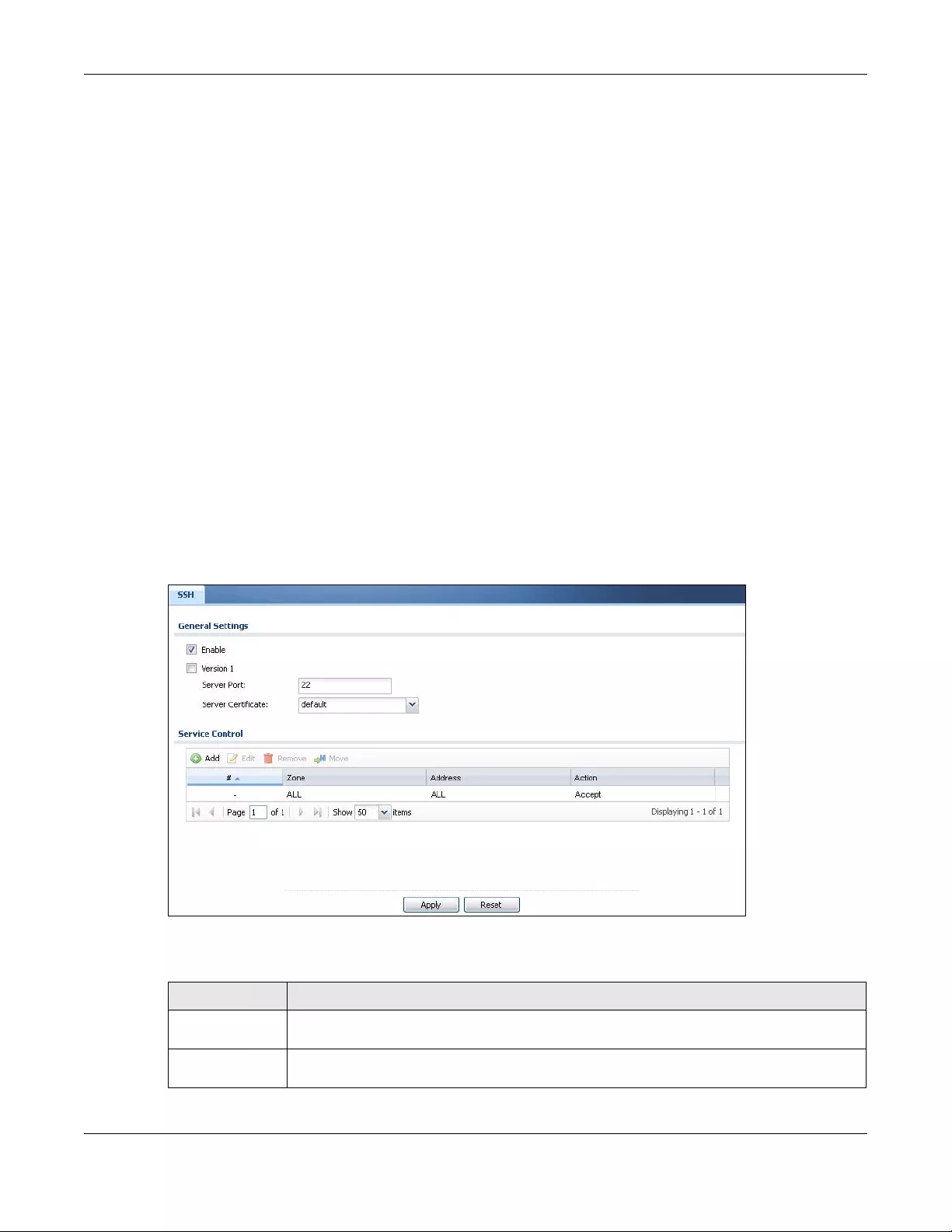
Chapter 44 System
USG/ZyWALL User’s Guide
867
3Authentication and Data Transmission
After the identification is verified and data encryption activated, a secure tunnel is established between
the client and the server. The client then sends its authentication information (user name and password)
to the server to log in to the server.
44.8.2 SSH Implementation on the Zyxel Device
Your Zyxel Device supports SSH versions 1 and 2 using RSA authentication and four encryption methods
(AES, 3DES, Archfour, and Blowfish). The SSH server is implemented on the Zyxel Device for management
using port 22 (by default).
44.8.3 Requirements for Using SSH
You must install an SSH client program on a client computer (Windows or Linux operating system) that is
used to connect to the Zyxel Device over SSH.
44.8.4 Configuring SSH
Click Configuration > System > SSH to change your Zyxel Device’s Secure Shell settings. Use this screen to
specify from which zones SSH can be used to manage the Zyxel Device. You can also specify from
which IP addresses the access can come.
Figure 625 Configuration > System > SSH
The following table describes the labels in this screen.
Table 362 Configuration > System > SSH
LABEL DESCRIPTION
Enable Select the check box to allow or disallow the computer with the IP address that matches the IP
address(es) in the Service Control table to access the Zyxel Device CLI using this service.
Version 1 Select the check box to have the Zyxel Device use both SSH version 1 and version 2 protocols.
If you clear the check box, the Zyxel Device uses only SSH version 2 protocol.
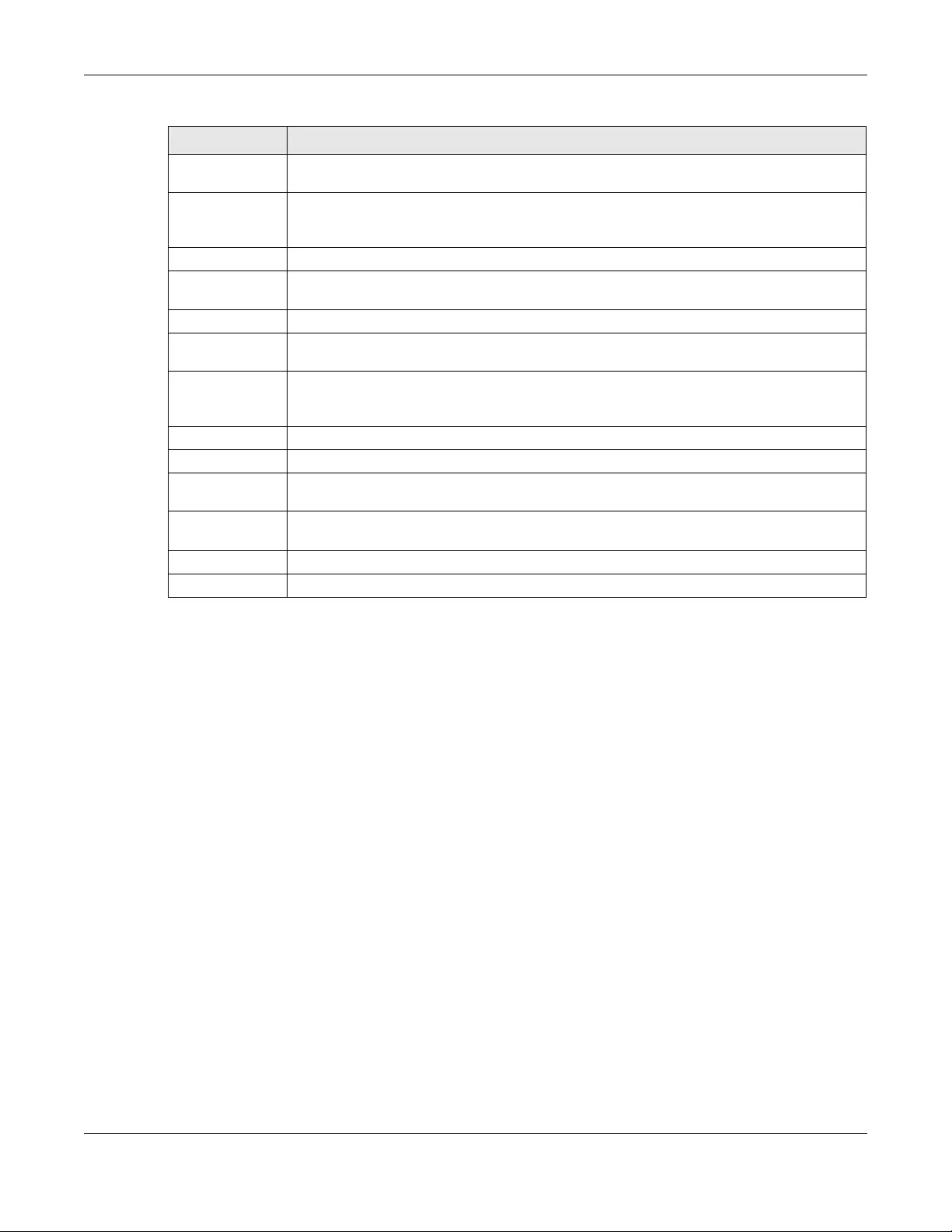
Chapter 44 System
USG/ZyWALL User’s Guide
868
44.8.5 Secure Telnet Using SSH Examples
This section shows two examples using a command interface and a graphical interface SSH client
program to remotely access the Zyxel Device. The configuration and connection steps are similar for
most SSH client programs. Refer to your SSH client program user’s guide.
44.8.5.1 Example 1: Microsoft Windows
This section describes how to access the Zyxel Device using the Secure Shell Client program.
1Launch the SSH client and specify the connection information (IP address, port number) for the Zyxel
Device.
2Configure the SSH client to accept connection using SSH version 1.
3A window displays prompting you to store the host key in you computer. Click Yes to continue.
Server Port You may change the server port number for a service if needed, however you must use the
same port number in order to use that service for remote management.
Server Certificate Select the certificate whose corresponding private key is to be used to identify the Zyxel
Device for SSH connections. You must have certificates already configured in the My
Certificates screen.
Service Control This specifies from which computers you can access which Zyxel Device zones.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after the
selected entry. Refer to Table 360 on page 853 for details on the screen that opens.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so. Note that subsequent entries move up by one when you take this action.
Move To change an entry’s position in the numbered list, select the method and click Move to
display a field to type a number for where you want to put it and press [ENTER] to move the rule
to the number that you typed.
#This the index number of the service control rule.
Zone This is the zone on the Zyxel Device the user is allowed or denied to access.
Address This is the object name of the IP address(es) with which the computer is allowed or denied to
access.
Action This displays whether the computer with the IP address specified above can access the Zyxel
Device zone(s) configured in the Zone field (Accept) or not (Deny).
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 362 Configuration > System > SSH (continued)
LABEL DESCRIPTION
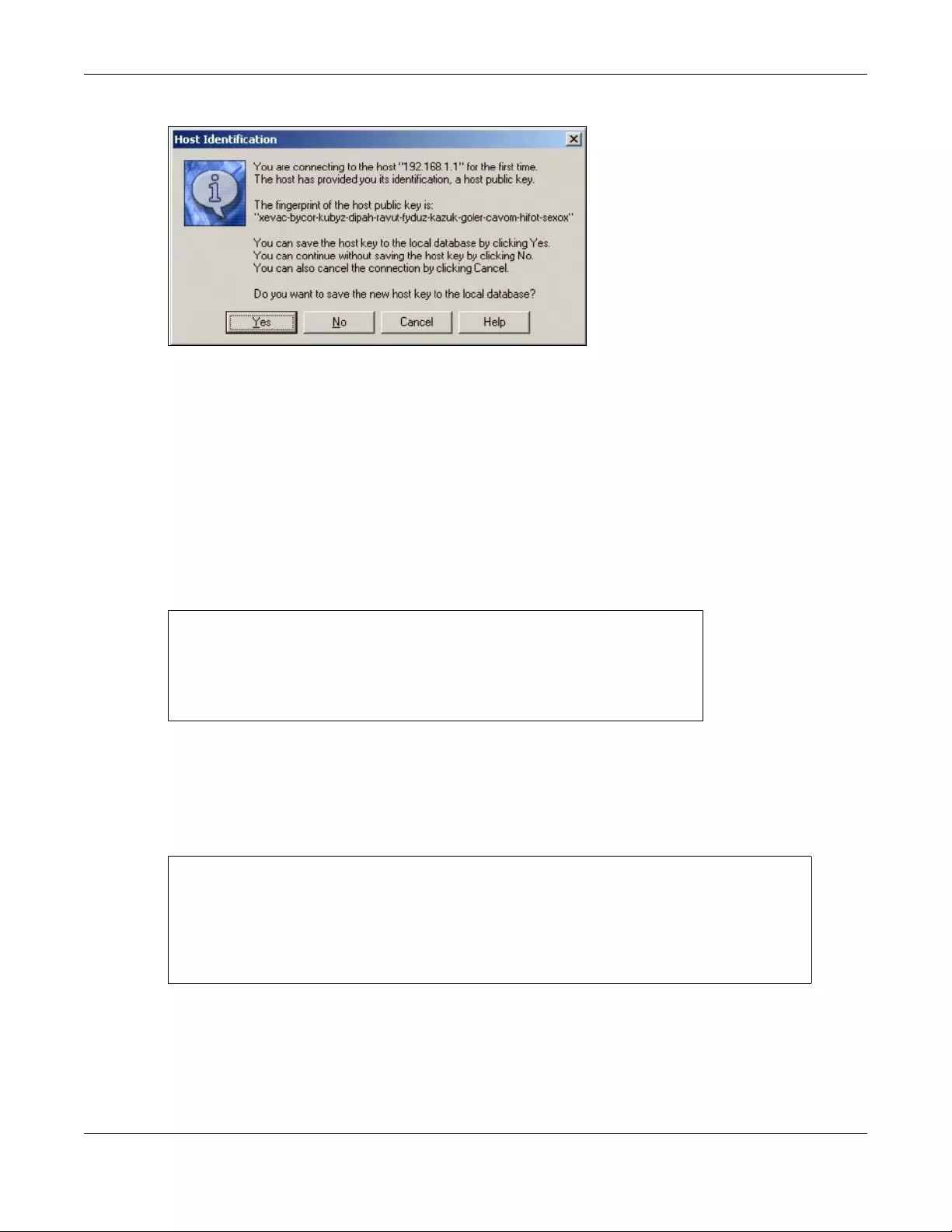
Chapter 44 System
USG/ZyWALL User’s Guide
869
Figure 626 SSH Example 1: Store Host Key
Enter the password to log in to the Zyxel Device. The CLI screen displays next.
44.8.5.2 Example 2: Linux
This section describes how to access the Zyxel Device using the OpenSSH client program that comes
with most Linux distributions.
1Test whether the SSH service is available on the Zyxel Device.
Enter “telnet 192.168.1.1 22” at a terminal prompt and press [ENTER]. The computer attempts to
connect to port 22 on the Zyxel Device (using the default IP address of 192.168.1.1).
A message displays indicating the SSH protocol version supported by the Zyxel Device.
Figure 627 SSH Example 2: Test
2Enter “ssh –1 192.168.1.1”. This command forces your computer to connect to the Zyxel Device
using SSH version 1. If this is the first time you are connecting to the Zyxel Device using SSH, a message
displays prompting you to save the host information of the Zyxel Device. Type “yes” and press [ENTER].
Then enter the password to log in to the Zyxel Device.
Figure 628 SSH Example 2: Log in
3The CLI screen displays next.
$ telnet 192.168.1.1 22
Trying 192.168.1.1...
Connected to 192.168.1.1.
Escape character is '^]'.
SSH-1.5-1.0.0
$ ssh –1 192.168.1.1
The authenticity of host '192.168.1.1 (192.168.1.1)' can't be established.
RSA1 key fingerprint is 21:6c:07:25:7e:f4:75:80:ec:af:bd:d4:3d:80:53:d1.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added '192.168.1.1' (RSA1) to the list of known hosts.
Administrator@192.168.1.1's password:
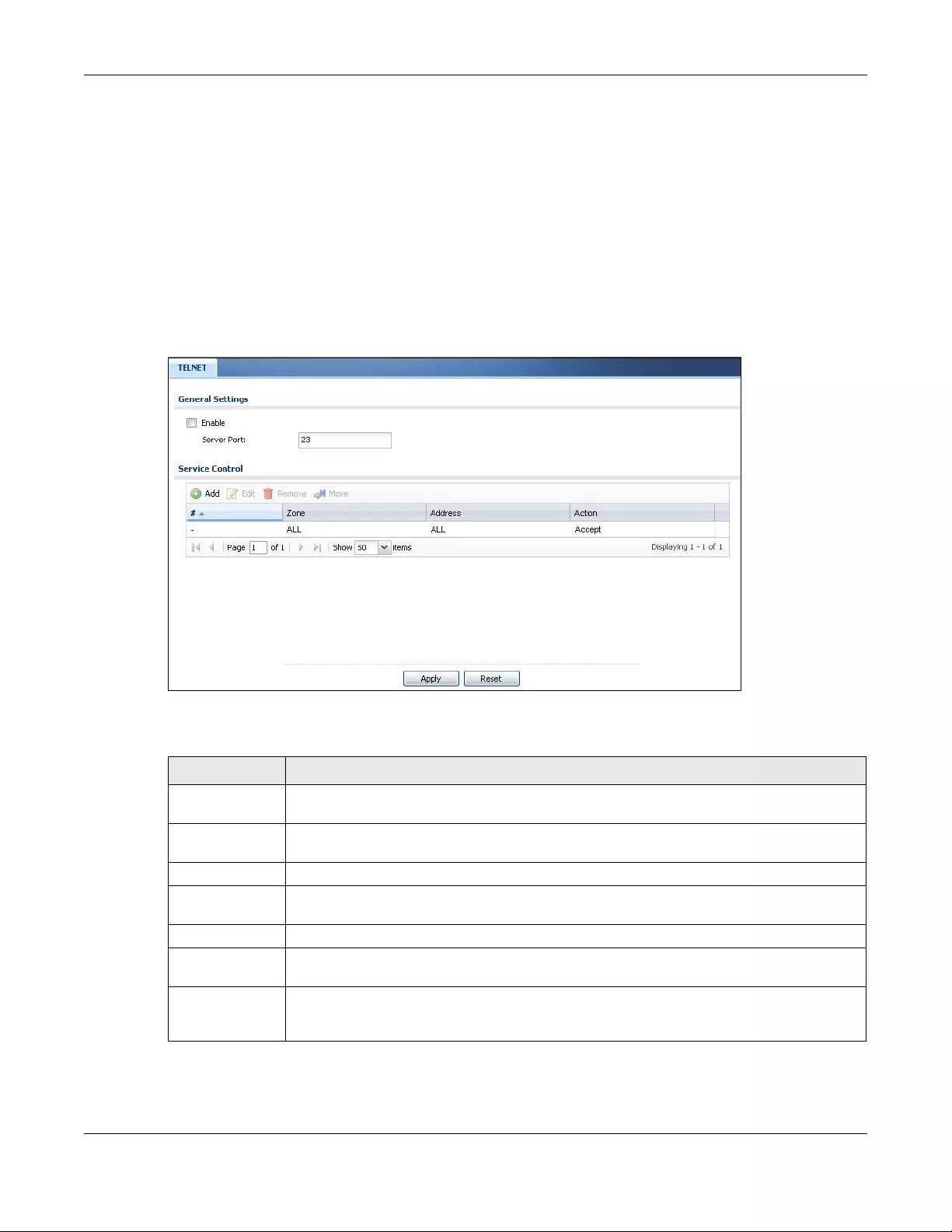
Chapter 44 System
USG/ZyWALL User’s Guide
870
44.9 Telnet
You can use Telnet to access the Zyxel Device’s command line interface. Specify which zones allow
Telnet access and from which IP address the access can come.
44.9.1 Configuring Telnet
Click Configuration > System > TELNET to configure your Zyxel Device for remote Telnet access. Use this
screen to specify from which zones Telnet can be used to manage the Zyxel Device. You can also
specify from which IP addresses the access can come.
Figure 629 Configuration > System > TELNET
The following table describes the labels in this screen.
Table 363 Configuration > System > TELNET
LABEL DESCRIPTION
Enable Select the check box to allow or disallow the computer with the IP address that matches the IP
address(es) in the Service Control table to access the Zyxel Device CLI using this service.
Server Port You may change the server port number for a service if needed, however you must use the
same port number in order to use that service for remote management.
Service Control This specifies from which computers you can access which Zyxel Device zones.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after the
selected entry. Refer to Table 360 on page 853 for details on the screen that opens.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so. Note that subsequent entries move up by one when you take this action.
Move To change an entry’s position in the numbered list, select the method and click Move to display
a field to type a number for where you want to put it and press [ENTER] to move the rule to the
number that you typed.
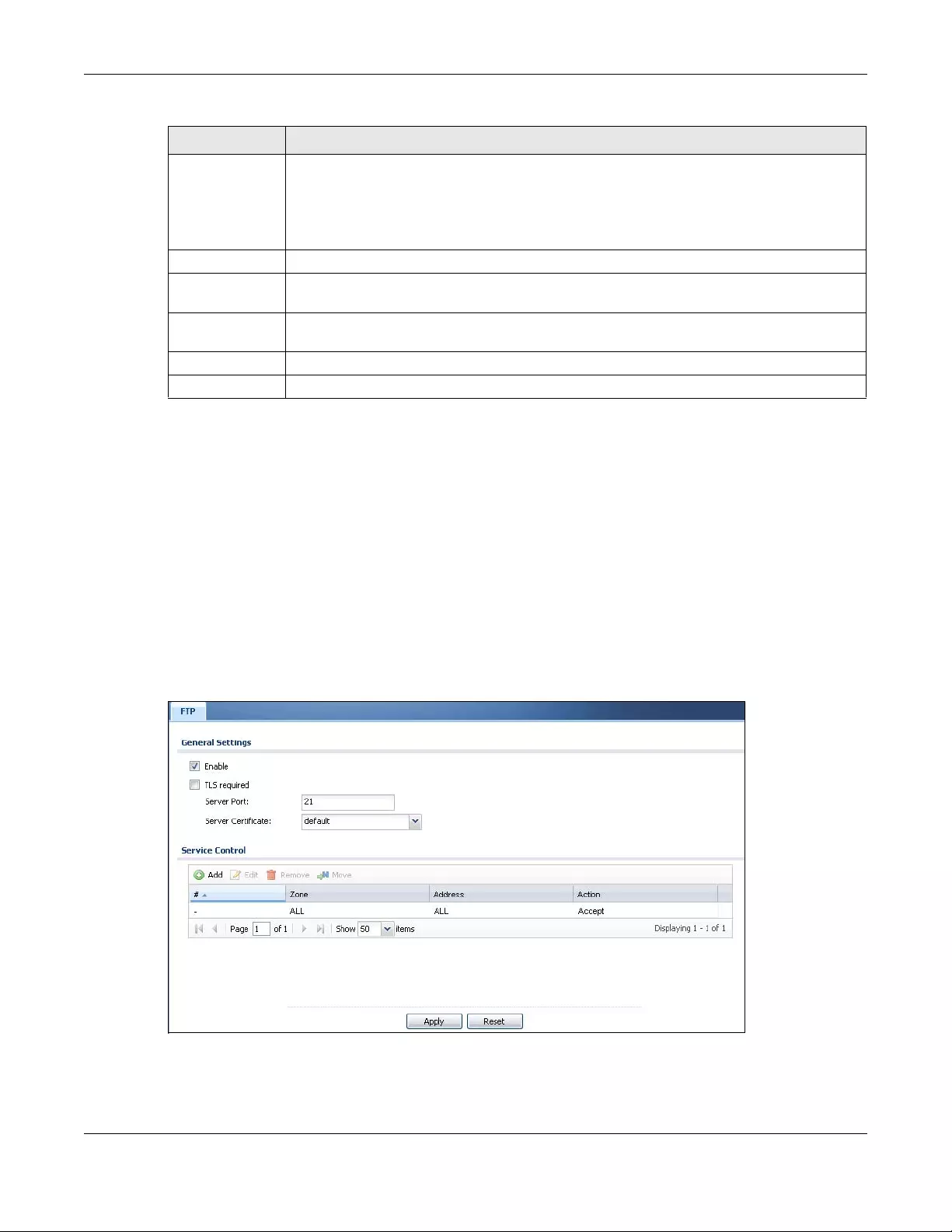
Chapter 44 System
USG/ZyWALL User’s Guide
871
44.10 FTP
You can upload and download the Zyxel Device’s firmware and configuration files using FTP. To use this
feature, your computer must have an FTP client.
44.10.1 Configuring FTP
To change your Zyxel Device’s FTP settings, click Configuration > System > FTP tab. The screen appears
as shown. Use this screen to specify from which zones FTP can be used to access the Zyxel Device. You
can also specify from which IP addresses the access can come.
Figure 630 Configuration > System > FTP
#This the index number of the service control rule.
The entry with a hyphen (-) instead of a number is the Zyxel Device’s (non-configurable) default
policy. The Zyxel Device applies this to traffic that does not match any other configured rule. It
is not an editable rule. To apply other behavior, configure a rule that traffic will match so the
Zyxel Device will not have to use the default policy.
Zone This is the zone on the Zyxel Device the user is allowed or denied to access.
Address This is the object name of the IP address(es) with which the computer is allowed or denied to
access.
Action This displays whether the computer with the IP address specified above can access the Zyxel
Device zone(s) configured in the Zone field (Accept) or not (Deny).
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 363 Configuration > System > TELNET (continued)
LABEL DESCRIPTION
Chapter 44 System
USG/ZyWALL User’s Guide
872
The following table describes the labels in this screen.
44.11 SNMP
Simple Network Management Protocol is a protocol used for exchanging management information
between network devices. Your Zyxel Device supports SNMP agent functionality, which allows a
manager station to manage and monitor the Zyxel Device through the network. The Zyxel Device
supports SNMP version one (SNMPv1), version two (SNMPv2c) and version 3 (SNMPv3). The next figure
illustrates an SNMP management operation.
Table 364 Configuration > System > FTP
LABEL DESCRIPTION
Enable Select the check box to allow or disallow the computer with the IP address that matches the IP
address(es) in the Service Control table to access the Zyxel Device using this service.
TLS required Select the check box to use FTP over TLS (Transport Layer Security) to encrypt communication.
This implements TLS as a security mechanism to secure FTP clients and/or servers.
Server Port You may change the server port number for a service if needed, however you must use the
same port number in order to use that service for remote management.
Server Certificate Select the certificate whose corresponding private key is to be used to identify the Zyxel Device
for FTP connections. You must have certificates already configured in the My Certificates
screen.
Service Control This specifies from which computers you can access which Zyxel Device zones.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after the
selected entry. Refer to Table 360 on page 853 for details on the screen that opens.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so. Note that subsequent entries move up by one when you take this action.
Move To change an entry’s position in the numbered list, select the method and click Move to display
a field to type a number for where you want to put it and press [ENTER] to move the rule to the
number that you typed.
#This the index number of the service control rule.
The entry with a hyphen (-) instead of a number is the Zyxel Device’s (non-configurable) default
policy. The Zyxel Device applies this to traffic that does not match any other configured rule. It
is not an editable rule. To apply other behavior, configure a rule that traffic will match so the
Zyxel Device will not have to use the default policy.
Zone This is the zone on the Zyxel Device the user is allowed or denied to access.
Address This is the object name of the IP address(es) with which the computer is allowed or denied to
access.
Action This displays whether the computer with the IP address specified above can access the Zyxel
Device zone(s) configured in the Zone field (Accept) or not (Deny).
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
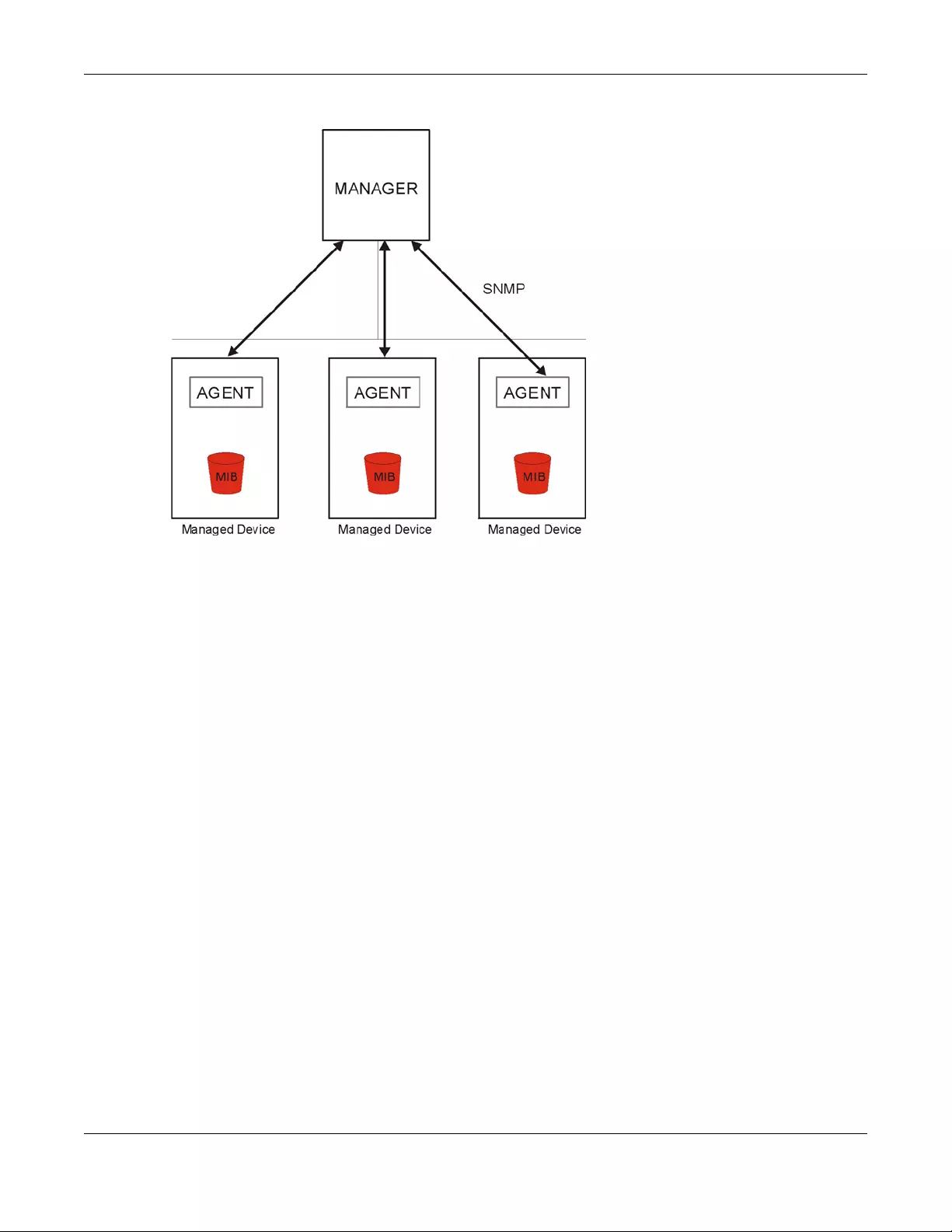
Chapter 44 System
USG/ZyWALL User’s Guide
873
Figure 631 SNMP Management Model
An SNMP managed network consists of two main types of component: agents and a manager.
An agent is a management software module that resides in a managed device (the Zyxel Device). An
agent translates the local management information from the managed device into a form compatible
with SNMP. The manager is the console through which network administrators perform network
management functions. It executes applications that control and monitor managed devices.
The managed devices contain object variables/managed objects that define each piece of
information to be collected about a device. Examples of variables include such as number of packets
received, node port status etc. A Management Information Base (MIB) is a collection of managed
objects. SNMP allows a manager and agents to communicate for the purpose of accessing these
objects.
SNMP itself is a simple request/response protocol based on the manager/agent model. The manager
issues a request and the agent returns responses using the following protocol operations:
• Get - Allows the manager to retrieve an object variable from the agent.
• GetNext - Allows the manager to retrieve the next object variable from a table or list within an agent.
In SNMPv1, when a manager wants to retrieve all elements of a table from an agent, it initiates a Get
operation, followed by a series of GetNext operations.
• Set - Allows the manager to set values for object variables within an agent.
• Trap - Used by the agent to inform the manager of some events.
44.11.1 SNMPv3 and Security
SNMPv3 enhances security for SNMP management using authentication and encryption. SNMP
managers can be required to authenticate with agents before conducting SNMP management
sessions.

Chapter 44 System
USG/ZyWALL User’s Guide
874
Security can be further enhanced by encrypting the SNMP messages sent from the managers.
Encryption protects the contents of the SNMP messages. When the contents of the SNMP messages are
encrypted, only the intended recipients can read them.
44.11.2 Supported MIBs
The Zyxel Device supports MIB II that is defined in RFC-1213 and RFC-1215. The Zyxel Device also supports
private MIBs (zywall.mib and zyxel-zywall-ZLD-Common.mib) to collect information about CPU and
memory usage and VPN total throughput. The focus of the MIBs is to let administrators collect statistical
data and monitor status and performance. You can download the Zyxel Device’s MIBs from
www.zyxel.com.
44.11.3 SNMP Traps
The Zyxel Device will send traps to the SNMP manager when any one of the following events occurs.
44.11.4 Configuring SNMP
To change your Zyxel Device’s SNMP settings, click Configuration > System > SNMP tab. The screen
appears as shown. Use this screen to configure your SNMP settings, including from which zones SNMP
can be used to access the Zyxel Device. You can also specify from which IP addresses the access can
come.
Table 365 SNMP Traps
OBJECT LABEL OBJECT ID DESCRIPTION
Cold Start 1.3.6.1.6.3.1.1.5.1 This trap is sent when the Zyxel Device is turned on or
an agent restarts.
linkDown 1.3.6.1.6.3.1.1.5.3 This trap is sent when the Ethernet link is down.
linkUp 1.3.6.1.6.3.1.1.5.4 This trap is sent when the Ethernet link is up.
authenticationFailure 1.3.6.1.6.3.1.1.5.5 This trap is sent when an SNMP request comes from
non-authenticated hosts.
vpnTunnelDisconnected 1.3.6.1.4.1.890.1.6.22.2.3 This trap is sent when an IPSec VPN tunnel is
disconnected.
vpnTunnelName 1.3.6.1.4.1.890.1.6.22.2.2.1.1 This trap is sent along with the
vpnTunnelDisconnected trap. This trap carries the
disconnected tunnel’s IPSec SA name.
vpnIKEName 1.3.6.1.4.1.890.1.6.22.2.2.1.2 This trap is sent along with the
vpnTunnelDisconnected trap. This trap carries the
disconnected tunnel’s IKE SA name.
vpnTunnelSPI 1.3.6.1.4.1.890.1.6.22.2.2.1.3 This trap is sent along with the
vpnTunnelDisconnected trap. This trap carries the
security parameter index (SPI) of the disconnected
VPN tunnel.
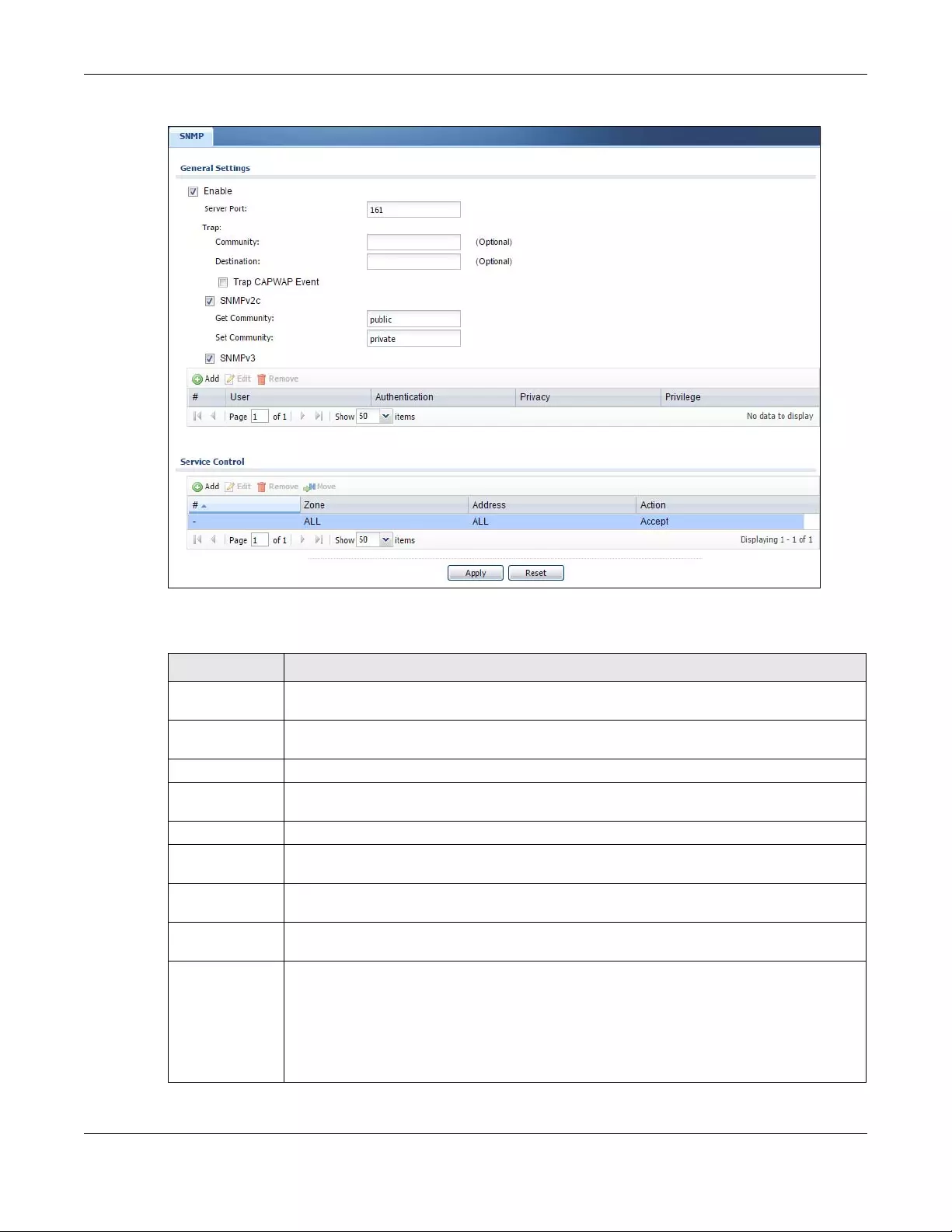
Chapter 44 System
USG/ZyWALL User’s Guide
875
Figure 632 Configuration > System > SNMP
The following table describes the labels in this screen.
Table 366 Configuration > System > SNMP
LABEL DESCRIPTION
Enable Select the check box to allow or disallow the computer with the IP address that matches the IP
address(es) in the Service Control table to access the Zyxel Device using this service.
Server Port You may change the server port number for a service if needed, however you must use the
same port number in order to use that service for remote management.
Trap
Community Type the trap community, which is the password sent with each trap to the SNMP manager. The
default is public and allows all requests.
Destination Type the IP address of the station to send your SNMP traps to.
SNMPv2c Select the SNMP version for the Zyxel Device. The SNMP version on the Zyxel Device must match
the version on the SNMP manager.
Get
Community Enter the Get Community, which is the password for the incoming Get and GetNext requests
from the management station. The default is public and allows all requests.
Set
Community Enter the Set community, which is the password for incoming Set requests from the
management station. The default is private and allows all requests.
SNMPv3 Select the SNMP version for the Zyxel Device. The SNMP version on the Zyxel Device must match
the version on the SNMP manager. SNMPv3 (RFCs 3413 to 3415) provides secure access by
authenticating and encrypting data packets over the network. The Zyxel Device uses your login
password as the SNMPv3 authentication and encryption passphrase.
Note: Your login password must consist of at least 8 printable characters for SNMPv3.
An error message will display if your login password has fewer characters.
Chapter 44 System
USG/ZyWALL User’s Guide
876
44.11.5 Add SNMPv3 User
Click Add under SNMPv3 in Configuration > System > SNMP to create an SNMPv3 user for authentication
with managers using SNMP v3. Use the username and password of the login accounts you specify in this
screen to create accounts on the SNMP v3 manager.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after the
selected entry
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so. Note that subsequent entries move up by one when you take this action.
#This is the index number of the entry.
User This displays the name of the user object to be sent to the SNMP manager along with the SNMP
v3 trap.
Authenticati
on This displays the authentication algorithm used for this entry. MD5 (Message Digest 5) and SHA
(Secure Hash Algorithm) are hash algorithms used to authenticate SNMP data. SHA
authentication is generally considered stronger than MD5, but is slower.
Privacy This displays the encryption method for SNMP communication from this user. Methods available
are:
•DES - Data Encryption Standard is a widely used (but breakable) method of data
encryption. It applies a 56-bit key to each 64-bit block of data.
•AES - Advanced Encryption Standard is another method for data encryption that also uses
a secret key. AES applies a 128-bit key to 128-bit blocks of data.
Privilege This displays the access rights to MIBs.
•Read-Write - The associated user can create and edit the MIBs on the Zyxel Device, except
the user account.
•Read-Only - The associated user can only collect information from the Zyxel Device MIBs.
Service Control This specifies from which computers you can access which Zyxel Device zones.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after the
selected entry. Refer to Table 360 on page 853 for details on the screen that opens.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so. Note that subsequent entries move up by one when you take this action.
Move To change an entry’s position in the numbered list, select the method and click Move to display
a field to type a number for where you want to put it and press [ENTER] to move the rule to the
number that you typed.
#This the index number of the service control rule.
The entry with a hyphen (-) instead of a number is the Zyxel Device’s (non-configurable) default
policy. The Zyxel Device applies this to traffic that does not match any other configured rule. It is
not an editable rule. To apply other behavior, configure a rule that traffic will match so the Zyxel
Device will not have to use the default policy.
Zone This is the zone on the Zyxel Device the user is allowed or denied to access.
Address This is the object name of the IP address(es) with which the computer is allowed or denied to
access.
Action This displays whether the computer with the IP address specified above can access the Zyxel
Device zone(s) configured in the Zone field (Accept) or not (Deny).
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 366 Configuration > System > SNMP (continued)
LABEL DESCRIPTION
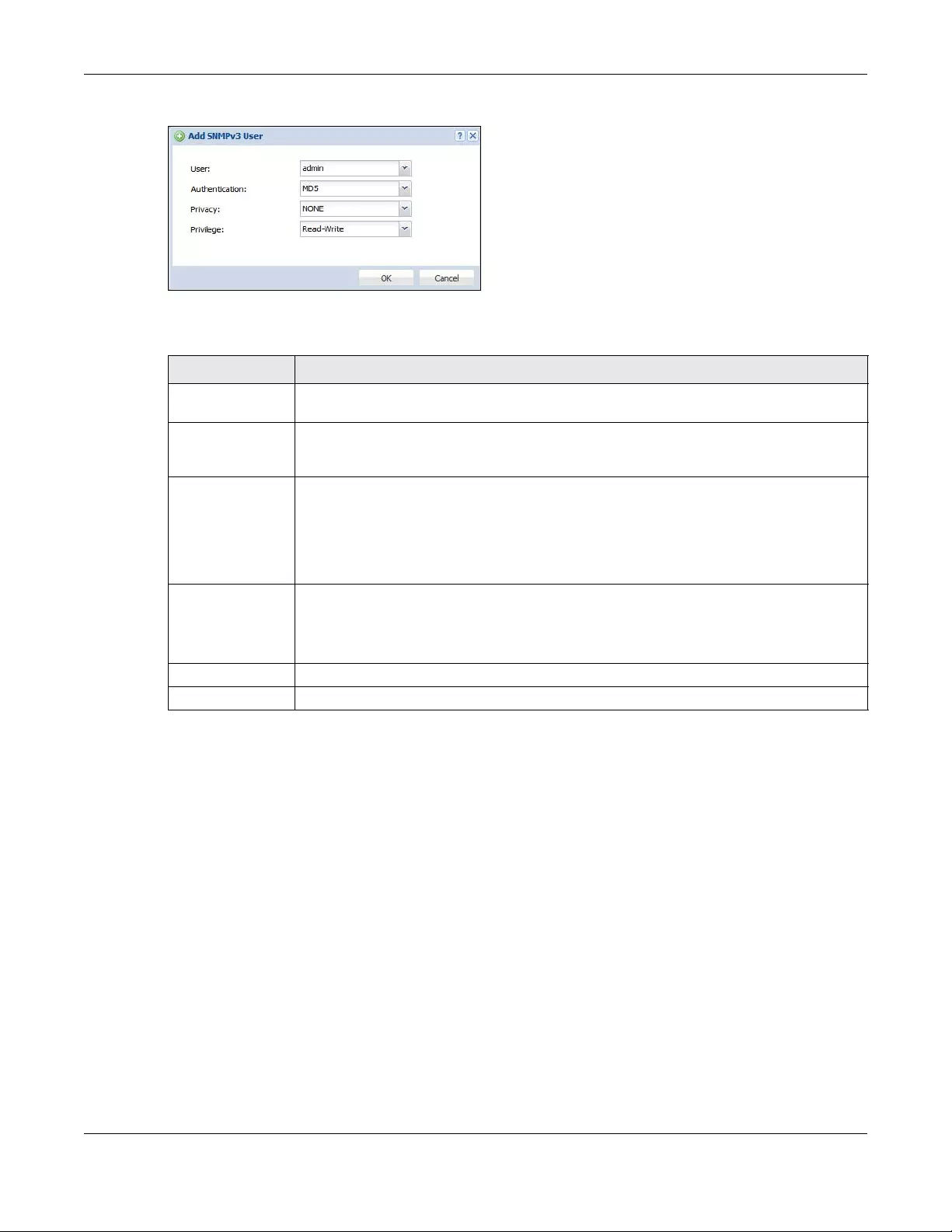
Chapter 44 System
USG/ZyWALL User’s Guide
877
Figure 633 Configuration > System > SNMP(v3) > Add
The following table describes the labels in this screen.
44.12 Authentication Server
You can set the Zyxel Device to work as a RADIUS server to exchange messages with a RADIUS client,
such as an AP for user authentication and authorization. Click Configuration > System > Auth. Server tab.
The screen appears as shown. Use this screen to enable the authentication server feature of the Zyxel
Device and specify the RADIUS client’s IP address.
Table 367 Configuration > System > SNMP(v3) > Add
LABEL DESCRIPTION
User Specify the username of a login account on the Zyxel Device. The associated password is
used in authentication algorithms and encryption methods.
Authentication Select an authentication algorithm. MD5 (Message Digest 5) and SHA (Secure Hash
Algorithm) are hash algorithms used to authenticate SNMP data. SHA authentication is
generally considered stronger than MD5, but is slower.
Privacy Specify the encryption method for SNMP communication from this user. You can choose one
of the following:
•DES - Data Encryption Standard is a widely used (but breakable) method of data
encryption. It applies a 56-bit key to each 64-bit block of data.
•AES - Advanced Encryption Standard is another method for data encryption that also
uses a secret key. AES applies a 128-bit key to 128-bit blocks of data.
Privilege Select the access rights to MIBs.
•Read-Write - The associated user can create and edit the MIBs on the Zyxel Device,
except the user account.
•Read-Only - The associated user can only collect information from the Zyxel Device MIBs.
OK Click OK to save the changes.
Cancel Click Cancel to begin configuring this screen afresh.
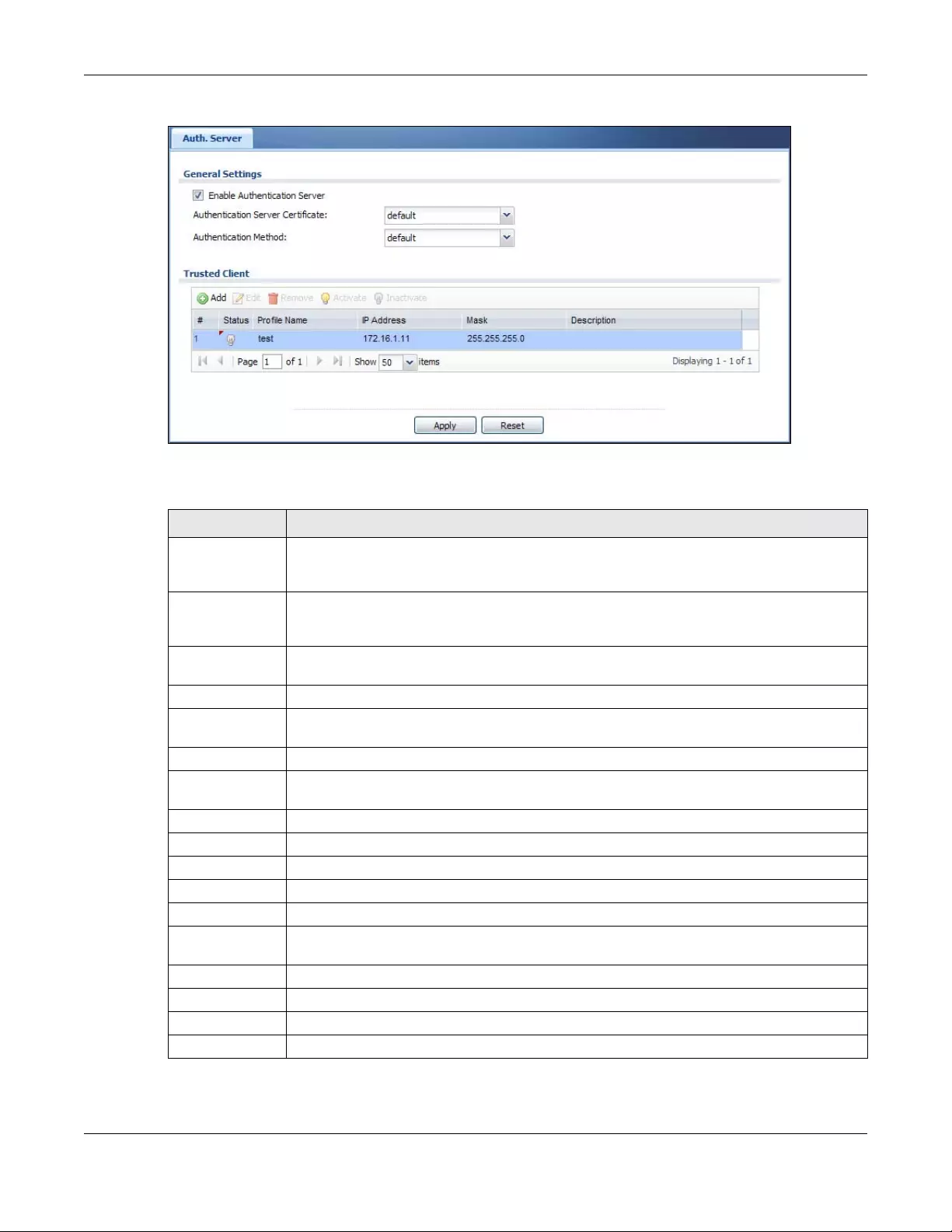
Chapter 44 System
USG/ZyWALL User’s Guide
878
Figure 634 Configuration > System > Auth. Server
The following table describes the labels in this screen.
Table 368 Configuration > System > Auth. Server
LABEL DESCRIPTION
Enable
Authentication
Server
Select the check box to have the Zyxel Device act as a RADIUS server.
Authentication
Server Certificate
Select the certificate whose corresponding private key is to be used to identify the Zyxel Device
to the RADIUS client. You must have certificates already configured in the My Certificates
screen.
Authentication
Method
Select an authentication method if you have created any in the Configuration > Object > Auth.
Method screen.
Trusted Client Use this section to configure trusted clients in the Zyxel Device RADIUS server database.
Add Click this to create a new entry. Select an entry and click Add to create a new entry after the
selected entry.
Edit Double-click an entry or select it and click Edit to be able to modify the entry’s settings.
Remove To remove an entry, select it and click Remove. The Zyxel Device confirms you want to remove
it before doing so. Note that subsequent entries move up by one when you take this action.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
#This is the index number of the entry.
Status This icon is lit when the entry is active and dimmed when the entry is inactive.
Profile Name This field indicates the name assigned to the profile.
IP Address This is the IP address of the RADIUS client that is allowed to exchange messages with the Zyxel
Device.
Mask This is the subnet mask of the RADIUS client.
Description This is the description of the RADIUS client.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
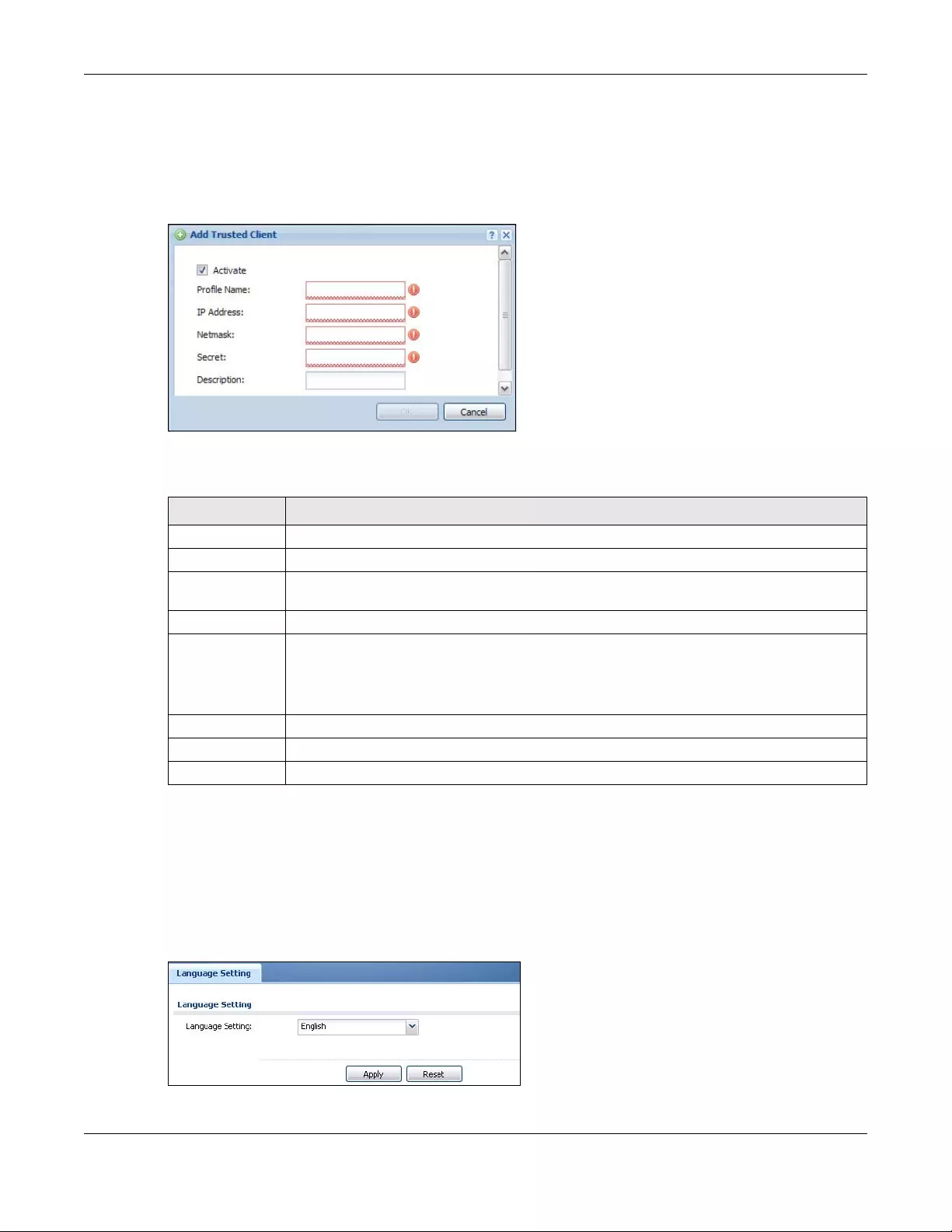
Chapter 44 System
USG/ZyWALL User’s Guide
879
44.12.1 Add/Edit Trusted RADIUS Client
Click Configuration > System > Auth. Server to display the Auth. Server screen. Click the Add icon or an
Edit icon to display the following screen. Use this screen to create a new entry or edit an existing one.
Figure 635 Configuration > System > Auth. Server > Add/Edit
The following table describes the labels in this screen.
44.13 Language Screen
Click Configuration > System > Language to open the following screen. Use this screen to select a
display language for the Zyxel Device’s Web Configurator screens.
Figure 636 Configuration > System > Language
Table 369 Configuration > System > Auth. Server > Add/Edit
LABEL DESCRIPTION
Activate Select this check box to make this profile active.
Profile Name Enter a descriptive name (up to 31 alphanumerical characters) for identification purposes.
IP Address Enter the IP address of the RADIUS client that is allowed to exchange messages with the Zyxel
Device.
Netmask Enter the subnet mask of the RADIUS client.
Secret Enter a password (up to 64 alphanumeric characters) as the key to be shared between the
Zyxel Device and the RADIUS client.
The key is not sent over the network. This key must be the same on the external authentication
server and the Zyxel Device.
Description Enter the description of each server, if any. You can use up to 60 printable ASCII characters.
OK Click OK to save the changes.
Cancel Click Cancel to discard the changes.
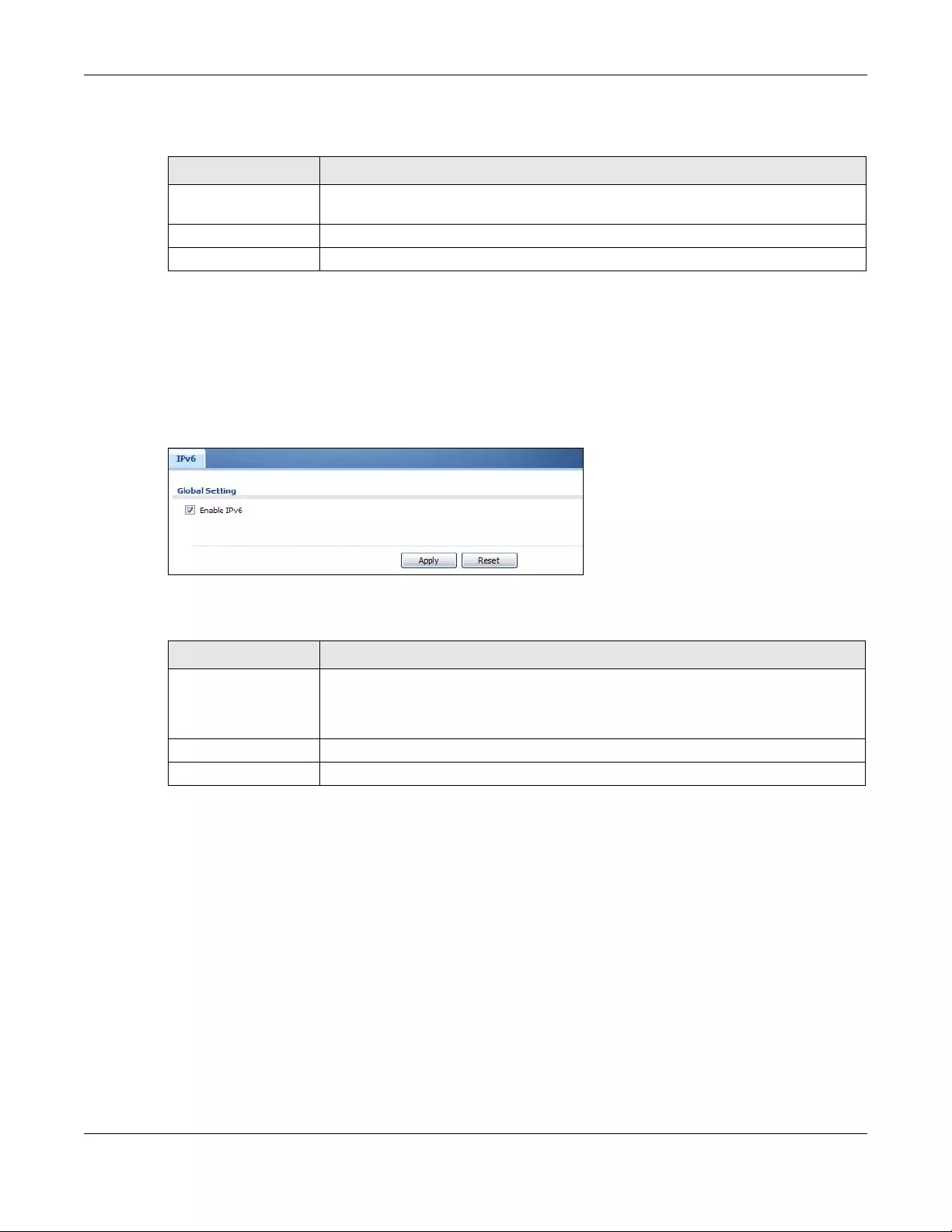
Chapter 44 System
USG/ZyWALL User’s Guide
880
The following table describes the labels in this screen.
44.14 IPv6 Screen
Click Configuration > System > IPv6 to open the following screen. Use this screen to enable IPv6 support
for the Zyxel Device’s Web Configurator screens.
Figure 637 Configuration > System > IPv6
The following table describes the labels in this screen.
44.15 Zyxel One Network (ZON) Utility
The Zyxel One Network (ZON) utility uses the Zyxel Discovery Protocol (ZDP) for discovering and
configuring ZDP-aware Zyxel devices in the same broadcast domain as the computer on which ZON is
installed.
The ZON Utility issues requests via ZDP and in response to the query, the Zyxel device responds with basic
information including IP address, firmware version, location, system and model name. The information is
then displayed in the ZON Utility screen and you can perform tasks like basic configuration of the
devices and batch firmware upgrade in it. You can download the ZON Utility at www.zyxel.com and
install it on a computer.
The following figure shows the ZON Utility screen.
Table 370 Configuration > System > Language
LABEL DESCRIPTION
Language Setting Select a display language for the Zyxel Device’s Web Configurator screens. You also
need to open a new browser session to display the screens in the new language.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
Table 371 Configuration > System > IPv6
LABEL DESCRIPTION
Enable IPv6 Select this to have the Zyxel Device support IPv6 and make IPv6 settings be available on
the screens that the functions support, such as the Configuration > Network > Interface >
Ethernet, VLAN, and Bridge screens. The Zyxel Device discards all IPv6 packets if you clear
this check box.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
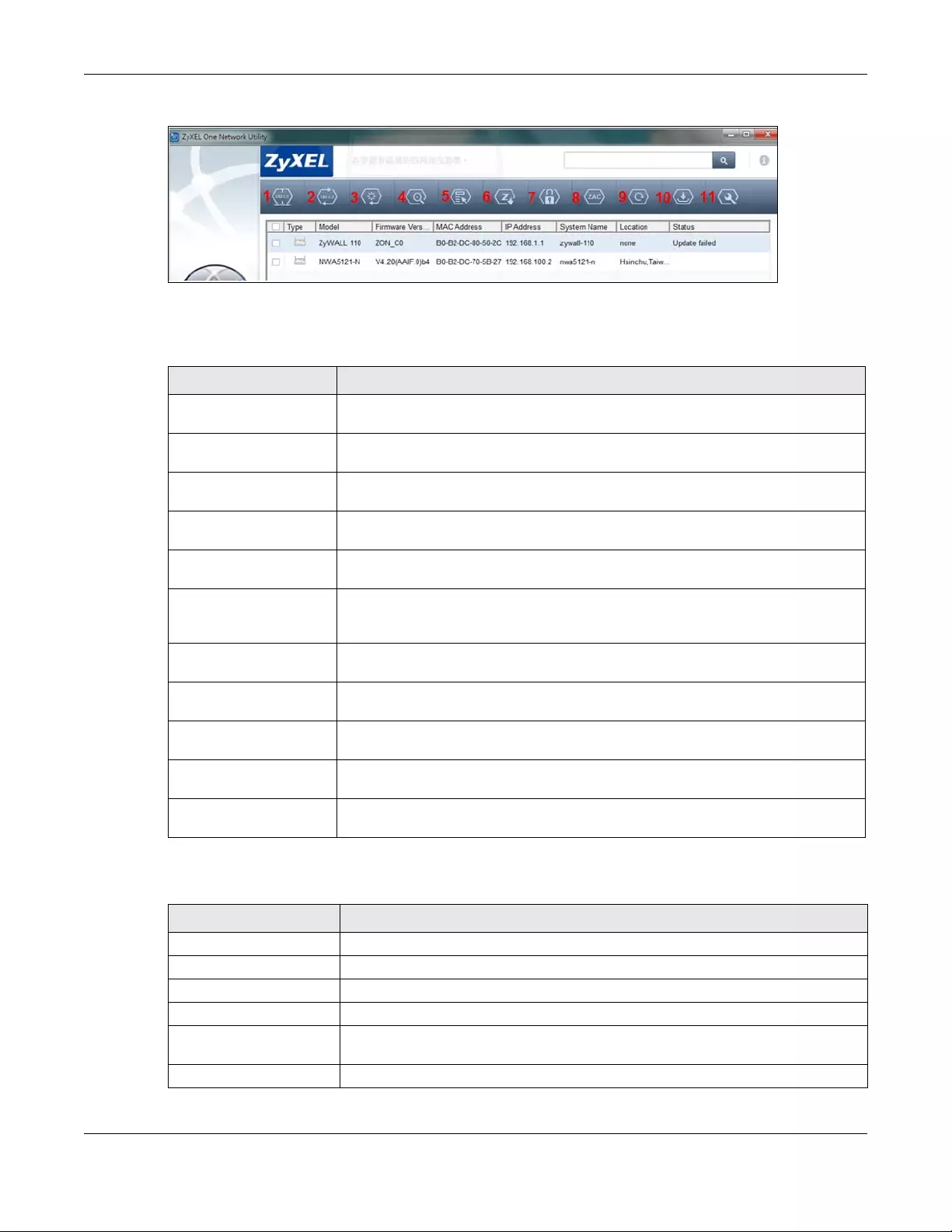
Chapter 44 System
USG/ZyWALL User’s Guide
881
Figure 638 ZON Utility Screen
In the ZON Utility, select a device and then use the icons to perform actions. The following table
describes the icons numbered from left to right in the ZON Utility screen.
The following table describes the fields in the ZON Utility main screen.
Table 372 ZON Utility Icons
ICON DESCRIPTION
1 IP configuration Change the selected device’s IP address. This is not supported by the Zyxel Device at
the time of writing.
2 Renew IP Update a DHCP-assigned dynamic IP address. This is not supported by the Zyxel
Device at the time of writing.
3 Reboot Device Use this icon to restart the selected device(s). This may be useful when troubleshooting
or upgrading new firmware.
4 Flash Locator LED Use this icon to locate the selected device by causing its Locator LED to blink. This is
not available on the Zyxel Device at the time of writing.
5 Web GUI Use this to access the selected device web configurator from your browser. You will
need a username and password to log in.
6 Firmware Upgrade Use this icon to upgrade new firmware to selected device(s) of the same model. Make
sure you have downloaded the firmware from the Zyxel website to your computer and
unzipped it in advance.
7 Change Admin
Password
Use this icon to change the admin password of the selected device. You must know
the current admin password before changing to a new one.
8 ZAC Use this icon to run the Zyxel AP Configurator of the selected AP. This is not supported
by the Zyxel Device at the time of writing.
9 Discovery You should use this icon first to display all connected devices in the same network as
your computer.
10 Save Configuration Use this icon to save configuration changes to permanent memory on a selected
device. This is not needed by the Zyxel Device at the time of writing.
11 Settings Use this icon to select a network adaptor for the computer on which the ZON utility is
installed, and the utility language.
Table 373 ZON Utility Fields
LABEL DESCRIPTION
Type This field displays an icon of the kind of device discovered.
Model This field displays the model name of the discovered device.
Firmware Version This field displays the firmware version of the discovered device.
MAC Address This field displays the MAC address of the discovered device.
IP Address This field displays the IP address of an internal interface on the discovered device that
first received an ZDP discovery request from the ZON utility.
System Name This field displays the system name of the discovered device.
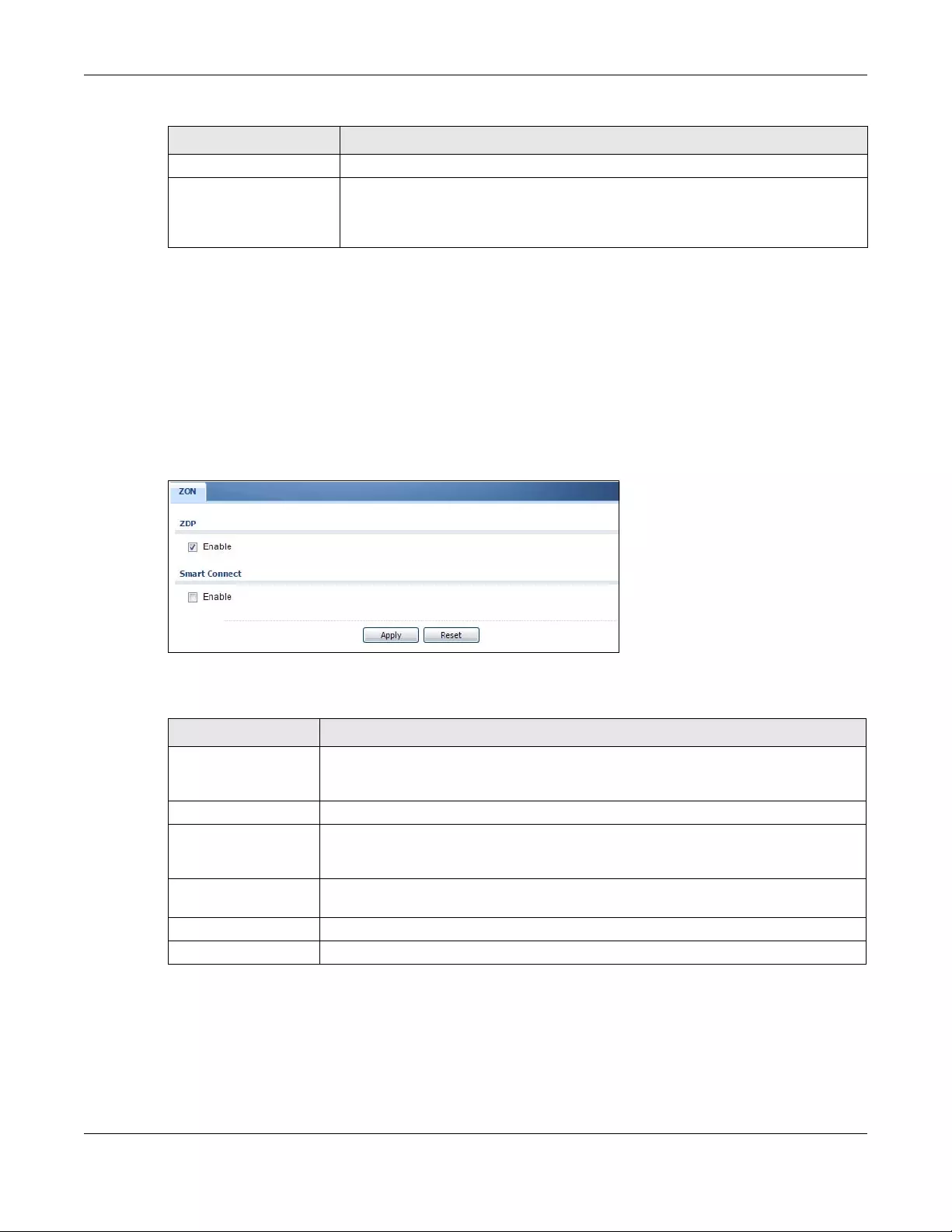
Chapter 44 System
USG/ZyWALL User’s Guide
882
44.15.1 Zyxel One Network (ZON) System Screen
Enable ZDP (ZON) and Smart Connect (Ethernet Neighbor) in the System > ZON screen.
See Monitor > System Status > Ethernet Neighbor for information on using Smart Connect (Link Layer
Discovery Protocol (LLDP)) for discovering and configuring LLDP-aware devices in the same broadcast
domain as the Zyxel Device that you’re logged into using the web configurator.
The following figure shows the System > ZON screen.
Figure 639 Configuration > System > ZON
The following table describes the labels in this screen.
Location This field displays where the discovered device is.
Status This field displays whether changes to the discovered device have been done
successfully. As the Zyxel Device does not support IP Configuration, Renew IP address
and Flash Locator LED, this field displays “Update failed”, “Not support Renew IP
address” and “Not support Flash Locator LED” respectively.
Table 373 ZON Utility Fields
LABEL DESCRIPTION
Table 374 Configuration > System > ZON
LABEL DESCRIPTION
ZDP Zyxel Discovery Protocol (ZDP) is the protocol that the Zyxel One Network (ZON) utility uses
for discovering and configuring ZDP-aware Zyxel devices in the same broadcast domain
as the computer on which ZON is installed.
Enable Select to activate ZDP discovery on the Zyxel Device.
Smart Connect Smart Connect uses Link Layer Discovery Protocol (LLDP) for discovering and configuring
LLDP-aware devices in the same broadcast domain as the Zyxel Device that you’re
logged into using the web configurator.
Enable Select to activate LLDP discovery on the Zyxel Device. See also Monitor > System Status >
Ethernet Discovery.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.

USG/ZyWALL User’s Guide
883
CHAPTER 45
Log and Report
45.1 Overview
Use these screens to configure daily reporting and log settings.
45.1.1 What You Can Do In this Chapter
• Use the Email Daily Report screen (Section 45.2 on page 883) to configure where and how to send
daily reports and what reports to send.
• Use the Log Setting screens (Section 45.3 on page 885) to specify settings for recording log messages
and alerts, e-mailing them, storing them on a connected USB storage device, and sending them to
remote syslog servers.
45.2 Email Daily Report
Use the Email Daily Report screen to start or stop data collection and view various statistics about traffic
passing through your Zyxel Device.
Note: Data collection may decrease the Zyxel Device’s traffic throughput rate.
Click Configuration > Log & Report > Email Daily Report to display the following screen. Configure this
screen to have the Zyxel Device e-mail you system statistics every day.
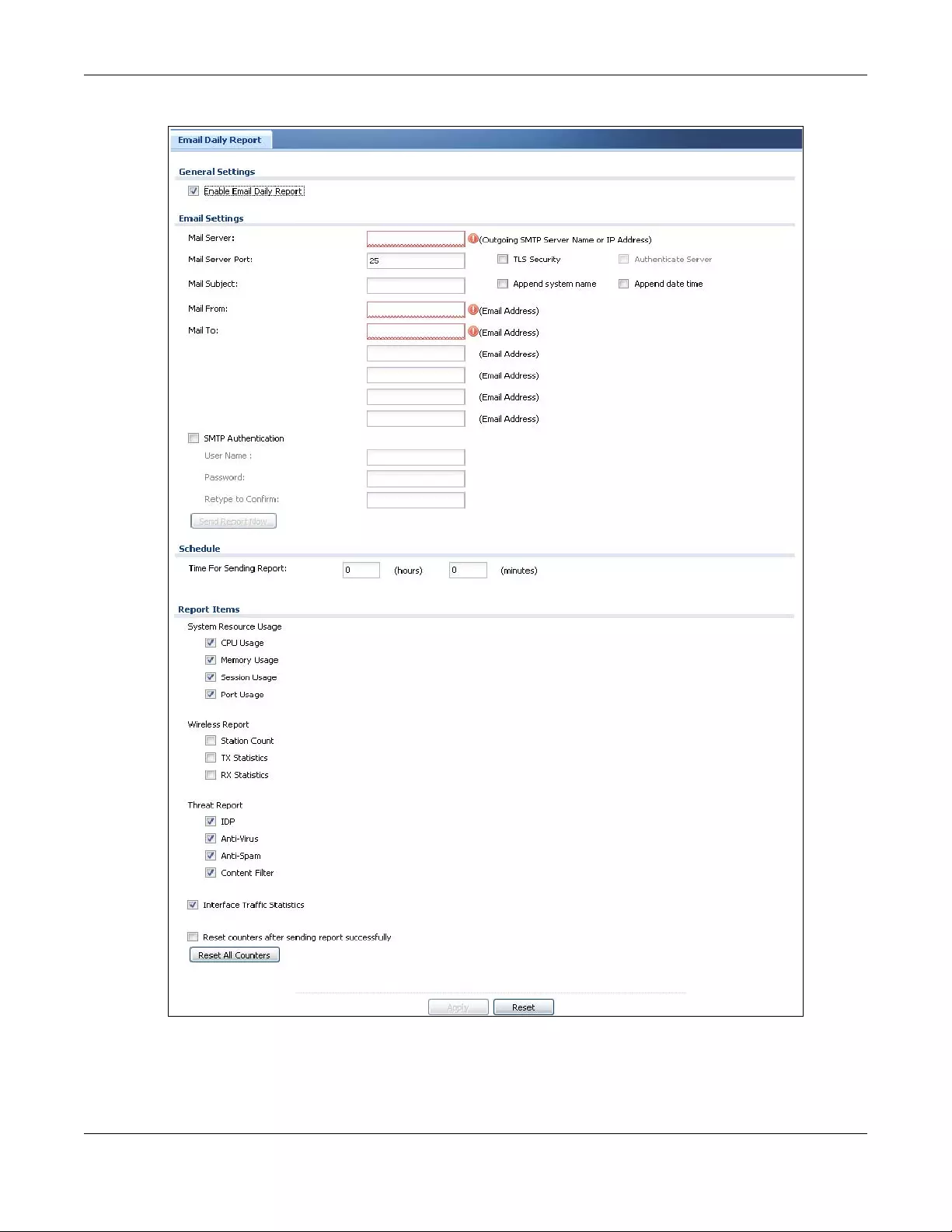
Chapter 45 Log and Report
USG/ZyWALL User’s Guide
884
Figure 640 Configuration > Log & Report > Email Daily Report
Chapter 45 Log and Report
USG/ZyWALL User’s Guide
885
The following table describes the labels in this screen.
45.3 Log Setting Screens
The Log Setting screens control log messages and alerts. A log message stores the information for
viewing or regular e-mailing later, and an alert is e-mailed immediately. Usually, alerts are used for
events that require more serious attention, such as system errors and attacks.
The Zyxel Device provides a system log and supports e-mail profiles and remote syslog servers. View the
system log in the MONITOR > Log screen. Use the e-mail profiles to mail log messages to the specific
Table 375 Configuration > Log & Report > Email Daily Report
LABEL DESCRIPTION
Enable Email Daily
Report
Select this to send reports by e-mail every day.
Mail Server Type the name or IP address of the outgoing SMTP server.
Mail Server Port Enter the same port number here as is on the mail server for mail traffic.
TLS Security Select Transport Layer Security (TLS) if you want encrypted communications between the mail
server and the Zyxel Device.
Authenticate
Server If you choose TLS Security, you may also select this to have the Zyxel Device authenticate the
mail server in the TLS handshake.
Mail Subject Type the subject line for outgoing e-mail from the Zyxel Device.
Append
system name Select Append system name to add the Zyxel Device’s system name to the subject.
Append date
time Select Append date time to add the Zyxel Device’s system date and time to the subject.
Mail From Type the e-mail address from which the outgoing e-mail is delivered. This address is used in
replies.
Mail To Type the e-mail address (or addresses) to which the outgoing e-mail is delivered.
SMTP
Authentication
Select this check box if it is necessary to provide a user name and password to the SMTP server.
User Name This box is effective when you select the SMTP Authentication check box. Type the user name
to provide to the SMTP server when the log is e-mailed.
Password This box is effective when you select the SMTP Authentication check box. Type the password to
provide to the SMTP server when the log is e-mailed.
Retype to
Confirm Type the password again to make sure that you have entered is correctly.
Send Report Now Click this button to have the Zyxel Device send the daily e-mail report immediately.
Time for sending
report
Select the time of day (hours and minutes) when the log is e-mailed. Use 24-hour notation.
Report Items Select the information to include in the report. Types of information include System Resou rce
Usage, Wireless Report, Threat Report, and Interface Traffic Statistics.
Select Reset counters after sending report successfully if you only want to see statistics for a 24
hour period.
Reset All Counters Click this to discard all report data and start all of the counters over at zero.
Apply Click Apply to save your changes back to the Zyxel Device.
Reset Click Reset to return the screen to its last-saved settings.
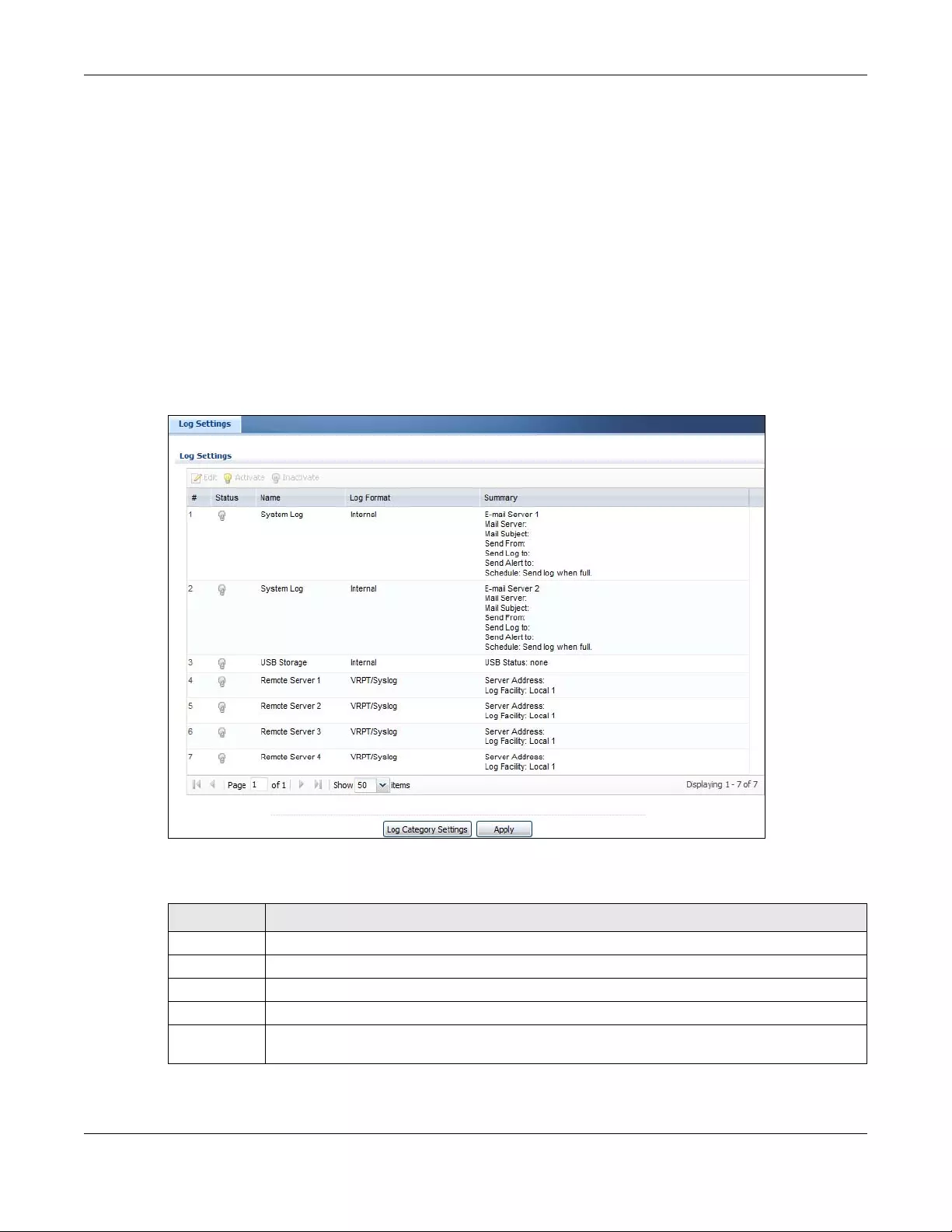
Chapter 45 Log and Report
USG/ZyWALL User’s Guide
886
destinations. You can also have the Zyxel Device store system logs on a connected USB storage device.
The other four logs are stored on specified syslog servers.
The Log Setting screens control what information the Zyxel Device saves in each log. You can also
specify which log messages to e-mail for the system log, and where and how often to e-mail them.
These screens also set for which events to generate alerts and where to email the alerts.
The first Log Setting screen provides a settings summary. Use the Edit screens to configure settings such as
log categories, e-mail addresses, and server names for any log. Use the Log Category Settings screen to
edit what information is included in the system log, USB storage, e-mail profiles, and remote servers.
45.3.1 Log Setting Summary
To access this screen, click Configuration > Log & Report > Log Setting.
Figure 641 Configuration > Log & Report > Log Setting
The following table describes the labels in this screen.
Table 376 Configuration > Log & Report > Log Setting
LABEL DESCRIPTION
Edit Double-click an entry or select it and click Edit to open a screen where you can modify it.
Activate To turn on an entry, select it and click Activate.
Inactivate To turn off an entry, select it and click Inactivate.
# This field is a sequential value, and it is not associated with a specific log.
Name This field displays the type of log setting entry (system log, logs stored on a USB storage device
connected to the Zyxel Device, or one of the remote servers).
Chapter 45 Log and Report
USG/ZyWALL User’s Guide
887
45.3.2 Edit System Log Settings
The Log Settings Edit screen controls the detailed settings for each log in the system log (which includes
the e-mail profiles). Go to the Log Settings Summary screen (see Section 45.3.1 on page 886), and click
the system log Edit icon.
Log Format This field displays the format of the log.
Internal - system log; you can view the log on the View Log tab.
VRPT/Syslog - Zyxel’s Vantage Report, syslog-compatible format.
CEF/Syslog - Common Event Format, syslog-compatible format.
Summary This field is a summary of the settings for each log. Please see Section 45.3.2 on page 887 for more
information.
Log Category
Settings
Click this button to open the Log Category Settings Edit screen.
Apply Click this button to save your changes (activate and deactivate logs) and make them take effect.
Table 376 Configuration > Log & Report > Log Setting (continued)
LABEL DESCRIPTION
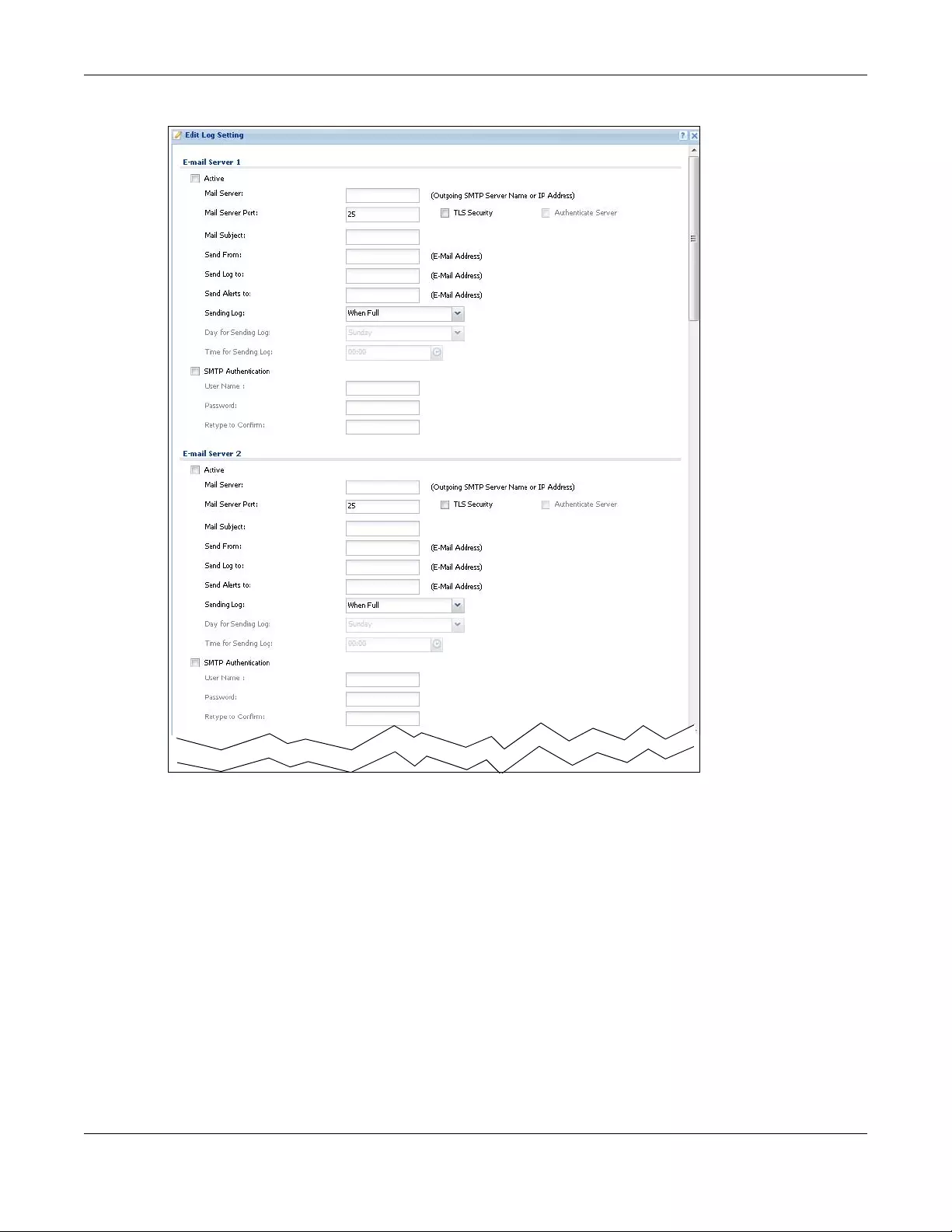
Chapter 45 Log and Report
USG/ZyWALL User’s Guide
888
Figure 642 Configuration > Log & Report > Log Setting > Edit (System Log - E-mail Servers)
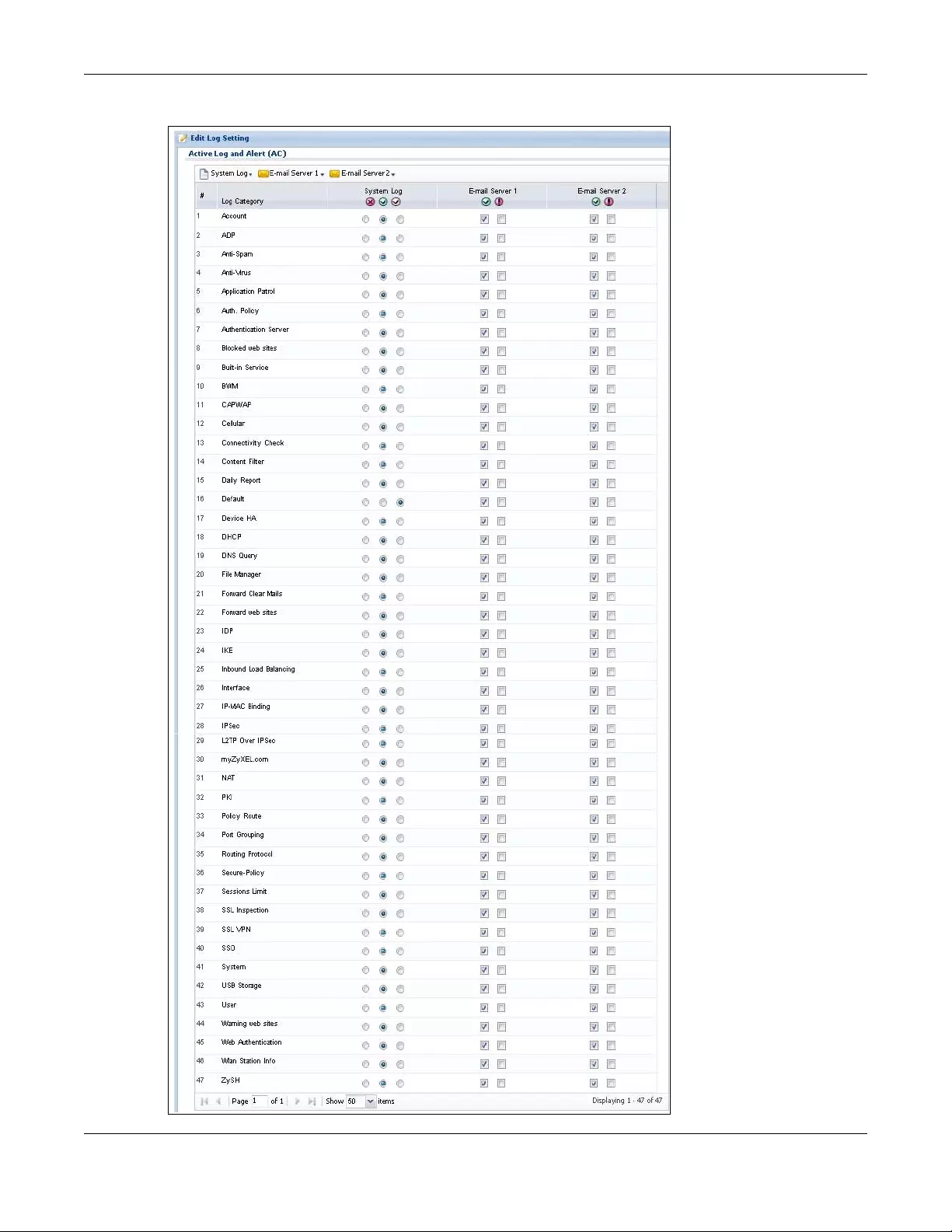
Chapter 45 Log and Report
USG/ZyWALL User’s Guide
889
Figure 643 Configuration > Log & Report > Log Setting > Edit (System Log - AC)
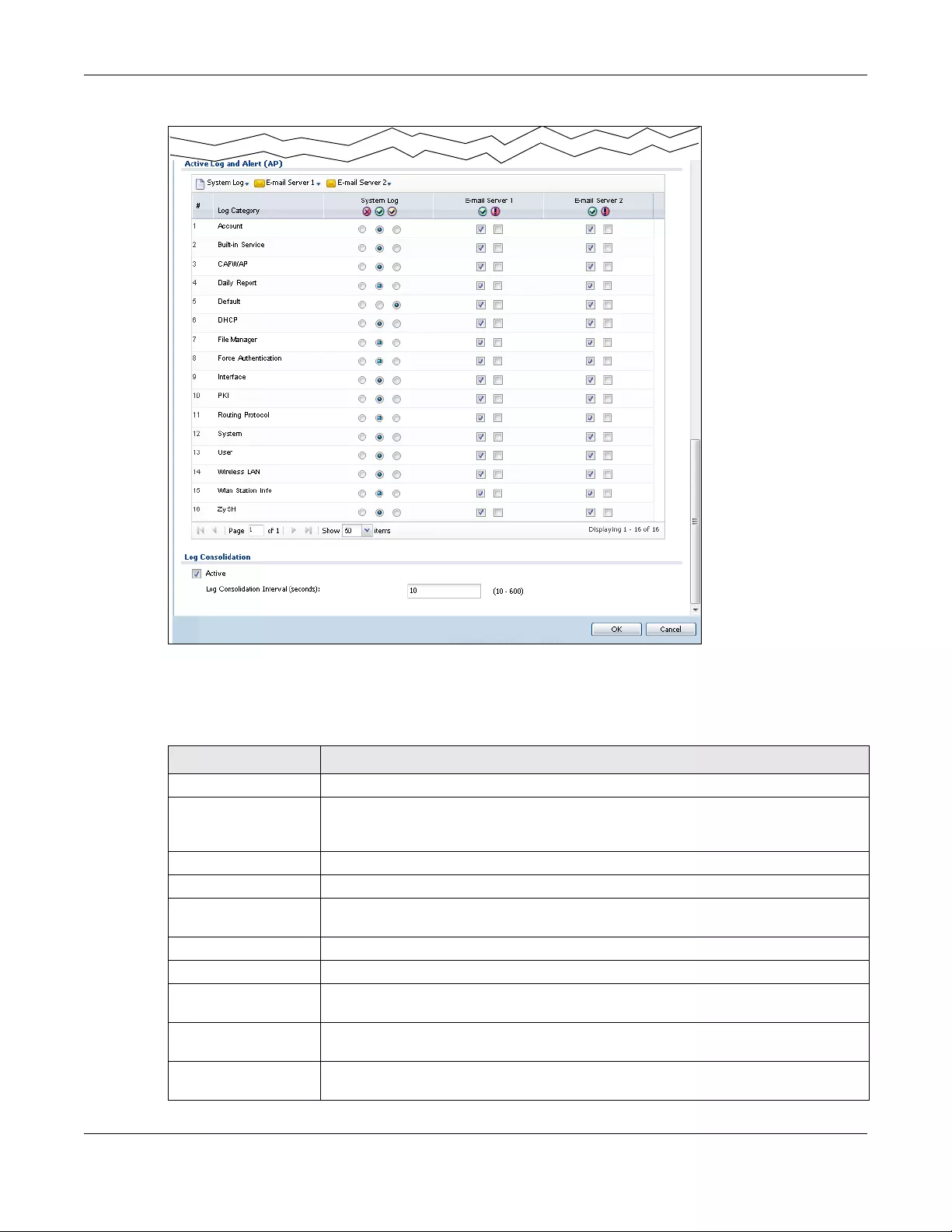
Chapter 45 Log and Report
USG/ZyWALL User’s Guide
890
Figure 644 Configuration > Log & Report > Log Setting > Edit (System Log - AP)
The following table describes the labels in this screen.
Table 377 Configuration > Log & Report > Log Setting > Edit (System Log)
LABEL DESCRIPTION
E-Mail Server 1/2
Active Select this to send log messages and alerts according to the information in this section.
You specify what kinds of log messages are included in log information and what kinds of
log messages are included in alerts in the Active Log and Alert section.
Mail Server Type the name or IP address of the outgoing SMTP server.
Mail Subject Type the subject line for the outgoing e-mail.
Send From Type the e-mail address from which the outgoing e-mail is delivered. This address is used in
replies.
Send Log To Type the e-mail address to which the outgoing e-mail is delivered.
Send Alerts To Type the e-mail address to which alerts are delivered.
Sending Log Select how often log information is e-mailed. Choices are: When Full, Hourly and When
Full, Daily and When Full, and Weekly and When Full.
Day for Sending
Log This field is available if the log is e-mailed weekly. Select the day of the week the log is e-
mailed.
Time for Sending
Log This field is available if the log is e-mailed weekly or daily. Select the time of day (hours
and minutes) when the log is e-mailed. Use 24-hour notation.
Chapter 45 Log and Report
USG/ZyWALL User’s Guide
891
SMTP
Authentication Select this check box if it is necessary to provide a user name and password to the SMTP
server.
User Name This box is effective when you select the SMTP Authentication check box. Type the user
name to provide to the SMTP server when the log is e-mailed.
Password This box is effective when you select the SMTP Authentication check box. Type the
password to provide to the SMTP server when the log is e-mailed.
Retype to Confirm Type the password again to make sure that you have entered is correctly.
Active Log and Alert
System Log Use the System Log drop-down list to change the log settings for all of the log categories.
disable all logs (red X) - do not log any information for any category for the system log or
e-mail any logs to e-mail server 1 or 2.
enable normal logs (green check mark) - create log messages and alerts for all
categories for the system log. If e-mail server 1 or 2 also has normal logs enabled, the Zyxel
Device will e-mail logs to them.
enable normal logs and debug logs (yellow check mark) - create log messages, alerts,
and debugging information for all categories. The Zyxel Device does not e-mail
debugging information, even if this setting is selected.
E-mail Server 1 Use the E-Mail Server 1 drop-down list to change the settings for e-mailing logs to e-mail
server 1 for all log categories.
Using the System Log drop-down list to disable all logs overrides your e-mail server 1
settings.
enable normal logs (green check mark) - e-mail log messages for all categories to e-mail
server 1.
enable alert logs (red exclamation point) - e-mail alerts for all categories to e-mail server
1.
E-mail Server 2 Use the E-Mail Server 2 drop-down list to change the settings for e-mailing logs to e-mail
server 2 for all log categories.
Using the System Log drop-down list to disable all logs overrides your e-mail server 2
settings.
enable normal logs (green check mark) - e-mail log messages for all categories to e-mail
server 2.
enable alert logs (red exclamation point) - e-mail alerts for all categories to e-mail server
2.
# This field is a sequential value, and it is not associated with a specific address.
Log Category This field displays each category of messages. It is the same value used in the Display and
Category fields in the View Log tab. The Default category includes debugging messages
generated by open source software.
System log Select which events you want to log by Log Category. There are three choices:
disable all logs (red X) - do not log any information from this category
enable normal logs (green check mark) - create log messages and alerts from this
category
enable normal logs and debug logs (yellow check mark) - create log messages, alerts,
and debugging information from this category; the Zyxel Device does not e-mail
debugging information, however, even if this setting is selected.
Table 377 Configuration > Log & Report > Log Setting > Edit (System Log) (continued)
LABEL DESCRIPTION
Chapter 45 Log and Report
USG/ZyWALL User’s Guide
892
45.3.3 Edit Log on USB Storage Setting
The Edit Log on USB Storage Setting screen controls the detailed settings for saving logs to a connected
USB storage device. Go to the Log Setting Summary screen (see Section 45.3.1 on page 886), and click
the USB storage Edit icon.
E-mail Server 1 Select whether each category of events should be included in the log messages when it
is e-mailed (green check mark) and/or in alerts (red exclamation point) for the e-mail
settings specified in E-Mail Server 1. The Zyxel Device does not e-mail debugging
information, even if it is recorded in the System log.
E-mail Server 2 Select whether each category of events should be included in log messages when it is e-
mailed (green check mark) and/or in alerts (red exclamation point) for the e-mail settings
specified in E-Mail Server 2. The Zyxel Device does not e-mail debugging information,
even if it is recorded in the System log.
Log Consolidation
Active Select this to activate log consolidation. Log consolidation aggregates multiple log
messages that arrive within the specified Log Consolidation Interval. In the View Log tab,
the text “[count=x]”, where x is the number of original log messages, is appended at the
end of the Message field, when multiple log messages were aggregated.
Log Consolidation
Interval Type how often, in seconds, to consolidate log information. If the same log message
appears multiple times, it is aggregated into one log message with the text “[count=x]”,
where x is the number of original log messages, appended at the end of the Message
field.
OK Click this to save your changes and return to the previous screen.
Cancel Click this to return to the previous screen without saving your changes.
Table 377 Configuration > Log & Report > Log Setting > Edit (System Log) (continued)
LABEL DESCRIPTION
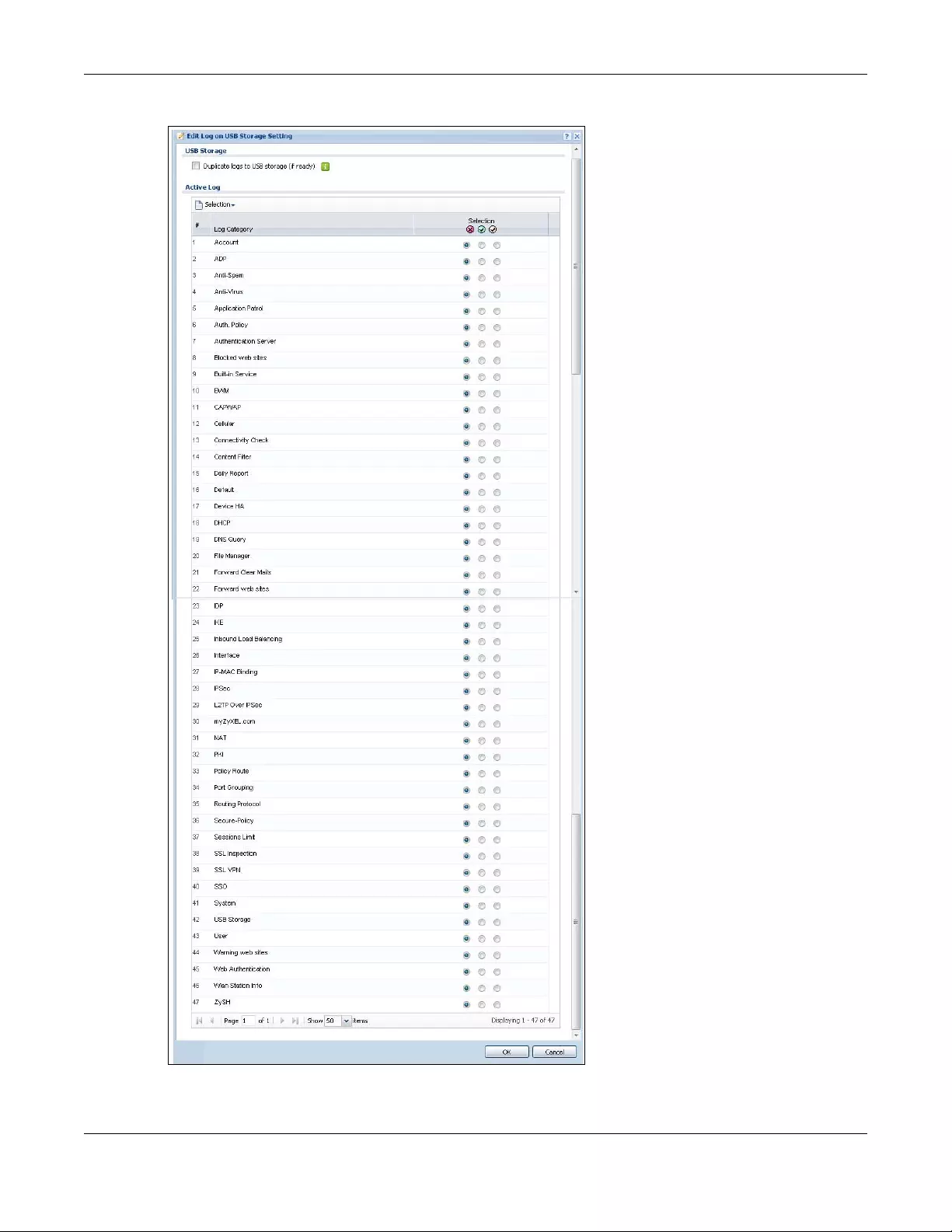
Chapter 45 Log and Report
USG/ZyWALL User’s Guide
893
Figure 645 Configuration > Log & Report > Log Setting > Edit (USB Storage)
Chapter 45 Log and Report
USG/ZyWALL User’s Guide
894
The following table describes the labels in this screen.
45.3.4 Edit Remote Server Log Settings
The Log Settings Edit screen controls the detailed settings for each log in the remote server (syslog). Go
to the Log Settings Summary screen (see Section 45.3.1 on page 886), and click a remote server Edit
icon.
Table 378 Configuration > Log & Report > Log Setting > Edit (USB Storage)
LABEL DESCRIPTION
Duplicate logs to
USB storage (if
ready)
Select this to have the Zyxel Device save a copy of its system logs to a connected USB storage
device. Use the Active Log section to specify what kinds of messages to include.
Active Log
Selection Use the Selection drop-down list to change the log settings for all of the log categories.
disable all logs (red X) - do not send the remote server logs for any log category.
enable normal logs (green check mark) - send the remote server log messages and alerts for
all log categories.
enable normal logs and debug logs (yellow check mark) - send the remote server log
messages, alerts, and debugging information for all log categories.
# This field is a sequential value, and it is not associated with a specific entry.
Log Category This field displays each category of messages. The Default category includes debugging
messages generated by open source software.
Selection Select what information you want to log from each Log Category (except All Logs; see below).
Choices are:
disable all logs (red X) - do not log any information from this category
enable normal logs (green check mark) - log regular information and alerts from this category
enable normal logs and debug logs (yellow check mark) - log regular information, alerts, and
debugging information from this category
OK Click this to save your changes and return to the previous screen.
Cancel Click this to return to the previous screen without saving your changes.
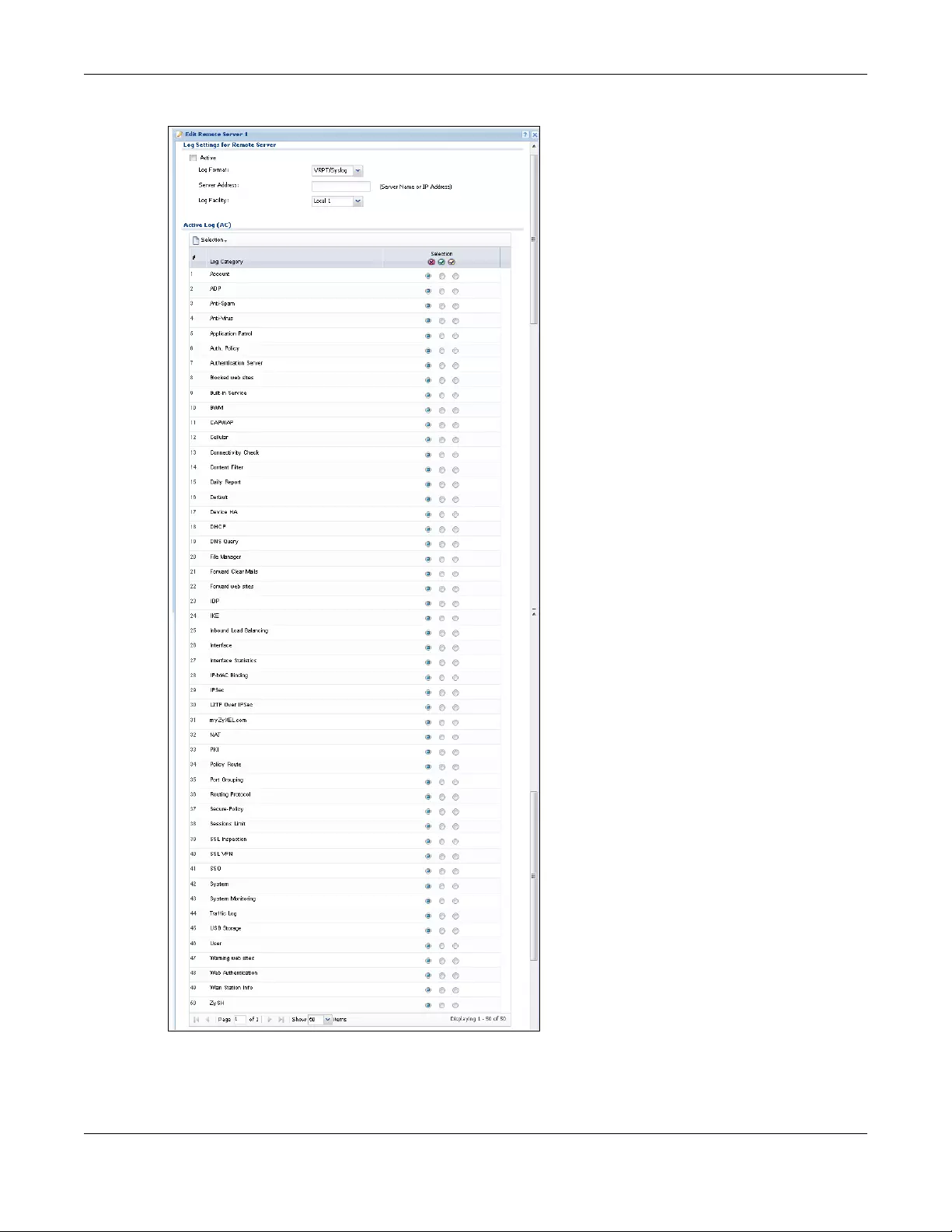
Chapter 45 Log and Report
USG/ZyWALL User’s Guide
895
Figure 646 Configuration > Log & Report > Log Setting > Edit (Remote Server - AC)
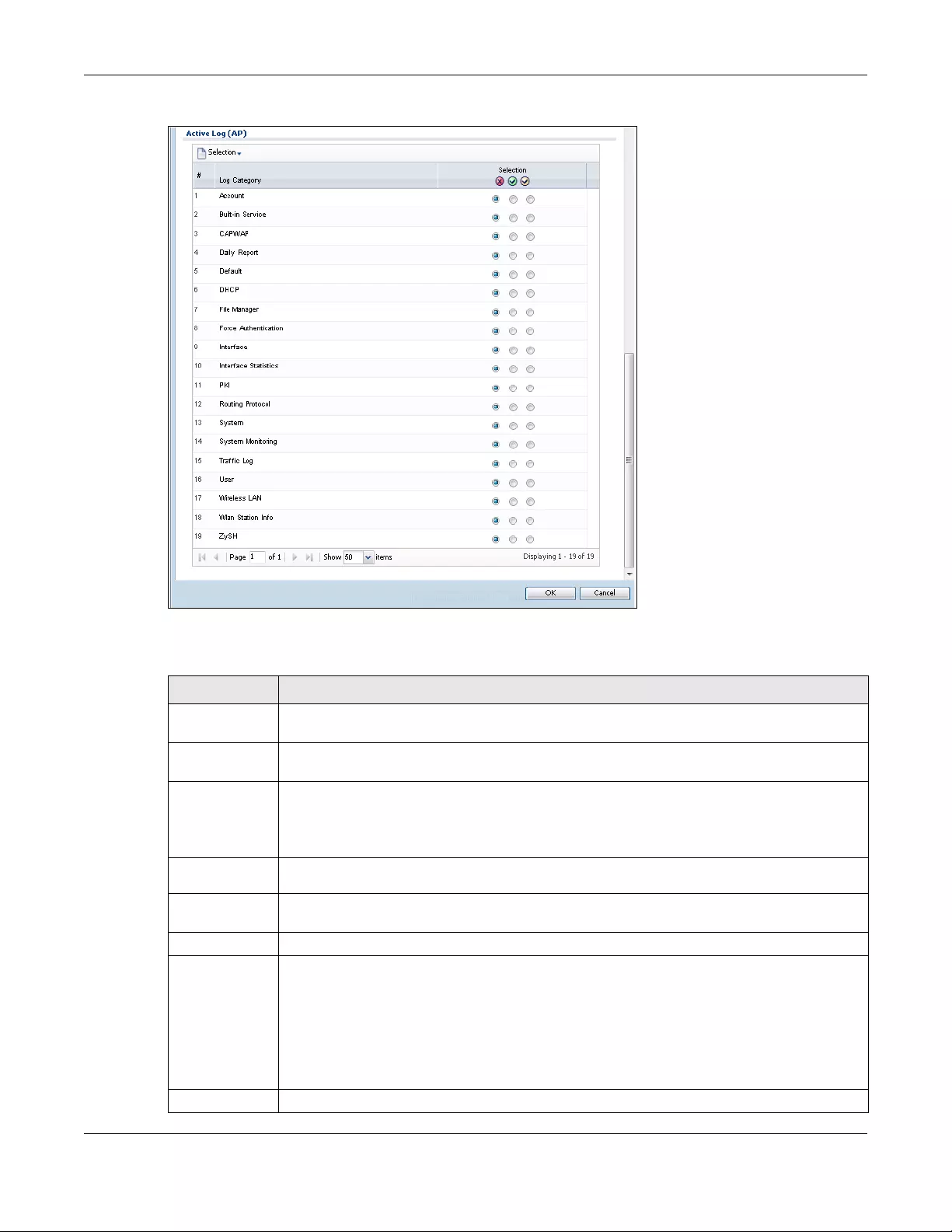
Chapter 45 Log and Report
USG/ZyWALL User’s Guide
896
Configuration > Log & Report > Log Setting > Edit (Remote Server - AP)
The following table describes the labels in this screen.
Table 379 Configuration > Log & Report > Log Setting > Edit (Remote Server)
LABEL DESCRIPTION
Log Settings for
Remote Server
Active Select this check box to send log information according to the information in this section. You
specify what kinds of messages are included in log information in the Active Log section.
Log Format This field displays the format of the log information. It is read-only.
VRPT/Syslog - Zyxel’s Vantage Report, syslog-compatible format.
CEF/Syslog - Common Event Format, syslog-compatible format.
Server
Address Type the server name or the IP address of the syslog server to which to send log information.
Log Facility Select a log facility. The log facility allows you to log the messages to different files in the syslog
server. Please see the documentation for your syslog program for more information.
Active Log
Selection Use the Selection drop-down list to change the log settings for all of the log categories.
disable all logs (red X) - do not send the remote server logs for any log category.
enable normal logs (green check mark) - send the remote server log messages and alerts for all
log categories.
enable normal logs and debug logs (yellow check mark) - send the remote server log messages,
alerts, and debugging information for all log categories.
# This field is a sequential value, and it is not associated with a specific address.
Chapter 45 Log and Report
USG/ZyWALL User’s Guide
897
45.3.5 Log Category Settings Screen
The Log Category Settings screen allows you to view and to edit what information is included in the
system log, USB storage, e-mail profiles, and remote servers at the same time. It does not let you change
other log settings (for example, where and how often log information is e-mailed or remote server
names). To access this screen, go to the Log Settings Summary screen (see Section 45.3.1 on page 886),
and click the Log Category Settings button.
Log
Category This field displays each category of messages. It is the same value used in the Display and
Category fields in the View Log tab. The Default category includes debugging messages
generated by open source software.
Selection Select what information you want to log from each Log Category (except All Logs; see below).
Choices are:
disable all logs (red X) - do not log any information from this category
enable normal logs (green check mark) - log regular information and alerts from this category
enable normal logs and debug logs (yellow check mark) - log regular information, alerts, and
debugging information from this category
OK Click this to save your changes and return to the previous screen.
Cancel Click this to return to the previous screen without saving your changes.
Table 379 Configuration > Log & Report > Log Setting > Edit (Remote Server) (continued)
LABEL DESCRIPTION
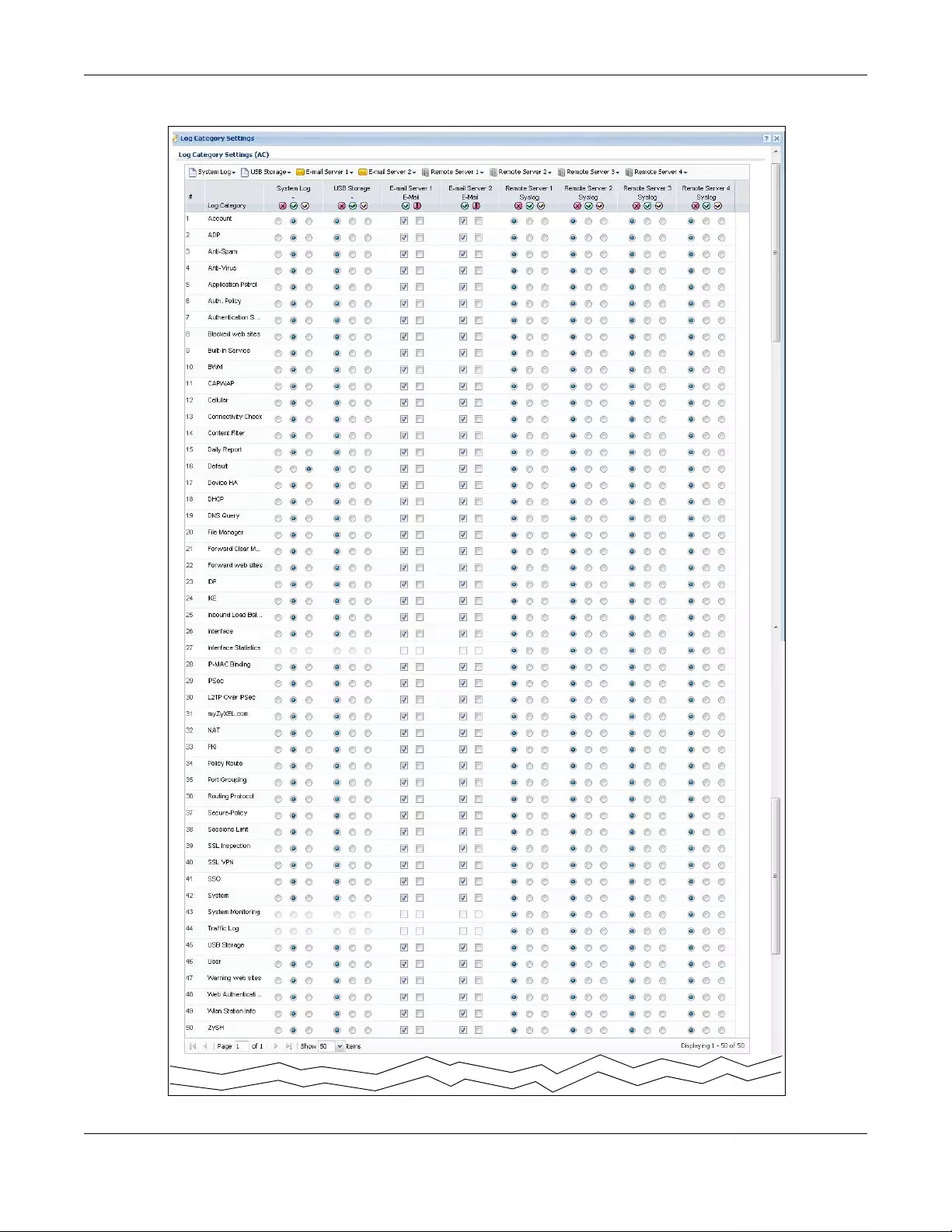
Chapter 45 Log and Report
USG/ZyWALL User’s Guide
898
Figure 647 Log Category Settings AC
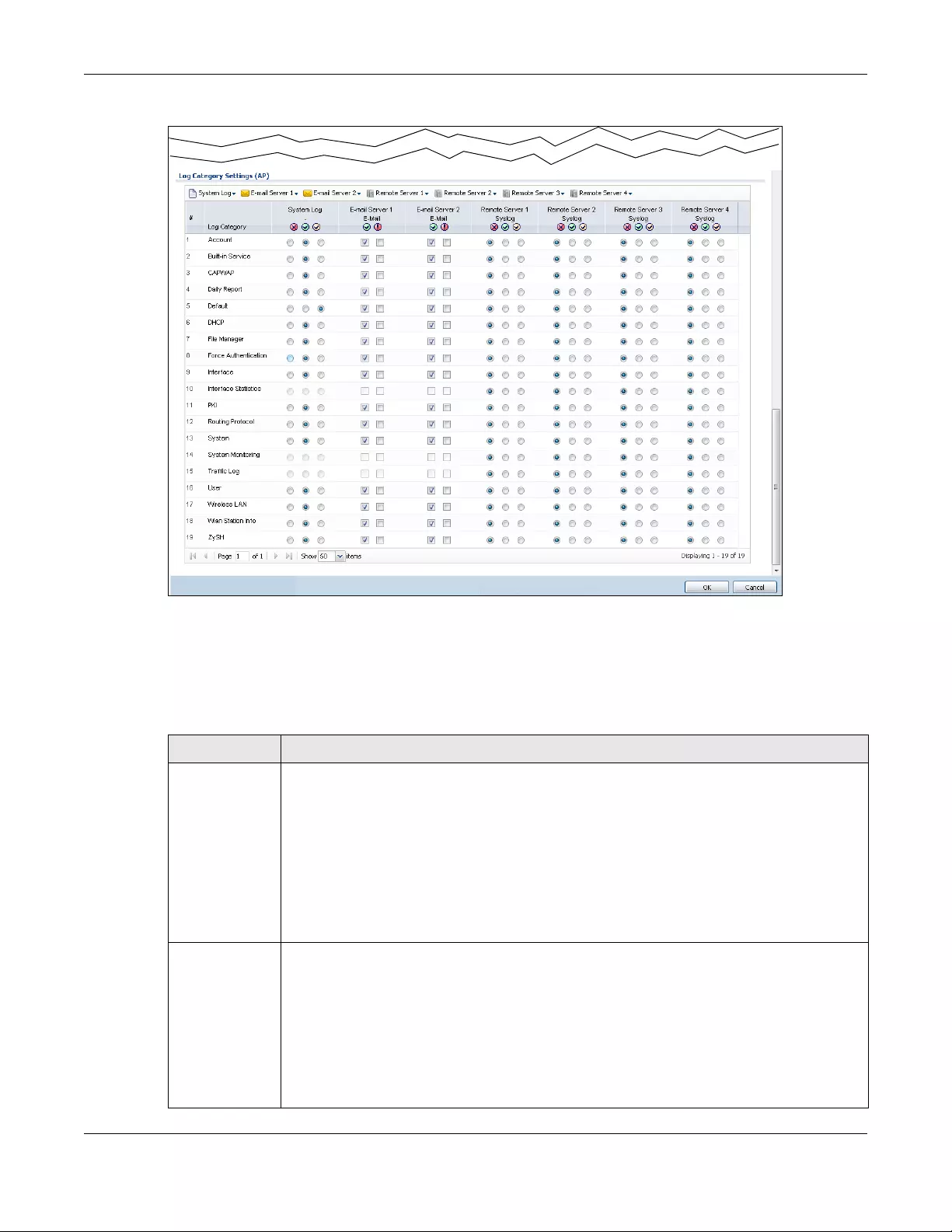
Chapter 45 Log and Report
USG/ZyWALL User’s Guide
899
Figure 648 Log Category Settings AP
This screen provides a different view and a different way of indicating which messages are included in
each log and each alert. Please see Section 45.3.2 on page 887, where this process is discussed. (The
Default category includes debugging messages generated by open source software.)
The following table describes the fields in this screen.
Table 380 Configuration > Log & Report > Log Setting > Log Category Settings
LABEL DESCRIPTION
System Log Use the System Log drop-down list to change the log settings for all of the log categories.
disable all logs (red X) - do not log any information for any category for the system log or e-mail
any logs to e-mail server 1 or 2.
enable normal logs (green check mark) - create log messages and alerts for all categories for
the system log. If e-mail server 1 or 2 also has normal logs enabled, the Zyxel Device will e-mail
logs to them.
enable normal logs and debug logs (yellow check mark) - create log messages, alerts, and
debugging information for all categories. The Zyxel Device does not e-mail debugging
information, even if this setting is selected.
USB Storage Use the USB Storage drop-down list to change the log settings for saving logs to a connected
USB storage device.
disable all logs (red X) - do not log any information for any category to a connected USB
storage device.
enable normal logs (green check mark) - create log messages and alerts for all categories and
save them to a connected USB storage device.
enable normal logs and debug logs (yellow check mark) - create log messages, alerts, and
debugging information for all categories and save them to a connected USB storage device.
Chapter 45 Log and Report
USG/ZyWALL User’s Guide
900
E-mail Server 1 Use the E-Mail Server 1 drop-down list to change the settings for e-mailing logs to e-mail server 1
for all log categories.
Using the System Log drop-down list to disable all logs overrides your e-mail server 1 settings.
enable normal logs (green check mark) - e-mail log messages for all categories to e-mail server
1.
enable alert logs (red exclamation point) - e-mail alerts for all categories to e-mail server 1.
E-mail Server 2 Use the E-Mail Server 2 drop-down list to change the settings for e-mailing logs to e-mail server 2
for all log categories.
Using the System Log drop-down list to disable all logs overrides your e-mail server 2 settings.
enable normal logs (green check mark) - e-mail log messages for all categories to e-mail server
2.
enable alert logs (red exclamation point) - e-mail alerts for all categories to e-mail server 2.
Remote Server
1~4
For each remote server, use the Selection drop-down list to change the log settings for all of the
log categories.
disable all logs (red X) - do not send the remote server logs for any log category.
enable normal logs (green check mark) - send the remote server log messages and alerts for all
log categories.
enable normal logs and debug logs (yellow check mark) - send the remote server log messages,
alerts, and debugging information for all log categories.
# This field is a sequential value, and it is not associated with a specific address.
Log Category This field displays each category of messages. It is the same value used in the Display and
Category fields in the View Log tab. The Default category includes debugging messages
generated by open source software.
System Log Select which events you want to log by Log Category. There are three choices:
disable all logs (red X) - do not log any information from this category
enable normal logs (green check mark) - create log messages and alerts from this category
enable normal logs and debug logs (yellow check mark) - create log messages, alerts, and
debugging information from this category; the Zyxel Device does not e-mail debugging
information, however, even if this setting is selected.
USB Storage Select which event log categories to save to a connected USB storage device. There are three
choices:
disable all logs (red X) - do not log any information from this category
enable normal logs (green check mark) - save log messages and alerts from this category
enable normal logs and debug logs (yellow check mark) - save log messages, alerts, and
debugging information from this category.
E-mail Server 1 E-
mail
Select whether each category of events should be included in the log messages when it is e-
mailed (green check mark) and/or in alerts (red exclamation point) for the e-mail settings
specified in E-Mail Server 1. The Zyxel Device does not e-mail debugging information, even if it is
recorded in the System log.
E-mail Server 2 E-
mail
Select whether each category of events should be included in log messages when it is e-mailed
(green check mark) and/or in alerts (red exclamation point) for the e-mail settings specified in E-
Mail Server 2. The Zyxel Device does not e-mail debugging information, even if it is recorded in
the System log.
Table 380 Configuration > Log & Report > Log Setting > Log Category Settings (continued)
LABEL DESCRIPTION
Chapter 45 Log and Report
USG/ZyWALL User’s Guide
901
Remote Server
1~4
For each remote server, select what information you want to log from each Log Category
(except All Logs; see below). Choices are:
disable all logs (red X) - do not log any information from this category
enable normal logs (green check mark) - log regular information and alerts from this category
enable normal logs and debug logs (yellow check mark) - log regular information, alerts, and
debugging information from this category
OK Click this to save your changes and return to the previous screen.
Cancel Click this to return to the previous screen without saving your changes.
Table 380 Configuration > Log & Report > Log Setting > Log Category Settings (continued)
LABEL DESCRIPTION

USG/ZyWALL User’s Guide
902
CHAPTER 46
File Manager
46.1 Overview
Configuration files define the Zyxel Device’s settings. Shell scripts are files of commands that you can
store on the Zyxel Device and run when you need them. You can apply a configuration file or run a shell
script without the Zyxel Device restarting. You can store multiple configuration files and shell script files
on the Zyxel Device. You can edit configuration files or shell scripts in a text editor and upload them to
the Zyxel Device. Configuration files use a .conf extension and shell scripts use a .zysh extension.
46.1.1 What You Can Do in this Chapter
• Use the Configuration File screen (see Section 46.2 on page 904) to store and name configuration
files. You can also download configuration files from the Zyxel Device to your computer and upload
configuration files from your computer to the Zyxel Device.
• Use the Firmware Package screen (see Section 46.3 on page 908) to check your current firmware
version and upload firmware to the Zyxel Device.
• Use the Shell Script screen (see Section 46.4 on page 913) to store, name, download, upload and run
shell script files.
46.1.2 What you Need to Know
Configuration Files and Shell Scripts
When you apply a configuration file, the Zyxel Device uses the factory default settings for any features
that the configuration file does not include. When you run a shell script, the Zyxel Device only applies the
commands that it contains. Other settings do not change.
Chapter 46 File Manager
USG/ZyWALL User’s Guide
903
These files have the same syntax, which is also identical to the way you run CLI commands manually. An
example is shown below.
While configuration files and shell scripts have the same syntax, the Zyxel Device applies configuration
files differently than it runs shell scripts. This is explained below.
You have to run the example in Figure 649 on page 903 as a shell script because the first command is run
in Privilege mode. If you remove the first command, you have to run the example as a configuration file
because the rest of the commands are executed in Configuration mode.
Comments in Configuration Files or Shell Scripts
In a configuration file or shell script, use “#” or “!” as the first character of a command line to have the
Zyxel Device treat the line as a comment.
Your configuration files or shell scripts can use “exit” or a command line consisting of a single “!” to have
the Zyxel Device exit sub command mode.
Note: “exit” or “!'” must follow sub commands if it is to make the Zyxel Device exit sub
command mode.
Figure 649 Configuration File / Shell Script: Example
# enter configuration mode
configure terminal
# change administrator password
username admin password 4321 user-type admin
# configure ge3
interface ge3
ip address 172.23.37.240 255.255.255.0
ip gateway 172.23.37.254 metric 1
exit
# create address objects for remote management / to-ZyWALL firewall rules
# use the address group in case we want to open up remote management later
address-object TW_SUBNET 172.23.37.0/24
object-group address TW_TEAM
address-object TW_SUBNET
exit
# enable Telnet access (not enabled by default, unlike other services)
ip telnet server
# open WAN-to-ZyWALL firewall for TW_TEAM for remote management
firewall WAN ZyWALL insert 4
sourceip TW_TEAM
service TELNET
action allow
exit
write
Table 381 Configuration Files and Shell Scripts in the Zyxel Device
Configuration Files (.conf) Shell Scripts (.zysh)
• Resets to default configuration.
•Goes into CLI Configuration mode.
• Runs the commands in the configuration file.
•Goes into CLI Privilege mode.
• Runs the commands in the shell script.
Chapter 46 File Manager
USG/ZyWALL User’s Guide
904
Line 3 in the following example exits sub command mode.
Lines 1 and 3 in the following example are comments and line 4 exits sub command mode.
Lines 1 and 2 are comments. Line 5 exits sub command mode.
Errors in Configuration Files or Shell Scripts
When you apply a configuration file or run a shell script, the Zyxel Device processes the file line-by-line.
The Zyxel Device checks the first line and applies the line if no errors are detected. Then it continues with
the next line. If the Zyxel Device finds an error, it stops applying the configuration file or shell script and
generates a log.
You can change the way a configuration file or shell script is applied. Include setenv stop-on-error
off in the configuration file or shell script. The Zyxel Device ignores any errors in the configuration file or
shell script and applies all of the valid commands. The Zyxel Device still generates a log for any errors.
46.2 The Configuration File Screen
Click Maintenance > File Manager > Configuration File to open the Configuration File screen. Use the
Configuration File screen to store, run, and name configuration files. You can also download
configuration files from the Zyxel Device to your computer and upload configuration files from your
computer to the Zyxel Device.
Once your Zyxel Device is configured and functioning properly, it is highly recommended that you back
up your configuration file before making further configuration changes. The backup configuration file
will be useful in case you need to return to your previous settings.
interface ge1
ip address dhcp
!
!
interface ge1
# this interface is a DHCP client
!
! this is from Joe
# on 2008/04/05
interface ge1
ip address dhcp
!
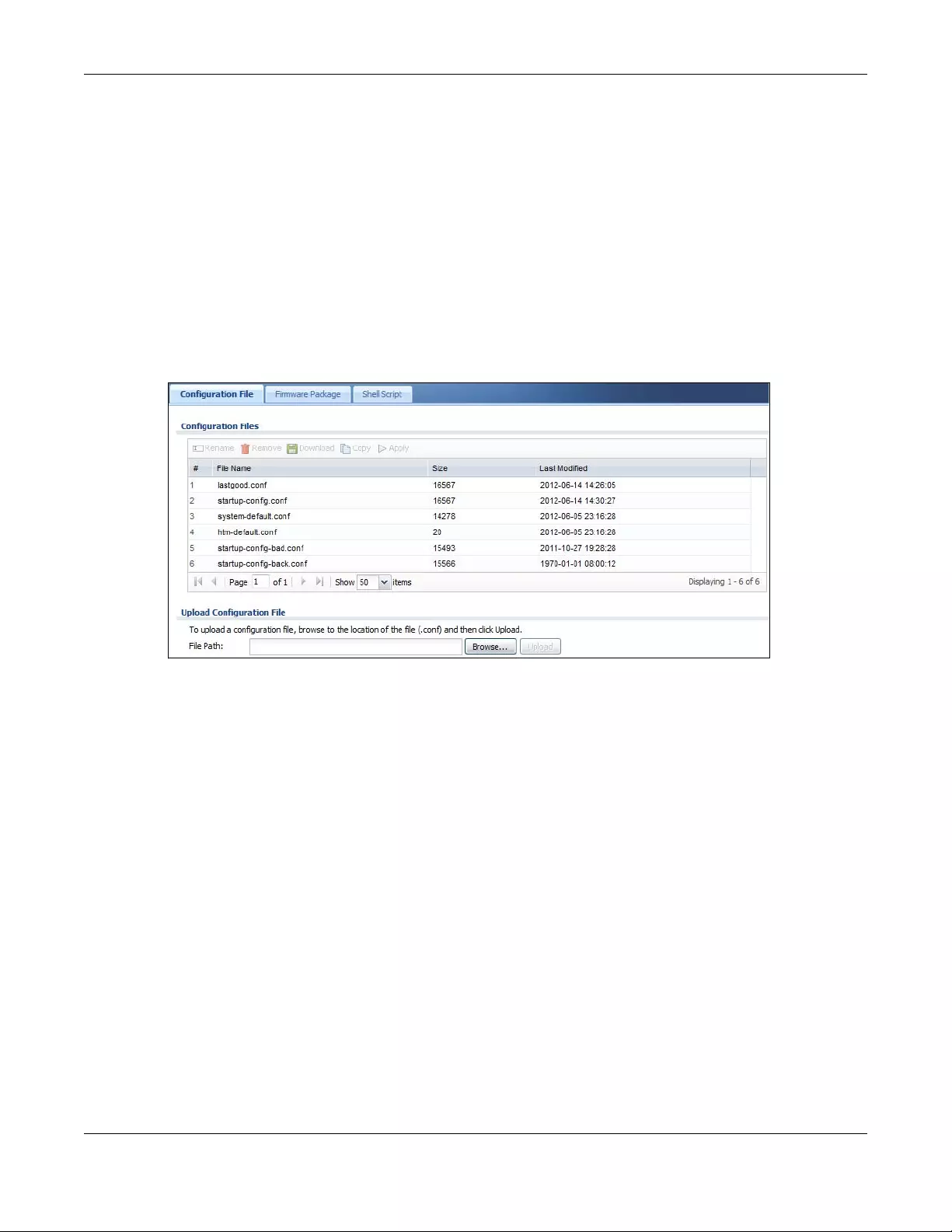
Chapter 46 File Manager
USG/ZyWALL User’s Guide
905
Configuration File Flow at Restart
• If there is not a startup-config.conf when you restart the Zyxel Device (whether through a
management interface or by physically turning the power off and back on), the Zyxel Device uses the
system-default.conf configuration file with the Zyxel Device’s default settings.
•If there is a startup-config.conf, the Zyxel Device checks it for errors and applies it. If there are no
errors, the Zyxel Device uses it and copies it to the lastgood.conf configuration file as a back up file. If
there is an error, the Zyxel Device generates a log and copies the startup-config.conf configuration
file to the startup-config-bad.conf configuration file and tries the existing lastgood.conf configuration
file. If there isn’t a lastgood.conf configuration file or it also has an error, the Zyxel Device applies the
system-default.conf configuration file.
• You can change the way the startup-config.conf file is applied. Include the setenv-startup stop-
on-error off command. The Zyxel Device ignores any errors in the startup-config.conf file and
applies all of the valid commands. The Zyxel Device still generates a log for any errors.
Figure 650 Maintenance > File Manager > Configuration File
Do not turn off the Zyxel Device while configuration file upload is in
progress.
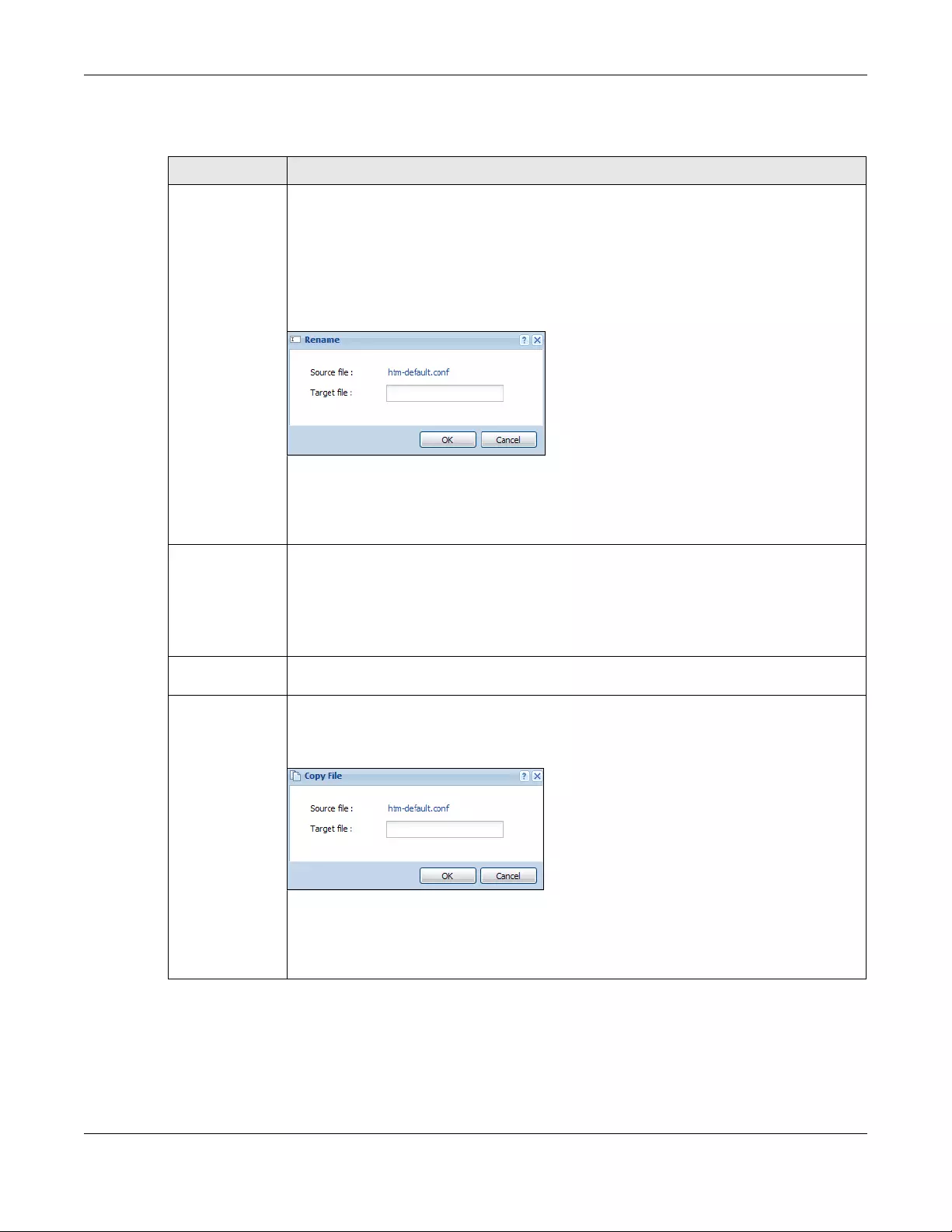
Chapter 46 File Manager
USG/ZyWALL User’s Guide
906
The following table describes the labels in this screen.
Table 382 Maintenance > File Manager > Configuration File
LABEL DESCRIPTION
Rename Use this button to change the label of a configuration file on the Zyxel Device. You can only
rename manually saved configuration files. You cannot rename the lastgood.conf, system-
default.conf and startup-config.conf files.
You cannot rename a configuration file to the name of another configuration file in the Zyxel
Device.
Click a configuration file’s row to select it and click Rename to open the Rename File screen.
Figure 651 Maintenance > File Manager > Configuration File > Rename
Specify the new name for the configuration file. Use up to 25 characters (including a-zA-Z0-
9;‘~!@#$%^&()_+[]{}’,.=-).
Click OK to save the duplicate or click Cancel to close the screen without saving a duplicate
of the configuration file.
Remove Click a configuration file’s row to select it and click Remove to delete it from the Zyxel Device.
You can only delete manually saved configuration files. You cannot delete the system-
default.conf, startup-config.conf and lastgood.conf files.
A pop-up window asks you to confirm that you want to delete the configuration file. Click OK
to delete the configuration file or click Cancel to close the screen without deleting the
configuration file.
Download Click a configuration file’s row to select it and click Download to save the configuration to your
computer.
Copy Use this button to save a duplicate of a configuration file on the Zyxel Device.
Click a configuration file’s row to select it and click Copy to open the Copy File screen.
Figure 652 Maintenance > File Manager > Configuration File > Copy
Specify a name for the duplicate configuration file. Use up to 25 characters (including a-zA-Z0-
9;‘~!@#$%^&()_+[]{}’,.=-).
Click OK to save the duplicate or click Cancel to close the screen without saving a duplicate
of the configuration file.
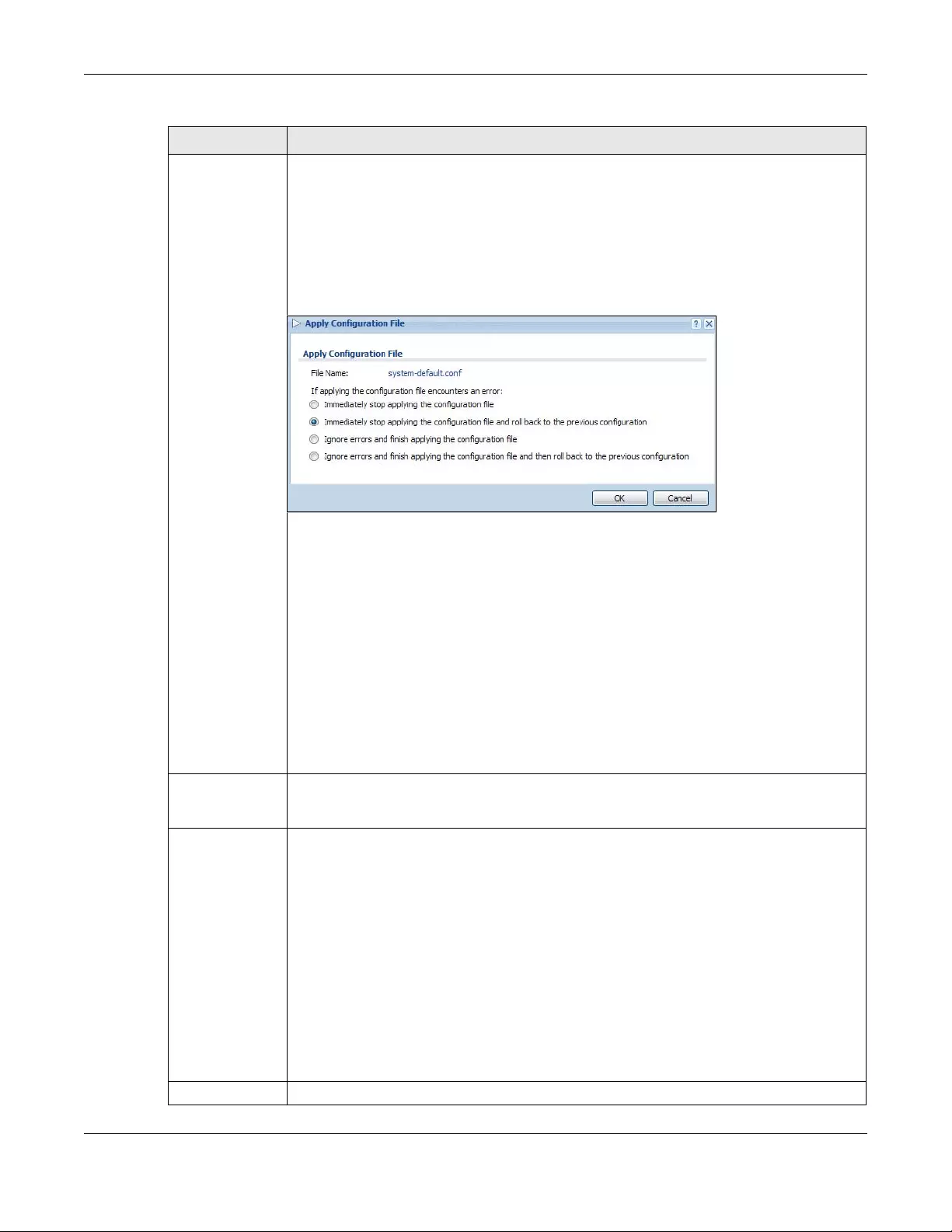
Chapter 46 File Manager
USG/ZyWALL User’s Guide
907
Apply Use this button to have the Zyxel Device use a specific configuration file.
Click a configuration file’s row to select it and click Apply to have the Zyxel Device use that
configuration file. The Zyxel Device does not have to restart in order to use a different
configuration file, although you will need to wait for a few minutes while the system
reconfigures.
The following screen gives you options for what the Zyxel Device is to do if it encounters an
error in the configuration file.
Figure 653 Maintenance > File Manager > Configuration File > Apply
Immediately stop applying the configuration file - this is not recommended because it would
leave the rest of the configuration blank. If the interfaces were not configured before the first
error, the console port may be the only way to access the device.
Immediately stop applying the configuration file and roll back to the previous configuration -
this gets the Zyxel Device started with a fully valid configuration file as quickly as possible.
Ignore errors and finish applying the configuration file - this applies the valid parts of the
configuration file and generates error logs for all of the configuration file’s errors. This lets the
Zyxel Device apply most of your configuration and you can refer to the logs for what to fix.
Ignore errors and finish applying the configuration file and then roll back to the previous
configuration - this applies the valid parts of the configuration file, generates error logs for all of
the configuration file’s errors, and starts the Zyxel Device with a fully valid configuration file.
Click OK to have the Zyxel Device start applying the configuration file or click Cancel to close
the screen
#This column displays the number for each configuration file entry. This field is a sequential value,
and it is not associated with a specific address. The total number of configuration files that you
can save depends on the sizes of the configuration files and the available flash storage space.
File Name This column displays the label that identifies a configuration file.
You cannot delete the following configuration files or change their file names.
The system-default.conf file contains the Zyxel Device’s default settings. Select this file and click
Apply to reset all of the Zyxel Device settings to the factory defaults. This configuration file is
included when you upload a firmware package.
The startup-config.conf file is the configuration file that the Zyxel Device is currently using. If you
make and save changes during your management session, the changes are applied to this
configuration file. The Zyxel Device applies configuration changes made in the Web
Configurator to the configuration file when you click Apply or OK. It applies configuration
changes made via commands when you use the write command.
The lastgood.conf is the most recently used (valid) configuration file that was saved when the
device last restarted. If you upload and apply a configuration file with an error, you can apply
lastgood.conf to return to a valid configuration.
Size This column displays the size (in KB) of a configuration file.
Table 382 Maintenance > File Manager > Configuration File (continued)
LABEL DESCRIPTION
Chapter 46 File Manager
USG/ZyWALL User’s Guide
908
46.3 Firmware Management
Use the Firmware Management screen to check your current firmware version and upload firmware to
the Zyxel Device. You can upload firmware to be the Running firmware or Standby firmware.
Note: The Web Configurator is the recommended method for uploading firmware. You only
need to use the command line interface if you need to recover the firmware. See the
CLI Reference Guide for how to determine if you need to recover the firmware and
how to recover it.
Find the firmware package at www.zyxel.com in a file that (usually) uses the system model name with a
.bin extension, for example, “zywall.bin”.
The Zyxel Device’s firmware package cannot go through the Zyxel Device when you enable the anti-
virus Destroy compressed files that could not be decompressed option. The Zyxel Device classifies the
firmware package as not being able to be decompressed and deletes it. You can upload the firmware
package to the Zyxel Device with the option enabled, so you only need to clear the Destroy
compressed files that could not be decompressed option while you download the firmware package.
See Section 39.2.1 on page 683 for more on the anti-virus Destroy compressed files that could not be
decompressed option.
The firmware update can take up to five minutes. Do not turn off or reset
the Zyxel Device while the firmware update is in progress!
46.3.1 Cloud Helper
Cloud Helper lets you know if there is a later firmware available on the Cloud Helper server and lets you
download it if you did. You must register your Zyxel Device Firmware license at myZyxel.com first. At the
time of writing, the Firmware Upgrade license providing Cloud Helper new firmware notifications is free
when you register your Zyxel Device.
Last Modified This column displays the date and time that the individual configuration files were last
changed or saved.
Upload
Configuration File
The bottom part of the screen allows you to upload a new or previously saved configuration
file from your computer to your Zyxel Device
You cannot upload a configuration file named system-default.conf or lastgood.conf.
If you upload startup-config.conf, it will replace the current configuration and immediately
apply the new settings.
File Path Type in the location of the file you want to upload in this field or click Browse ... to find it.
Browse... Click Browse... to find the .conf file you want to upload. The configuration file must use a
“.conf” filename extension. You will receive an error message if you try to upload a fie of a
different format. Remember that you must decompress compressed (.zip) files before you can
upload them.
Upload Click Upload to begin the upload process. This process may take up to two minutes.
Table 382 Maintenance > File Manager > Configuration File (continued)
LABEL DESCRIPTION

Chapter 46 File Manager
USG/ZyWALL User’s Guide
909
The following table explains the Upgrade icons in the web configurator.
Table 383 Cloud Helper Firmware Icons
Cloud Helper New A later firmware is available on the Cloud Helper Server. Click this icon to
display a What’s New pop-up screen. You need a Firmware Upgrade license
to upgrade the firmware. If you do not have a license, Upgrade Now is
grayed out. If you have a license, click Upgrade Now to directly upgrade
firmware to the standby partition and have the Zyxel Device reboot
automatically so that the new standby firmware becomes the running
firmware. The previous running firmware becomes the standby firmware.
Cloud Helper Flag Cloud firmware is being downloaded from the Cloud Helper Server. If you
select another partition or the local firmware upgrade icon, you will see the
following warning message.
When firmware is downloading, you can pause, resume, stop or retry the
firmware download.
Local Firmware Use this if you have already downloaded the latest firmware from the Zyxel
website to your computer and unzipped it. Click the icon and then browse to
the location of the unzipped files.
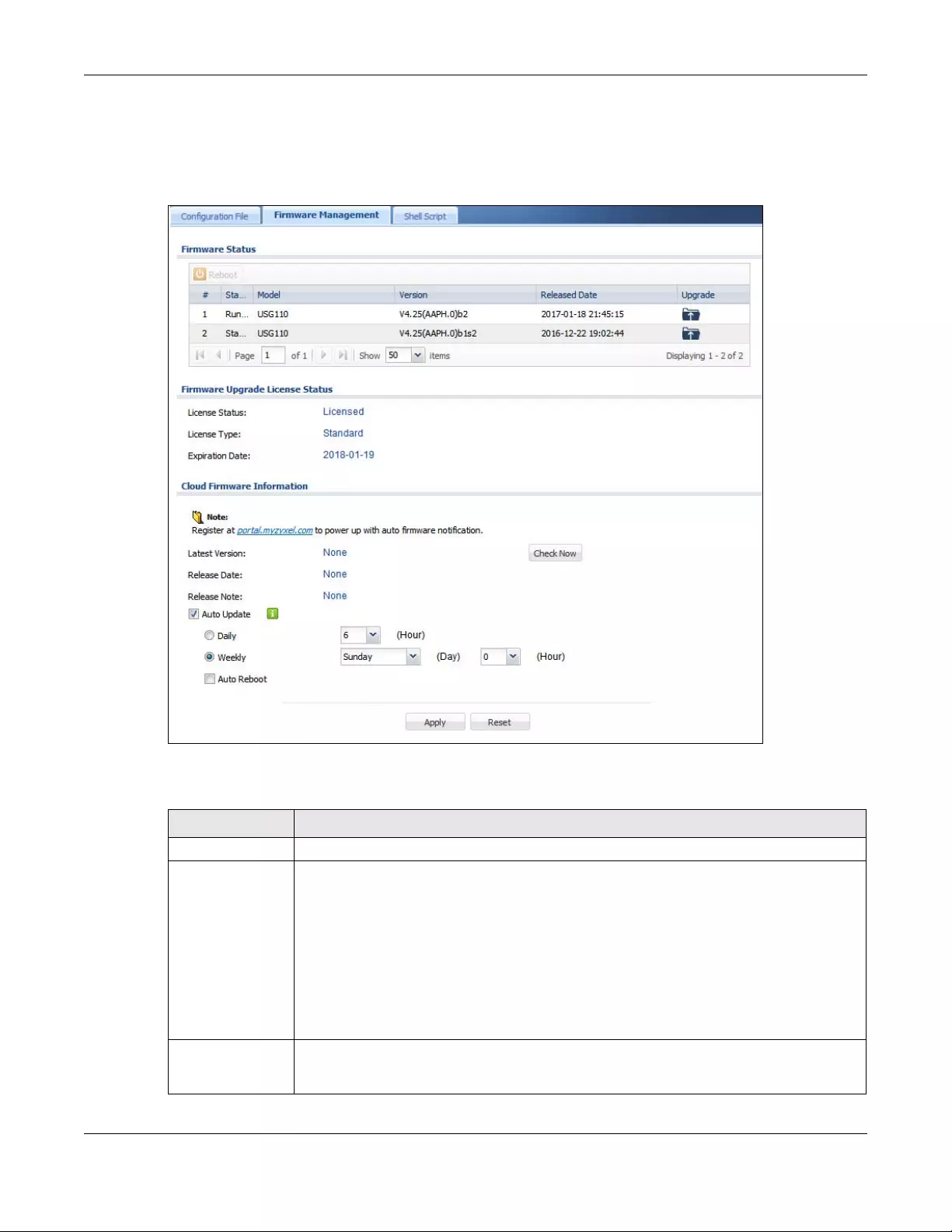
Chapter 46 File Manager
USG/ZyWALL User’s Guide
910
46.3.2 The Firmware Management Screen
Click Maintenance > File Manager > Firmware Management to open the Firmware Management screen.
Figure 654 Maintenance > File Manager > Firmware Management
The following table describes the labels in this screen.
Table 384 Maintenance > File Manager > Firmware Management
LABEL DESCRIPTION
Firmware Status
Reboot Click the Reboot icon to restart the Zyxel Device. If you applied changes in the Web
configurator, these were saved automatically and do not change when you reboot. If you
made changes in the CLI, however, you have to use the write command to save the
configuration before you reboot. Otherwise, the changes are lost when you reboot.
If you want the Standby firmware to be the Running firmware, then select the Standby
firmware row and click Reboot. Wait a few minutes until the login screen appears. If the login
screen does not appear, clear your browser cache and refresh the screen or type the IP
address of the Zyxel Device in your Web browser again.
You can also use the CLI command reboot to restart the Zyxel Device.
# This displays the system space (partition) index number where the firmware is located. The
firmware can be either Standby or Running; only one firmware can be running at any one
time.
Chapter 46 File Manager
USG/ZyWALL User’s Guide
911
After you see the Firmware Upload in Process screen, wait a few minutes before logging into the Zyxel
Device again.
Figure 655 Firmware Upload In Process
Note: The Zyxel Device automatically reboots after a successful upload.
The Zyxel Device automatically restarts causing a temporary network disconnect. In some operating
systems, you may see the following icon on your desktop.
Status This indicates whether the firmware is Running, or not running but already uploaded to the
Zyxel Device and is on Standby. It displays N/A if there is no firmware uploaded to that system
space.
Model This is the model name of the device which the firmware is running on.
Version This is the firmware version and the date created.
Released Date This is the date that the version of the firmware was created.
Upgrade A cloud helper icon displays if there is a later firmware on the Cloud Server than the firmware
in the partition. Click the cloud helper icon to download a later firmware from the Cloud
Helper Server.
Use the local firmware icon if you have already downloaded the latest firmware from the
Zyxel website to your computer and unzipped it.
Firmware Upgrade License Status
License Status This field displays whether the firmware license service is activated (Licensed) or not (Not
Licensed) or expired (Expired).
License Type This field displays the registration firmware license type: Standard or None.
Expiration Date This field displays the date your firmware license service expires. Go to myZyxel.com to
reactivate the license.
Cloud Firmware
Information
You must register your Zyxel Device at myZyxel.com first to use cloud firmware.
Latest Version This displays the latest firmware version at the Cloud Helper Server. Click Check Now to see if
there is a later firmware at the Cloud Server.
Release Date This displays the date the latest firmware version was made available.
Release Note The release note contains details of latest firmware version such as new features and bug
fixes.
Auto Update Select this check box to have the Zyxel Device automatically check for and download new
firmware to the standby partition at the time and day specified.
You should select a time when your network is not busy for minimal interruption.
Daily Select this option to have the Zyxel Device check for new firmware every day at the specified
time. The time format is the 24 hour clock, so ‘0’ means midnight for example.
Weekly Select this option to have the Zyxel Device check for new firmware once a week on the day
and at the time specified.
Auto Reboot Select this to have the newly downloaded firmware in the standby partition become the
running firmware after the Zyxel Device automatically restarts.
Table 384 Maintenance > File Manager > Firmware Management (continued)
LABEL DESCRIPTION
Chapter 46 File Manager
USG/ZyWALL User’s Guide
912
Figure 656 Network
After five minutes, log in again and check your new firmware version in the Dashboard screen.
If the upload was not successful, the following message appears in the status bar at the bottom of the
screen.
Figure 657 Firmware Upload Error
46.3.3 Firmware Upgrade via USB Stick
In addition to uploading firmware via the web configurator or console port (see the CLI Reference
Guide), you can also upload firmware directly from a USB stick connected to the Zyxel Device.
1Create a folder on the USB stick called ‘/[ProductName_dir]/firmware’. For example, if your Zyxel Device
is USG110, then create a ‘/usg110_dir/firmware/’ folder on the stick.
2Put one firmware ‘bin’ file into the firmware folder. Make sure the firmware ID and version number are
correct for your model (the firmware ID is in brackets after the firmware version number - for USG100 it is
AAPH).
Note: Do not put more than one firmware ‘bin’ file into the firmware folder.
The firmware version in the USB stick must be different to the currently running firmware.
If the firmware on the USB stick is older, then the Zyxel Device will ‘upgrade’ to the older
version. It is recommended that the firmware on the USB stick be the latest firmware
version.
3Insert the USB stick into the Zyxel Device. The firmware uploads to the standby system space.
4The SYS LED blinks when the Zyxel Device automatically reboots making the upgraded firmware in
standby become the running firmware.
Note: If the startup-config.conf configuration file has problems and you are upgrading to 4.25
or later firmware, then the Zyxel Device will revert (failover) to the previously running
firmware.
If the startup-config.conf configuration file has problems and you are upgrading to
earlier than 4.25 firmware, then the Zyxel Device uses the new earlier firmware, but
generates a log and tries the existing lastgood.conf configuration file. If there isn’t a
lastgood.conf configuration file or it also has an error, the Zyxel Device applies the
system-default.conf configuration file.
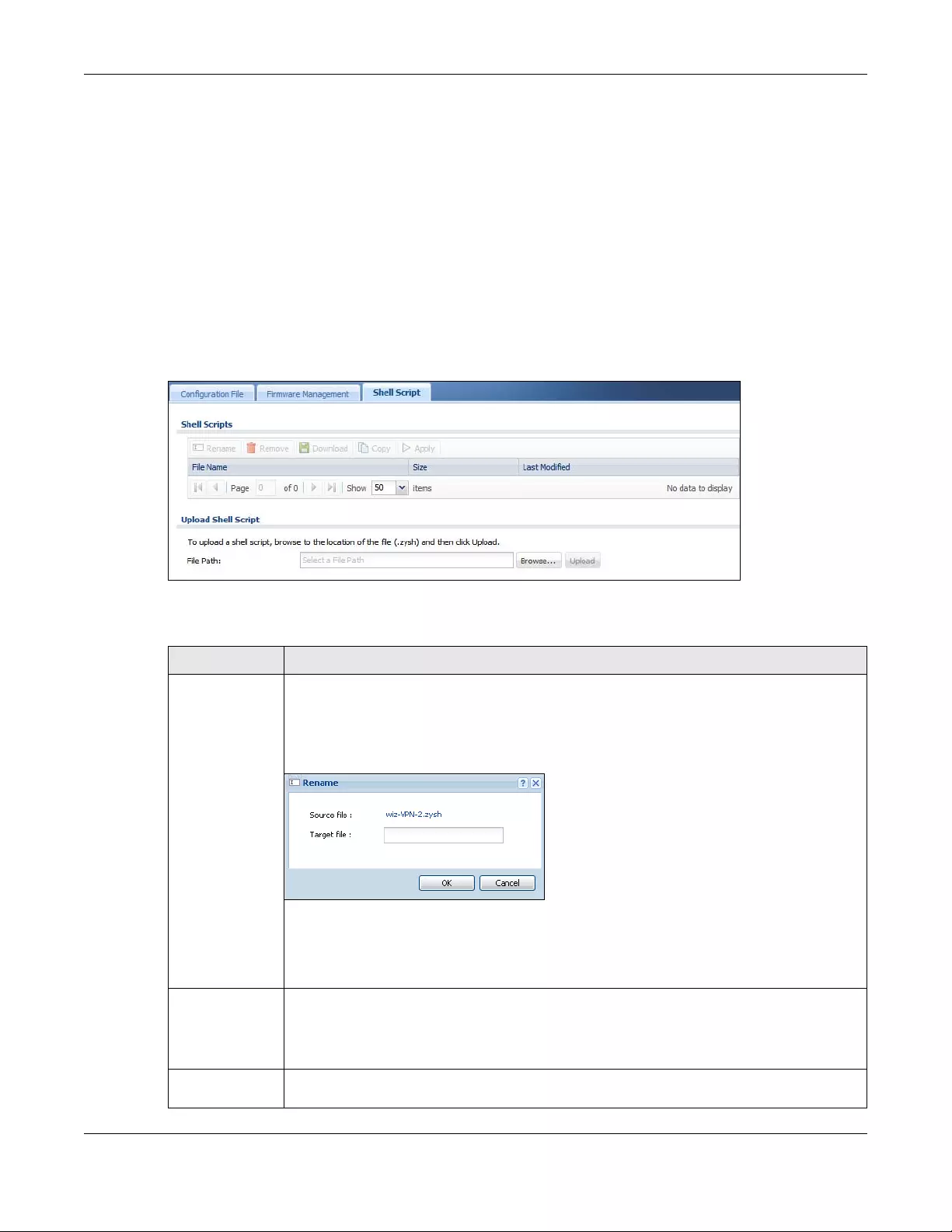
Chapter 46 File Manager
USG/ZyWALL User’s Guide
913
46.4 The Shell Script Screen
Use shell script files to have the Zyxel Device use commands that you specify. Use a text editor to create
the shell script files. They must use a “.zysh” filename extension.
Click Maintenance > File Manager > Shell Script to open the Shell Script screen. Use the Shell Script
screen to store, name, download, upload and run shell script files. You can store multiple shell script files
on the Zyxel Device at the same time.
Note: You should include write commands in your scripts. If you do not use the write
command, the changes will be lost when the Zyxel Device restarts. You could use
multiple write commands in a long script.
Figure 658 Maintenance > File Manager > Shell Script
Each field is described in the following table.
Table 385 Maintenance > File Manager > Shell Script
LABEL DESCRIPTION
Rename Use this button to change the label of a shell script file on the Zyxel Device.
You cannot rename a shell script to the name of another shell script in the Zyxel Device.
Click a shell script’s row to select it and click Rename to open the Rename File screen.
Figure 659 Maintenance > File Manager > Shell Script > Rename
Specify the new name for the shell script file. Use up to 25 characters (including a-zA-Z0-
9;‘~!@#$%^&()_+[]{}’,.=-).
Click OK to save the duplicate or click Cancel to close the screen without saving a duplicate of
the configuration file.
Remove Click a shell script file’s row to select it and click Remove to delete the shell script file from the
Zyxel Device.
A pop-up window asks you to confirm that you want to delete the shell script file. Click OK to
delete the shell script file or click Cancel to close the screen without deleting the shell script file.
Download Click a shell script file’s row to select it and click Download to save the configuration to your
computer.
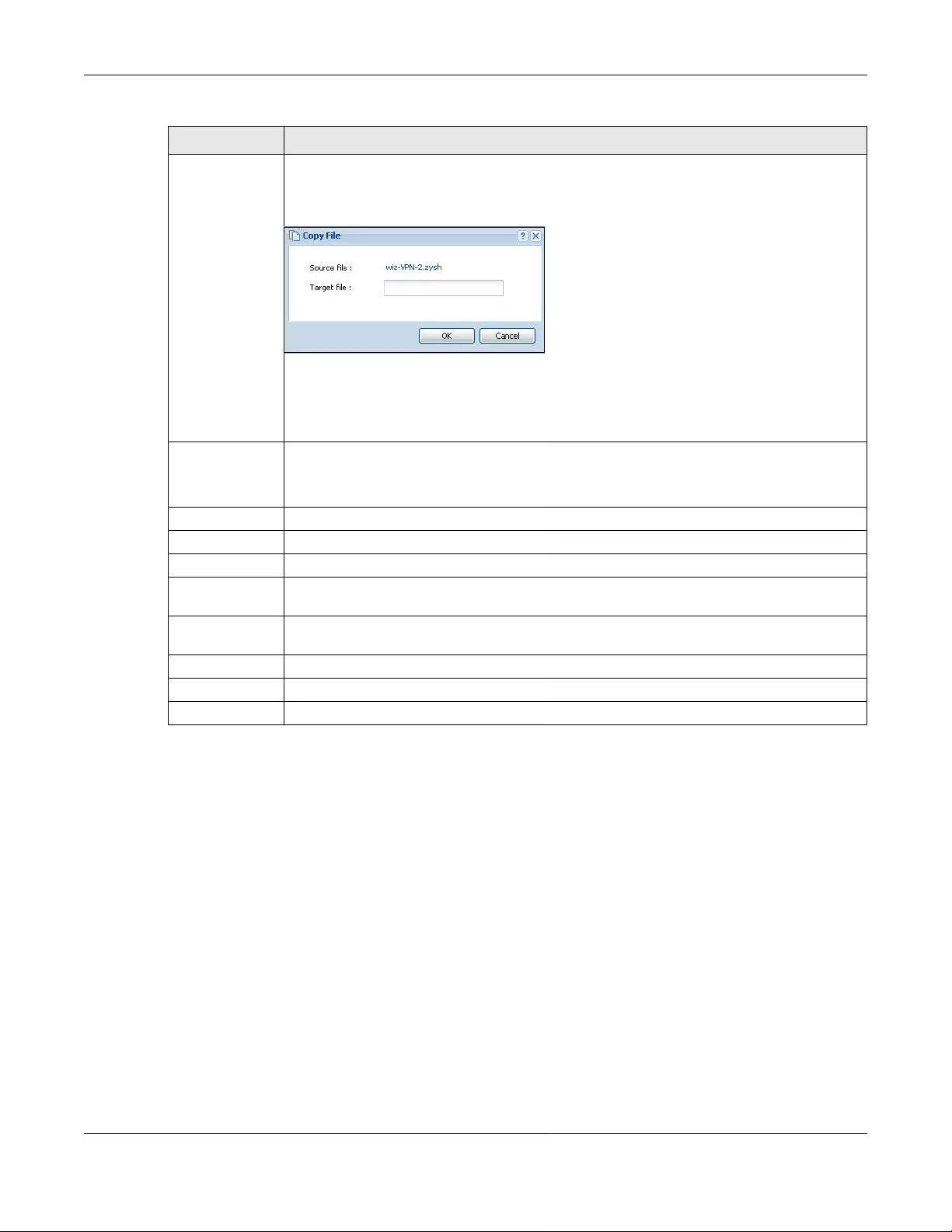
Chapter 46 File Manager
USG/ZyWALL User’s Guide
914
Copy Use this button to save a duplicate of a shell script file on the Zyxel Device.
Click a shell script file’s row to select it and click Copy to open the Copy File screen.
Figure 660 Maintenance > File Manager > Shell Script > Copy
Specify a name for the duplicate file. Use up to 25 characters (including a-zA-Z0-
9;‘~!@#$%^&()_+[]{}’,.=-).
Click OK to save the duplicate or click Cancel to close the screen without saving a duplicate of
the configuration file.
Apply Use this button to have the Zyxel Device use a specific shell script file.
Click a shell script file’s row to select it and click Apply to have the Zyxel Device use that shell
script file. You may need to wait awhile for the Zyxel Device to finish applying the commands.
#This column displays the number for each shell script file entry.
File Name This column displays the label that identifies a shell script file.
Size This column displays the size (in KB) of a shell script file.
Last Modified This column displays the date and time that the individual shell script files were last changed or
saved.
Upload Shell
Script
The bottom part of the screen allows you to upload a new or previously saved shell script file
from your computer to your Zyxel Device.
File Path Type in the location of the file you want to upload in this field or click Browse ... to find it.
Browse... Click Browse... to find the .zysh file you want to upload.
Upload Click Upload to begin the upload process. This process may take up to several minutes.
Table 385 Maintenance > File Manager > Shell Script (continued)
LABEL DESCRIPTION
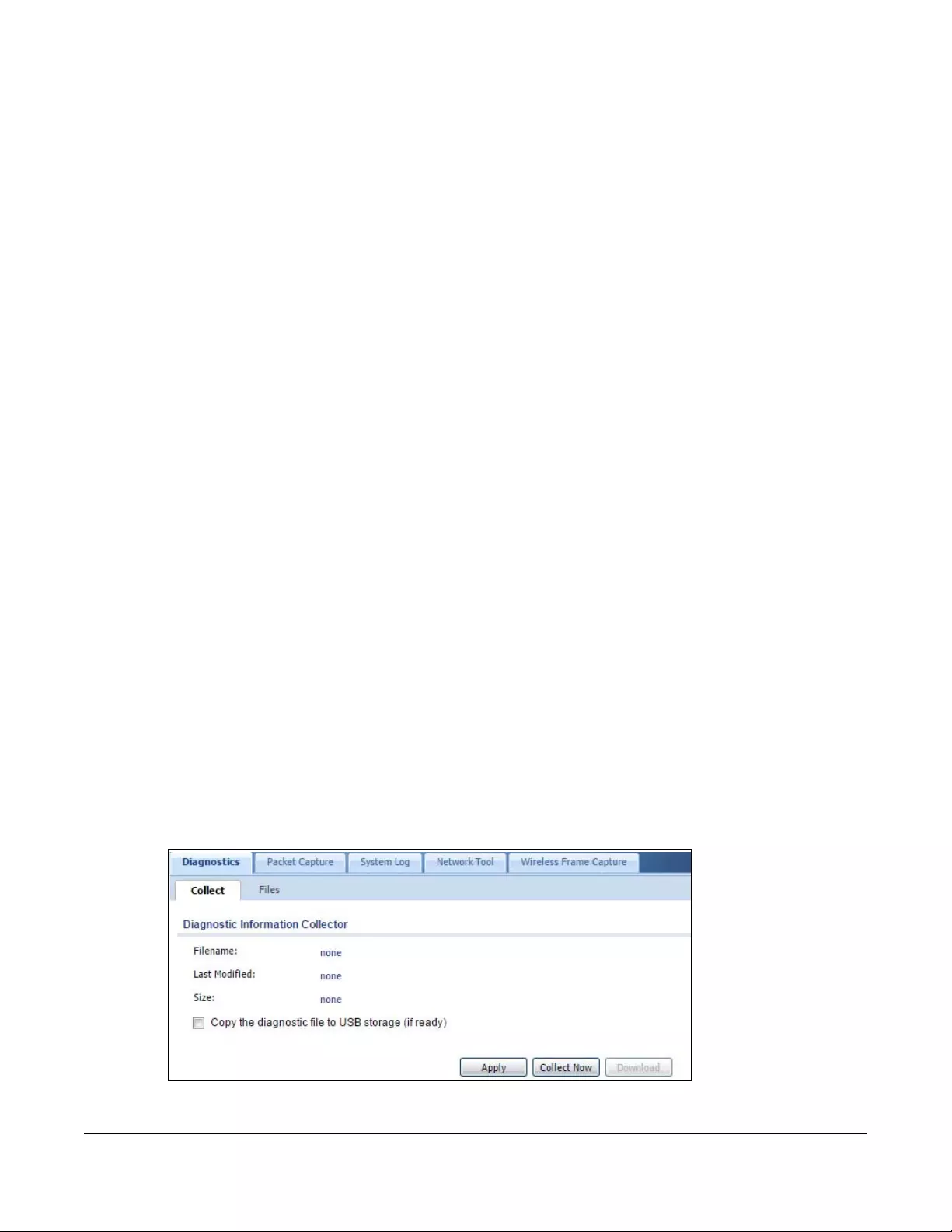
USG/ZyWALL User’s Guide
915
CHAPTER 47
Diagnostics
47.1 Overview
Use the diagnostics screens for troubleshooting.
47.1.1 What You Can Do in this Chapter
• Use the Diagnostics screen (see Section 47.2 on page 915) to generate a file containing the Zyxel
Device’s configuration and diagnostic information if you need to provide it to customer support
during troubleshooting.
• Use the Packet Capture screens (see Section 47.3 on page 917) to capture packets going through the
Zyxel Device.
• Use the System Logs screen (see Section 47.4 on page 920) to see system logs stored on a connected
USB storage device on the Zyxel Device.
• Use the Network Tool screen (see Section 47.5 on page 921) to ping an IP address or trace the route
packets take to a host.
• Use the Wireless Frame Capture screens (see Section 47.6 on page 922) to capture network traffic
going through the AP interfaces connected to your Zyxel Device.
47.2 The Diagnostic Screen
The Diagnostic screen provides an easy way for you to generate a file containing the Zyxel Device’s
configuration and diagnostic information. You may need to send this file to customer support for
troubleshooting.
Click Maintenance > Diagnostics to open the Diagnostic screen.
Figure 661 Maintenance > Diagnostics
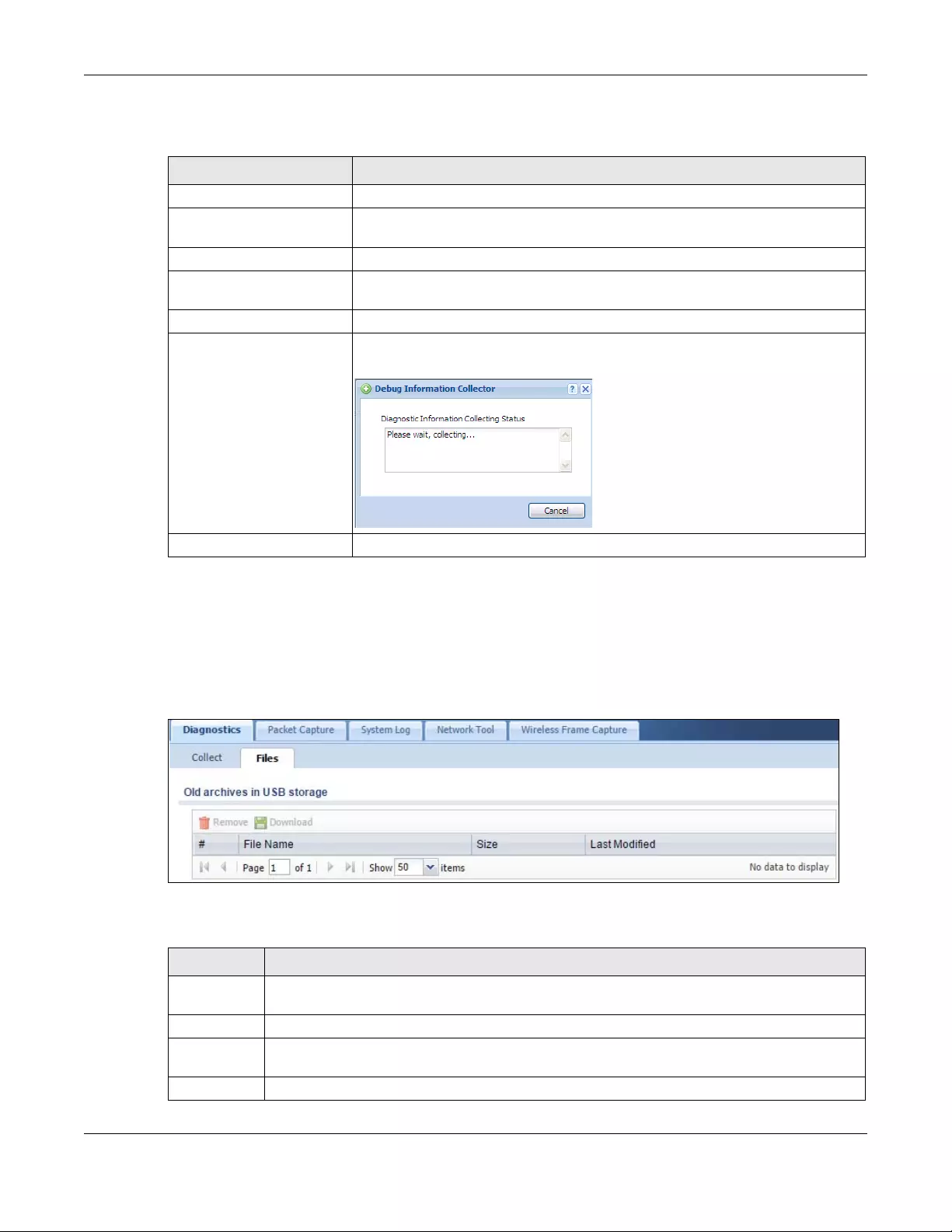
Chapter 47 Diagnostics
USG/ZyWALL User’s Guide
916
The following table describes the labels in this screen.
47.2.1 The Diagnostics Files Screen
Click Maintenance > Diagnostics > Files to open the diagnostic files screen. This screen lists the files of
diagnostic information the Zyxel Device has collected and stored in a connected USB storage device.
You may need to send these files to customer support for troubleshooting.
Figure 662 Maintenance > Diagnostics > Files
The following table describes the labels in this screen.
Table 386 Maintenance > Diagnostics
LABEL DESCRIPTION
Filename This is the name of the most recently created diagnostic file.
Last modified This is the date and time that the last diagnostic file was created. The format is yyyy-
mm-dd hh:mm:ss.
Size This is the size of the most recently created diagnostic file.
Copy the diagnostic file to
USB storage (if ready)
Select this to have the Zyxel Device create an extra copy of the diagnostic file to a
connected USB storage device.
Apply Click Apply to save your changes.
Collect Now Click this to have the Zyxel Device create a new diagnostic file.
Wait while information is collected.
Download Click this to save the most recent diagnostic file to a computer.
Table 387 Maintenance > Diagnostics > Files
LABEL DESCRIPTION
Remove Select files and click Remove to delete them from the Zyxel Device. Use the [Shift] and/or [Ctrl] key
to select multiple files. A pop-up window asks you to confirm that you want to delete.
Download Click a file to select it and click Download to save it to your computer.
#This column displays the number for each file entry. The total number of files that you can save
depends on the file sizes and the available storage space.
File Name This column displays the label that identifies the file.
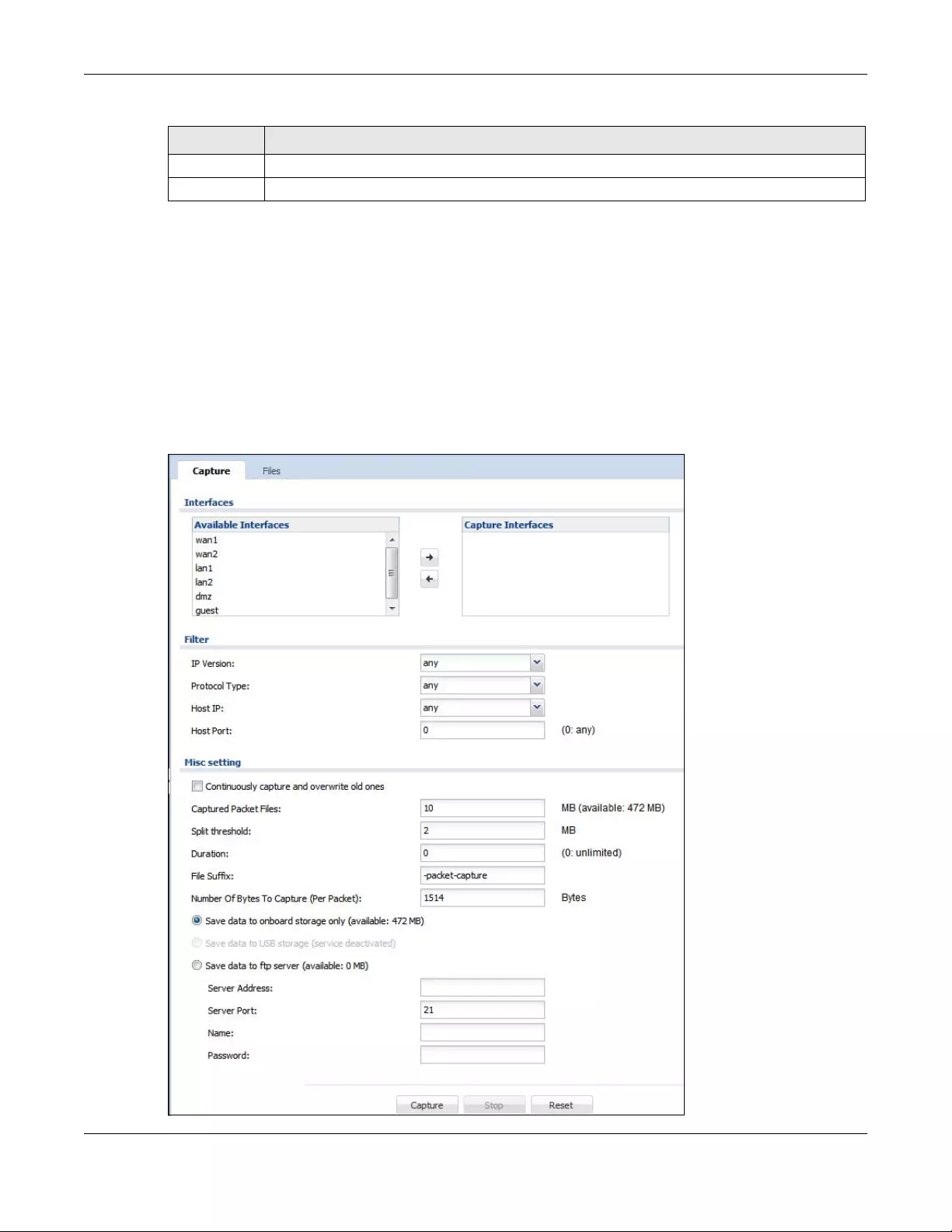
Chapter 47 Diagnostics
USG/ZyWALL User’s Guide
917
47.3 The Packet Capture Screen
Use this screen to capture network traffic going through the Zyxel Device’s interfaces. Studying these
packet captures may help you identify network problems. Click Maintenance > Diagnostics > Packet
Capture to open the packet capture screen.
Note: New capture files overwrite existing files of the same name. Change the File Suffix field’s
setting to avoid this.
Figure 663 Maintenance > Diagnostics > Packet Capture
Size This column displays the size (in bytes) of a file.
Last Modified This column displays the date and time that the individual files were saved.
Table 387 Maintenance > Diagnostics > Files (continued)
LABEL DESCRIPTION
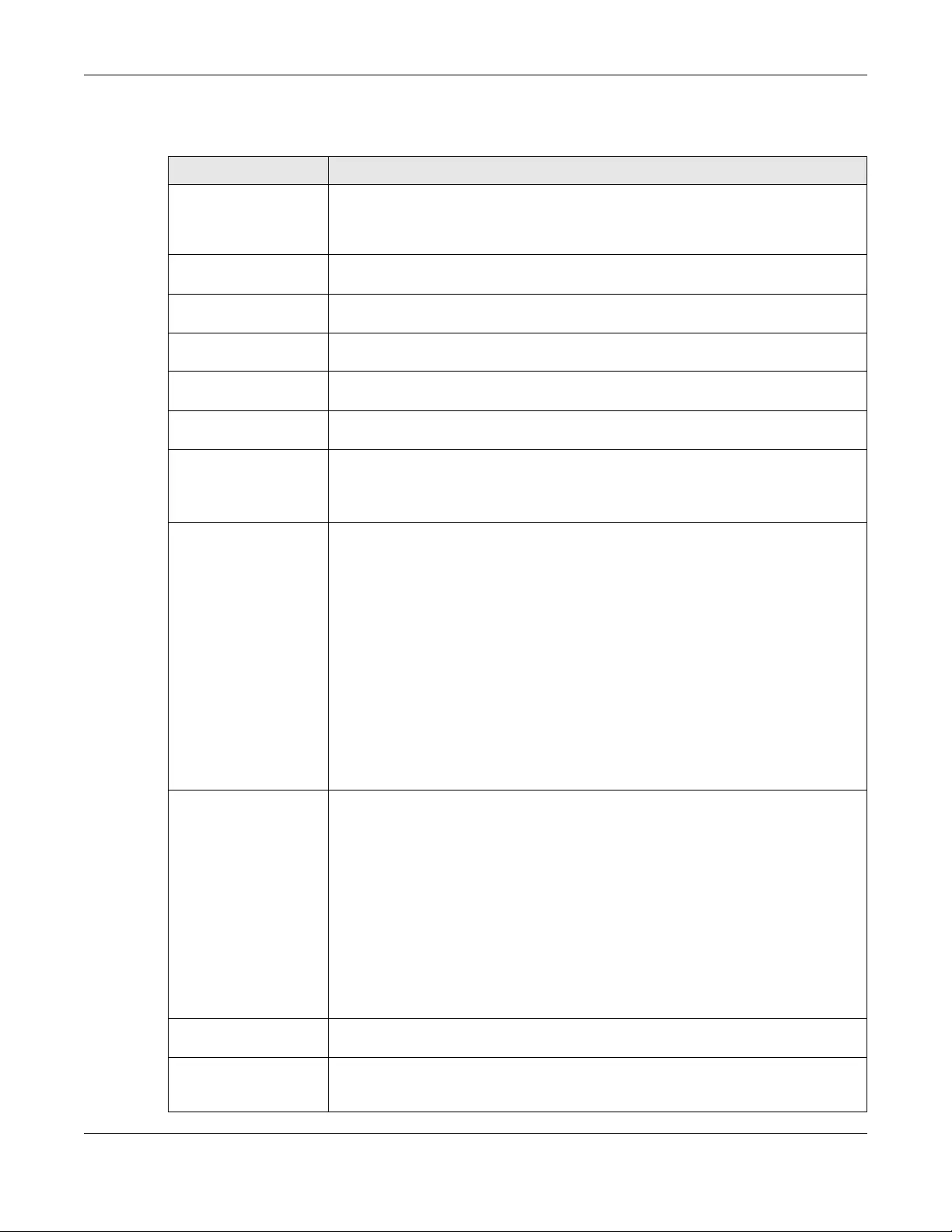
Chapter 47 Diagnostics
USG/ZyWALL User’s Guide
918
The following table describes the labels in this screen.
Table 388 Maintenance > Diagnostics > Packet Capture
LABEL DESCRIPTION
Interfaces Enabled interfaces (except for virtual interfaces) appear under Available Interfaces.
Select interfaces for which to capture packets and click the right arrow button to move
them to the Capture Interfaces list. Use the [Shift] and/or [Ctrl] key to select multiple
objects.
IP Version Select the version of IP for which to capture packets. Select any to capture packets for
all IP versions.
Protocol Type Select the protocol of traffic for which to capture packets. Select any to capture
packets for all types of traffic.
Host IP Select a host IP address object for which to capture packets. Select any to capture
packets for all hosts. Select User Defined to be able to enter an IP address.
Host Port This field is configurable when you set the IP Type to any, tcp, or udp. Specify the port
number of traffic to capture.
Continuously capture
and overwrite old ones
Select this to have the Zyxel Device keep capturing traffic and overwriting old packet
capture entries when the available storage space runs out.
Save data to onboard
storage only
Select this to have the Zyxel Device only store packet capture entries on the Zyxel
Device. The available storage size is displayed as well.
Note: The Zyxel Device reserves some on board storage space as a buffer.
Save data to USB
storage
Select this to have the Zyxel Device store packet capture entries only on a USB storage
device connected to the Zyxel Device if the Zyxel Device allows this.
Status:
Unused - the connected USB storage device was manually unmounted by using the
Remove Now button or for some reason the Zyxel Device cannot mount it.
none - no USB storage device is connected.
service deactivated - USB storage feature is disabled (in Configuration > System > USB
Storage), so the Zyxel Device cannot use a connected USB device to store system logs
and other diagnostic information.
available - you can have the Zyxel Device use the USB storage device. The available
storage capacity also displays.
Note: The Zyxel Device reserves some USB storage space as a buffer.
Captured Packet Files When saving packet captures only to the Zyxel Device’s on board storage, specify a
maximum limit in megabytes for the total combined size of all the capture files on the
Zyxel Device.
When saving packet captures to a connected USB storage device, specify a maximum
limit in megabytes for each capture file.
Note: If you have existing capture files and have not selected the
Continuously capture and overwrite old ones option, you may need to
set this size larger or delete existing capture files.
The valid range depends on the available on board/USB storage size. The Zyxel Device
stops the capture and generates the capture file when either the file reaches this size or
the time period specified in the Duration field expires.
Split threshold Specify a maximum size limit in megabytes for individual packet capture files. After a
packet capture file reaches this size, the Zyxel Device starts another packet capture file.
Duration Set a time limit in seconds for the capture. The Zyxel Device stops the capture and
generates the capture file when either this period of time has passed or the file reaches
the size specified in the File Size field. 0 means there is no time limit.
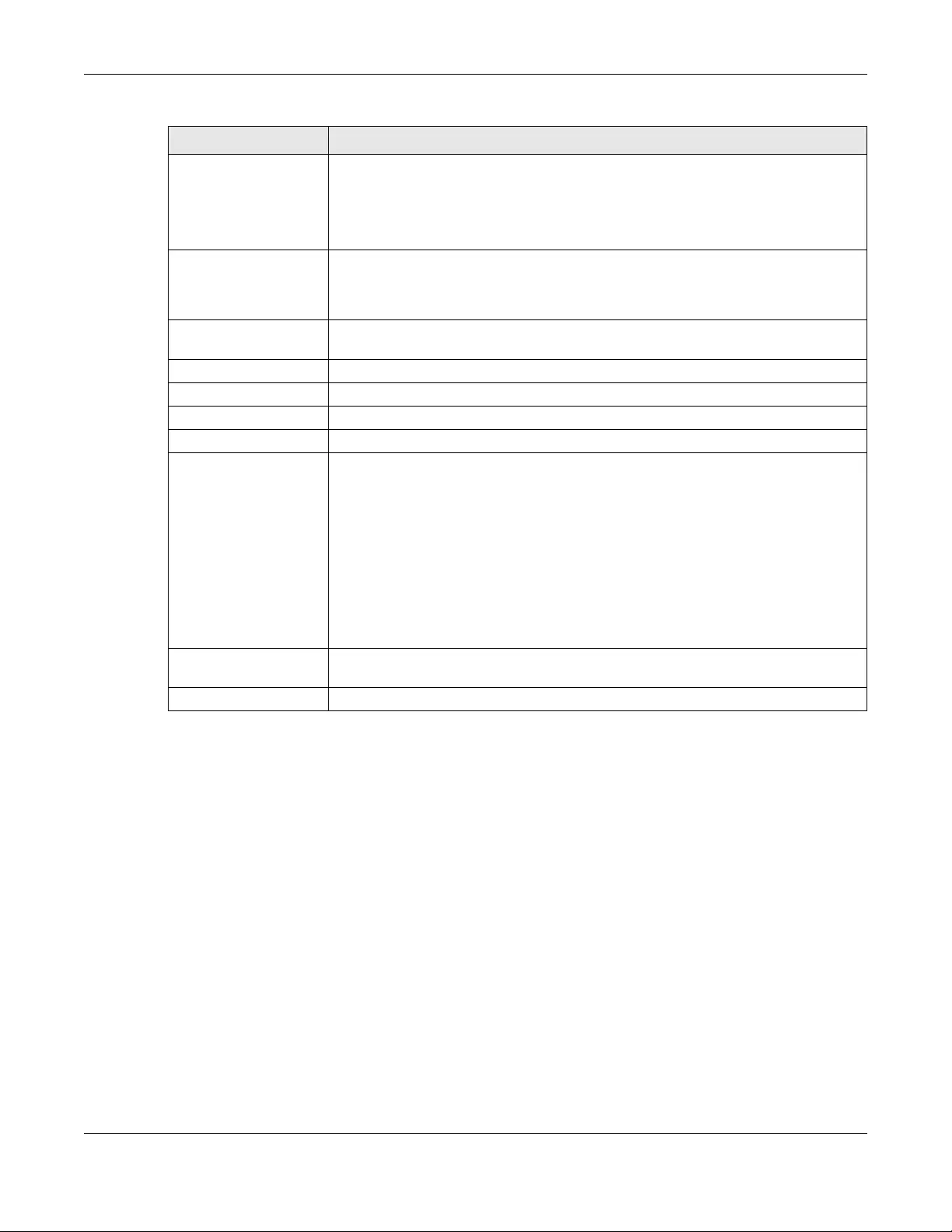
Chapter 47 Diagnostics
USG/ZyWALL User’s Guide
919
47.3.1 The Packet Capture Files Screen
Click Maintenance > Diagnostics > Packet Capture > Files to open the packet capture files screen. This
screen lists the files of packet captures stored on the Zyxel Device or a connected USB storage device.
You can download the files to your computer where you can study them using a packet analyzer (also
known as a network or protocol analyzer) such as Wireshark.
File Suffix Specify text to add to the end of the file name (before the dot and filename extension)
to help you identify the packet capture files. Modifying the file suffix also avoids making
new capture files that overwrite existing files of the same name.
The file name format is “interface name-file suffix.cap”, for example “vlan2-packet-
capture.cap”.
Number Of Bytes To
Capture (Per Packet)
Specify the maximum number of bytes to capture per packet. The Zyxel Device
automatically truncates packets that exceed this size. As a result, when you view the
packet capture files in a packet analyzer, the actual size of the packets may be larger
than the size of captured packets.
Save data to ftp server
(available: xx MB)
Select this to have the Zyxel Device store packet capture entries on the defined FTP site.
The available storage size is displayed as well.
Server Address Type the IP address of the FTP server.
Server Port Type the port this server uses for FTP traffic. The default FTP port is 21.
Name Type the login username to access the FTP server.
Password Type the associated login password to access the FTP server.
Capture Click this button to have the Zyxel Device capture packets according to the settings
configured in this screen.
You can configure the Zyxel Device while a packet capture is in progress although you
cannot modify the packet capture settings.
The Zyxel Device’s throughput or performance may be affected while a packet capture
is in progress.
After the Zyxel Device finishes the capture it saves a separate capture file for each
selected interface. The total number of packet capture files that you can save depends
on the file sizes and the available flash storage space. Once the flash storage space is
full, adding more packet captures will fail.
Stop Click this button to stop a currently running packet capture and generate a separate
capture file for each selected interface.
Reset Click this button to return the screen to its last-saved settings.
Table 388 Maintenance > Diagnostics > Packet Capture (continued)
LABEL DESCRIPTION
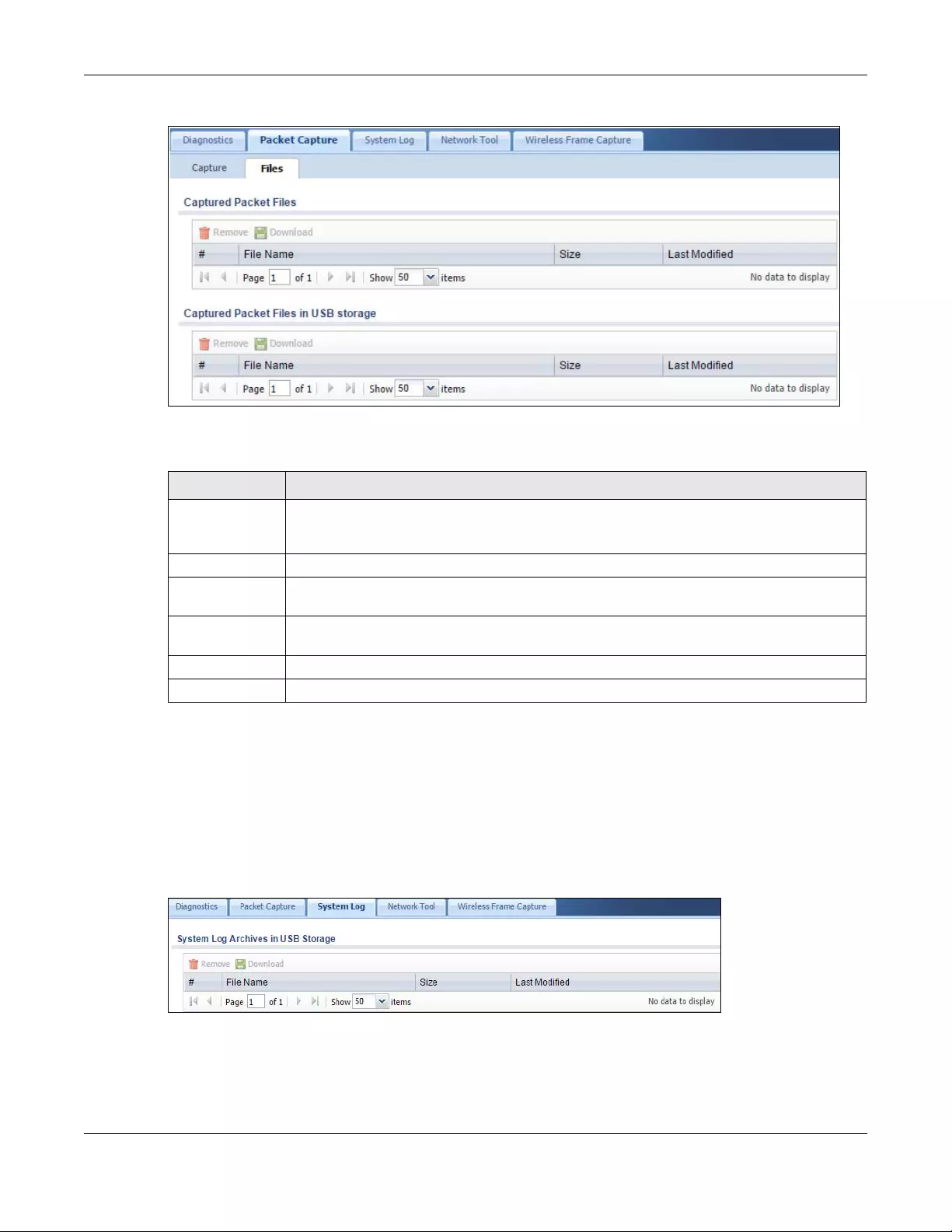
Chapter 47 Diagnostics
USG/ZyWALL User’s Guide
920
Figure 664 Maintenance > Diagnostics > Packet Capture > Files
The following table describes the labels in this screen.
47.4 The System Log Screen
Click Maintenance > Diagnostics > System Log to open the system log files screen. This screen lists the
files of system logs stored on a connected USB storage device. The files are in comma separated value
(csv) format. You can download them to your computer and open them in a tool like Microsoft’s Excel.
Figure 665 Maintenance > Diagnostics > System Log
Table 389 Maintenance > Diagnostics > Packet Capture > Files
LABEL DESCRIPTION
Remove Select files and click Remove to delete them from the Zyxel Device or the connected USB
storage device. Use the [Shift] and/or [Ctrl] key to select multiple files. A pop-up window asks
you to confirm that you want to delete.
Download Click a file to select it and click Download to save it to your computer.
#This column displays the number for each packet capture file entry. The total number of packet
capture files that you can save depends on the file sizes and the available flash storage space.
File Name This column displays the label that identifies the file. The file name format is interface name-file
suffix.cap.
Size This column displays the size (in bytes) of a configuration file.
Last Modified This column displays the date and time that the individual files were saved.
Chapter 47 Diagnostics
USG/ZyWALL User’s Guide
921
The following table describes the labels in this screen.
47.5 The Network Tool Screen
Use this screen to ping or traceroute an IP address.
Click Maintenance > Diagnostics > Network Tool to display this screen.
Figure 666 Maintenance > Diagnostics > Network Tool
Table 390 Maintenance > Diagnostics > System Log
LABEL DESCRIPTION
Remove Select files and click Remove to delete them from the Zyxel Device. Use the [Shift] and/or [Ctrl]
key to select multiple files. A pop-up window asks you to confirm that you want to delete.
Download Click a file to select it and click Download to save it to your computer.
#This column displays the number for each file entry. The total number of files that you can save
depends on the file sizes and the available storage space.
File Name This column displays the label that identifies the file.
Size This column displays the size (in bytes) of a file.
Last Modified This column displays the date and time that the individual files were saved.
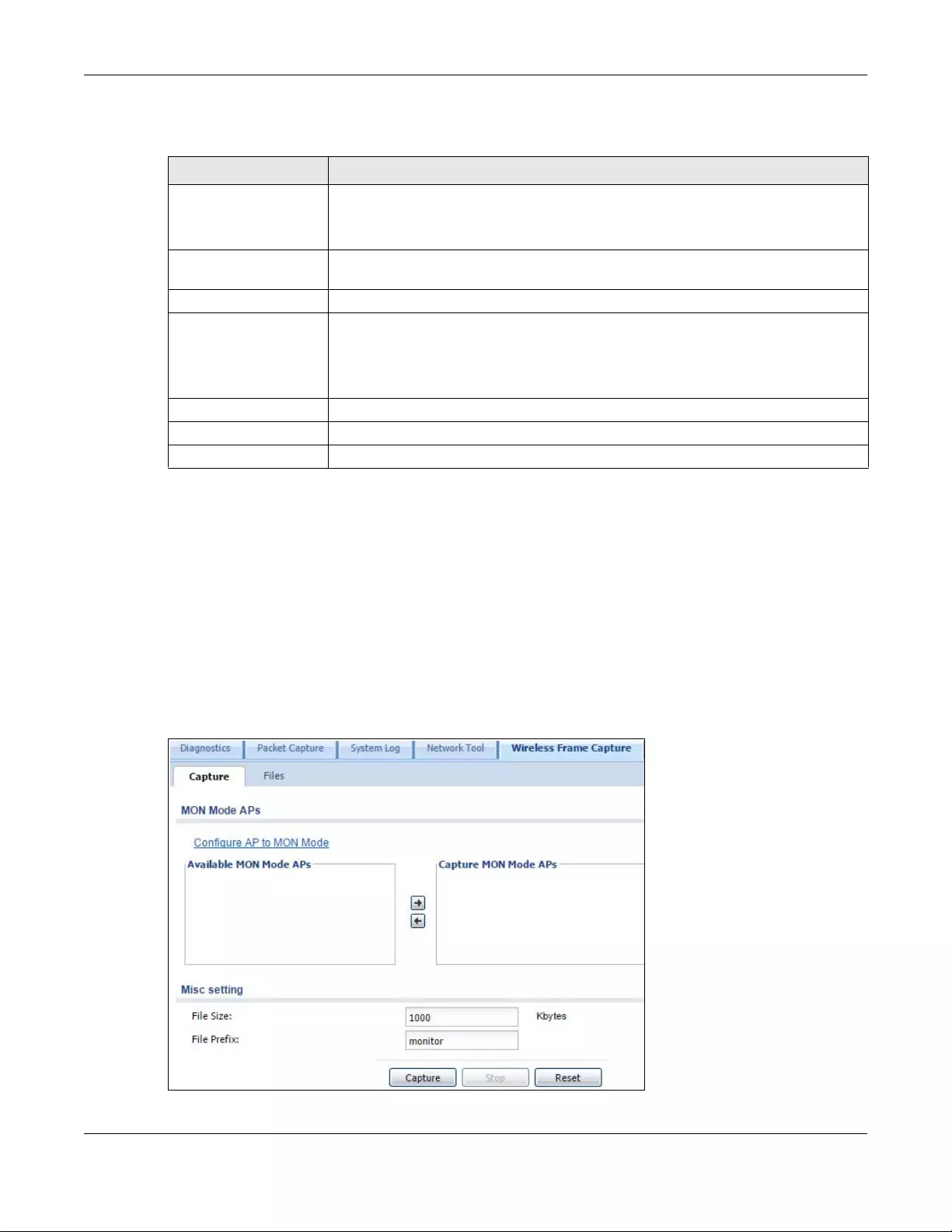
Chapter 47 Diagnostics
USG/ZyWALL User’s Guide
922
The following table describes the labels in this screen.
47.6 The Wireless Frame Capture Screen
Use this screen to capture wireless network traffic going through the AP interfaces connected to your
Zyxel Device. Studying these frame captures may help you identify network problems.
Click Maintenance > Diagnostics > Wireless Frame Capture to display this screen.
Note: New capture files overwrite existing files of the same name. Change the File Prefix
field’s setting to avoid this.
Figure 667 Maintenance > Diagnostics > Wireless Frame Capture > Capture
Table 391 Maintenance > Diagnostics > Network Tool
LABEL DESCRIPTION
Network Tool Select PING IPv4 to ping the IP address that you entered.
Select TRACEROUTE IPv4 to perform the traceroute function. This determines the path a
packet takes to the specified computer.
Domain Name or IP
Address
Type the IPv4 address of a computer that you want to perform ping or traceroute in
order to test a connection.
Interface Select an interface through which the packet is transmitted.
Extension Option Enter the extended option if you want to use an extended ping or traceroute
command. For example, enter “-c count” (where count is the number of ping
requests) to set how many times the Zyxel Device pings the destination IP address, or
enter “-w waittime” (where waittime is a time period in seconds) to set how long the
Zyxel Device waits for a response to a probe before running another traceroute.
Test Click this button to start to ping or run a traceroute.
Stop Click this button to terminate the current ping operation or traceroute.
Reset Click this button to return the screen to its last-saved settings.
Chapter 47 Diagnostics
USG/ZyWALL User’s Guide
923
The following table describes the labels in this screen.
Table 392 Maintenance > Diagnostics > Wireless Frame Capture > Capture
LABEL DESCRIPTION
MON Mode APs
Configure AP to
MON Mode Click this to go the Configuration > Wireless > AP Management screen, where you can
set one or more APs to monitor mode.
Available MON
Mode APs This column displays which APs on your wireless network are currently configured for
monitor mode.
Use the arrow buttons to move APs off this list and onto the Captured MON Mode APs
list.
Capture MON Mode
APs This column displays the monitor-mode configured APs selected to for wireless frame
capture.
Misc Setting
File Size Specify a maximum size limit in kilobytes for the total combined size of all the capture
files on the Zyxel Device, including any existing capture files and any new capture files
you generate.
Note: If you have existing capture files you may need to set this size larger or
delete existing capture files.
The valid range is 1 to 50000. The Zyxel Device stops the capture and generates the
capture file when either the file reaches this size.
File Prefix Specify text to add to the front of the file name in order to help you identify frame
capture files.
You can modify the prefix to also create new frame capture files each time you perform
a frame capture operation. Doing this does no overwrite existing frame capture files.
The file format is: [file prefix].cap. For example, “monitor.cap”.
Capture Click this button to have the Zyxel Device capture frames according to the settings
configured in this screen.
You can configure the Zyxel Device while a frame capture is in progress although you
cannot modify the frame capture settings.
The Zyxel Device’s throughput or performance may be affected while a frame capture
is in progress.
After the Zyxel Device finishes the capture it saves a combined capture file for all APs.
The total number of frame capture files that you can save depends on the file sizes and
the available flash storage space. Once the flash storage space is full, adding more
frame captures will fail.
Stop Click this button to stop a currently running frame capture and generate a combined
capture file for all APs.
Reset Click this button to return the screen to its last-saved settings.
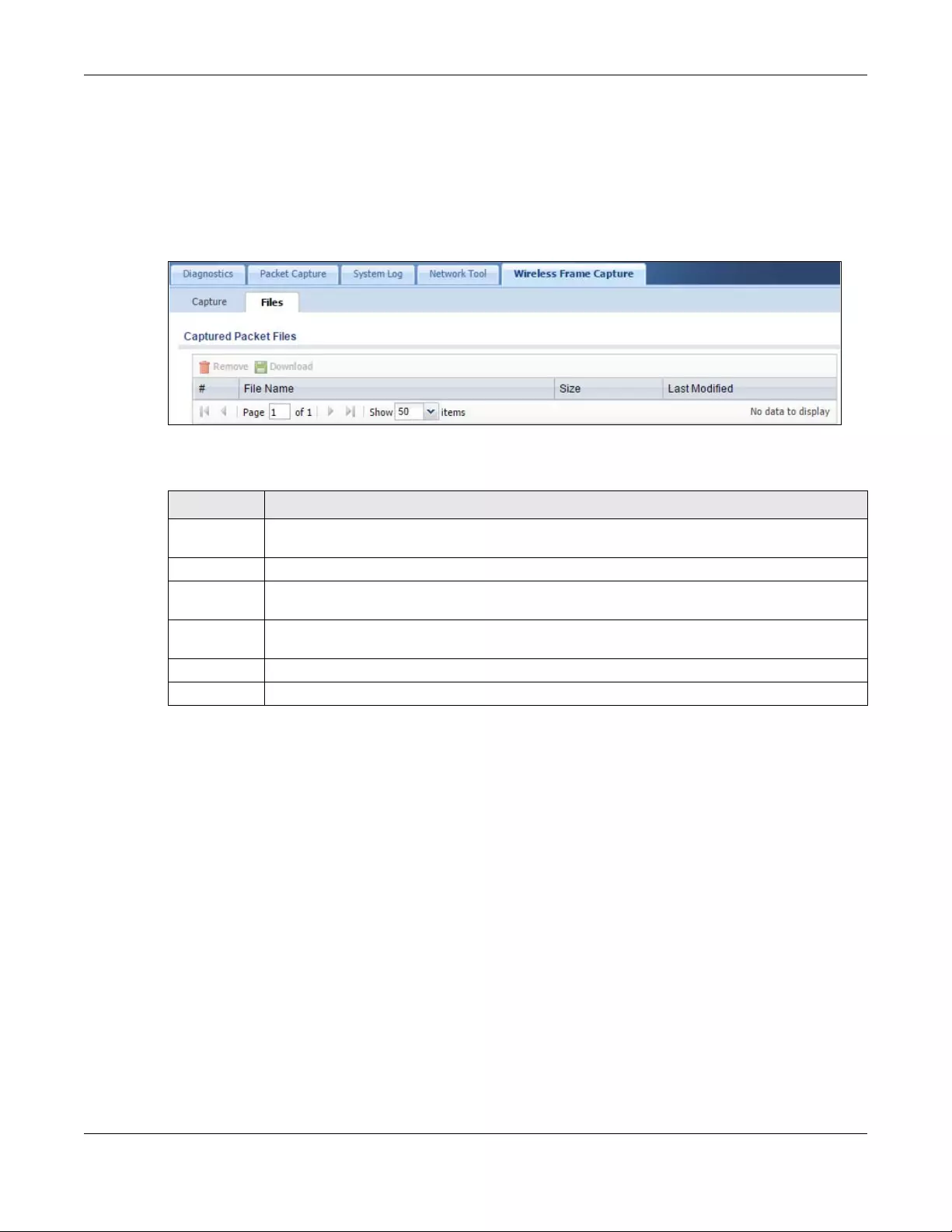
Chapter 47 Diagnostics
USG/ZyWALL User’s Guide
924
47.6.1 The Wireless Frame Capture Files Screen
Click Maintenance > Diagnostics > Wireless Frame Capture > Files to open this screen. This screen lists the
files of wireless frame captures the Zyxel Device has performed. You can download the files to your
computer where you can study them using a packet analyzer (also known as a network or protocol
analyzer) such as Wireshark.
Figure 668 Maintenance > Diagnostics > Wireless Frame Capture > Files
The following table describes the labels in this screen.
Table 393 Maintenance > Diagnostics > Wireless Frame Capture > Files
LABEL DESCRIPTION
Remove Select files and click Remove to delete them from the Zyxel Device. Use the [Shift] and/or [Ctrl] key
to select multiple files. A pop-up window asks you to confirm that you want to delete.
Download Click a file to select it and click Download to save it to your computer.
#This column displays the number for each packet capture file entry. The total number of packet
capture files that you can save depends on the file sizes and the available flash storage space.
File Name This column displays the label that identifies the file. The file name format is interface name-file
suffix.cap.
Size This column displays the size (in bytes) of a configuration file.
Last Modified This column displays the date and time that the individual files were saved.
USG/ZyWALL User’s Guide
925
CHAPTER 48
Packet Flow Explore
48.1 Overview
Use this to get a clear picture on how the Zyxel Device determines where to forward a packet and how
to change the source IP address of the packet according to your current settings. This function provides
you a summary of all your routing and SNAT settings and helps troubleshoot any related problems.
48.1.1 What You Can Do in this Chapter
• Use the Routing Status screen (see Section 48.2 on page 925) to view the overall routing flow and
each routing function’s settings.
• Use the SNAT Status screen (see Section 48.3 on page 930) to view the overall source IP address
conversion (SNAT) flow and each SNAT function’s settings.
48.2 The Routing Status Screen
The Routing Status screen allows you to view the current routing flow and quickly link to specific routing
settings. Click a function box in the Routing Flow section, the related routes (activated) will display in the
Routing Table section. To access this screen, click Maintenance > Packet Flow Explore.
The order of the routing flow may vary depending on whether you:
•Select use policy route to override direct route in the CONFIGURATION > Network > Routing > Policy
Route screen.
• Use policy routes to control 1-1 NAT by using the policy control-virtual-server-rules
activate command.
•Select use policy routes to control dynamic IPSec rules in the CONFIGURATION > VPN > IPSec VPN >
VPN Connection screen.
Note: Once a packet matches the criteria of a routing rule, the Zyxel Device takes the
corresponding action and does not perform any further flow checking.
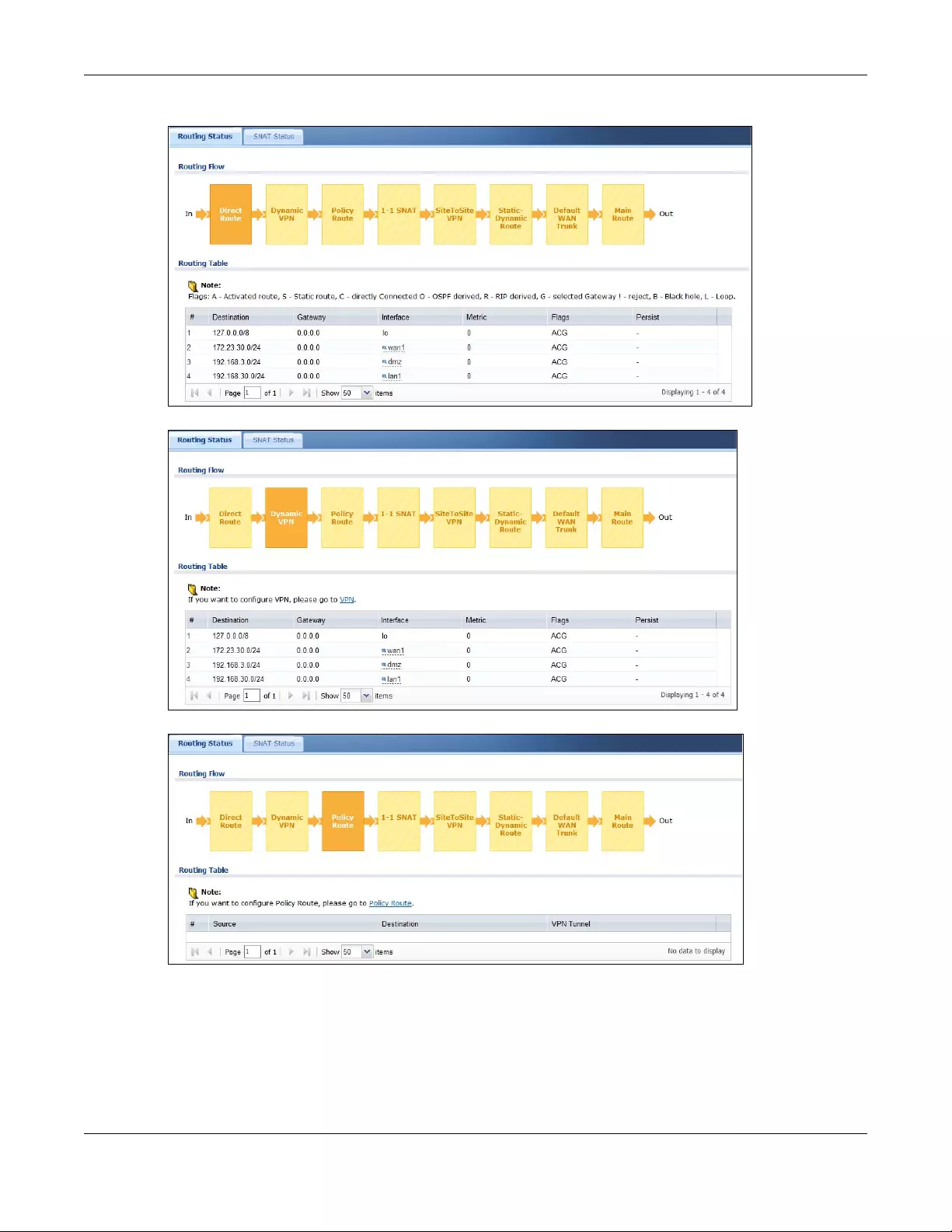
Chapter 48 Packet Flow Explore
USG/ZyWALL User’s Guide
926
Figure 669 Maintenance > Packet Flow Explore > Routing Status (Direct Route)
Figure 670 Maintenance > Packet Flow Explore > Dynamic VPN
Figure 671 Maintenance > Packet Flow Explore > Routing Status (Policy Route)
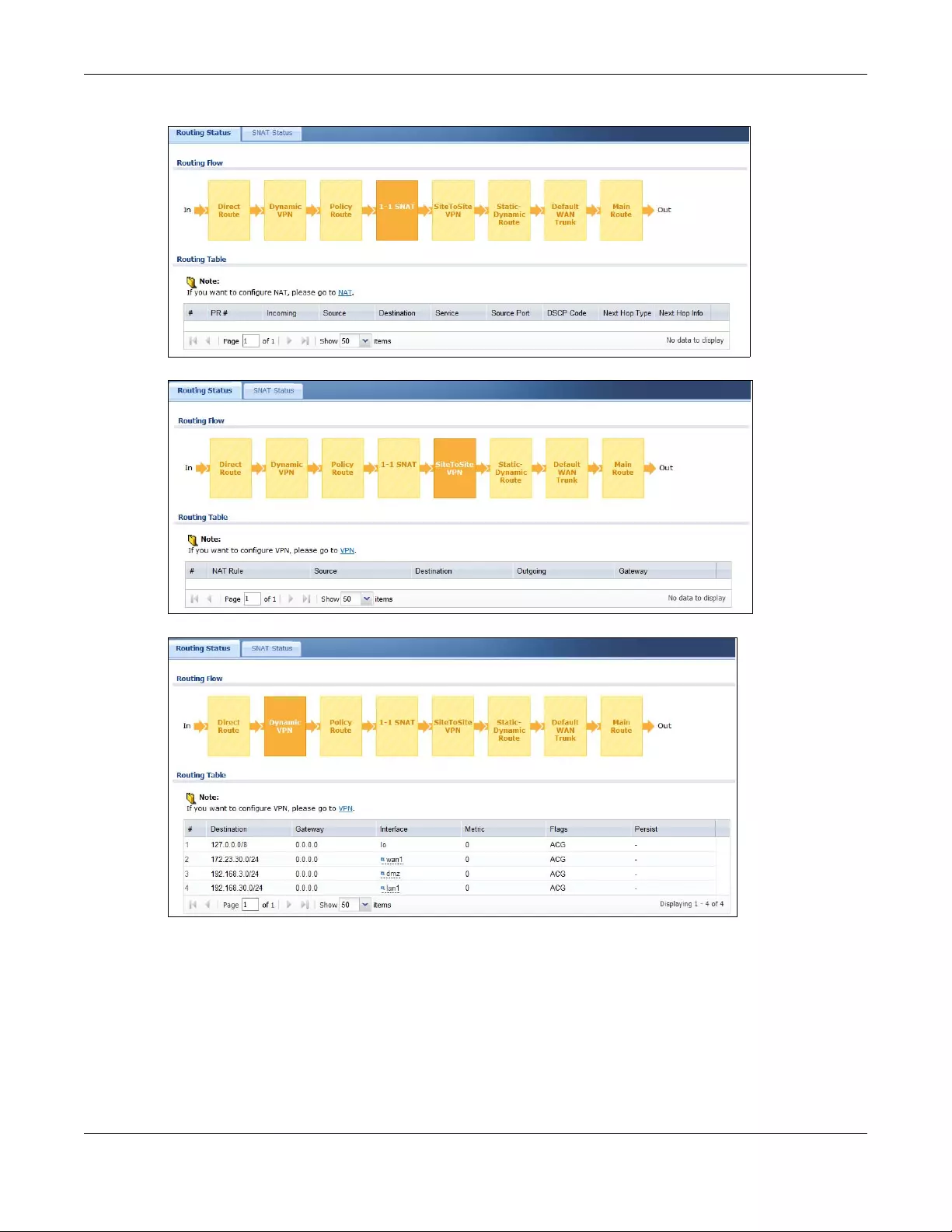
Chapter 48 Packet Flow Explore
USG/ZyWALL User’s Guide
927
Figure 672 Maintenance > Packet Flow Explore > Routing Status (1-1 SNAT)
Figure 673 Maintenance > Packet Flow Explore > Routing Status (SiteToSite VPN)
Figure 674 Maintenance > Packet Flow Explore > Routing Status (Dynamic VPN)
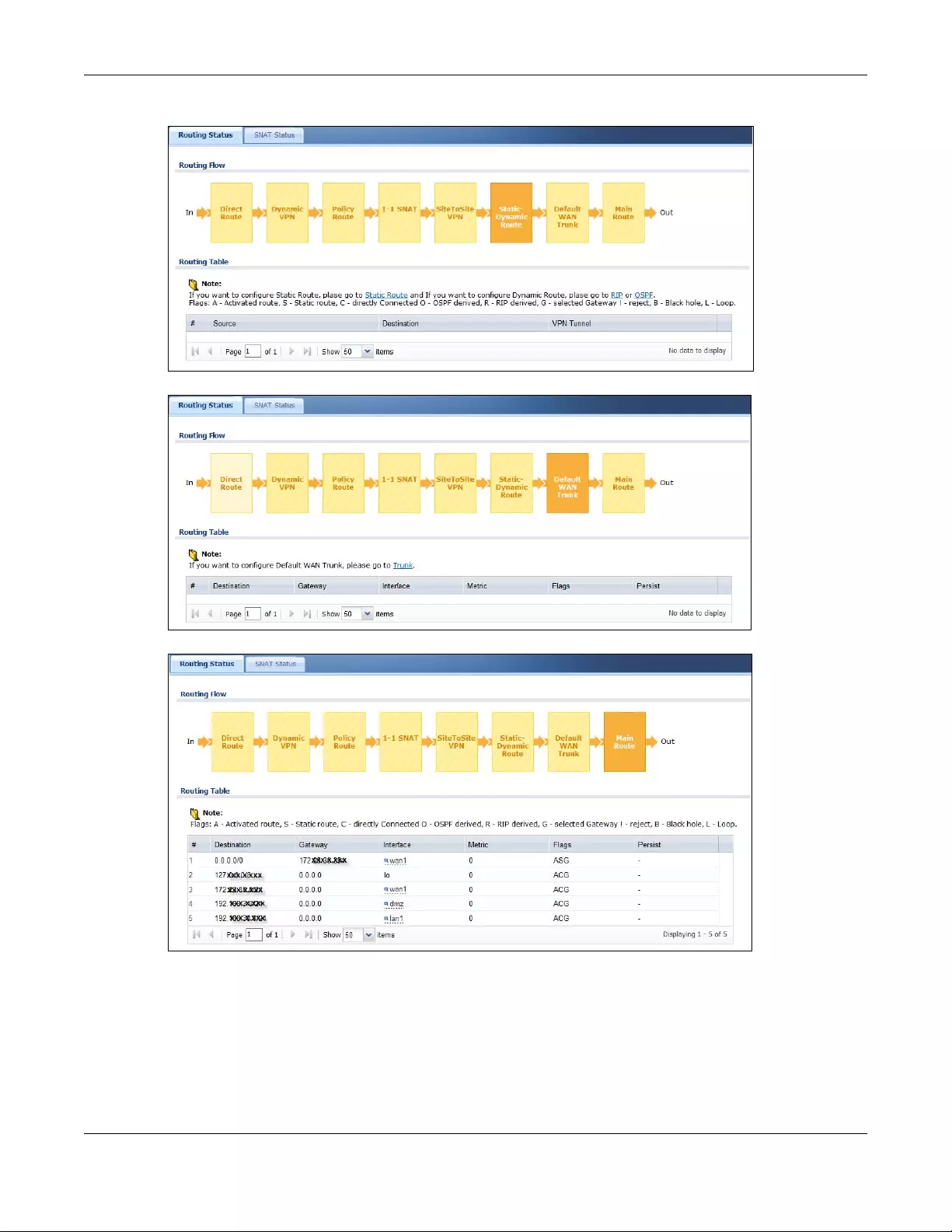
Chapter 48 Packet Flow Explore
USG/ZyWALL User’s Guide
928
Figure 675 Maintenance > Packet Flow Explore > Routing Status (Static-Dynamic Route)
Figure 676 Maintenance > Packet Flow Explore > Routing Status (Default WAN Trunk)
Figure 677 Maintenance > Packet Flow Explore > Routing Status (Main Route)
Chapter 48 Packet Flow Explore
USG/ZyWALL User’s Guide
929
The following table describes the labels in this screen.
Table 394 Maintenance > Packet Flow Explore > Routing Status
LABEL DESCRIPTION
Routing Flow This section shows you the flow of how the Zyxel Device determines where to route a packet.
Click a function box to display the related settings in the Routing Table section.
Routing Table This section shows the corresponding settings according to the function box you click in the
Routing Flow section.
The following fields are available if you click Di rect Route, Static-Dynamic Route, or Main Route in the Routing Flow
section.
#This field is a sequential value, and it is not associated with any entry.
Destination This is the destination IP address of a route.
Gateway This is the IP address of the next-hop gateway or the interface through which the traffic is
routed.
Interface This is the name of an interface associated with the route.
Metric This is the route’s priority among the displayed routes.
Flags This indicates additional information for the route. The possible flags are:
•A - this route is currently activated
•S - this is a static route
•C - this is a direct connected route
•O - this is a dynamic route learned through OSPF
•R - this is a dynamic route learned through RIP
•G - the route is to a gateway (router) in the same network.
•! - this is a route which forces a route lookup to fail.
•B - this is a route which discards packets.
•L - this is a recursive route.
Persist This is the remaining time of a dynamically learned route. The Zyxel Device removes the route
after this time period is counted down to zero.
The following fields are available if you click Policy Route in the Routing Flow section.
#This field is a sequential value, and it is not associated with any entry.
PR # This is the number of an activated policy route. If you have configured a schedule for the route,
this screen only displays the route at the scheduled time.
Incoming This is the interface on which the packets are received.
Source This is the source IP address(es) from which the packets are sent.
Destination This is the destination IP address(es) to which the packets are transmitted.
Service This is the name of the service object. any means all services.
DSCP Code This is the DSCP value of incoming packets to which this policy route applies. See Section 11.2
on page 369 for more information.
Next Hop Type This is the type of the next hop to which packets are directed.
Next Hop Info • This is the main route if the next hop type is Auto.
• This is the interface name and gateway IP address if the next hop type is Interface /GW.
• This is the tunnel name if the next hop type is VPN Tunnel.
• This is the trunk name if the next hop type is Trunk.
The following fields are available if you click 1-1 SNAT in the Routing Flow section.
#This field is a sequential value, and it is not associated with any entry.
NAT Rule This is the name of an activated 1:1 or Many 1:1 NAT rule in the NAT table.
Source This is the original source IP address(es). any means any IP address.
Destination This is the original destination IP address(es). any means any IP address.
Outgoing This is the name of an interface which transmits packets out of the Zyxel Device.
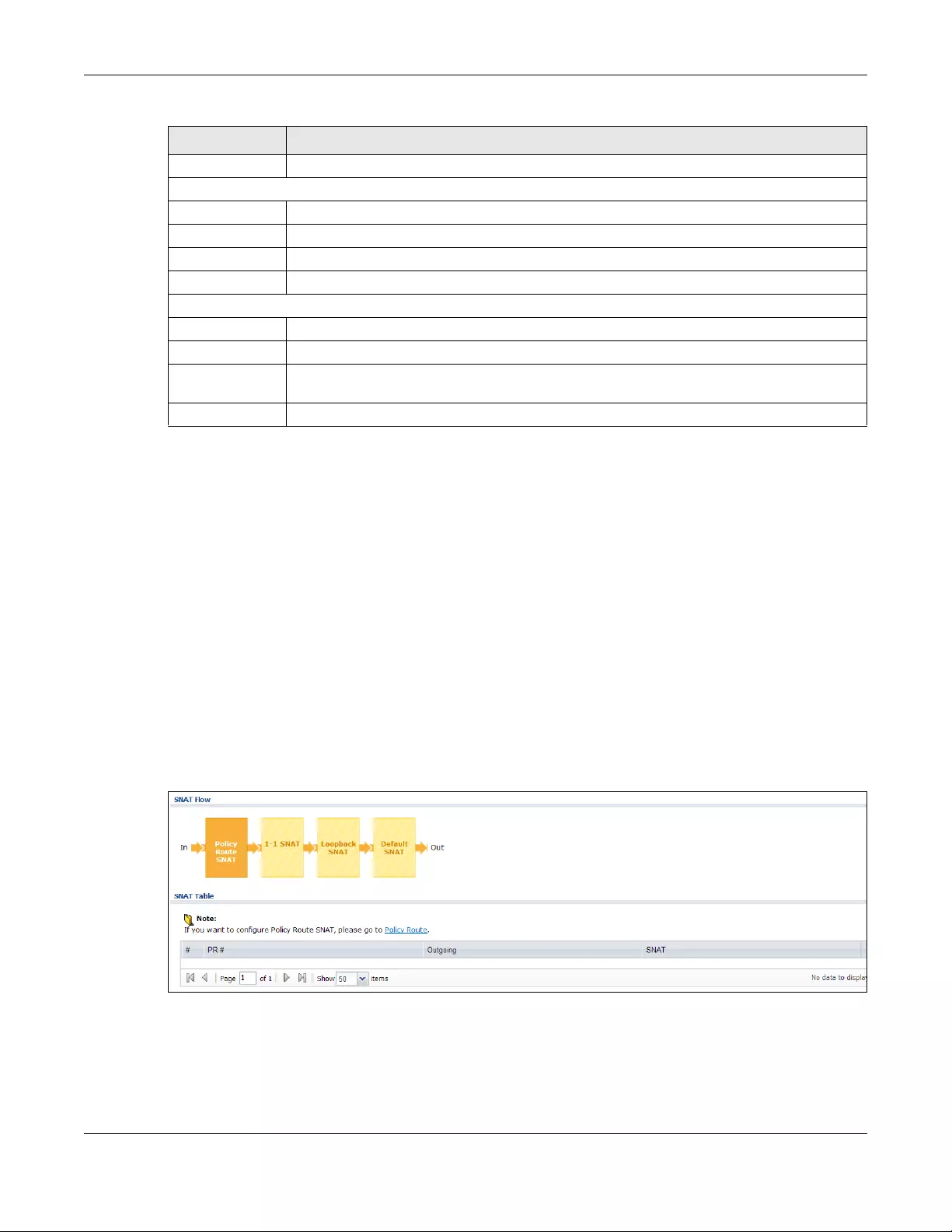
Chapter 48 Packet Flow Explore
USG/ZyWALL User’s Guide
930
48.3 The SNAT Status Screen
The SNAT Status screen allows you to view and quickly link to specific source NAT (SNAT) settings. Click a
function box in the SNAT Flow section, the related SNAT rules (activated) will display in the SNAT Table
section. To access this screen, click Maintenance > Packet Flow Explore > SNAT Status.
The order of the SNAT flow may vary depending on whether you:
•select use default SNAT in the CONFIGURATION > Network > Interface > Trunk screen.
• use policy routes to control 1-1 NAT by using the policy control-virtual-server-rules
activate command.
Note: Once a packet matches the criteria of an SNAT rule, the Zyxel Device takes the
corresponding action and does not perform any further flow checking.
Figure 678 Maintenance > Packet Flow Explore > SNAT Status (Policy Route SNAT)
Gateway This is the IP address of the gateway in the same network of the outgoing interface.
The following fields are available if you click Dynamic VPN or SiteToSite VPN in the Routing Flow section.
#This field is a sequential value, and it is not associated with any entry.
Source This is the IP address(es) of the local VPN network.
Destination This is the IP address(es) for the remote VPN network.
VPN Tunnel This is the name of the VPN tunnel.
The following fields are available if you click Default WAN Trun k in the Routing Flow section.
#This field is a sequential value, and it is not associated with any entry.
Source This is the source IP address(es) from which the packets are sent. any means any IP address.
Destination This is the destination IP address(es) to which the packets are transmitted. any means any IP
address.
Trunk This is the name of the WAN trunk through which the matched packets are transmitted.
Table 394 Maintenance > Packet Flow Explore > Routing Status (continued)
LABEL DESCRIPTION
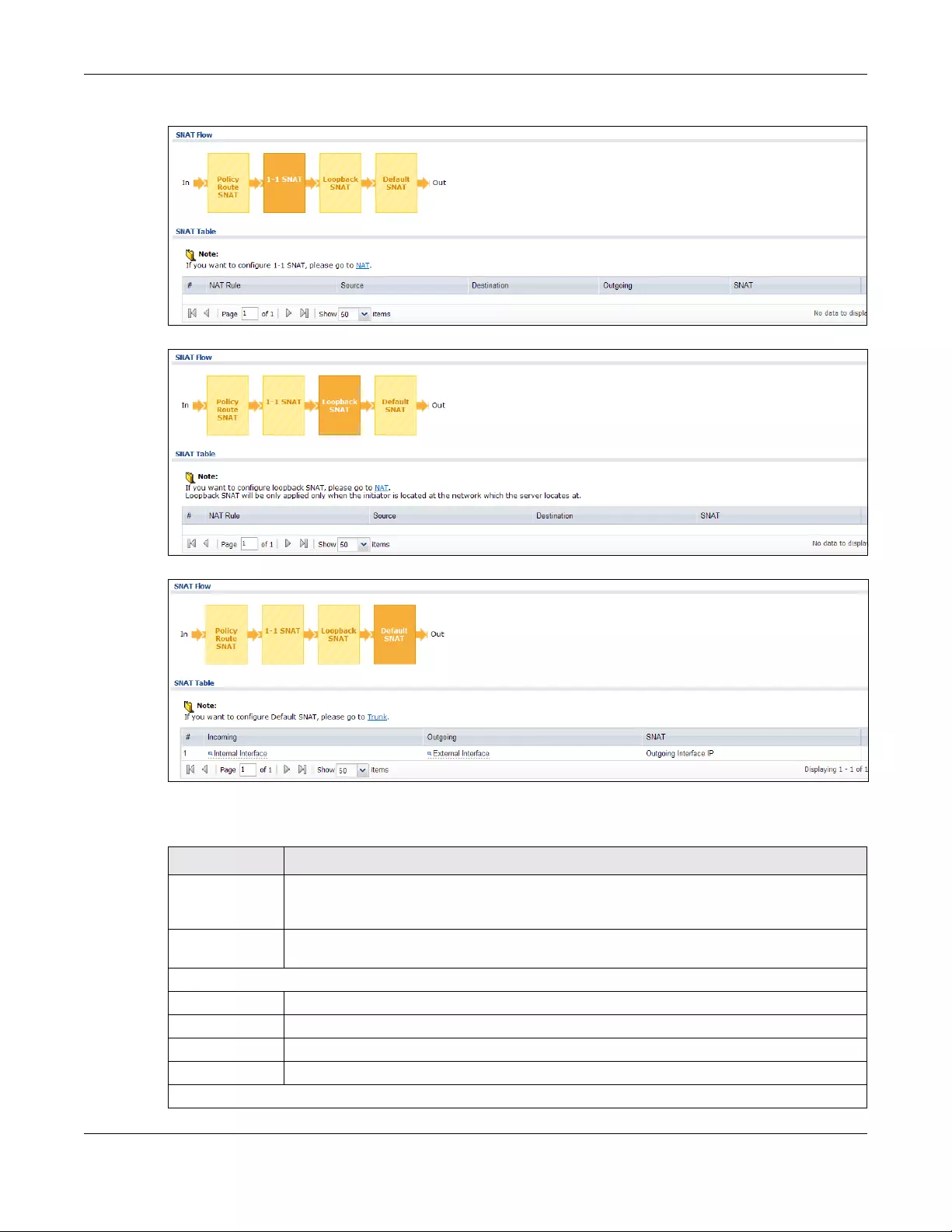
Chapter 48 Packet Flow Explore
USG/ZyWALL User’s Guide
931
Figure 679 Maintenance > Packet Flow Explore > SNAT Status (1-1 SNAT)
Figure 680 Maintenance > Packet Flow Explore > SNAT Status (Loopback SNAT)
Figure 681 Maintenance > Packet Flow Explore > SNAT Status (Default SNAT)
The following table describes the labels in this screen.
Table 395 Maintenance > Packet Flow Explore > SNAT Status
LABEL DESCRIPTION
SNAT Flow This section shows you the flow of how the Zyxel Device changes the source IP address for a
packet according to the rules you have configured in the Zyxel Device. Click a function box to
display the related settings in the SNAT Table section.
SNAT Table The table fields in this section vary depending on the function box you select in the SNAT Flo w
section.
The following fields are available if you click Policy Route SNAT in the SNAT Flow section.
#This field is a sequential value, and it is not associated with any entry.
PR # This is the number of an activated policy route which uses SNAT.
Outgoing This is the outgoing interface that the route uses to transmit packets.
SNAT This is the source IP address(es) that the SNAT rule uses finally.
The following fields are available if you click 1-1 SNAT in the SNAT Flo w section.
Chapter 48 Packet Flow Explore
USG/ZyWALL User’s Guide
932
#This field is a sequential value, and it is not associated with any entry.
NAT Rule This is the name of an activated NAT rule which uses SNAT.
Source This is the original source IP address(es).
Destination This is the original destination IP address(es).
Outgoing This is the outgoing interface that the SNAT rule uses to transmit packets.
SNAT This is the source IP address(es) that the SNAT rule uses finally.
The following fields are available if you click Loopback SNAT in the SNAT Flow section.
#This field is a sequential value, and it is not associated with any entry.
NAT Rule This is the name of an activated NAT rule which uses SNAT and enables NAT loopback.
Source This is the original source IP address(es). any means any IP address.
Destination This is the original destination IP address(es). any means any IP address.
SNAT This indicates which source IP address the SNAT rule uses finally. For example, Outgoing
Interface IP means that the Zyxel Device uses the IP address of the outgoing interface as the
source IP address for the matched packets it sends out through this rule.
The following fields are available if you click Default SNAT in the SNAT Flow section.
#This field is a sequential value, and it is not associated with any entry.
Incoming This indicates internal interface(s) on which the packets are received.
Outgoing This indicates external interface(s) from which the packets are transmitted.
SNAT This indicates which source IP address the SNAT rule uses finally. For example, Outgoing
Interface IP means that the Zyxel Device uses the IP address of the outgoing interface as the
source IP address for the matched packets it sends out through this rule.
Table 395 Maintenance > Packet Flow Explore > SNAT Status (continued)
LABEL DESCRIPTION
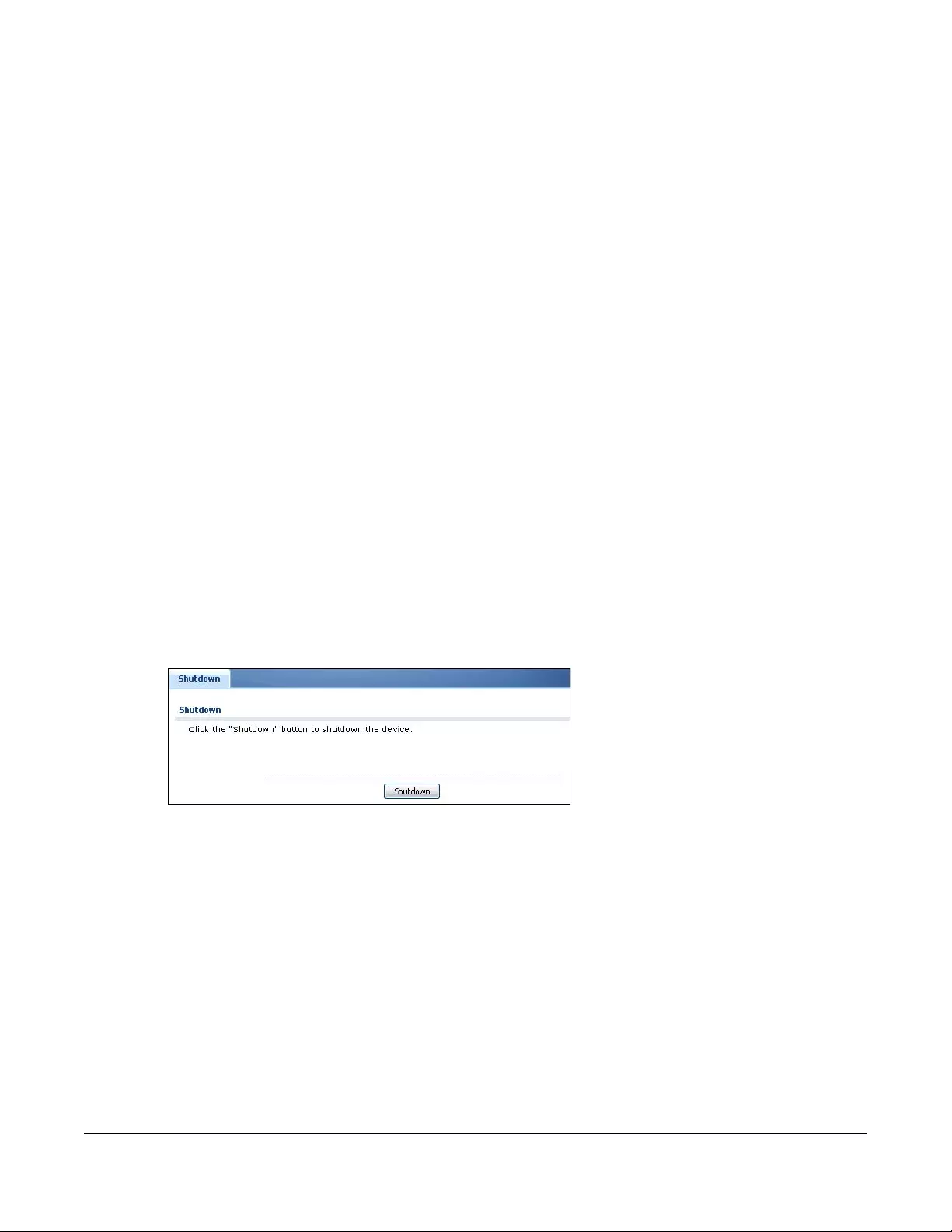
USG/ZyWALL User’s Guide
933
CHAPTER 49
Shutdown
49.1 Overview
Use this to shutdown the device in preparation for disconnecting the power.
Always use the Maintenance > Shutdown > Shutdown screen or the
“shutdown” command before you turn off the Zyxel Device or remove
the power. Not doing so can cause the firmware to become corrupt.
49.1.1 What You Need To Know
Shutdown writes all cached data to the local storage and stops the system processes.
49.2 The Shutdown Screen
To access this screen, click Maintenance > Shutdown.
Figure 682 Maintenance > Shutdown
Click the Shutdown button to shut down the Zyxel Device. Wait for the device to shut down before you
manually turn off or remove the power. It does not turn off the power.
You can also use the CLI command shutdown to shutdown the Zyxel Device.
USG/ZyWALL User’s Guide
934
CHAPTER 50
Troubleshooting
This chapter offers some suggestions to solve problems you might encounter.
• You can also refer to the logs (see Chapter 7 on page 234).
• For the order in which the Zyxel Device applies its features and checks, see Chapter 48 on page 925.
None of the LEDs turn on.
Make sure that you have the power cord connected to the Zyxel Device and plugged in to an
appropriate power source. Make sure you have the Zyxel Device turned on. Check all cable
connections.
If the LEDs still do not turn on, you may have a hardware problem. In this case, you should contact your
local vendor.
Cannot access the Zyxel Device from the LAN.
• Check the cable connection between the Zyxel Device and your computer or switch.
• Ping the Zyxel Device from a LAN computer. Make sure your computer’s Ethernet card is installed and
functioning properly. Also make sure that its IP address is in the same subnet as the Zyxel Device’s.
• In the computer, click Start, (All) Programs, Accessories and then Command Prompt. In the
Command Prompt window, type “ping” followed by the Zyxel Device’s LAN IP address (192.168.1.1 is
the default) and then press [ENTER]. The Zyxel Device should reply.
• If you’ve forgotten the Zyxel Device’s password, use the RESET button. Press the button in for about 5
seconds (or until the SYS LED starts to blink), then release it. It returns the Zyxel Device to the factory
defaults (password is 1234, LAN IP address 192.168.1.1 etc.
• If you’ve forgotten the Zyxel Device’s IP address, you can use the commands through the console
port to check it. Connect your computer to the CONSOLE port using a console cable. Your computer
should have a terminal emulation communications program (such as HyperTerminal) set to VT100
terminal emulation, no parity, 8 data bits, 1 stop bit, no flow control and 115200 bps port speed.
I cannot access the Internet.
• Check the Zyxel Device’s connection to the Ethernet jack with Internet access. Make sure the Internet
gateway device (such as a DSL modem) is working properly.
• Check the WAN interface's status in the Dashboard. Use the installation setup wizard again and make
sure that you enter the correct settings. Use the same case as provided by your ISP.
Chapter 50 Troubleshooting
USG/ZyWALL User’s Guide
935
I cannot update the anti-virus signatures.
• Make sure your Zyxel Device has the anti-virus service registered and that the license is not expired.
Purchase a new license if the license is expired.
• Make sure your Zyxel Device is connected to the Internet.
I cannot update the IDP/application patrol signatures.
• Make sure your Zyxel Device has the IDP/application patrol service registered and that the license is
not expired. Purchase a new license if the license is expired.
• Make sure your Zyxel Device is connected to the Internet.
I downloaded updated anti-virus or IDP/application patrol signatures. Why has the Zyxel Device
not re-booted yet?
The Zyxel Device does not have to reboot when you upload new signatures.
The content filter category service is not working.
• Make sure your Zyxel Device has the content filter category service registered and that the license is
not expired. Purchase a new license if the license is expired.
• Make sure your Zyxel Device is connected to the Internet.
I configured security settings but the Zyxel Device is not applying them for certain interfaces.
Many security settings are usually applied to zones. Make sure you assign the interfaces to the
appropriate zones. When you create an interface, there is no security applied on it until you assign it to
a zone.
The Zyxel Device is not applying the custom policy route I configured.
The Zyxel Device checks the policy routes in the order that they are listed. So make sure that your
custom policy route comes before any other routes that the traffic would also match.
Chapter 50 Troubleshooting
USG/ZyWALL User’s Guide
936
The Zyxel Device is not applying the custom security policy I configured.
The Zyxel Device checks the security policies in the order that they are listed. So make sure that your
custom security policy comes before any other rules that the traffic would also match.
I cannot enter the interface name I want.
The format of interface names other than the Ethernet interface names is very strict. Each name consists
of 2-4 letters (interface type), followed by a number (x, limited by the maximum number of each type of
interface). For example, VLAN interfaces are vlan0, vlan1, vlan2,...; and so on.
• The names of virtual interfaces are derived from the interfaces on which they are created. For
example, virtual interfaces created on Ethernet interface wan1 are called wan1:1, wan1:2, and so
on. Virtual interfaces created on VLAN interface vlan2 are called vlan2:1, vlan2:2, and so on. You
cannot specify the number after the colon(:) in the Web Configurator; it is a sequential number. You
can specify the number after the colon if you use the CLI to set up a virtual interface.
I cannot set up a PPP interface, virtual Ethernet interface or virtual VLAN interface on an Ethernet
interface.
You cannot set up a PPP interface, virtual Ethernet interface or virtual VLAN interface if the underlying
interface is a member of a bridge. You also cannot add an Ethernet interface or VLAN interface to a
bridge if the member interface has a virtual interface or PPP interface on top of it.
My rules and settings that apply to a particular interface no longer work.
The interface’s IP address may have changed. To avoid this create an IP address object based on the
interface. This way the Zyxel Device automatically updates every rule or setting that uses the object
whenever the interface’s IP address settings change. For example, if you change LAN1’s IP address, the
Zyxel Device automatically updates the corresponding interface-based, LAN1 subnet address object.
I cannot set up a PPP interface.
You have to set up an ISP account before you create a PPPoE or PPTP interface.
The data rates through my cellular connection are no-where near the rates I expected.
Chapter 50 Troubleshooting
USG/ZyWALL User’s Guide
937
The actual cellular data rate you obtain varies depending on the cellular device you use, the signal
strength to the service provider’s base station, and so on.
I created a cellular interface but cannot connect through it.
• Make sure you have a compatible mobile broadband device installed or connected. See
www.zyxel.com for details.
• Make sure you have the cellular interface enabled.
• Make sure the cellular interface has the correct user name, password, and PIN code configured with
the correct casing.
• If the Zyxel Device has multiple WAN interfaces, make sure their IP addresses are on different subnets.
Hackers have accessed my WEP-encrypted wireless LAN.
WEP is extremely insecure. Its encryption can be broken by an attacker, using widely-available software.
It is strongly recommended that you use a more effective security mechanism. Use the strongest security
mechanism that all the wireless devices in your network support. WPA2 or WPA2-PSK is recommended.
The wireless security is not following the re-authentication timer setting I specified.
If a RADIUS server authenticates wireless stations, the re-authentication timer on the RADIUS server has
priority. Change the RADIUS server’s configuration if you need to use a different re-authentication timer
setting.
I cannot configure a particular VLAN interface on top of an Ethernet interface even though I
have it configured it on top of another Ethernet interface.
Each VLAN interface is created on top of only one Ethernet interface.
The Zyxel Device is not applying an interface’s configured ingress bandwidth limit.
At the time of writing, the Zyxel Device does not support ingress bandwidth management.
The Zyxel Device is not applying my application patrol bandwidth management settings.
Chapter 50 Troubleshooting
USG/ZyWALL User’s Guide
938
Bandwidth management in policy routes has priority over application patrol bandwidth management.
The Zyxel Device’s performance slowed down after I configured many new application patrol
entries.
The Zyxel Device checks the ports and conditions configured in application patrol entries in the order
they appear in the list. While this sequence does not affect the functionality, you might improve the
performance of the Zyxel Device by putting more commonly used ports at the top of the list.
The Zyxel Device’s anti-virus scanner cleaned an infected file but now I cannot use the file.
The scanning engine checks the contents of the packets for virus. If a virus pattern is matched, the Zyxel
Device removes the infected portion of the file along with the rest of the file. The uninfected portion of
the file before a virus pattern was matched still goes through. Since the Zyxel Device erases the infected
portion of the file before sending it, you may not be able to open the file.
The Zyxel Device is not scanning some zipped files.
The Zyxel Device cannot unzip password protected ZIP files or a ZIP file within another ZIP file. There are also limits to
the number of ZIP files that the Zyxel Device can concurrently unzip.
The Zyxel Device is deleting some zipped files.
The anti-virus policy may be set to delete zipped files that the Zyxel Device cannot unzip. The Zyxel
Device cannot unzip password protected ZIP files or a ZIP file within another ZIP file. There are also limits
to the number of ZIP files that the Zyxel Device can concurrently unzip.
The Zyxel Device’s performance seems slower after configuring IDP.
Depending on your network topology and traffic load, binding every packet direction to an IDP profile
may affect the Zyxel Device’s performance. You may want to focus IDP scanning on certain traffic
directions such as incoming traffic.
IDP is dropping traffic that matches a rule that says no action should be taken.
The Zyxel Device checks all signatures and continues searching even after a match is found. If two or
more rules have conflicting actions for the same packet, then the Zyxel Device applies the more
Chapter 50 Troubleshooting
USG/ZyWALL User’s Guide
939
restrictive action (reject-both, reject-receiver or reject-sender, drop, none in this order). If a packet
matches a rule for reject-receiver and it also matches a rule for reject-sender, then the Zyxel Device will
reject-both.
I uploaded a custom signature file and now all of my earlier custom signatures are gone.
The name of the complete custom signature file on the Zyxel Device is ‘custom.rules’. If you import a file
named ‘custom.rules’, then all custom signatures on the Zyxel Device are overwritten with the new file. If
this is not your intention, make sure that the files you import are not named ‘custom.rules’.
I cannot configure some items in IDP that I can configure in Snort.
Not all Snort functionality is supported in the Zyxel Device.
The Zyxel Device’s performance seems slower after configuring ADP.
Depending on your network topology and traffic load, applying an anomaly profile to each and every
packet direction may affect the Zyxel Device’s performance.
The Zyxel Device routes and applies SNAT for traffic from some interfaces but not from others.
The Zyxel Device automatically uses SNAT for traffic it routes from internal interfaces to external
interfaces. For example LAN to WAN traffic. You must manually configure a policy route to add routing
and SNAT settings for an interface with the Interface Type set to General. You can also configure a
policy route to override the default routing and SNAT behavior for an interface with the Interface Type
set to Internal or External.
I cannot get Dynamic DNS to work.
• You must have a public WAN IP address to use Dynamic DNS.
• Make sure you recorded your DDNS account’s user name, password, and domain name and have
entered them properly in the Zyxel Device.
• You may need to configure the DDNS entry’s IP Address setting to Auto if the interface has a dynamic
IP address or there are one or more NAT routers between the Zyxel Device and the DDNS server.
• The Zyxel Device may not determine the proper IP address if there is an HTTP proxy server between the
Zyxel Device and the DDNS server.
Chapter 50 Troubleshooting
USG/ZyWALL User’s Guide
940
I cannot create a second HTTP redirect rule for an incoming interface.
You can configure up to one HTTP redirect rule for each (incoming) interface.
I cannot get the application patrol to manage SIP traffic.
Make sure you have the SIP ALG enabled.
I cannot get the application patrol to manage H.323 traffic.
Make sure you have the H.323 ALG enabled.
I cannot get the application patrol to manage FTP traffic.
Make sure you have the FTP ALG enabled.
The Zyxel Device keeps resetting the connection.
If an alternate gateway on the LAN has an IP address in the same subnet as the Zyxel Device’s LAN IP
address, return traffic may not go through the Zyxel Device. This is called an asymmetrical or “triangle”
route. This causes the Zyxel Device to reset the connection, as the connection has not been
acknowledged.
You can set the Zyxel Device’s security policy to permit the use of asymmetrical route topology on the
network (so it does not reset the connection) although this is not recommended since allowing
asymmetrical routes may let traffic from the WAN go directly to the LAN without passing through the
Zyxel Device. A better solution is to use virtual interfaces to put the Zyxel Device and the backup
gateway on separate subnets. See Asymmetrical Routes on page 519 and the chapter about interfaces
for more information.
I cannot set up an IPSec VPN tunnel to another device.
If the IPSec tunnel does not build properly, the problem is likely a configuration error at one of the IPSec
routers. Log into both Zyxel IPSec routers and check the settings in each field methodically and slowly.

Chapter 50 Troubleshooting
USG/ZyWALL User’s Guide
941
Make sure both the Zyxel Device and remote IPSec router have the same security settings for the VPN
tunnel. It may help to display the settings for both routers side-by-side.
Here are some general suggestions. See also Chapter 30 on page 545.
• The system log can often help to identify a configuration problem.
• If you enable NAT traversal, the remote IPSec device must also have NAT traversal enabled.
• The Zyxel Device and remote IPSec router must use the same authentication method to establish the
IKE SA.
• Both routers must use the same negotiation mode.
• Both routers must use the same encryption algorithm, authentication algorithm, and DH key group.
• When using pre-shared keys, the Zyxel Device and the remote IPSec router must use the same pre-
shared key.
• The Zyxel Device’s local and peer ID type and content must match the remote IPSec router’s peer
and local ID type and content, respectively.
• The Zyxel Device and remote IPSec router must use the same active protocol.
• The Zyxel Device and remote IPSec router must use the same encapsulation.
• The Zyxel Device and remote IPSec router must use the same SPI.
• If the sites are/were previously connected using a leased line or ISDN router, physically disconnect
these devices from the network before testing your new VPN connection. The old route may have
been learned by RIP and would take priority over the new VPN connection.
• To test whether or not a tunnel is working, ping from a computer at one site to a computer at the
other.
Before doing so, ensure that both computers have Internet access (via the IPSec routers).
• It is also helpful to have a way to look at the packets that are being sent and received by the Zyxel
Device and remote IPSec router (for example, by using a packet sniffer).
Check the configuration for the following Zyxel Device features.
• The Zyxel Device does not put IPSec SAs in the routing table. You must create a policy route for each
VPN tunnel. See Chapter 11 on page 367.
• Make sure the To-Zyxel Device security policies allow IPSec VPN traffic to the Zyxel Device. IKE uses
UDP port 500, AH uses IP protocol 51, and ESP uses IP protocol 50.
• The Zyxel Device supports UDP port 500 and UDP port 4500 for NAT traversal. If you enable this, make
sure the To-Zyxel Device security policies allow UDP port 4500 too.
• Make sure regular security policies allow traffic between the VPN tunnel and the rest of the network.
Regular security policies check packets the Zyxel Device sends before the Zyxel Device encrypts
them and check packets the Zyxel Device receives after the Zyxel Device decrypts them. This
depends on the zone to which you assign the VPN tunnel and the zone from which and to which
traffic may be routed.
• If you set up a VPN tunnel across the Internet, make sure your ISP supports AH or ESP (whichever you
are using).
• If you have the Zyxel Device and remote IPSec router use certificates to authenticate each other, You
must set up the certificates for the Zyxel Device and remote IPSec router first and make sure they trust
each other’s certificates. If the Zyxel Device’s certificate is self-signed, import it into the remote IPSec
router. If it is signed by a CA, make sure the remote IPSec router trusts that CA. The Zyxel Device uses
one of its Trusted Certificates to authenticate the remote IPSec router’s certificate. The trusted
certificate can be the remote IPSec router’s self-signed certificate or that of a trusted CA that signed
the remote IPSec router’s certificate.
• Multiple SAs connecting through a secure gateway must have the same negotiation mode.
Chapter 50 Troubleshooting
USG/ZyWALL User’s Guide
942
The VPN connection is up but VPN traffic cannot be transmitted through the VPN tunnel.
If you have the Configuration > VPN > IPSec VPN > VPN Connection screen’s Use Policy Route to control
dynamic IPSec rules option enabled, check the routing policies to see if they are sending traffic
elsewhere instead of through the VPN tunnels.
I uploaded a logo to show in the SSL VPN user screens but it does not display properly.
The logo graphic must be GIF, JPG, or PNG format. The graphic should use a resolution of 103 x 29 pixels
to avoid distortion when displayed. The Zyxel Device automatically resizes a graphic of a different
resolution to 103 x 29 pixels. The file size must be 100 kilobytes or less. Transparent background is
recommended.
I logged into the SSL VPN but cannot see some of the resource links.
Available resource links vary depending on the SSL application object’s configuration.
I cannot download the Zyxel Device’s firmware package.
The Zyxel Device’s firmware package cannot go through the Zyxel Device when you enable the anti-
virus Destroy compressed files that could not be decompressed option. The Zyxel Device classifies the
firmware package as not being able to be decompressed and deletes it.
You can upload the firmware package to the Zyxel Device with the option enabled, so you only need
to clear the Destroy compressed files that could not be decompressed option while you download the
firmware package. See Section 39.2.1 on page 683 for more on the anti-virus Destroy compressed files
that could not be decompressed option.
I changed the LAN IP address and can no longer access the Internet.
The Zyxel Device automatically updates address objects based on an interface’s IP address, subnet, or
gateway if the interface’s IP address settings change. However, you need to manually edit any address
objects for your LAN that are not based on the interface.
Chapter 50 Troubleshooting
USG/ZyWALL User’s Guide
943
I configured application patrol to allow and manage access to a specific service but access is
blocked.
• If you want to use a service, make sure the security policy allows UTM application patrol to go through
the Zyxel Device.
I configured policy routes to manage the bandwidth of TCP and UDP traffic but the bandwidth
management is not being applied properly.
It is recommended to use application patrol instead of policy routes to manage the bandwidth of TCP
and UDP traffic.
I cannot get the RADIUS server to authenticate the Zyxel Device‘s default admin account.
The default admin account is always authenticated locally, regardless of the authentication method
setting.
The Zyxel Device fails to authentication the ext-user user accounts I configured.
An external server such as AD, LDAP or RADIUS must authenticate the ext-user accounts. If the Zyxel
Device tries to use the local database to authenticate an ext-user, the authentication attempt will
always fail. (This is related to AAA servers and authentication methods, which are discussed in other
chapters in this guide.)
I cannot add the admin users to a user group with access users.
You cannot put access users and admin users in the same user group.
I cannot add the default admin account to a user group.
You cannot put the default admin account into any user group.
The schedule I configured is not being applied at the configured times.
Chapter 50 Troubleshooting
USG/ZyWALL User’s Guide
944
Make sure the Zyxel Device’s current date and time are correct.
I cannot get a certificate to import into the Zyxel Device.
1For My Certificates, you can import a certificate that matches a corresponding certification request that
was generated by the Zyxel Device. You can also import a certificate in PKCS#12 format, including the
certificate’s public and private keys.
2You must remove any spaces from the certificate’s filename before you can import the certificate.
3Any certificate that you want to import has to be in one of these file formats:
• Binary X.509: This is an ITU-T recommendation that defines the formats for X.509 certificates.
• PEM (Base-64) encoded X.509: This Privacy Enhanced Mail format uses lowercase letters, uppercase
letters and numerals to convert a binary X.509 certificate into a printable form.
• Binary PKCS#7: This is a standard that defines the general syntax for data (including digital signatures)
that may be encrypted. A PKCS #7 file is used to transfer a public key certificate. The private key is not
included. The Zyxel Device currently allows the importation of a PKS#7 file that contains a single
certificate.
• PEM (Base-64) encoded PKCS#7: This Privacy Enhanced Mail (PEM) format uses lowercase letters,
uppercase letters and numerals to convert a binary PKCS#7 certificate into a printable form.
• Binary PKCS#12: This is a format for transferring public key and private key certificates.The private key
in a PKCS #12 file is within a password-encrypted envelope. The file’s password is not connected to
your certificate’s public or private passwords. Exporting a PKCS #12 file creates this and you must
provide it to decrypt the contents when you import the file into the Zyxel Device.
Note: Be careful not to convert a binary file to text during the transfer process. It is easy for this
to occur since many programs use text files by default.
I cannot access the Zyxel Device from a computer connected to the Internet.
Check the service control rules and to-Zyxel Device security policies.
I uploaded a logo to display on the upper left corner of the Web Configurator login screen and
access page but it does not display properly.
Make sure the logo file is a GIF, JPG, or PNG of 100 kilobytes or less.
I uploaded a logo to use as the screen or window background but it does not display properly.
Make sure the logo file is a GIF, JPG, or PNG of 100 kilobytes or less.
Chapter 50 Troubleshooting
USG/ZyWALL User’s Guide
945
The Zyxel Device’s traffic throughput rate decreased after I started collecting traffic statistics.
Data collection may decrease the Zyxel Device’s traffic throughput rate.
I can only see newer logs. Older logs are missing.
When a log reaches the maximum number of log messages, new log messages automatically overwrite
existing log messages, starting with the oldest existing log message first.
The commands in my configuration file or shell script are not working properly.
• In a configuration file or shell script, use “#” or “!” as the first character of a command line to have the
Zyxel Device treat the line as a comment.
• Your configuration files or shell scripts can use “exit” or a command line consisting of a single “!” to
have the Zyxel Device exit sub command mode.
•Include write commands in your scripts. Otherwise the changes will be lost when the Zyxel Device
restarts. You could use multiple write commands in a long script.
Note: “exit” or “!'” must follow sub commands if it is to make the Zyxel Device exit sub
command mode.
See Chapter 46 on page 902 for more on configuration files and shell scripts.
I cannot get the firmware uploaded using the commands.
The Web Configurator is the recommended method for uploading firmware. You only need to use the
command line interface if you need to recover the firmware. See the CLI Reference Guide for how to
determine if you need to recover the firmware and how to recover it.
My packet capture captured less than I wanted or failed.
The packet capture screen’s File Size sets a maximum size limit for the total combined size of all the
capture files on the Zyxel Device, including any existing capture files and any new capture files you
generate. If you have existing capture files you may need to set this size larger or delete existing capture
files.
The Zyxel Device stops the capture and generates the capture file when either the capture files reach
the File Size or the time period specified in the Duration field expires.

Chapter 50 Troubleshooting
USG/ZyWALL User’s Guide
946
My earlier packet capture files are missing.
New capture files overwrite existing files of the same name. Change the File Suffix field’s setting to avoid
this.
50.1 Resetting the Zyxel Device
If you cannot access the Zyxel Device by any method, try restarting it by turning the power off and then
on again. If you still cannot access the Zyxel Device by any method or you forget the administrator
password(s), you can reset the Zyxel Device to its factory-default settings. Any configuration files or shell
scripts that you saved on the Zyxel Device should still be available afterwards.
Use the following procedure to reset the Zyxel Device to its factory-default settings. This overwrites the
settings in the startup-config.conf file with the settings in the system-default.conf file.
Note: This procedure removes the current configuration.
1Make sure the SYS LED is on and not blinking.
2Press the RESET button and hold it until the SYS LED begins to blink. (This usually takes about five seconds.)
3Release the RESET button, and wait for the Zyxel Device to restart.
You should be able to access the Zyxel Device using the default settings.
50.2 Getting More Troubleshooting Help
Search for support information for your model at www.zyxel.com for more troubleshooting suggestions.

USG/ZyWALL User’s Guide
947
APPENDIX A
Customer Support
In the event of problems that cannot be solved by using this manual, you should contact your vendor. If
you cannot contact your vendor, then contact a Zyxel office for the region in which you bought the
device.
Regional websites are listed below.
See also http://www.zyxel.com/about_zyxel/zyxel_worldwide.shtml.
Please have the following information ready when you contact an office.
Required Information
• Product model and serial number.
• Warranty Information.
• Date that you received your device.
• Brief description of the problem and the steps you took to solve it.
Corporate Headquarters (Worldwide)
Taiwan
• Zyxel Communications Corporation
• http://www.zyxel.com
Asia
China
• Zyxel Communications (Shanghai) Corp.
Zyxel Communications (Beijing) Corp.
Zyxel Communications (Tianjin) Corp.
• http://www.zyxel.cn
India
•Zyxel Technology India Pvt Ltd
• http://www.zyxel.in
Kazakhstan
•Zyxel Kazakhstan
• http://www.zyxel.kz

Appendix A Customer Support
USG/ZyWALL User’s Guide
948
Korea
• Zyxel Korea Corp.
• http://www.zyxel.kr
Malaysia
• Zyxel Malaysia Sdn Bhd.
• http://www.zyxel.com.my
Pakistan
• Zyxel Pakistan (Pvt.) Ltd.
• http://www.zyxel.com.pk
Philippines
• Zyxel Philippines
• http://www.zyxel.com.ph
Singapore
• Zyxel Singapore Pte Ltd.
• http://www.zyxel.com.sg
Taiwan
• Zyxel Communications Corporation
• http://www.zyxel.com
Thailand
• Zyxel Thailand Co., Ltd
• http://www.zyxel.co.th
Vietnam
• Zyxel Communications Corporation-Vietnam Office
• http://www.zyxel.com/vn/vi
Europe
Austria
•Zyxel Deutschland GmbH
• http://www.zyxel.de

Appendix A Customer Support
USG/ZyWALL User’s Guide
949
Belarus
•Zyxel BY
• http://www.zyxel.by
Belgium
• Zyxel Communications B.V.
• http://www.zyxel.com/be/nl/
Bulgaria
•Zyxel България
• http://www.zyxel.com/bg/bg/
Czech
• Zyxel Communications Czech s.r.o
• http://www.zyxel.cz
Denmark
• Zyxel Communications A/S
• http://www.zyxel.dk
Estonia
• Zyxel Estonia
• http://www.zyxel.com/ee/et/
Finland
• Zyxel Communications
• http://www.zyxel.fi
France
•Zyxel France
• http://www.zyxel.fr
Germany
•Zyxel Deutschland GmbH
• http://www.zyxel.de
Hungary
• Zyxel Hungary & SEE
• http://www.zyxel.hu
Latvia
•Zyxel Latvia

Appendix A Customer Support
USG/ZyWALL User’s Guide
950
• http://www.zyxel.com/lv/lv/homepage.shtml
Lithuania
•Zyxel Lithuania
• http://www.zyxel.com/lt/lt/homepage.shtml
Netherlands
• Zyxel Benelux
• http://www.zyxel.nl
Norway
• Zyxel Communications
• http://www.zyxel.no
Poland
• Zyxel Communications Poland
• http://www.zyxel.pl
Romania
• Zyxel Romania
• http://www.zyxel.com/ro/ro
Russia
• Zyxel Russia
• http://www.zyxel.ru
Slovakia
• Zyxel Communications Czech s.r.o. organizacna zlozka
• http://www.zyxel.sk
Spain
•Zyxel Spain
• http://www.zyxel.es
Sweden
• Zyxel Communications
• http://www.zyxel.se
Switzerland
•Studerus AG

Appendix A Customer Support
USG/ZyWALL User’s Guide
951
• http://www.zyxel.ch/
Turkey
• Zyxel Turkey A.S.
• http://www.zyxel.com.tr
UK
• Zyxel Communications UK Ltd.
• http://www.zyxel.co.uk
Ukraine
•Zyxel Ukraine
• http://www.ua.zyxel.com
Latin America
Argentina
• Zyxel Communication Corporation
• http://www.zyxel.com/ec/es/
Ecuador
• Zyxel Communication Corporation
• http://www.zyxel.com/ec/es/
Middle East
Israel
• Zyxel Communication Corporation
• http://il.zyxel.com/homepage.shtml
Middle East
• Zyxel Communication Corporation
• http://www.zyxel.com/me/en/
North America
USA
• Zyxel Communications, Inc. - North America Headquarters
• http://www.us.zyxel.com/

Appendix A Customer Support
USG/ZyWALL User’s Guide
952
Oceania
Australia
• Zyxel Communications Corporation
• http://www.zyxel.com/au/en/
Africa
South Africa
• Nology (Pty) Ltd.
• http://www.zyxel.co.za
USG/ZyWALL User’s Guide
953
APPENDIX B
Legal Information
Copyright
Copyright © 2017 by Zyxel Communications Corporation.
The contents of this publication may not be reproduced in any part or as a whole, transcribed, stored in a retrieval system, translated into any
language, or transmitted in any form or by any means, electronic, mechanical, magnetic, optical, chemical, photocopying, manual, or
otherwise, without the prior written permission of Zyxel Communications Corporation. Published by Zyxel Communications Corporation. All rights
reserved.
Disclaimer
Zyxel does not assume any liability arising out of the application or use of any products, or software described herein. Neither does it convey any
license under its patent rights nor the patent rights of others. Zyxel further reserves the right to make changes in any products described herein
without notice. This publication is subject to change without notice.
Regulatory Notice and Statement (Class A)
Model List: ZyWALL 110, ZyWALL 310, ZyWALL 1100, USG40W, USG60W, USG110, USG210, USG310,
USG1110, USG1900, USG2200-VPN
United States of America
The following information applies if you use the product within USA area.
FCC EMC Statement
• This device complies with part 15 of the FCC Rules. Operation is subject to the following two conditions:
(1) This device may not cause harmful interference, and
(2) This device must accept any interference received, including interference that may cause undesired operation.
• Changes or modifications not expressly approved by the party responsible for compliance could void the user’s authority to operate the
equipment.
• This device has been tested and found to comply with the limits for a Class A digital device, pursuant to part 15 of the FCC Rules. These limits
are designed to provide reasonable protection against harmful interference when the equipment is operated in a commercial environment.
This equipment generates, uses, and can radiate radio frequency energy and, if not installed and used in accordance with the instruction
manual, may cause harmful interference to radio communications. Operation of this equipment in a residential area is likely to cause harmful
interference in which case the user will be required to correct the interference at his own expense.
The following information applies if you use the product with RF function within USA area.
FCC Radiation exposure statement
This equipment complies with FCC RF radiation exposure limits set forth for an uncontrolled environment.
This transmitter must be at least 20 cm from the user and must not be co-located or operating in conjunction with any other antenna or
transmitter.
Canada The following information applies if you use the product within Canada area
Industry Canada ICES statement
CAN ICES-3 (A)/NMB-3(A)
Industry Canada RSS-GEN & RSS-247 statement
• This device complies with Industry Canada license-exempt RSS standard(s). Operation is subject to the following two conditions: (1) this
device may not cause interference, and (2) this device must accept any interference, including interference that may cause undesired
operation of the device.
• This radio transmitter (USG40W: 2468C-Z2FPM9582; USG60W: 2468C-Z2FPM9582 , 2468C-Z5SPM9382) has been approved by Industry Canada
to operate with the antenna types listed below with the maximum permissible gain and required antenna impedance for each antenna
type indicated. Antenna types not included in this list, having a gain greater than the maximum gain indicated for that type, are strictly
prohibited for use with this device.
Appendix B Legal Information
USG/ZyWALL User’s Guide
954
Antenna Information
If the product with 5G wireless function operating in 5150-5250 MHz and 5725-5850 MHz , the following attention must be paid,
• The device for operation in the band 5150-5250 MHz is only for indoor use to reduce the potential for harmful interference to co-channel
mobile satellite systems.
• For devices with detachable antenna(s), the maximum antenna gain permitted for devices in the band 5725-5850 MHz shall be such that the
equipment still complies with the e.i.r.p. limits specified for point-to-point and non-point-to-point operation as appropriate; and
• The worst-case tilt angle(s) necessary to remain compliant with the e.i.r.p. elevation mask requirement set forth in Section 6.2.2(3) of RSS 247
shall be clearly indicated.
If the product with 5G wireless function operating in 5250-5350 MHz and 5470-5725 MHz , the following attention must be paid.
• For devices with detachable antenna(s), the maximum antenna gain permitted for devices in the bands 5250-5350 MHz and 5470-5725 MHz
shall be such that the equipment still complies with the e.i.r.p. limit
• Le présent appareil est conforme aux CNR d’Industrie Canada applicables aux appareils radio exempts de licence. L’exploitation est
autorisée aux deux conditions suivantes : (1) l’appareil ne doit pas produire de brouillage, et (2) l’utilisateur de l’appareil doit accepter tout
brouillage radioélectrique subi, même si le brouillage est susceptible d’en compromettre le fonctionnement.
• Le présent émetteur radio (USG40W: 2468C-Z2FPM9582; USG60W: 2468C-Z2FPM9582 , 2468C-Z5SPM9382) de modèle s'il fait partie du matériel
de catégorieI) a été approuvé par Industrie Canada pour fonctionner avec les types d'antenne énumérés ci-dessous et ayant un gain
admissible maximal et l'impédance requise pour chaque type d'antenne. Les types d'antenne non inclus dans cette liste, ou dont le gain est
supérieur au gain maximal indiqué, sont strictement interdits pour l'exploitation de l'émetteur.
Informations Antenne
Lorsque la fonction sans fil 5G fonctionnant en 5150-5250 MHz and 5725-5850 MHz est activée pour ce produit , il est nécessaire de porter une
attention particulière aux choses suivantes
• Les dispositifs fonctionnant dans la bande 5150-5250 MHz sont réservés uniquement pour une utilisation à l’intérieur afin de réduire les risques
de brouillage préjudiciable aux systèmes de satellites mobiles utilisant les mêmes canaux;
• Pour les dispositifs munis d’antennes amovibles, le gain maximal d'antenne permis (pour les dispositifs utilisant la bande de 5 725 à 5 850 MHz)
doit être conforme à la limite de la p.i.r.e. spécifiée pour l'exploitation point à point et l’exploitation non point à point, selon le cas;
• Les pires angles d’inclinaison nécessaires pour rester conforme à l’exigence de la p.i.r.e. applicable au masque d’élévation, et énoncée à la
section 6.2.2 3) du CNR-247, doivent être clairement indiqués.
Lorsque la fonction sans fil 5G fonctionnant en 5250-5350 MHz et 5470-5725 MHz est activée pour ce produit , il est nécessaire de porter une
attention particulière aux choses suivantes.
• Pour les dispositifs munis d’antennes amovibles, le gain maximal d'antenne permis pour les dispositifs utilisant les bandes de 5 250 à 5 350 MHz
et de 5 470 à 5 725 MHz doit être conforme à la limite de la p.i.r.e.
Industry Canada radiation exposure statement
This device complies with IC radiation exposure limits set forth for an uncontrolled environment. This device should be installed and operated
with a minimum distance of 20 cm between the radiator and your body.
Déclaration d’exposition aux radiations:
Cet équipement est conforme aux limites d’exposition aux rayonnements IC établies pour un environnement non contrôlé. Cet équipement doit
être installé et utilisé avec un minimum de 20 cm de distance entre la source de rayonnement et votre corps.
European Union
The following information applies if you use the product within the European Union.
CE EMC statement
WARNING: This equipment is compliant with Class A of EN55032. In a residential environment this equipment may cause radio interference.
Declaration of Conformity with Regard to EU Directive 1999/5/EC (R&TTE Directive)
• Compliance information for 2.4GHz and/or 5GHz wireless products relevant to the EU and other Countries following the EU Directive 1999/5/
EC (R&TTE).
Type Manufacturer Gain Connector
Dipole LYNwave (USG40W, USG60W) 3dBi Reverse SMA
Dipole Master Wave (USG40W, USG60W) 3dBi Reverse SMA
Type Fabricant Gain Connecteur
Dipole LYNwave (USG40W, USG60W) 3dBi Reverse SMA
Dipole Master Wave (USG40W, USG60W) 3dBi Reverse SMA
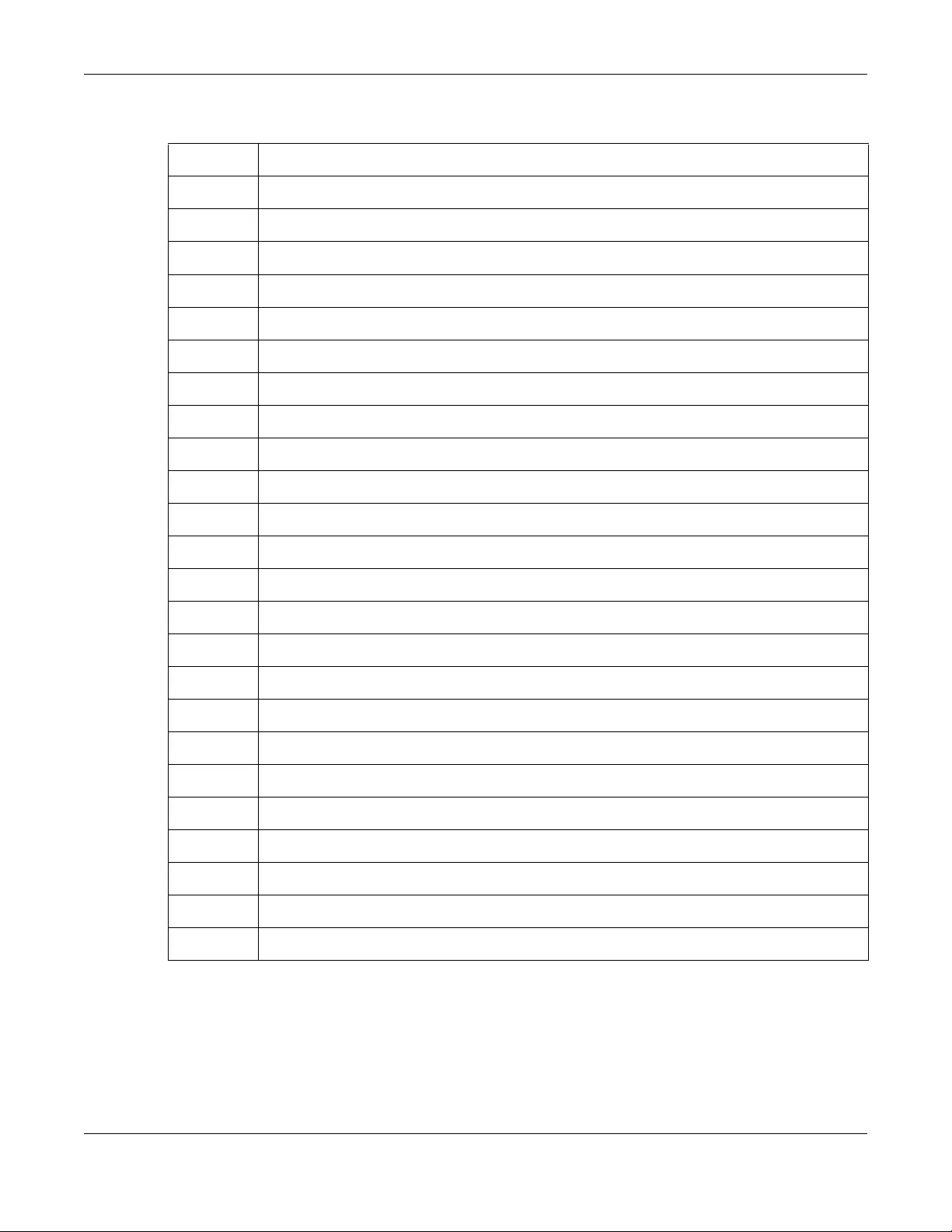
Appendix B Legal Information
USG/ZyWALL User’s Guide
955
• This device is restricted to indoor use only when operating in the 5150 to 5350 MHz frequency range.
National Restrictions
• This product may be used in all EU countries (and other countries following the EU Directive 1999/5/EC) without any limitation except for the
countries mentioned below:
• Ce produit peut être utilisé dans tous les pays de l’UE (et dans tous les pays ayant transposés la directive 1999/5/CE) sans aucune limitation,
excepté pour les pays mentionnés ci-dessous:
• Questo prodotto è utilizzabile in tutte i paesi EU (ed in tutti gli altri paesi che seguono le direttiva 1999/5/EC) senza nessuna limitazione,
eccetto per i paesii menzionati di seguito:
• Das Produkt kann in allen EU Staaten ohne Einschränkungen eingesetzt werden (sowie in anderen Staaten die der Richtlinie 1999/5/CE
folgen) mit Außnahme der folgenden aufgeführten Staaten:
Български
(Bulgarian)
С настоящото Zyxel декларира, че това оборудване е в съответствие със съществените изисквания и другите
приложими разпоредбите на Директива 1999/5/ЕC.
Español
(Spanish)
Por medio de la presente Zyxel declara que el equipo cumple con los requisitos esenciales y cualesquiera otras
disposiciones aplicables o exigibles de la Directiva 1999/5/CE.
Čeština
(Czech)
Zyxel tímto prohlašuje, že tento zařízení je ve shodě se základními požadavky a dalšími příslušnými ustanoveními směrnice
1999/5/EC.
Dansk (Danish) Undertegnede Zyxel erklærer herved, at følgende udstyr udstyr overholder de væsentlige krav og øvrige relevante krav i
direktiv 1999/5/EF.
Deutsch
(German)
Hiermit erklärt Zyxel, dass sich das Gerät Ausstattung in Übereinstimmung mit den grundlegenden Anforderungen und den
übrigen einschlägigen Bestimmungen der Richtlinie 1999/5/EU befindet.
Eesti keel
(Estonian)
Käesolevaga kinnitab Zyxel seadme seadmed vastavust direktiivi 1999/5/EÜ põhinõuetele ja nimetatud direktiivist
tulenevatele teistele asjakohastele sätetele.
Ελληνικά
(Greek)
ΜΕ ΤΗΝ ΠΑΡΟΥΣΑ Zyxel ∆ΗΛΩΝΕΙ ΟΤΙ εξοπλισμός ΣΥΜΜΟΡΦΩΝΕΤΑΙ ΠΡΟΣ ΤΙΣ ΟΥΣΙΩ∆ΕΙΣ ΑΠΑΙΤΗΣΕΙΣ ΚΑΙ ΤΙΣ ΛΟΙΠΕΣ ΣΧΕΤΙΚΕΣ
∆ΙΑΤΑΞΕΙΣ ΤΗΣ Ο∆ΗΓΙΑΣ 1999/5/ΕC.
English Hereby, Zyxel declares that this device is in compliance with the essential requirements and other relevant provisions of
Directive 1999/5/EC.
Français
(French)
Par la présente Zyxel déclare que l'appareil équipements est conforme aux exigences essentielles et aux autres dispositions
pertinentes de la directive 1999/5/EC.
Hrvatski
(Croatian)
Zyxel ovime izjavljuje da je radijska oprema tipa u skladu s Direktivom 1999/5/EC.
Íslenska
(Icelandic)
Hér með lýsir, Zyxel því yfir að þessi búnaður er í samræmi við grunnkröfur og önnur viðeigandi ákvæði tilskipunar 1999/5/EC.
Italiano (Italian) Con la presente Zyxel dichiara che questo attrezzatura è conforme ai requisiti essenziali ed alle altre disposizioni pertinenti
stabilite dalla direttiva 1999/5/CE.
Latviešu valoda
(Latvian)
Ar šo Zyxel deklarē, ka iekārtas atbilst Direktīvas 1999/5/EK būtiskajām prasībām un citiem ar to saistītajiem noteikumiem.
Lietuvių kalba
(Lithuanian)
Šiuo Zyxel deklaruoja, kad šis įranga atitinka esminius reikalavimus ir kitas 1999/5/EB Direktyvos nuostatas.
Magyar
(Hungarian)
Alulírott, Zyxel nyilatkozom, hogy a berendezés megfelel a vonatkozó alapvetõ követelményeknek és az 1999/5/EK irányelv
egyéb elõírásainak.
Malti (Maltese) Hawnhekk, Zyxel, jiddikjara li dan tagħmir jikkonforma mal-ħtiġijiet essenzjali u ma provvedimenti oħrajn relevanti li hemm
fid-Dirrettiva 1999/5/EC.
Nederlands
(Dutch)
Hierbij verklaart Zyxel dat het toestel uitrusting in overeenstemming is met de essentiële eisen en de andere relevante
bepalingen van richtlijn 1999/5/EC.
Polski (Polish) Niniejszym Zyxel oświadcza, że sprzęt jest zgodny z zasadniczymi wymogami oraz pozostałymi stosownymi postanowieniami
Dyrektywy 1999/5/EC.
Português
(Portuguese)
Zyxel declara que este equipamento está conforme com os requisitos essenciais e outras disposições da Directiva 1999/5/
EC.
Română
(Romanian)
Prin prezenta, Zyxel declară că acest echipament este în conformitate cu cerinţele esenţiale şi alte prevederi relevante ale
Directivei 1999/5/EC.
Slovenčina
(Slovak)
Zyxel týmto vyhlasuje, že zariadenia spĺňa základné požiadavky a všetky príslušné ustanovenia Smernice 1999/5/EC.
Slovenščina
(Slovene)
Zyxel izjavlja, da je ta oprema v skladu z bistvenimi zahtevami in ostalimi relevantnimi določili direktive 1999/5/EC.
Suomi (Finnish) Zyxel vakuuttaa täten että laitteet tyyppinen laite on direktiivin 1999/5/EY oleellisten vaatimusten ja sitä koskevien direktiivin
muiden ehtojen mukainen.
Svenska
(Swedish)
Härmed intygar Zyxel att denna utrustning står I överensstämmelse med de väsentliga egenskapskrav och övriga relevanta
bestämmelser som framgår av direktiv 1999/5/EC.
Norsk
(Norwegian)
Erklærer herved Zyxel at dette utstyret er I samsvar med de grunnleggende kravene og andre relevante bestemmelser I
direktiv 1999/5/EF.
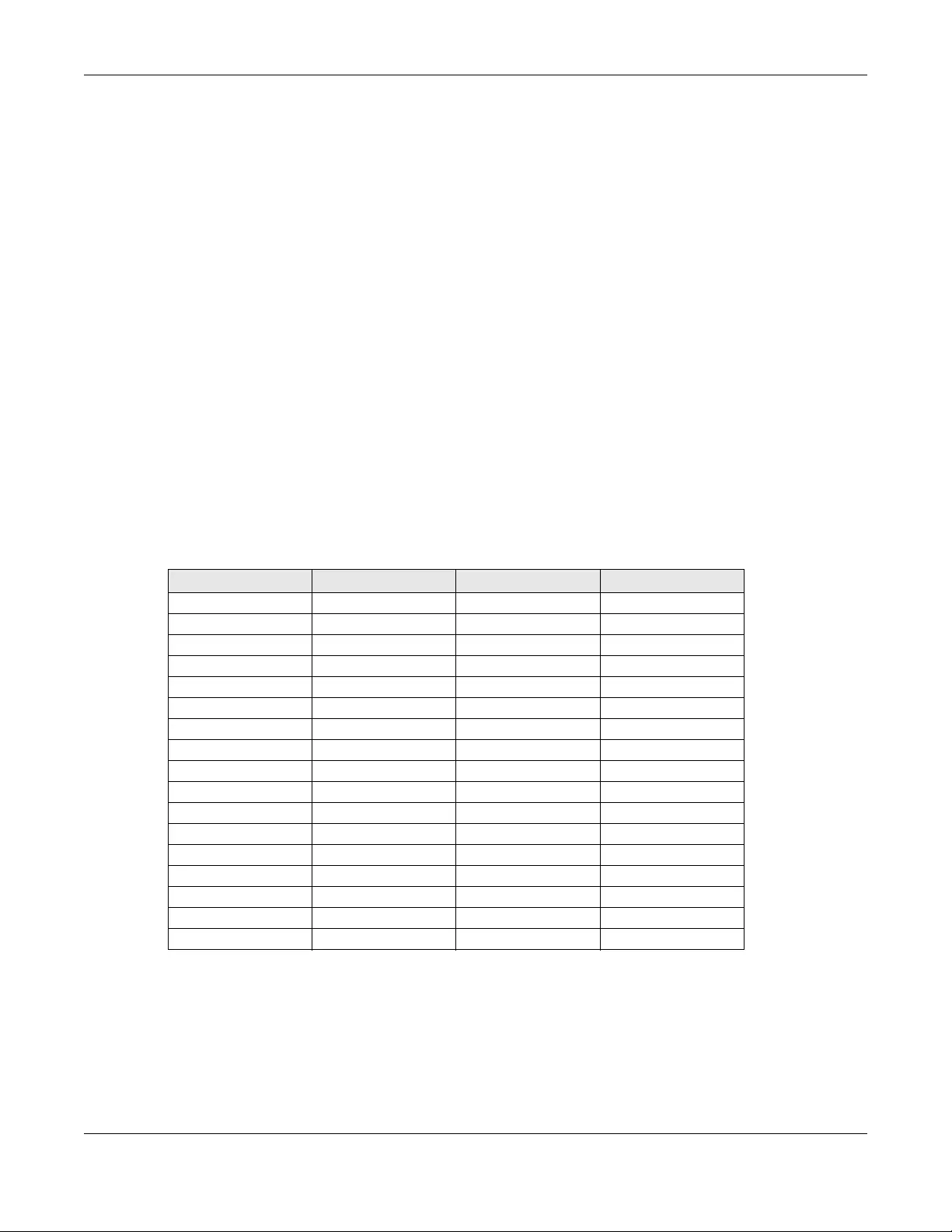
Appendix B Legal Information
USG/ZyWALL User’s Guide
956
In the majority of the EU and other European countries, the 2.4GHz and 5GHz bands have been made available for the use of wireless local area
networks (LANs). Later in this document you will find an overview of countries in which additional restrictions or requirements or both are
applicable. The requirements for any country may evolve. ZyXEL recommends that you check with the local authorities for the latest status of
their national regulations for both the 2.4GHz and 5GHz wireless LANs. The following countries have restrictions and/or requirements in addition to
those given in the table labeled “Overview of Regulatory Requirements for Wireless LANs”:
Belgium:
• The Belgian Institute for Postal Services and Telecommunications (BIPT) must be notified of any outdoor wireless link having a range
exceeding 300 meters. Please check http://www.bipt.be for more details.
• Draadloze verbindingen voor buitengebruik en met een reikwijdte van meer dan 300 meter dienen aangemeld te worden bij het Belgisch
Instituut voor postdiensten en telecommunicatie (BIPT). Zie http://www.bipt.be voor meer gegevens.
• Les liaisons sans fil pour une utilisation en extérieur d’une distance supérieure à 300 mètres doivent être notifiées à l’Institut Belge des services
Postaux et des Télécommunications (IBPT). Visitez http://www.ibpt.be pour de plus amples détails.
Denmark:
• In Denmark, the band 5150 - 5350 MHz is also allowed for outdoor usage.
• Danmark må frekvensbåndet 5150 - 5350 også anvendes udendørs.
Italy:
• This product meets the National Radio Interface and the requirements specified in the National Frequency Allocation Table for Italy. Unless
this wireless LAN product is operating within the boundaries of the owner's property, its use requires a “general authorization.” Please check
http://www.sviluppoeconomico.gov.it/ for more details.
• Questo prodotto è conforme alla specifiche di Interfaccia Radio Nazionali e rispetta il Piano Nazionale di ripartizione delle frequenze in Italia.
Se non viene installato all 'interno del proprio fondo, l'utilizzo di prodotti Wireless LAN richiede una “Autorizzazione Generale”. Consultare
http://www.sviluppoeconomico.gov.it/ per maggiori dettagli.
Latvia:
• The outdoor usage of the 2.4 GHz band requires an authorization from the Electronic Communications Office. Please check http://
www.esd.lv for more details.
• 2.4 GHz frekvenèu joslas izmantoðanai ârpus telpâm nepiecieðama atïauja no Elektronisko sakaru direkcijas. Vairâk informâcijas: http://
www.esd.lv.
Notes:
1. Although Norway, Switzerland and Liechtenstein are not EU member states, the EU Directive 1999/5/EC has also been implemented in those
countries.
2. The regulatory limits for maximum output power are specified in EIRP. The EIRP level (in dBm) of a device can be calculated by adding the
gain of the antenna used (specified in dBi) to the output power available at the connector (specified in dBm).
List of National Codes
Safety Warnings
• Do not use this product near water, for example, in a wet basement or near a swimming pool.
• Do not expose your device to dampness, dust or corrosive liquids.
• Do not store things on the device.
• Do not obstruct the device ventilation slots as insufficient airflow may harm your device. For example, do not place the device in an
enclosed space such as a box or on a very soft surface such as a bed or sofa.
• Do not install, use, or service this device during a thunderstorm. There is a remote risk of electric shock from lightning.
• Connect ONLY suitable accessories to the device.
• Do not open the device or unit. Opening or removing covers can expose you to dangerous high voltage points or other risks. Only qualified
service personnel should service or disassemble this device. Please contact your vendor for further information.
• Make sure to connect the cables to the correct ports.
• Place connecting cables carefully so that no one will step on them or stumble over them.
COUNTRY ISO 3166 2 LETTER CODE COUNTRY ISO 3166 2 LETTER CODE
Austria AT Liechtenstein LI
Belgium BE Lithuania LT
Bulgaria BG Luxembourg LU
Croatia HR Malta MT
Cyprus CY Netherlands NL
Czech Republic CR Norway NO
Denmark DK Poland PL
Estonia EE Portugal PT
Finland FI Romania RO
France FR Serbia RS
Germany DE Slovakia SK
Greece GR Slovenia SI
Hungary HU Spain ES
Iceland IS Sweden SE
Ireland IE Switzerland CH
Italy IT Turkey TR
Latvia LV United Kingdom GB
Appendix B Legal Information
USG/ZyWALL User’s Guide
957
• Always disconnect all cables from this device before servicing or disassembling.
• Do not remove the plug and connect it to a power outlet by itself; always attach the plug to the power adaptor first before connecting it to
a power outlet.
• Do not allow anything to rest on the power adaptor or cord and do NOT place the product where anyone can walk on the power adaptor
or cord.
• Please use the provided or designated connection cables/power cables/ adaptors. Connect it to the right supply voltage (for example,
110V AC in North America or 230V AC in Europe). If the power adaptor or cord is damaged, it might cause electrocution. Remove it from the
device and the power source, repairing the power adapter or cord is prohibited. Contact your local vendor to order a new one.
• Do not use the device outside, and make sure all the connections are indoors. There is a remote risk of electric shock from lightning.
• Caution: Risk of explosion if battery is replaced by an incorrect type, dispose of used batteries according to the instruction. Dispose them at
the applicable collection point for the recycling of electrical and electronic device. For detailed information about recycling of this product,
please contact your local city office, your household waste disposal service or the store where you purchased the product.
• Use ONLY power wires of the appropriate wire gauge for your device. Connect it to a power supply of the correct voltage.
• Fuse Warning! Replace a fuse only with a fuse of the same type and rating.
• The POE (Power over Ethernet) devices that supply or receive power and their connected Ethernet cables must all be completely indoors.
• The following warning statements apply, where the disconnect device is not incorporated in the device or where the plug on the power
supply cord is intended to serve as the disconnect device,
- For permanently connected devices, a readily accessible disconnect device shall be incorporated external to the device;
- For pluggable devices, the socket-outlet shall be installed near the device and shall be easily accessible.
• This device must be grounded. Never defeat the ground conductor or operate the device in the absence of a suitably installed ground
conductor. Contact the appropriate electrical inspection authority or an electrician if you are uncertain that suitable grounding is available.
• When connecting or disconnecting power to hot-pluggable power supplies, if offered with your system, observe the following guidelines:
- Install the power supply before connecting the power cable to the power supply.
- Unplug the power cable before removing the power supply.
- If the system has multiple sources of power, disconnect power from the system by unplugging all power cables from the power supply.
Environment Statement
European Union - Disposal and Recycling Information
The symbol below means that according to local regulations your product and/or its battery shall be disposed of separately from domestic
waste. If this product is end of life, take it to a recycling station designated by local authorities. At the time of disposal, the separate collection of
your product and/or its battery will help save natural resources and ensure that the environment is sustainable development.
Die folgende Symbol bedeutet, dass Ihr Produkt und/oder seine Batterie gemäß den örtlichen Bestimmungen getrennt vom Hausmüll entsorgt
werden muss. Wenden Sie sich an eine Recyclingstation, wenn dieses Produkt das Ende seiner Lebensdauer erreicht hat. Zum Zeitpunkt der
Entsorgung wird die getrennte Sammlung von Produkt und/oder seiner Batterie dazu beitragen, natürliche Ressourcen zu sparen und die Umwelt
und die menschliche Gesundheit zu schützen.
El símbolo de abajo indica que según las regulaciones locales, su producto y/o su batería deberán depositarse como basura separada de la
doméstica. Cuando este producto alcance el final de su vida útil, llévelo a un punto limpio. Cuando llegue el momento de desechar el
producto, la recogida por separado éste y/o su batería ayudará a salvar los recursos naturales y a proteger la salud humana y
medioambiental.
Le symbole ci-dessous signifie que selon les réglementations locales votre produit et/ou sa batterie doivent être éliminés séparément des ordures
ménagères. Lorsque ce produit atteint sa fin de vie, amenez-le à un centre de recyclage. Au moment de la mise au rebut, la collecte séparée
de votre produit et/ou de sa batterie aidera à économiser les ressources naturelles et protéger l'environnement et la santé humaine.
Il simbolo sotto significa che secondo i regolamenti locali il vostro prodotto e/o batteria deve essere smaltito separatamente dai rifiuti domestici.
Quando questo prodotto raggiunge la fine della vita di servizio portarlo a una stazione di riciclaggio. Al momento dello smaltimento, la raccolta
separata del vostro prodotto e/o della sua batteria aiuta a risparmiare risorse naturali e a proteggere l'ambiente e la salute umana.
Symbolen innebär att enligt lokal lagstiftning ska produkten och/eller dess batteri kastas separat från hushållsavfallet. När den här produkten når
slutet av sin livslängd ska du ta den till en återvinningsstation. Vid tiden för kasseringen bidrar du till en bättre miljö och mänsklig hälsa genom att
göra dig av med den på ett återvinningsställe.
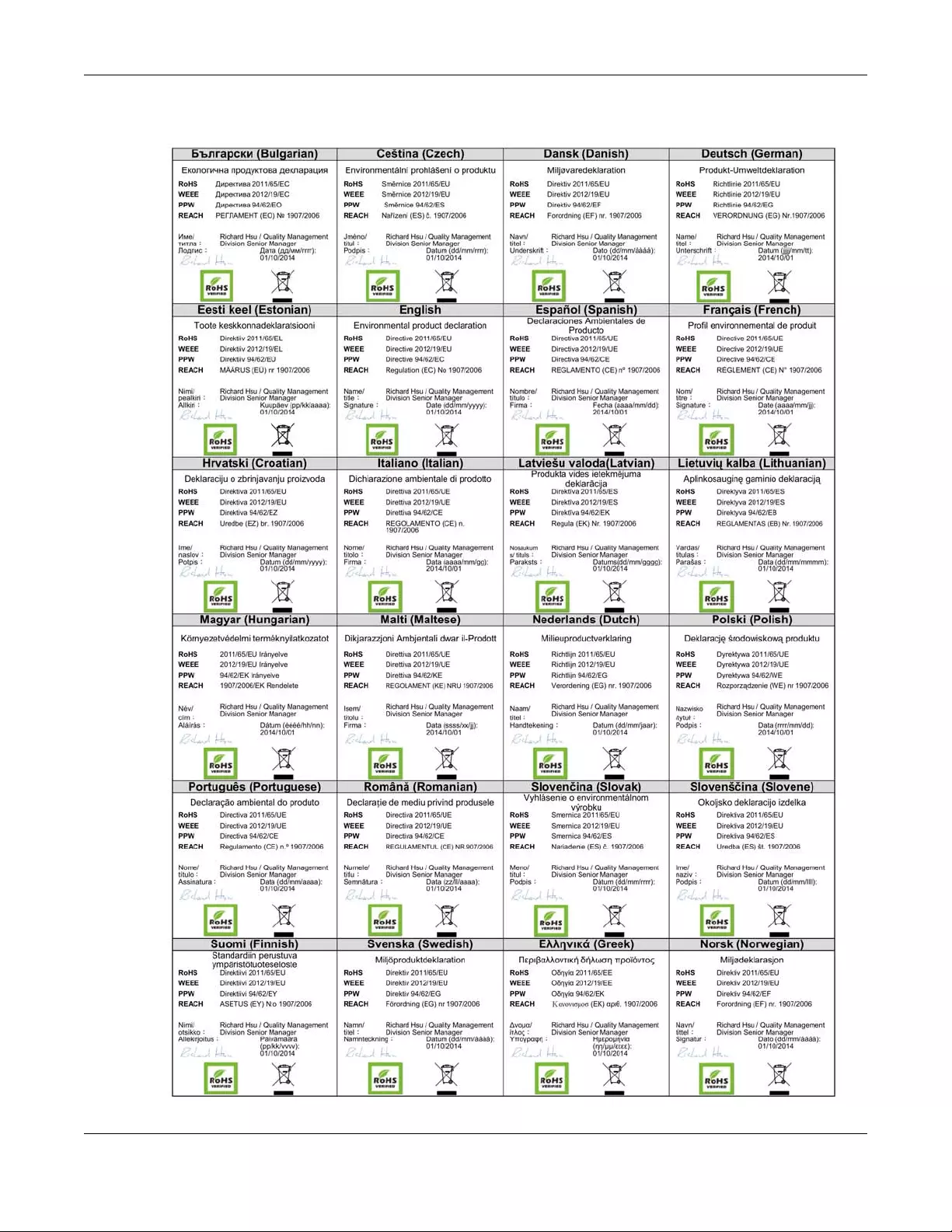
Appendix B Legal Information
USG/ZyWALL User’s Guide
958
Environmental Product Declaration

Appendix B Legal Information
USG/ZyWALL User’s Guide
959
台灣
以下訊息僅適用於產品具有無線功能且銷售至台灣地區
• 第十二條 經型式認證合格之低功率射頻電機,非經許可,公司,商號或使用者均不得擅自變更頻率、加大功率或變更原設計之特性及功能。
• 第十四條 低功率射頻電機之使用不得影響飛航安全及干擾合法通信;經發現有干擾現象時,應立即停用,並改善至無干擾時方得繼續使用。
前項合法通信,指依電信法規定作業之無線電通信。 低功率射頻電機須忍受合法通信或工業、科學及醫療用電波輻射性電機設備之干擾。
• 電磁波曝露量 MPE 標準值 1mW/cm2,送測產品實測值為: 0.150 mW/ cm2 (USG60W); 0.108 mW/ cm2 (USG40W);; 本產品使用時建議應距離人體
20 cm
• 無線資訊傳輸設備忍受合法通信之干擾且不得干擾合法通信;如造成干擾,應立即停用, 俟無干擾之虞,始得繼續使用。
• 無線資訊傳設備的製造廠商應確保頻率穩定性,如依製造廠商使用手冊上所述正常操作, 發射的信號應維持於操作頻帶中
以下訊息僅適用於產品操作於 5.25-5.35 秭赫頻帶內並銷售至台灣地區
• 在 5.25-5.35 秭赫頻帶內操作之無線資訊傳輸設備,限於室內使用。
以下訊息僅適用於產品屬於專業安裝並銷售至台灣地區
• 本器材須經專業工程人員安裝及設定,始得設置使用,且不得直接販售給一般消費者。
安全警告 - 為了您的安全,請先閱讀以下警告及指示 :
• 請勿將此產品接近水、火焰或放置在高溫的環境。
• 避免設備接觸 :
- 任何液體 - 切勿讓設備接觸水、雨水、高濕度、污水腐蝕性的液體或其他水份。
- 灰塵及污物 - 切勿接觸灰塵、污物、沙土、食物或其他不合適的材料。
• 雷雨天氣時,不要安裝,使用或維修此設備。有遭受電擊的風險。
• 切勿重摔或撞擊設備,並勿使用不正確的電源變壓器。
• 若接上不正確的電源變壓器會有爆炸的風險。
• 請勿隨意更換產品內的電池。
• 如果更換不正確之電池型式,會有爆炸的風險,請依製造商說明書處理使用過之電池。
• 請將廢電池丟棄在適當的電器或電子設備回收處。
• 請勿將設備解體。
• 請勿阻礙設備的散熱孔,空氣對流不足將會造成設備損害。
• 請插在正確的電壓供給插座 ( 如 : 北美 / 台灣電壓 110V AC,歐洲是 230V AC)。
• 假若電源變壓器或電源變壓器的纜線損壞,請從插座拔除,若您還繼續插電使用,會有觸電死亡的風險。
• 請勿試圖修理電源變壓器或電源變壓器的纜線,若有毀損,請直接聯絡您購買的店家,購買一個新的電源變壓器。
• 請勿將此設備安裝於室外,此設備僅適合放置於室內。
• 請勿隨一般垃圾丟棄。
• 請參閱產品背貼上的設備額定功率。
• 請參考產品型錄或是彩盒上的作業溫度。
• 產品沒有斷電裝置或者採用電源線的插頭視為斷電裝置的一部分,以下警語將適用 :
- 對永久連接之設備, 在設備外部須安裝可觸及之斷電裝置;
- 對插接式之設備, 插座必須接近安裝之地點而且是易於觸及的。
About the Symbols
Various symbols are used in this product to ensure correct usage, to prevent danger to the user and others, and to prevent property damage.
The meaning of these symbols are described below. It is important that you read these descriptions thoroughly and fully understand the
contents.
Appendix B Legal Information
USG/ZyWALL User’s Guide
960
Explanation of the Symbols
Viewing Certifications
Go to http://www.zyxel.com to view this product’s documentation and certifications.
Zyxel Limited Warranty
Zyxel warrants to the original end user (purchaser) that this product is free from any defects in material or workmanship for a specific period (the
Warranty Period) from the date of purchase. The Warranty Period varies by region. Check with your vendor and/or the authorized Zyxel local
distributor for details about the Warranty Period of this product. During the warranty period, and upon proof of purchase, should the product
have indications of failure due to faulty workmanship and/or materials, Zyxel will, at its discretion, repair or replace the defective products or
components without charge for either parts or labor, and to whatever extent it shall deem necessary to restore the product or components to
proper operating condition. Any replacement will consist of a new or re-manufactured functionally equivalent product of equal or higher value,
and will be solely at the discretion of Zyxel. This warranty shall not apply if the product has been modified, misused, tampered with, damaged by
an act of God, or subjected to abnormal working conditions.
Note
Repair or replacement, as provided under this warranty, is the exclusive remedy of the purchaser. This warranty is in lieu of all other warranties,
express or implied, including any implied warranty of merchantability or fitness for a particular use or purpose. Zyxel shall in no event be held
liable for indirect or consequential damages of any kind to the purchaser.
To obtain the services of this warranty, contact your vendor. You may also refer to the warranty policy for the region in which you bought the
device at http://www.zyxel.com/web/support_warranty_info.php.
Registration
Register your product online to receive e-mail notices of firmware upgrades and information at www.zyxel.com for global products, or at
www.us.zyxel.com for North American products.
Open Source Licenses
This product contains in part some free software distributed under GPL license terms and/or GPL like licenses. Open source licenses are provided
with the firmware package. You can download the latest firmware at www.zyxel.com. To obtain the source code covered under those Licenses,
please contact support@zyxel.com.tw to get it.
Regulatory Notice and Statement (Class B)
Model List: USG20-VPN, USG20W-VPN, USG40, USG60
UNITED STATES of AMERICA
The following information applies if you use the product within USA area.
SYMBOL EXPLANATION
Alternating current (AC):
AC is an electric current in which the flow of electric charge periodically reverses direction.
Direct current (DC):
DC if the unidirectional flow or movement of electric charge carriers.
Earth; ground:
A wiring terminal intended for connection of a Protective Earthing Conductor.
Class II equipment:
The method of protection against electric shock in the case of class II equipment is either double insulation
or reinforced insulation.
Appendix B Legal Information
USG/ZyWALL User’s Guide
961
FCC EMC Statement
• The device complies with Part 15 of FCC rules. Operation is subject to the following two conditions:
(1) This device may not cause harmful interference, and
(2) This device must accept any interference received, including interference that may cause undesired operation.
• Changes or modifications not expressly approved by the party responsible for compliance could void the user’s authority to operate the
device.
• This product has been tested and complies with the specifications for a Class B digital device, pursuant to Part 15 of the FCC Rules. These
limits are designed to provide reasonable protection against harmful interference in a residential installation. This device generates, uses, and
can radiate radio frequency energy and, if not installed and used according to the instructions, may cause harmful interference to radio
communications. However, there is no guarantee that interference will not occur in a particular installation.
• If this device does cause harmful interference to radio or television reception, which is found by turning the device off and on, the user is
encouraged to try to correct the interference by one or more of the following measures:
• Reorient or relocate the receiving antenna
• Increase the separation between the devices
• Connect the equipment to an outlet other than the receiver’s
• Consult a dealer or an experienced radio/TV technician for assistance
The following information applies if you use the product with RF function within USA area.
FCC Radiation Exposure Statement
• This device complies with FCC RF radiation exposure limits set forth for an uncontrolled environment.
• This transmitter must be at least 20 cm from the user and must not be co-located or operating in conjunction with any other antenna or
transmitter.
CANADA
The following information applies if you use the product within Canada area.
Industry Canada ICES statement
CAN ICES-3 (B)/NMB-3(B)
Industry Canada RSS-GEN & RSS-247 statement
• This device complies with Industry Canada license-exempt RSS standard(s). Operation is subject to the following two conditions: (1) this
device may not cause interference, and (2) this device must accept any interference, including interference that may cause undesired
operation of the device.
• This radio transmitter (USG20W-VPN: 2468C-USG20WVPN) has been approved by Industry Canada to operate with the antenna types listed
below with the maximum permissible gain and required antenna impedance for each antenna type indicated. Antenna types not included
in this list, having a gain greater than the maximum gain indicated for that type, are strictly prohibited for use with this device.
Antenna Information
If the product with 5G wireless function operating in 5150-5250 MHz and 5725-5850 MHz , the following attention must be paid,
• The device for operation in the band 5150-5250 MHz is only for indoor use to reduce the potential for harmful interference to co-channel
mobile satellite systems.
• For devices with detachable antenna(s), the maximum antenna gain permitted for devices in the band 5725-5850 MHz shall be such that the
equipment still complies with the e.i.r.p. limits specified for point-to-point and non-point-to-point operation as appropriate; and
• The worst-case tilt angle(s) necessary to remain compliant with the e.i.r.p. elevation mask requirement set forth in Section 6.2.2(3) of RSS 247
shall be clearly indicated.
If the product with 5G wireless function operating in 5250-5350 MHz and 5470-5725 MHz , the following attention must be paid.
• For devices with detachable antenna(s), the maximum antenna gain permitted for devices in the bands 5250-5350 MHz and 5470-5725 MHz
shall be such that the equipment still complies with the e.i.r.p. limit
• Le présent appareil est conforme aux CNR d’Industrie Canada applicables aux appareils radio exempts de licence. L’exploitation est
autorisée aux deux conditions suivantes : (1) l’appareil ne doit pas produire de brouillage, et (2) l’utilisateur de l’appareil doit accepter tout
brouillage radioélectrique subi, même si le brouillage est susceptible d’en compromettre le fonctionnement.
• Le présent émetteur radio (USG20W-VPN: 2468C-USG20WVPN) de modèle s'il fait partie du matériel de catégorieI) a été approuvé par
Industrie Canada pour fonctionner avec les types d'antenne énumérés ci-dessous et ayant un gain admissible maximal et l'impédance
requise pour chaque type d'antenne. Les types d'antenne non inclus dans cette liste, ou dont le gain est supérieur au gain maximal indiqué,
sont strictement interdits pour l'exploitation de l'émetteur.
Type Manufacturer Gain Connector
Dipole WHA YU (USG20W-VPN) 2dBi Reverse SMA
Dipole WHA YU (USG20W-VPN) 3dBi Reverse SMA
Appendix B Legal Information
USG/ZyWALL User’s Guide
962
Informations Antenne
Lorsque la fonction sans fil 5G fonctionnant en 5150-5250 MHz and 5725-5850 MHz est activée pour ce produit , il est nécessaire de porter une
attention particulière aux choses suivantes
• Les dispositifs fonctionnant dans la bande 5150-5250 MHz sont réservés uniquement pour une utilisation à l’intérieur afin de réduire les risques
de brouillage préjudiciable aux systèmes de satellites mobiles utilisant les mêmes canaux;
• Pour les dispositifs munis d’antennes amovibles, le gain maximal d'antenne permis (pour les dispositifs utilisant la bande de 5 725 à 5 850 MHz)
doit être conforme à la limite de la p.i.r.e. spécifiée pour l'exploitation point à point et l’exploitation non point à point, selon le cas;
• Les pires angles d’inclinaison nécessaires pour rester conforme à l’exigence de la p.i.r.e. applicable au masque d’élévation, et énoncée à la
section 6.2.2 3) du CNR-247, doivent être clairement indiqués.
Lorsque la fonction sans fil 5G fonctionnant en 5250-5350 MHz et 5470-5725 MHz est activée pour ce produit , il est nécessaire de porter une
attention particulière aux choses suivantes.
• Pour les dispositifs munis d’antennes amovibles, le gain maximal d'antenne permis pour les dispositifs utilisant les bandes de 5 250 à 5 350 MHz
et de 5 470 à 5 725 MHz doit être conforme à la limite de la p.i.r.e.
Industry Canada radiation exposure statement
This device complies with IC radiation exposure limits set forth for an uncontrolled environment. This device should be installed and operated
with a minimum distance of 20 cm between the radiator and your body.
Déclaration d’exposition aux radiations:
Cet équipement est conforme aux limites d’exposition aux rayonnements IC établies pour un environnement non contrôlé. Cet équipement doit
être installé et utilisé avec un minimum de 20 cm de distance entre la source de rayonnement et votre corps.
EUROPEA N UNION
The following information applies if you use the product within the European Union.
Declaration of Conformity with Regard to EU Directive 1999/5/EC (R&TTE Directive)
• Compliance information for 2.4GHz and/or 5GHz wireless products relevant to the EU and other Countries following the EU Directive 1999/5/
EC (R&TTE).
• This device is restricted to indoor use only when operating in the 5150 to 5350 MHz frequency range.
Type Fabricant Gain Connecteur
Dipole WHA YU (USG20W-VPN) 2dBi Reverse SMA
Dipole WHA YU (USG20W-VPN) 3dBi Reverse SMA
Български
(Bulgarian)
С настоящото Zyxel декларира, че това оборудване е в съответствие със съществените изисквания и другите
приложими разпоредбите на Директива 1999/5/ЕC.
Español
(Spanish)
Por medio de la presente Zyxel declara que el equipo cumple con los requisitos esenciales y cualesquiera otras
disposiciones aplicables o exigibles de la Directiva 1999/5/CE.
Čeština
(Czech)
Zyxel tímto prohlašuje, že tento zařízení je ve shodě se základními požadavky a dalšími příslušnými ustanoveními směrnice
1999/5/EC.
Dansk (Danish) Undertegnede Zyxel erklærer herved, at følgende udstyr udstyr overholder de væsentlige krav og øvrige relevante krav i
direktiv 1999/5/EF.
Deutsch
(German)
Hiermit erklärt Zyxel, dass sich das Gerät Ausstattung in Übereinstimmung mit den grundlegenden Anforderungen und den
übrigen einschlägigen Bestimmungen der Richtlinie 1999/5/EU befindet.
Eesti keel
(Estonian)
Käesolevaga kinnitab Zyxel seadme seadmed vastavust direktiivi 1999/5/EÜ põhinõuetele ja nimetatud direktiivist
tulenevatele teistele asjakohastele sätetele.
Ελληνικά
(Greek)
ΜΕ ΤΗΝ ΠΑΡΟΥΣΑ Zyxel ∆ΗΛΩΝΕΙ ΟΤΙ εξοπλισμός ΣΥΜΜΟΡΦΩΝΕΤΑΙ ΠΡΟΣ ΤΙΣ ΟΥΣΙΩ∆ΕΙΣ ΑΠΑΙΤΗΣΕΙΣ ΚΑΙ ΤΙΣ ΛΟΙΠΕΣ ΣΧΕΤΙΚΕΣ
∆ΙΑΤΑΞΕΙΣ ΤΗΣ Ο∆ΗΓΙΑΣ 1999/5/ΕC.
English Hereby, Zyxel declares that this device is in compliance with the essential requirements and other relevant provisions of
Directive 1999/5/EC.
Français
(French)
Par la présente Zyxel déclare que l'appareil équipements est conforme aux exigences essentielles et aux autres dispositions
pertinentes de la directive 1999/5/EC.
Hrvatski
(Croatian)
Zyxel ovime izjavljuje da je radijska oprema tipa u skladu s Direktivom 1999/5/EC.
Íslenska
(Icelandic)
Hér með lýsir, Zyxel því yfir að þessi búnaður er í samræmi við grunnkröfur og önnur viðeigandi ákvæði tilskipunar 1999/5/EC.
Appendix B Legal Information
USG/ZyWALL User’s Guide
963
National Restrictions
• This product may be used in all EU countries (and other countries following the EU Directive 1999/5/EC) without any limitation except for the
countries mentioned below:
• Ce produit peut être utilisé dans tous les pays de l’UE (et dans tous les pays ayant transposés la directive 1999/5/CE) sans aucune limitation,
excepté pour les pays mentionnés ci-dessous:
• Questo prodotto è utilizzabile in tutte i paesi EU (ed in tutti gli altri paesi che seguono le direttiva 1999/5/EC) senza nessuna limitazione,
eccetto per i paesii menzionati di seguito:
• Das Produkt kann in allen EU Staaten ohne Einschränkungen eingesetzt werden (sowie in anderen Staaten die der Richtlinie 1999/5/CE
folgen) mit Außnahme der folgenden aufgeführten Staaten:
In the majority of the EU and other European countries, the 2.4GHz and 5GHz bands have been made available for the use of wireless local area
networks (LANs). Later in this document you will find an overview of countries in which additional restrictions or requirements or both are
applicable. The requirements for any country may evolve. Zyxel recommends that you check with the local authorities for the latest status of
their national regulations for both the 2.4GHz and 5GHz wireless LANs. The following countries have restrictions and/or requirements in addition to
those given in the table labeled “Overview of Regulatory Requirements for Wireless LANs”:.
Belgium
• The Belgian Institute for Postal Services and Telecommunications (BIPT) must be notified of any outdoor wireless link having a range
exceeding 300 meters. Please check http://www.bipt.be for more details.
• Draadloze verbindingen voor buitengebruik en met een reikwijdte van meer dan 300 meter dienen aangemeld te worden bij het Belgisch
Instituut voor postdiensten en telecommunicatie (BIPT). Zie http://www.bipt.be voor meer gegevens.
• Les liaisons sans fil pour une utilisation en extérieur d’une distance supérieure à 300 mètres doivent être notifiées à l’Institut Belge des services
Postaux et des Télécommunications (IBPT). Visitez http://www.ibpt.be pour de plus amples détails.
Denmark
• In Denmark, the band 5150 - 5350 MHz is also allowed for outdoor usage.
• I Danmark må frekvensbåndet 5150 - 5350 også anvendes udendørs.
Italy
• This product meets the National Radio Interface and the requirements specified in the National Frequency Allocation Table for Italy. Unless
this wireless LAN product is operating within the boundaries of the owner's property, its use requires a “general authorization.” Please check
http://www.sviluppoeconomico.gov.it/ for more details.
• Questo prodotto è conforme alla specifiche di Interfaccia Radio Nazionali e rispetta il Piano Nazionale di ripartizione delle frequenze in Italia.
Se non viene installato all 'interno del proprio fondo, l'utilizzo di prodotti Wireless LAN richiede una “Autorizzazione Generale”. Consultare
http://www.sviluppoeconomico.gov.it/ per maggiori dettagli.
Latvia
• The outdoor usage of the 2.4 GHz band requires an authorization from the Electronic Communications Office. Please check http://
www.esd.lv for more details.
• 2.4 GHz frekvenèu joslas izmantoðanai ârpus telpâm nepiecieðama atïauja no Elektronisko sakaru direkcijas. Vairâk informâcijas: http://
www.esd.lv.
Italiano (Italian) Con la presente Zyxel dichiara che questo attrezzatura è conforme ai requisiti essenziali ed alle altre disposizioni pertinenti
stabilite dalla direttiva 1999/5/CE.
Latviešu valoda
(Latvian)
Ar šo Zyxel deklarē, ka iekārtas atbilst Direktīvas 1999/5/EK būtiskajām prasībām un citiem ar to saistītajiem noteikumiem.
Lietuvių kalba
(Lithuanian)
Šiuo Zyxel deklaruoja, kad šis įranga atitinka esminius reikalavimus ir kitas 1999/5/EB Direktyvos nuostatas.
Magyar
(Hungarian)
Alulírott, Zyxel nyilatkozom, hogy a berendezés megfelel a vonatkozó alapvetõ követelményeknek és az 1999/5/EK irányelv
egyéb elõírásainak.
Malti (Maltese) Hawnhekk, Zyxel, jiddikjara li dan tagħmir jikkonforma mal-ħtiġijiet essenzjali u ma provvedimenti oħrajn relevanti li hemm
fid-Dirrettiva 1999/5/EC.
Nederlands
(Dutch)
Hierbij verklaart Zyxel dat het toestel uitrusting in overeenstemming is met de essentiële eisen en de andere relevante
bepalingen van richtlijn 1999/5/EC.
Polski (Polish) Niniejszym Zyxel oświadcza, że sprzęt jest zgodny z zasadniczymi wymogami oraz pozostałymi stosownymi postanowieniami
Dyrektywy 1999/5/EC.
Português
(Portuguese)
Zyxel declara que este equipamento está conforme com os requisitos essenciais e outras disposições da Directiva 1999/5/
EC.
Română
(Romanian)
Prin prezenta, Zyxel declară că acest echipament este în conformitate cu cerinţele esenţiale şi alte prevederi relevante ale
Directivei 1999/5/EC.
Slovenčina
(Slovak)
Zyxel týmto vyhlasuje, že zariadenia spĺňa základné požiadavky a všetky príslušné ustanovenia Smernice 1999/5/EC.
Slovenščina
(Slovene)
Zyxel izjavlja, da je ta oprema v skladu z bistvenimi zahtevami in ostalimi relevantnimi določili direktive 1999/5/EC.
Suomi (Finnish) Zyxel vakuuttaa täten että laitteet tyyppinen laite on direktiivin 1999/5/EY oleellisten vaatimusten ja sitä koskevien direktiivin
muiden ehtojen mukainen.
Svenska
(Swedish)
Härmed intygar Zyxel att denna utrustning står I överensstämmelse med de väsentliga egenskapskrav och övriga relevanta
bestämmelser som framgår av direktiv 1999/5/EC.
Norsk
(Norwegian)
Erklærer herved Zyxel at dette utstyret er I samsvar med de grunnleggende kravene og andre relevante bestemmelser I
direktiv 1999/5/EF.
Appendix B Legal Information
USG/ZyWALL User’s Guide
964
Notes:
1. Although Norway, Switzerland and Liechtenstein are not EU member states, the EU Directive 1999/5/EC has also been implemented in
those countries.
2. The regulatory limits for maximum output power are specified in EIRP. The EIRP level (in dBm) of a device can be calculated by adding the
gain of the antenna used (specified in dBi) to the output power available at the connector (specified in dBm).
List of national codes
Safety Warnings
• Do not use this product near water, for example, in a wet basement or near a swimming pool.
• Do not expose your device to dampness, dust or corrosive liquids.
• Do not store things on the device.
• Do not obstruct the device ventilation slots as insufficient airflow may harm your device. For example, do not place the device in an
enclosed space such as a box or on a very soft surface such as a bed or sofa.
• Do not install, use, or service this device during a thunderstorm. There is a remote risk of electric shock from lightning.
• Connect ONLY suitable accessories to the device.
• Do not open the device or unit. Opening or removing covers can expose you to dangerous high voltage points or other risks. ONLY qualified
service personnel should service or disassemble this device. Please contact your vendor for further information.
• Make sure to connect the cables to the correct ports.
• Place connecting cables carefully so that no one will step on them or stumble over them.
• Always disconnect all cables from this device before servicing or disassembling.
• Do not remove the plug and connect it to a power outlet by itself; always attach the plug to the power adaptor first before connecting it to
a power outlet.
• Do not allow anything to rest on the power adaptor or cord and do NOT place the product where anyone can walk on the power adaptor
or cord.
• Please use the provided or designated connection cables/power cables/ adaptors. Connect it to the right supply voltage (for example,
110V AC in North America or 230V AC in Europe). If the power adaptor or cord is damaged, it might cause electrocution. Remove it from the
device and the power source, repairing the power adapter or cord is prohibited. Contact your local vendor to order a new one.
• Do not use the device outside, and make sure all the connections are indoors. There is a remote risk of electric shock from lightning.
• CAUTION: Risk of explosion if battery is replaced by an incorrect type, dispose of used batteries according to the instruction. Dispose them at
the applicable collection point for the recycling of electrical and electronic devices. For detailed information about recycling of this
product, please contact your local city office, your household waste disposal service or the store where you purchased the product.
• The following warning statements apply, where the disconnect device is not incorporated in the device or where the plug on the power
supply cord is intended to serve as the disconnect device,
- For permanently connected devices, a readily accessible disconnect device shall be incorporated external to the device;
- For pluggable devices, the socket-outlet shall be installed near the device and shall be easily accessible.
Environment Statement
ErP (Energy-related Products)
Zyxel products put on the EU market in compliance with the requirement of the European Parliament and the Council published Directive 2009/
125/EC establishing a framework for the setting of ecodesign requirements for energy-related products (recast), so called as "ErP Directive
(Energy-related Products directive) as well as ecodesign requirement laid down in applicable implementing measures, power consumption has
satisfied regulation requirements which are:
• Network standby power consumption < 8W, and/or
• Off mode power consumption < 0.5W, and/or
• Standby mode power consumption < 0.5W.
COUNTRY ISO 3166 2 LETTER CODE COUNTRY ISO 3166 2 LETTER CODE
Austria AT Liechtenstein LI
Belgium BE Lithuania LT
Bulgaria BG Luxembourg LU
Croatia HR Malta MT
Cyprus CY Netherlands NL
Czech Republic CZ Norway NO
Denmark DK Poland PL
Estonia EE Portugal PT
Finland FI Romania RO
France FR Serbia RS
Germany DE Slovakia SK
Greece GR Slovenia SI
Hungary HU Spain ES
Iceland IS Switzerland CH
Ireland IE Sweden SE
Italy IT Turkey TR
Latvia LV United Kingdom GB
Appendix B Legal Information
USG/ZyWALL User’s Guide
965
(Wireless setting, please refer to "Wireless" chapter for more detail.)
European Union - Disposal and Recycling Information
The symbol below means that according to local regulations your product and/or its battery shall be disposed of separately from domestic
waste. If this product is end of life, take it to a recycling station designated by local authorities. At the time of disposal, the separate collection of
your product and/or its battery will help save natural resources and ensure that the environment is sustainable development.
Die folgende Symbol bedeutet, dass Ihr Produkt und/oder seine Batterie gemäß den örtlichen Bestimmungen getrennt vom Hausmüll entsorgt
werden muss. Wenden Sie sich an eine Recyclingstation, wenn dieses Produkt das Ende seiner Lebensdauer erreicht hat. Zum Zeitpunkt der
Entsorgung wird die getrennte Sammlung von Produkt und/oder seiner Batterie dazu beitragen, natürliche Ressourcen zu sparen und die Umwelt
und die menschliche Gesundheit zu schützen.
El símbolo de abajo indica que según las regulaciones locales, su producto y/o su batería deberán depositarse como basura separada de la
doméstica. Cuando este producto alcance el final de su vida útil, llévelo a un punto limpio. Cuando llegue el momento de desechar el
producto, la recogida por separado éste y/o su batería ayudará a salvar los recursos naturales y a proteger la salud humana y
medioambiental.
Le symbole ci-dessous signifie que selon les réglementations locales votre produit et/ou sa batterie doivent être éliminés séparément des ordures
ménagères. Lorsque ce produit atteint sa fin de vie, amenez-le à un centre de recyclage. Au moment de la mise au rebut, la collecte séparée
de votre produit et/ou de sa batterie aidera à économiser les ressources naturelles et protéger l'environnement et la santé humaine.
Il simbolo sotto significa che secondo i regolamenti locali il vostro prodotto e/o batteria deve essere smaltito separatamente dai rifiuti domestici.
Quando questo prodotto raggiunge la fine della vita di servizio portarlo a una stazione di riciclaggio. Al momento dello smaltimento, la raccolta
separata del vostro prodotto e/o della sua batteria aiuta a risparmiare risorse naturali e a proteggere l'ambiente e la salute umana.
Symbolen innebär att enligt lokal lagstiftning ska produkten och/eller dess batteri kastas separat från hushållsavfallet. När den här produkten når
slutet av sin livslängd ska du ta den till en återvinningsstation. Vid tiden för kasseringen bidrar du till en bättre miljö och mänsklig hälsa genom att
göra dig av med den på ett återvinningsställe.
Appendix B Legal Information
USG/ZyWALL User’s Guide
966
Environmental Product Declaration

Appendix B Legal Information
USG/ZyWALL User’s Guide
967
台灣
以下訊息僅適用於產品具有無線功能且銷售至台灣地區
• 第十二條 經型式認證合格之低功率射頻電機,非經許可,公司,商號或使用者均不得擅自變更頻率、加大功率或變更原設計之特性及功能。
• 第十四條 低功率射頻電機之使用不得影響飛航安全及干擾合法通信;經發現有干擾現象時,應立即停用,並改善至無干擾時方得繼續使用。
前項合法通信,指依電信法規定作業之無線電通信。 低功率射頻電機須忍受合法通信或工業、科學及醫療用電波輻射性電機設備之干擾。
• 電磁波曝露量 MPE 標準值 1mW/cm2,送測產品實測值為:0.918 mW/cm2(USG20W-VPN); 本產品使用時建議應距離人體 20 cm
• 無線資訊傳輸設備忍受合法通信之干擾且不得干擾合法通信;如造成干擾,應立即停用, 俟無干擾之虞,始得繼續使用。
• 無線資訊傳設備的製造廠商應確保頻率穩定性,如依製造廠商使用手冊上所述正常操作, 發射的信號應維持於操作頻帶中
以下訊息僅適用於產品操作於 5.25-5.35 秭赫頻帶內並銷售至台灣地區
• 在 5.25-5.35 秭赫頻帶內操作之無線資訊傳輸設備,限於室內使用。
以下訊息僅適用於產品屬於專業安裝並銷售至台灣地區
• 本器材須經專業工程人員安裝及設定,始得設置使用,且不得直接販售給一般消費者。
安全警告 - 為了您的安全,請先閱讀以下警告及指示 :
• 請勿將此產品接近水、火焰或放置在高溫的環境。
• 避免設備接觸 :
- 任何液體 - 切勿讓設備接觸水、雨水、高濕度、污水腐蝕性的液體或其他水份。
- 灰塵及污物 - 切勿接觸灰塵、污物、沙土、食物或其他不合適的材料。
• 雷雨天氣時,不要安裝,使用或維修此設備。有遭受電擊的風險。
• 切勿重摔或撞擊設備,並勿使用不正確的電源變壓器。
• 若接上不正確的電源變壓器會有爆炸的風險。
• 請勿隨意更換產品內的電池。
• 如果更換不正確之電池型式,會有爆炸的風險,請依製造商說明書處理使用過之電池。
• 請將廢電池丟棄在適當的電器或電子設備回收處。
• 請勿將設備解體。
• 請勿阻礙設備的散熱孔,空氣對流不足將會造成設備損害。
• 請插在正確的電壓供給插座 ( 如 : 北美 / 台灣電壓 110V AC,歐洲是 230V AC)。
• 假若電源變壓器或電源變壓器的纜線損壞,請從插座拔除,若您還繼續插電使用,會有觸電死亡的風險。
• 請勿試圖修理電源變壓器或電源變壓器的纜線,若有毀損,請直接聯絡您購買的店家,購買一個新的電源變壓器。
• 請勿將此設備安裝於室外,此設備僅適合放置於室內。
• 請勿隨一般垃圾丟棄。
• 請參閱產品背貼上的設備額定功率。
• 請參考產品型錄或是彩盒上的作業溫度。
• 產品沒有斷電裝置或者採用電源線的插頭視為斷電裝置的一部分,以下警語將適用 :
- 對永久連接之設備, 在設備外部須安裝可觸及之斷電裝置;
- 對插接式之設備, 插座必須接近安裝之地點而且是易於觸及的。
About the Symbols
Various symbols are used in this product to ensure correct usage, to prevent danger to the user and others, and to prevent property damage.
The meaning of these symbols are described below. It is important that you read these descriptions thoroughly and fully understand the
contents.
Appendix B Legal Information
USG/ZyWALL User’s Guide
968
Explanation of the Symbols
Viewing Certifications
Go to http://www.zyxel.com to view this product’s documentation and certifications.
Zyxel Limited Warranty
Zyxel warrants to the original end user (purchaser) that this product is free from any defects in material or workmanship for a specific period (the
Warranty Period) from the date of purchase. The Warranty Period varies by region. Check with your vendor and/or the authorized Zyxel local
distributor for details about the Warranty Period of this product. During the warranty period, and upon proof of purchase, should the product
have indications of failure due to faulty workmanship and/or materials, Zyxel will, at its discretion, repair or replace the defective products or
components without charge for either parts or labor, and to whatever extent it shall deem necessary to restore the product or components to
proper operating condition. Any replacement will consist of a new or re-manufactured functionally equivalent product of equal or higher value,
and will be solely at the discretion of Zyxel. This warranty shall not apply if the product has been modified, misused, tampered with, damaged by
an act of God, or subjected to abnormal working conditions.
Note
Repair or replacement, as provided under this warranty, is the exclusive remedy of the purchaser. This warranty is in lieu of all other warranties,
express or implied, including any implied warranty of merchantability or fitness for a particular use or purpose. Zyxel shall in no event be held
liable for indirect or consequential damages of any kind to the purchaser.
To obtain the services of this warranty, contact your vendor. You may also refer to the warranty policy for the region in which you bought the
device at http://www.zyxel.com/web/support_warranty_info.php.
Registration
Register your product online to receive e-mail notices of firmware upgrades and information at www.zyxel.com for global products, or at
www.us.zyxel.com for North American products.
Open Source Licenses
This product contains in part some free software distributed under GPL license terms and/or GPL like licenses. Open source licenses are provided
with the firmware package. You can download the latest firmware at www.zyxel.com. To obtain the source code covered under those Licenses,
please contact support@zyxel.com.tw to get it.
SYMBOL EXPLANATION
Alternating current (AC):
AC is an electric current in which the flow of electric charge periodically reverses direction.
Direct current (DC):
DC if the unidirectional flow or movement of electric charge carriers.
Earth; ground:
A wiring terminal intended for connection of a Protective Earthing Conductor.
Class II equipment:
The method of protection against electric shock in the case of class II equipment is either double insulation or
reinforced insulation.
USG/ZyWALL User’s Guide
969
APPENDIX C
Product Features
Please refer to the product datasheet for the latest product features.
Table 396 Product Features 1
MODEL
NAME USG40 USG40W USG60 USG60W ZYWALL
110 USG110 USG210 ZYWALL
310 USG310 ZYWALL
1100 USG1100 USG1900
# of MAC56687778888 8
Interface
VLAN 8 8 16 16 16 16 32 64 64 128 128 128
Virtual
(alias) per
interface
4 4 4 4 4 4 4 4 4 4 4 4
PPP (system
default)
22223338888 8
PPP (user
create)
22444481616323232
Bridge22448881616161616
Tunnel
(GRE/IPv6
Transition)
44444444444 4
Routing
Static route 64 64 128 128 128 128 256 256 256 512 512 512
Policy route 100 100 200 200 500 500 500 1000 1000 1000 1000 2000
Sessions
(Forwarding
, NAT/
firewall)
50000 50000 100000 100000 150000 150000 200000 500000 500000 1000000 1000000 1000000
Reserved
Sessions For
Managed
Devices
500 500 500 500 500 500 500 500 500 500 500 500
NAT
Max. Virtual
Server
Number
128 128 256 256 256 256 512 1024 1024 1024 1024 1024
Firewall
(Security
policy)
Max
Firewall ACL
Rule
Number =
Secure
Policy
Number
500 500 500 500 500 500 500 2000 2000 5000 5000 10000
Max Session
Limit per
Host Rules
1000 1000 1000 1000 1000 1000 1000 1000 1000 1000 1000 1000
Appendix C Product Features
USG/ZyWALL User’s Guide
970
ADP
Max. ADP
Profile
Number
88888881616161632
Max. ADP
Rule
Number
32 32 32 32 32 32 32 32 32 32 32 32
Application
Patrol
Max. App
patrol
Profile
32 32 32 32 32 32 32 64 64 64 64 64
Max
Application
Object In
Each Profile
(Object +
Object
Group)
32 32 32 32 32 32 32 32 32 32 32 32
User Profile
Max. Local
User
64 64 128 128 128 128 128 256 256 512 512 1024
Max. Admin
User
555555555101010
Max. User
Group.
16 16 32 32 32 32 32 64 64 128 128 256
Max User In
One User
Group
64 64 128 128 128 128 128 256 256 512 512 1024
Max.
Concurrent
Device
Upgrade
64 64 128 128 200 to
300
(Extend
by
license)
200 to
300
(Extend
by
license)
200 to
300
(Extend
by
license)
500 to
800
(Extend
by
license)
500 to
800
(Extend
by
license)
800 to
1500
(Extend
by
license)
800 to
1500
(Extend
by
license)
1500 to
2000
(Extend
by
license)
HTTPd
Max. HTTPd
(Hypertext
Transfer
Protocol
daemon)
128 128 128 128 256 256 256 512 512 512 512 1024
Objects
Address
Object
300 300 300 300 300 300 500 1000 1000 2000 2000 2000
Address
Group
25 25 50 50 50 50 100 200 200 400 400 400
Max.
Address
Object In
One Group
64 64 128 128 128 128 128 128 128 256 256 256
Service
Object
200 200 200 200 500 500 500 1000 1000 1000 1000 1000
Service
Group
50 50 50 50 100 100 100 200 200 200 200 200
Table 396 Product Features 1 (continued)
MODEL
NAME USG40 USG40W USG60 USG60W ZYWALL
110 USG110 USG210 ZYWALL
310 USG310 ZYWALL
1100 USG1100 USG1900
Appendix C Product Features
USG/ZyWALL User’s Guide
971
Max.
Service
Object In
One Group
64 64 128 128 128 128 128 128 128 256 256 256
Schedule
Object
32 32 32 32 32 32 32 32 32 32 32 32
Schedule
Group
16 16 16 16 16 16 16 16 16 16 16 16
Max.
Schedule
Object In
One Group
24 24 24 24 24 24 24 24 24 24 24 24
Application
Object
500 500 500 500 500 500 500 1000 1000 1000 1000 1000
Application
Group
100 100 100 100 100 100 100 200 200 200 200 200
Max.
Application
Object In
One Group
128 128 128 128 128 128 128 128 128 256 256 256
ISP Account 16(PPP+
3G)
16(PPP+
3G)
16(PPP+
3G)
16(PPP+
3G)
16(PPP+
3G)
16(PPP+
3G)
16(PPP+
3G)
32(PPP+
3G)
32(PPP+
3G)
32(PPP+
3G)
128(PPP
+3G)
128(PPP
+3G)
Max. LDAP
Server
Object #
22228881616161616
Max. Radius
Server
Object #
22228881616161616
Max. AD
Server
Object #
44448881616161616
Max. Zone
Number
(System
Default)
88888888888 8
Max. Zone
Number
(User
Define)
8 8 16 16 16 16 16 16 16 32 32 32
Max. Trunk
Number
(System
Default)
11111111111 1
Max. Trunk
Number
(User
Define)
44444481616323232
Max Radio
Profile
16 16 16 16 16 16 16 16 16 16 16 16
Max SSID
Profile
32 32 32 32 32 32 32 32 32 128 128 128
Max
Security
Profile
32 32 32 32 32 32 32 32 32 32 32 32
Max
Macfilter
Profile
32 32 32 32 32 32 32 32 32 32 32 32
Table 396 Product Features 1 (continued)
MODEL
NAME USG40 USG40W USG60 USG60W ZYWALL
110 USG110 USG210 ZYWALL
310 USG310 ZYWALL
1100 USG1100 USG1900
Appendix C Product Features
USG/ZyWALL User’s Guide
972
Max MAC
Entry Per
Macfilter
Profile
512 512 512 512 512 512 512 512 512 512 512 512
VPN
Max. VPN
Tunnels
Number
20 20 40 40 100 100 200 300 300 1000 1000 2000
Max. VPN
Concentrat
or Number
22222221616323264
Max. VPN
Configurati
on Provision
Rule
Number
20 20 40 40 100 100 200 300 300 1000 1000 2000
Certificate
Certificate
Buffer Size
128k 128k 128k 128k 256k 256k 256k 512k 512k 512k 512k 1024k
Built-in
service
A record 32 32 64 64 64 64 64 128 128 128 128 128
NS record
(DNS
Domain
Zone
Forward)
8 8 8 8 16 16 16 16 16 16 16 16
MX record44888881616161616
Max Service
Control
Entries
16 per
service
16 per
service
16 per
service
16 per
service
16 per
service
16 per
service
16 per
service
32 per
service
32 per
service
32 per
service
32 per
service
32 per
service
Max. Dhcp
Network
Pool
vlan+br
g+ether
net
vlan+br
g+ether
net
vlan+br
g+ether
net
vlan+br
g+ether
net
vlan+br
g+ether
net
vlan+br
g+ether
net
vlan+br
g+ether
net
vlan+br
g+ether
net
vlan+br
g+ether
net
vlan+br
g+ether
net
vlan+br
g+ether
net
vlan+br
g+ether
net
Max. DHCP
Host Pool
(Static
Dhcp)
64 64 96 96 256 256 256 512 512 1024 1024 1024
Max. DHCP
Extended
Options
10 10 10 10 15 15 15 30 30 30 30 30
Max DDNS
Profiles
5 5 10 10 10 10 10 10 10 10 10 10
DHCP Relay 2 per
interfac
e
2 per
interfac
e
2 per
interfac
e
2 per
interfac
e
2 per
interfac
e
2 per
interfac
e
2 per
interfac
e
2 per
interfac
e
2 per
interfac
e
2 per
interfac
e
2 per
interfac
e
2 per
interfac
e
USB Storage
Device
Number
11222222222 2
Centralized
Log
Log Entries 512 512 512 512 1024 1024 1024 1024 1024 2048 2048 2048
Table 396 Product Features 1 (continued)
MODEL
NAME USG40 USG40W USG60 USG60W ZYWALL
110 USG110 USG210 ZYWALL
310 USG310 ZYWALL
1100 USG1100 USG1900
Appendix C Product Features
USG/ZyWALL User’s Guide
973
Debug Log
Entries
1024 1024 1024 1024 1024 1024 1024 1024 1024 1024 1024 1024
Admin E-
mail
Address
22222222222 2
Syslog
Server
44444444444 4
IDP
Max. IDP
Profile
Number
88888881616161632
Max.
Custom
Signatures
32 32 32 32 32 32 32 256 256 512 512 512
SSL
Inspection
Max. SSL
Inspection
Profile
n/a n/a n/a n/a 8 8 8 16 16 16 16 16
Max.
Exclude List
n/a n/a n/a n/a 256 256 256 256 256 256 256 256
Content
Filtering
Max.
Number Of
Content
Filter Policy
16 16 16 16 16 16 16 32 32 64 64 128
Forbidden
Domain
Entry
Number
256 per
profile
256 per
profile
256 per
profile
256 per
profile
256 per
profile
256 per
profile
256 per
profile
512 per
profile
512 per
profile
512 per
profile
512 per
profile
512 per
profile
Trusted
Domain
Entry
Number
256 per
profile
256 per
profile
256 per
profile
256 per
profile
256 per
profile
256 per
profile
256 per
profile
512 per
profile
512 per
profile
512 per
profile
512 per
profile
512 per
profile
Keyword
Blocking
Number
128 per
profile
128 per
profile
128 per
profile
128 per
profile
128 per
profile
128 per
profile
128 per
profile
256 per
profile
256 per
profile
256 per
profile
256 per
profile
256 per
profile
Common
Forbidden
Domain
Entry
Number
1024 1024 1024 1024 1024 1024 1024 1024 1024 1024 1024 1024
Common
Trusted
Domain
Entry
Number
1024 1024 1024 1024 1024 1024 1024 1024 1024 1024 1024 1024
Anti-Spam
Maximum
AS Rule
Number
(Profile)
16 16 16 16 32 32 32 64 64 64 64 64
Table 396 Product Features 1 (continued)
MODEL
NAME USG40 USG40W USG60 USG60W ZYWALL
110 USG110 USG210 ZYWALL
310 USG310 ZYWALL
1100 USG1100 USG1900
Appendix C Product Features
USG/ZyWALL User’s Guide
974
Maximum
White List
Rule
Support
128 128 128 128 128 128 128 256 256 256 256 256
Maximum
Black List
Rule
Support
128 128 128 128 128 128 128 256 256 256 256 256
Maximum
DNSBL
Domain
Support
55555551010101010
Max.
Statistics
Number
500 500 500 500 500 500 500 500 500 500 500 500
Max.
Statistics
Ranking
10 10 10 10 10 10 10 10 10 10 10 10
Anti-Virus
Max. AV
Rule
(Profile)
16 16 16 16 16 16 16 32 32 32 32 32
Max.
Statistics
Number
500 500 500 500 500 500 500 500 500 500 500 500
Max.
Statistics
Ranking
10 10 10 10 10 10 10 10 10 10 10 10
MyZyxel.co
m
SKU update
interval
(day)
2 ~ 6 hrs 2 ~ 6 hrs 2 ~ 6 hrs 2 ~ 6 hrs 2 ~ 6 hrs 2 ~ 6 hrs 2 ~ 6 hrs 2 ~ 6 hrs 2 ~ 6 hrs 2 ~ 6 hrs 2 ~ 6 hrs 2 ~ 6 hrs
SSL VPN
Default SSL
VPN
Connection
s
5 5 5 5 25 25 35 50 50 250 250 250
Maximum
SSL VPN
Connection
s
15 15 20 20 150 150 150 150 150 500 500 750
Max. SSL
VPN
Network List
88888888888 8
SSL VPN
Max Policy
16 16 16 16 16 16 16 16 16 16 16 16
AP
controller
Default #
Of Control
AP
22222222222 2
Max. # Of
Control AP
18 18 18 18 34 34 34 34 34 66 66 66
Table 396 Product Features 1 (continued)
MODEL
NAME USG40 USG40W USG60 USG60W ZYWALL
110 USG110 USG210 ZYWALL
310 USG310 ZYWALL
1100 USG1100 USG1900
Appendix C Product Features
USG/ZyWALL User’s Guide
975
The following table is for the USG-VPN models.
Others
Device HA
VRRP
Group
n/a n/a n/a n/a 32 32 32 32 32 32 32 32
Max OSPF
Areas
32 32 32 32 32 32 32 32 32 32 32 32
BWM
Maximum
BWM Rule
Number
128 128 128 128 256 256 256 512 512 1024 1024 1024
SIP
Maximum
SIP
Concurrent
Call
50 50 50 50 100 100 100 100 100 200 200 200
Custom
Web Portal
Page
Max
internal
Web Portal
Customize
File
44444444444 4
Upload Zip
File Size
Up to
2MB
Up to
2MB
Up to
2MB
Up to
2MB
Up to
2MB
Up to
2MB
Up to
2MB
Up to
2MB
Up to
2MB
Up to
2MB
Up to
2MB
Up to
2MB
Unzip File
Size
Up to
5MB
Up to
5MB
Up to
5MB
Up to
5MB
Up to
5MB
Up to
5MB
Up to
5MB
Up to
5MB
Up to
5MB
Up to
5MB
Up to
5MB
Up to
5MB
Hotspot
Manageme
nt
Max
Dynamic
Account
List
n/a n/a n/a n/a 2000 2000 2000 2000 2000 3000 3000 4000
Hotspot
Support
n/an/an/an/an/aProject-
based
Project-
based
Project-
based
Yes Yes Yes Yes
Walled
Garden -
URL Base
n/a n/a n/a n/a 50 50 50 50 50 50 50 50
Walled
Garden -
Domain/IP
base
n/a n/a n/a n/a 50 50 50 50 50 50 50 50
Advertisem
ent
n/a n/a n/a n/a 20 20 20 20 20 20 20 20
Table 396 Product Features 1 (continued)
MODEL
NAME USG40 USG40W USG60 USG60W ZYWALL
110 USG110 USG210 ZYWALL
310 USG310 ZYWALL
1100 USG1100 USG1900
Table 397 Product Features 2
MODEL NAME USG20-VPN USG20W-VPN USG2200-VPN
# of MAC 6 7 18
Interface
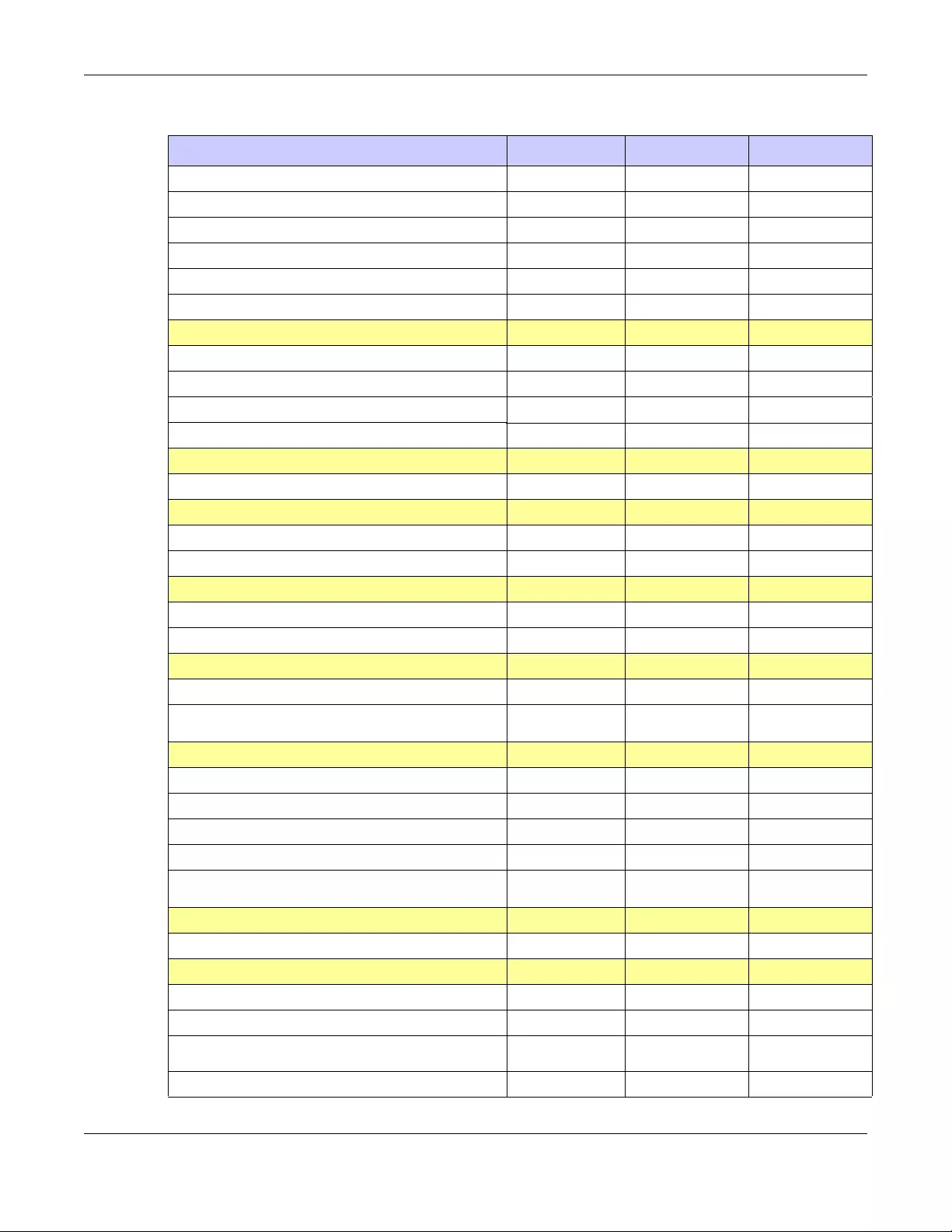
Appendix C Product Features
USG/ZyWALL User’s Guide
976
VLAN 8 8 128
Virtual (alias) per interface 4 4 4
PPP (system default) 2 2 8
PPP (user create) 2 2 32
Bridge 2 2 16
Tunnel (GRE/IPv6 Transition) 4 4 4
Routing
Static route 64 64 1024
Policy route 100 100 4000
Sessions (Forwarding, NAT/firewall) 20000 20000 1500000
Reserved Sessions For Managed Devices 500 500 500
NAT
Max. Virtual Server Number 128 128 2048
Firewall (Security policy)
Max Firewall ACL Rule Number = Secure Policy Number 500 500 20000
Max Session Limit per Host Rules 1000 1000 1000
ADP
Max. ADP Profile Number n/a n/a 32
Max. ADP Rule Number n/a n/a 32
Application Patrol
Max. App patrol Profile n/a n/a 64
Max Application Object In Each Profile
(Object + Object Group)
n/a n/a 32
User Profile
Max. Local User 64 64 2000
Max. Admin User 5 5 10
Max. User Group. 16 16 256
Max User In One User Group 64 64 1024
Max concurrent device upgrade 64 64 2000 to 5000 (extend
by license)
HTTPd
Max. HTTPd (Hypertext Transfer Protocol daemon) 128 128 2048
Objects
Address Object 300 300 4000
Address Group 25 25 400
Max. Address Object In One Group 64 64 256
Service Object 200 200 1000
Table 397 Product Features 2 (continued)
MODEL NAME USG20-VPN USG20W-VPN USG2200-VPN
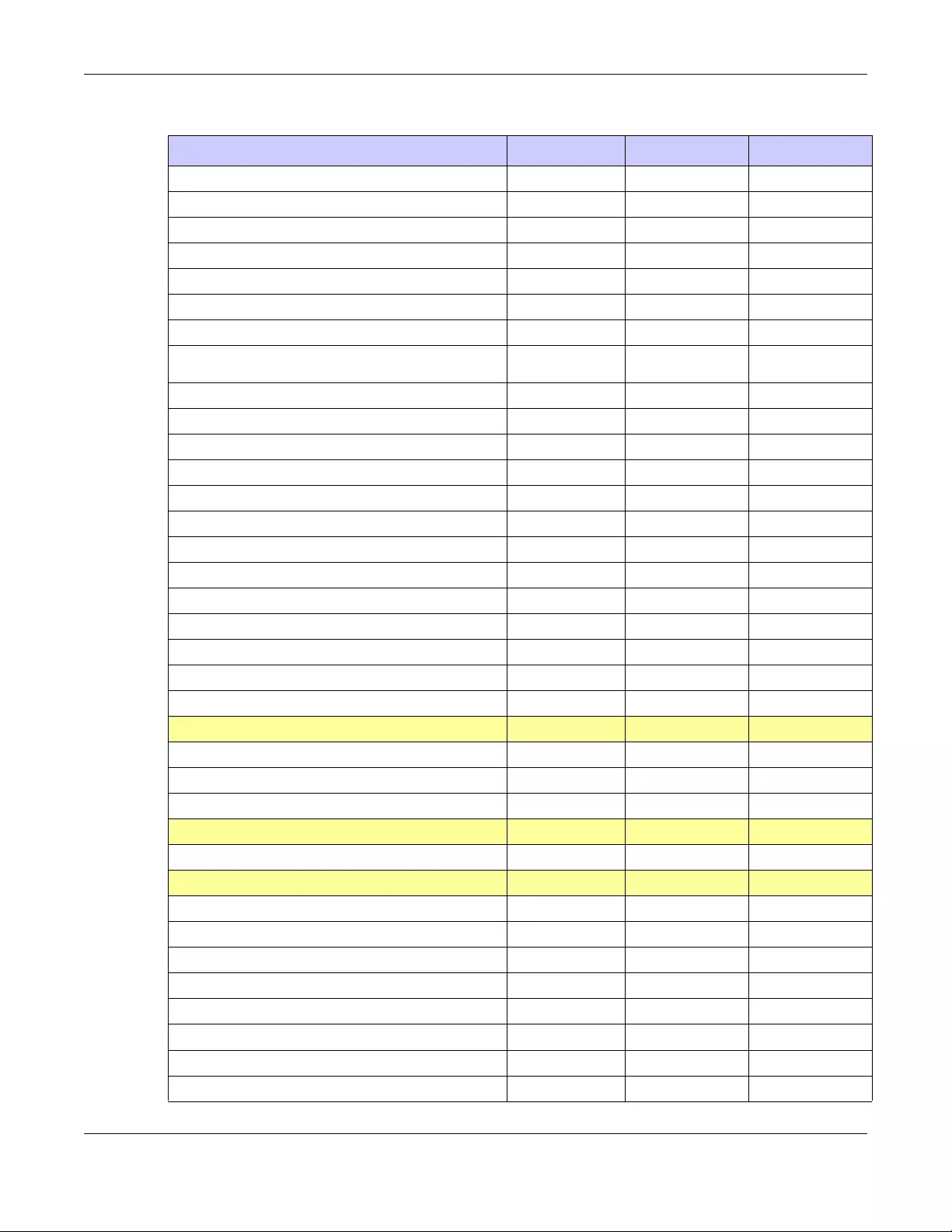
Appendix C Product Features
USG/ZyWALL User’s Guide
977
Service Group 50 50 200
Max. Service Object In One Group 64 64 256
Schedule Object 32 32 32
Schedule Group 16 16 16
Max. Schedule Object In One Group 24 24 24
Application Object n/a n/a 1000
Application Group n/a n/a 200
Max. Application Object In One Group n/a n/a 512
ISP Account 16(PPP+3G) 16(PPP+3G) 128(PPP+3G)
Max. LDAP Server Object # 2 2 16
Max. RADIUS Server Object # 2 2 16
Max. AD Server Object # 4 4 16
Max. Zone Number (System Default) 8 8 8
Max. Zone Number (User Define) 8 8 32
Max. Trunk Number (System Default) 1 1 1
Max. Trunk Number (User Define) 4 4 32
Max Radio Profile 16 16 16
Max SSID Profile 32 32 128
Max Security Profile 32 32 32
Max Macfilter Profile 32 32 32
Max MAC Entry Per Macfilter Profile 512 512 512
VPN
Max. VPN Tunnels Number 10 10 3000
Max. VPN Concentrator Number 2 2 128
Max. VPN Configuration Provision Rule Number 10 10 3000
Certificate
Certificate Buffer Size 128k 128k 1024k
Built-in service
A record 32 32 128
NS record (DNS Domain Zone Forward) 8 8 16
MX record 4 4 16
Max Service Control Entries 16 per service 16 per service 32 per service
Max. DHCP Network Pool vlan+brg+ethernet vlan+brg+ethernet vlan+brg+ethernet
Max. DHCP Host Pool(Static DHCP) 64 64 1024
Max. DHCP Extended Options 10 10 30
Max DDNS Profiles 5 5 10
Table 397 Product Features 2 (continued)
MODEL NAME USG20-VPN USG20W-VPN USG2200-VPN
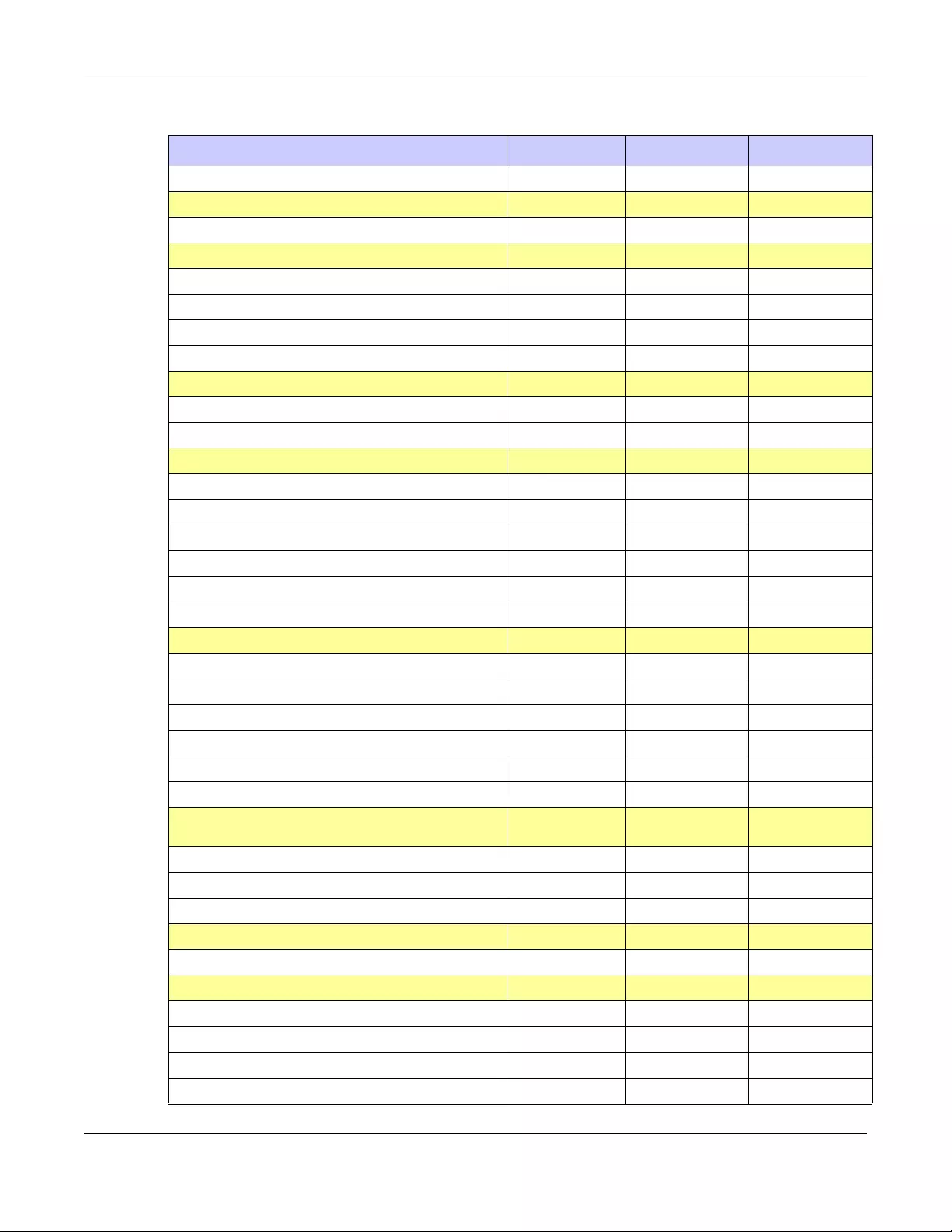
Appendix C Product Features
USG/ZyWALL User’s Guide
978
DHCP Relay 2 per interface 2 per interface 2 per interface
USB Storage
Device Number 1 1 2
Centralized Log
Log Entries 512 512 2048
Debug Log Entries 1024 1024 1024
Admin E-mail Address 2 2 2
Syslog Server 4 4 4
SSL Inspection
Max. SSL Inspection Profile n/a n/a 16
Max. Exclude List n/a n/a 256
Content Filtering
Max. Number of Content Filter Policy 16 16 128
Forbidden Domain Entry Number 256 per profile 256 per profile 512 per profile
Trusted Domain Entry Number 256 per profile 256 per profile 512 per profile
Keyword Blocking Number 128 per profile 128 per profile 256 per profile
Common Forbidden Domain Entry Number 1024 1024 1024
Common Trusted Domain Entry Number 1024 1024 1024
Anti-Spam
Maximum AS Rule Number (Profile) 16 16 64
Maximum White List Rule Support 128 128 256
Maximum Black List Rule Support 128 128 256
Maximum DNSBL Domain Support 5 5 10
Max. Statistics Number 500 500 500
Max. Statistics Ranking 10 10 10
Anti-Virus
Max. AV Rule (Profile) n/a n/a n/a
Max. Statistics Number n/a n/a 500
Max. Statistics Ranking n/a n/a 10
MyZyxel.com
SKU update interval (day) 2 ~ 6 hrs 2 ~ 6 hrs 2 ~ 6 hrs
SSL VPN
Default SSL VPN Connections 5 5 250
Maximum SSL VPN Connections 15 15 1000
Max. SSL VPN Network List 8 8 8
SSL VPN Max Policy 16 16 16
Table 397 Product Features 2 (continued)
MODEL NAME USG20-VPN USG20W-VPN USG2200-VPN
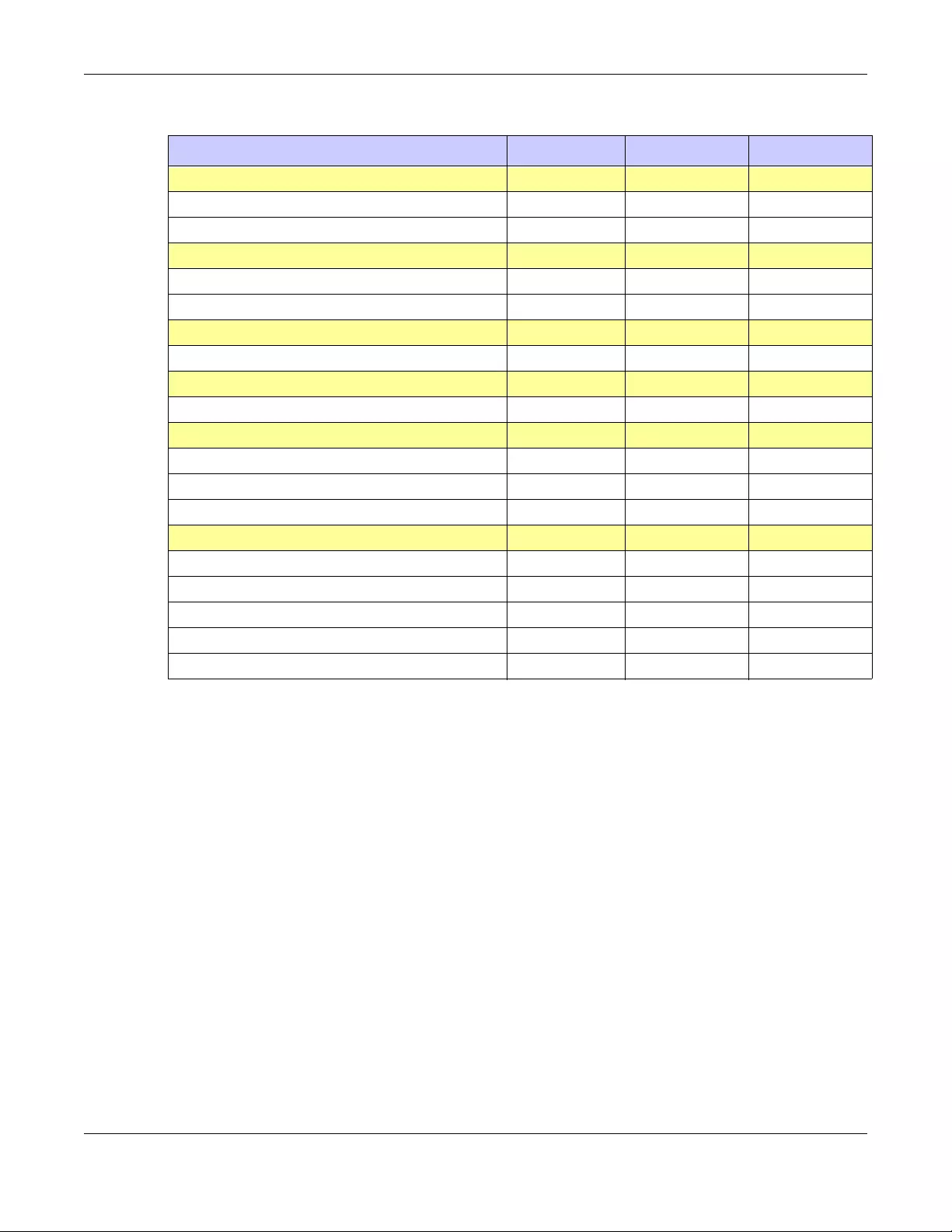
Appendix C Product Features
USG/ZyWALL User’s Guide
979
AP controller
Default # of Control AP n/a n/a 2
Max. # of Control AP n/a n/a 66
Others
Device HA VRRP Group n/a n/a 32
Max OSPF Areas 32 32 32
BWM
Maximum BWM Rule Number 128 128 2048
SIP
Maximum SIP Concurrent Call 50 50 200
Custom Web Portal Page
Max internal Web Portal Customize File 4 4 4
Upload Zip File Size Up to 2MB Up to 2MB Up to 2MB
Unzip File Size Up to 5MB Up to 5MB Up to 5MB
Hotspot Management
Max Dynamic Account List n/a n/a 6000
Hotspot Support n/a n/a Yes
Walled Garden - URL Base n/a n/a 50
Walled Garden - Domain/IP base n/a n/a 50
Advertisement n/a n/a 20
Table 397 Product Features 2 (continued)
MODEL NAME USG20-VPN USG20W-VPN USG2200-VPN

Index
USG/ZyWALL User’s Guide
980
Index
Symbols
Numbers
3322 Dynamic DNS 389
3DES 573
6in4 tunneling 314
6to4 tunneling 314
A
AAA
Base DN 796
Bind DN 796, 798
directory structure 795
Distinguished Name, see DN
DN 795, 796, 798
password 798
port 798, 800
search time limit 798
SSL 798
AAA server 793
AD 795
and users 737
directory service 793
LDAP 793, 795
local user database 795
RADIUS 794, 795, 799
RADIUS group 799
see also RADIUS
access 31
access control attacks 662
Access Point Name, see APN
access users 736, 738
custom page 853
forcing login 441
idle timeout 744
logging in 441
multiple logins 744
see also users 736
Web Configurator 746
access users, see also force user authentication
policies
account
user 736, 827
accounting server 793
Active Directory, see AD
active protocol 577
AH 577
and encapsulation 577
ESP 577
active sessions 179, 198
ActiveX 649
AD 793, 795, 796, 798
directory structure 795
Distinguished Name, see DN
password 798
port 798, 800
search time limit 798
SSL 798
address groups 775
and content filtering 635, 636
and FTP 872
and security policy 445
and SNMP 876
and SSH 868
and Telnet 871
and WWW 853
address objects 775
and content filtering 635, 636
and FTP 872
and NAT 375, 398
and policy routes 374
and security policy 445
and SNMP 876
and SSH 868
and Telnet 871
and VPN connections 550
and WWW 853
HOST 775

Index
USG/ZyWALL User’s Guide
981
RANGE 775
SUBNET 775
types of 775, 781
address record 841
admin user
troubleshooting 943
admin users 736
multiple logins 744
see also users 736
ADP 525
false negatives 527
false positives 527
inline profile 527
monitor profile 527
Advanced Encryption Standard, see AES
AES 573
AF 378
AH 556, 577
and transport mode 578
alerts 890, 891, 894, 897, 899, 900
anti-spam 694
anti-virus 684
IDP 659, 660, 711, 712
ALG 408, 414
and NAT 408, 410
and policy routes 410, 414
and security policy 408, 410
and trunks 414
FTP 408, 409
H.323 408, 409, 414
peer-to-peer calls 410
RTP 415
see also VoIP pass through 408
SIP 408, 409
Anomaly Detection and Prevention, see ADP
anti-spam 690, 694, 697
action for spam mails 695
alerts 694
and registration 693
black list 690, 694, 697
concurrent e-mail sessions 232, 692
DNSBL 691, 695, 702
e-mail header buffer 691
e-mail headers 691
excess e-mail sessions 692
general settings 692
identifying legitimate e-mail 690
identifying spam 690
log options 694
mail scan 695
mail sessions threshold 692
POP2 691
POP3 691
registration status 693
regular expressions 700
SMTP 691
status 232
white list 690, 694, 699, 700
anti-virus 134, 679, 680
alerts 684
black list 684, 685
boot sector virus 688
EICAR 682
e-mail virus 688
engines 680
file decompression 684
file infector virus 688
firmware package blocking 684
log options 684
macro virus 688
packet scan 680
packet types 680
polymorphic virus 688
registration status 683
scanner types 689
signatures 687
statistics 228
troubleshooting 935, 938
troubleshooting signatures update 935
updating signatures 245
virus 134, 680
virus types 688
white list 687
worm 134, 680
AP group 214, 253, 255
APN 309
Application Layer Gateway, see ALG
application patrol 629
actions 629
and HTTP redirect 403
and security policy 629
classification 629
exceptions 629
port-less 629
ports 630
service ports 630
troubleshooting 935, 940, 943

Index
USG/ZyWALL User’s Guide
982
troubleshooting signatures update 935
updating signatures 246
AppPatrol, see application patrol 246
ASAS (Authenex Strong Authentication System) 794
asymmetrical routes 519
allowing through the security policy 522
vs virtual interfaces 519
attacks
access control 662
backdoor 662
buffer overflow 662
Denial of Service (DoS) 554
DoS/DDoS 662
false negatives 657
false positives 657
IM 662
known 655
P2P 662
scan 663
severity of 660
spam 663
trapdoor 662
trojan 662
virus 134, 663, 680
worm 663
Authenex Strong Authentication System (ASAS) 794
authentication
in IPSec 557
LDAP/AD 795
server 793
authentication algorithms 388, 572, 573
and active protocol 572
and routing protocols 388
MD5 388, 573
SHA1 573
text 388
Authentication Header, see AH
authentication method objects 801
and users 737
and WWW 852
create 802
example 801
authentication policy
exceptional services 443
Authentication server
RADIUS client 879
authentication server 877
authentication type 143, 821
Authentication, Authorization, Accounting servers,
see AAA server
authorization server 793
auxiliary interfaces 270
B
backdoor attacks 662
backing up configuration files 904
bandwidth
egress 310, 319
ingress 310, 319
bandwidth limit
troubleshooting 937
bandwidth management 629
maximize bandwidth usage 378, 618
see also application patrol 629
troubleshooting 937
Base DN 796
base profiles
in IDP 656
Batch import 540
Bind DN 796, 798
BitTorrent 662
black list 694, 697
anti-spam 690
Blaster 676
bookmarks 597
boot sector virus 688
bridge interfaces 270, 334
and virtual interfaces of members 334
basic characteristics 270
effect on routing table 334
member interfaces 334
virtual 293
bridges 333
buffer overflow 662
buffer overflow attacks 662
C
CA
and certificates 805

Index
USG/ZyWALL User’s Guide
983
CA (Certificate Authority), see certificates
Calling Station ID 761
capturing packets 917
card SIM 310
CEF (Common Event Format) 887, 896
cellular 304
APN 309
interfaces 270
signal quality 206, 207
SIM card 310
status 208
system 206
troubleshooting 936, 937
certificate
troubleshooting 944
Certificate Authority (CA)
see certificates
Certificate Revocation List (CRL) 805
vs OCSP 819
certificates 804
advantages of 805
and CA 805
and FTP 872
and HTTPS 848
and IKE SA 577
and SSH 868
and synchronization (Device HA) 732
and VPN gateways 550
and WWW 850
certification path 805, 812, 817
expired 805
factory-default 805
file formats 805
fingerprints 813, 818
importing 808
in IPSec 563
not used for encryption 805
revoked 805
self-signed 805, 810
serial number 812, 817
storage space 808, 815
thumbprint algorithms 806
thumbprints 806
used for authentication 805
verifying fingerprints 806
certification requests 810
certifications 964
viewing 960, 968
Challenge Handshake Authentication Protocol
(CHAP) 821
CHAP (Challenge Handshake Authentication
Protocol) 821
CHAP/PAP 821
CLI 30, 36
button 36
messages 36
popup window 36
Reference Guide 2
client 605
cluster ID 724
commands 30
sent by Web Configurator 36
Common Event Format (CEF) 887, 896
compression (stac) 822
computer names 290, 331, 343, 350, 365, 612
computer virus 134, 680
infection and prevention 689
see also virus
concurrent e-mail sessions 232, 692
configuration
information 915
web-based SSL application example 823
configuration file
troubleshooting 945
configuration files 902
at restart 905
backing up 904
downloading 906, 924
downloading with FTP 871
editing 902
how applied 903
lastgood.conf 905, 907
managing 904
startup-config.conf 907
startup-config-bad.conf 905
syntax 903
system-default.conf 907
uploading 908
uploading with FTP 871
use without restart 902
connection
troubleshooting 940
connection monitor (in SSL) 222
connectivity check 289, 303, 310, 319, 330, 344, 351,
355, 557

Index
USG/ZyWALL User’s Guide
984
console port
speed 837
contact information 947, 969
content (pattern) 673
content filter
troubleshooting 935
content filtering 635, 636
and address groups 635, 636
and address objects 635, 636
and registration 638, 641
and schedules 635, 636
and user groups 635
and users 635
by category 635, 636, 642
by keyword (in URL) 636, 650
by URL 636, 649, 651, 652
by web feature 636, 649
cache 653
categories 642
category service 641
default policy 636
external web filtering service 641, 653
filter list 636
managed web pages 642
policies 635, 636
registration status 244, 638, 639, 641
statistics 225
testing 643
uncategorized pages 642
unsafe web pages 641
URL for blocked access 638
cookies 30, 649
copyright 953
CPU usage 179
current date/time 175, 833
and schedules 787
daylight savings 835
setting manually 836
time server 837
current user list 222
custom
access user page 853
login page 853
custom signatures 666, 669, 939
applying 675
example 673
verifying 675
custom.rules file 669, 939
customer support 947, 969
D
Data Encryption Standard, see DES
date 833
daylight savings 835
DDNS 389
backup mail exchanger 394
mail exchanger 394
service providers 389
troubleshooting 939
DDoS attacks 662
Dead Peer Detection, see DPD
decompression of files (in anti-virus) 684
default
security policy behavior 518
Default_L2TP_VPN_GW 610
Denial of Service (DoS) attacks 662
Denial of Service (Dos) attacks 554
DES 572
device access
troubleshooting 934
Device HA 718
management access 719
management IP address 719
monitored interfaces 728
device HA
active-passive mode 719, 724
cluster ID 724
copying configuration 719
device role 726
HA status 720
legacy mode 719
modes 719
monitored interfaces 724
password 728
synchronization 719, 732
synchronization password 728
synchronization port number 728
virtual router 721, 724
virtual router and management IP addresses 724
device High Availability see Device HA 718
DHCP 364, 832
and DNS servers 365

Index
USG/ZyWALL User’s Guide
985
and domain name 832
and interfaces 365
pool 365
static DHCP 365
DHCP Unique IDentifier 274
DHCPv6 827
DHCP Unique IDentifier 274
DHCPv6 Request 827
diagnostics 915
Differentiated Services Code Point (DSCP) 667
Diffie-Hellman key group 573
DiffServ 378
Digital Signature Algorithm public-key algorithm, see
DSA
direct routes 370
directory 793
directory service 793
file structure 795
disclaimer 953
Distinguished Name (DN) 795, 796, 798
Distributed Denial of Service (DDoS) attacks 662
DN 795, 796, 798
DNS 838
address records 841
domain name forwarders 843
domain name to IP address 841
IP address to domain name 842
L2TP VPN 612
Mail eXchange (MX) records 844
pointer (PTR) records 842
DNS Blacklist see DNSBL 691
DNS inbound LB 434
DNS servers 144, 838, 843
and interfaces 365
DNSBL 691, 695, 702
see also anti-spam 691
domain name 832
Domain Name System, see DNS
DoS (Denial of Service) attacks 662
DPD 565
DSA 810
DSCP 371, 374, 620, 929
DUID 274
Dynamic Domain Name System, see DDNS
dynamic guest 202
dynamic guest account 202, 737
Dynamic Host Configuration Protocol, see DHCP.
dynamic peers in IPSec 555
DynDNS 389
DynDNS see also DDNS 389
Dynu 389
E
e-Donkey 662
egress bandwidth 310, 319
EICAR 682
Ekahau RTLS 264
e-mail 690
daily statistics report 883
header buffer 691
headers 691
virus 688
e-Mule 662
Encapsulating Security Payload, see ESP
encapsulation
and active protocol 577
IPSec 556
transport mode 577
tunnel mode 577
VPN 577
encryption
and anti-virus 684
IPSec 557
RSA 812
encryption algorithms 572
3DES 573
AES 573
and active protocol 572
DES 572
encryption method 821
end of IP list 667
enforcing policies in IPSec 555
ESP 556, 577
and transport mode 578
Ethernet interfaces 270
and OSPF 278
and RIP 278
and routing protocols 276
basic characteristics 270

Index
USG/ZyWALL User’s Guide
986
virtual 293
exceptional services 443
extended authentication
and VPN gateways 550
IKE SA 576
Extended Service Set IDentification 750
ext-user
troubleshooting 943
F
false negatives 527, 657
false positives 527, 530, 657
file decompression (in anti-virus) 684
file extensions
configuration files 902
shell scripts 902
file infector 688
file manager 902
file sharing SSL application
create 825
Firefox 30
firewall
and SMTP redirect 404
firmware
and restart 908
current version 174, 911
getting updated 908
uploading 910
uploading with FTP 871
firmware package
troubleshooting 942
firmware upload
troubleshooting 945
flags 667
flash usage 179
forcing login 441
FQDN 841
fragmentation flag 671
fragmentation offset 671
free guest account 497
free time 497
configuration 497
enable 497
FTP 871
additional signaling port 413
ALG 408
and address groups 872
and address objects 872
and certificates 872
and zones 872
signaling port 413
troubleshooting 940
with Transport Layer Security (TLS) 872
full tunnel mode 581, 585
Fully-Qualified Domain Name, see FQDN
G
Generic Routing Encapsulation, see GRE.
global SSL setting 586
user portal logo 587
Grace Period 26
GRE 366
GSM 310
Guide
CLI Reference 2
Quick Start 2
H
H.323 414
additional signaling port 413
ALG 408, 414
and RTP 415
and security policy 409
signaling port 413
troubleshooting 940
HA status see device HA 720
header checksum 667
host-based intrusions 676
HSDPA 310
HTTP
over SSL, see HTTPS
redirect to HTTPS 851
vs HTTPS 848
HTTP redirect
and application patrol 403

Index
USG/ZyWALL User’s Guide
987
and interfaces 407
and policy routes 403, 404
and security policy 403
packet flow 403
troubleshooting 940
HTTPS 848
and certificates 848
authenticating clients 848
avoiding warning messages 859
example 858
vs HTTP 848
with Internet Explorer 858
with Netscape Navigator 858
hub-and-spoke VPN, see VPN concentrator
HyperText Transfer Protocol over Secure Socket Layer,
see HTTPS
I
ICMP 784
code 672
sequence number 672
type 672
identification (IP) 671
identifying
legitimate e-mail 690
spam 690
IDP 654
action 533, 659, 661, 712
alerts 659, 660, 711, 712
applying custom signatures 675
base profiles 656
custom signature example 673
custom signatures 666
false negatives 657
false positives 657
inline profile 657
log options 530, 534, 659, 660, 661, 711, 712
monitor profile 657
packet inspection profiles 657
packet inspection signatures 657
query view 659, 661
registration status 656
reject sender 533, 659, 661, 712
reject-both 533, 659, 661, 712
reject-receiver 533, 659, 661, 712
service group 663
severity 660
signature ID 661, 712
signatures 654
signatures and synchronization (Device HA) 732
Snort signatures 677
statistics 226
troubleshooting 935, 938
troubleshooting signatures update 935
updating signatures 246
verifying custom signatures 675
IEEE 802.1q VLAN
IEEE 802.1q. See VLAN.
IEEE 802.1x 750
IHL (IP Header Length) 667
IKE SA
aggressive mode 571, 575
and certificates 577
and RADIUS 576
and to-ZyWALL security policy 941
authentication algorithms 572, 573
content 574
Dead Peer Detection (DPD) 565
Diffie-Hellman key group 573
encryption algorithms 572
extended authentication 576
ID type 574
IP address, remote IPSec router 572
IP address, Zyxel device 572
local identity 574
main mode 571, 575
NAT traversal 576
negotiation mode 571
password 576
peer identity 574
pre-shared key 574
proposal 572
see also VPN
user name 576
IM (Instant Messenger) 662
IMAP 691
iMesh 662
inbound LB algorithm
least connection 436
least load 436
weighted round robin 436
inbound load balancing 434
time to live 437
incoming bandwidth 310, 319

Index
USG/ZyWALL User’s Guide
988
ingress bandwidth 310, 319
inline profile 527, 657
inspection signatures 655
installation
precautions 70
Instant Messenger (IM) 629, 662
managing 629
interface
status 193
troubleshooting 936
interfaces 269
and DNS servers 365
and HTTP redirect 407
and layer-3 virtualization 270
and NAT 398
and physical ports 270
and policy routes 374
and static routes 377
and VPN gateways 550
and zones 270
as DHCP relays 365
as DHCP servers 365, 832
auxiliary, see also auxiliary interfaces.
backup, see trunks
bandwidth management 361, 363, 364
bridge, see also bridge interfaces.
cellular 270
DHCP clients 364
Ethernet, see also Ethernet interfaces.
gateway 364
general characteristics 270
IP address 363
metric 364
MTU 364
overlapping IP address and subnet mask 364
port groups, see also port groups.
PPPoE/PPTP, see also PPPoE/PPTP interfaces.
prerequisites 271
relationships between 271
static DHCP 365
subnet mask 363
trunks, see also trunks.
Tunnel, see also Tunnel interfaces.
types 270
virtual, see also virtual interfaces.
VLAN, see also VLAN interfaces.
WLAN, see also WLAN interfaces.
Internet access
troubleshooting 934, 942
Internet Control Message Protocol, see ICMP
Internet Explorer 30
Internet Message Access Protocol, see IMAP 691
Internet Protocol (IP) 666
Internet Protocol Security, see IPSec
Internet Protocol version 6, see IPv6
Intrusion, Detection and Prevention see IDP 654
intrusions
host 676
network 676
IP (Internet Protocol) 666
IP options 667, 672
IP policy routing, see policy routes
IP pool 585
IP protocols 783
and service objects 784
ICMP, see ICMP
TCP, see TCP
UDP, see UDP
IP security option 667
IP static routes, see static routes
IP stream identifier 667
IP v4 packet headers 667
IP/MAC binding 425
exempt list 428
monitor 201
static DHCP 427
IPSec 137, 517, 545
active protocol 556
AH 556
and certificates 550
authentication 557
basic troubleshooting 941
certificates 563
connections 550
connectivity check 557
Default_L2TP_VPN_GW 610
encapsulation 556
encryption 557
ESP 556
established in two phases 547
L2TP VPN 609
local network 545
local policy 555
NetBIOS 554
peer 545
Perfect Forward Secrecy 557

Index
USG/ZyWALL User’s Guide
989
PFS 557
phase 2 settings 556
policy enforcement 555
remote access 555
remote IPSec router 545
remote network 545
remote policy 555
replay detection 554
SA life time 556
SA monitor 221
SA see also IPSec SA 577
see also VPN
site-to-site with dynamic peer 555
static site-to-site 555
transport encapsulation 556
tunnel encapsulation 556
VPN gateway 550
IPSec SA
active protocol 577
and security policy 941
and to-ZyWALL security policy 941
authentication algorithms 572, 573
destination NAT for inbound traffic 580
encapsulation 577
encryption algorithms 572
local policy 577
NAT for inbound traffic 579
NAT for outbound traffic 579
Perfect Forward Secrecy (PFS) 578
proposal 578
remote policy 577
search by name 221
search by policy 221
Security Parameter Index (SPI) (manual keys) 578
see also IPSec
see also VPN
source NAT for inbound traffic 579
source NAT for outbound traffic 579
status 221
transport mode 577
tunnel mode 577
when IKE SA is disconnected 577
IPSec VPN
troubleshooting 940
IPv6 272
link-local address 273
prefix 272
prefix delegation 273
prefix length 272
stateless autoconfiguration 273
IPv6 tunnelings
6in4 tunneling 314
6to4 tunneling 314
IPv6-in-IPv4 tunneling 314
ISP account
CHAP 821
CHAP/PAP 821
MPPE 821
MSCHAP 821
MSCHAP-V2 821
PAP 821
ISP accounts 819
and PPPoE/PPTP interfaces 298, 819
authentication type 821
encryption method 821
stac compression 822
J
Java 649
permissions 30
JavaScripts 30
K
key pairs 804
L
L2TP VPN 609
Default_L2TP_VPN_GW 610
DNS 612
IPSec configuration 609
policy routes 610
session monitor 223
WINS 612
lastgood.conf 905, 907
Layer 2 Tunneling Protocol Virtual Private Network, see
L2TP VPN 609
layer-2 isolation 430
example 430
IP 431

Index
USG/ZyWALL User’s Guide
990
LDAP 793
and users 737
Base DN 796
Bind DN 796, 798
directory 793
directory structure 795
Distinguished Name, see DN
DN 795, 796, 798
password 798
port 798, 800
search time limit 798
SSL 798
user attributes 749
least connection algorithm 436
least load algorithm 436
least load first load balancing 357
LED troubleshooting 934
legitimate e-mail 690
level-4 inspection 630
level-7 inspection 629
licensing 242
Lightweight Directory Access Protocol, see LDAP
Link Layer Discovery Protocol (LLDP ) 209
LLDP (Link Layer Discovery Protocol) 209
load balancing 258, 355
algorithms 356, 360, 362
DNS inbound 434
least load first 357
round robin 357
see also trunks 355
session-oriented 356
spillover 358
weighted round robin 357
local user database 795
log
troubleshooting 945
log messages
categories 891, 894, 897, 899, 900
debugging 236
regular 236
types of 236
log options 684, 694
(IDP) 530, 534, 659, 660, 661, 711, 712
login
custom page 853
SSL user 593
logo
troubleshooting 944
logo in SSL 587
logout
SSL user 598
Web Configurator 34
logs
and security policy 525
e-mail profiles 885
e-mailing log messages 240, 890
formats 887
log consolidation 892
settings 885
syslog servers 885
system 885
types of 885
loose source routing 667
M
MAC address 747
and VLAN 320
Ethernet interface 285
range 174
MAC authentication 761
Calling Station ID 761
case 761
delimiter 761
mac role 747
macro virus 688
mail sessions threshold 692
managed web pages 642
management access
troubleshooting 944
management access and Device HA 719
Management Information Base (MIB) 873, 874
managing the device
using SNMP. See SNMP.
MD5 573
memory usage 179
Message Digest 5, see MD5
messages
CLI 36
metrics, see reports
Microsoft

Index
USG/ZyWALL User’s Guide
991
Challenge-Handshake Authentication Protocol
(MSCHAP) 821
Challenge-Handshake Authentication Protocol
Version 2 (MSCHAP-V2) 821
Point-to-Point Encryption (MPPE) 821
mobile broadband see also cellular 304
model name 174
Monitor 540
monitor 222
SA 221
monitor profile
ADP 527
IDP 657
monitored interfaces 724
Device HA 728
mounting
rack 29, 67
wall 71
MPPE (Microsoft Point-to-Point Encryption) 821
MSCHAP (Microsoft Challenge-Handshake
Authentication Protocol) 821
MSCHAP-V2 (Microsoft Challenge-Handshake
Authentication Protocol Version 2) 821
MTU 310, 319
multicast 755
multicast rate 755
mutation virus 688
My Certificates, see also certificates 807
MyDoom 676
myZyXEL.com 25, 246
accounts, creating 26, 135
and IDP 631, 656
N
NAT 378, 395
ALG, see ALG
and address objects 375
and address objects (HOST) 398
and ALG 408, 410
and interfaces 398
and policy routes 368, 375
and security policy 520
and to-ZyWALL security policy 399
and VoIP pass through 410
and VPN 575
loopback 400
port forwarding, see NAT
port translation, see NAT
traversal 576
NAT Port Mapping Protocol 416
NAT Traversal 416
NAT-PMP 416
NBNS 290, 331, 343, 350, 365, 585
NetBIOS
Broadcast over IPSec 554
Name Server, see NBNS.
NetBIOS Name Server, see NBNS
NetMeeting 414
see also H.323
Netscape Navigator 30
network access mode 28
full tunnel 581
Network Address Translation, see NAT
network list, see SSL 586
Network Time Protocol (NTP) 836
network-based intrusions 676
Nimda 676
no IP options 667
No-IP 389
NSSA 381
O
objects 582
AAA server 793
addresses and address groups 775
authentication method 801
certificates 804
schedules 787
services and service groups 783
SSL application 822
users, user groups 736, 827
offset (patterns) 673
One-Time Password (OTP) 794
Online Certificate Status Protocol (OCSP) 819
vs CRL 819
Open Shortest Path First, see OSPF
operating mode 257
OSI (Open System Interconnection) 654, 655

Index
USG/ZyWALL User’s Guide
992
OSI level-4 630
OSI level-7 629
OSPF 381
and Ethernet interfaces 278
and RIP 382
and static routes 382
and to-ZyWALL security policy 381
area 0 382
areas, see OSPF areas
authentication method 278
autonomous system (AS) 381
backbone 382
configuration steps 383
direction 278
link cost 278
priority 279
redistribute 382
redistribute type (cost) 384, 385
routers, see OSPF routers
virtual links 383
vs RIP 379, 381
OSPF areas 381
and Ethernet interfaces 278
backbone 381
Not So Stubby Area (NSSA) 381
stub areas 381
types of 381
OSPF routers 382
area border (ABR) 382
autonomous system boundary (ASBR) 382
backbone (BR) 382
backup designated (BDR) 383
designated (DR) 383
internal (IR) 382
link state advertisements
priority 383
types of 382
OTP (One-Time Password) 794
outgoing bandwidth 310, 319
P
P2P (Peer-to-peer) 662
attacks 662
see also Peer-to-peer
packet
inspection signatures 655, 657
scan 680
statistics 190, 191, 212
packet capture 917
files 916, 919, 920
troubleshooting 945
packet captures
downloading files 916, 920, 921
padding 667
PAP (Password Authentication Protocol) 821
Password Authentication Protocol (PAP) 821
payload
option 672
size 673
Peanut Hull 389
Peer-to-peer (P2P) 662
calls 410
managing 629
Perfect Forward Secrecy (PFS) 557
Diffie-Hellman key group 578
performance
troubleshooting 938, 939
Personal Identification Number code, see PIN code
PFS (Perfect Forward Secrecy) 557, 578
physical ports
packet statistics 190, 191, 212
PIN code 310
PIN generator 794
pointer record 842
Point-to-Point Protocol over Ethernet, see PPPoE.
Point-to-Point Tunneling Protocol, see PPTP
policy enforcement in IPSec 555
policy route
troubleshooting 935, 943
policy routes 368
actions 369
and address objects 374
and ALG 410, 414
and HTTP redirect 403, 404
and interfaces 374
and NAT 368
and schedules 374, 619, 623
and service objects 784
and SMTP redirect 404
and trunks 356, 374
and user groups 373, 619, 623
and users 373, 619, 623
Index
USG/ZyWALL User’s Guide
993
and VoIP pass through 410
and VPN connections 374, 941
benefits 368
BWM 370
criteria 369
L2TP VPN 610
overriding direct routes 370
polymorphic virus 688
POP
POP2 691
POP3 691
pop-up windows 30
port forwarding, see NAT
port groups 270, 275, 276
port roles 274
and Ethernet interfaces 274
and physical ports 274
port translation, see NAT
Post Office Protocol, see POP 691
power off 933
PPP 366
troubleshooting 936
PPP interfaces
subnet mask 364
PPPoE 366
and RADIUS 366
TCP port 1723 366
PPPoE/PPTP interfaces 270, 297
and ISP accounts 298, 819
basic characteristics 270
gateway 298
subnet mask 298
PPTP 366
and GRE 366
as VPN 366
prefix delegation 273
printer
status 220
printer firmware 486
printer list 486
printer management 486
problems 934
profiles
packet inspection 657
proxy servers 403
web, see web proxy servers
PTR record 842
Public-Key Infrastructure (PKI) 805
public-private key pairs 804
Q
QoS 368, 615
query view (IDP) 659, 661
Quick Start Guide 2
R
rack-mounting 29, 67
RADIUS 794, 795
advantages 794
and IKE SA 576
and PPPoE 366
and users 737
user attributes 749
RADIUS server 877
troubleshooting 943
RDP 823
Real-time Transport Protocol, see RTP
RealVNC 823
record route 667
Reference Guide, CLI 2
registration 242
and anti-spam 693
and content filtering 638, 641
registration status
anti-virus 683
IDP 656
reject (IDP)
both 533, 659, 661, 712
receiver 533, 659, 661, 712
sender 533, 659, 661, 712
Relative Distinguished Name (RDN) 795, 796, 798
remote access IPSec 555
Remote Authentication Dial-In User Service, see
RADIUS
remote desktop connections 823
Remote Desktop Protocol
see RDP

Index
USG/ZyWALL User’s Guide
994
remote management
FTP, see FTP
see also service control 847
Telnet 870
to-Device security policy 518
WWW, see WWW
remote network 545
remote user screen links 823
replay detection 554
reports
anti-virus 228
collecting data 196
content filtering 225
daily 883
daily e-mail 883
IDP 226
specifications 197
traffic statistics 195
reset 946
RESET button 946
RFC
1058 (RIP) 379
1389 (RIP) 379
1587 (OSPF areas) 381
1631 (NAT) 378
1889 (RTP) 415
2131 (DHCP) 364
2132 (DHCP) 364
2328 (OSPF) 381
2402 (AH) 556, 577
2406 (ESP) 556, 577
2516 (PPPoE) 366
2637 (PPTP) 366
2890 (GRE) 366
3261 (SIP) 414
RIP 379
and Ethernet interfaces 278
and OSPF 379
and static routes 379
and to-ZyWALL security policyl 379
authentication 379
direction 278
redistribute 379
RIP-2 broadcasting methods 278
versions 278
vs OSPF 379
Rivest, Shamir and Adleman public-key algorithm
(RSA) 810
round robin 357
routing
troubleshooting 939
Routing Information Protocol, see RIP
routing protocols 378
and authentication algorithms 388
and Ethernet interfaces 276
RSA 810, 812, 818
RSSI threshold 755
RTLS 264
RTP 415
see also ALG 415
S
same IP 672
scan attacks 663
scanner types 689
schedule
troubleshooting 943
schedules 787
and content filtering 635, 636
and current date/time 787
and policy routes 374, 619, 623
and security policy 445, 525, 619, 623
one-time 788
recurring 788
types of 787
screen resolution 30
SecuExtender 605
Secure Hash Algorithm, see SHA1
Secure Socket Layer, see SSL
security associations, see IPSec
security policy 518
actions 525
and address groups 445
and address objects 445
and ALG 408, 410
and application patrol 629
and H.323 (ALG) 409
and HTTP redirect 403
and IPSec VPN 941
and logs 525
and NAT 520
and schedules 445, 525, 619, 623

Index
USG/ZyWALL User’s Guide
995
and service groups 524
and service objects 784
and services 524
and SIP (ALG) 409
and user groups 525, 536
and users 525, 536
and VoIP pass through 410
and zones 518, 523
asymmetrical routes 519, 522
global rules 519
priority 522
rule criteria 519
see also to-Device security policy 518
session limits 519, 534
triangle routes 519, 522
troubleshooting 936
security settings
troubleshooting 935
sensitivity level 530
serial number 174
service control 847
and to-ZyWALL security policy 847
and users 848
limitations 847
timeouts 848
service groups 784
and security policy 524
in IDP 663
service objects 783
and IP protocols 784
and policy routes 784
and security policy 784
Service Set 750
service subscription status 244
services 783
and Device HA 719
and security policy 524
Session Initiation Protocol, see SIP
session limits 519, 534
session monitor (L2TP VPN) 223
sessions 198
sessions usage 179
severity (IDP) 657, 660
SHA1 573
shell script
troubleshooting 945
shell scripts 902
and users 749
downloading 913
editing 913
how applied 903
managing 913
syntax 903
uploading 914
Short Message Service 501
shutdown 933
signal quality 206, 207
signature categories
access control 662
backdoor/Trojan 662
buffer overflow 662
DoS/DDoS 662
IM 662
P2P 662
scan 663
spam 663
virus/worm 663
Web attack 663
signature ID 661, 668, 671, 712
signatures 655
anti-virus 687
IDP 654
packet inspection 657
updating 245
SIM card 310
Simple Mail Transfer Protocol, see SMTP 691
Simple Network Management Protocol, see SNMP
Simple Traversal of UDP through NAT, see STUN
SIP 409, 414
ALG 408
and RTP 415
and security policy 409
media inactivity timeout 412
signaling inactivity timeout 413
signaling port 413
troubleshooting 940
SMS 501
configuration 501
send account information 501
ViaNett account 501
SMS gateway 501
SMTP 691
SMTP redirect
and firewall 404

Index
USG/ZyWALL User’s Guide
996
and policy routes 404
packet flow 404
SNAT 378
troubleshooting 939
SNMP 30, 872, 873
agents 873
and address groups 876
and address objects 876
and zones 876
authentication 877
Get 873
GetNext 873
Manager 873
managers 873
MIB 873, 874
network components 873
Set 873
Trap 873
traps 874
version 3 and security 873
versions 872
Snort
equivalent terms 677
rule header 677
rule options 677
signatures 677
Source Network Address Translation, see SNAT
spam 137, 517, 663, 690
spillover (for load balancing) 358
SQL slammer 676
SSH 865
and address groups 868
and address objects 868
and certificates 868
and zones 868
client requirements 867
encryption methods 867
for secure Telnet 868
how connection is established 866
versions 867
with Linux 869
with Microsoft Windows 868
SSL 581, 585, 848
access policy 581
and AAA 798
and AD 798
and LDAP 798
certificates 593
client 605
client virtual desktop logo 587
computer names 585
connection monitor 222
full tunnel mode 585
global setting 586
IP pool 585
network list 586
remote user login 593
remote user logout 598
SecuExtender 605
see also SSL VPN 581
troubleshooting 942
user application screens 598
user file sharing 599
user screen bookmarks 597
user screens 592, 596
user screens access methods 592
user screens certificates 593
user screens login 593
user screens logout 598
user screens required information 593
user screens system requirements 592
WINS 585
SSL application object 822
file sharing application 825
remote user screen links 823
summary 824
types 822
web-based 822, 825
web-based example 823
SSL policy
add 583
edit 583
objects used 582
SSL VPN 581
access policy 581
full tunnel mode 581
network access mode 28
remote desktop connections 823
see also SSL 581
troubleshooting 942
weblink 823
stac compression 822
startup-config.conf 907
and synchronization (Device HA) 732
if errors 905
missing at restart 905
present at restart 905

Index
USG/ZyWALL User’s Guide
997
startup-config-bad.conf 905
static DHCP 427
static routes 368
and interfaces 377
and OSPF 382
and RIP 379
metric 377
statistics
anti-virus 228
content filtering 225
daily e-mail report 883
IDP 226
traffic 195
status 171
streaming protocols management 629
strict source routing 667
stub area 381
STUN 410
and ALG 410
subscription services
and synchronization (Device HA) 719
SSL VPN 135, 242
SSL VPN, see also SSL VPN
status 244, 683
supported browsers 30
SWM 370
synchronization 719
and subscription services 719
information synchronized 732
password 728
port number 728
restrictions 732
syslog 887, 896
syslog servers, see also logs
system log, see logs
system name 174, 832
system reports, see reports
system uptime 175
system-default.conf 907
T
TCP 783
ACK number 672
attack packet 533, 659, 661, 712
connections 783
flag bits 672
port numbers 784
window size 672
Telnet 870
and address groups 871
and address objects 871
and zones 871
with SSH 868
throughput rate
troubleshooting 945
TightVNC 823
time 833
time servers (default) 836
time to live 667
timestamp 667
to-Device security policy
and remote management 518
global rules 518
see also security policy 518
token 794
to-ZyWALL security policy
and NAT 399
and NAT traversal (VPN) 941
and OSPF 381
and RIP 379
and service control 847
and VPN 941
TR-069 protocol 539
traffic statistics 195
Transmission Control Protocol, see TCP
transport encapsulation 556
Transport Layer Security (TLS) 872
trapdoor attacks 662
triangle routes 519
allowing through the security policy 522
vs virtual interfaces 519
Triple Data Encryption Standard, see 3DES
trojan attacks 662
troubleshooting 915, 934
admin user 943
anti-virus 935, 938
anti-virus signatures update 935
application patrol 935, 940, 943
application patrol signatures update 935
bandwidth limit 937
bandwidth management 937

Index
USG/ZyWALL User’s Guide
998
cellular 936, 937
certificate 944
configuration file 945
connection resets 940
content filter 935
DDNS 939
device access 934
ext-user 943
firmware package 942
firmware upload 945
FTP 940
H.323 940
HTTP redirect 940
IDP 935, 938
IDP signatures update 935
interface 936
Internet access 934, 942
IPSec VPN 940
LEDs 934
logo 944
logs 945
management access 944
packet capture 945
performance 938, 939
policy route 935, 943
PPP 936
RADIUS server 943
routing 939
schedules 943
security policy 936
security settings 935
shell scripts 945
SIP 940
SNAT 939
SSL 942
SSL VPN 942
throughput rate 945
VLAN 937
VPN 942
WLAN 937
zipped files 938
trunks 270, 355
and ALG 414
and policy routes 356, 374
member interface mode 361, 362
member interfaces 361, 362
see also load balancing 355
Trusted Certificates, see also certificates 814
tunnel encapsulation 556
Tunnel interfaces 270
U
UDP 783
attack packet 533, 659, 661, 712
messages 783
port numbers 784
UltraVNC 823
Universal Plug and Play 123, 416
Application 416
security issues 417
unsafe web pages 641
unsolicited commercial e-mail 137, 517, 690
updating
anti-virus signatures 245
IDP and application patrol signatures 246
signatures 245
upgrading
firmware 910
uploading
configuration files 908
firmware 910
shell scripts 913
UPnP 416
URI (Uniform Resource Identifier) 673
usage
CPU 179
flash 179
memory 179
onboard flash 179
sessions 179
user accounts
for WLAN 738
user authentication 736
external 737
local user database 795
user awareness 738
User Datagram Protocol, see UDP
user group objects 736, 827
user groups 736, 738, 827
and content filtering 635
and policy routes 373, 619, 623
and security policy 525, 536
user name

Index
USG/ZyWALL User’s Guide
999
rules 739
user objects 736, 827
user portal
links 823
logo 587
see SSL user screens 592, 596
user sessions, see sessions
user SSL screens 592, 596
access methods 592
bookmarks 597
certificates 593
login 593
logout 598
required information 593
system requirements 592
user-aware 446
users 736, 827
access, see also access users
admin (type) 736
admin, see also admin users
and AAA servers 737
and authentication method objects 737
and content filtering 635
and LDAP 737
and policy routes 373, 619, 623
and RADIUS 737
and security policy 525, 536
and service control 848
and shell scripts 749
attributes for Ext-User 737
attributes for LDAP 749
attributes for RADIUS 749
attributes in AAA servers 749
currently logged in 175
default lease time 744, 746
default reauthentication time 744, 746
default type for Ext-User 737
ext-group-user (type) 736
Ext-User (type) 737
ext-user (type) 736
groups, see user groups
Guest (type) 736
guest-manager (type) 736
lease time 741
limited-admin (type) 736
lockout 745
reauthentication time 741
types of 736
user (type) 736
user names 739
V
Vantage Report (VRPT) 887, 896
virtual interfaces 270, 293
basic characteristics 270
not DHCP clients 364
types of 293
vs asymmetrical routes 519
vs triangle routes 519
Virtual Local Area Network, see VLAN.
Virtual Local Area Network. See VLAN.
Virtual Network Computing
see VNC
Virtual Private Network, see VPN
virtual router 721, 724
virus 663
attack 134, 663, 680
boot sector 688
e-mail 688
file infector 688
life cycle 689
macro 688
mutation 688
polymorphic 688
scan 680
VLAN 313, 319
advantages 320
and MAC address 320
ID 320
troubleshooting 937
VLAN interfaces 270, 321
and Ethernet interfaces 321, 937
basic characteristics 270
virtual 293
VoIP pass through 414
and NAT 410
and policy routes 410
and security policy 410
see also ALG 408
VPN 545
active protocol 577
and NAT 575
basic troubleshooting 941
hub-and-spoke, see VPN concentrator

Index
USG/ZyWALL User’s Guide
1000
IKE SA, see IKE SA
IPSec 137, 517, 545
IPSec SA
proposal 572
security associations (SA) 547
see also IKE SA
see also IPSec 137, 517, 545
see also IPSec SA
status 175
troubleshooting 942
VPN concentrator 567
advantages 567
and IPSec SA policy enforcement 569
disadvantages 567
VPN connections
and address objects 550
and policy routes 374, 941
VPN gateways
and certificates 550
and extended authentication 550
and interfaces 550
and to-ZyWALL security policy 941
VRPT (Vantage Report) 887, 896
W
wall-mounting 71
warranty 960, 968
note 960, 968
Web attack 663
Web Configurator 29
access 31
access users 746
requirements 30
supported browsers 30
web features
ActiveX 649
cookies 649
Java 649
web proxy servers 649
web proxy servers 403, 649
web-based SSL application 822
configuration example 823
create 825
weblink 823
weighted round robin (for load balancing) 357
weighted round robin algorithm 436
WEP (Wired Equivalent Privacy) 750
white list (anti-spam) 690, 694, 699, 700
Wi-Fi Protected Access 750
Windows Internet Naming Service, see WINS
Windows Internet Naming Service, see WINS.
Windows Remote Desktop 823
WINS 290, 331, 343, 350, 365, 585
in L2TP VPN 612
WINS server 290, 612
Wireshark 674
Wizard Setup 47, 138
WLAN
troubleshooting 937
user accounts 738
WLAN interfaces 270
worm 134, 663, 680
attacks 663
WPA 750
WPA2 750
WWW 849
and address groups 853
and address objects 853
and authentication method objects 852
and certificates 850
and zones 853
see also HTTP, HTTPS 849
Z
zipped files
troubleshooting 938
ZON Utility 880
zones 733
and FTP 872
and interfaces 733
and security policy 518, 523
and SNMP 876
and SSH 868
and Telnet 871
and VPN 733
and WWW 853
extra-zone traffic 734
inter-zone traffic 734
intra-zone traffic 734